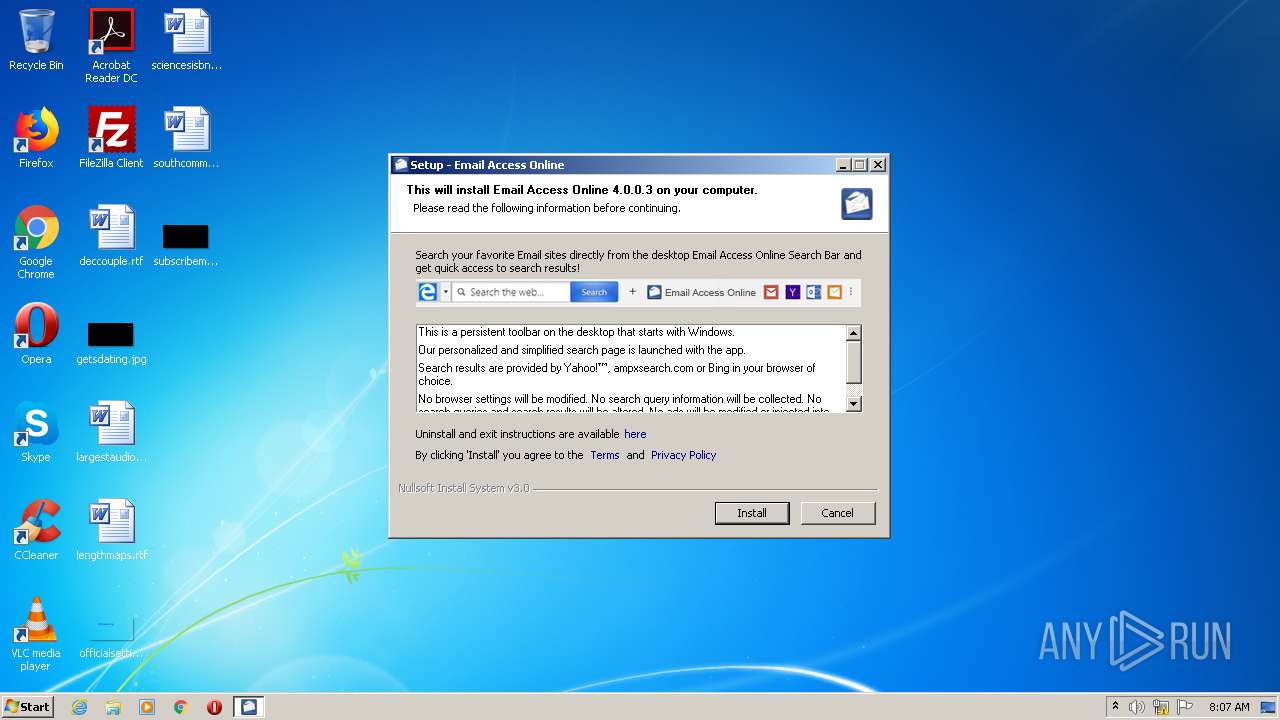
| File name: | installer_.exe |
| Full analysis: | https://app.any.run/tasks/1b9041d6-745c-4048-a80a-0e42cdb49ed1 |
| Verdict: | Malicious activity |
| Analysis date: | October 20, 2020, 07:07:07 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | F94C6C3AC2C9338D5304FB7996F91D2D |
| SHA1: | 61F27DCC47054978060947175AD4E72799663846 |
| SHA256: | 61C5BF4BDD651CADAB7398B4FFA20D48BF1DEFD15DCA9B16A4BD3AC56F6CF4B1 |
| SSDEEP: | 12288:tgHo2o0oPDDOIhXPNRTZv5nwbqzoB92ONBfKvR81bghnUgVHwgfl:co0orDFhfN7v9yB9pNBfMRgMn3VF |
MALICIOUS
Loads dropped or rewritten executable
- installer_.exe (PID: 1856)
Application was dropped or rewritten from another process
- Email Access Online.exe (PID: 3320)
SUSPICIOUS
Reads Internet Cache Settings
- Email Access Online.exe (PID: 3320)
Changes IE settings (feature browser emulation)
- Email Access Online.exe (PID: 3320)
Executable content was dropped or overwritten
- installer_.exe (PID: 1856)
Creates a software uninstall entry
- Email Access Online.exe (PID: 3320)
- installer_.exe (PID: 1856)
Reads internet explorer settings
- Email Access Online.exe (PID: 3320)
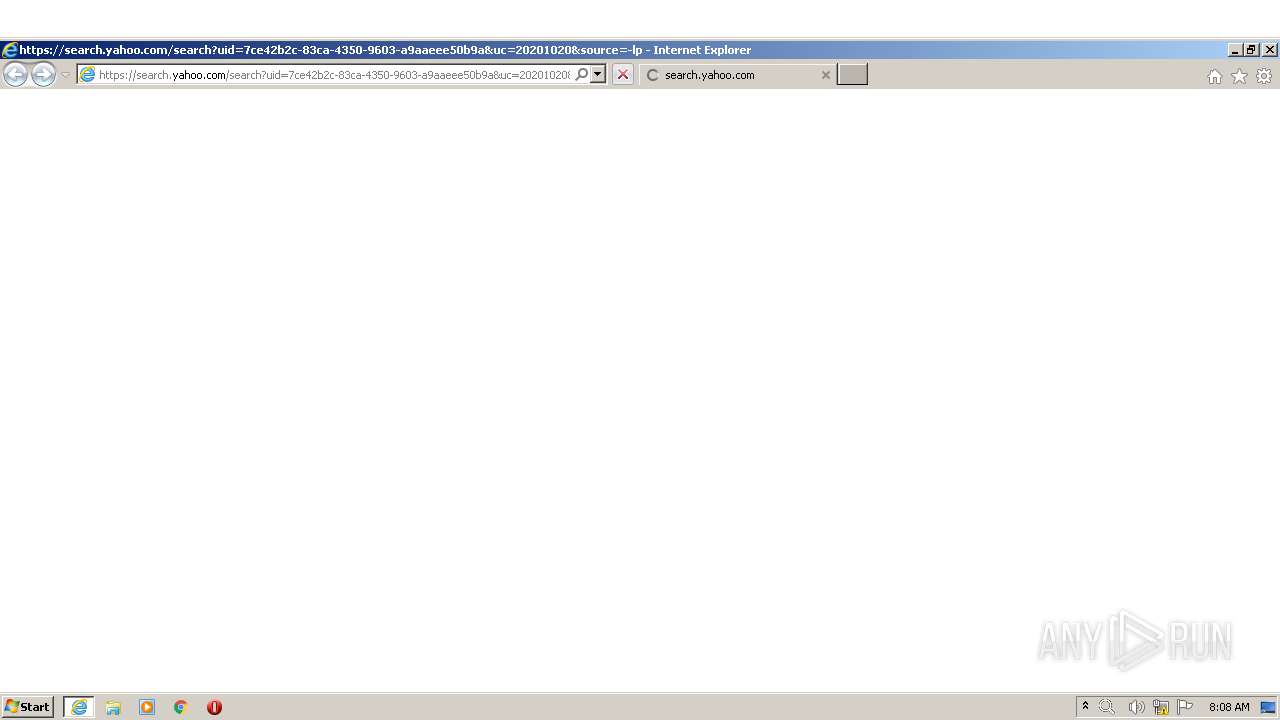
Starts Internet Explorer
- Email Access Online.exe (PID: 3320)
INFO
Reads settings of System Certificates
- IEXPLORE.EXE (PID: 3836)
- IEXPLORE.EXE (PID: 884)
Changes internet zones settings
- IEXPLORE.EXE (PID: 884)
Reads Internet Cache Settings
- IEXPLORE.EXE (PID: 3836)
- IEXPLORE.EXE (PID: 884)
Reads internet explorer settings
- IEXPLORE.EXE (PID: 3836)
Application launched itself
- IEXPLORE.EXE (PID: 884)
Adds / modifies Windows certificates
- IEXPLORE.EXE (PID: 884)
Changes settings of System certificates
- IEXPLORE.EXE (PID: 884)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2016:07:25 02:55:51+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 25088 |
| InitializedDataSize: | 141824 |
| UninitializedDataSize: | 2048 |
| EntryPoint: | 0x33b6 |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 4.0.0.3 |
| ProductVersionNumber: | 4.0.0.3 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | ASCII |
| CompanyName: | Better Cloud Solutions LTD |
| FileDescription: | Desktop web search |
| FileVersion: | 4.0.0.3 |
| LegalCopyright: | (c) 2019 Better Cloud Solutions LTD |
| OriginalFileName: | SBInstaller |
| ProductName: | Desktop Search Bar |
| ProductVersion: | 4.0.0.3 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 25-Jul-2016 00:55:51 |
| Detected languages: |
|
| CompanyName: | Better Cloud Solutions LTD |
| FileDescription: | Desktop web search |
| FileVersion: | 4.0.0.3 |
| LegalCopyright: | (c) 2019 Better Cloud Solutions LTD |
| OriginalFilename: | SBInstaller |
| ProductName: | Desktop Search Bar |
