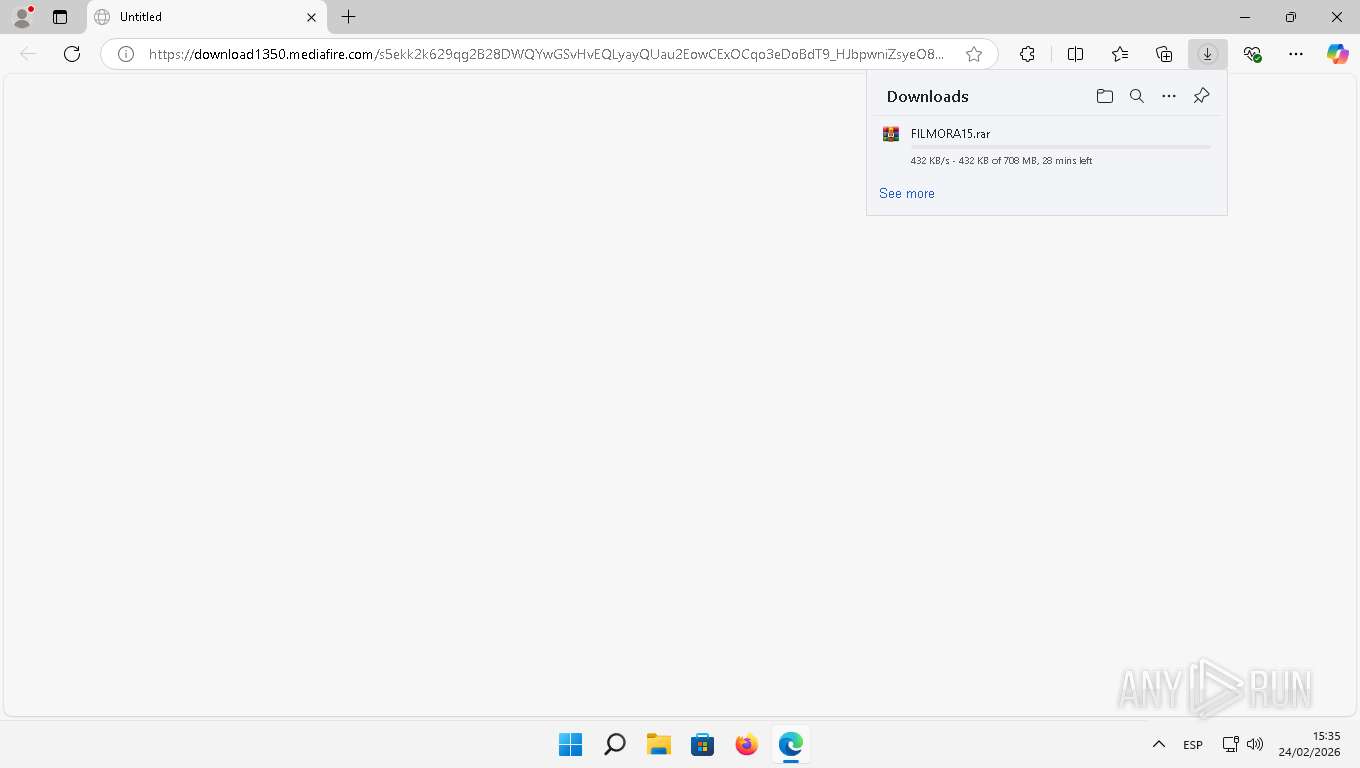
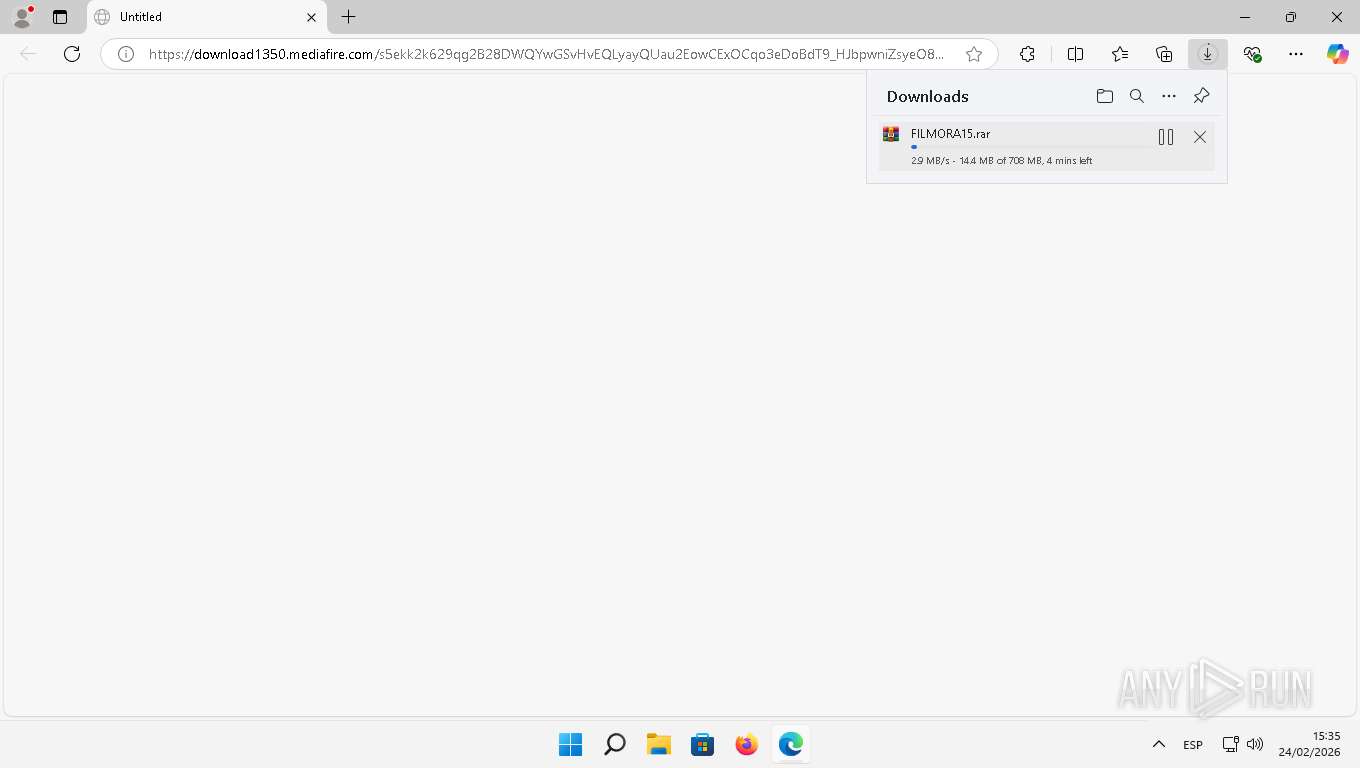
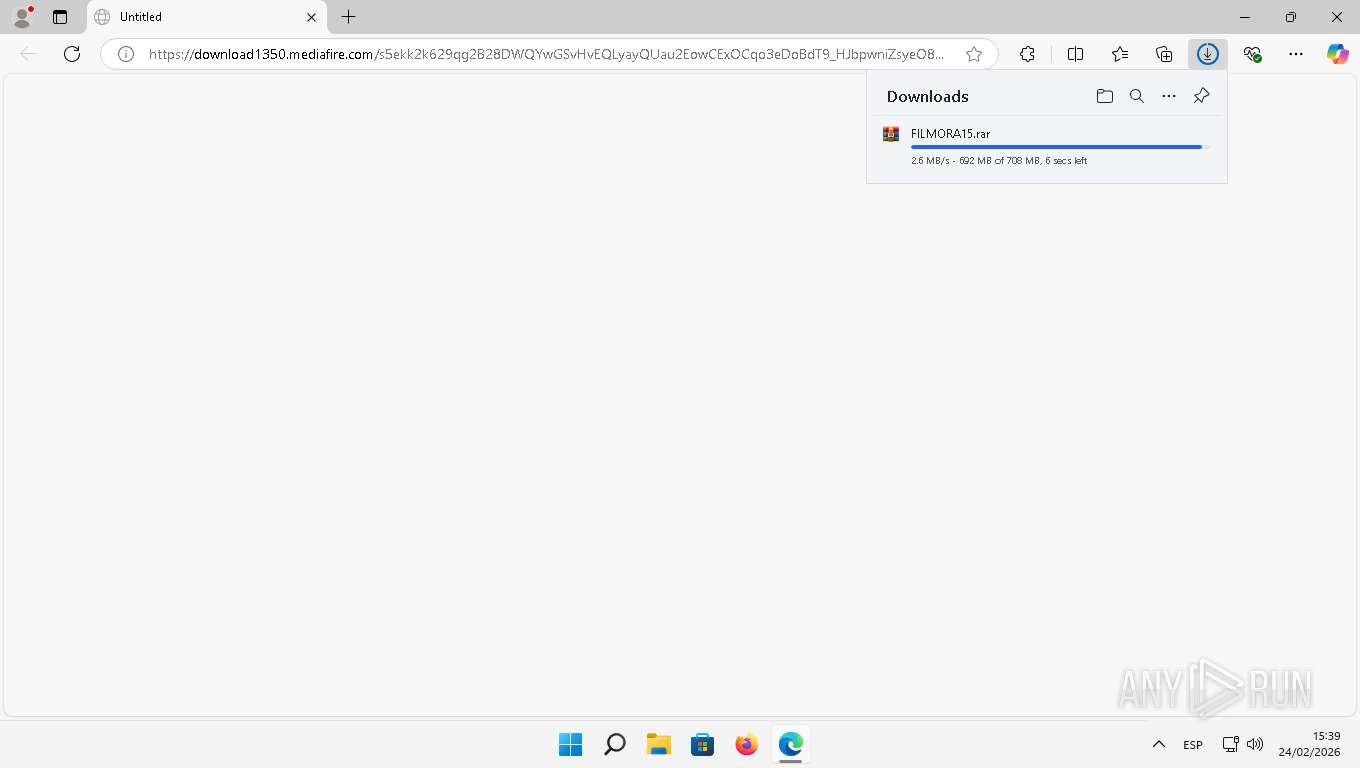
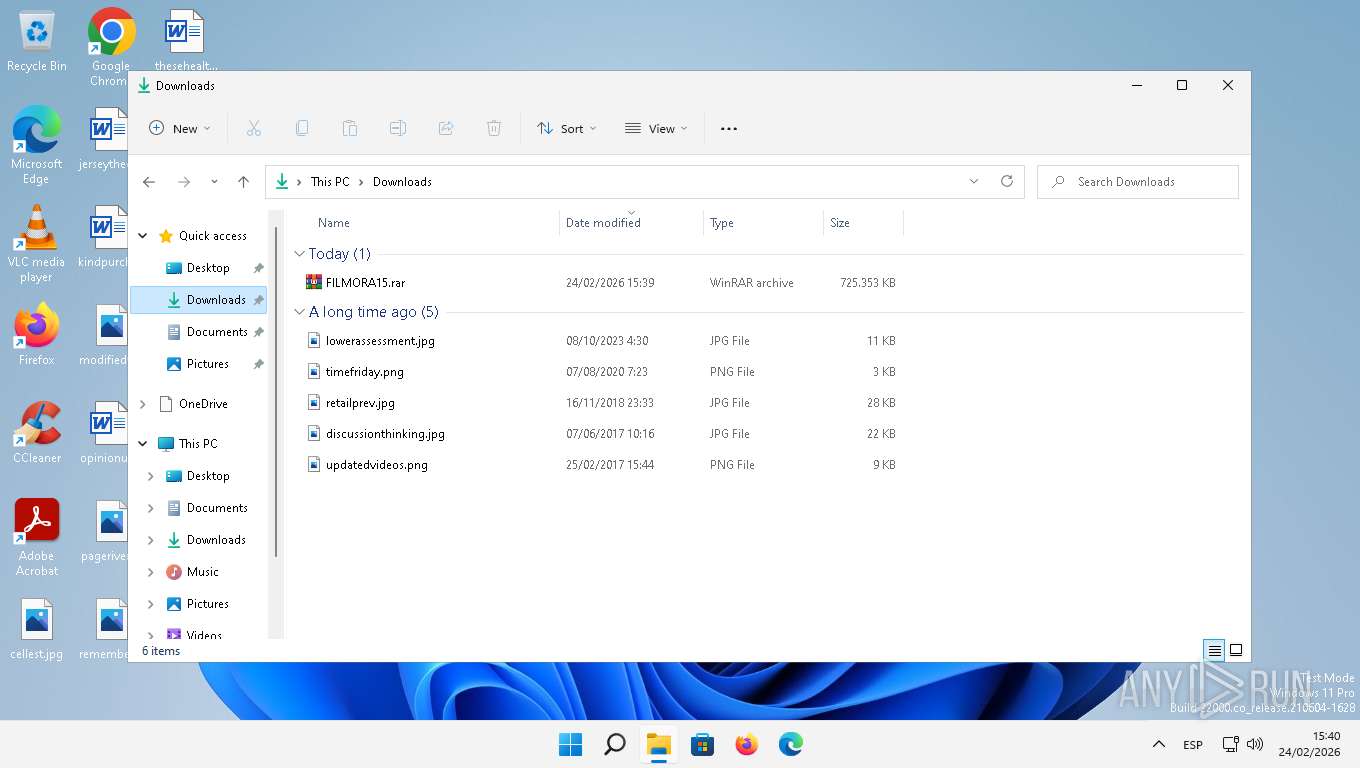
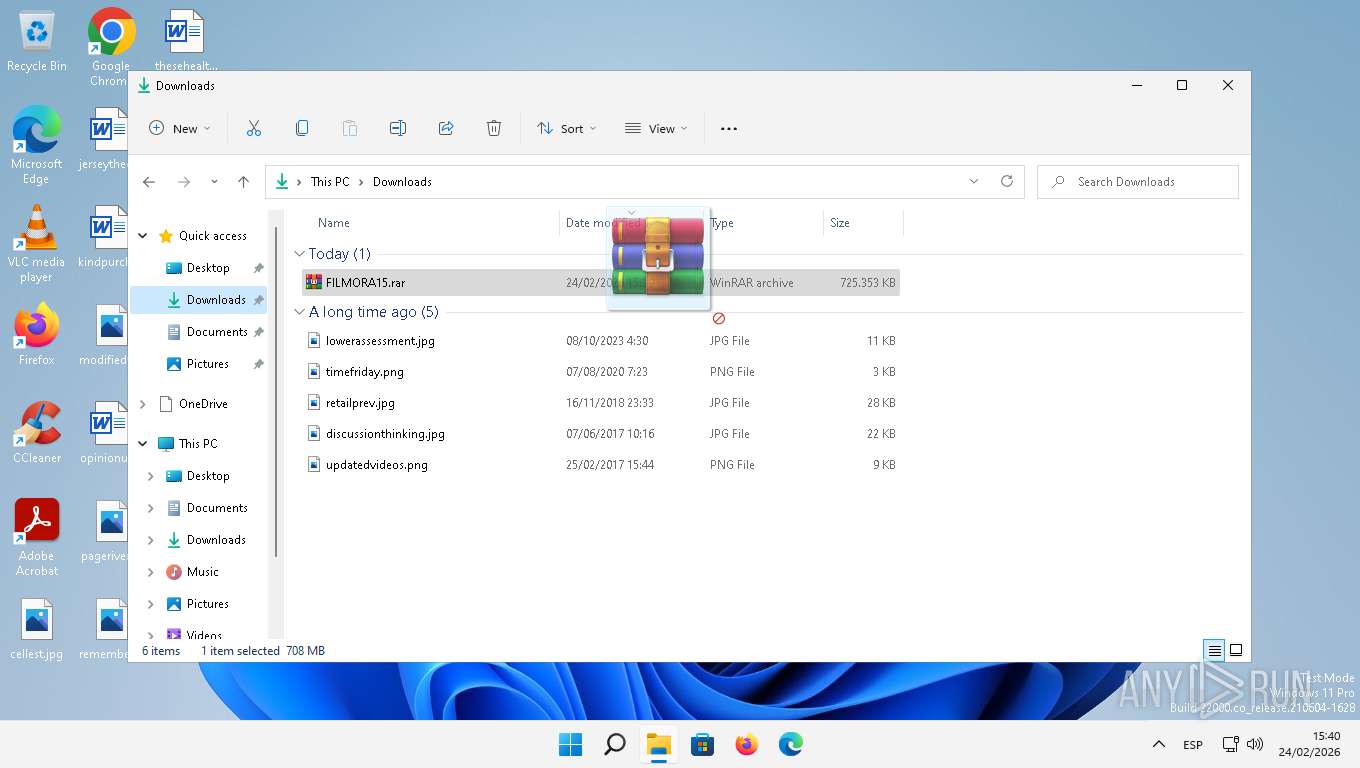
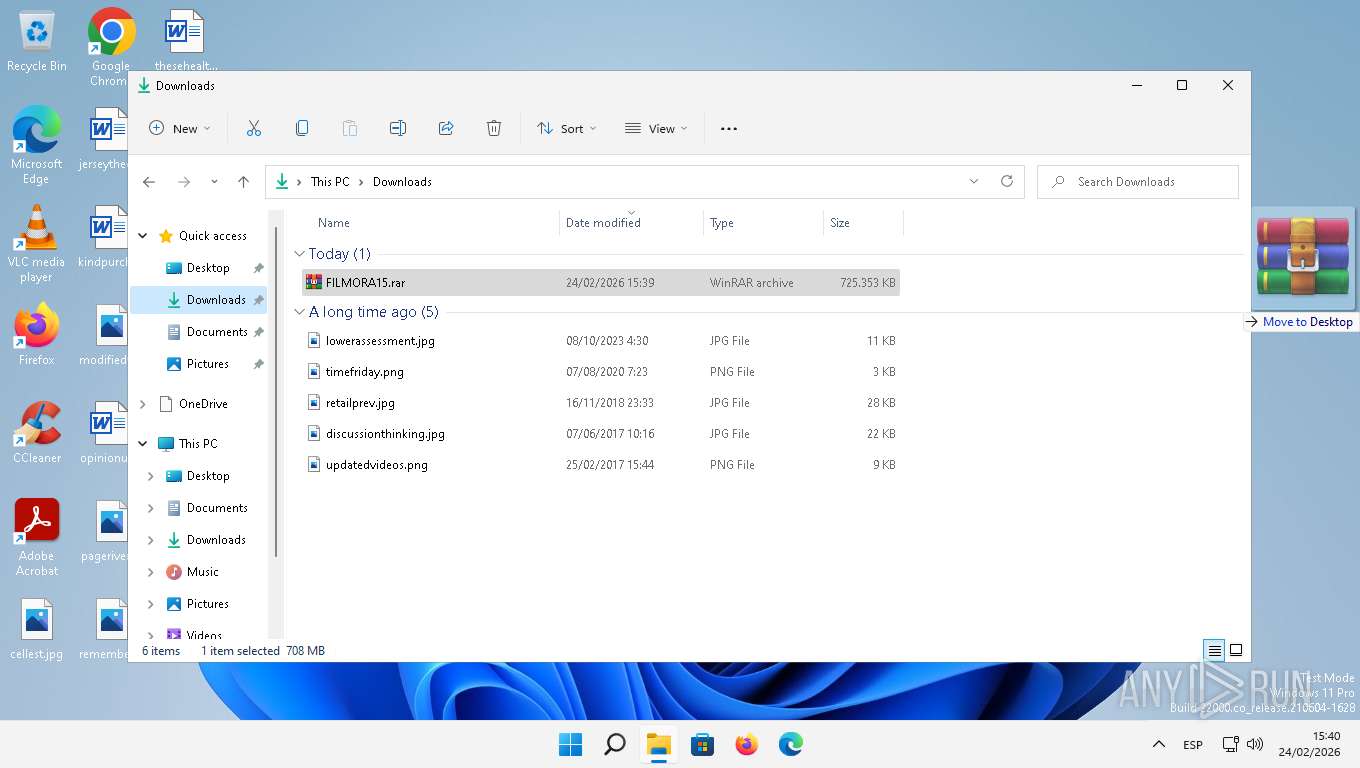
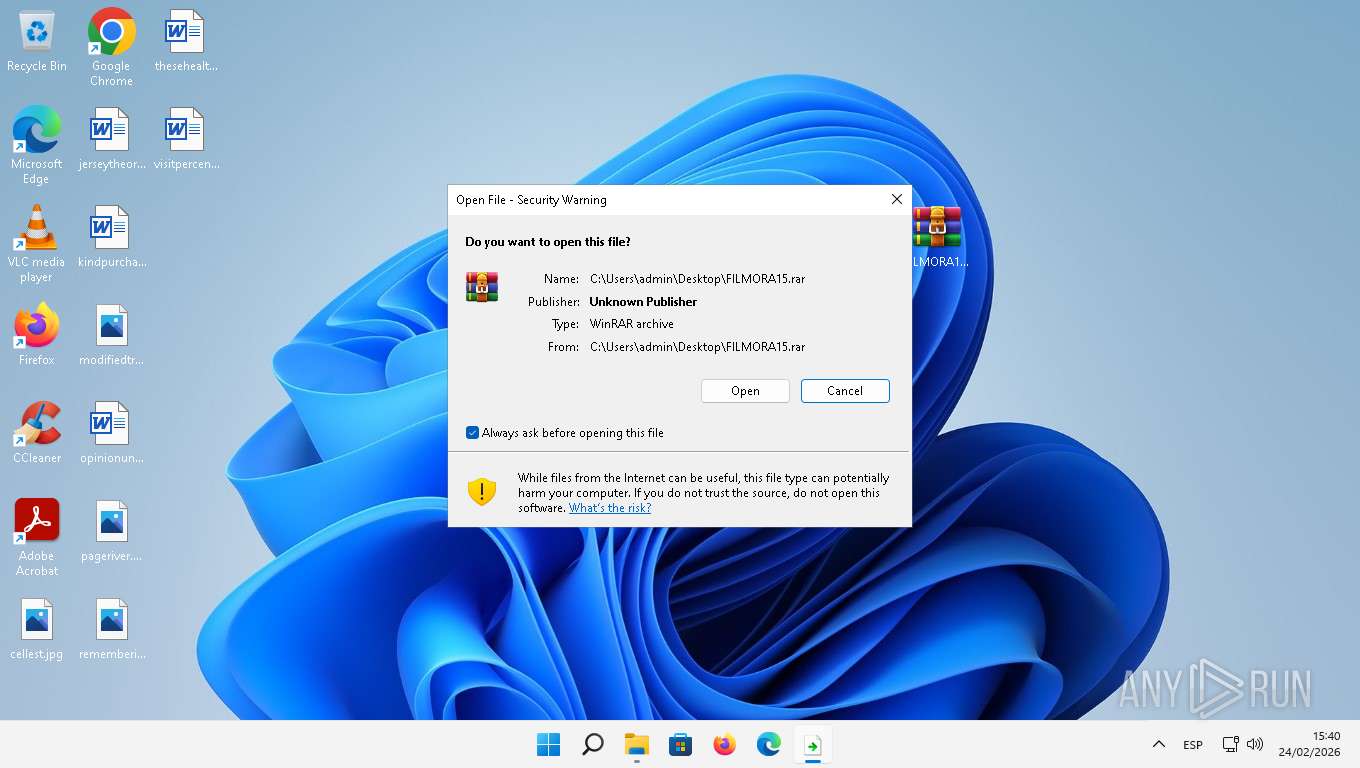
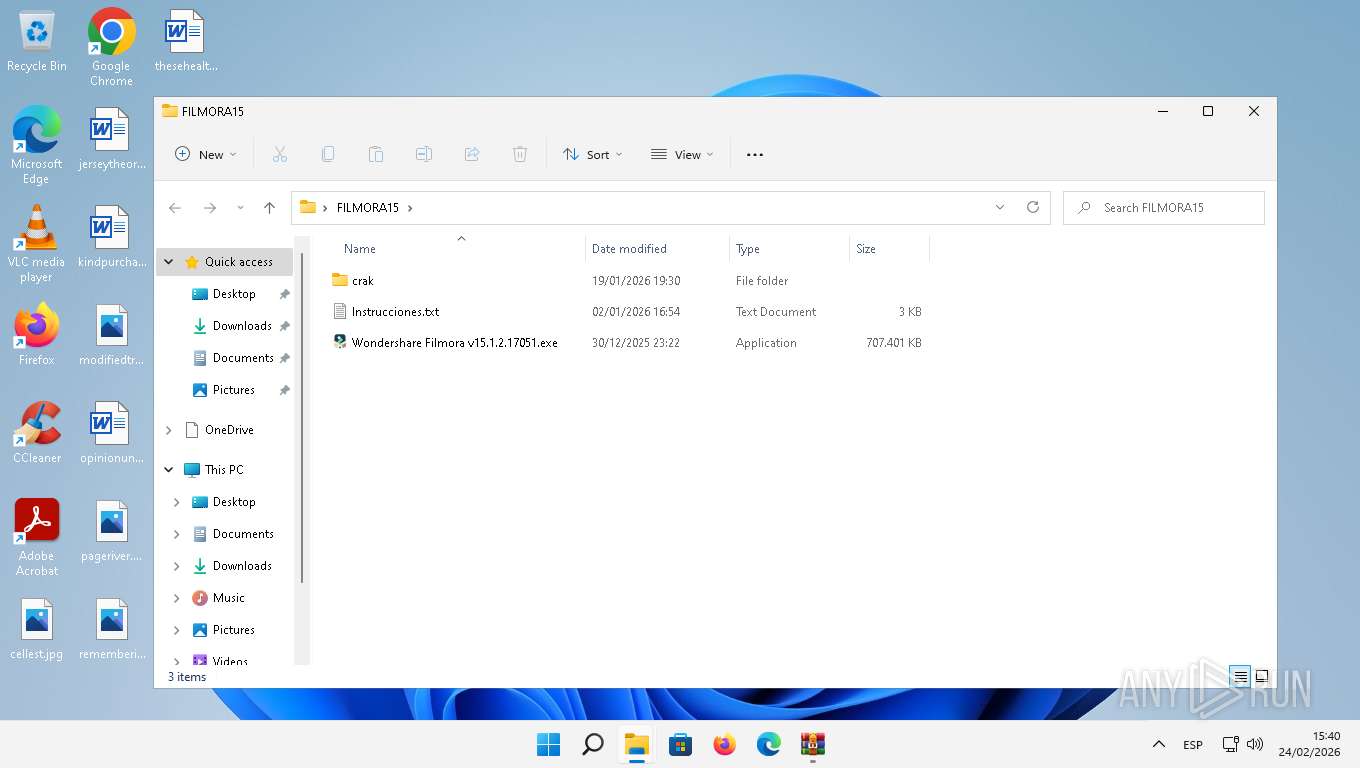
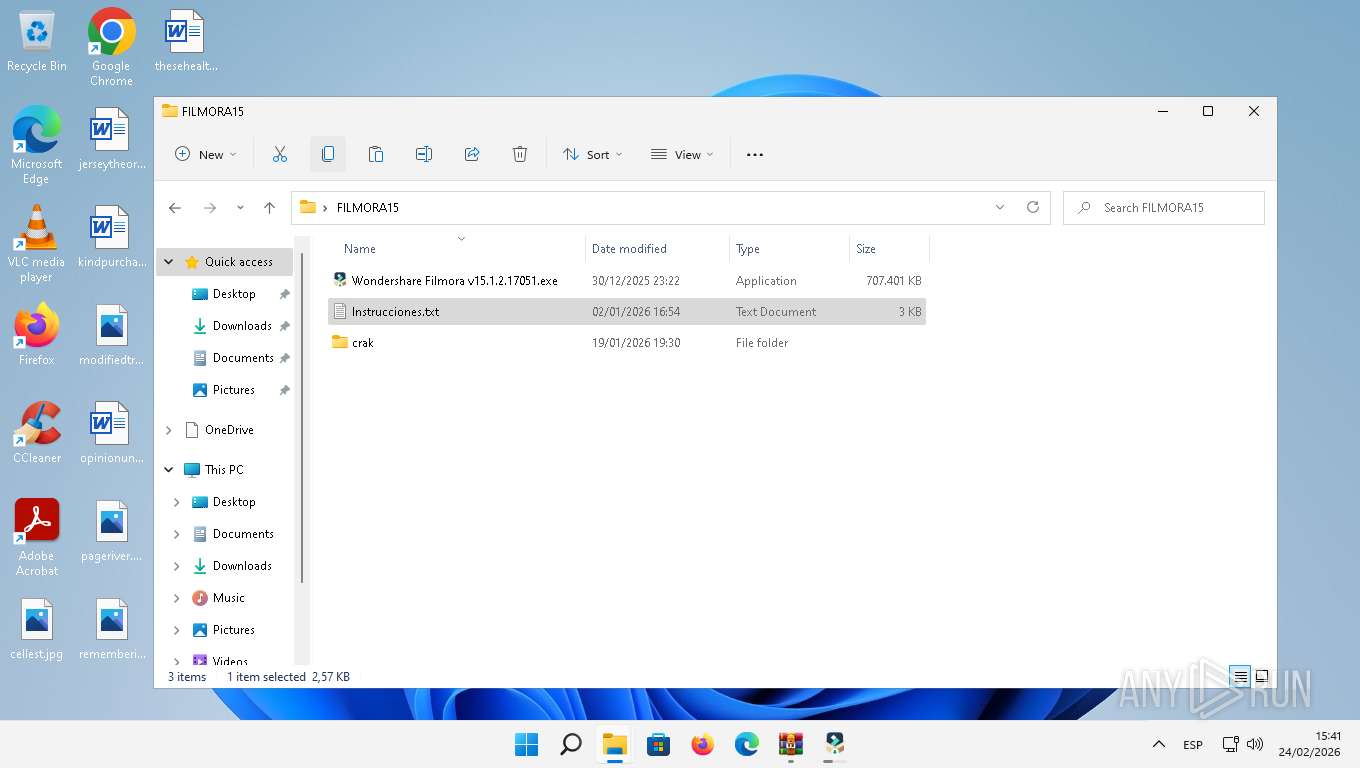
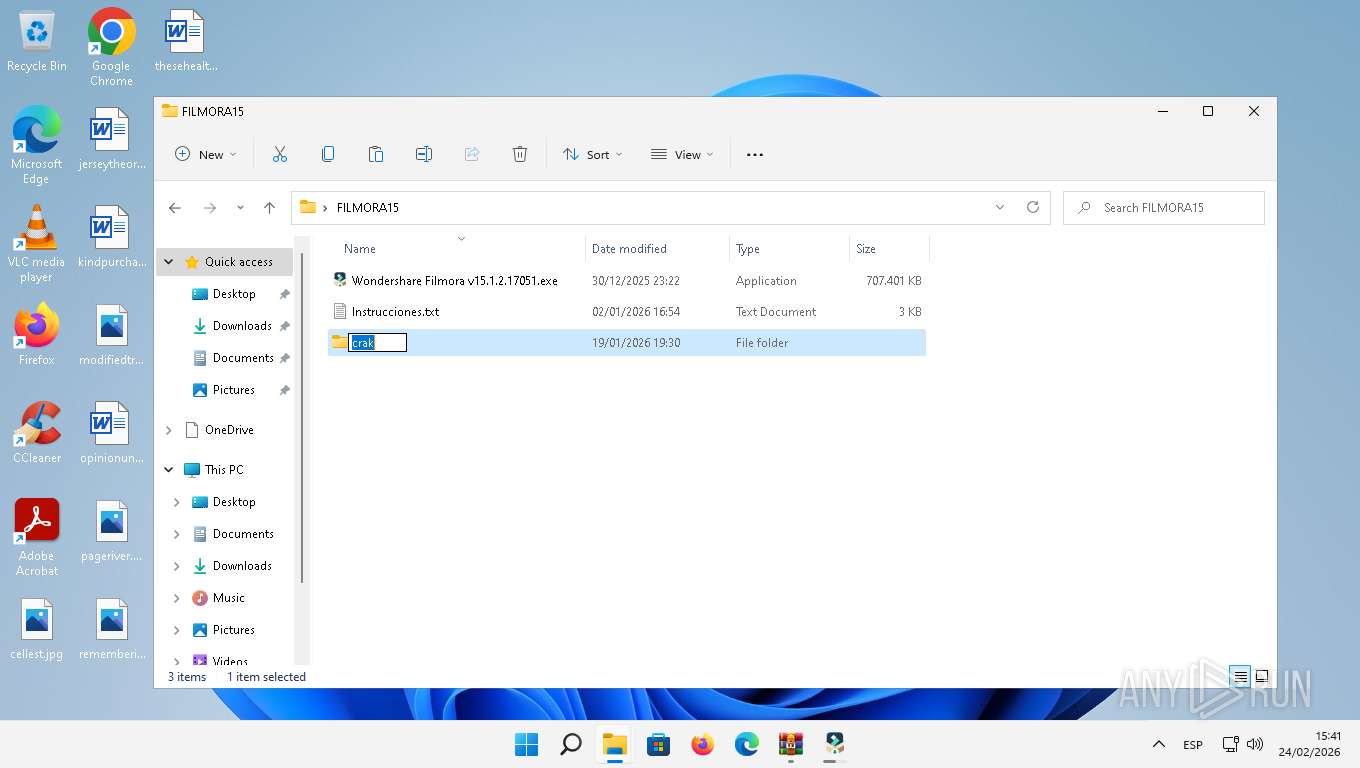
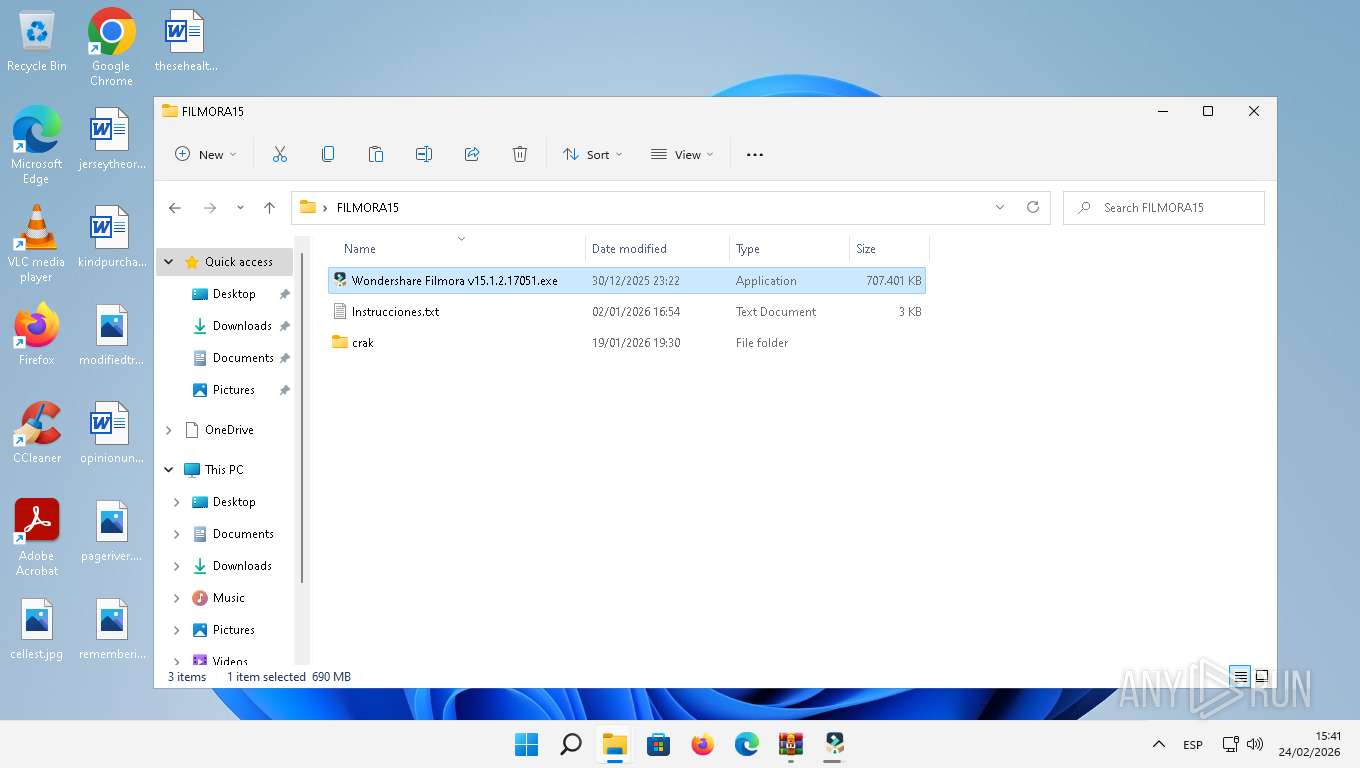
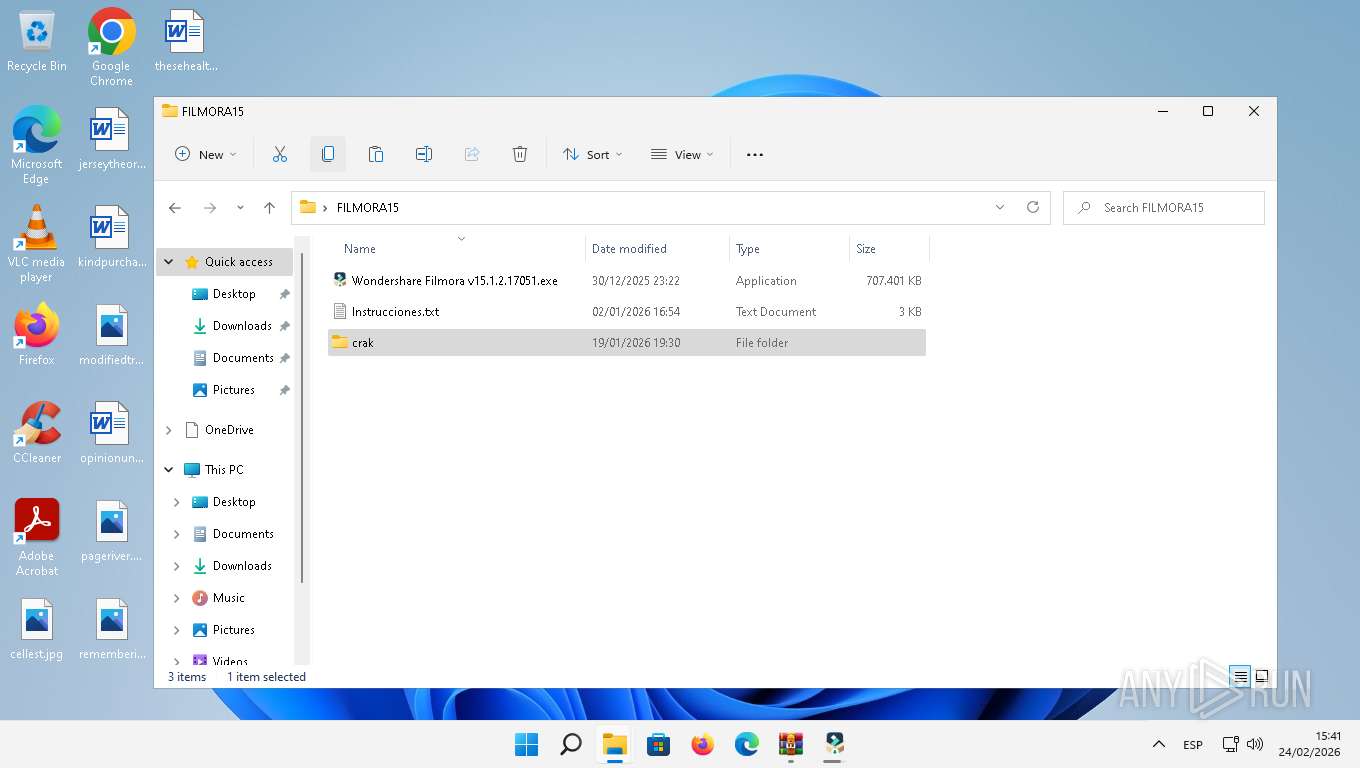
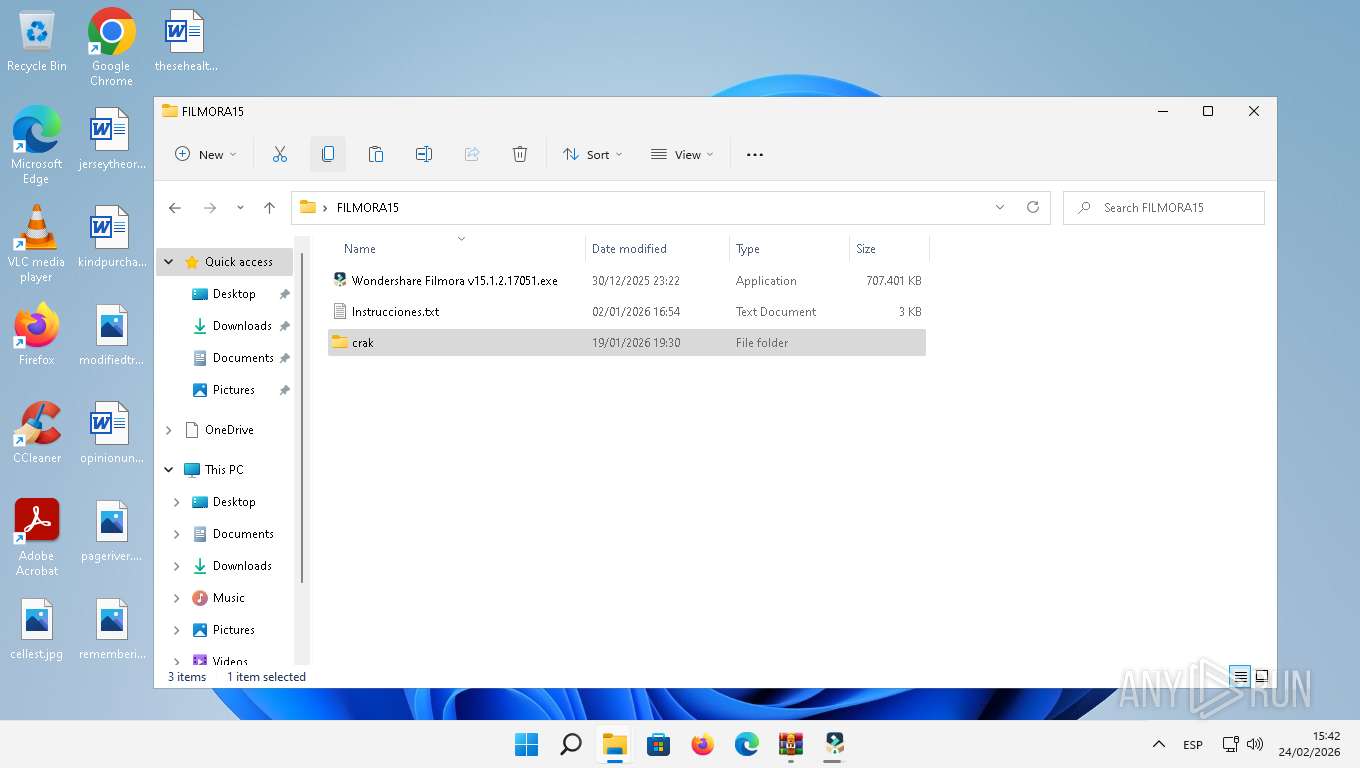
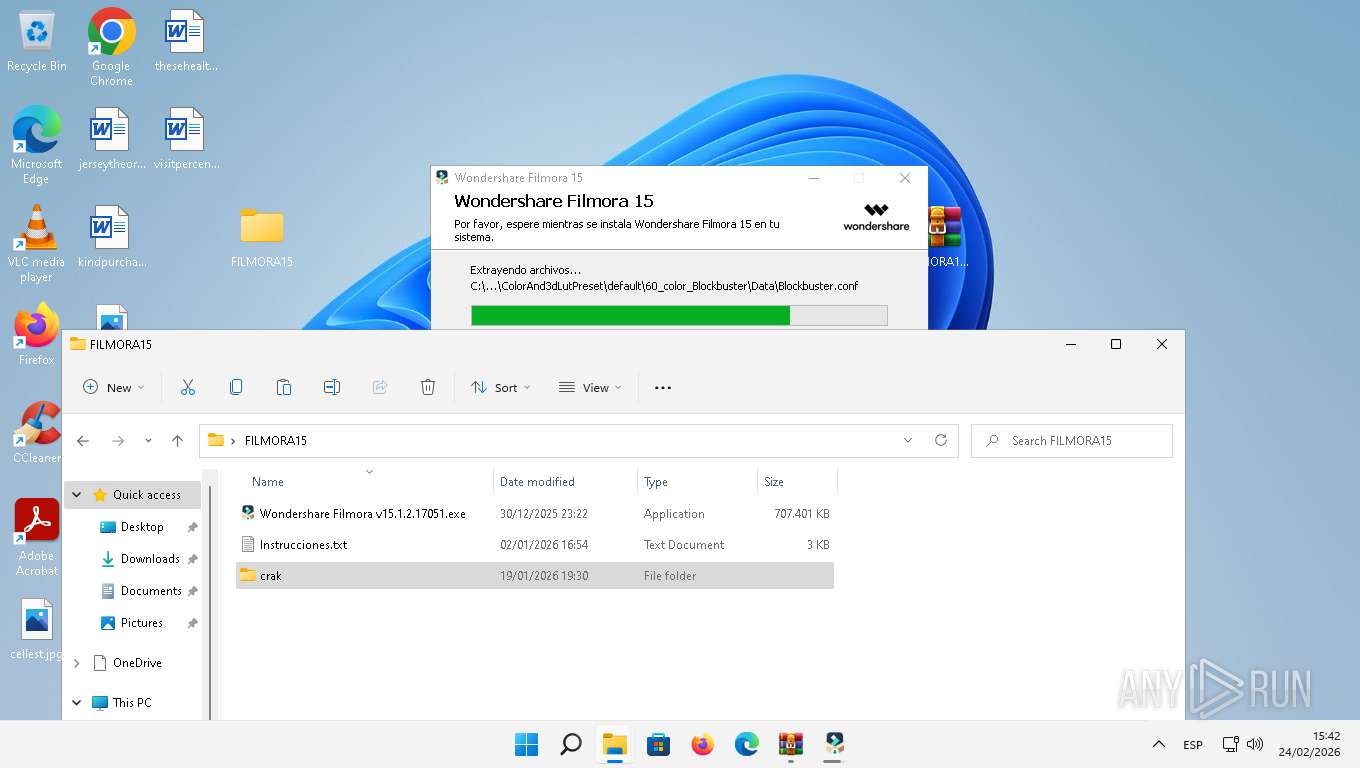
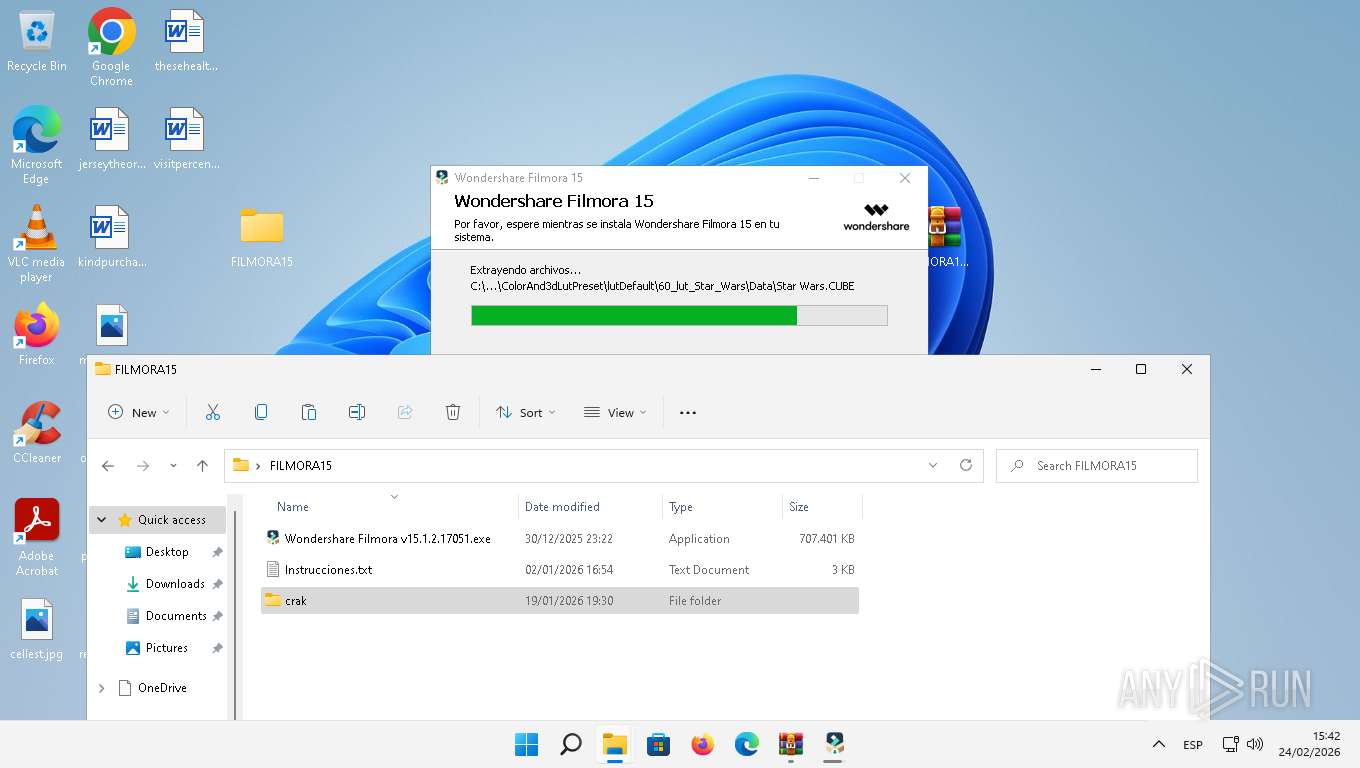
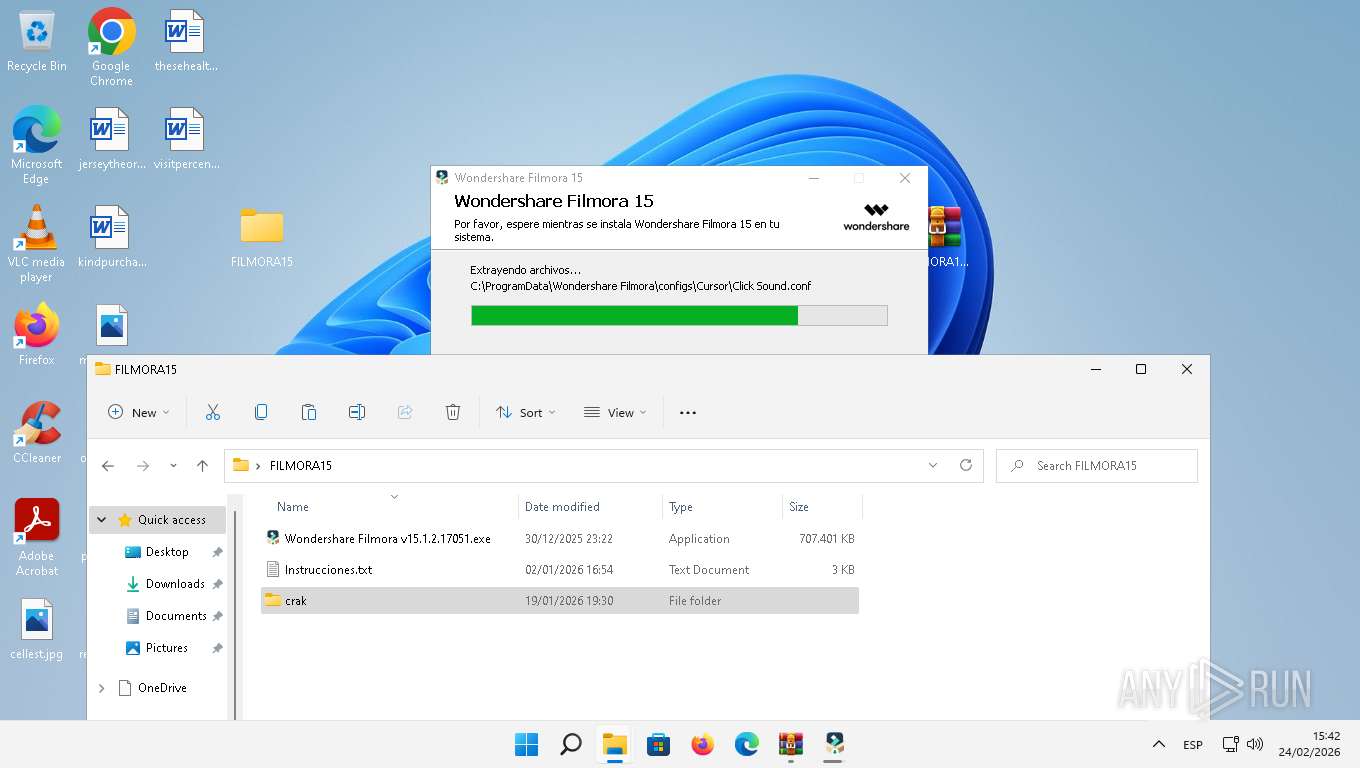
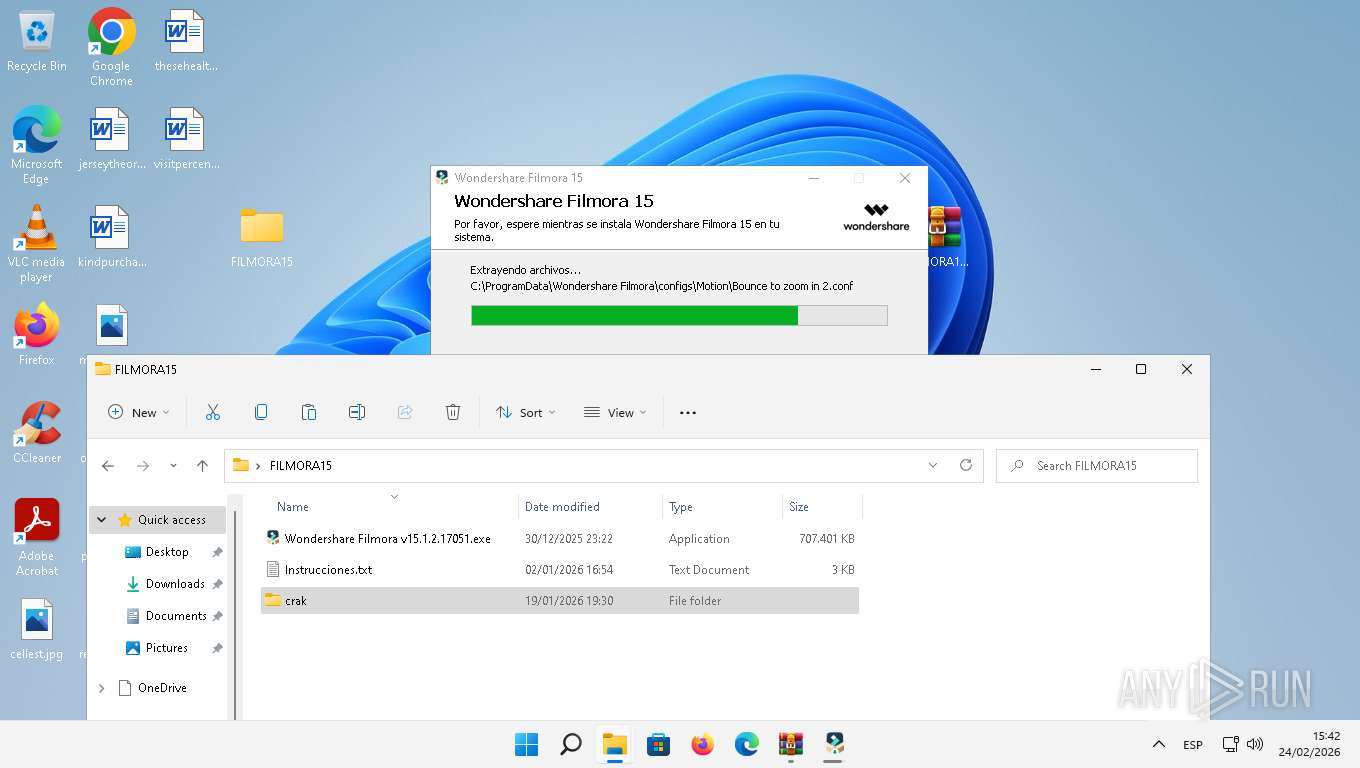
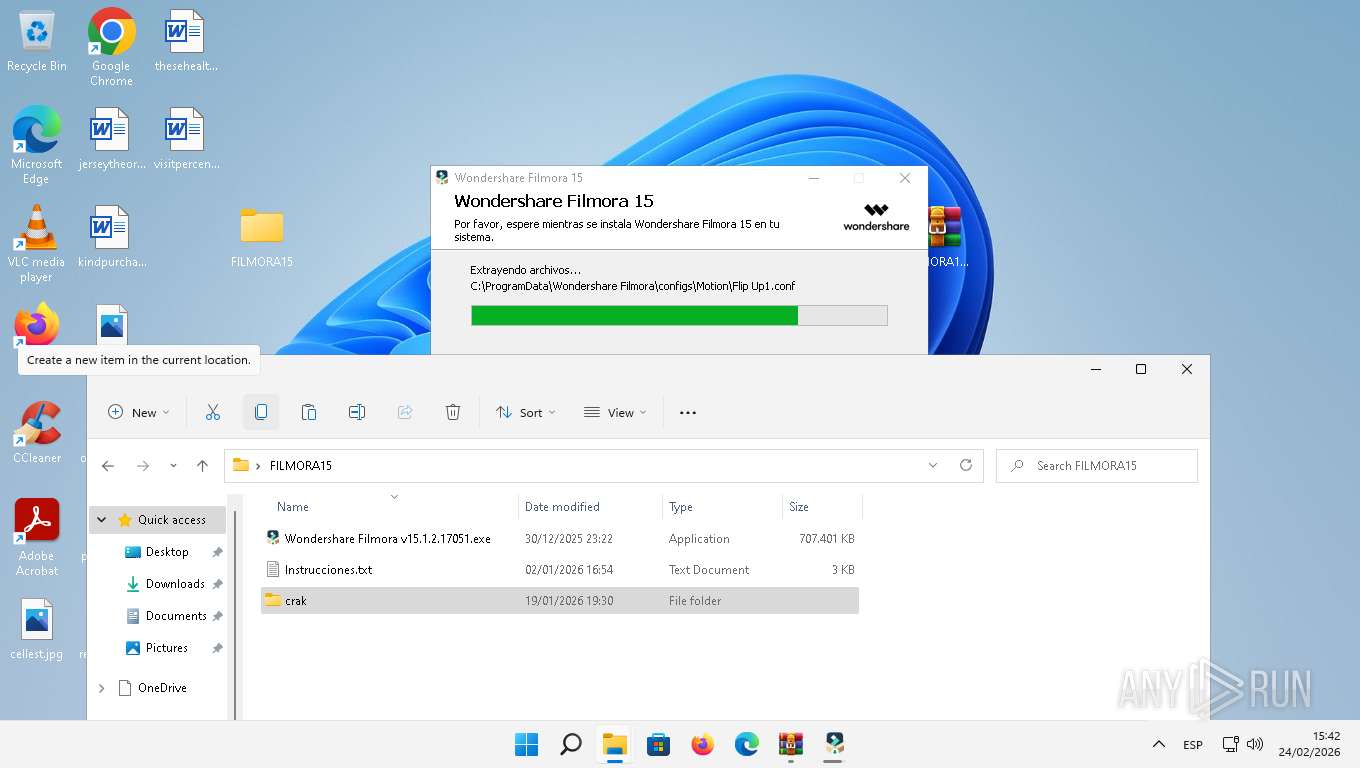
| URL: | https://download1350.mediafire.com/s5ekk2k629qg2B28DWQYwGSvHvEQLyayQUau2EowCExOCqo3eDoBdT9_HJbpwniZsyeO8zoVh6sn_W2A6TxV6J_opAIzXn7IzVgPuT3pMaaw57aFcijpx8Ku6_2VATIzi5m7vT1XC1OImtXqupCiYwH5YtPIyljmgfjYsWzT7-sAWA/x8kx5v4jsa77nr5/FILMORA15.rar |
| Full analysis: | https://app.any.run/tasks/569472f0-bf4d-4d72-9aa5-7cfa9ff70dac |
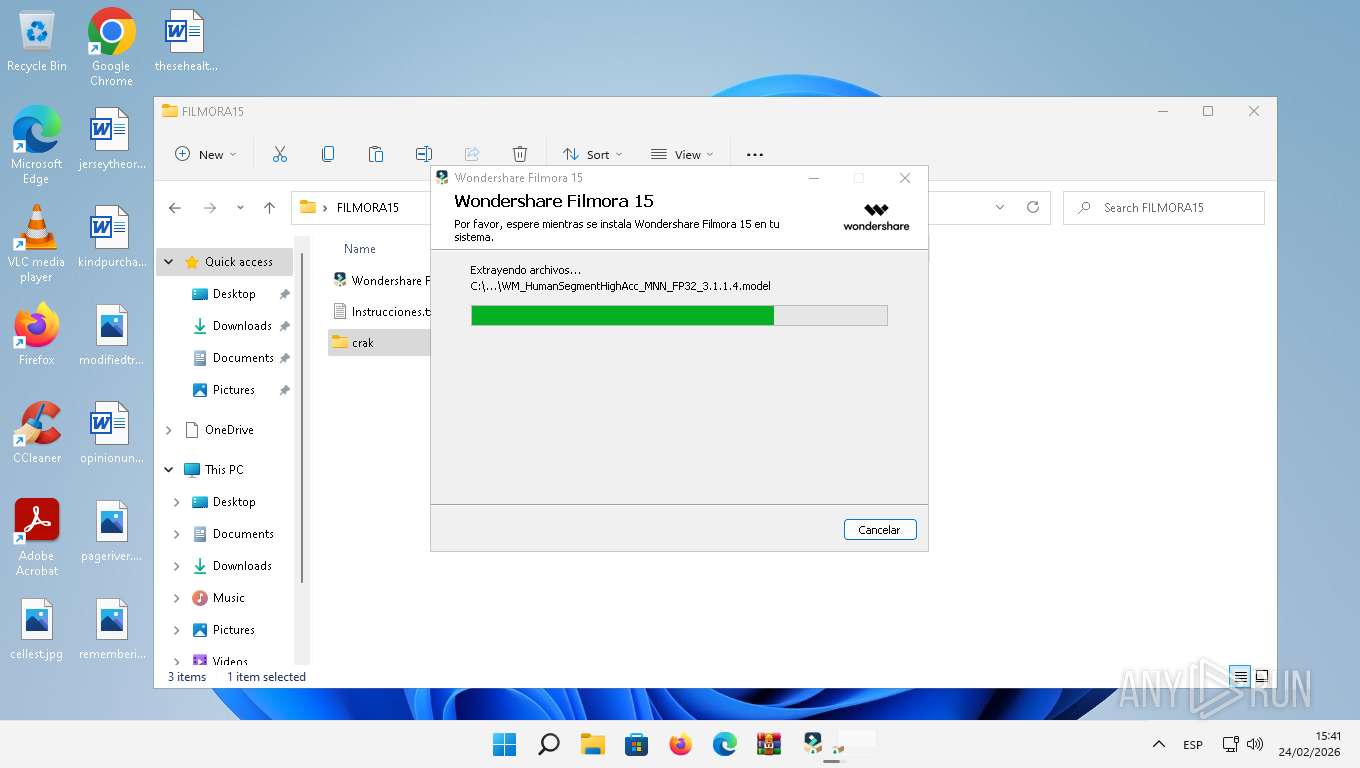
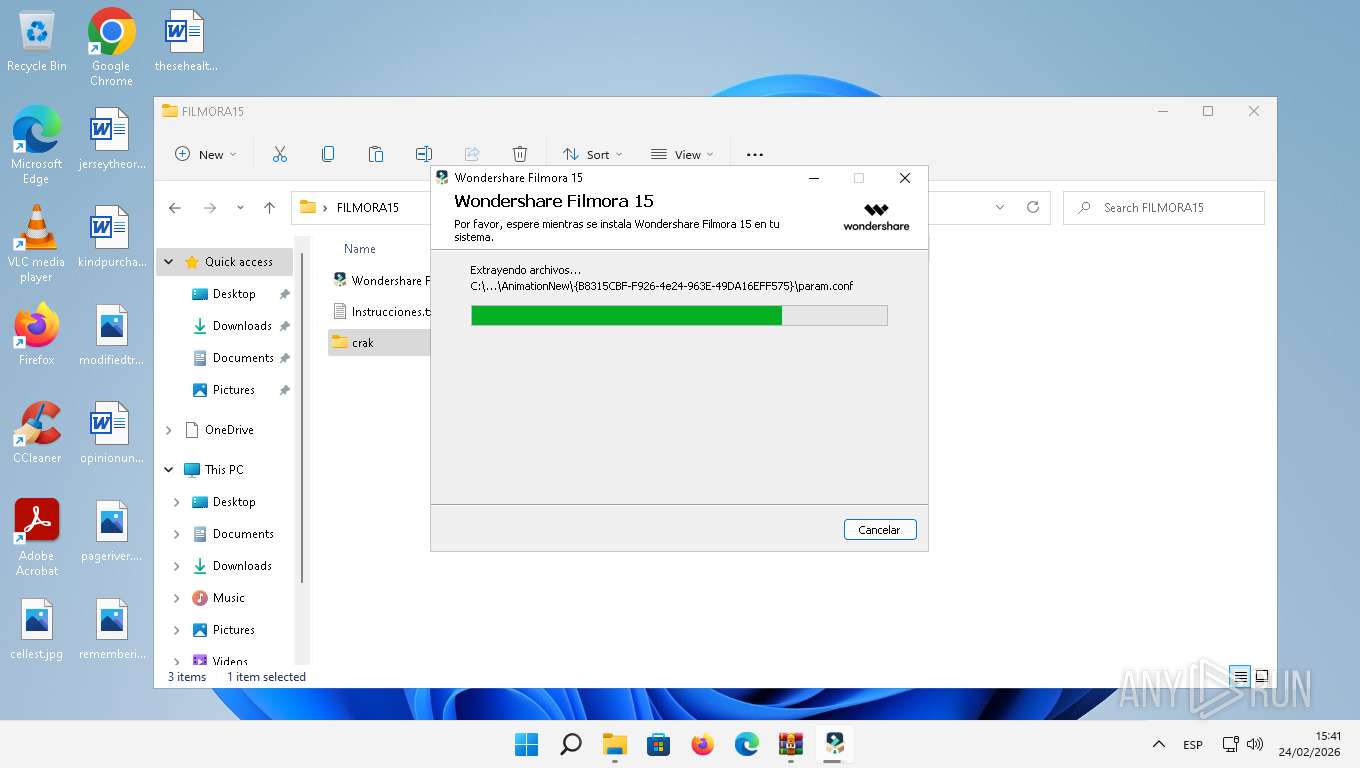
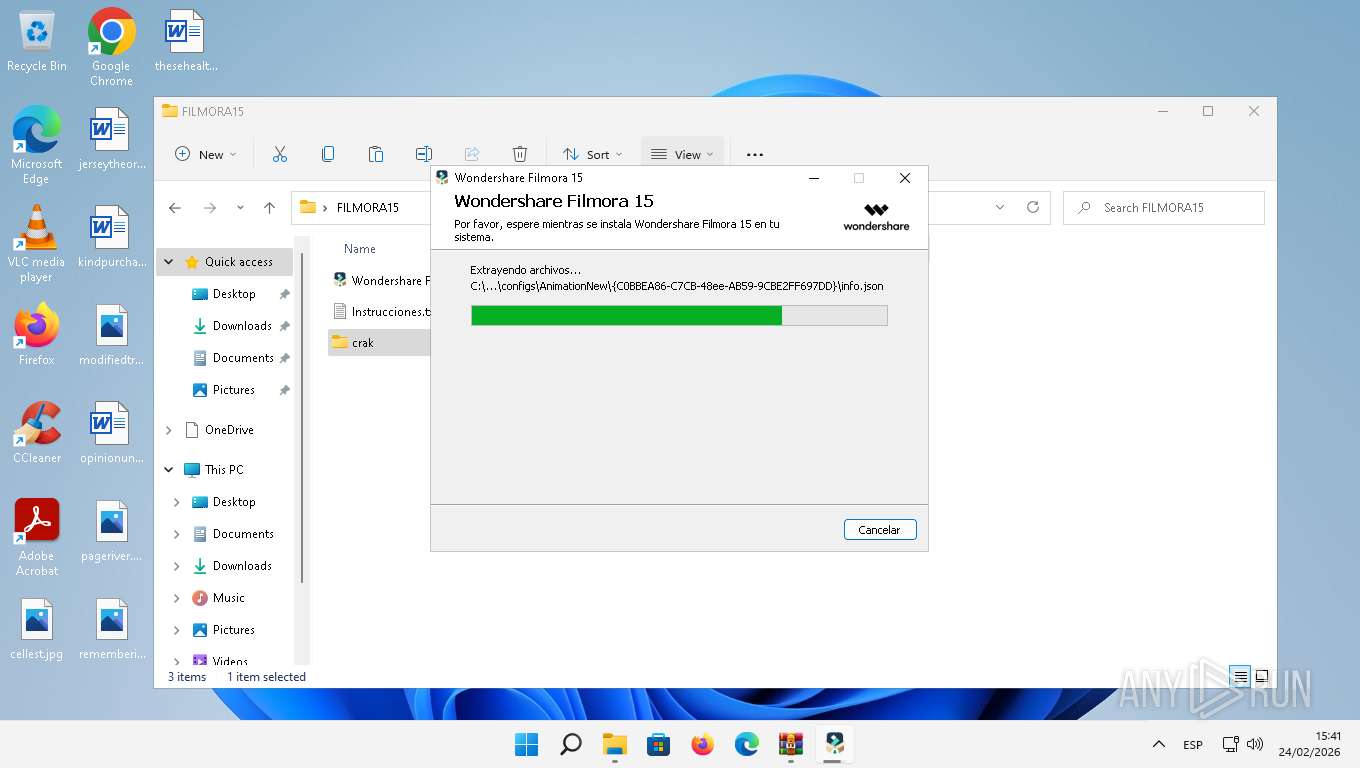
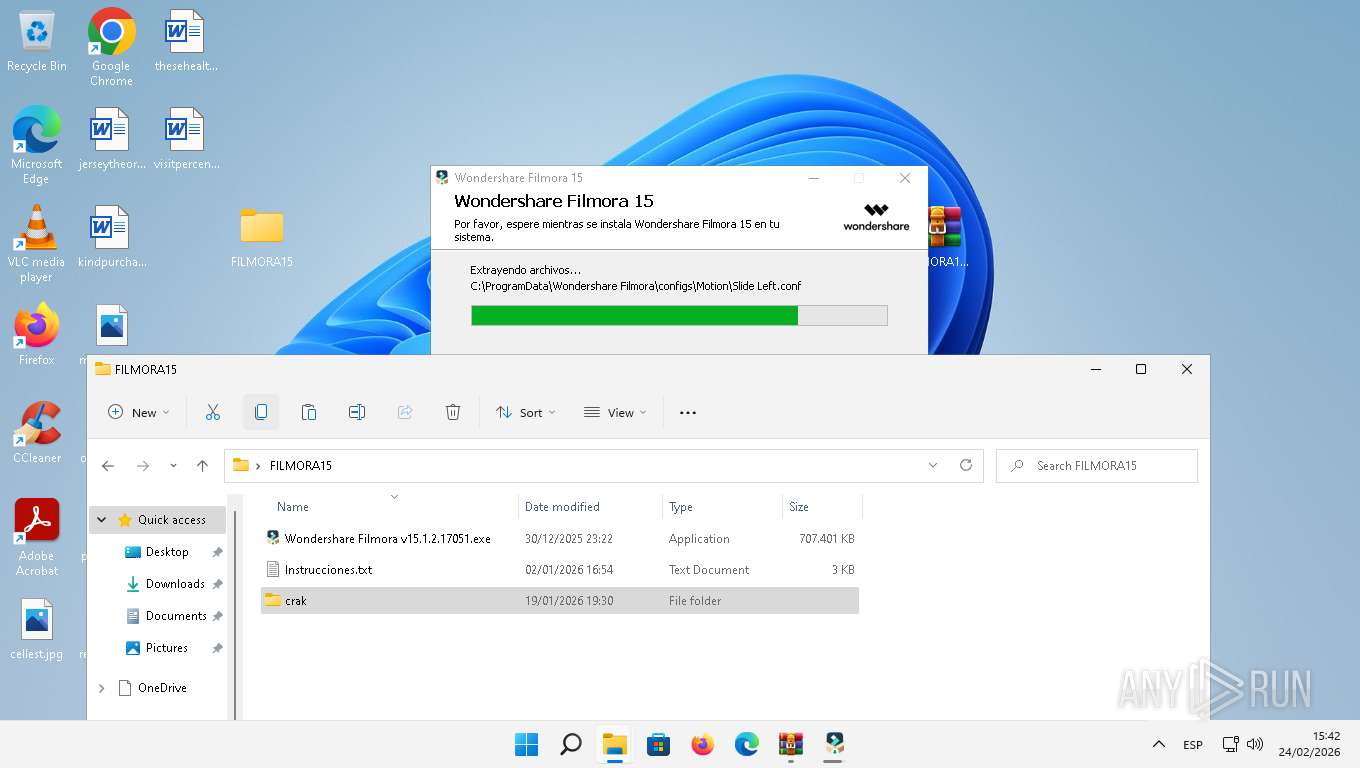
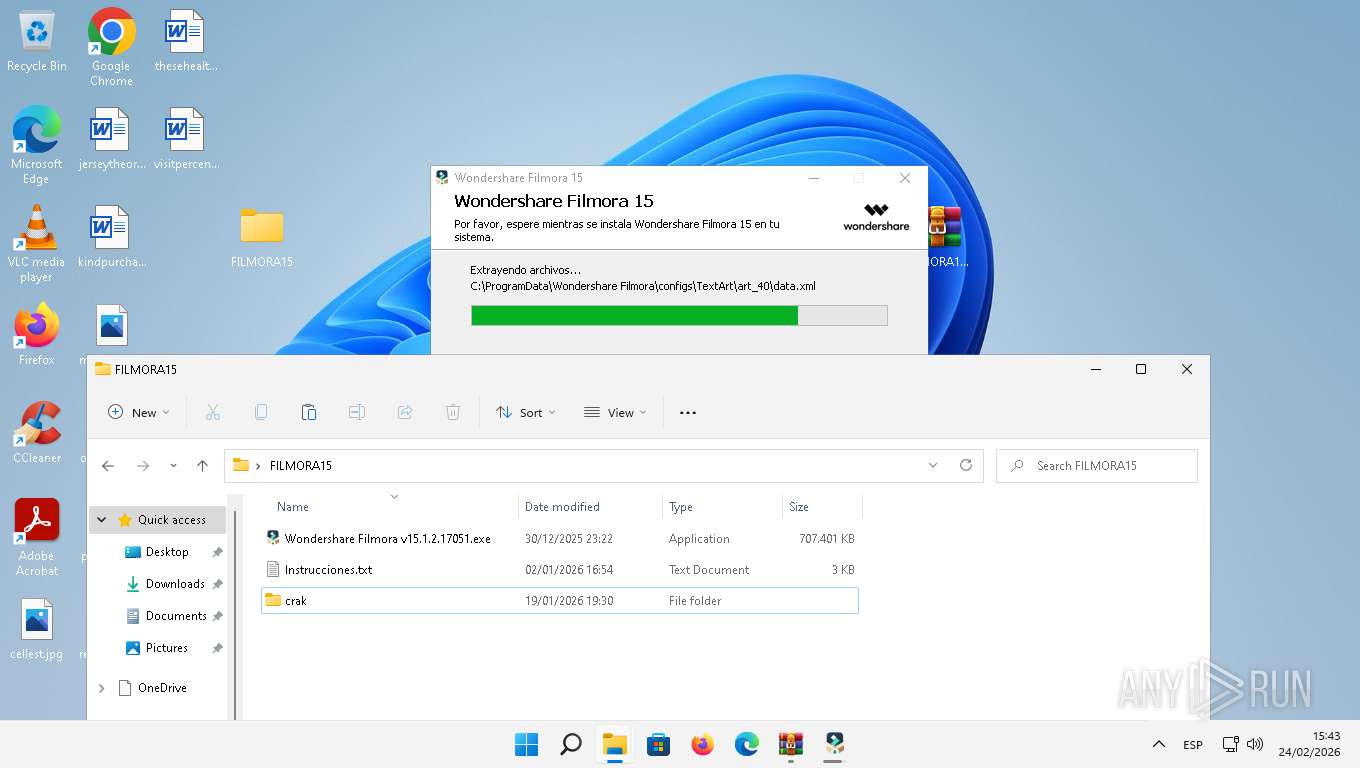
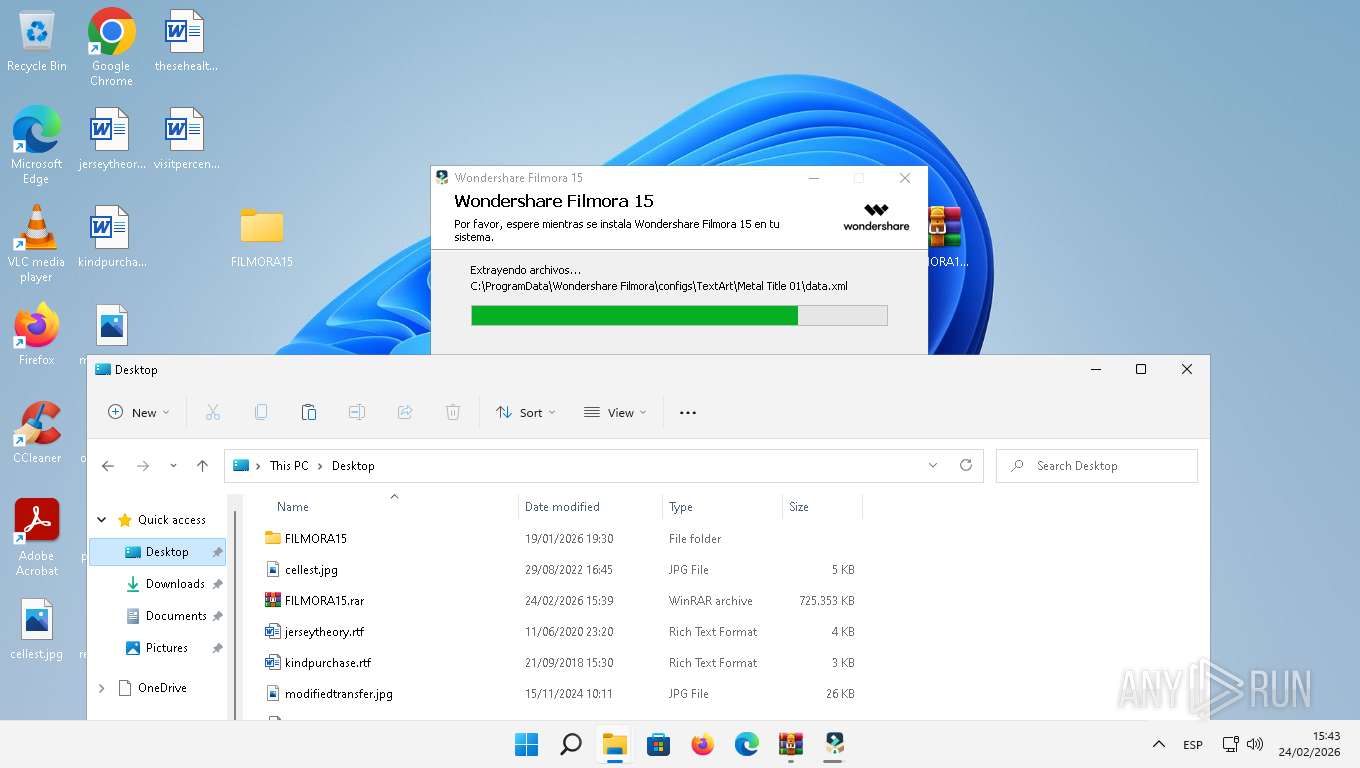
| Verdict: | Malicious activity |
| Analysis date: | February 24, 2026, 14:35:28 |
| OS: | Windows 11 Professional (build: 22000, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 09C1E1FD6F313CB5CD9893C6A33A3041 |
| SHA1: | 358BDDFCF9E4788436324503A803D5E7CC4CA28F |
| SHA256: | 61C4C9D09D3BA296BEA338DDC5915DC9096F37B67F337CCD2344558110A22A4F |
| SSDEEP: | 6:2S8Qh2eGB+TMLNNi0TMcitrvxOy0rlzV/jKR2Q87sIWoqLUX:2Z9eBTSiwbitnif7kKpWoqLUX |
MALICIOUS
GENERIC has been found (auto)
- Wondershare Filmora SubPack 2.tmp (PID: 7064)
- Wondershare Filmora SubPack 3.tmp (PID: 1328)
Registers / Runs the DLL via REGSVR32.EXE
- Wondershare Filmora v15.1.2.17051.tmp (PID: 2004)
Executing a file with an untrusted certificate
- vcredist_x64.exe (PID: 5372)
- WSHelper.exe (PID: 2900)
- install.exe (PID: 8016)
- WSHelper.exe (PID: 2156)
Changes the autorun value in the registry
- Wondershare Helper Compact.tmp (PID: 3736)
Proxy execution via Explorer
- Wondershare Filmora Launcher.exe (PID: 6964)
SUSPICIOUS
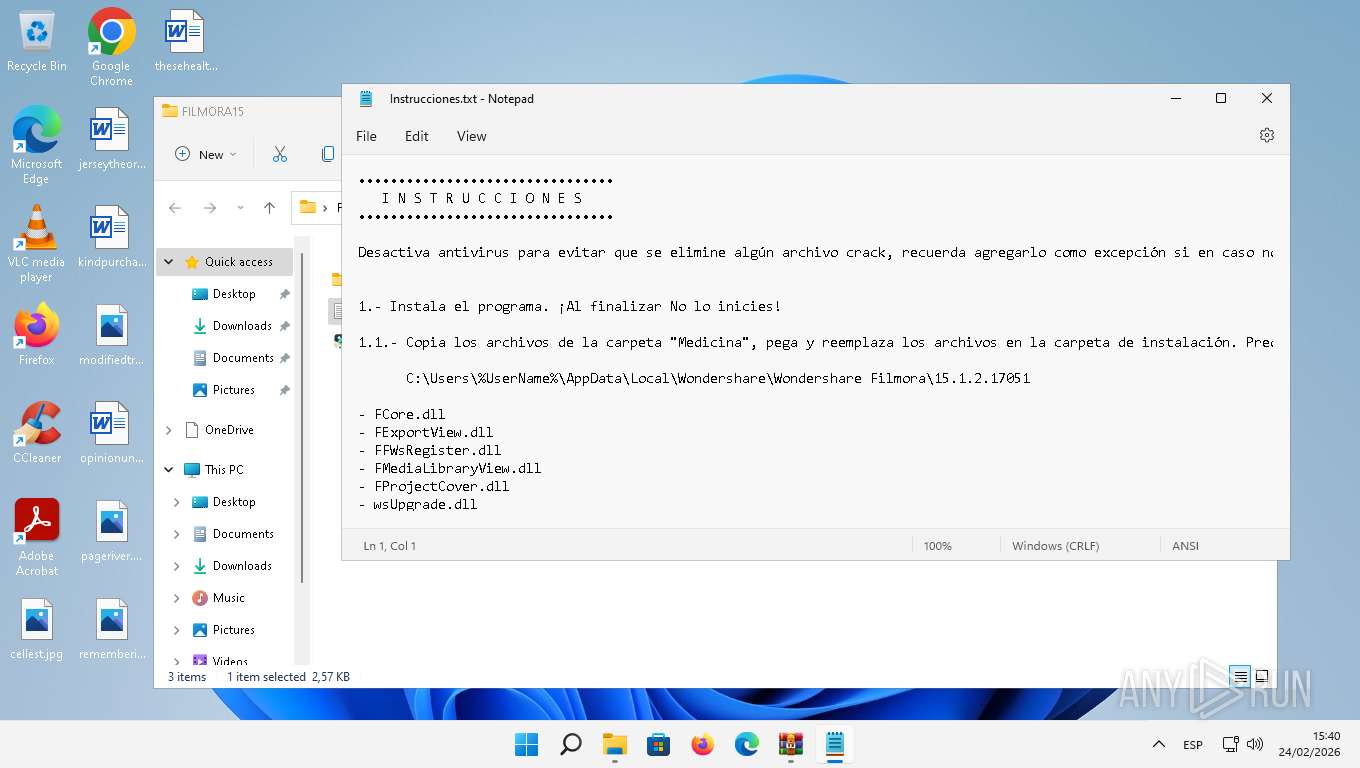
Reads the Internet Settings
- Notepad.exe (PID: 6936)
- Wondershare Filmora v15.1.2.17051.tmp (PID: 576)
- Wondershare Launcher.exe (PID: 1428)
- Wondershare Filmora v15.1.2.17051.tmp (PID: 2004)
- WSHelper.exe (PID: 2156)
- Wondershare Filmora Launcher.exe (PID: 6964)
- Wondershare Filmora.exe (PID: 7696)
- PlayServer.exe (PID: 2456)
- DataReporting.exe (PID: 4424)
- FilmoraPlayer.exe (PID: 1520)
- WMIC.exe (PID: 2740)
- WMIC.exe (PID: 5660)
- WebBrowser.exe (PID: 3500)
- ShellExperienceHost.exe (PID: 6808)
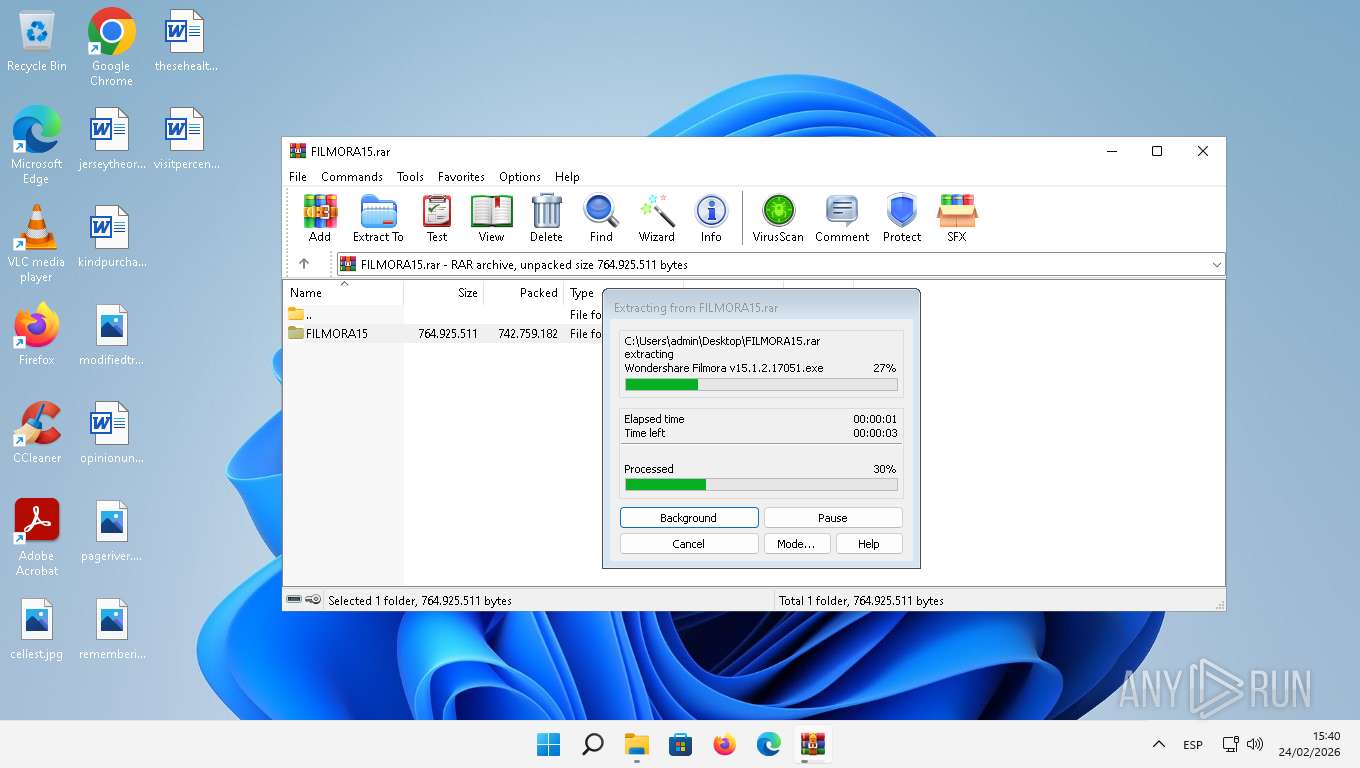
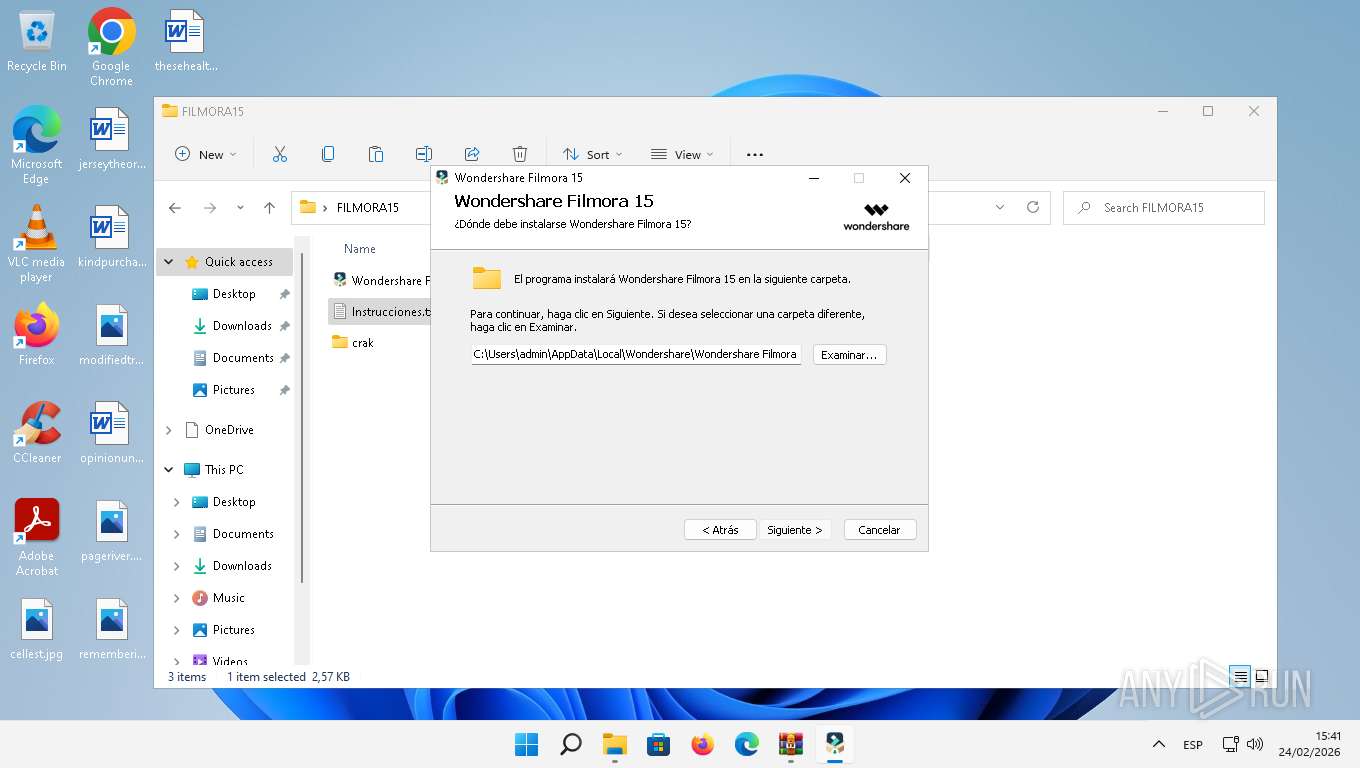
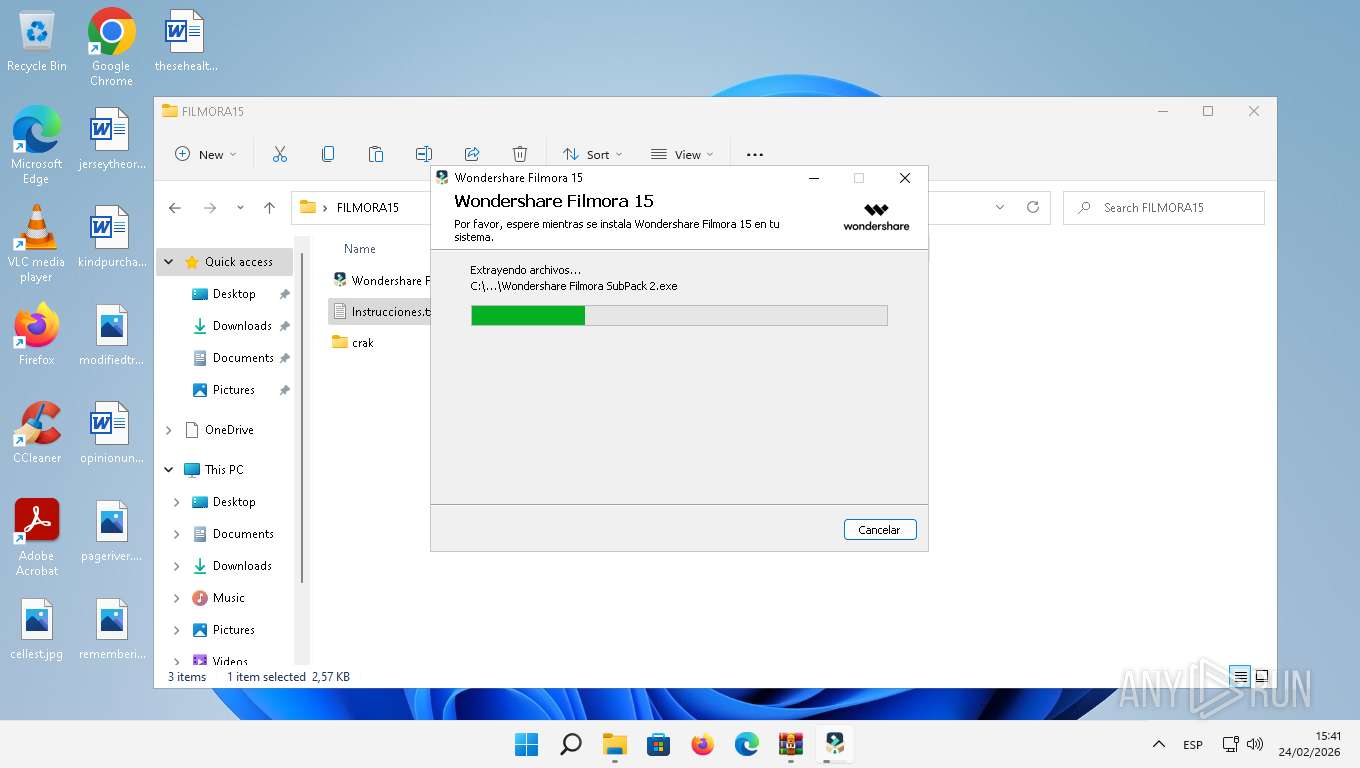
Executable content was dropped or overwritten
- Wondershare Filmora v15.1.2.17051.exe (PID: 8108)
- Wondershare Filmora v15.1.2.17051.exe (PID: 7604)
- Wondershare Filmora v15.1.2.17051.tmp (PID: 576)
- Wondershare Filmora v15.1.2.17051.tmp (PID: 2004)
- Wondershare Filmora SubPack 1.exe (PID: 2248)
- Wondershare Filmora SubPack 2.exe (PID: 3160)
- Wondershare Filmora SubPack 2.tmp (PID: 7064)
- Wondershare Filmora SubPack 1.tmp (PID: 7840)
- Wondershare Filmora SubPack 3.exe (PID: 3392)
- Wondershare Filmora SubPack 3.tmp (PID: 1328)
- Wondershare NativePush.exe (PID: 3180)
- Wondershare NativePush.tmp (PID: 6160)
- Wondershare Helper Compact.tmp (PID: 3736)
- Wondershare Helper Compact.exe (PID: 7896)
- vcredist_x64.exe (PID: 5372)
- TiWorker.exe (PID: 6868)
- Wondershare Filmora Update(x64).tmp (PID: 7972)
- Wondershare Filmora Update(x64).exe (PID: 6796)
Reads the date of Windows installation
- Wondershare Launcher.exe (PID: 1428)
- Wondershare Filmora Launcher.exe (PID: 6964)
Reads the Windows owner or organization settings
- Wondershare Filmora v15.1.2.17051.tmp (PID: 576)
- Wondershare Filmora v15.1.2.17051.tmp (PID: 2004)
- Wondershare Filmora SubPack 2.tmp (PID: 7064)
- Wondershare Filmora SubPack 1.tmp (PID: 7840)
- Wondershare Filmora SubPack 3.tmp (PID: 1328)
- Wondershare NativePush.tmp (PID: 6160)
- Wondershare Helper Compact.tmp (PID: 3736)
- msiexec.exe (PID: 1892)
- Wondershare Filmora Update(x64).tmp (PID: 7972)
Process drops SQLite DLL files
- Wondershare Filmora SubPack 3.tmp (PID: 1328)
The process drops C-runtime libraries
- Wondershare Filmora SubPack 3.tmp (PID: 1328)
- msiexec.exe (PID: 1892)
- TiWorker.exe (PID: 6868)
- Wondershare Filmora Update(x64).tmp (PID: 7972)
Get information on the list of running processes
- Wondershare NativePush.tmp (PID: 6160)
- cmd.exe (PID: 1108)
- cmd.exe (PID: 1240)
- Wondershare Filmora.exe (PID: 7696)
Creates/Modifies COM task schedule object
- regsvr32.exe (PID: 7692)
Starts CMD.EXE for commands execution
- Wondershare NativePush.tmp (PID: 6160)
- Wondershare Filmora.exe (PID: 7696)
Hides command output
- cmd.exe (PID: 1240)
- cmd.exe (PID: 1108)
Uses NETSH.EXE to add a firewall rule or allowed programs
- Wondershare NativePush.tmp (PID: 6160)
Executes as Windows Service
- WsNativePushService.exe (PID: 5484)
Starts a Microsoft application from unusual location
- vcredist_x64.exe (PID: 5372)
Explorer used for Indirect Command Execution
- explorer.exe (PID: 4528)
Reads settings of System Certificates
- Wondershare Filmora.exe (PID: 7696)
- PlayServer.exe (PID: 2456)
- WebBrowser.exe (PID: 3500)
Uses WMIC.EXE to obtain physical disk drive information
- Wondershare Filmora.exe (PID: 7696)
INFO
Checks supported languages
- identity_helper.exe (PID: 2432)
- identity_helper.exe (PID: 1568)
- Notepad.exe (PID: 6936)
- Wondershare Filmora v15.1.2.17051.exe (PID: 8108)
- Wondershare Filmora v15.1.2.17051.tmp (PID: 576)
- Wondershare Launcher.exe (PID: 1428)
- Wondershare Filmora v15.1.2.17051.tmp (PID: 2004)
- Wondershare Filmora v15.1.2.17051.exe (PID: 7604)
- Wondershare Filmora SubPack 1.tmp (PID: 7840)
- _setup64.tmp (PID: 3192)
- Wondershare Filmora SubPack 1.exe (PID: 2248)
- Wondershare Filmora SubPack 2.tmp (PID: 7064)
- Wondershare Filmora SubPack 2.exe (PID: 3160)
- Wondershare Filmora SubPack 3.tmp (PID: 1328)
- Wondershare Filmora SubPack 3.exe (PID: 3392)
- _setup64.tmp (PID: 6816)
- Wondershare NativePush.exe (PID: 3180)
- Wondershare NativePush.tmp (PID: 6160)
- _setup64.tmp (PID: 2948)
- WsNativePushService.exe (PID: 7932)
- WsNativePushService.exe (PID: 3132)
- Wondershare Helper Compact.exe (PID: 7896)
- WsToastNotification.exe (PID: 2708)
- Wondershare Helper Compact.tmp (PID: 3736)
- WsNativePushService.exe (PID: 5484)
- WSHelper.exe (PID: 2900)
- vcredist_x64.exe (PID: 5372)
- install.exe (PID: 8016)
- WSHelper.exe (PID: 2156)
- msiexec.exe (PID: 1892)
- _setup64.tmp (PID: 6548)
- Wondershare Filmora Launcher.exe (PID: 6964)
- Performance.exe (PID: 7500)
- Wondershare Filmora.exe (PID: 7696)
- FilmoraPlayer.exe (PID: 1520)
- PlayServer.exe (PID: 2456)
- DataReporting.exe (PID: 4424)
- ofx_check.exe (PID: 1808)
- WebBrowser.exe (PID: 3500)
- cmdCheckATI.exe (PID: 3872)
- cmdCheckHEVC.exe (PID: 7436)
- coremediaserver.exe (PID: 2724)
- CefViewWing.exe (PID: 2956)
- CefViewWing.exe (PID: 7856)
- CefViewWing.exe (PID: 3088)
- Wondershare Filmora Update(x64).exe (PID: 6796)
- Wondershare Filmora Update(x64).tmp (PID: 7972)
- CefViewWing.exe (PID: 7024)
- _setup64.tmp (PID: 1176)
- magic_xe_supported_detect.exe (PID: 5180)
- CefViewWing.exe (PID: 7548)
- CefViewWing.exe (PID: 8644)
- CefViewWing.exe (PID: 8276)
- CefViewWing.exe (PID: 8404)
- magic_xe_supported_detect.exe (PID: 8512)
- CefViewWing.exe (PID: 8988)
- magic_xe_supported_detect.exe (PID: 7704)
- magic_xe_supported_detect.exe (PID: 7684)
Application launched itself
- msedge.exe (PID: 6292)
- msedge.exe (PID: 7876)
- chrome.exe (PID: 7288)
Drops script file
- chrome.exe (PID: 7288)
- msedge.exe (PID: 4856)
- msedge.exe (PID: 6056)
- _setup64.tmp (PID: 3192)
- Wondershare Filmora v15.1.2.17051.tmp (PID: 2004)
- msedge.exe (PID: 7708)
- Wondershare NativePush.tmp (PID: 6160)
- Wondershare Helper Compact.tmp (PID: 3736)
Reads the computer name
- identity_helper.exe (PID: 2432)
- Notepad.exe (PID: 6936)
- identity_helper.exe (PID: 1568)
- Wondershare Launcher.exe (PID: 1428)
- Wondershare Filmora v15.1.2.17051.tmp (PID: 576)
- Wondershare Filmora v15.1.2.17051.tmp (PID: 2004)
- Wondershare Filmora SubPack 1.tmp (PID: 7840)
- Wondershare Filmora SubPack 2.tmp (PID: 7064)
- Wondershare Filmora SubPack 3.tmp (PID: 1328)
- Wondershare NativePush.tmp (PID: 6160)
- WsNativePushService.exe (PID: 3132)
- WsNativePushService.exe (PID: 7932)
- WsNativePushService.exe (PID: 5484)
- Wondershare Helper Compact.tmp (PID: 3736)
- WsToastNotification.exe (PID: 2708)
- WSHelper.exe (PID: 2900)
- vcredist_x64.exe (PID: 5372)
- install.exe (PID: 8016)
- msiexec.exe (PID: 1892)
- WSHelper.exe (PID: 2156)
- Wondershare Filmora Launcher.exe (PID: 6964)
- Wondershare Filmora.exe (PID: 7696)
- Performance.exe (PID: 7500)
- PlayServer.exe (PID: 2456)
- FilmoraPlayer.exe (PID: 1520)
- DataReporting.exe (PID: 4424)
- cmdCheckATI.exe (PID: 3872)
- WebBrowser.exe (PID: 3500)
- coremediaserver.exe (PID: 2724)
- cmdCheckHEVC.exe (PID: 7436)
- CefViewWing.exe (PID: 3088)
- CefViewWing.exe (PID: 2956)
- Wondershare Filmora Update(x64).tmp (PID: 7972)
- magic_xe_supported_detect.exe (PID: 7684)
- magic_xe_supported_detect.exe (PID: 5180)
- CefViewWing.exe (PID: 8404)
- magic_xe_supported_detect.exe (PID: 7704)
- magic_xe_supported_detect.exe (PID: 8512)
Reads Environment values
- identity_helper.exe (PID: 2432)
- identity_helper.exe (PID: 1568)
- Wondershare Filmora.exe (PID: 7696)
- FilmoraPlayer.exe (PID: 1520)
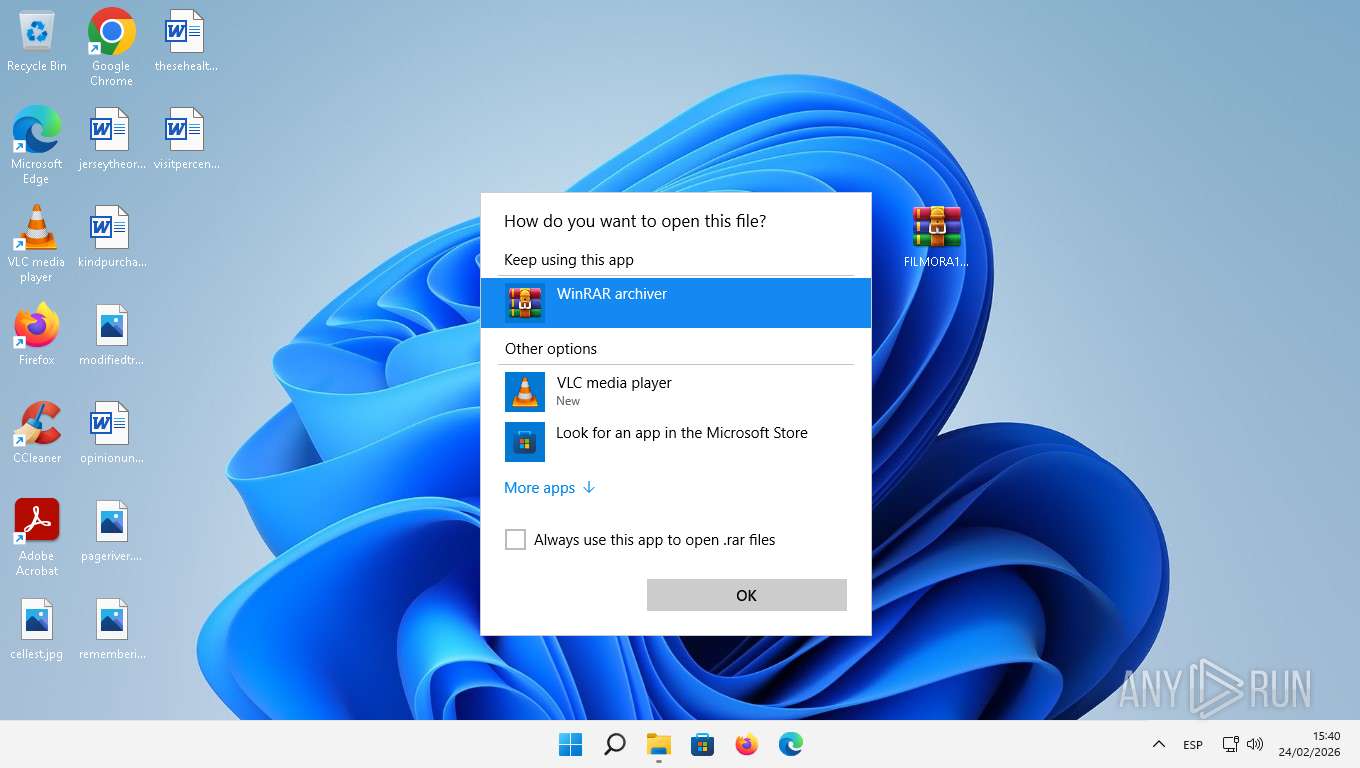
Reads Microsoft Office registry keys
- OpenWith.exe (PID: 5212)
- OpenWith.exe (PID: 1868)
- OpenWith.exe (PID: 6576)
- OpenWith.exe (PID: 1300)
- OpenWith.exe (PID: 6888)
Reads security settings of Internet Explorer
- OpenWith.exe (PID: 5212)
- OpenWith.exe (PID: 1868)
- OpenWith.exe (PID: 6576)
- OpenWith.exe (PID: 1300)
- Notepad.exe (PID: 6936)
- OpenWith.exe (PID: 6888)
- Wondershare Launcher.exe (PID: 1428)
- Wondershare Filmora v15.1.2.17051.tmp (PID: 576)
- Wondershare Filmora v15.1.2.17051.tmp (PID: 2004)
- WSHelper.exe (PID: 2156)
- ie4uinit.exe (PID: 7528)
- Wondershare Filmora Launcher.exe (PID: 6964)
- explorer.exe (PID: 1980)
- Wondershare Filmora.exe (PID: 7696)
- DataReporting.exe (PID: 4424)
- PlayServer.exe (PID: 2456)
- WMIC.exe (PID: 2740)
- WMIC.exe (PID: 5660)
- WebBrowser.exe (PID: 3500)
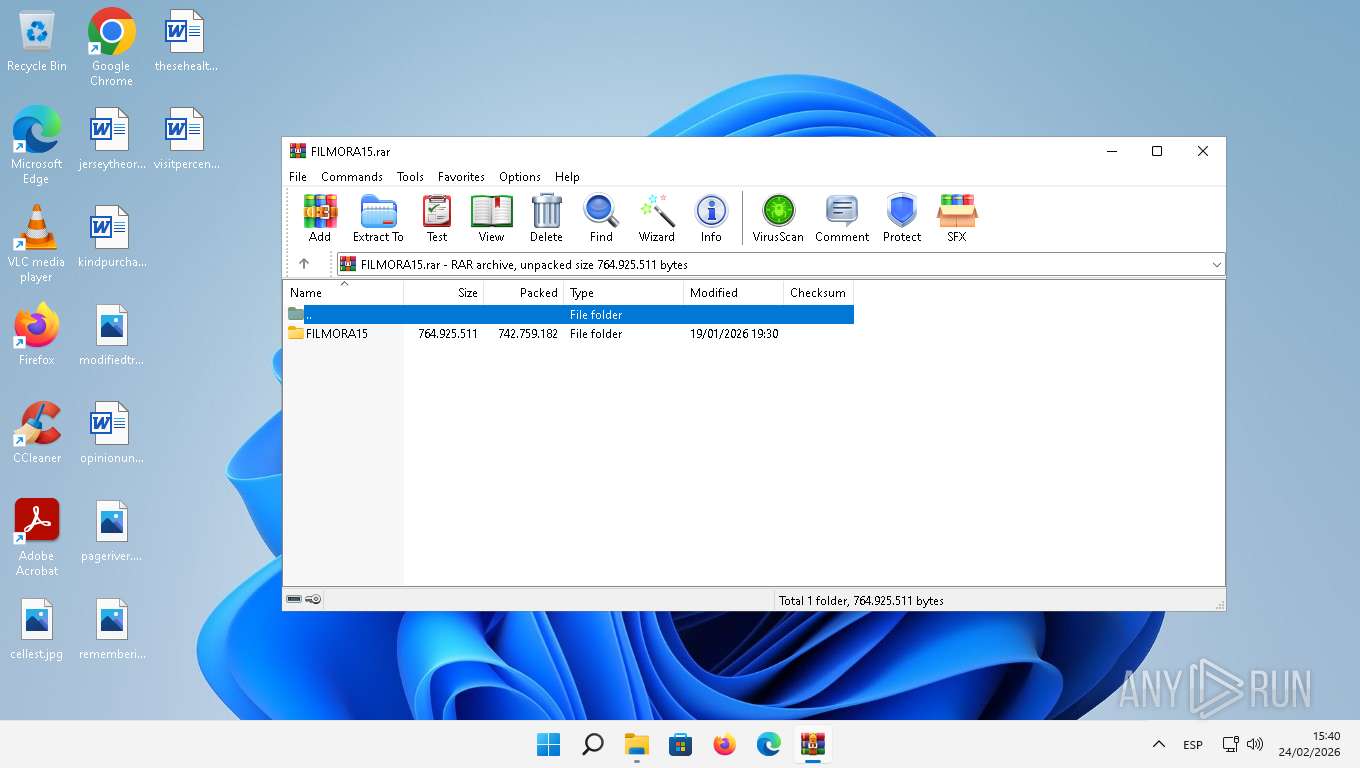
Executable content was dropped or overwritten
- WinRAR.exe (PID: 5592)
- msedge.exe (PID: 1696)
- msedge.exe (PID: 3992)
- msiexec.exe (PID: 1892)
- msedge.exe (PID: 7236)
The sample compiled with english language support
- WinRAR.exe (PID: 5592)
- Wondershare Filmora v15.1.2.17051.tmp (PID: 576)
- Wondershare Filmora v15.1.2.17051.tmp (PID: 2004)
- Wondershare Filmora SubPack 1.tmp (PID: 7840)
- Wondershare Filmora SubPack 2.tmp (PID: 7064)
- Wondershare Filmora SubPack 3.tmp (PID: 1328)
- msedge.exe (PID: 1696)
- msedge.exe (PID: 3992)
- Wondershare NativePush.tmp (PID: 6160)
- Wondershare Helper Compact.tmp (PID: 3736)
- vcredist_x64.exe (PID: 5372)
- msiexec.exe (PID: 1892)
- TiWorker.exe (PID: 6868)
- msedge.exe (PID: 7236)
- Wondershare Filmora Update(x64).tmp (PID: 7972)
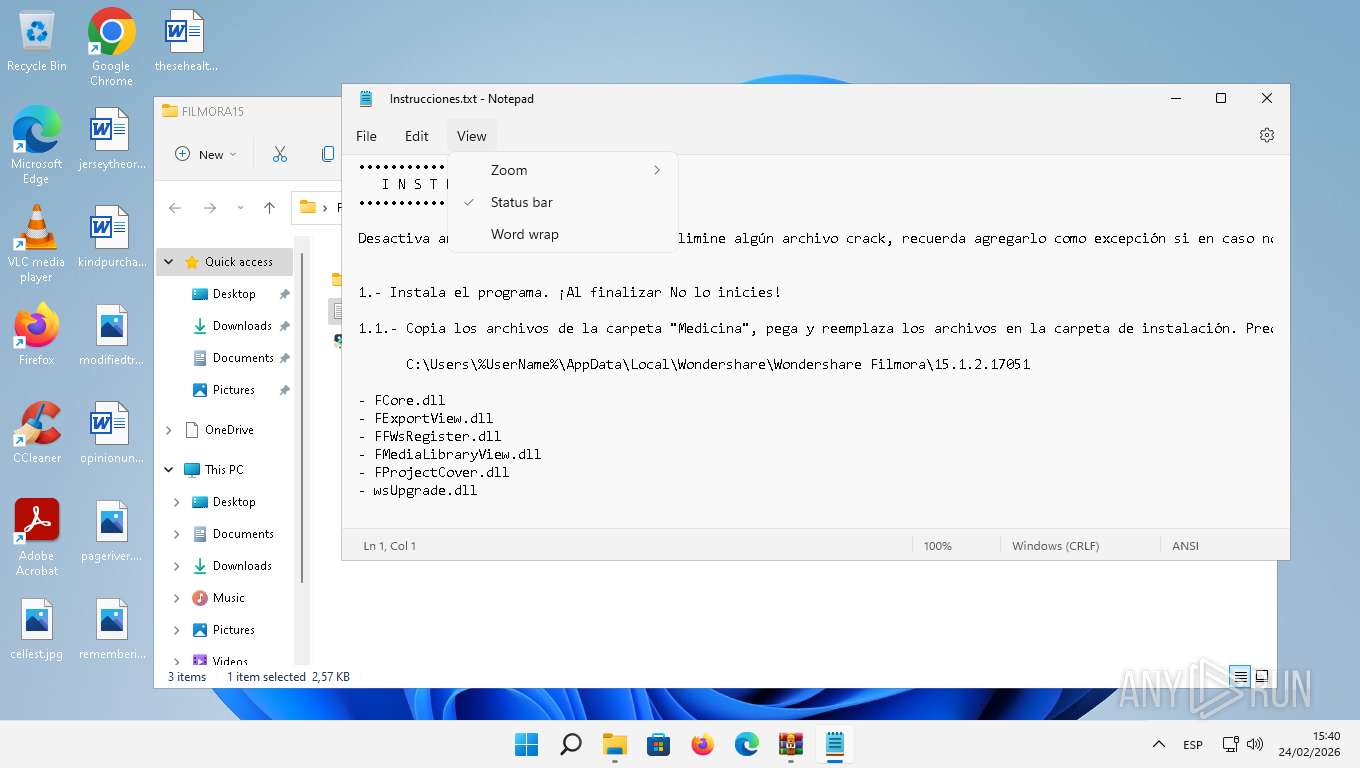
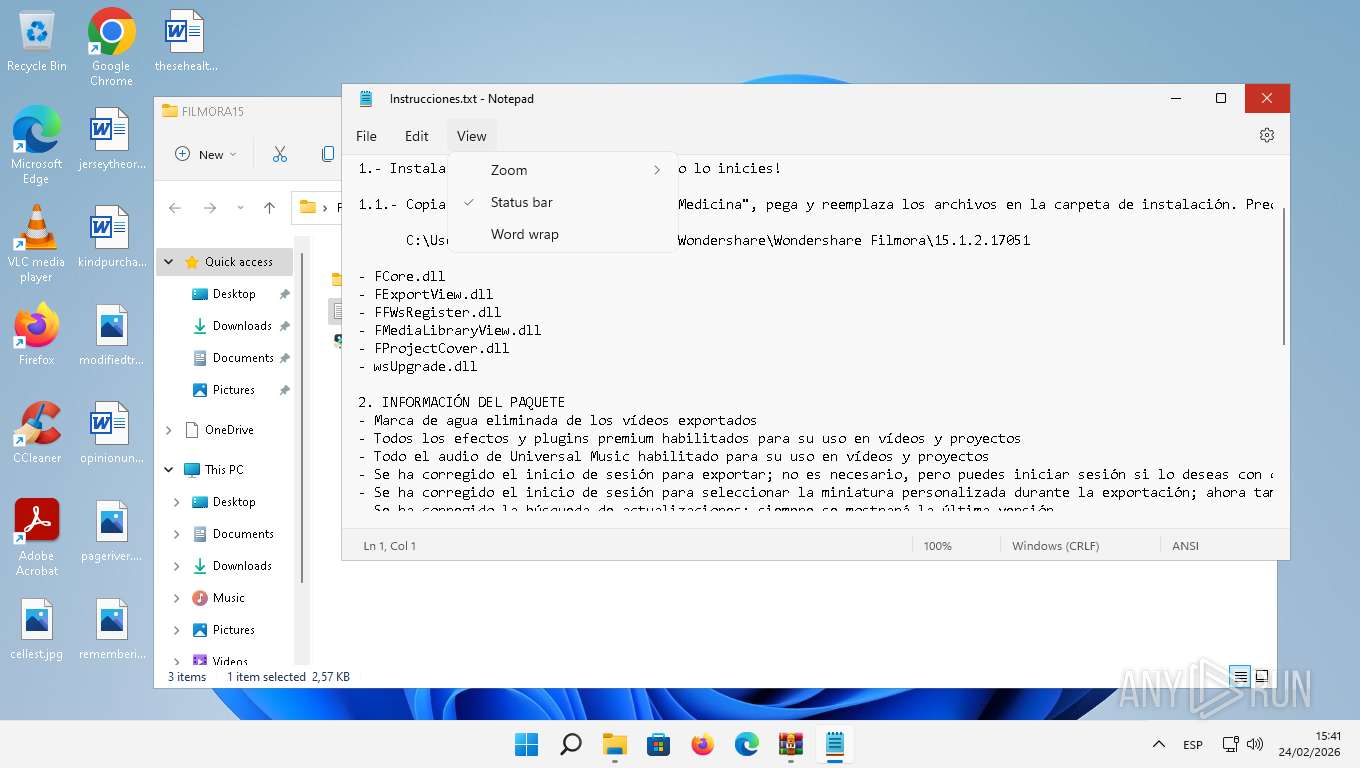
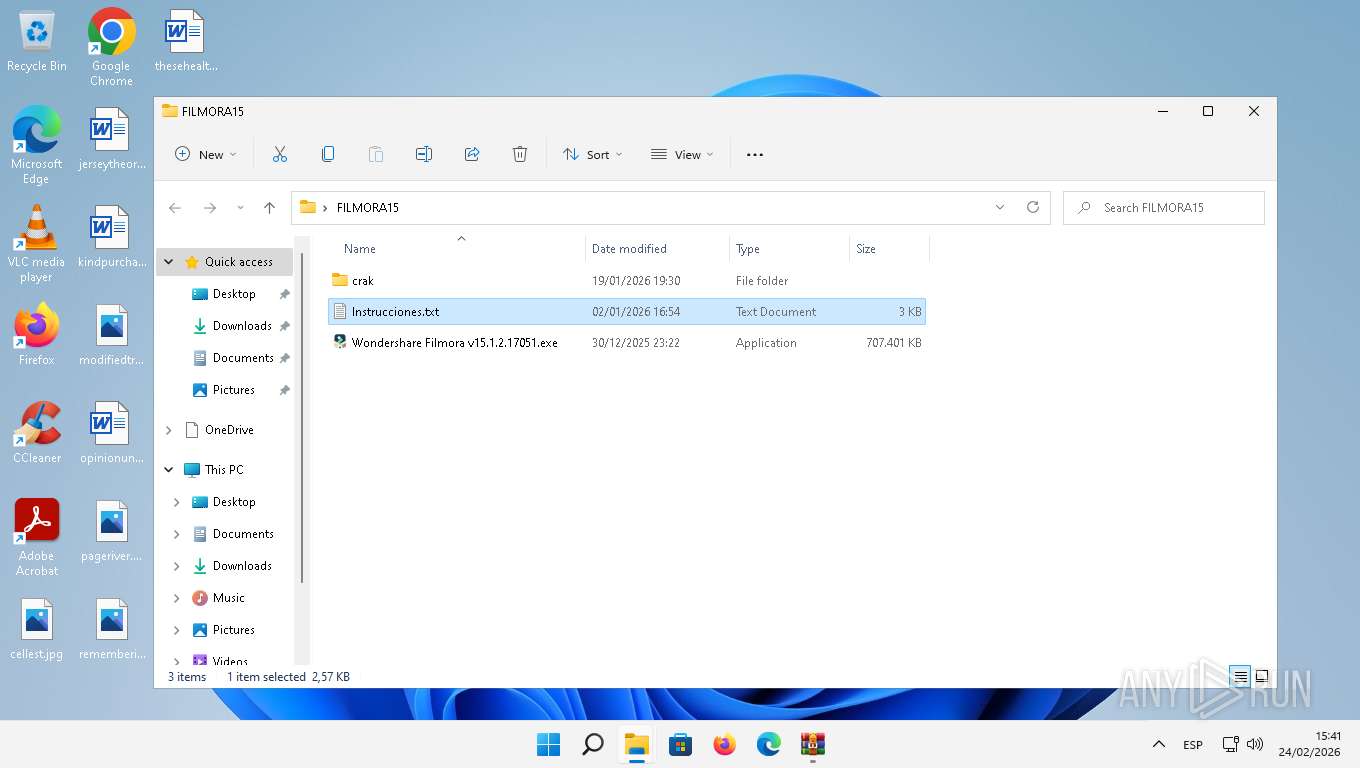
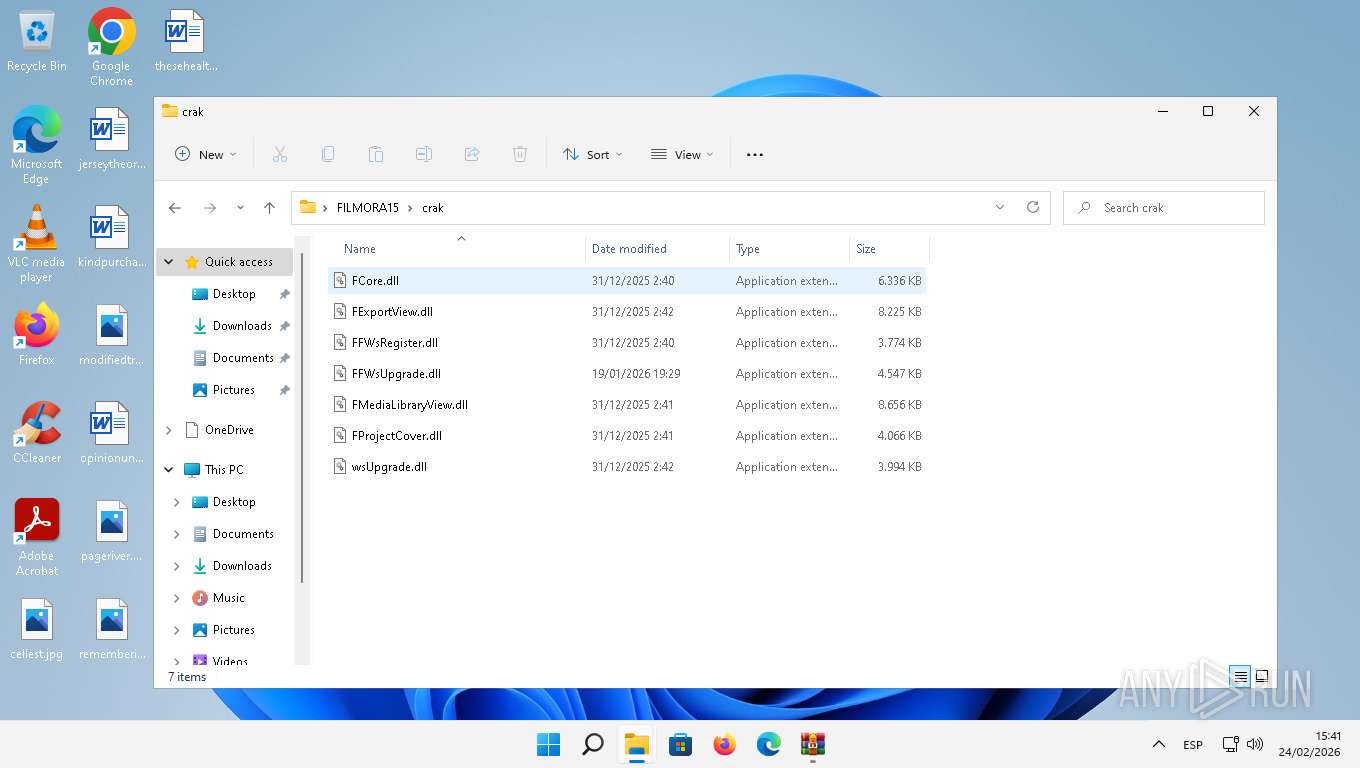
Manual execution by a user
- Notepad.exe (PID: 6936)
- Wondershare Filmora v15.1.2.17051.exe (PID: 8108)
- WSHelper.exe (PID: 2156)
- cmd.exe (PID: 3536)
The sample compiled with chinese language support
- WinRAR.exe (PID: 5592)
- Wondershare Filmora v15.1.2.17051.tmp (PID: 576)
- Wondershare Filmora v15.1.2.17051.tmp (PID: 2004)
- Wondershare Filmora SubPack 1.tmp (PID: 7840)
- Wondershare Filmora SubPack 2.tmp (PID: 7064)
- Wondershare Filmora SubPack 3.tmp (PID: 1328)
- Wondershare NativePush.exe (PID: 3180)
- Wondershare NativePush.tmp (PID: 6160)
- Wondershare Helper Compact.tmp (PID: 3736)
- vcredist_x64.exe (PID: 5372)
- TiWorker.exe (PID: 6868)
- msiexec.exe (PID: 1892)
- Wondershare Filmora Update(x64).tmp (PID: 7972)
Create files in a temporary directory
- Wondershare Filmora v15.1.2.17051.exe (PID: 8108)
- Wondershare Launcher.exe (PID: 1428)
- Wondershare Filmora v15.1.2.17051.exe (PID: 7604)
- Wondershare Filmora v15.1.2.17051.tmp (PID: 576)
- Wondershare Filmora v15.1.2.17051.tmp (PID: 2004)
- Wondershare Filmora SubPack 1.exe (PID: 2248)
- Wondershare Filmora SubPack 1.tmp (PID: 7840)
- Wondershare Filmora SubPack 2.exe (PID: 3160)
- Wondershare Filmora SubPack 2.tmp (PID: 7064)
- Wondershare Filmora SubPack 3.tmp (PID: 1328)
- Wondershare Filmora SubPack 3.exe (PID: 3392)
- Wondershare NativePush.exe (PID: 3180)
- Wondershare NativePush.tmp (PID: 6160)
- WsNativePushService.exe (PID: 7932)
- Wondershare Helper Compact.exe (PID: 7896)
- WsToastNotification.exe (PID: 2708)
- Wondershare Helper Compact.tmp (PID: 3736)
- install.exe (PID: 8016)
- Wondershare Filmora.exe (PID: 7696)
- Performance.exe (PID: 7500)
- FilmoraPlayer.exe (PID: 1520)
- ofx_check.exe (PID: 1808)
- coremediaserver.exe (PID: 2724)
- Wondershare Filmora Update(x64).exe (PID: 6796)
- Wondershare Filmora Update(x64).tmp (PID: 7972)
- WebBrowser.exe (PID: 3500)
Detects InnoSetup installer (YARA)
- Wondershare Filmora v15.1.2.17051.exe (PID: 8108)
- Wondershare Filmora v15.1.2.17051.tmp (PID: 576)
- Wondershare Filmora v15.1.2.17051.exe (PID: 7604)
- Wondershare Filmora v15.1.2.17051.tmp (PID: 2004)
- Wondershare Filmora SubPack 3.exe (PID: 3392)
- Wondershare Filmora SubPack 1.exe (PID: 2248)
- Wondershare Filmora SubPack 2.exe (PID: 3160)
- Wondershare Filmora SubPack 1.tmp (PID: 7840)
- Wondershare Filmora SubPack 2.tmp (PID: 7064)
- Wondershare Filmora SubPack 3.tmp (PID: 1328)
Compiled with Borland Delphi (YARA)
- Wondershare Filmora v15.1.2.17051.exe (PID: 8108)
- Wondershare Filmora v15.1.2.17051.tmp (PID: 576)
- Wondershare Filmora v15.1.2.17051.exe (PID: 7604)
- Wondershare Filmora v15.1.2.17051.tmp (PID: 2004)
- Wondershare Filmora SubPack 1.tmp (PID: 7840)
- Wondershare Filmora SubPack 1.exe (PID: 2248)
- Wondershare Filmora SubPack 2.exe (PID: 3160)
- Wondershare Filmora SubPack 2.tmp (PID: 7064)
- Wondershare Filmora SubPack 3.exe (PID: 3392)
- Wondershare Filmora SubPack 3.tmp (PID: 1328)
- WSHelper.exe (PID: 2156)
Creates files in the program directory
- Wondershare Filmora v15.1.2.17051.tmp (PID: 2004)
- Wondershare Helper Compact.tmp (PID: 3736)
- WSHelper.exe (PID: 2900)
- WSHelper.exe (PID: 2156)
- Wondershare Filmora.exe (PID: 7696)
- WebBrowser.exe (PID: 3500)
- CefViewWing.exe (PID: 2956)
- DataReporting.exe (PID: 4424)
- PlayServer.exe (PID: 2456)
Creates files or folders in the user directory
- Wondershare Filmora v15.1.2.17051.tmp (PID: 2004)
- Wondershare Filmora SubPack 1.tmp (PID: 7840)
- Wondershare Filmora SubPack 2.tmp (PID: 7064)
- Wondershare Filmora SubPack 3.tmp (PID: 1328)
- Wondershare NativePush.tmp (PID: 6160)
- WSHelper.exe (PID: 2900)
- WsToastNotification.exe (PID: 2708)
- ie4uinit.exe (PID: 7528)
- Wondershare Filmora.exe (PID: 7696)
- PlayServer.exe (PID: 2456)
- DataReporting.exe (PID: 4424)
- FilmoraPlayer.exe (PID: 1520)
- Performance.exe (PID: 7500)
- cmdCheckATI.exe (PID: 3872)
- WebBrowser.exe (PID: 3500)
- cmdCheckHEVC.exe (PID: 7436)
- coremediaserver.exe (PID: 2724)
- Wondershare Filmora Update(x64).tmp (PID: 7972)
Creates a software uninstall entry
- Wondershare Filmora v15.1.2.17051.tmp (PID: 2004)
- Wondershare NativePush.tmp (PID: 6160)
- Wondershare Helper Compact.tmp (PID: 3736)
- msiexec.exe (PID: 1892)
Reads the machine GUID from the registry
- WsToastNotification.exe (PID: 2708)
- vcredist_x64.exe (PID: 5372)
- msiexec.exe (PID: 1892)
- Wondershare Filmora.exe (PID: 7696)
- Performance.exe (PID: 7500)
- FilmoraPlayer.exe (PID: 1520)
- DataReporting.exe (PID: 4424)
- PlayServer.exe (PID: 2456)
- WebBrowser.exe (PID: 3500)
Launching a file from a Registry key
- Wondershare Helper Compact.tmp (PID: 3736)
The sample compiled with russian language support
- vcredist_x64.exe (PID: 5372)
- msiexec.exe (PID: 1892)
- TiWorker.exe (PID: 6868)
The sample compiled with korean language support
- vcredist_x64.exe (PID: 5372)
- msiexec.exe (PID: 1892)
- TiWorker.exe (PID: 6868)
The sample compiled with japanese language support
- vcredist_x64.exe (PID: 5372)
- msiexec.exe (PID: 1892)
- TiWorker.exe (PID: 6868)
The sample compiled with french language support
- vcredist_x64.exe (PID: 5372)
- TiWorker.exe (PID: 6868)
- msiexec.exe (PID: 1892)
The sample compiled with Italian language support
- vcredist_x64.exe (PID: 5372)
- msiexec.exe (PID: 1892)
- TiWorker.exe (PID: 6868)
The sample compiled with spanish language support
- vcredist_x64.exe (PID: 5372)
- msiexec.exe (PID: 1892)
- TiWorker.exe (PID: 6868)
Checks proxy server information
- WSHelper.exe (PID: 2156)
- Wondershare Filmora.exe (PID: 7696)
- WebBrowser.exe (PID: 3500)
The sample compiled with german language support
- vcredist_x64.exe (PID: 5372)
- TiWorker.exe (PID: 6868)
- msiexec.exe (PID: 1892)
There is functionality for taking screenshot (YARA)
- WSHelper.exe (PID: 2156)
Reads CPU info
- Wondershare Filmora.exe (PID: 7696)
- Performance.exe (PID: 7500)
- cmdCheckATI.exe (PID: 3872)
- coremediaserver.exe (PID: 2724)
- cmdCheckHEVC.exe (PID: 7436)
Reads the Internet Settings
- explorer.exe (PID: 1980)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
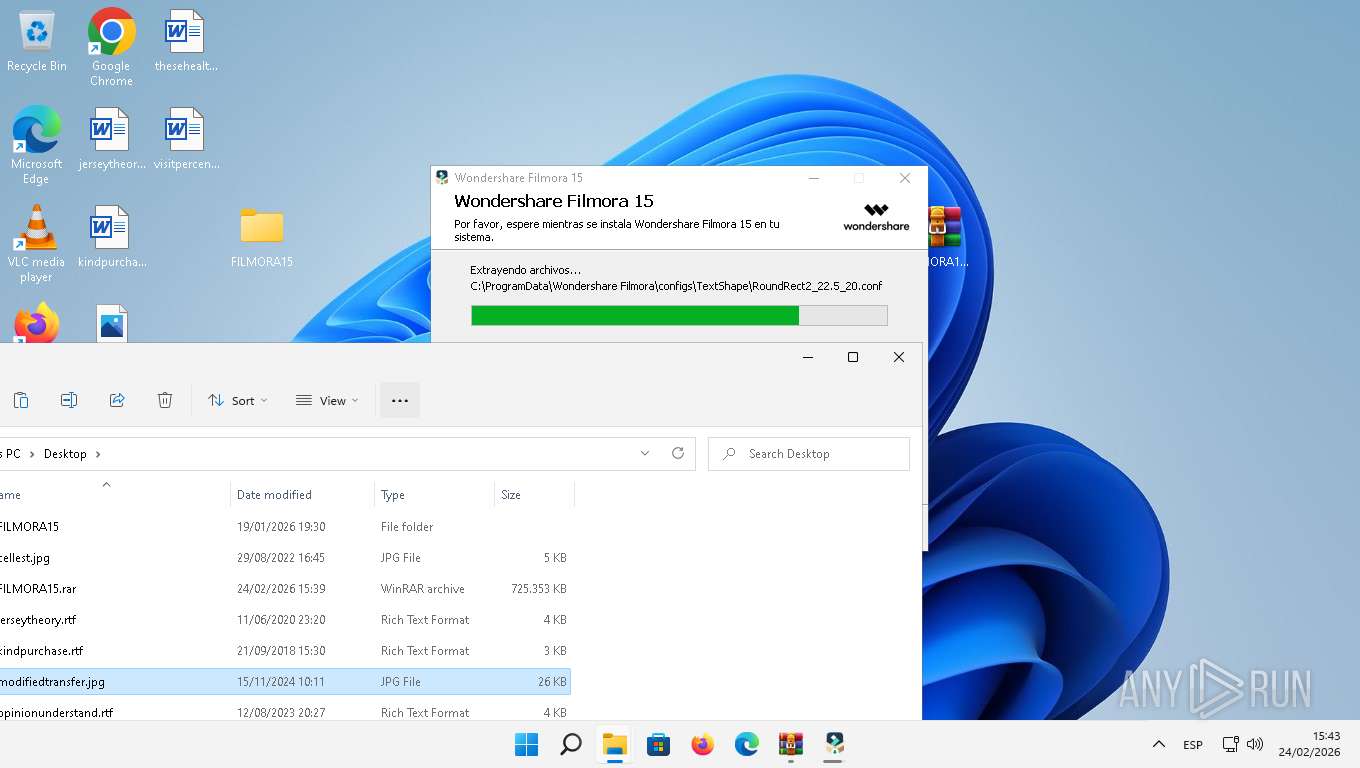
Total processes
304
Monitored processes
178
Malicious processes
8
Suspicious processes
10
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 536 | \??\C:\Windows\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | magic_xe_supported_detect.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.22000.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 576 | "C:\Users\admin\AppData\Local\Temp\is-KHOKE.tmp\Wondershare Filmora v15.1.2.17051.tmp" /SL5="$600D4,722143970,401920,C:\Users\admin\Desktop\FILMORA15\Wondershare Filmora v15.1.2.17051.exe" | C:\Users\admin\AppData\Local\Temp\is-KHOKE.tmp\Wondershare Filmora v15.1.2.17051.tmp | Wondershare Filmora v15.1.2.17051.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 788 | "C:\Program Files (x86)\Google\GoogleUpdater\135.0.7023.0\updater.exe" --wake --system | C:\Program Files (x86)\Google\GoogleUpdater\135.0.7023.0\updater.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Google LLC Integrity Level: SYSTEM Description: Google Updater Exit code: 0 Version: 135.0.7023.0 Modules
| |||||||||||||||
| 892 | find /I /N "WsToastNotification.exe" | C:\Windows\System32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (grep) Utility Exit code: 1 Version: 10.0.22000.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 900 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=gpu-process --string-annotations --gpu-preferences=UAAAAAAAAADgAAAEAAAAAAAAAAAAAAAAAABgAAEAAAAAAAAAAAAAAAAAAAACAAAAAAAAAAAAAAAAAAAAAAAAABAAAAAAAAAAEAAAAAAAAAAIAAAAAAAAAAgAAAAAAAAA --always-read-main-dll --field-trial-handle=1916,i,10353432696406222046,212634301285576645,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version --mojo-platform-channel-handle=1936 /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1028 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --disable-quic --message-loop-type-ui --string-annotations --always-read-main-dll --field-trial-handle=5024,i,4150068317980714789,2678932716247315731,262144 --variations-seed-version --mojo-platform-channel-handle=4916 /prefetch:14 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1108 | "cmd.exe" /C tasklist /FI "IMAGENAME eq WsNativePushService.exe" 2>NUL | find /I /N "WsNativePushService.exe" | C:\Windows\System32\cmd.exe | — | Wondershare NativePush.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 10.0.22000.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1156 | \??\C:\Windows\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | _setup64.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.22000.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1172 | "C:\Program Files (x86)\Microsoft\Edge\Application\133.0.3065.92\identity_helper.exe" --type=utility --utility-sub-type=winrt_app_id.mojom.WinrtAppIdService --lang=en-US --service-sandbox-type=none --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=4620,i,4150068317980714789,2678932716247315731,262144 --variations-seed-version --mojo-platform-channel-handle=4516 /prefetch:14 | C:\Program Files (x86)\Microsoft\Edge\Application\133.0.3065.92\identity_helper.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: PWA Identity Proxy Host Exit code: 3221226029 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1176 | helper 105 0x43C | C:\Users\admin\AppData\Local\Temp\is-9CSK2.tmp\_isetup\_setup64.tmp | — | Wondershare Filmora Update(x64).tmp | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
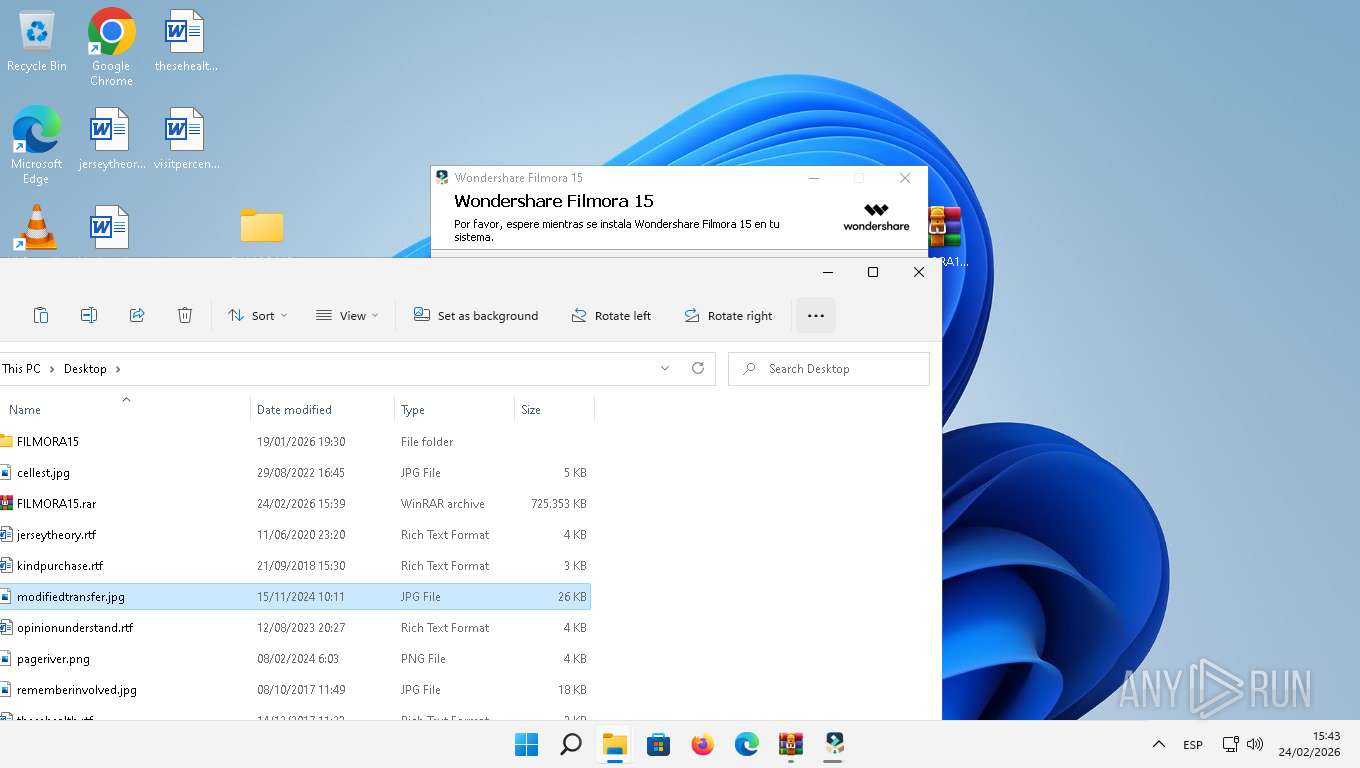
Total events
183 351
Read events
104 589
Write events
38 718
Delete events
40 044
Modification events
| (PID) Process: | (5212) OpenWith.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MrtCache\C:%5CProgram Files%5CWindowsApps%5CMicrosoft.WindowsNotepad_11.2205.11.0_x64__8wekyb3d8bbwe%5Cmicrosoft.system.package.metadata%5CS-1-5-21-166304369-59083888-3082702900-1001-MergedResources-1.pri\1d89c6c72eec470\e0fa8f0 |
| Operation: | write | Name: | @{Microsoft.WindowsNotepad_11.2205.11.0_x64__8wekyb3d8bbwe?ms-resource://Microsoft.WindowsNotepad/Resources/AppDisplayName_Notepad} |
Value: Notepad | |||
| (PID) Process: | (5212) OpenWith.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\4e\52C64B7E |
| Operation: | write | Name: | @C:\Program Files\Microsoft Office\root\VFS\ProgramFilesCommonX64\Microsoft Shared\Office16\oregres.dll,-205 |
Value: Word | |||
| (PID) Process: | (5212) OpenWith.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\4e\52C64B7E |
| Operation: | write | Name: | @wmploc.dll,-102 |
Value: Windows Media Player | |||
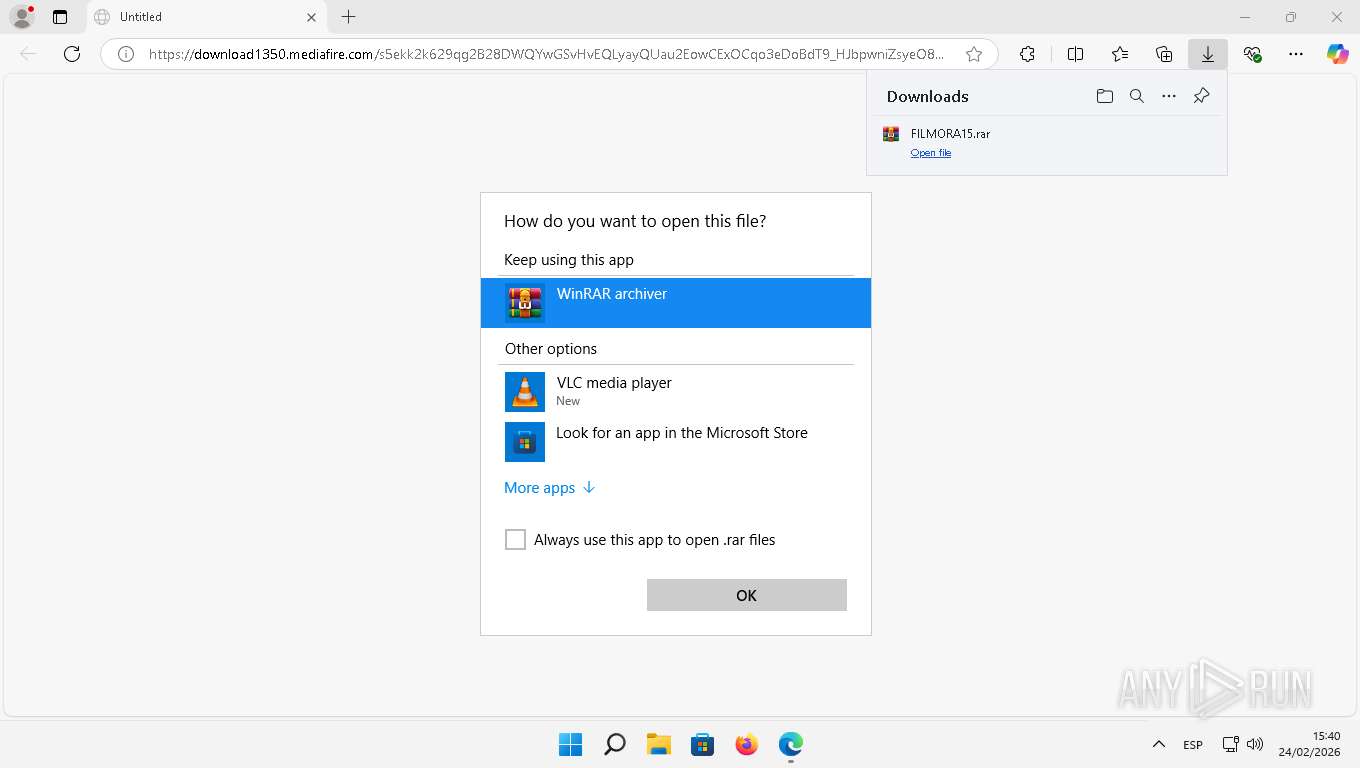
| (PID) Process: | (5212) OpenWith.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.rar\OpenWithProgids |
| Operation: | write | Name: | WinRAR |
Value: | |||
| (PID) Process: | (1868) OpenWith.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.rar\OpenWithProgids |
| Operation: | write | Name: | WinRAR |
Value: | |||
| (PID) Process: | (6576) OpenWith.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.rar\OpenWithProgids |
| Operation: | write | Name: | WinRAR |
Value: | |||
| (PID) Process: | (1300) OpenWith.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.rar\OpenWithProgids |
| Operation: | write | Name: | WinRAR |
Value: | |||
| (PID) Process: | (6888) OpenWith.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.rar\OpenWithProgids |
| Operation: | write | Name: | WinRAR |
Value: | |||
| (PID) Process: | (6888) OpenWith.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\ApplicationAssociationToasts |
| Operation: | write | Name: | VLC.rar_.rar |
Value: 0 | |||
| (PID) Process: | (6888) OpenWith.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\ApplicationAssociationToasts |
| Operation: | write | Name: | AppXkv2jqn1pq8ajm0p5dhgqde7aafykkrrn_.rar |
Value: 0 | |||
Executable files
1 545
Suspicious files
1 496
Text files
13 498
Unknown types
61
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6292 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Profile 1\ClientCertificates\LOG.old~RF128bcd.TMP | — | |
MD5:— | SHA256:— | |||
| 6292 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Profile 1\ClientCertificates\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6292 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Profile 1\PersistentOriginTrials\LOG.old~RF128bec.TMP | — | |
MD5:— | SHA256:— | |||
| 6292 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Profile 1\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6292 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Profile 1\discounts_db\LOG.old~RF128bec.TMP | — | |
MD5:— | SHA256:— | |||
| 6292 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Profile 1\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6292 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Profile 1\LOG.old~RF128bec.TMP | — | |
MD5:— | SHA256:— | |||
| 6292 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Profile 1\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6292 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Profile 1\parcel_tracking_db\LOG.old~RF128c0c.TMP | — | |
MD5:— | SHA256:— | |||
| 6292 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Profile 1\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
237
TCP/UDP connections
370
DNS requests
354
Threats
73
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4044 | msedge.exe | GET | — | 205.196.123.38:443 | https://download1350.mediafire.com/s5ekk2k629qg2B28DWQYwGSvHvEQLyayQUau2EowCExOCqo3eDoBdT9_HJbpwniZsyeO8zoVh6sn_W2A6TxV6J_opAIzXn7IzVgPuT3pMaaw57aFcijpx8Ku6_2VATIzi5m7vT1XC1OImtXqupCiYwH5YtPIyljmgfjYsWzT7-sAWA/x8kx5v4jsa77nr5/FILMORA15.rar | unknown | — | — | unknown |
4044 | msedge.exe | GET | 304 | 150.171.28.11:443 | https://edge.microsoft.com/abusiveadblocking/api/v1/blocklist | unknown | — | — | whitelisted |
4080 | svchost.exe | GET | 304 | 2.16.168.39:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?7fd7302d7c852bb7 | unknown | — | — | unknown |
— | — | GET | 200 | 23.55.161.155:80 | http://www.msftconnecttest.com/connecttest.txt | unknown | — | — | unknown |
3292 | OfficeClickToRun.exe | GET | 304 | 2.16.168.39:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?75851085d8530717 | unknown | — | — | unknown |
4044 | msedge.exe | GET | 200 | 150.171.27.11:80 | http://edge.microsoft.com/browsernetworktime/time/1/current?cup2key=2:enKr4aCUNpxDCdgqMtEQdmoyNjw38RIKl3mug75VwZY&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | unknown | — | — | whitelisted |
4080 | svchost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
3292 | OfficeClickToRun.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
4044 | msedge.exe | GET | 200 | 104.18.23.222:443 | https://copilot.microsoft.com/c/api/user/eligibility | unknown | text | 25 b | whitelisted |
4044 | msedge.exe | GET | 200 | 150.171.28.11:443 | https://edge.microsoft.com/serviceexperimentation/v3/?osname=win&channel=stable&osver=10.0.22000&devicefamily=desktop&installdate=1645822881&clientversion=133.0.3065.92&experimentationmode=2&scpguard=0&scpfull=0&scpver=0 | unknown | text | 446 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 52.110.17.75:443 | officeclient.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:137 | — | Not routed | — | whitelisted |
— | — | 23.55.161.155:80 | — | AKAMAI-ASN1 | NL | whitelisted |
3876 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
2800 | svchost.exe | 104.102.63.189:443 | fs.microsoft.com | AKAMAI-AS | US | whitelisted |
4080 | svchost.exe | 20.190.159.4:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4080 | svchost.exe | 2.16.168.39:80 | ctldl.windowsupdate.com | AKAMAI-ASN1 | NL | whitelisted |
4080 | svchost.exe | 184.30.131.245:80 | ocsp.digicert.com | AKAMAI-AS | US | whitelisted |
3292 | OfficeClickToRun.exe | 20.50.73.9:443 | self.events.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4044 | msedge.exe | 150.171.28.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
officeclient.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
fs.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
download1350.mediafire.com |
| unknown |
api.edgeoffer.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Misc activity | ET INFO Microsoft Connection Test |
4044 | msedge.exe | Potentially Bad Traffic | ET FILE_SHARING File Sharing Related Domain in DNS Lookup (download .mediafire .com) |
4044 | msedge.exe | Potentially Bad Traffic | ET FILE_SHARING File Sharing Related Domain in DNS Lookup (download .mediafire .com) |
3284 | svchost.exe | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |
1736 | svchost.exe | Misc activity | INFO [ANY.RUN] .cc TLD domain request |
1616 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
1616 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
1616 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
7696 | Wondershare Filmora.exe | Misc activity | INFO [ANY.RUN] USER_AGENTS Suspicious User-Agent (Mozilla/5.0) |
7696 | Wondershare Filmora.exe | Misc activity | INFO [ANY.RUN] USER_AGENTS Suspicious User-Agent (Mozilla/5.0) |
Process | Message |
|---|---|
WSHelper.exe | HTTP/1.1 200 OK |
TiWorker.exe | |
TiWorker.exe | SKU MDM licensing allow list string from SLAPI:
|
TiWorker.exe | Populating UpdatePolicy AllowList |
TiWorker.exe | All policies are allowed
|
TiWorker.exe | AboveLock|Accounts|ActiveXControls|ADMXIngest|AllowMessageSync|AppHVSI|ApplicationDefaults|AllowAllTrustedApps|AllowAppStoreAutoUpdate|AllowAutomaticAppArchiving|AllowDeveloperUnlock|AllowGameDVR|AllowSharedUserAppData|ApplicationRestrictions|Audit|ConfigureChatIcon|LaunchAppAfterLogOn|MSIAllowUserControlOverInstall|MSIAlwaysInstallWithElevatedPrivileges|RestrictAppDataToSystemVolume|RestrictAppToSystemVolume|AppRuntime|AttachmentManager|Authentication|Autoplay|BitLocker|BITS|Bluetooth|Browser|Camera|Cellular|Connectivity|ControlPolicyConflict|CredentialProviders|CredentialsDelegation|CredentialsUI|Cryptography|DataProtection|DataUsage|Defender|DeliveryOptimization|Desktop|ConfigureSystemGuardLaunch|EnableVirtualizationBasedSecurity|DeviceHealthMonitoring|DeviceInstallation|DeviceLock|Display|DmaGuard|ErrorReporting|Eap|Education|EnterpriseCloudPrint|EventLogService|AllowClipboardHistory|AllowCopyPaste|AllowCortana|AllowDeviceDiscovery|AllowManualMDMUnenrollment|AllowSaveAsOfOfficeFiles|AllowScreenCapture|AllowSharingOfOfficeFiles|AllowSIMErrorDialogPromptWhenNoSIM|AllowSyncMySettings|AllowTailoredExperiencesWithDiagnosticData|AllowTaskSwitcher|AllowThirdPartySuggestionsInWindowsSpotlight|AllowVoiceRecording|DoNotShowFeedbackNotifications|DoNotSyncBrowserSettings|AllowFindMyDevice|ExploitGuard|Feeds|FileExplorer|Games|Handwriting|HumanPresence|InternetExplorer|Kerberos|KioskBrowser|Knobs|LanmanWorkstation|Licensing|LocalPoliciesSecurityOptions|LocalUsersAndGroups|Lockdown|Maps|MemoryDump|MSSecurityGuide|MSSLegacy|Multitasking|NetworkIsolation|NetworkListManager|NewsAndInterests|Notifications|OneDrive|Power|Printers|Privacy|RemoteAssistance|RemoteDesktopServices|RemoteDesktop|RemoteManagement|RemoteProcedureCall|RemoteShell|RestrictedGroups|Search|Security|Settings|SmartScreen|Speech|Start|Storage|System|SystemServices|TaskManager|TaskScheduler|TenantRestrictions|TextInput|TimeLanguageSettings|Troubleshooting|Update|UserRights|VirtualizationBasedTechnology|WiFi|WindowsLogon|WirelessDisplay|Location|WindowsAutopilot|WindowsConnectionManager|WindowsDefenderSecurityCenter|WindowsInkWorkspace|WindowsPowerShell|WindowsSandbox|WiredNetwork|ADMX_ |
WSHelper.exe | HTTP/1.1 200 OK |
WSHelper.exe | HTTP/1.1 404 Not Found |
WSHelper.exe | HTTP/1.1 404 Not Found |
WSHelper.exe | HTTP/1.1 404 Not Found |