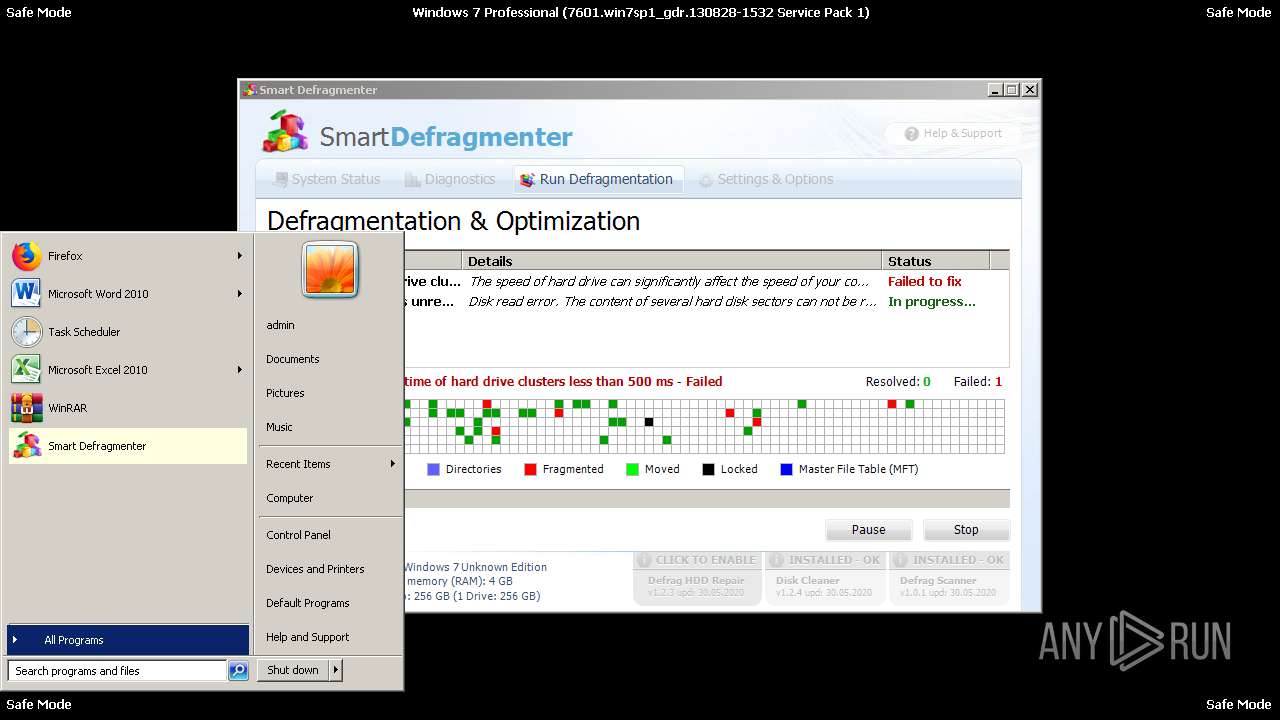
| File name: | Endermanch@SmartDefragmenter.exe |
| Full analysis: | https://app.any.run/tasks/acf89086-5b4c-4b1a-b3a6-cba94d198254 |
| Verdict: | Malicious activity |
| Analysis date: | May 30, 2020, 14:41:59 |
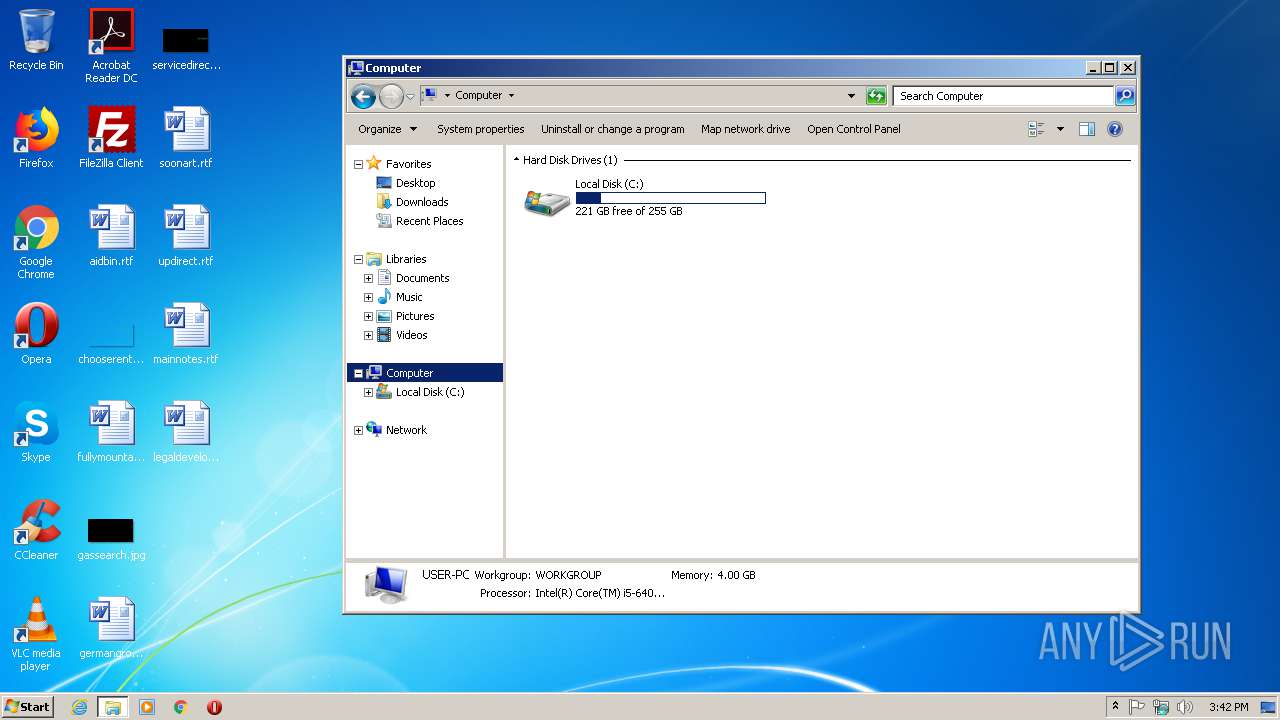
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 03BAEBA6B4224371CCA7FA6F95AE61C0 |
| SHA1: | 8731202D2F954421A37B5C9E01D971131BD515F1 |
| SHA256: | 61A9E3278B6BCC29A2A0405B06FB2A3BBCB1751C3DD564A8F94CC89EA957EC35 |
| SSDEEP: | 6144:hBGrTx2fgEViq+JoQ9tpecSXFADhKXPEKJRlETLV+PwoVUqwhlKq6yem8lhg:6rLEyptwnX+gXrRlESwKKhlP6yxGh |
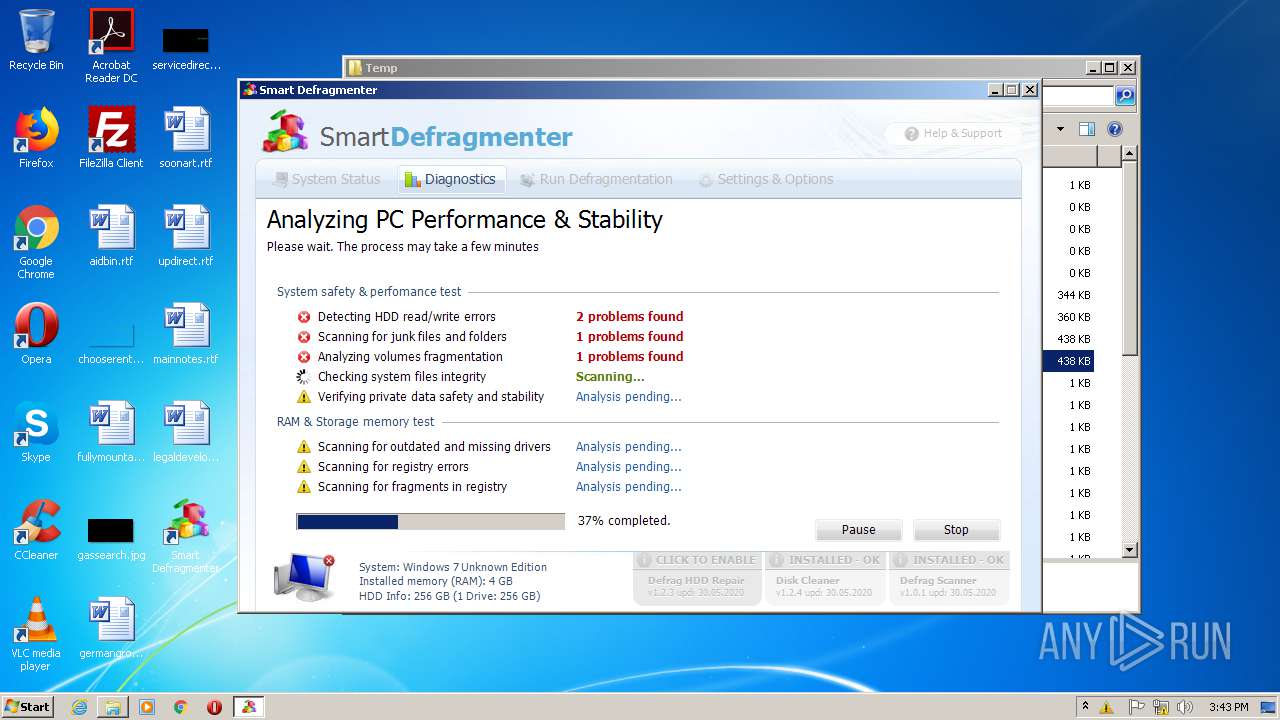
MALICIOUS
Changes the autorun value in the registry
- Endermanch@SmartDefragmenter.exe (PID: 636)
- 683953.exe (PID: 3308)
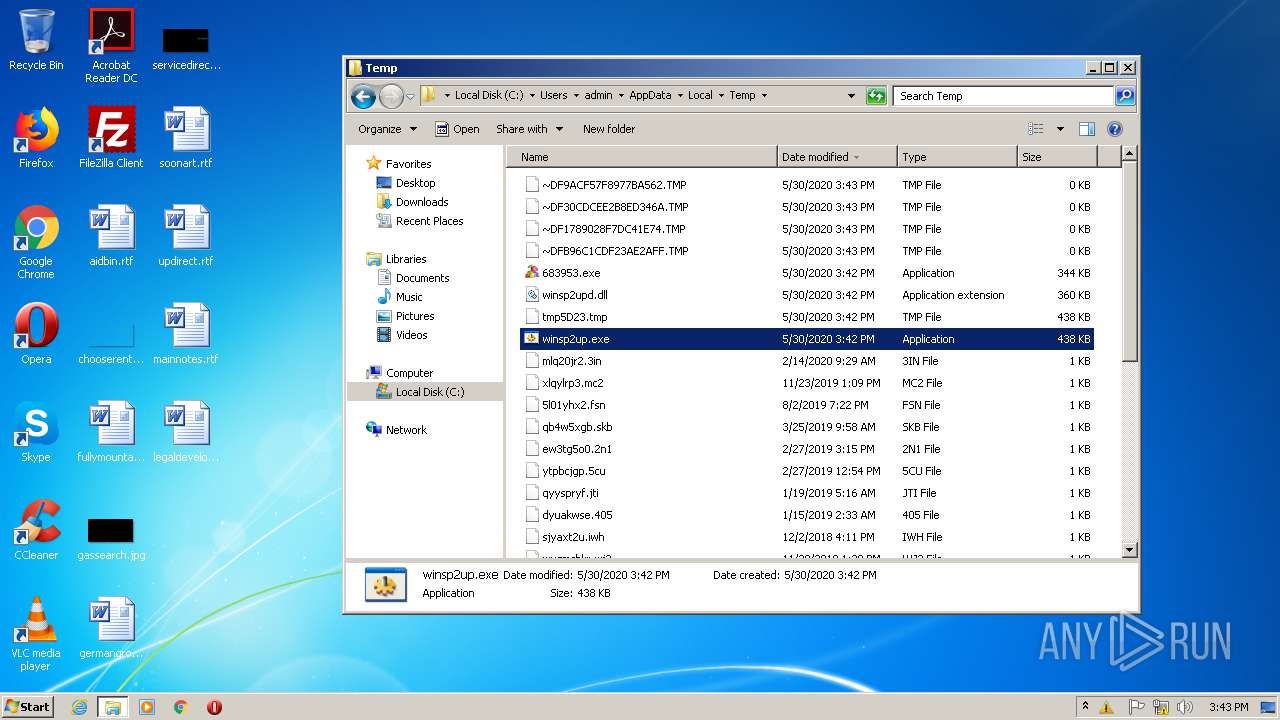
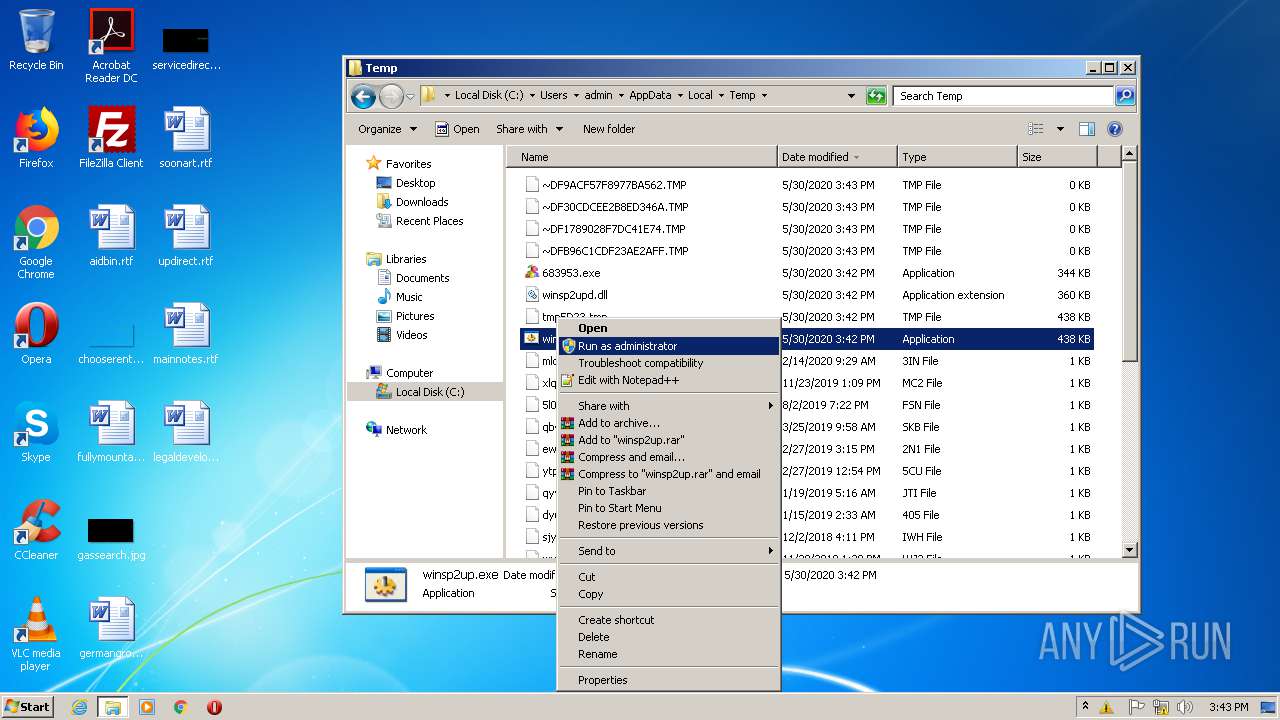
Loads dropped or rewritten executable
- explorer.exe (PID: 1884)
Runs injected code in another process
- winsp2up.exe (PID: 3972)
Application was injected by another process
- explorer.exe (PID: 1884)
Actions looks like stealing of personal data
- explorer.exe (PID: 1884)
Application was dropped or rewritten from another process
- 683953.exe (PID: 3308)
Changes internet zones settings
- 683953.exe (PID: 3308)
SUSPICIOUS
Starts itself from another location
- Endermanch@SmartDefragmenter.exe (PID: 636)
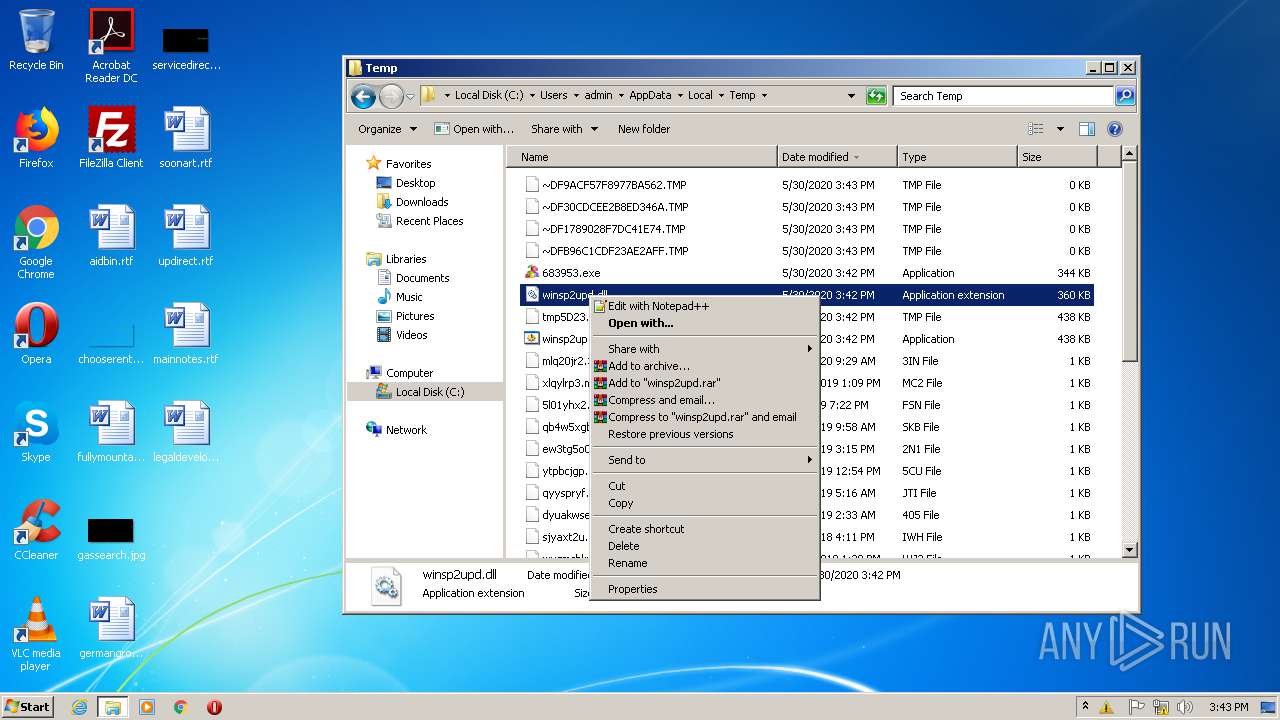
Executable content was dropped or overwritten
- Endermanch@SmartDefragmenter.exe (PID: 636)
- winsp2up.exe (PID: 3972)
- explorer.exe (PID: 1884)
Reads Internet Cache Settings
- explorer.exe (PID: 1884)
- 683953.exe (PID: 3308)
Application launched itself
- explorer.exe (PID: 1884)
Starts Internet Explorer
- explorer.exe (PID: 1884)
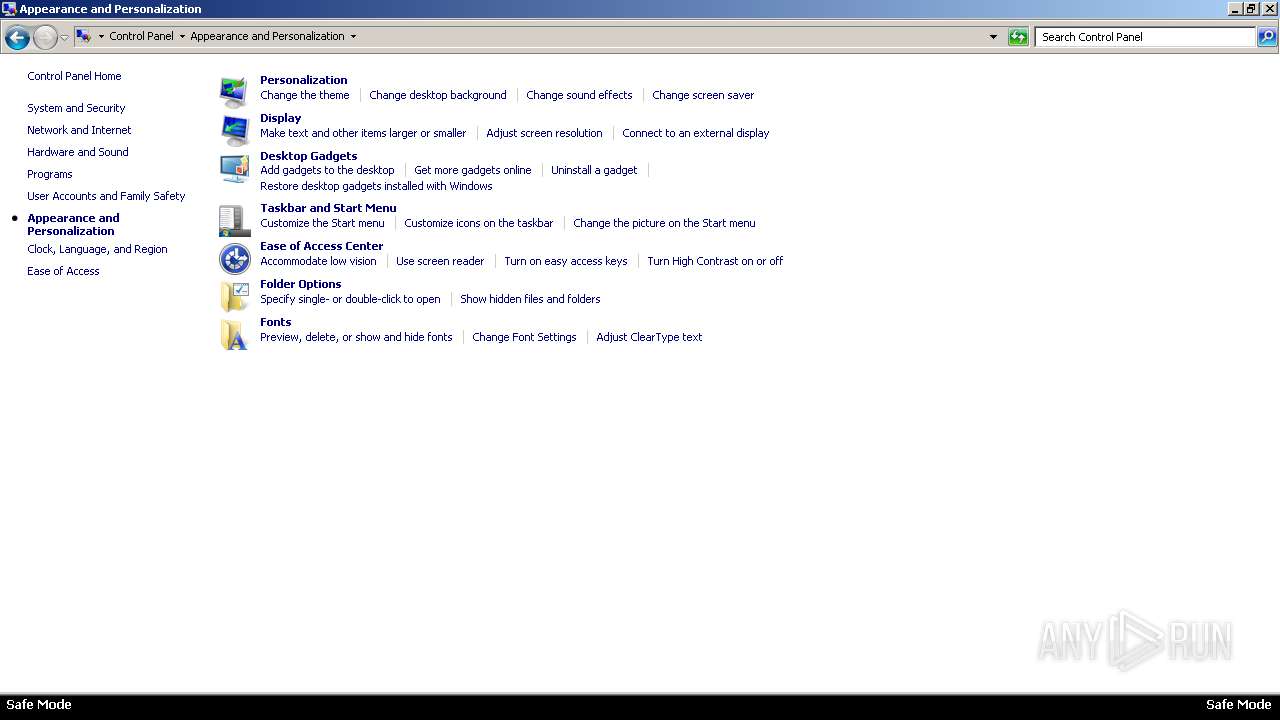
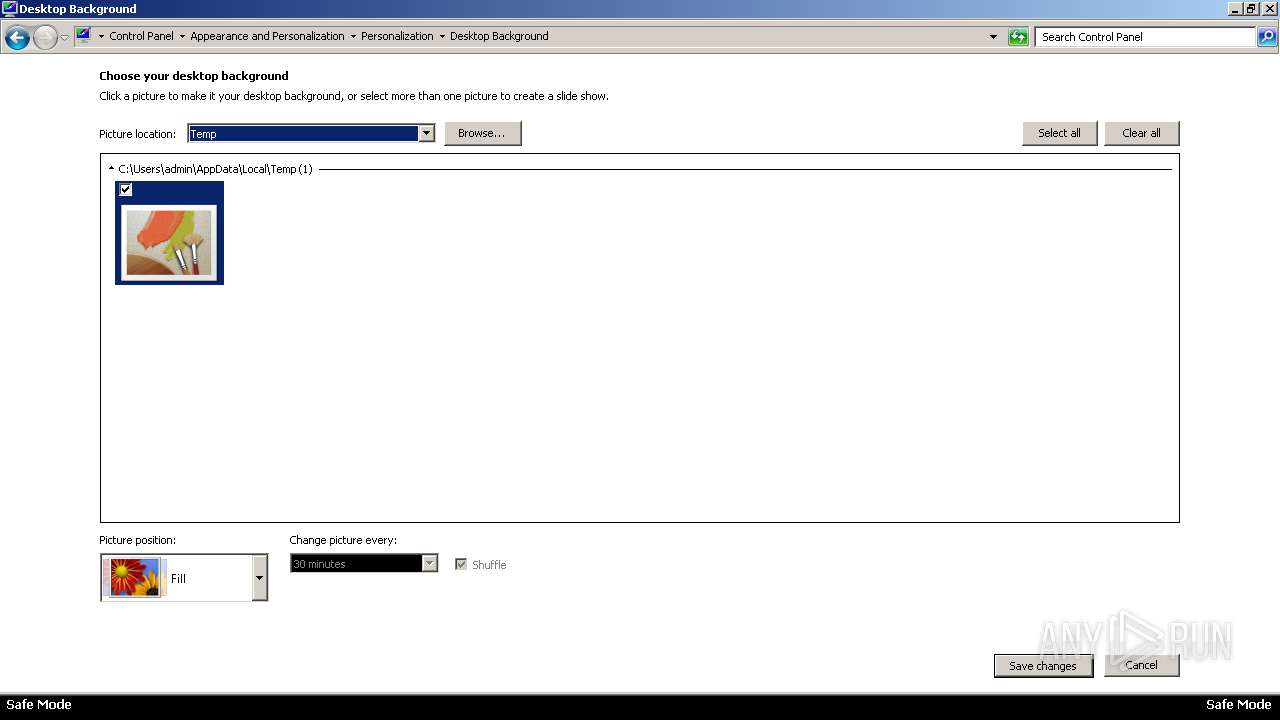
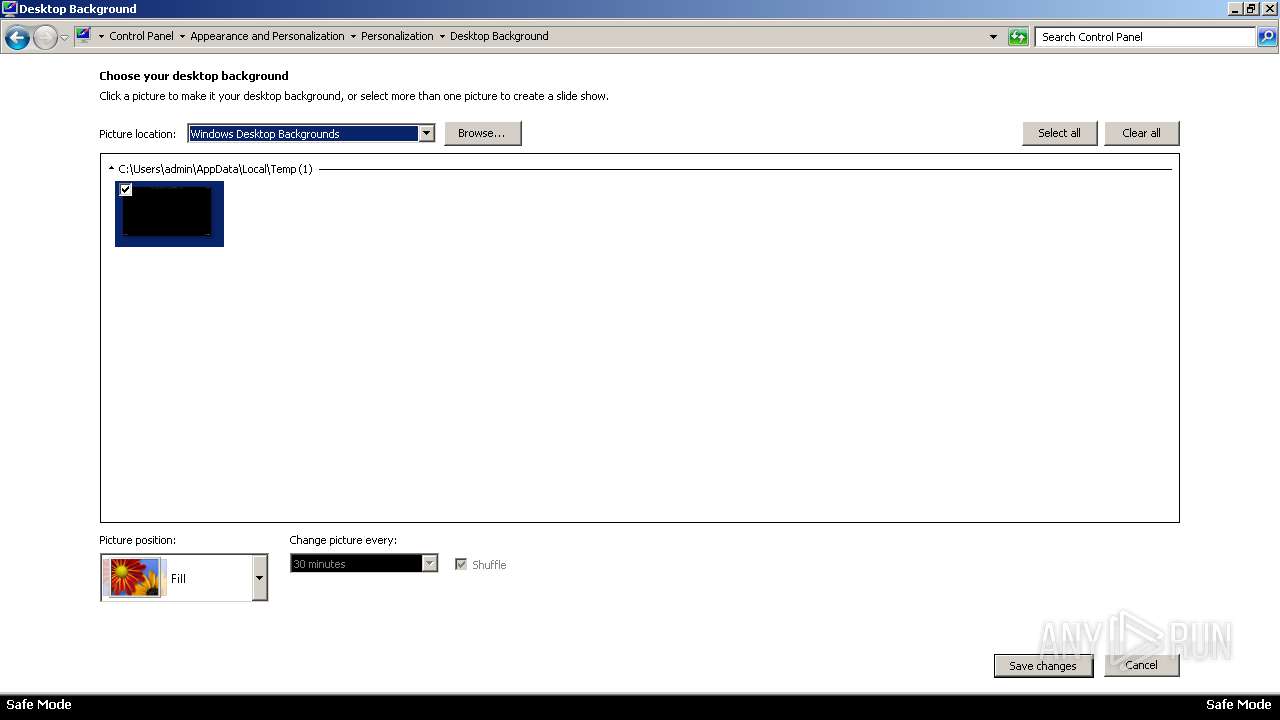
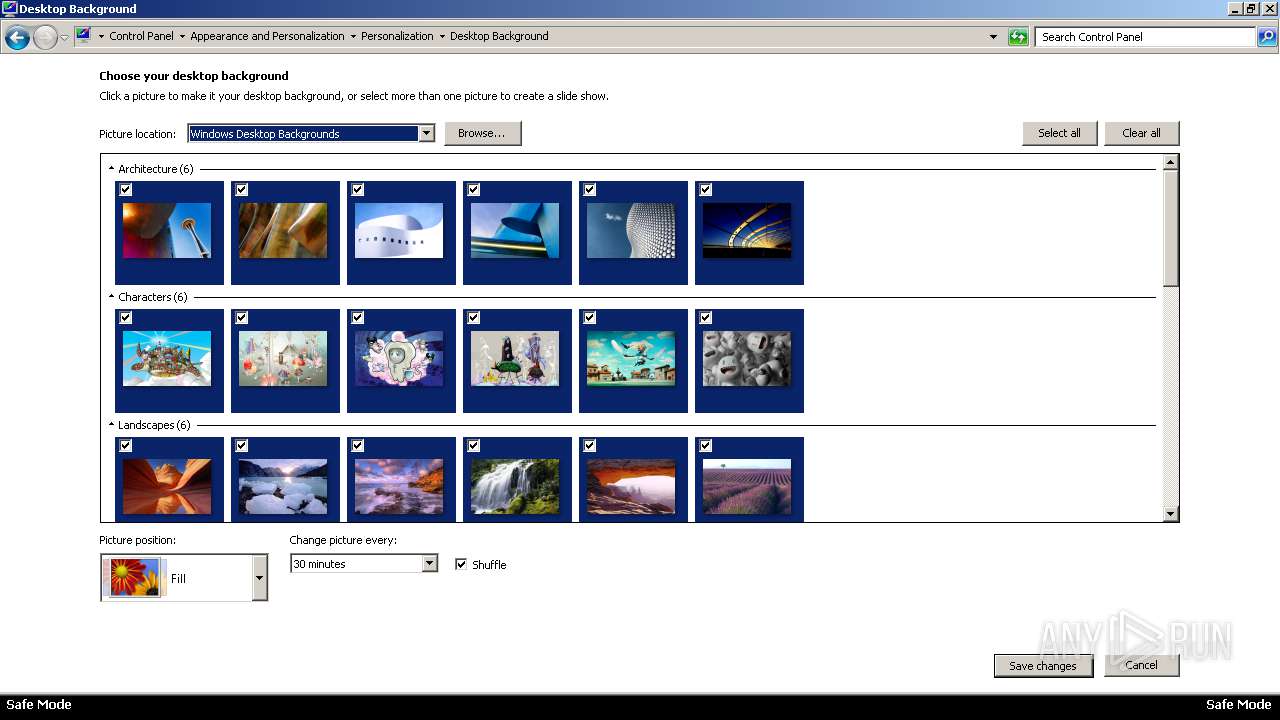
Changes the desktop background image
- 683953.exe (PID: 3308)
Creates files in the user directory
- explorer.exe (PID: 1884)
- 683953.exe (PID: 3308)
INFO
Reads Internet Cache Settings
- iexplore.exe (PID: 3272)
- iexplore.exe (PID: 3824)
Application launched itself
- iexplore.exe (PID: 3272)
Changes internet zones settings
- iexplore.exe (PID: 3272)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (61.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.6) |
| .exe | | | Win32 Executable (generic) (10) |
| .exe | | | Win16/32 Executable Delphi generic (4.6) |
| .exe | | | Generic Win/DOS Executable (4.4) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2007:11:10 17:33:02+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 6144 |
| InitializedDataSize: | 1354240 |
| UninitializedDataSize: | 917504 |
| EntryPoint: | 0xe90a7 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 10-Nov-2007 16:33:02 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 4 |
| Time date stamp: | 10-Nov-2007 16:33:02 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.rsrc | 0x00001000 | 0x00007572 | 0x00007600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.99786 |
.data | 0x00009000 | 0x000E0000 | 0x00001200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.38948 |
.text | 0x000E9000 | 0x00001759 | 0x00001800 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.31474 |
.rdata | 0x000EB000 | 0x0006322A | 0x00063400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.70284 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.8861 | 699 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 3.59975 | 296 | UNKNOWN | English - United States | RT_ICON |
3 | 5.98727 | 3752 | UNKNOWN | English - United States | RT_ICON |
4 | 6.53228 | 2216 | UNKNOWN | English - United States | RT_ICON |
5 | 4.53632 | 1384 | UNKNOWN | English - United States | RT_ICON |
6 | 4.8735 | 9640 | UNKNOWN | English - United States | RT_ICON |
7 | 5.18766 | 4264 | UNKNOWN | English - United States | RT_ICON |
8 | 4.89552 | 1128 | UNKNOWN | English - United States | RT_ICON |
105 | 2.81487 | 118 | UNKNOWN | English - United States | RT_GROUP_ICON |
Imports
KERNEL32.dll |
OLEACC.dll |
RPCRT4.dll |
SHELL32.dll |
SHLWAPI.dll |
WININET.dll |
WS2_32.dll |
msvcrt.dll |
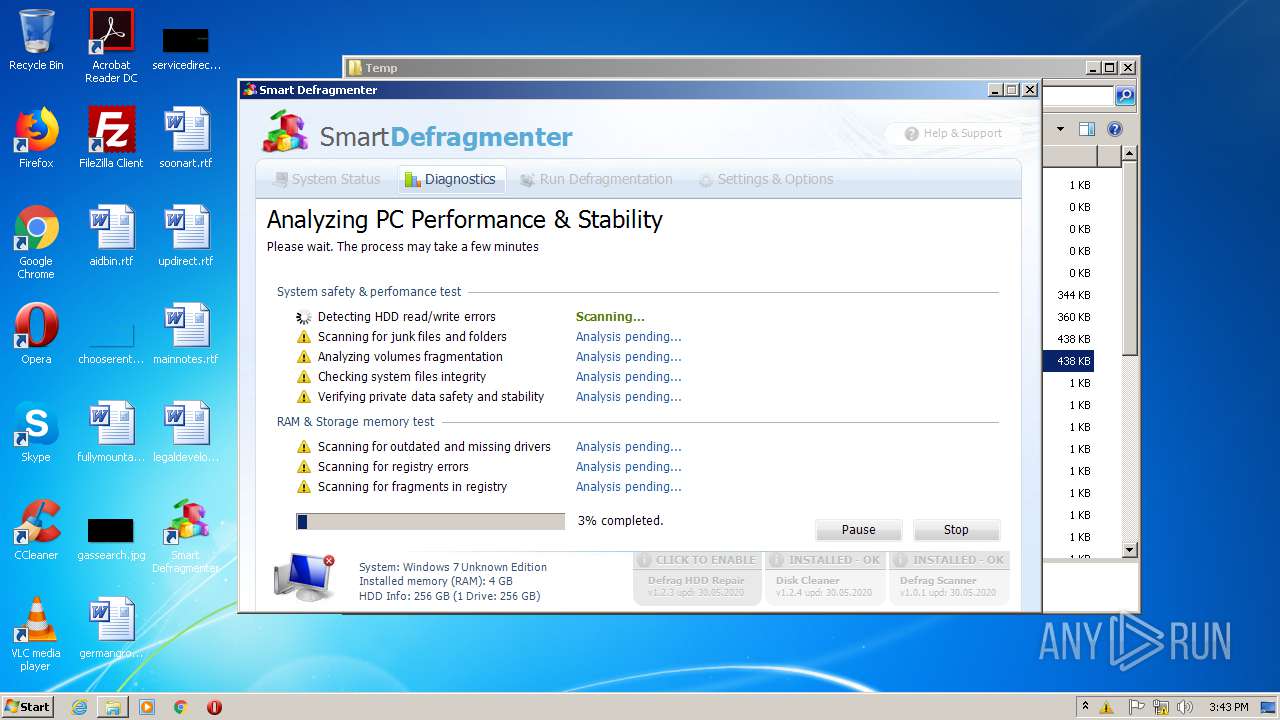
Total processes
50
Monitored processes
8
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 636 | "C:\Users\admin\AppData\Local\Temp\Endermanch@SmartDefragmenter.exe" | C:\Users\admin\AppData\Local\Temp\Endermanch@SmartDefragmenter.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: UtilMan EXE Exit code: 0 Version: 5.1.2600.5512 (xpsp.080413-2105) Modules
| |||||||||||||||
| 960 | "C:\Users\admin\AppData\Local\Temp\winsp2up.exe" | C:\Users\admin\AppData\Local\Temp\winsp2up.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: UtilMan EXE Exit code: 0 Version: 5.1.2600.5512 (xpsp.080413-2105) Modules
| |||||||||||||||
| 1548 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1884 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3272 | "C:\Program Files\Internet Explorer\iexplore.exe" http://temp/ | C:\Program Files\Internet Explorer\iexplore.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3308 | C:\Users\admin\AppData\Local\Temp\683953.exe | C:\Users\admin\AppData\Local\Temp\683953.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Defragmenter MFC Application Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 3824 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3272 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | — | iexplore.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3972 | "C:\Users\admin\AppData\Local\Temp\winsp2up.exe" | C:\Users\admin\AppData\Local\Temp\winsp2up.exe | Endermanch@SmartDefragmenter.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: UtilMan EXE Exit code: 0 Version: 5.1.2600.5512 (xpsp.080413-2105) Modules
| |||||||||||||||
Total events
5 101
Read events
3 855
Write events
1 239
Delete events
7
Modification events
| (PID) Process: | (636) Endermanch@SmartDefragmenter.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (636) Endermanch@SmartDefragmenter.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (636) Endermanch@SmartDefragmenter.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | winsp2up.exe |
Value: C:\Users\admin\AppData\Local\Temp\winsp2up.exe | |||
| (PID) Process: | (1884) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (1884) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A1000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (1884) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (1884) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (1884) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (1884) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft |
| Operation: | write | Name: | BootData |
Value: 43003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C004C006F00630061006C005C00540065006D0070005C003600380033003900350033002E006500780065000000 | |||
| (PID) Process: | (1884) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{CEBFF5CD-ACE2-4F4F-9178-9926F41749EA}\Count |
| Operation: | write | Name: | {S38OS404-1Q43-42S2-9305-67QR0O28SP23}\rkcybere.rkr |
Value: 000000000C0000001A00000057BE0F00000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BFFFFFFFFF906AB6919036D60100000000 | |||
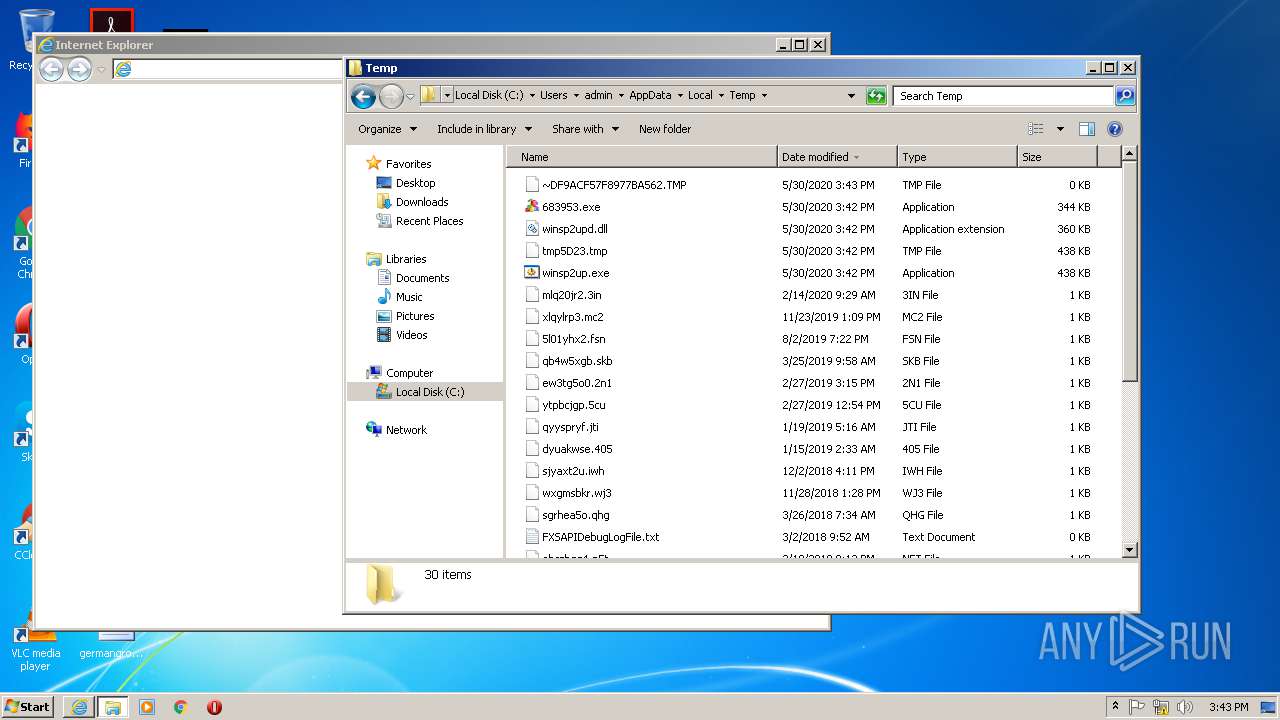
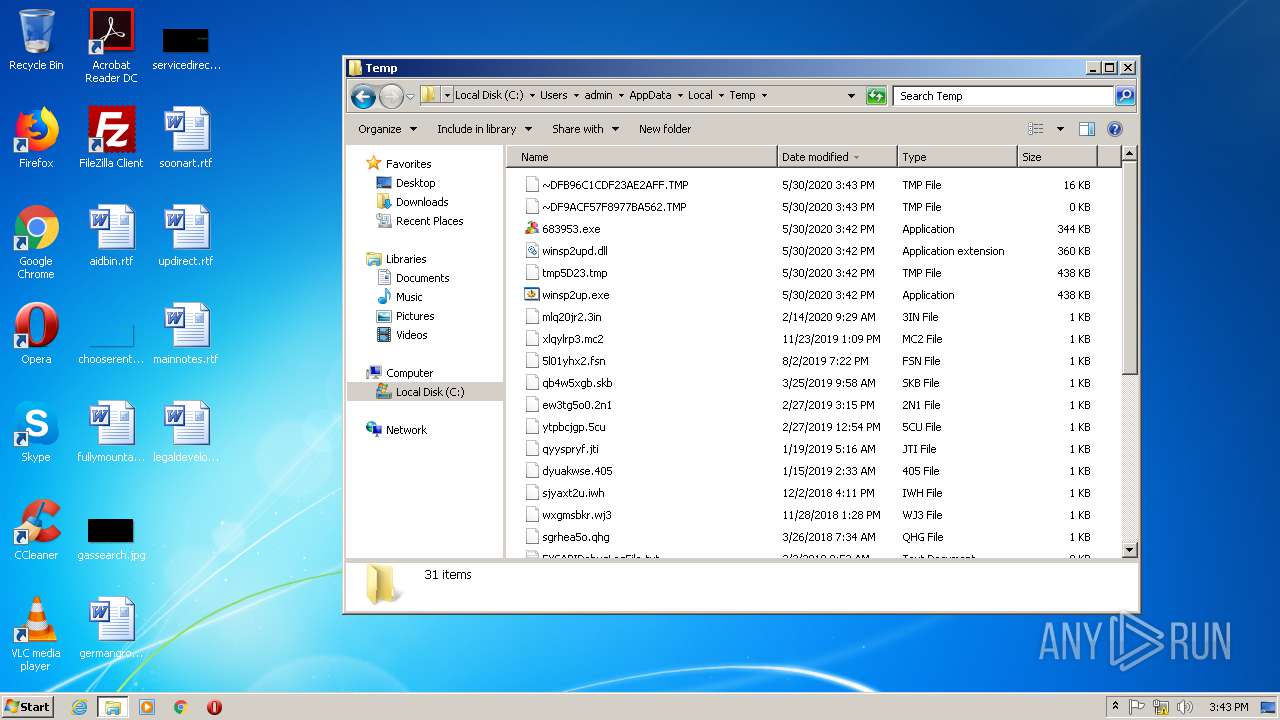
Executable files
4
Suspicious files
4
Text files
4
Unknown types
4
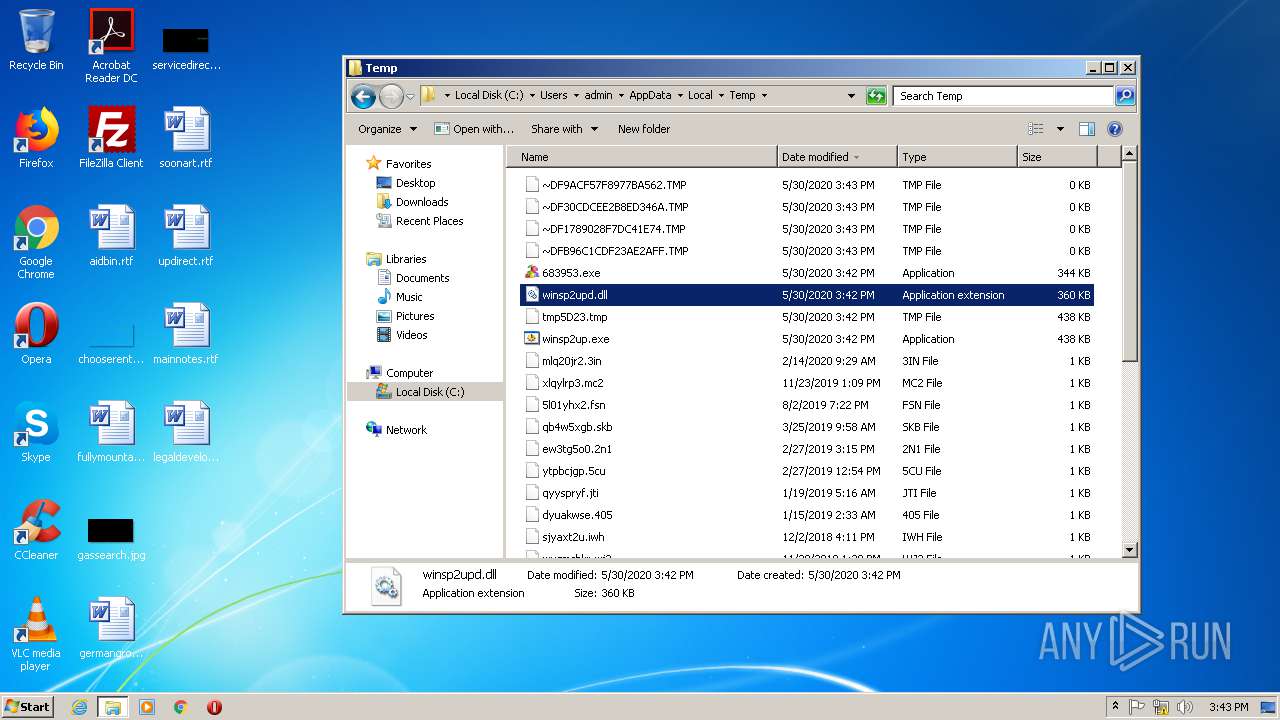
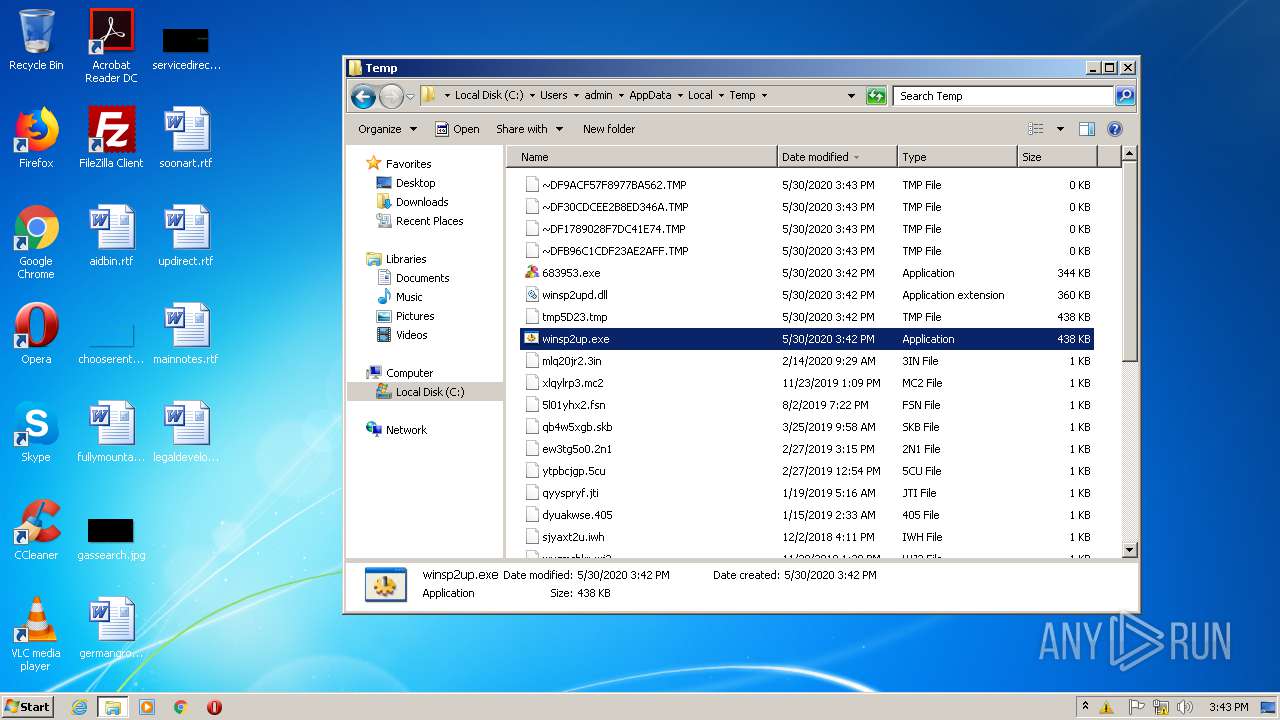
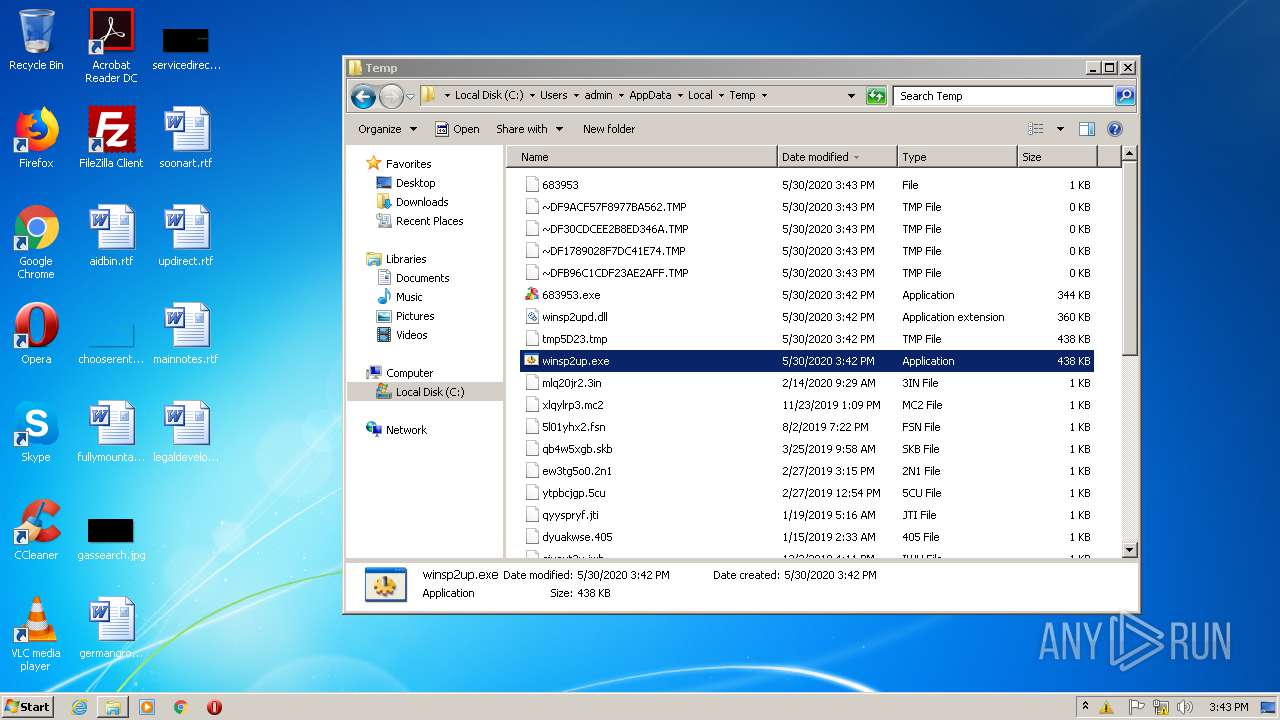
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3272 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF1789028F7DC41E74.TMP | — | |
MD5:— | SHA256:— | |||
| 3272 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF30CDCEE2B8ED346A.TMP | — | |
MD5:— | SHA256:— | |||
| 3272 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DFB96C1CDF23AE2AFF.TMP | — | |
MD5:— | SHA256:— | |||
| 3272 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Active\{E4213C59-A283-11EA-B44D-5254004A04AF}.dat | — | |
MD5:— | SHA256:— | |||
| 3272 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF9ACF57F8977BA562.TMP | — | |
MD5:— | SHA256:— | |||
| 3272 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Active\RecoveryStore.{DE116DC7-A283-11EA-B44D-5254004A04AF}.dat | — | |
MD5:— | SHA256:— | |||
| 1884 | explorer.exe | C:\Users\admin\AppData\Local\Temp\~DF7DE0700D289BAF14.TMP | — | |
MD5:— | SHA256:— | |||
| 1884 | explorer.exe | C:\Users\admin\AppData\Local\Temp\~DF598106F2C74C6943.TMP | — | |
MD5:— | SHA256:— | |||
| 1884 | explorer.exe | C:\Users\admin\AppData\Local\Temp\~DF264CA6E0B7D88396.TMP | — | |
MD5:— | SHA256:— | |||
| 1884 | explorer.exe | C:\Users\admin\AppData\Local\Temp\~DFFA2C1520744EC849.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
2
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
DNS requests
Domain | IP | Reputation |
|---|---|---|
ashamedice.com |
| unknown |
searchaccount.org |
| unknown |