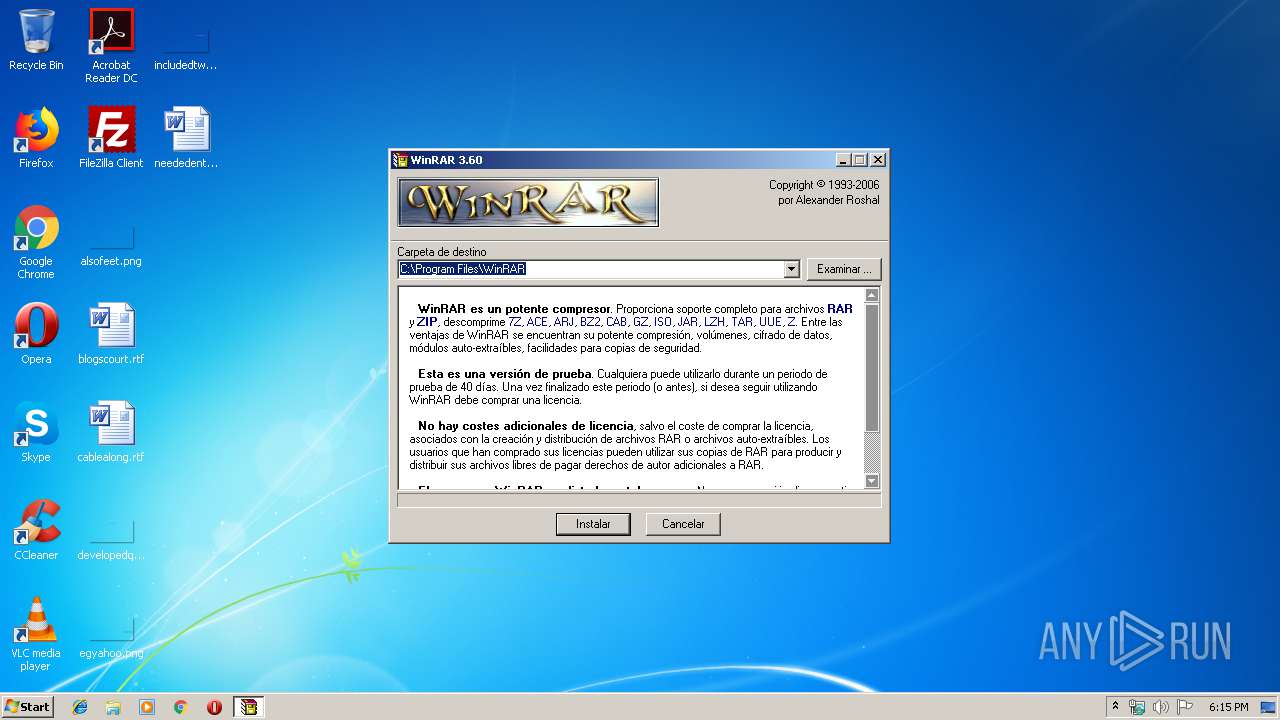
| File name: | wrar360es.exe |
| Full analysis: | https://app.any.run/tasks/22681082-73c7-4e8b-b31d-8b33560f0541 |
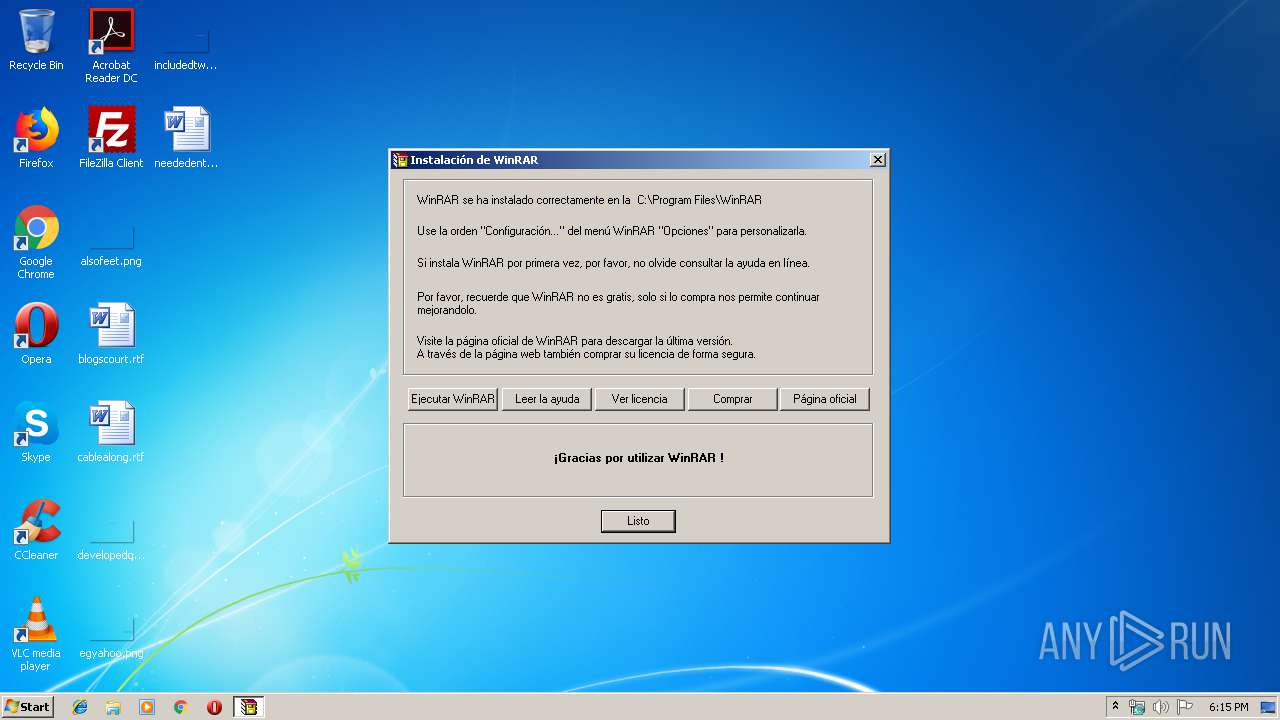
| Verdict: | Malicious activity |
| Analysis date: | January 17, 2020, 18:14:56 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | AA8E61781A7DAEDCA2C7F6905F0F4599 |
| SHA1: | 49D70F5A490DDDAA3E24220850F27914707173EB |
| SHA256: | 61C8460CE3F011C6EB2CA4768EF4F77CD2E7EAA0F75A6BAB87BE9FEEE28A7BEF |
| SSDEEP: | 24576:gab4tAOnh0ai6C3tT7YtB+xHpn6ZS9OLvHuZrGN201G7TXz:1Elh29IP+xp6ZSYLvHuxGN27Tj |
MALICIOUS
Application was dropped or rewritten from another process
- uninstall.exe (PID: 3048)
- WinRAR.exe (PID: 956)
Loads dropped or rewritten executable
- WinRAR.exe (PID: 956)
SUSPICIOUS
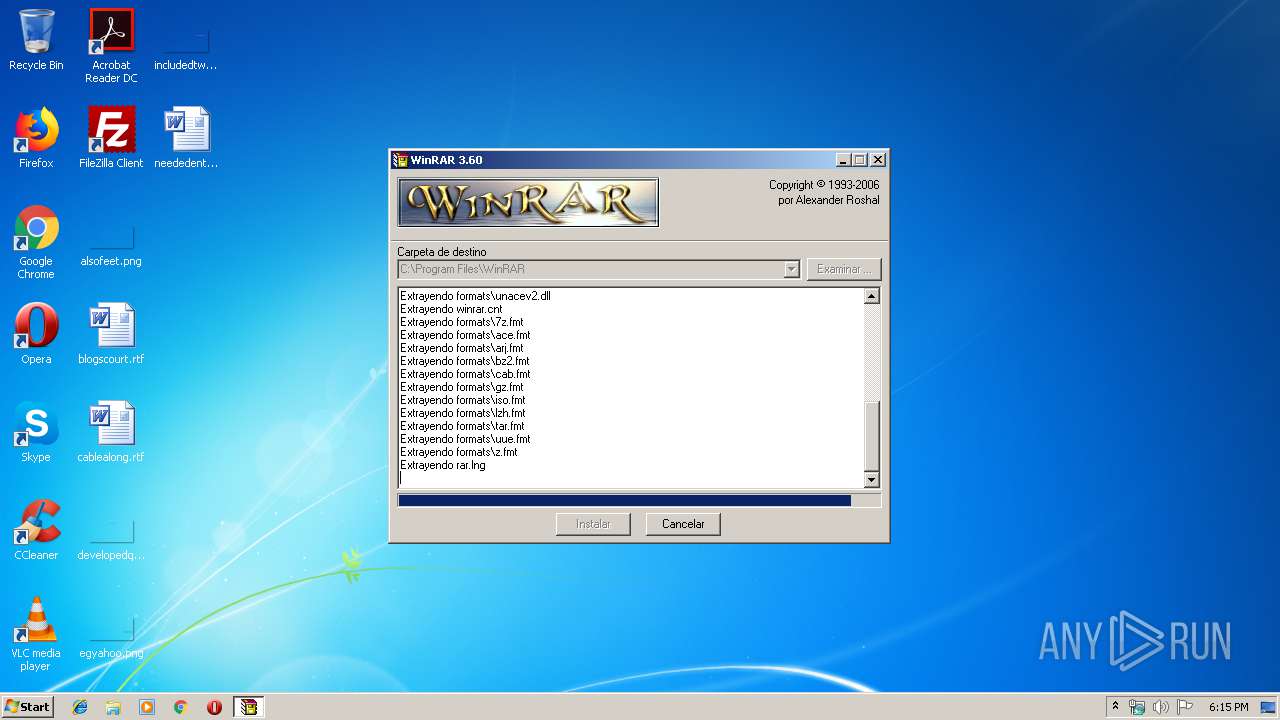
Executable content was dropped or overwritten
- wrar360es.exe (PID: 2924)
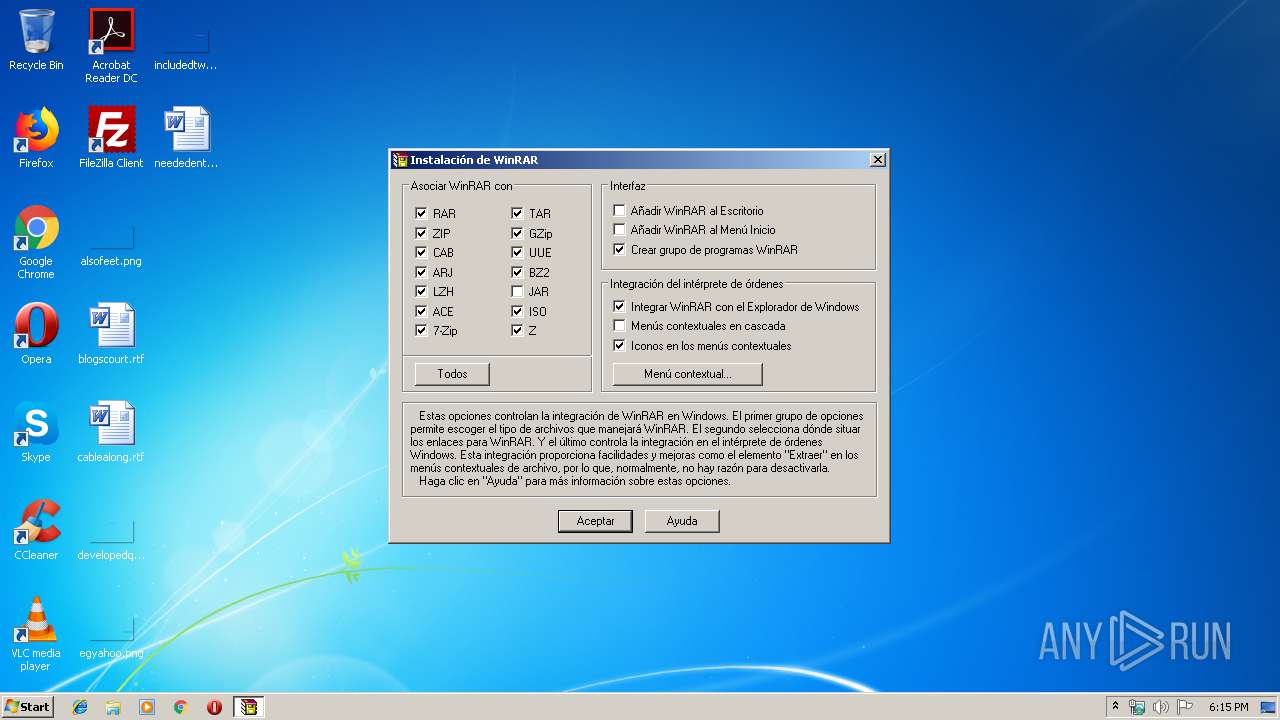
