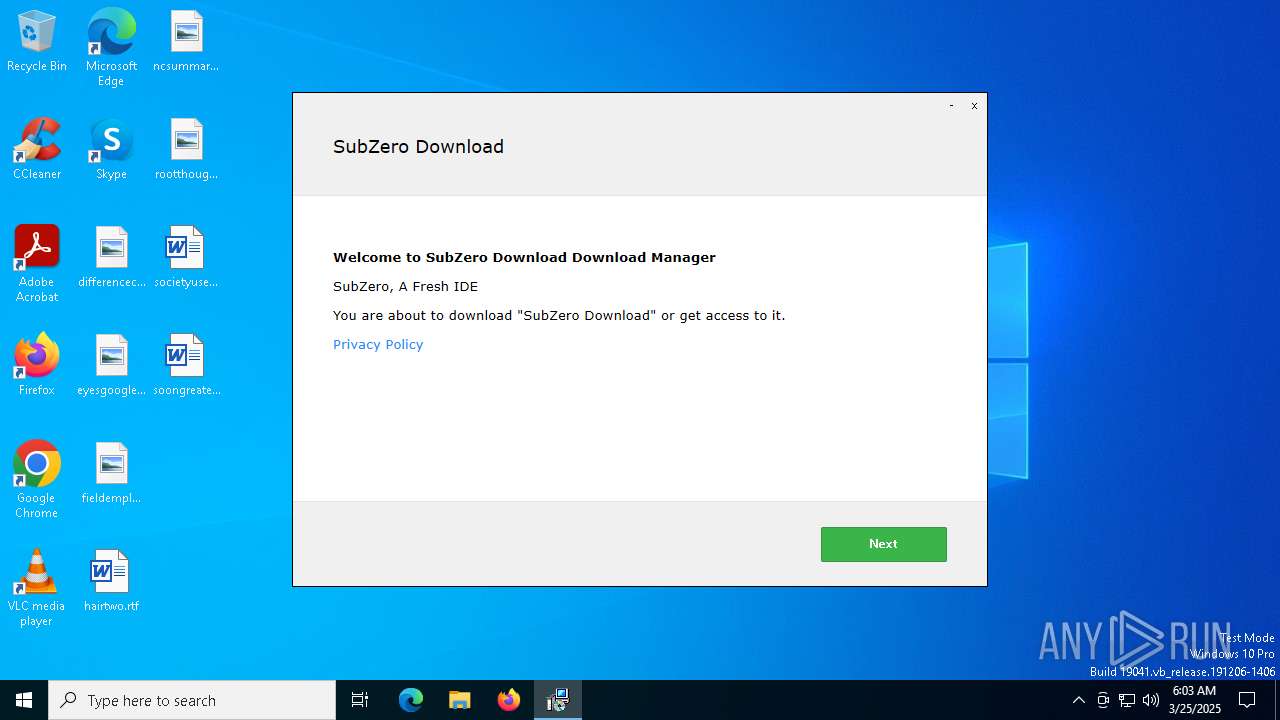
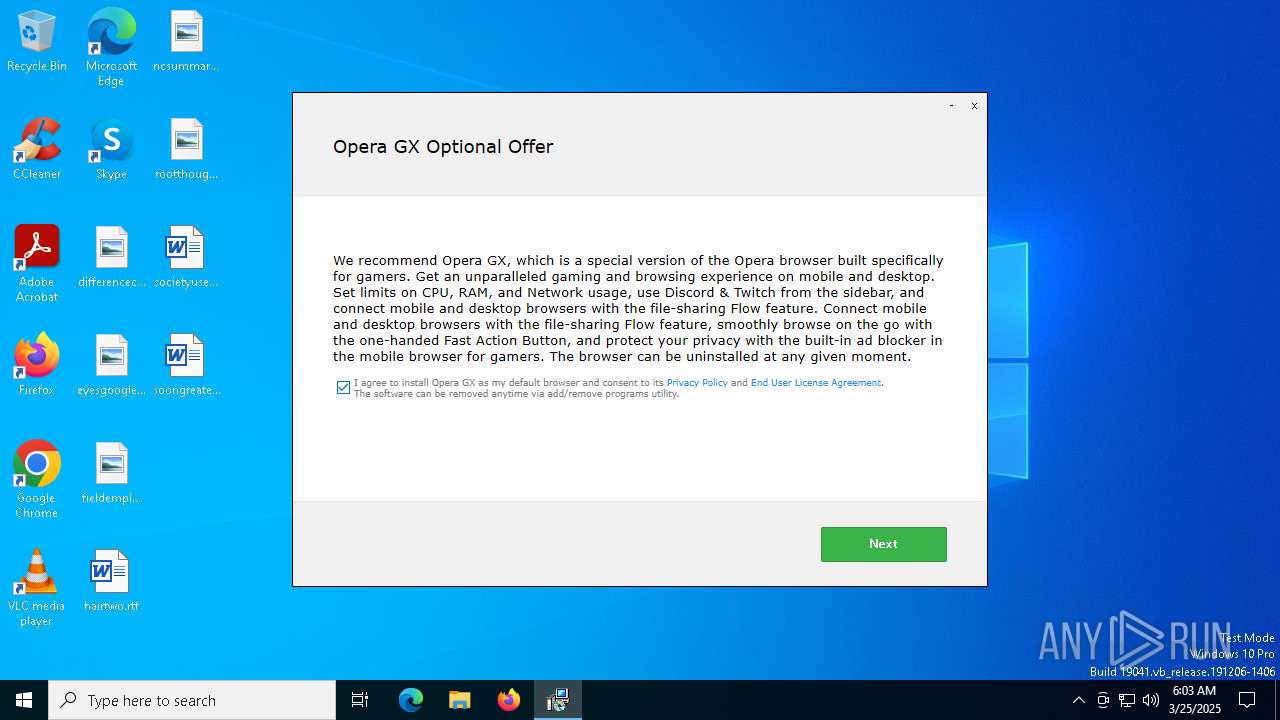
| File name: | SubZero Download_88231676.exe |
| Full analysis: | https://app.any.run/tasks/5a8851f0-52f3-4a7d-b368-4eb6b5c0e3c6 |
| Verdict: | Malicious activity |
| Analysis date: | March 25, 2025, 06:03:20 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 5 sections |
| MD5: | 15D1C495FF66BF7CEA8A6D14BFDF0A20 |
| SHA1: | 942814521FA406A225522F208AC67F90DBDE0AE7 |
| SHA256: | 61C2C4A5D7C14F77EE88871DED4CC7F1E49DAE3E4EF209504C66FEDF4D22DE42 |
| SSDEEP: | 98304:DtjM+LgnHM8mNLNpOmMGl2p9tjIQh+1GHp8PGmDFzMVv3kdcpR41TBN14BC6SkPT:Kw8 |
MALICIOUS
GENERIC has been found (auto)
- SubZero Download_88231676.exe (PID: 7148)
SUSPICIOUS
There is functionality for taking screenshot (YARA)
- SubZero Download_88231676.exe (PID: 7148)
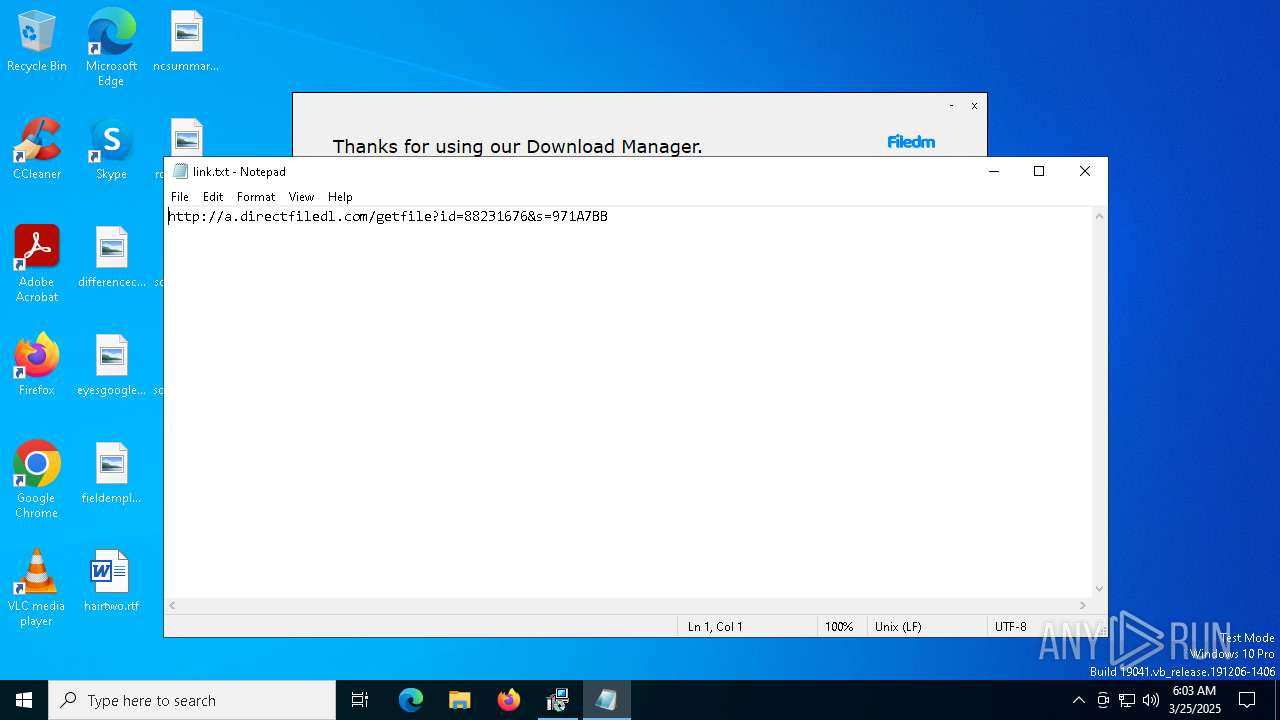
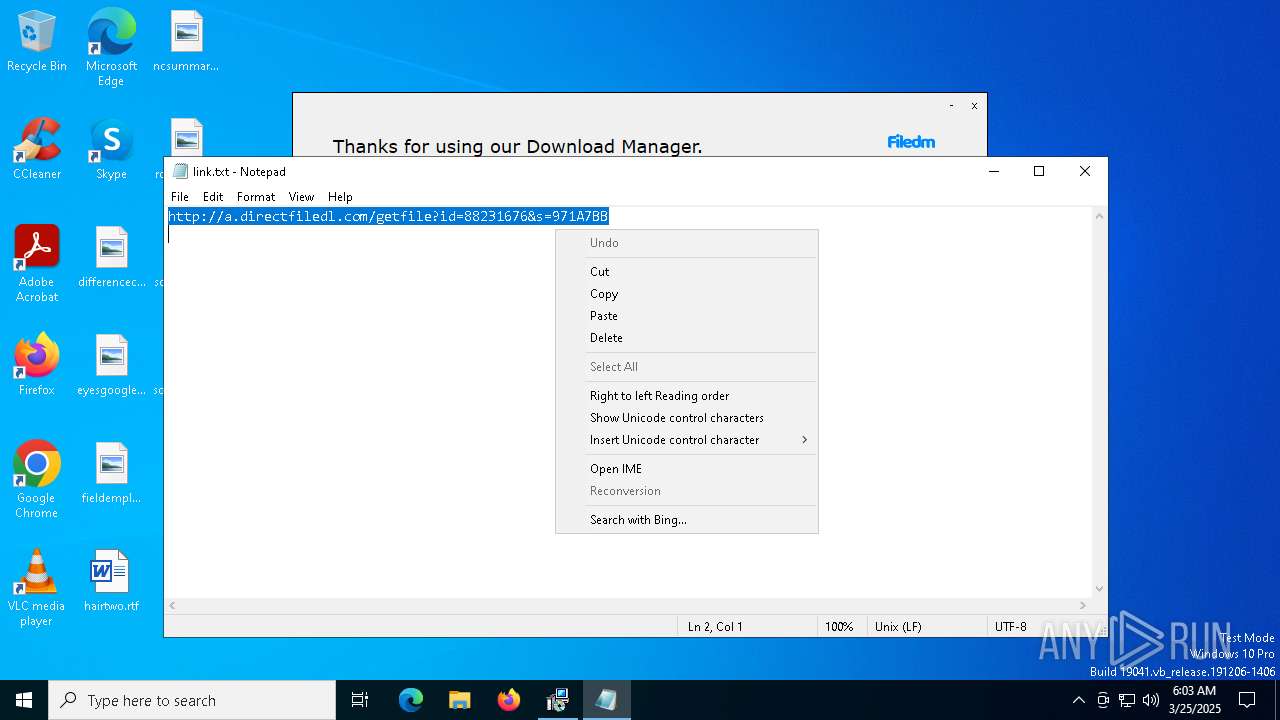
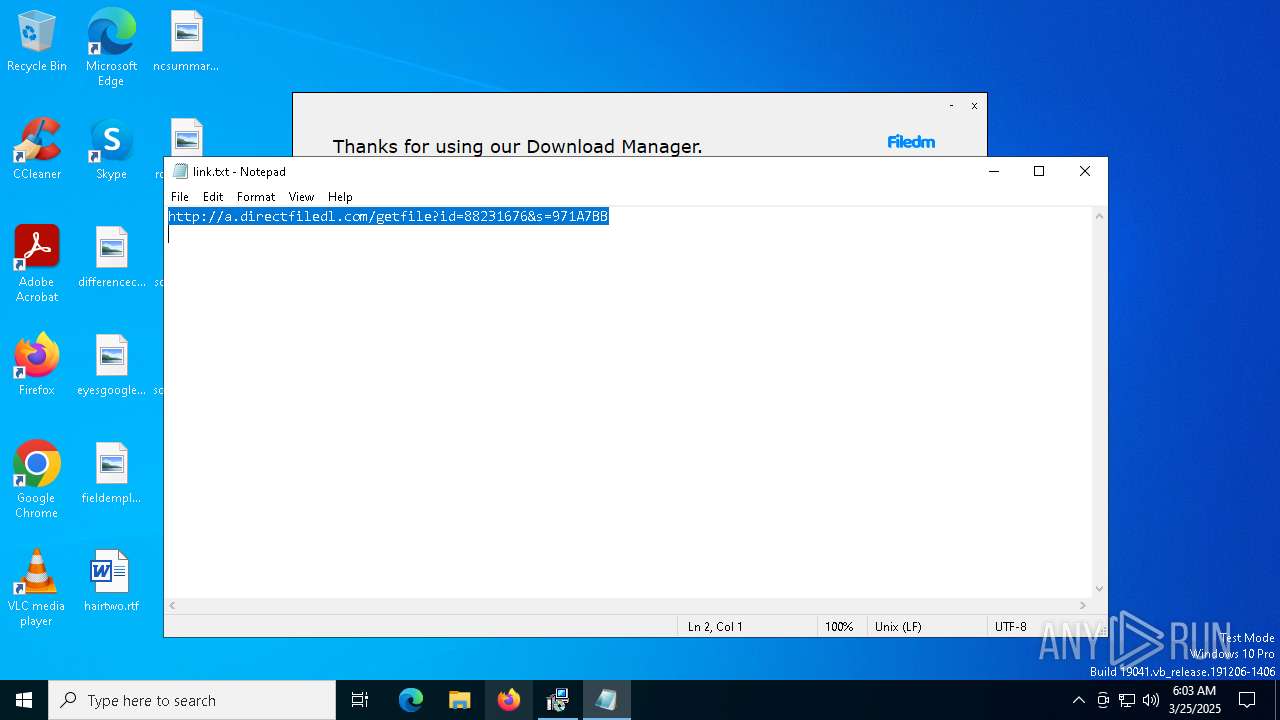
Start notepad (likely ransomware note)
- SubZero Download_88231676.exe (PID: 7148)
Reads security settings of Internet Explorer
- SubZero Download_88231676.exe (PID: 7148)
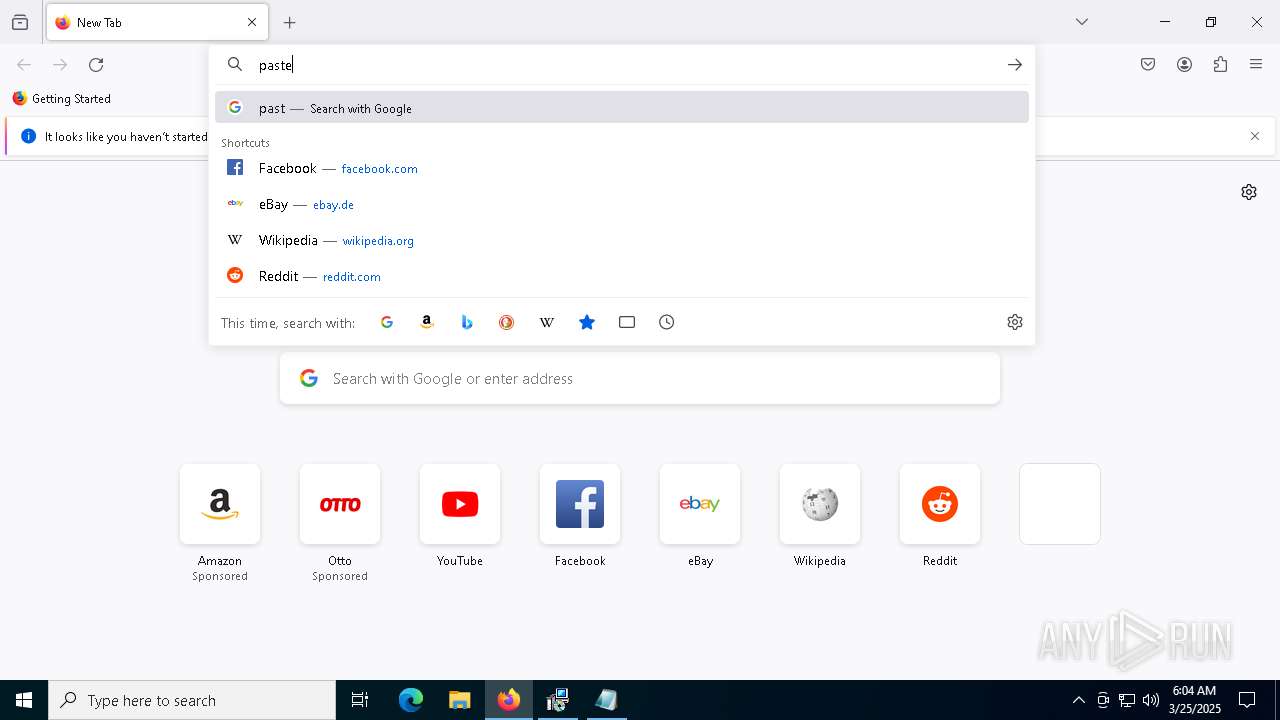
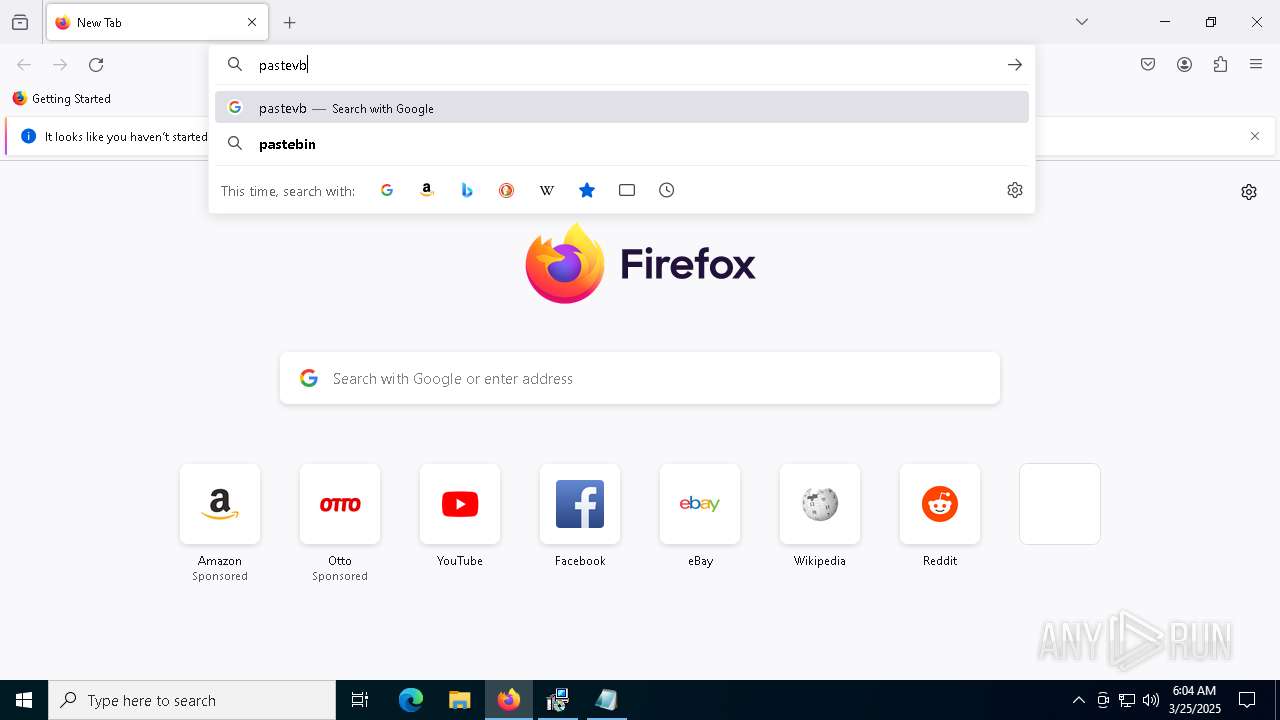
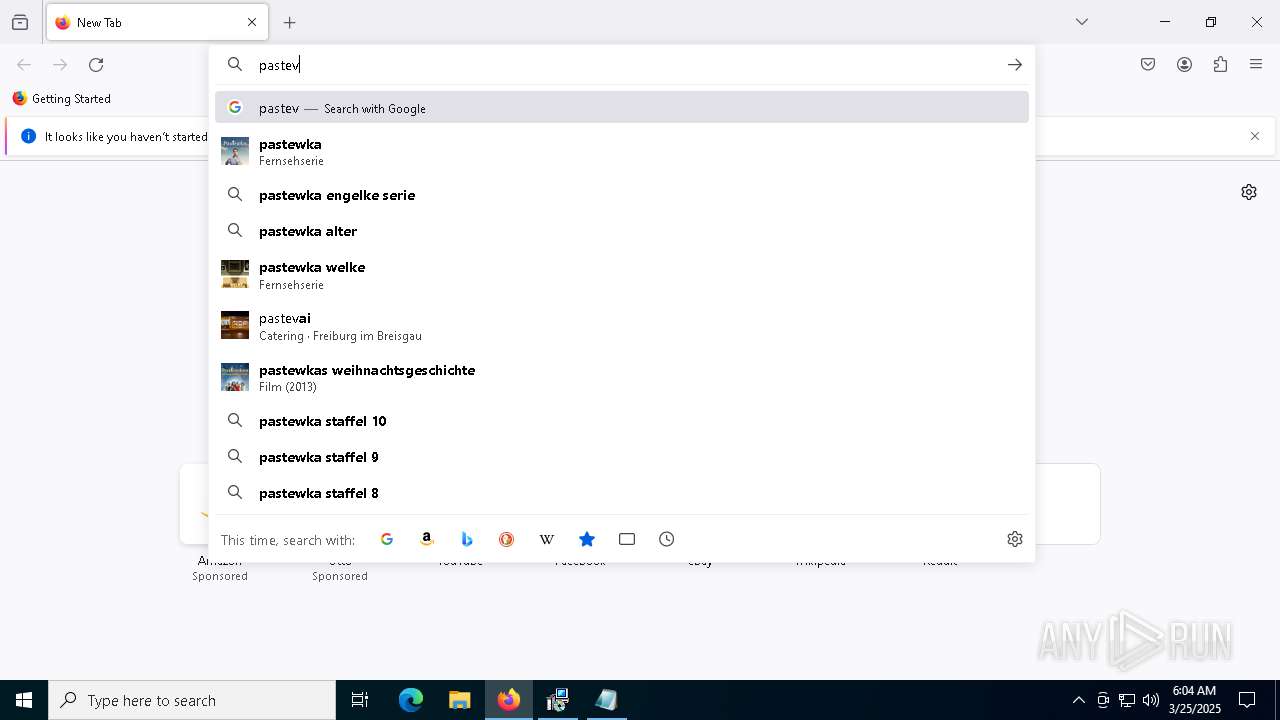
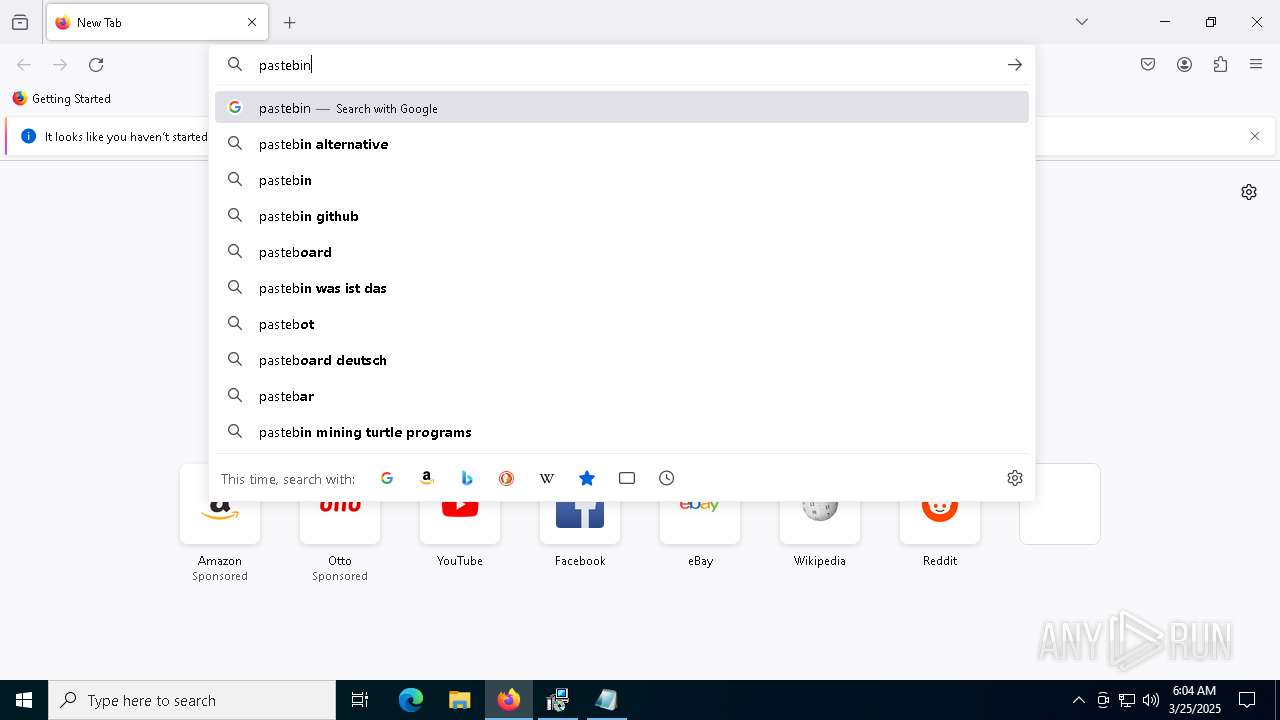
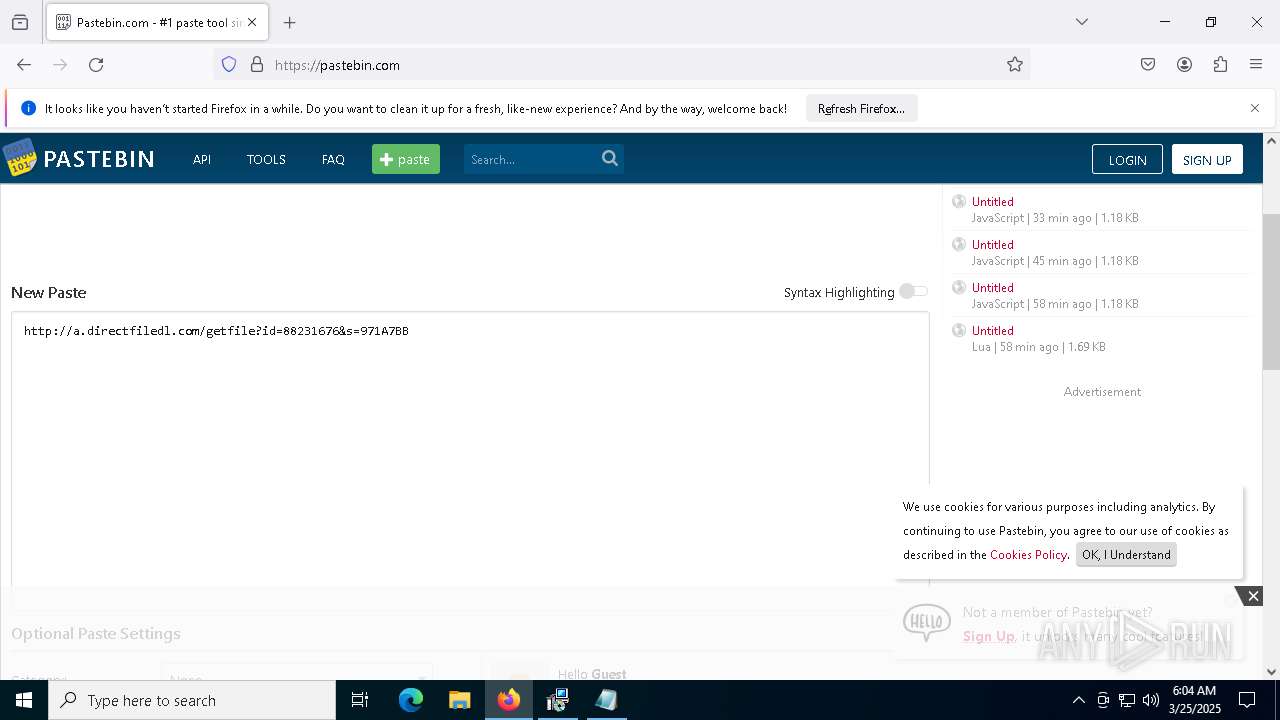
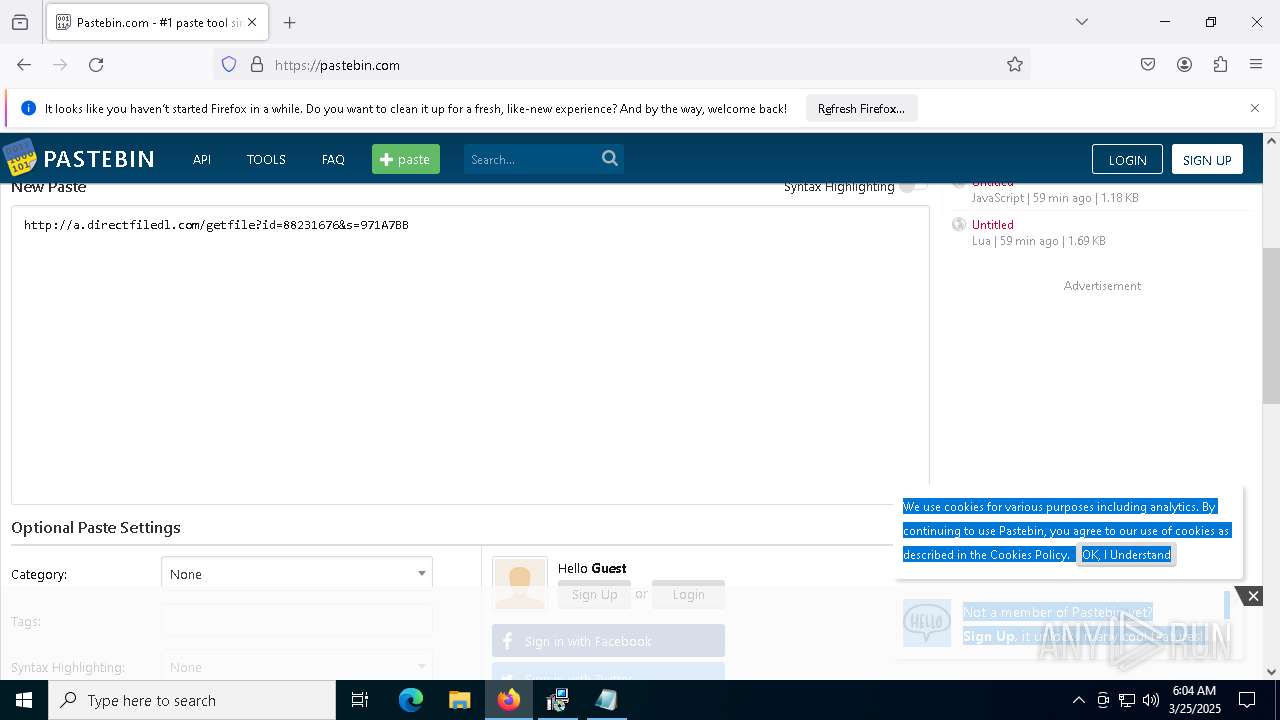
Requests information from PasteBin
- firefox.exe (PID: 2552)
INFO
Checks supported languages
- SubZero Download_88231676.exe (PID: 7148)
Reads the machine GUID from the registry
- SubZero Download_88231676.exe (PID: 7148)
Reads security settings of Internet Explorer
