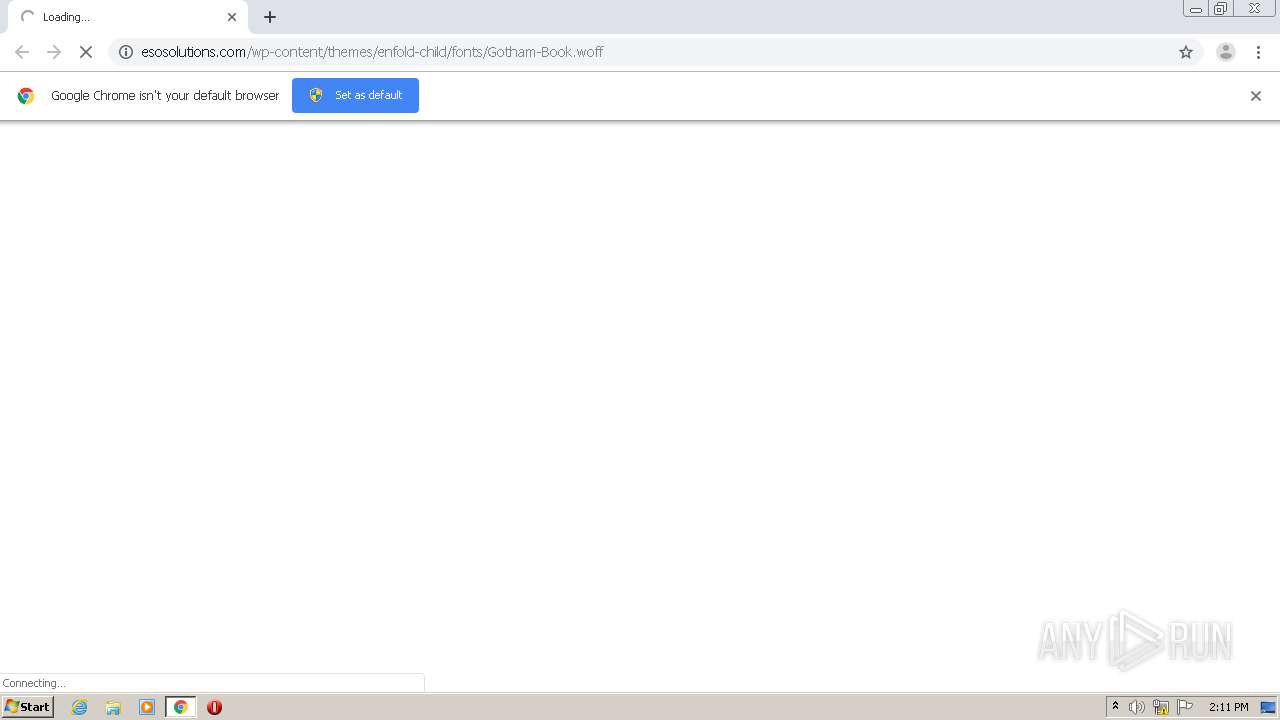
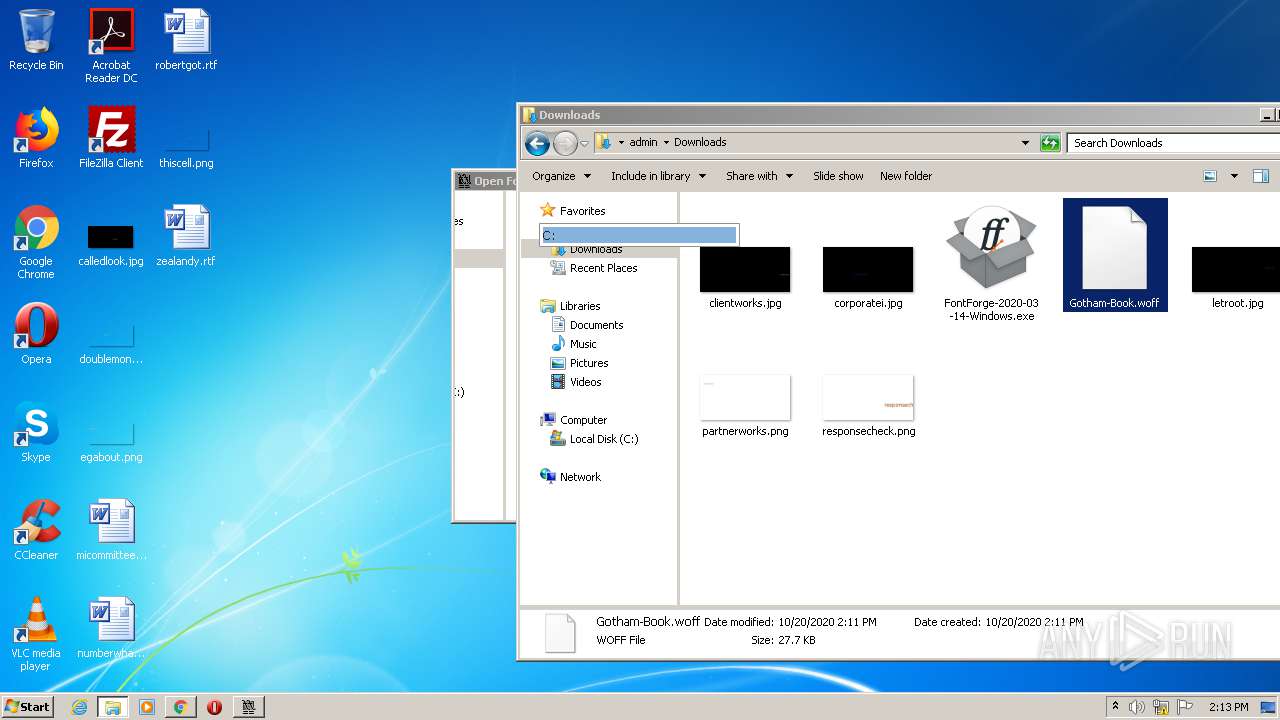
| URL: | http://esosolutions.com/wp-content/themes/enfold-child/fonts/Gotham-Book.woff |
| Full analysis: | https://app.any.run/tasks/c05f8eac-315b-4d1d-a7aa-19e41ec3789d |
| Verdict: | Malicious activity |
| Analysis date: | October 20, 2020, 13:10:49 |
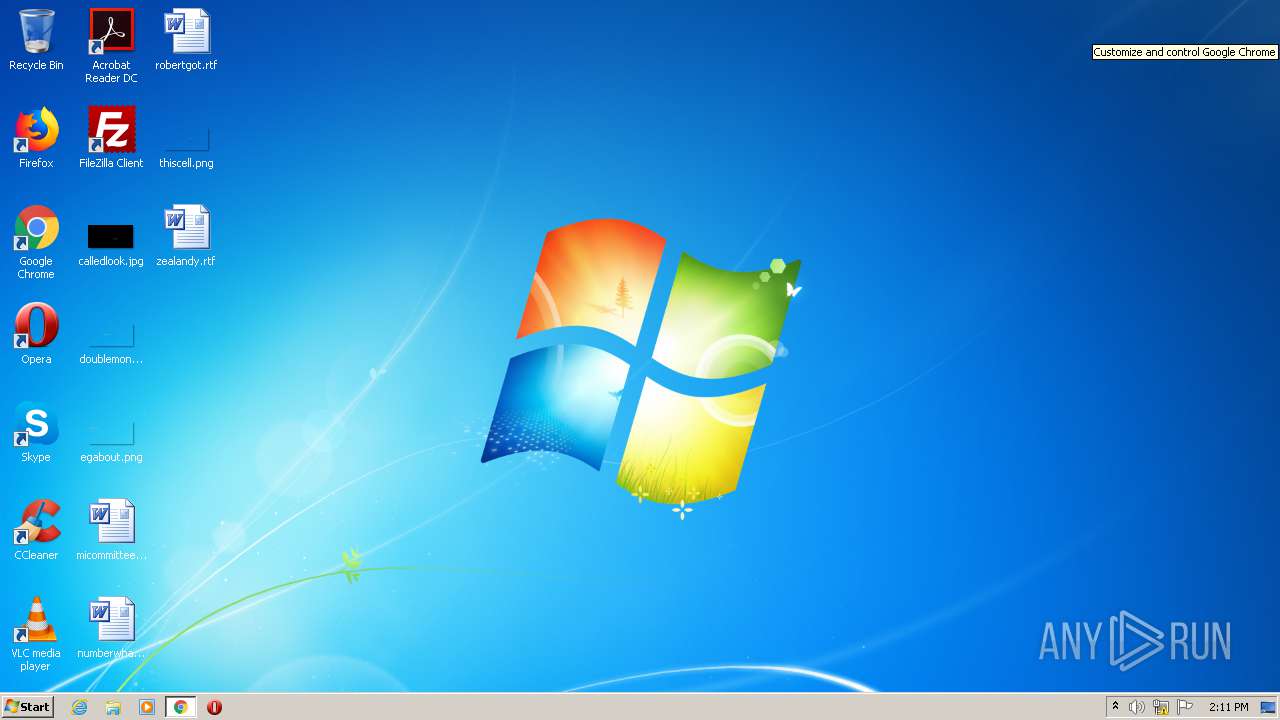
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 3006078F4B5873C7769F51FC5A730E65 |
| SHA1: | 3BABB245E2E0DBEFE361EC4434F33A6EC7CF4A94 |
| SHA256: | 616FB70CCCDC52366F7FCEC2E555016785E9B148A85C7C2E77D000C88FF7C18F |
| SSDEEP: | 3:N1KbNsuiVOlAQrFuJBBMRZW1W5f:CZiVOlAkFuPBN1WB |
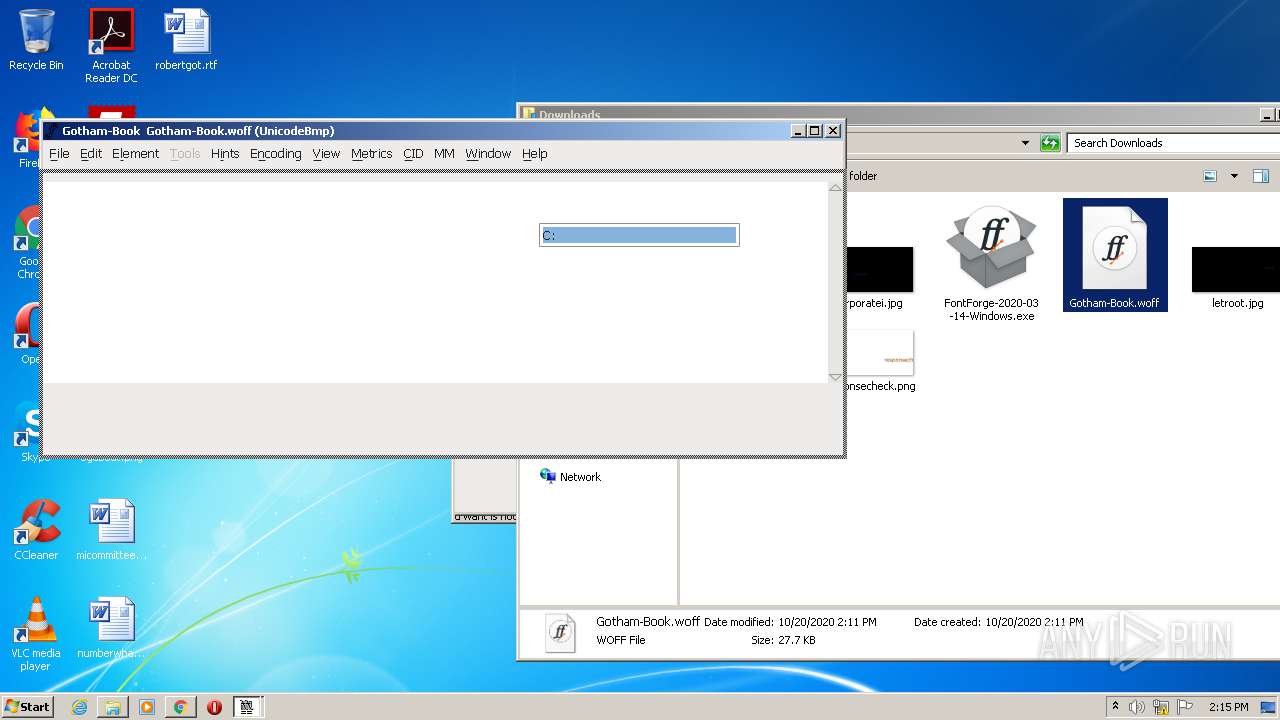
MALICIOUS
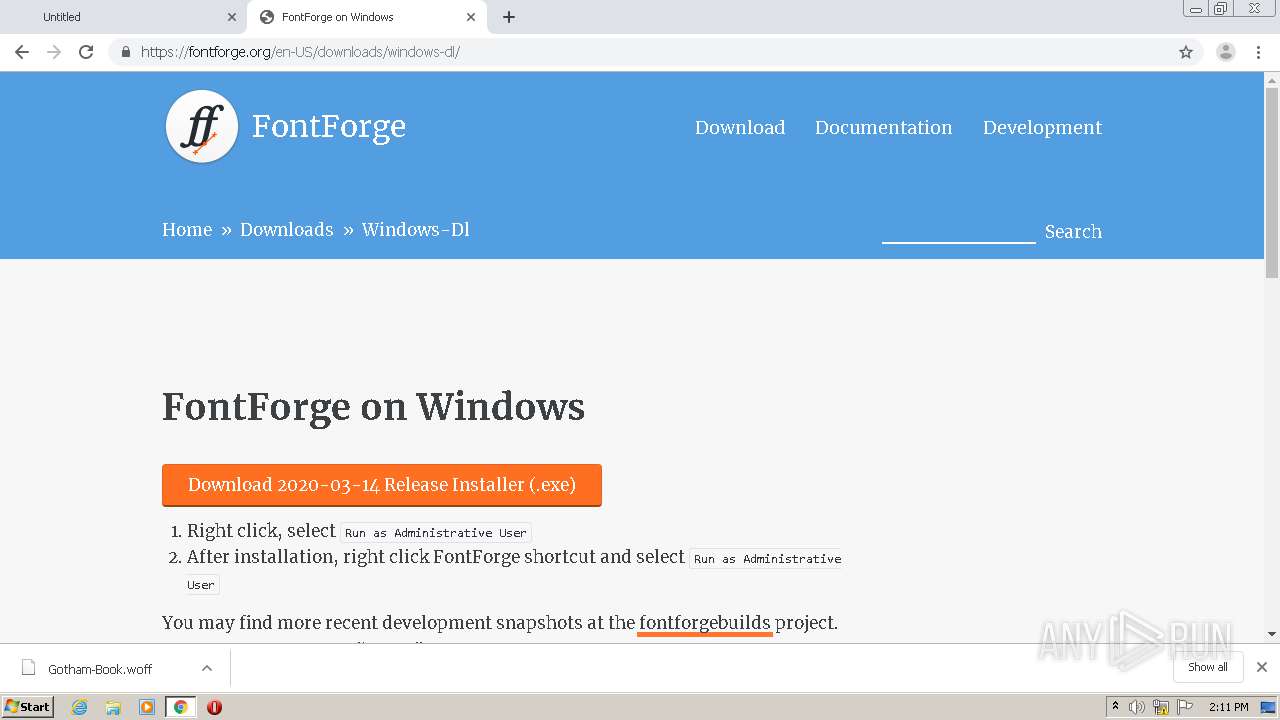
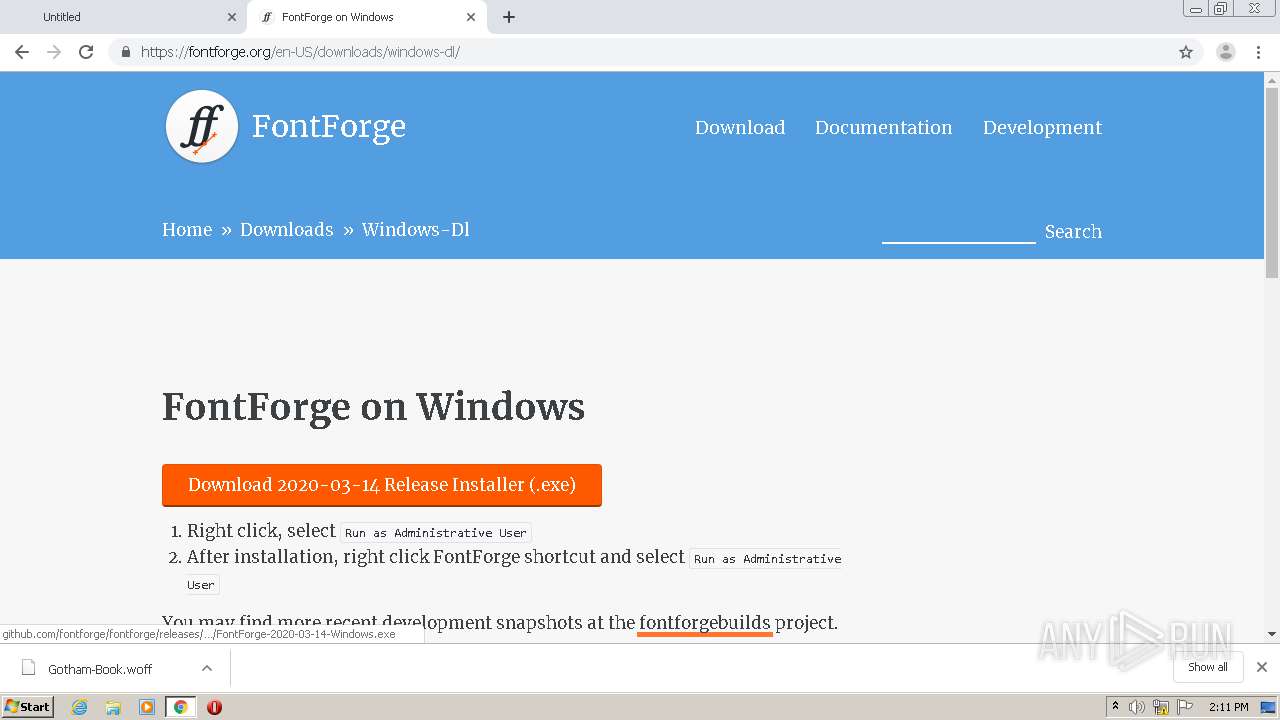
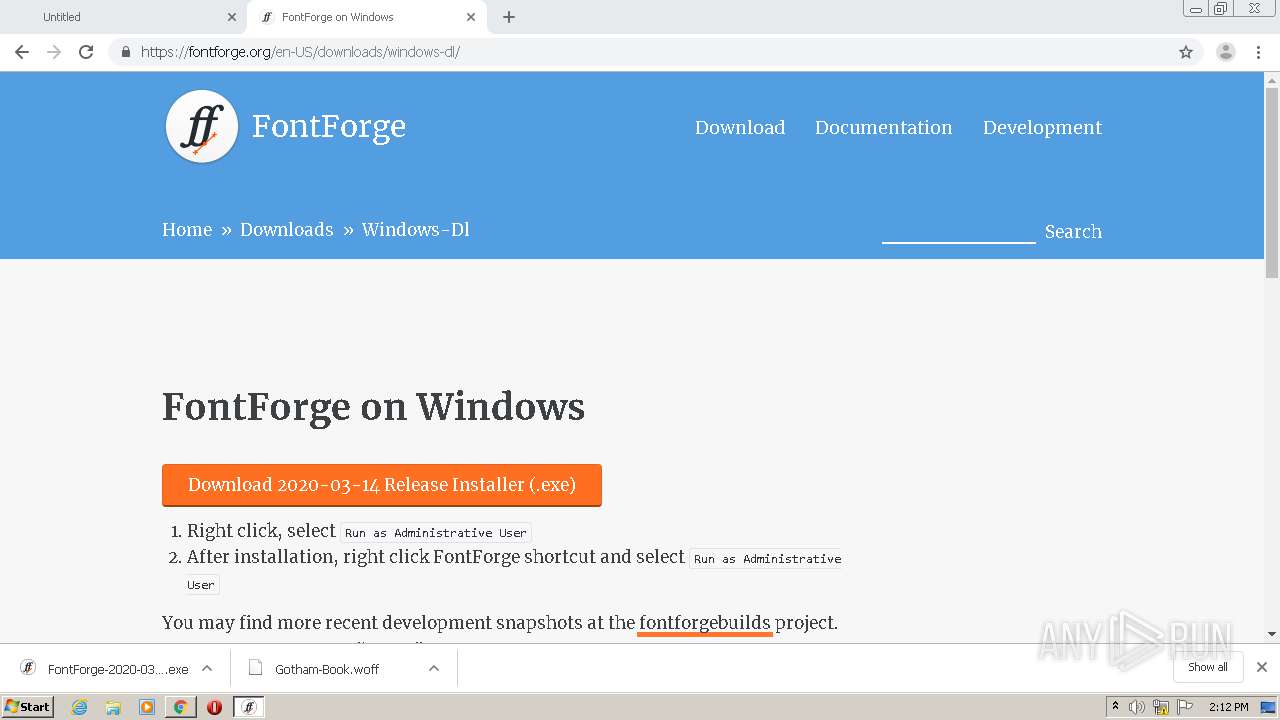
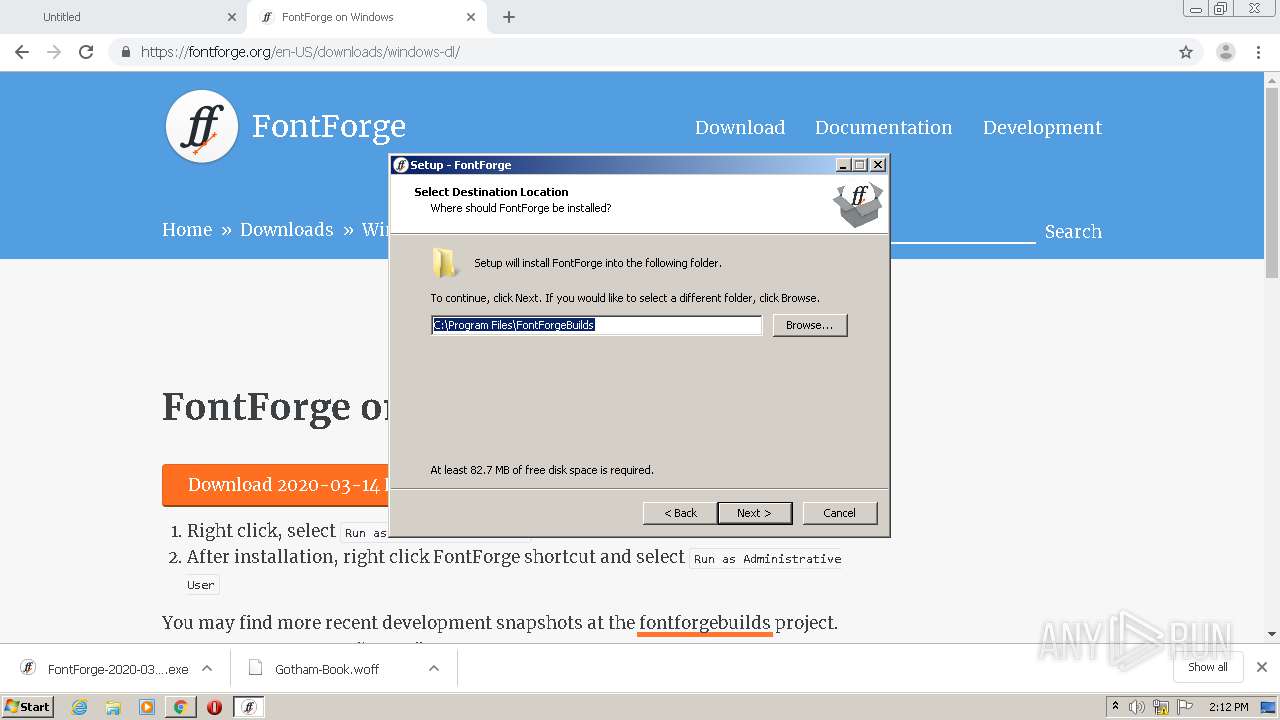
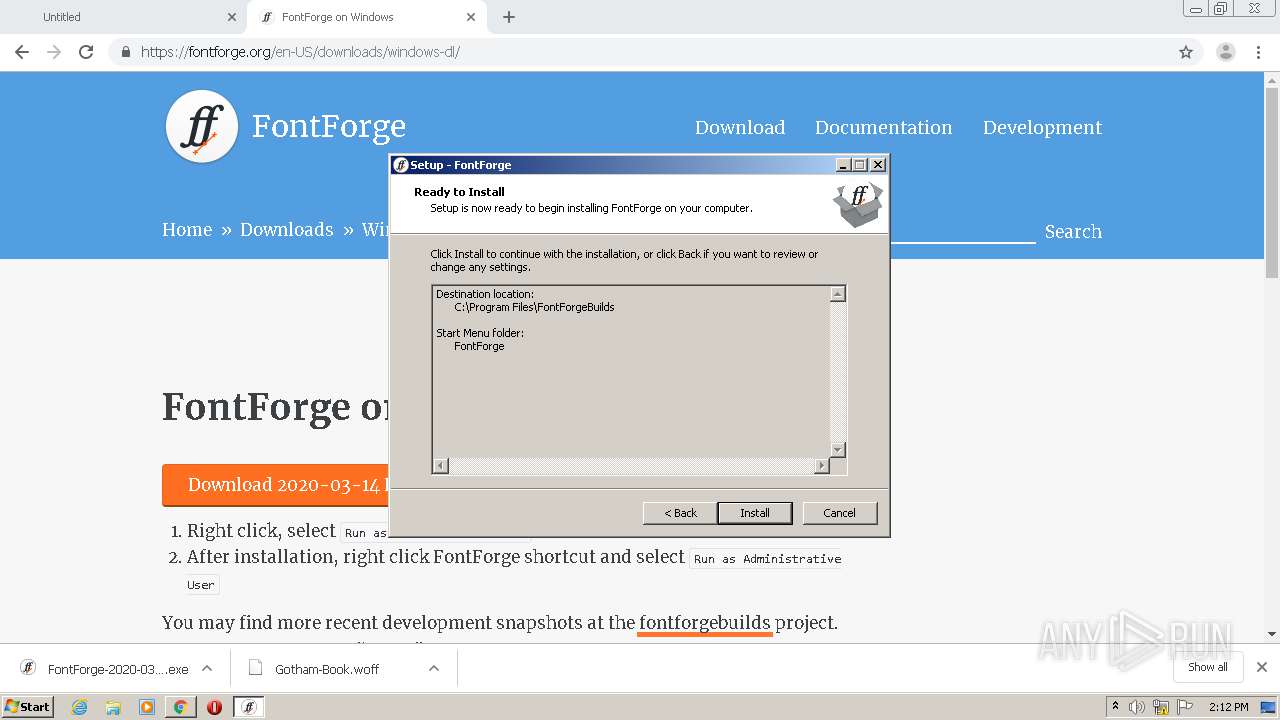
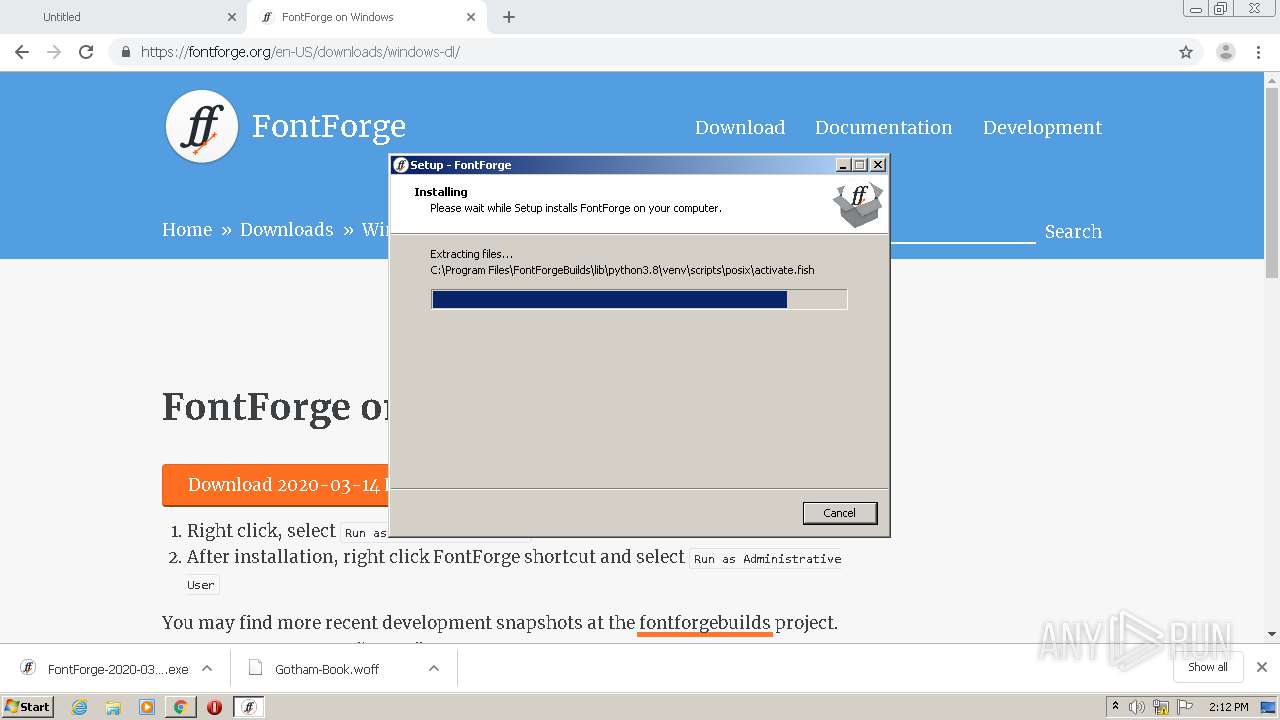
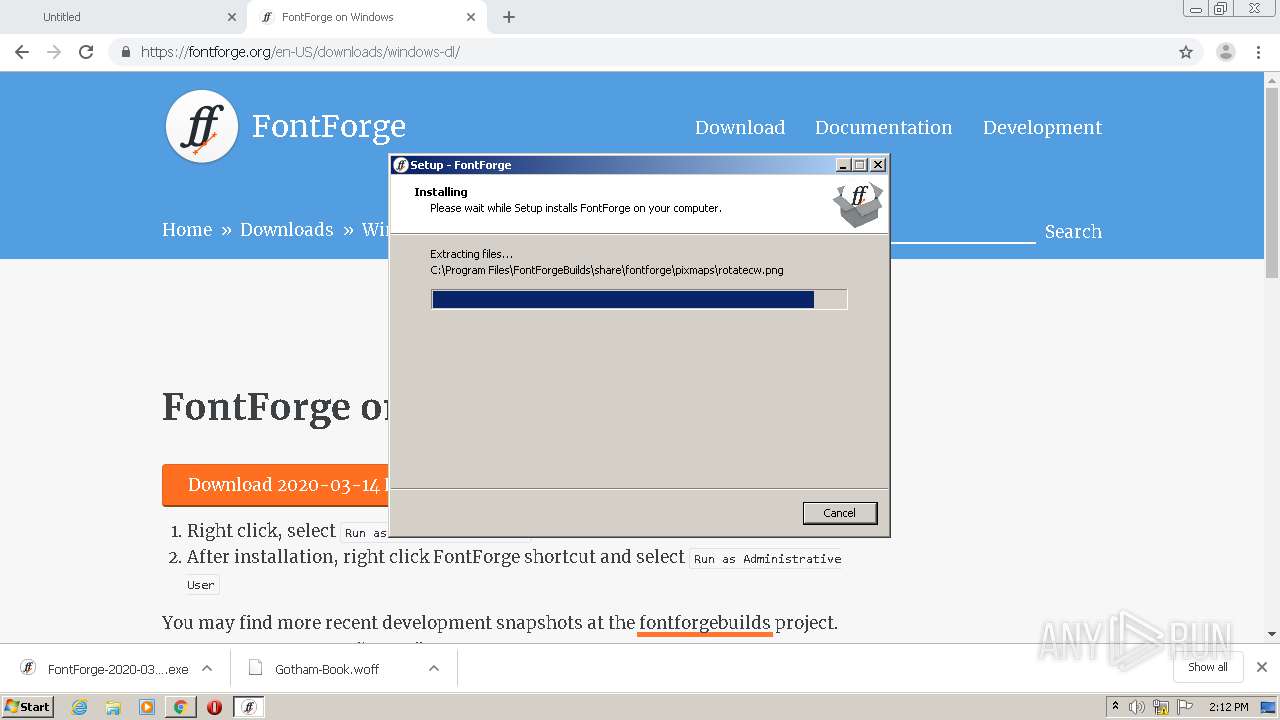
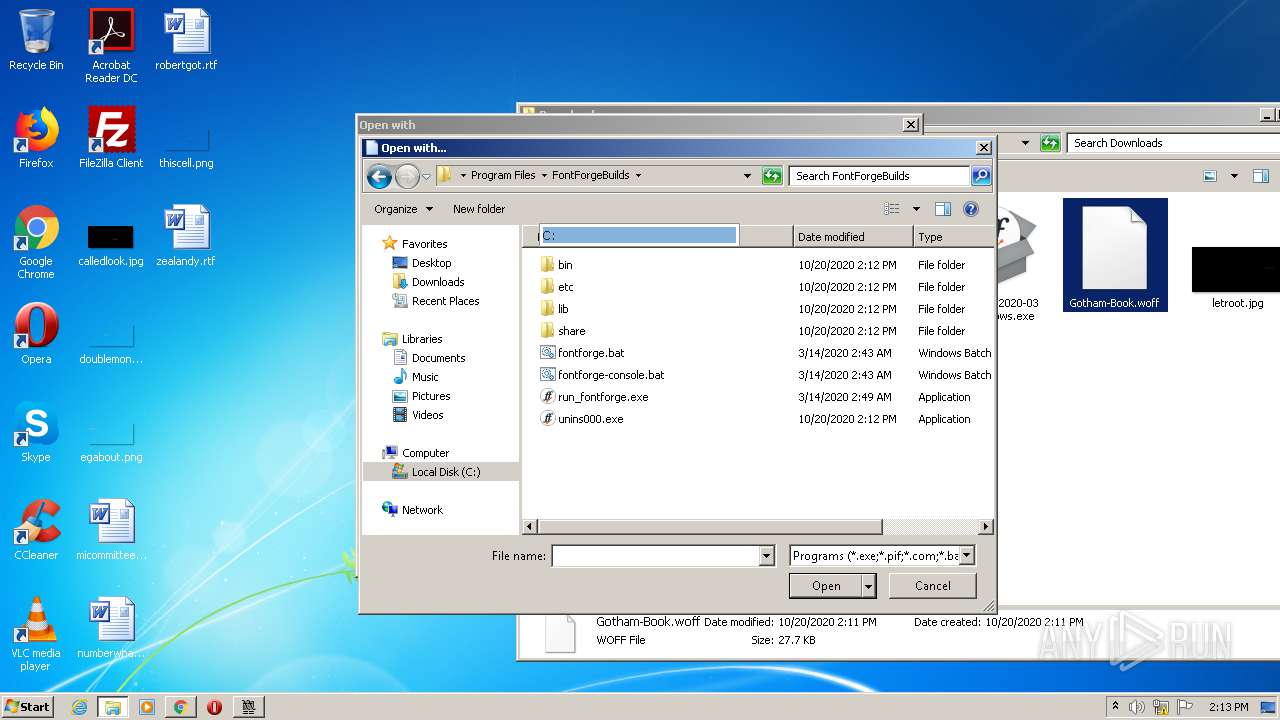
Application was dropped or rewritten from another process
- FontForge-2020-03-14-Windows.exe (PID: 1520)
- FontForge-2020-03-14-Windows.exe (PID: 4004)
- run_fontforge.exe (PID: 3112)
- fontforge.exe (PID: 1508)
- run_fontforge.exe (PID: 4016)
- fontforge.exe (PID: 4084)