Creates COM task schedule object
- uninstall.exe (PID: 3048)
Creates files in the program directory
- wrar360es.exe (PID: 2924)
- uninstall.exe (PID: 3048)
Creates a software uninstall entry
- uninstall.exe (PID: 3048)
Modifies the open verb of a shell class
- uninstall.exe (PID: 3048)
Starts Microsoft Office Application
- WinRAR.exe (PID: 956)
Reads internet explorer settings
- wrar360es.exe (PID: 2924)
INFO
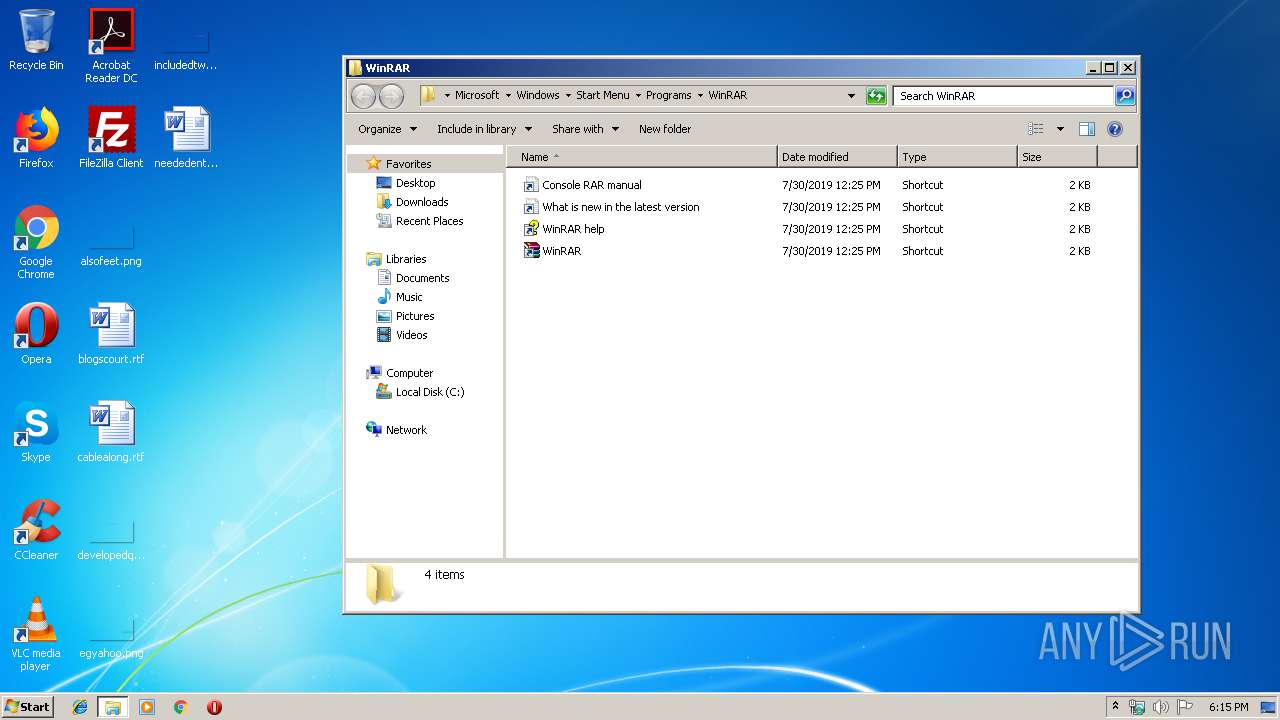
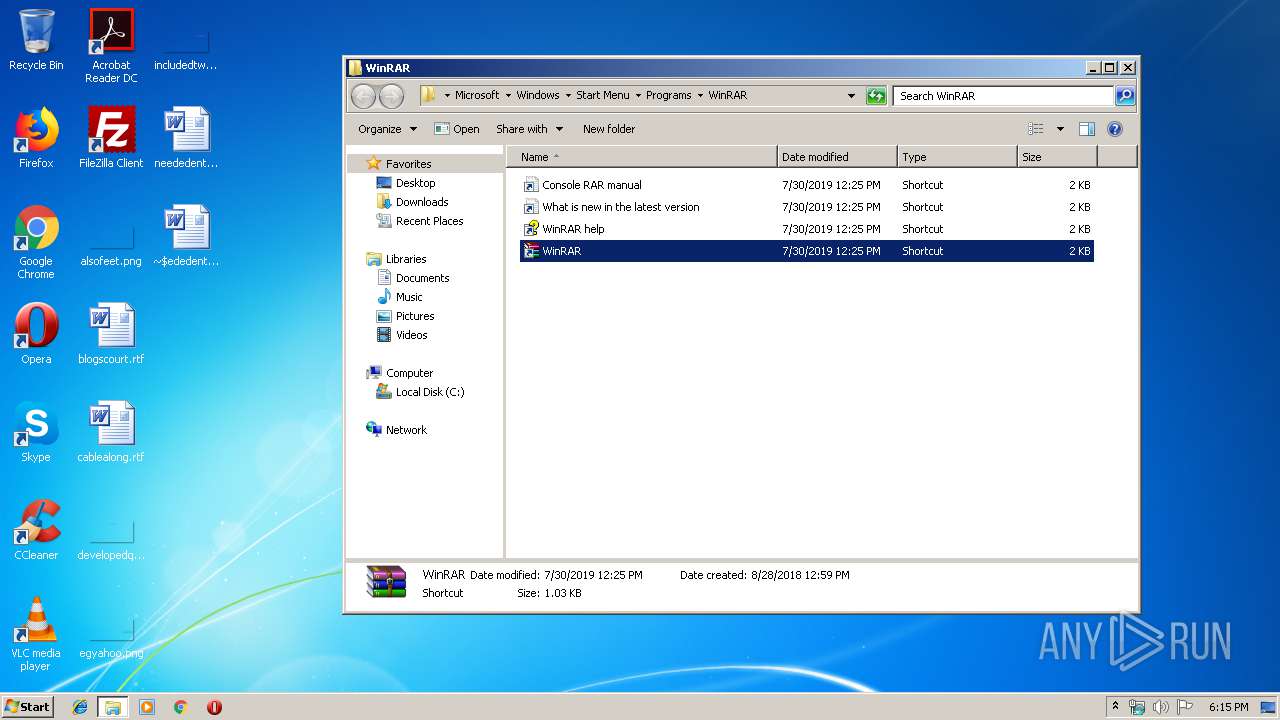
Manual execution by user
- WinRAR.exe (PID: 956)
Creates files in the user directory
- WINWORD.EXE (PID: 3804)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 3804)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | WinRAR Self Extracting archive (94.8) |
|---|---|---|
| .scr | | | Windows screen saver (2.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (1.2) |
| .exe | | | Win32 Executable (generic) (0.8) |