- notepad.exe (PID: 664)
- BackgroundTransferHost.exe (PID: 2148)
- BackgroundTransferHost.exe (PID: 4208)
- BackgroundTransferHost.exe (PID: 2984)
Creates files or folders in the user directory
- BackgroundTransferHost.exe (PID: 2984)
- SubZero Download_88231676.exe (PID: 7148)
Process checks computer location settings
- SubZero Download_88231676.exe (PID: 7148)
Checks proxy server information
- SubZero Download_88231676.exe (PID: 7148)
- BackgroundTransferHost.exe (PID: 2984)
Manual execution by a user
- firefox.exe (PID: 4336)
Application launched itself
- firefox.exe (PID: 2552)
- firefox.exe (PID: 4336)
Reads the software policy settings
- slui.exe (PID: 4040)
- BackgroundTransferHost.exe (PID: 2984)
- SubZero Download_88231676.exe (PID: 7148)
Reads the computer name
- SubZero Download_88231676.exe (PID: 7148)
The sample compiled with english language support
- SubZero Download_88231676.exe (PID: 7148)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (76.4) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (12.4) |
| .exe | | | Generic Win/DOS Executable (5.5) |
| .exe | | | DOS Executable Generic (5.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2024:10:18 17:00:18+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 14.22 |
| CodeSize: | 4353024 |
| InitializedDataSize: | 1675776 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x398c98 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Unknown (0) |
| ObjectFileType: | Unknown |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
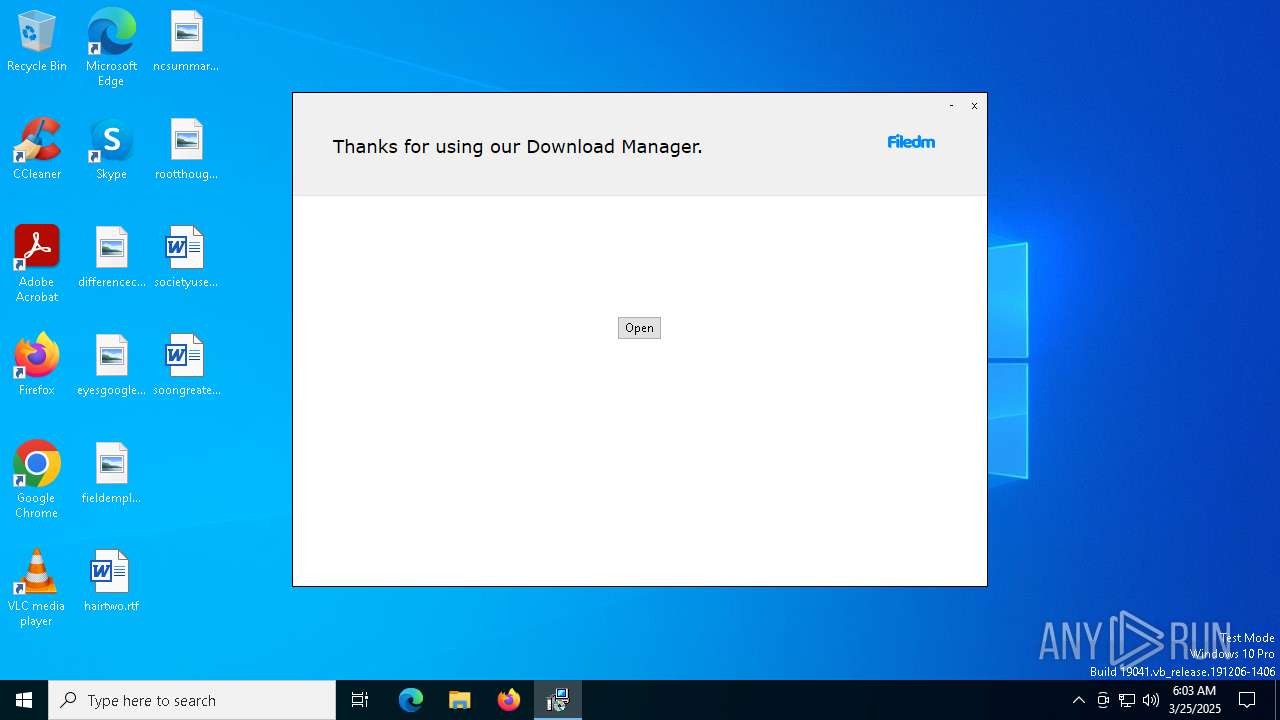