| ProductVersion: | 4.0.0.3 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000C8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 25-Jul-2016 00:55:51 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0000615D | 0x00006200 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.45023 |
.rdata | 0x00008000 | 0x000013A4 | 0x00001400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.163 |
.data | 0x0000A000 | 0x00020338 | 0x00000600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.9824 |
.ndata | 0x0002B000 | 0x0002A000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x00055000 | 0x00007C50 | 0x00007E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.04475 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.29536 | 1058 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 6.01823 | 9640 | UNKNOWN | English - United States | RT_ICON |
3 | 6.44112 | 4264 | UNKNOWN | English - United States | RT_ICON |
4 | 6.6049 | 2440 | UNKNOWN | English - United States | RT_ICON |
5 | 6.45535 | 1128 | UNKNOWN | English - United States | RT_ICON |
6 | 0 | 744 | UNKNOWN | English - United States | RT_ICON |
7 | 0 | 296 | UNKNOWN | English - United States | RT_ICON |
103 | 2.82942 | 104 | UNKNOWN | English - United States | RT_GROUP_ICON |
105 | 2.73893 | 514 | UNKNOWN | English - United States | RT_DIALOG |
106 | 2.91148 | 248 | UNKNOWN | English - United States | RT_DIALOG |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
ole32.dll |
Total processes
41
Monitored processes
4
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 884 | "C:\Program Files\Internet Explorer\IEXPLORE.EXE" https://search.yahoo.com/search?uid=7ce42b2c-83ca-4350-9603-a9aaeee50b9a&uc=20201020&source=-lp0-bb8-sbe&i_id=email_&ap=appfocus1 | C:\Program Files\Internet Explorer\IEXPLORE.EXE | Email Access Online.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 1856 | "C:\Users\admin\AppData\Local\Temp\installer_.exe" | C:\Users\admin\AppData\Local\Temp\installer_.exe | explorer.exe | ||||||||||||
User: admin Company: Better Cloud Solutions LTD Integrity Level: MEDIUM Description: Desktop web search Exit code: 0 Version: 4.0.0.3 Modules
| |||||||||||||||
| 3320 | "C:\Users\admin\AppData\Local\Email Access Online\Email Access Online.exe" /firstrun | C:\Users\admin\AppData\Local\Email Access Online\Email Access Online.exe | installer_.exe | ||||||||||||
User: admin Company: SpringTech Ltd Integrity Level: MEDIUM Description: Desktop web search Exit code: 0 Version: 4.0.0.3 Modules
| |||||||||||||||
| 3836 | "C:\Program Files\Internet Explorer\IEXPLORE.EXE" SCODEF:884 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\IEXPLORE.EXE | IEXPLORE.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
1 060
Read events
974
Write events
85
Delete events
1
Modification events
| (PID) Process: | (1856) installer_.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Uninstall\Email Access Online |
| Operation: | write | Name: | UninstallImp |