| .exe | | | Generic Win/DOS Executable (0.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2006:08:04 20:28:14+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 5 |
| CodeSize: | 65536 |
| InitializedDataSize: | 12288 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1000 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 04-Aug-2006 18:28:14 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000200 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 04-Aug-2006 18:28:14 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00010000 | 0x00010000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 6.39482 |
.data | 0x00011000 | 0x00003000 | 0x00000A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.66492 |
.idata | 0x00014000 | 0x00001000 | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.78568 |
.rsrc | 0x00015000 | 0x00006000 | 0x00006000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.72741 |
.sdata | 0x0001B000 | 0x00012000 | 0x00012000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.10885 | 531 | UNKNOWN | Russian - Russia | RT_MANIFEST |
2 | 4.38844 | 1384 | UNKNOWN | Russian - Russia | RT_ICON |
3 | 3.39424 | 744 | UNKNOWN | Russian - Russia | RT_ICON |
4 | 3.4927 | 296 | UNKNOWN | Russian - Russia | RT_ICON |
7 | 3.24143 | 556 | UNKNOWN | Russian - Russia | RT_STRING |
8 | 3.30032 | 886 | UNKNOWN | Russian - Russia | RT_STRING |
9 | 3.01893 | 512 | UNKNOWN | Russian - Russia | RT_STRING |
100 | 2.6902 | 62 | UNKNOWN | Russian - Russia | RT_GROUP_ICON |
TITLE_BMP | 7.69131 | 14000 | UNKNOWN | Russian - Russia | RT_BITMAP |
LICENSEDLG | 3.24243 | 216 | UNKNOWN | Russian - Russia | RT_DIALOG |
Imports
ADVAPI32.DLL |
COMCTL32.DLL |
COMDLG32.DLL |
GDI32.DLL |
KERNEL32.DLL |
OLE32.DLL |
SHELL32.DLL |
USER32.DLL |
Total processes
46
Monitored processes
6
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 640 | "C:\Users\admin\AppData\Local\Temp\wrar360es.exe" | C:\Users\admin\AppData\Local\Temp\wrar360es.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
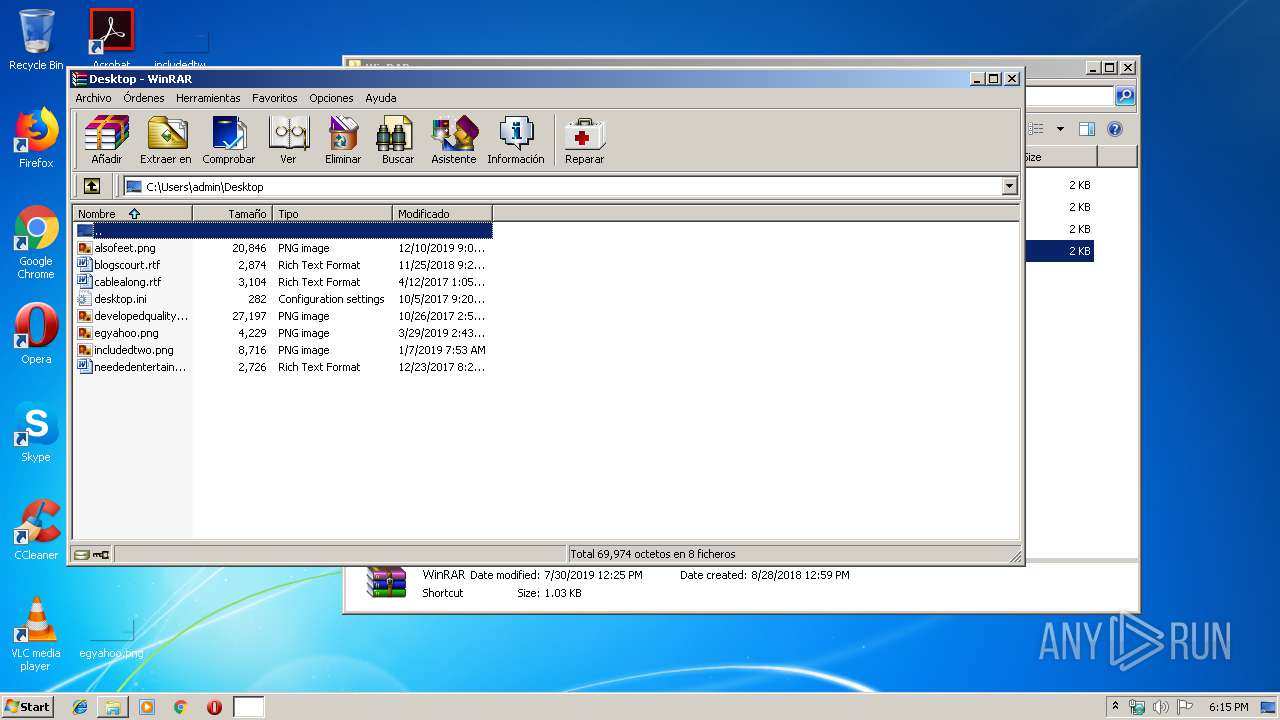
| 956 | "C:\Program Files\WinRAR\WinRAR.exe" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2132 | "C:\Program Files\WinRAR\uninstall.exe" /clean | C:\Program Files\WinRAR\uninstall.exe | — | wrar360es.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: HIGH Description: Uninstall WinRAR Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 2924 | "C:\Users\admin\AppData\Local\Temp\wrar360es.exe" | C:\Users\admin\AppData\Local\Temp\wrar360es.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 3048 | "C:\Program Files\WinRAR\uninstall.exe" /setup | C:\Program Files\WinRAR\uninstall.exe | — | wrar360es.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
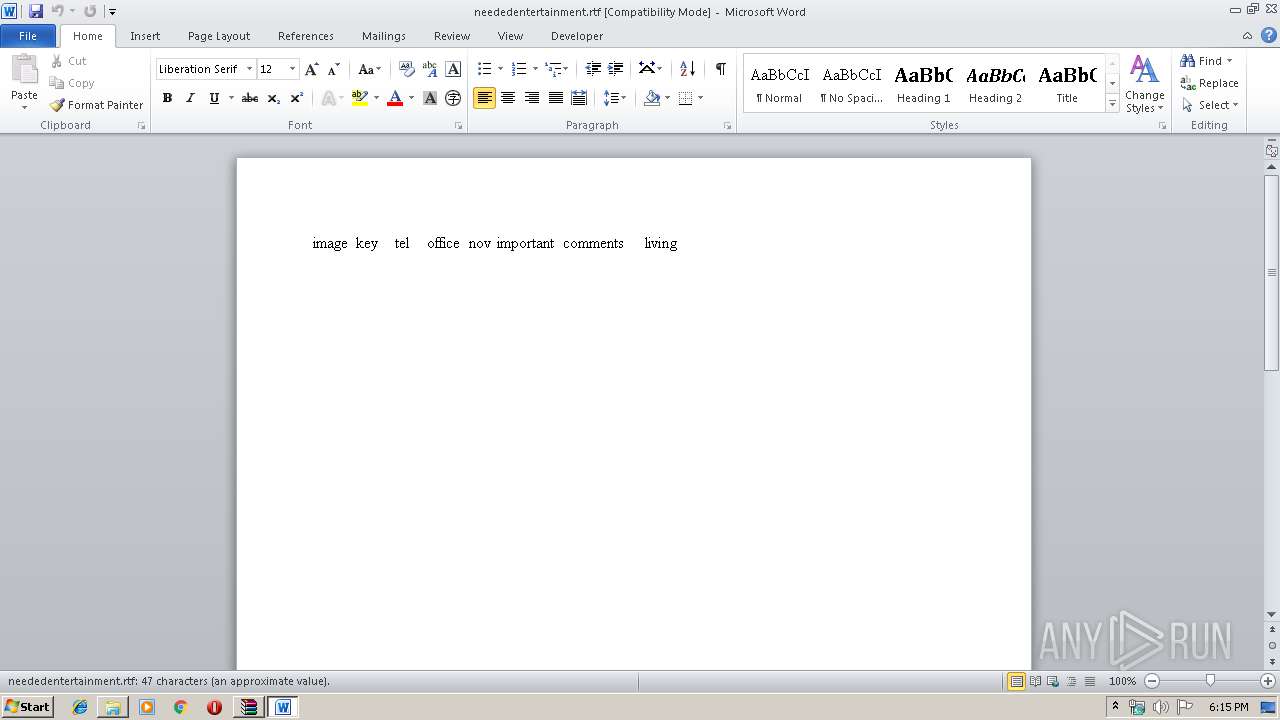
| 3804 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\neededentertainment.rtf" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | WinRAR.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