| FileDescription: | Download Manager |
| FileVersion: | 1 |
| InternalName: | Download Manager |
| LegalCopyright: | Download Manager |
| OriginalFileName: | Download Manager |
| ProductName: | Download Manager |
| ProductVersion: | 1 |
Total processes
168
Monitored processes
36
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 664 | "C:\WINDOWS\system32\NOTEPAD.EXE" C:\Users\admin\AppData\Local\link.txt | C:\Windows\SysWOW64\notepad.exe | — | SubZero Download_88231676.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Notepad Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 672 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=6616 -childID 14 -isForBrowser -prefsHandle 6304 -prefMapHandle 6392 -prefsLen 31556 -prefMapSize 244583 -jsInitHandle 1472 -jsInitLen 235124 -parentBuildID 20240213221259 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {5935d5df-ea6d-418b-bebb-218e6bc18062} 2552 "\\.\pipe\gecko-crash-server-pipe.2552" 222f63ddbd0 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 123.0 Modules
| |||||||||||||||
| 1280 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1628 | "C:\Users\admin\AppData\Local\Temp\SubZero Download_88231676.exe" | C:\Users\admin\AppData\Local\Temp\SubZero Download_88231676.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Download Manager Exit code: 3221226540 Version: 1 Modules
| |||||||||||||||
| 2148 | "BackgroundTransferHost.exe" -ServerName:BackgroundTransferHost.1 | C:\Windows\System32\BackgroundTransferHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Download/Upload Host Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2552 | "C:\Program Files\Mozilla Firefox\firefox.exe" | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Version: 123.0 Modules
| |||||||||||||||
| 2984 | "BackgroundTransferHost.exe" -ServerName:BackgroundTransferHost.1 | C:\Windows\System32\BackgroundTransferHost.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Download/Upload Host Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3156 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=6504 -childID 19 -isForBrowser -prefsHandle 4396 -prefMapHandle 6692 -prefsLen 31556 -prefMapSize 244583 -jsInitHandle 1472 -jsInitLen 235124 -parentBuildID 20240213221259 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {a3cf60d5-92d7-43fe-b1b7-c26b49ff80c5} 2552 "\\.\pipe\gecko-crash-server-pipe.2552" 222ff2474d0 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Version: 123.0 Modules
| |||||||||||||||
| 4040 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | SppExtComObj.Exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4208 | "BackgroundTransferHost.exe" -ServerName:BackgroundTransferHost.1 | C:\Windows\System32\BackgroundTransferHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Download/Upload Host Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
29 951
Read events
29 931
Write events
20
Delete events
0
Modification events
| (PID) Process: | (7148) SubZero Download_88231676.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (7148) SubZero Download_88231676.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (7148) SubZero Download_88231676.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (7148) SubZero Download_88231676.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.txt\OpenWithProgids |
| Operation: | write | Name: | txtfile |
Value: | |||
| (PID) Process: | (4208) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (4208) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (4208) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2984) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2984) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2984) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
Executable files
0
Suspicious files
201
Text files
25
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7148 | SubZero Download_88231676.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\24BD96D5497F70B3F510A6B53CD43F3E_3A89246FB90C5EE6620004F1AE0EB0EA | binary | |
MD5:16FB34FDFF735D7FCE2B5AE972DB97BB | SHA256:7D8E95B8F16A97299DB6DD2E351254B169A86B6EFD2258D229608C4EA36FECEC | |||
| 7148 | SubZero Download_88231676.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\24BD96D5497F70B3F510A6B53CD43F3E_3A89246FB90C5EE6620004F1AE0EB0EA | binary | |
MD5:361DB7F3479AAED1AF6C74DD31773650 | SHA256:D402D6D735F6D085EF5B9928E6B6738077C96180C924AB6813DEF7616B06BD32 | |||
| 7148 | SubZero Download_88231676.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\05DDC6AA91765AACACDB0A5F96DF8199 | binary | |
MD5:D9620575248E67711D998E13F920DBEE | SHA256:1C150AC2518BB85ACBA28437927E5FA4516BAAA7B364AA42F4E7774853F19285 | |||
| 7148 | SubZero Download_88231676.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\05DDC6AA91765AACACDB0A5F96DF8199 | binary | |