Value: {"domain":"hemailaccessonline.com","iid":"bio-sbe-email","partner":true,"source":"-lp0-bb8-sbe","ua":"SB","uc":"20201020","uid":true}
| |||
| (PID) Process: | (1856) installer_.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Uninstall\Email Access Online |
| Operation: | write | Name: | DisplayIcon |
Value: C:\Users\admin\AppData\Local\Email Access Online\Icon.ico | |||
| (PID) Process: | (1856) installer_.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Uninstall\Email Access Online |
| Operation: | write | Name: | DisplayName |
Value: Email Access Online | |||
| (PID) Process: | (1856) installer_.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Uninstall\Email Access Online |
| Operation: | write | Name: | UninstallString |
Value: "C:\Users\admin\AppData\Local\Email Access Online\uninstall.exe" Email Access Online | |||
| (PID) Process: | (1856) installer_.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Uninstall\Email Access Online |
| Operation: | write | Name: | Publisher |
Value: Better Cloud Solutions LTD | |||
| (PID) Process: | (1856) installer_.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Uninstall\Email Access Online |
| Operation: | write | Name: | NoModify |
Value: 1 | |||
| (PID) Process: | (1856) installer_.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Uninstall\Email Access Online |
| Operation: | write | Name: | NoRepair |
Value: 1 | |||
| (PID) Process: | (1856) installer_.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Uninstall\Email Access Online |
| Operation: | write | Name: | InstallLocation |
Value: C:\Users\admin\AppData\Local\Email Access Online | |||
| (PID) Process: | (1856) installer_.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Uninstall\Email Access Online |
| Operation: | write | Name: | DisplayVersion |
Value: 4.0.0.3 | |||
| (PID) Process: | (1856) installer_.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Uninstall\Email Access Online |
| Operation: | write | Name: | EstimatedSize |
Value: 1538 | |||
Executable files
5
Suspicious files
10
Text files
30
Unknown types
7
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1856 | installer_.exe | C:\Users\admin\AppData\Local\Temp\nst426E.tmp | — | |
MD5:— | SHA256:— | |||
| 3320 | Email Access Online.exe | C:\Users\admin\AppData\Local\Temp\Cab8409.tmp | — | |
MD5:— | SHA256:— | |||
| 3320 | Email Access Online.exe | C:\Users\admin\AppData\Local\Temp\Tar840A.tmp | — | |
MD5:— | SHA256:— | |||
| 3320 | Email Access Online.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\6Z2BCOUL\jquery_min[1] | — | |
MD5:— | SHA256:— | |||
| 3320 | Email Access Online.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\PO2HN1X2\jquery_min[1] | — | |
MD5:— | SHA256:— | |||
| 1856 | installer_.exe | C:\Users\admin\AppData\Local\Temp\nst426F.tmp\npHelper.dll | executable | |
MD5:— | SHA256:— | |||
| 3320 | Email Access Online.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\PO2HN1X2\suggest[1] | html | |
MD5:— | SHA256:— | |||
| 1856 | installer_.exe | C:\Users\admin\AppData\Local\Email Access Online\Email Access Online.exe | executable | |
MD5:— | SHA256:— | |||
| 3320 | Email Access Online.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\6Z2BCOUL\main_templates[1] | html | |
MD5:— | SHA256:— | |||
| 1856 | installer_.exe | C:\Users\admin\AppData\Local\Email Access Online\Uninstall.exe | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
18
DNS requests
8
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3320 | Email Access Online.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfqhLjKLEJQZPin0KCzkdAQpVYowQUsT7DaQP4v0cB1JgmGggC72NkK8MCEATh56TcXPLzbcArQrhdFZ8%3D | US | der | 471 b | whitelisted |
3836 | IEXPLORE.EXE | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTPJvUY%2Bsl%2Bj4yzQuAcL2oQno5fCgQUUWj%2FkK8CB3U8zNllZGKiErhZcjsCEA5YO%2Bg3NjOtZ72iw7%2B2Ct4%3D | US | der | 471 b | whitelisted |
3836 | IEXPLORE.EXE | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTPJvUY%2Bsl%2Bj4yzQuAcL2oQno5fCgQUUWj%2FkK8CB3U8zNllZGKiErhZcjsCEA%2Fs6XNNrlNEzESYih72LPo%3D | US | der | 471 b | whitelisted |
3836 | IEXPLORE.EXE | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTPJvUY%2Bsl%2Bj4yzQuAcL2oQno5fCgQUUWj%2FkK8CB3U8zNllZGKiErhZcjsCEA%2Fs6XNNrlNEzESYih72LPo%3D | US | der | 471 b | whitelisted |
884 | IEXPLORE.EXE | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
3836 | IEXPLORE.EXE | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTPJvUY%2Bsl%2Bj4yzQuAcL2oQno5fCgQUUWj%2FkK8CB3U8zNllZGKiErhZcjsCEA5YO%2Bg3NjOtZ72iw7%2B2Ct4%3D | US | der | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3836 | IEXPLORE.EXE | 212.82.100.137:443 | search.yahoo.com | Yahoo! UK Services Limited | CH | shared |
3836 | IEXPLORE.EXE | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3836 | IEXPLORE.EXE | 52.50.125.148:443 | guce.yahoo.com | Amazon.com, Inc. | IE | unknown |
3836 | IEXPLORE.EXE | 87.248.118.23:443 | s.yimg.com | Yahoo! UK Services Limited | GB | malicious |
884 | IEXPLORE.EXE | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
884 | IEXPLORE.EXE | 87.248.118.23:443 | s.yimg.com | Yahoo! UK Services Limited | GB | malicious |
3836 | IEXPLORE.EXE | 54.229.241.143:443 | guce.yahoo.com | Amazon.com, Inc. | IE | unknown |
— | — | 87.248.118.23:443 | s.yimg.com | Yahoo! UK Services Limited | GB | malicious |
3320 | Email Access Online.exe | 212.82.100.137:443 | search.yahoo.com | Yahoo! UK Services Limited | CH | shared |
3320 | Email Access Online.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
search.yahoo.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
guce.yahoo.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
consent.yahoo.com |
| whitelisted |
s.yimg.com |
| shared |