Total events
2 125
Read events
1 543
Write events
434
Delete events
148
Modification events
| (PID) Process: | (2924) wrar360es.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\wrar360es_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (2924) wrar360es.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\wrar360es_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (2924) wrar360es.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\wrar360es_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (2924) wrar360es.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\wrar360es_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (2924) wrar360es.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\wrar360es_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (2924) wrar360es.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\wrar360es_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (2924) wrar360es.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\wrar360es_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (2924) wrar360es.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\wrar360es_RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (2924) wrar360es.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\wrar360es_RASMANCS |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (2924) wrar360es.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\wrar360es_RASMANCS |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
Executable files
23
Suspicious files
0
Text files
19
Unknown types
19
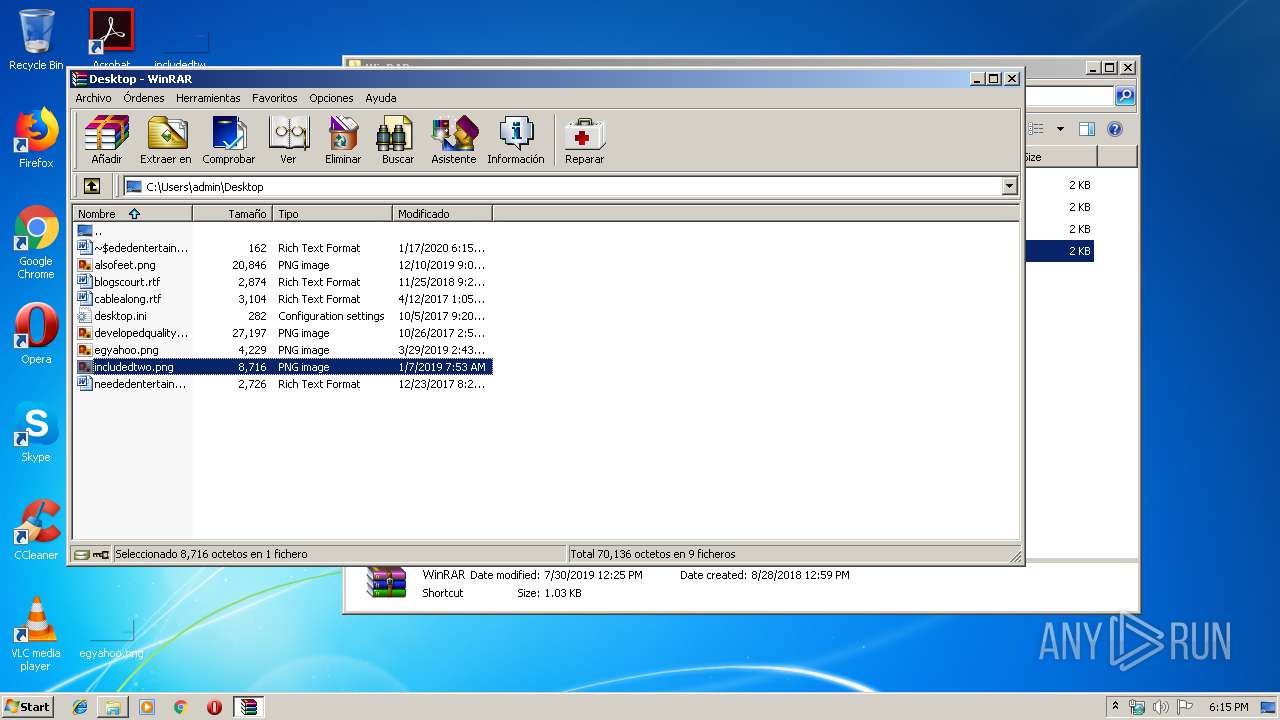
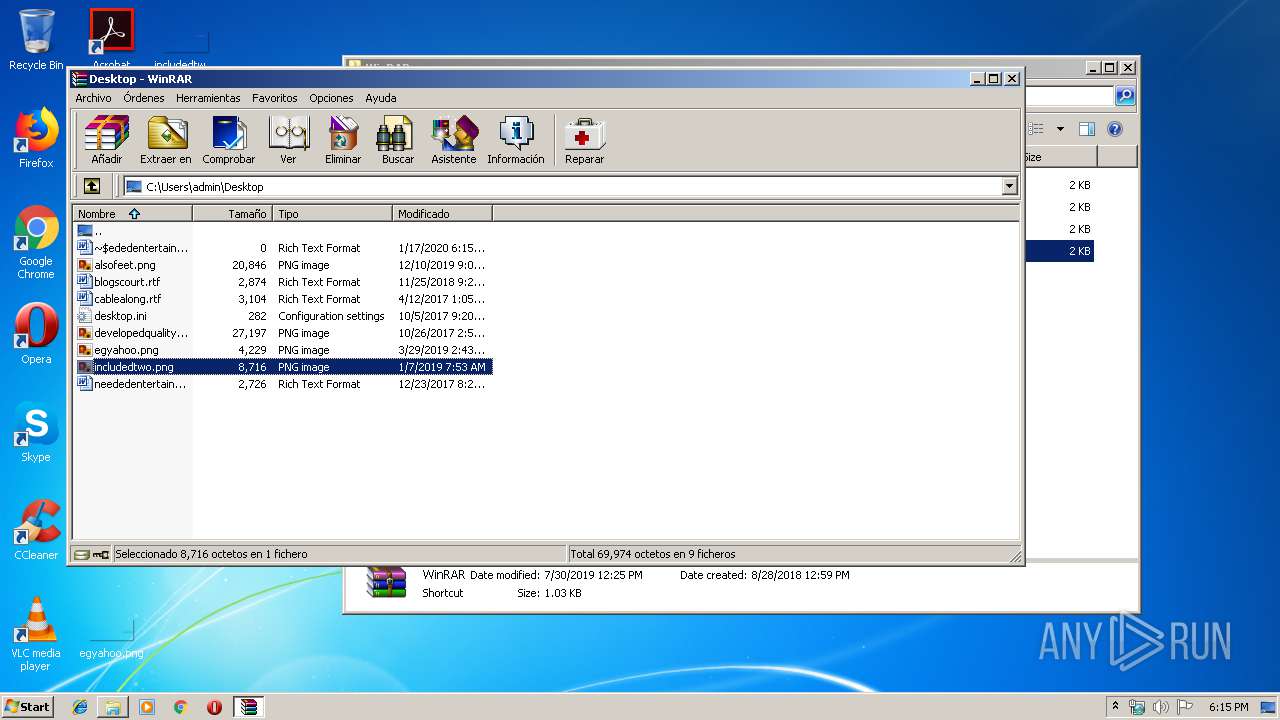
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2924 | wrar360es.exe | C:\Program Files\WinRAR\licencia.txt | text | |
MD5:— | SHA256:— | |||
| 2924 | wrar360es.exe | C:\Program Files\WinRAR\file_id.diz | text | |
MD5:— | SHA256:— | |||
| 2924 | wrar360es.exe | C:\Program Files\WinRAR\leame.txt | text | |
MD5:— | SHA256:— | |||
| 2924 | wrar360es.exe | C:\Program Files\WinRAR\unrarsrc.txt | text | |
MD5:— | SHA256:— | |||
| 2924 | wrar360es.exe | C:\Program Files\WinRAR\uninstall.lst | text | |
MD5:— | SHA256:— | |||
| 2924 | wrar360es.exe | C:\Program Files\WinRAR\order.htm | html | |
MD5:— | SHA256:— | |||
| 2924 | wrar360es.exe | C:\Program Files\WinRAR\winrar.hlp | hlp | |
MD5:— | SHA256:— | |||
| 2924 | wrar360es.exe | C:\Program Files\WinRAR\descript.ion | text | |
MD5:— | SHA256:— | |||
| 2924 | wrar360es.exe | C:\Program Files\WinRAR\notastec.txt | text | |
MD5:— | SHA256:— | |||
| 2924 | wrar360es.exe | C:\Program Files\WinRAR\whatsnew.txt | text | |
MD5:5CEA4A3B60BD6B3396C365A5EB3DA952 | SHA256:96BB401E9F529A8CAF849C7ED81F6848393D4427E68B7A5988D96675E898D747 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report