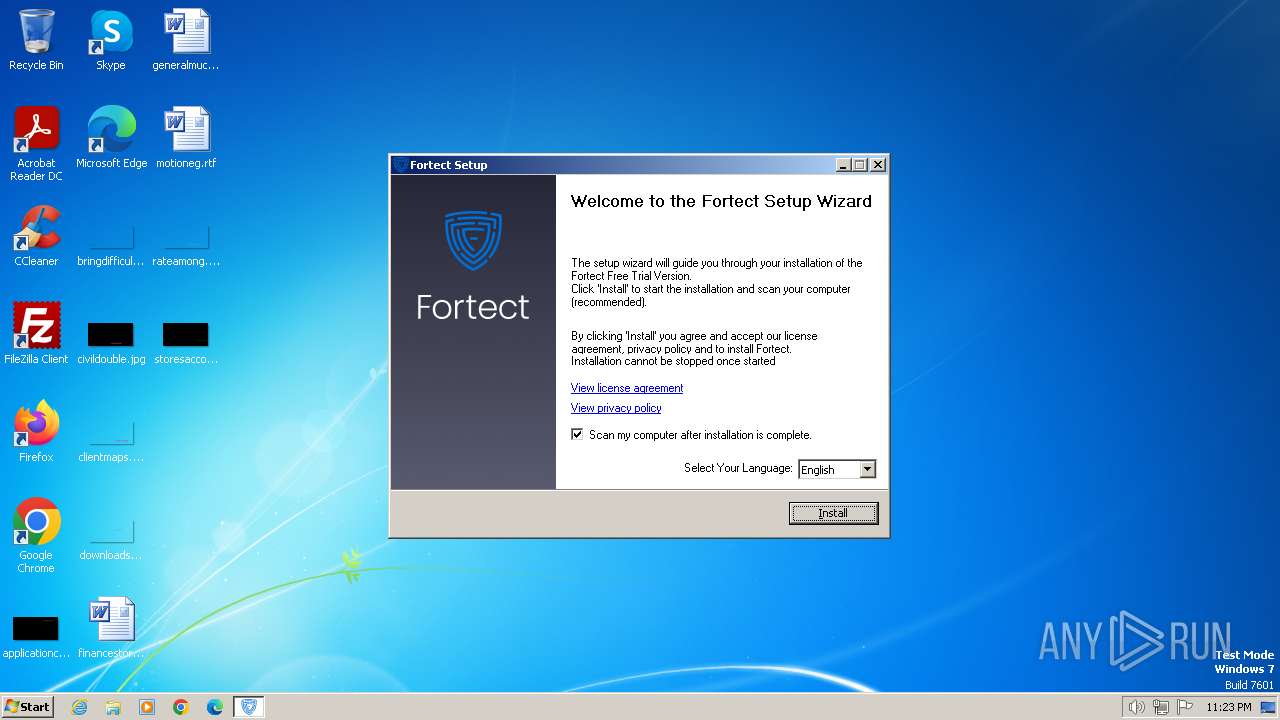
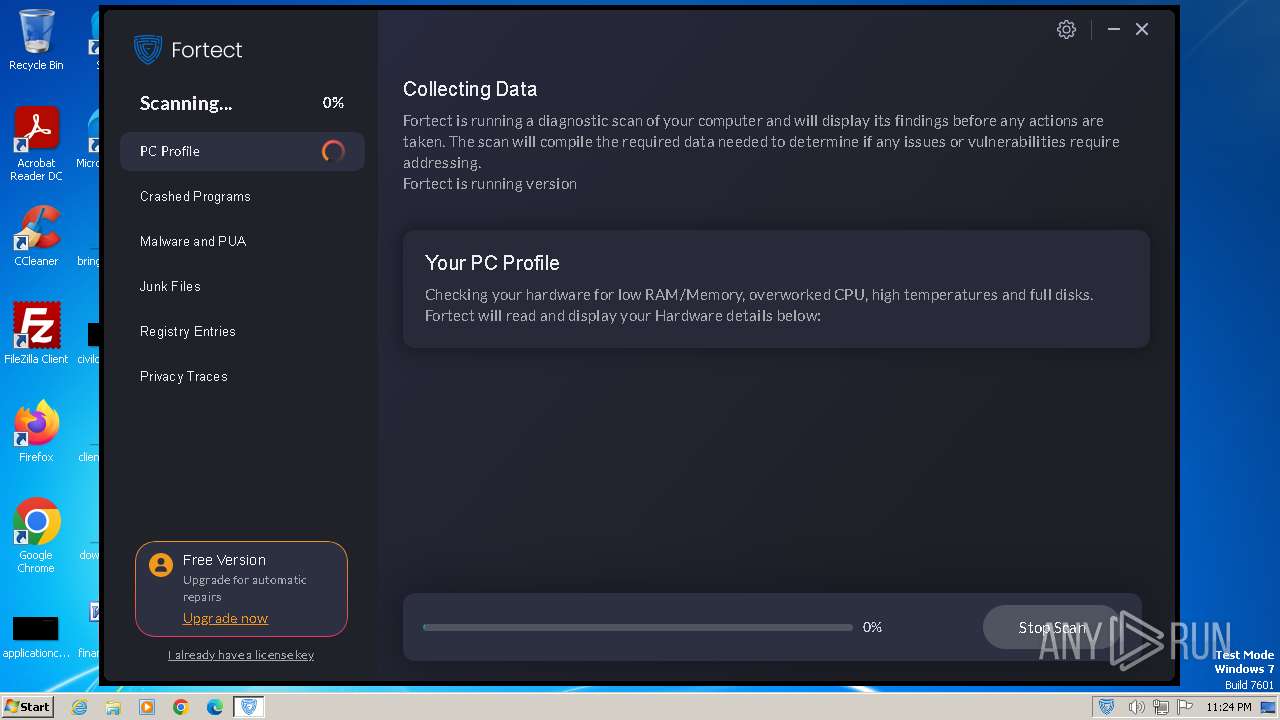
| File name: | Fortect.exe |
| Full analysis: | https://app.any.run/tasks/d991e9f7-8569-438a-82e4-976d92be3bb0 |
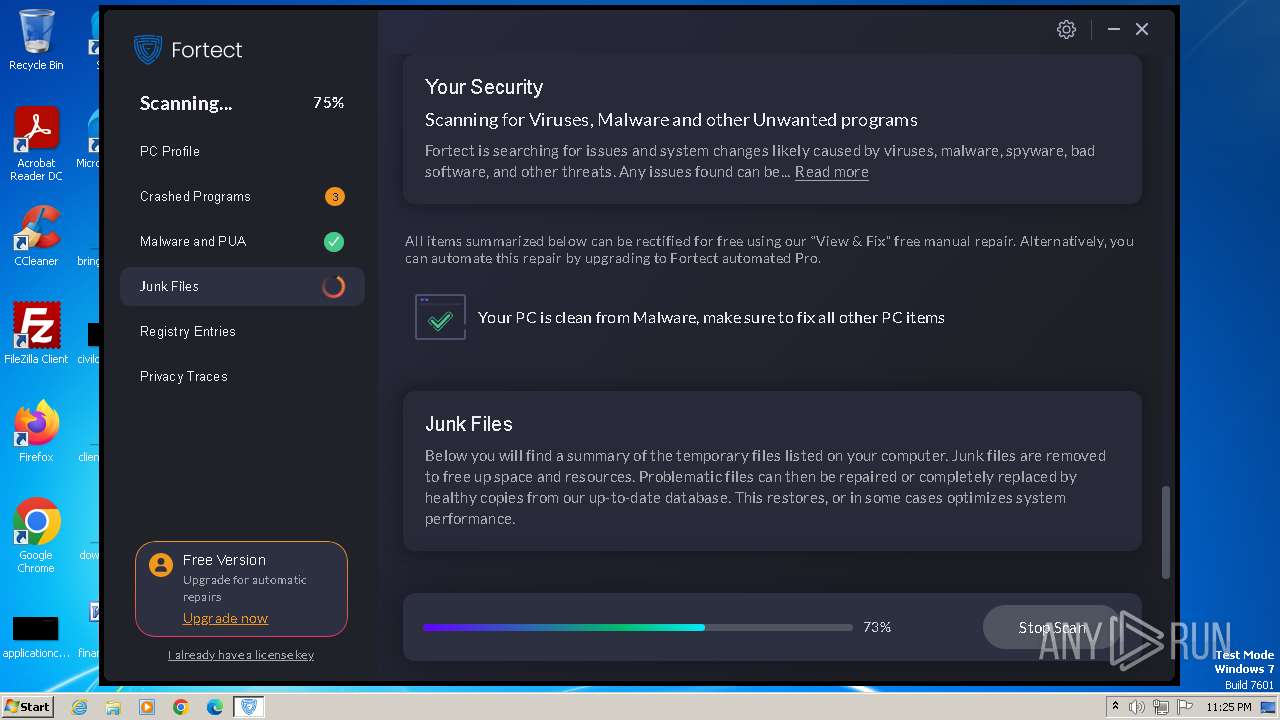
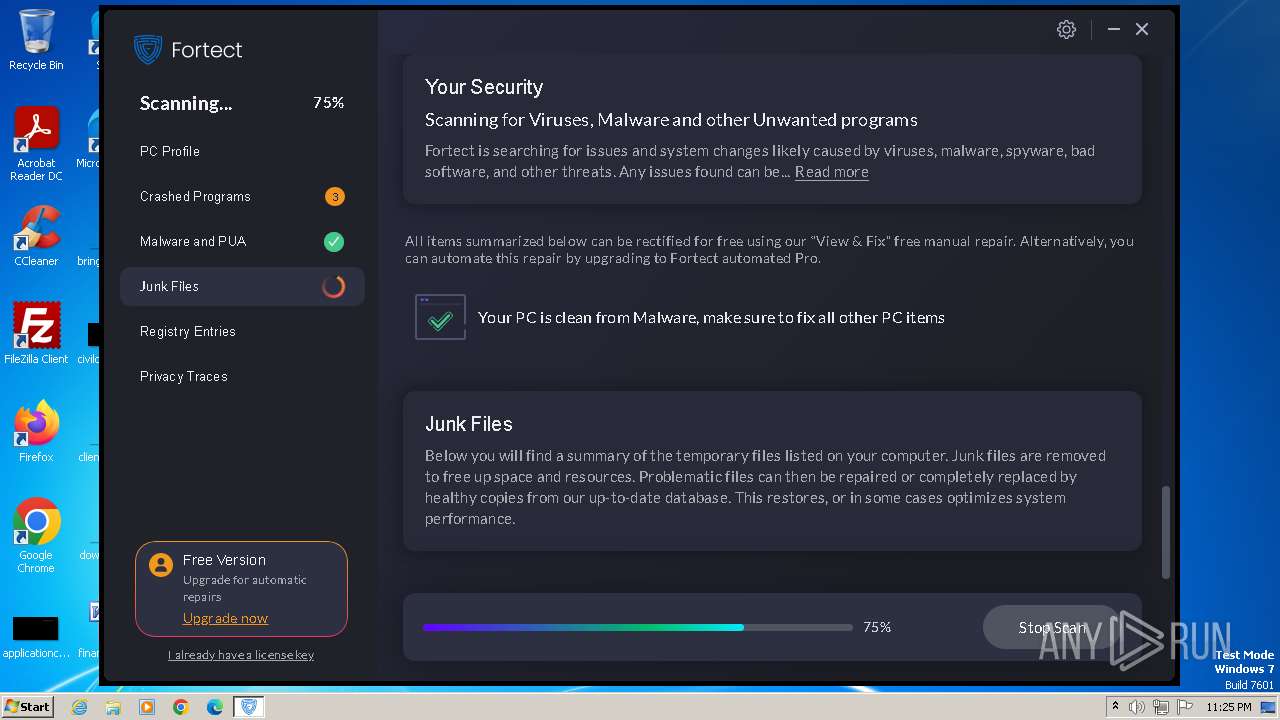
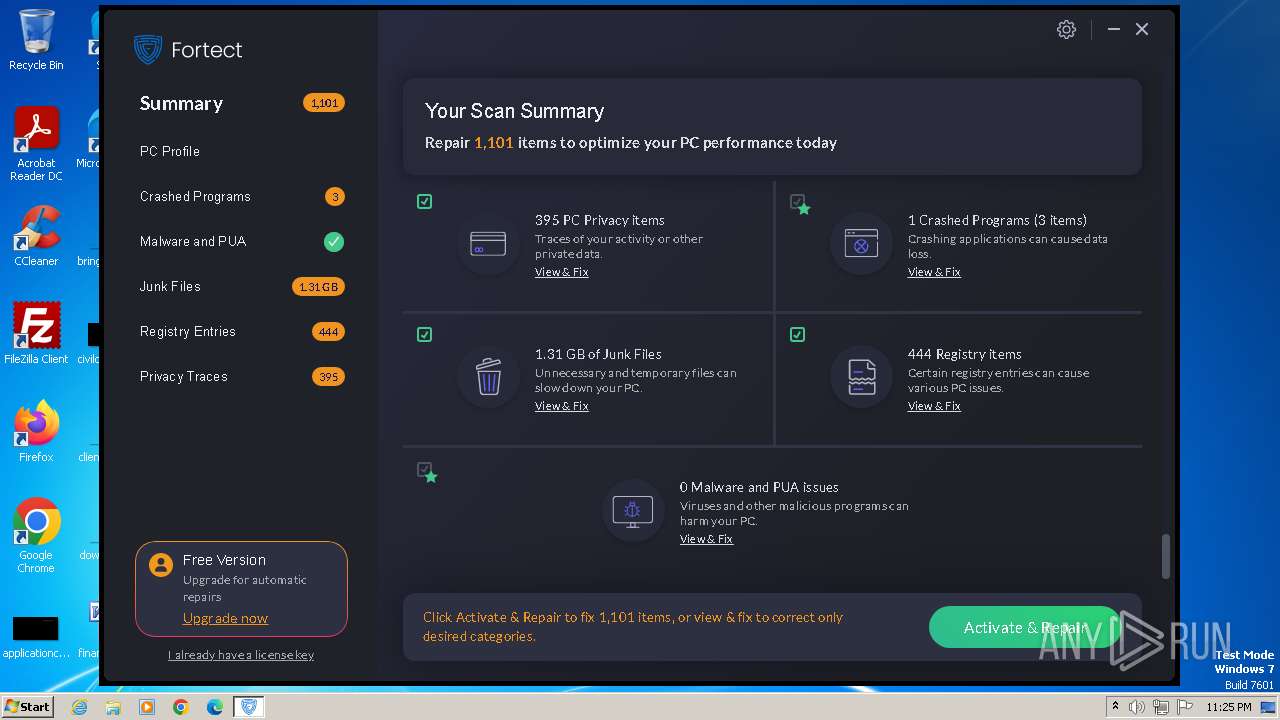
| Verdict: | Malicious activity |
| Analysis date: | December 24, 2023, 23:22:58 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | E51A16EB29252251A898DB99AEE47203 |
| SHA1: | 1873BE57C59A1AF587E816CA775A564CC6C154B8 |
| SHA256: | 6150AA3D9B1D62C79EF7D94981A08AD2A19F4F0F84671900AF89578E02C38169 |
| SSDEEP: | 12288:jJ8J/xydJrKvt9duEbPjfABcQuKx4gH7Hbbyi6iDyGO4:jJ8RruEbPbWcjKx4gH7HbbyiLDyGO4 |
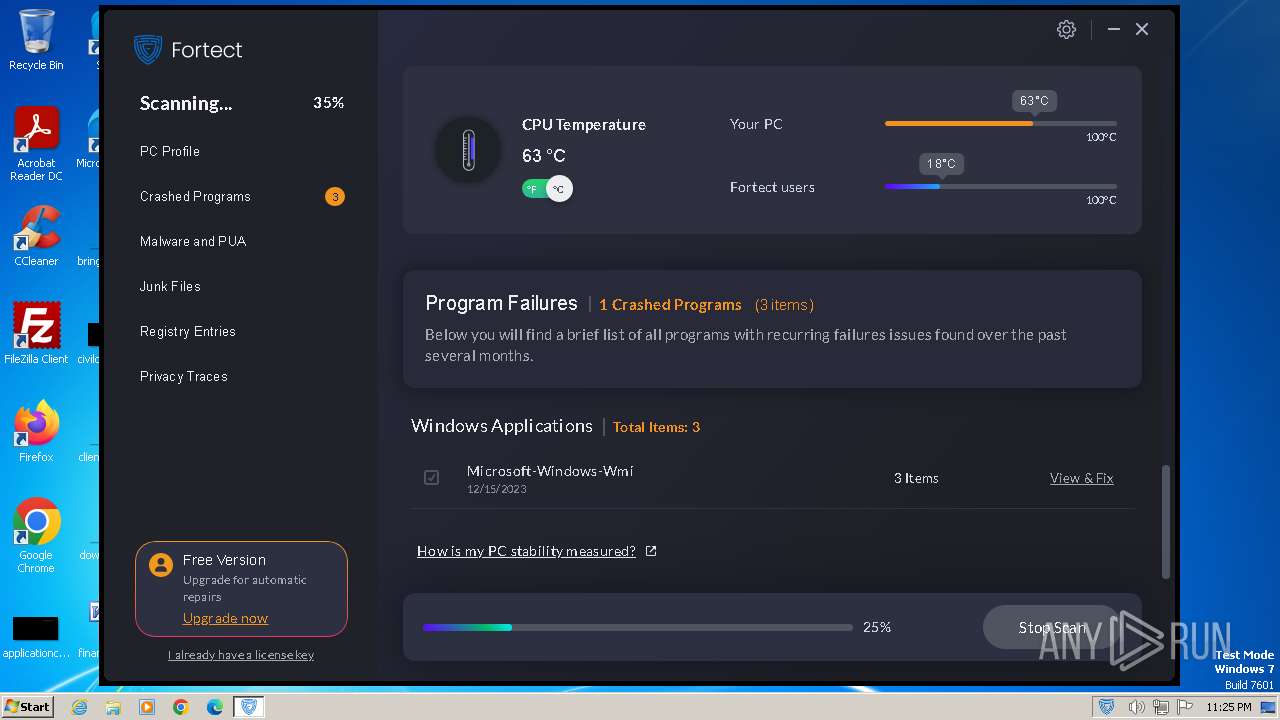
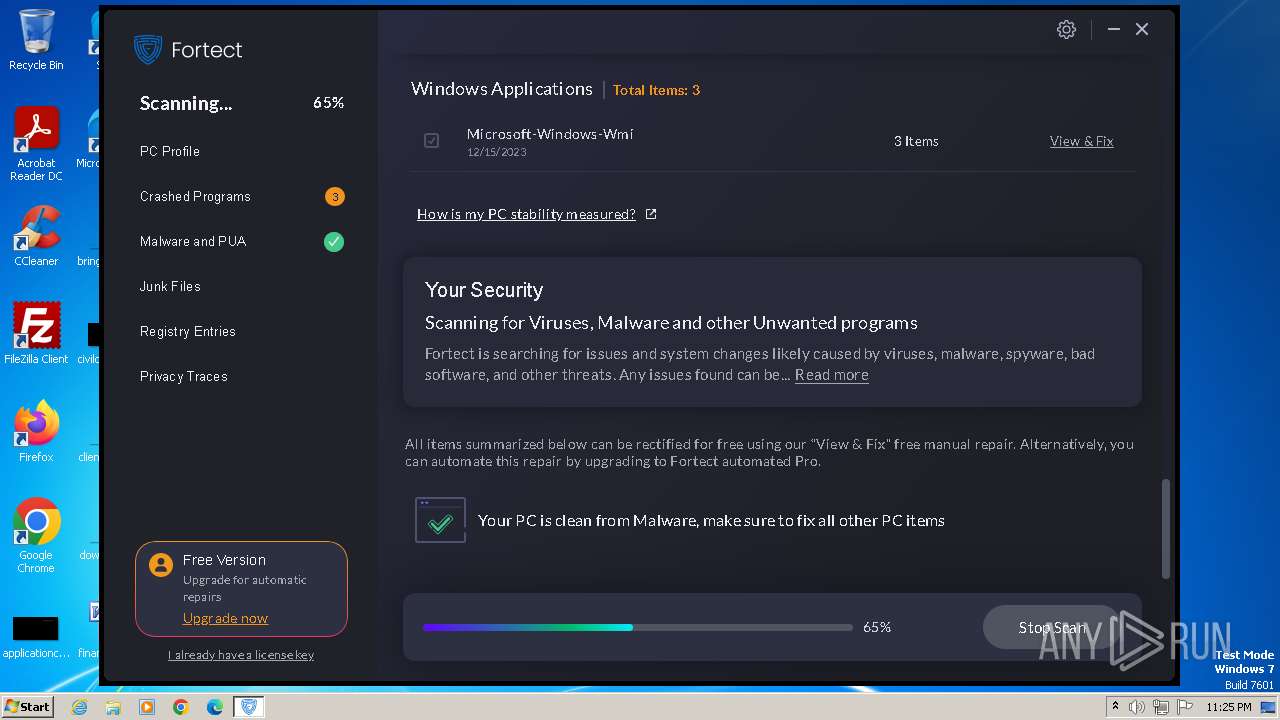
MALICIOUS
Actions looks like stealing of personal data
- MainService.exe (PID: 2536)
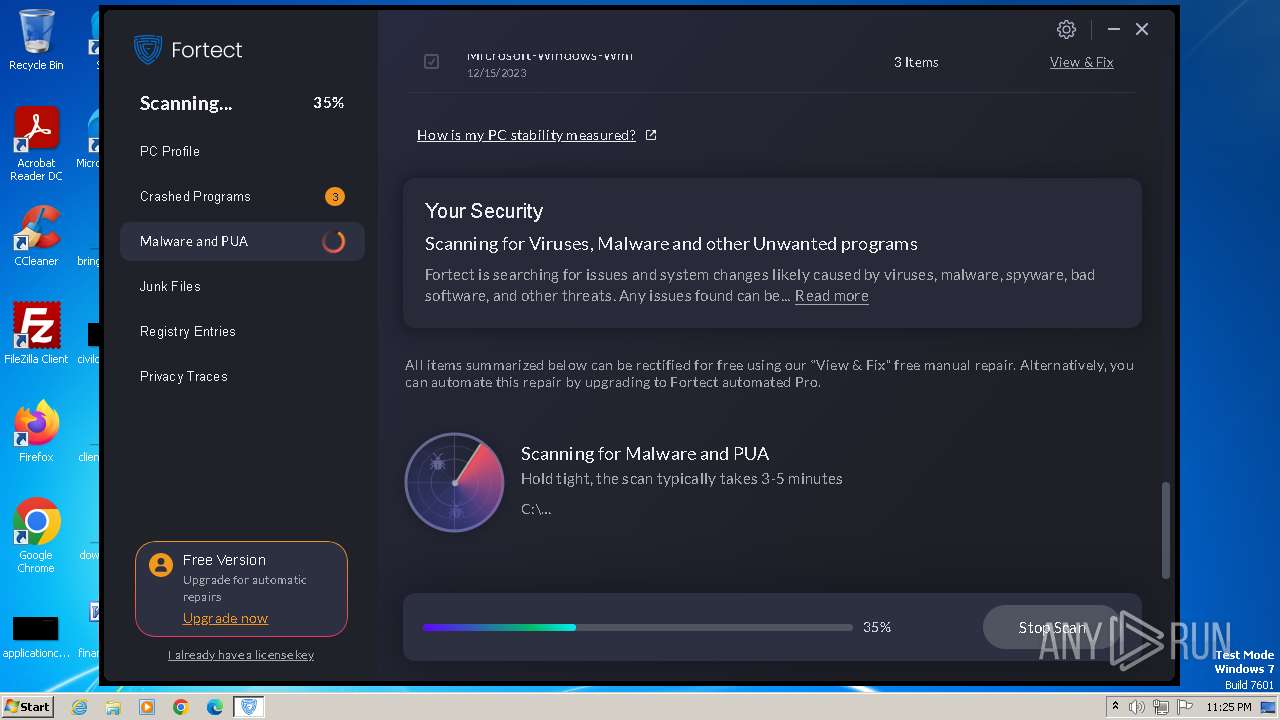
SUSPICIOUS
The process creates files with name similar to system file names
- Fortect.exe (PID: 2064)
Reads the Internet Settings
- WMIC.exe (PID: 548)
- WMIC.exe (PID: 1840)
- WMIC.exe (PID: 1832)
- WMIC.exe (PID: 1544)
- Fortect.exe (PID: 2064)
- FortectMain.exe (PID: 900)
Starts CMD.EXE for commands execution
- Fortect.exe (PID: 2064)
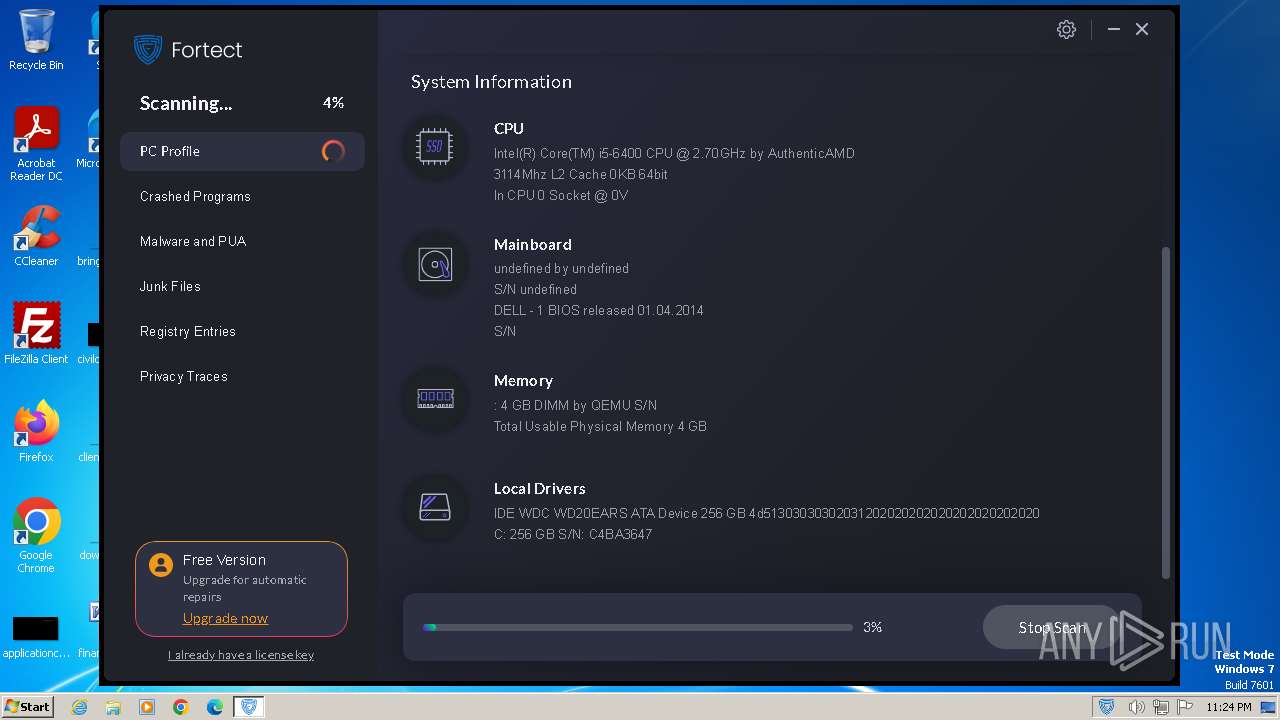
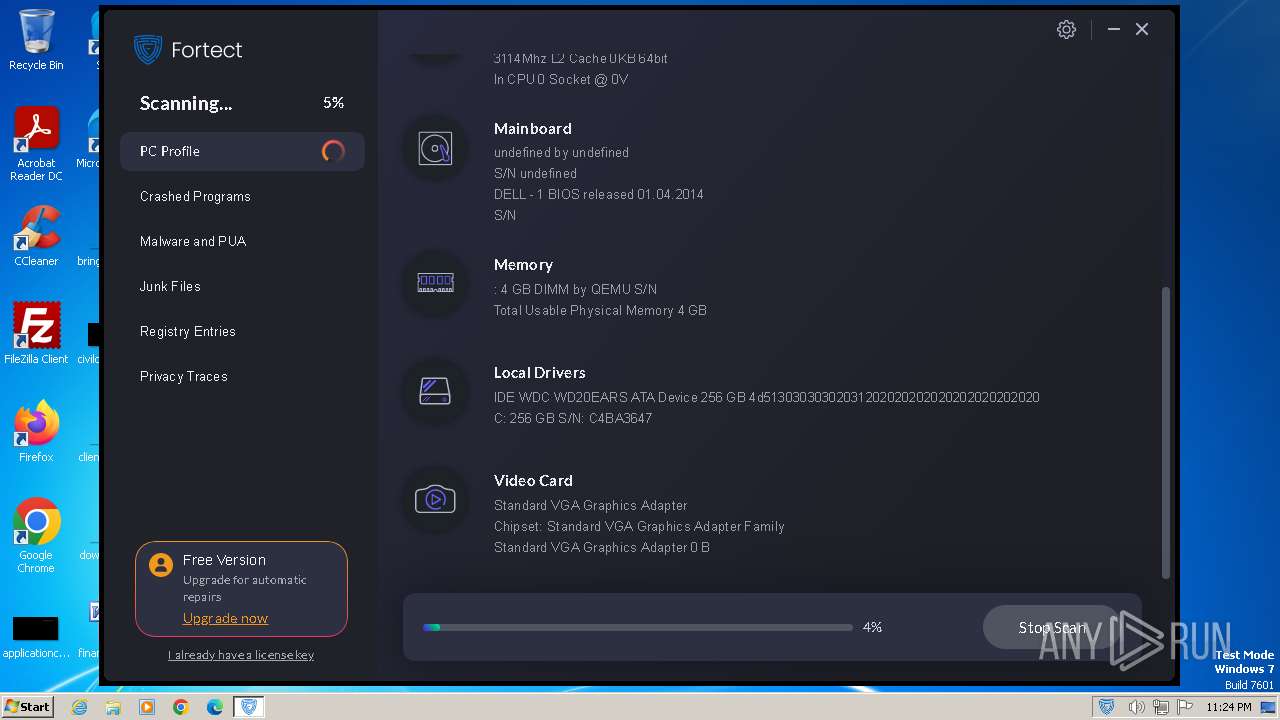
Uses WMIC.EXE to obtain BIOS management information
- cmd.exe (PID: 2024)
Accesses computer name via WMI (SCRIPT)
- WMIC.exe (PID: 1840)
Uses WMIC.EXE to obtain physical disk drive information
- Fortect.exe (PID: 2064)
Uses WMIC.EXE to obtain data on the partitioned areas of a physical disk
- Fortect.exe (PID: 2064)
Uses WMIC.EXE to obtain Windows Installer data
- cmd.exe (PID: 1928)
Accesses product unique identifier via WMI (SCRIPT)
- WMIC.exe (PID: 1544)
Checks Windows Trust Settings
- Fortect.exe (PID: 2064)
- MainDaemon.exe (PID: 2052)
- MainService.exe (PID: 2536)
Reads settings of System Certificates
- Fortect.exe (PID: 2064)
- MainDaemon.exe (PID: 2052)
- FortectMain.exe (PID: 900)
Reads security settings of Internet Explorer
- Fortect.exe (PID: 2064)
- MainDaemon.exe (PID: 2052)
Searches for installed software
- MainDaemon.exe (PID: 2320)
- MainService.exe (PID: 2536)
Reads Microsoft Outlook installation path
- MainService.exe (PID: 2536)
Reads Internet Explorer settings
- MainService.exe (PID: 2536)
Adds/modifies Windows certificates
- MainService.exe (PID: 2536)
INFO
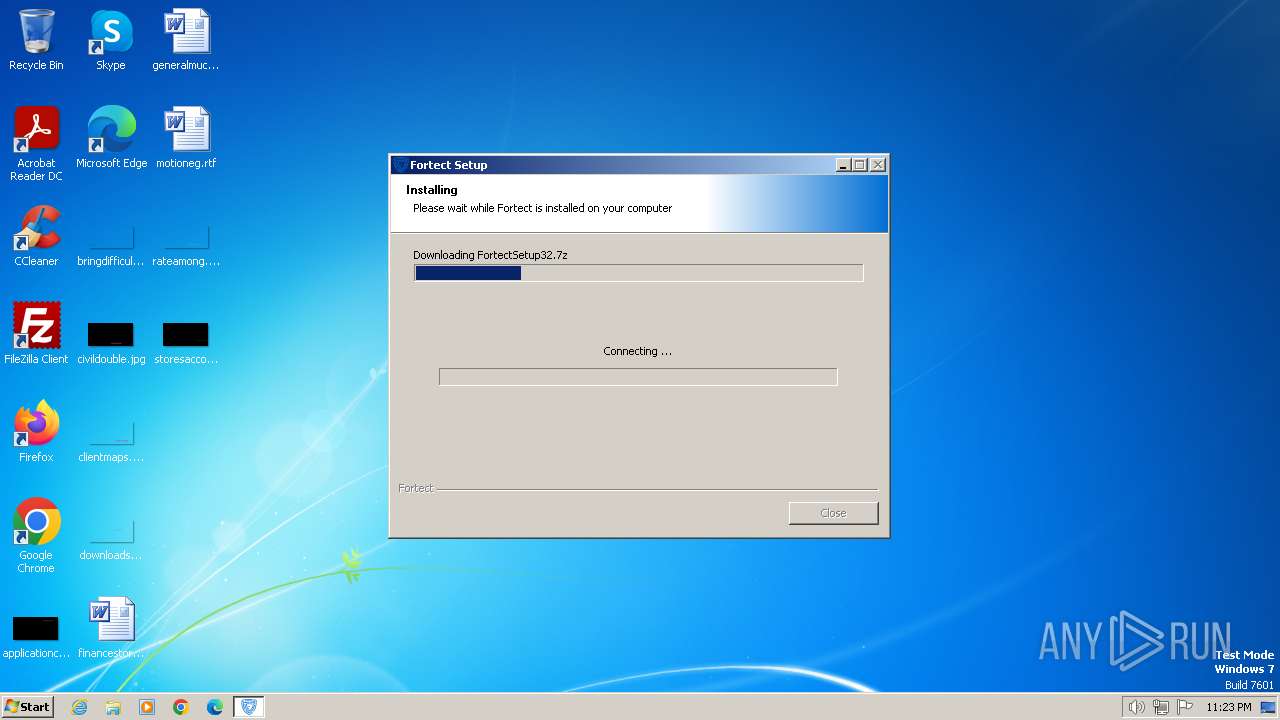
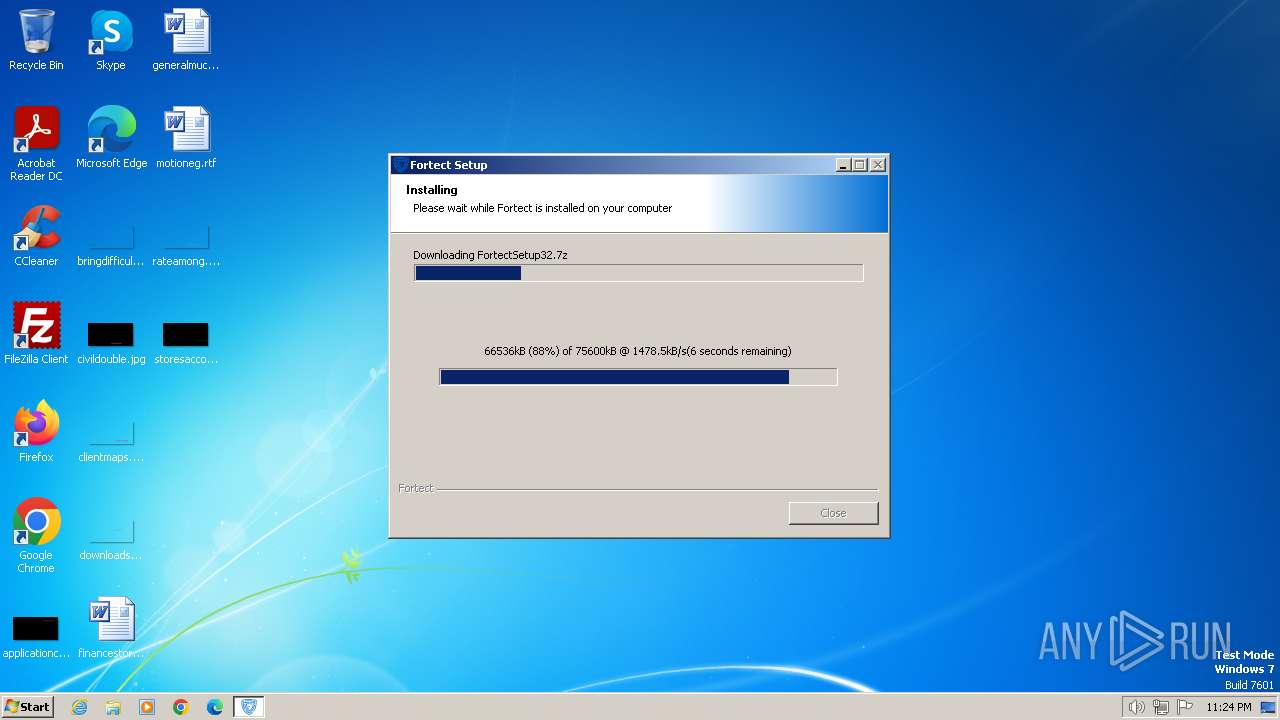
Drops the executable file immediately after the start
- Fortect.exe (PID: 2064)
- FortectMain.exe (PID: 900)
Checks supported languages
- Fortect.exe (PID: 2064)
- MainDaemon.exe (PID: 2052)
- MainService.exe (PID: 2816)
- MainService.exe (PID: 2536)
- FortectTray.exe (PID: 2516)
- MainDaemon.exe (PID: 2320)
- FortectMain.exe (PID: 2664)
- FortectMain.exe (PID: 3032)
- FortectMain.exe (PID: 900)
- FortectMain.exe (PID: 3356)
- FortectMain.exe (PID: 3092)
Reads the computer name
- Fortect.exe (PID: 2064)
- MainDaemon.exe (PID: 2052)
- MainService.exe (PID: 2816)
- MainService.exe (PID: 2536)
- MainDaemon.exe (PID: 2320)
- FortectMain.exe (PID: 3092)
- FortectMain.exe (PID: 3032)
- FortectMain.exe (PID: 900)
- FortectMain.exe (PID: 3356)
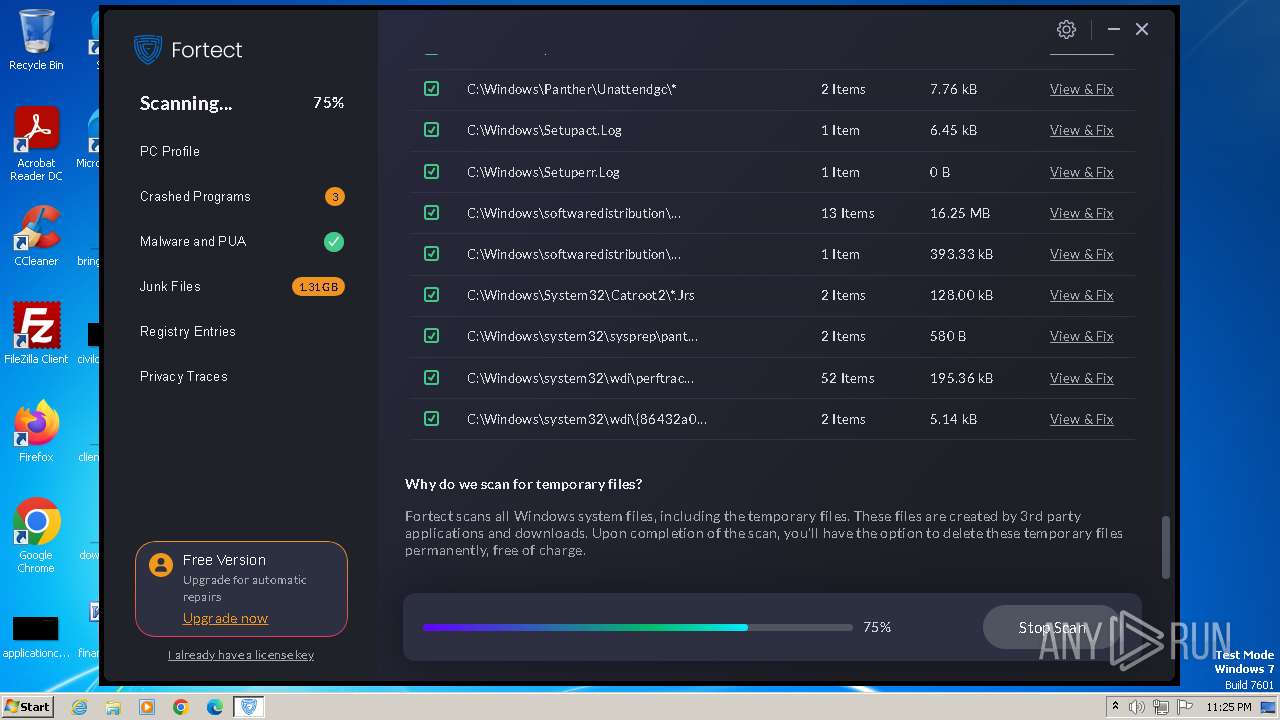
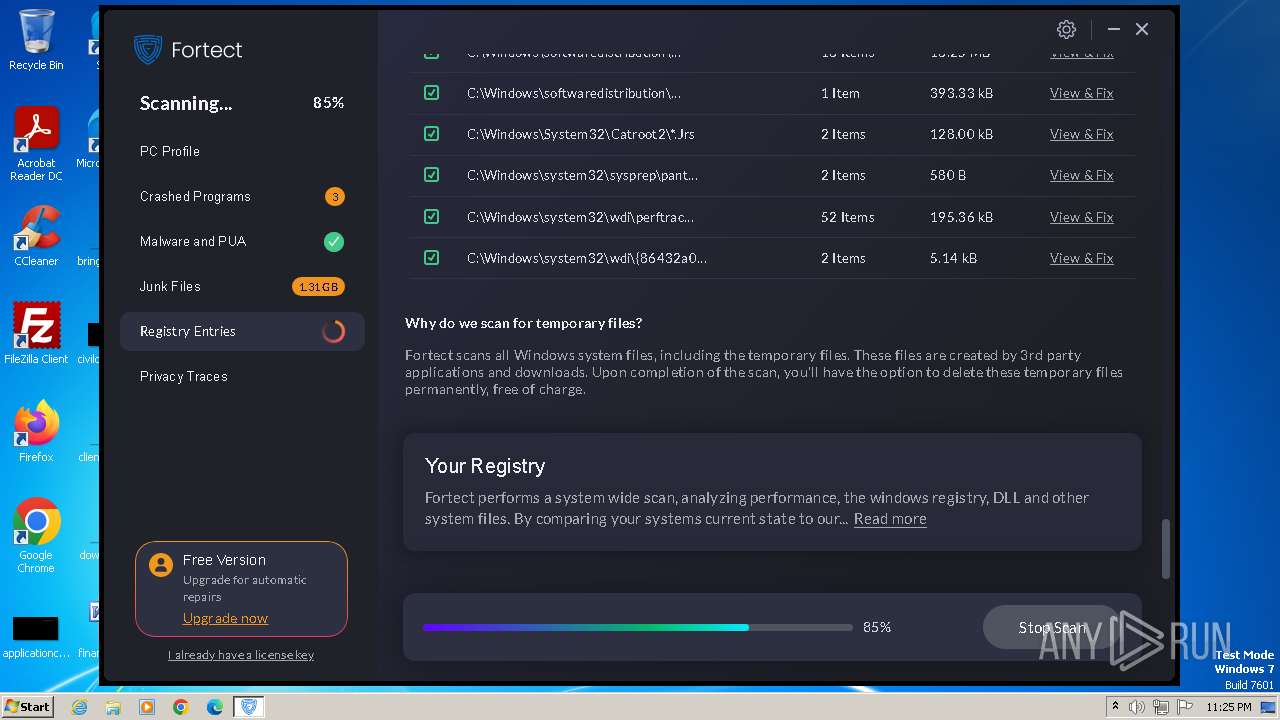
Create files in a temporary directory
- Fortect.exe (PID: 2064)
- FortectMain.exe (PID: 900)
Reads Environment values
- Fortect.exe (PID: 2064)
- MainDaemon.exe (PID: 2052)
- MainService.exe (PID: 2816)
- MainService.exe (PID: 2536)
- MainDaemon.exe (PID: 2320)
- FortectMain.exe (PID: 900)
Reads the machine GUID from the registry
- Fortect.exe (PID: 2064)
- MainDaemon.exe (PID: 2052)
- MainDaemon.exe (PID: 2320)
- MainService.exe (PID: 2536)
- FortectMain.exe (PID: 900)
Checks proxy server information
- Fortect.exe (PID: 2064)
Dropped object may contain TOR URL's
- Fortect.exe (PID: 2064)
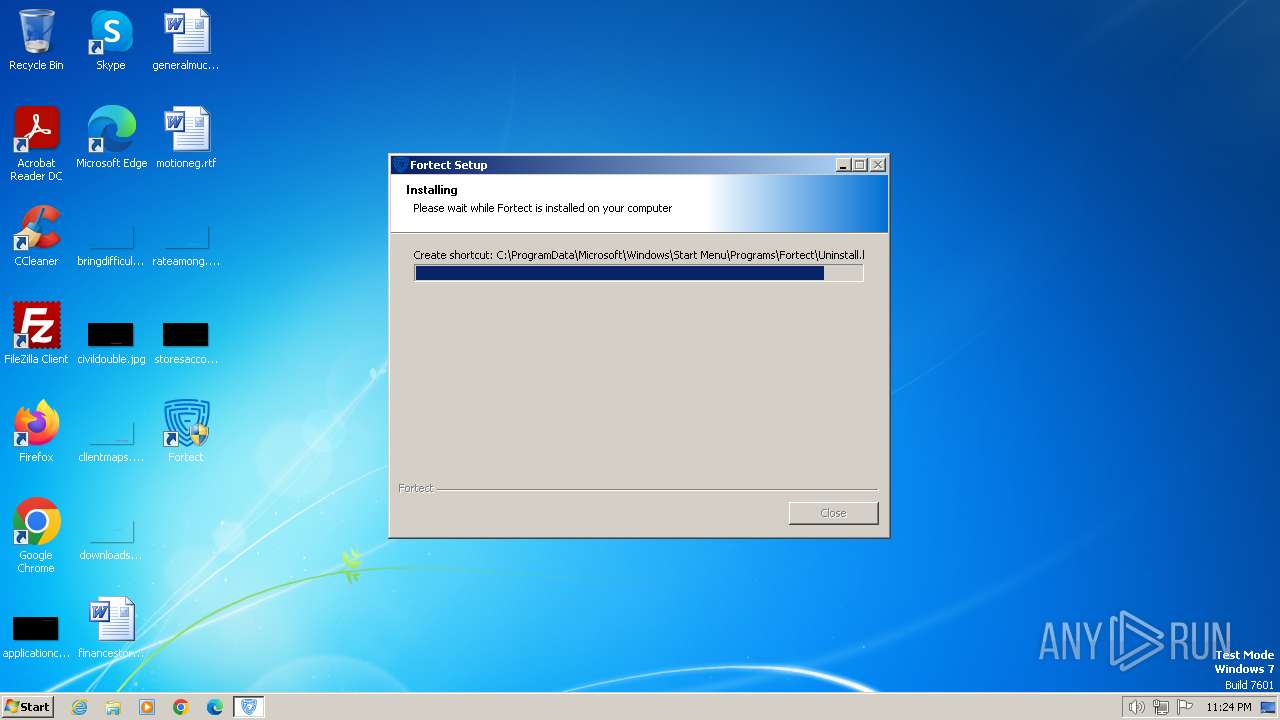
Creates files or folders in the user directory
- Fortect.exe (PID: 2064)
- FortectMain.exe (PID: 900)
- FortectMain.exe (PID: 3092)
Drops 7-zip archiver for unpacking
- Fortect.exe (PID: 2064)
Creates files in the program directory
- Fortect.exe (PID: 2064)
- MainDaemon.exe (PID: 2052)
- MainService.exe (PID: 2816)
- MainService.exe (PID: 2536)
- MainDaemon.exe (PID: 2320)
Process drops legitimate windows executable
- Fortect.exe (PID: 2064)
Executes as Windows Service
- MainService.exe (PID: 2536)
- MainDaemon.exe (PID: 2320)
Manual execution by a user
- FortectMain.exe (PID: 900)
Reads product name
- FortectMain.exe (PID: 900)
Process checks computer location settings
- FortectMain.exe (PID: 2664)
- MainService.exe (PID: 2536)
- FortectMain.exe (PID: 900)
Application launched itself
- FortectMain.exe (PID: 900)
Process checks the number of cached credentials
- MainService.exe (PID: 2536)
Reads mouse settings
- MainService.exe (PID: 2536)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (67.4) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.2) |
| .exe | | | Win32 Executable (generic) (9.7) |
| .exe | | | Generic Win/DOS Executable (4.3) |
| .exe | | | DOS Executable Generic (4.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2021:09:25 23:56:47+02:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 26624 |
| InitializedDataSize: | 141824 |
| UninitializedDataSize: | 2048 |
| EntryPoint: | 0x3640 |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
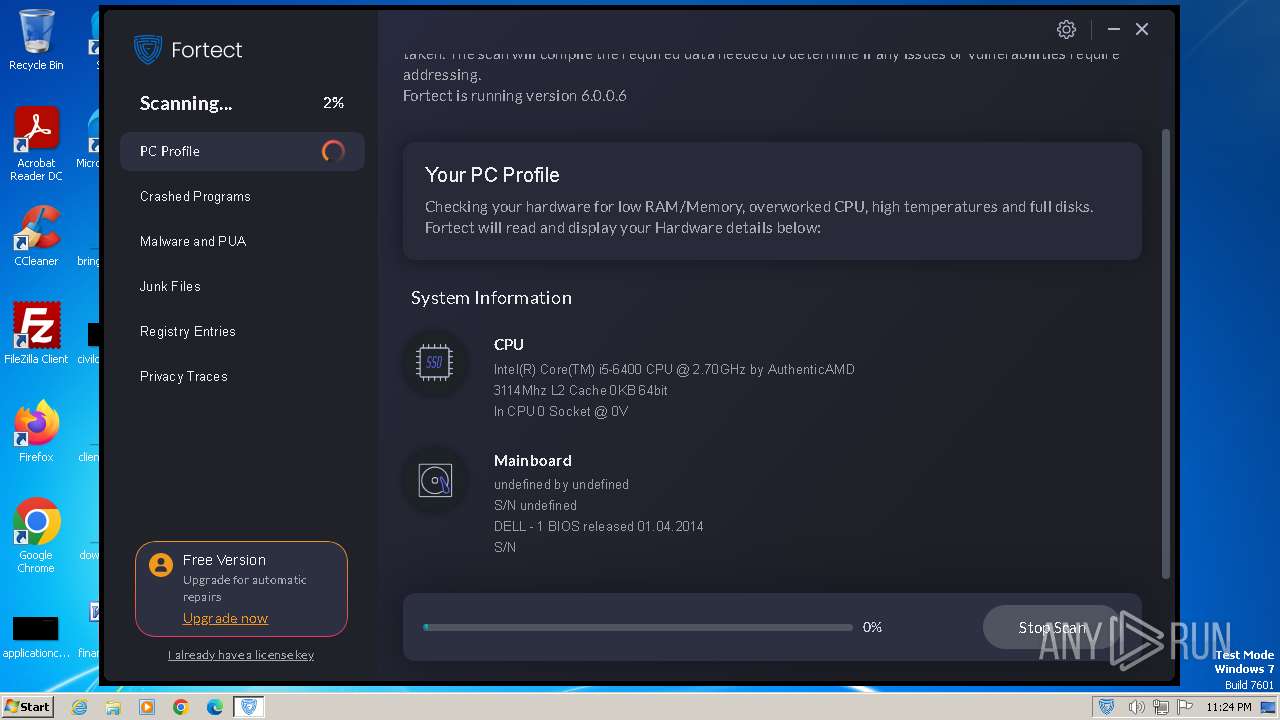
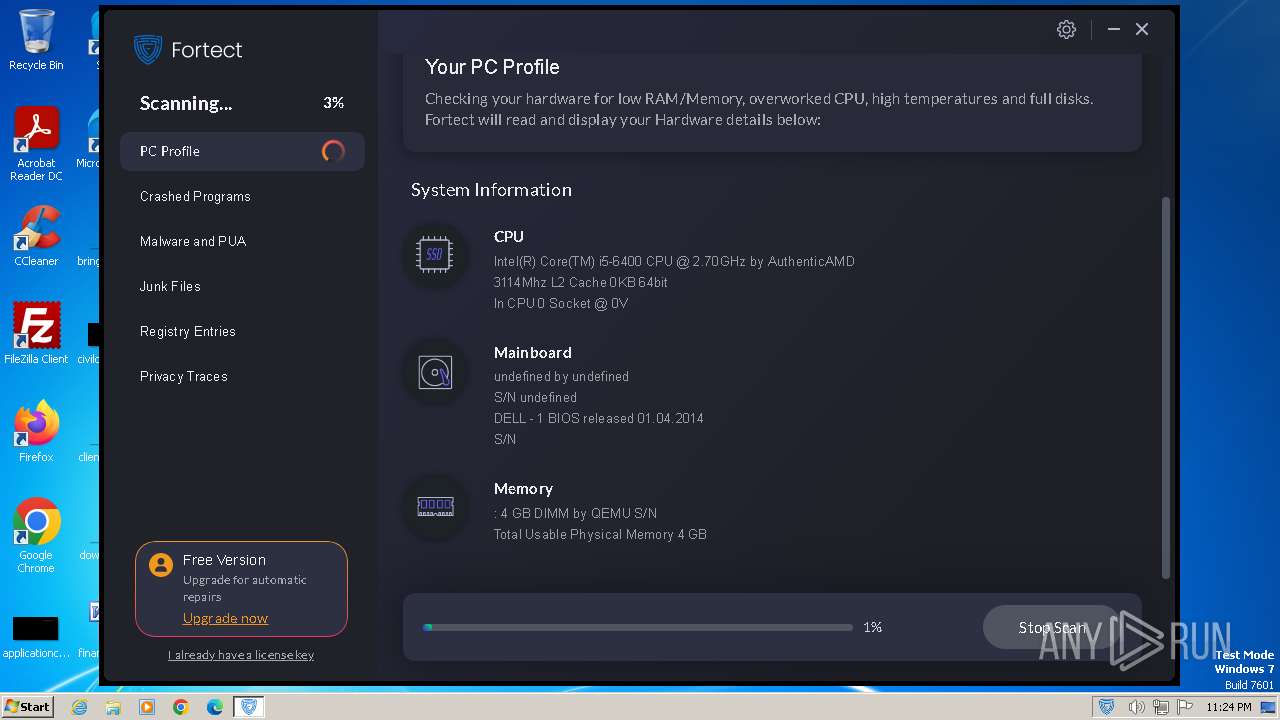
| FileVersionNumber: | 6.0.0.6 |
| ProductVersionNumber: | 6.0.0.6 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
| CompanyName: | Fortect |
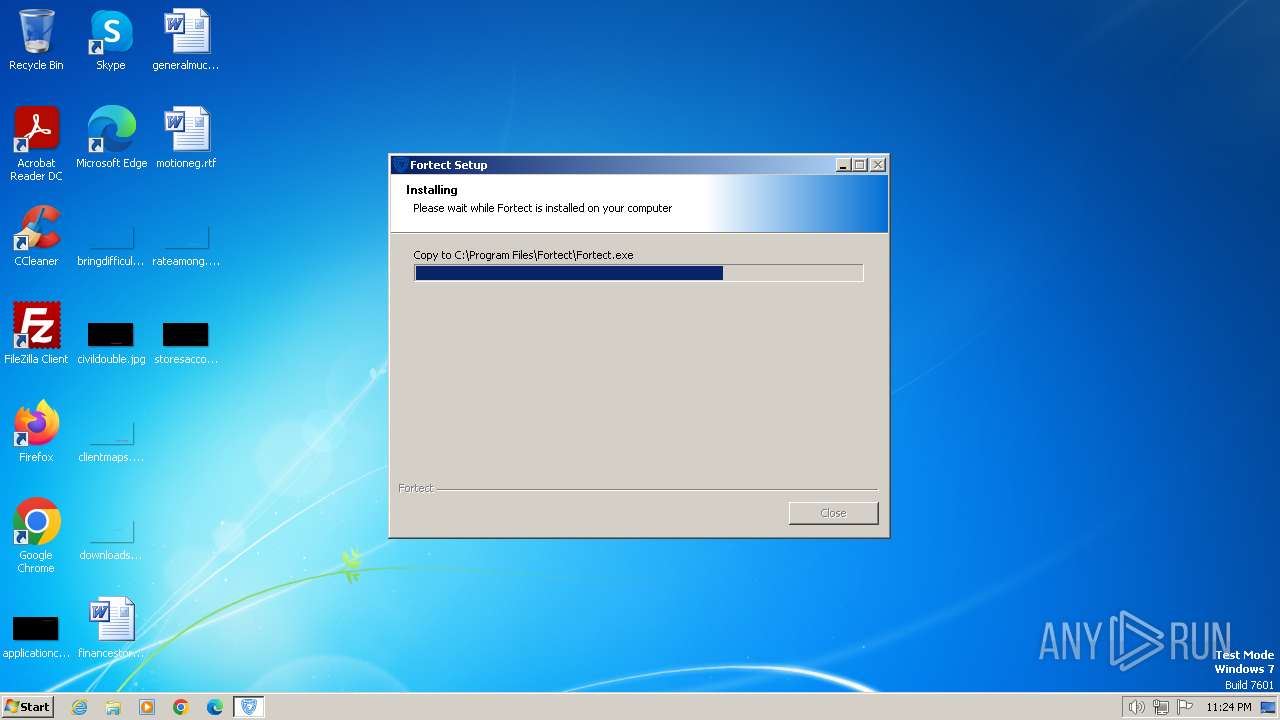
| FileDescription: | Fortect Setup |
| FileVersion: | 6.0.0.6 |
| InternalName: | Fortect.exe |
| LegalCopyright: | © Fortect |
| LegalTrademarks: | © Fortect |
| OriginalFileName: | Fortect.exe |
| ProductName: | Fortect |
| ProductVersion: | 6.0.0.6 |
Total processes
63
Monitored processes
18
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 120 | "C:\Users\admin\AppData\Local\Temp\Fortect.exe" | C:\Users\admin\AppData\Local\Temp\Fortect.exe | — | explorer.exe | |||||||||||
User: admin Company: Fortect Integrity Level: MEDIUM Description: Fortect Setup Exit code: 3221226540 Version: 6.0.0.6 Modules
| |||||||||||||||
| 548 | C:\Windows\System32\wbem\wmic.exe path Win32_BIOS get SerialNumber | C:\Windows\System32\wbem\WMIC.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: WMI Commandline Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 900 | "C:\Program Files\Fortect\FortectMain.exe" --lang=en --firstRun --runId=32d83e8b-df0e-4b8e-be5b-19573358a393 | C:\Program Files\Fortect\FortectMain.exe | — | explorer.exe | |||||||||||
User: admin Company: Fortect LTD® Integrity Level: MEDIUM Description: Fortect Main Exit code: 0 Version: 6.0.0.6 Modules
| |||||||||||||||
| 1544 | C:\Windows\System32\wbem\wmic.exe path Win32_ComputerSystemProduct get UUID | C:\Windows\System32\wbem\WMIC.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: WMI Commandline Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1832 | "C:\Windows\system32\wbem\wmic.exe" diskdrive where "DeviceID like '%%PHYSICALDRIVE0'" get SerialNumber | C:\Windows\System32\wbem\WMIC.exe | — | Fortect.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: WMI Commandline Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1840 | "C:\Windows\system32\wbem\wmic.exe" logicaldisk where "DeviceID='C:'" ASSOC /assocclass:Win32_LogicalDiskToPartition | C:\Windows\System32\wbem\WMIC.exe | — | Fortect.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: WMI Commandline Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1928 | C:\Windows\system32\cmd.exe /Q /C "%SYSTEMROOT%\System32\wbem\wmic.exe" path Win32_ComputerSystemProduct get UUID | C:\Windows\System32\cmd.exe | — | Fortect.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2024 | C:\Windows\system32\cmd.exe /Q /C "%SYSTEMROOT%\System32\wbem\wmic.exe" path Win32_BIOS get SerialNumber | C:\Windows\System32\cmd.exe | — | Fortect.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2052 | "C:\Program Files\Fortect\bin\MainDaemon.exe" --install | C:\Program Files\Fortect\bin\MainDaemon.exe | Fortect.exe | ||||||||||||
User: admin Company: Fortect Ltd. Integrity Level: HIGH Description: Fortect Daemon Exit code: 0 Version: 6.0.0.6 Modules
| |||||||||||||||
| 2064 | "C:\Users\admin\AppData\Local\Temp\Fortect.exe" | C:\Users\admin\AppData\Local\Temp\Fortect.exe | explorer.exe | ||||||||||||
User: admin Company: Fortect Integrity Level: HIGH Description: Fortect Setup Exit code: 0 Version: 6.0.0.6 Modules
| |||||||||||||||
Total events
90 712
Read events
90 607
Write events
105
Delete events
0
Modification events
| (PID) Process: | (2064) Fortect.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2064) Fortect.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 460000005B010000090000000000000000000000000000000400000000000000C0E333BBEAB1D3010000000000000000000000000100000002000000C0A8016B000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2064) Fortect.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2064) Fortect.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (2064) Fortect.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (2064) Fortect.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (2064) Fortect.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2064) Fortect.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2064) Fortect.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Wpad\{FCC67766-6201-4AD1-A6B8-2F4553C93D47} |
| Operation: | write | Name: | WpadDecisionReason |
Value: 1 | |||
| (PID) Process: | (2064) Fortect.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Wpad\{FCC67766-6201-4AD1-A6B8-2F4553C93D47} |
| Operation: | write | Name: | WpadDecisionTime |
Value: F0866B27C036DA01 | |||
Executable files
52
Suspicious files
189
Text files
66
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2064 | Fortect.exe | C:\Users\admin\AppData\Local\Temp\Fortect\plugins\LogEx.dll | executable | |
MD5:065130BD4BC3B4D769FFB0050A5464D0 | SHA256:568871B5048CF3E9A9C200C6527938FC616139353E084C43D283F96BA16B4EBB | |||
| 2064 | Fortect.exe | C:\Users\admin\AppData\Local\Temp\Fortect\plugins\Crypto.dll | executable | |
MD5:5F8DDDD0537CF9D33230C5F690C0ECA0 | SHA256:09140B70AA226CCD3C4EB0EA5DB056E4774004A96B4A32EEB1E51ECD799FDAEA | |||
| 2064 | Fortect.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\PO2HN1X2\events[1].htm | text | |
MD5:444BCB3A3FCF8389296C49467F27E1D6 | SHA256:2689367B205C16CE32ED4200942B8B8B1E262DFC70D9BC9FBC77C49699A4F1DF | |||
| 2064 | Fortect.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | compressed | |
MD5:1BFE591A4FE3D91B03CDF26EAACD8F89 | SHA256:9CF94355051BF0F4A45724CA20D1CC02F76371B963AB7D1E38BD8997737B13D8 | |||
| 2064 | Fortect.exe | C:\Users\admin\AppData\Local\Temp\Fortect\plugins\System.dll | executable | |
MD5:F64B9DFC805639380A2336BF2E803523 | SHA256:69CAE8B431D364968BB4D77352718F7D862563EF3EFD1D3D18DA10B0C2813B2B | |||
| 2064 | Fortect.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\24BD96D5497F70B3F510A6B53CD43F3E_3A89246FB90C5EE6620004F1AE0EB0EA | binary | |
MD5:E99C729661D361CFDECCB76FB786AEA4 | SHA256:FFAB13B85532E329F80D61CEF78D604E593CF8D409E5AA117E3B9B3C96926159 | |||
| 2064 | Fortect.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\CAF4703619713E3F18D8A9D5D88D6288_F2DAF19C1F776537105D08FC8D978464 | binary | |
MD5:DD30B0EC3118787F115288939366CE6C | SHA256:F296B0BE12828C9C399405D0B52AB7C25F2EC0553534C6F860BE51B37DD9447B | |||
| 2064 | Fortect.exe | C:\Users\admin\AppData\Local\Temp\Fortect\plugins\INetC.dll | executable | |
MD5:9F3C809A6F525A8EF0C981C84113560E | SHA256:4D7A2D9151E02B971F38D10FFE8937F34227AD5A2CE11E7879DF094482DECA72 | |||
| 2064 | Fortect.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\CAF4703619713E3F18D8A9D5D88D6288_F2DAF19C1F776537105D08FC8D978464 | binary | |
MD5:8202A1CD02E7D69597995CABBE881A12 | SHA256:58F381C3A0A0ACE6321DA22E40BD44A597BD98B9C9390AB9258426B5CF75A7A5 | |||
| 2064 | Fortect.exe | C:\Users\admin\AppData\Local\Temp\Fortect\plugins\nsProcess.dll | executable | |
MD5:92E43D9E657A2366B412475683AD7B07 | SHA256:1093622EA8E01F5614F343603D8C622193EAFA5B35773E5BD2C2DC0911F22A48 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
28
TCP/UDP connections
79
DNS requests
12
Threats
43
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2064 | Fortect.exe | GET | 200 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?d172a76546008f21 | unknown | compressed | 4.66 Kb | unknown |
2064 | Fortect.exe | GET | 200 | 142.250.186.67:80 | http://ocsp.pki.goog/gsr1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCEHe9DWzbNvka6iEPxPBY0w0%3D | unknown | binary | 1.41 Kb | unknown |
2536 | MainService.exe | GET | 200 | 50.56.4.183:80 | http://cloud.toppcprotection.com/lib/cloud-scan.php?param1=WVl2eFs2MD+3KnqZHGwtpbwcd6VoHbMYvJlib4qjlw5XA2h7DgC8VxEgK0Knskf2ySYv3vlmPyyxqrlQiAFhk39pvGuWus5J36cA2FsohEJBB2oqUbqSz8b5U4d++KVHXPrbkbhnIeDP8Smr9SQ7Y+Fbd5o8/+BsNYG6YNuDj1xo8MZXO/9Tm21lIRqhQ3y+ | unknown | text | 64 b | unknown |
2536 | MainService.exe | GET | 200 | 50.56.4.183:80 | http://cloud.toppcprotection.com/lib/cloud-scan.php?param1=WVl2eFs2MD+3KnqZHGwtpUVUu2nuvVrTHzBkk9DeOv9YPIR/Rz8Dav1b2rBMY5OYCKj5V9S9+MWUOKHHeSOAaRiIcrjgy8qLeQ9Hvb31ifl7xuym0w/lDfXYXWPysm1BJ583KYjk4jN7hfCWIz02+RdmOjVfg8LU0aWPVp5BztyIpmXafKZV1mI/dvPpknq6 | unknown | text | 64 b | unknown |
2064 | Fortect.exe | GET | 200 | 142.250.186.67:80 | http://ocsp.pki.goog/gtsr1/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBQwkcLWD4LqGJ7bE7B1XZsEbmfwUAQU5K8rJnEaK0gnhS9SZizv8IkTcT4CDQIDvFCjJ1PwkYAi7fE%3D | unknown | binary | 724 b | unknown |
2536 | MainService.exe | GET | 200 | 50.56.4.183:80 | http://cloud.toppcprotection.com/lib/cloud-scan.php?param1=WVl2eFs2MD+3KnqZHGwtpSrKqAqwReqbCt6tbgnICIX36l2Jz0u4lkEbruW84vmRrxF53PE2QH82GuEe9yBWPb7v1rV5gyusWReh3tP+f+02O/04nKgwqfi84MPbexCrlIlsxy4Eq3Y1ub7ITk1M+2Fme+eyHAusXi55BMOXYwsbcNJOiIq0idck6WzcMmgguTyuS6MXv44swTaa6E5q5Q== | unknown | text | 64 b | unknown |
2536 | MainService.exe | GET | 200 | 50.56.4.183:80 | http://cloud.toppcprotection.com/lib/cloud-scan.php?param1=WVl2eFs2MD+3KnqZHGwtpfqZEliFmw9+HCkC6ZkDlHgPS4uKis0eVssdz6+Uk2LqKElbiiwkUEjZNx0VtHsK/CsvBRTMzusTmSlVKcyfaGkTYGvHt+VQUR7RWQYbof9C5UmEsCIqYq476pb+hrG33dJRWZdIcLSpxnHDusDbur5/U7EjRvfs5XNIL017WJWH | unknown | text | 64 b | unknown |
2536 | MainService.exe | GET | 200 | 50.56.4.183:80 | http://cloud.toppcprotection.com/lib/cloud-scan.php?param1=WVl2eFs2MD+3KnqZHGwtpSQidvnQqNU1Rfp3Gud+hih49HZvdgCR1qXP23LRerLXJXEHijEILy3lT5my6Nl3L50Hd8a2mU1xSoIgCNKE/dnXJXuGza+dFXS/P1sndXCn7oYrxpt/XT6ErwbG+Y9PL/1AxvQ0LqRBt+tzdxJas4LzhYbOVewW+VX4l/Db5GuI6I9TR+D3Xws5Ui7iFL3n0w== | unknown | text | 64 b | unknown |
2536 | MainService.exe | GET | 200 | 50.56.4.183:80 | http://cloud.toppcprotection.com/lib/cloud-scan.php?param1=WVl2eFs2MD+3KnqZHGwtpRknKneUh6QekDiw+1AE8EnKf9BHqqbWTPYFgh6+HSK5xEGqpyY57qu8SRyraSnieTem6z557msbhXQa07pzC9+lbt+IMk7QMXo9oIqiBG/bOgz4SndKHNiO7v3iQzMDsa8Nt25yzLSZyOGdHtIIfUU= | unknown | text | 64 b | unknown |
2536 | MainService.exe | GET | 200 | 50.56.4.183:80 | http://cloud.toppcprotection.com/lib/cloud-scan.php?param1=WVl2eFs2MD+3KnqZHGwtpRSe+yoww+W2eAgpZ38LSBTzjGgp8Tlq9Kee27A7aT2FBuLMAAJlciI/nM8HR3fTdMrnTq6wGzXm+K5YU20uHtXn7zWPqFjQLc+nDIXtpbgEf+YfGg5OOZ3i228zNvHUjO/TAliuS0b6e8+UqvVRTbw= | unknown | text | 64 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2064 | Fortect.exe | 104.26.2.16:443 | app.fortect.com | CLOUDFLARENET | US | unknown |
2064 | Fortect.exe | 93.184.221.240:80 | ctldl.windowsupdate.com | EDGECAST | GB | whitelisted |
2064 | Fortect.exe | 142.250.186.67:80 | ocsp.pki.goog | GOOGLE | US | whitelisted |
2052 | MainDaemon.exe | 172.67.75.40:443 | app.fortect.com | CLOUDFLARENET | US | unknown |
2320 | MainDaemon.exe | 172.67.75.40:443 | app.fortect.com | CLOUDFLARENET | US | unknown |
3092 | FortectMain.exe | 74.125.173.200:443 | r3---sn-4g5e6nzz.gvt1.com | — | — | whitelisted |
2536 | MainService.exe | 104.26.2.16:443 | app.fortect.com | CLOUDFLARENET | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
app.fortect.com |
| unknown |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.pki.goog |
| whitelisted |
cloud.fortect.com |
| unknown |
service.fortect.com |
| unknown |
redirector.gvt1.com |
| whitelisted |
r3---sn-4g5e6nzz.gvt1.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
cloud.toppcprotection.com |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1080 | svchost.exe | Possibly Unwanted Program Detected | ET ADWARE_PUP Observed DNS Query to PC Optimizer Software Domain (fortect .com) |
2064 | Fortect.exe | Possibly Unwanted Program Detected | ET ADWARE_PUP Observed PC Optimizer Software Domain (fortect .com in TLS SNI) |
1080 | svchost.exe | Possibly Unwanted Program Detected | ET ADWARE_PUP Observed DNS Query to PC Optimizer Software Domain (fortect .com) |
2064 | Fortect.exe | Possibly Unwanted Program Detected | ET ADWARE_PUP Observed PC Optimizer Software Domain (fortect .com in TLS SNI) |
1080 | svchost.exe | Possibly Unwanted Program Detected | ET ADWARE_PUP Observed DNS Query to PC Optimizer Software Domain (fortect .com) |
2052 | MainDaemon.exe | Possibly Unwanted Program Detected | ET ADWARE_PUP Observed PC Optimizer Software Domain (fortect .com in TLS SNI) |
2052 | MainDaemon.exe | Possibly Unwanted Program Detected | ET ADWARE_PUP Observed PC Optimizer Software Domain (fortect .com in TLS SNI) |
2052 | MainDaemon.exe | Possibly Unwanted Program Detected | ET ADWARE_PUP Observed PC Optimizer Software Domain (fortect .com in TLS SNI) |
2052 | MainDaemon.exe | Possibly Unwanted Program Detected | ET ADWARE_PUP Observed PC Optimizer Software Domain (fortect .com in TLS SNI) |
2064 | Fortect.exe | Possibly Unwanted Program Detected | ET ADWARE_PUP Observed PC Optimizer Software Domain (fortect .com in TLS SNI) |
Process | Message |
|---|---|
Fortect.exe | ExecShellAsUser: elevated process detected |
Fortect.exe | ExecShellAsUser: got desktop |
Fortect.exe | ExecShellAsUser: thread finished |
Fortect.exe | ExecShellAsUser: DLL_PROCESS_DETACH |