Loads dropped or rewritten executable
- fontforge.exe (PID: 4084)
- fontforge.exe (PID: 1508)
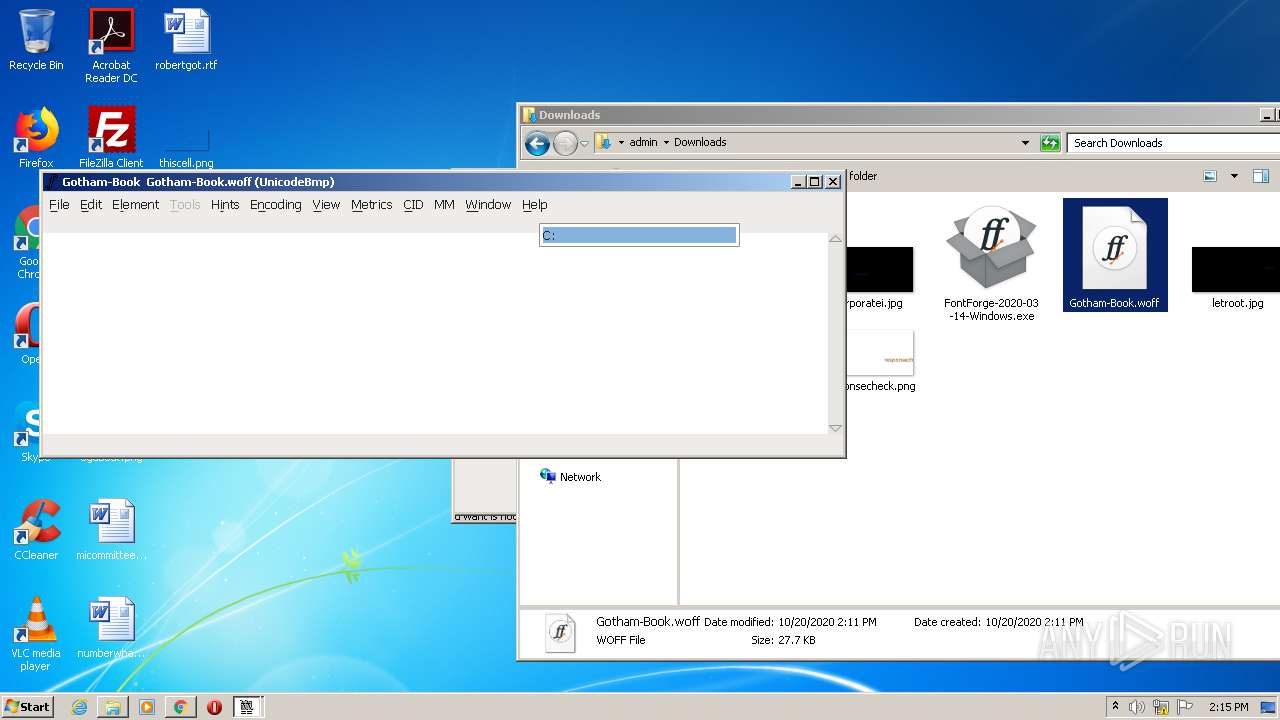
SUSPICIOUS
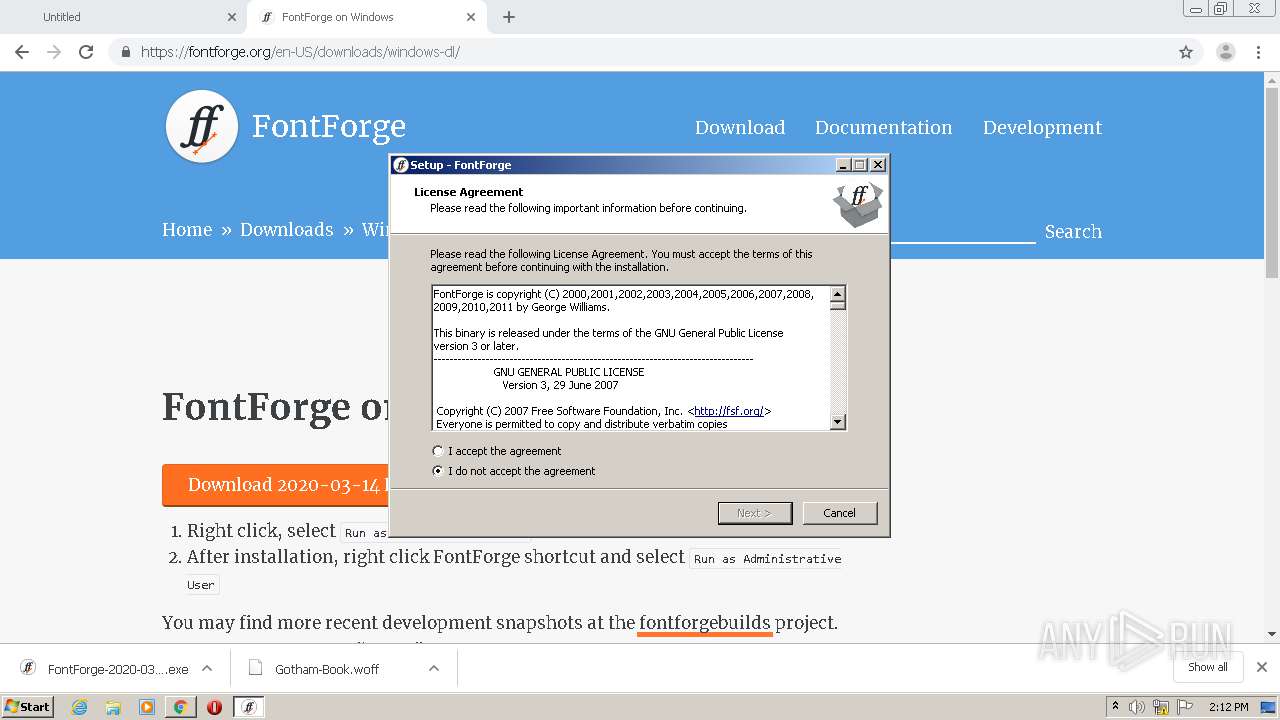
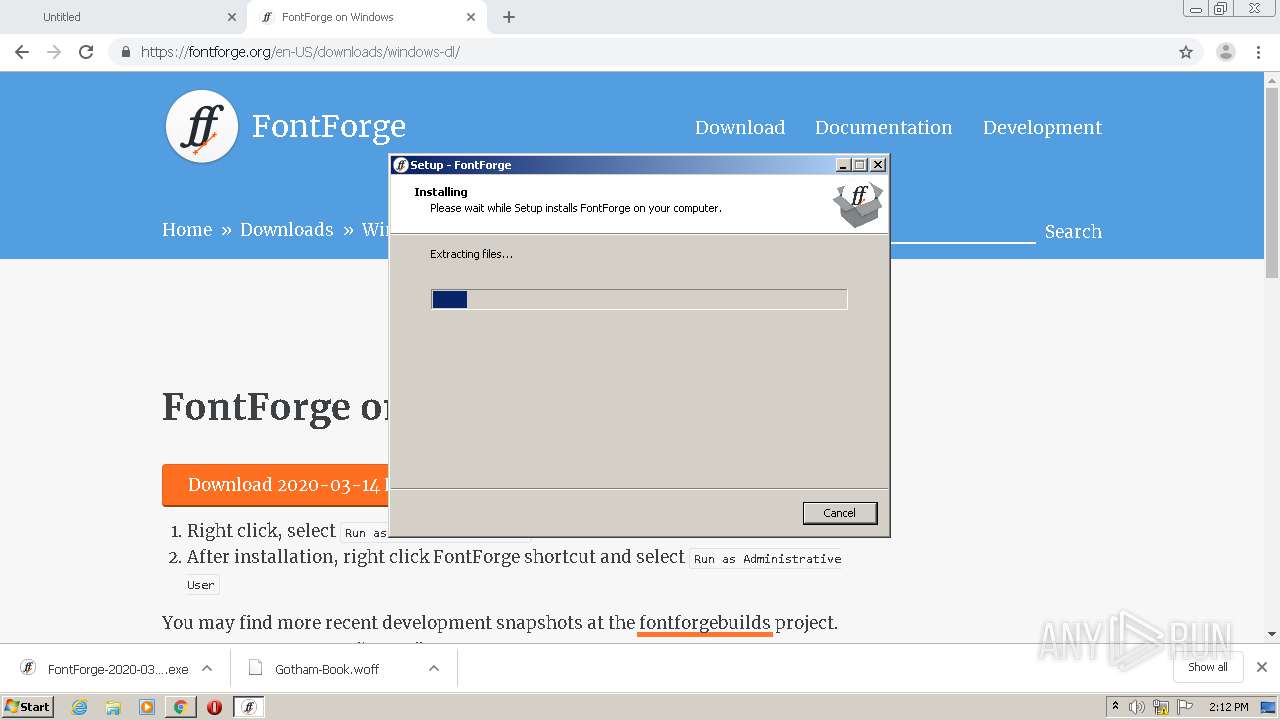
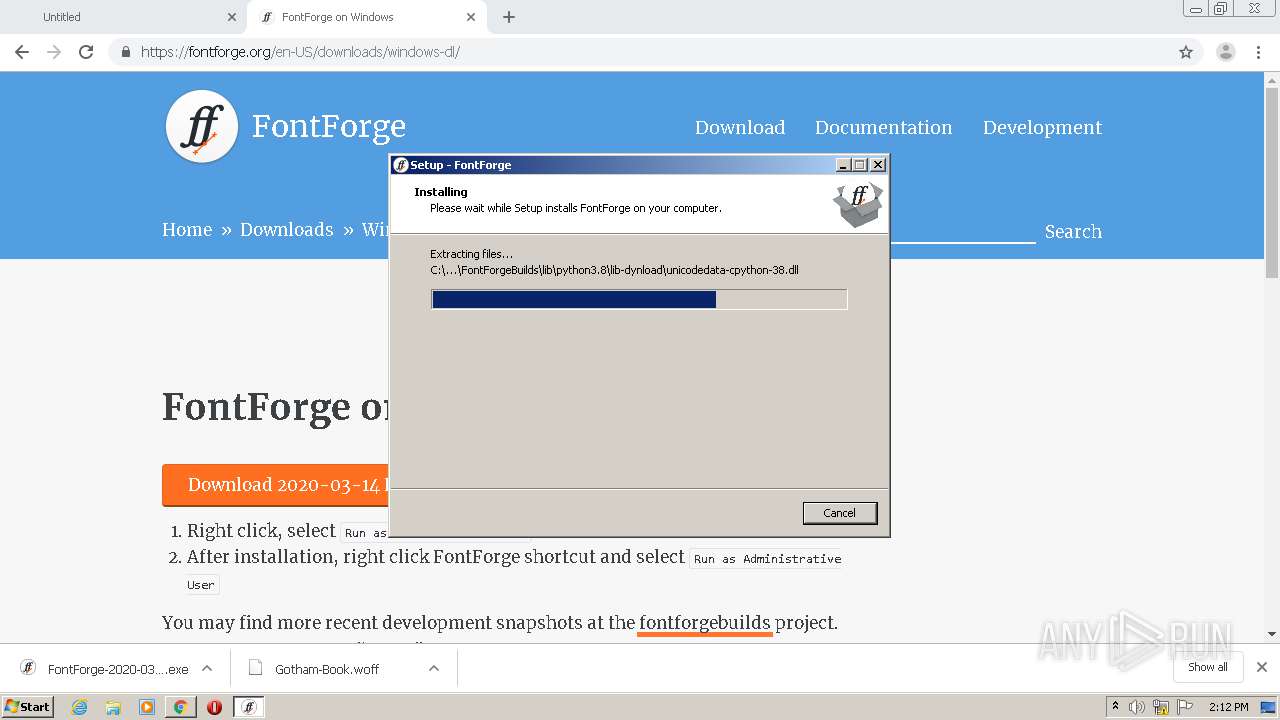
Executable content was dropped or overwritten
- FontForge-2020-03-14-Windows.exe (PID: 1520)
- chrome.exe (PID: 2688)
- chrome.exe (PID: 2380)
- FontForge-2020-03-14-Windows.exe (PID: 4004)
- FontForge-2020-03-14-Windows.tmp (PID: 1864)
Reads Windows owner or organization settings
- FontForge-2020-03-14-Windows.tmp (PID: 1864)
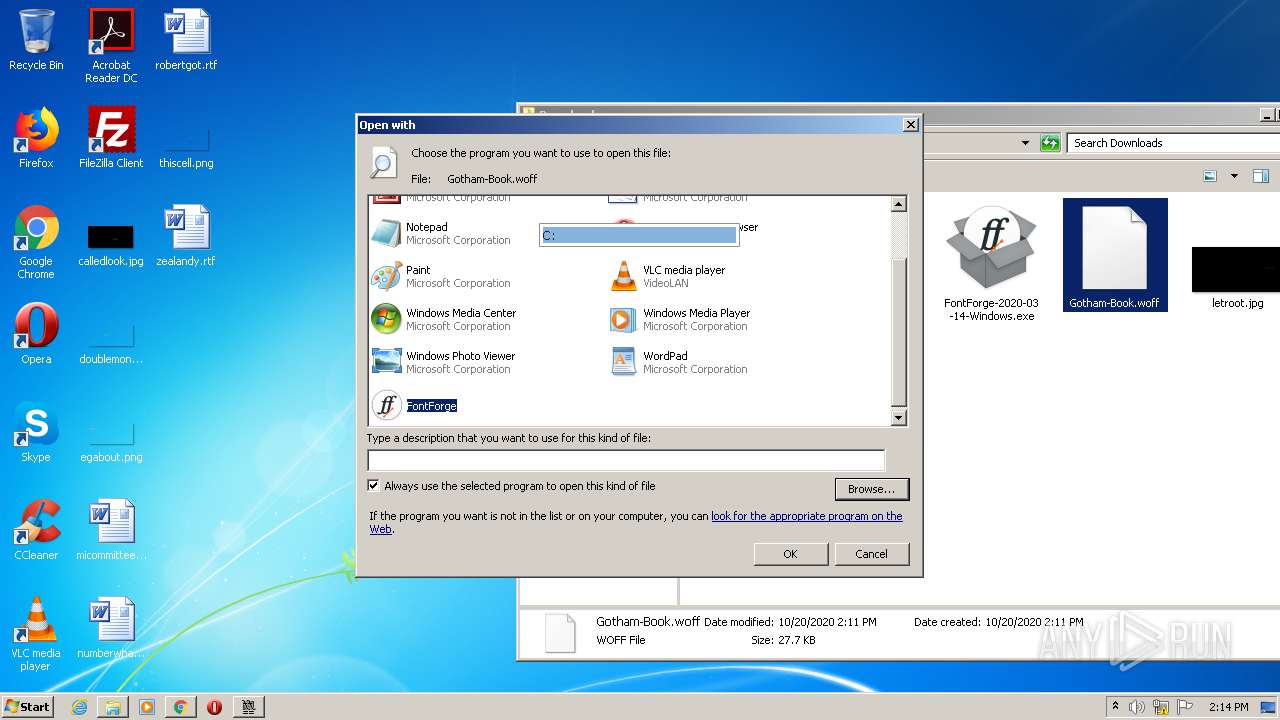
Modifies the open verb of a shell class
- FontForge-2020-03-14-Windows.tmp (PID: 1864)
Reads the Windows organization settings
- FontForge-2020-03-14-Windows.tmp (PID: 1864)
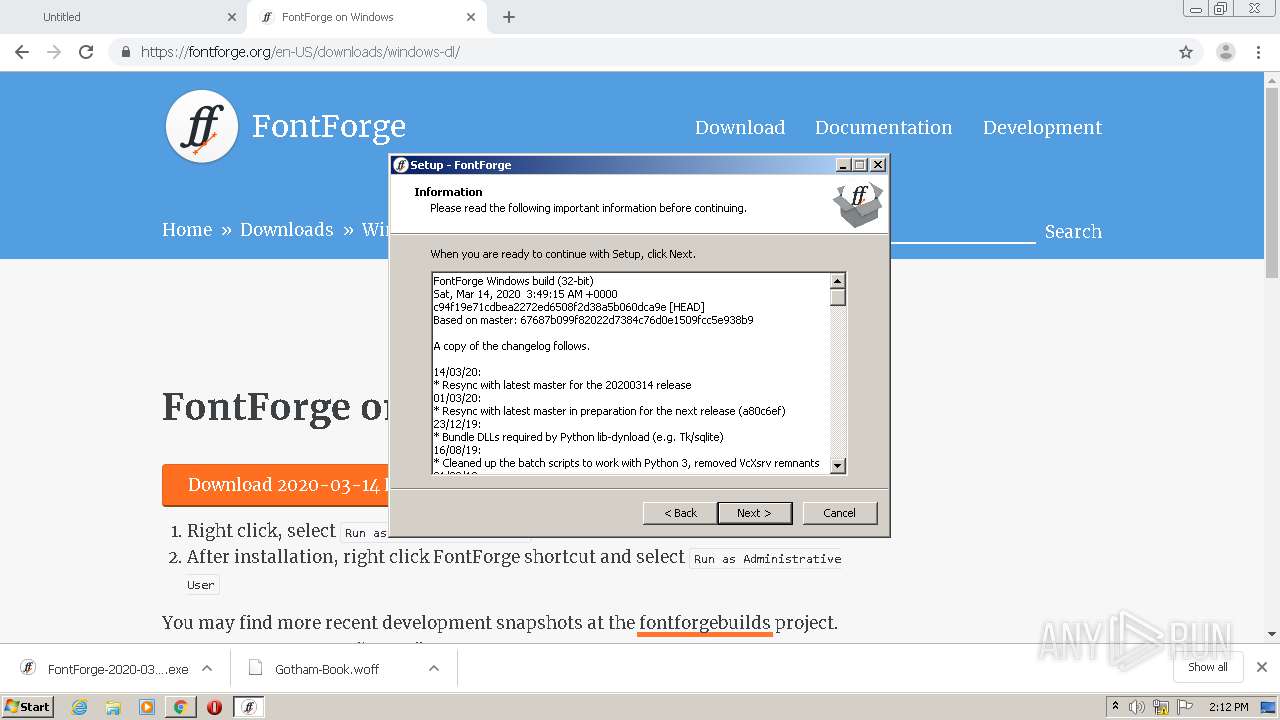
Starts CMD.EXE for commands execution
- run_fontforge.exe (PID: 3112)
- cmd.exe (PID: 252)
- run_fontforge.exe (PID: 4016)
- cmd.exe (PID: 2872)
Application launched itself
- cmd.exe (PID: 252)
- cmd.exe (PID: 2872)
Creates files in the user directory
- fontforge.exe (PID: 1508)
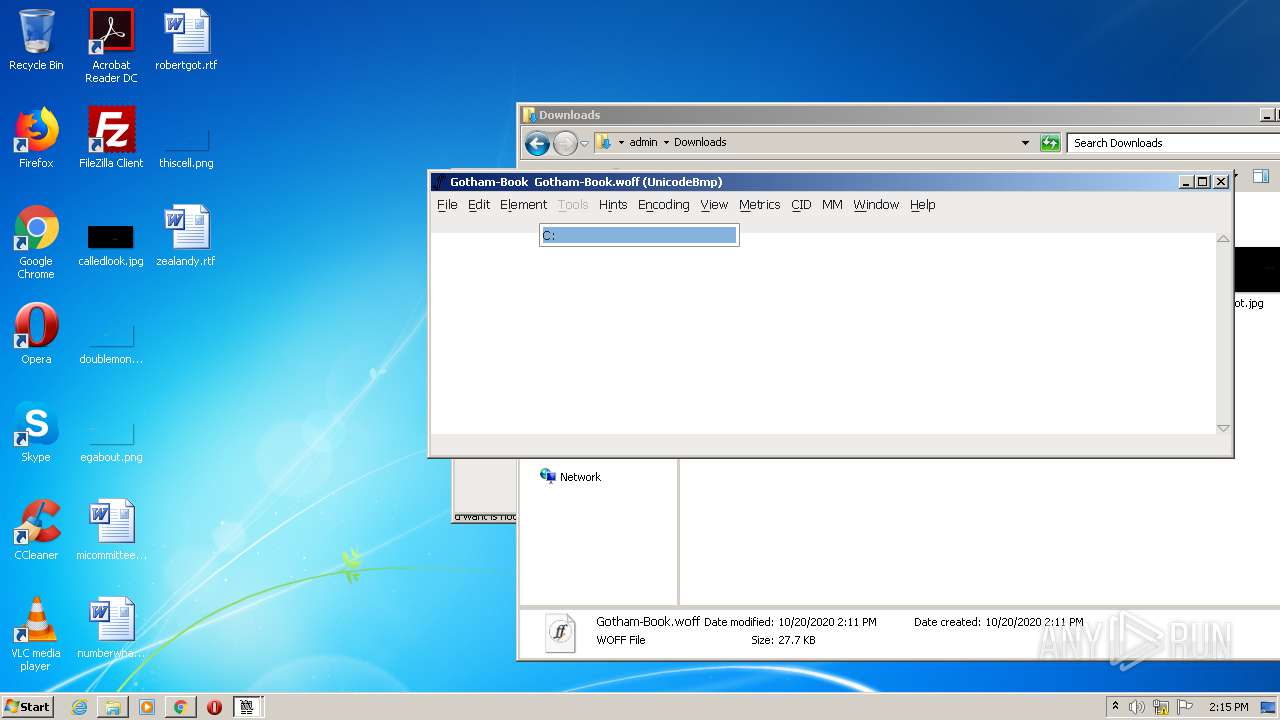
INFO
Application launched itself
- chrome.exe (PID: 2688)
Reads the hosts file
- chrome.exe (PID: 2688)
- chrome.exe (PID: 2380)
Reads Internet Cache Settings
- chrome.exe (PID: 2688)
Dropped object may contain Bitcoin addresses
- FontForge-2020-03-14-Windows.tmp (PID: 1864)
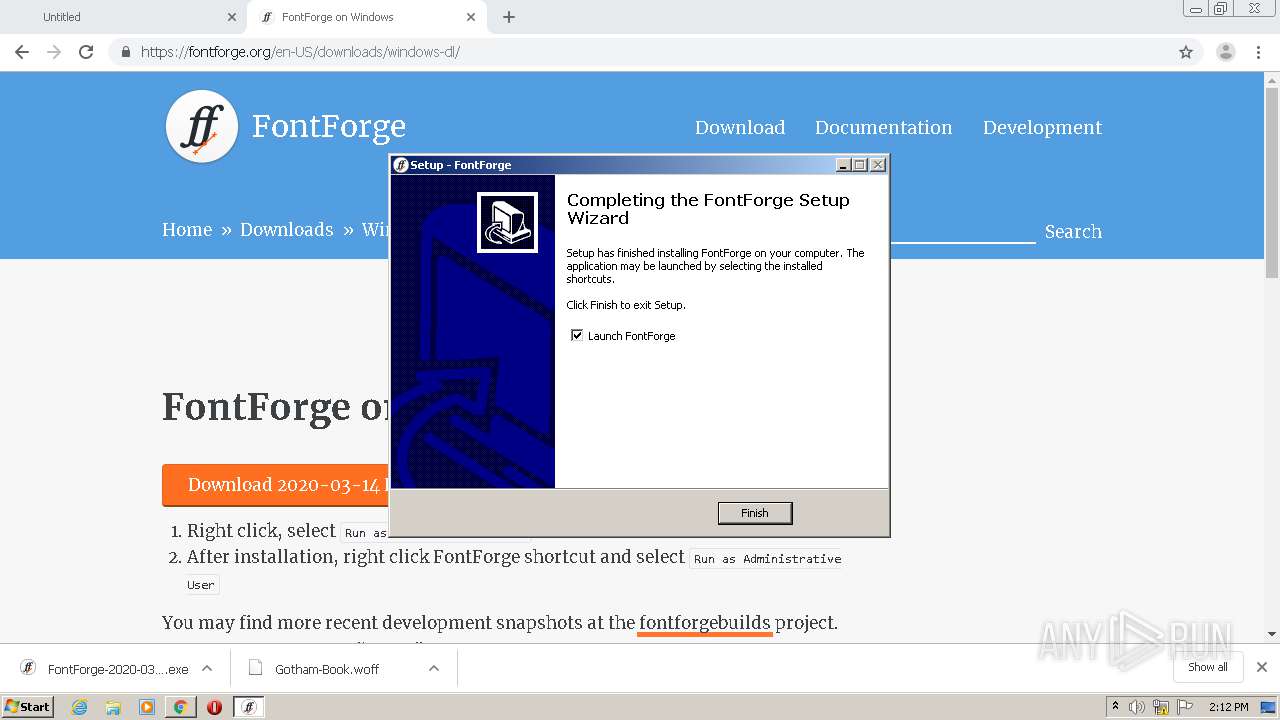
Creates a software uninstall entry
- FontForge-2020-03-14-Windows.tmp (PID: 1864)
Application was dropped or rewritten from another process
- FontForge-2020-03-14-Windows.tmp (PID: 2252)
- FontForge-2020-03-14-Windows.tmp (PID: 1864)
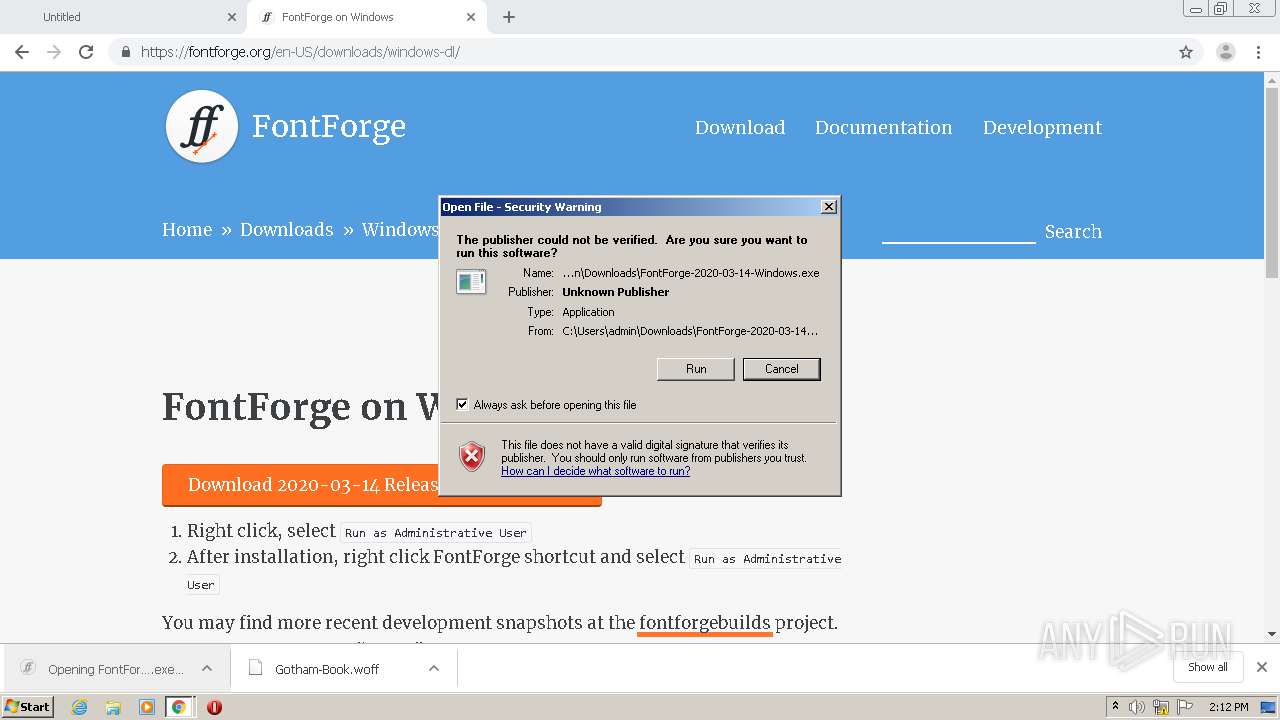
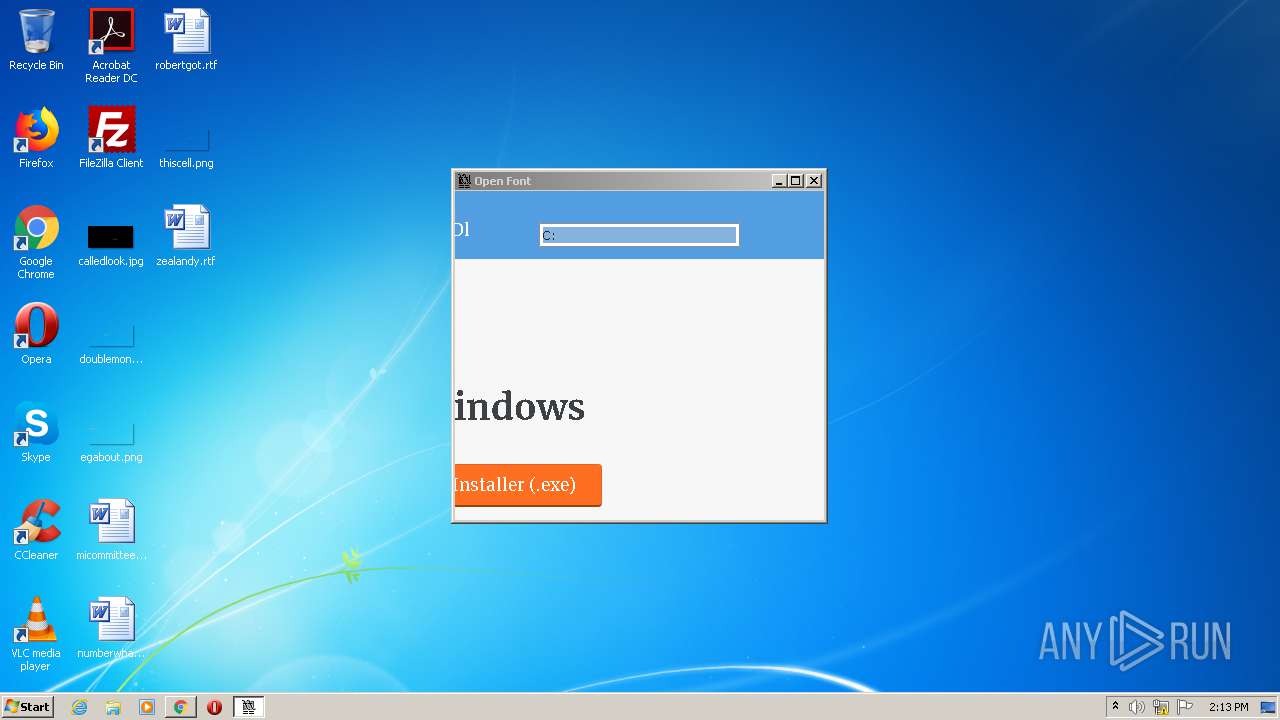
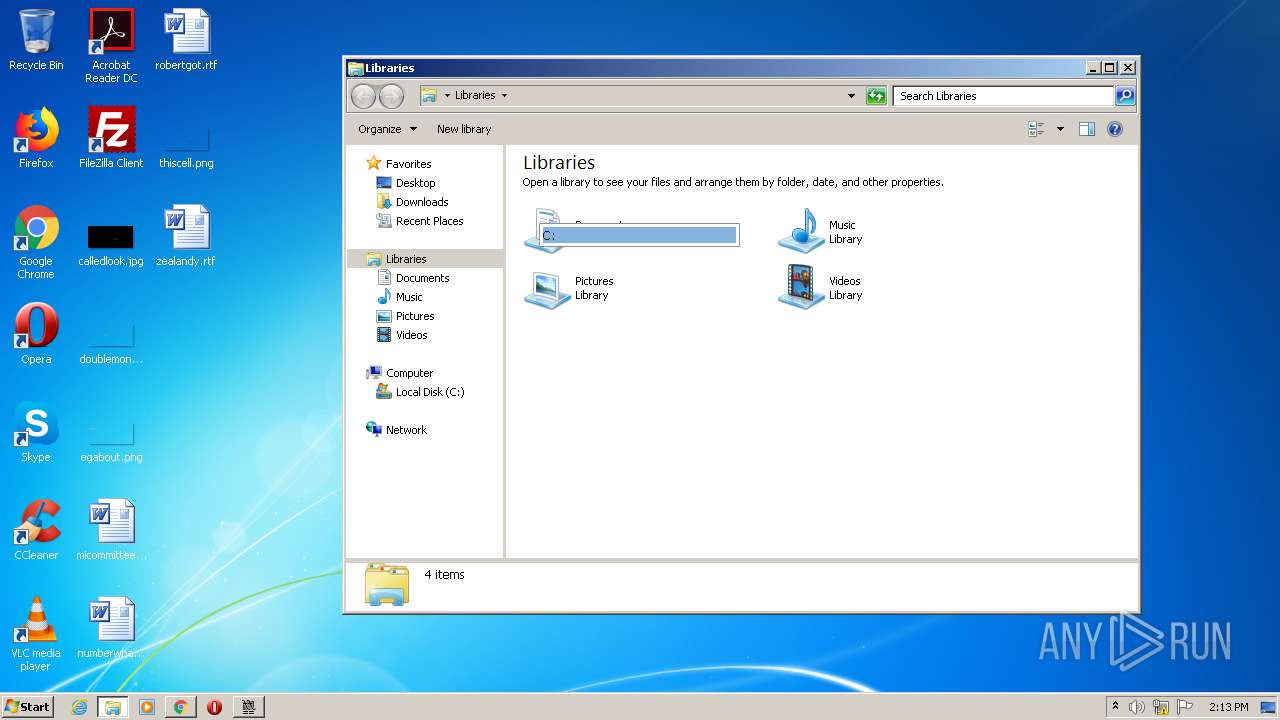
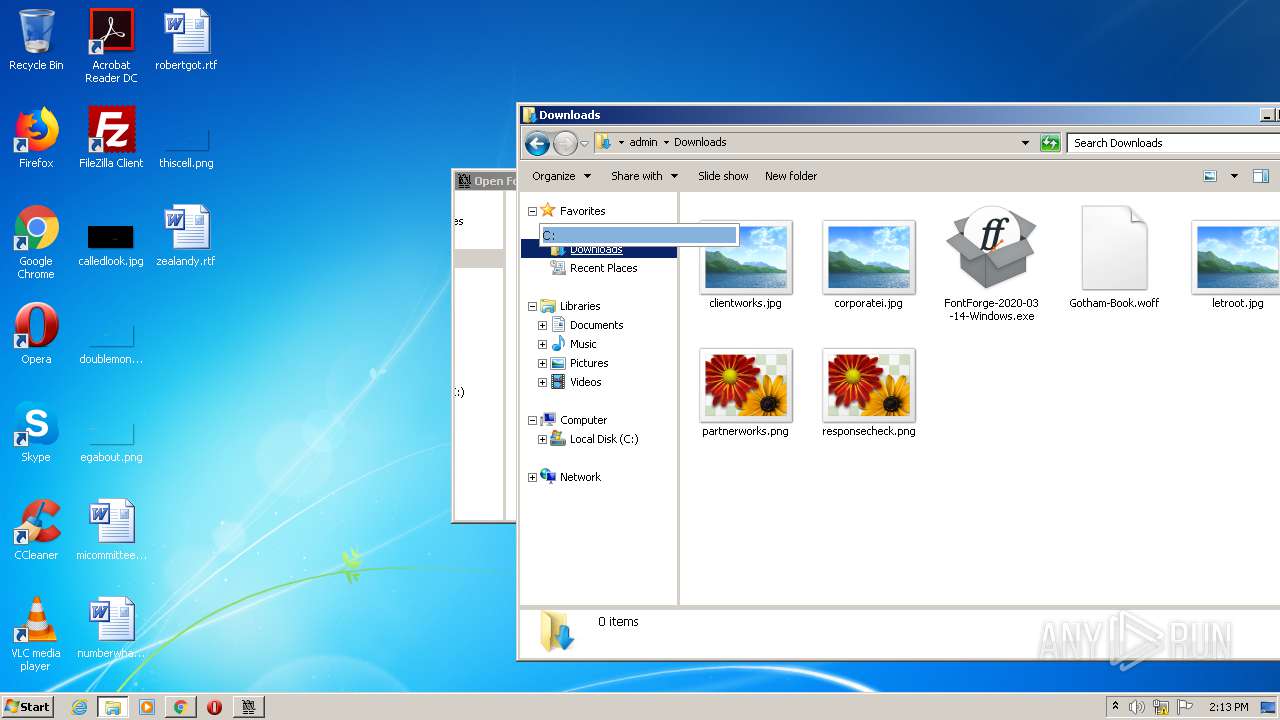
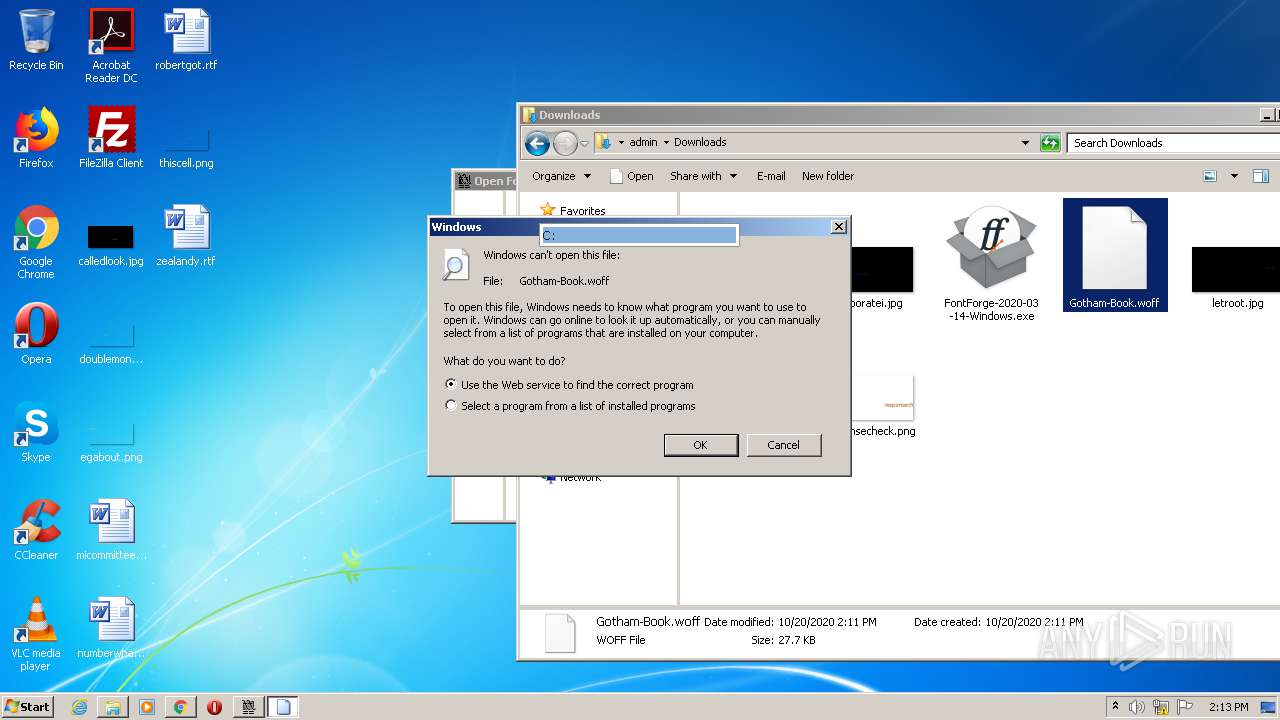
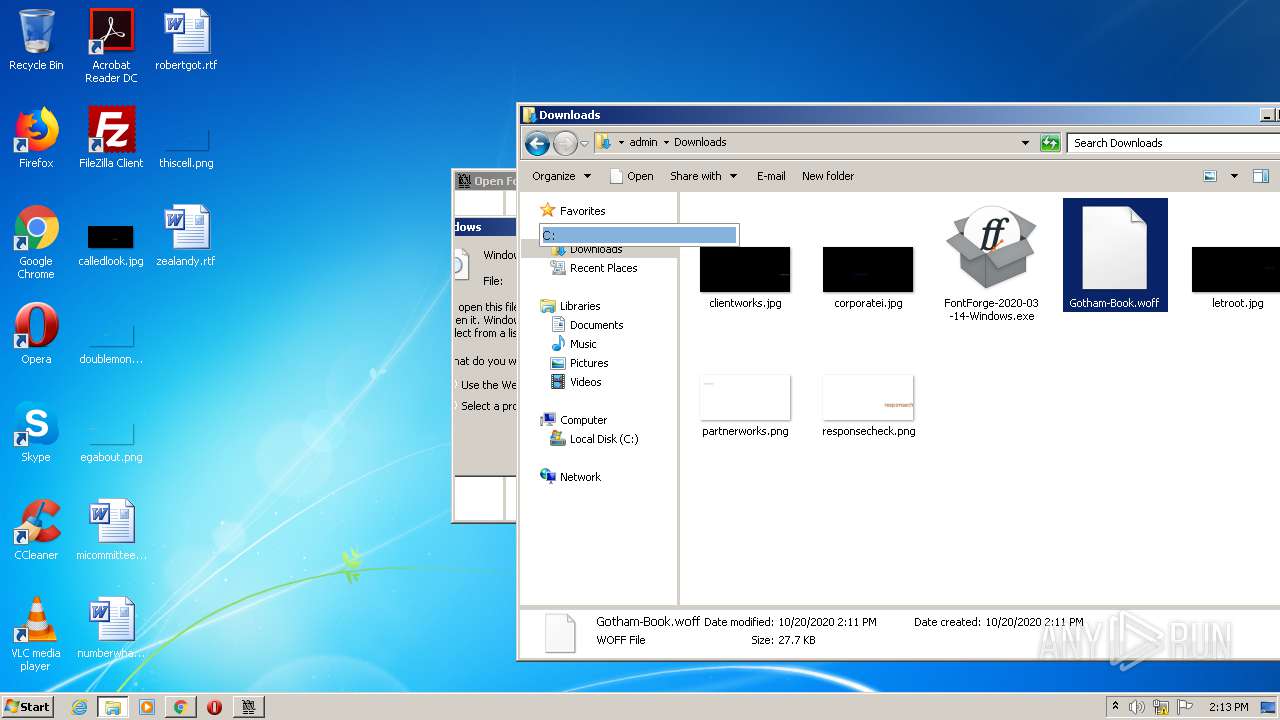
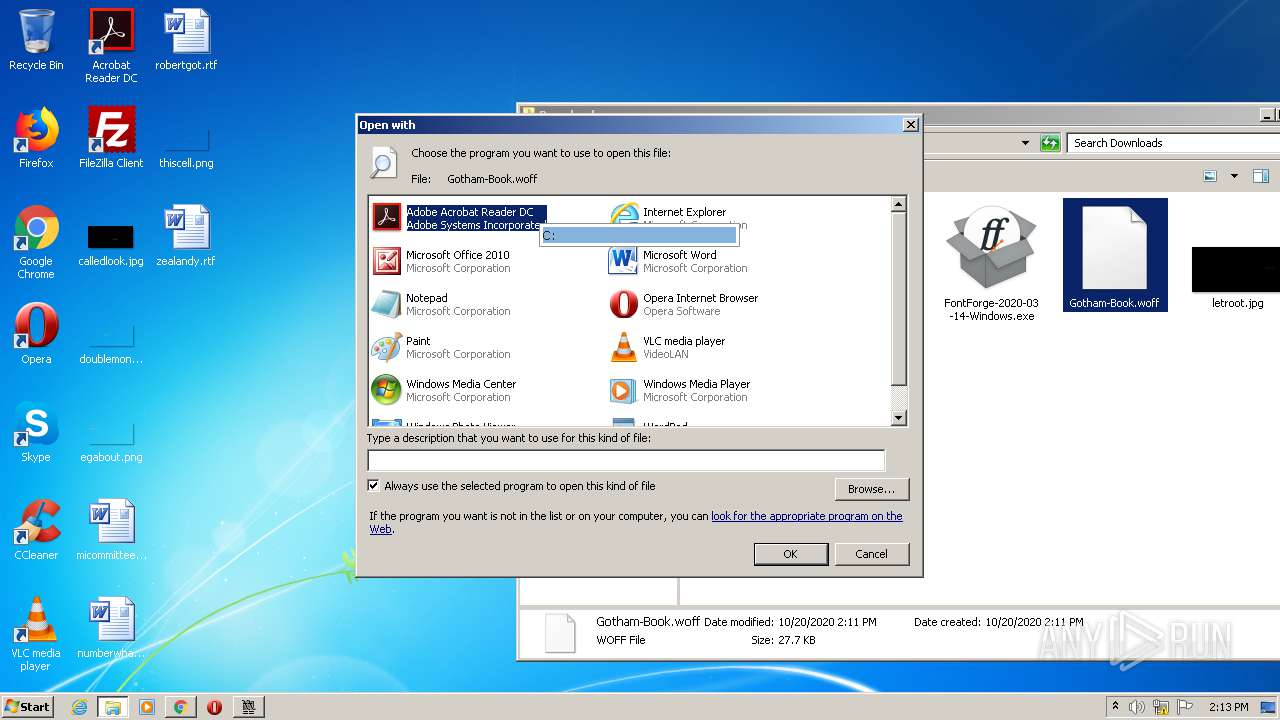
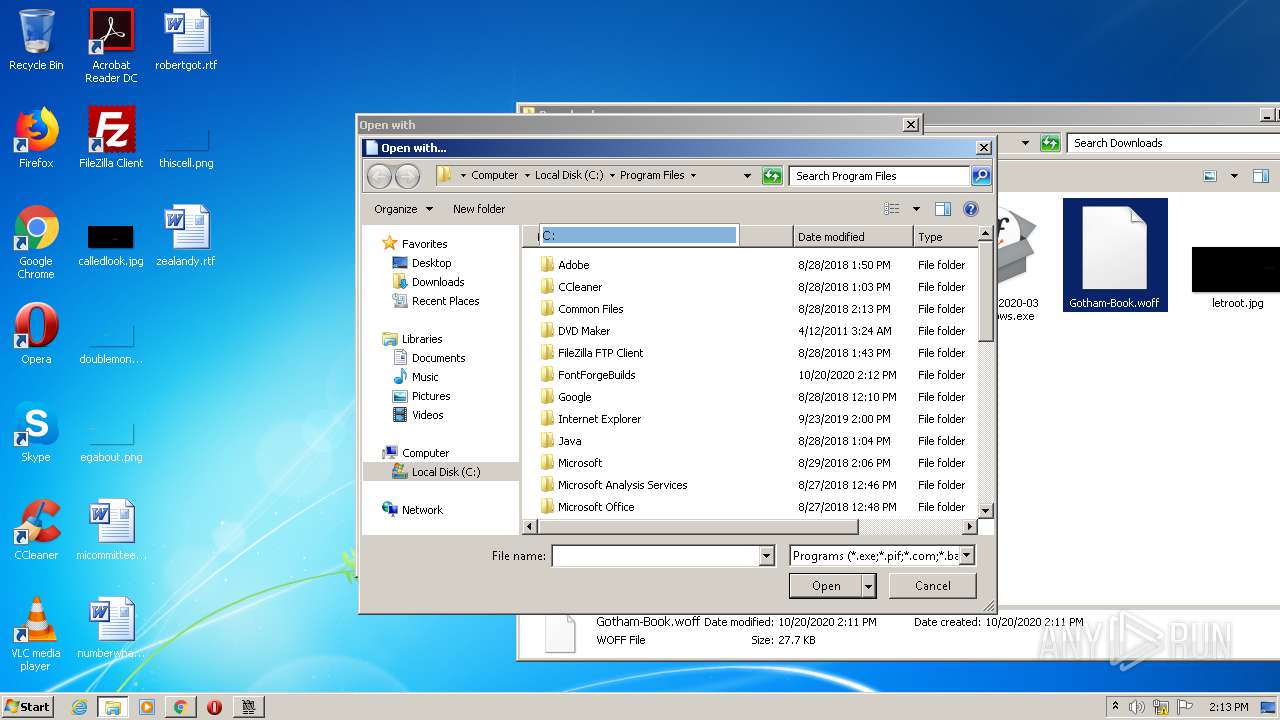
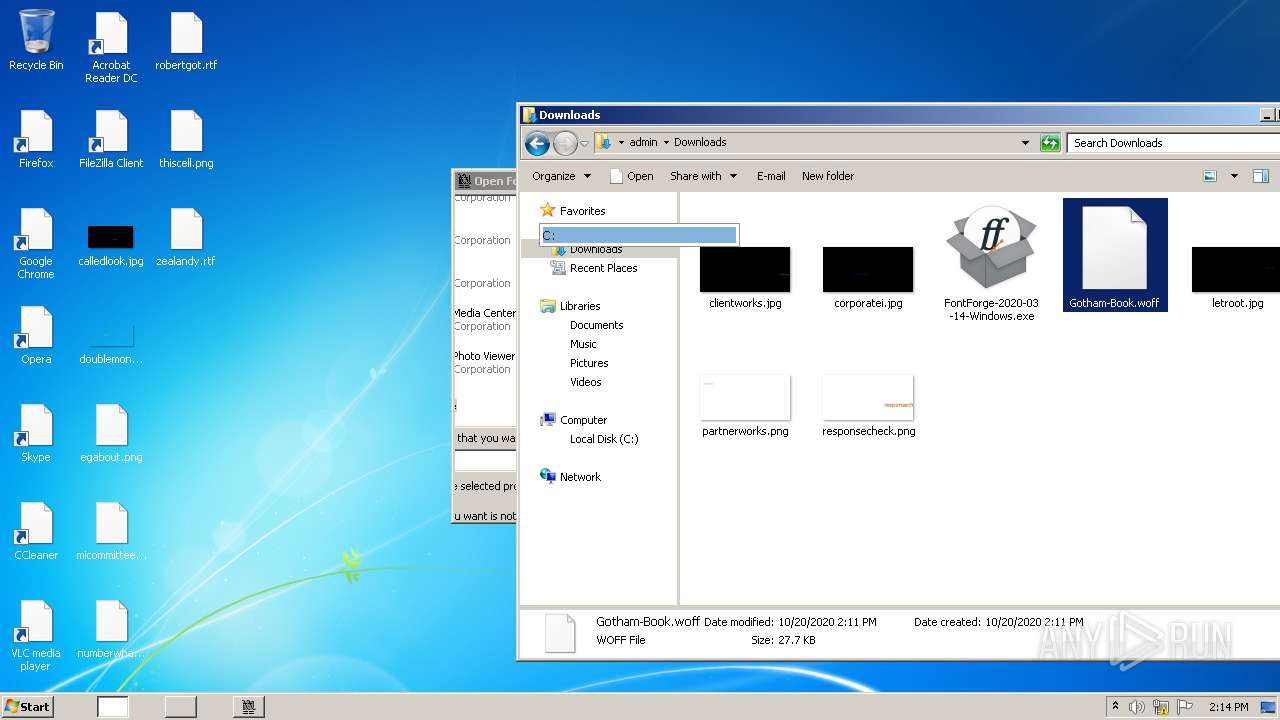
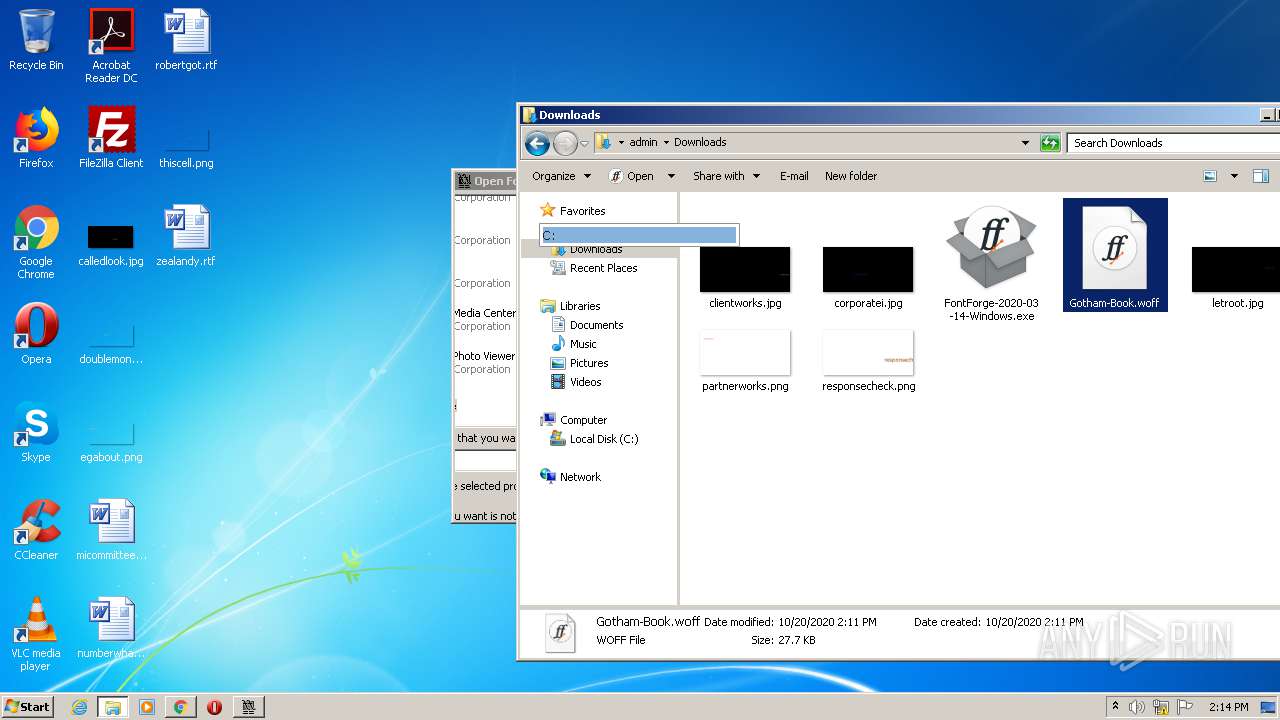
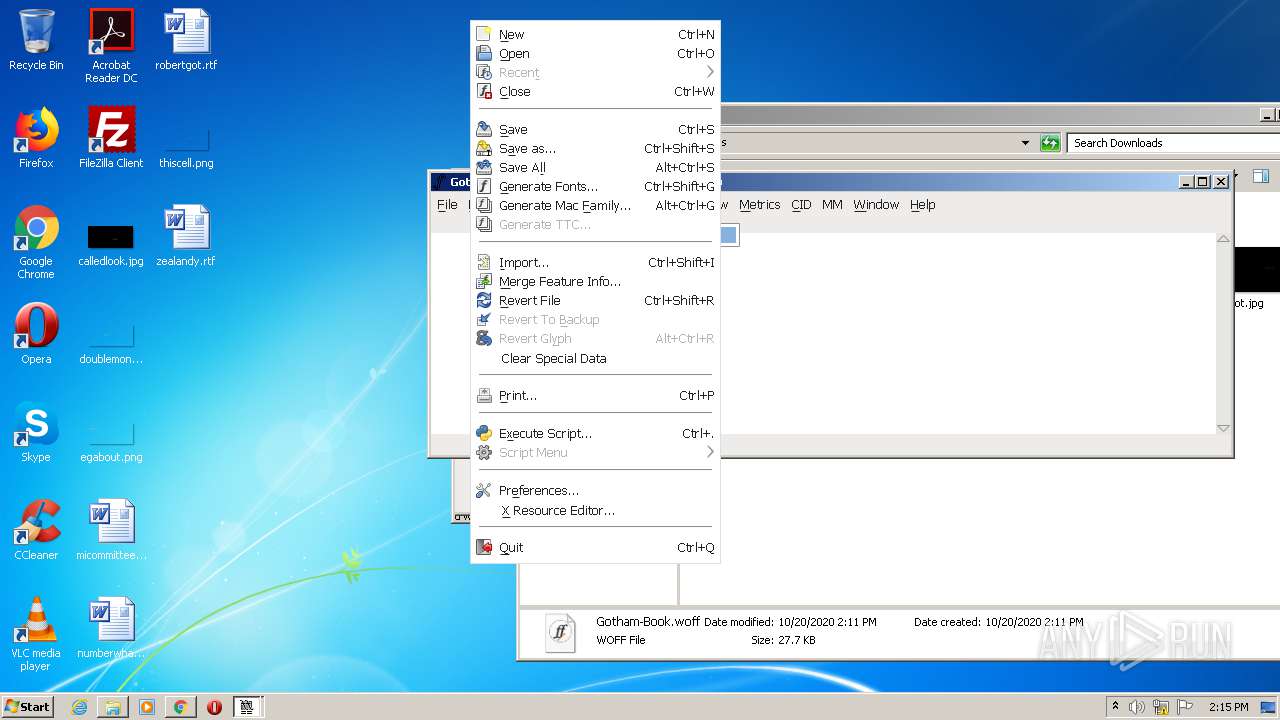
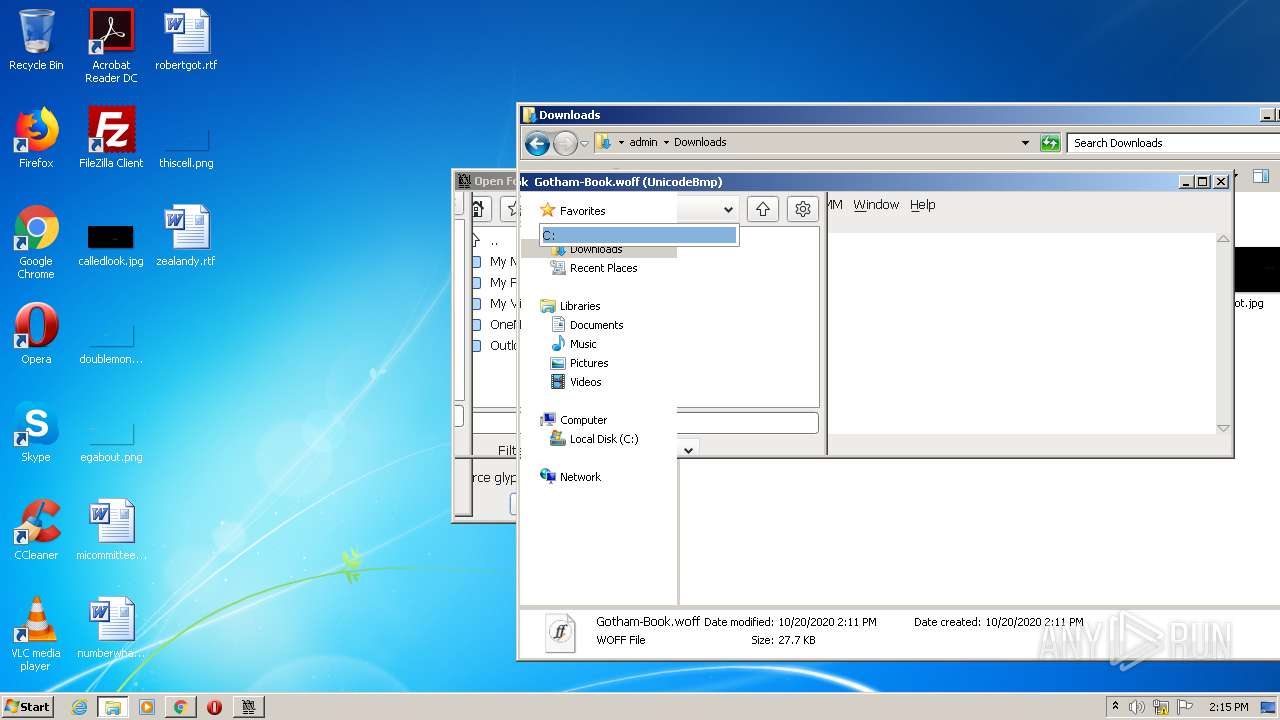
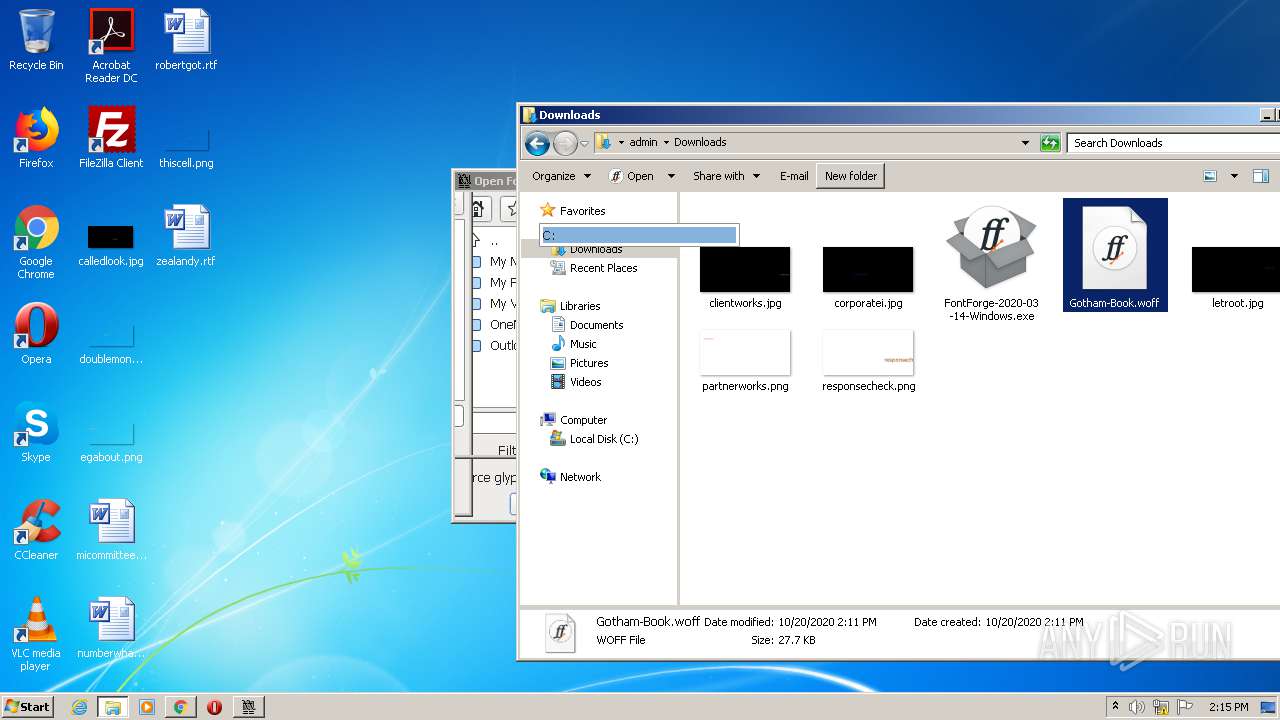
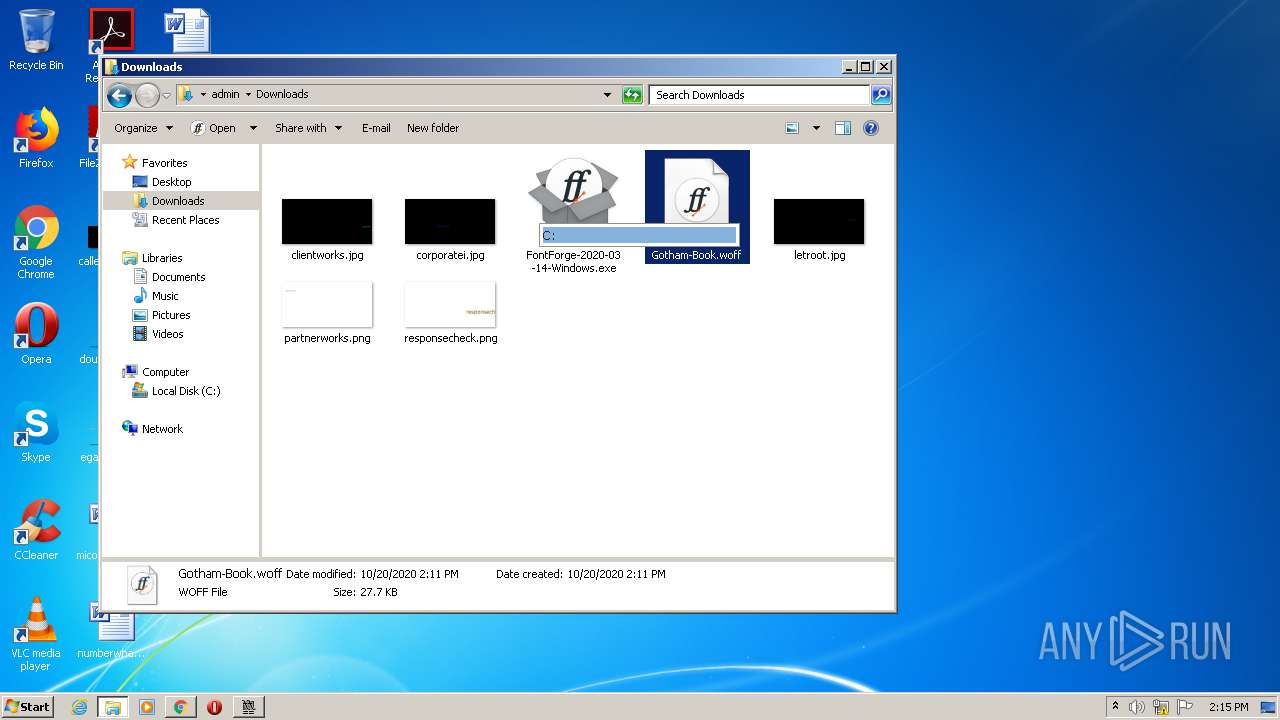
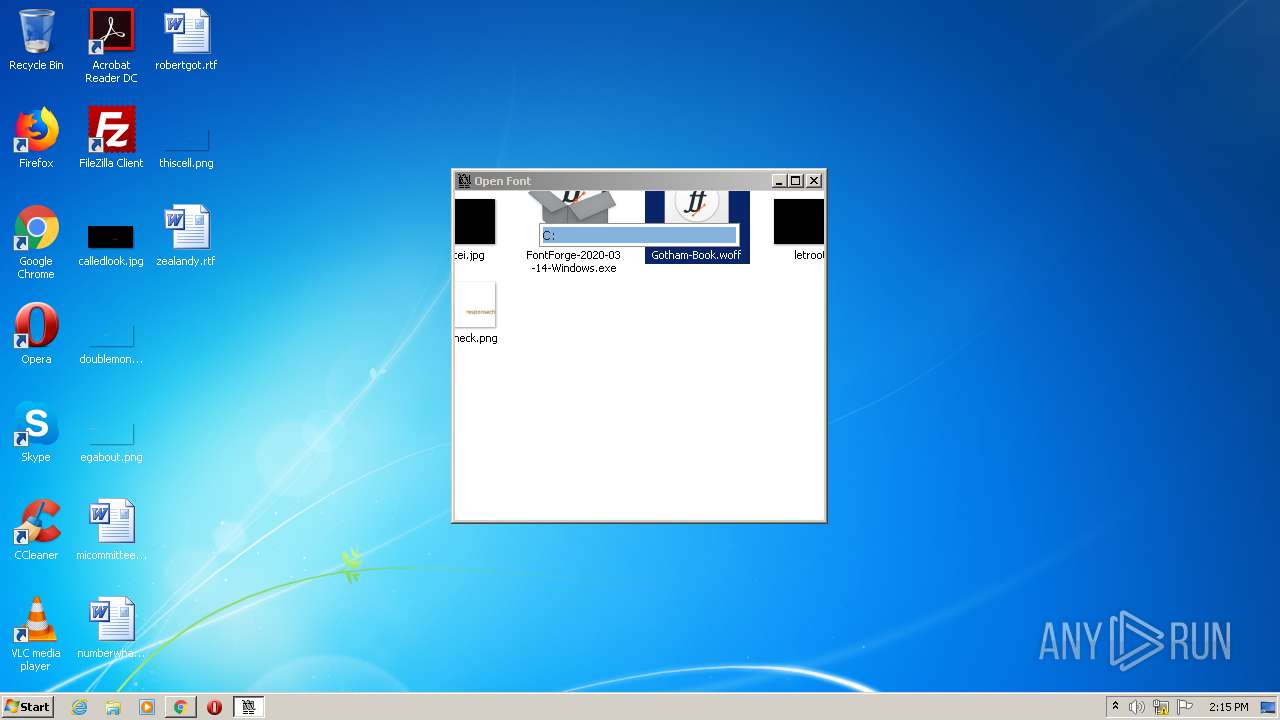
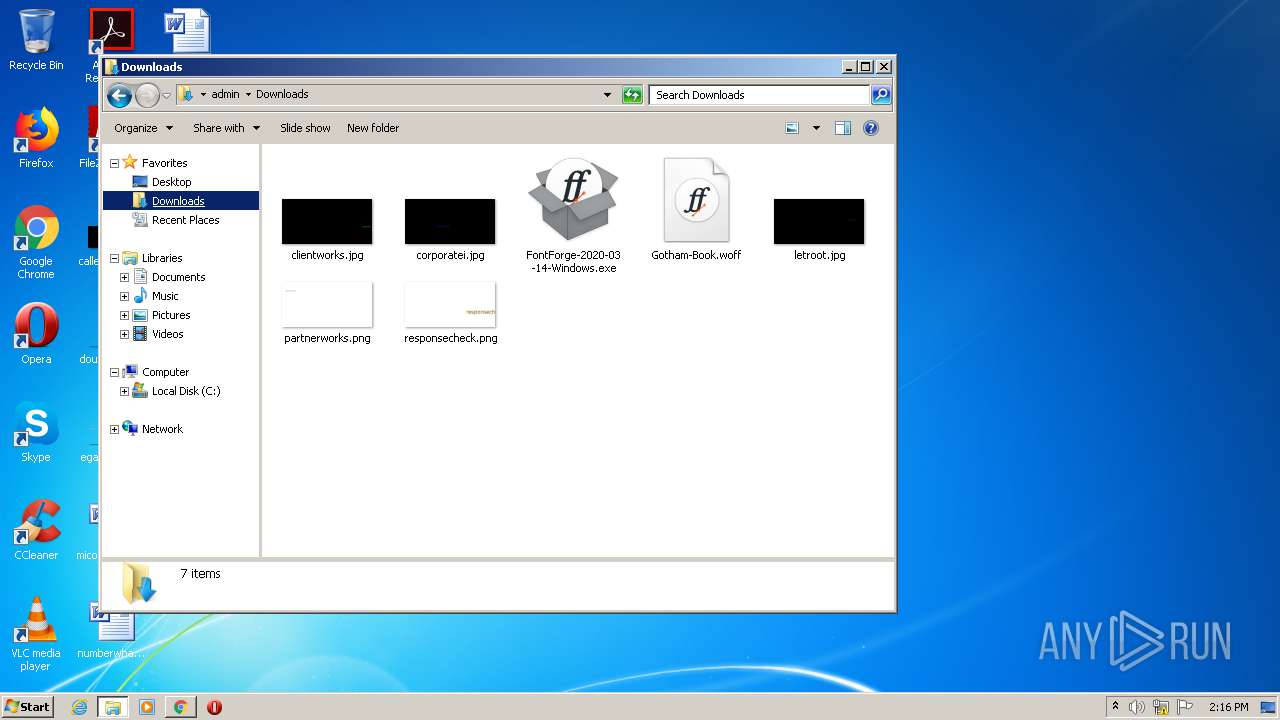
Manual execution by user
- explorer.exe (PID: 3068)
- rundll32.exe (PID: 3392)
- explorer.exe (PID: 1376)
Modifies the open verb of a shell class
- rundll32.exe (PID: 3392)
Creates files in the program directory
- FontForge-2020-03-14-Windows.tmp (PID: 1864)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
82
Monitored processes
36
Malicious processes
10
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 252 | /c ""C:\Program Files\FontForgeBuilds\fontforge.bat" " | C:\Windows\system32\cmd.exe | — | run_fontforge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 932 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=2740 --on-initialized-event-handle=324 --parent-handle=328 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1376 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
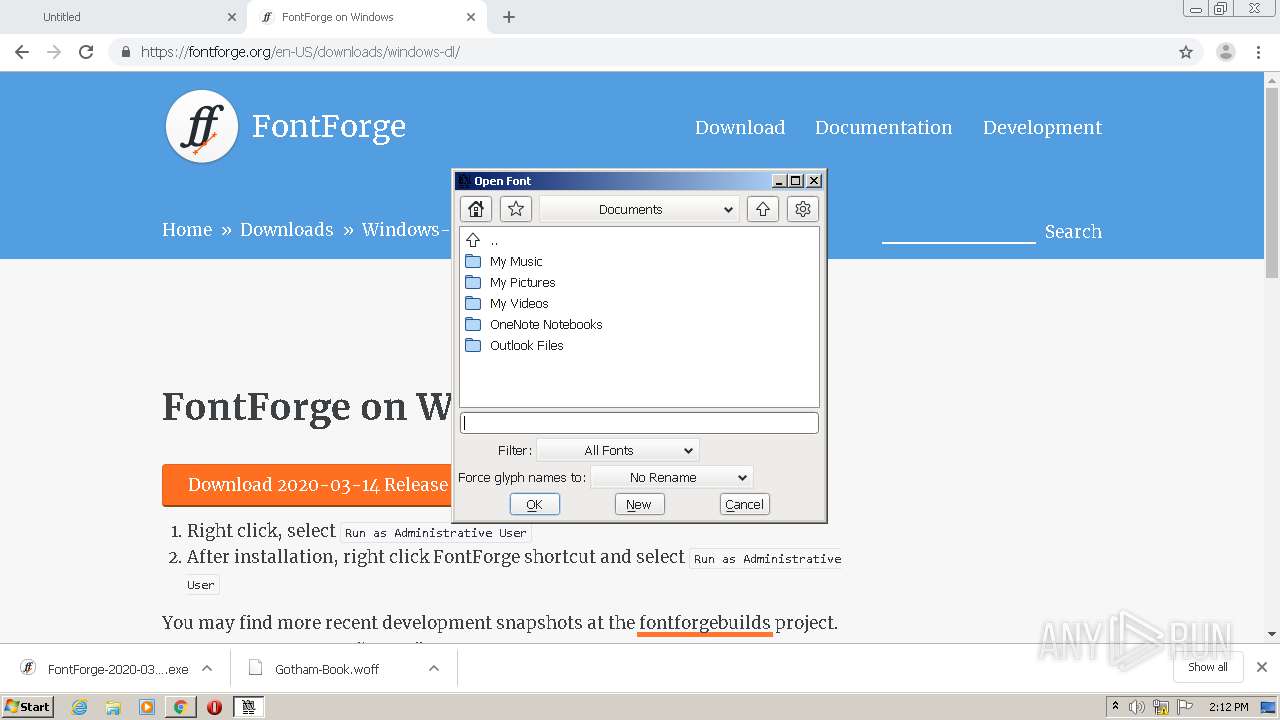
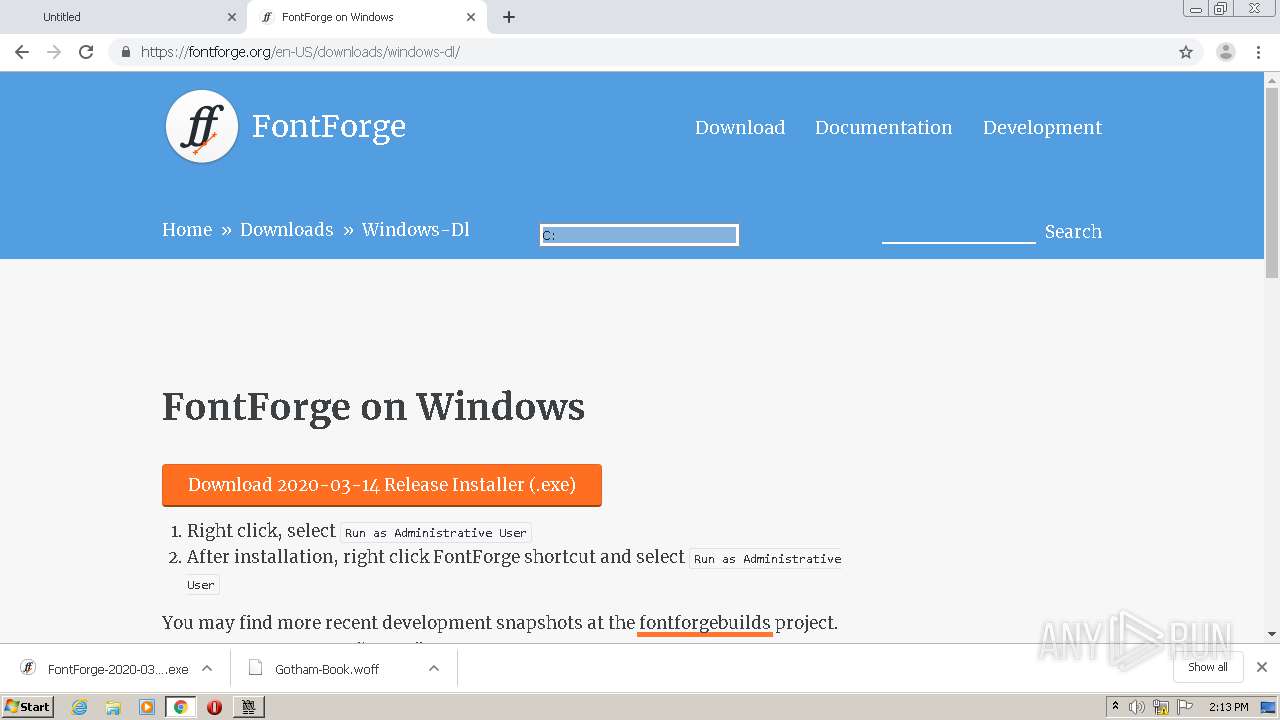
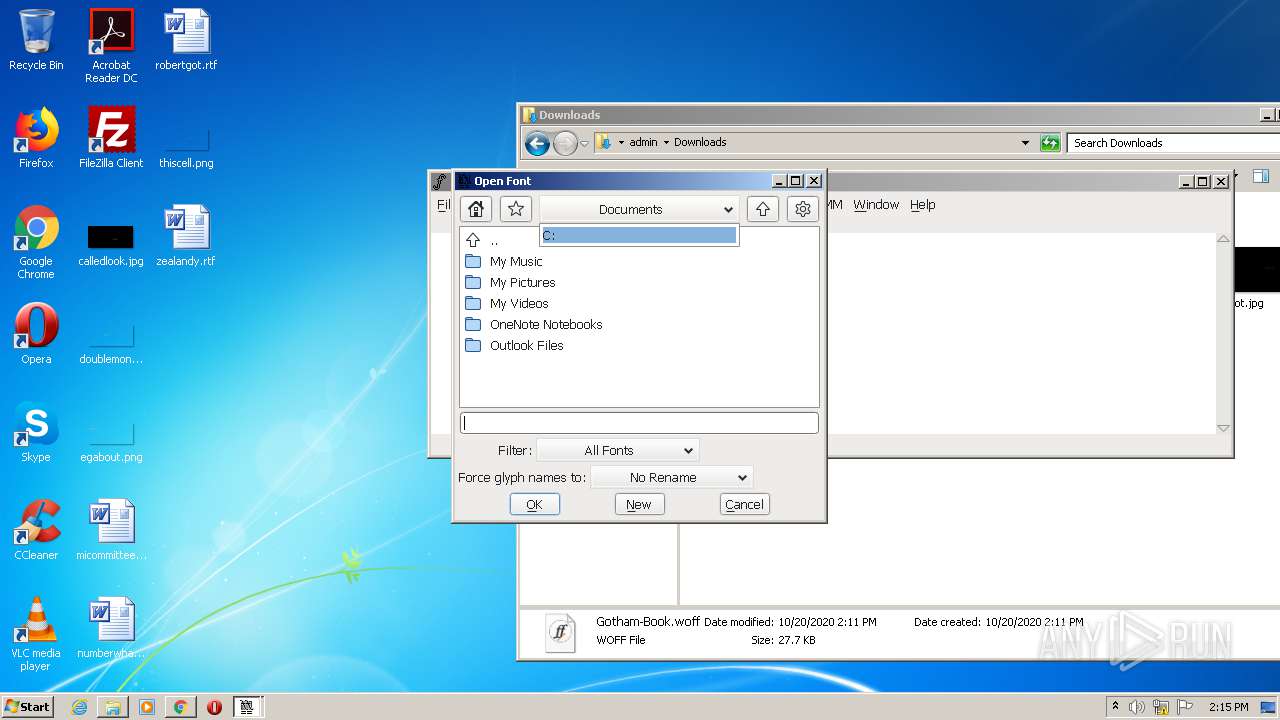
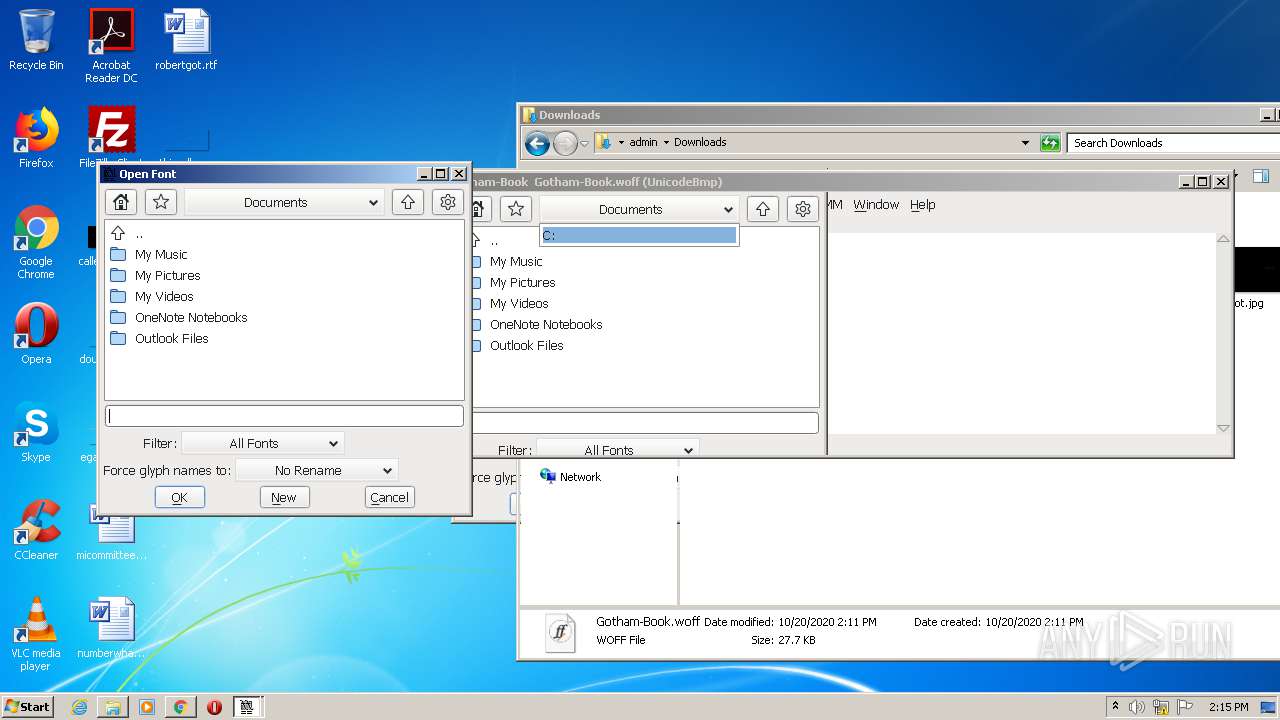
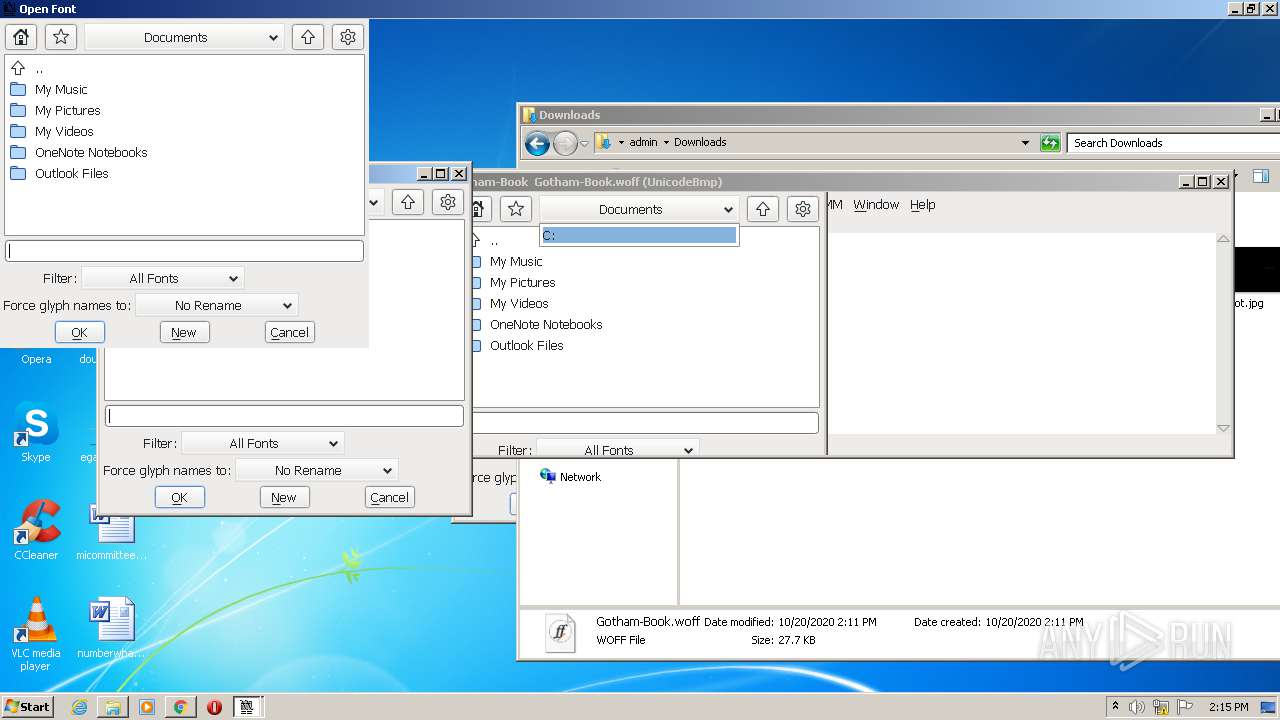
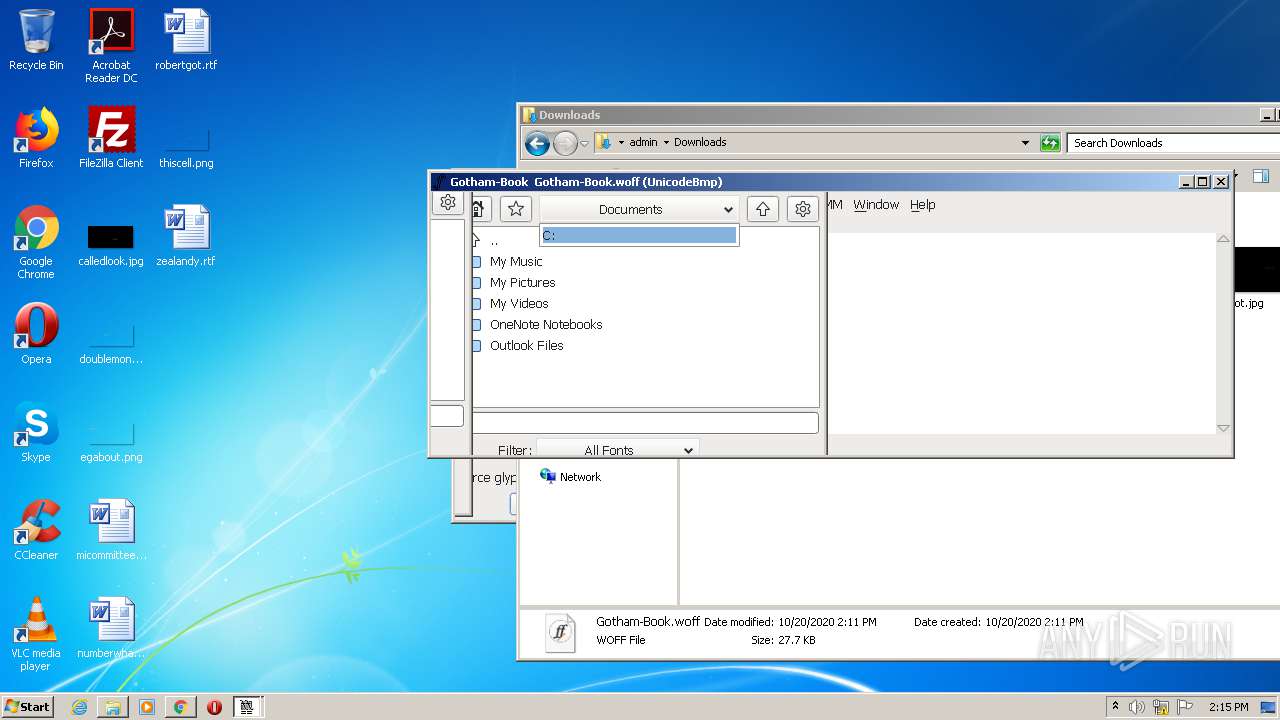
| 1508 | "C:\Program Files\FontForgeBuilds\\bin\fontforge.exe" -nosplash "C:\Users\admin\Downloads\Gotham-Book.woff" | C:\Program Files\FontForgeBuilds\bin\fontforge.exe | — | cmd.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1520 | "C:\Users\admin\Downloads\FontForge-2020-03-14-Windows.exe" /SPAWNWND=$13019C /NOTIFYWND=$502D0 | C:\Users\admin\Downloads\FontForge-2020-03-14-Windows.exe | FontForge-2020-03-14-Windows.tmp | ||||||||||||
User: admin Company: FontForgeBuilds Integrity Level: HIGH Description: FontForge Setup Exit code: 0 Version: Modules
