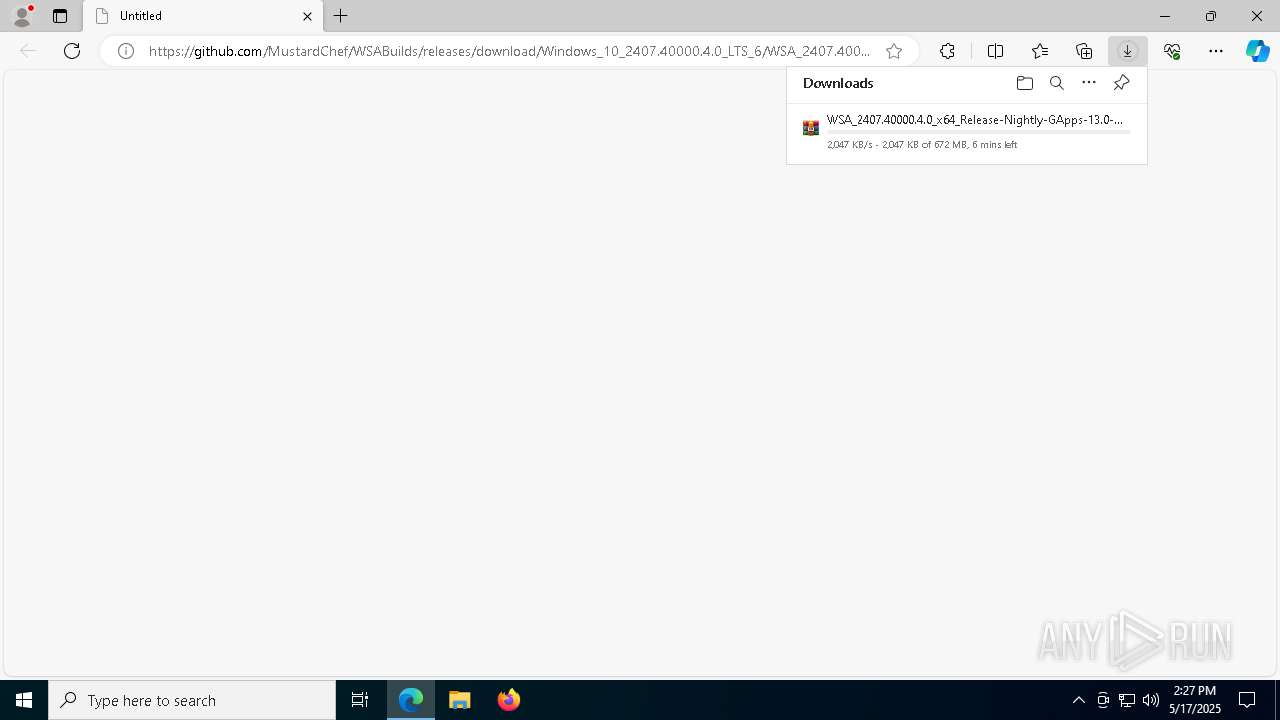
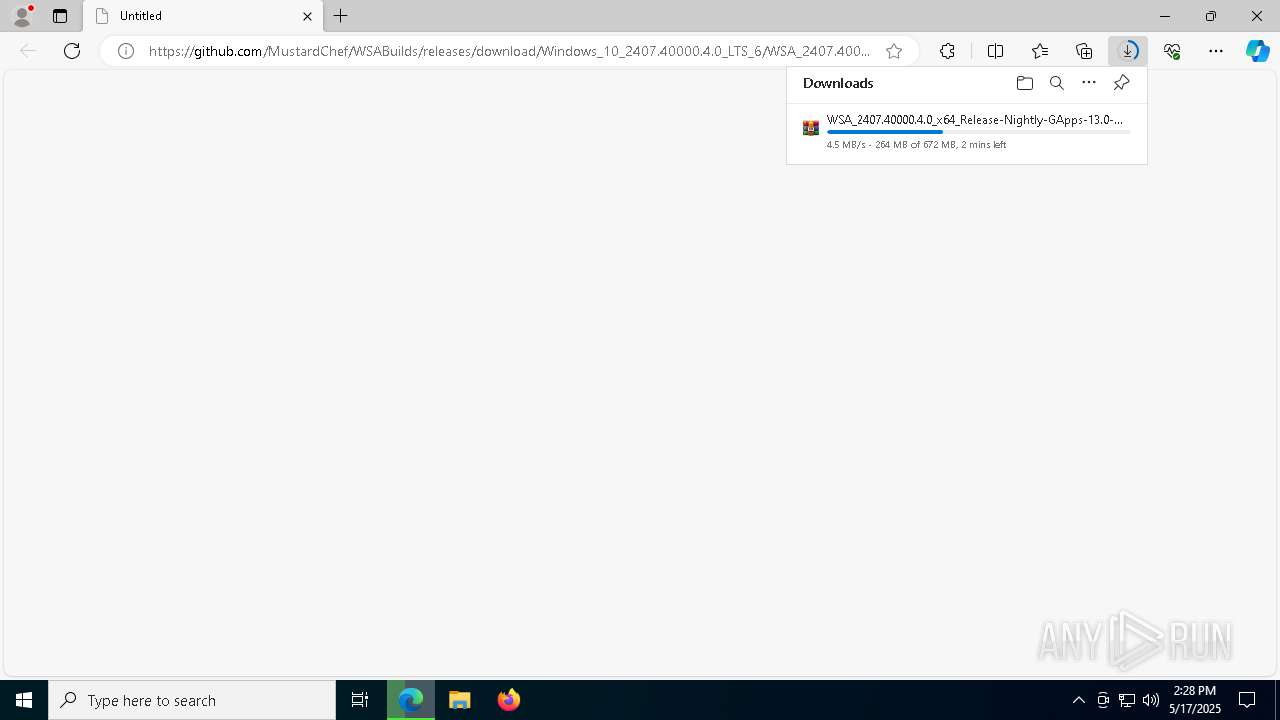
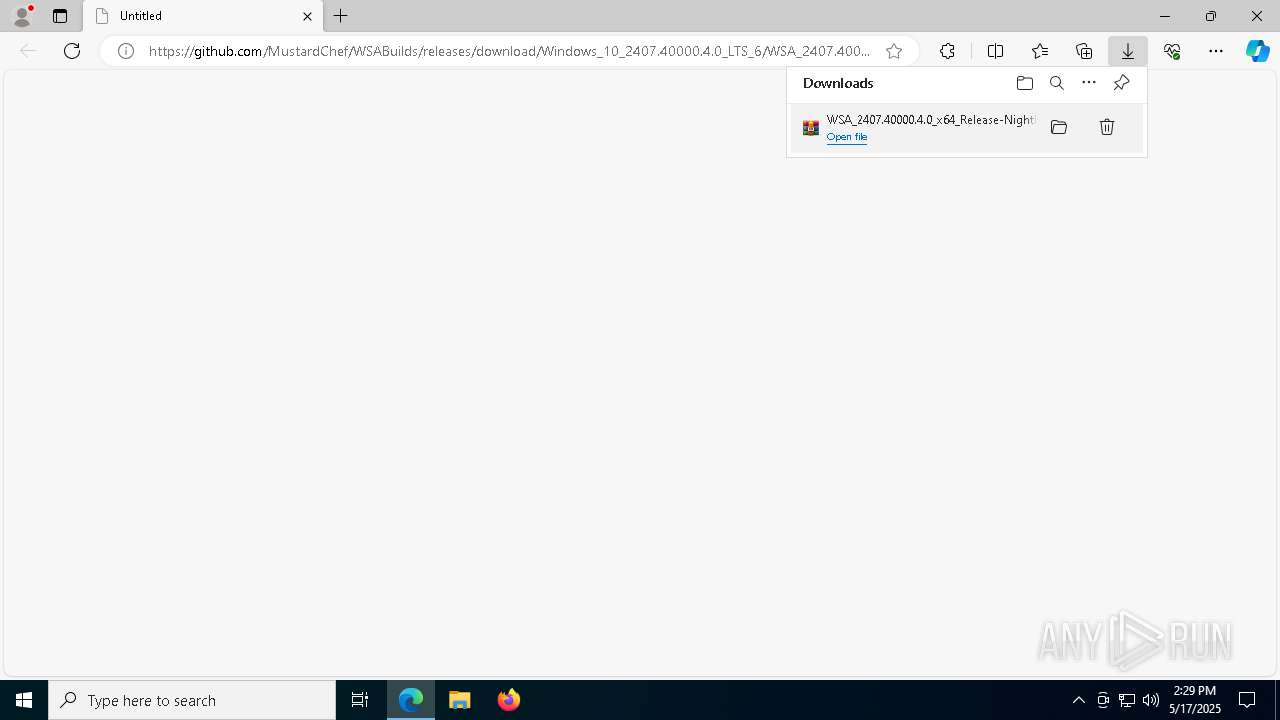
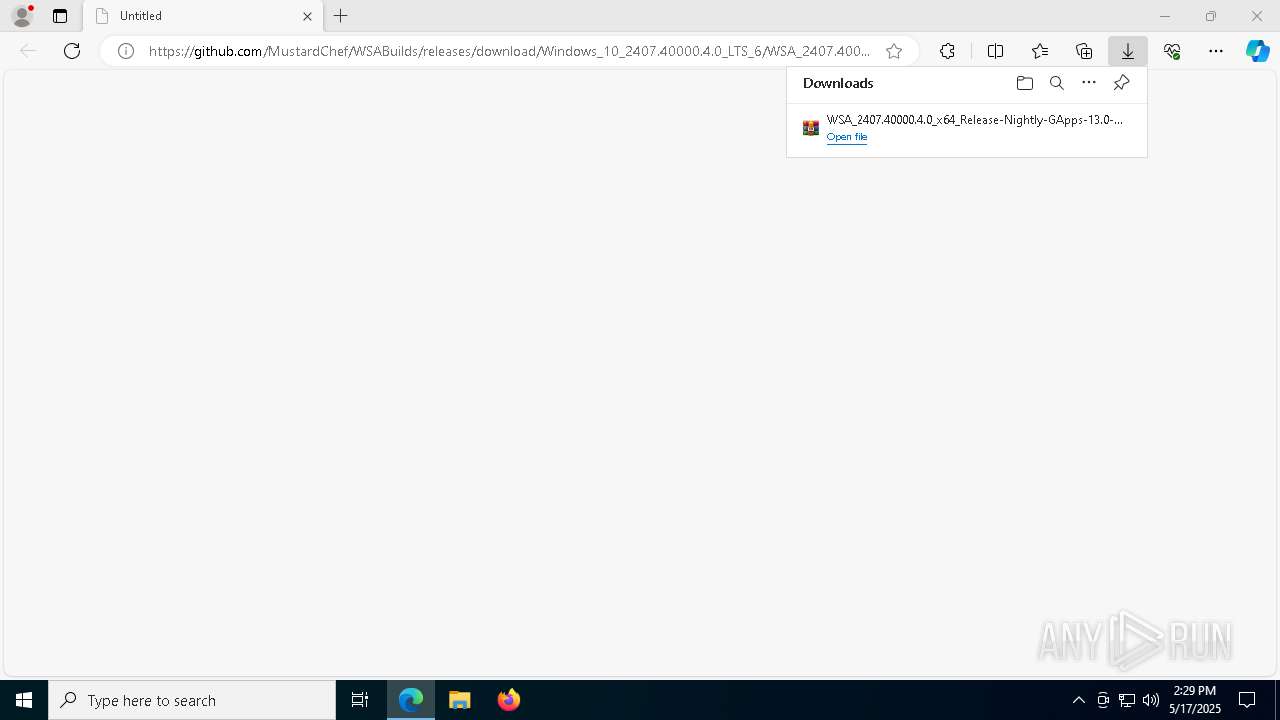
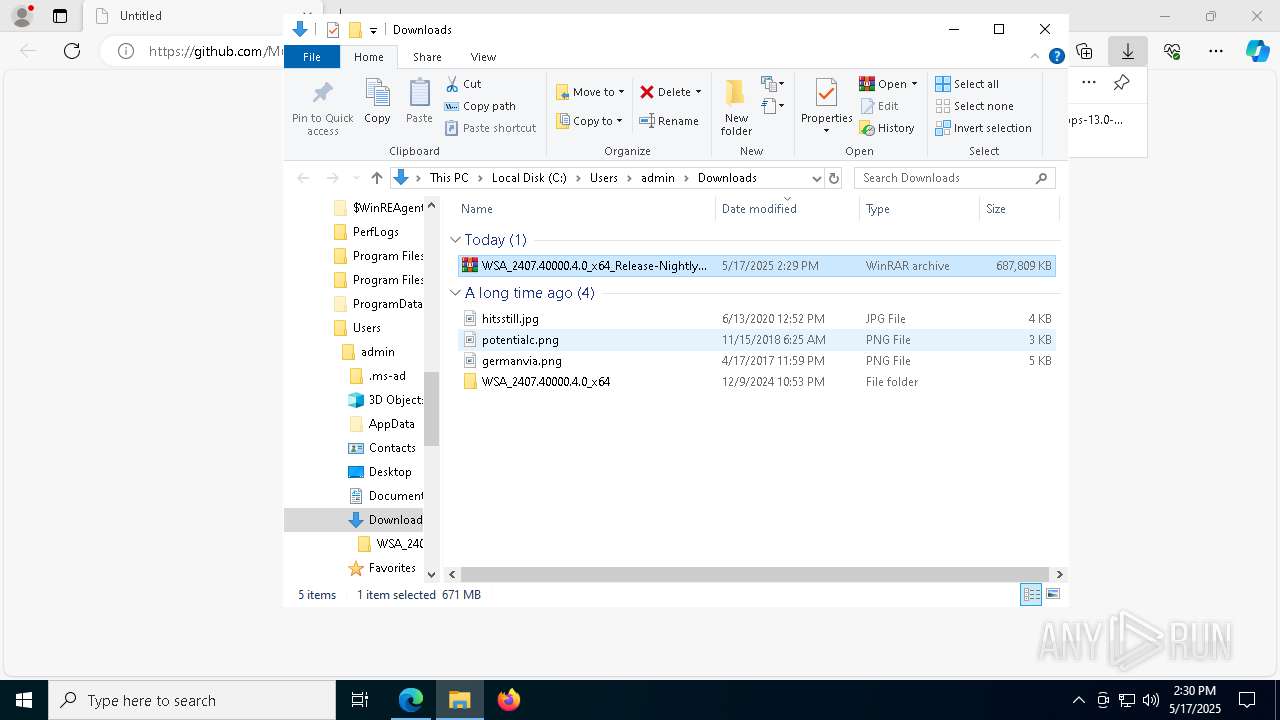
| URL: | https://github.com/MustardChef/WSABuilds/releases/download/Windows_10_2407.40000.4.0_LTS_6/WSA_2407.40000.4.0_x64_Release-Nightly-GApps-13.0-NoAmazon_Windows_10.7z |
| Full analysis: | https://app.any.run/tasks/561663a5-05cf-4c05-87f9-c8a747b8d6bc |
| Verdict: | Malicious activity |
| Analysis date: | May 17, 2025, 14:26:56 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MD5: | FC1B1AFD3CF43BB702E73C6E5AAA7AD0 |
| SHA1: | F8D13E3CE9147607042A3FD8A96473E51BCAE93E |
| SHA256: | 617F240942479AA000A4C5BC915791B8C2E0ECC9269F5240DC12863F922A71B9 |
| SSDEEP: | 3:N8tEd0ioK0ArkCfLBJ2QXWhlHp6h24ioY+1IrhnP2hsn:2uroI9LBJ2QXA4TYXl22 |
MALICIOUS
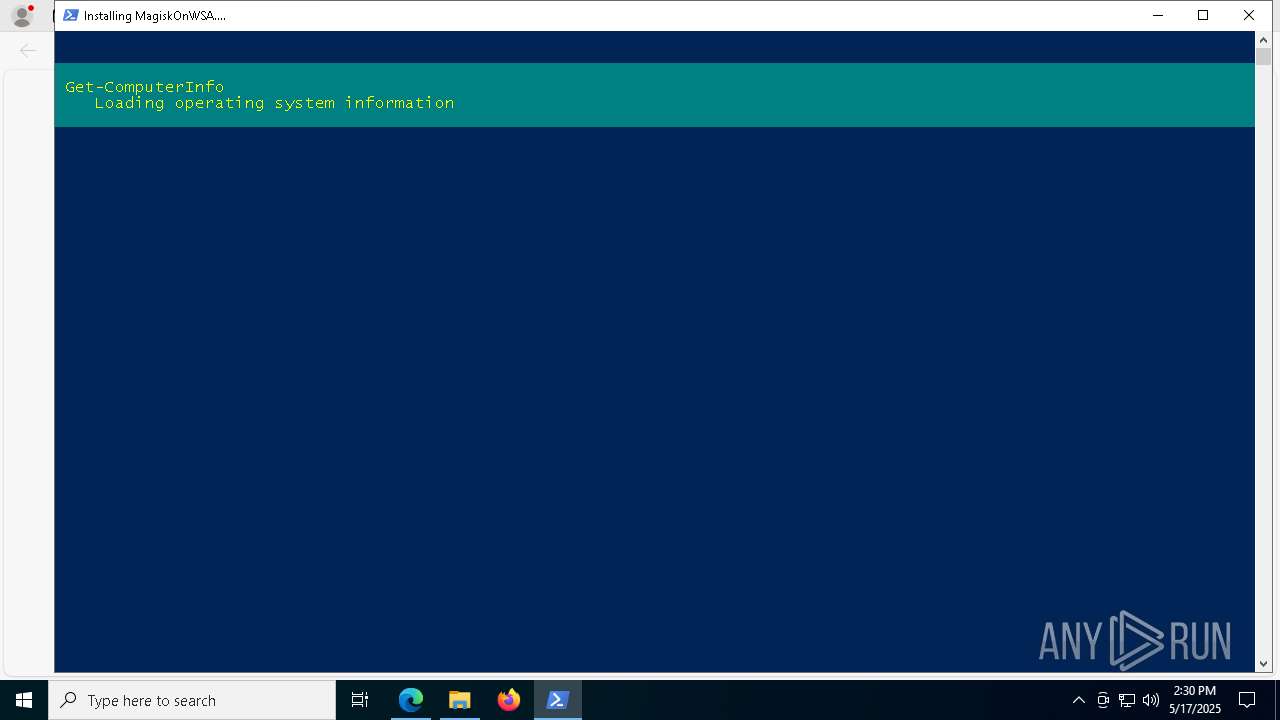
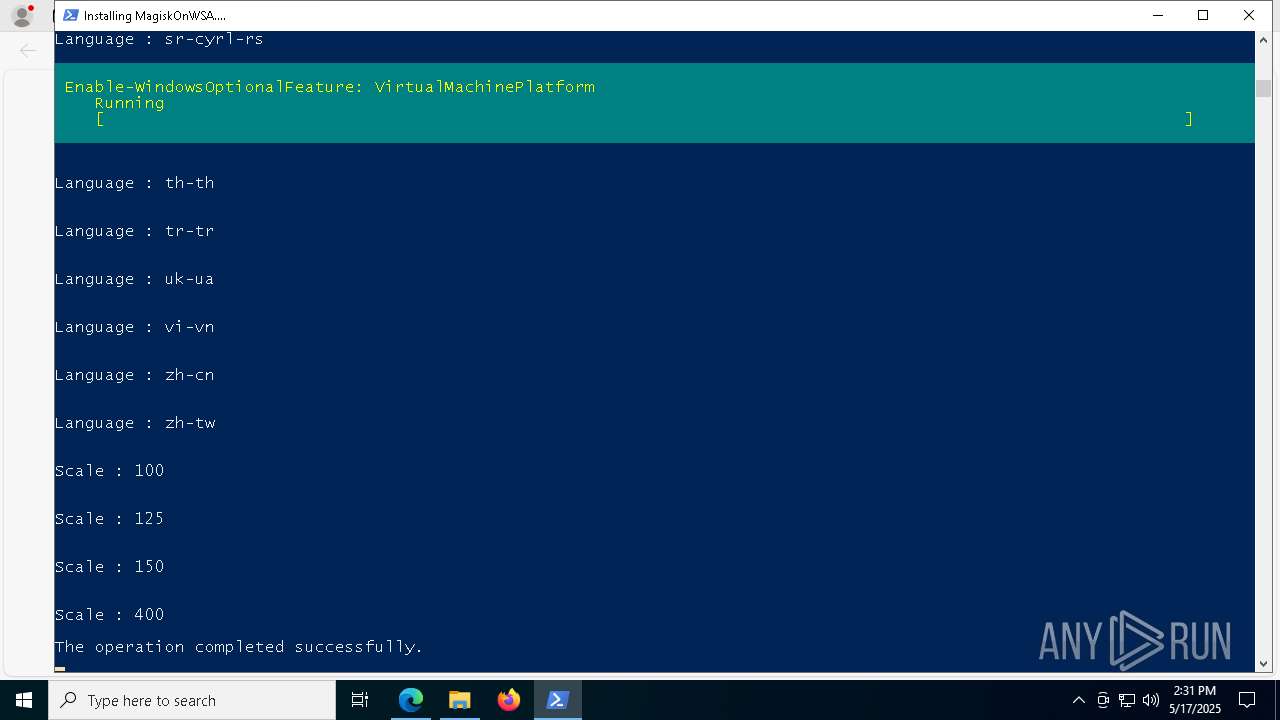
Bypass execution policy to execute commands
- powershell.exe (PID: 3800)
- powershell.exe (PID: 1280)
Changes powershell execution policy (Bypass)
- cmd.exe (PID: 4304)
- powershell.exe (PID: 3800)
SUSPICIOUS
Process drops legitimate windows executable
- WinRAR.exe (PID: 664)
- powershell.exe (PID: 3800)
- TiWorker.exe (PID: 1188)
The process creates files with name similar to system file names
- WinRAR.exe (PID: 664)
Starts POWERSHELL.EXE for commands execution
- powershell.exe (PID: 3800)
- cmd.exe (PID: 4304)
The process executes Powershell scripts
- cmd.exe (PID: 4304)
- powershell.exe (PID: 3800)
Application launched itself
- powershell.exe (PID: 3800)
Uses REG/REGEDIT.EXE to modify registry
- powershell.exe (PID: 3800)
Executable content was dropped or overwritten
- powershell.exe (PID: 3800)
- TiWorker.exe (PID: 1188)
Starts a Microsoft application from unusual location
- DismHost.exe (PID: 4180)
- DismHost.exe (PID: 6488)
Executes as Windows Service
- VSSVC.exe (PID: 4376)
Drops a system driver (possible attempt to evade defenses)
- TiWorker.exe (PID: 1188)
INFO
Reads Environment values
- identity_helper.exe (PID: 5332)
Reads the software policy settings
- slui.exe (PID: 6828)
- slui.exe (PID: 1184)
Application launched itself
- msedge.exe (PID: 976)
Reads the computer name
- identity_helper.exe (PID: 5332)
Checks supported languages
- identity_helper.exe (PID: 5332)
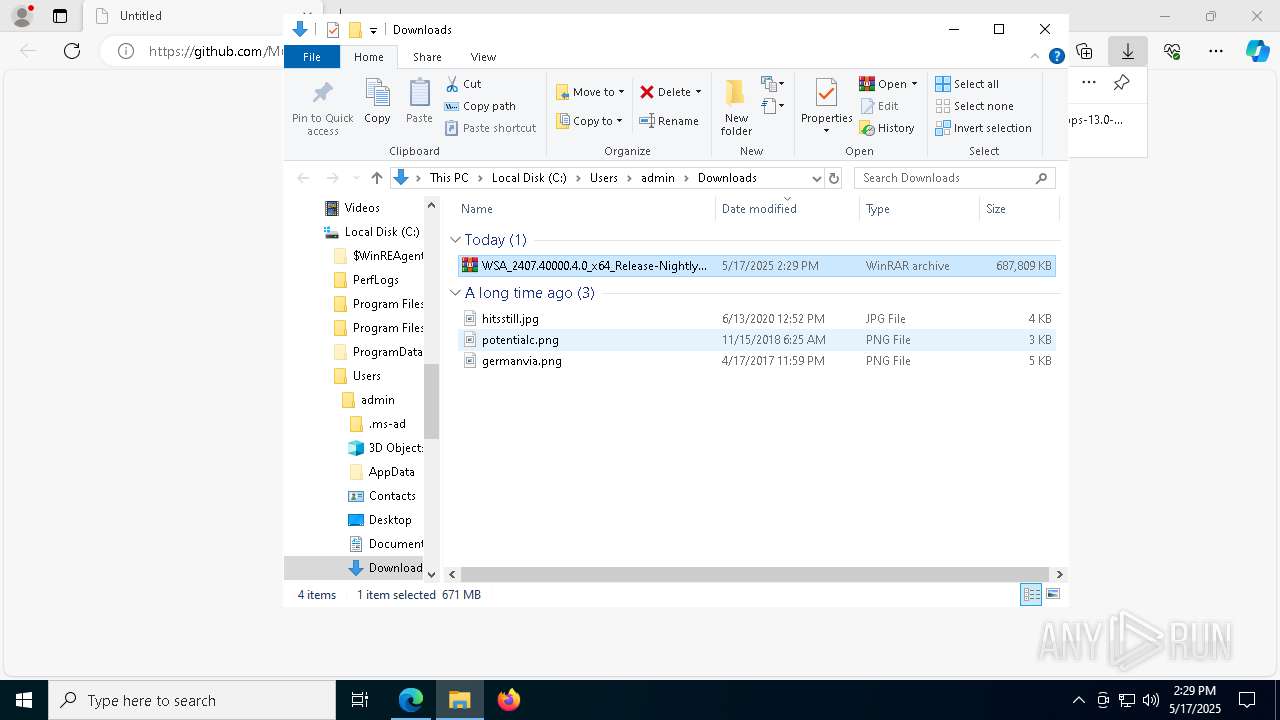
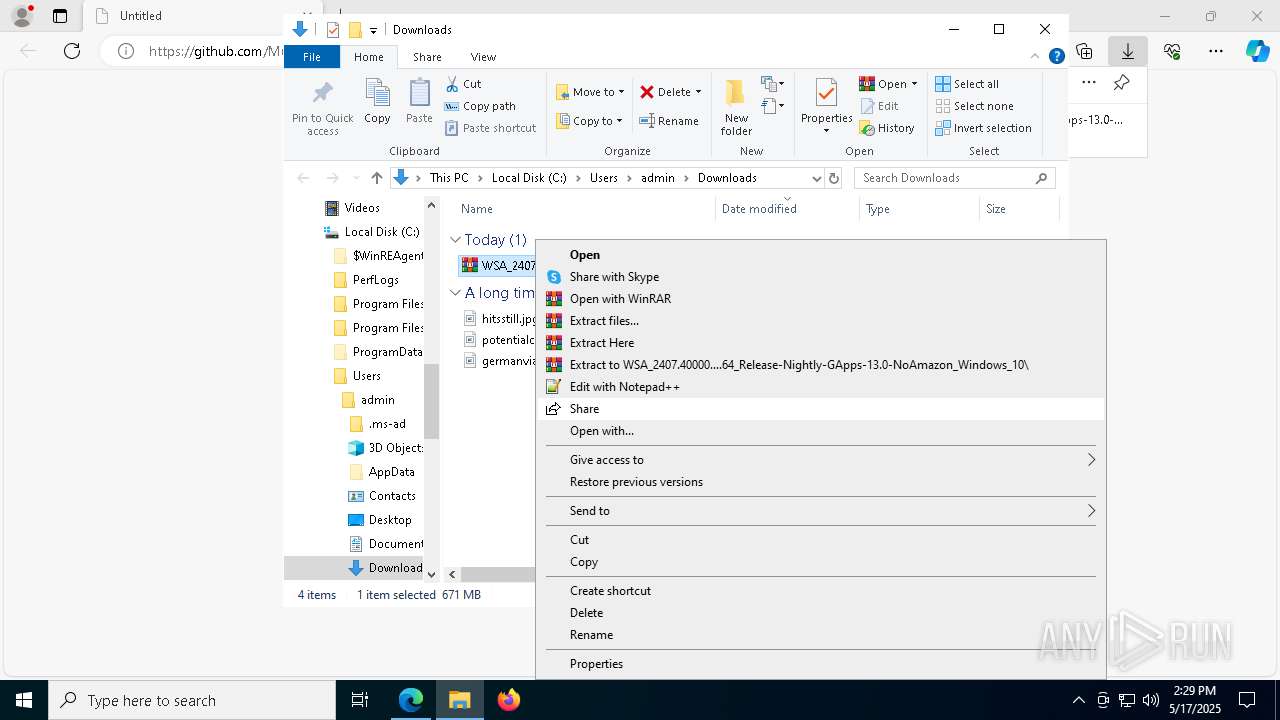
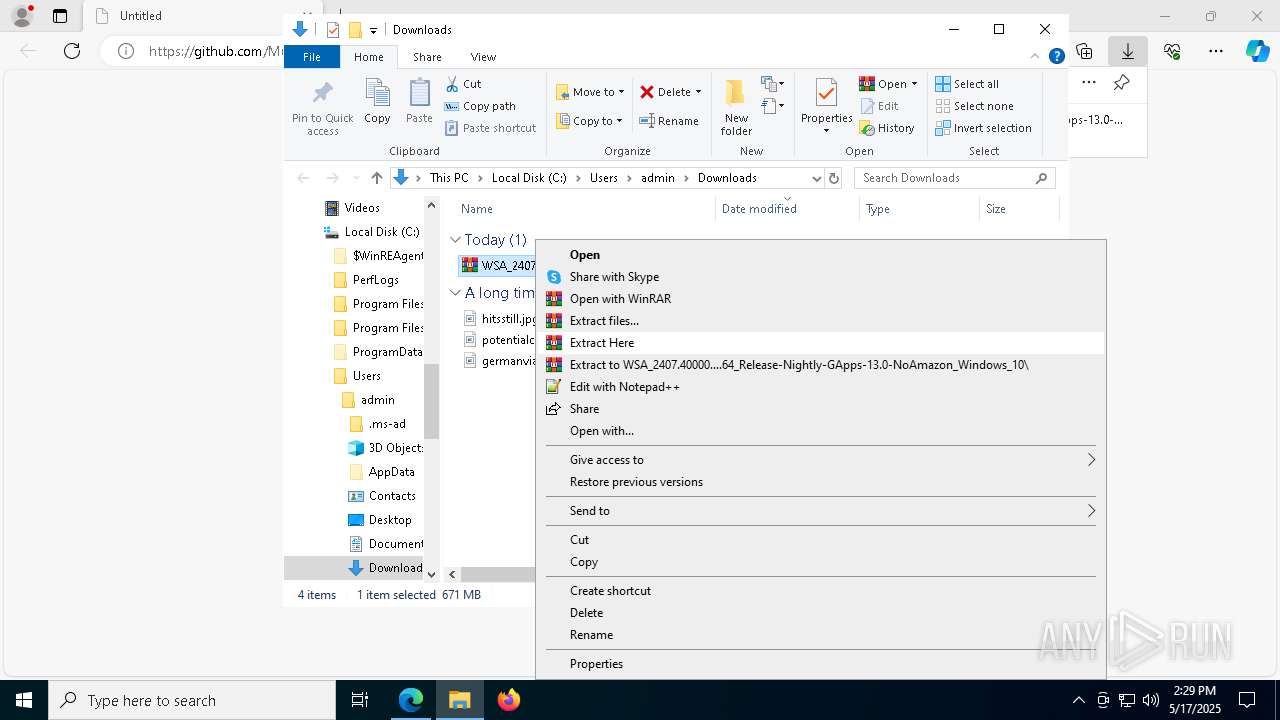
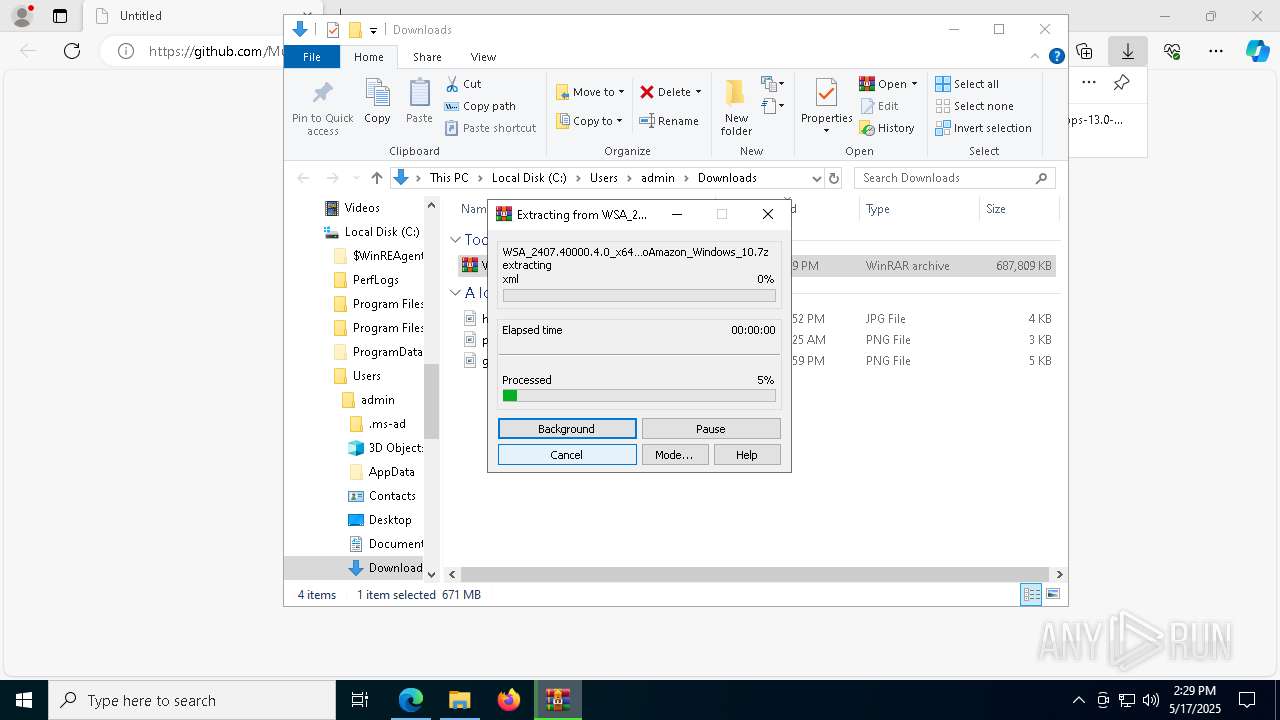
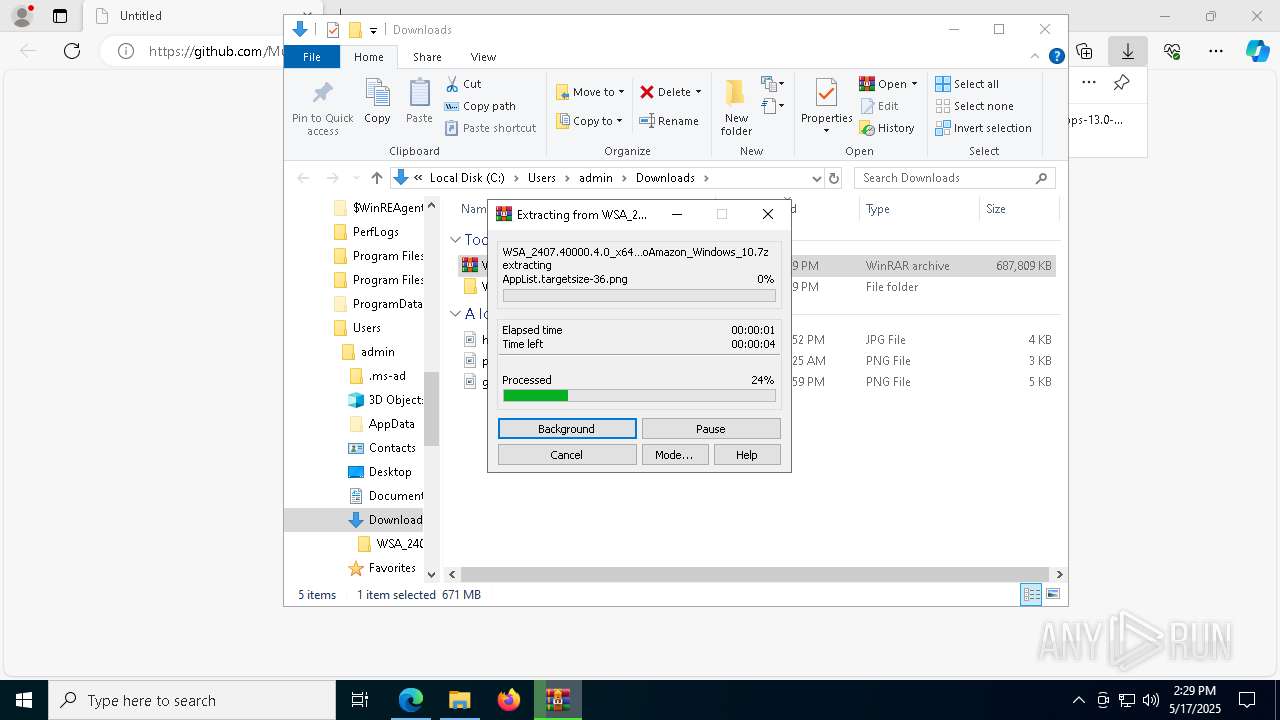
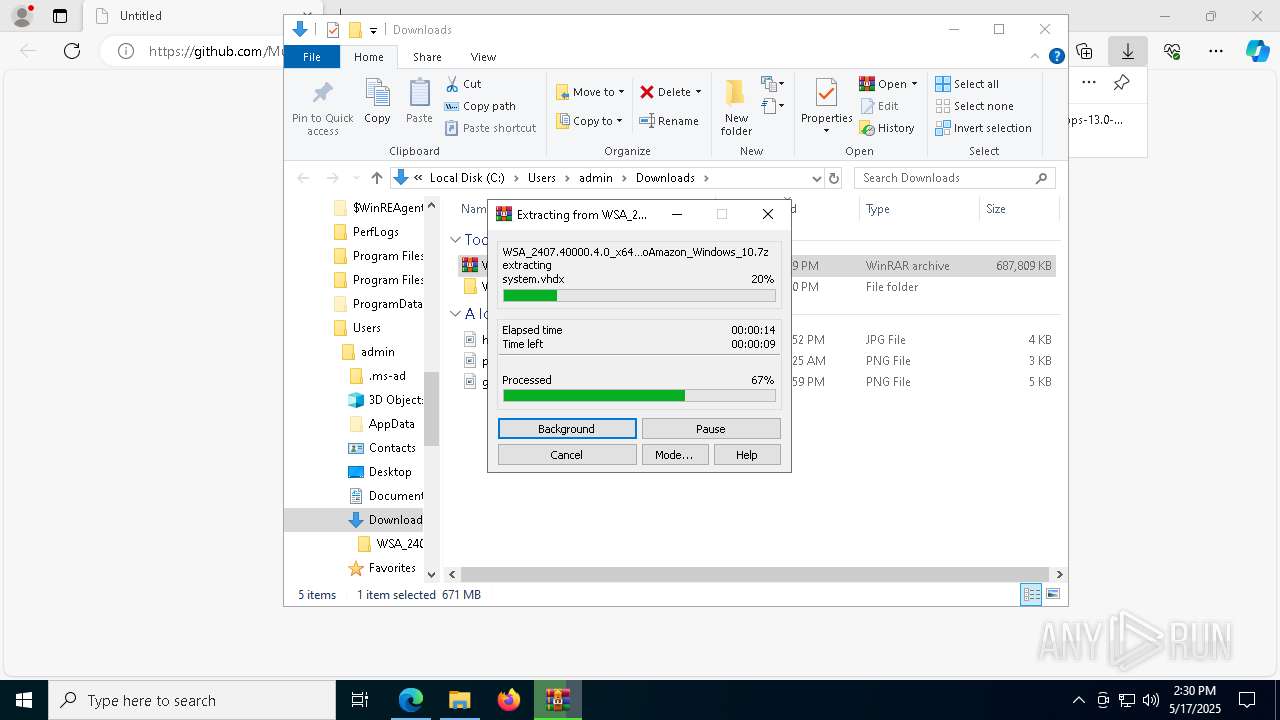
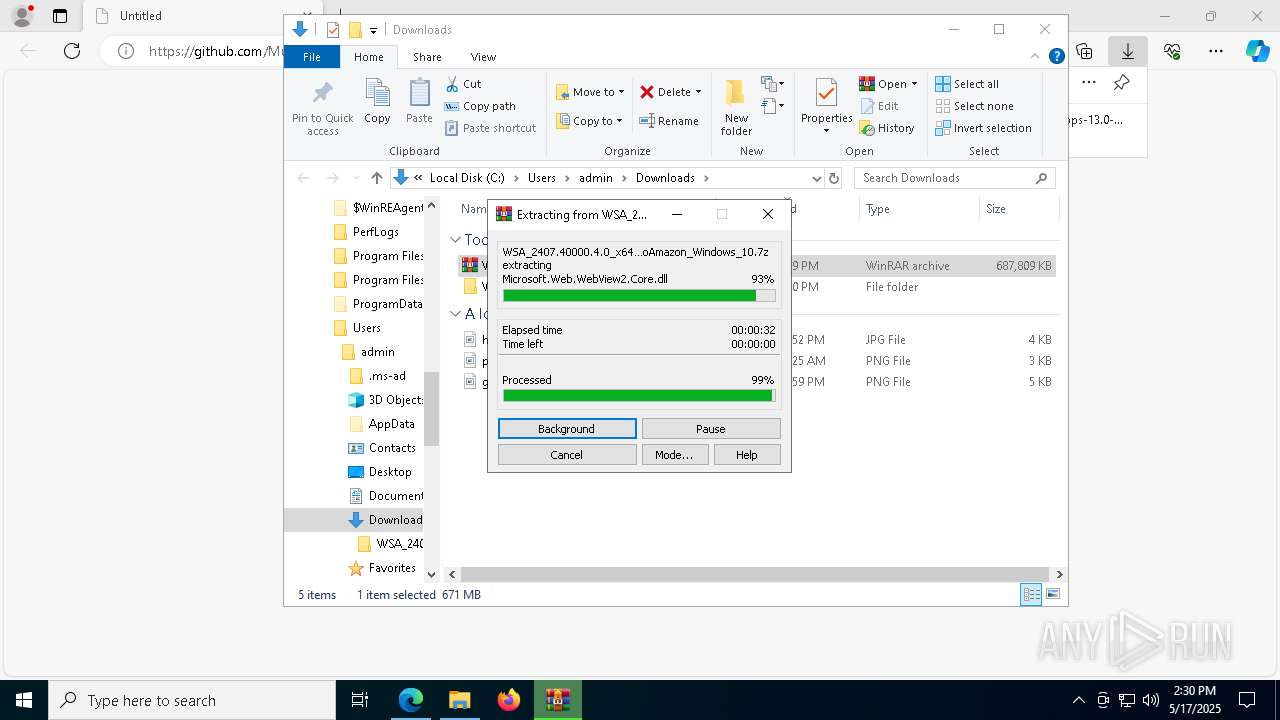
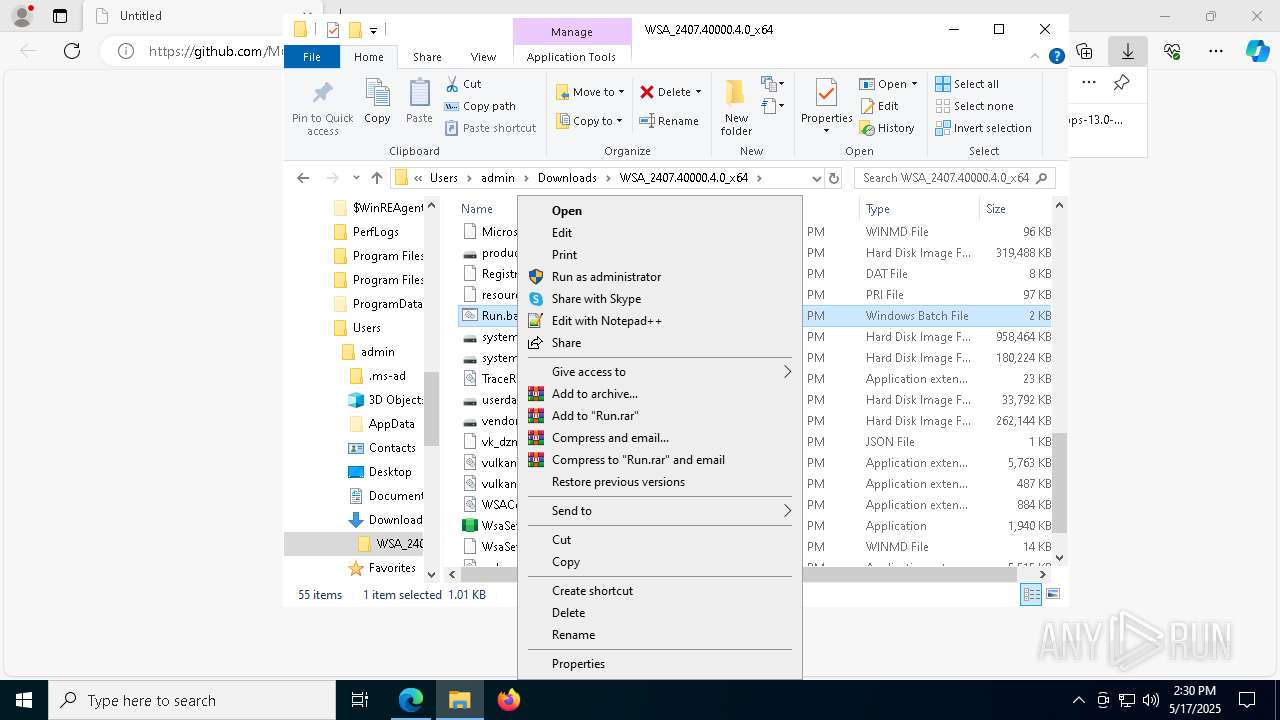
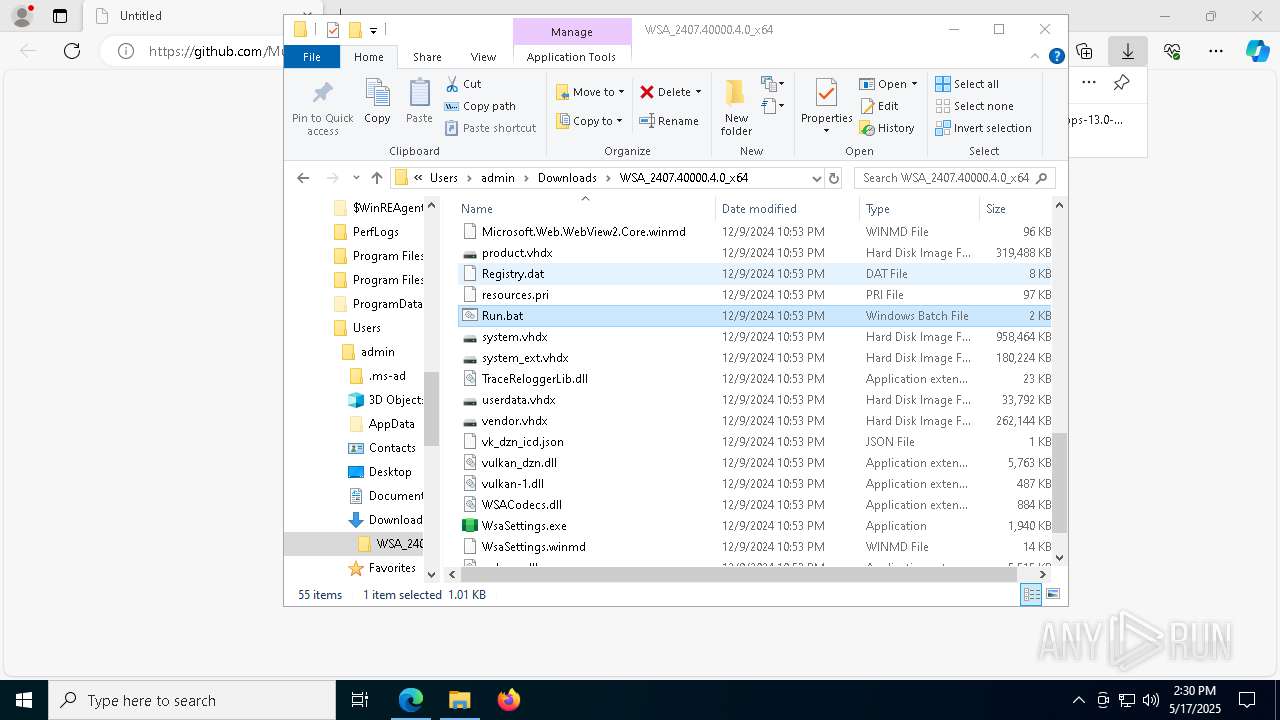
Manual execution by a user
- WinRAR.exe (PID: 664)
- cmd.exe (PID: 4304)
The sample compiled with english language support
- WinRAR.exe (PID: 664)
- powershell.exe (PID: 3800)
- TiWorker.exe (PID: 1188)
- msedge.exe (PID: 4884)
Checks proxy server information
- slui.exe (PID: 6828)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 664)
- msedge.exe (PID: 4884)
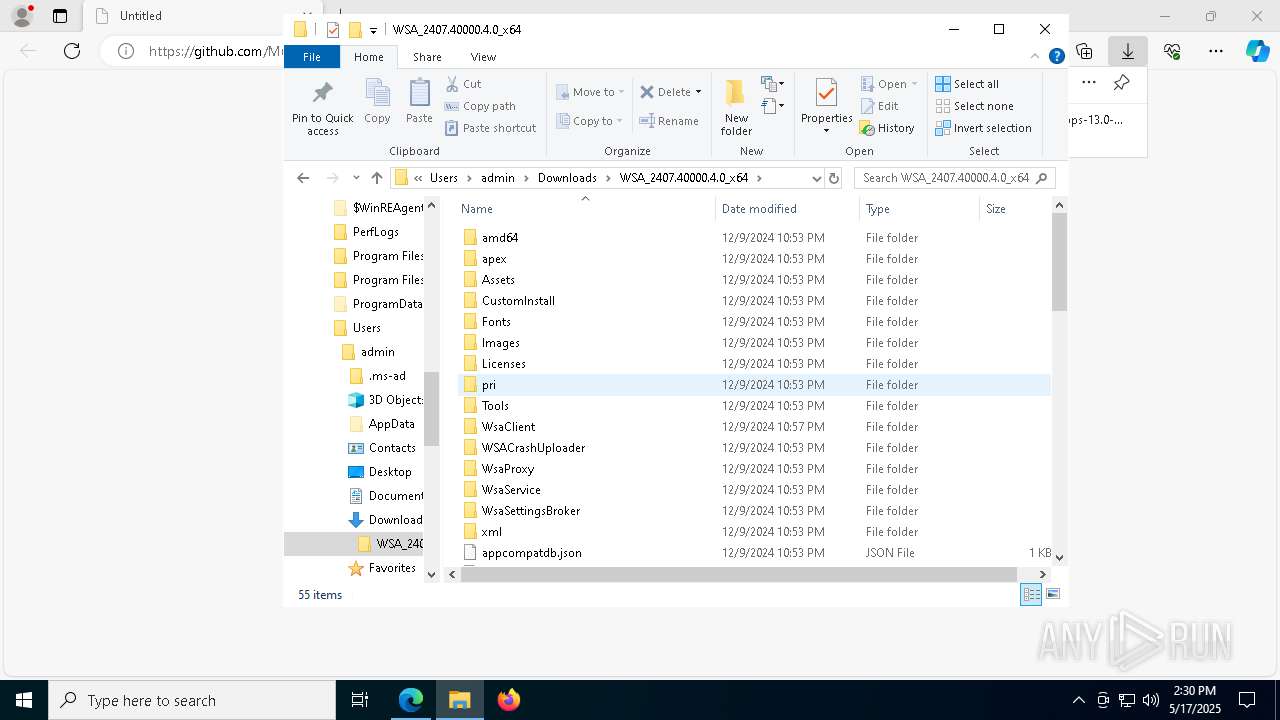
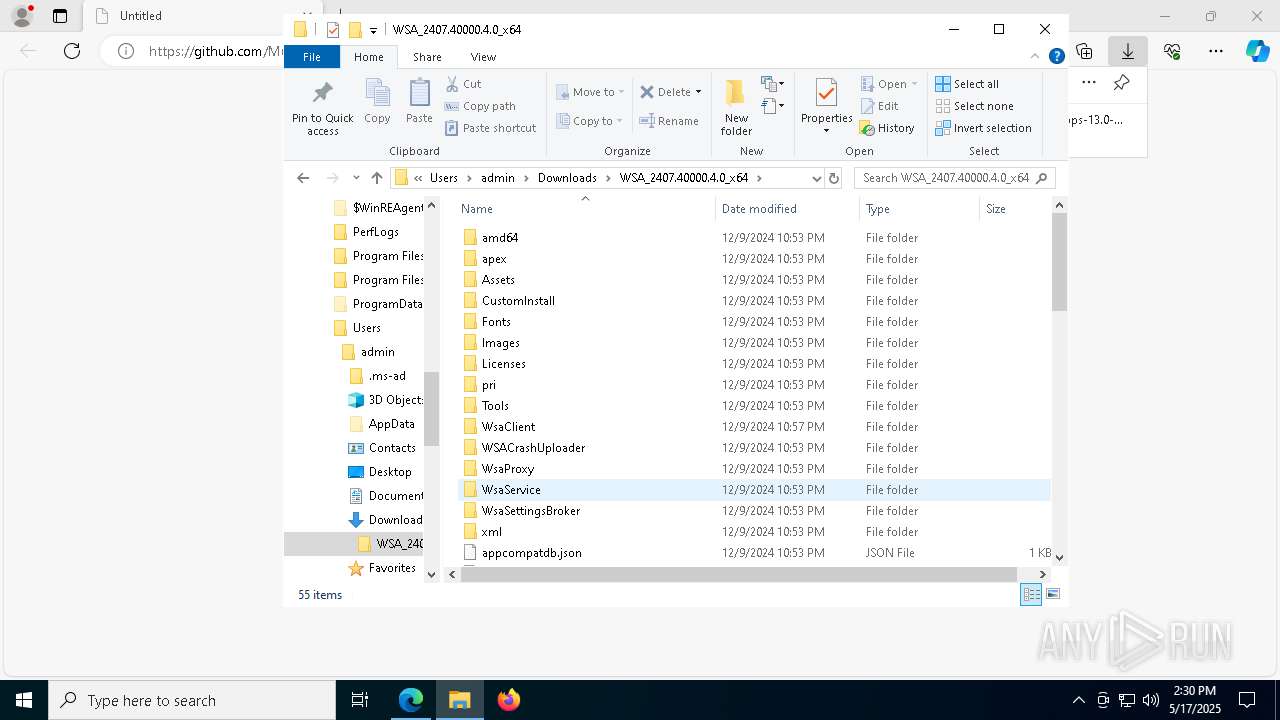
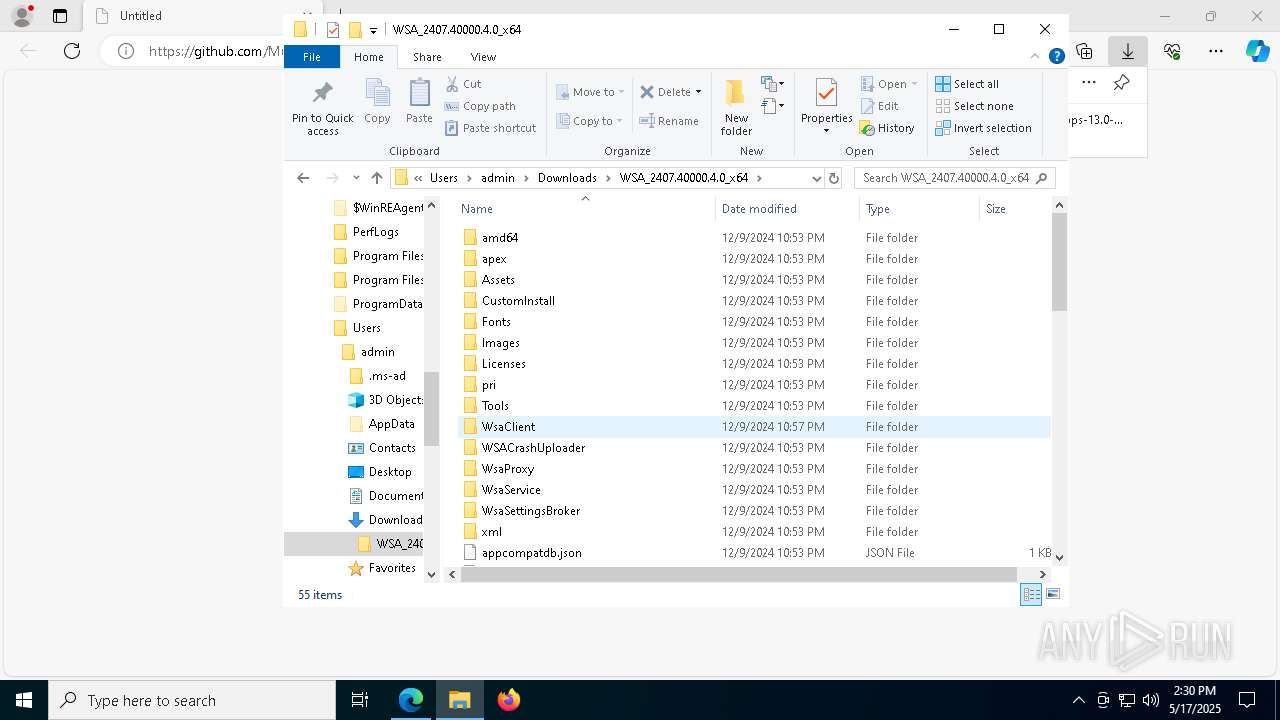
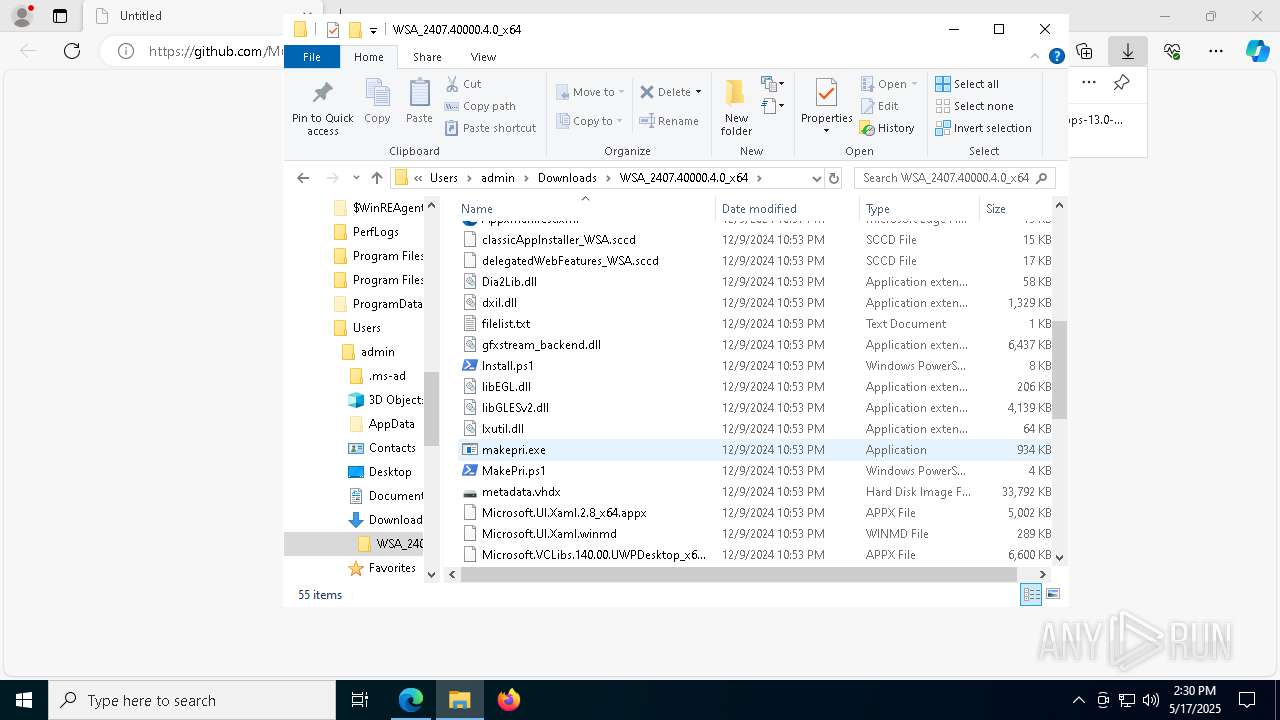
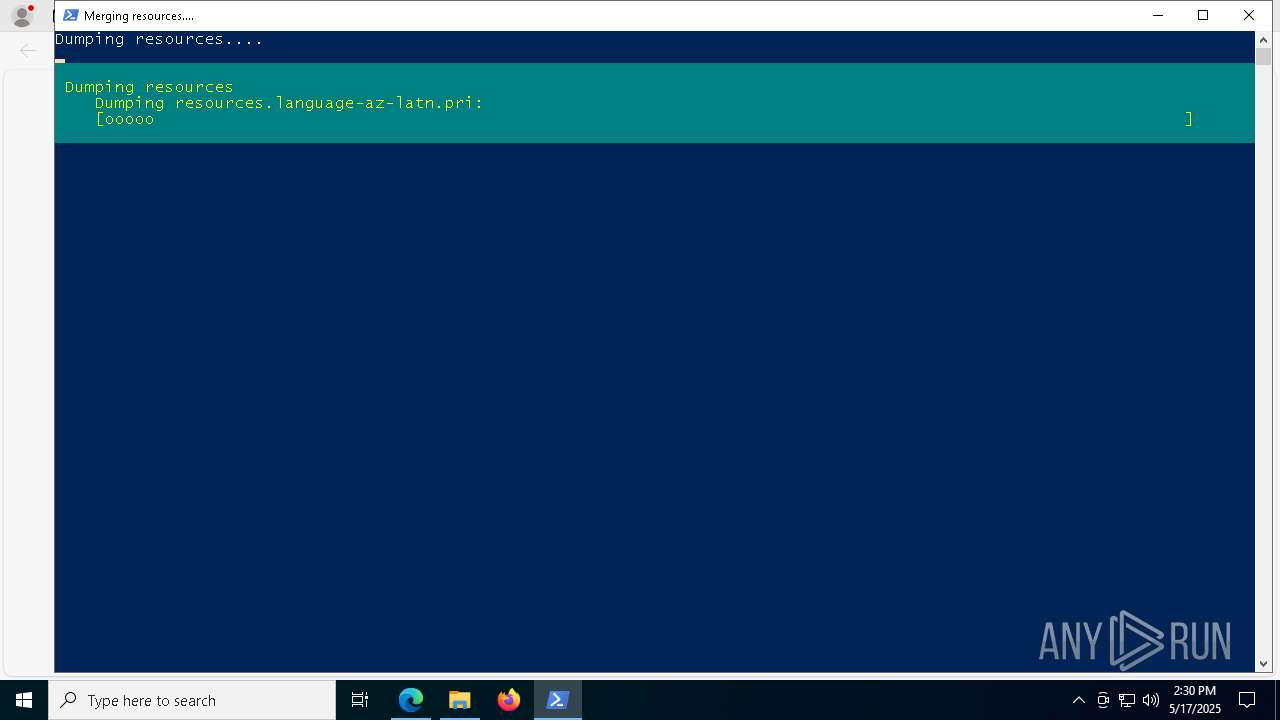
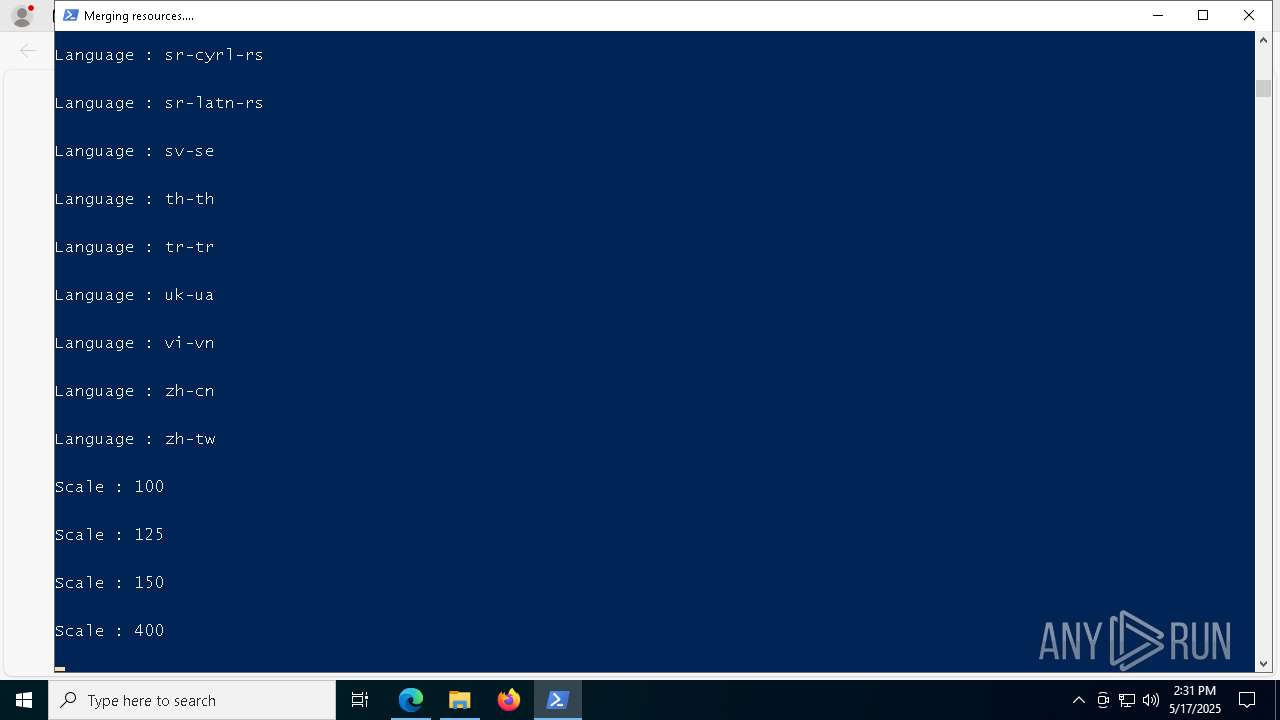
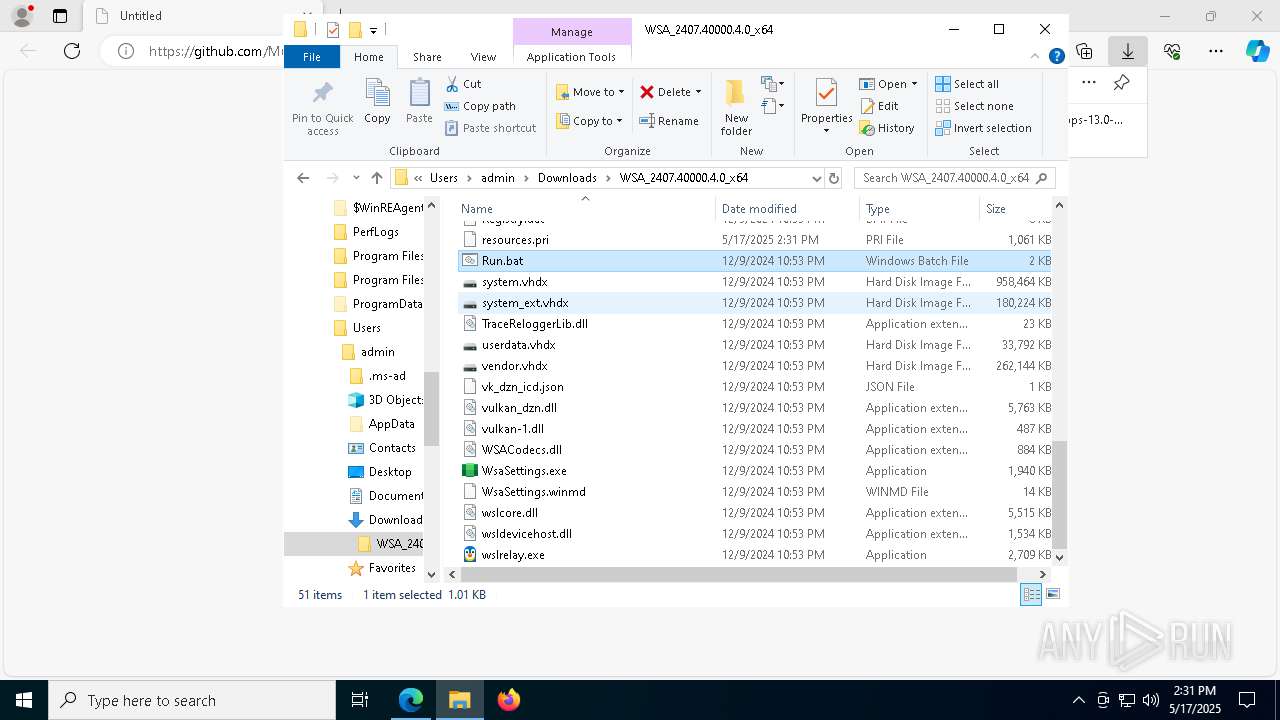
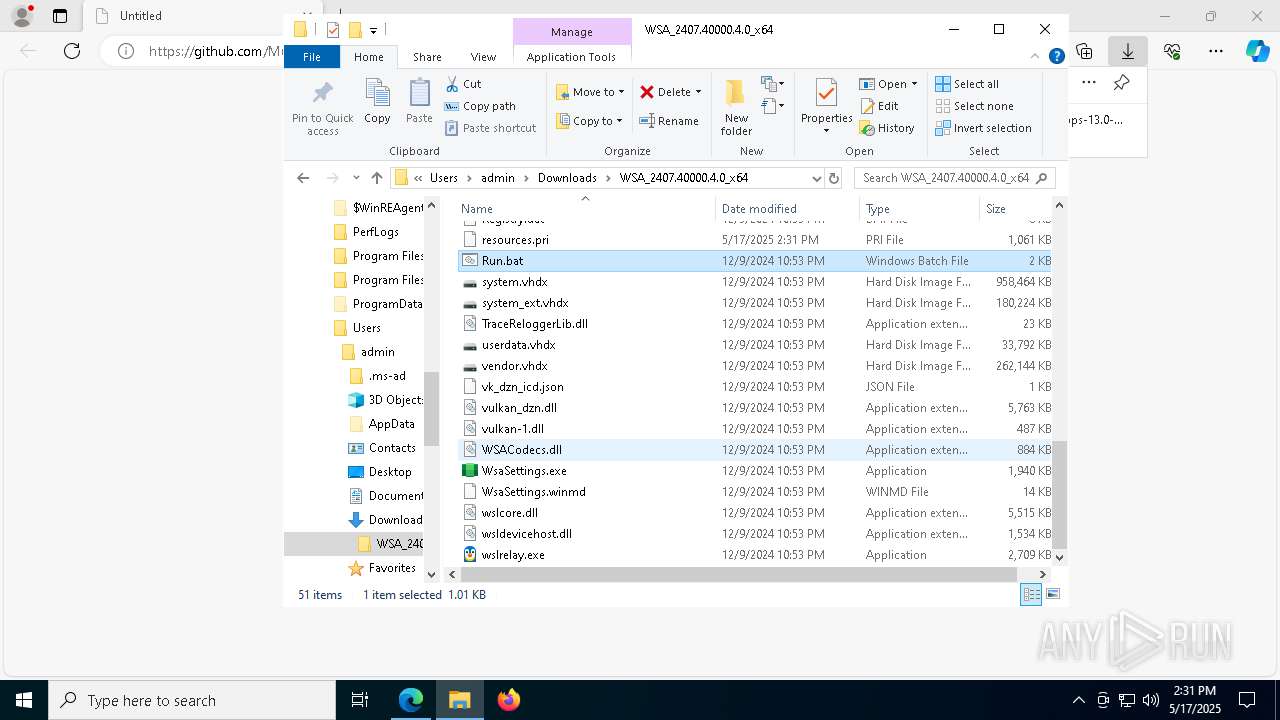
The executable file from the user directory is run by the Powershell process
- makepri.exe (PID: 3180)
- makepri.exe (PID: 4784)
- makepri.exe (PID: 8156)
- makepri.exe (PID: 7984)
- makepri.exe (PID: 6132)
- makepri.exe (PID: 5504)
- makepri.exe (PID: 208)
- makepri.exe (PID: 6960)
- makepri.exe (PID: 2152)
- makepri.exe (PID: 8092)
- makepri.exe (PID: 1764)
- makepri.exe (PID: 5776)
- makepri.exe (PID: 6340)
- makepri.exe (PID: 6372)
- makepri.exe (PID: 5332)
- makepri.exe (PID: 800)
- makepri.exe (PID: 6752)
- makepri.exe (PID: 5216)
- makepri.exe (PID: 776)
- makepri.exe (PID: 7884)
- makepri.exe (PID: 4920)
- makepri.exe (PID: 8108)
- makepri.exe (PID: 7104)
- makepri.exe (PID: 6264)
- makepri.exe (PID: 5312)
- makepri.exe (PID: 7816)
- makepri.exe (PID: 3192)
- makepri.exe (PID: 8140)
- makepri.exe (PID: 6388)
- makepri.exe (PID: 4736)
- makepri.exe (PID: 2772)
- makepri.exe (PID: 7048)
- makepri.exe (PID: 6744)
- makepri.exe (PID: 2664)
- makepri.exe (PID: 6276)
- makepri.exe (PID: 2840)
- makepri.exe (PID: 4932)
- makepri.exe (PID: 1096)
- makepri.exe (PID: 3024)
- makepri.exe (PID: 4452)
- makepri.exe (PID: 6156)
- makepri.exe (PID: 7432)
- makepri.exe (PID: 4188)
- makepri.exe (PID: 1452)
- makepri.exe (PID: 4228)
- makepri.exe (PID: 8080)
- makepri.exe (PID: 5364)
- makepri.exe (PID: 300)
- makepri.exe (PID: 6436)
- makepri.exe (PID: 3028)
- makepri.exe (PID: 6248)
- makepri.exe (PID: 2084)
- makepri.exe (PID: 6972)
- makepri.exe (PID: 7764)
- makepri.exe (PID: 6904)
- makepri.exe (PID: 8168)
- makepri.exe (PID: 2564)
- makepri.exe (PID: 2268)
- makepri.exe (PID: 7052)
- DismHost.exe (PID: 4180)
- DismHost.exe (PID: 6488)
- makepri.exe (PID: 8084)
- makepri.exe (PID: 2108)
Manages system restore points
- SrTasks.exe (PID: 5600)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
321
Monitored processes
178
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 208 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=3912 --field-trial-handle=2416,i,15777758606739974815,9367639427434540258,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 208 | "C:\Users\admin\Downloads\WSA_2407.40000.4.0_x64\makepri.exe" dump /if .\pri\resources.language-bg.pri /o /es .\pri\resources.pri /of .\priinfo\resources.language-bg.pri.xml /dt detailed | C:\Users\admin\Downloads\WSA_2407.40000.4.0_x64\makepri.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Command line tool for creating PRI files Exit code: 0 Version: 10.0.22621.755 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 300 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | makepri.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 300 | "C:\Users\admin\Downloads\WSA_2407.40000.4.0_x64\makepri.exe" dump /if .\pri\resources.language-sv.pri /o /es .\pri\resources.pri /of .\priinfo\resources.language-sv.pri.xml /dt detailed | C:\Users\admin\Downloads\WSA_2407.40000.4.0_x64\makepri.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Command line tool for creating PRI files Exit code: 0 Version: 10.0.22621.755 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 456 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | makepri.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 660 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | makepri.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 664 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=7080 --field-trial-handle=2416,i,15777758606739974815,9367639427434540258,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 664 | "C:\Program Files\WinRAR\WinRAR.exe" x -iext -ow -ver -- "C:\Users\admin\Downloads\WSA_2407.40000.4.0_x64_Release-Nightly-GApps-13.0-NoAmazon_Windows_10.7z" C:\Users\admin\Downloads\ | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 776 | "C:\Users\admin\Downloads\WSA_2407.40000.4.0_x64\makepri.exe" dump /if .\pri\resources.language-gl.pri /o /es .\pri\resources.pri /of .\priinfo\resources.language-gl.pri.xml /dt detailed | C:\Users\admin\Downloads\WSA_2407.40000.4.0_x64\makepri.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Command line tool for creating PRI files Exit code: 0 Version: 10.0.22621.755 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 780 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | makepri.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
62 628
Read events
60 449
Write events
1 620
Delete events
559
Modification events
| (PID) Process: | (976) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 2CECD5F9EB932F00 | |||
| (PID) Process: | (976) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\524998 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {D49662FD-C001-460D-842E-5D10DEC5E5F2} | |||
| (PID) Process: | (976) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (976) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (976) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (976) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (976) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 4095CDF9EB932F00 | |||
| (PID) Process: | (976) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\524998 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {3BAB0B25-D1D5-4E5C-A7D3-2BF2DFFF1CC2} | |||
| (PID) Process: | (976) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: E797FCF9EB932F00 | |||
| (PID) Process: | (976) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | MicrosoftEdgeAutoLaunch_29EBC4579851B72EE312C449CF839B1A |
Value: "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --no-startup-window --win-session-start | |||
Executable files
233
Suspicious files
414
Text files
222
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 976 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF10b73c.TMP | — | |
MD5:— | SHA256:— | |||
| 976 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 976 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF10b73c.TMP | — | |
MD5:— | SHA256:— | |||
| 976 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF10b73c.TMP | — | |
MD5:— | SHA256:— | |||
| 976 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 976 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 976 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF10b74c.TMP | — | |
MD5:— | SHA256:— | |||
| 976 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 976 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF10b75b.TMP | — | |
MD5:— | SHA256:— | |||
| 976 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
40
TCP/UDP connections
62
DNS requests
59
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.219.150.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6132 | SIHClient.exe | GET | 200 | 23.219.150.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 2.19.11.120:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6184 | svchost.exe | HEAD | 200 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1747698231&P2=404&P3=2&P4=QmaRXp6peHF3cUHMxO24tVdxkXuW%2fi9pN4%2b13pjfoQklOL9cydLADDFKWh1%2f%2bQYpoMIOAs8sepv%2bNF9pnbOkkw%3d%3d | unknown | — | — | whitelisted |
6132 | SIHClient.exe | GET | 200 | 23.219.150.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
6184 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1747698231&P2=404&P3=2&P4=QmaRXp6peHF3cUHMxO24tVdxkXuW%2fi9pN4%2b13pjfoQklOL9cydLADDFKWh1%2f%2bQYpoMIOAs8sepv%2bNF9pnbOkkw%3d%3d | unknown | — | — | whitelisted |
6184 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1747698231&P2=404&P3=2&P4=QmaRXp6peHF3cUHMxO24tVdxkXuW%2fi9pN4%2b13pjfoQklOL9cydLADDFKWh1%2f%2bQYpoMIOAs8sepv%2bNF9pnbOkkw%3d%3d | unknown | — | — | whitelisted |
6184 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1747698231&P2=404&P3=2&P4=QmaRXp6peHF3cUHMxO24tVdxkXuW%2fi9pN4%2b13pjfoQklOL9cydLADDFKWh1%2f%2bQYpoMIOAs8sepv%2bNF9pnbOkkw%3d%3d | unknown | — | — | whitelisted |
6184 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1747698231&P2=404&P3=2&P4=QmaRXp6peHF3cUHMxO24tVdxkXuW%2fi9pN4%2b13pjfoQklOL9cydLADDFKWh1%2f%2bQYpoMIOAs8sepv%2bNF9pnbOkkw%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 2.19.11.120:80 | crl.microsoft.com | Elisa Oyj | NL | whitelisted |
— | — | 23.219.150.101:80 | www.microsoft.com | AKAMAI-AS | CL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
976 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
7324 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7324 | msedge.exe | 13.107.6.158:443 | business.bing.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7324 | msedge.exe | 150.171.27.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7324 | msedge.exe | 140.82.121.4:443 | github.com | GITHUB | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
github.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
business.bing.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
objects.githubusercontent.com |
| whitelisted |