| File name: | Documentos_2700814.xls |
| Full analysis: | https://app.any.run/tasks/b61a49ca-2942-45f8-997d-7381fba8718f |
| Verdict: | Malicious activity |
| Analysis date: | October 04, 2022, 21:02:00 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.ms-excel |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 10.0, Code page: 1251, Author: SRGHRSHSH, Last Saved By: RGSGK, Name of Creating Application: Microsoft Excel, Create Time/Date: Fri Jun 5 18:19:34 2015, Last Saved Time/Date: Wed Jun 22 18:18:37 2022, Security: 0 |
| MD5: | DBAA6D60D6723D0572B7037E23E624EE |
| SHA1: | ACDB12494F4AA1FBADDDDFC68EC024E205005C9D |
| SHA256: | 61617195E6AC7097101F36AD2FFA54D64BA1876FB9C55F7D218157CB77FD9A67 |
| SSDEEP: | 1536:f+Kpb8rGYrMPe3q7Q0XV5xtezEsi8/dg/QvXCVQN:2Kpb8rGYrMPe3q7Q0XV5xtezEsi8/dg2 |
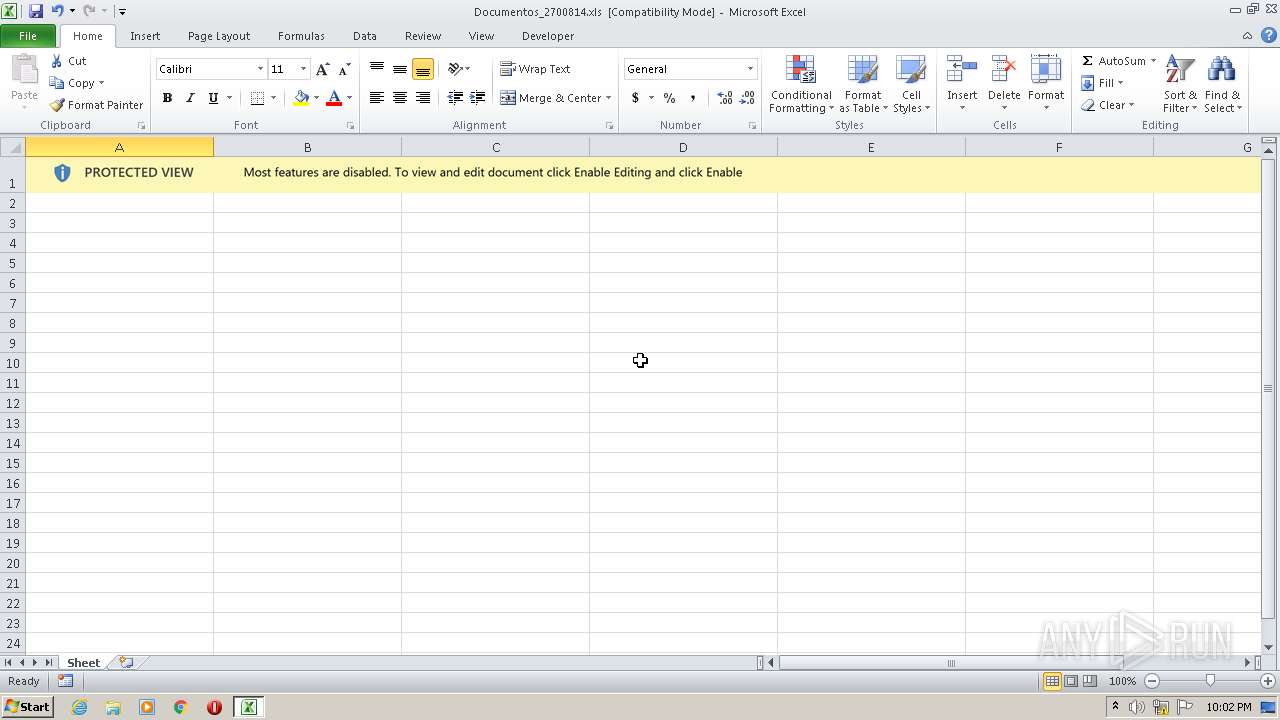
MALICIOUS
Registers / Runs the DLL via REGSVR32.EXE
- EXCEL.EXE (PID: 3652)
Unusual execution from Microsoft Office
- EXCEL.EXE (PID: 3652)
SUSPICIOUS
No suspicious indicators.INFO
Checks supported languages
- regsvr32.exe (PID: 3076)
- EXCEL.EXE (PID: 3652)
- regsvr32.exe (PID: 2060)
- regsvr32.exe (PID: 3036)
- regsvr32.exe (PID: 496)
Reads the computer name
- EXCEL.EXE (PID: 3652)
Checks Windows Trust Settings
- EXCEL.EXE (PID: 3652)
Reads settings of System Certificates
- EXCEL.EXE (PID: 3652)
Creates files in the user directory
- EXCEL.EXE (PID: 3652)
Reads Microsoft Office registry keys
- EXCEL.EXE (PID: 3652)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .xls | | | Microsoft Excel sheet (78.9) |
|---|
Total processes
39
Monitored processes
5
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 496 | C:\Windows\System32\regsvr32.exe /S ..\udh3.ocx | C:\Windows\System32\regsvr32.exe | — | EXCEL.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft(C) Register Server Exit code: 3 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2060 | C:\Windows\System32\regsvr32.exe /S ..\udh2.ocx | C:\Windows\System32\regsvr32.exe | — | EXCEL.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft(C) Register Server Exit code: 3 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3036 | C:\Windows\System32\regsvr32.exe /S ..\udh4.ocx | C:\Windows\System32\regsvr32.exe | — | EXCEL.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft(C) Register Server Exit code: 3 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3076 | C:\Windows\System32\regsvr32.exe /S ..\udh1.ocx | C:\Windows\System32\regsvr32.exe | — | EXCEL.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft(C) Register Server Exit code: 3 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3652 | "C:\Program Files\Microsoft Office\Office14\EXCEL.EXE" /dde | C:\Program Files\Microsoft Office\Office14\EXCEL.EXE | Explorer.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Excel Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
Total events
7 051
Read events
6 974
Write events
66
Delete events
11
Modification events
| (PID) Process: | (3652) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency\StartupItems |
| Operation: | write | Name: | ""? |
Value: 22223F00440E0000010000000000000000000000 | |||
| (PID) Process: | (3652) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (3652) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (3652) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (3652) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (3652) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (3652) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (3652) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (3652) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (3652) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: Off | |||
Executable files
0
Suspicious files
7
Text files
3
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3652 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\CVRBE02.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3652 | EXCEL.EXE | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\77EC63BDA74BD0D0E0426DC8F8008506 | compressed | |
MD5:— | SHA256:— | |||
| 3652 | EXCEL.EXE | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\77EC63BDA74BD0D0E0426DC8F8008506 | binary | |
MD5:— | SHA256:— | |||
| 3652 | EXCEL.EXE | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:— | SHA256:— | |||
| 3652 | EXCEL.EXE | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\103621DE9CD5414CC2538780B4B75751 | binary | |
MD5:— | SHA256:— | |||
| 3652 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\Tar2A7A.tmp | cat | |
MD5:— | SHA256:— | |||
| 3652 | EXCEL.EXE | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\22DBCAF188C786DFCF2128AD4555E265 | binary | |
MD5:— | SHA256:— | |||
| 3652 | EXCEL.EXE | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | compressed | |
MD5:F7DCB24540769805E5BB30D193944DCE | SHA256:6B88C6AC55BBD6FEA0EBE5A760D1AD2CFCE251C59D0151A1400701CB927E36EA | |||
| 3652 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\Cab2A79.tmp | compressed | |
MD5:— | SHA256:— | |||
| 3652 | EXCEL.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\78RFYB7Z\session_timeout[1].htm | html | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
9
DNS requests
9
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3652 | EXCEL.EXE | GET | 301 | 103.83.192.58:80 | http://eapro.in/wp-admin/cb/ | US | — | — | suspicious |
3652 | EXCEL.EXE | GET | 301 | 103.83.192.58:80 | http://www.eapro.in/wp-admin/cb/ | US | — | — | suspicious |
3652 | EXCEL.EXE | GET | 406 | 93.191.156.5:80 | http://dvinge.com/wp-includes/9wOquCr9TAANex6RJOX/ | DK | html | 551 b | malicious |
3652 | EXCEL.EXE | GET | 200 | 184.24.77.75:80 | http://r3.o.lencr.org/MFMwUTBPME0wSzAJBgUrDgMCGgUABBRI2smg%2ByvTLU%2Fw3mjS9We3NfmzxAQUFC6zF7dYVsuuUAlA5h%2BvnYsUwsYCEgTUQFzqR21Rq4KDyDAkxf4cPA%3D%3D | US | der | 503 b | shared |
3652 | EXCEL.EXE | GET | 200 | 96.16.145.230:80 | http://x1.c.lencr.org/ | US | der | 717 b | whitelisted |
3652 | EXCEL.EXE | GET | 200 | 8.247.185.126:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?18c81d0089a8b27a | US | compressed | 60.9 Kb | whitelisted |
3652 | EXCEL.EXE | GET | 200 | 8.247.185.126:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?f32e63fd478901c5 | US | compressed | 4.70 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3652 | EXCEL.EXE | 93.191.156.5:80 | dvinge.com | team.blue Denmark A/S | DK | malicious |
3652 | EXCEL.EXE | 45.122.220.108:80 | dulichdichvu.net | Viet Solutions Services Trading Company Limited | VN | malicious |
— | — | 103.83.192.58:80 | eapro.in | LeapSwitch Networks Pvt Ltd | IN | suspicious |
3652 | EXCEL.EXE | 103.83.192.58:443 | eapro.in | LeapSwitch Networks Pvt Ltd | IN | suspicious |
3652 | EXCEL.EXE | 96.16.145.230:80 | x1.c.lencr.org | AKAMAI-AS | DE | suspicious |
3652 | EXCEL.EXE | 8.247.185.126:80 | ctldl.windowsupdate.com | LEVEL3 | US | unknown |
3652 | EXCEL.EXE | 148.139.69.159:443 | www.e-xim.pl | SNC | US | unknown |
3652 | EXCEL.EXE | 184.24.77.75:80 | r3.o.lencr.org | Akamai International B.V. | DE | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
dulichdichvu.net |
| malicious |
dvinge.com |
| unknown |
eapro.in |
| suspicious |
www.eapro.in |
| suspicious |
ctldl.windowsupdate.com |
| whitelisted |
x1.c.lencr.org |
| whitelisted |
www.e-xim.pl |
| unknown |
r3.o.lencr.org |
| shared |