MD5:E935BC5762068CAF3E24A2683B1B8A88 | SHA256:A8ACCFCFEB51BD73DF23B91F4D89FF1A9EB7438EF5B12E8AFDA1A6FF1769E89D | |||
| 2984 | BackgroundTransferHost.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.ContentDeliveryManager_cw5n1h2txyewy\AC\BackgroundTransferApi\08289391-3d51-431b-ad36-bce82115de47.down_data | — | |
MD5:— | SHA256:— | |||
| 7148 | SubZero Download_88231676.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\B77FAD61EB4A40E3443FA60D1451BEB4_5F55BE09F9262B37AA5427711092D3D4 | binary | |
MD5:F34426B175BDCC1FDA9DC9E030E13AB0 | SHA256:7A7E8C562AC5827ED8533EBC6324862970F85BB8445CD565456C964A55691DCE | |||
| 7148 | SubZero Download_88231676.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\IE\KCV3KQBA\service[1].htm | text | |
MD5:CDCBF1585C8FC4E753212FA7E0CB8701 | SHA256:38D99781A809D7C2A7EB478898E2094DA5D216C351A832DD4D298B7587C8C4E8 | |||
| 7148 | SubZero Download_88231676.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\B77FAD61EB4A40E3443FA60D1451BEB4_5F55BE09F9262B37AA5427711092D3D4 | binary | |
MD5:3A8412E47170F359CFC24E9C6E109148 | SHA256:50F9407C3A11A1CCBDF6717DC5F56EF32891F9A1E590D1BB5CECF9F28F7931EF | |||
| 7148 | SubZero Download_88231676.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\IE\RR3E01RZ\geo[1].htm | text | |
MD5:482846ADD93E7C3A7CE4C6D51F028BE9 | SHA256:72CE783E1317588760616D60675AA32557B96382EF995D589C44B5817EA6EE3B | |||
| 7148 | SubZero Download_88231676.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\83D863F495E7D991917B3ABB3E1EB382_4D9C2C5E642FAF6FA3B8098AB3241EF2 | binary | |
MD5:0C653FE4C712FEFC11090C82B4B0D685 | SHA256:33B7C4073173D33E3CE9D4733E58994AA208405933EA1B0229DCB9F41DBC71EF | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
63
TCP/UDP connections
242
DNS requests
262
Threats
9
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.53.40.178:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
7148 | SubZero Download_88231676.exe | GET | 200 | 142.250.186.35:80 | http://ocsp.pki.goog/gsr1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCEHe9DWzbNvka6iEPxPBY0w0%3D | unknown | — | — | whitelisted |
7148 | SubZero Download_88231676.exe | GET | 200 | 142.250.186.35:80 | http://o.pki.goog/s/wr3/mV0/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBQSq0i5t2Pafi2Gw9uzwnc7KTctWgQUx4H1%2FY6I2QA8TWOiUDEkoM4j%2FiMCEQCZXRxDEgK4oBBPRElcaU8c | unknown | — | — | whitelisted |
7148 | SubZero Download_88231676.exe | GET | 200 | 142.250.186.35:80 | http://c.pki.goog/r/r1.crl | unknown | — | — | whitelisted |
7148 | SubZero Download_88231676.exe | GET | 200 | 142.250.186.35:80 | http://c.pki.goog/r/gsr1.crl | unknown | — | — | whitelisted |
7148 | SubZero Download_88231676.exe | GET | 200 | 142.250.186.35:80 | http://c.pki.goog/r/r4.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
7148 | SubZero Download_88231676.exe | GET | 200 | 142.250.186.35:80 | http://o.pki.goog/s/wr3/Vdw/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQSq0i5t2Pafi2Gw9uzwnc7KTctWgQUx4H1%2FY6I2QA8TWOiUDEkoM4j%2FiMCEFXcf42tINpLCbnQS8S2feE%3D | unknown | — | — | whitelisted |
7084 | backgroundTaskHost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
2984 | BackgroundTransferHost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 23.53.40.178:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
7148 | SubZero Download_88231676.exe | 35.190.60.70:443 | www.dlsft.com | GOOGLE | US | whitelisted |
7148 | SubZero Download_88231676.exe | 142.250.186.35:80 | ocsp.pki.goog | GOOGLE | US | whitelisted |
3216 | svchost.exe | 40.113.103.199:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6544 | svchost.exe | 20.190.159.129:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
7148 | SubZero Download_88231676.exe | 104.21.16.1:443 | filedm.com | CLOUDFLARENET | — | malicious |
6544 | svchost.exe | 184.30.131.245:80 | ocsp.digicert.com | AKAMAI-AS | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.dlsft.com |
| unknown |
ocsp.pki.goog |
| whitelisted |
c.pki.goog |
| whitelisted |
o.pki.goog |
| whitelisted |
client.wns.windows.com |
| whitelisted |
dlsft.com |
| unknown |
login.live.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2196 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
2196 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Online Pastebin Text Storage |
2196 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
2196 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Online Pastebin Text Storage |
2196 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Online Pastebin Text Storage |
2196 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
2196 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |
2196 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare turnstile CAPTCHA challenge |
2196 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |