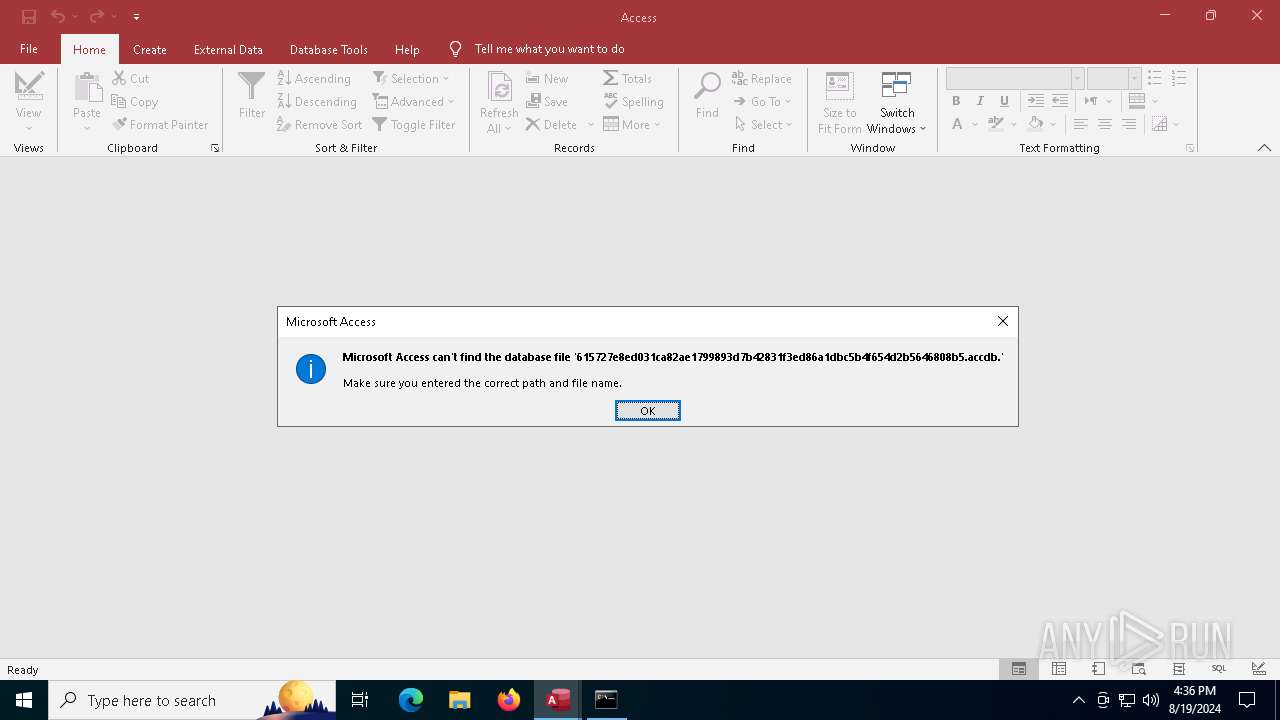
| File name: | 615727e8ed031ca82ae1799893d7b42831f3ed86a1dbc5b4f654d2b5646808b5 |
| Full analysis: | https://app.any.run/tasks/c907ad20-9d1d-4f14-85e8-7f913f978fb3 |
| Verdict: | Malicious activity |
| Analysis date: | August 19, 2024, 16:34:19 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
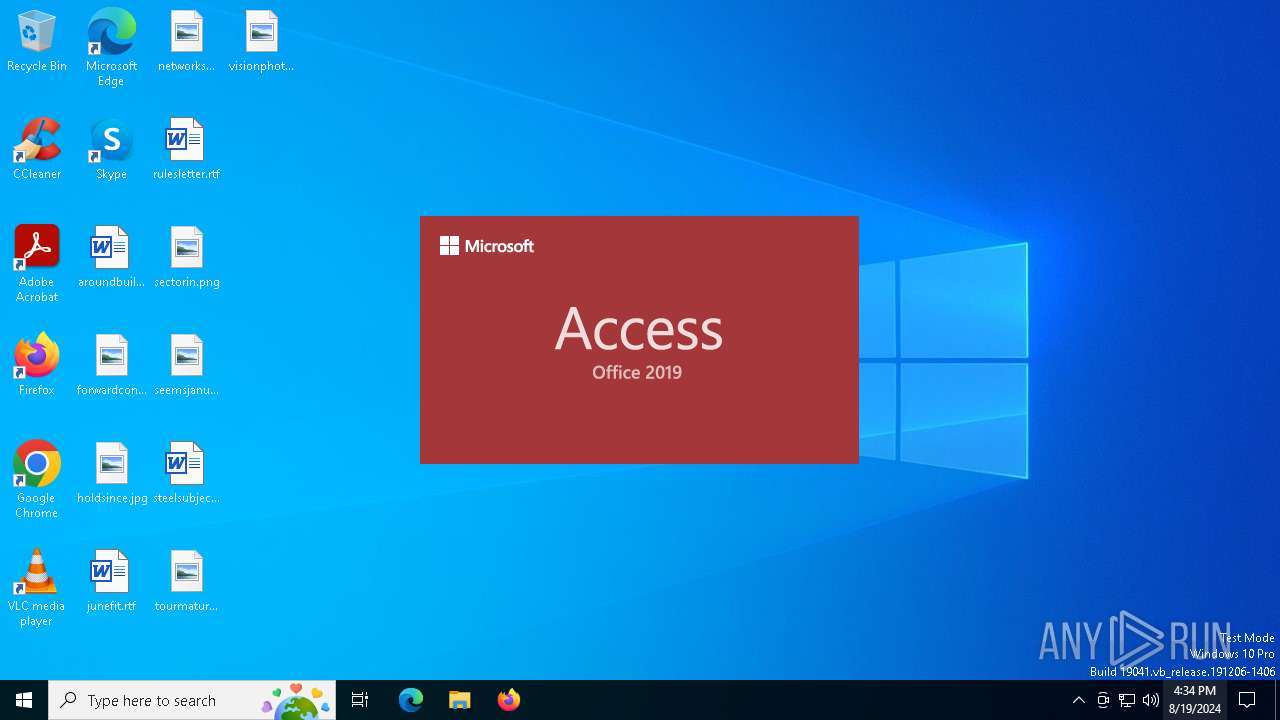
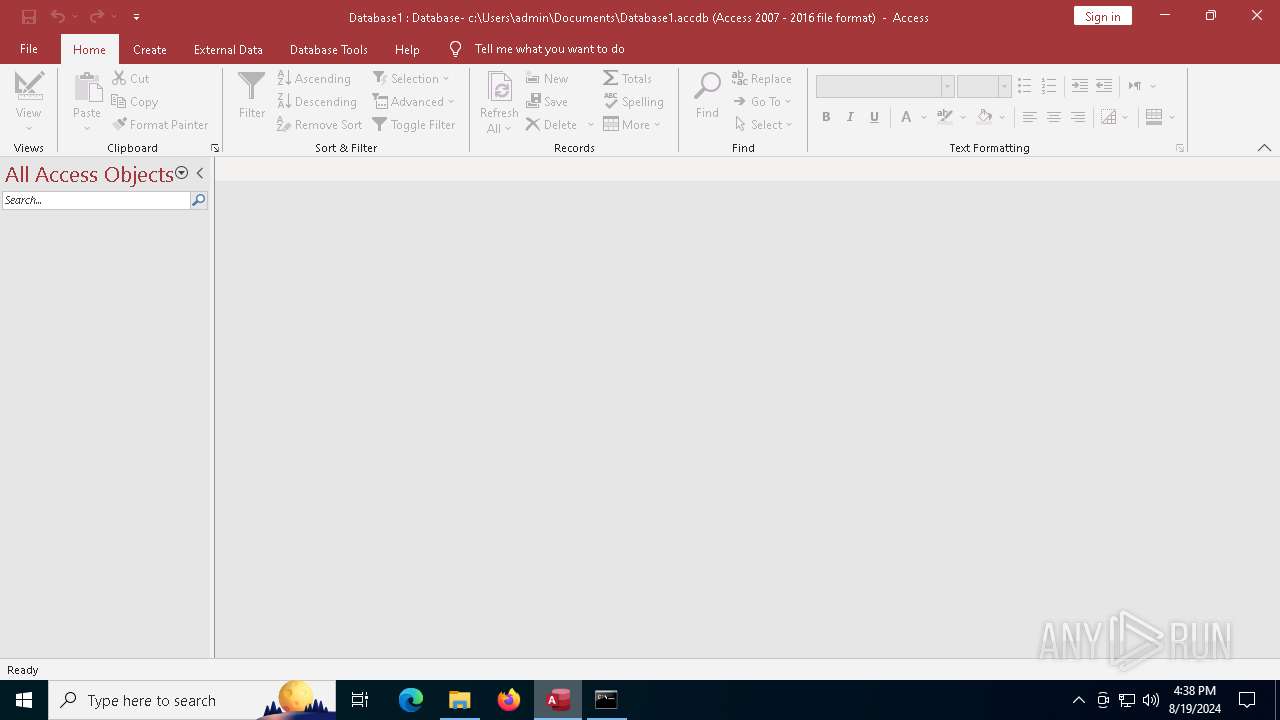
| MIME: | application/x-msaccess |
| File info: | Microsoft Access Database |
| MD5: | 44BA348E73305929239883508FA0380A |
| SHA1: | 7AB2D08EF52D443ACDBD2BC0C754145C83F7B587 |
| SHA256: | 615727E8ED031CA82AE1799893D7B42831F3ED86A1DBC5B4F654D2B5646808B5 |
| SSDEEP: | 1536:UDrxFe+7/PqoFXJdfNrFzmzwxRqZtk6E3or6YF1RiJDjyBJtqByJOqxInPbdM9dp:U/r7/PqoFXJhxFzf3uB8qxokZ |
MALICIOUS
Scans artifacts that could help determine the target
- MSACCESS.EXE (PID: 6576)
- MSACCESS.EXE (PID: 2660)
- MSACCESS.EXE (PID: 6920)
Checks whether a specified folder exists (SCRIPT)
- MSACCESS.EXE (PID: 6576)
Creates a new folder (SCRIPT)
- MSACCESS.EXE (PID: 6576)
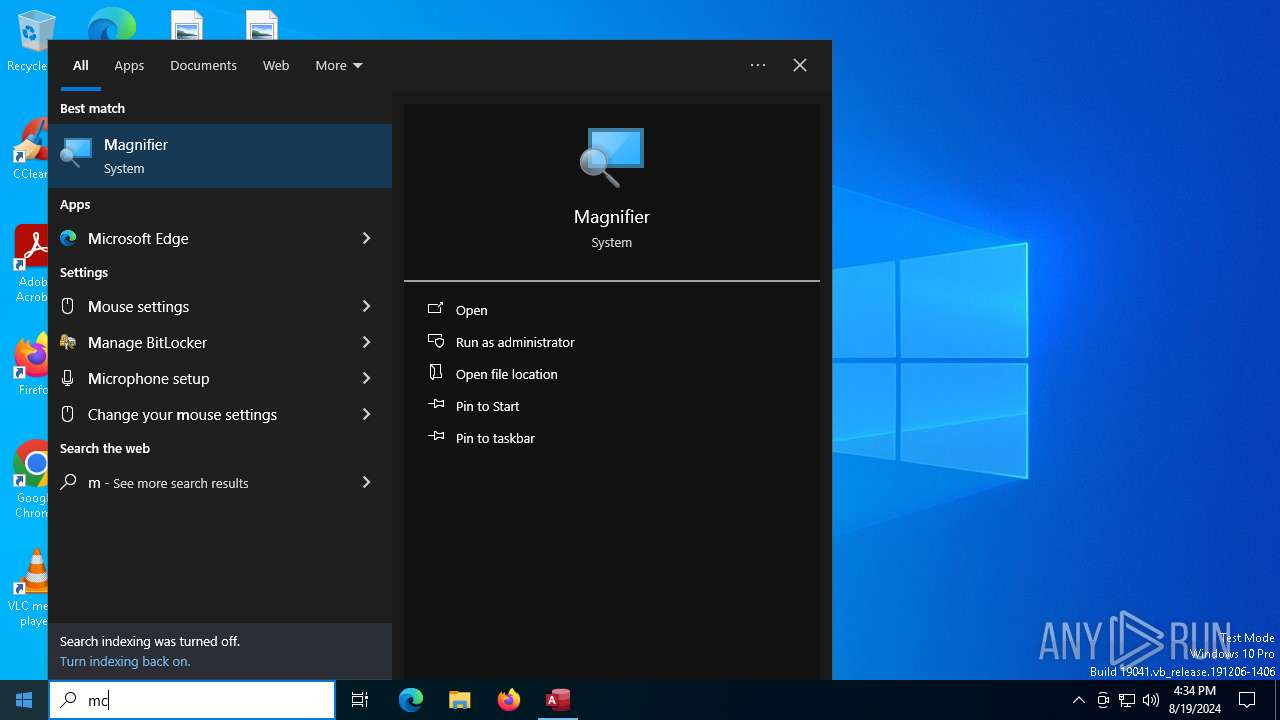
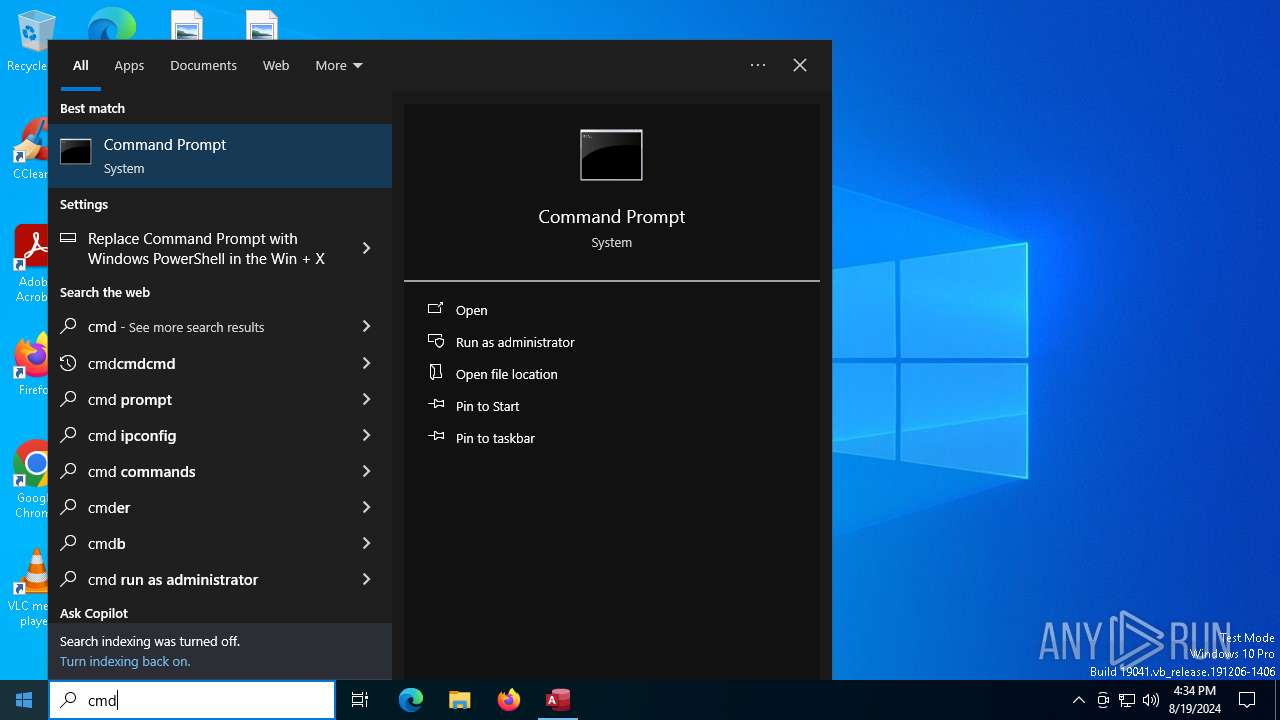
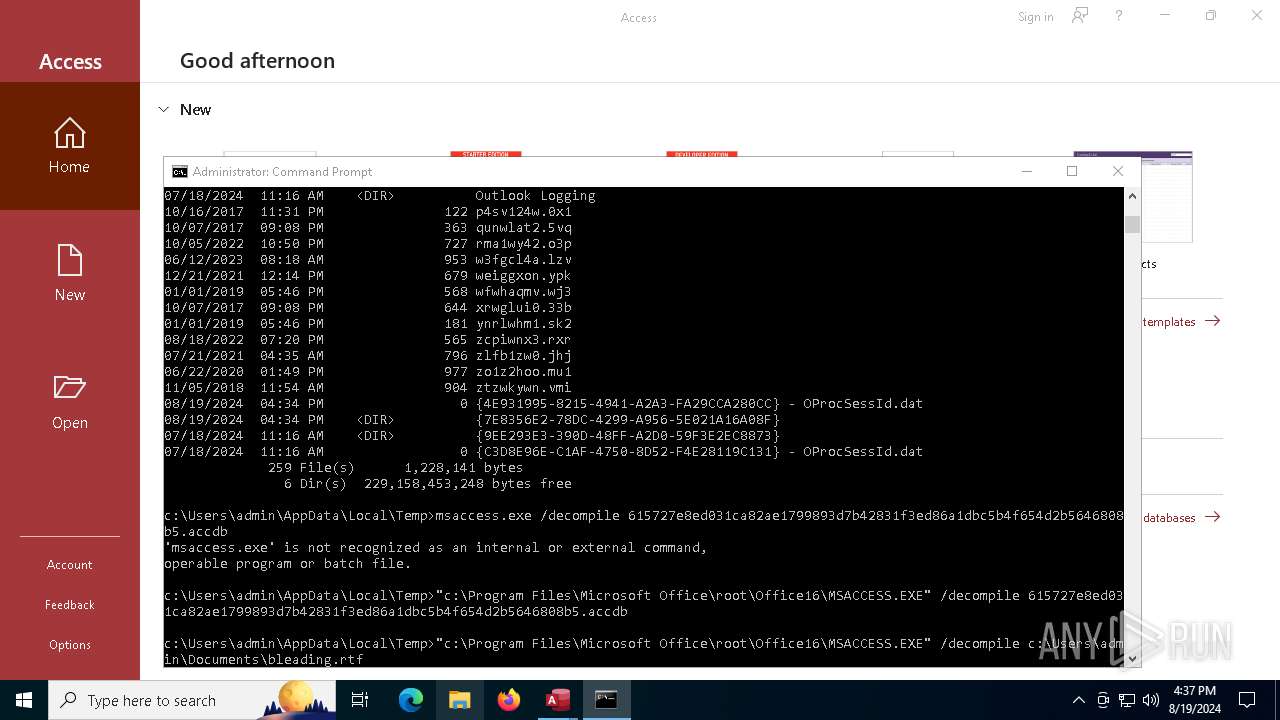
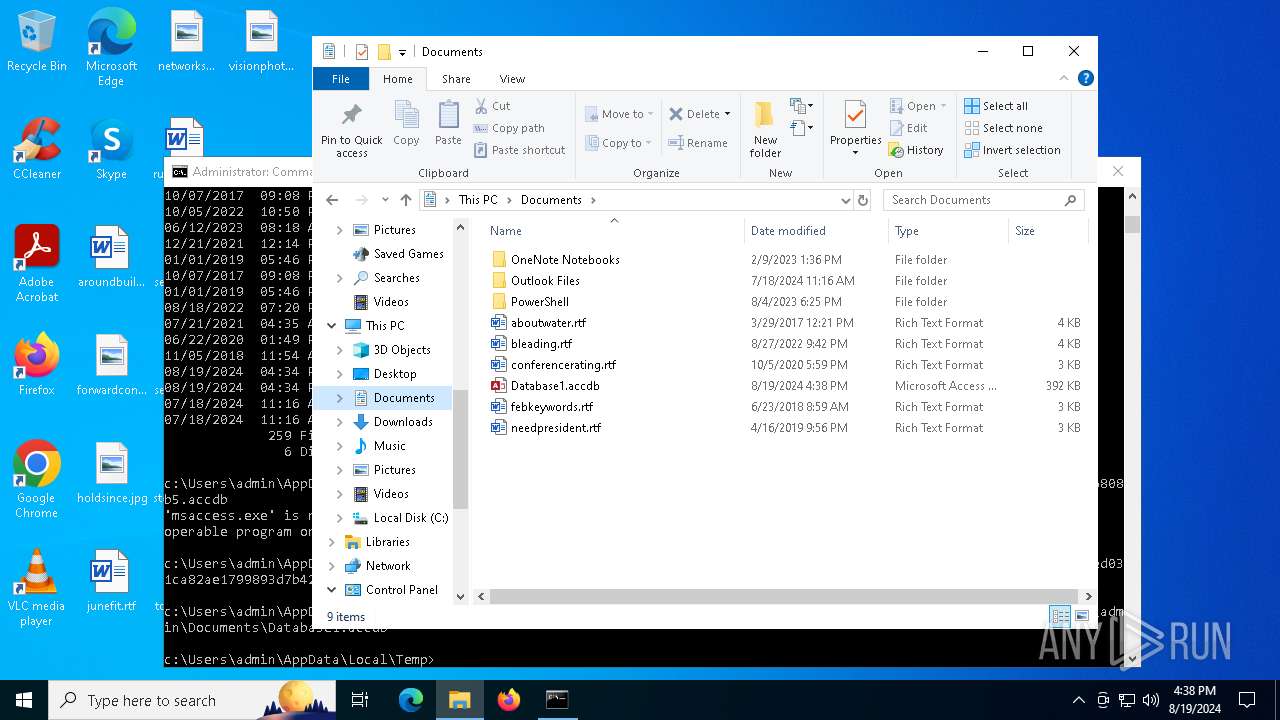
Uses Task Scheduler to run other applications
- cmd.exe (PID: 1692)
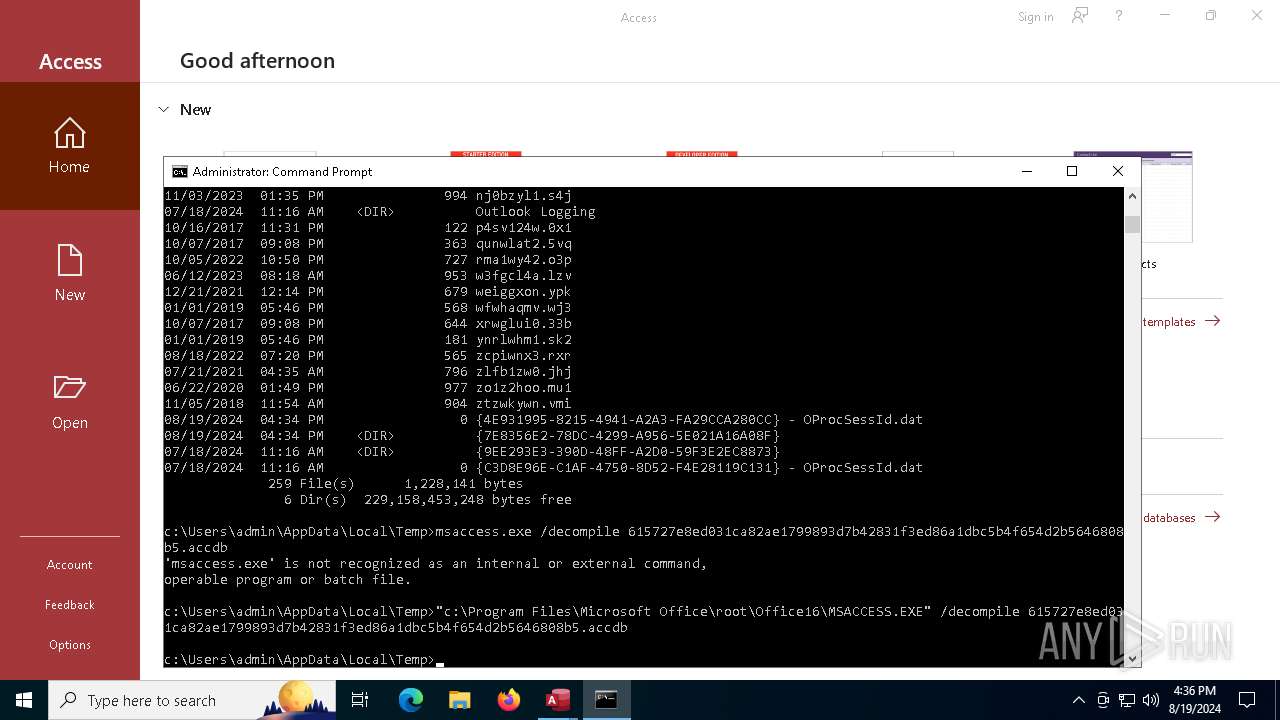
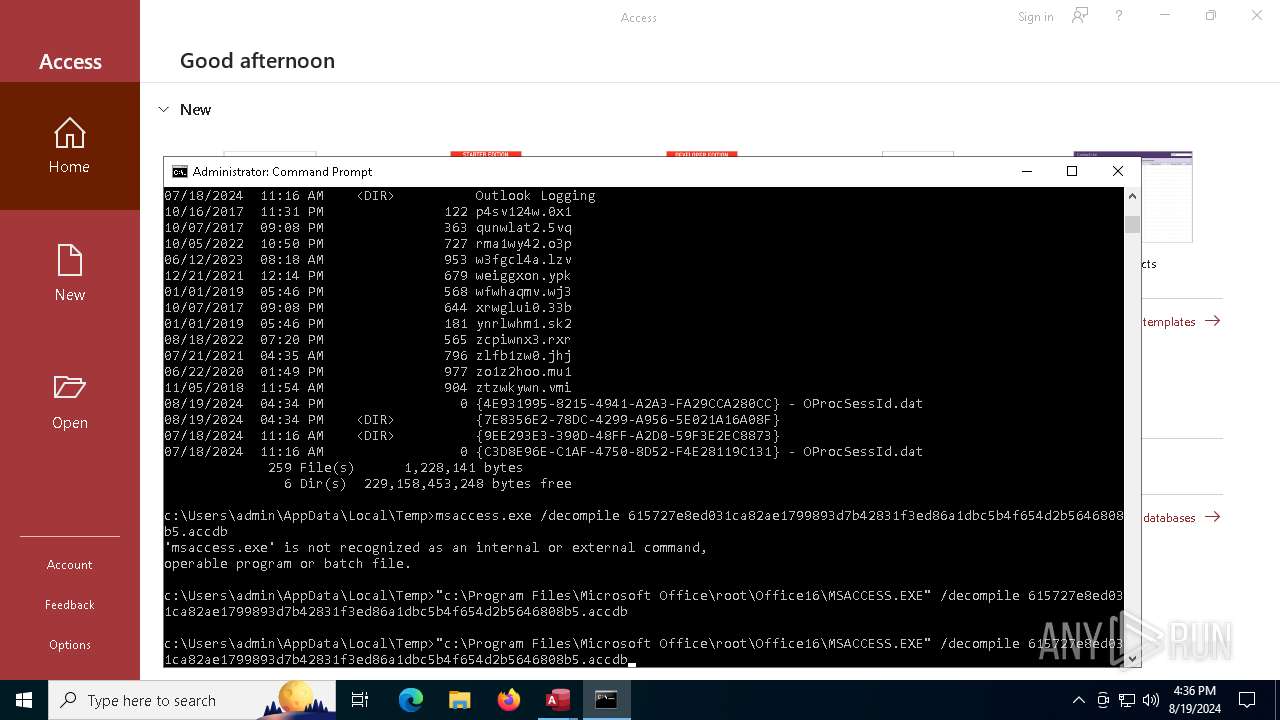
Unusual execution from MS Office
- MSACCESS.EXE (PID: 6576)
SUSPICIOUS
Reads the date of Windows installation
- MSACCESS.EXE (PID: 6576)
- MSACCESS.EXE (PID: 2660)
- MSACCESS.EXE (PID: 6920)
Creates FileSystem object to access computer's file system (SCRIPT)
- MSACCESS.EXE (PID: 6576)
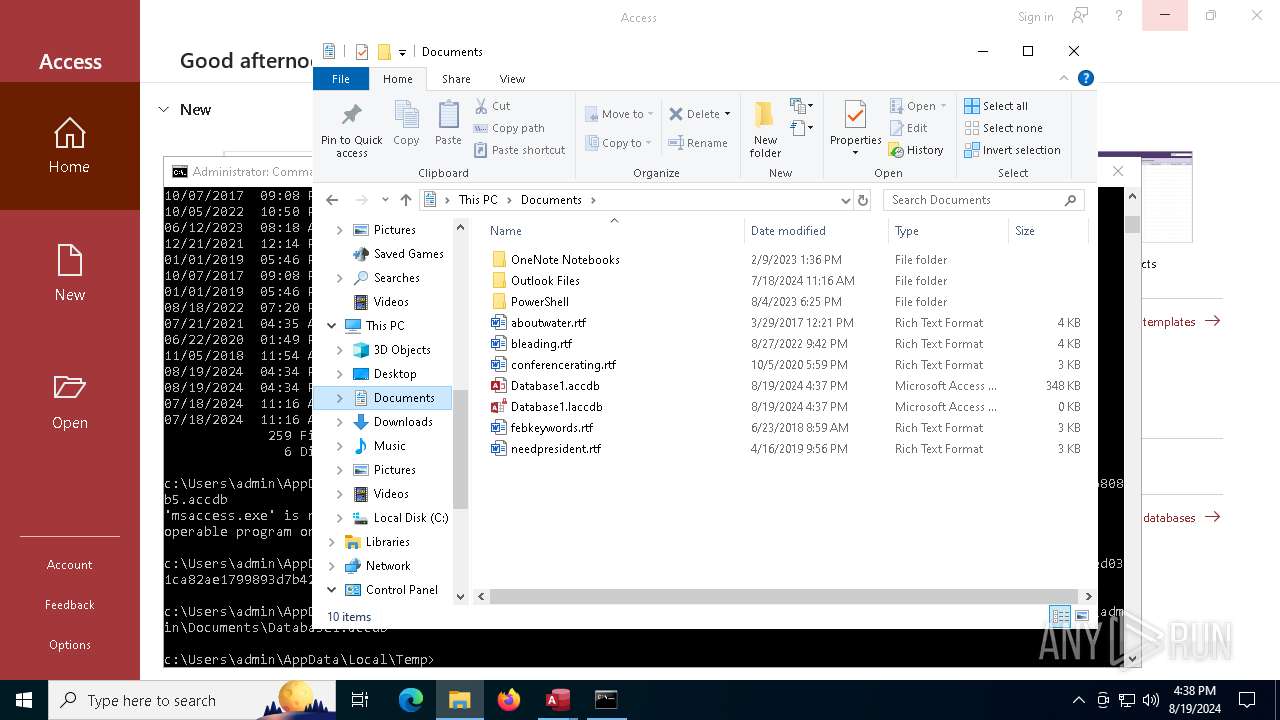
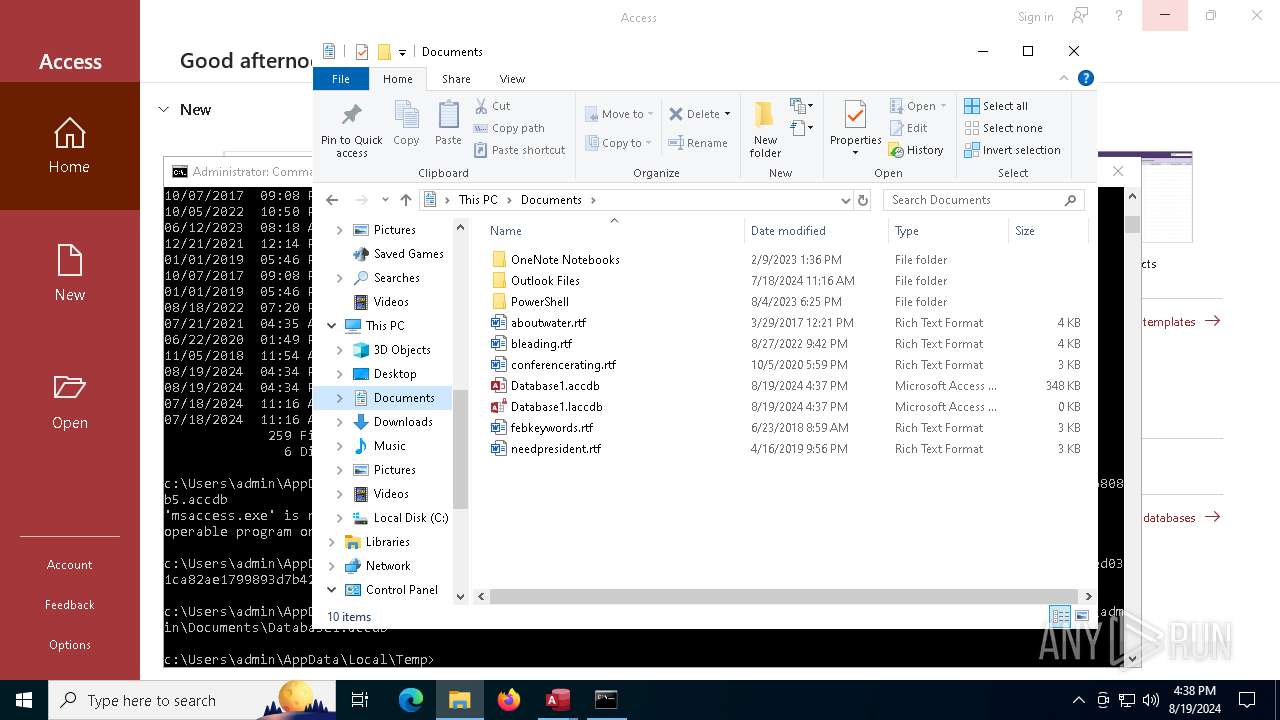
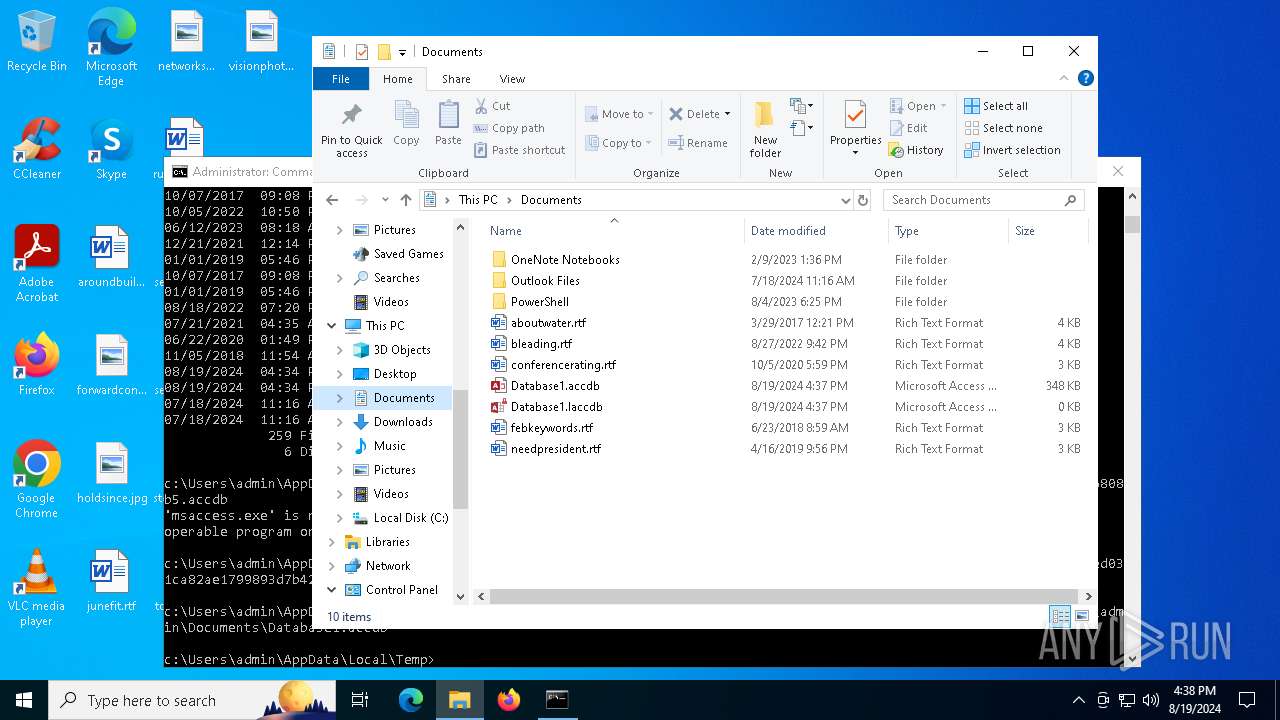
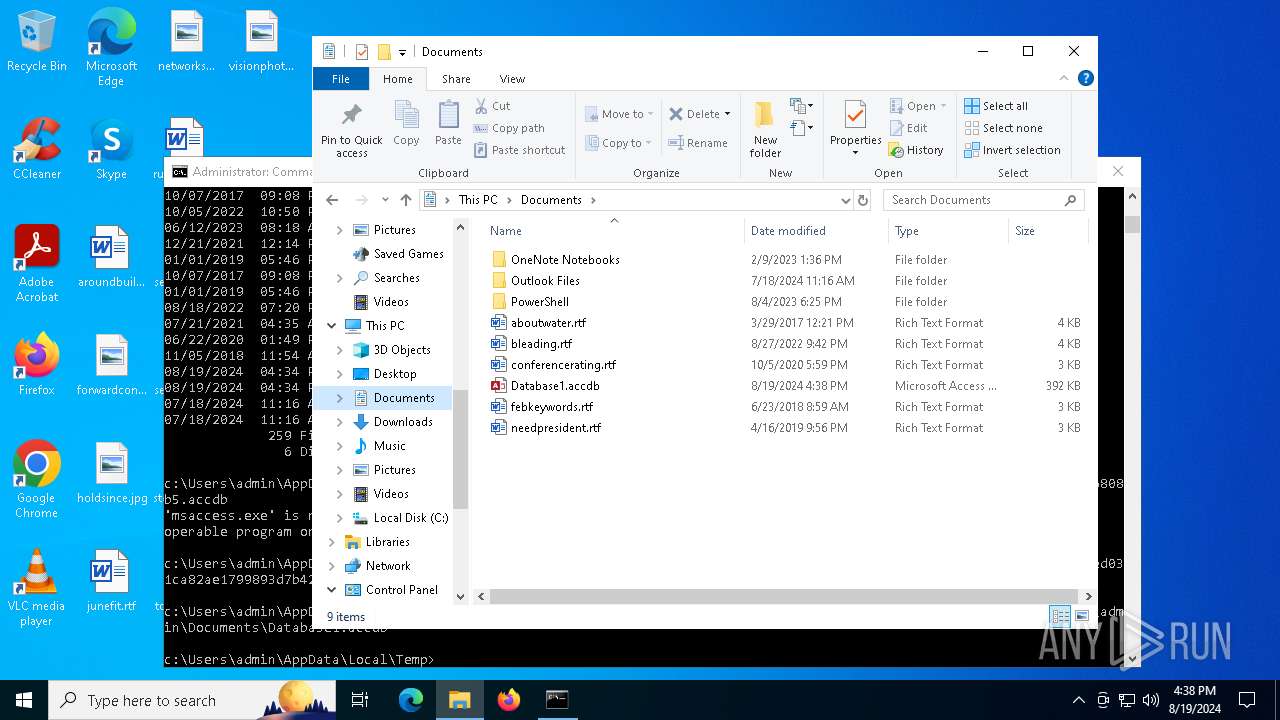
Executable content was dropped or overwritten
- MSACCESS.EXE (PID: 6576)
Reads security settings of Internet Explorer
- MSACCESS.EXE (PID: 6576)
- MSACCESS.EXE (PID: 2660)
- MSACCESS.EXE (PID: 6920)
Drops the executable file immediately after the start
- MSACCESS.EXE (PID: 6576)
Checks Windows Trust Settings
- MSACCESS.EXE (PID: 6576)
- MSACCESS.EXE (PID: 2660)
- MSACCESS.EXE (PID: 6920)
Starts CMD.EXE for commands execution
- KbUpdate.exe (PID: 6500)
INFO
Reads the computer name
- MSACCESS.EXE (PID: 6576)
- MSACCESS.EXE (PID: 2660)
- MSACCESS.EXE (PID: 6920)
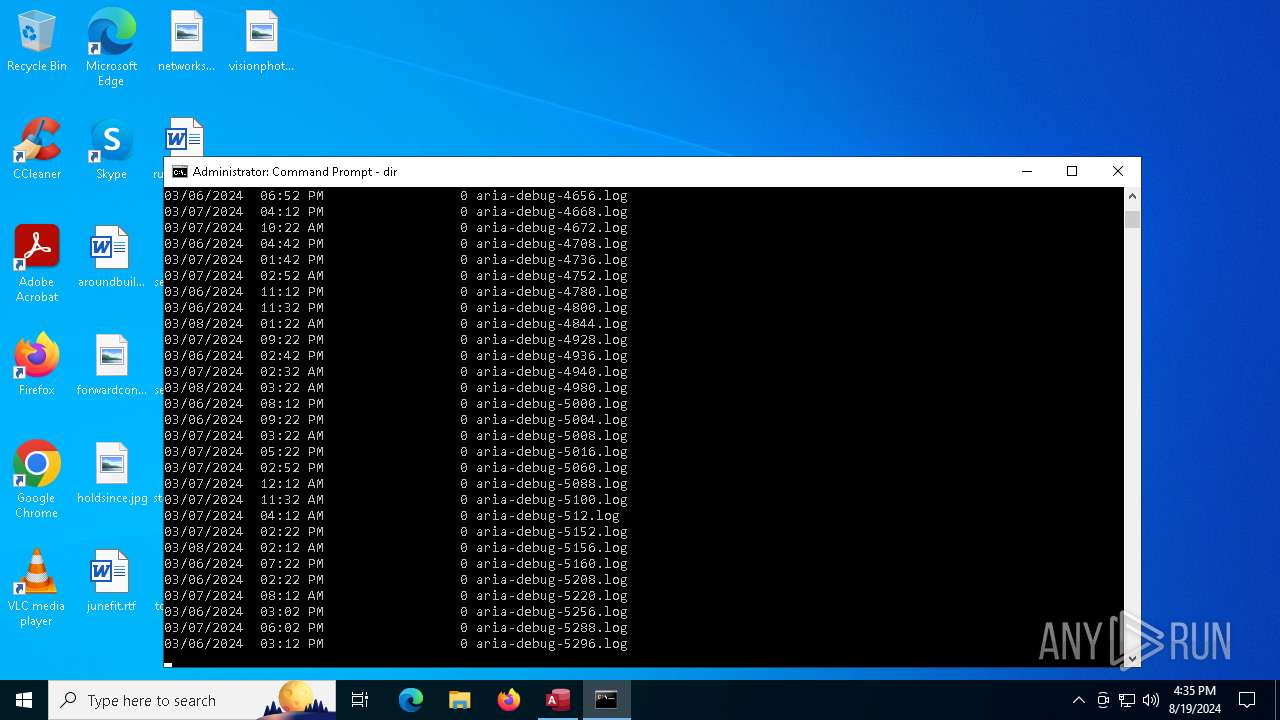
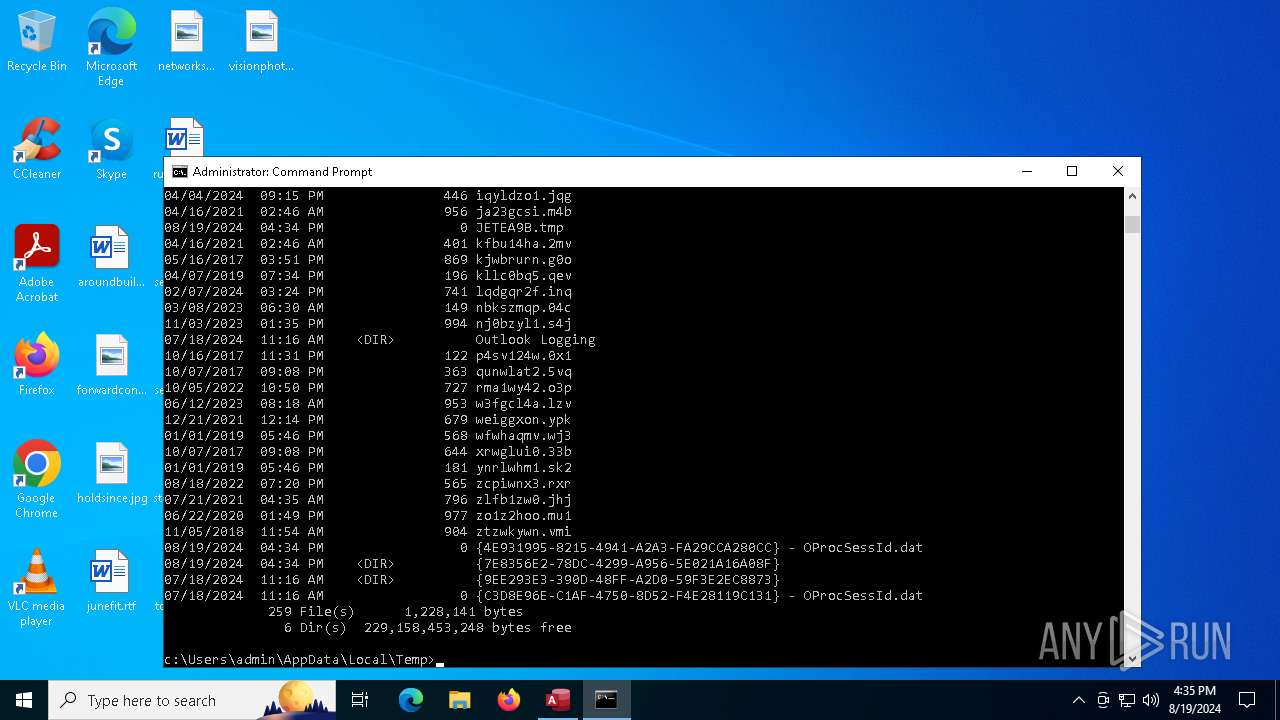
Create files in a temporary directory
- MSACCESS.EXE (PID: 6576)
- MSACCESS.EXE (PID: 2660)
- MSACCESS.EXE (PID: 6920)
Reads product name
- MSACCESS.EXE (PID: 6576)
- MSACCESS.EXE (PID: 2660)
- MSACCESS.EXE (PID: 6920)
Process checks computer location settings
- MSACCESS.EXE (PID: 6576)
- MSACCESS.EXE (PID: 6920)
- MSACCESS.EXE (PID: 2660)
Reads the machine GUID from the registry
- MSACCESS.EXE (PID: 6576)
- MSACCESS.EXE (PID: 2660)
- MSACCESS.EXE (PID: 6920)
Reads the software policy settings
- MSACCESS.EXE (PID: 6576)
- MSACCESS.EXE (PID: 2660)
- MSACCESS.EXE (PID: 6920)
Checks proxy server information
- MSACCESS.EXE (PID: 6576)
- MSACCESS.EXE (PID: 2660)
- MSACCESS.EXE (PID: 6920)
Reads Environment values
- MSACCESS.EXE (PID: 6576)
- MSACCESS.EXE (PID: 2660)
- MSACCESS.EXE (PID: 6920)
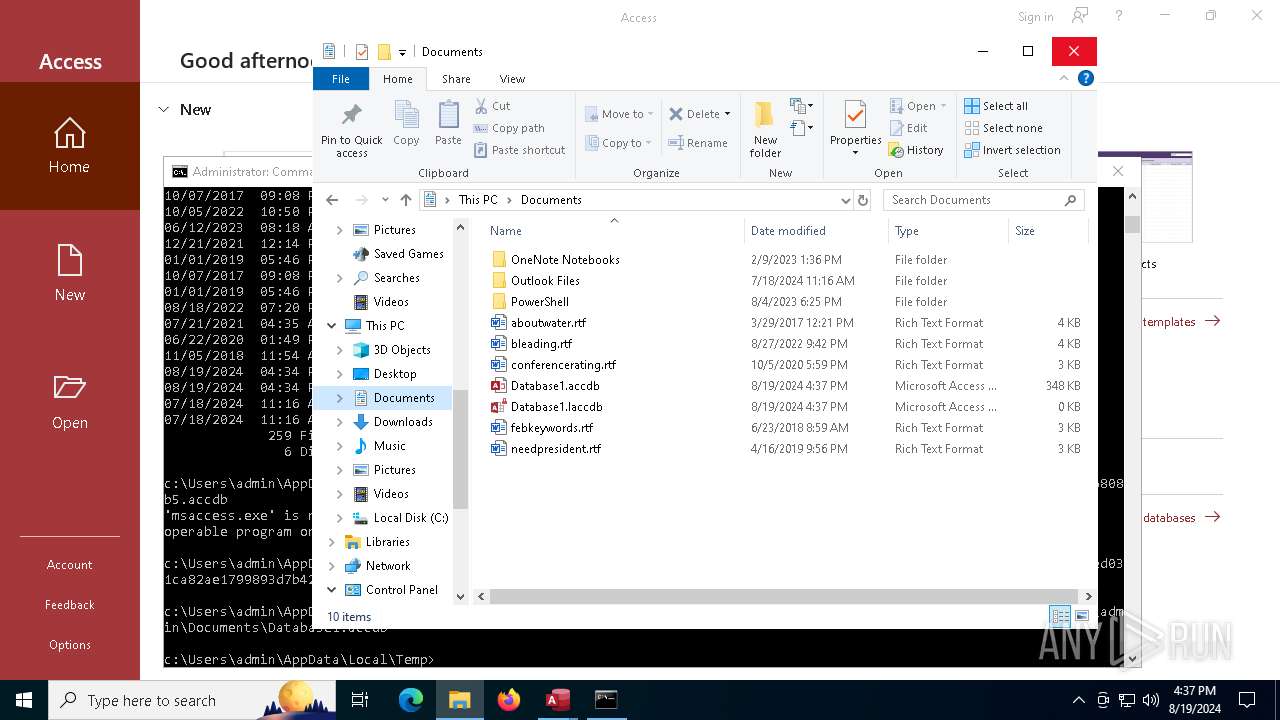
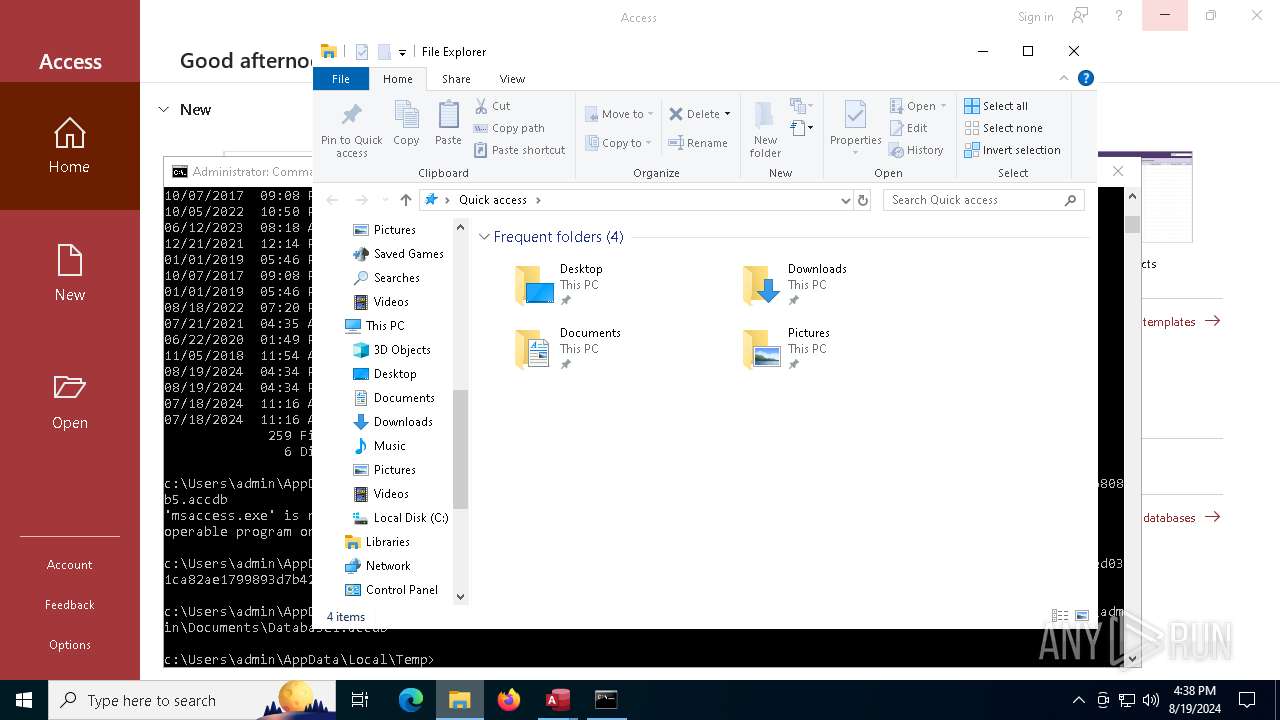
Creates files or folders in the user directory
- MSACCESS.EXE (PID: 6576)
- MSACCESS.EXE (PID: 2660)
- MSACCESS.EXE (PID: 6920)
Reads CPU info
- MSACCESS.EXE (PID: 6576)
- MSACCESS.EXE (PID: 6920)
- MSACCESS.EXE (PID: 2660)
Reads Microsoft Office registry keys
- MSACCESS.EXE (PID: 6576)
- MSACCESS.EXE (PID: 2660)
- MSACCESS.EXE (PID: 6920)
Checks supported languages
- MSACCESS.EXE (PID: 6576)
- KbUpdate.exe (PID: 6500)
- MSACCESS.EXE (PID: 2660)
- MSACCESS.EXE (PID: 6920)
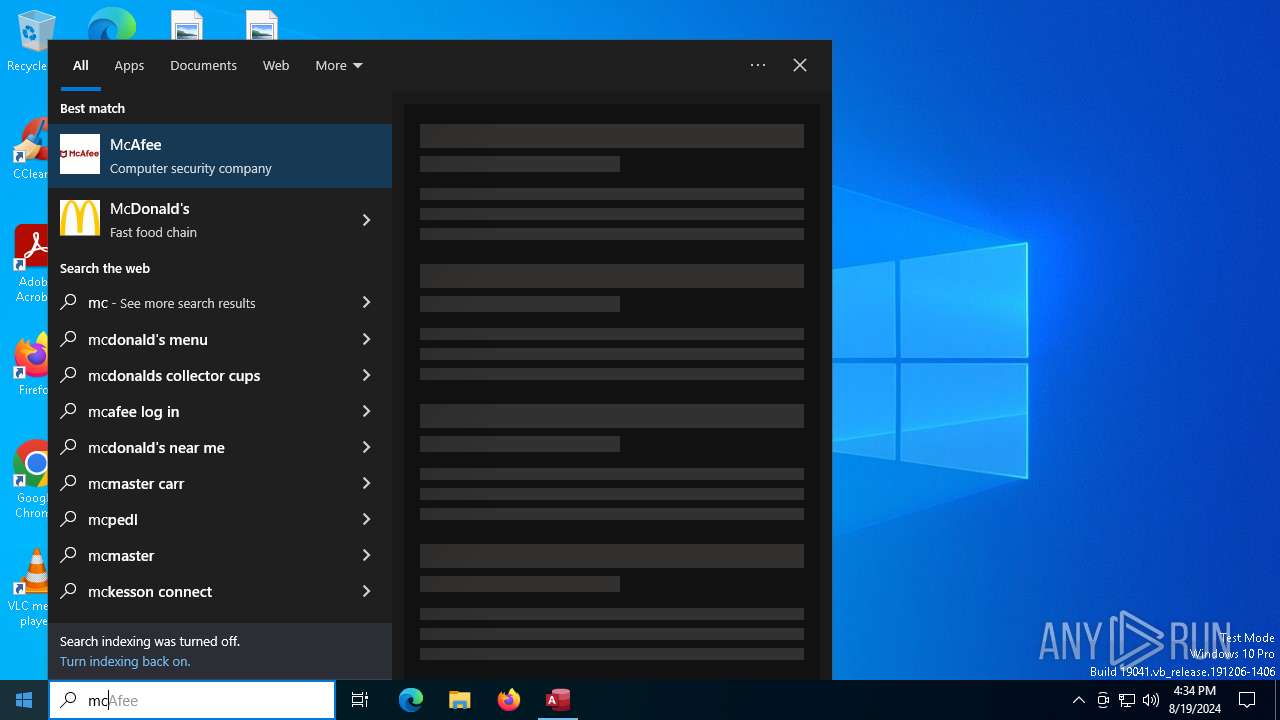
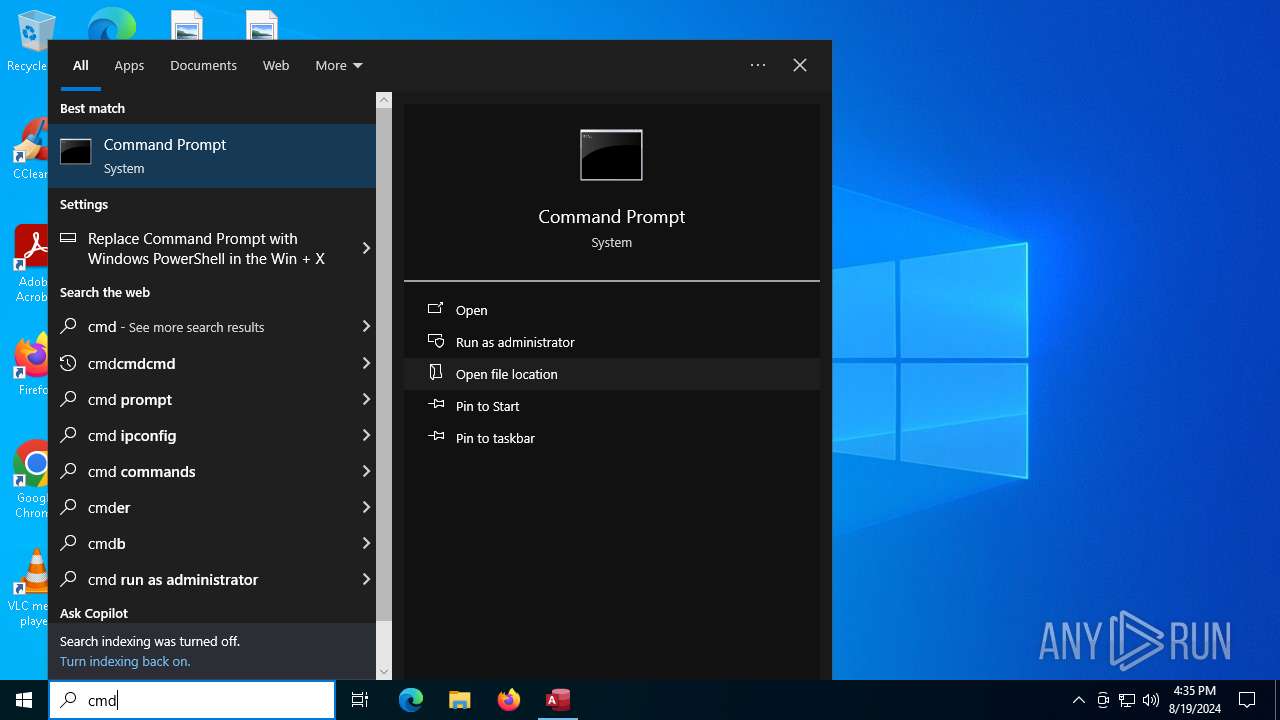
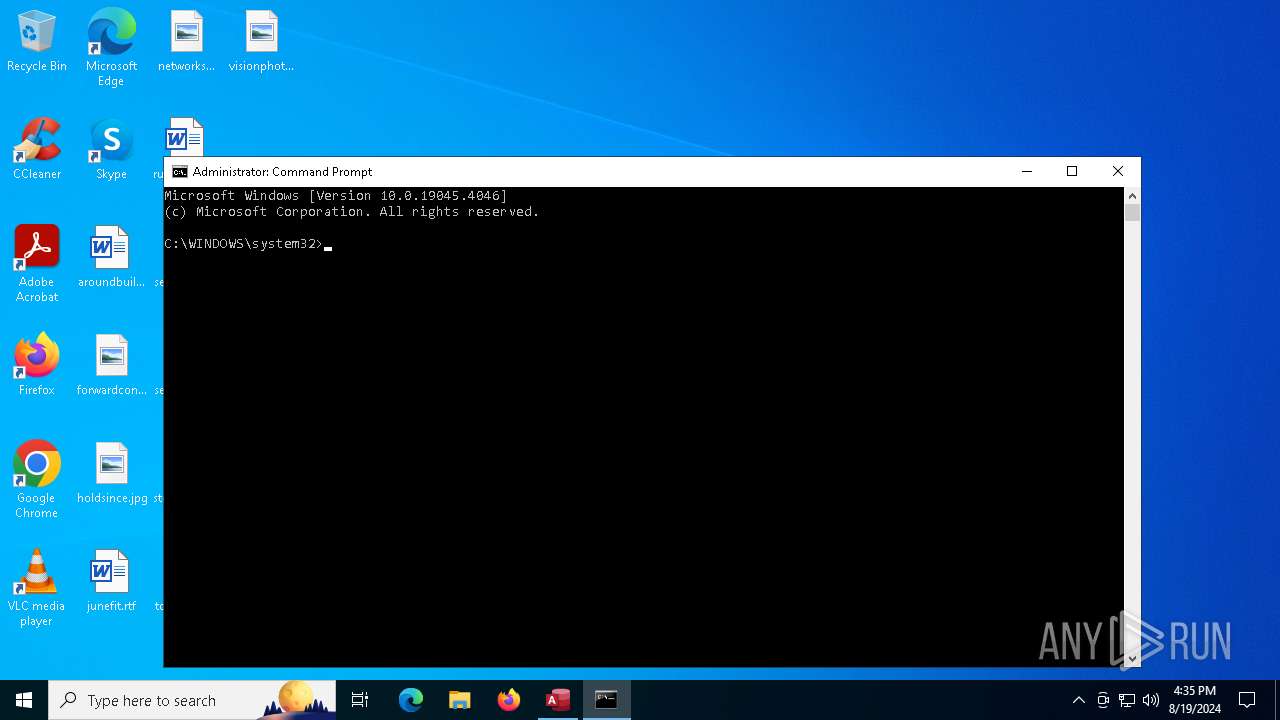
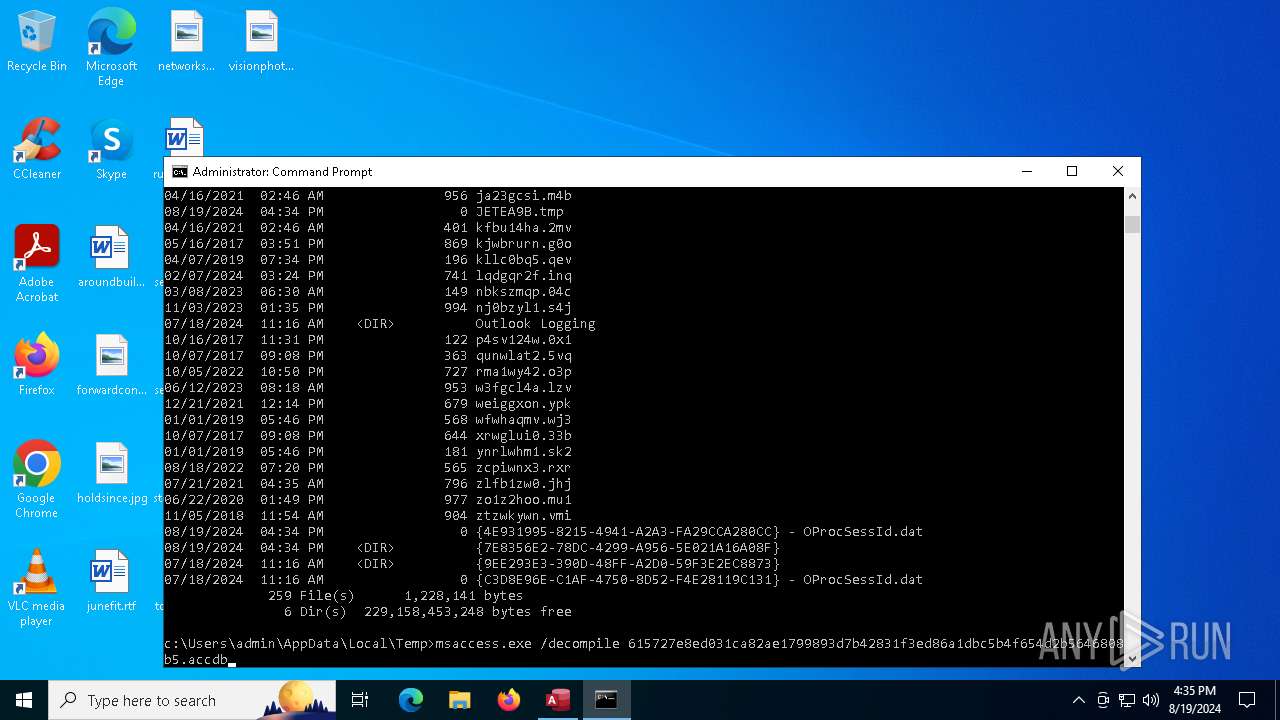
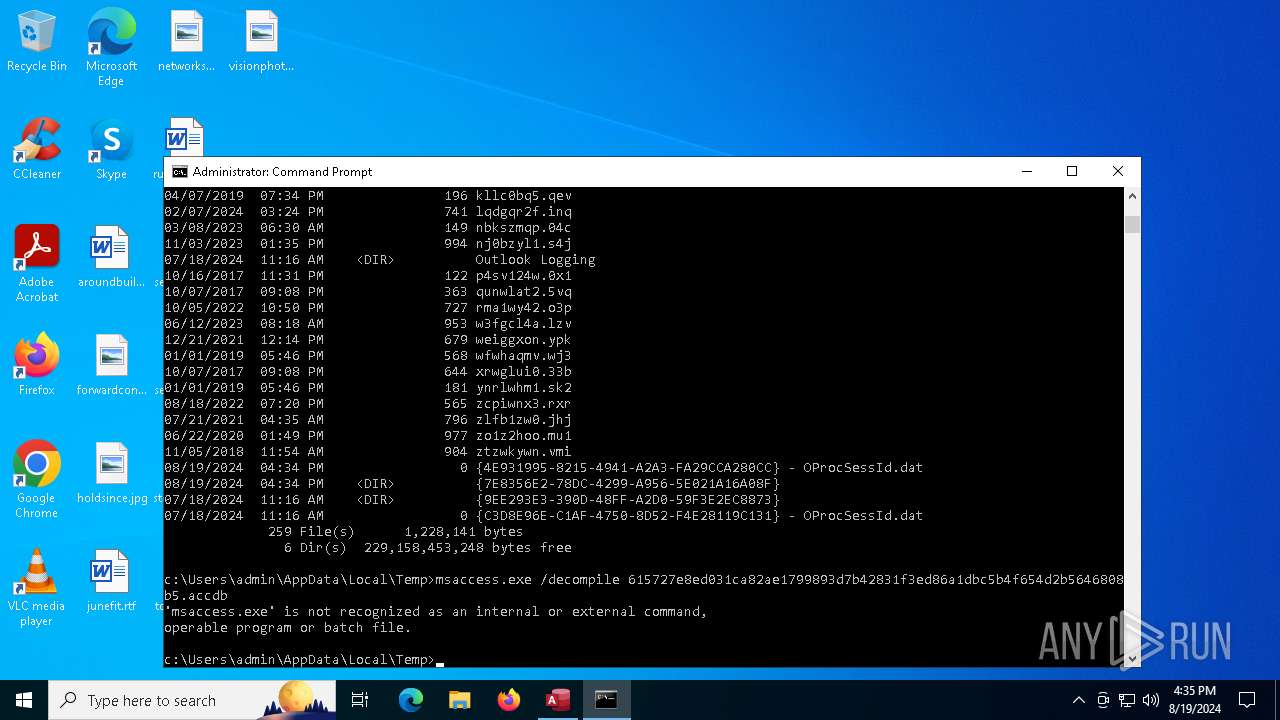
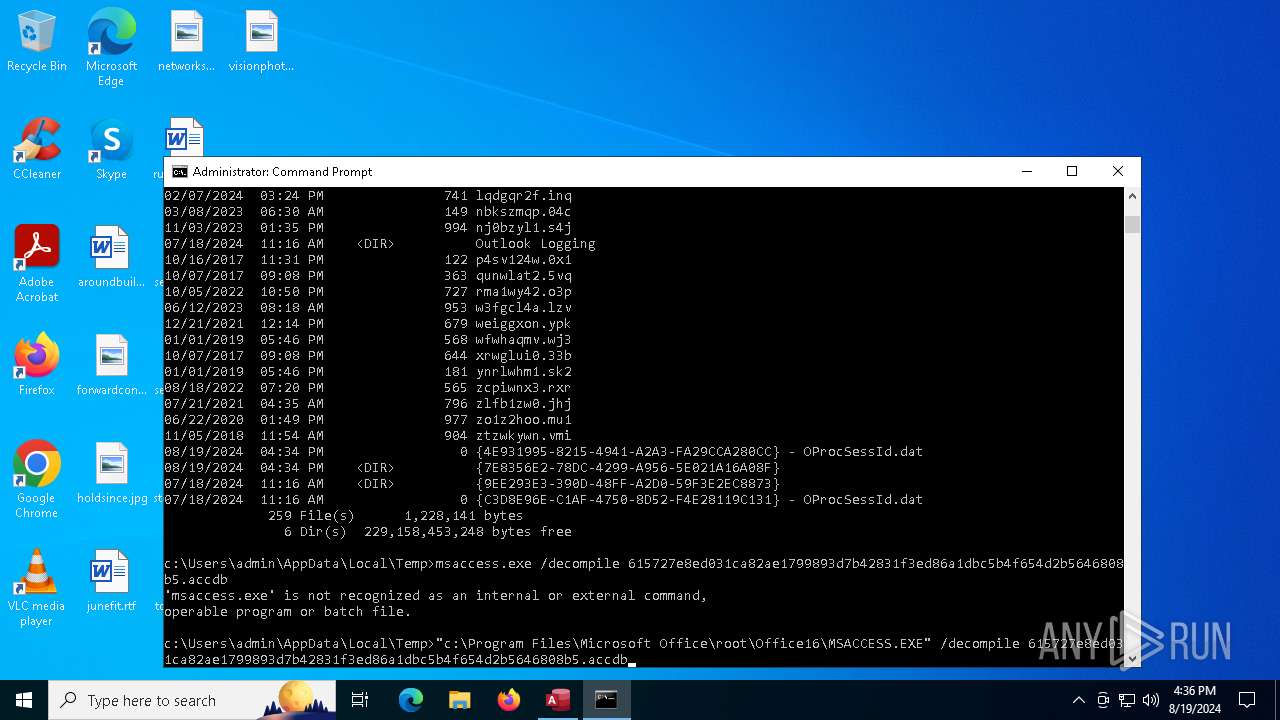
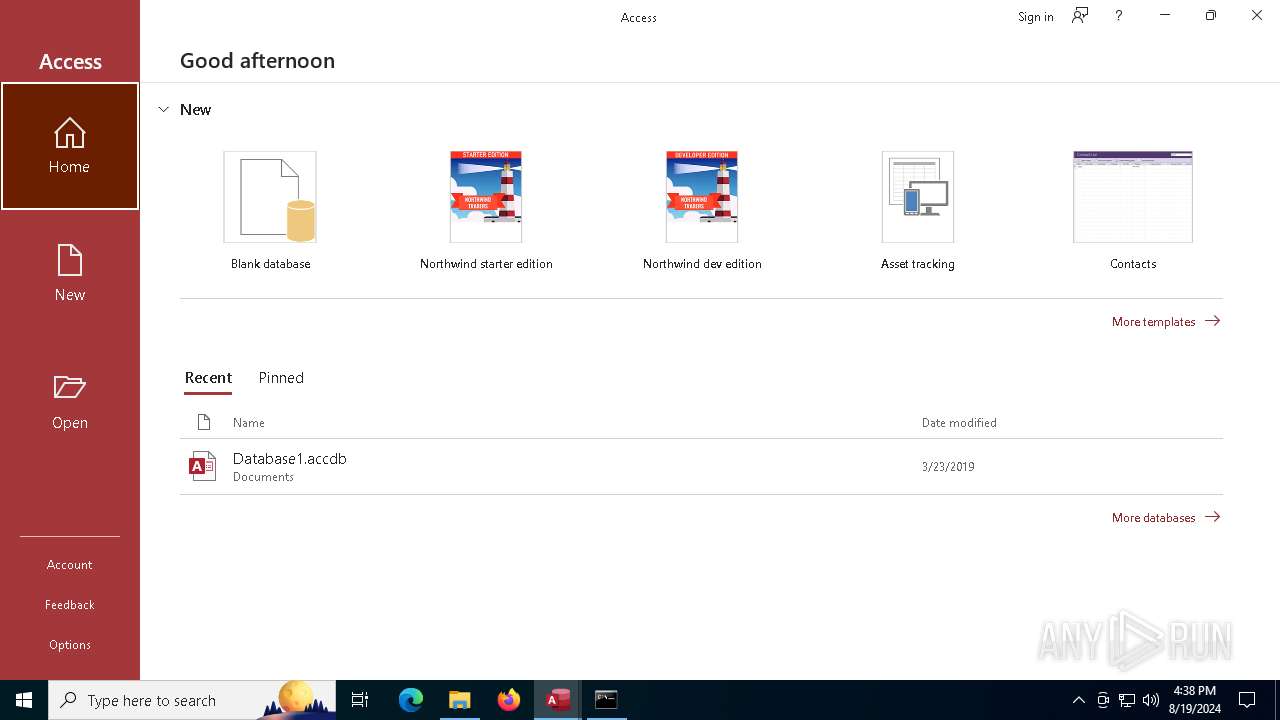
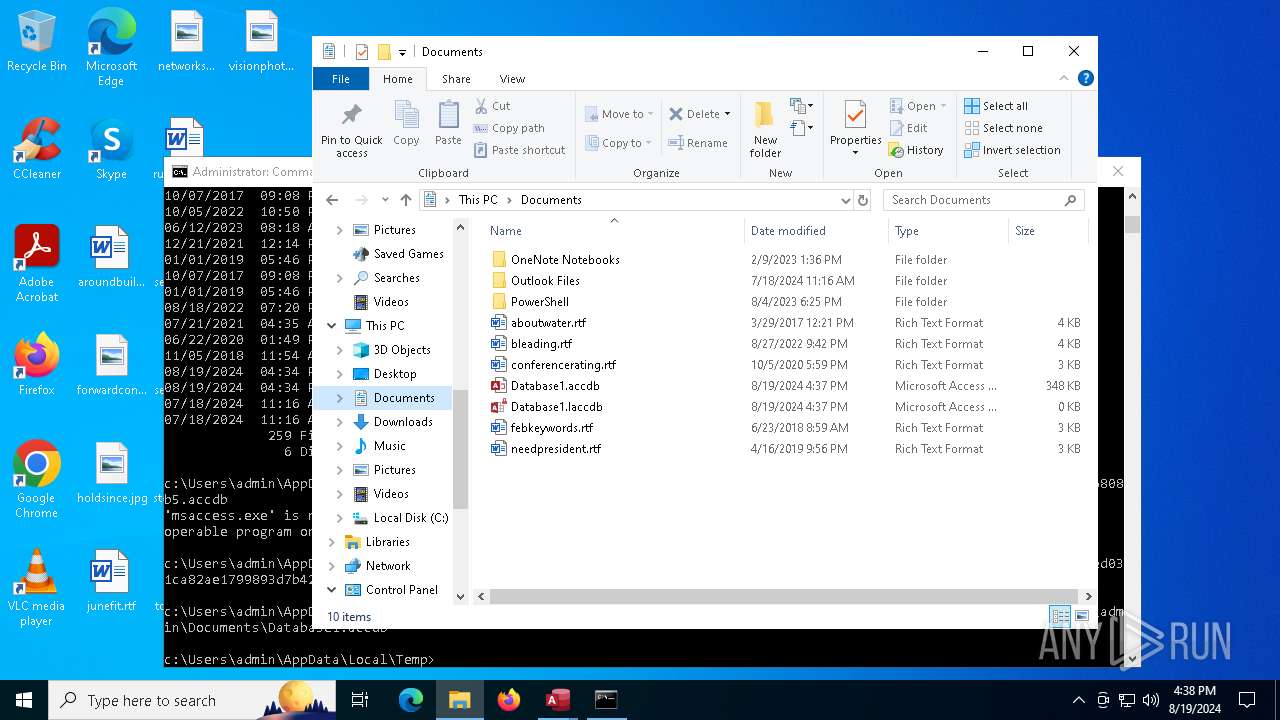
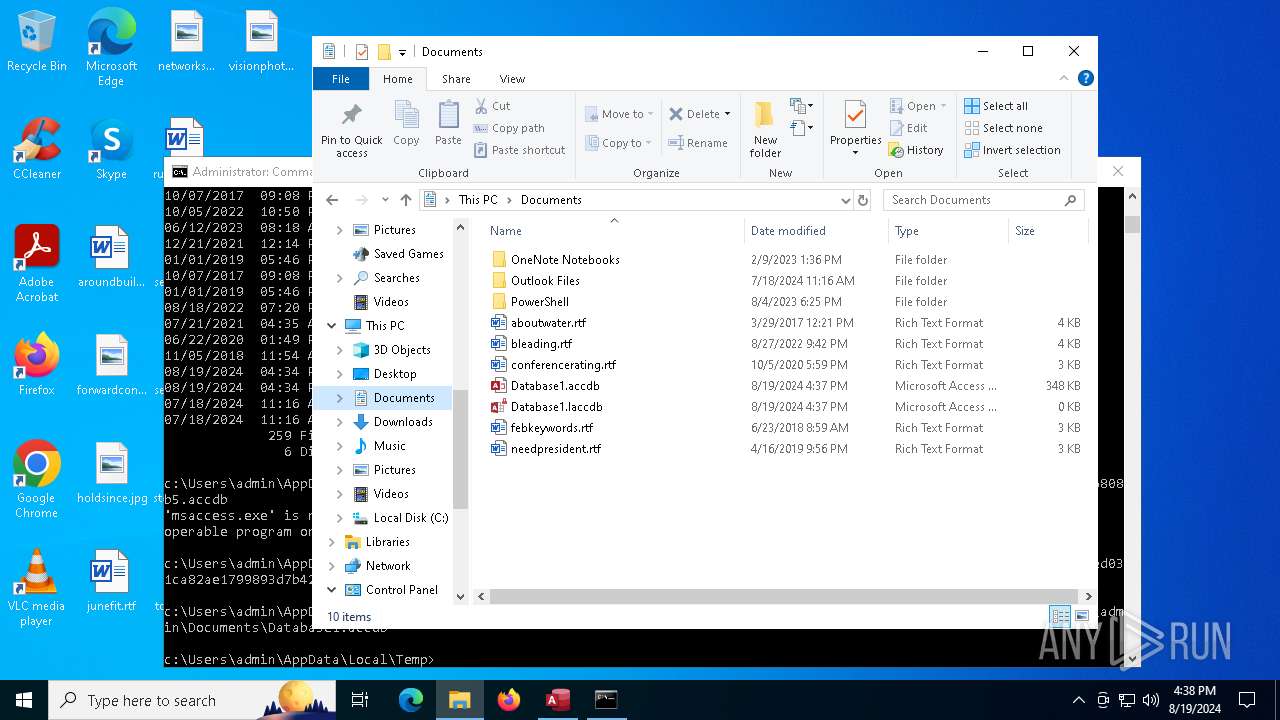
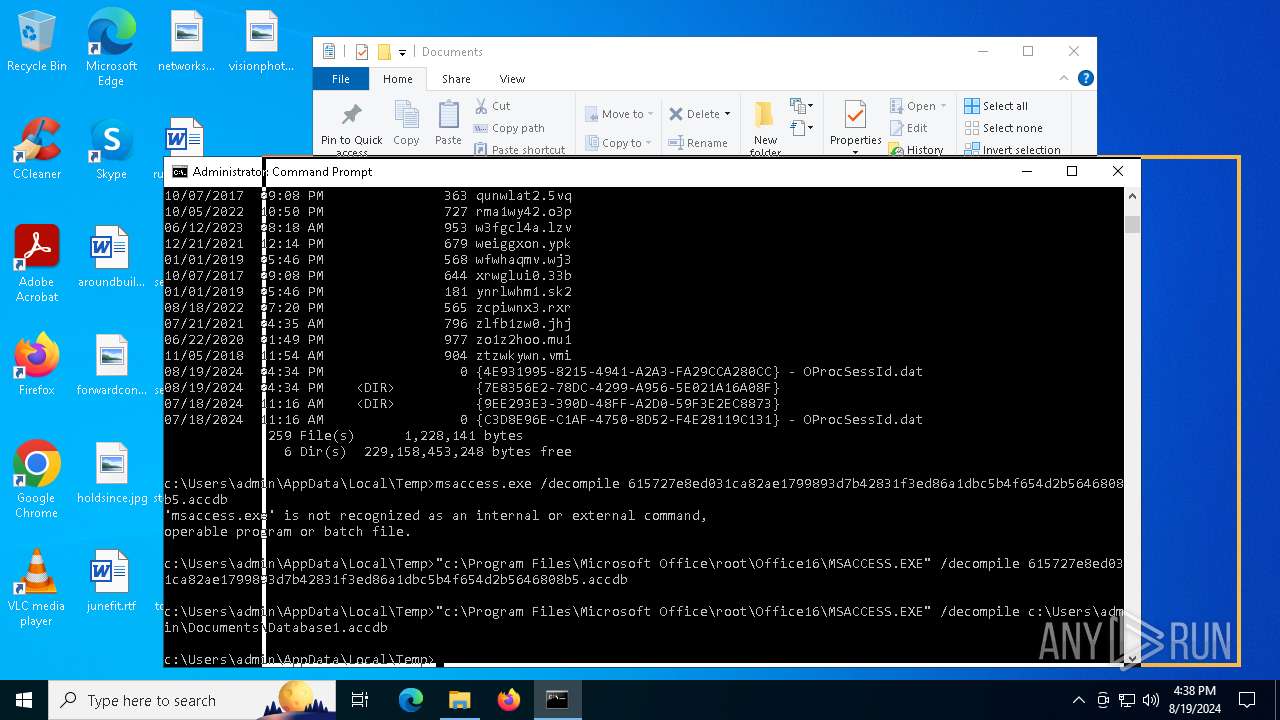
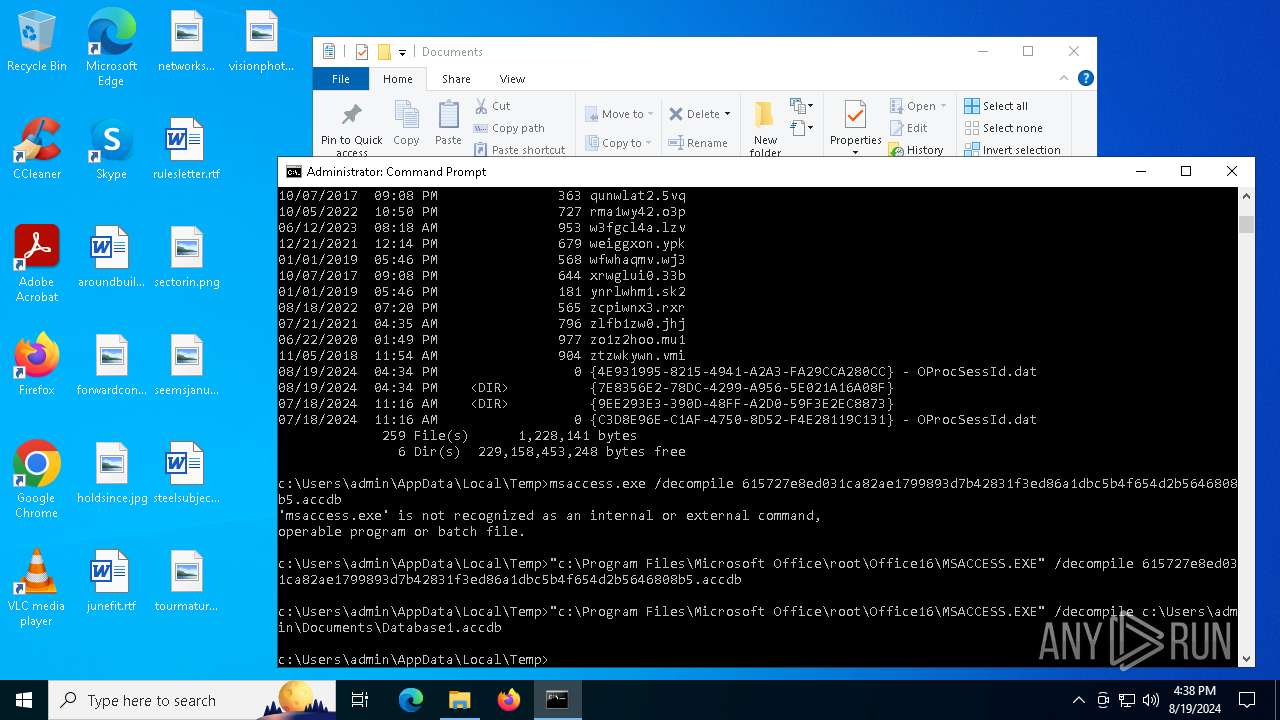
Manual execution by a user
- cmd.exe (PID: 1644)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .accdb | | | Microsoft Access 2007 Database (90.4) |
|---|---|---|
| .pi2 | | | DEGAS med-res bitmap (9.5) |
Total processes
156
Monitored processes
13
Malicious processes
4
Suspicious processes
2
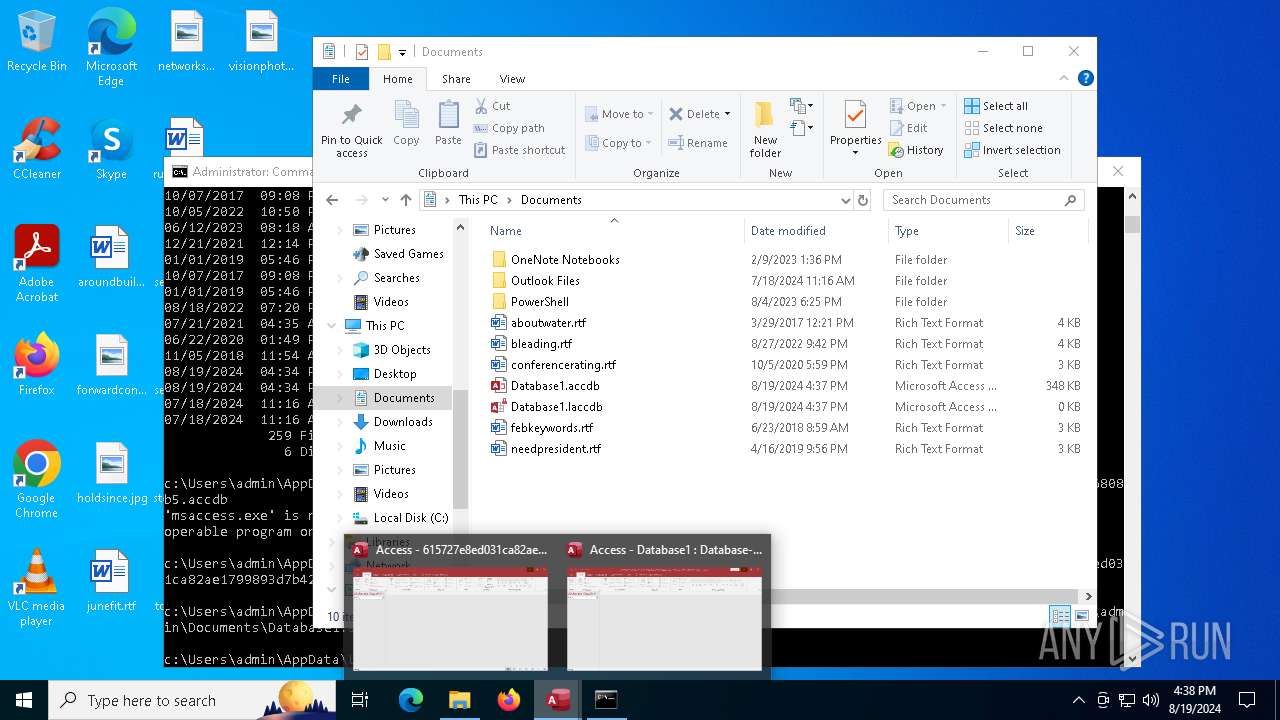
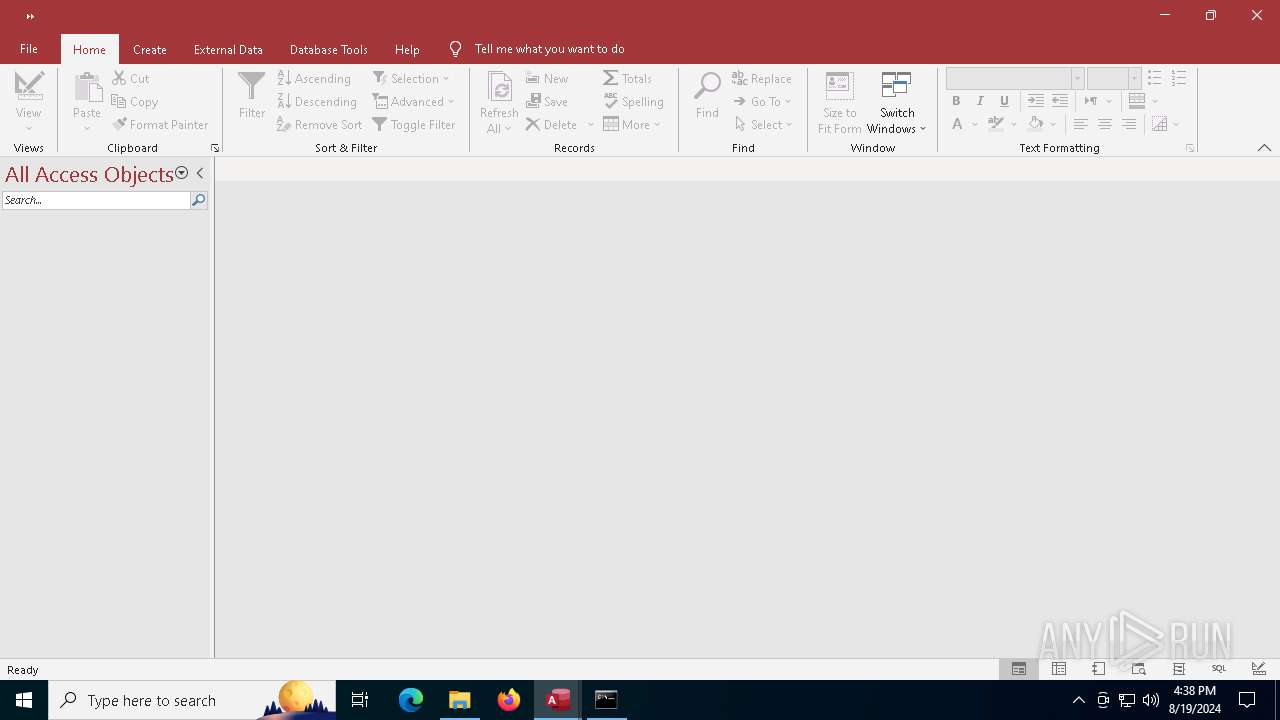
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1644 | "C:\WINDOWS\system32\cmd.exe" | C:\Windows\System32\cmd.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
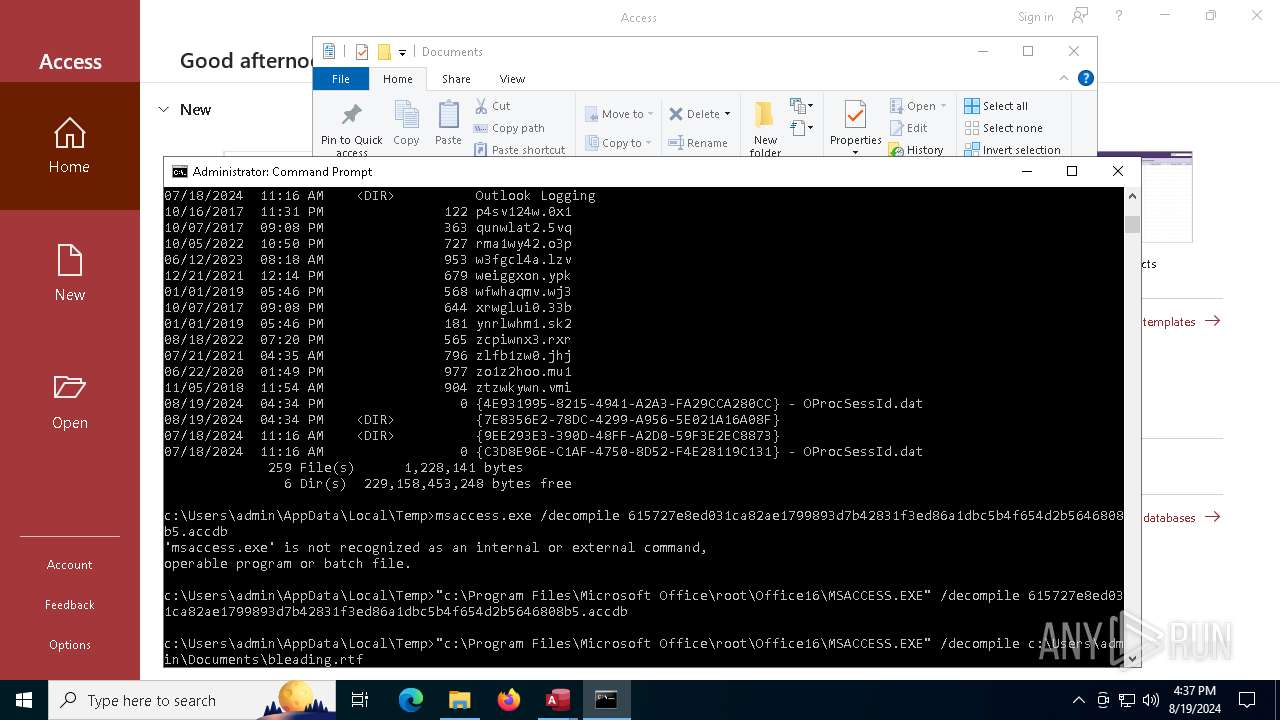
| 1692 | cmd.exe /c " schtasks /create /tn "OneDrive" /tr "cmd" /sc daily /st 09:30 /f && schtasks /create /tn "Skype" /tr "cmd" /sc daily /st 12:00 /f && schtasks /create /tn "WindowsUpdate" /tr "cmd" /sc daily /st 15:00 /f" | C:\Windows\System32\cmd.exe | — | KbUpdate.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
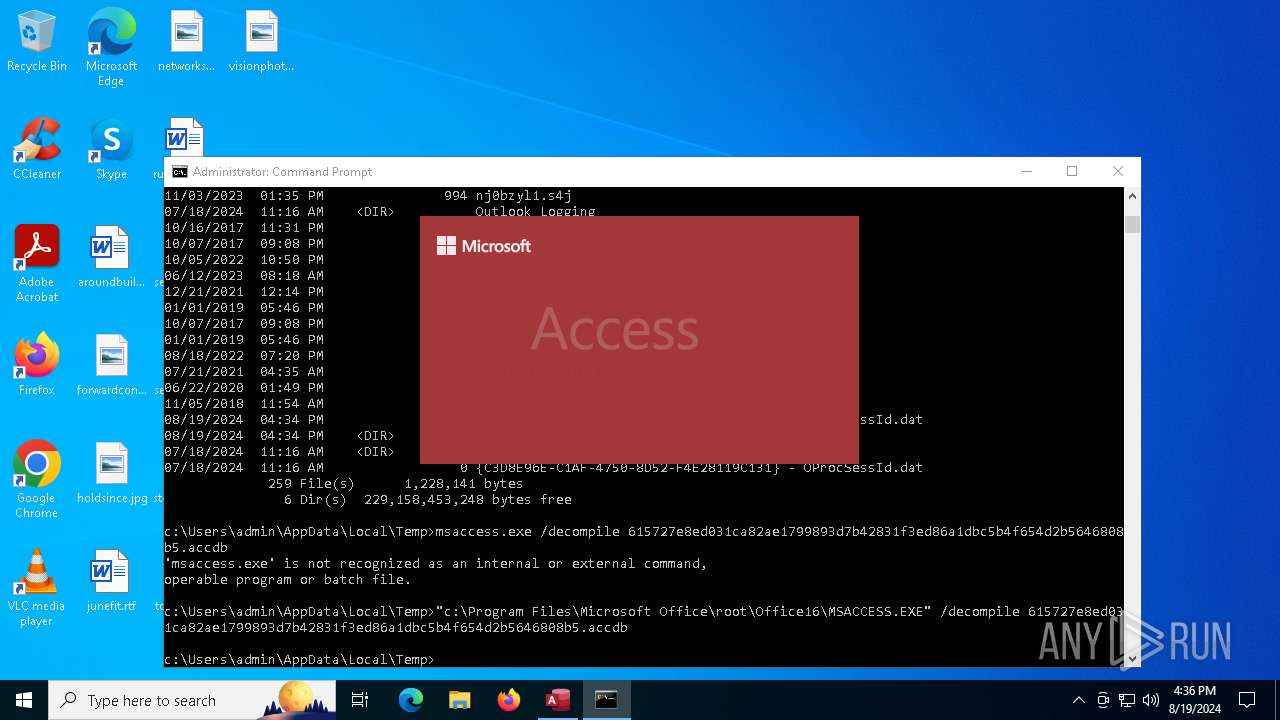
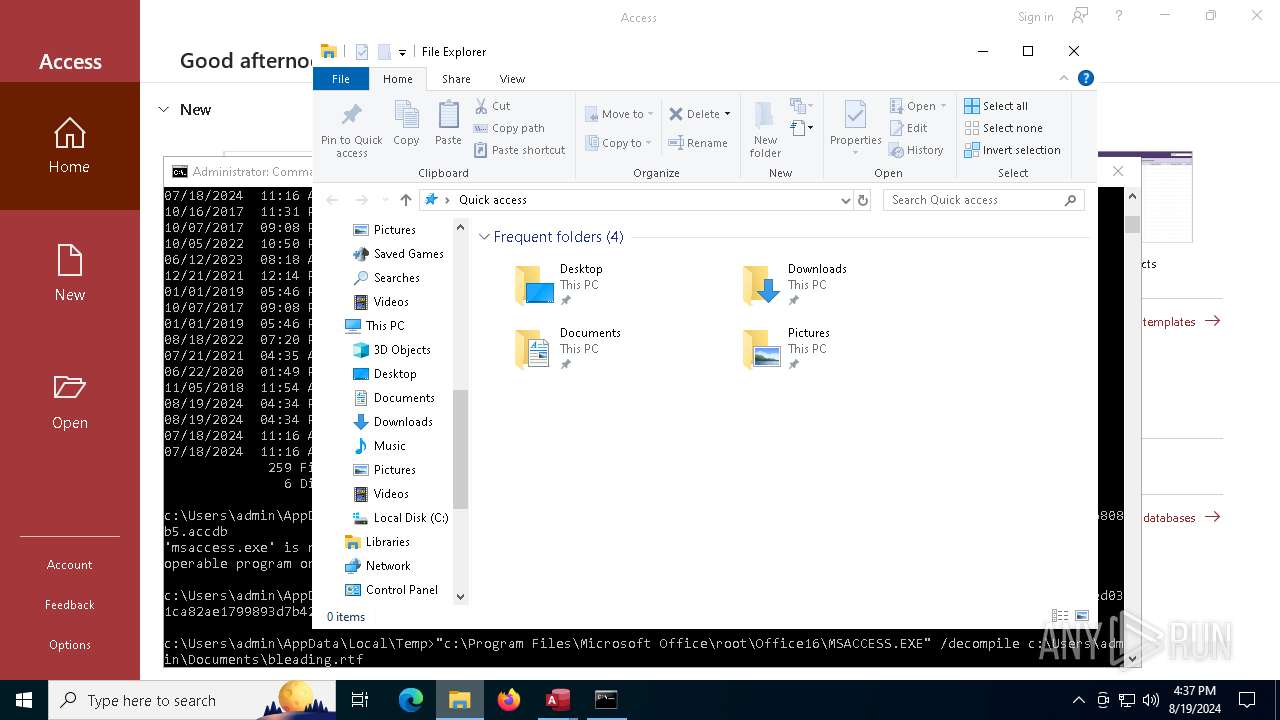
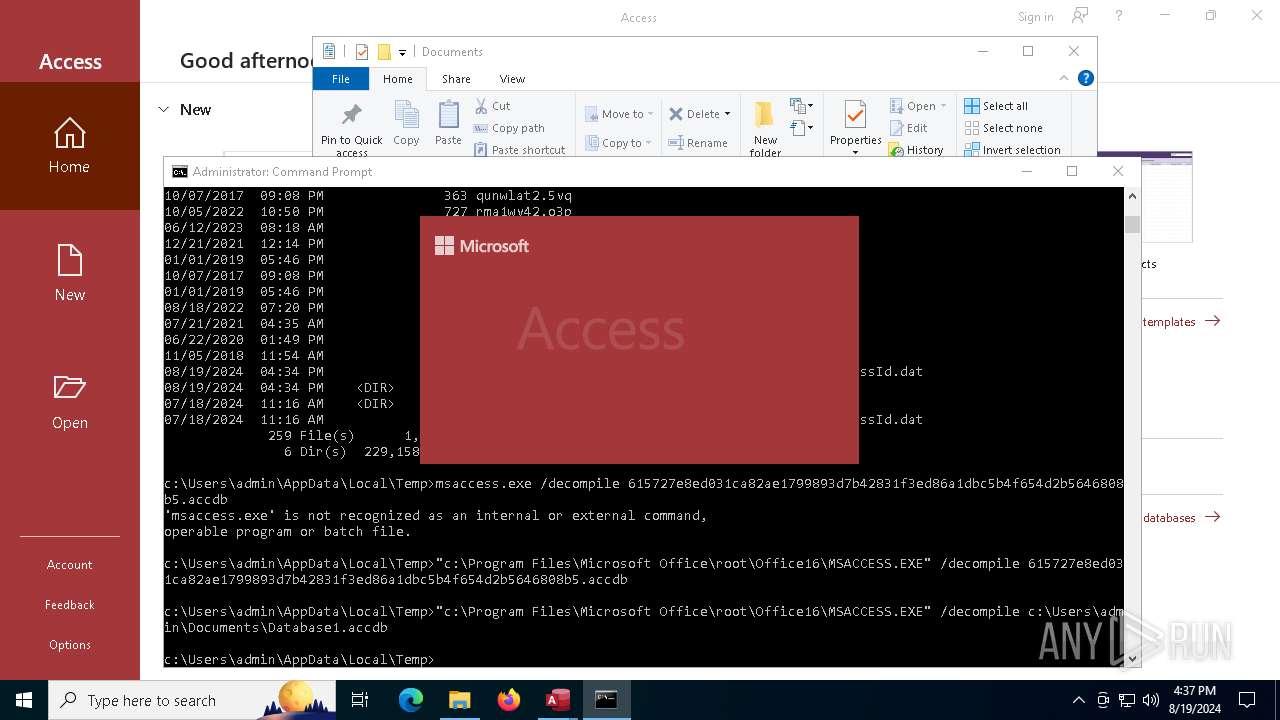
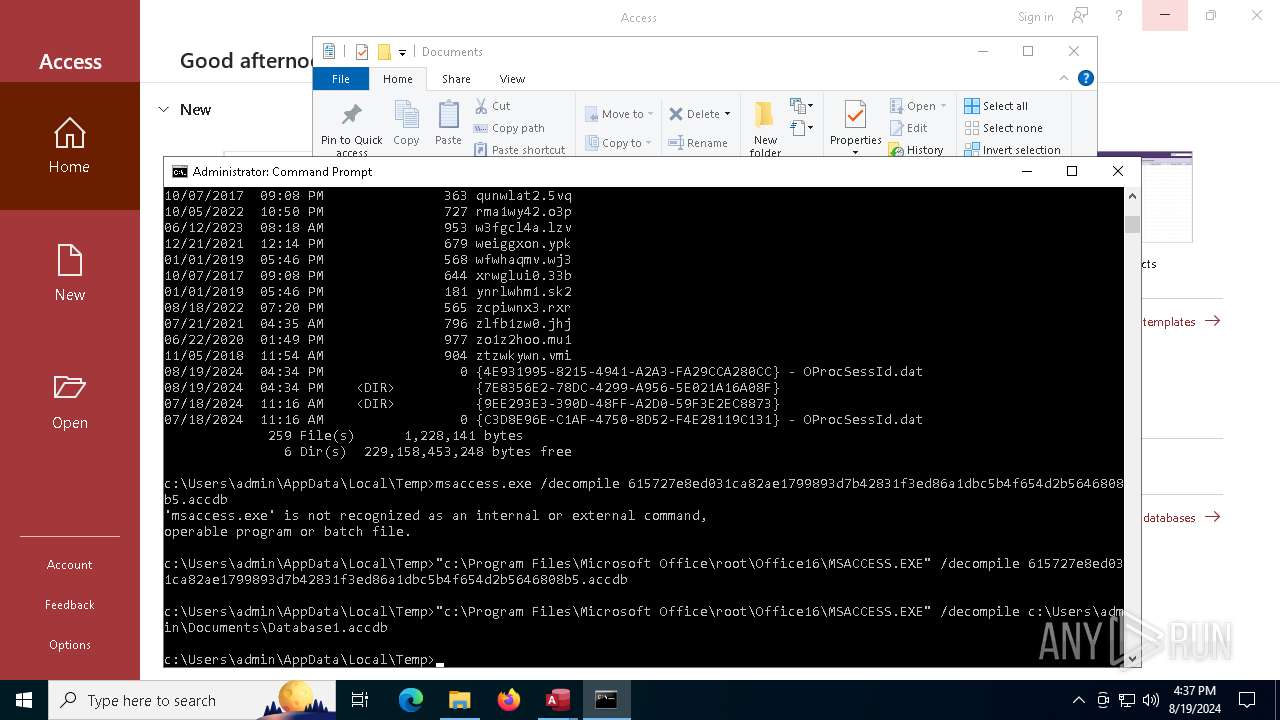
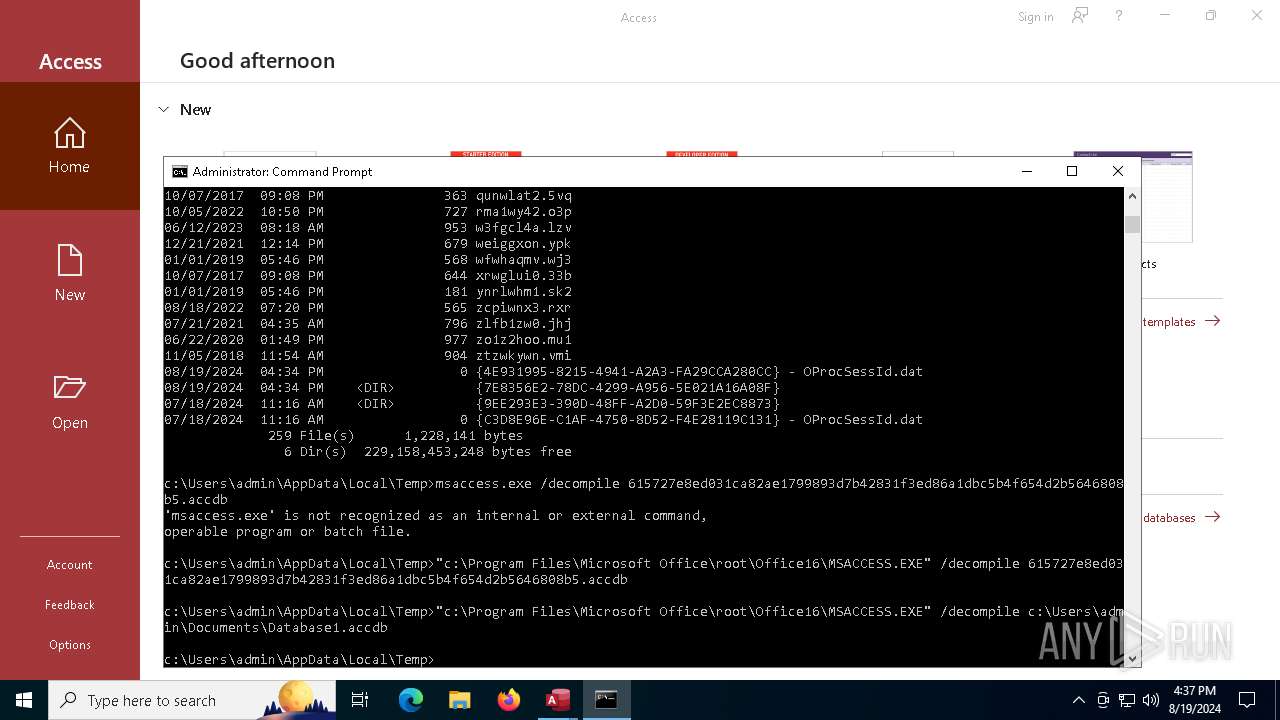
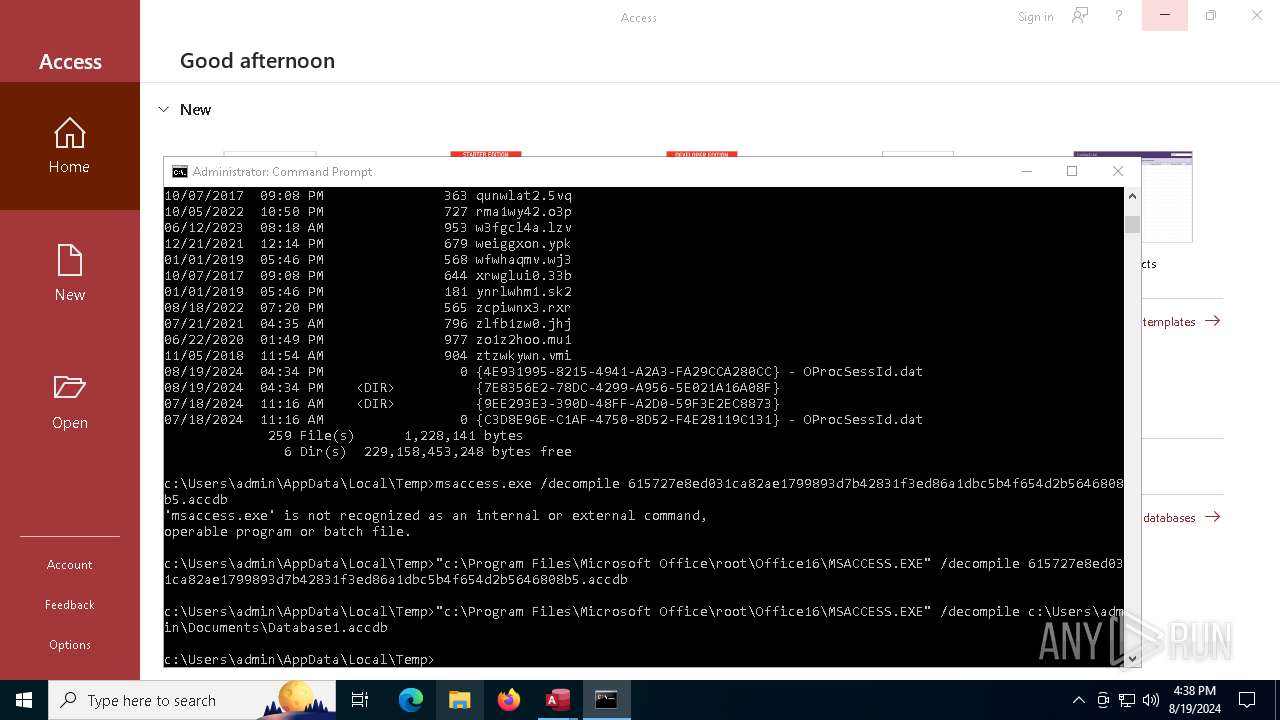
| 2660 | "c:\Program Files\Microsoft Office\root\Office16\MSACCESS.EXE" /decompile 615727e8ed031ca82ae1799893d7b42831f3ed86a1dbc5b4f654d2b5646808b5.accdb | C:\Program Files\Microsoft Office\root\Office16\MSACCESS.EXE | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Access Exit code: 3221225547 Version: 16.0.16026.20146 Modules
| |||||||||||||||
| 3584 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4084 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5180 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6240 | schtasks /create /tn "Skype" /tr "cmd" /sc daily /st 12:00 /f | C:\Windows\System32\schtasks.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Task Scheduler Configuration Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6304 | schtasks /create /tn "WindowsUpdate" /tr "cmd" /sc daily /st 15:00 /f | C:\Windows\System32\schtasks.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Task Scheduler Configuration Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6468 | schtasks /create /tn "OneDrive" /tr "cmd" /sc daily /st 09:30 /f | C:\Windows\System32\schtasks.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Task Scheduler Configuration Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6500 | "C:\Wintows\KbUpdate.exe" | C:\Wintows\KbUpdate.exe | MSACCESS.EXE | ||||||||||||
User: admin Integrity Level: MEDIUM Modules
| |||||||||||||||
Total events
29 788
Read events
29 213
Write events
494
Delete events
81
Modification events
| (PID) Process: | (6576) MSACCESS.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\Common\ClientTelemetry\Sampling |
| Operation: | write | Name: | 2 |
Value: 01600E000000001000B24E9A3E01000000000000000200000000000000 | |||
| (PID) Process: | (6576) MSACCESS.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\Common\CrashPersistence\MSACCESS\6576 |
| Operation: | write | Name: | 0 |
Value: 0B0E109519934E15824149A2A3FA29CCA280CC2300468B94FEBEDACABCED016A04102400449A7D64B29D01008500A907556E6B6E6F776EC9062E223733476255664B62784F56664E70753657616837594A2F4D45484154685631664A6E64643072694C4A67493D22CA0DC2190000C91003783634C511B033D2120C6D0073006100630063006500730073002E00650078006500C51620C517808004C91808323231322D44656300 | |||
| (PID) Process: | (6576) MSACCESS.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | en-US |
Value: 2 | |||
| (PID) Process: | (6576) MSACCESS.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | de-de |
Value: 2 | |||
| (PID) Process: | (6576) MSACCESS.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | fr-fr |
Value: 2 | |||
| (PID) Process: | (6576) MSACCESS.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | es-es |
Value: 2 | |||
| (PID) Process: | (6576) MSACCESS.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | it-it |
Value: 2 | |||
| (PID) Process: | (6576) MSACCESS.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | ja-jp |
Value: 2 | |||
| (PID) Process: | (6576) MSACCESS.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | ko-kr |
Value: 2 | |||
| (PID) Process: | (6576) MSACCESS.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | pt-br |
Value: 2 | |||
Executable files
2
Suspicious files
33
Text files
10
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6576 | MSACCESS.EXE | C:\Users\admin\AppData\Local\Microsoft\TokenBroker\Cache\089d66ba04a8cec4bdc5267f42f39cf84278bb67.tbres | binary | |
MD5:DC84A7E9E209450058795DA629E82F3B | SHA256:542B3B9C743117D7C0DE19E711A522B8DBFC294B26B0DFF38DA7169243CFE3C0 | |||
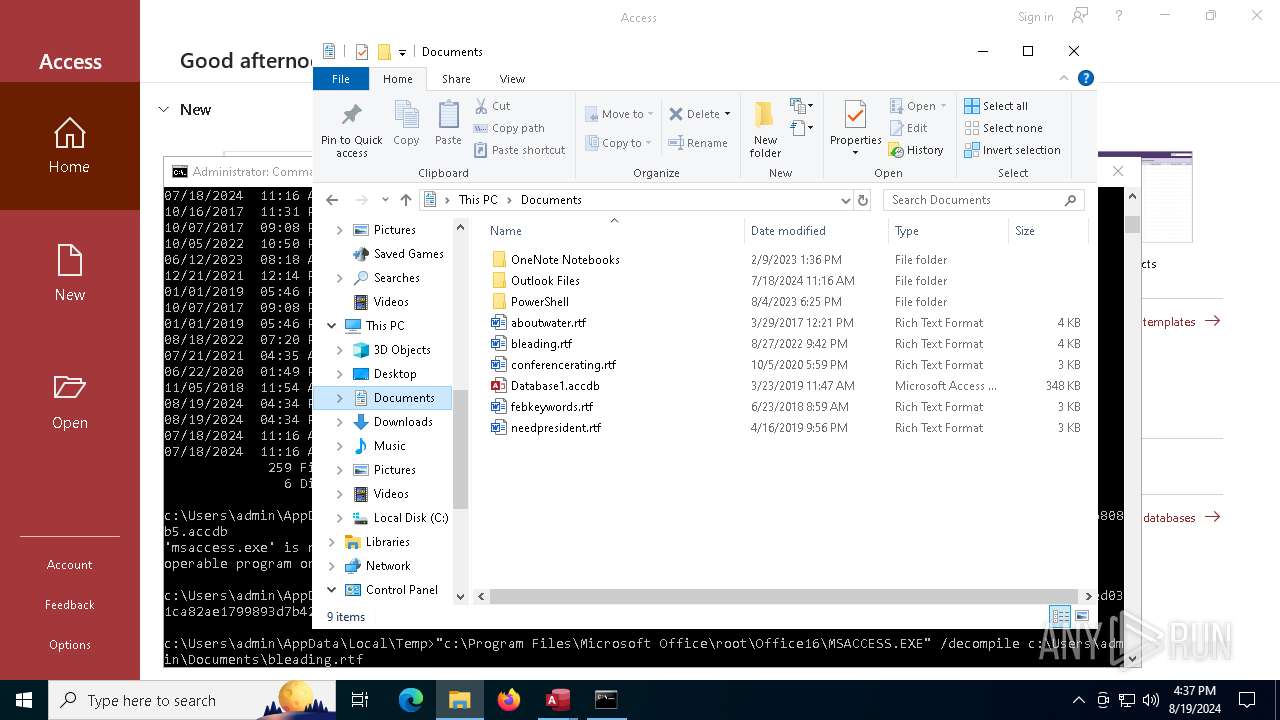
| 6576 | MSACCESS.EXE | C:\Wintows\KbUpdate.exe | executable | |
MD5:12FD9100E372806C878C33F109CEED7C | SHA256:54D3F21009ACDE870817CD42597447786F7C728183FA16966BDEEBB1BC3C87E5 | |||
| 2660 | MSACCESS.EXE | C:\Users\admin\AppData\Local\Microsoft\Office\16.0\WebServiceCache\AllUsers\officeclient.microsoft.com\2E4B7DAE-DB46-490F-AD62-2258C11AFF50 | xml | |
MD5:9C98D19ED8F657527B58C59437981167 | SHA256:0B1D971624E1A9DA2857ACFAD11811D5A85BCE0995DB9A6F2AE34665B808B177 | |||
| 6576 | MSACCESS.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\U6UE918QCBT5XBE3U276.temp | binary | |
MD5:E4A1661C2C886EBB688DEC494532431C | SHA256:B76875C50EF704DBBF7F02C982445971D1BBD61AEBE2E4B28DDC58A1D66317D5 | |||
| 6576 | MSACCESS.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\319f01bf9fe00f2d.customDestinations-ms | binary | |
MD5:E4A1661C2C886EBB688DEC494532431C | SHA256:B76875C50EF704DBBF7F02C982445971D1BBD61AEBE2E4B28DDC58A1D66317D5 | |||
| 2660 | MSACCESS.EXE | C:\Users\admin\AppData\Local\Microsoft\Office\16.0\DTS\en-US{A3DDA2AD-16B9-492C-9620-4D1DE8704226}\{64D16153-6DBE-4C66-A26A-B91F9E1B4DFF}mt01225343.png | image | |
MD5:28D825FED592B6B24FD4A632F4AC24F5 | SHA256:895688D88A7B3F5B7372D07584AD0DE540D9032EF13942A417D909EEE9471007 | |||
| 2660 | MSACCESS.EXE | C:\Users\admin\AppData\Local\Microsoft\Office\16.0\DTS\en-US{A3DDA2AD-16B9-492C-9620-4D1DE8704226}\{2FCB17B5-E7B1-4DC8-8252-941B43243B8F}mt01225342.png | image | |
MD5:D4E07E723C3A2F2EAF3AD5CAAD7BDC44 | SHA256:6A0BCF1FCBCF6945713B7934A7DA6BFA3A10F66E38D00DE97EFE47D31A37BA61 | |||
| 6576 | MSACCESS.EXE | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\E2C6CBAF0AF08CF203BA74BF0D0AB6D5_0FB9553B978E7F00C6B2309507DEB64A | binary | |
MD5:FD4080F99017434287E57484DC95A77E | SHA256:E4C3D4383B1E0D9198119E204C3AE4BBFE04400EE457A6CD85A8FDBE110EAA43 | |||
| 2660 | MSACCESS.EXE | C:\Users\admin\AppData\Local\Microsoft\Office\OTele\msaccess.exe.db-wal | binary | |
MD5:835E8652B8BB59F7EDA4E65A8F64CBD2 | SHA256:CDDA69A5D4A618FD605F4232D6576E8EB0ADDBA54BC2A4C49F6C116DD7BA8D90 | |||
| 2660 | MSACCESS.EXE | C:\Users\admin\AppData\Local\Microsoft\Office\16.0\DTS\en-US{A3DDA2AD-16B9-492C-9620-4D1DE8704226}\{7A08BBCC-E932-40A6-A5C9-8E63CA26D50B}mt01225345.png | image | |
MD5:EC74A94632262E9A0CFECE0DA4B885E1 | SHA256:5A520C5C7DC6E0A711AB9682FD0AEACF4C61F1BD1049DA001D9825A9CC0EE702 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
121
DNS requests
32
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4672 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
4672 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6576 | MSACCESS.EXE | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
6320 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
7044 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
5336 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEApDqVCbATUviZV57HIIulA%3D | unknown | — | — | whitelisted |
5336 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
5336 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2120 | MoUsoCoreWorker.exe | 51.104.136.2:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3180 | RUXIMICS.exe | 51.104.136.2:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4876 | svchost.exe | 51.104.136.2:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6576 | MSACCESS.EXE | 52.113.194.132:443 | ecs.office.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
4876 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
3260 | svchost.exe | 40.113.110.67:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4672 | svchost.exe | 40.126.32.68:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | unknown |
4672 | svchost.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
6500 | KbUpdate.exe | 185.227.82.65:8080 | — | Access2.IT Group B.V. | NL | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
ecs.office.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |
arc.msn.com |
| whitelisted |
www.bing.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |