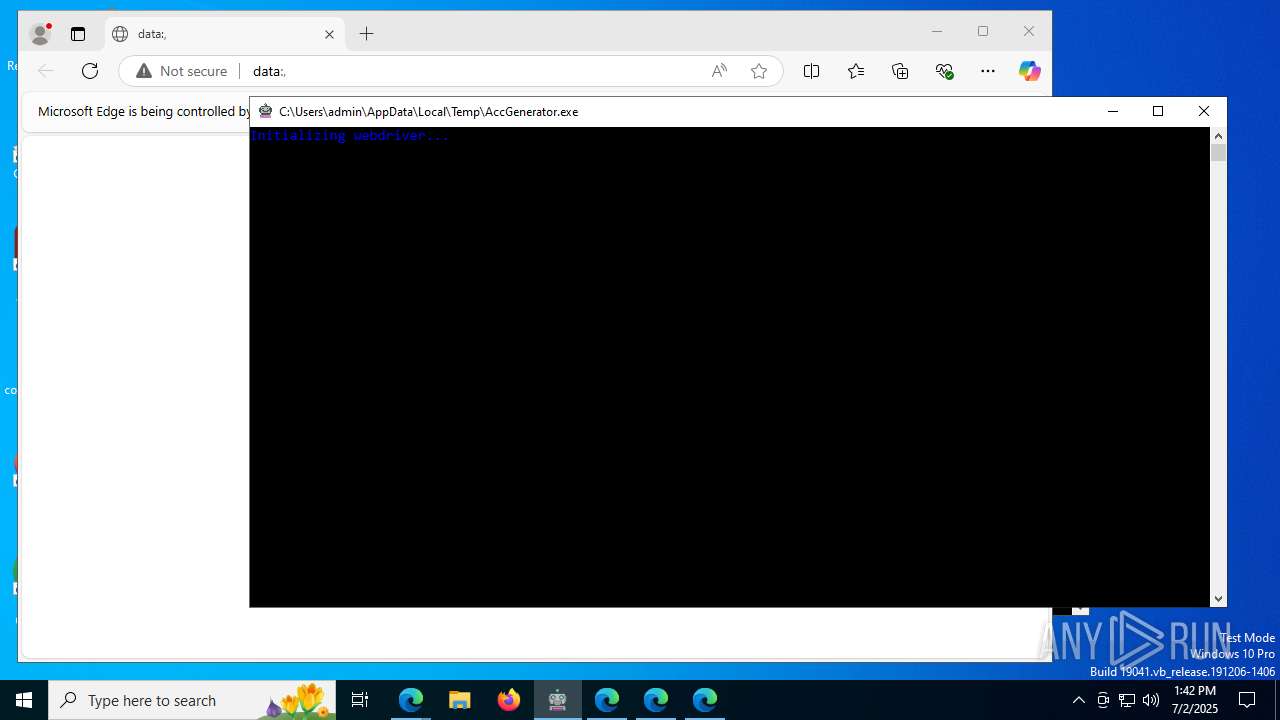
| File name: | AccGenerator.exe |
| Full analysis: | https://app.any.run/tasks/ef189aa1-4c88-40c4-9efc-5c6c4d87992e |
| Verdict: | Malicious activity |
| Analysis date: | July 02, 2025, 13:41:18 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32+ executable (console) x86-64, for MS Windows, 7 sections |
| MD5: | 6945D0630139E2D1F6195F8455D36553 |
| SHA1: | FE83987EF7CE5B17A06387D5BB3729803812B8C1 |
| SHA256: | 6198793CDE7E2F3DC53C62036E300EE46BBEFE5956F30EA78C6088C40DB1ABD9 |
| SSDEEP: | 98304:6XEGsuDFqWXAz+lrEnzVMEuAbYpB4RplQ94geo7HNR9dIofyxmxqMogIn/B25cQF:B6YYXji+yGI3swdmVGa2 |
MALICIOUS
No malicious indicators.SUSPICIOUS
Process drops legitimate windows executable
- AccGenerator.exe (PID: 6852)
- selenium-manager.exe (PID: 1936)
The process drops C-runtime libraries
- AccGenerator.exe (PID: 6852)
Process drops python dynamic module
- AccGenerator.exe (PID: 6852)
Executable content was dropped or overwritten
- AccGenerator.exe (PID: 6852)
- selenium-manager.exe (PID: 1936)
Loads Python modules
- AccGenerator.exe (PID: 5712)
Starts CMD.EXE for commands execution
- AccGenerator.exe (PID: 5712)
- selenium-manager.exe (PID: 4948)
- selenium-manager.exe (PID: 1936)
- selenium-manager.exe (PID: 7476)
- selenium-manager.exe (PID: 9196)
- selenium-manager.exe (PID: 9772)
- selenium-manager.exe (PID: 2320)
- selenium-manager.exe (PID: 10928)
Uses WMIC.EXE
- cmd.exe (PID: 4648)
- cmd.exe (PID: 7188)
- cmd.exe (PID: 8048)
- cmd.exe (PID: 9860)
- cmd.exe (PID: 10284)
- cmd.exe (PID: 5188)
- cmd.exe (PID: 3052)
Application launched itself
- AccGenerator.exe (PID: 6852)
Uses WMIC.EXE to obtain operating system information
- cmd.exe (PID: 6228)
- cmd.exe (PID: 7484)
- cmd.exe (PID: 5496)
- cmd.exe (PID: 8652)
- cmd.exe (PID: 9800)
- cmd.exe (PID: 3908)
- cmd.exe (PID: 11164)
INFO
Create files in a temporary directory
- AccGenerator.exe (PID: 6852)
- selenium-manager.exe (PID: 1936)
- msedgedriver.exe (PID: 1192)
- msedgedriver.exe (PID: 7436)
- msedgedriver.exe (PID: 7500)
- msedgedriver.exe (PID: 8736)
- msedgedriver.exe (PID: 9948)
- msedgedriver.exe (PID: 10368)
- msedgedriver.exe (PID: 10332)
Checks supported languages
- AccGenerator.exe (PID: 6852)
- AccGenerator.exe (PID: 5712)
- selenium-manager.exe (PID: 1936)
- msedgedriver.exe (PID: 1192)
- selenium-manager.exe (PID: 4948)
- selenium-manager.exe (PID: 7476)
- msedgedriver.exe (PID: 7500)
- selenium-manager.exe (PID: 9196)
- msedgedriver.exe (PID: 8736)
- selenium-manager.exe (PID: 9772)
- msedgedriver.exe (PID: 9948)
- selenium-manager.exe (PID: 2320)
- msedgedriver.exe (PID: 10368)
- msedgedriver.exe (PID: 7436)
- selenium-manager.exe (PID: 10928)
- msedgedriver.exe (PID: 10332)
Reads the computer name
- AccGenerator.exe (PID: 6852)
- AccGenerator.exe (PID: 5712)
- selenium-manager.exe (PID: 1936)
- msedgedriver.exe (PID: 1192)
- msedgedriver.exe (PID: 7436)
- msedgedriver.exe (PID: 7500)
- msedgedriver.exe (PID: 8736)
- msedgedriver.exe (PID: 9948)
- msedgedriver.exe (PID: 10368)
- msedgedriver.exe (PID: 10332)
Checks proxy server information
- AccGenerator.exe (PID: 5712)
- selenium-manager.exe (PID: 1936)
- selenium-manager.exe (PID: 4948)
- selenium-manager.exe (PID: 7476)
- selenium-manager.exe (PID: 9196)
- selenium-manager.exe (PID: 9772)
- selenium-manager.exe (PID: 2320)
- selenium-manager.exe (PID: 10928)
The sample compiled with english language support
- AccGenerator.exe (PID: 6852)
- selenium-manager.exe (PID: 1936)
Reads security settings of Internet Explorer
- WMIC.exe (PID: 5824)
- WMIC.exe (PID: 420)
- WMIC.exe (PID: 1192)
- WMIC.exe (PID: 2116)
- WMIC.exe (PID: 5876)
- WMIC.exe (PID: 7204)
- WMIC.exe (PID: 7408)
- WMIC.exe (PID: 9816)
- WMIC.exe (PID: 9876)
- WMIC.exe (PID: 7356)
- WMIC.exe (PID: 7204)
- WMIC.exe (PID: 10392)
- WMIC.exe (PID: 11176)
- WMIC.exe (PID: 10300)
Checks operating system version
- AccGenerator.exe (PID: 5712)
Application launched itself
- msedge.exe (PID: 5884)
- msedge.exe (PID: 2180)
- msedge.exe (PID: 7524)
- msedge.exe (PID: 7504)
- msedge.exe (PID: 4576)
- msedge.exe (PID: 2116)
- msedge.exe (PID: 1852)
- msedge.exe (PID: 3872)
- msedge.exe (PID: 10012)
- msedge.exe (PID: 10028)
- msedge.exe (PID: 10440)
- msedge.exe (PID: 6152)
- msedge.exe (PID: 6676)
- msedge.exe (PID: 10456)
PyInstaller has been detected (YARA)
- AccGenerator.exe (PID: 5712)
- AccGenerator.exe (PID: 6852)
Reads Environment values
- msedgedriver.exe (PID: 1192)
- msedgedriver.exe (PID: 7436)
- msedgedriver.exe (PID: 7500)
- msedgedriver.exe (PID: 8736)
- msedgedriver.exe (PID: 9948)
- msedgedriver.exe (PID: 10368)
- msedgedriver.exe (PID: 10332)
Drops encrypted JS script (Microsoft Script Encoder)
- AccGenerator.exe (PID: 5712)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (87.3) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (6.3) |
| .exe | | | DOS Executable Generic (6.3) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2023:11:14 21:00:07+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 14.34 |
| CodeSize: | 166400 |
| InitializedDataSize: | 160256 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xa6a0 |
| OSVersion: | 5.2 |
| ImageVersion: | - |
| SubsystemVersion: | 5.2 |
| Subsystem: | Windows command line |
Total processes
312
Monitored processes
175
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 420 | wmic datafile where name='C:\\Program Files (x86)\\Microsoft\\Edge\\Application\\msedge.exe' get Version /value | C:\Windows\SysWOW64\wbem\WMIC.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: WMI Commandline Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 440 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | AccGenerator.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
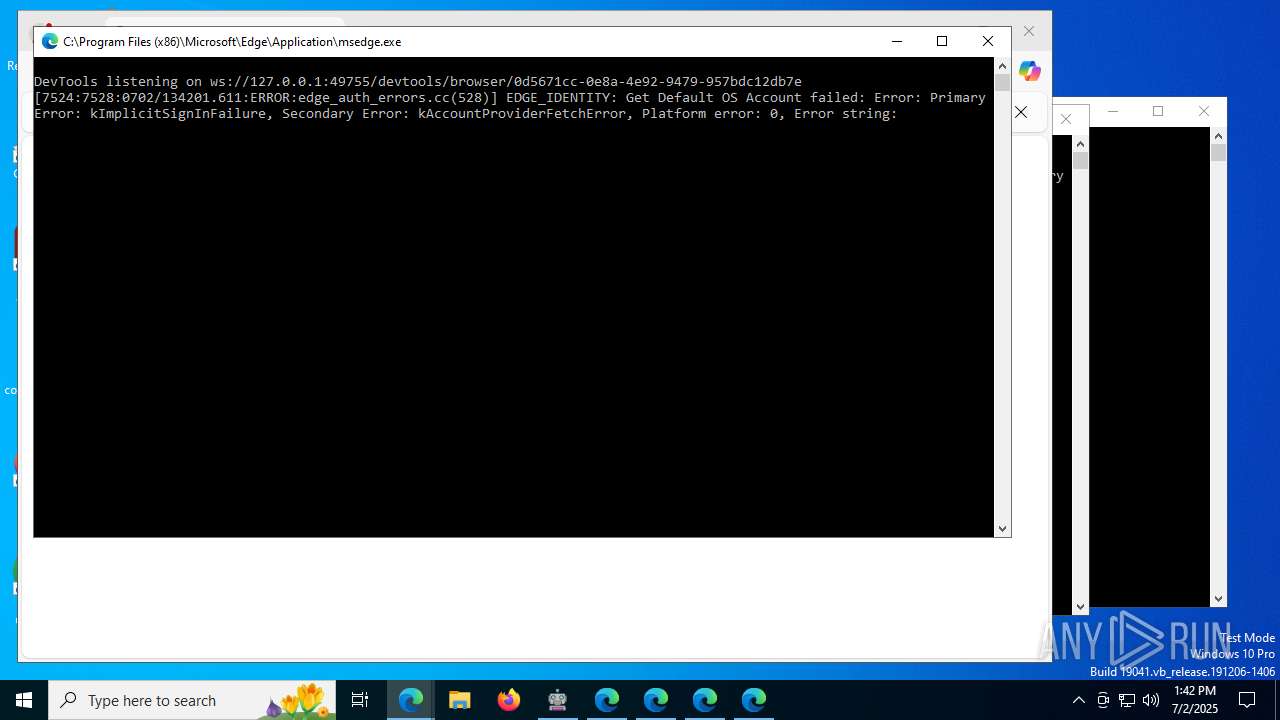
| 1192 | C:\Users\admin\.cache\selenium\msedgedriver\win64\133.0.3065.92\msedgedriver.exe --port=49718 | C:\Users\admin\.cache\selenium\msedgedriver\win64\133.0.3065.92\msedgedriver.exe | — | AccGenerator.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge WebDriver Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1192 | wmic os get osarchitecture | C:\Windows\SysWOW64\wbem\WMIC.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: WMI Commandline Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1828 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=entity_extraction_service.mojom.Extractor --lang=en-US --service-sandbox-type=entity_extraction --onnx-enabled-for-ee --string-annotations --user-data-dir="C:\Users\admin\AppData\Local\Temp\scoped_dir7436_1427555969" --always-read-main-dll --field-trial-handle=5148,i,3748878810388496638,17713084898621160815,262144 --enable-features=msMetricsLogFastStartup,msSendMetricsLogOnClose --variations-seed-version --enable-logging=handle --log-file=5252 --log-level=0 --mojo-platform-channel-handle=5248 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1852 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --allow-pre-commit-input --disable-background-networking --disable-backgrounding-occluded-windows --disable-client-side-phishing-detection --disable-default-apps --disable-hang-monitor --disable-popup-blocking --disable-prompt-on-repost --disable-sync --enable-automation --enable-logging --log-level=0 --no-first-run --no-service-autorun --password-store=basic --remote-debugging-port=0 --test-type=webdriver --use-mock-keychain --user-data-dir="C:\Users\admin\AppData\Local\Temp\scoped_dir8736_1358956989" data:, | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedgedriver.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1936 | C:\Users\admin\AppData\Local\Temp\_MEI68522\selenium\webdriver\common\windows\selenium-manager.exe --browser MicrosoftEdge --output json | C:\Users\admin\AppData\Local\Temp\_MEI68522\selenium\webdriver\common\windows\selenium-manager.exe | AccGenerator.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1948 | "cmd" /v/c "msedgedriver --version" | C:\Windows\SysWOW64\cmd.exe | — | selenium-manager.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2116 | wmic os get osarchitecture | C:\Windows\SysWOW64\wbem\WMIC.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: WMI Commandline Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2116 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --allow-pre-commit-input --disable-background-networking --disable-backgrounding-occluded-windows --disable-client-side-phishing-detection --disable-default-apps --disable-hang-monitor --disable-popup-blocking --disable-prompt-on-repost --disable-sync --enable-automation --enable-logging --log-level=0 --no-first-run --no-service-autorun --password-store=basic --remote-debugging-port=0 --test-type=webdriver --use-mock-keychain --user-data-dir="C:\Users\admin\AppData\Local\Temp\scoped_dir7500_969261918" --edge-skip-compat-layer-relaunch data:, | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | msedge.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
Total events
21 025
Read events
20 941
Write events
84
Delete events
0
Modification events
| (PID) Process: | (2180) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 1 | |||
| (PID) Process: | (2180) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (5884) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (5884) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2180) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\DualEngineCacheContainerTracker |
| Operation: | write | Name: | JUMV2GCI |
Value: C:\Users\admin\AppData\Local\Temp\scoped_dir1192_1933169074\Default | |||
| (PID) Process: | (2180) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (2180) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\PrefsLightweight |
| Operation: | write | Name: | lw_a7990ebf1786dcf322123a76278ae048 |
Value: 101 | |||
| (PID) Process: | (2180) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\328508 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {C97848CB-751A-4953-B8DB-73048AE2627B} | |||
| (PID) Process: | (2180) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: A69D5BB588972F00 | |||
| (PID) Process: | (2180) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\328508 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {1E66AC73-F1DC-410E-BD24-8000144AF92F} | |||
Executable files
19
Suspicious files
481
Text files
252
Unknown types
288
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6852 | AccGenerator.exe | C:\Users\admin\AppData\Local\Temp\_MEI68522\selenium\webdriver\common\linux\selenium-manager | — | |
MD5:— | SHA256:— | |||
| 6852 | AccGenerator.exe | C:\Users\admin\AppData\Local\Temp\_MEI68522\VCRUNTIME140.dll | executable | |
MD5:4585A96CC4EEF6AAFD5E27EA09147DC6 | SHA256:A8F950B4357EC12CFCCDDC9094CCA56A3D5244B95E09EA6E9A746489F2D58736 | |||
| 6852 | AccGenerator.exe | C:\Users\admin\AppData\Local\Temp\_MEI68522\_queue.pyd | executable | |
MD5:06248702A6CD9D2DD20C0B1C6B02174D | SHA256:AC177CD84C12E03E3A68BCA30290BC0B8F173EEE518EF1FA6A9DCE3A3E755A93 | |||
| 6852 | AccGenerator.exe | C:\Users\admin\AppData\Local\Temp\_MEI68522\_hashlib.pyd | executable | |
MD5:787B82D4466F393366657B8F1BC5F1A9 | SHA256:241322647BA9F94BDC3AE387413FFB57AE14C8CF88BD564A31FE193C6CA43E37 | |||
| 6852 | AccGenerator.exe | C:\Users\admin\AppData\Local\Temp\_MEI68522\_bz2.pyd | executable | |
MD5:A62207FC33140DE460444E191AE19B74 | SHA256:EBCAC51449F323AE3AE961A33843029C34B6A82138CCD9214CF99F98DD2148C2 | |||
| 6852 | AccGenerator.exe | C:\Users\admin\AppData\Local\Temp\_MEI68522\_ssl.pyd | executable | |
MD5:AB0E4FBFFB6977D0196C7D50BC76CF2D | SHA256:680AD2DE8A6CFF927822C1D7DD22112A3E8A824E82A7958EE409A7B9CE45EC70 | |||
| 6852 | AccGenerator.exe | C:\Users\admin\AppData\Local\Temp\_MEI68522\libcrypto-1_1.dll | executable | |
MD5:9D7A0C99256C50AFD5B0560BA2548930 | SHA256:9B7B4A0AD212095A8C2E35C71694D8A1764CD72A829E8E17C8AFE3A55F147939 | |||
| 6852 | AccGenerator.exe | C:\Users\admin\AppData\Local\Temp\_MEI68522\charset_normalizer\md.cp311-win_amd64.pyd | executable | |
MD5:FA50D9F8BCE6BD13652F5090E7B82C4D | SHA256:FFF69928DEA1432E0C7CB1225AB96F94FD38D5D852DE9A6BB8BF30B7D2BEDCEB | |||
| 6852 | AccGenerator.exe | C:\Users\admin\AppData\Local\Temp\_MEI68522\_socket.pyd | executable | |
MD5:26DD19A1F5285712068B9E41808E8FA0 | SHA256:EAABF6B78840DAEAF96B5BDBF06ADF0E4E2994DFEEE5C5E27FEFD824DBDA5220 | |||
| 6852 | AccGenerator.exe | C:\Users\admin\AppData\Local\Temp\_MEI68522\base_library.zip | compressed | |
MD5:EBB4F1A115F0692698B5640869F30853 | SHA256:4AB0DEB6A298D14A0F50D55DC6CE5673B6C5320817EC255ACF282191642A4576 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
14
TCP/UDP connections
103
DNS requests
118
Threats
15
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
7004 | msedge.exe | GET | 200 | 150.171.28.11:80 | http://edge.microsoft.com/browsernetworktime/time/1/current?cup2key=2:rPnHBU3My0r078xA4v10FGdP3Hom9vuAuAam2YNt8G0&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 2.16.241.12:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
4980 | svchost.exe | GET | 200 | 2.16.241.12:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
2876 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
8300 | msedge.exe | GET | 200 | 150.171.27.11:80 | http://edge.microsoft.com/browsernetworktime/time/1/current?cup2key=2:X5sDC2mjxvZqqgFl7rFtmcEJSxqqVKJQeDOybrM8Nho&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | unknown | — | — | whitelisted |
4980 | svchost.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicCodSigPCA2011_2011-07-08.crl | unknown | — | — | whitelisted |
7196 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
7804 | msedge.exe | GET | 200 | 150.171.28.11:80 | http://edge.microsoft.com/browsernetworktime/time/1/current?cup2key=2:ZhuTASxm2PPeW9odccGZiOtrmFXA-JRRXJHC3LjCWDo&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | unknown | — | — | whitelisted |
10716 | msedge.exe | GET | 200 | 150.171.27.11:80 | http://edge.microsoft.com/browsernetworktime/time/1/current?cup2key=2:v5A3FL5zcERE0AkIQEEYjkn7f5F3ju9Qo10wzl5LNqI&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
5944 | MoUsoCoreWorker.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1268 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6368 | RUXIMICS.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5712 | AccGenerator.exe | 185.199.108.133:443 | raw.githubusercontent.com | FASTLY | US | whitelisted |
1936 | selenium-manager.exe | 13.107.246.53:443 | msedgedriver.azureedge.net | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
1268 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1268 | svchost.exe | 2.16.241.12:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
1268 | svchost.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
raw.githubusercontent.com |
| whitelisted |
msedgedriver.azureedge.net |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
copilot.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2200 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |
7004 | msedge.exe | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
7004 | msedge.exe | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
7004 | msedge.exe | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
7804 | msedge.exe | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
7804 | msedge.exe | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
8300 | msedge.exe | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
8300 | msedge.exe | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
8040 | msedge.exe | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
8040 | msedge.exe | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
Process | Message |
|---|---|
msedge.exe | RecursiveDirectoryCreate( C:\Users\admin\AppData\Local\Temp directory exists )
|
msedge.exe | RecursiveDirectoryCreate( C:\Users\admin\AppData\Local\Temp\scoped_dir7436_1427555969 directory exists )
|
msedge.exe | RecursiveDirectoryCreate( C:\Users\admin\AppData\Local\Temp directory exists )
|
msedge.exe | RecursiveDirectoryCreate( C:\Users\admin\AppData\Local\Temp\scoped_dir8736_1358956989 directory exists )
|
msedge.exe | RecursiveDirectoryCreate( C:\Users\admin\AppData\Local\Temp directory exists )
|
msedge.exe | RecursiveDirectoryCreate( C:\Users\admin\AppData\Local\Temp directory exists )
|
msedge.exe | RecursiveDirectoryCreate( C:\Users\admin\AppData\Local\Temp directory exists )
|