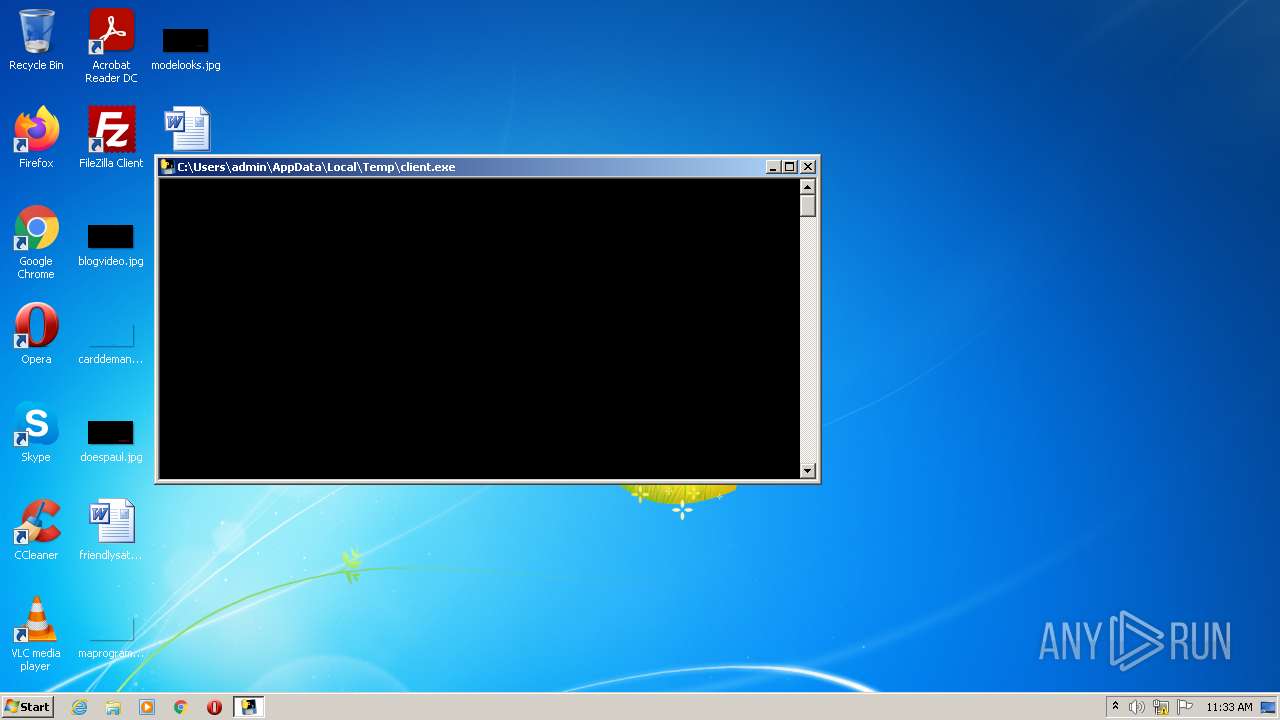
| File name: | client.exe |
| Full analysis: | https://app.any.run/tasks/3e7a85d0-74d9-4731-84b8-2ad519392315 |
| Verdict: | Malicious activity |
| Analysis date: | June 27, 2022, 10:33:06 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (console) Intel 80386, for MS Windows |
| MD5: | DAE78793177AEECAD523E1063C236E9B |
| SHA1: | 115A7FE513FA822E96D941C7F75A7C614D7AB66F |
| SHA256: | 6159396851EF7BEC7E69238733488138014C684A703F70702629D95FEC1600D1 |
| SSDEEP: | 98304:aiMHkyNJXmTjJ5q9Jt4gy9ImjXE3cPtEBO7oVIIg2wsbgRlbrtTZm3yOtGs:9AkyH4J5q9D4ImjXEMGBO7oxgmUTrtTy |
MALICIOUS
Loads dropped or rewritten executable
- client.exe (PID: 3992)
Drops executable file immediately after starts
- client.exe (PID: 3288)
SUSPICIOUS
Checks supported languages
- client.exe (PID: 3288)
- client.exe (PID: 3992)
Application launched itself
- client.exe (PID: 3288)
Reads the computer name
- client.exe (PID: 3992)
Loads Python modules
- client.exe (PID: 3992)
Executable content was dropped or overwritten
- client.exe (PID: 3288)
Drops a file with a compile date too recent
- client.exe (PID: 3288)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| Subsystem: | Windows command line |
|---|---|
| SubsystemVersion: | 5.1 |
| ImageVersion: | - |
| OSVersion: | 5.1 |
| EntryPoint: | 0x779a |
| UninitializedDataSize: | - |
| InitializedDataSize: | 172032 |
| CodeSize: | 128000 |
| LinkerVersion: | 14 |
| PEType: | PE32 |
| TimeStamp: | 2018:09:04 16:42:13+02:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_CUI |
| Compilation Date: | 04-Sep-2018 14:42:13 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000108 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 6 |
| Time date stamp: | 04-Sep-2018 14:42:13 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0001F224 | 0x0001F400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.65269 |
.rdata | 0x00021000 | 0x0000B0EC | 0x0000B200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.10091 |
.data | 0x0002D000 | 0x0000E680 | 0x00000A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 1.94098 |
.gfids | 0x0003C000 | 0x000000B8 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 1.89006 |
.rsrc | 0x0003D000 | 0x0000EA38 | 0x0000EC00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.29706 |
.reloc | 0x0004C000 | 0x000017B8 | 0x00001800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.65088 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.58652 | 3752 | UNKNOWN | UNKNOWN | RT_ICON |
2 | 6.05629 | 2216 | UNKNOWN | UNKNOWN | RT_ICON |
3 | 5.5741 | 1384 | UNKNOWN | UNKNOWN | RT_ICON |
4 | 7.95079 | 37019 | UNKNOWN | UNKNOWN | RT_ICON |
5 | 5.29119 | 9640 | UNKNOWN | UNKNOWN | RT_ICON |
6 | 5.43869 | 4264 | UNKNOWN | UNKNOWN | RT_ICON |
7 | 5.89356 | 1128 | UNKNOWN | UNKNOWN | RT_ICON |
101 | 2.71858 | 104 | UNKNOWN | UNKNOWN | RT_GROUP_ICON |
Imports
KERNEL32.dll |
WS2_32.dll |
Total processes
35
Monitored processes
2
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 3288 | "C:\Users\admin\AppData\Local\Temp\client.exe" | C:\Users\admin\AppData\Local\Temp\client.exe | Explorer.EXE | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 1 Modules
| |||||||||||||||
| 3992 | "C:\Users\admin\AppData\Local\Temp\client.exe" | C:\Users\admin\AppData\Local\Temp\client.exe | — | client.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 1 Modules
| |||||||||||||||
Total events
151
Read events
151
Write events
0
Delete events
0
Modification events
Executable files
53
Suspicious files
1
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3288 | client.exe | C:\Users\admin\AppData\Local\Temp\_MEI32882\api-ms-win-core-file-l2-1-0.dll | executable | |
MD5:29CA2B6232E41863673BE6540425039E | SHA256:AF12DD95EA783BDB13873E6A175380FA7280BCDE7C8D552970E14954AD43D09D | |||
| 3288 | client.exe | C:\Users\admin\AppData\Local\Temp\_MEI32882\_lzma.pyd | executable | |
MD5:2A8FFABBEC5E95F8A0BA388265FE57F3 | SHA256:1FE26E0940EADB05BAC03BBC553FD9011FDB0C067B8082B896C1D425D17F7542 | |||
| 3288 | client.exe | C:\Users\admin\AppData\Local\Temp\_MEI32882\_ssl.pyd | executable | |
MD5:36E29BB673D0DD63EDAC4AB90C307C4E | SHA256:9280FE6A4FD3324754548BC19CFAB60AAE8A824E7C7B7BA41592BF1587B29A4B | |||
| 3288 | client.exe | C:\Users\admin\AppData\Local\Temp\_MEI32882\api-ms-win-core-debug-l1-1-0.dll | executable | |
MD5:35E0A11F1BDBFF0C994F769FC5BEFA14 | SHA256:740FE94F94043B42710641ABF81693F4794D57D4DE9AB552498F796046550B13 | |||
| 3288 | client.exe | C:\Users\admin\AppData\Local\Temp\_MEI32882\api-ms-win-core-file-l1-1-0.dll | executable | |
MD5:DD5B0D3AEA79781F532712413D0A4B47 | SHA256:36424777D41A90D57C2F129405BC0859D629402FD3C35A12E9118021C8EE7A8D | |||
| 3288 | client.exe | C:\Users\admin\AppData\Local\Temp\_MEI32882\api-ms-win-core-heap-l1-1-0.dll | executable | |
MD5:68B97E0084EA10785D16259AE1D7DCD6 | SHA256:128AB7811295EEAFA4E47514962D6C3F7D9A36372FD12B03C09255EE4B4E3A8C | |||
| 3288 | client.exe | C:\Users\admin\AppData\Local\Temp\_MEI32882\api-ms-win-core-console-l1-1-0.dll | executable | |
MD5:E4DFC2BFE7B21233BE21F6D1724F6D4B | SHA256:9ABB11919240F1A7A0C7FF1564DA0F369BBBCAD24E07B27A304C845C1EACC4DE | |||
| 3288 | client.exe | C:\Users\admin\AppData\Local\Temp\_MEI32882\api-ms-win-core-handle-l1-1-0.dll | executable | |
MD5:37DD1E5B624D12B45FD748A43F2C0874 | SHA256:BE82B32DF8E454D4F3FBE35F8D8393BA2EC37F1D4BD6369A163D0BFA63697E1C | |||
| 3288 | client.exe | C:\Users\admin\AppData\Local\Temp\_MEI32882\api-ms-win-core-localization-l1-2-0.dll | executable | |
MD5:A02A03FA2D7C75F3B79F1B1C049A36A1 | SHA256:76911BD316F4F94BCA7806CD2A5E91125999818C37306789A26B171B44DB557A | |||
| 3288 | client.exe | C:\Users\admin\AppData\Local\Temp\_MEI32882\_ctypes.pyd | executable | |
MD5:FB3961DD31ADE7EDCC40F97F2ADDBF7E | SHA256:B85DC8634E14E2542A54045283A58789988ED0803B3E8FE52EED6AE6A51D6389 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report