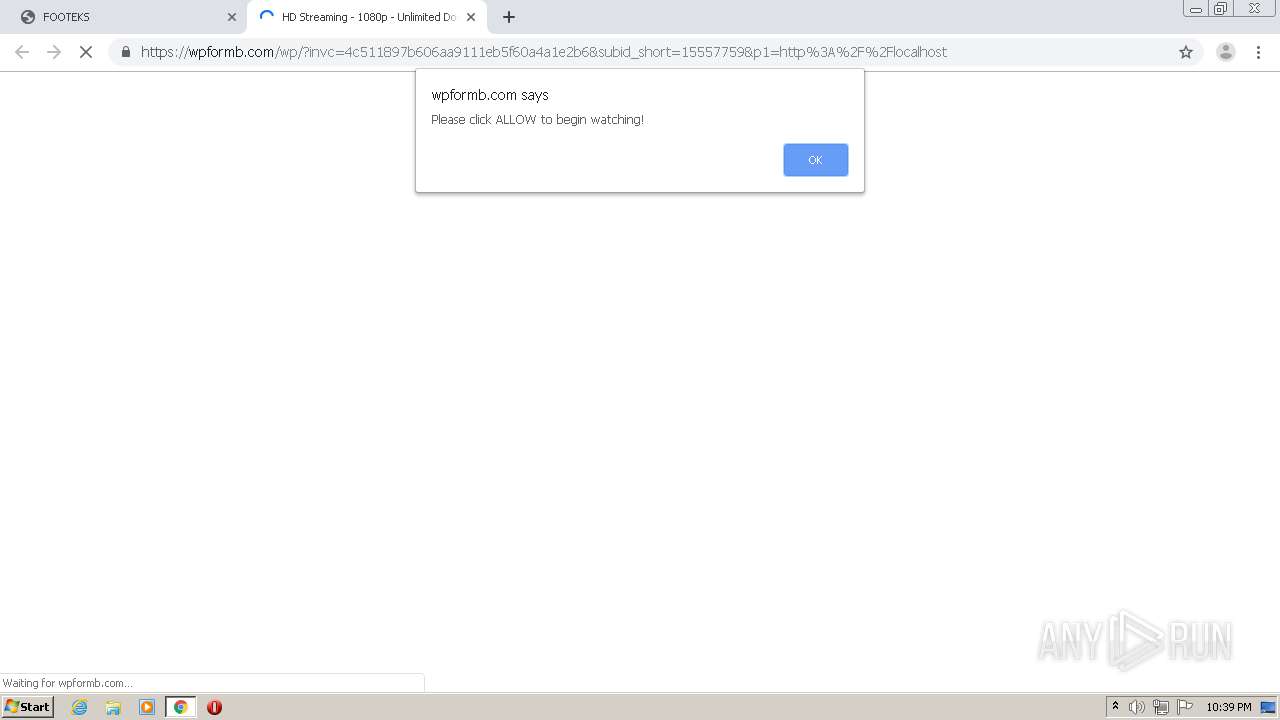
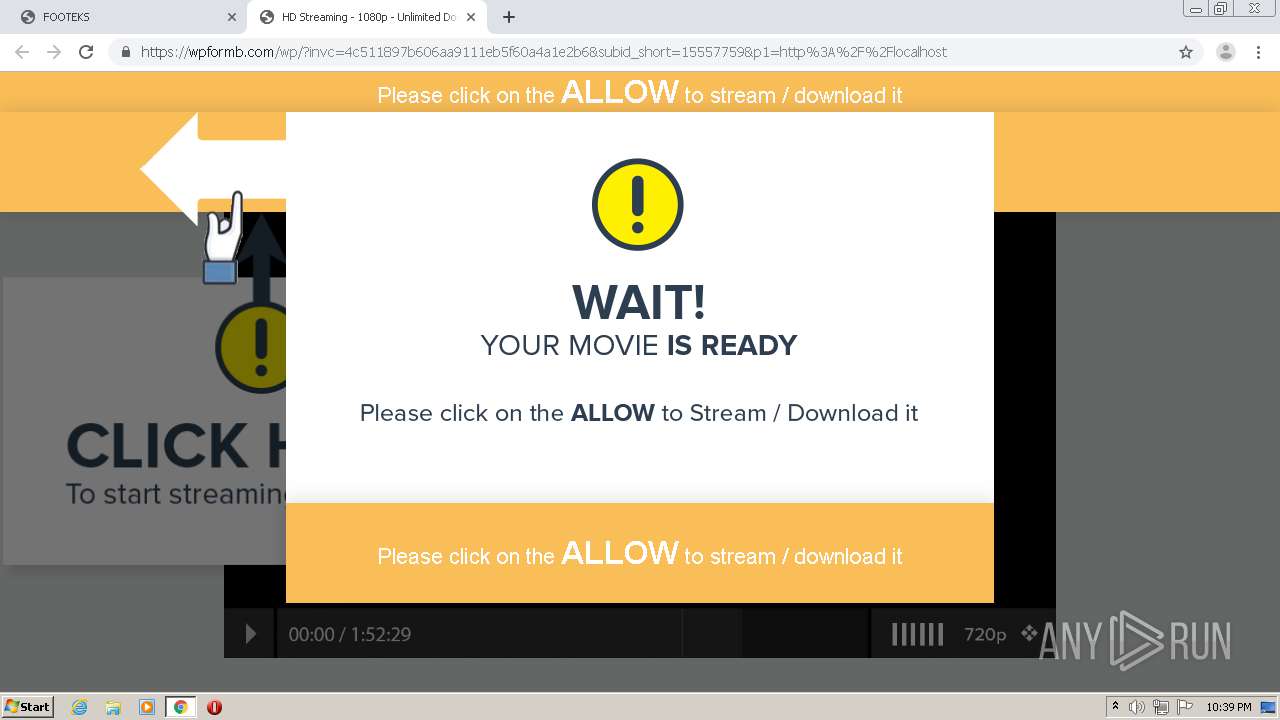
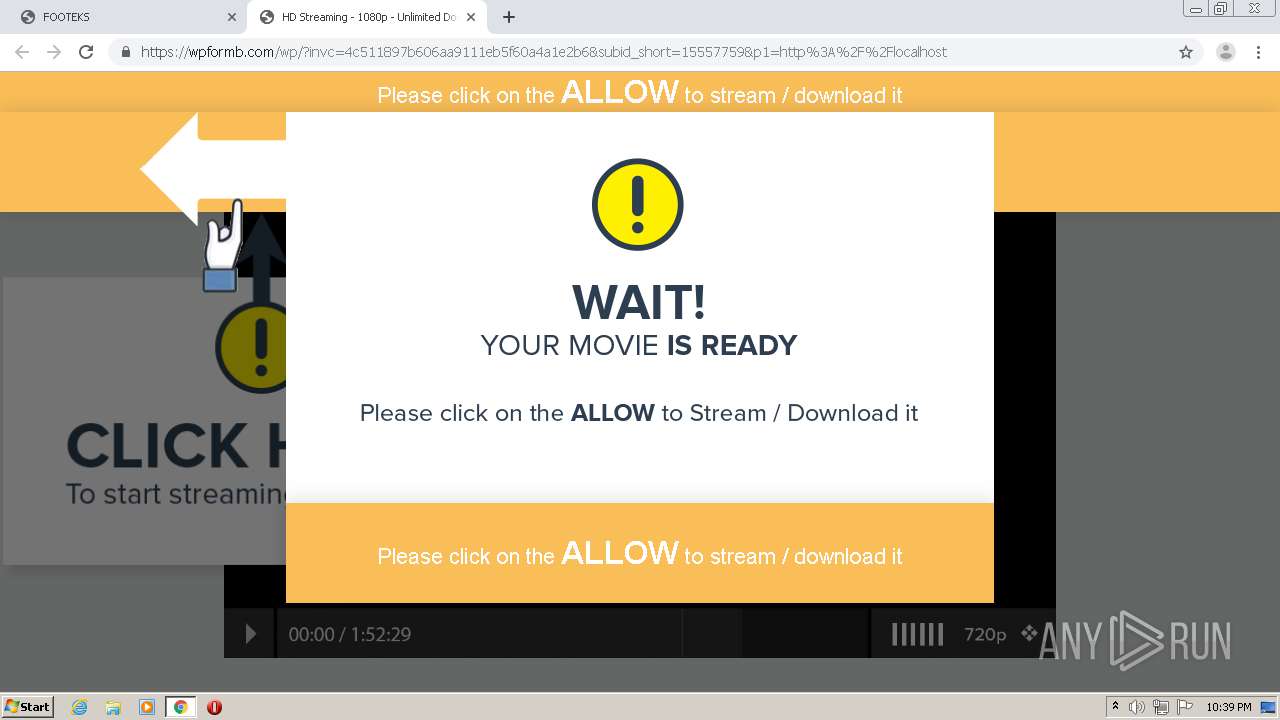
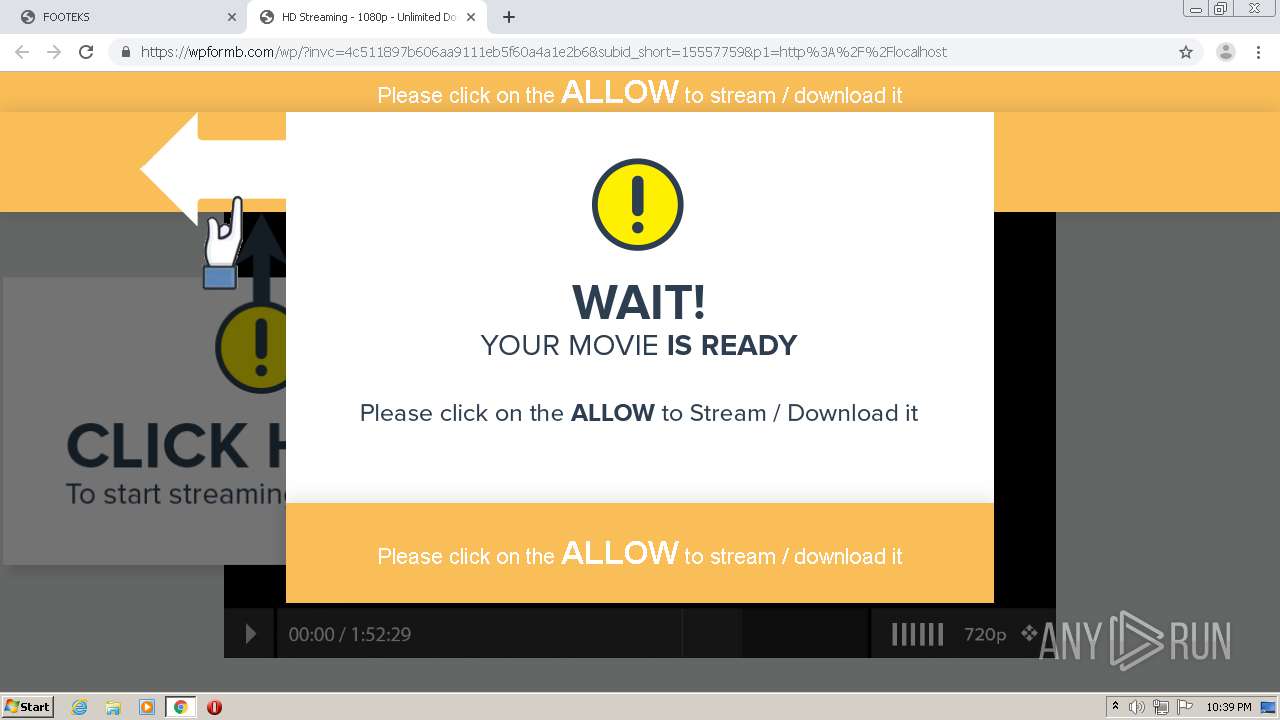
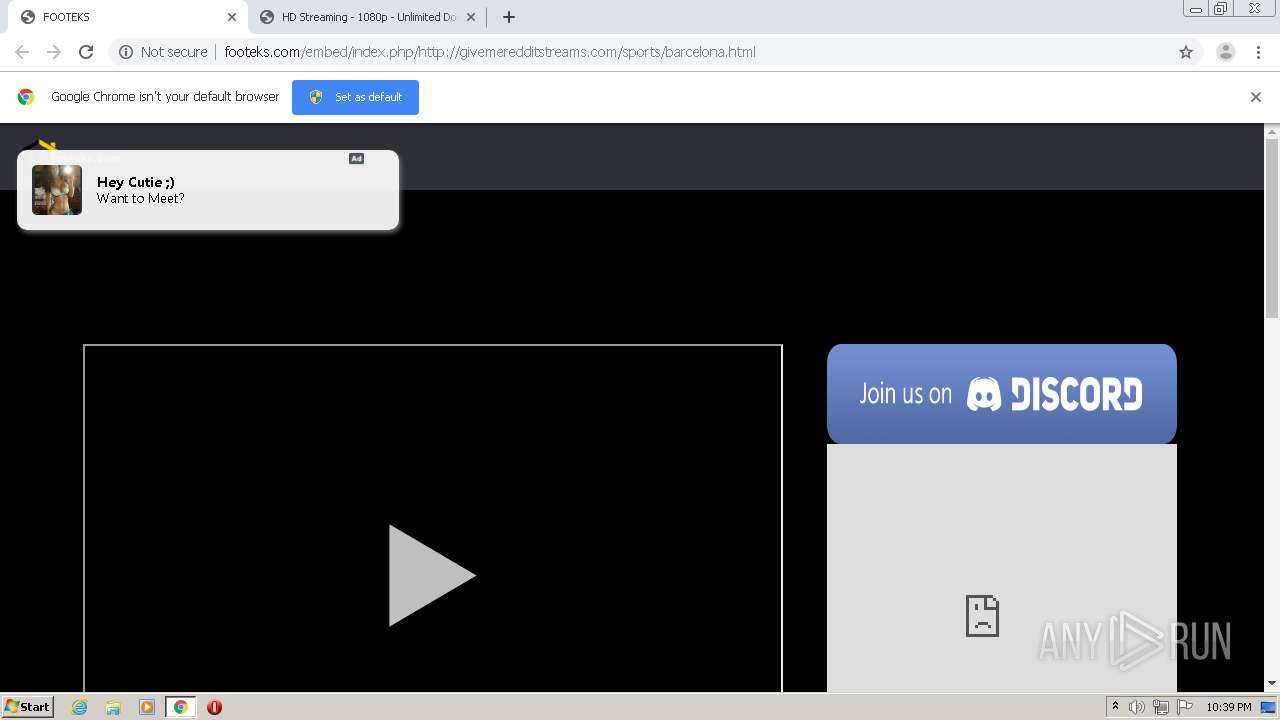
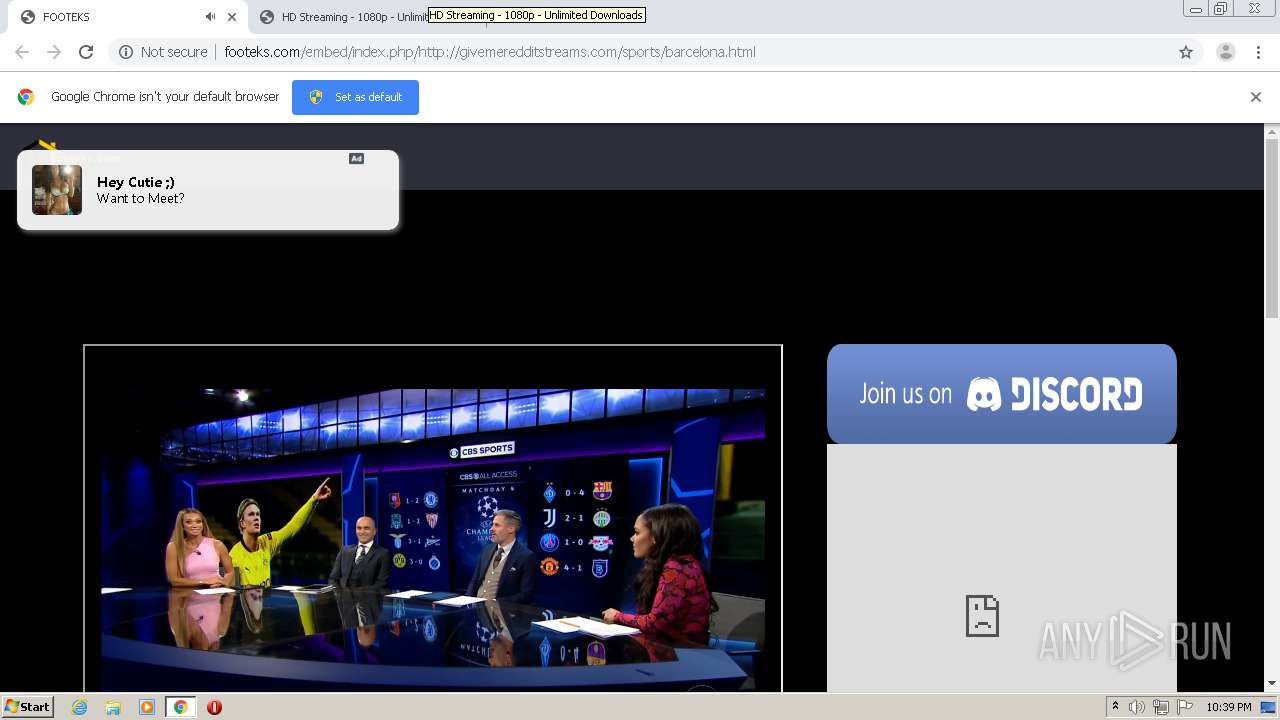
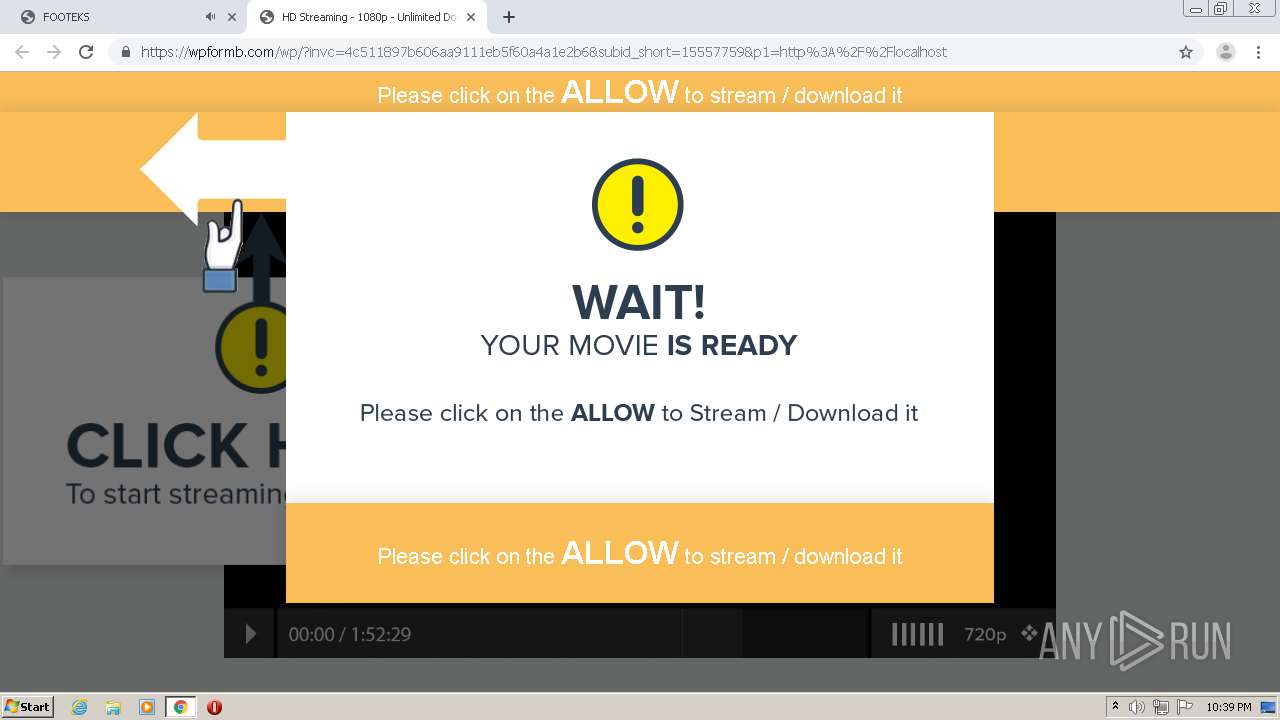
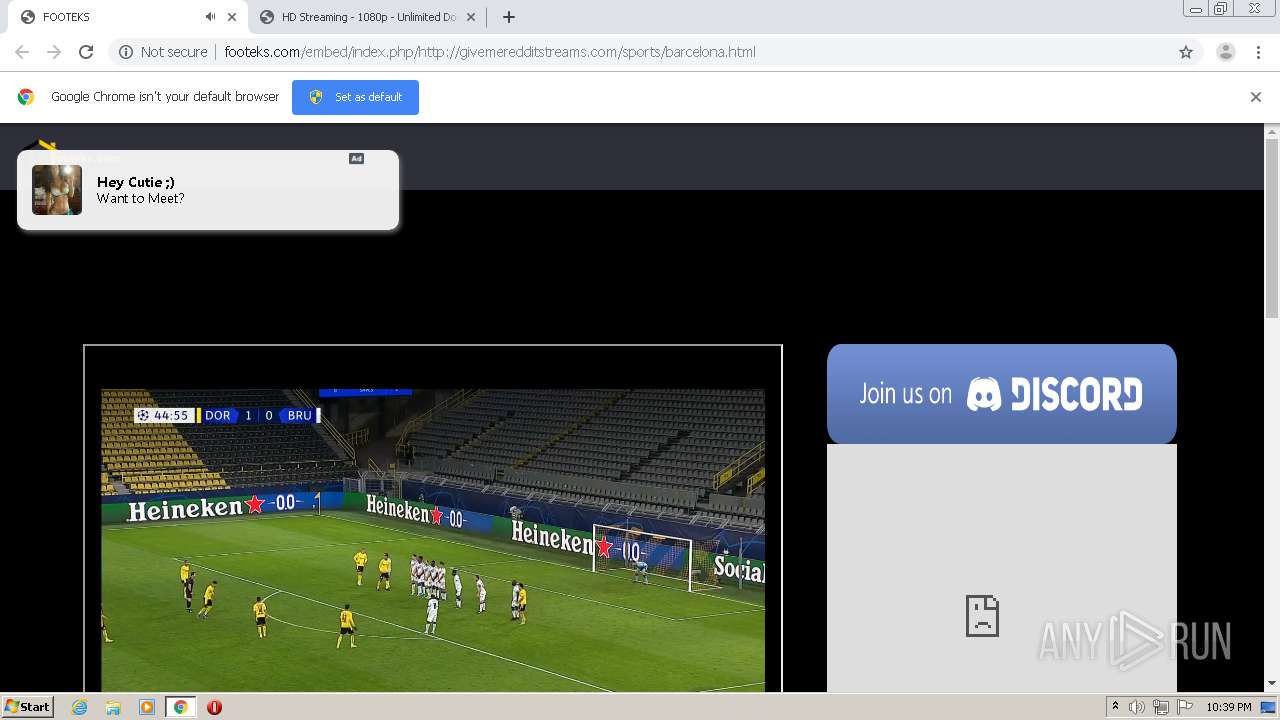
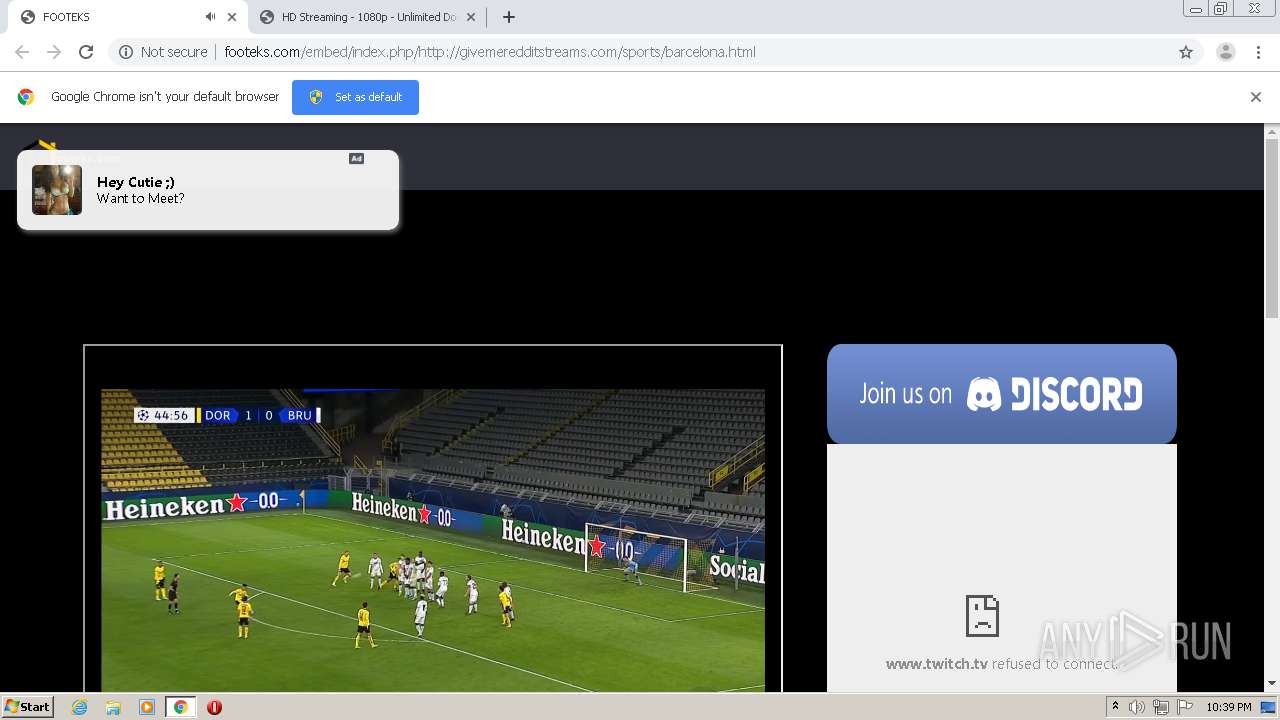
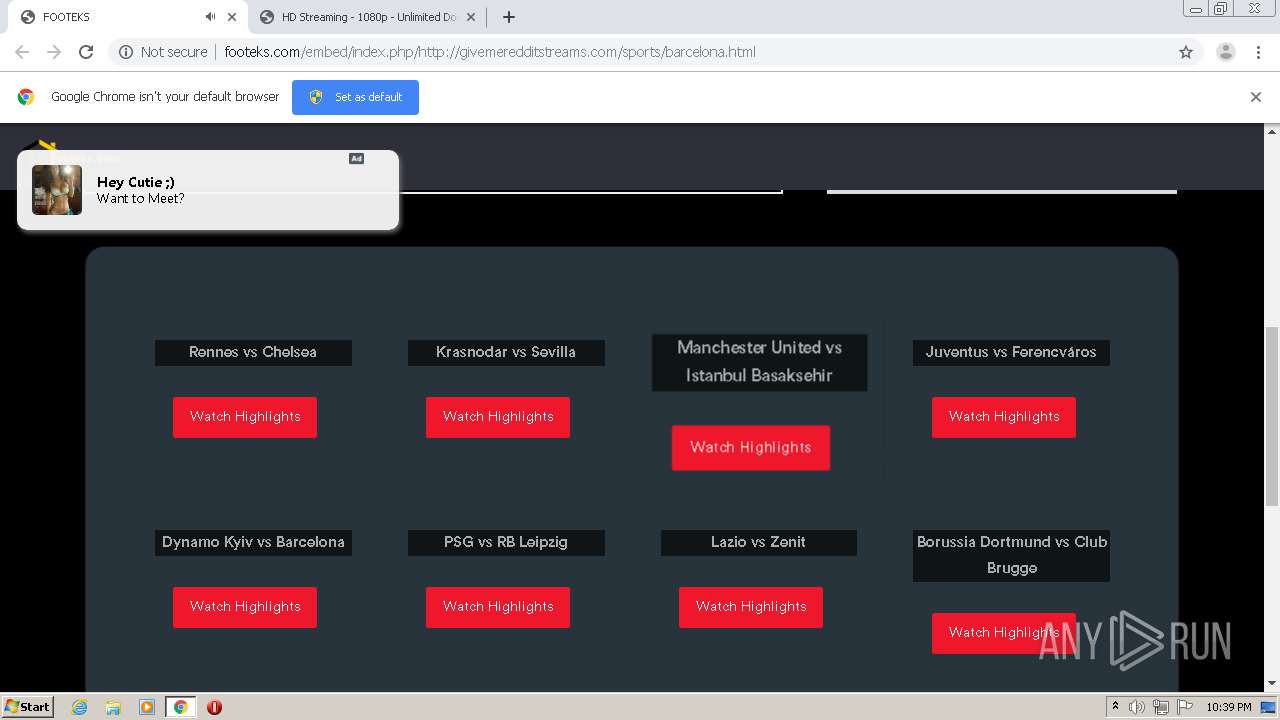
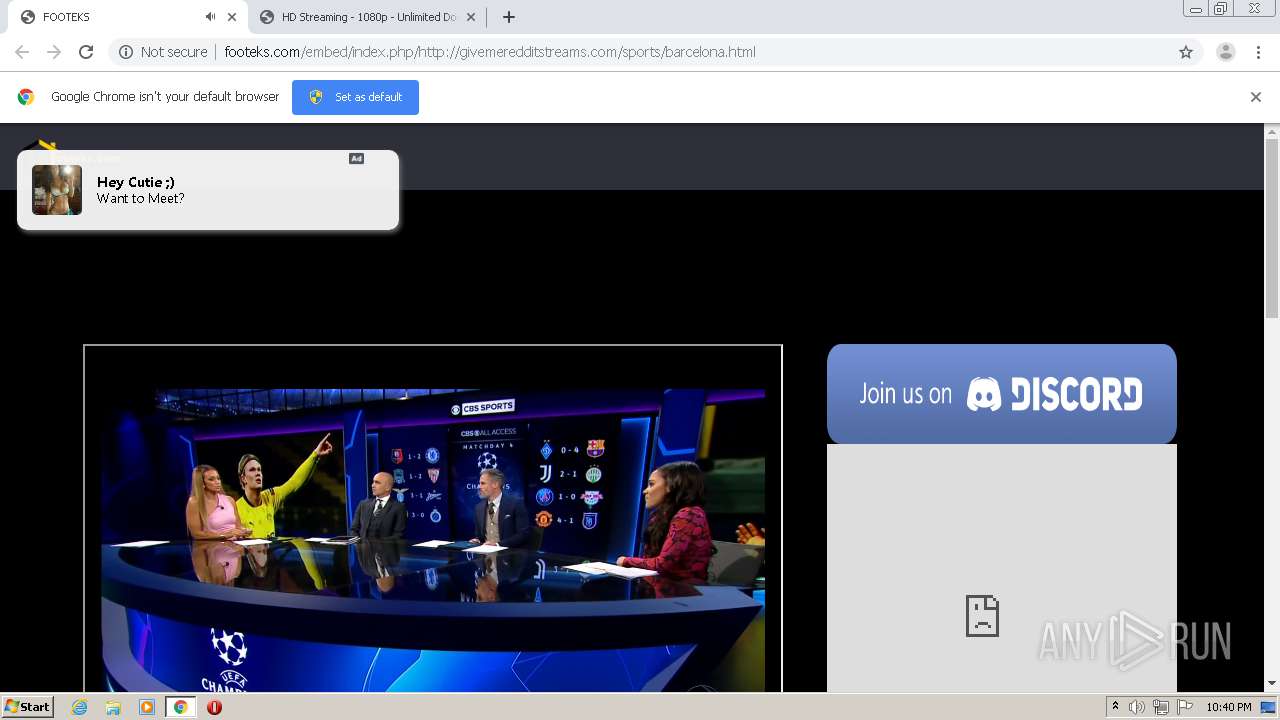
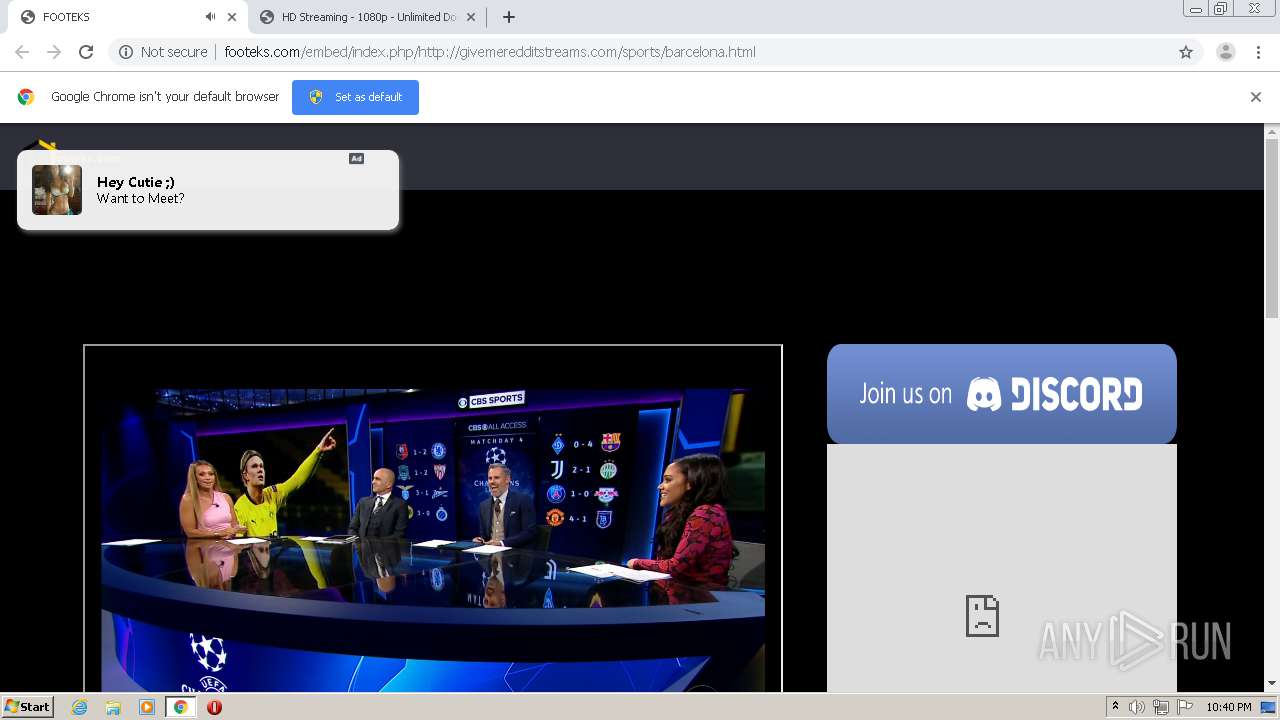
| URL: | http://footeks.com/embed/index.php/http://givemeredditstreams.com/sports/barcelona.html |
| Full analysis: | https://app.any.run/tasks/218fc434-abec-404b-ae8b-5e92ca289b68 |
| Verdict: | Malicious activity |
| Analysis date: | November 24, 2020, 22:39:03 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | BF5BAF3B5A0B79EF6E274B5CDC6330C9 |
| SHA1: | 0C8DA2C9463A49E142A6614B724D2CD4A6CBD367 |
| SHA256: | 6172F34F1471FB34E37771E57512061CBE614B0CDD49C32C3F68611620C2C5BA |
| SSDEEP: | 3:N1KYwsK3A7CHWlfkMTA9QB6wRXhfRWVAEk9:CYwEGHWFFM9U6fVW9 |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Reads the hosts file
- chrome.exe (PID: 840)
- chrome.exe (PID: 2056)
Application launched itself
- chrome.exe (PID: 840)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
54
Monitored processes
18
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 332 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1020,16008868883977782734,15711290928351378626,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=4956581817094517459 --renderer-client-id=14 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3816 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 840 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --disk-cache-dir=null --disk-cache-size=1 --media-cache-size=1 --disable-gpu-shader-disk-cache --disable-background-networking "http://footeks.com/embed/index.php/http://givemeredditstreams.com/sports/barcelona.html" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1340 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1020,16008868883977782734,15711290928351378626,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgACAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=8385628929646009133 --mojo-platform-channel-handle=1032 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1508 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1020,16008868883977782734,15711290928351378626,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=2868623200173535565 --renderer-client-id=8 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3184 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2036 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1020,16008868883977782734,15711290928351378626,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=8204109061106089535 --renderer-client-id=7 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3208 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2052 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1020,16008868883977782734,15711290928351378626,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=17314050402501147475 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2172 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2056 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1020,16008868883977782734,15711290928351378626,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=11924857019194363397 --mojo-platform-channel-handle=1480 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2096 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1020,16008868883977782734,15711290928351378626,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgACAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=3103177475412396005 --mojo-platform-channel-handle=4308 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2464 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1020,16008868883977782734,15711290928351378626,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=10073455316215125737 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2180 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2492 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1020,16008868883977782734,15711290928351378626,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=5174952730239059862 --renderer-client-id=9 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3492 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
605
Read events
546
Write events
56
Delete events
3
Modification events
| (PID) Process: | (2656) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 840-13250731157916375 |
Value: 259 | |||
| (PID) Process: | (840) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (840) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (840) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (840) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (840) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (840) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (840) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (840) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3252-13245750958665039 |
Value: 0 | |||
| (PID) Process: | (840) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
0
Suspicious files
24
Text files
62
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 840 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5FBD8B96-348.pma | — | |
MD5:— | SHA256:— | |||
| 840 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\87a08d95-17d0-495f-8596-6dc5906403a5.tmp | — | |
MD5:— | SHA256:— | |||
| 840 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000048.dbtmp | — | |
MD5:— | SHA256:— | |||
| 840 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2720 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\CrashpadMetrics.pma | binary | |
MD5:B59113C2DCD2D346F31A64F231162ADA | SHA256:1D97C69AEA85D3B06787458EA47576B192CE5C5DB9940E5EAA514FF977CE2DC2 | |||
| 840 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:1A89A1BEBE6C843C4FF582E7ED33CA1F | SHA256:65099CA087B66AA8CA420AB121DAAD713E1DB5A61C5A574D9B1C0DF24F012520 | |||
| 840 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:FB5B20517A0D1F7DAD485989565BEE5E | SHA256:99405F66EDBEB2306F4D0B4469DCADFF5293B5E1549C588CCFACEA439BB3B101 | |||
| 840 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RFfcb65.TMP | text | |
MD5:C2DDBA63E4A2BD2E39A8B6C2C6384AAE | SHA256:6D5C1C78341C6F84911055D970ADDB0EC3499F8BF7FADE062122A22209CE67D9 | |||
| 840 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 840 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RFfcd59.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
59
TCP/UDP connections
69
DNS requests
42
Threats
8
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2056 | chrome.exe | GET | 200 | 104.27.181.46:80 | http://footeks.com/embed/index.php/http://givemeredditstreams.com/sports/barcelona.html | US | html | 2.46 Kb | malicious |
2056 | chrome.exe | GET | 200 | 104.27.181.46:80 | http://footeks.com/embed/vendor/fonts/circular-std/style.css | US | text | 269 b | malicious |
2056 | chrome.exe | GET | 200 | 104.27.181.46:80 | http://footeks.com/embed/css/style.css | US | text | 20.5 Kb | malicious |
2056 | chrome.exe | GET | 200 | 104.27.181.46:80 | http://footeks.com/embed/vendor/bootstrap/css/bootstrap.min.css | US | text | 20.5 Kb | malicious |
2056 | chrome.exe | GET | 204 | 65.9.70.118:80 | http://d1ukp4rdr0i4nl.cloudfront.net/?rpkud=903152 | US | — | — | whitelisted |
2056 | chrome.exe | GET | 200 | 104.27.181.46:80 | http://footeks.com/embed/vendor/fonts/fontawesome/css/fontawesome-all.css | US | text | 8.27 Kb | malicious |
2056 | chrome.exe | GET | 200 | 104.27.181.46:80 | http://footeks.com/embed/vendor/charts/chartist-bundle/chartist.css | US | text | 1.54 Kb | malicious |
2056 | chrome.exe | GET | 200 | 104.27.181.46:80 | http://footeks.com/embed/vendor/fonts/material-design-iconic-font/css/materialdesignicons.min.css | US | text | 14.2 Kb | malicious |
2056 | chrome.exe | GET | 200 | 104.27.181.46:80 | http://footeks.com/embed/vendor/charts/morris-bundle/morris.css | US | text | 413 b | malicious |
2056 | chrome.exe | GET | 200 | 104.27.181.46:80 | http://footeks.com/embed/vendor/charts/c3charts/c3.css | US | text | 1.03 Kb | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2056 | chrome.exe | 195.181.175.48:443 | www.displayvertising.com | Datacamp Limited | DE | suspicious |
2056 | chrome.exe | 104.27.181.46:80 | footeks.com | Cloudflare Inc | US | shared |
2056 | chrome.exe | 216.58.207.45:443 | accounts.google.com | Google Inc. | US | whitelisted |
2056 | chrome.exe | 65.9.70.118:80 | d3dq1nh1l1pzqy.cloudfront.net | AT&T Services, Inc. | US | whitelisted |
2056 | chrome.exe | 104.18.58.176:443 | fmnetwork.nl | Cloudflare Inc | US | shared |
2056 | chrome.exe | 104.24.108.24:80 | stream-cr7.net | Cloudflare Inc | US | shared |
2056 | chrome.exe | 104.27.138.26:80 | streamcr7.com | Cloudflare Inc | US | unknown |
2056 | chrome.exe | 99.86.7.60:443 | uinoringho.fun | AT&T Services, Inc. | US | suspicious |
2056 | chrome.exe | 99.84.156.2:80 | esusivebe.top | AT&T Services, Inc. | US | suspicious |
2056 | chrome.exe | 173.194.200.138:80 | www.google-analytics.com | Google Inc. | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
footeks.com |
| malicious |
accounts.google.com |
| shared |
d3dq1nh1l1pzqy.cloudfront.net |
| whitelisted |
d1ukp4rdr0i4nl.cloudfront.net |
| whitelisted |
fmnetwork.nl |
| malicious |
stream-cr7.net |
| malicious |
streamcr7.com |
| malicious |
uinoringho.fun |
| suspicious |
www.google-analytics.com |
| whitelisted |
esusivebe.top |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1056 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a *.top domain - Likely Hostile |
2056 | chrome.exe | Potentially Bad Traffic | ET INFO HTTP Request to a *.top domain |
2056 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Response) |
2056 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Response) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Response) |