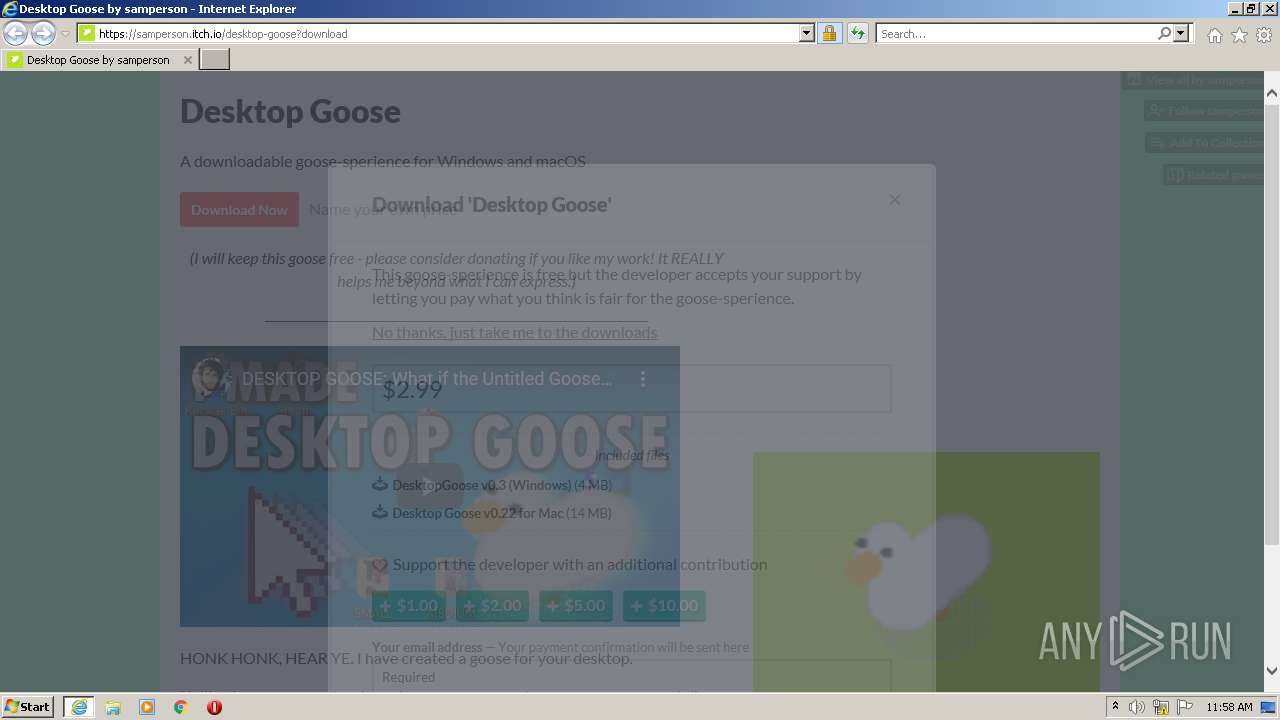
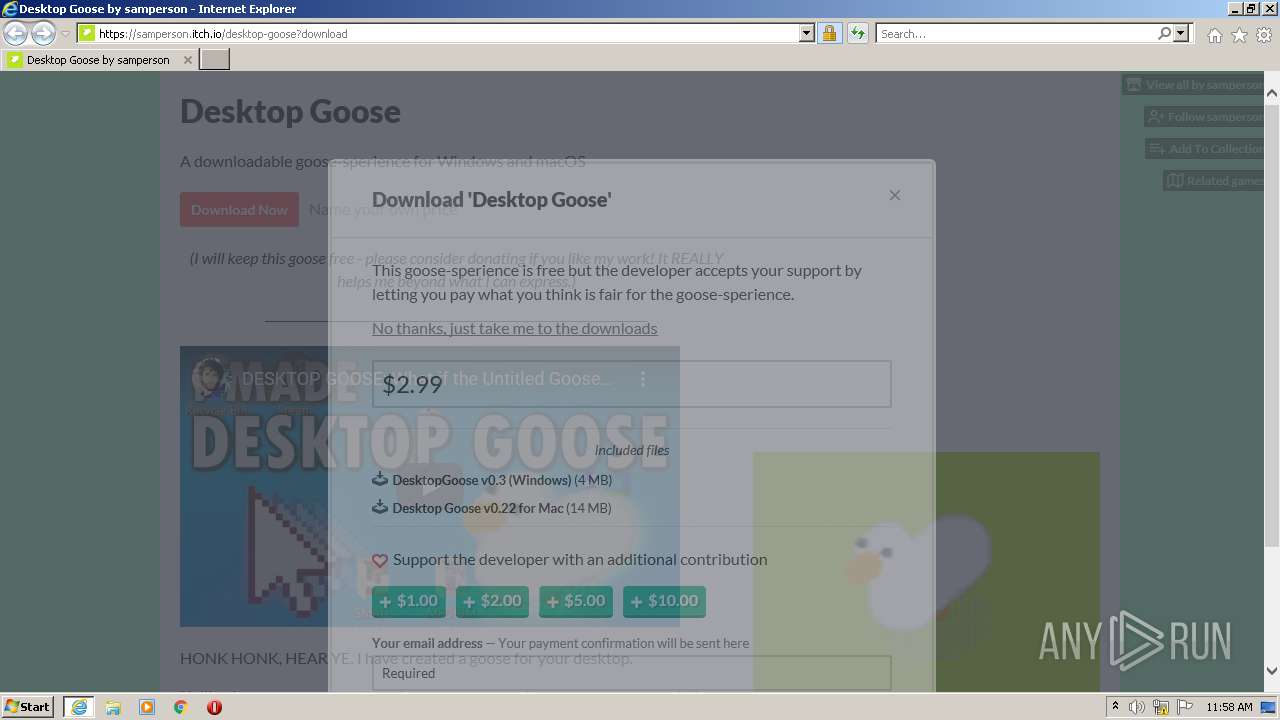
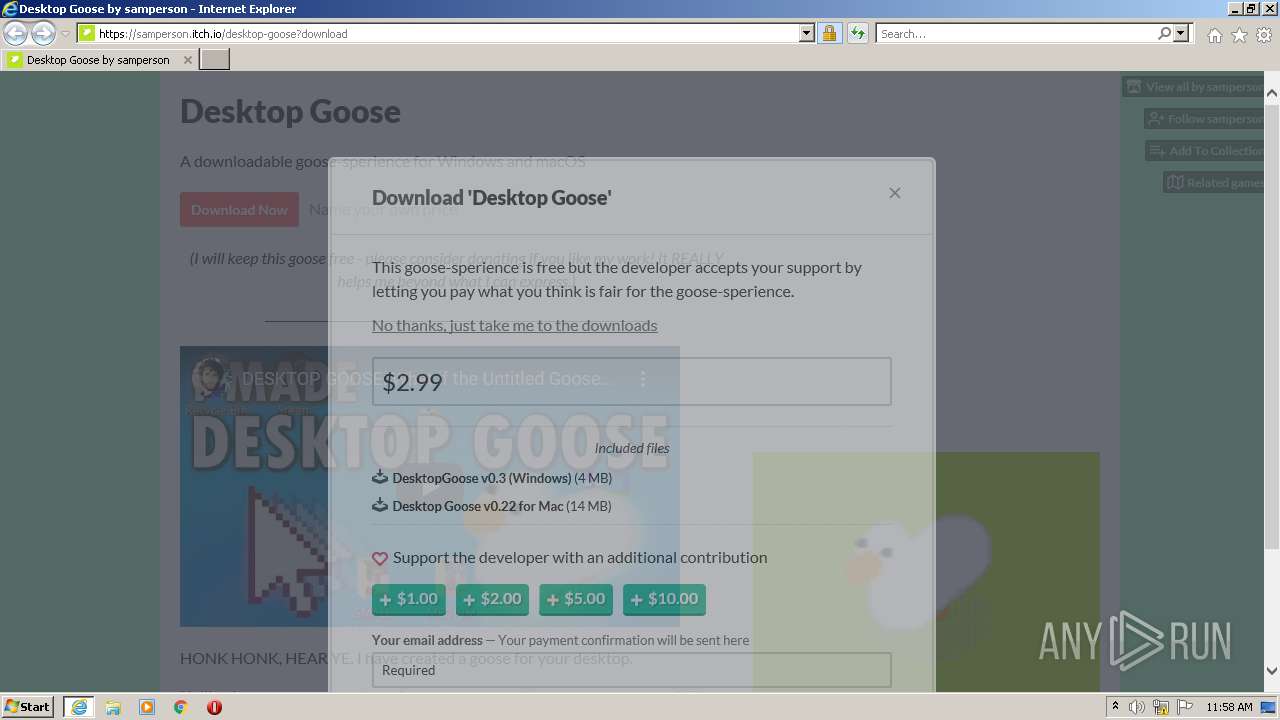
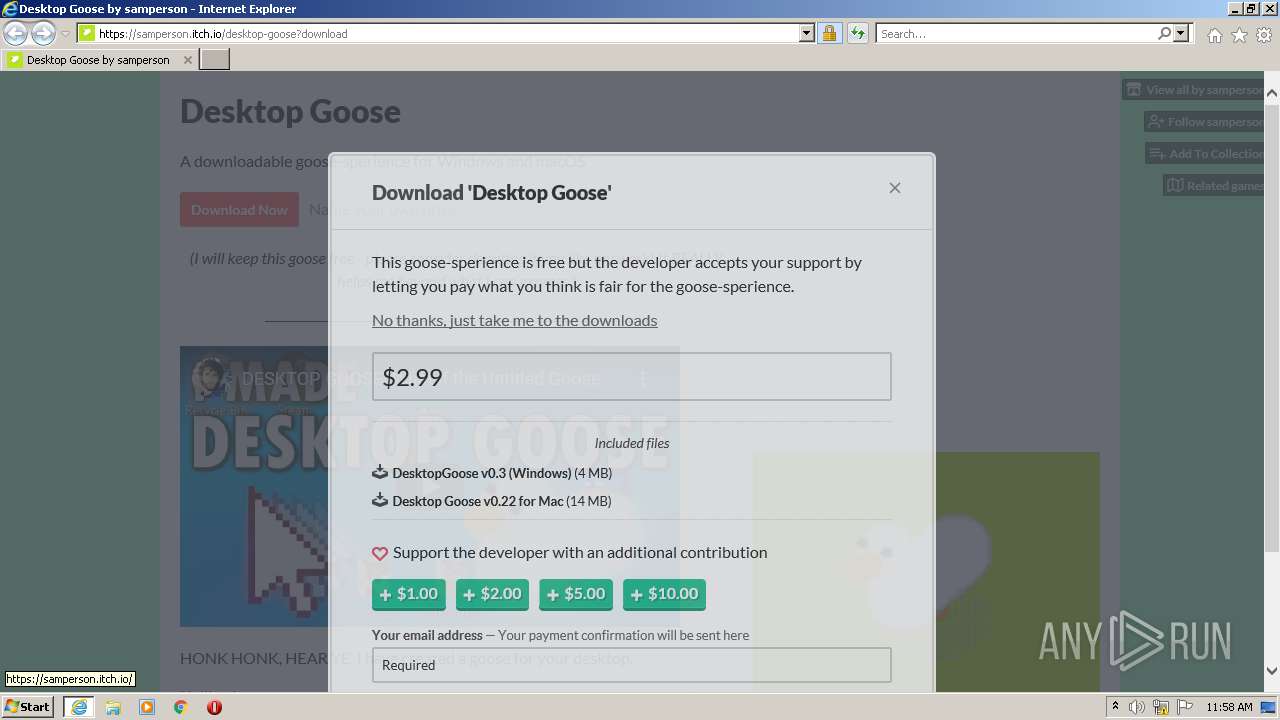
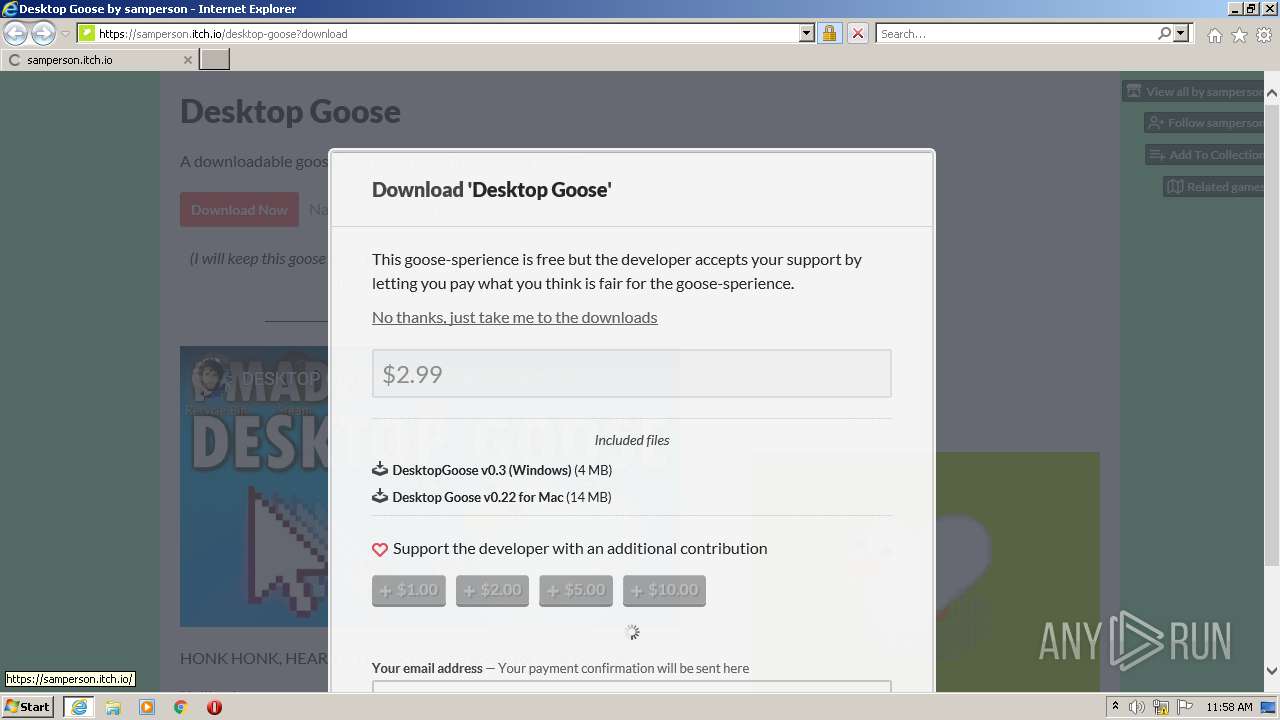
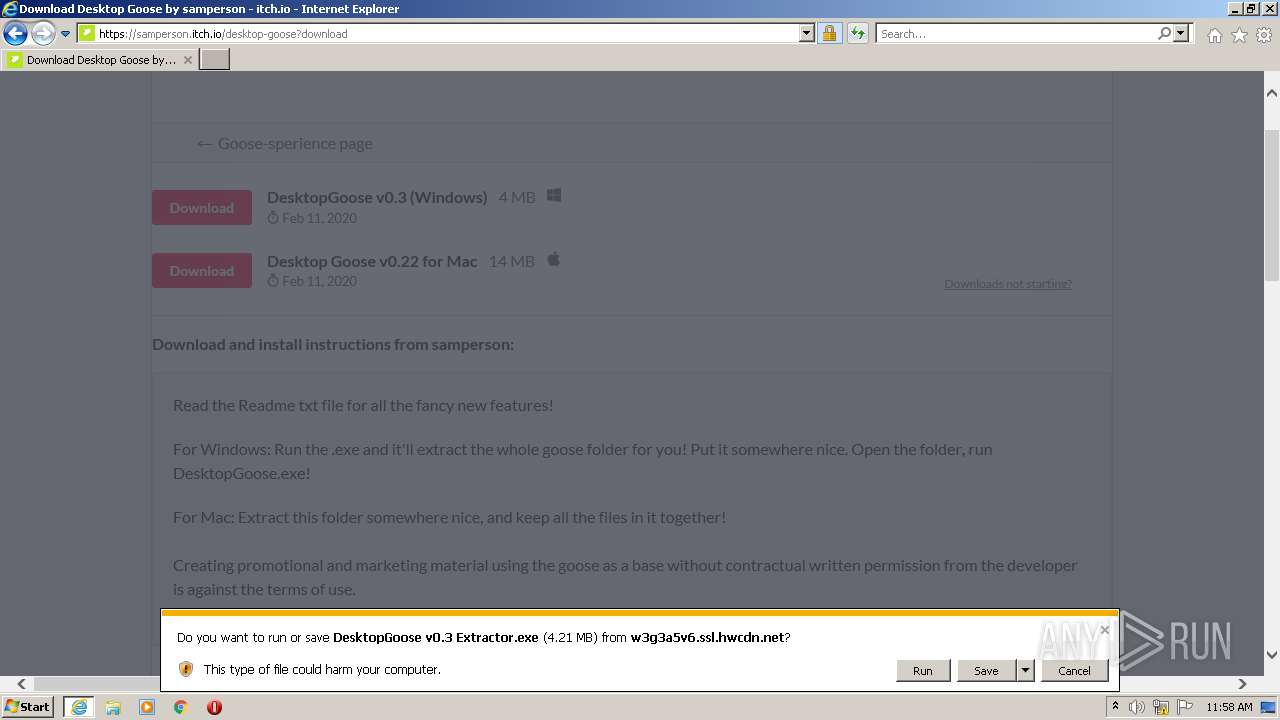
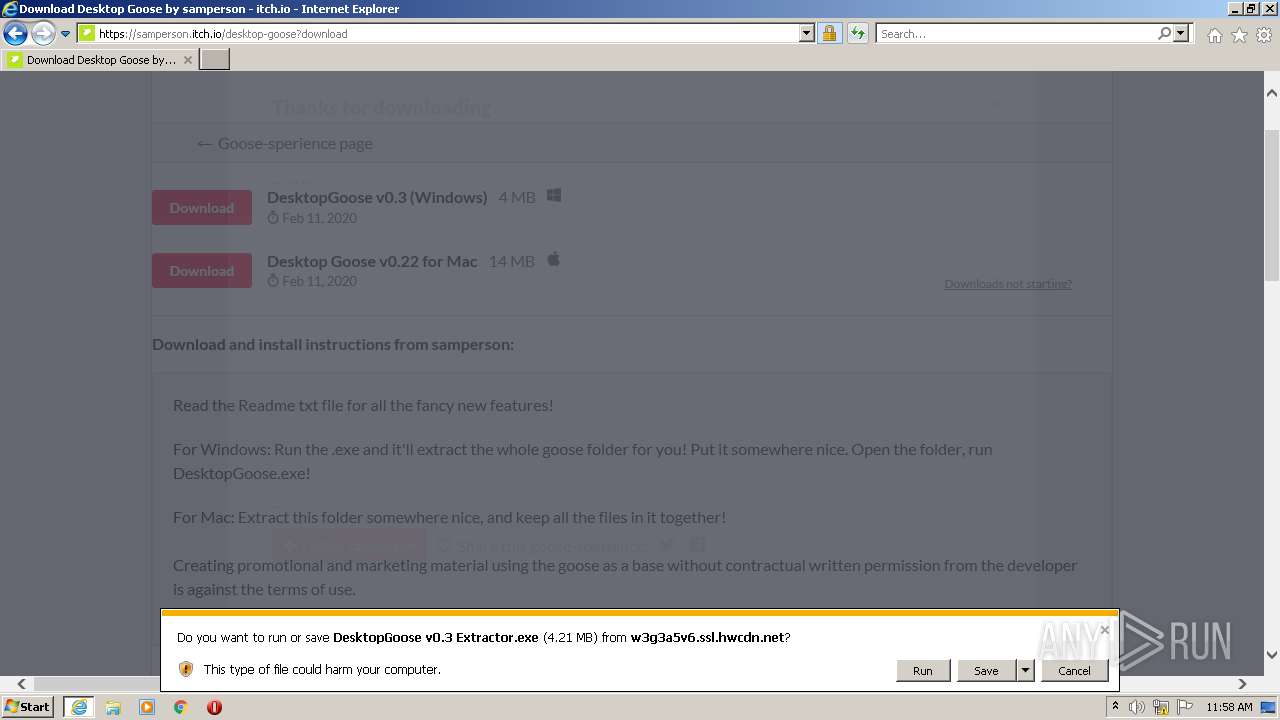
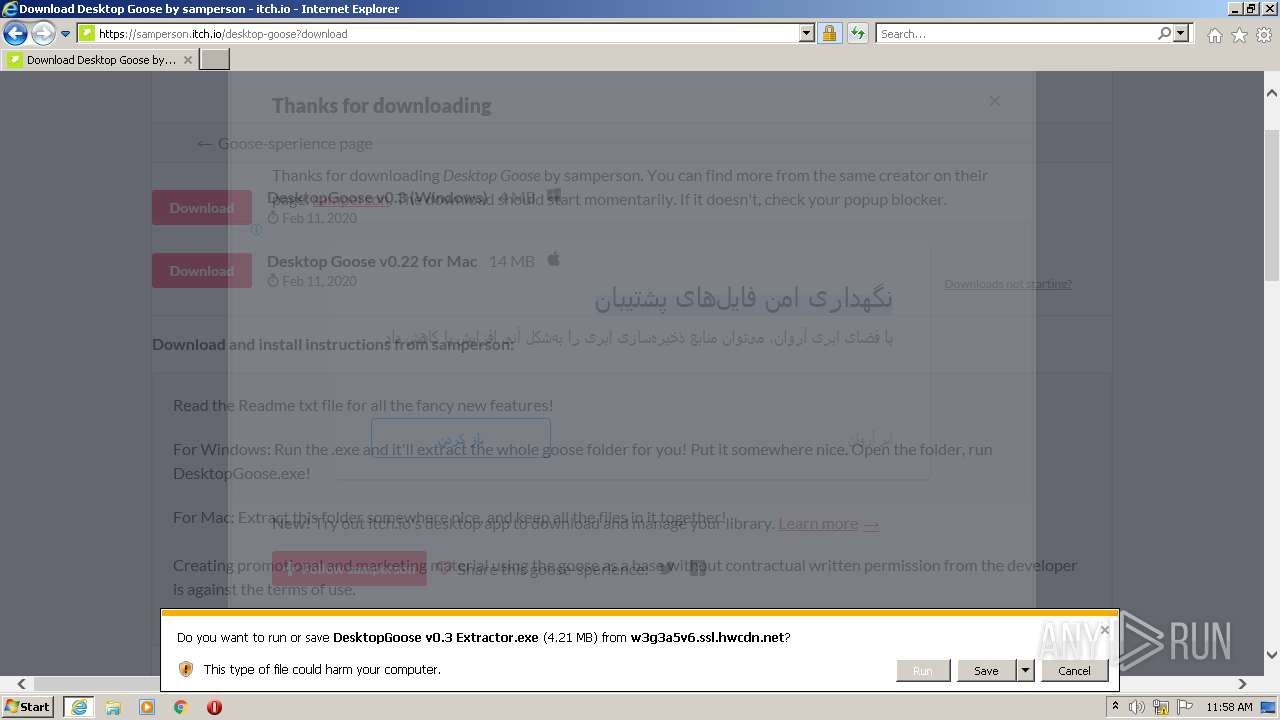
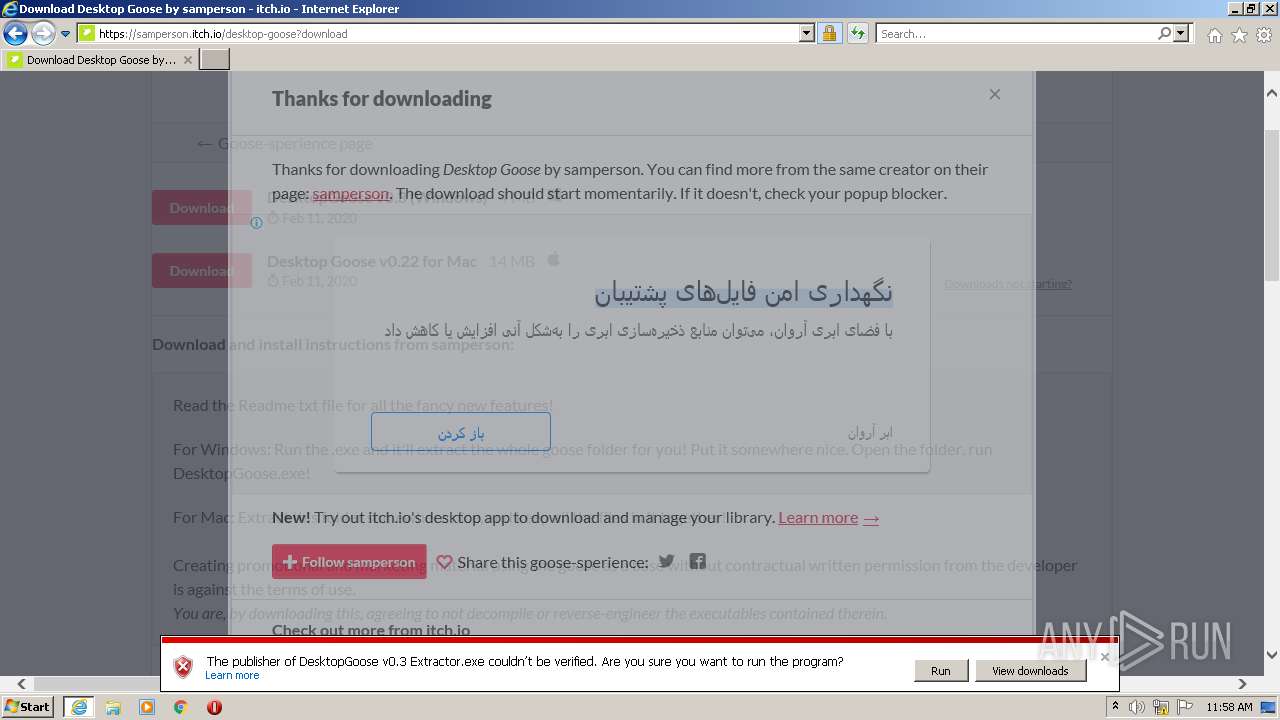
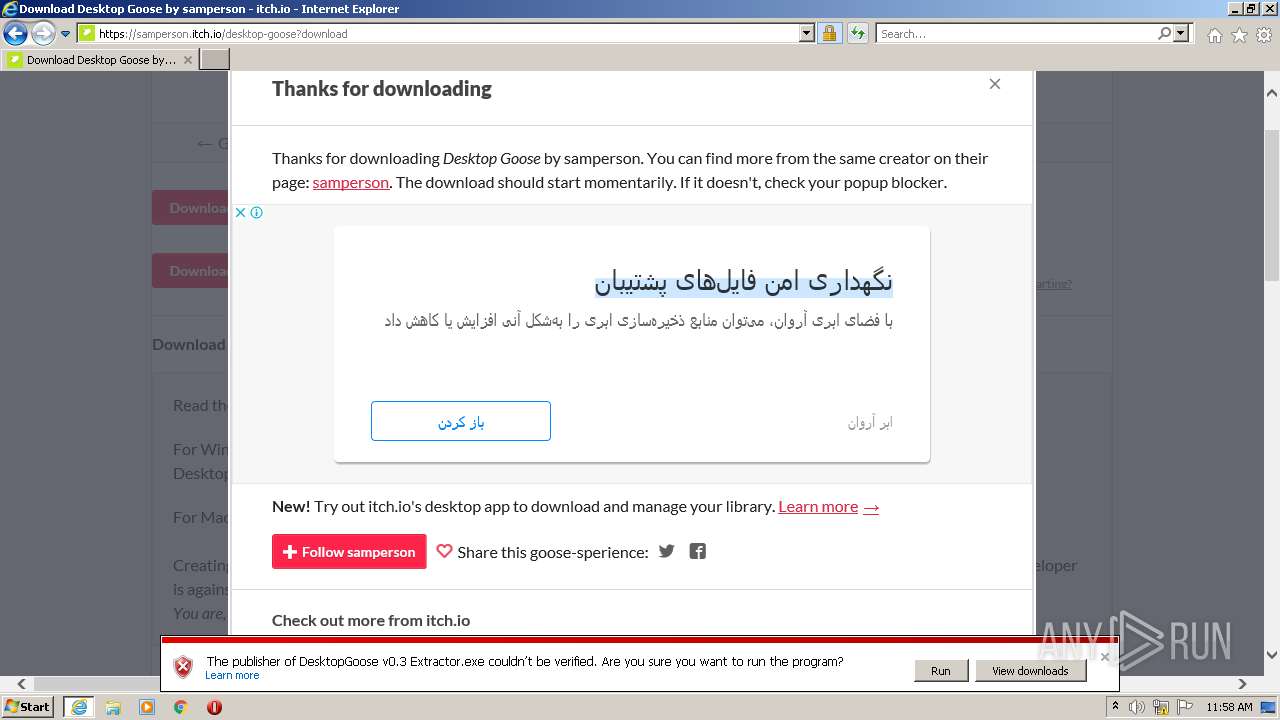
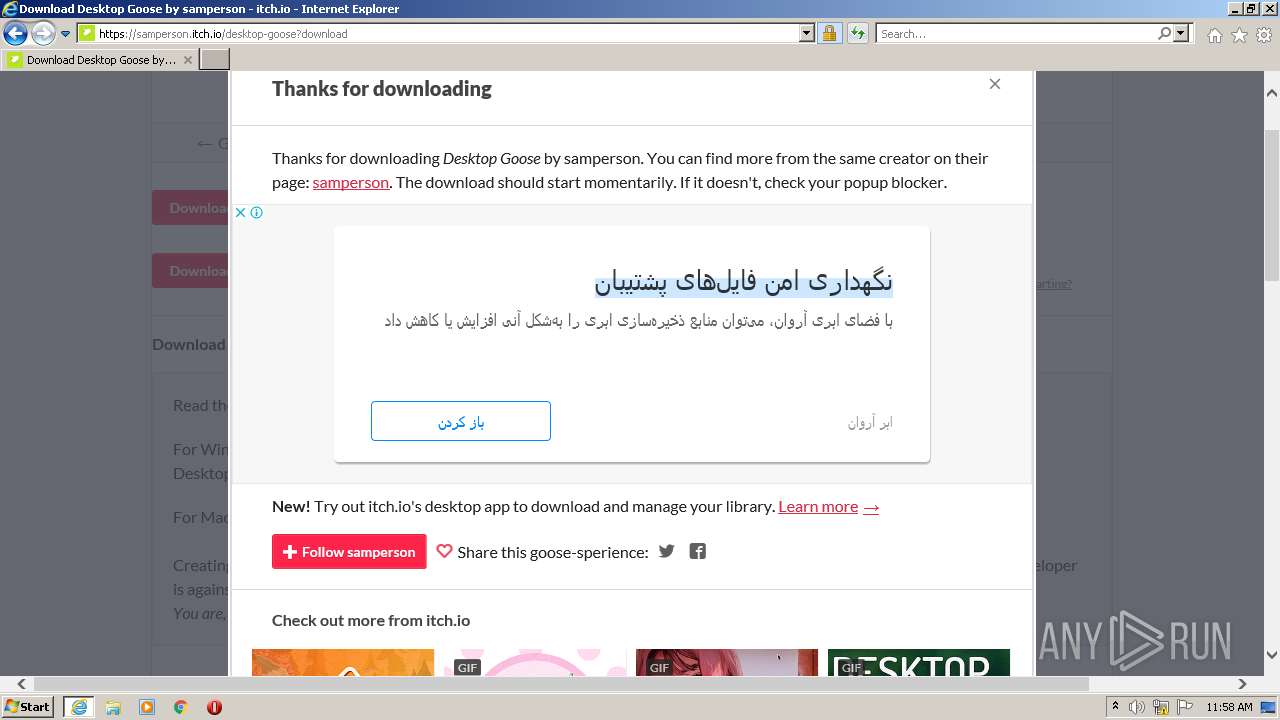
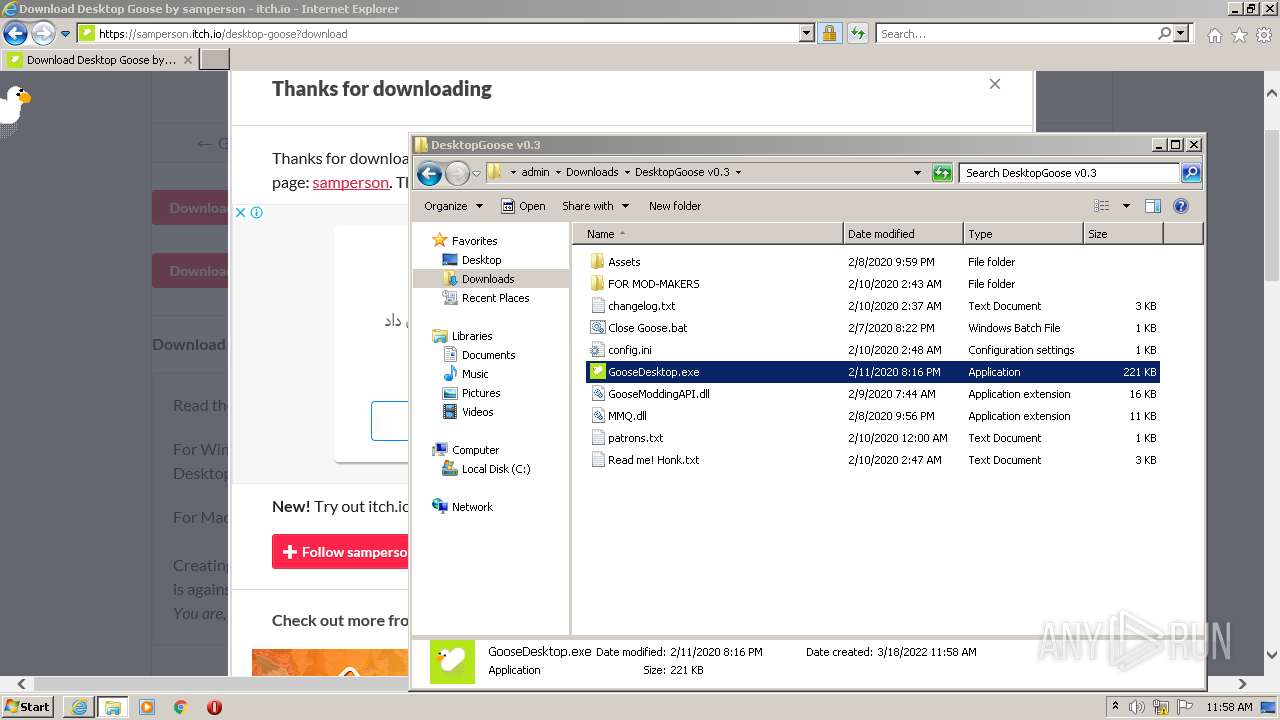
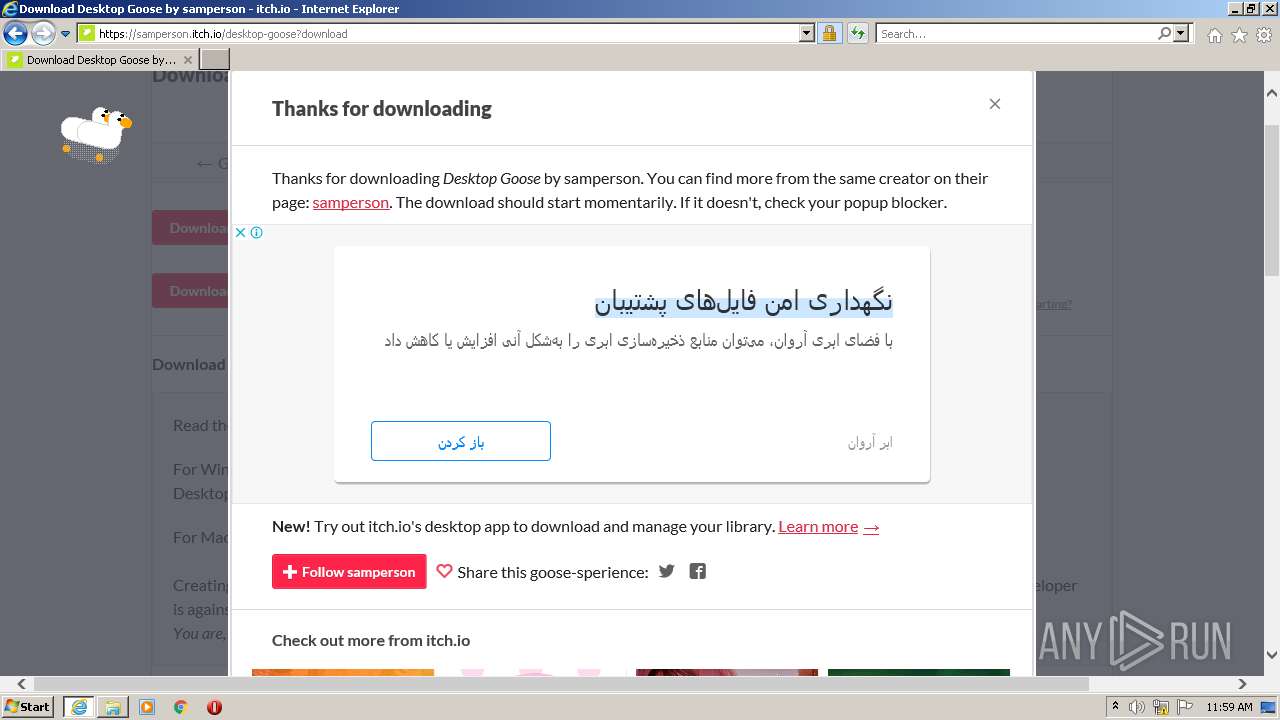
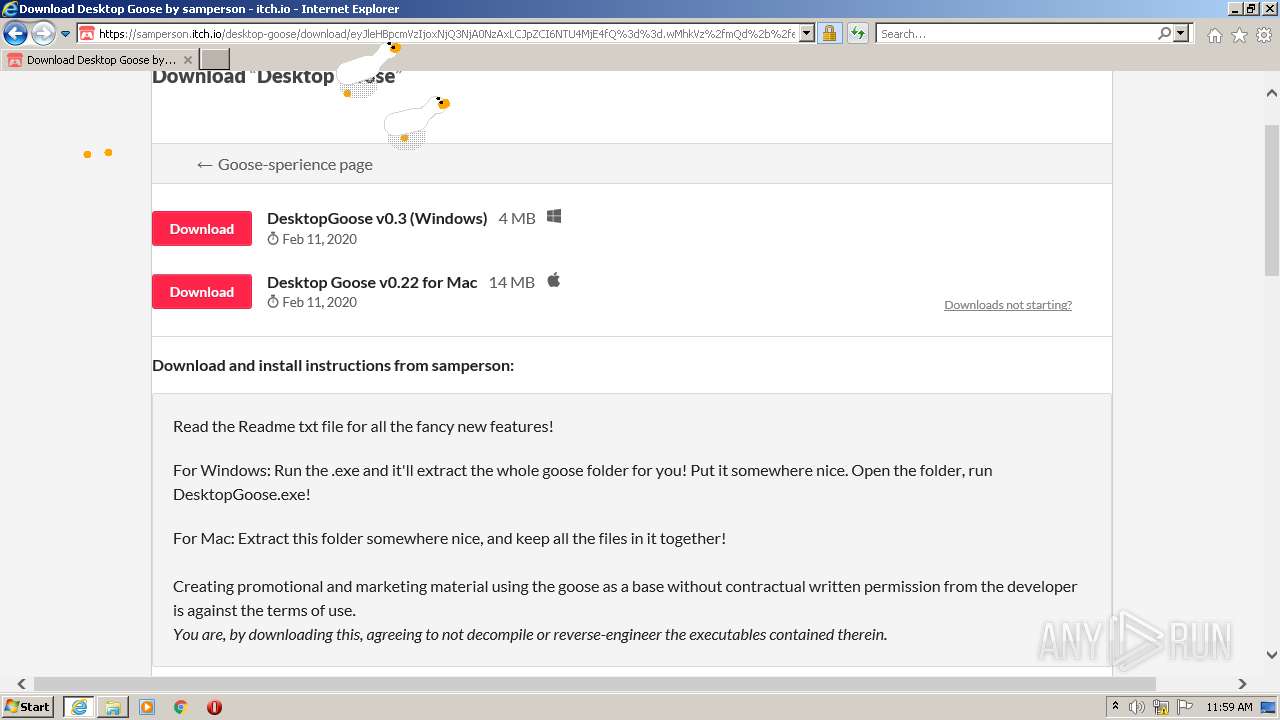
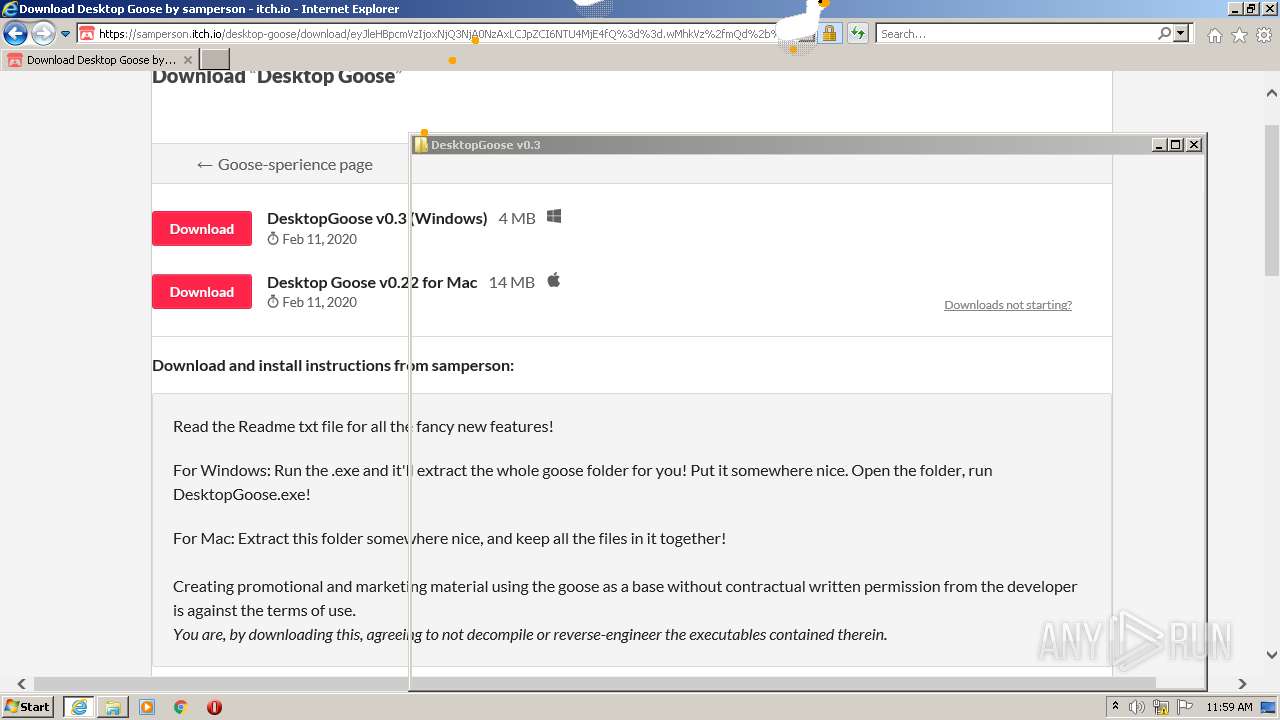
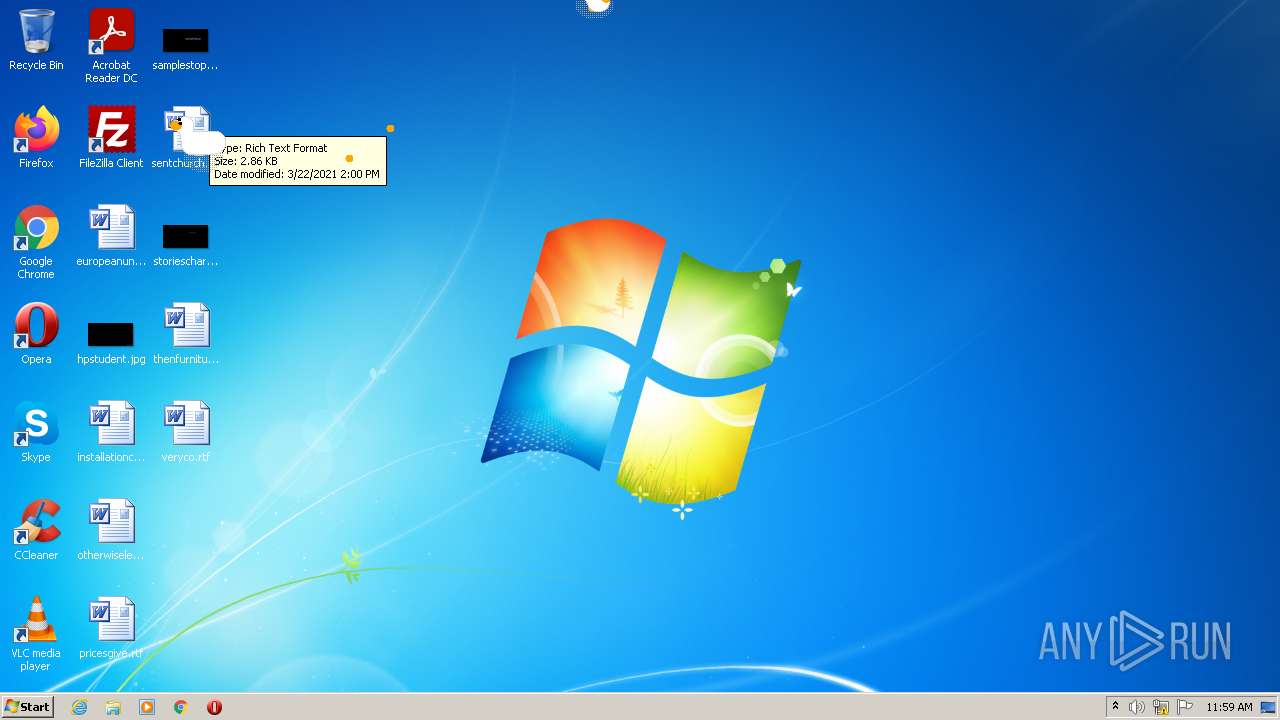
| URL: | http://samperson.itch.io/desktop-goose?download |
| Full analysis: | https://app.any.run/tasks/e52b91a4-3d83-40c4-a4f8-e97d7163ae47 |
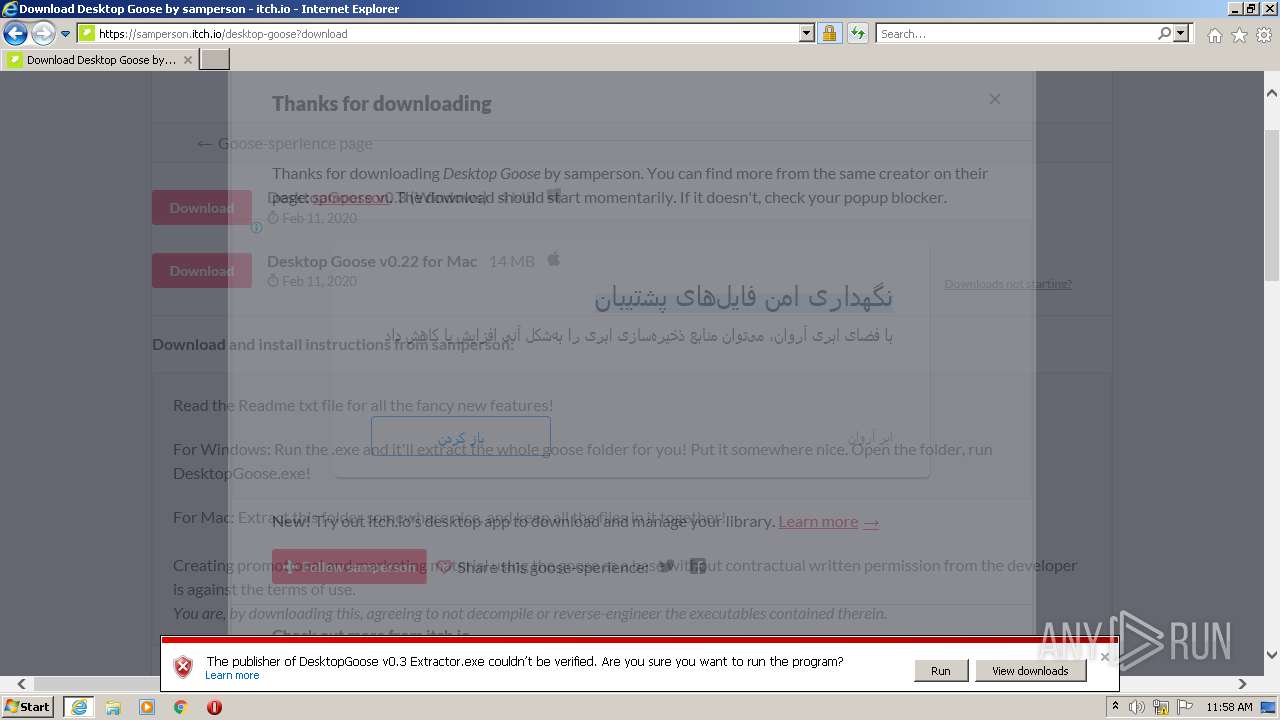
| Verdict: | Malicious activity |
| Analysis date: | March 18, 2022, 11:57:50 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 1379DB87A8D684935EDF34142E44AB1A |
| SHA1: | E7798951473BA61EEB78B8732911A069B7041856 |
| SHA256: | 6182843244EA847DAA0ABDF8CAE280EBC2B55102222C1A1235E577D3194E4B57 |
| SSDEEP: | 3:N1KNEI3e0z1VID9Ko:CWIz4 |
MALICIOUS
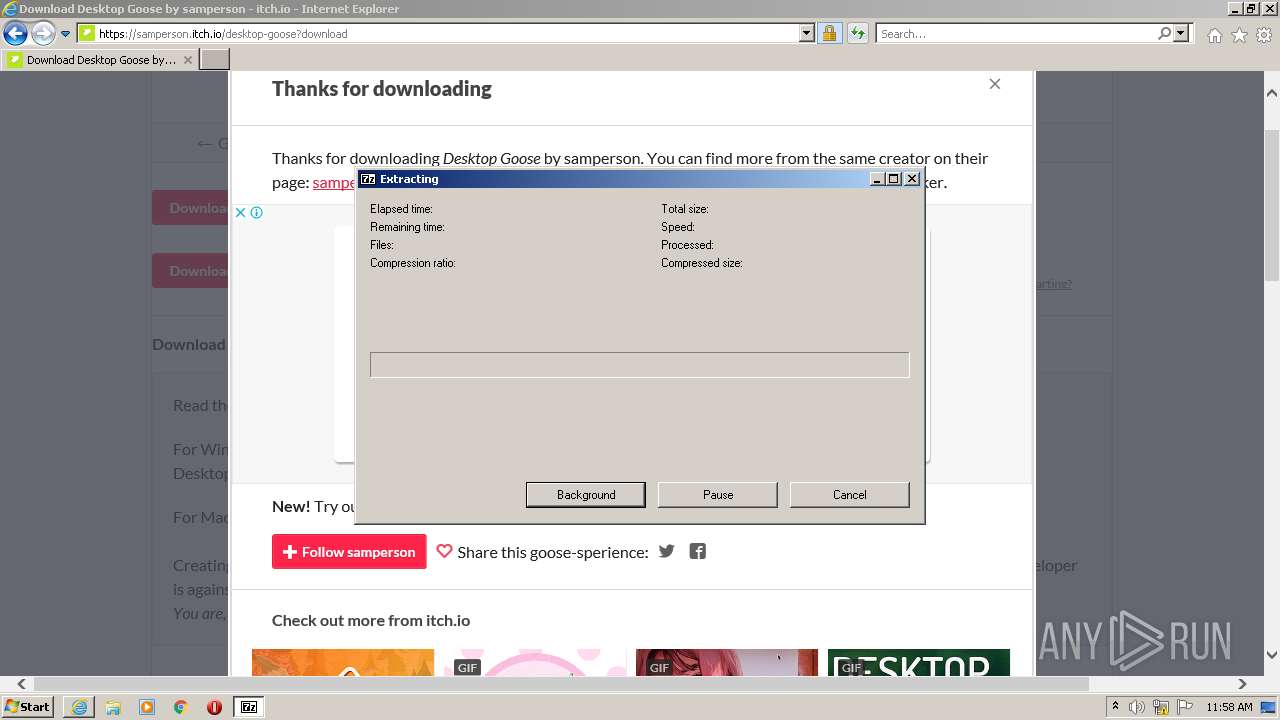
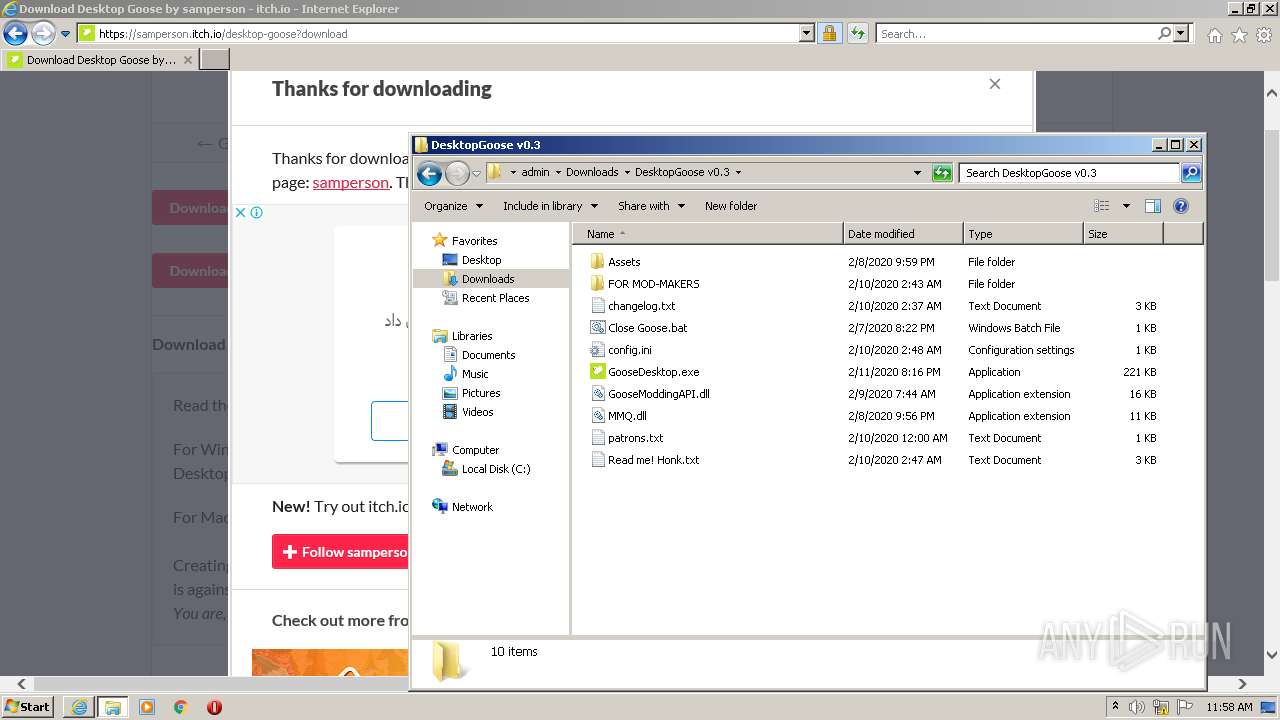
Loads dropped or rewritten executable
- SearchProtocolHost.exe (PID: 2228)
- GooseDesktop.exe (PID: 4060)
- GooseDesktop.exe (PID: 2096)
Application was dropped or rewritten from another process
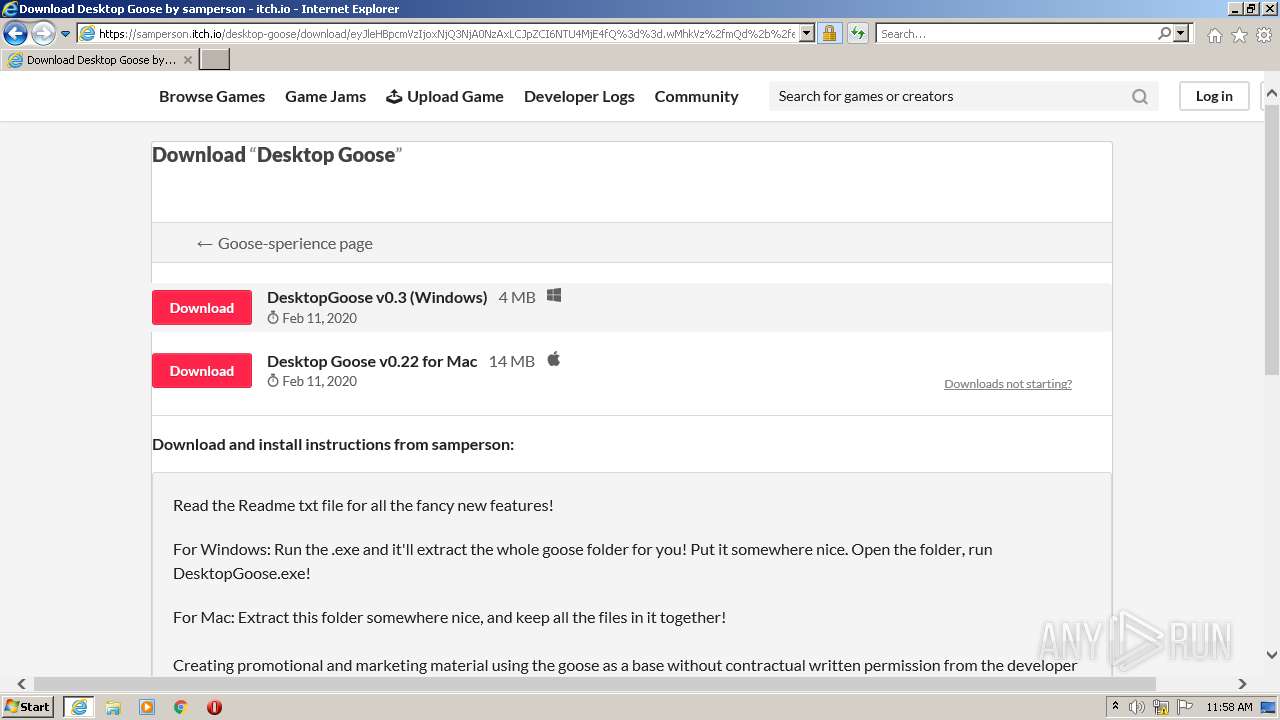
- DesktopGoose v0.3 Extractor.exe (PID: 3928)
- GooseDesktop.exe (PID: 4060)
- GooseDesktop.exe (PID: 2096)
SUSPICIOUS
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 532)
Checks supported languages
- FlashUtil32_32_0_0_453_ActiveX.exe (PID: 2460)
- DesktopGoose v0.3 Extractor.exe (PID: 3928)
- GooseDesktop.exe (PID: 4060)
- GooseDesktop.exe (PID: 2096)
Executed via COM
- FlashUtil32_32_0_0_453_ActiveX.exe (PID: 2460)
Reads the computer name
- FlashUtil32_32_0_0_453_ActiveX.exe (PID: 2460)
- DesktopGoose v0.3 Extractor.exe (PID: 3928)
- GooseDesktop.exe (PID: 4060)
- GooseDesktop.exe (PID: 2096)
Creates files in the user directory
- FlashUtil32_32_0_0_453_ActiveX.exe (PID: 2460)
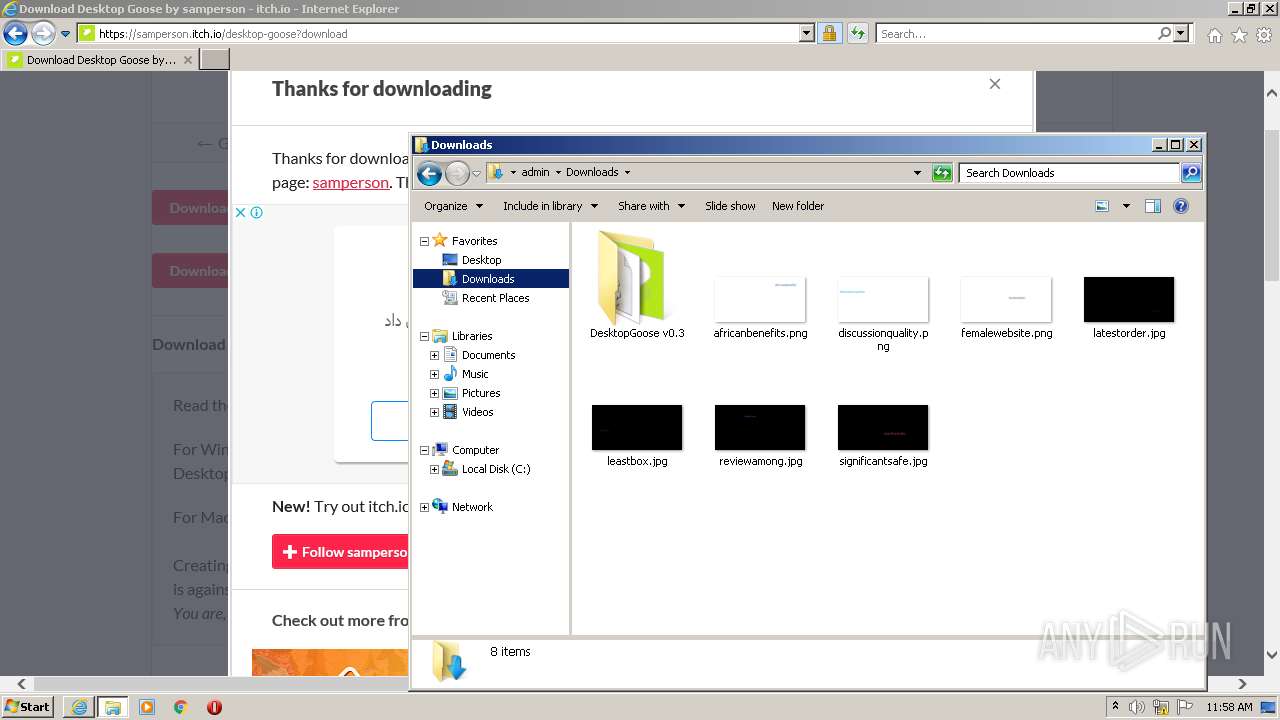
Executable content was dropped or overwritten
- iexplore.exe (PID: 2948)
- iexplore.exe (PID: 532)
- DesktopGoose v0.3 Extractor.exe (PID: 3928)
Drops a file that was compiled in debug mode
- DesktopGoose v0.3 Extractor.exe (PID: 3928)
INFO
Reads the computer name
- iexplore.exe (PID: 2948)
- iexplore.exe (PID: 532)
- explorer.exe (PID: 3192)
- explorer.exe (PID: 3996)
Checks supported languages
- iexplore.exe (PID: 532)
- iexplore.exe (PID: 2948)
- explorer.exe (PID: 3192)
- explorer.exe (PID: 3996)
- NOTEPAD.EXE (PID: 3804)
Reads settings of System Certificates
- iexplore.exe (PID: 532)
- iexplore.exe (PID: 2948)
Application launched itself
- iexplore.exe (PID: 2948)
Reads internet explorer settings
- iexplore.exe (PID: 532)
Changes settings of System certificates
- iexplore.exe (PID: 2948)
Checks Windows Trust Settings
- iexplore.exe (PID: 2948)
- iexplore.exe (PID: 532)
Changes internet zones settings
- iexplore.exe (PID: 2948)
Creates files in the user directory
- iexplore.exe (PID: 532)
- iexplore.exe (PID: 2948)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2948)
Reads CPU info
- iexplore.exe (PID: 532)
Modifies the phishing filter of IE
- iexplore.exe (PID: 2948)
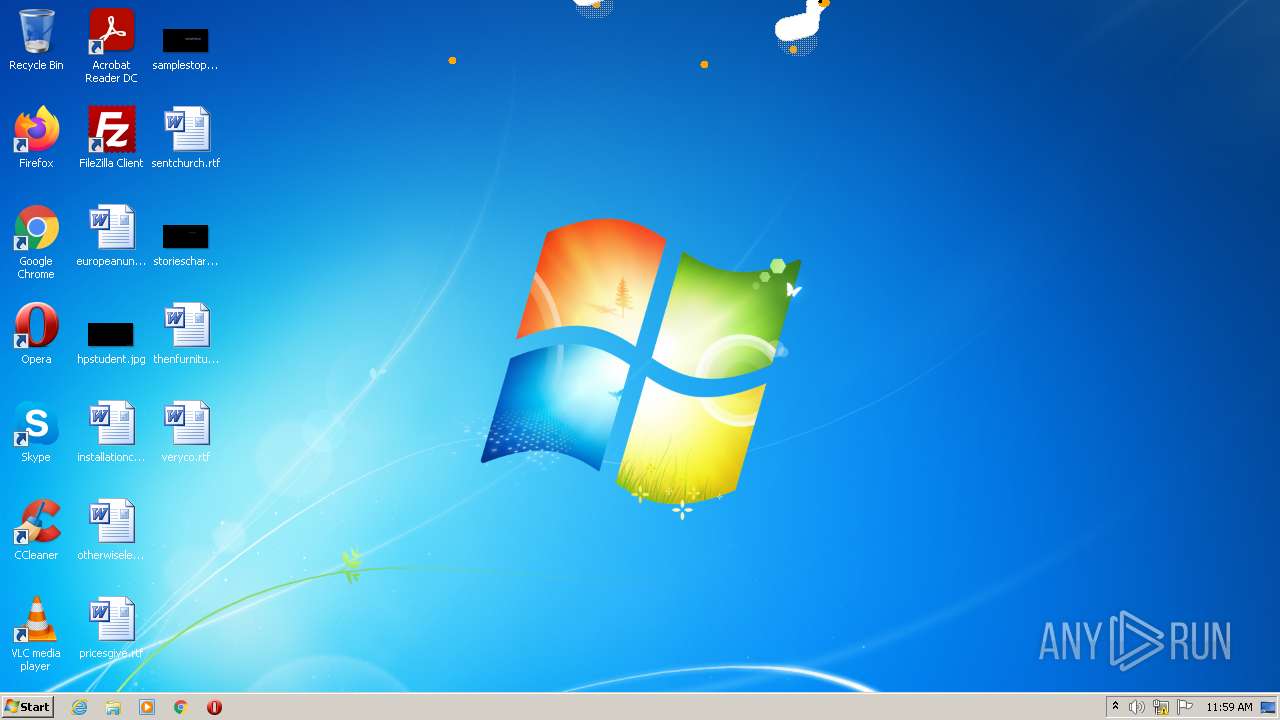
Manual execution by user
- explorer.exe (PID: 3192)
- GooseDesktop.exe (PID: 4060)
- GooseDesktop.exe (PID: 2096)
- explorer.exe (PID: 3996)
- NOTEPAD.EXE (PID: 3804)
Reads the date of Windows installation
- iexplore.exe (PID: 2948)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
48
Monitored processes
10
Malicious processes
4
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
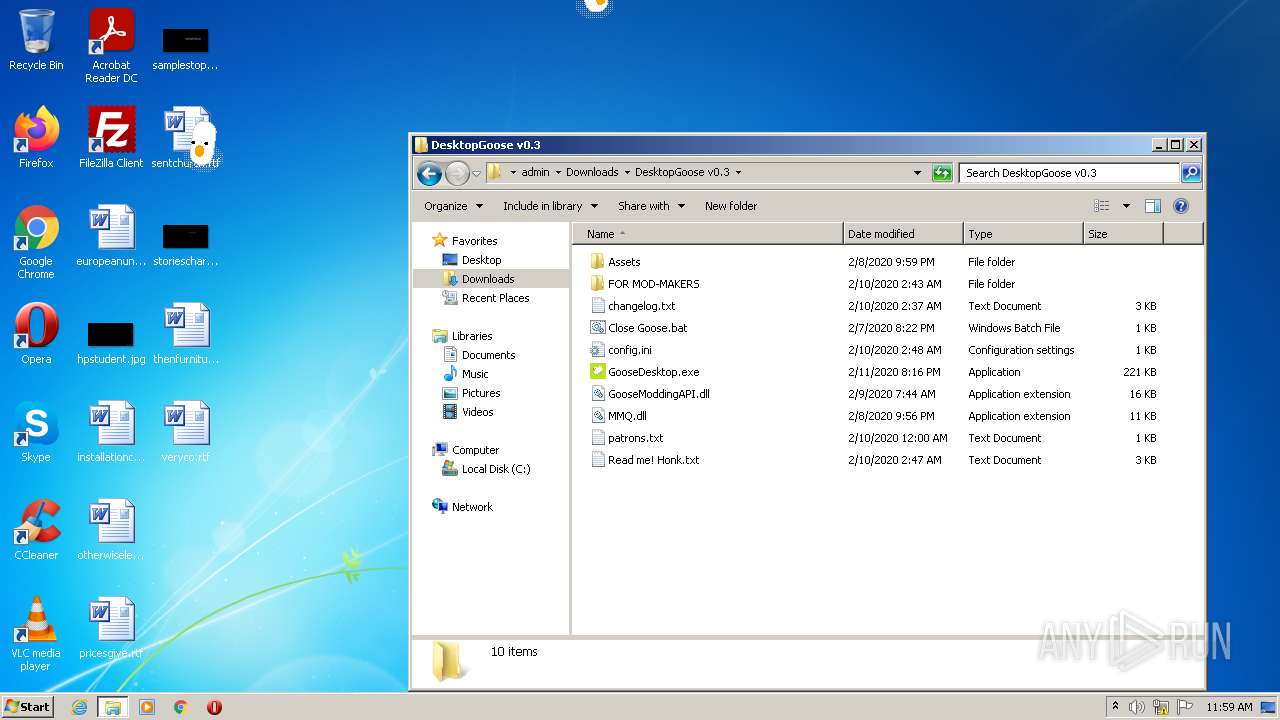
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 532 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2948 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
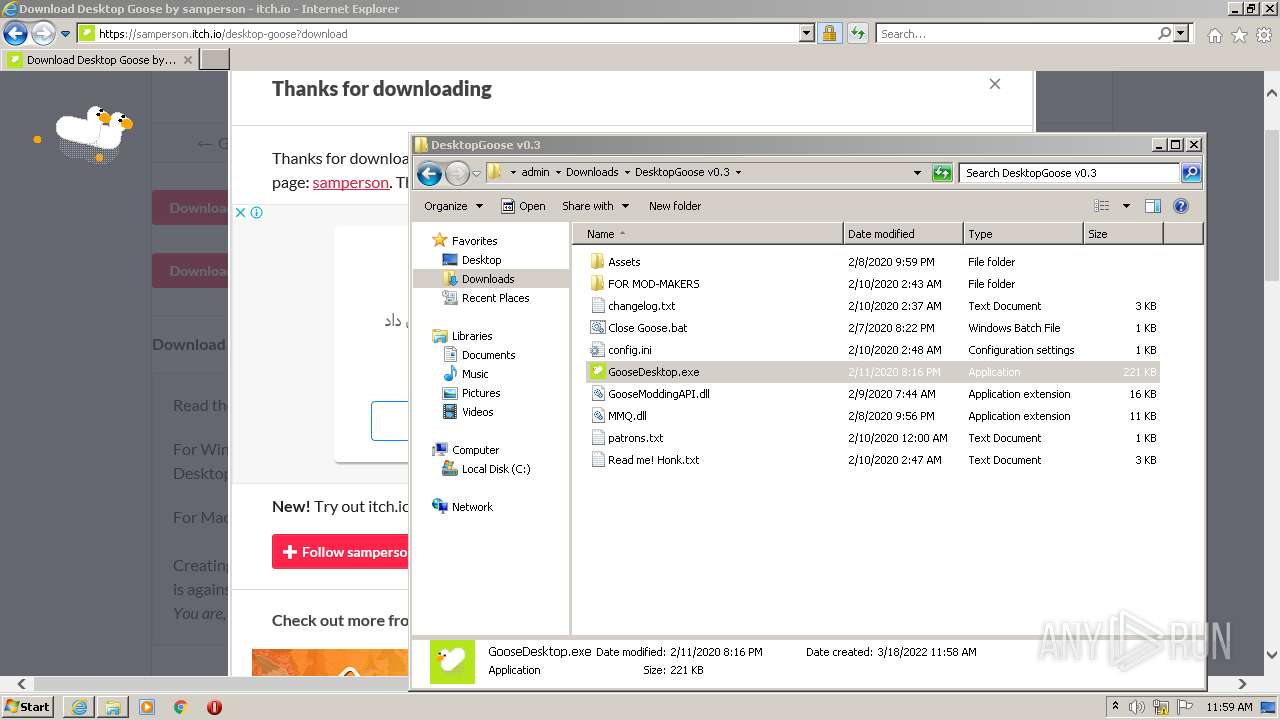
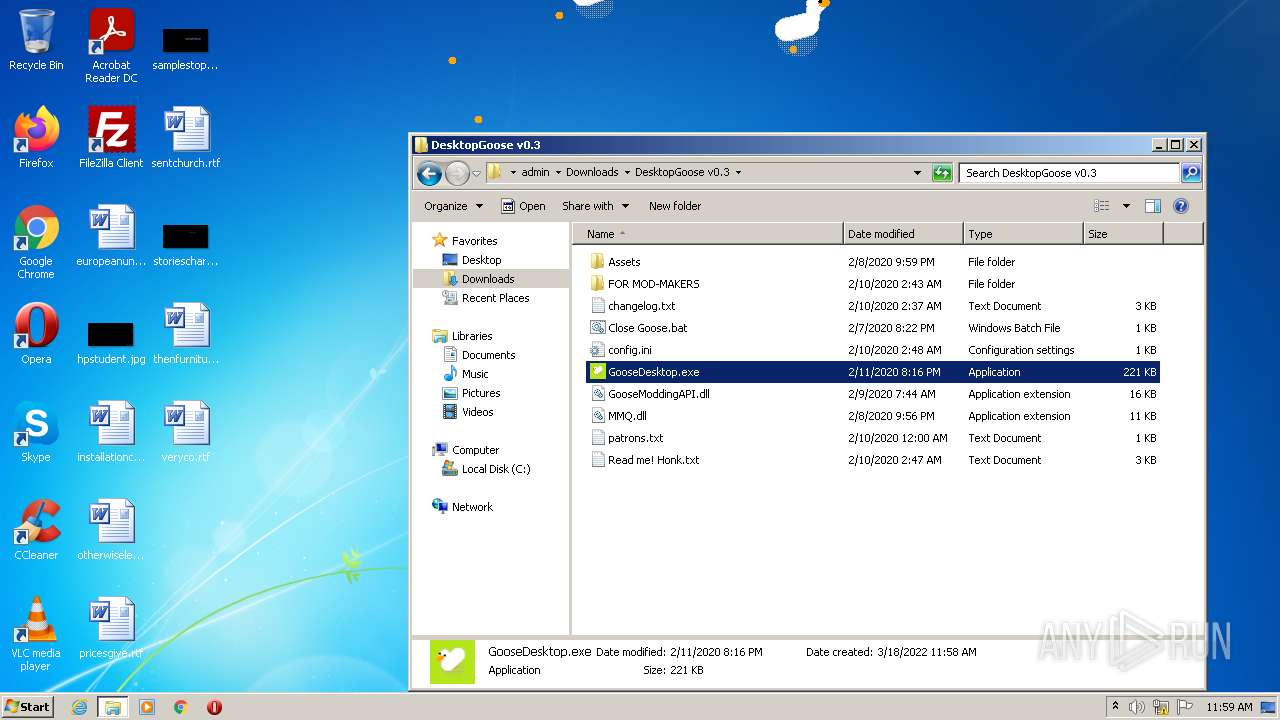
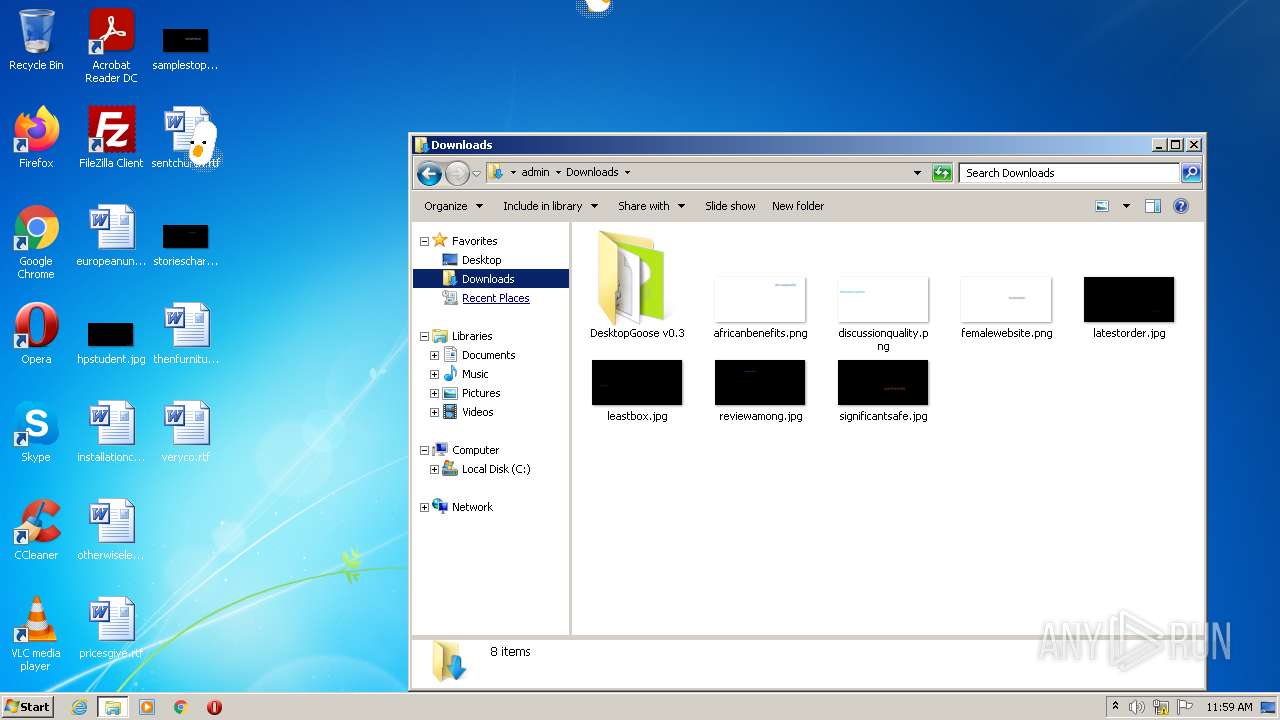
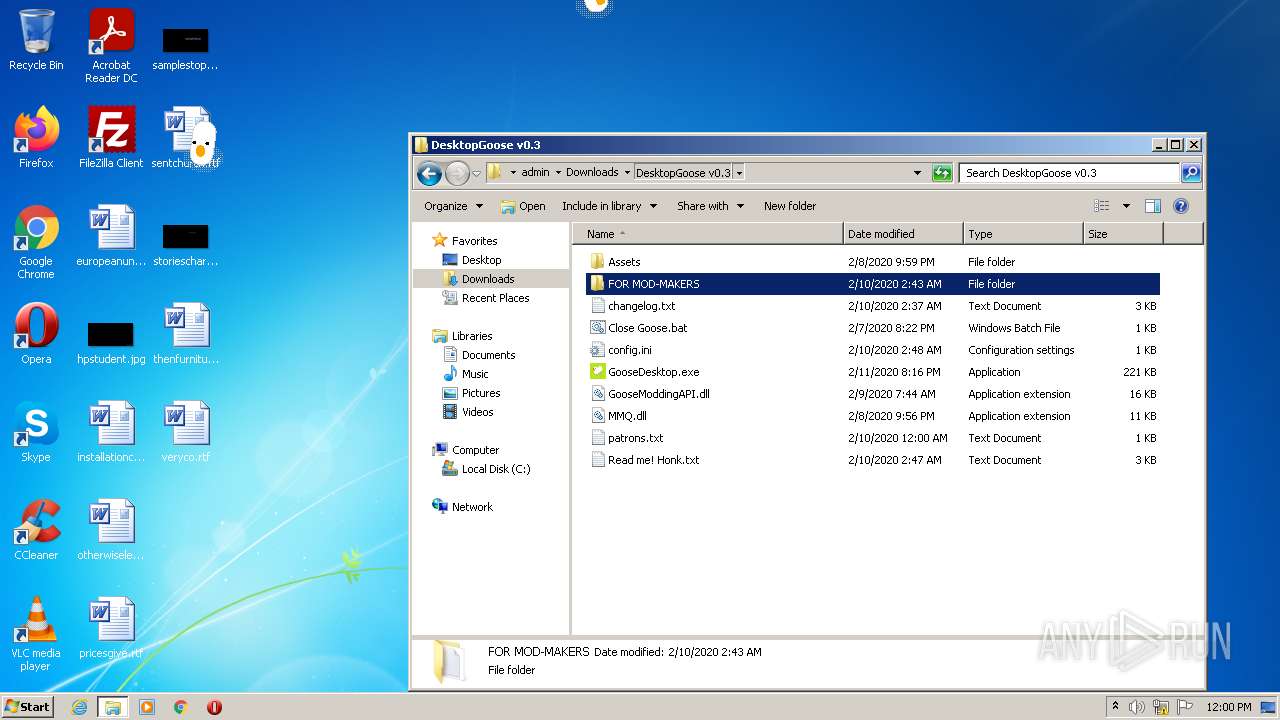
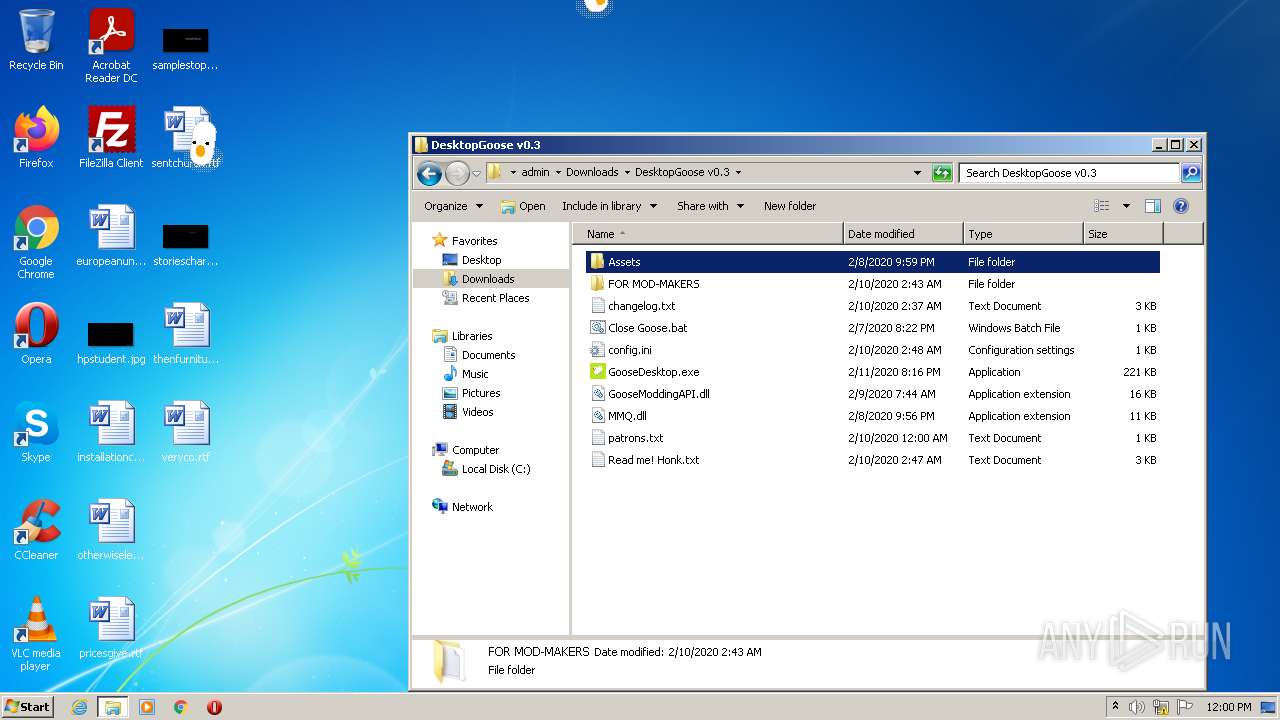
| 2096 | "C:\Users\admin\Downloads\DesktopGoose v0.3\GooseDesktop.exe" | C:\Users\admin\Downloads\DesktopGoose v0.3\GooseDesktop.exe | — | Explorer.EXE | |||||||||||
User: admin Integrity Level: MEDIUM Description: GooseDesktop Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 2228 | "C:\Windows\system32\SearchProtocolHost.exe" Global\UsGthrFltPipeMssGthrPipe2_ Global\UsGthrCtrlFltPipeMssGthrPipe2 1 -2147483646 "Software\Microsoft\Windows Search" "Mozilla/4.0 (compatible; MSIE 6.0; Windows NT; MS Search 4.0 Robot)" "C:\ProgramData\Microsoft\Search\Data\Temp\usgthrsvc" "DownLevelDaemon" | C:\Windows\system32\SearchProtocolHost.exe | — | SearchIndexer.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Windows Search Protocol Host Exit code: 0 Version: 7.00.7601.24542 (win7sp1_ldr_escrow.191209-2211) Modules
| |||||||||||||||
| 2460 | C:\Windows\system32\Macromed\Flash\FlashUtil32_32_0_0_453_ActiveX.exe -Embedding | C:\Windows\system32\Macromed\Flash\FlashUtil32_32_0_0_453_ActiveX.exe | — | svchost.exe | |||||||||||
User: admin Company: Adobe Integrity Level: MEDIUM Description: Adobe� Flash� Player Installer/Uninstaller 32.0 r0 Exit code: 0 Version: 32,0,0,453 Modules
| |||||||||||||||
| 2948 | "C:\Program Files\Internet Explorer\iexplore.exe" "http://samperson.itch.io/desktop-goose?download" | C:\Program Files\Internet Explorer\iexplore.exe | Explorer.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3192 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
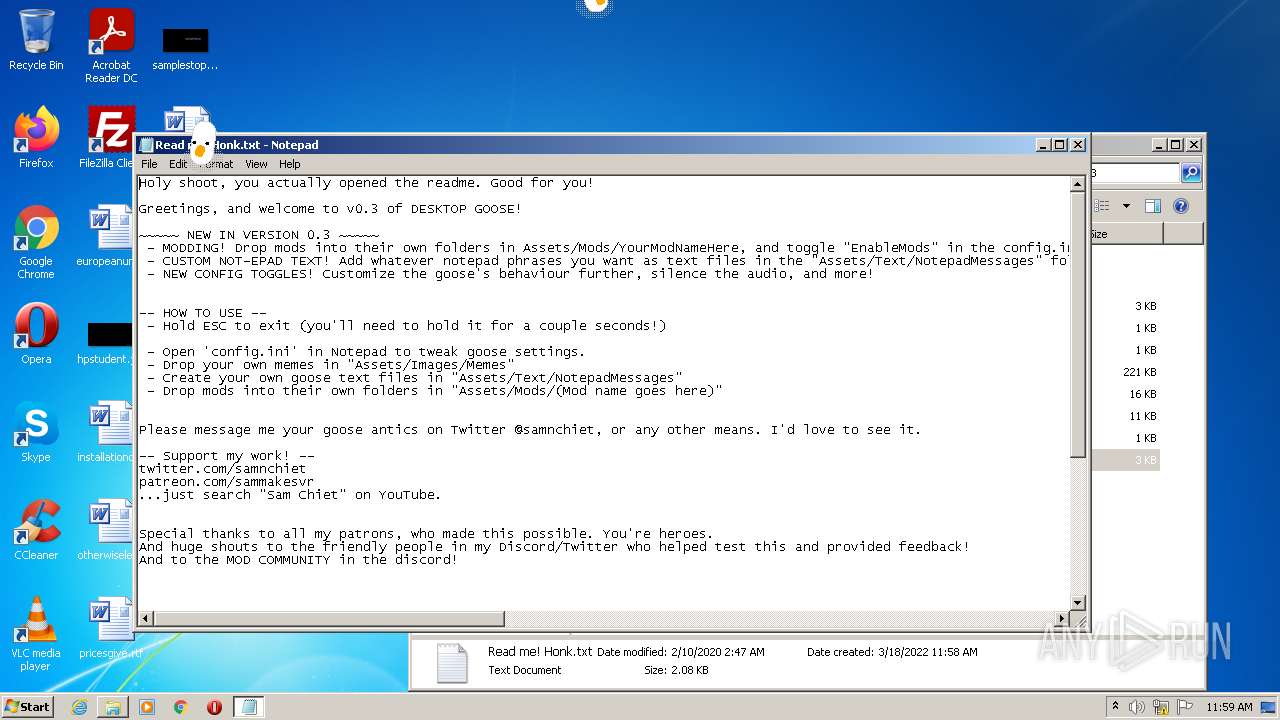
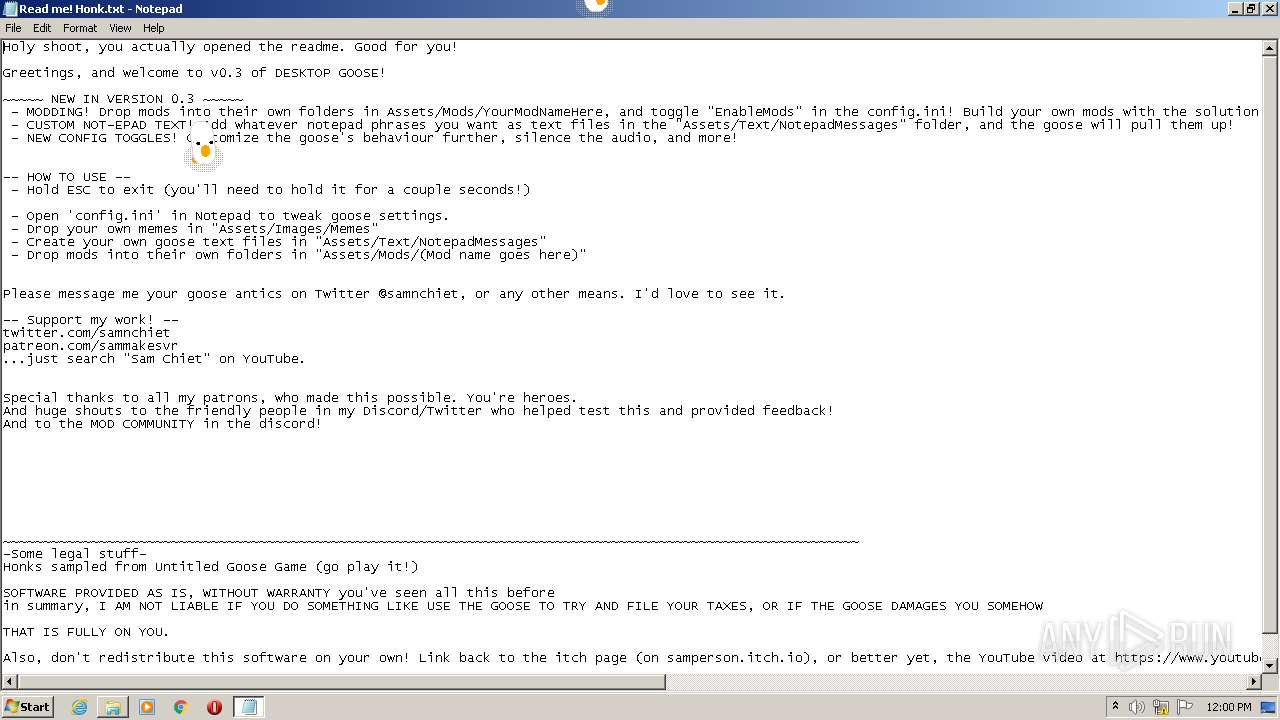
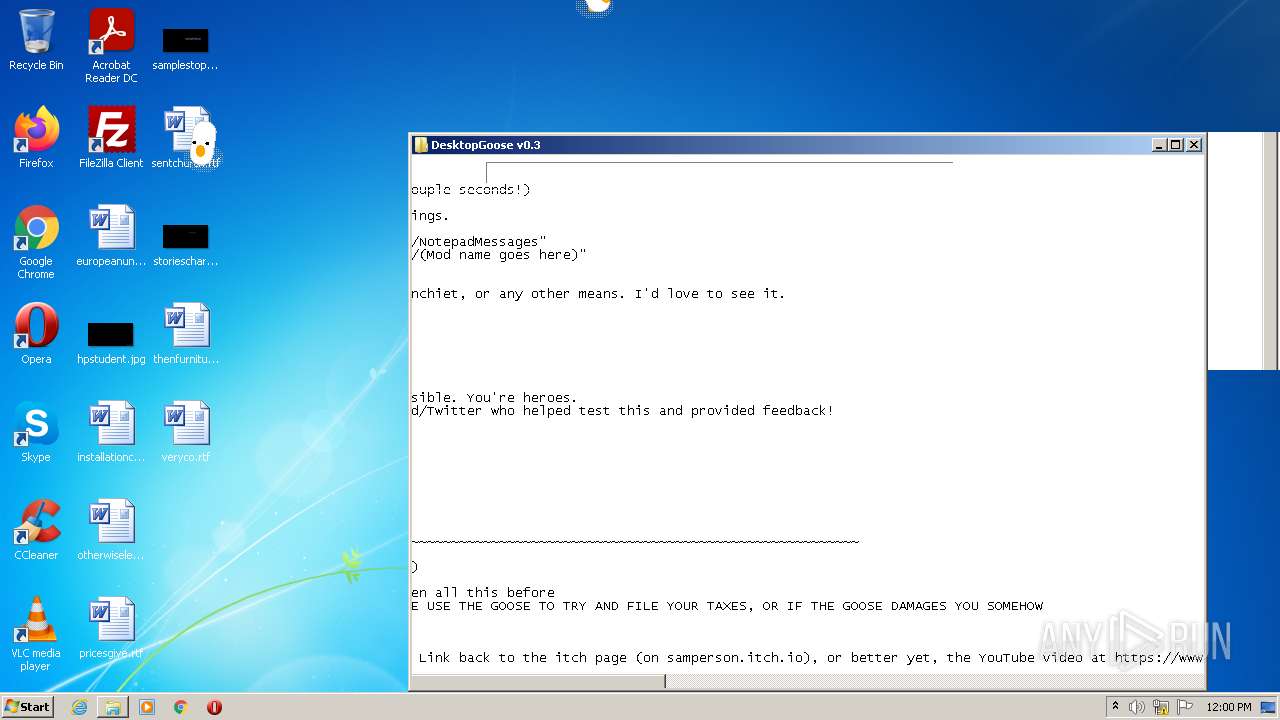
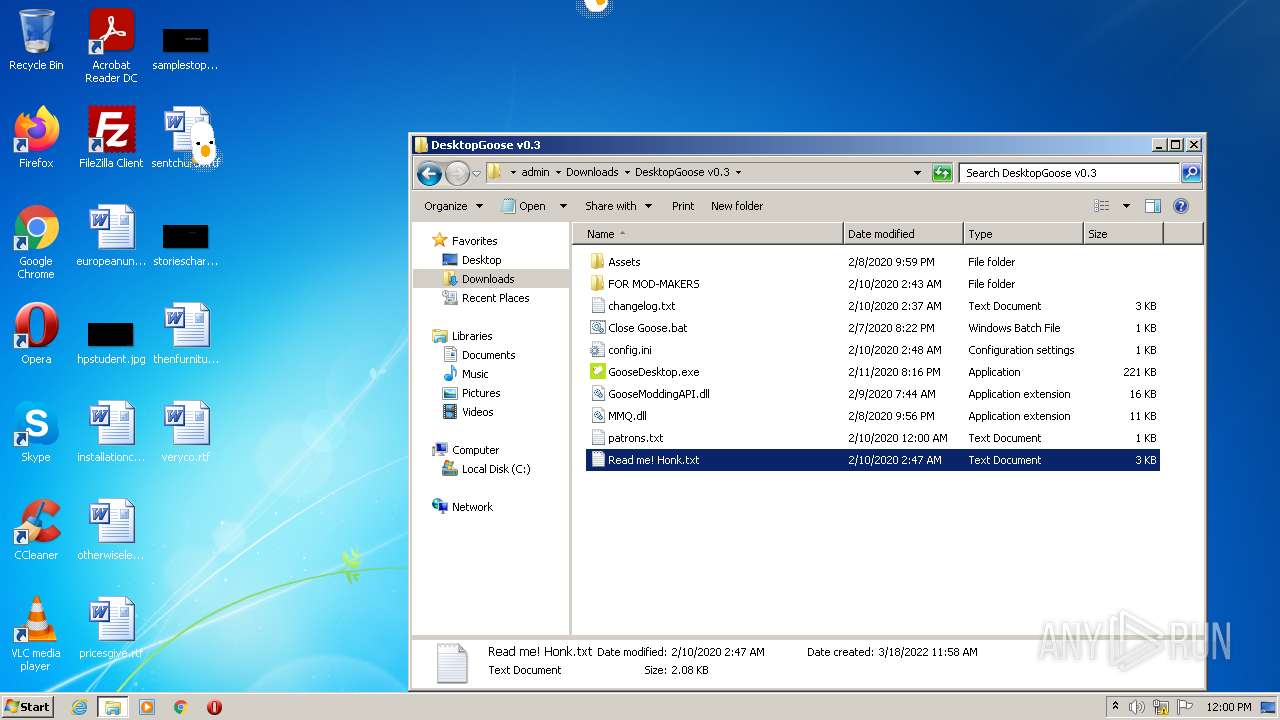
| 3804 | "C:\Windows\system32\NOTEPAD.EXE" C:\Users\admin\Downloads\DesktopGoose v0.3\Read me! Honk.txt | C:\Windows\system32\NOTEPAD.EXE | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
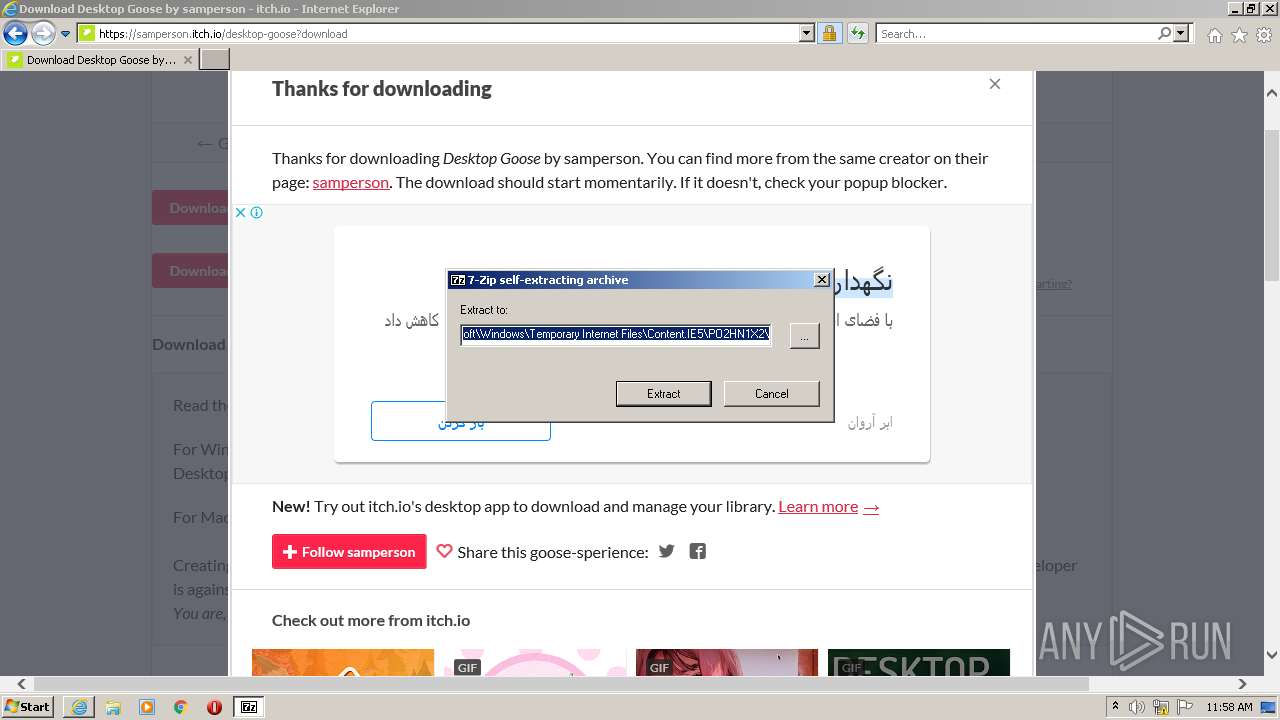
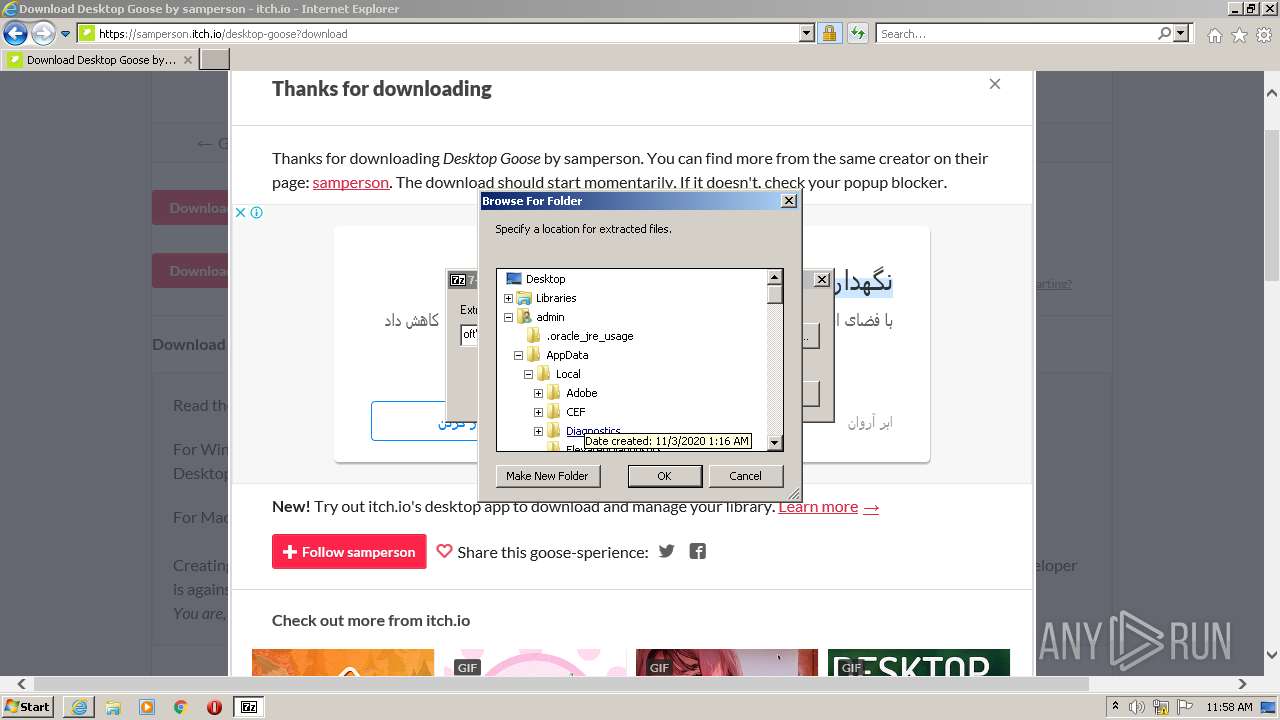
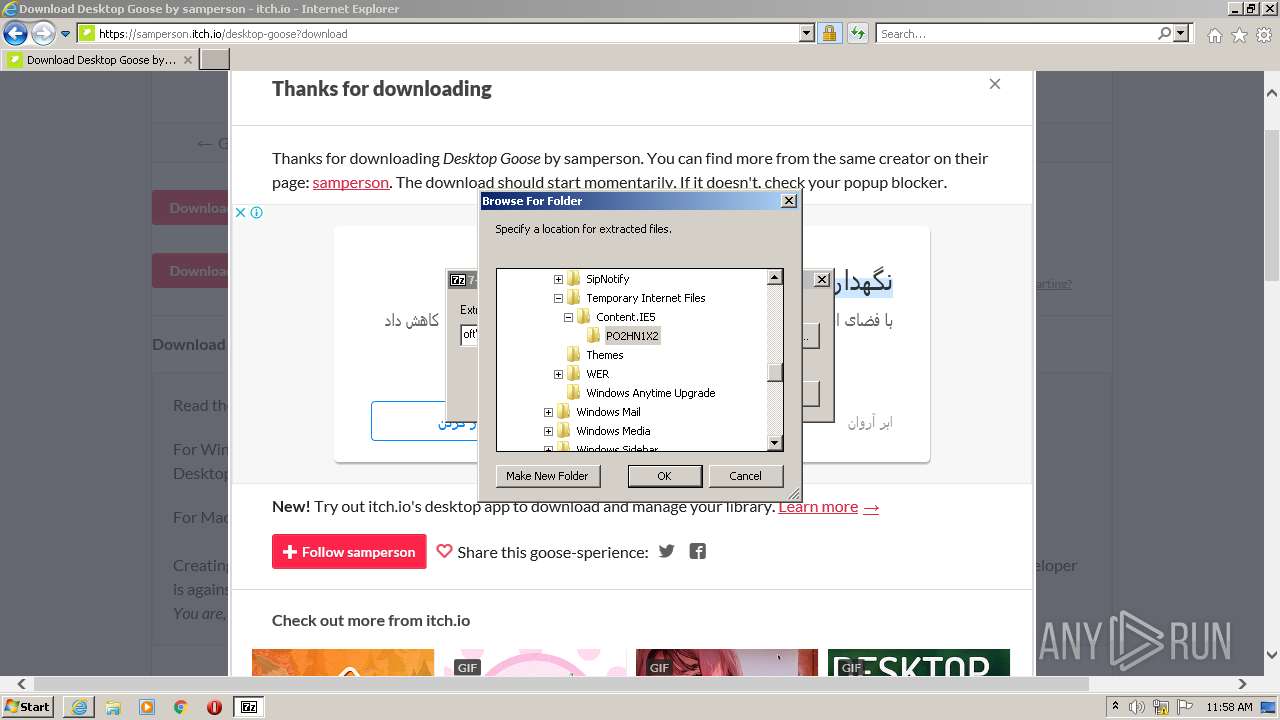
| |||||||||||||||
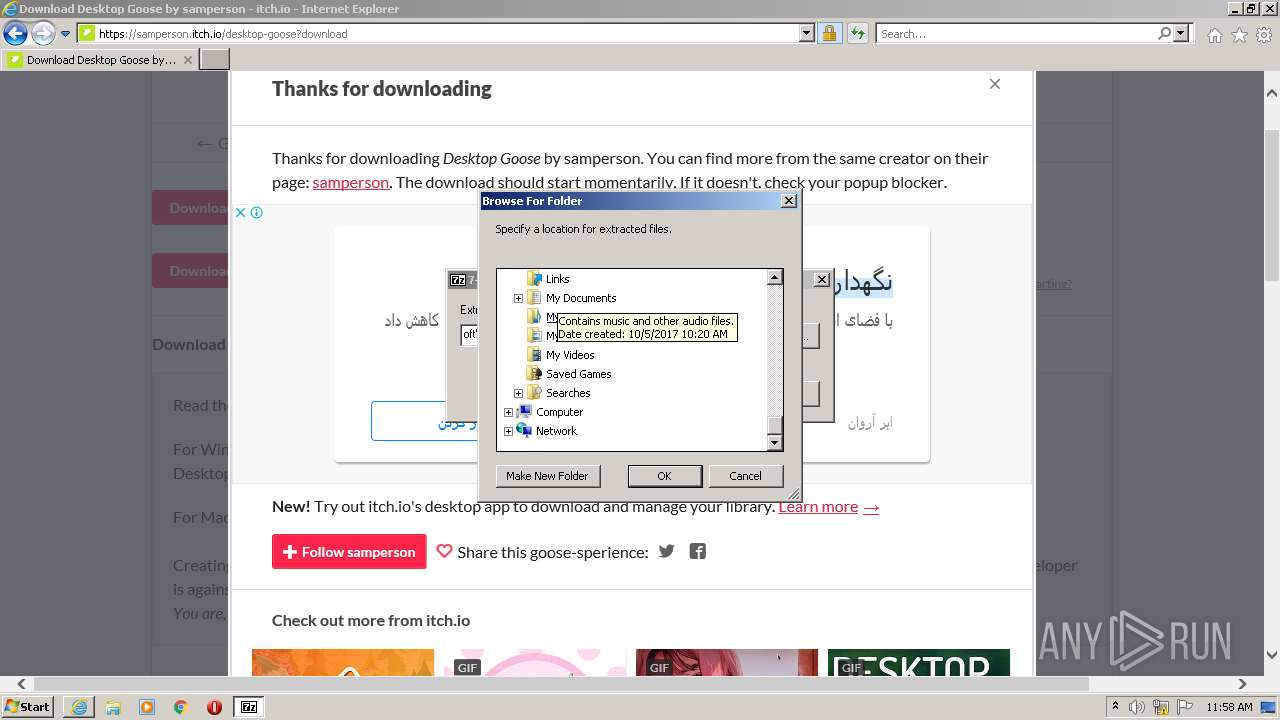
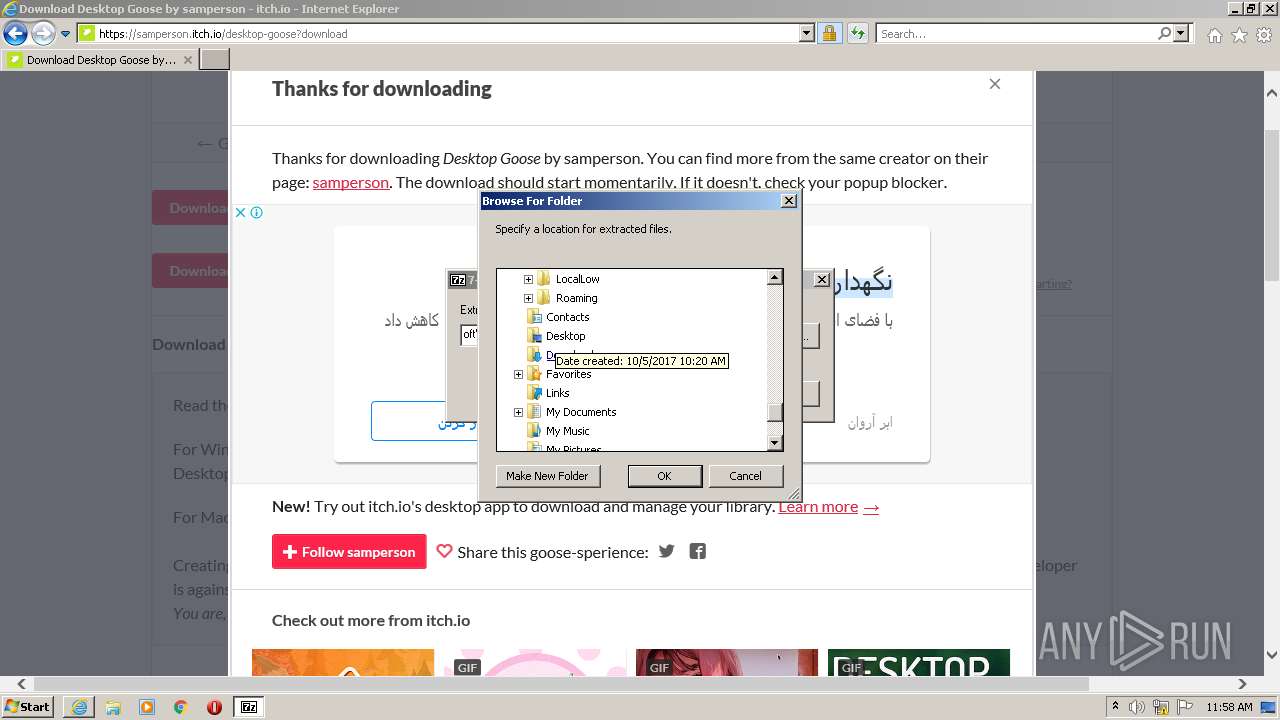
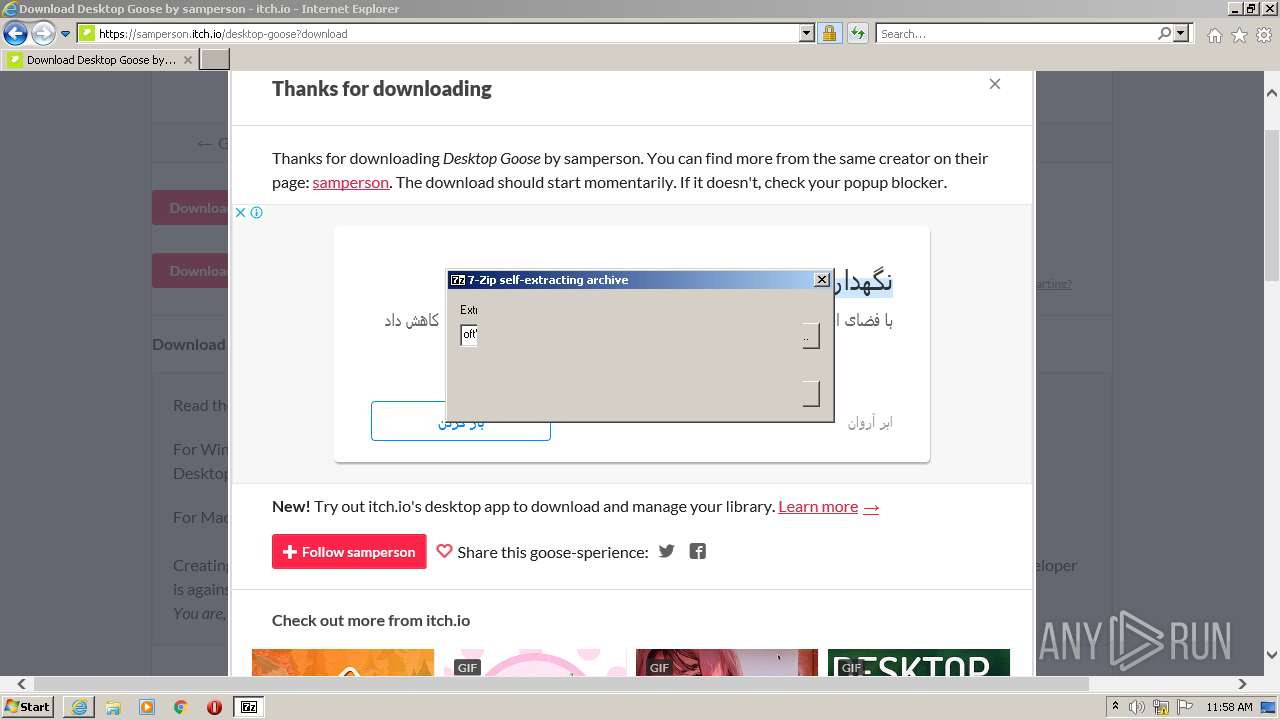
| 3928 | "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\PO2HN1X2\DesktopGoose v0.3 Extractor.exe" | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\PO2HN1X2\DesktopGoose v0.3 Extractor.exe | iexplore.exe | ||||||||||||
User: admin Company: Igor Pavlov Integrity Level: MEDIUM Description: 7z SFX Exit code: 0 Version: 19.00 Modules
| |||||||||||||||
| 3996 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 4060 | "C:\Users\admin\Downloads\DesktopGoose v0.3\GooseDesktop.exe" | C:\Users\admin\Downloads\DesktopGoose v0.3\GooseDesktop.exe | — | Explorer.EXE | |||||||||||
User: admin Integrity Level: MEDIUM Description: GooseDesktop Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
Total events
23 490
Read events
23 151
Write events
330
Delete events
9
Modification events
| (PID) Process: | (2948) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (2948) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: | |||
| (PID) Process: | (2948) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30948031 | |||
| (PID) Process: | (2948) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (2948) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30948031 | |||
| (PID) Process: | (2948) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2948) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2948) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2948) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2948) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
12
Suspicious files
49
Text files
181
Unknown types
58
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 532 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\07CEF2F654E3ED6050FFC9B6EB844250_3431D4C539FB2CFCB781821E9902850D | binary | |
MD5:0CCDC286C3648D79DB526451C1673158 | SHA256:006F6A08CE9349D13609A5FBF9B167A2CD232E6C0B502A6C76AE5C5CC7DD22C3 | |||
| 532 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\873B83631F5C07363DB932ADBDC91A7B | der | |
MD5:1595D45BFB45C9AA078D65D8FF34289E | SHA256:EA6135DA0EFAE5B5DD57E22DFCE0DF6014BA04CE54AF0F860C3D3DA66E73E955 | |||
| 532 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\07CEF2F654E3ED6050FFC9B6EB844250_3431D4C539FB2CFCB781821E9902850D | der | |
MD5:100637164E14CBC20A73958563773D1B | SHA256:751C2B661EC636DF41A0C6E9C9AB0F72E74B9839D6CCD18FE3DD749B722F5270 | |||
| 532 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\B2FAF7692FD9FFBD64EDE317E42334BA_D7393C8F62BDE4D4CB606228BC7A711E | der | |
MD5:4E4CBB8D2687E2100CC42A336C0BD6C9 | SHA256:FB358F1675D44E282D9650712E70CBB5669900780CC5D96F5D3F105227AE10A3 | |||
| 532 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\77EC63BDA74BD0D0E0426DC8F8008506 | compressed | |
MD5:637481DF32351129E60560D5A5C100B5 | SHA256:1F1029D94CA4656A577D554CEDD79D447658F475AF08620084897A5523587052 | |||
| 532 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\game.min[1].js | text | |
MD5:6318203D519F1F8332AEFD35AC1A58AA | SHA256:21D12A7040BE7F1425D4E1C9C685D400CA7F75FE95CA6B257D8EE53DD5014713 | |||
| 532 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\TarE2FA.tmp | cat | |
MD5:30644DA711C99BE812B06023C163B751 | SHA256:96DBA3D67364C1E75DAB241D4A023B48F4D6453F495175B210F525E930CF144B | |||
| 532 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\6BADA8974A10C4BD62CC921D13E43B18_28DEA62A0AE77228DD387E155AD0BA27 | binary | |
MD5:B2533C846D79123694C609D6E6870290 | SHA256:D22DB9F6B41D3768E63633A8A9DA59E09B003456680A398B03CE2465176444F6 | |||
| 532 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\5IWPIAR9\desktop-goose[1].htm | html | |
MD5:81B27C966CA7762ECD685A0200C87EE8 | SHA256:8F0C023EC8F106324096016EF8618C781D5C175A87543ECBCC69A28A54FE5493 | |||
| 532 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\B2FAF7692FD9FFBD64EDE317E42334BA_D7393C8F62BDE4D4CB606228BC7A711E | binary | |
MD5:B48464F1CCEEAB61E251572DE3B0FE3A | SHA256:4E694C807A2957FA06EF810AFEDEBFF9D8883B1B604A86264E39D8C1F4E38A0A | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
29
TCP/UDP connections
113
DNS requests
37
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
532 | iexplore.exe | GET | 301 | 173.255.250.29:80 | http://samperson.itch.io/desktop-goose?download | US | html | 166 b | suspicious |
532 | iexplore.exe | GET | 200 | 104.18.31.182:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRTtU9uFqgVGHhJwXZyWCNXmVR5ngQUoBEKIz6W8Qfs4q8p74Klf9AwpLQCEDlyRDr5IrdR19NsEN0xNZU%3D | US | der | 471 b | whitelisted |
532 | iexplore.exe | GET | 200 | 104.18.30.182:80 | http://ocsp.usertrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTNMNJMNDqCqx8FcBWK16EHdimS6QQUU3m%2FWqorSs9UgOHYm8Cd8rIDZssCEH1bUSa0droR23QWC7xTDac%3D | US | der | 727 b | whitelisted |
532 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEAo3h2ReX7SMIk79G%2B0UDDw%3D | US | der | 1.47 Kb | whitelisted |
532 | iexplore.exe | GET | — | 142.250.186.131:80 | http://ocsp.pki.goog/gts1c3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEFpGXT%2Blo3bTEgAAAAAETeY%3D | US | — | — | whitelisted |
532 | iexplore.exe | GET | 200 | 209.197.3.8:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?12e657623403473e | US | compressed | 4.70 Kb | whitelisted |
532 | iexplore.exe | GET | 200 | 104.18.31.182:80 | http://ocsp.sectigo.com/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRDC9IOTxN6GmyRjyTl2n4yTUczyAQUjYxexFStiuF36Zv5mwXhuAGNYeECEQC09QjW2pAyQ%2Bc%2FbOIo9ugF | US | der | 472 b | whitelisted |
532 | iexplore.exe | GET | — | 142.250.186.131:80 | http://ocsp.pki.goog/gts1c3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEFpGXT%2Blo3bTEgAAAAAETeY%3D | US | — | — | whitelisted |
532 | iexplore.exe | GET | 200 | 142.250.186.131:80 | http://ocsp.pki.goog/gts1c3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEFJXl5%2FOUoVICgAAAAE3h2s%3D | US | der | 471 b | whitelisted |
2948 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8Ull8gIGmZT9XHrHiJQeI%3D | US | der | 1.47 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
532 | iexplore.exe | 173.255.250.29:80 | samperson.itch.io | Linode, LLC | US | suspicious |
532 | iexplore.exe | 173.255.250.29:443 | samperson.itch.io | Linode, LLC | US | suspicious |
532 | iexplore.exe | 104.26.9.198:443 | static.itch.io | Cloudflare Inc | US | unknown |
532 | iexplore.exe | 69.16.175.42:443 | img.itch.zone | Highwinds Network Group, Inc. | US | malicious |
532 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
532 | iexplore.exe | 142.250.184.238:443 | www.youtube.com | Google Inc. | US | whitelisted |
532 | iexplore.exe | 142.251.39.110:443 | www.google-analytics.com | Google Inc. | US | whitelisted |
532 | iexplore.exe | 104.89.32.83:80 | x1.c.lencr.org | Akamai Technologies, Inc. | NL | suspicious |
532 | iexplore.exe | 142.250.181.246:443 | i.ytimg.com | Google Inc. | US | unknown |
532 | iexplore.exe | 142.250.186.131:80 | ocsp.pki.goog | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
samperson.itch.io |
| suspicious |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.comodoca.com |
| whitelisted |
ocsp.usertrust.com |
| whitelisted |
ocsp.sectigo.com |
| whitelisted |
static.itch.io |
| whitelisted |
img.itch.zone |
| malicious |
ocsp.digicert.com |
| whitelisted |
www.google-analytics.com |
| whitelisted |
www.youtube.com |
| whitelisted |