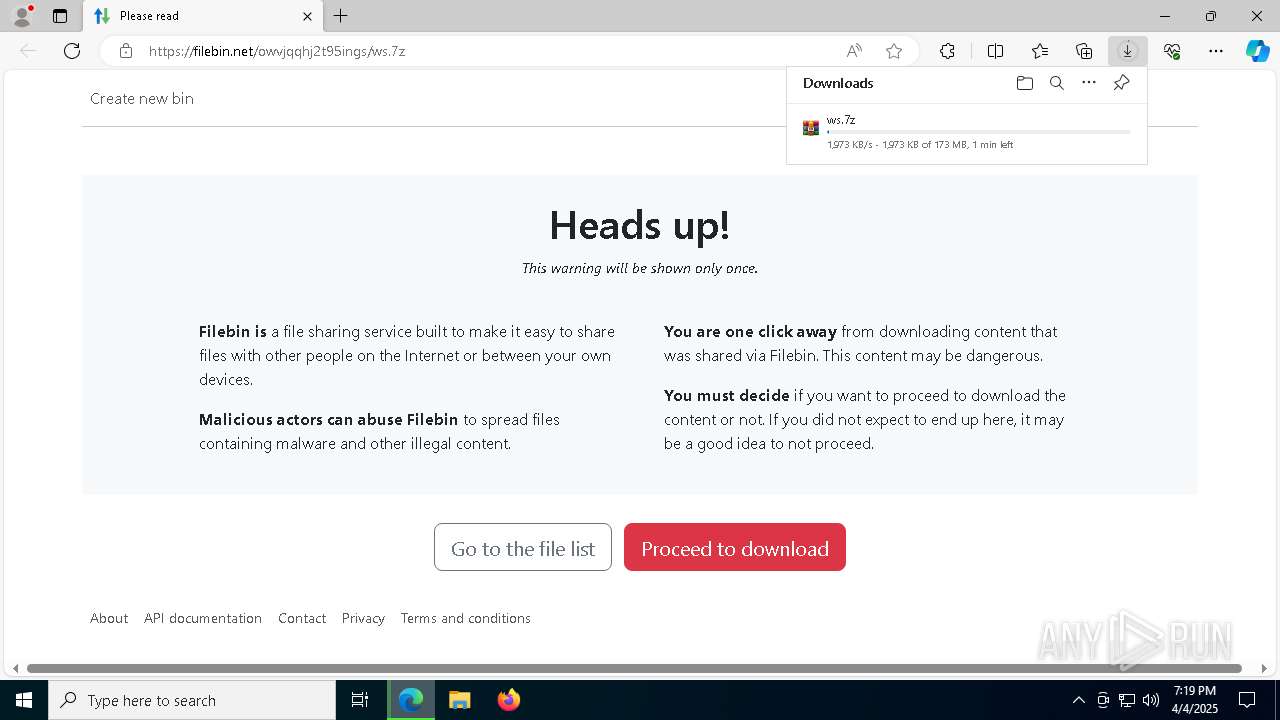
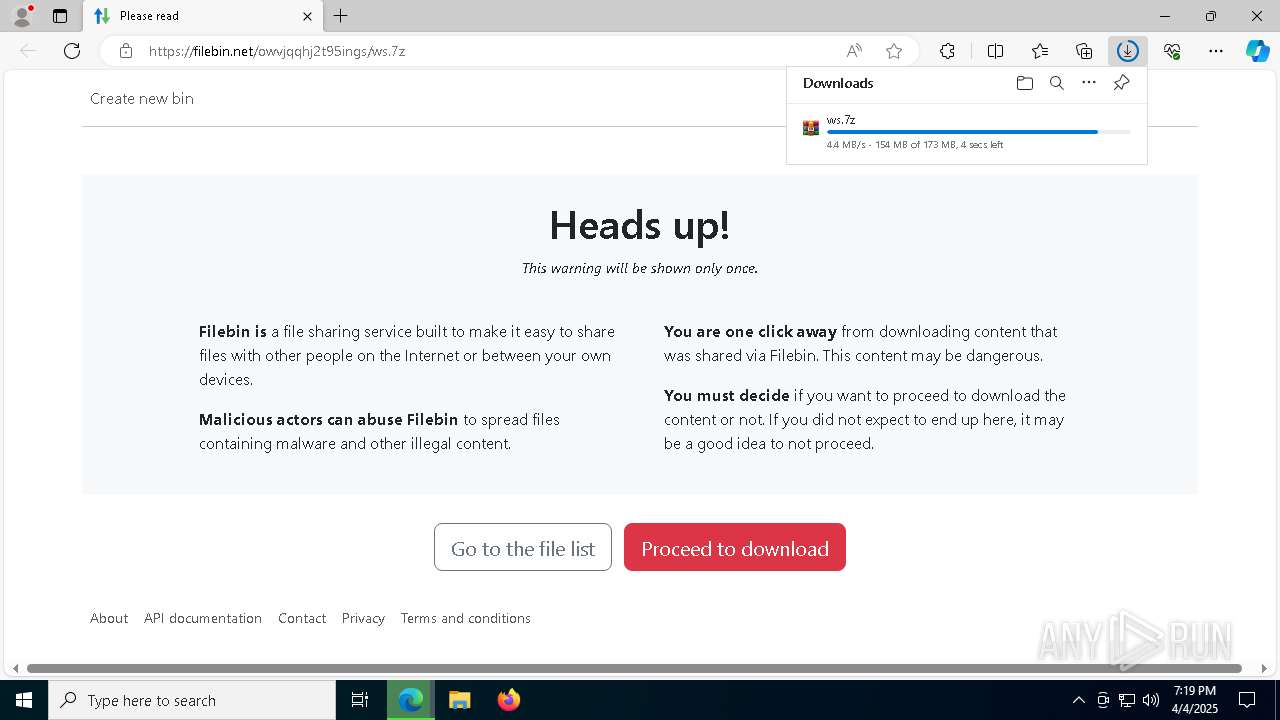
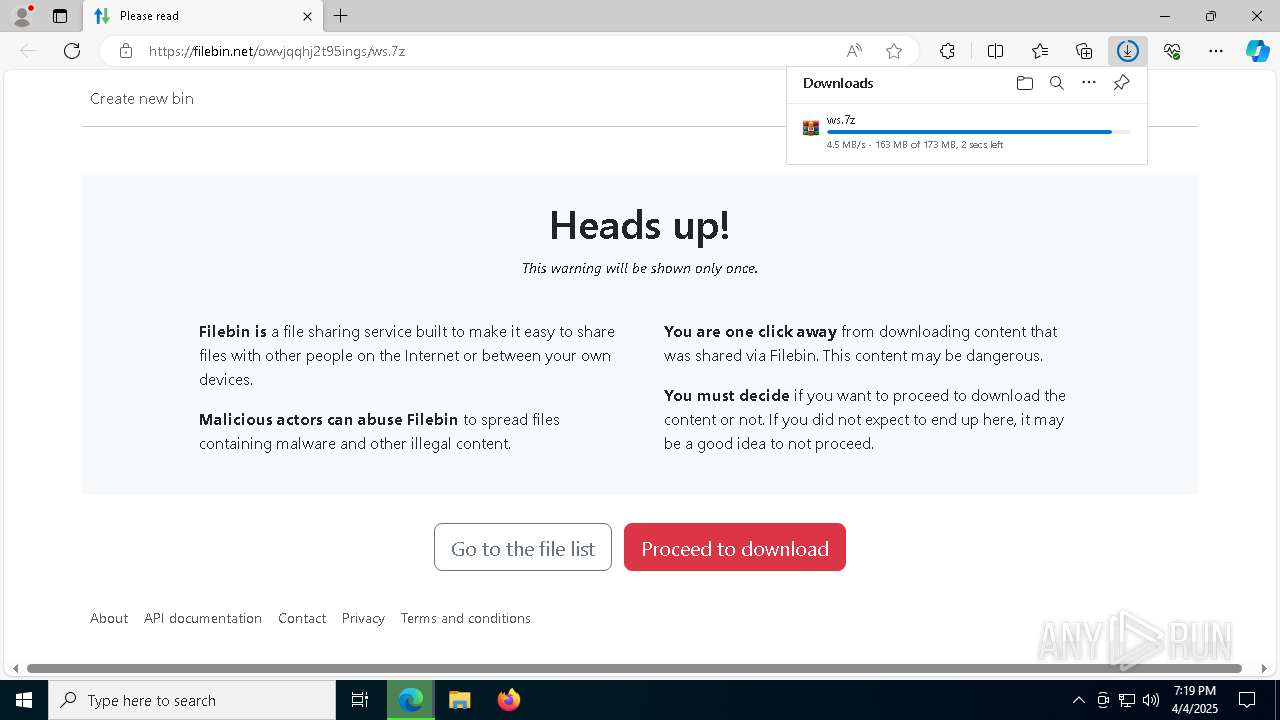
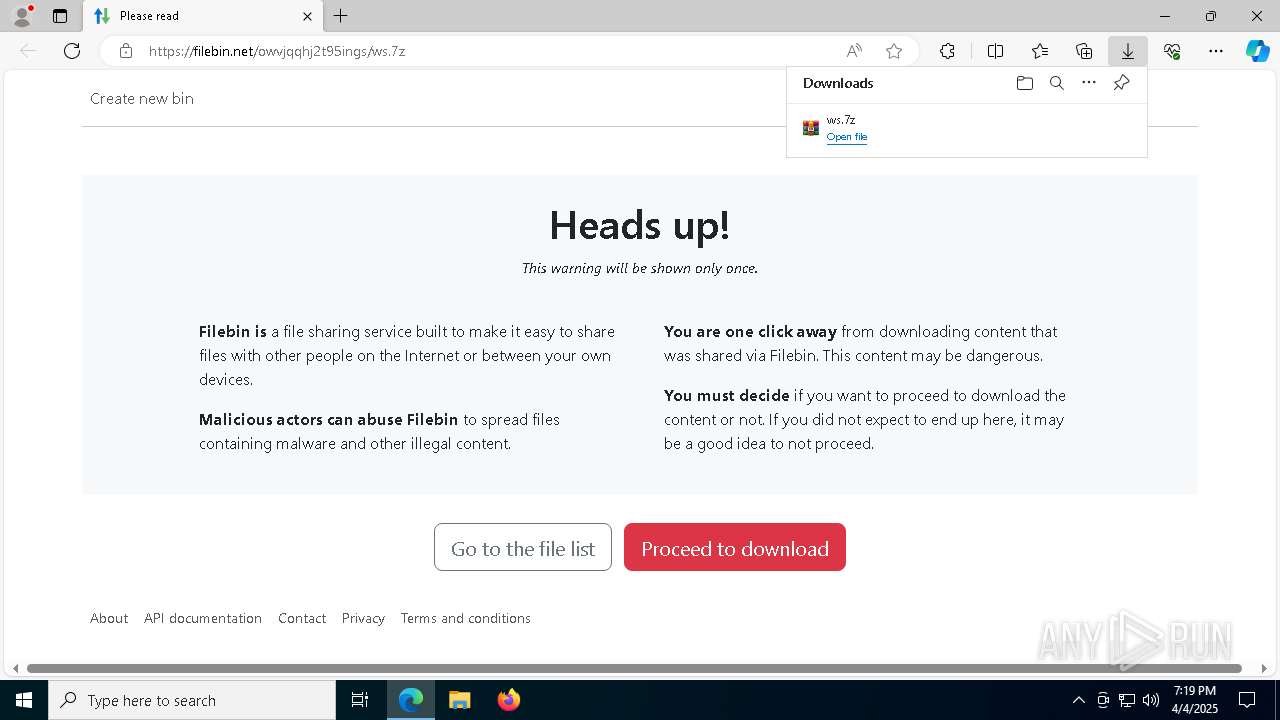
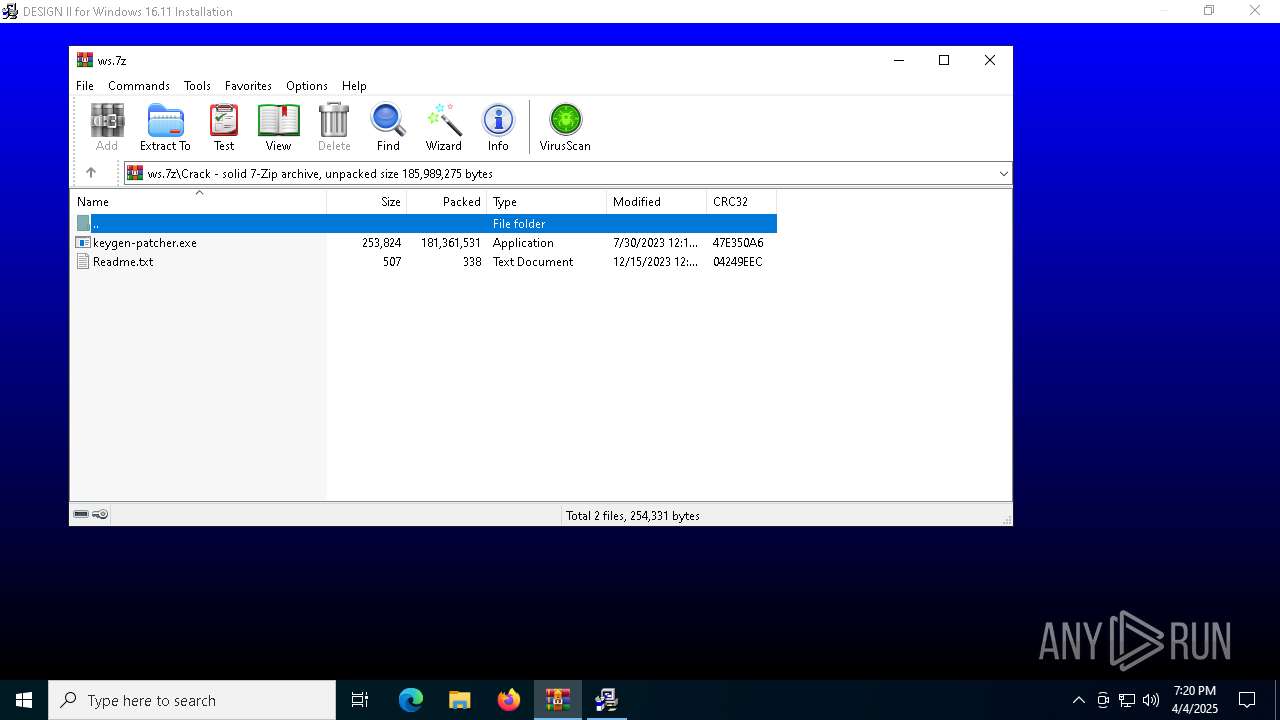
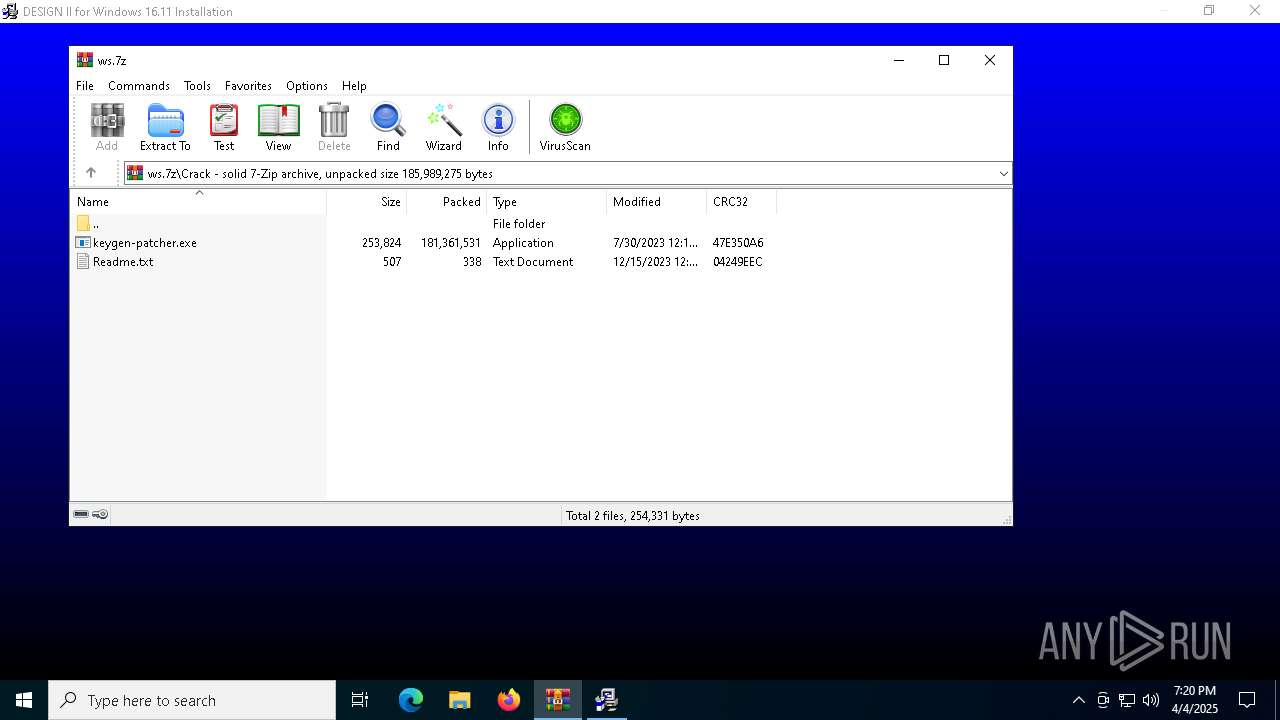
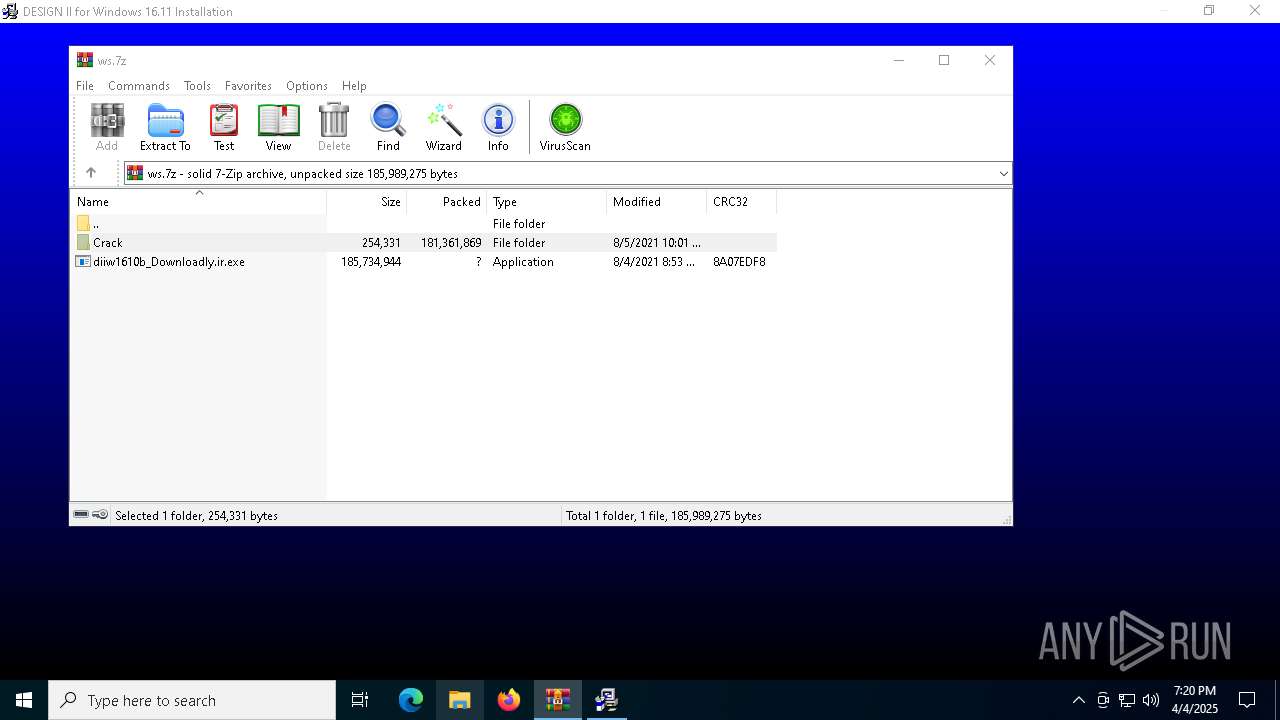
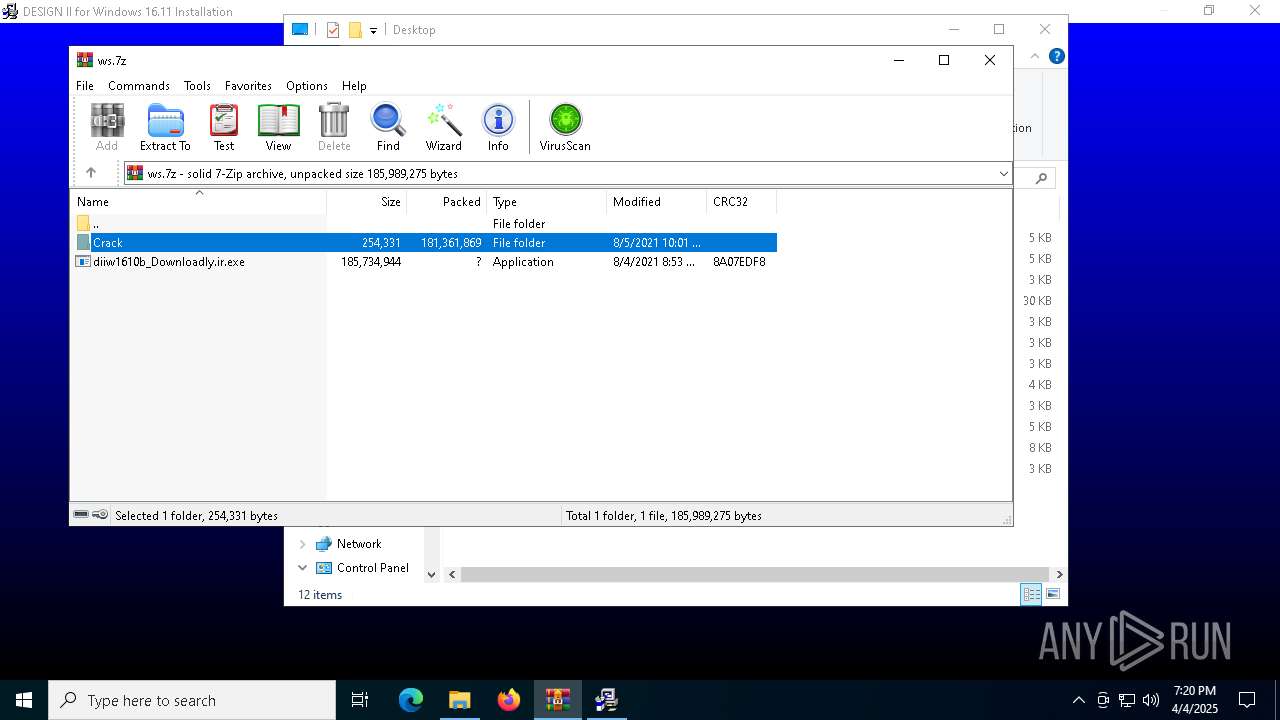
| URL: | https://filebin.net/owvjqqhj2t95ings/ws.7z |
| Full analysis: | https://app.any.run/tasks/d915a9d6-34f6-4d0b-abe5-8252f29de17d |
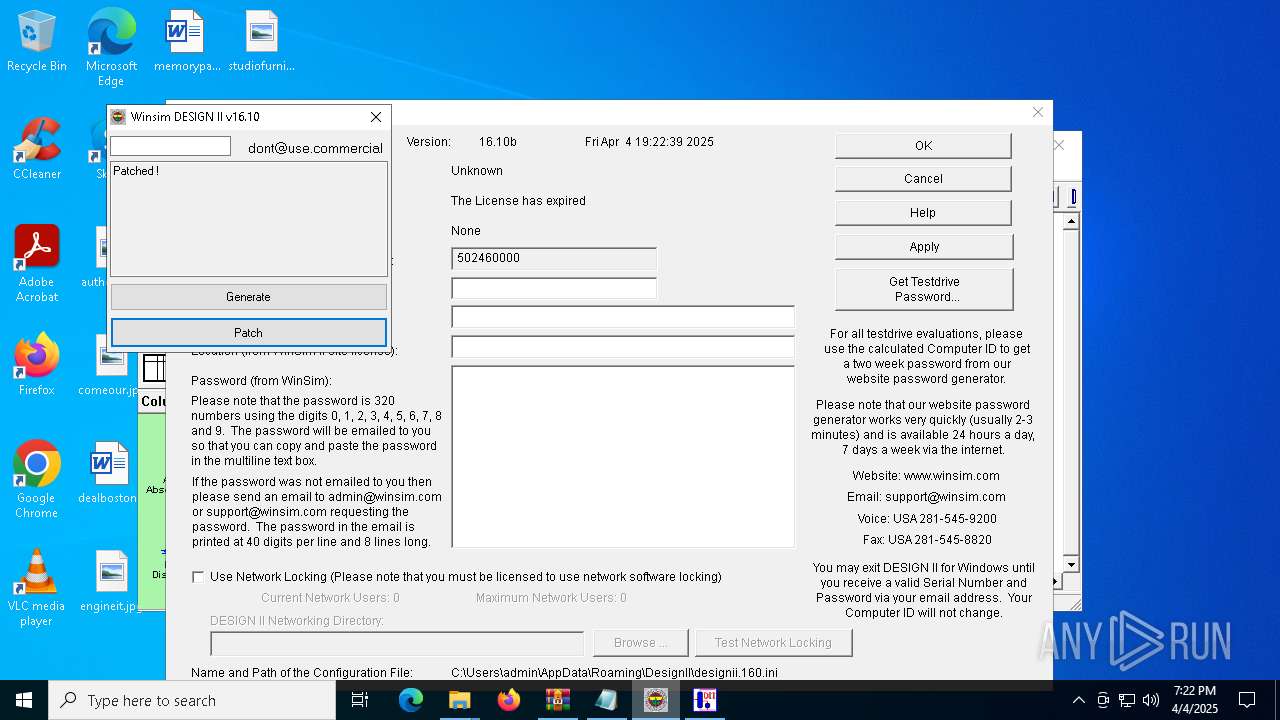
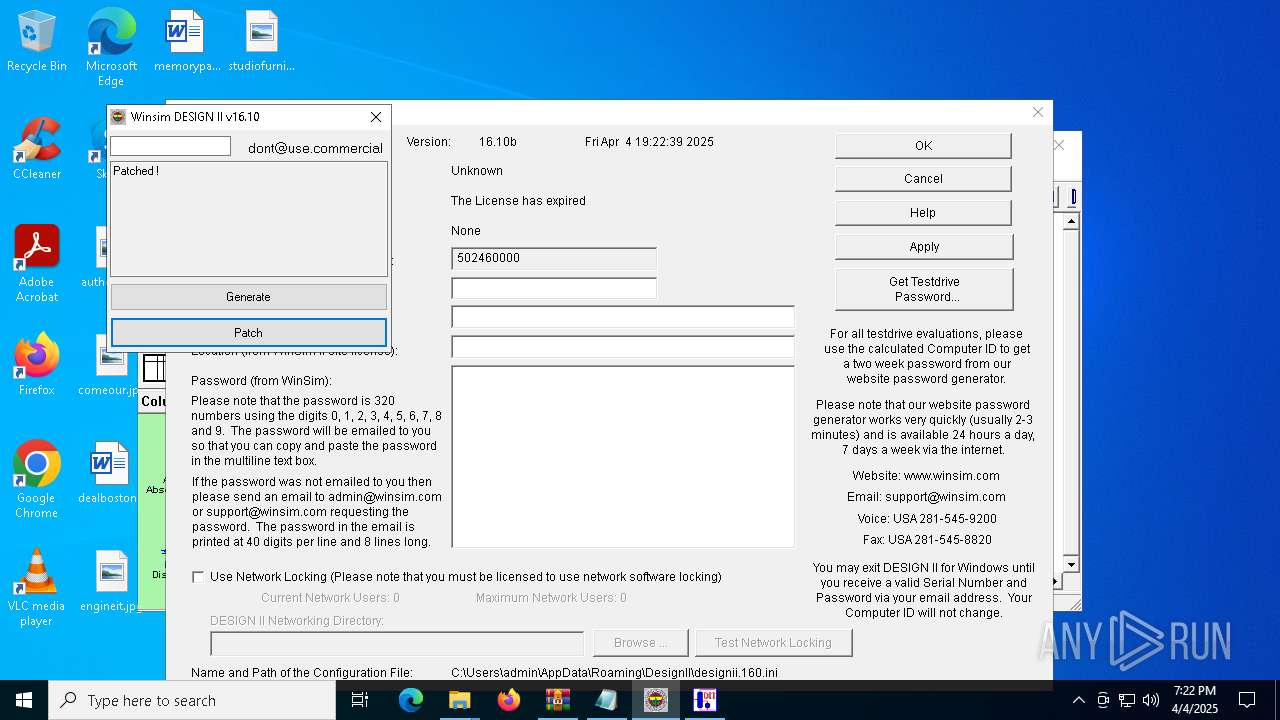
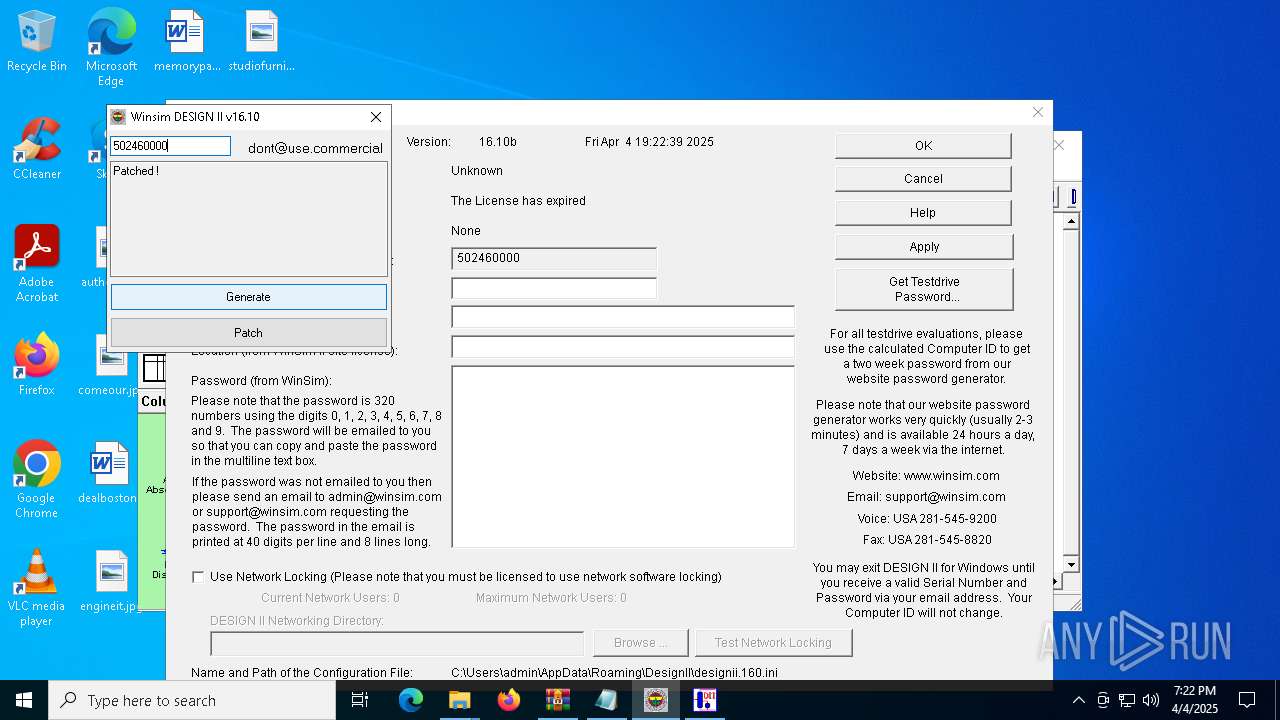
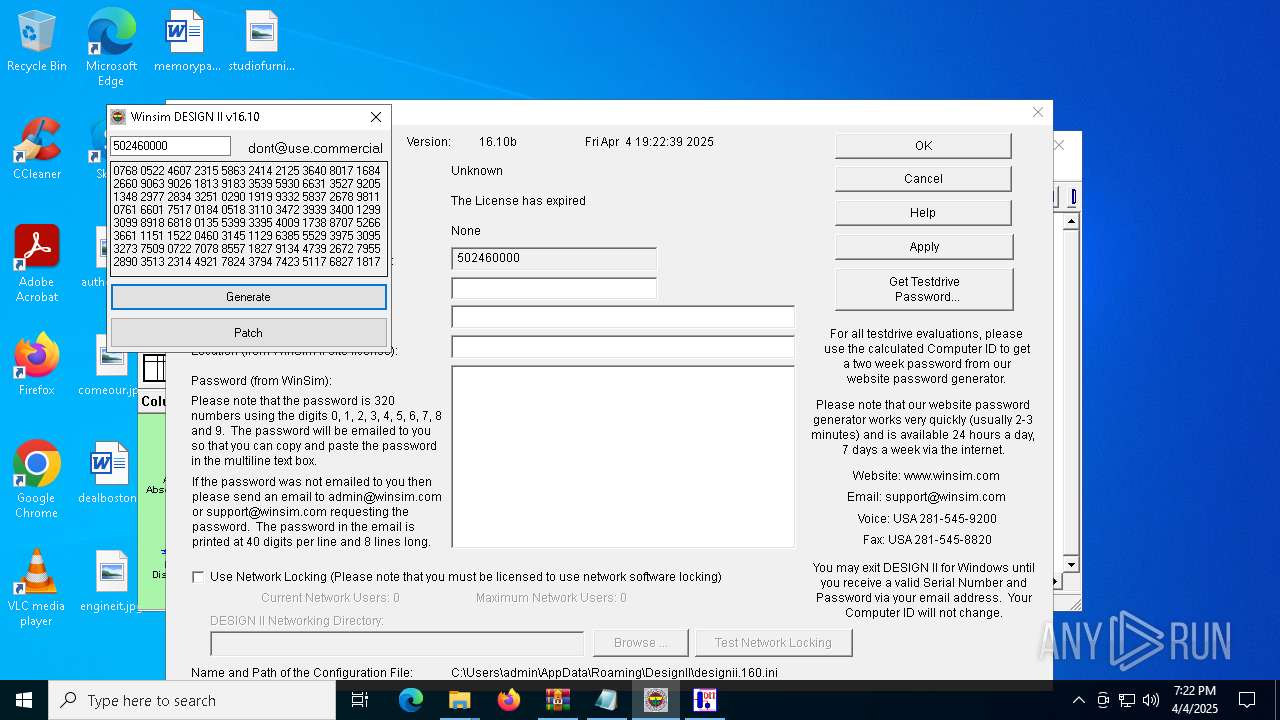
| Verdict: | Malicious activity |
| Analysis date: | April 04, 2025, 19:19:04 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MD5: | D9AAF3A65E6F18800510F582D7AFA4B2 |
| SHA1: | A7C26EE308AD33F69A00512DA4A26698C53BC669 |
| SHA256: | 61B6C73E3ADD88783CAD8E933D1981F0A2F0FFCBC1429773FEEC062A94F13A67 |
| SSDEEP: | 3:N8wLlTPUQILVJWmf:2sPUQhmf |
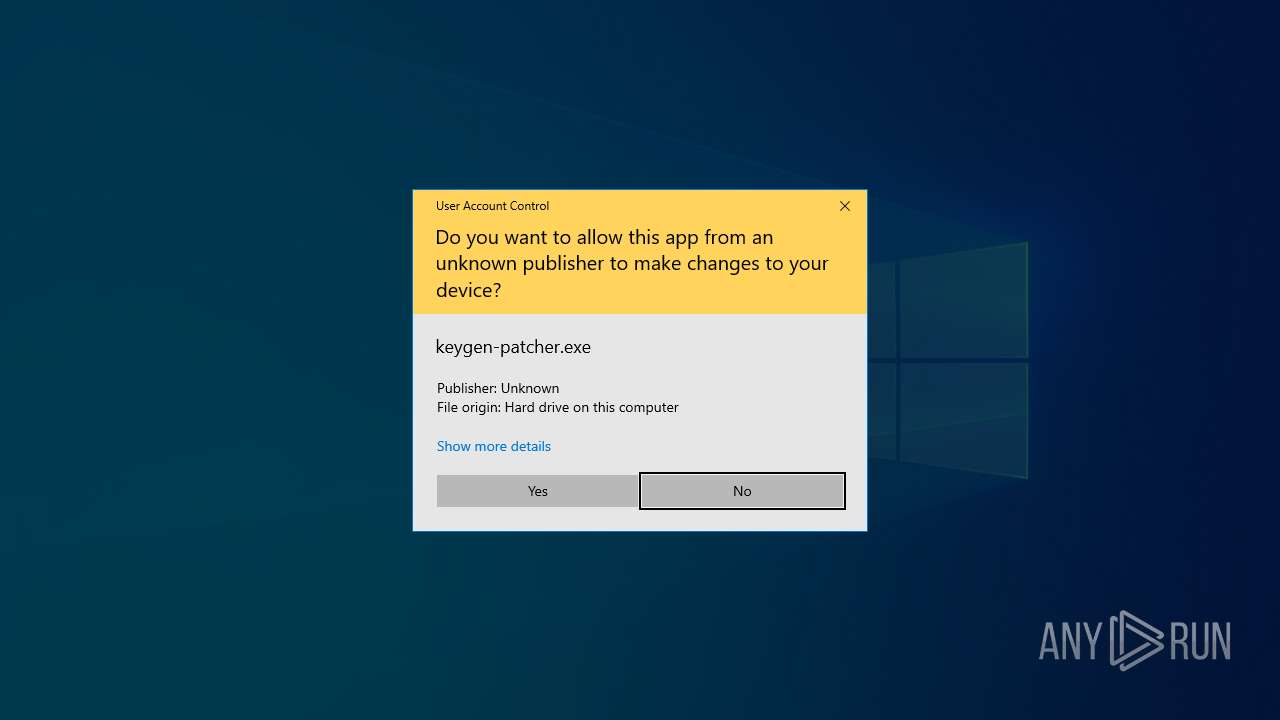
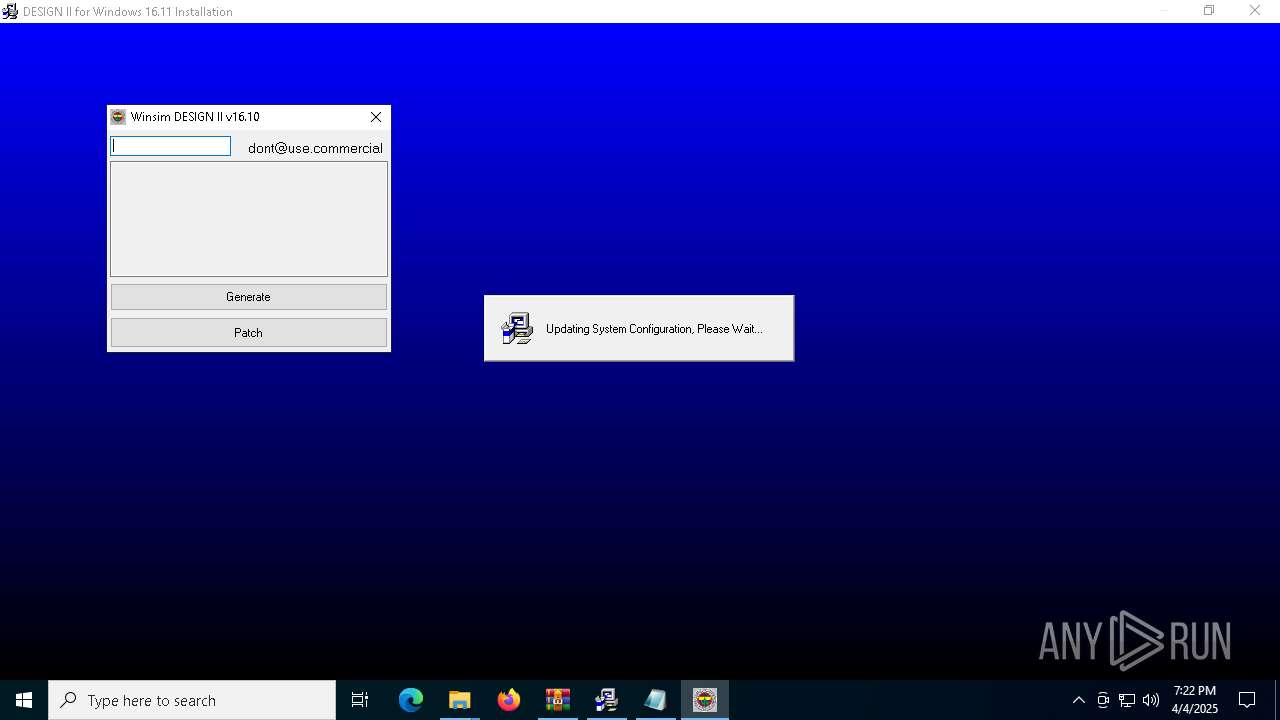
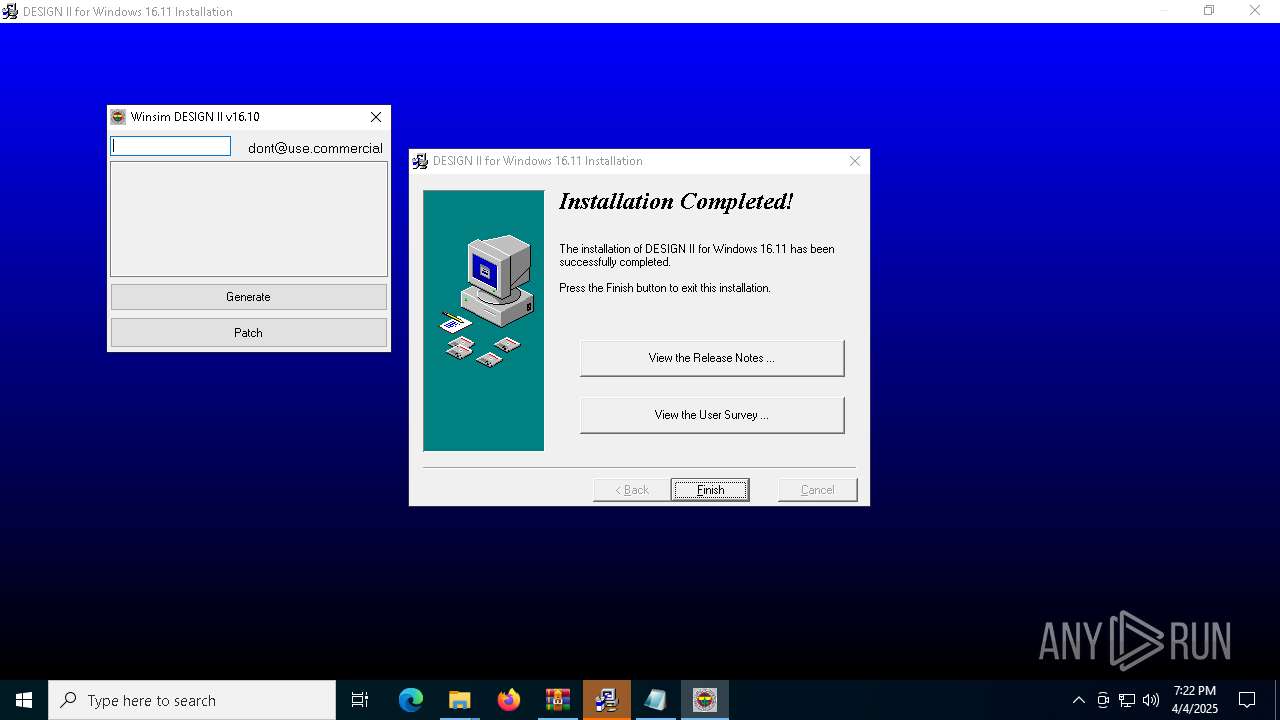
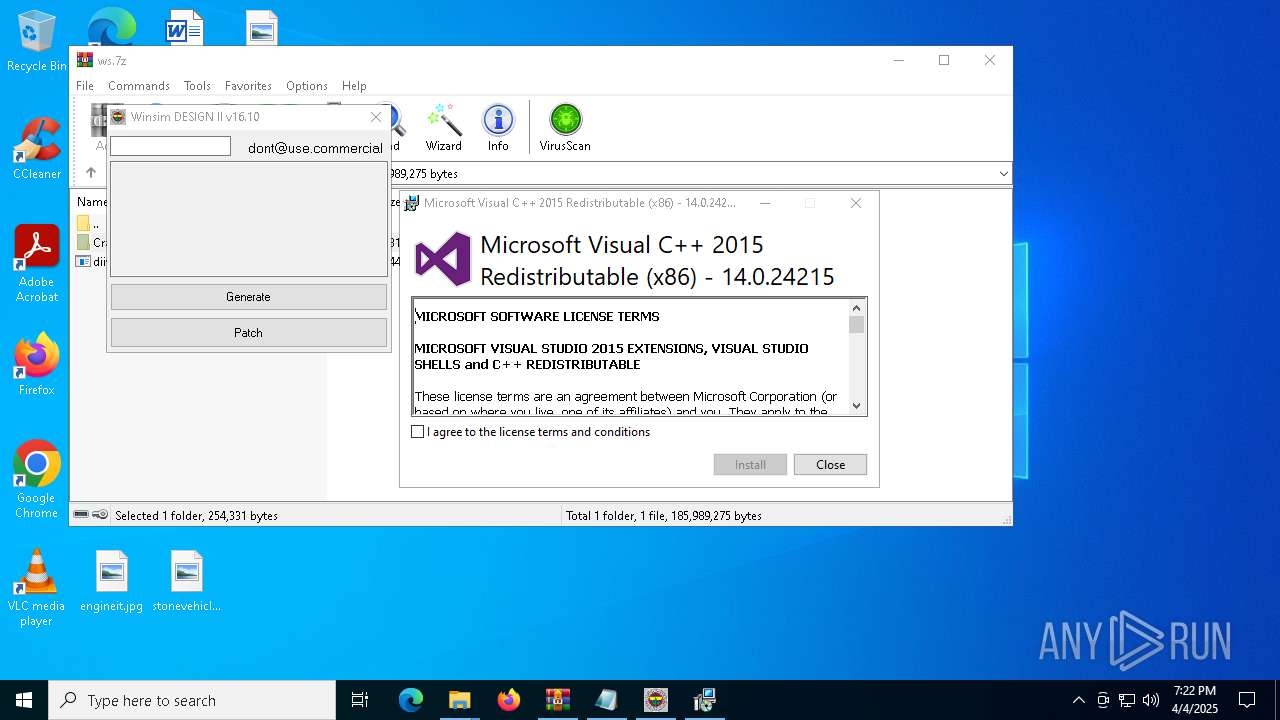
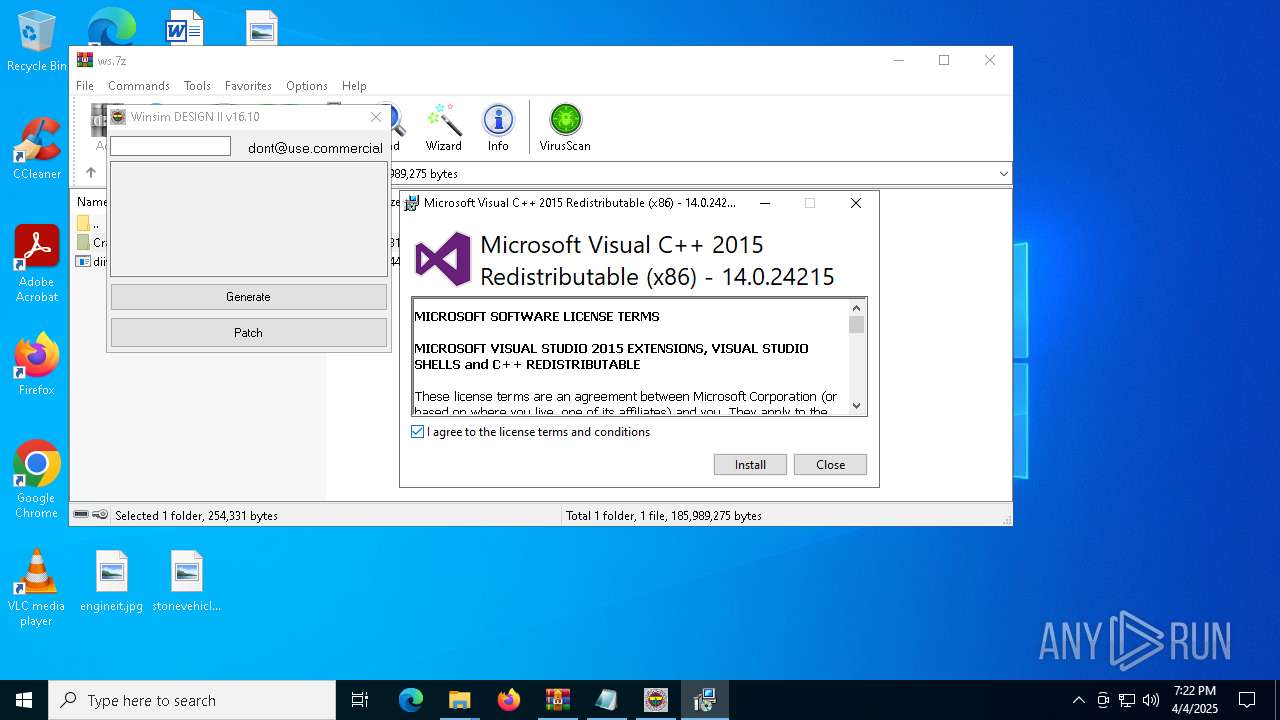
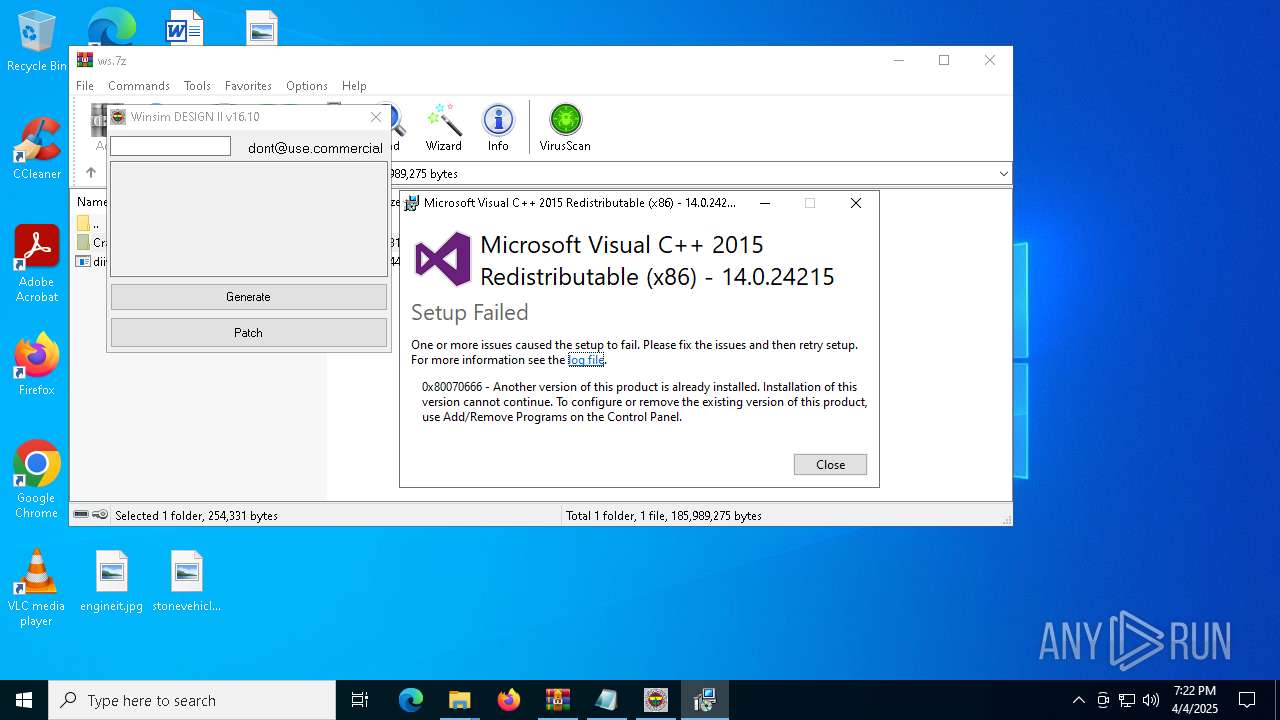
MALICIOUS
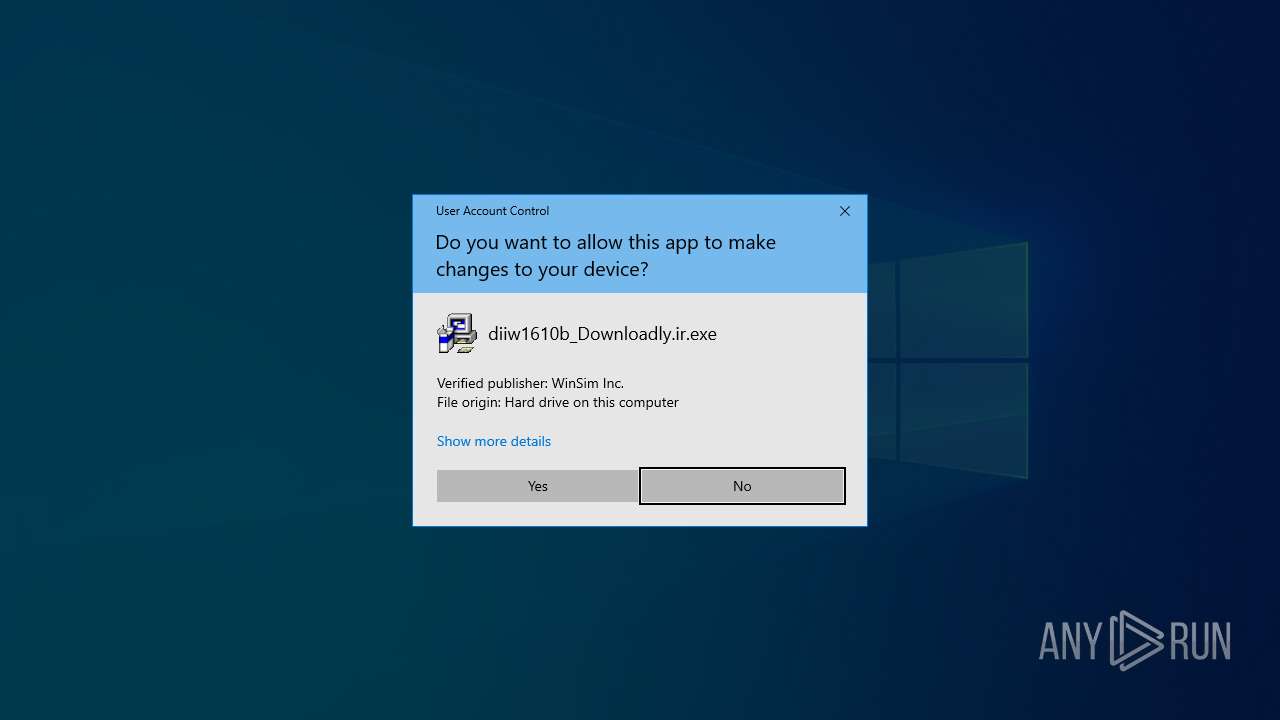
Executing a file with an untrusted certificate
- vcredist_x86.exe (PID: 7368)
- vcredist_x86.exe (PID: 4692)
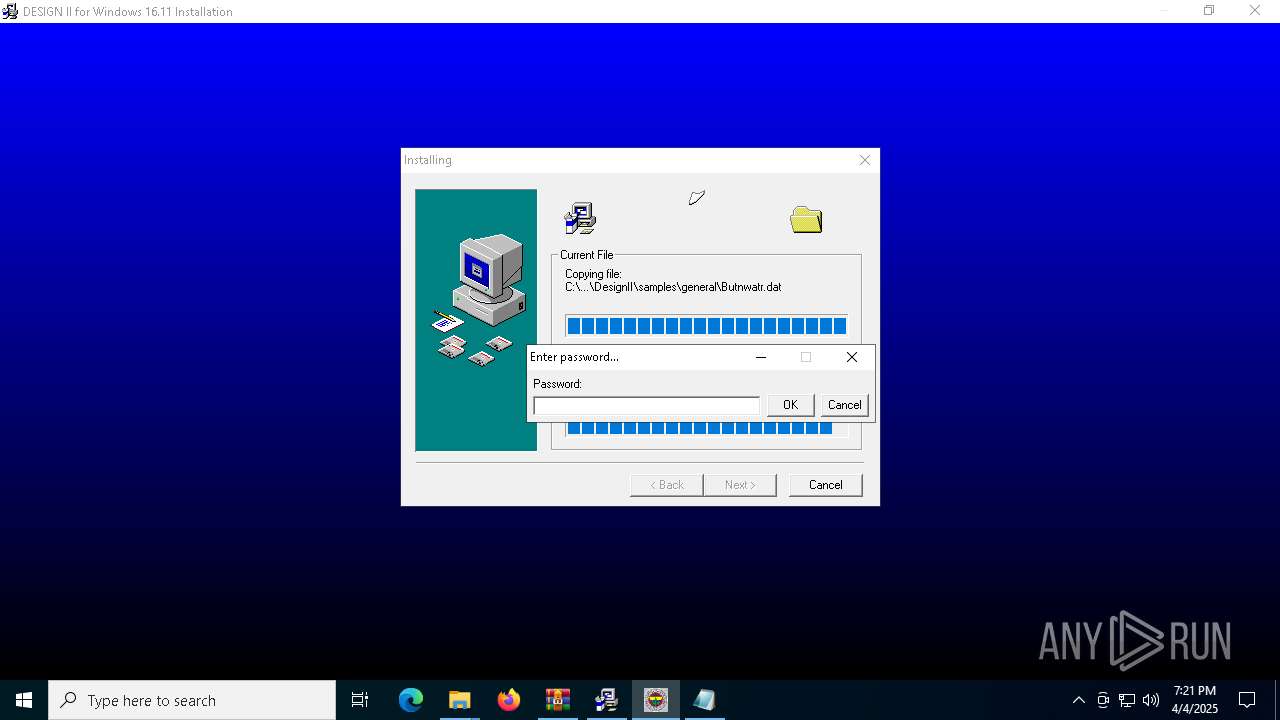
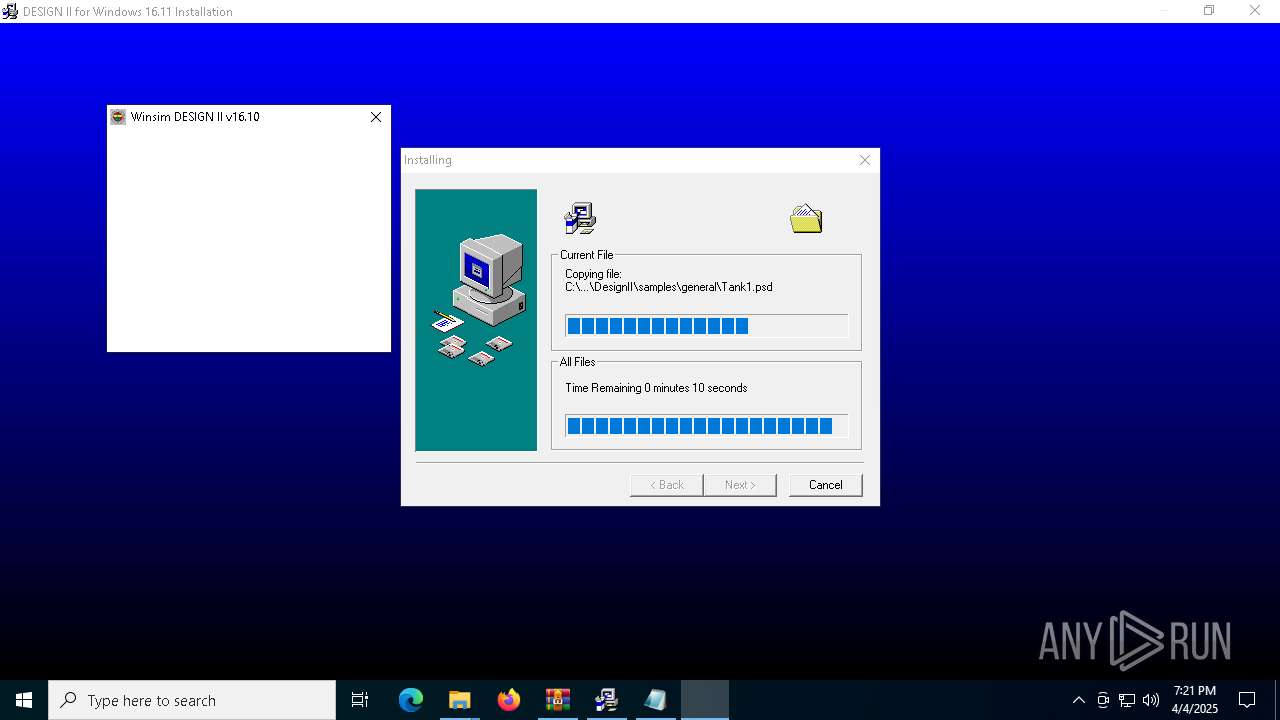
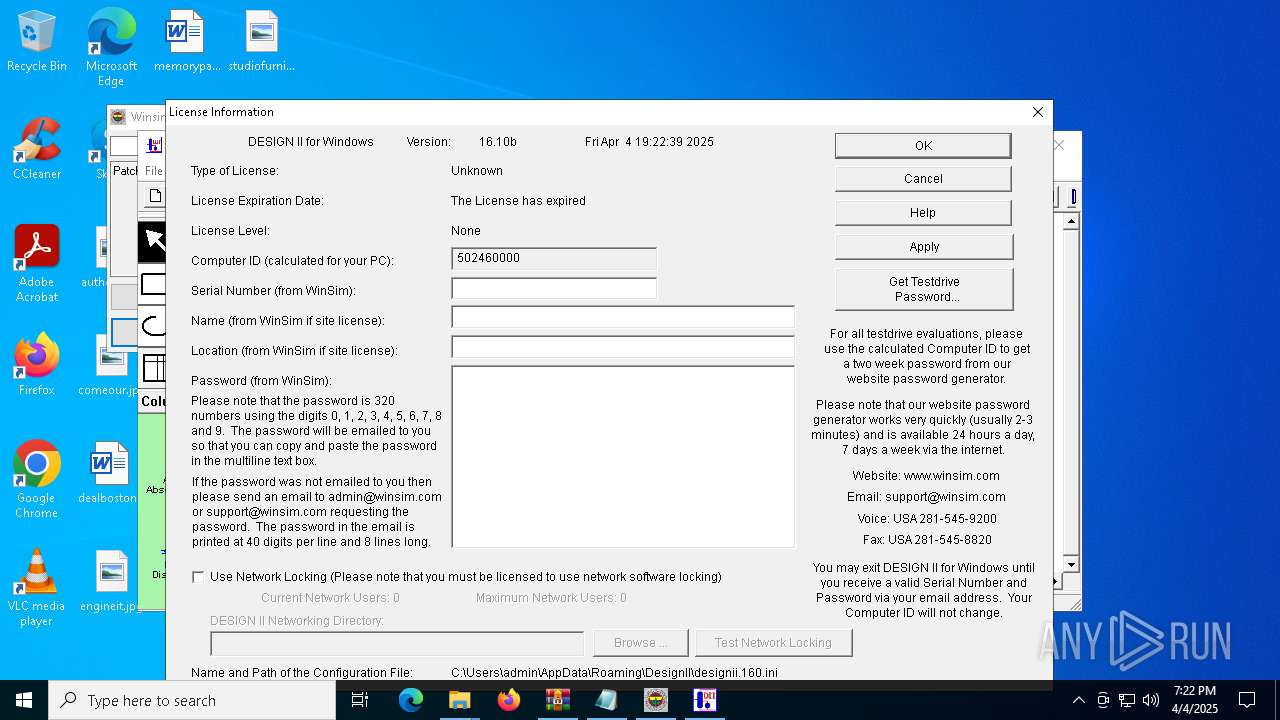
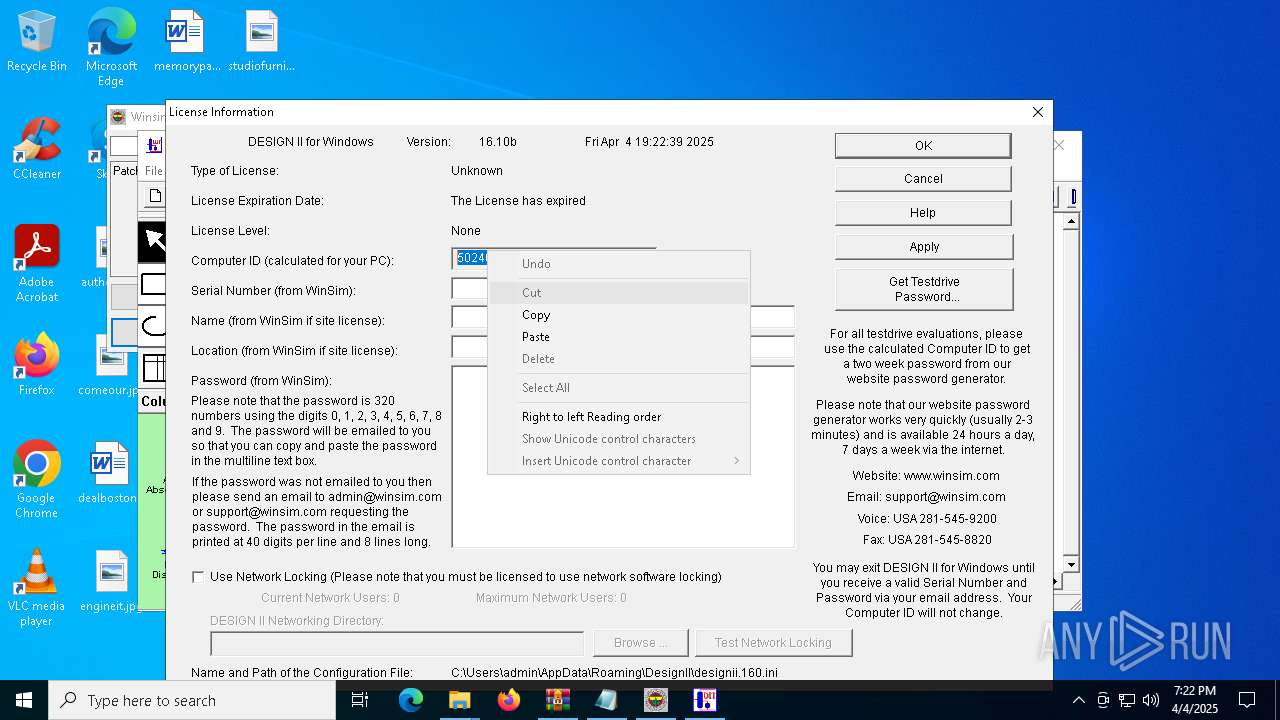
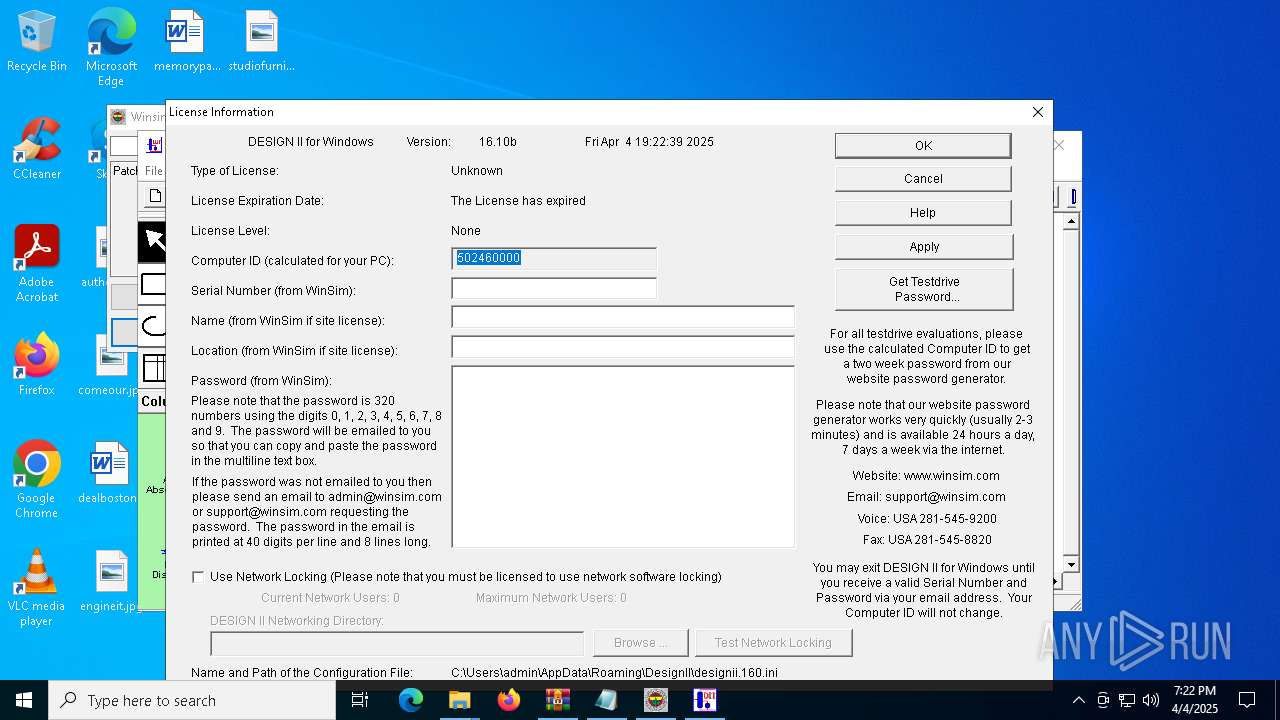
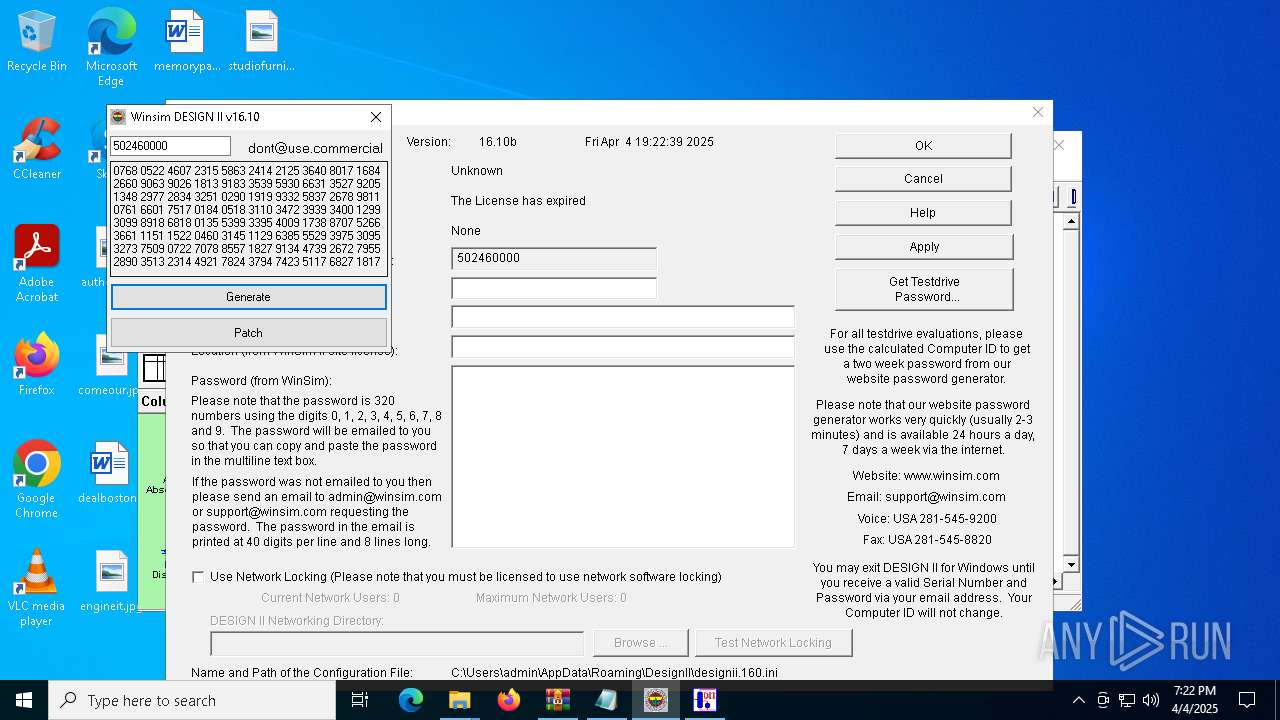
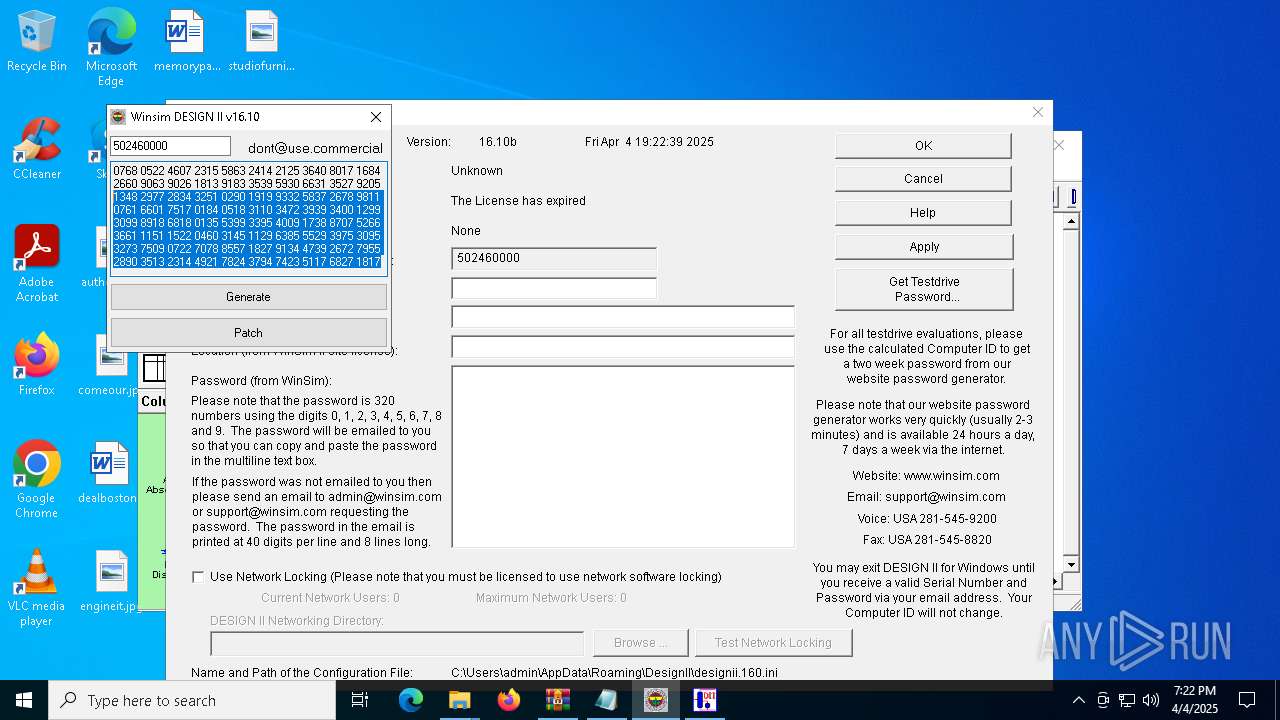
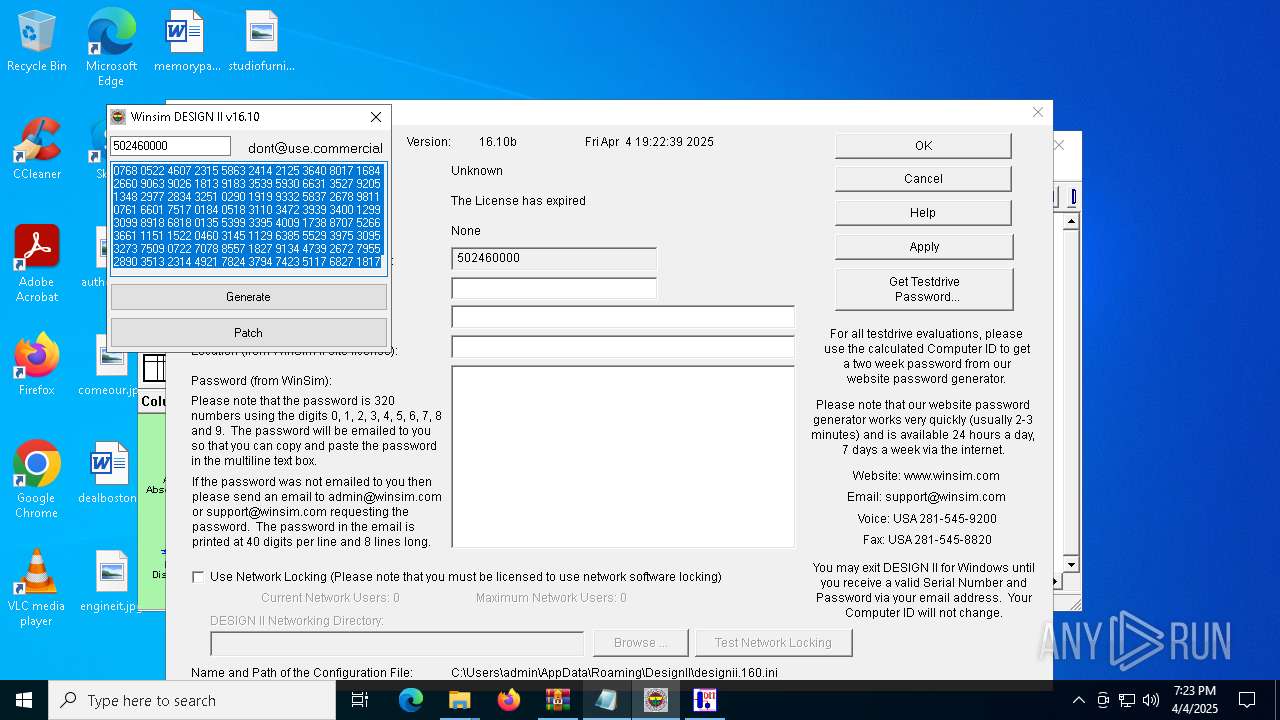
- DESWIN.exe (PID: 7684)
SUSPICIOUS
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 4180)
- ShellExperienceHost.exe (PID: 7100)
- GLBBAA2.tmp (PID: 7616)
- DESWIN.exe (PID: 7684)
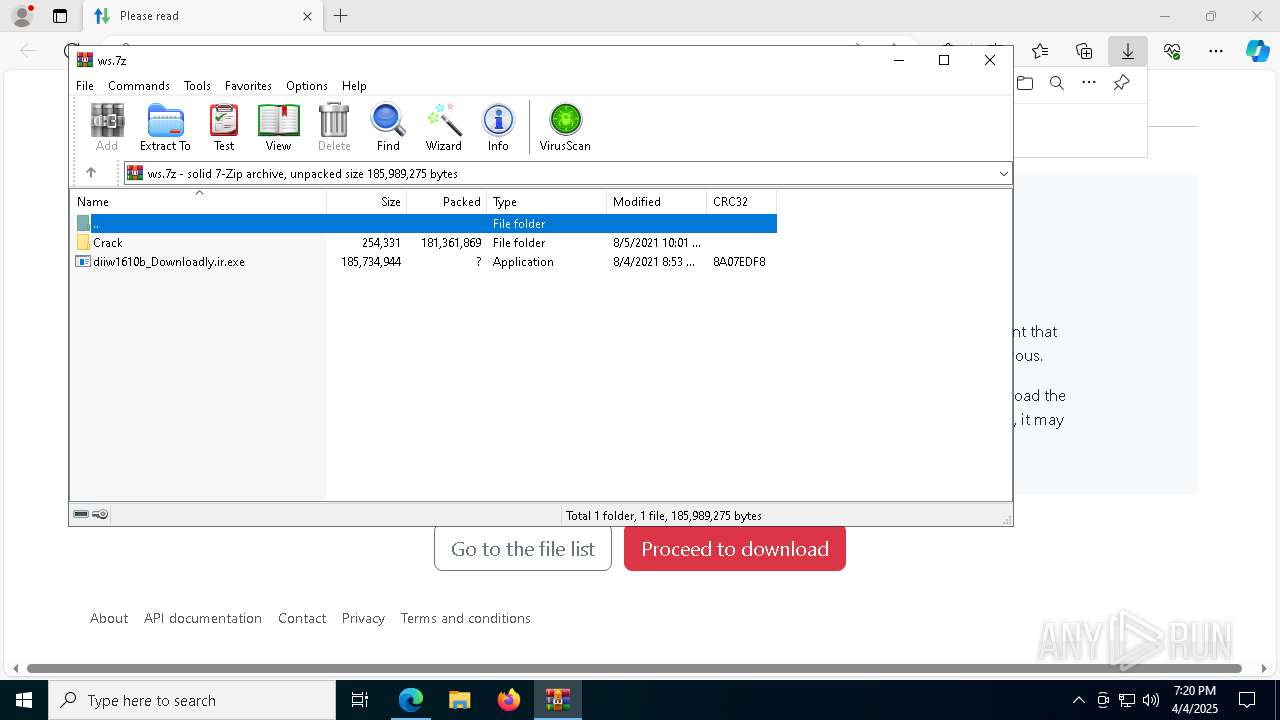
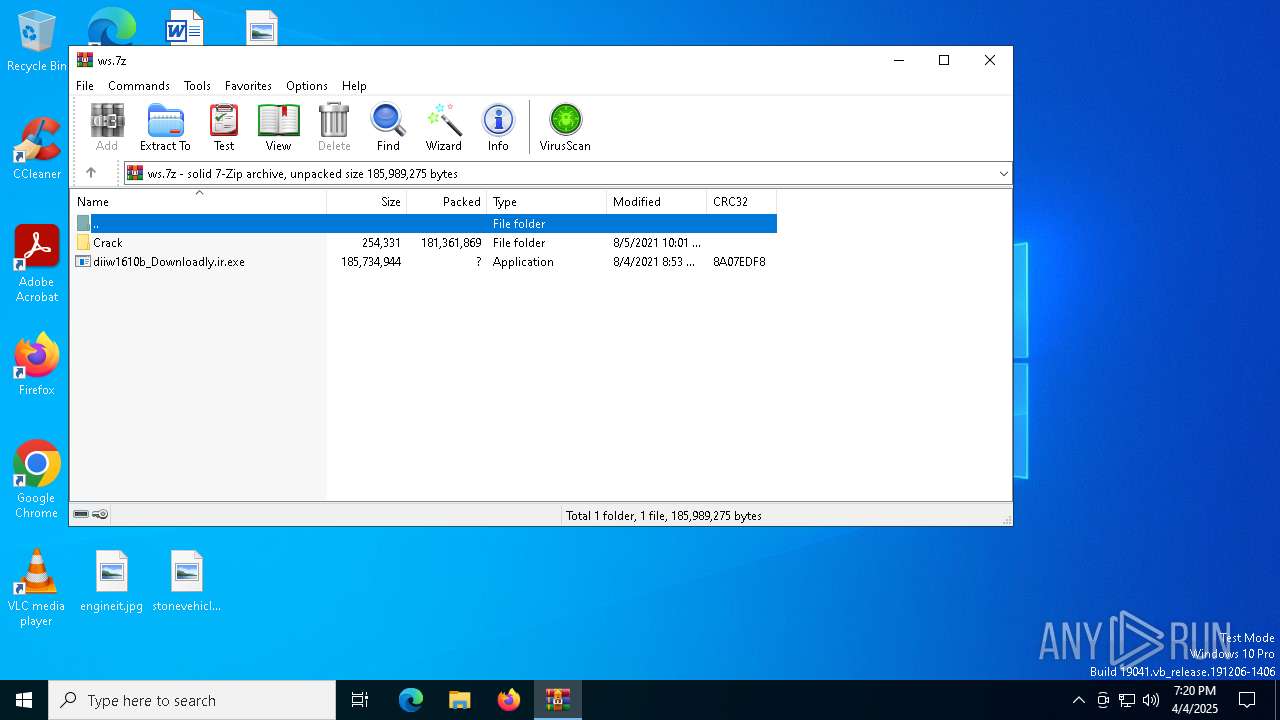
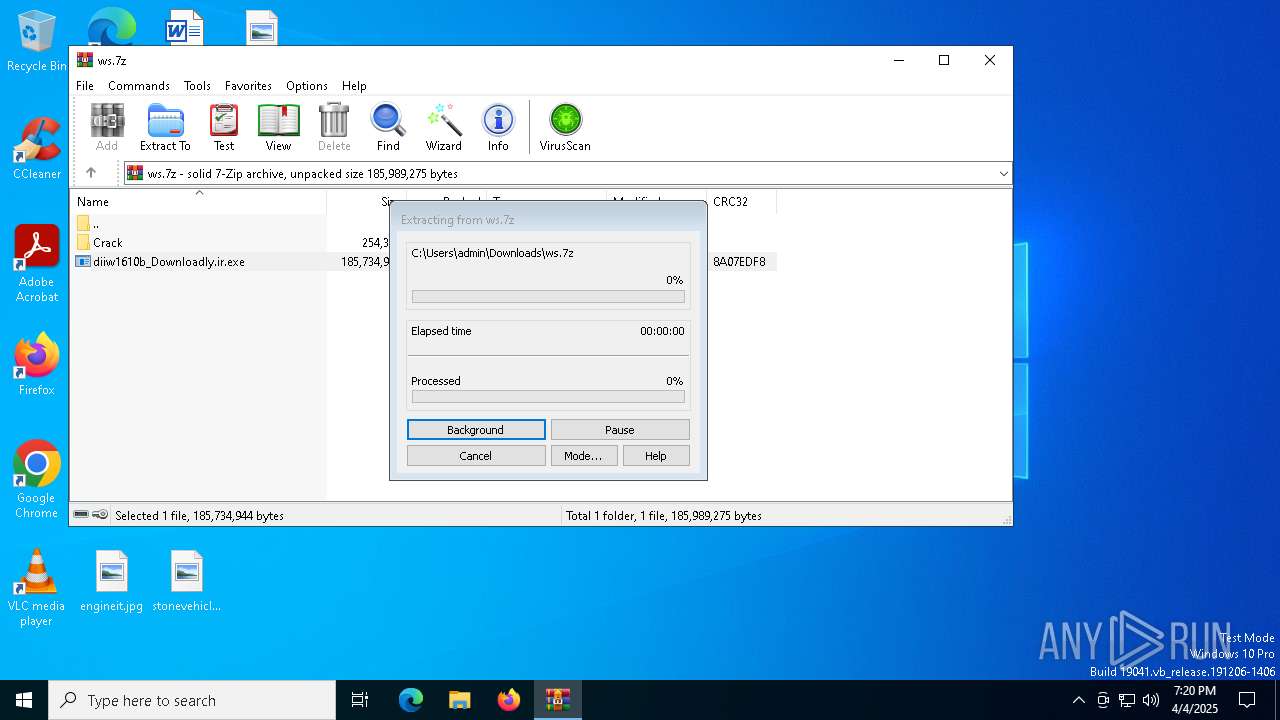
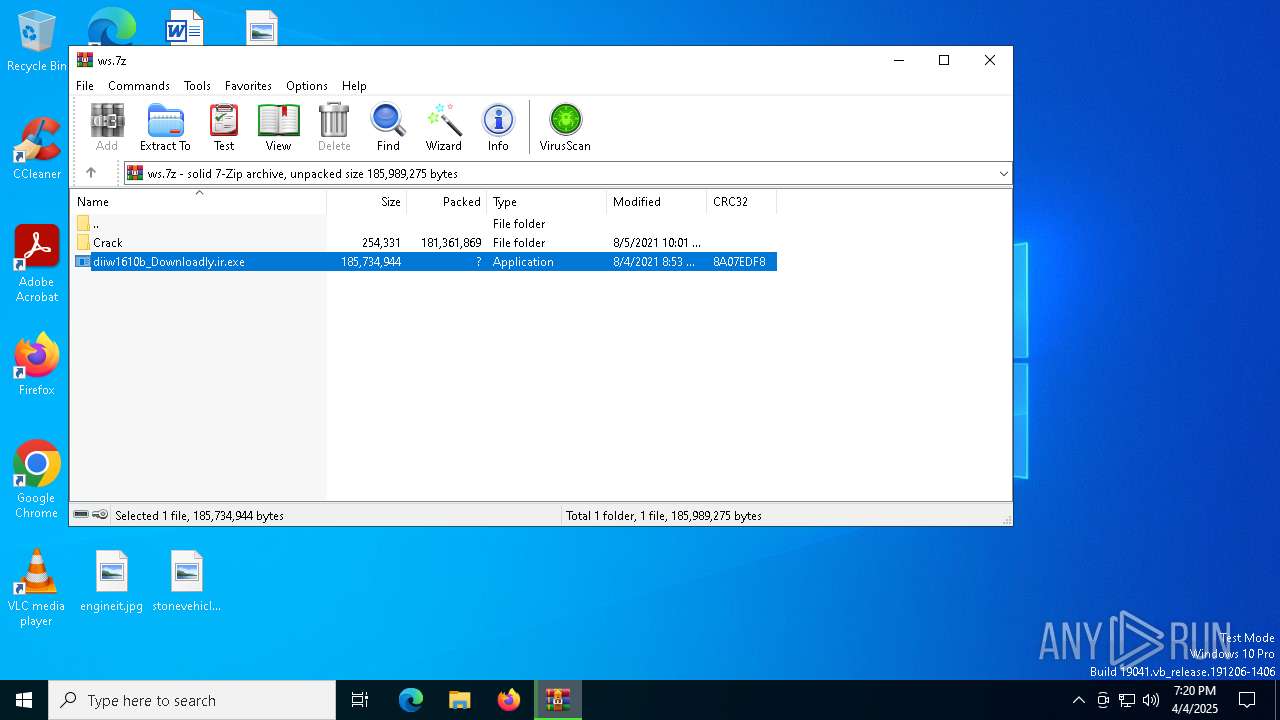
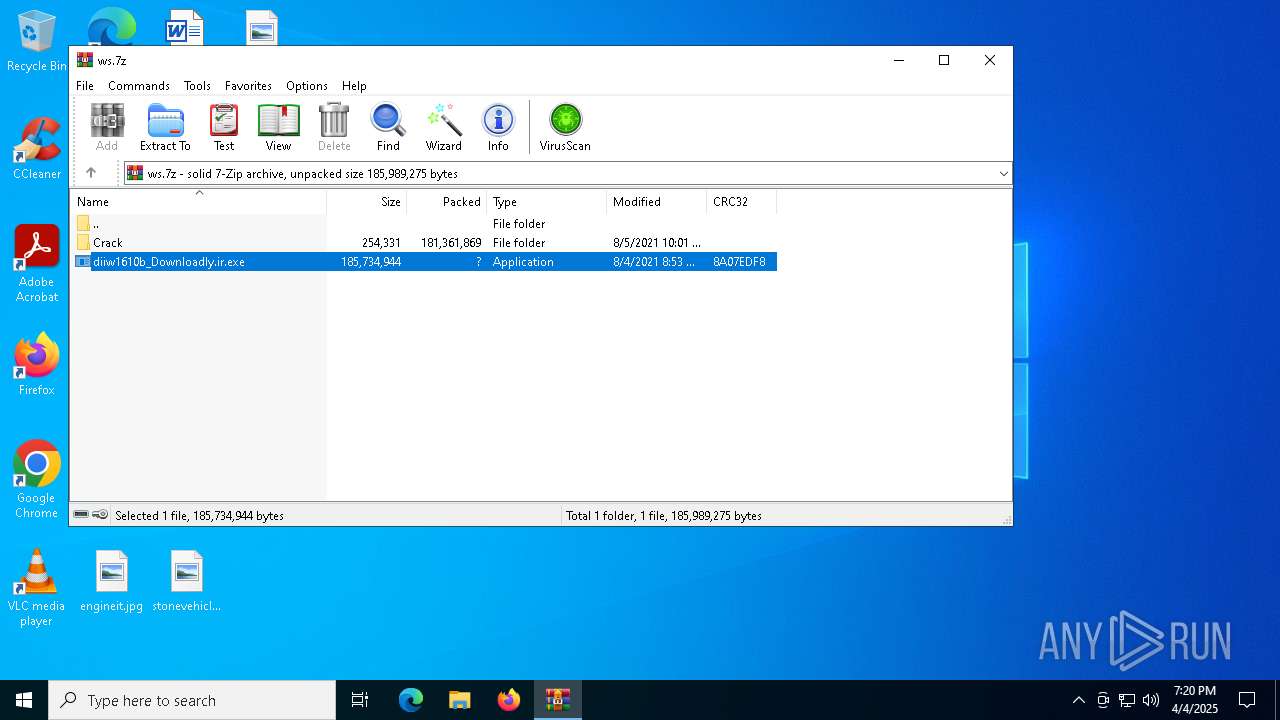
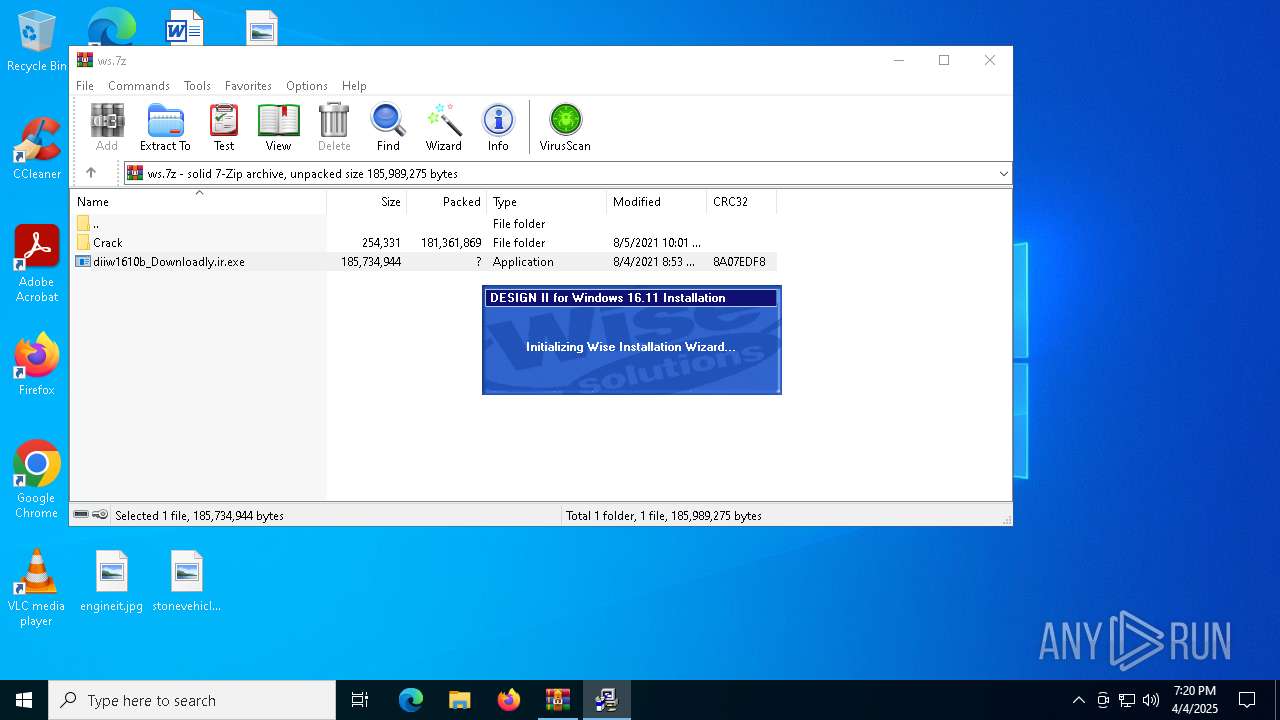
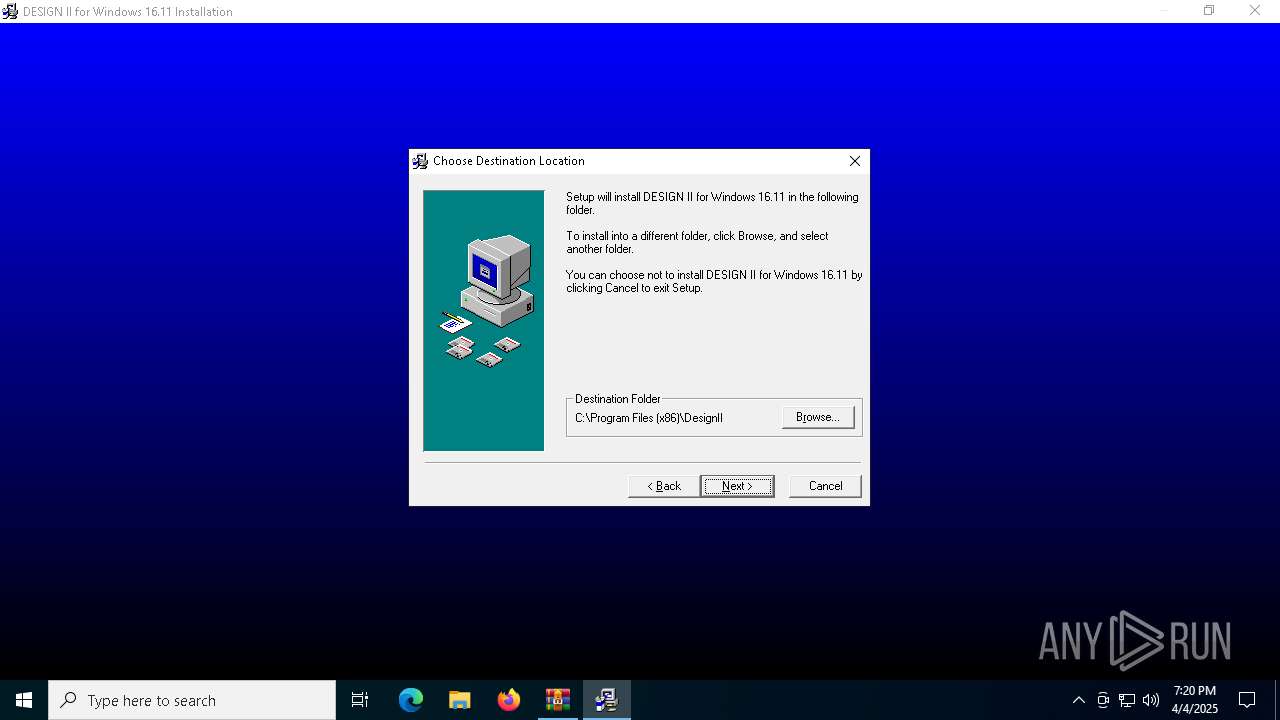
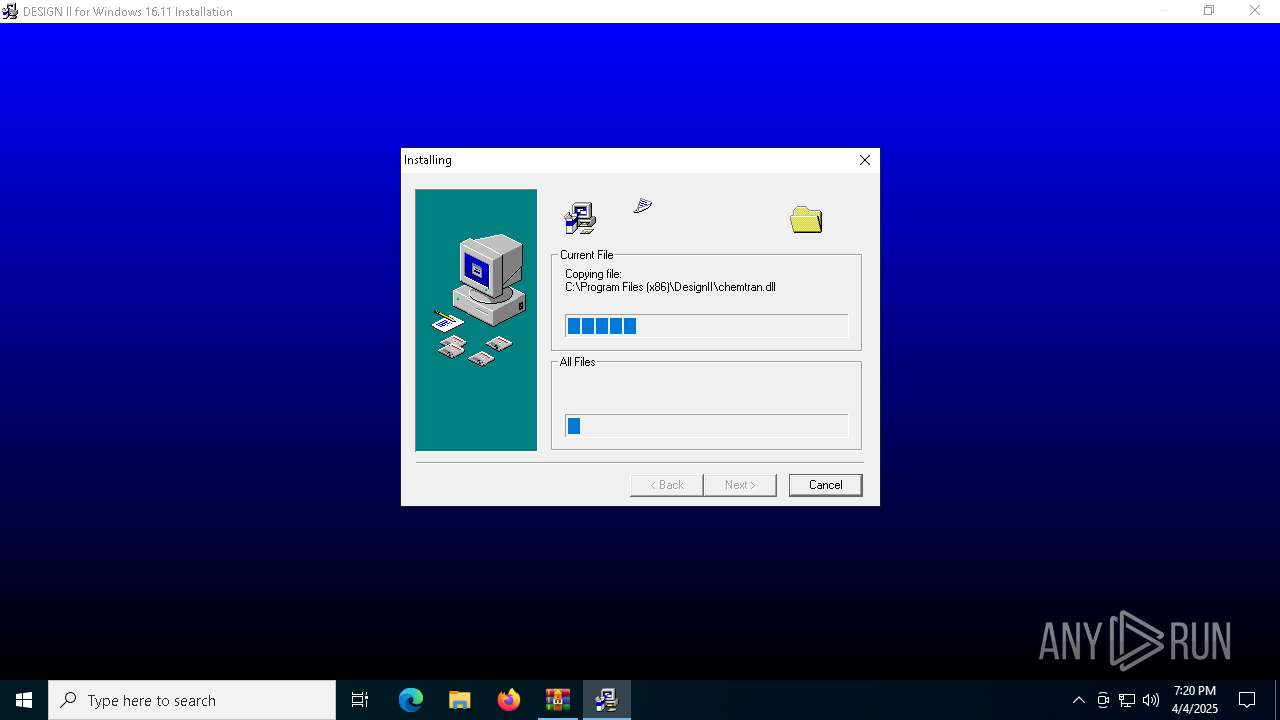
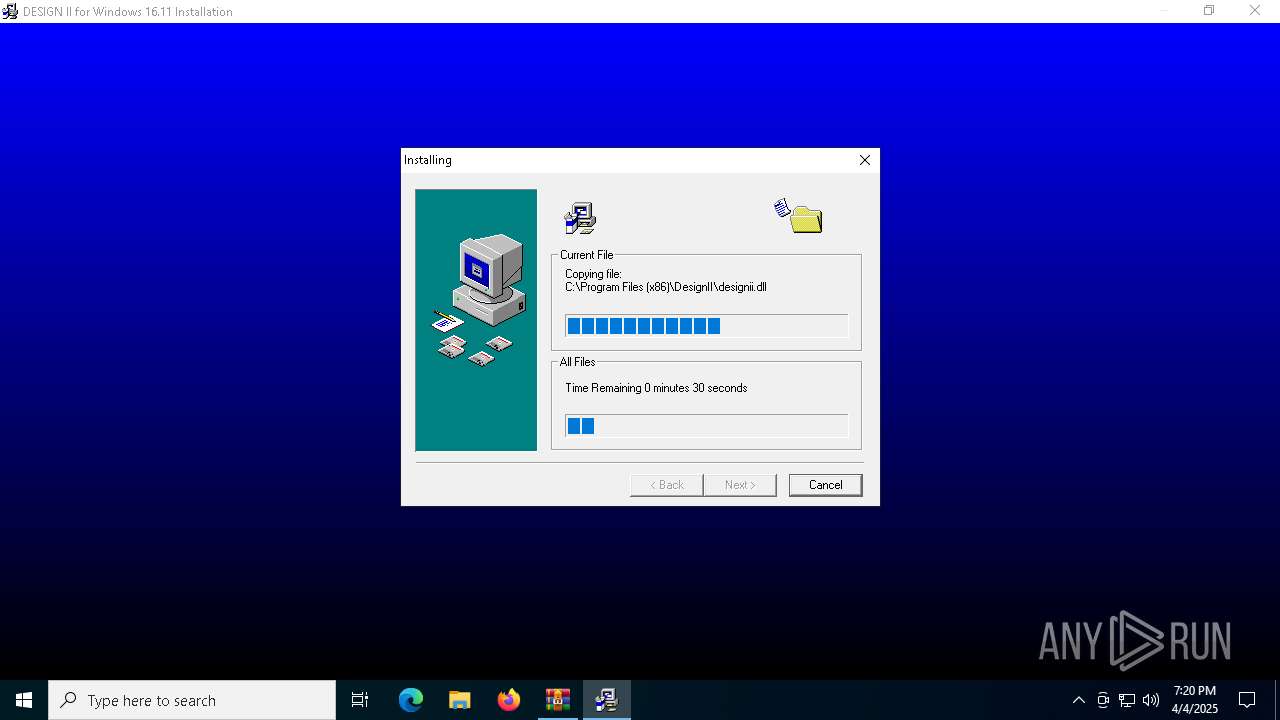
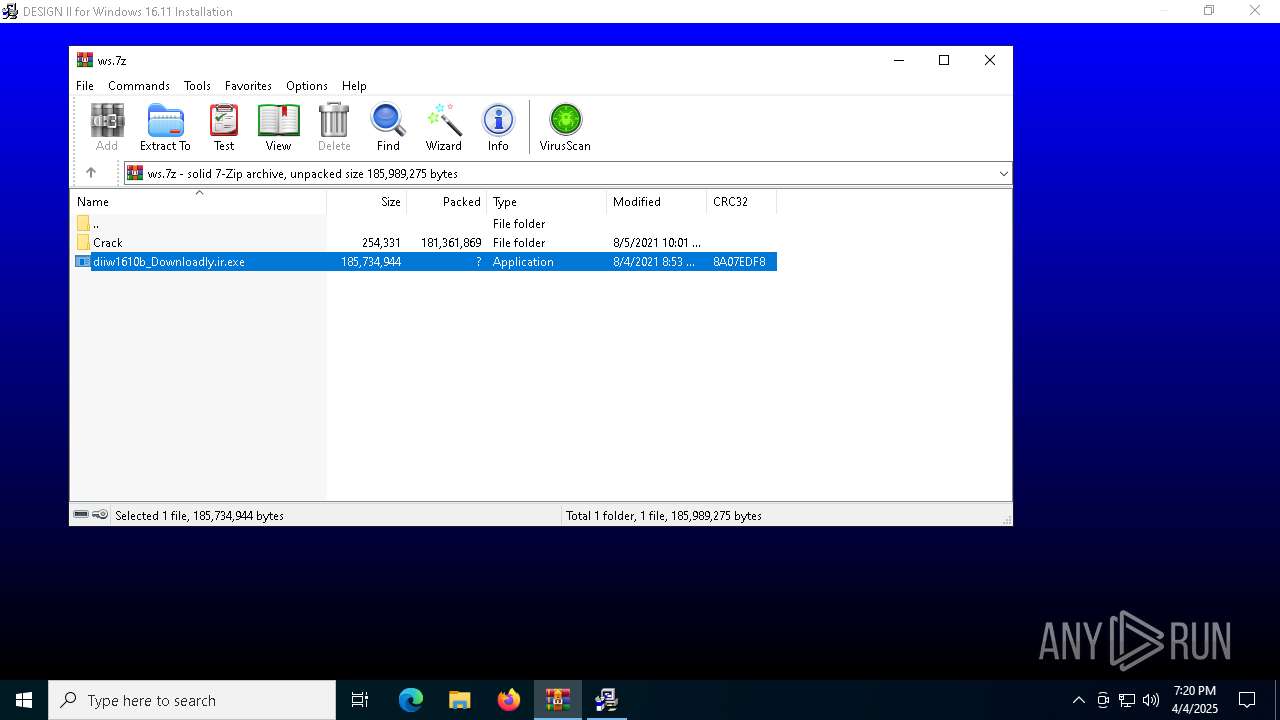
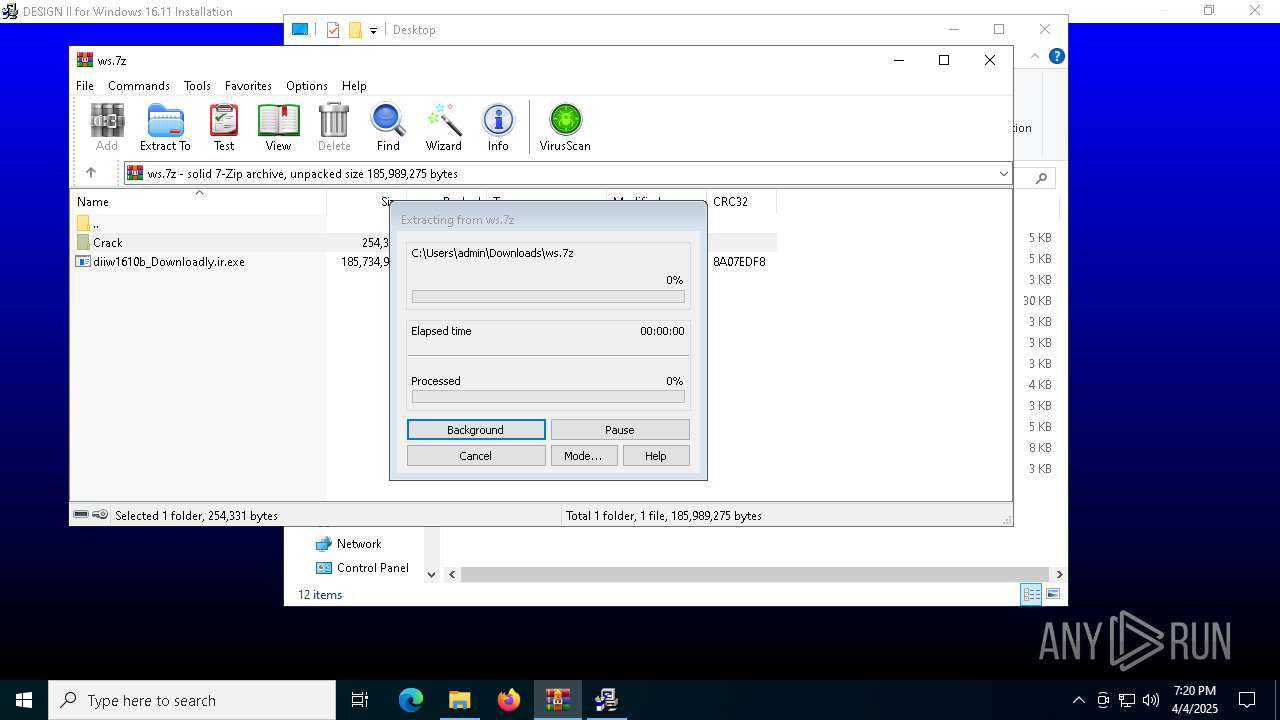
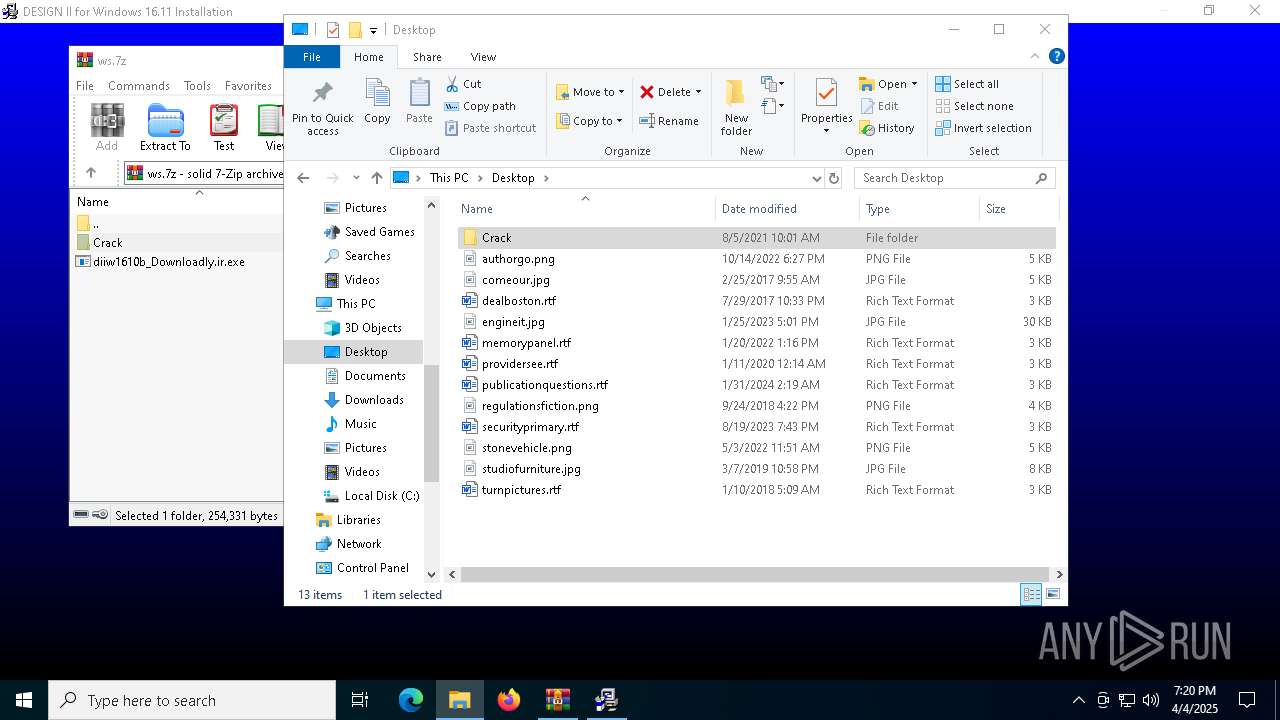
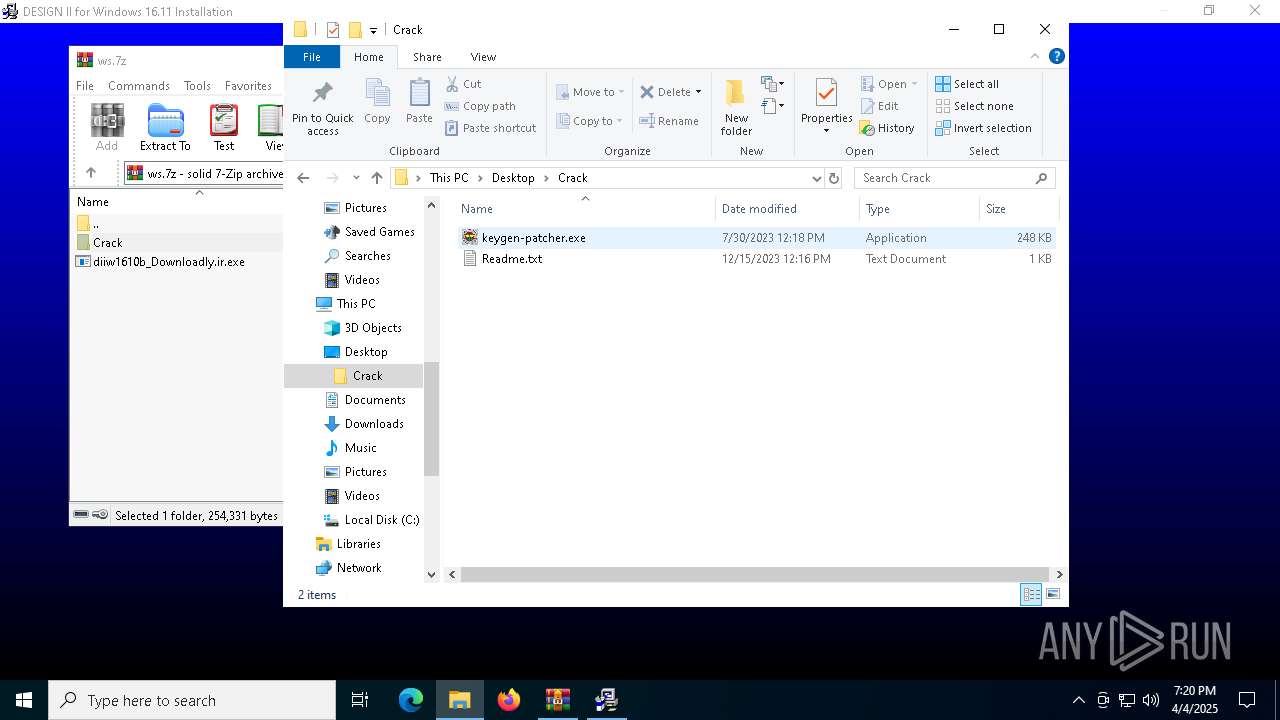
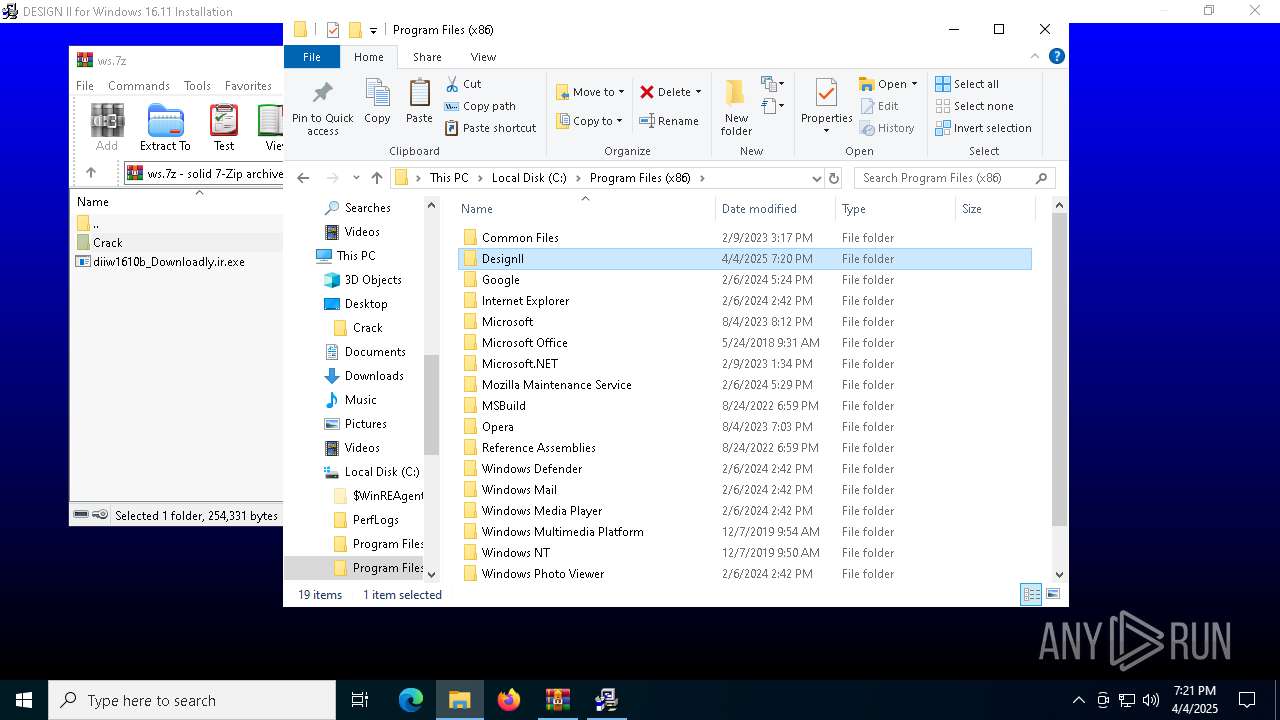
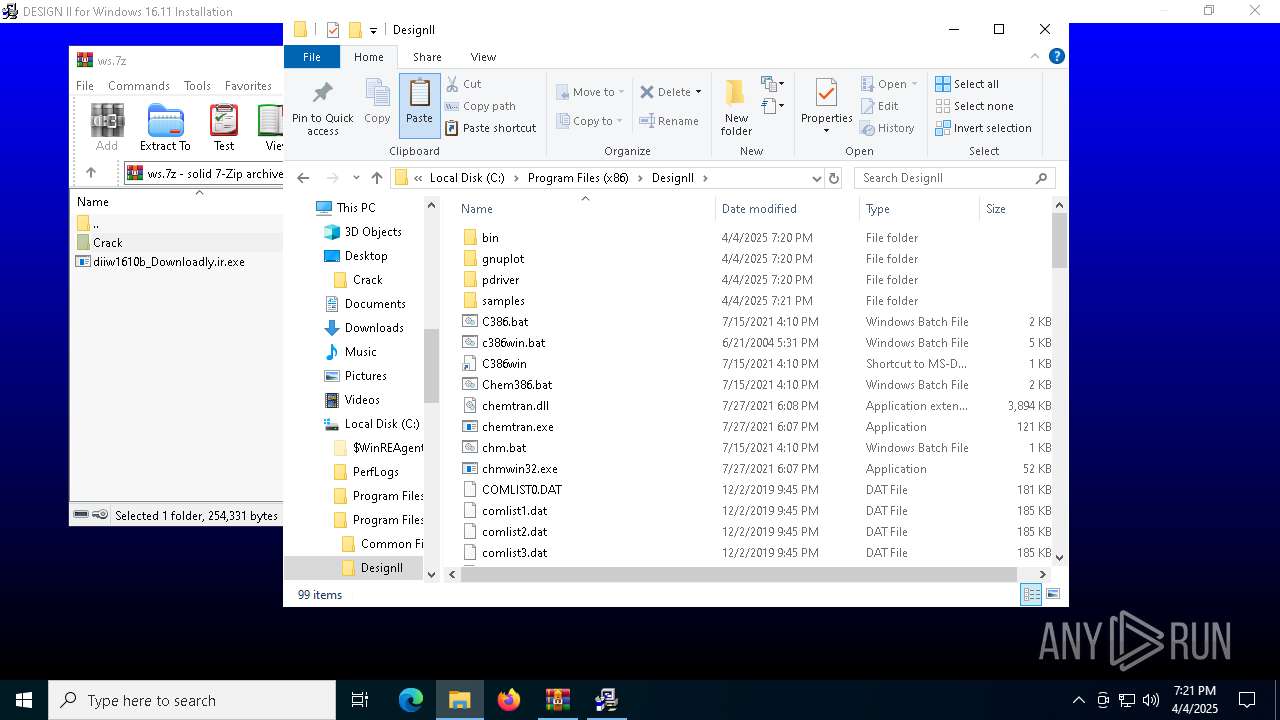
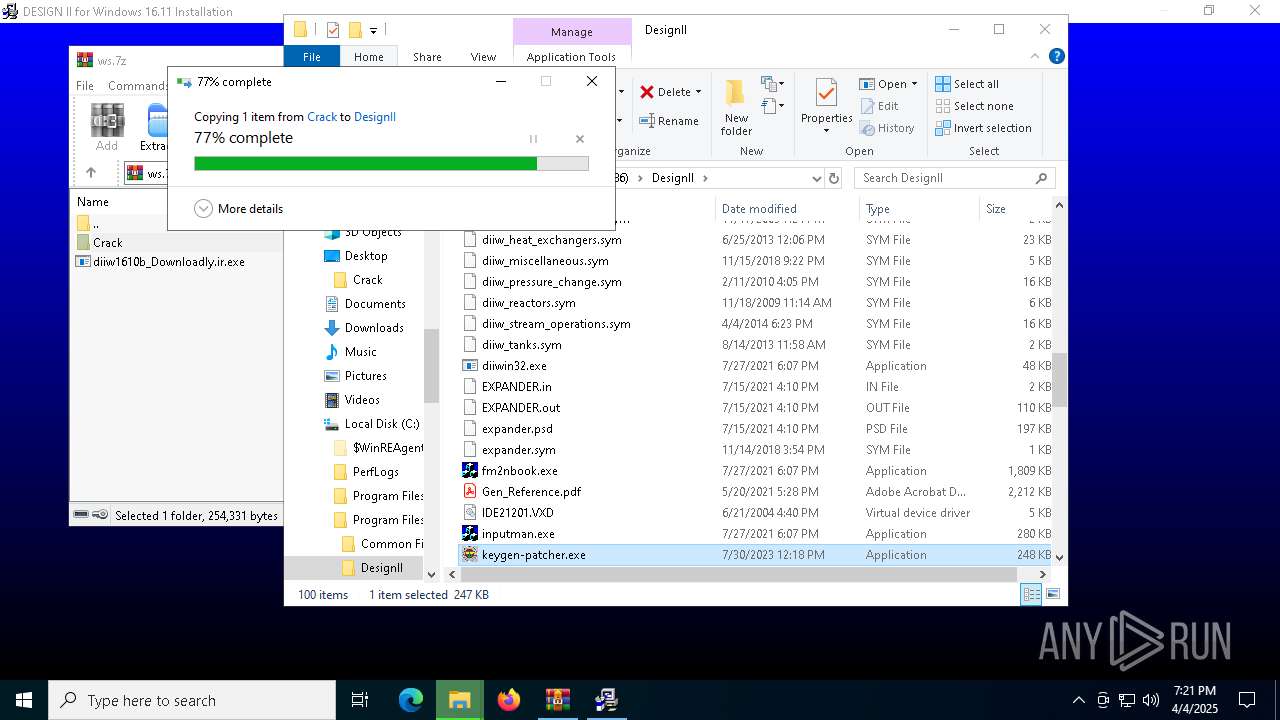
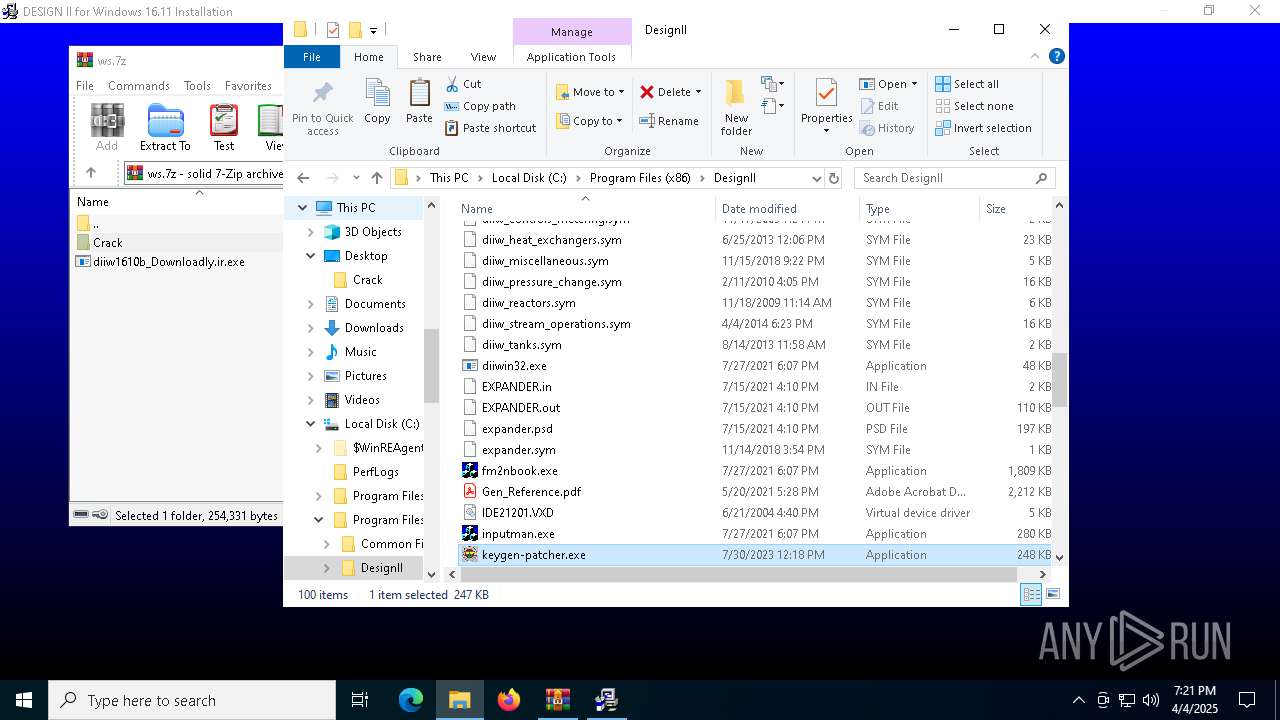
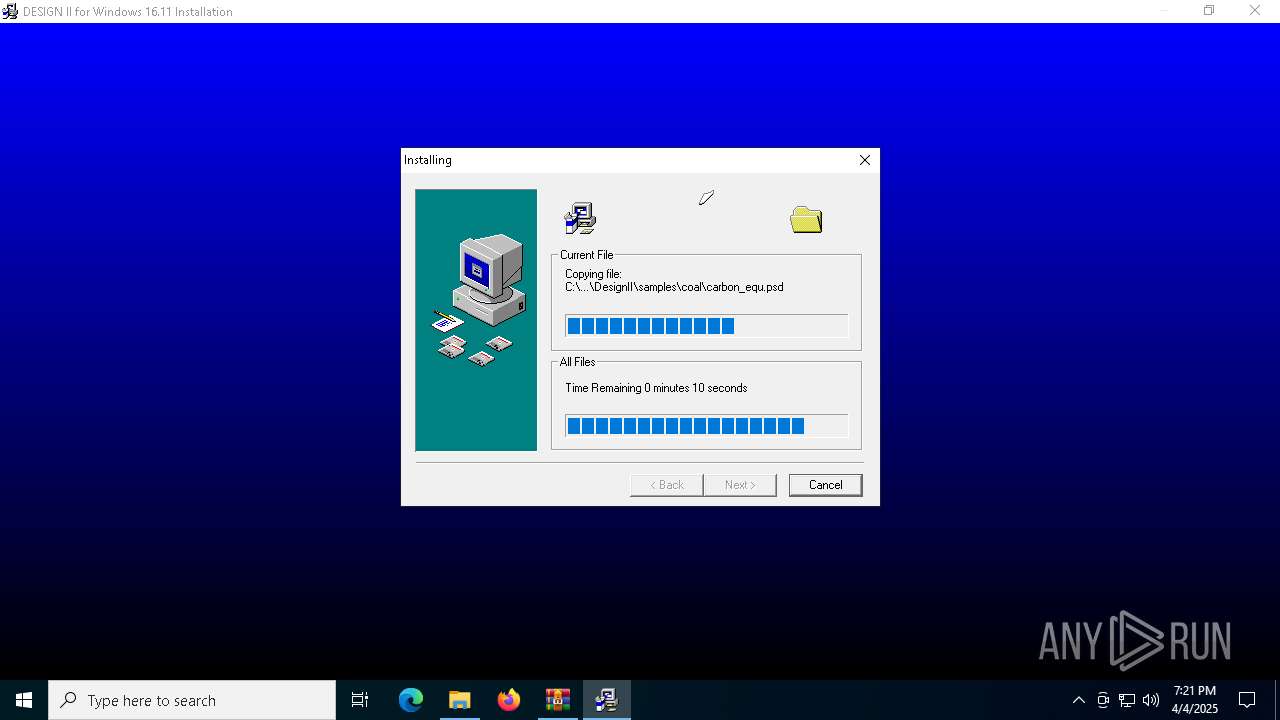
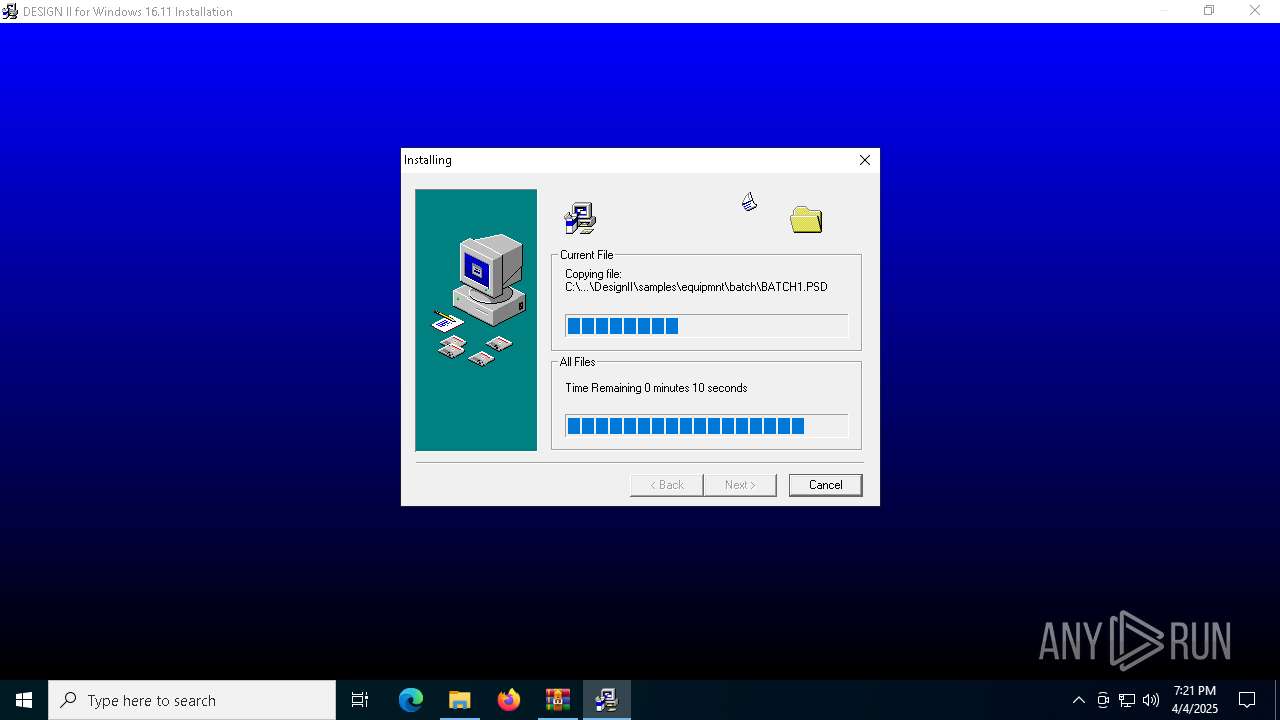
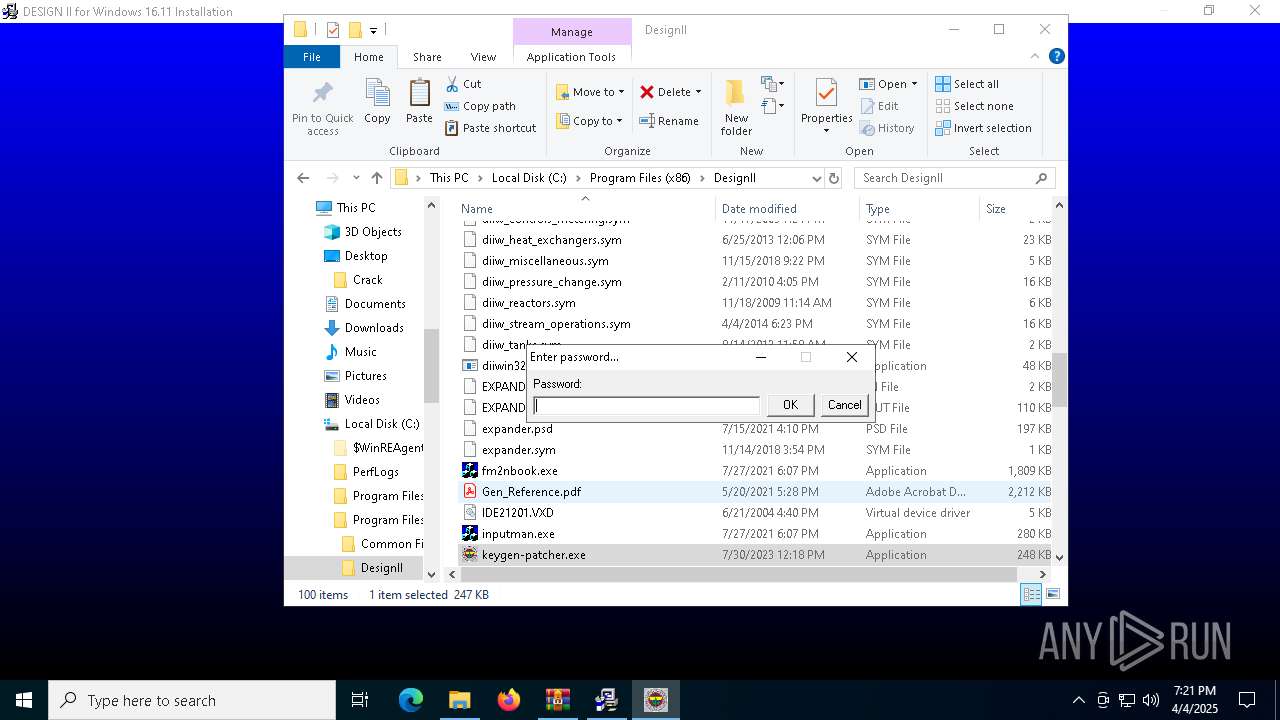
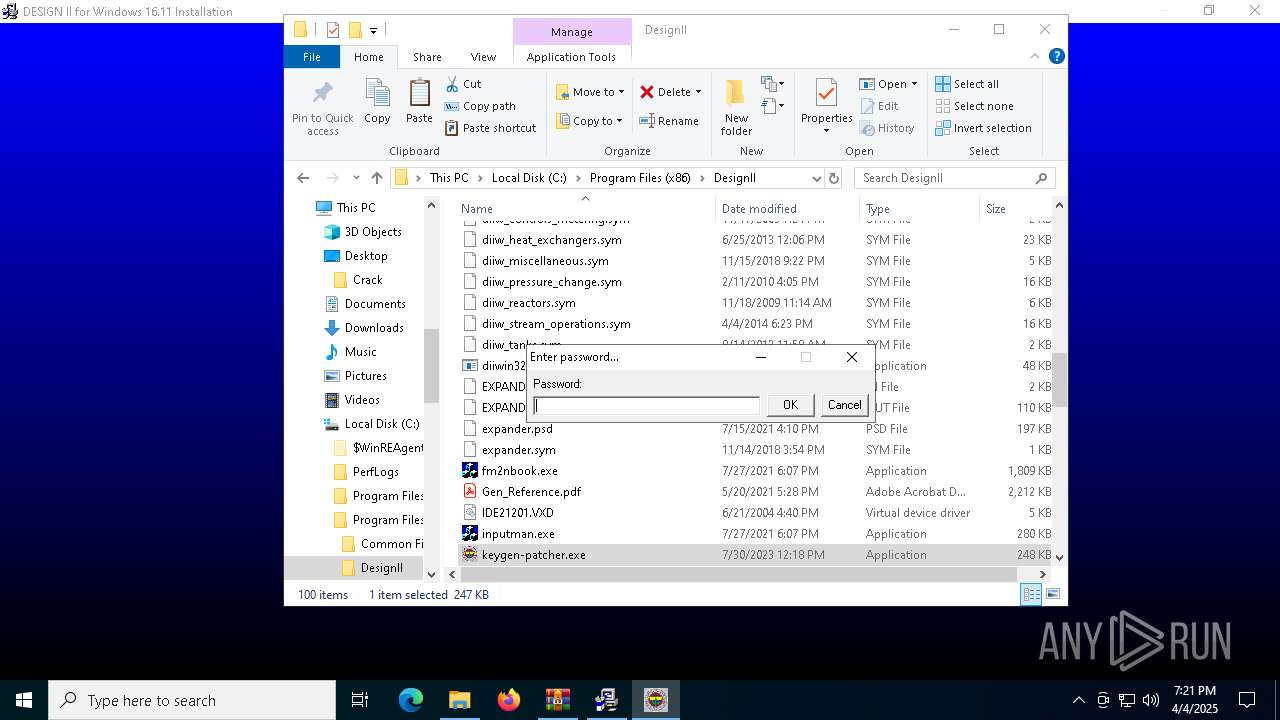
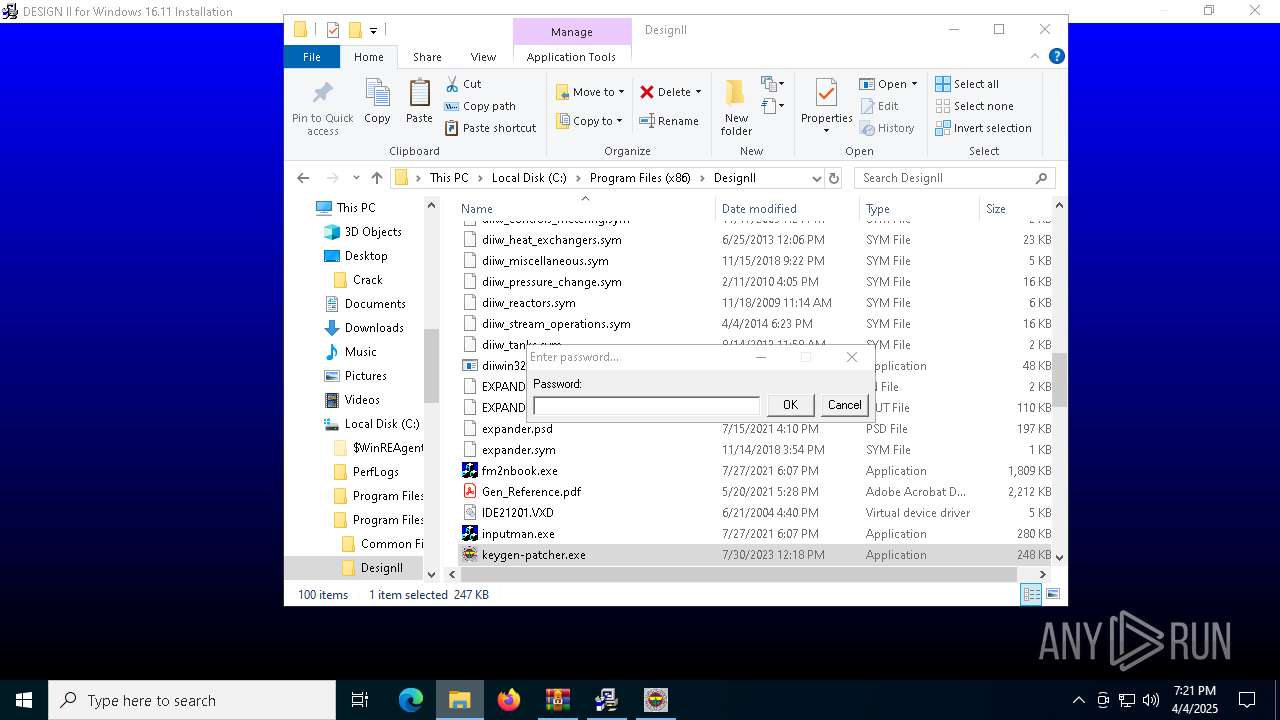
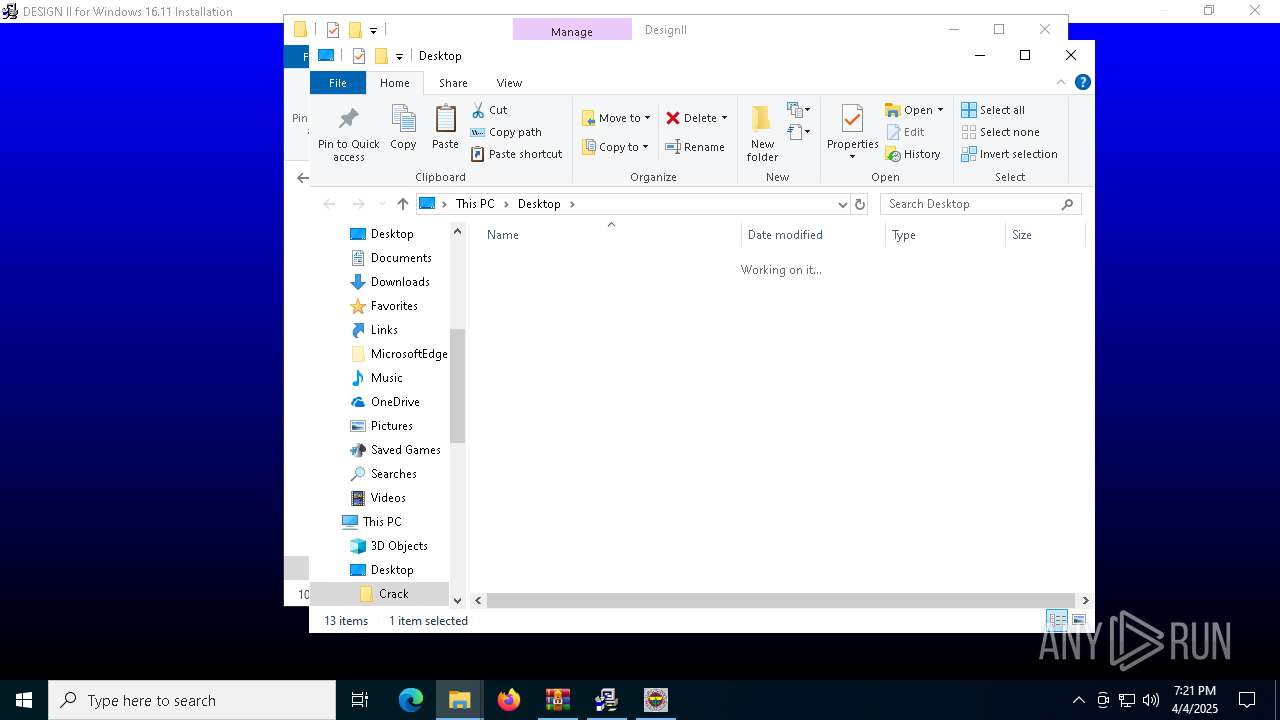
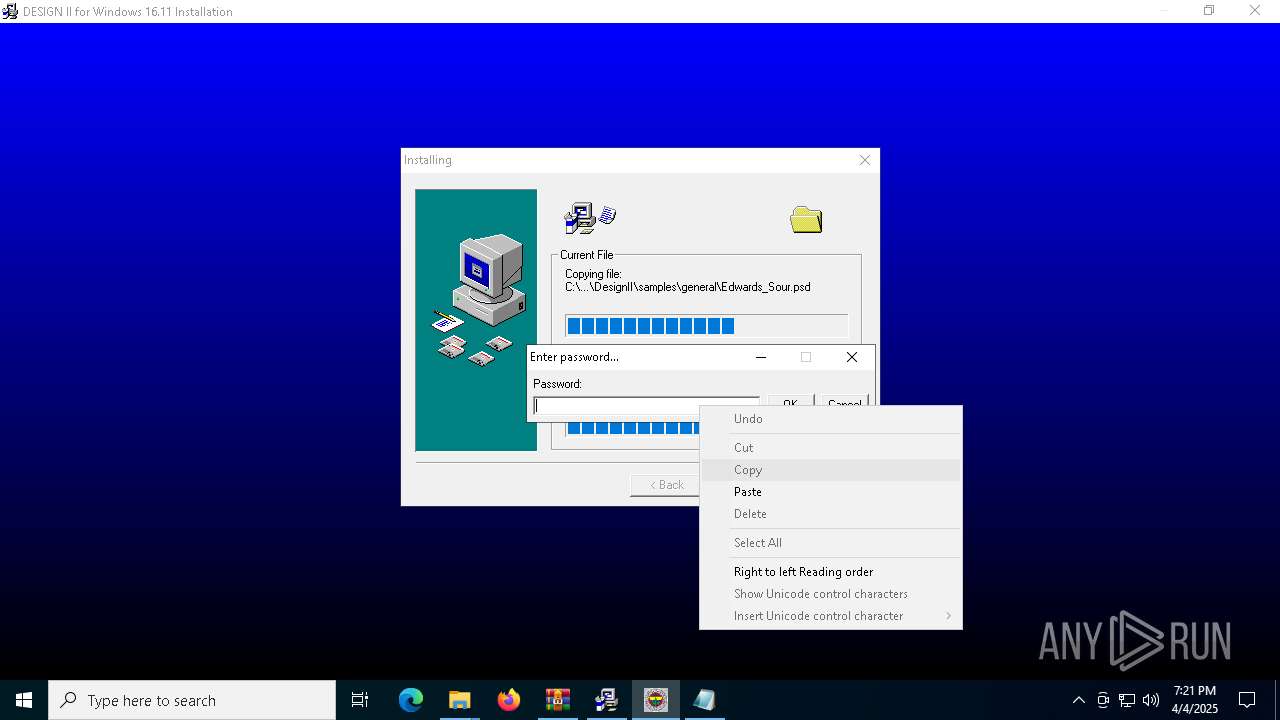
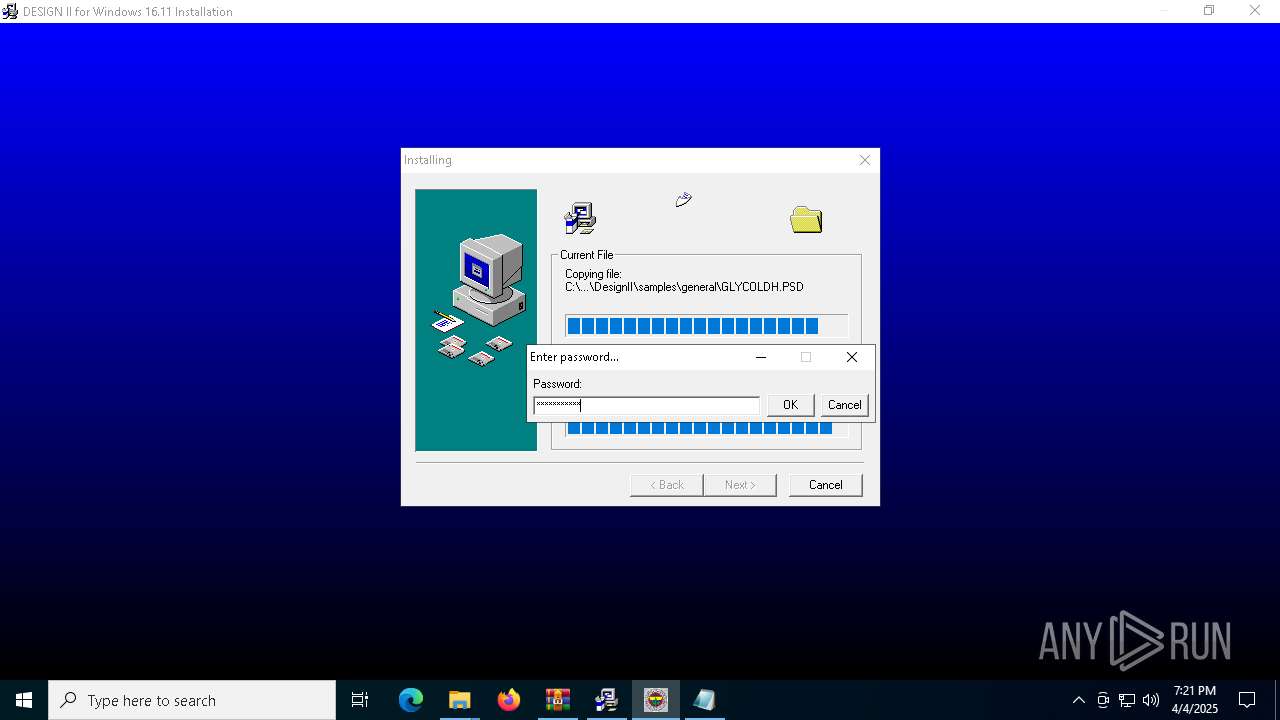
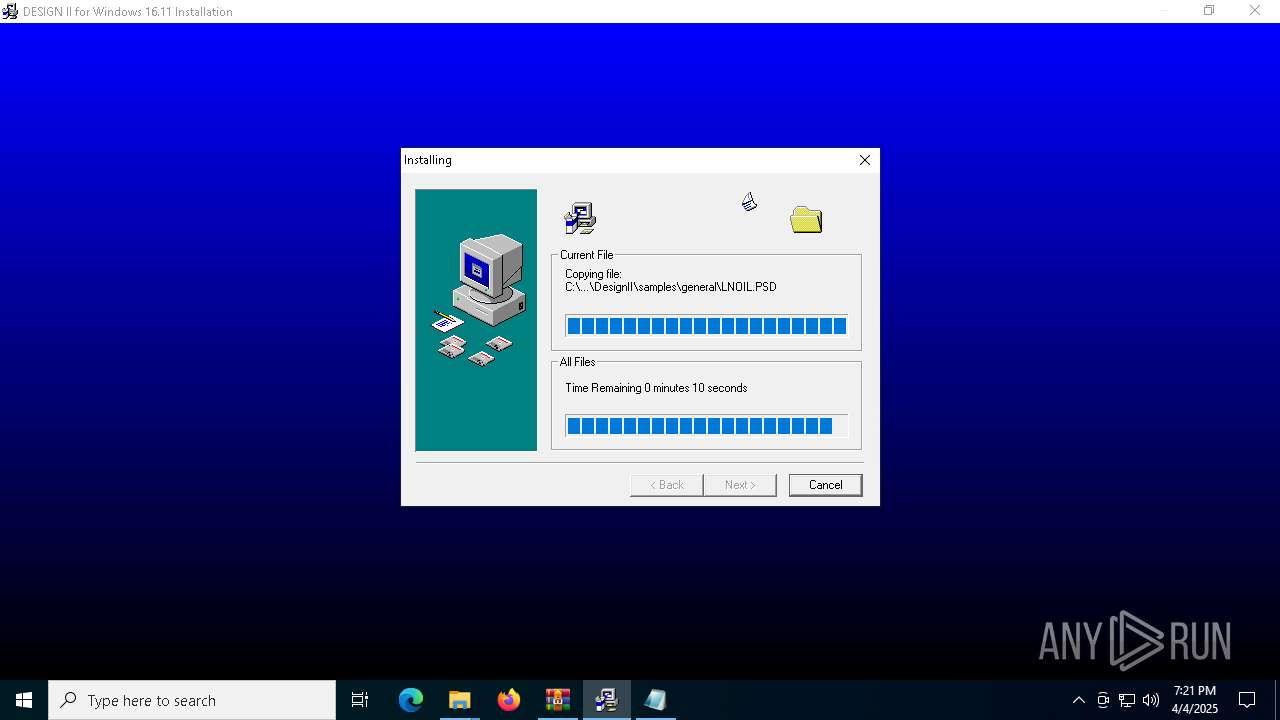
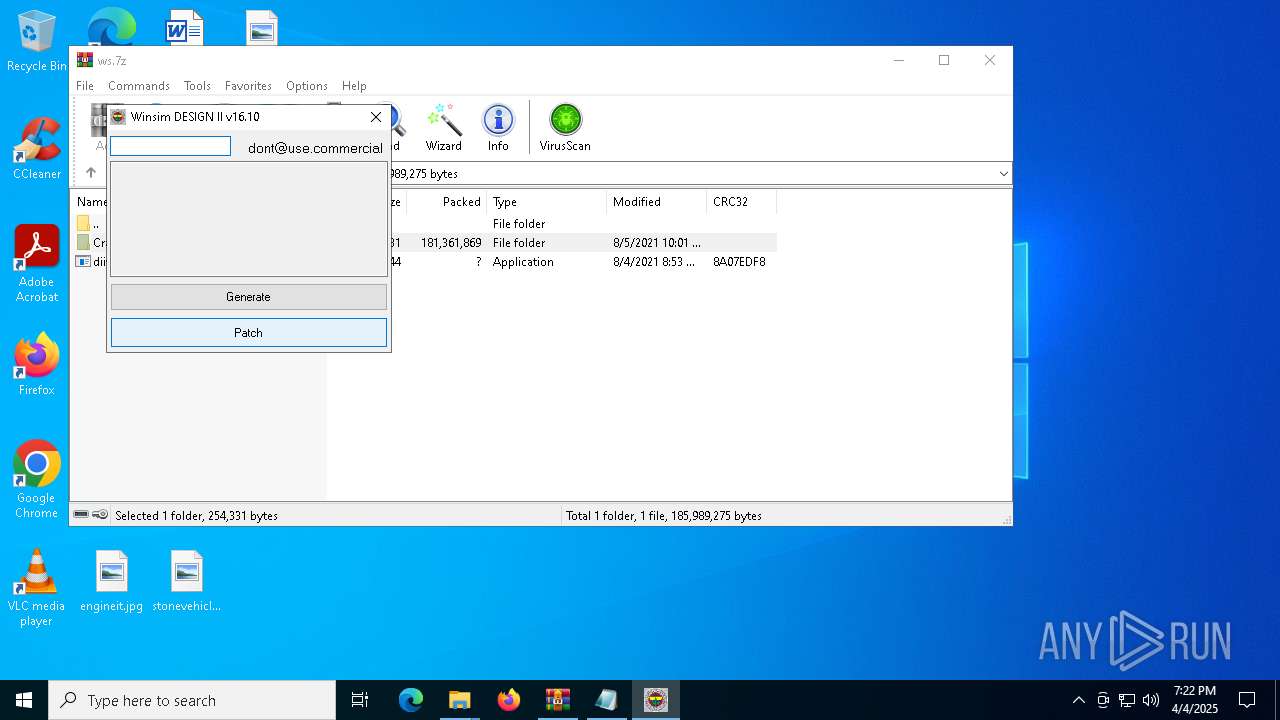
Executable content was dropped or overwritten
- diiw1610b_Downloadly.ir.exe (PID: 7604)
- GLBBAA2.tmp (PID: 7616)
- dllhost.exe (PID: 2316)
- vcredist_x86.exe (PID: 4692)
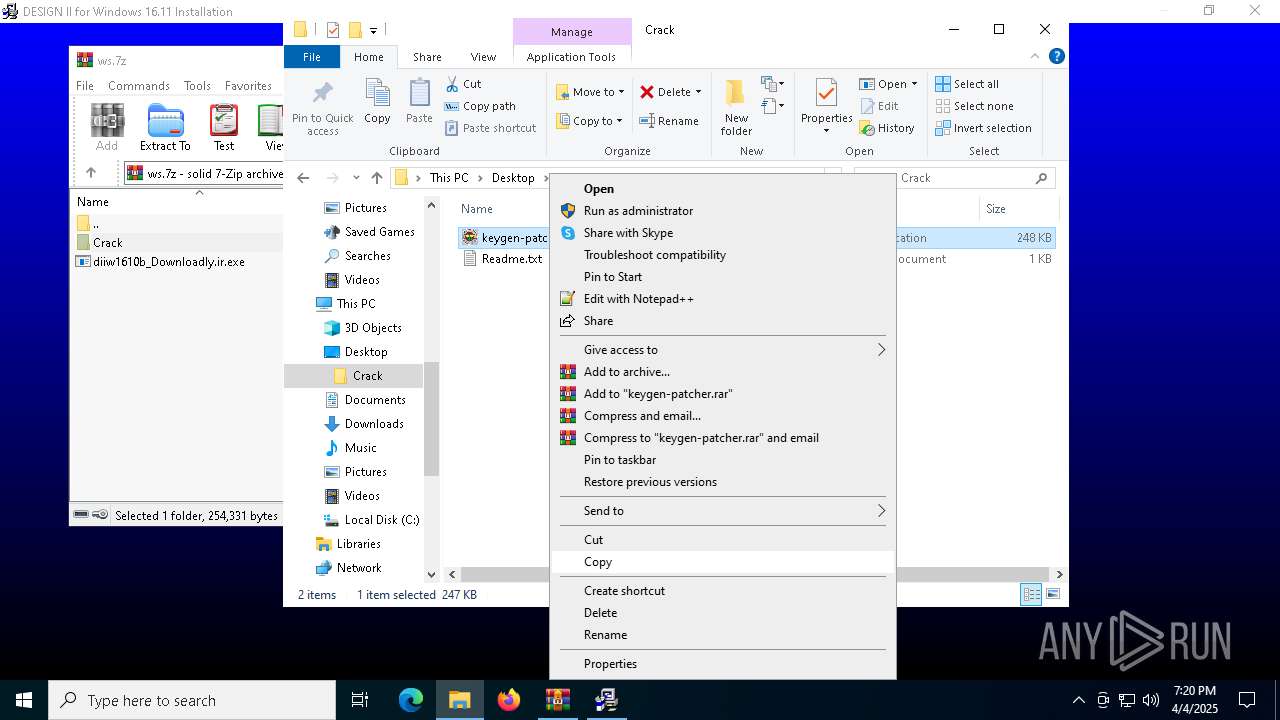
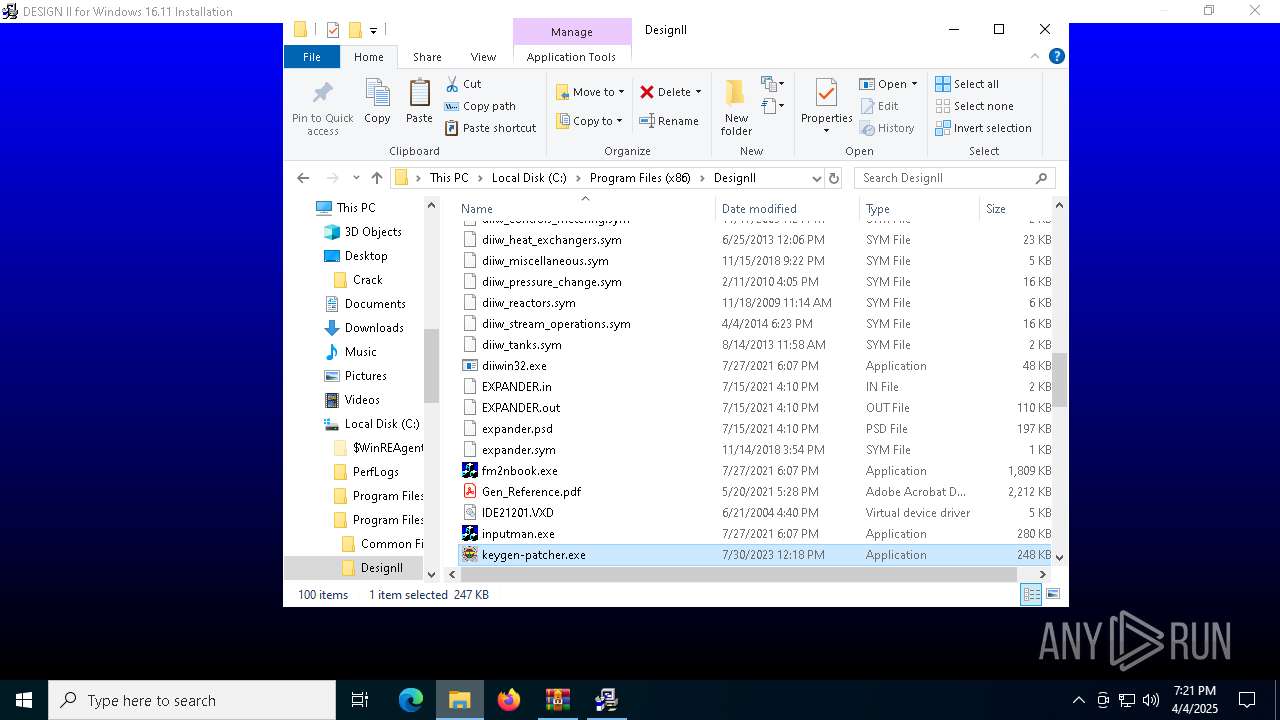
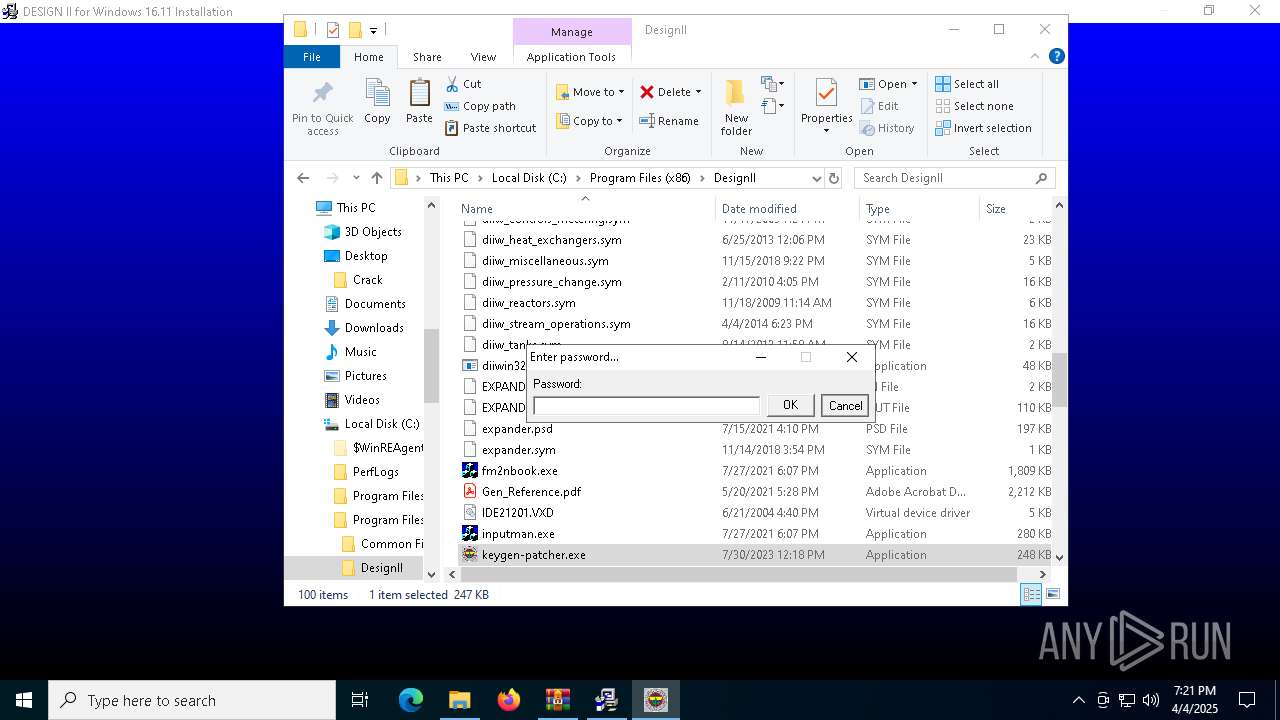
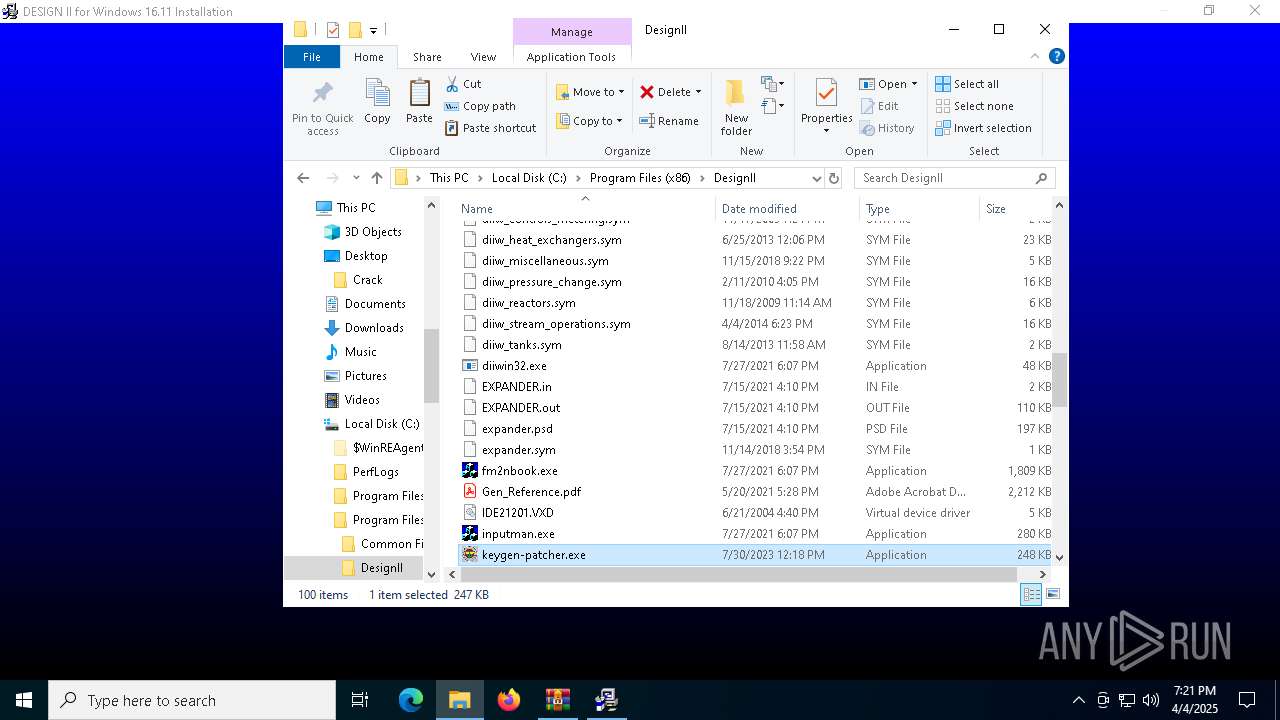
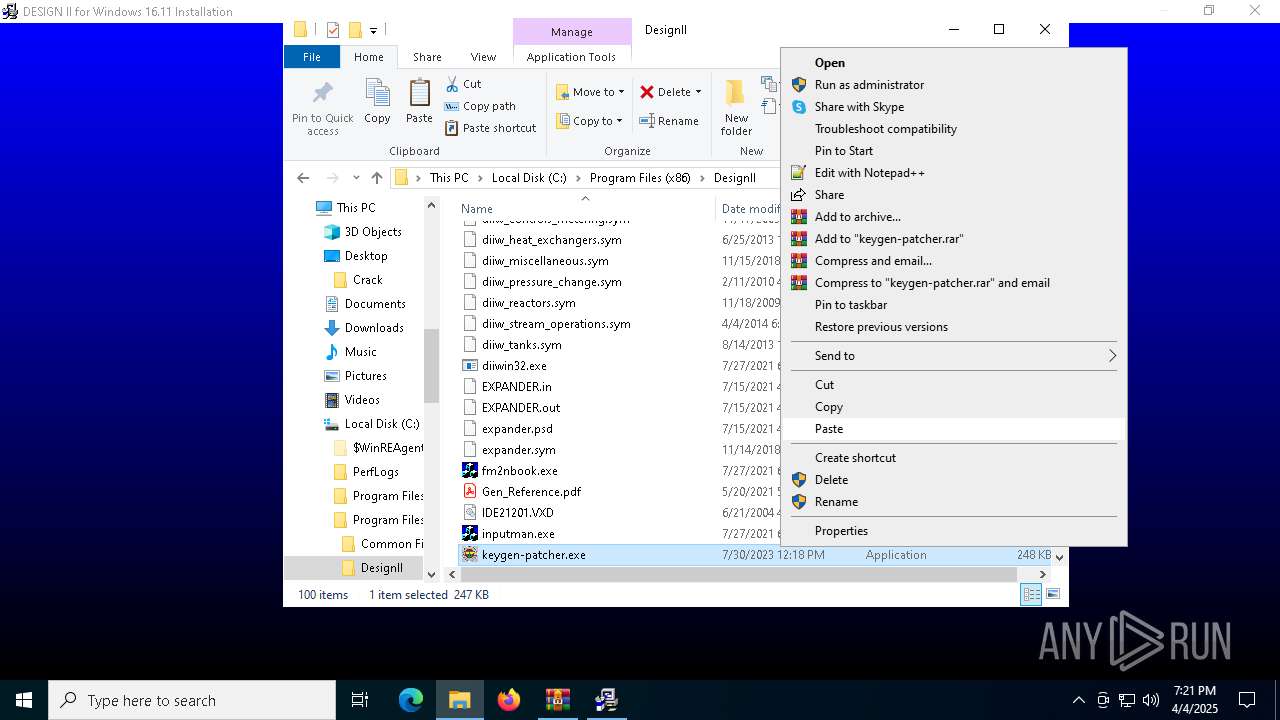
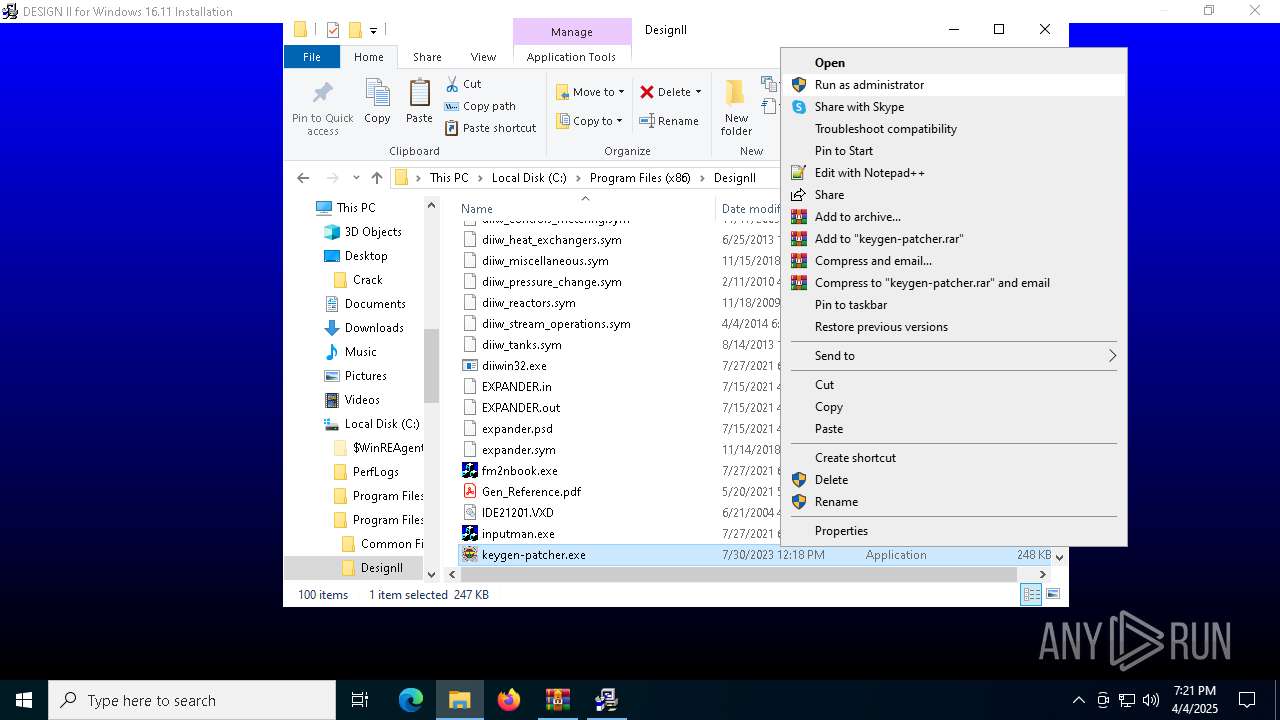
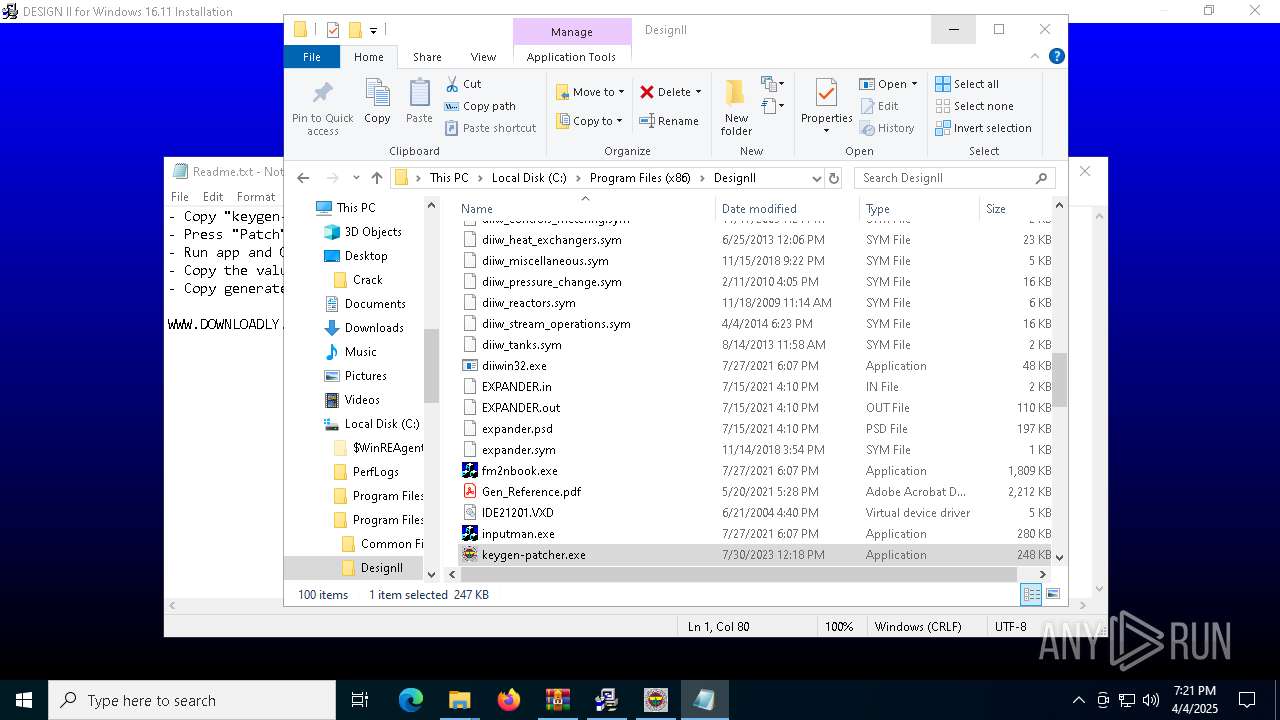
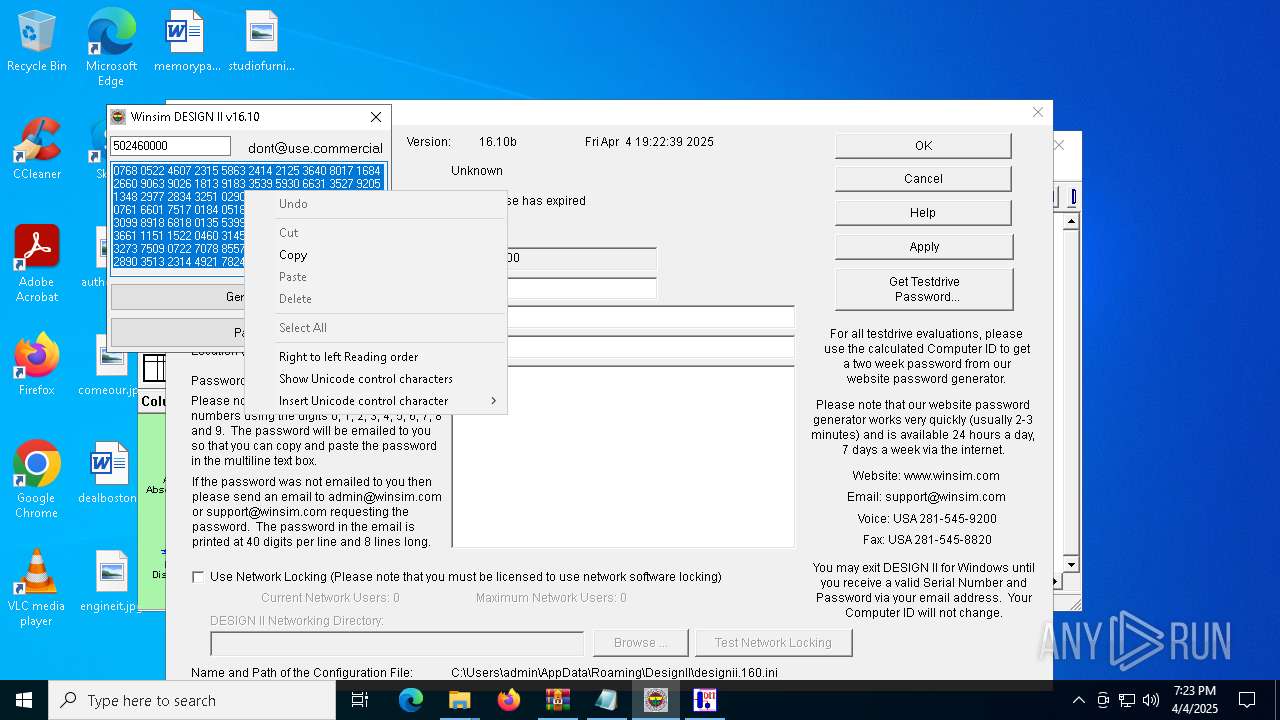
- keygen-patcher.exe (PID: 6248)
Starts application with an unusual extension
- diiw1610b_Downloadly.ir.exe (PID: 7604)
- GLBBAA2.tmp (PID: 7616)
Process drops legitimate windows executable
- GLBBAA2.tmp (PID: 7616)
- vcredist_x86.exe (PID: 4692)
Searches for installed software
- GLBBAA2.tmp (PID: 7616)
- vcredist_x86.exe (PID: 4692)
Creates a software uninstall entry
- GLBBAA2.tmp (PID: 7616)
There is functionality for taking screenshot (YARA)
- GLBBAA2.tmp (PID: 7616)
- DESWIN.exe (PID: 7684)
The process drops C-runtime libraries
- GLBBAA2.tmp (PID: 7616)
Creates/Modifies COM task schedule object
- GLJBB4F.tmp (PID: 4724)
- GLJBB4F.tmp (PID: 7752)
- GLJBB4F.tmp (PID: 7236)
- GLJBB4F.tmp (PID: 4068)
Application launched itself
- vcredist_x86.exe (PID: 7368)
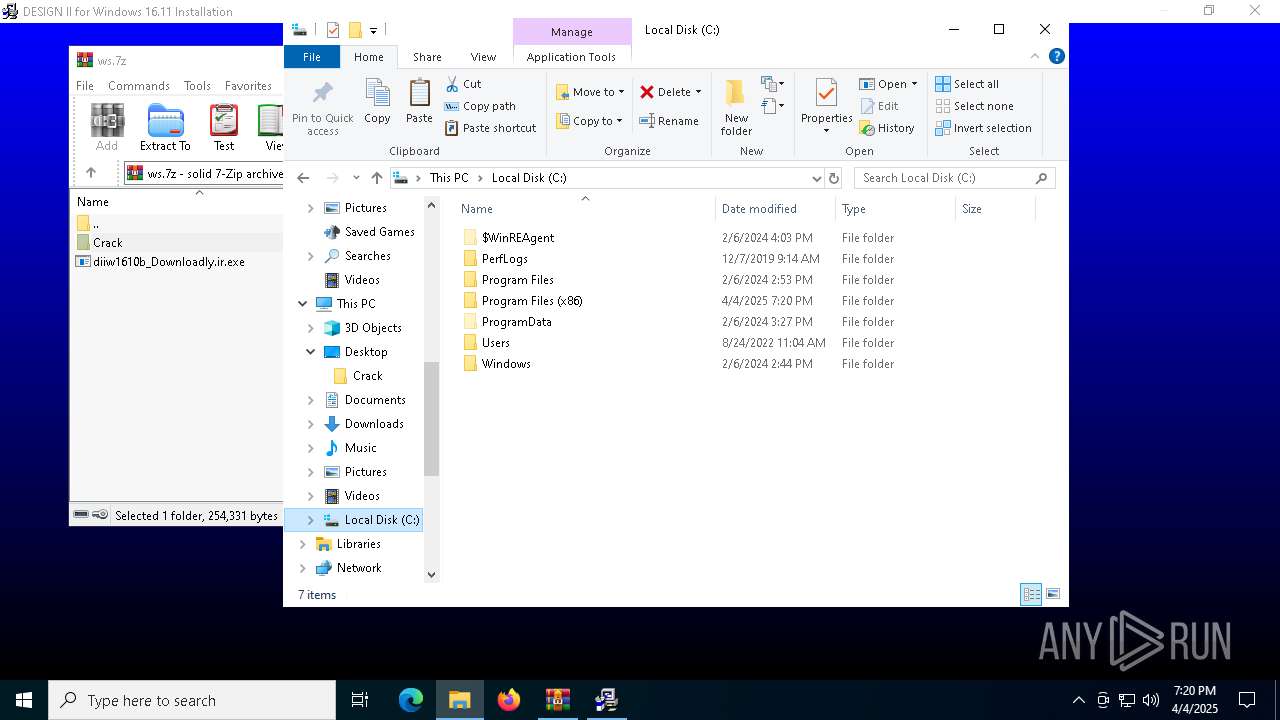
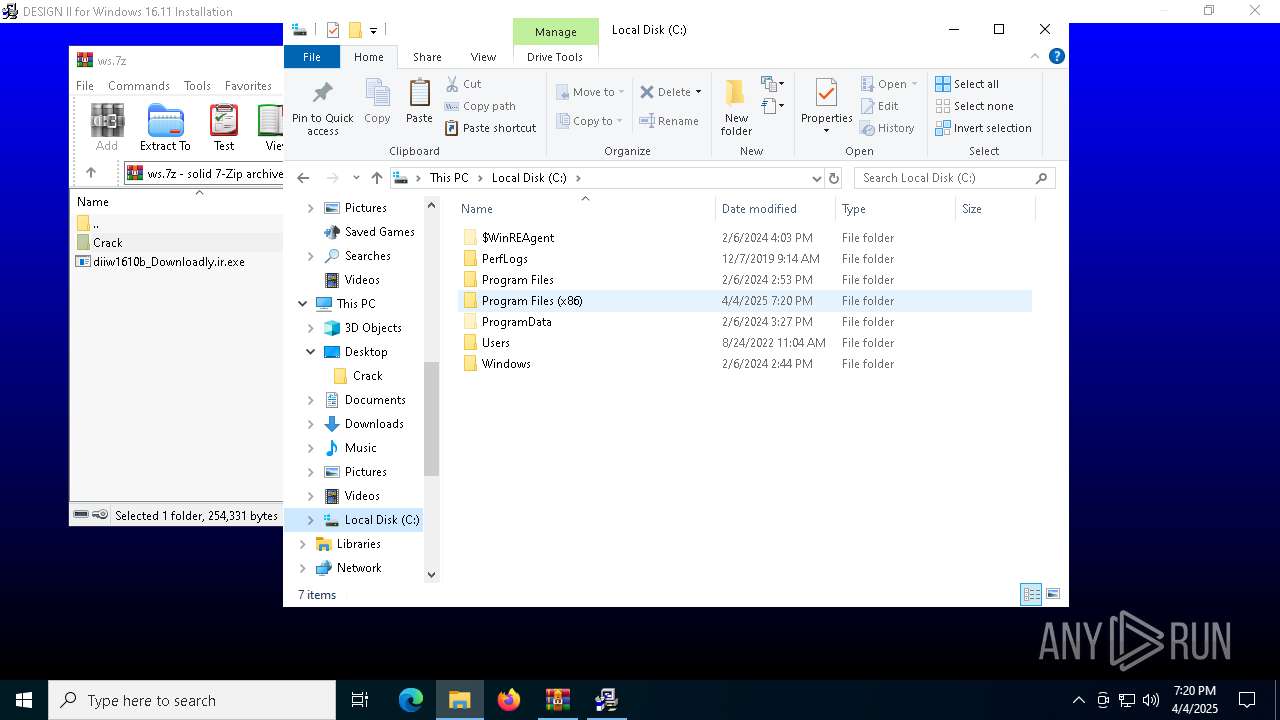
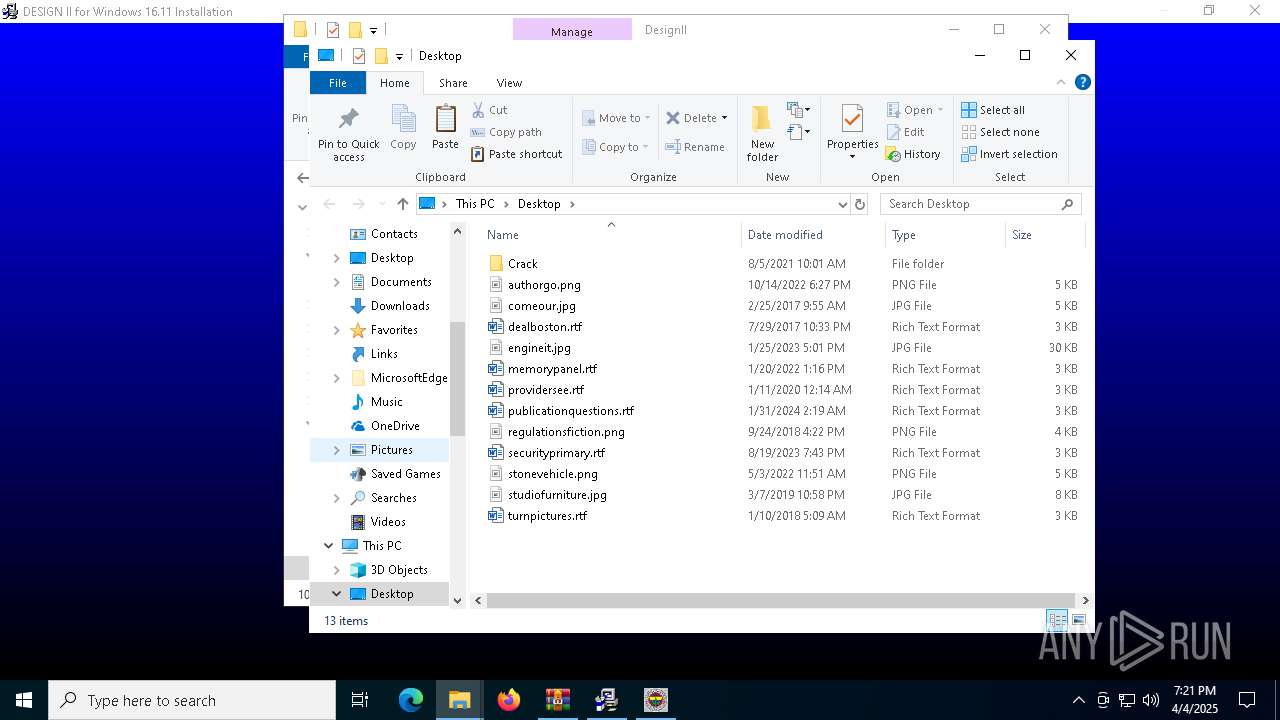
Creates file in the systems drive root
- DESWIN.exe (PID: 7684)
INFO
Checks supported languages
- identity_helper.exe (PID: 7748)
- identity_helper.exe (PID: 2064)
- diiw1610b_Downloadly.ir.exe (PID: 7604)
- GLBBAA2.tmp (PID: 7616)
- keygen-patcher.exe (PID: 7540)
- keygen-patcher.exe (PID: 6248)
- GLJBB4F.tmp (PID: 4724)
- GLJBB4F.tmp (PID: 7752)
- GLJBB4F.tmp (PID: 7236)
- GLJBB4F.tmp (PID: 4068)
- ShellExperienceHost.exe (PID: 7100)
- vcredist_x86.exe (PID: 7368)
- vcredist_x86.exe (PID: 4692)
- DESWIN.exe (PID: 7684)
Autorun file from Downloads
- msedge.exe (PID: 6272)
Reads Microsoft Office registry keys
- msedge.exe (PID: 5960)
Reads the computer name
- identity_helper.exe (PID: 7748)
- identity_helper.exe (PID: 2064)
- GLBBAA2.tmp (PID: 7616)
- keygen-patcher.exe (PID: 7540)
- ShellExperienceHost.exe (PID: 7100)
- GLJBB4F.tmp (PID: 7752)
- GLJBB4F.tmp (PID: 4724)
- GLJBB4F.tmp (PID: 7236)
- keygen-patcher.exe (PID: 6248)
- GLJBB4F.tmp (PID: 4068)
- vcredist_x86.exe (PID: 7368)
- vcredist_x86.exe (PID: 4692)
- DESWIN.exe (PID: 7684)
Reads Environment values
- identity_helper.exe (PID: 7748)
- identity_helper.exe (PID: 2064)
Application launched itself
- msedge.exe (PID: 5960)
- msedge.exe (PID: 1168)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 4180)
- msedge.exe (PID: 7636)
Reads the software policy settings
- slui.exe (PID: 8044)
- slui.exe (PID: 1764)
Create files in a temporary directory
- diiw1610b_Downloadly.ir.exe (PID: 7604)
- GLBBAA2.tmp (PID: 7616)
- vcredist_x86.exe (PID: 4692)
The sample compiled with english language support
- diiw1610b_Downloadly.ir.exe (PID: 7604)
- GLBBAA2.tmp (PID: 7616)
- vcredist_x86.exe (PID: 4692)
- msedge.exe (PID: 7636)
- keygen-patcher.exe (PID: 6248)
Checks proxy server information
- slui.exe (PID: 1764)
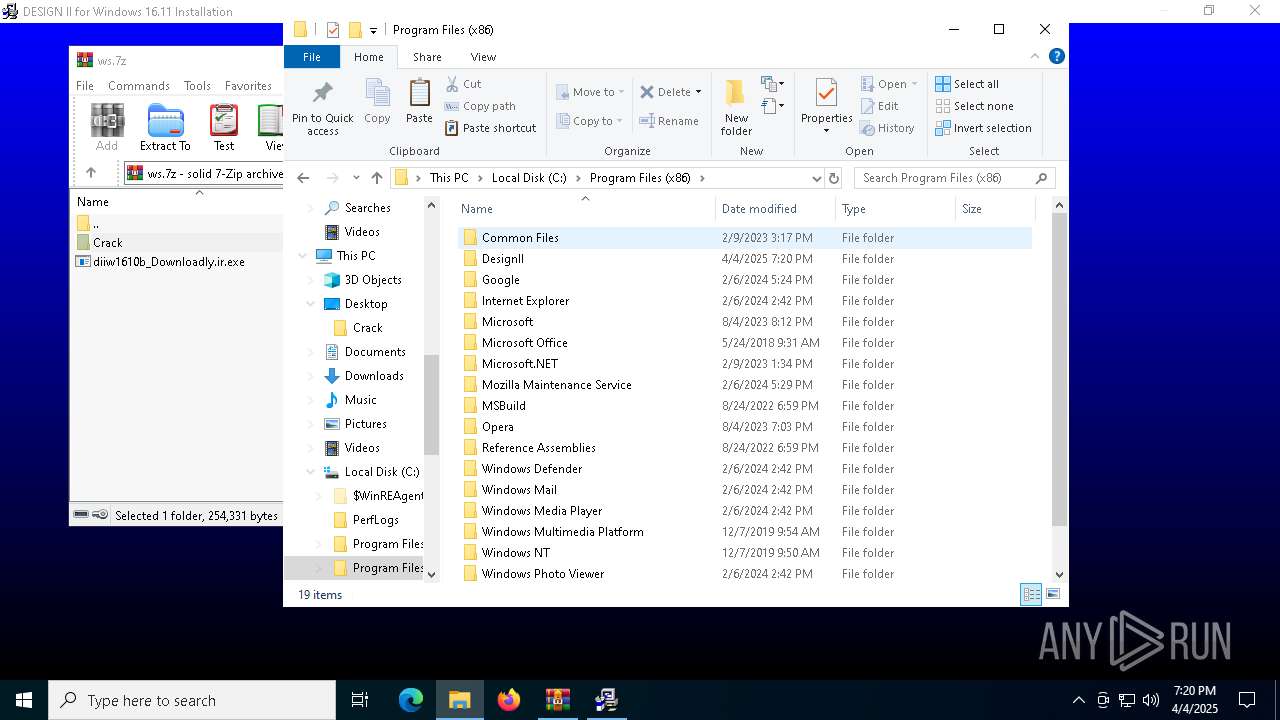
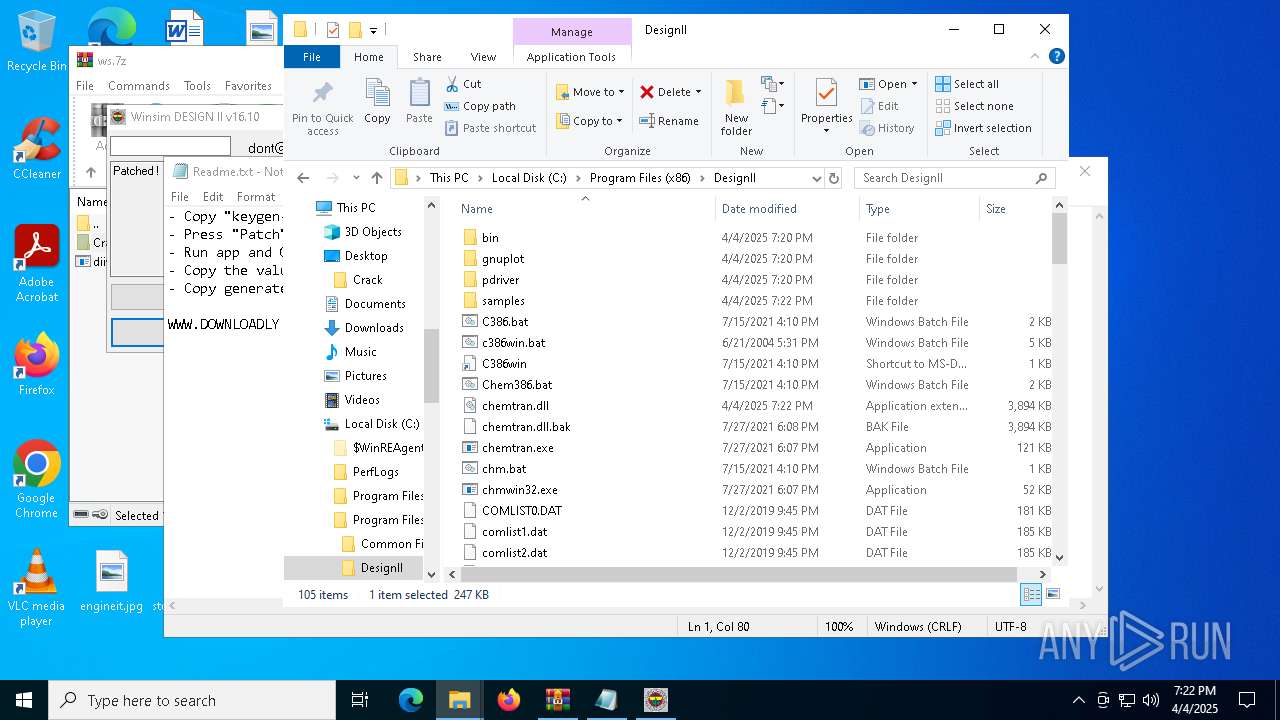
Creates files in the program directory
- GLBBAA2.tmp (PID: 7616)
- dllhost.exe (PID: 2316)
- keygen-patcher.exe (PID: 6248)
Reads security settings of Internet Explorer
- dllhost.exe (PID: 2316)
- notepad.exe (PID: 7444)
The sample compiled with german language support
- GLBBAA2.tmp (PID: 7616)
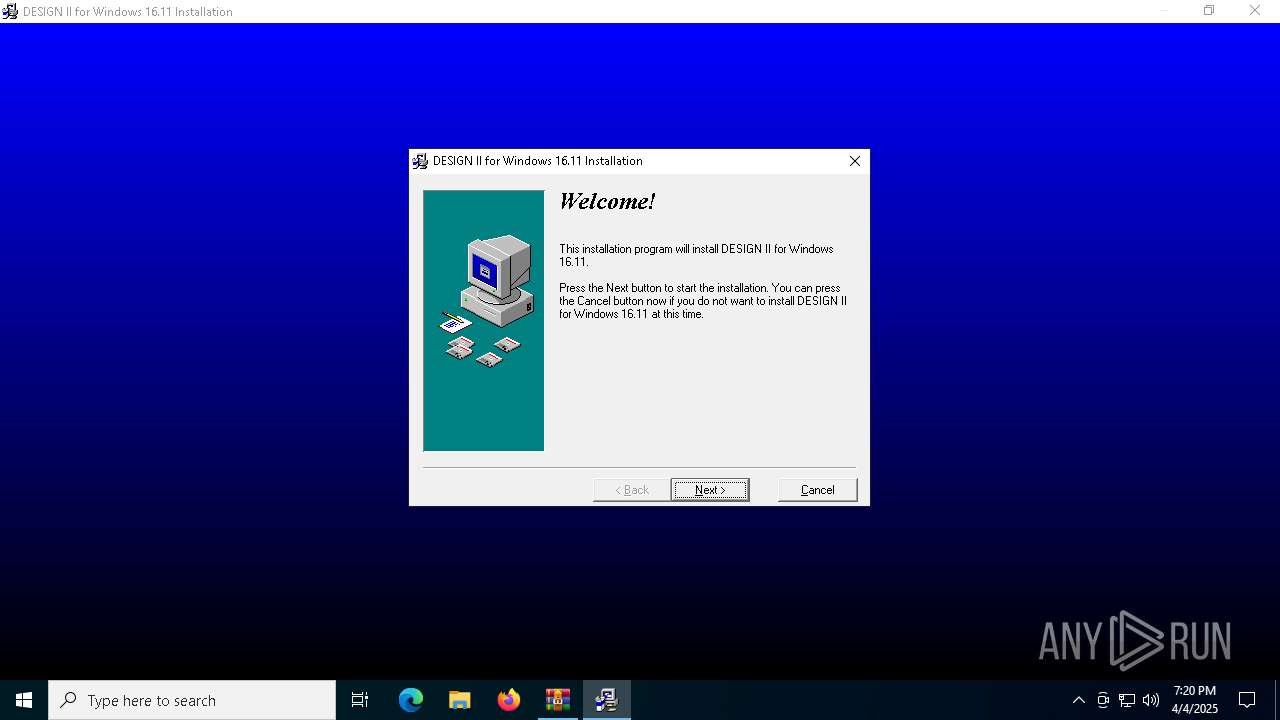
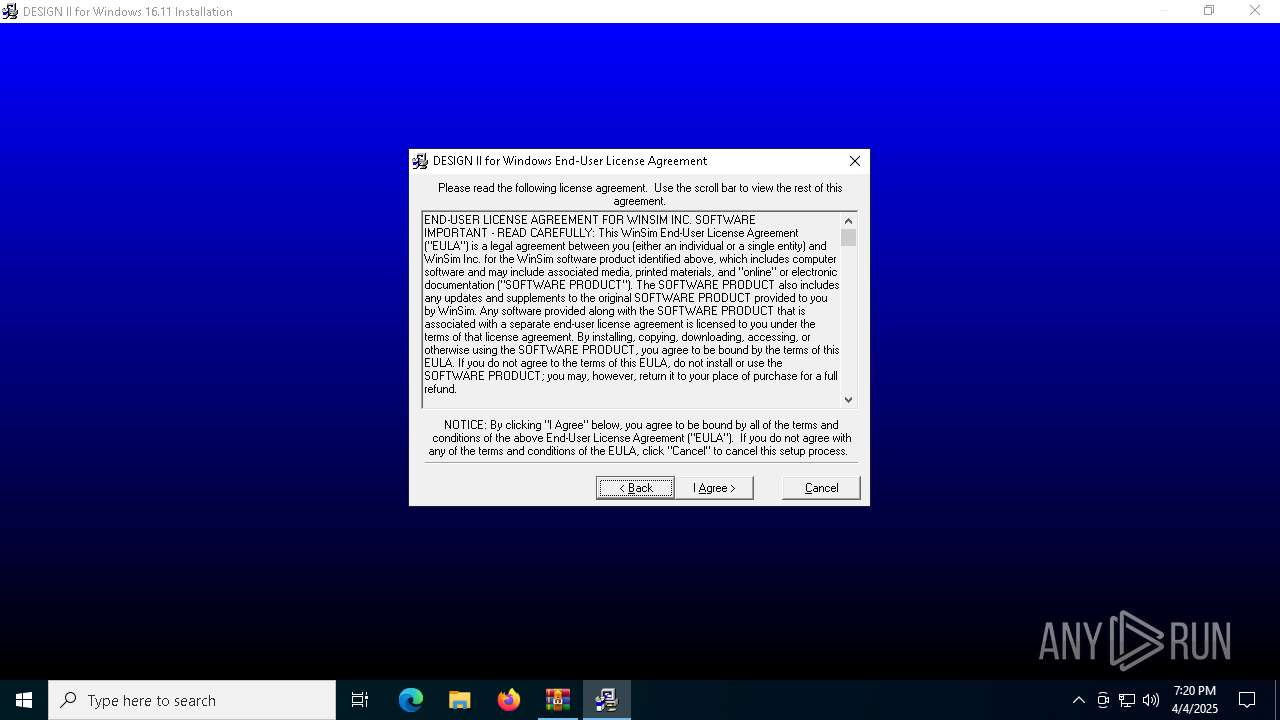
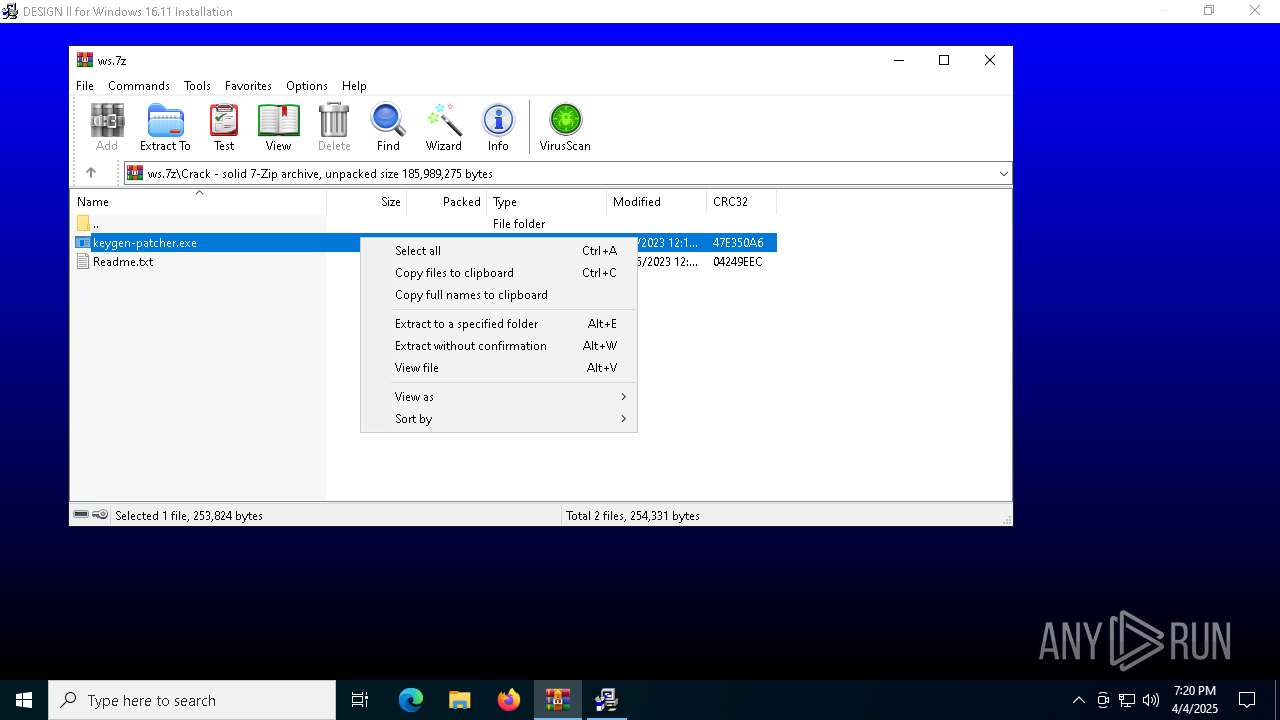
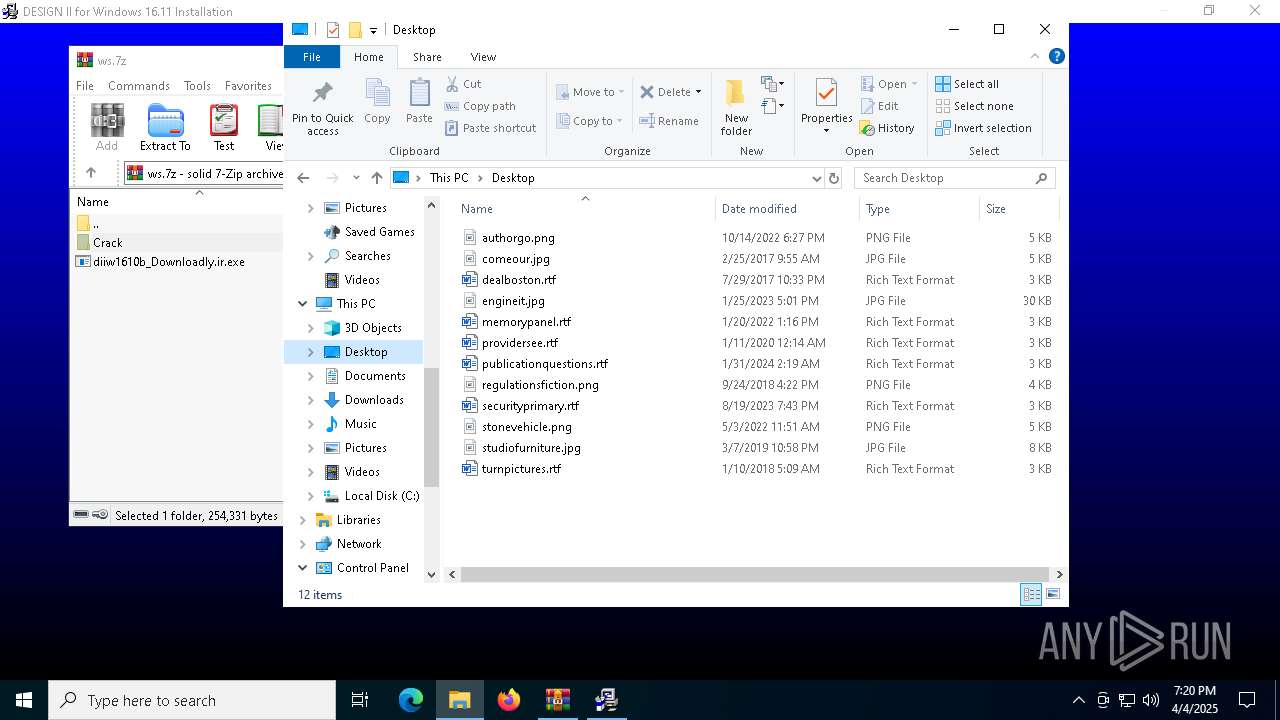
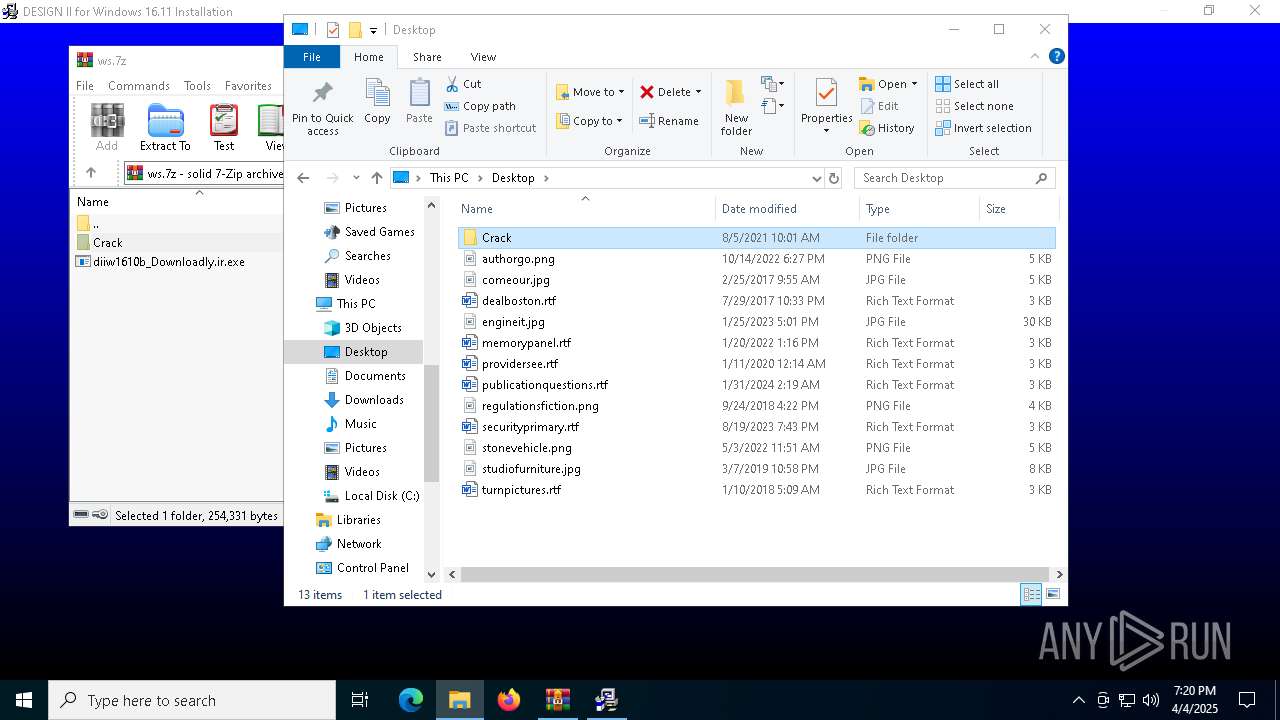
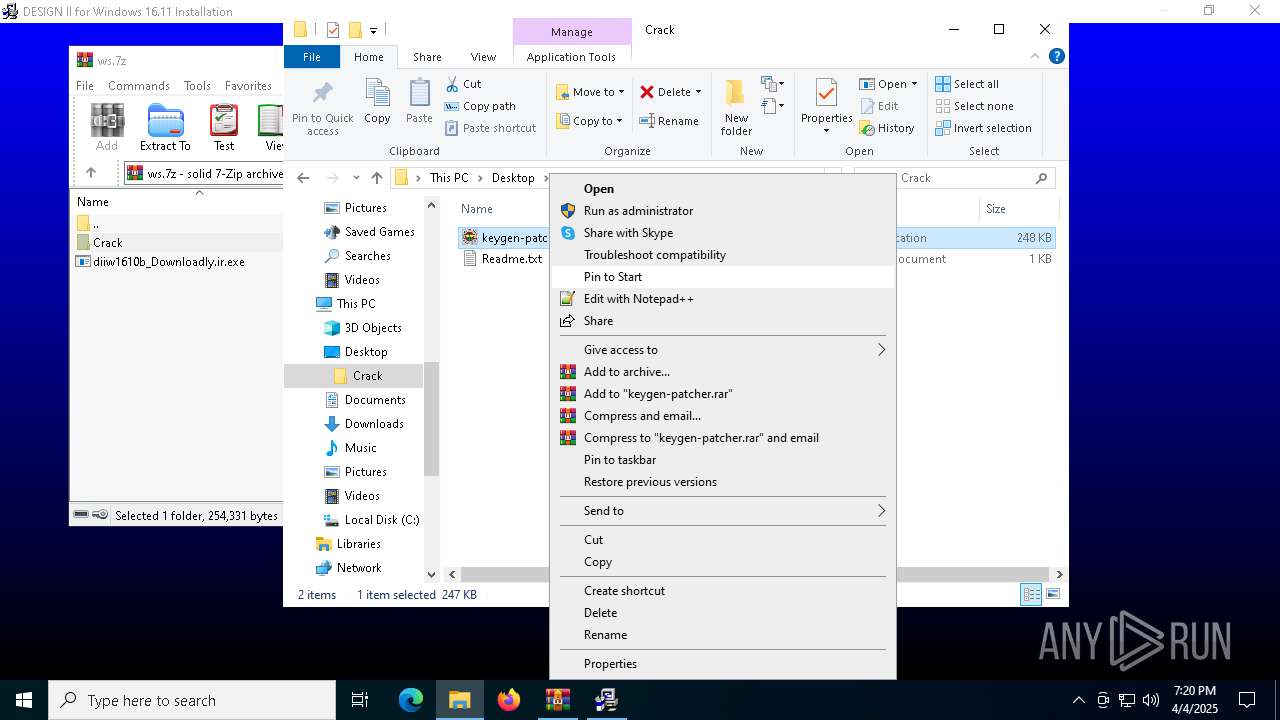
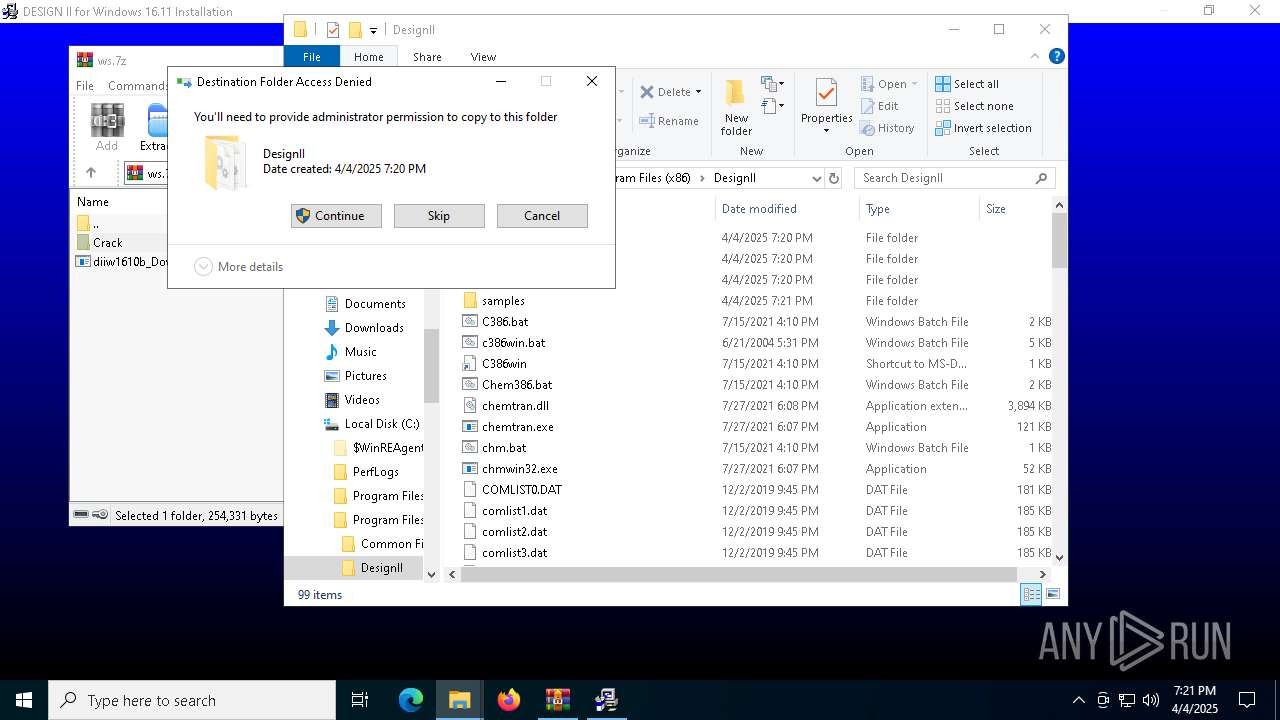
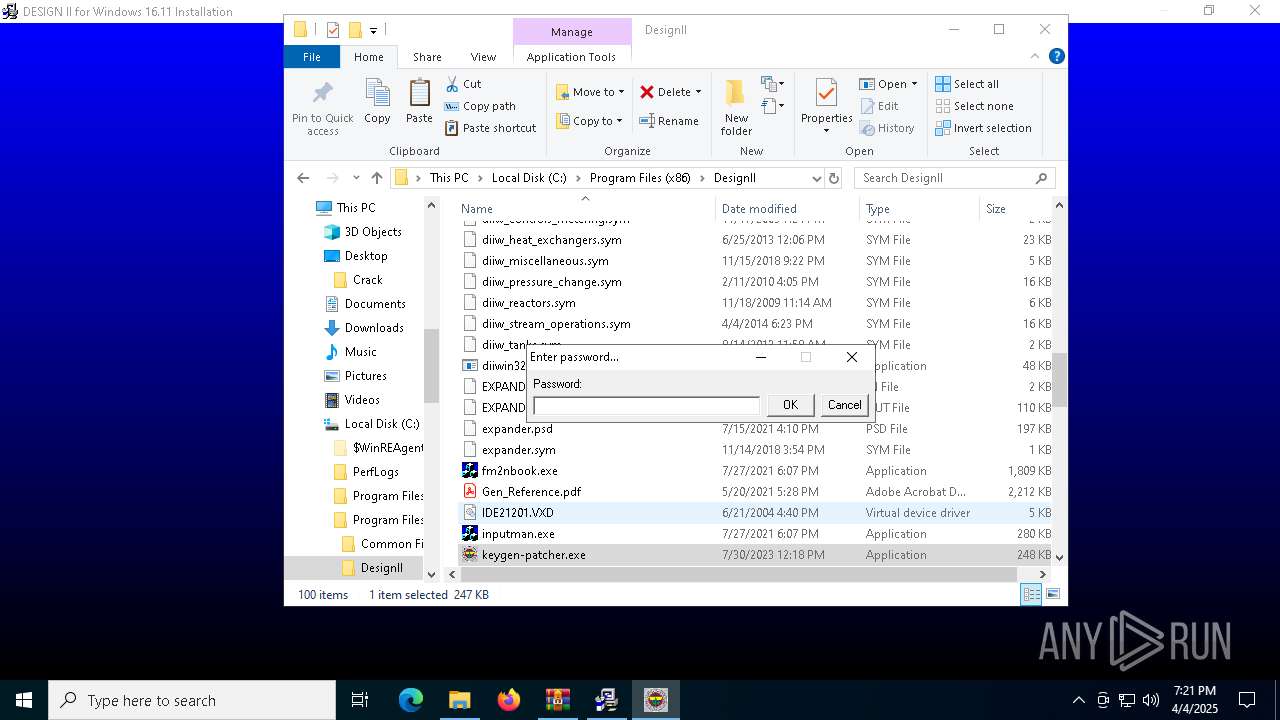
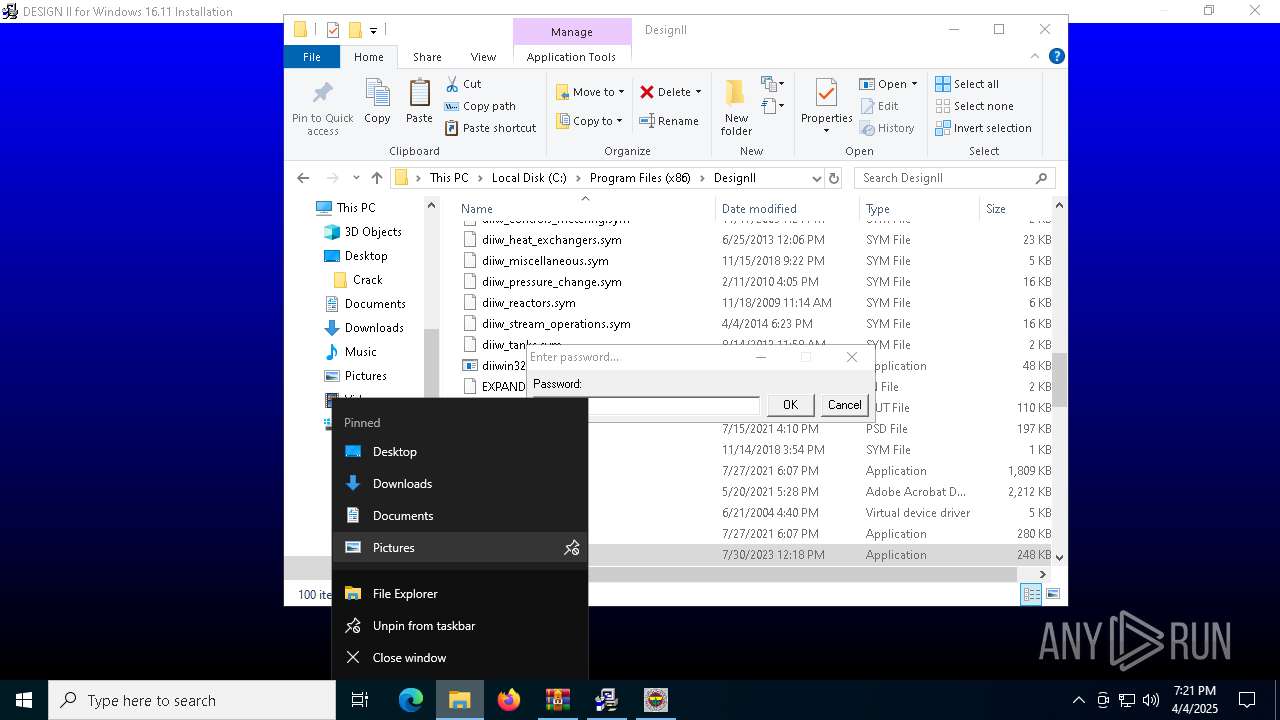
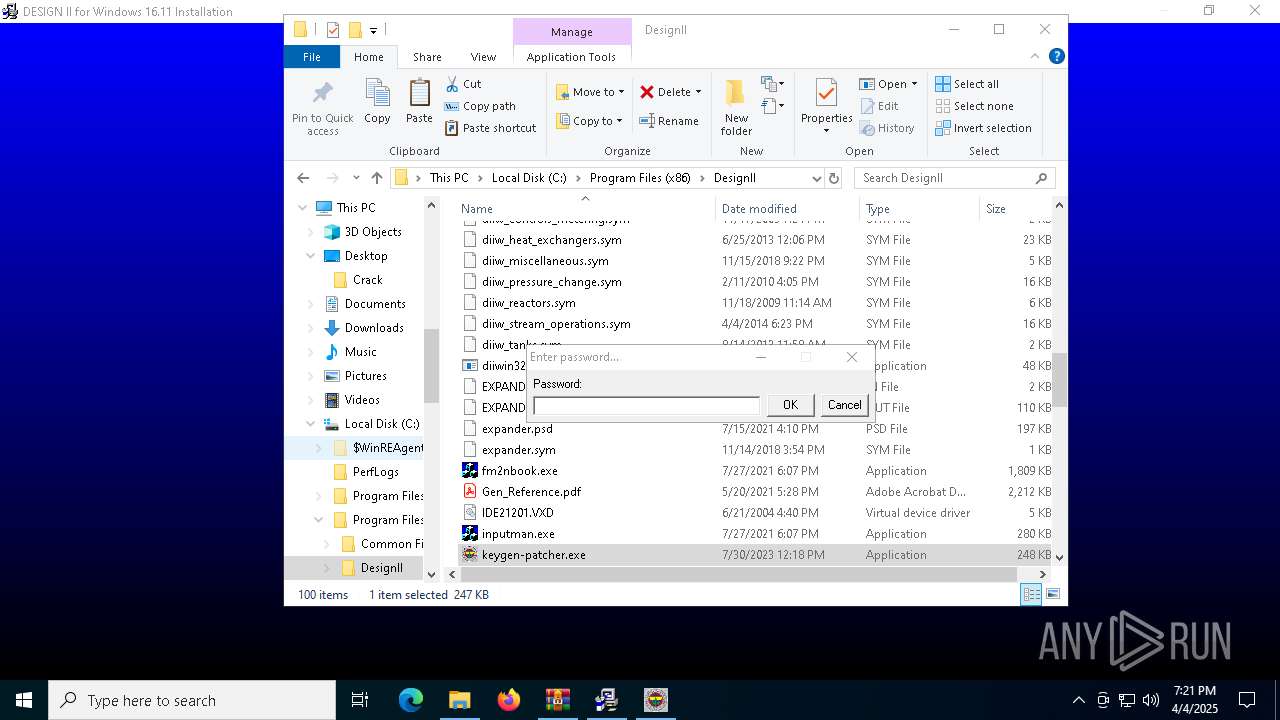
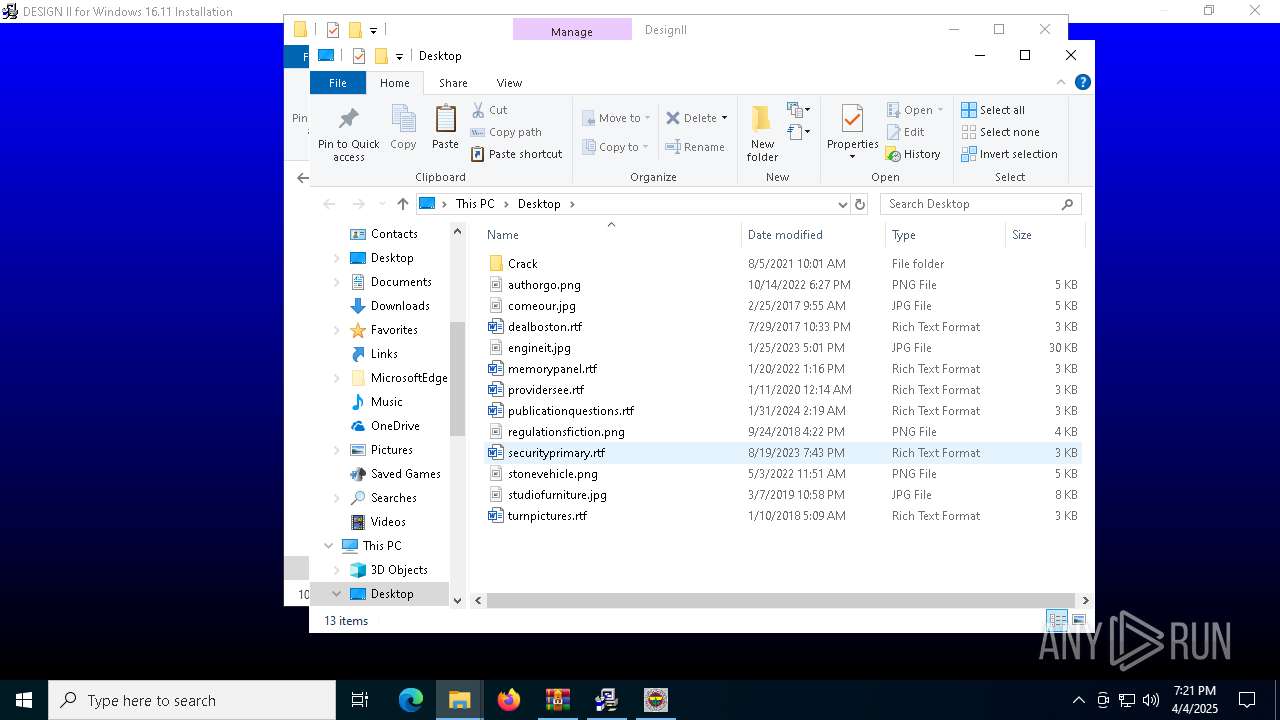
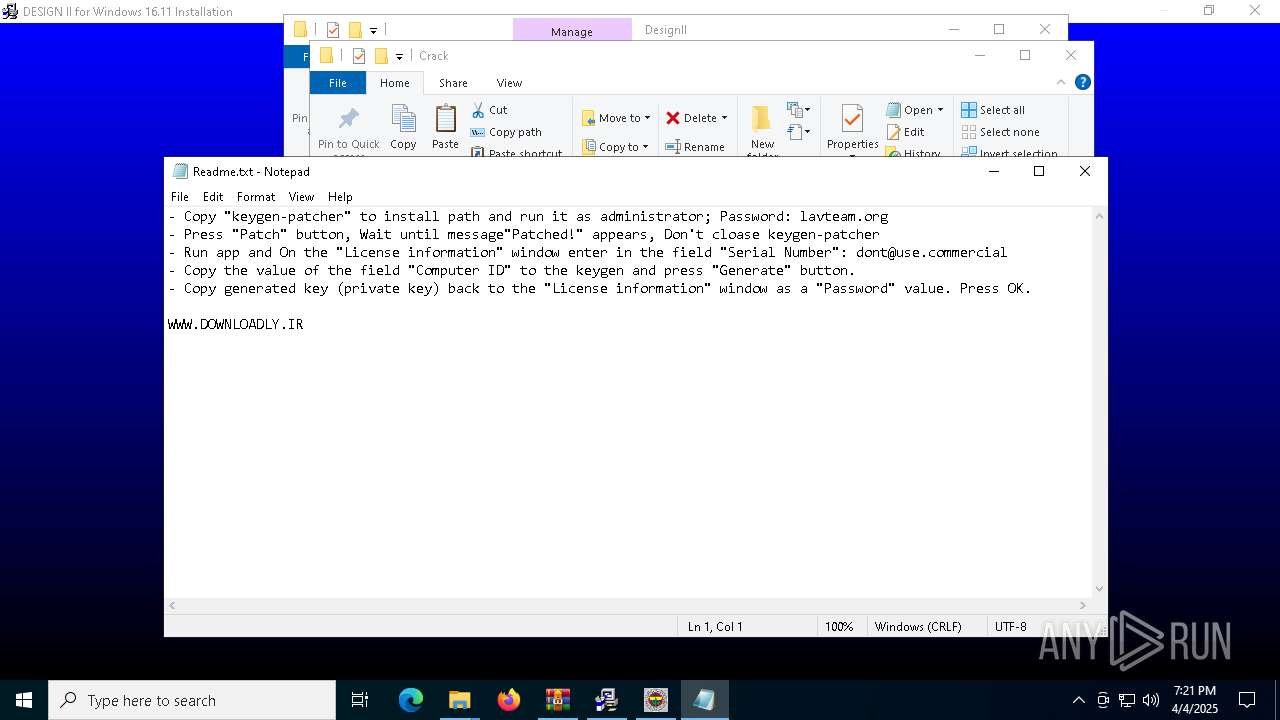
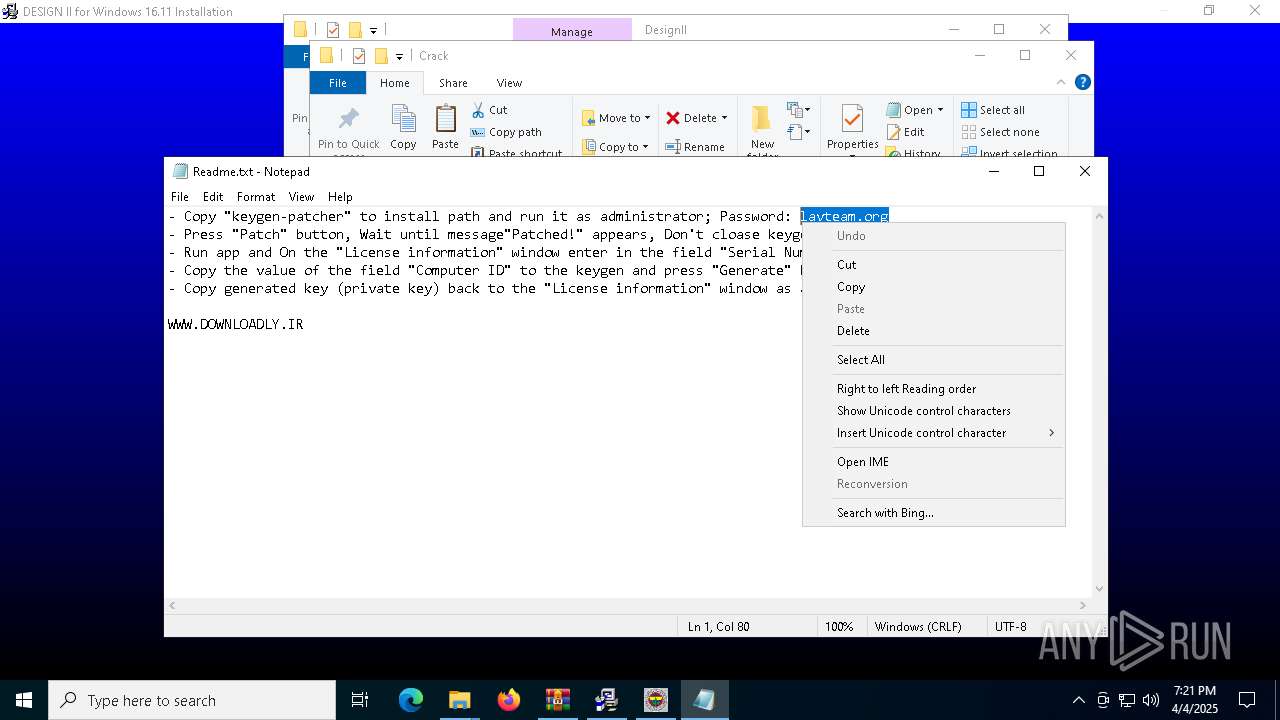
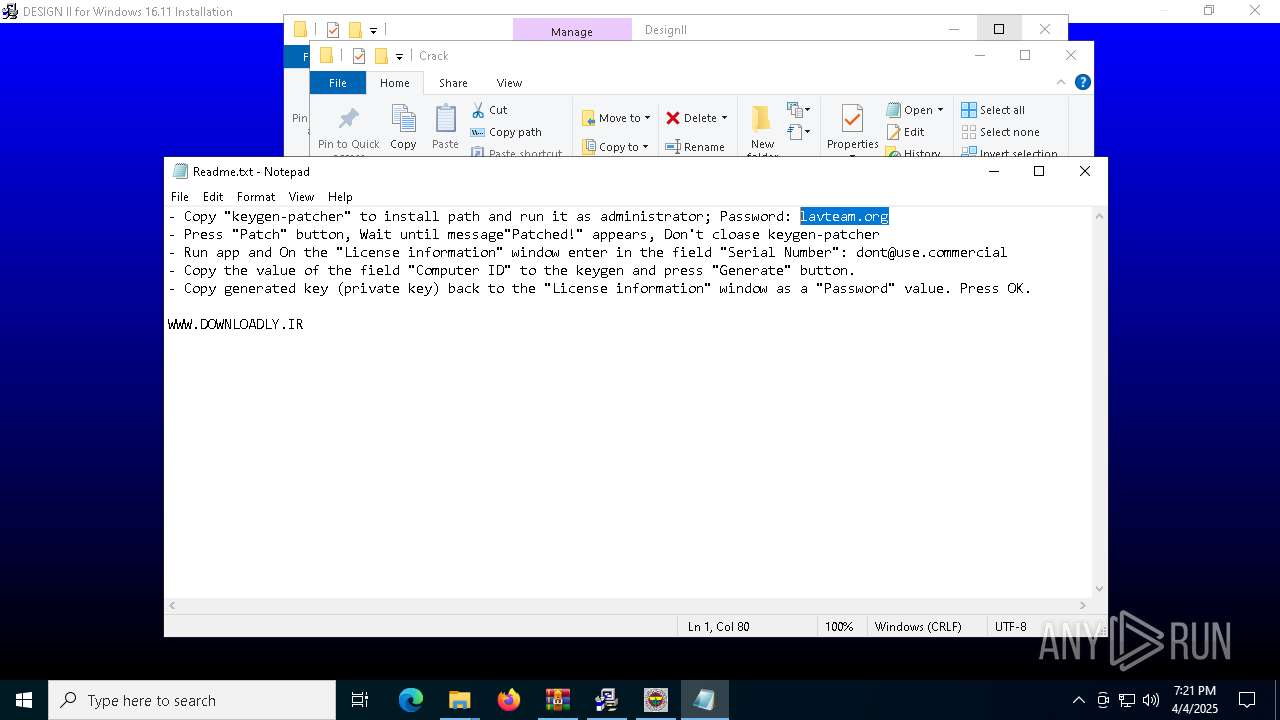
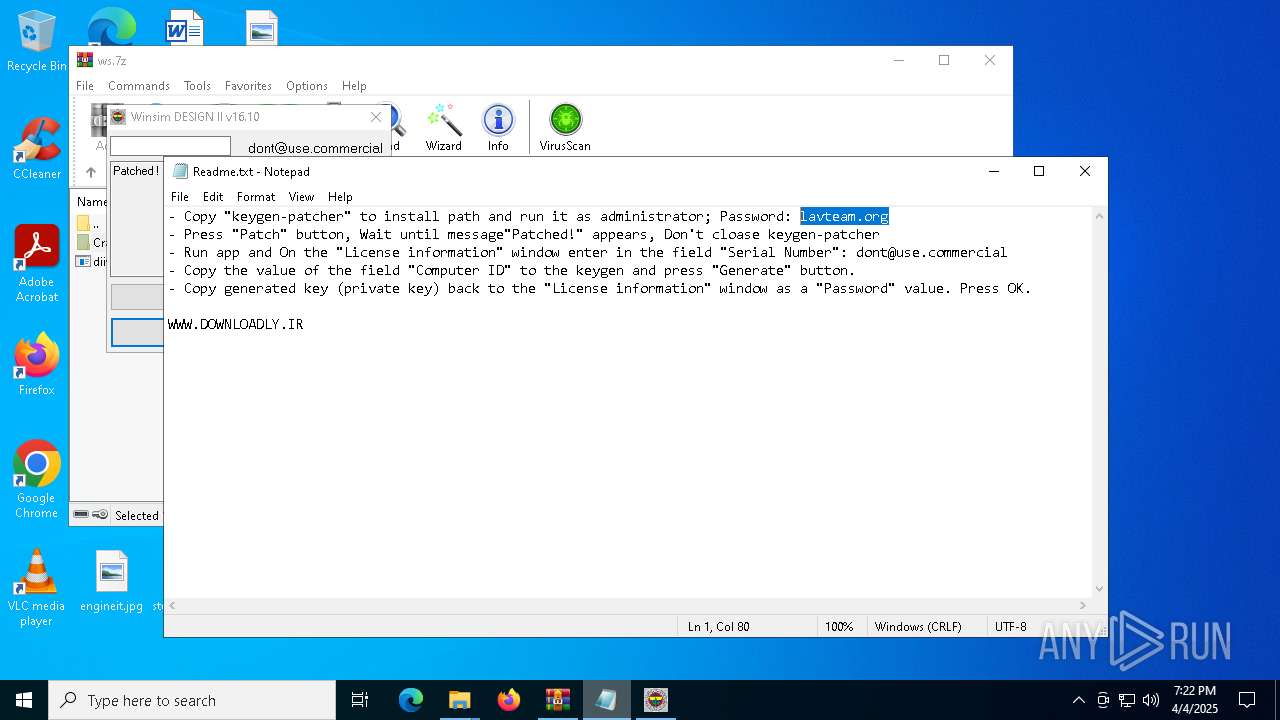
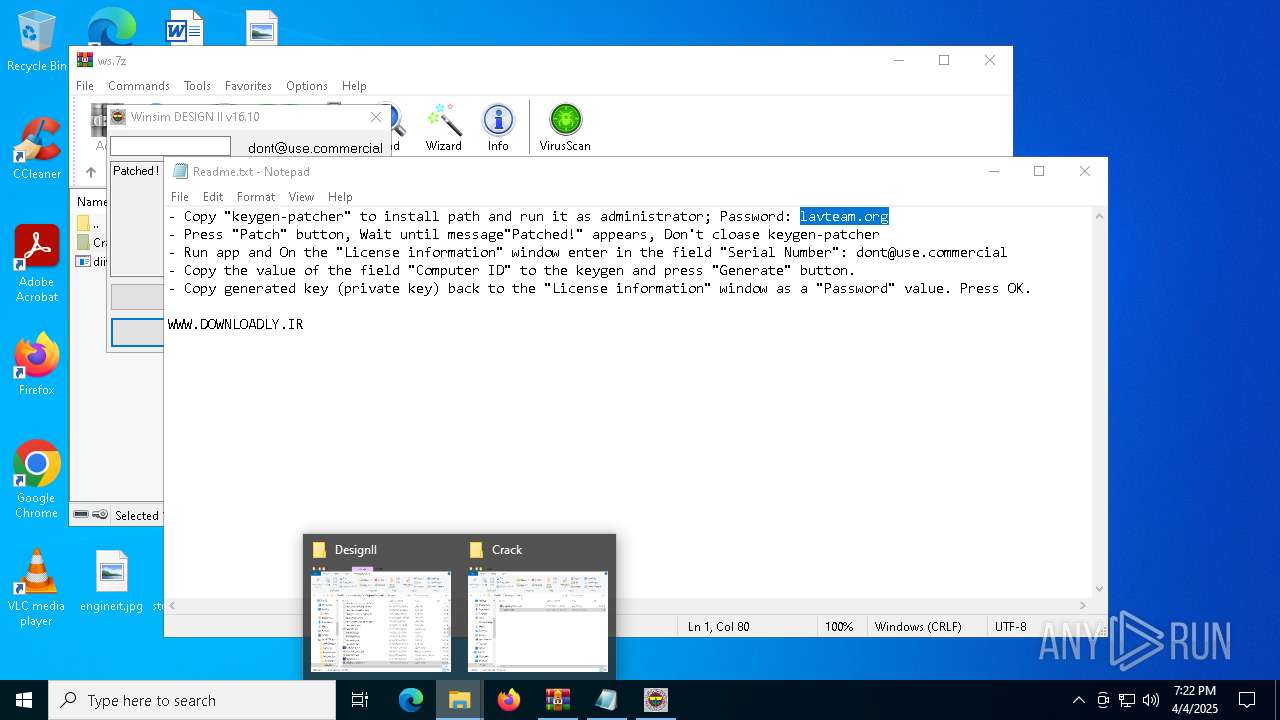
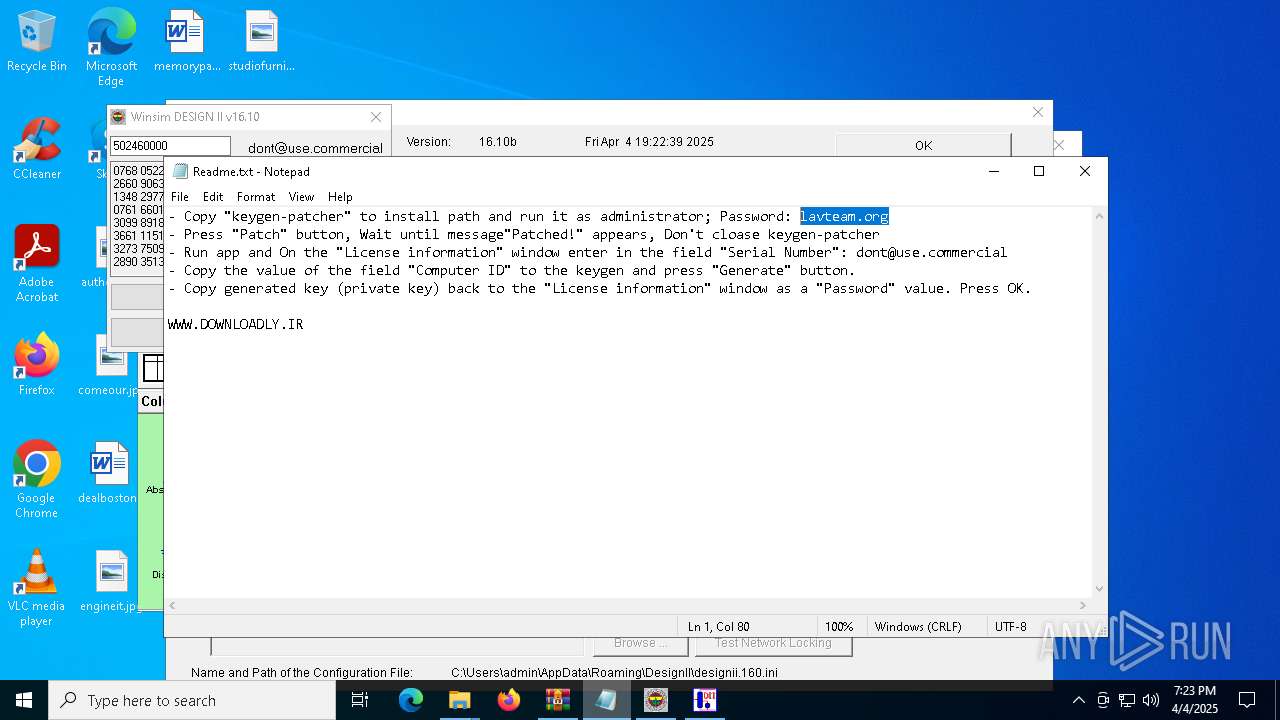
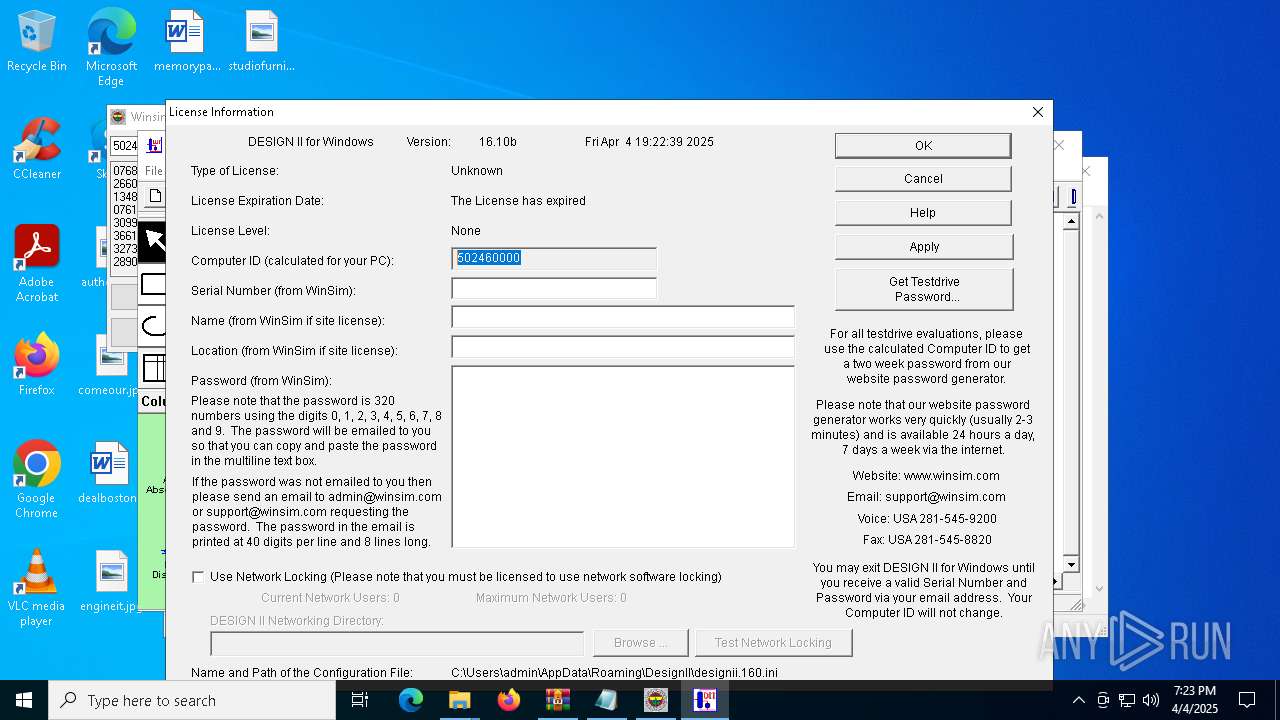
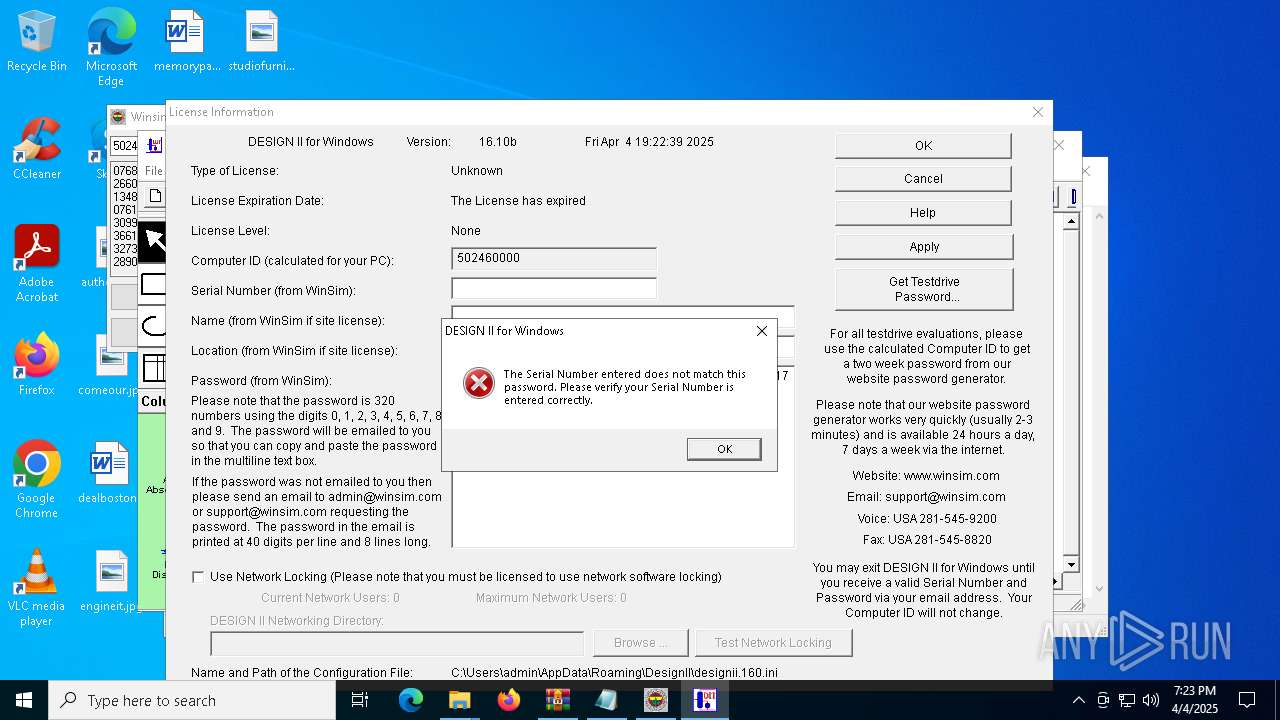
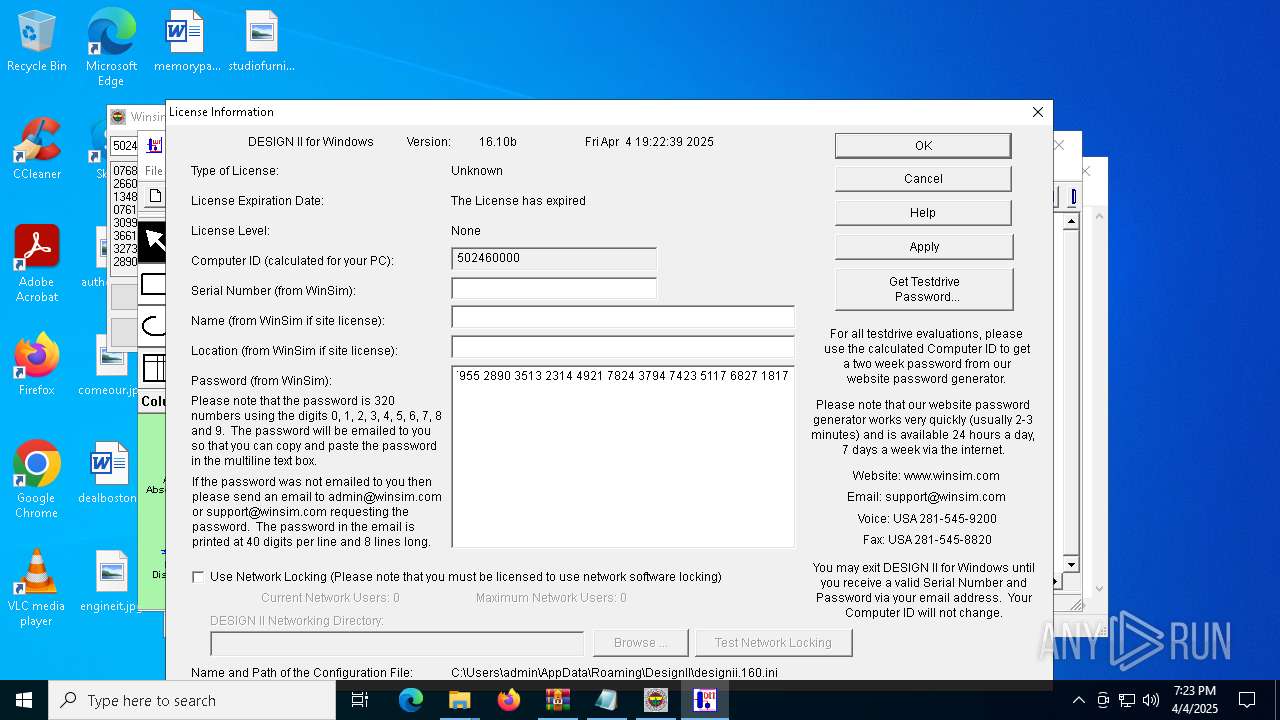
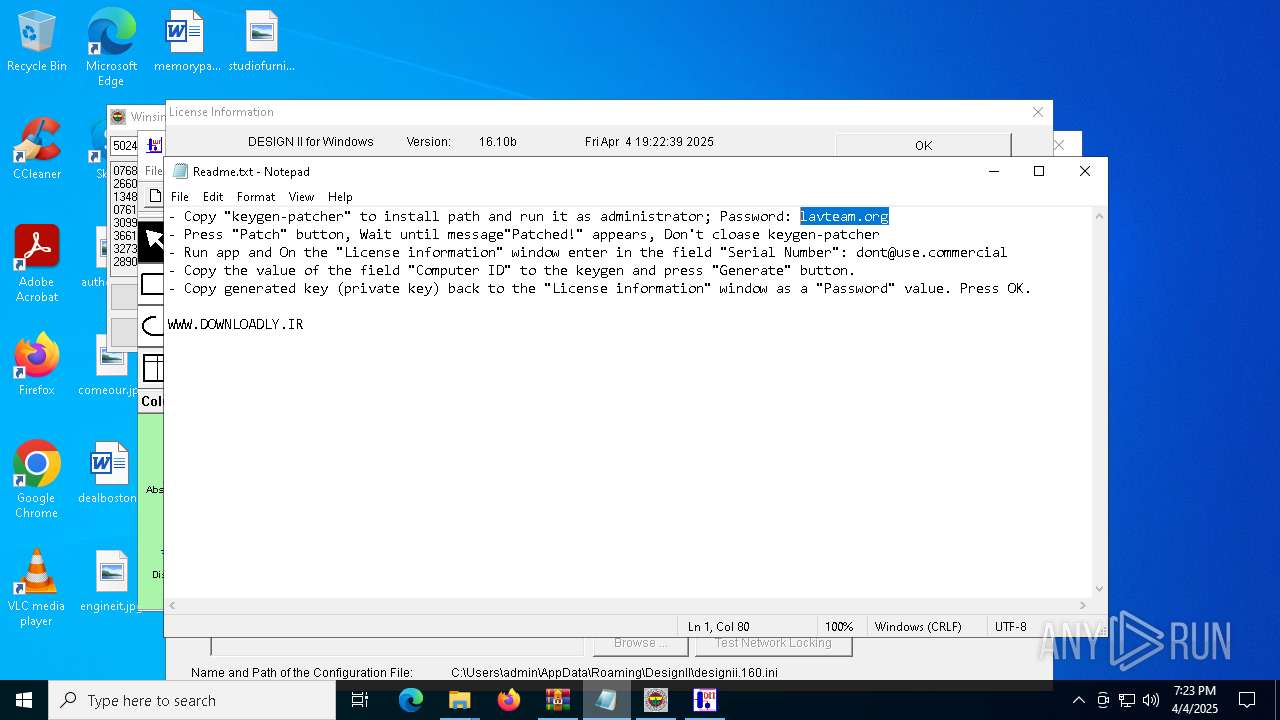
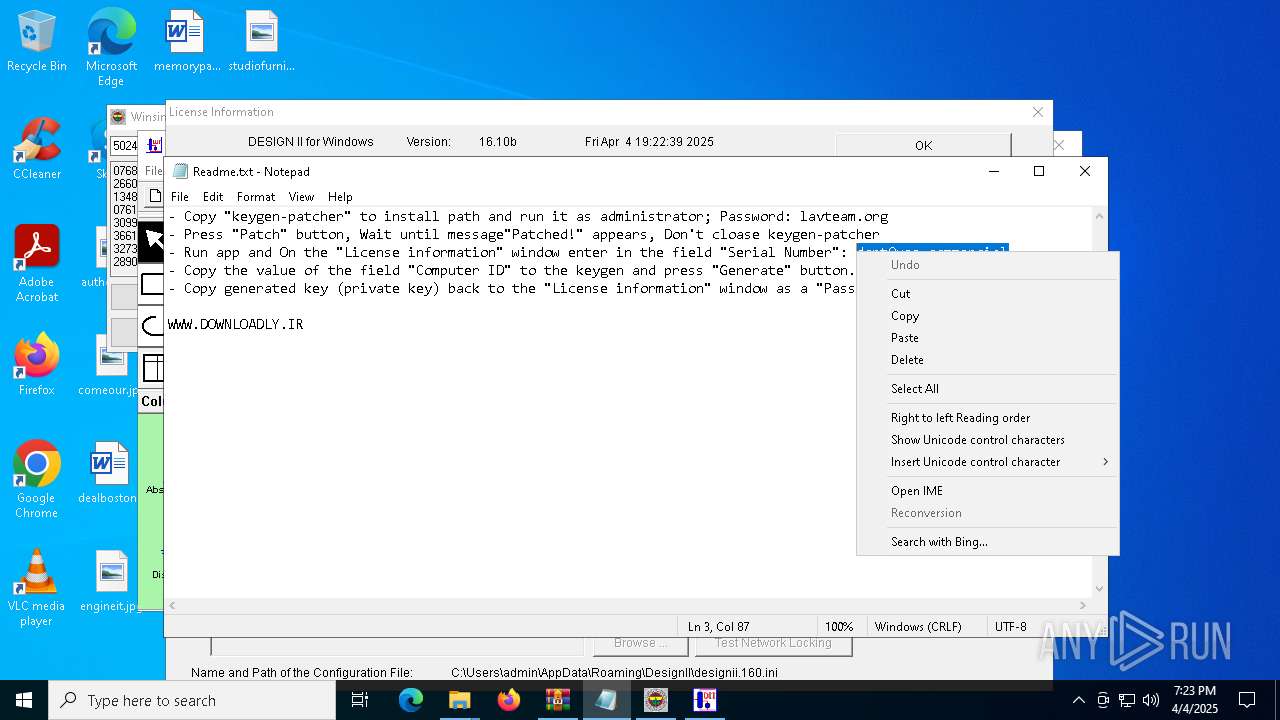
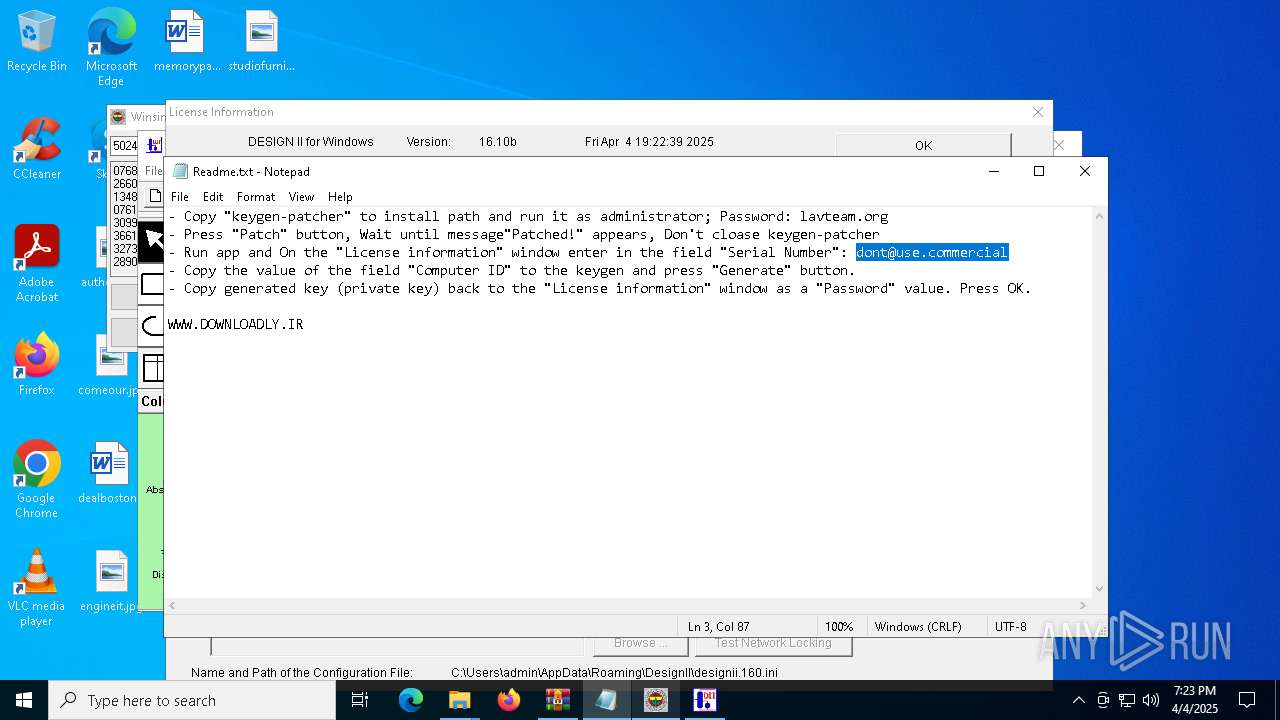
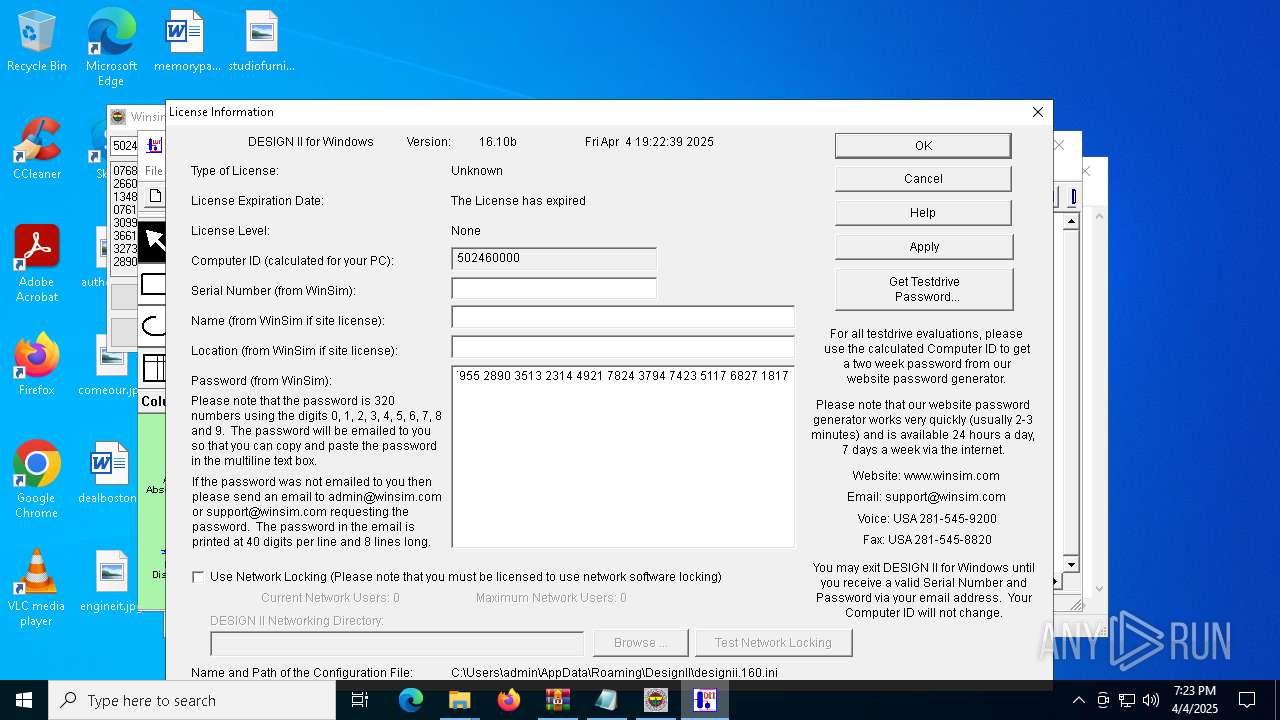
Manual execution by a user
- keygen-patcher.exe (PID: 6248)
- keygen-patcher.exe (PID: 7540)
- notepad.exe (PID: 7444)
- DESWIN.exe (PID: 7684)
Reads the machine GUID from the registry
- keygen-patcher.exe (PID: 6248)
Reads mouse settings
- GLJBB4F.tmp (PID: 4724)
Creates files or folders in the user directory
- GLBBAA2.tmp (PID: 7616)
- DESWIN.exe (PID: 7684)
Process checks computer location settings
- GLBBAA2.tmp (PID: 7616)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
240
Monitored processes
97
Malicious processes
6
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 240 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=4948 --field-trial-handle=2424,i,7811004206980992334,775177087345730412,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 720 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=29 --mojo-platform-channel-handle=6952 --field-trial-handle=2344,i,8073063577029059849,10806980097671999361,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 780 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6360 --field-trial-handle=2344,i,8073063577029059849,10806980097671999361,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 812 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5796 --field-trial-handle=2424,i,7811004206980992334,775177087345730412,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 904 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data" /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Crashpad" --annotation=IsOfficialBuild=1 --annotation=channel= --annotation=chromium-version=122.0.6261.70 "--annotation=exe=C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --annotation=plat=Win64 "--annotation=prod=Microsoft Edge" --annotation=ver=122.0.2365.59 --initial-client-data=0x290,0x294,0x298,0x288,0x2a0,0x7ffc88185fd8,0x7ffc88185fe4,0x7ffc88185ff0 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1040 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=2600 --field-trial-handle=2424,i,7811004206980992334,775177087345730412,262144 --variations-seed-version /prefetch:3 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | msedge.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1116 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5488 --field-trial-handle=2424,i,7811004206980992334,775177087345730412,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1168 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --no-startup-window | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | msedge.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1764 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1812 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6048 --field-trial-handle=2424,i,7811004206980992334,775177087345730412,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
Total events
19 299
Read events
18 890
Write events
337
Delete events
72
Modification events
| (PID) Process: | (5960) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (5960) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (5960) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (5960) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (5960) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: EE44490B8F902F00 | |||
| (PID) Process: | (5960) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 9AD8510B8F902F00 | |||
| (PID) Process: | (5960) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\459474 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {53360321-4836-4C6B-88C4-E3F990D6D828} | |||
| (PID) Process: | (2320) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2320) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2320) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
Executable files
209
Suspicious files
1 519
Text files
402
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5960 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF10b75b.TMP | — | |
MD5:— | SHA256:— | |||
| 5960 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF10b75b.TMP | — | |
MD5:— | SHA256:— | |||
| 5960 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5960 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5960 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF10b76b.TMP | — | |
MD5:— | SHA256:— | |||
| 5960 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF10b76b.TMP | — | |
MD5:— | SHA256:— | |||
| 5960 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5960 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5960 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF10b7a9.TMP | — | |
MD5:— | SHA256:— | |||
| 5960 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
53
TCP/UDP connections
64
DNS requests
75
Threats
17
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 2.19.126.147:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
2516 | SIHClient.exe | GET | 200 | 23.52.120.96:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 2.19.126.147:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
2516 | SIHClient.exe | GET | 200 | 23.52.120.96:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
5960 | svchost.exe | HEAD | 200 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/fb6dd03b-99d7-4cc8-a878-91c8e655c2d3?P1=1743956738&P2=404&P3=2&P4=P%2bYrxNEX7%2fiZ63Lhrh0bkiJmrgy5NyOwhgDzc6IVfP1lOUrbWiHuTktGy1x9JwWhjAnvsfKdv8ykiILlLyy6XA%3d%3d | unknown | — | — | whitelisted |
5960 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/fb6dd03b-99d7-4cc8-a878-91c8e655c2d3?P1=1743956738&P2=404&P3=2&P4=P%2bYrxNEX7%2fiZ63Lhrh0bkiJmrgy5NyOwhgDzc6IVfP1lOUrbWiHuTktGy1x9JwWhjAnvsfKdv8ykiILlLyy6XA%3d%3d | unknown | — | — | whitelisted |
5960 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/fb6dd03b-99d7-4cc8-a878-91c8e655c2d3?P1=1743956738&P2=404&P3=2&P4=P%2bYrxNEX7%2fiZ63Lhrh0bkiJmrgy5NyOwhgDzc6IVfP1lOUrbWiHuTktGy1x9JwWhjAnvsfKdv8ykiILlLyy6XA%3d%3d | unknown | — | — | whitelisted |
5960 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/68591036-2289-4858-9f7f-9149e89c8a08?P1=1743956739&P2=404&P3=2&P4=BcJ%2buC6YUsgM1DJSndNpr%2fl7LAAX4ULnUAyTJ8Q9vJfSyMQE3XtFEuz3l8QX6A%2b%2bQ9M%2fGVhZ5S4Y6neQel7g3g%3d%3d | unknown | — | — | whitelisted |
5960 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/68591036-2289-4858-9f7f-9149e89c8a08?P1=1743956739&P2=404&P3=2&P4=BcJ%2buC6YUsgM1DJSndNpr%2fl7LAAX4ULnUAyTJ8Q9vJfSyMQE3XtFEuz3l8QX6A%2b%2bQ9M%2fGVhZ5S4Y6neQel7g3g%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 2.19.126.147:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5496 | MoUsoCoreWorker.exe | 2.19.126.147:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5960 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
7300 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7300 | msedge.exe | 88.99.137.18:443 | filebin.net | Hetzner Online GmbH | DE | suspicious |
7300 | msedge.exe | 150.171.28.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7300 | msedge.exe | 13.107.6.158:443 | business.bing.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
filebin.net |
| unknown |
config.edge.skype.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
business.bing.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
bzib.nelreports.net |
| whitelisted |
client.wns.windows.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2196 | svchost.exe | Misc activity | ET FILE_SHARING Observed DNS Query to Abused File Sharing Domain in DNS Lookup (filebin .net) |
7300 | msedge.exe | Misc activity | ET FILE_SHARING Observed DNS Query to Abused File Sharing Domain in DNS Lookup (filebin .net) |
7300 | msedge.exe | Misc activity | ET FILE_SHARING Observed DNS Query to Abused File Sharing Domain in DNS Lookup (filebin .net) |
7300 | msedge.exe | Misc activity | ET INFO Observed Abused File Sharing Domain in TLS SNI (filebin .net) |
7300 | msedge.exe | Misc activity | ET INFO Observed Abused File Sharing Domain in TLS SNI (filebin .net) |
7300 | msedge.exe | Misc activity | ET INFO Observed Abused File Sharing Domain in TLS SNI (filebin .net) |
7300 | msedge.exe | Misc activity | ET INFO Observed Abused File Sharing Domain in TLS SNI (filebin .net) |
7300 | msedge.exe | Misc activity | ET FILE_SHARING Observed DNS Query to Abused File Sharing Domain in DNS Lookup (filebin .net) |
7300 | msedge.exe | Misc activity | ET INFO Observed Abused File Sharing Domain in TLS SNI (filebin .net) |
7300 | msedge.exe | Misc activity | ET FILE_SHARING Observed DNS Query to Abused File Sharing Domain in DNS Lookup (filebin .net) |