| |||||||||||||||
| 1832 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1020,3603471138826646063,16387016814188915107,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=6400747656539409495 --mojo-platform-channel-handle=2556 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1864 | "C:\Users\admin\AppData\Local\Temp\is-8NG9B.tmp\FontForge-2020-03-14-Windows.tmp" /SL5="$1501A2,22141371,192000,C:\Users\admin\Downloads\FontForge-2020-03-14-Windows.exe" /SPAWNWND=$13019C /NOTIFYWND=$502D0 | C:\Users\admin\AppData\Local\Temp\is-8NG9B.tmp\FontForge-2020-03-14-Windows.tmp | FontForge-2020-03-14-Windows.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 2252 | "C:\Users\admin\AppData\Local\Temp\is-E12QJ.tmp\FontForge-2020-03-14-Windows.tmp" /SL5="$502D0,22141371,192000,C:\Users\admin\Downloads\FontForge-2020-03-14-Windows.exe" | C:\Users\admin\AppData\Local\Temp\is-E12QJ.tmp\FontForge-2020-03-14-Windows.tmp | — | FontForge-2020-03-14-Windows.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 2256 | C:\Windows\system32\cmd.exe /c dir /b "C:\Program Files\FontForgeBuilds\lib\python*" | C:\Windows\system32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2380 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1020,3603471138826646063,16387016814188915107,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=16702034049924481315 --mojo-platform-channel-handle=1560 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
3 457
Read events
3 185
Write events
262
Delete events
10
Modification events
| (PID) Process: | (2688) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2688) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2688) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2688) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2688) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (932) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2688-13247673065193000 |
Value: 259 | |||
| (PID) Process: | (2688) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2688) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2688) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3252-13245750958665039 |
Value: 0 | |||
| (PID) Process: | (2688) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 2688-13247673065193000 |
Value: 259 | |||
Executable files
153
Suspicious files
76
Text files
2 710
Unknown types
40
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2688 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5F8EE1E9-A80.pma | — | |
MD5:— | SHA256:— | |||
| 2688 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\4a362ce8-e8f4-4e29-be39-a65af7d4bc42.tmp | — | |
MD5:— | SHA256:— | |||
| 2688 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000048.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2688 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2688 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2688 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old~RF2d3f21.TMP | text | |
MD5:— | SHA256:— | |||
| 2688 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2688 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF2d3ef2.TMP | text | |
MD5:— | SHA256:— | |||
| 2688 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\metadata\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2688 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
46
DNS requests
24
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
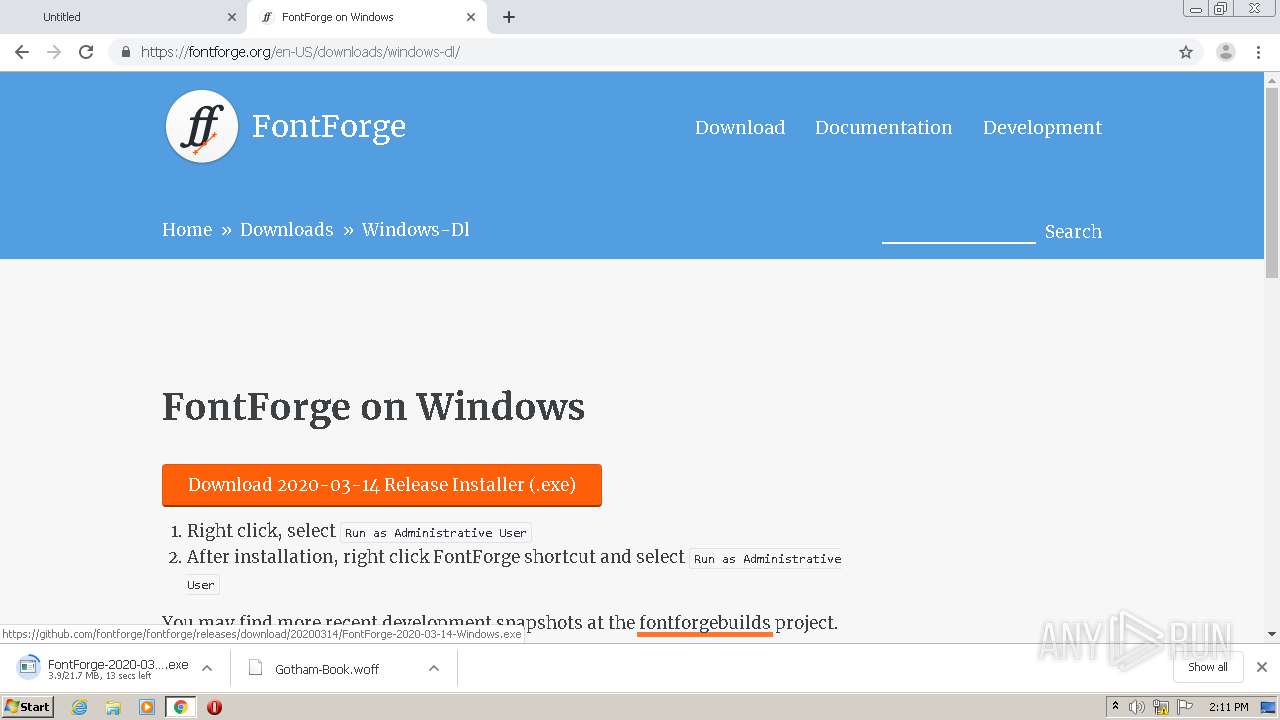
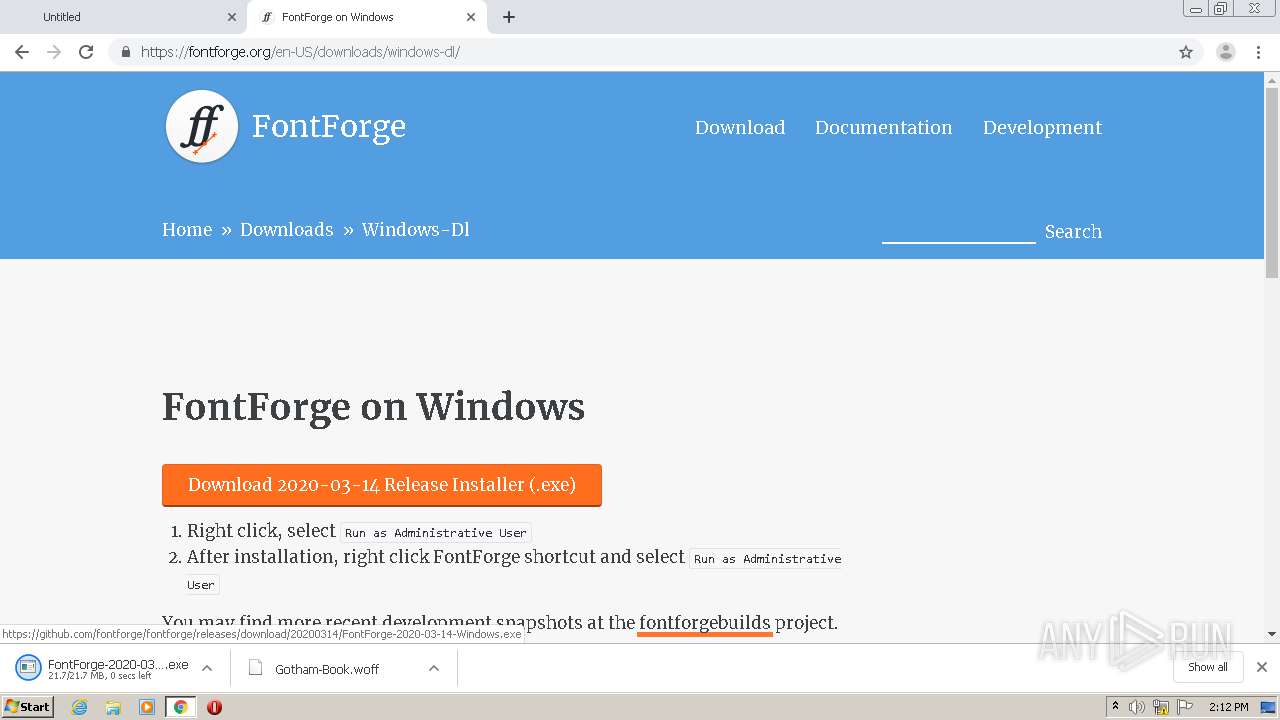
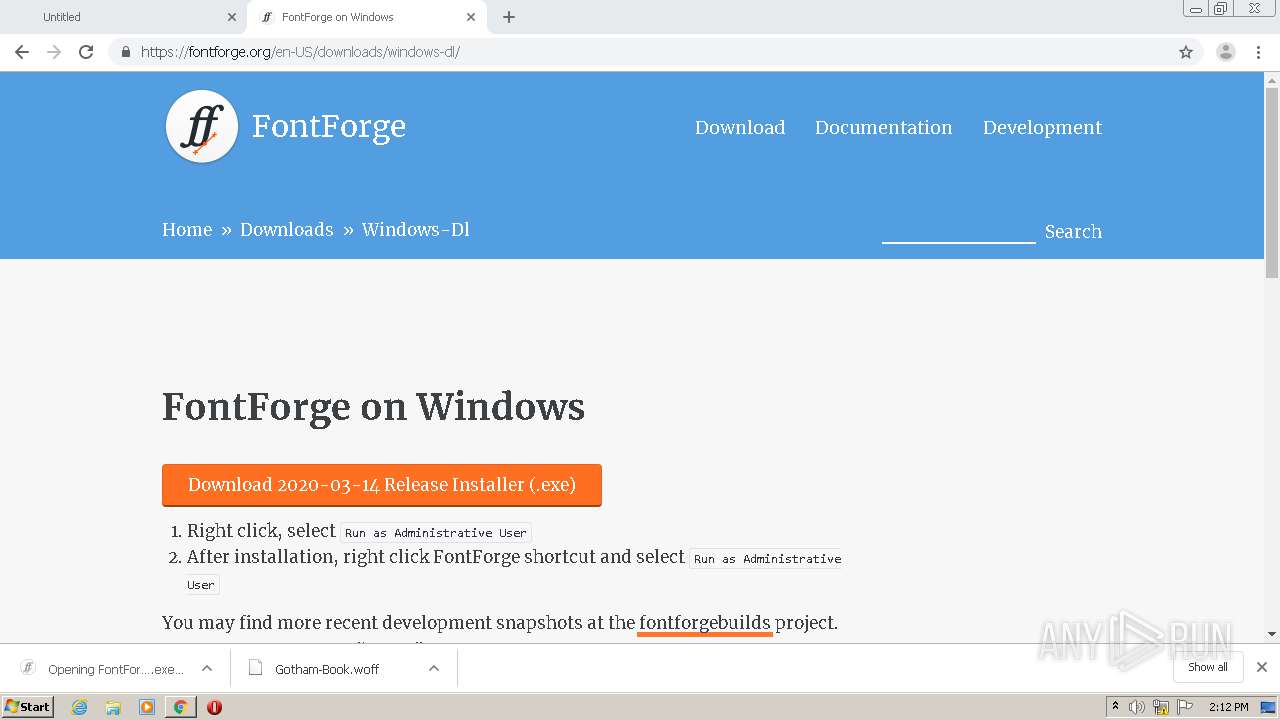
2380 | chrome.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfqhLjKLEJQZPin0KCzkdAQpVYowQUsT7DaQP4v0cB1JgmGggC72NkK8MCEAx5qUSwjBGVIJJhX%2BJrHYM%3D | US | der | 471 b | whitelisted |
2380 | chrome.exe | GET | 301 | 185.199.109.153:80 | http://fontforge.github.io/en-US/downloads/windows-dl/ | NL | html | 162 b | whitelisted |
2380 | chrome.exe | GET | 301 | 104.198.26.61:80 | http://www.esosolutions.com/wp-content/themes/enfold-child/fonts/Gotham-Book.woff | US | html | 162 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2380 | chrome.exe | 172.217.22.99:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2380 | chrome.exe | 104.198.26.61:80 | esosolutions.com | Google Inc. | US | unknown |
2380 | chrome.exe | 172.217.23.109:443 | accounts.google.com | Google Inc. | US | suspicious |
2380 | chrome.exe | 216.58.206.14:443 | sb-ssl.google.com | Google Inc. | US | whitelisted |
2380 | chrome.exe | 13.107.246.10:443 | www.eso.com | Microsoft Corporation | US | whitelisted |
2380 | chrome.exe | 172.217.21.195:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
2380 | chrome.exe | 216.58.206.4:443 | www.google.com | Google Inc. | US | whitelisted |
2380 | chrome.exe | 216.58.212.170:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
2380 | chrome.exe | 172.217.23.99:443 | www.gstatic.com | Google Inc. | US | whitelisted |
2380 | chrome.exe | 172.217.22.67:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
esosolutions.com |
| unknown |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.esosolutions.com |
| unknown |
www.eso.com |
| whitelisted |
sb-ssl.google.com |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
www.google.com |
| malicious |
fonts.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |