| File name: | ReimagePackage.exe |
| Full analysis: | https://app.any.run/tasks/52de5af6-1317-4b3e-bc01-fa669b684b3d |
| Verdict: | Malicious activity |
| Analysis date: | February 18, 2019, 18:10:44 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | E335BB1E2296E1819D4CFD23884B79F0 |
| SHA1: | BBEA936191C000B8AD8693B305CFCED4642CD550 |
| SHA256: | 6143C2B8A8BAF518B74388AD49F1DF143FC2F46587A716686E7E43DF7DD419C7 |
| SSDEEP: | 12288:lEeafd3LQ6xbqjhyJEWEw+ekrCJsODKi2ybz+S9USvJwVt:lta13LFWlymYCAsO+DyX+daA |
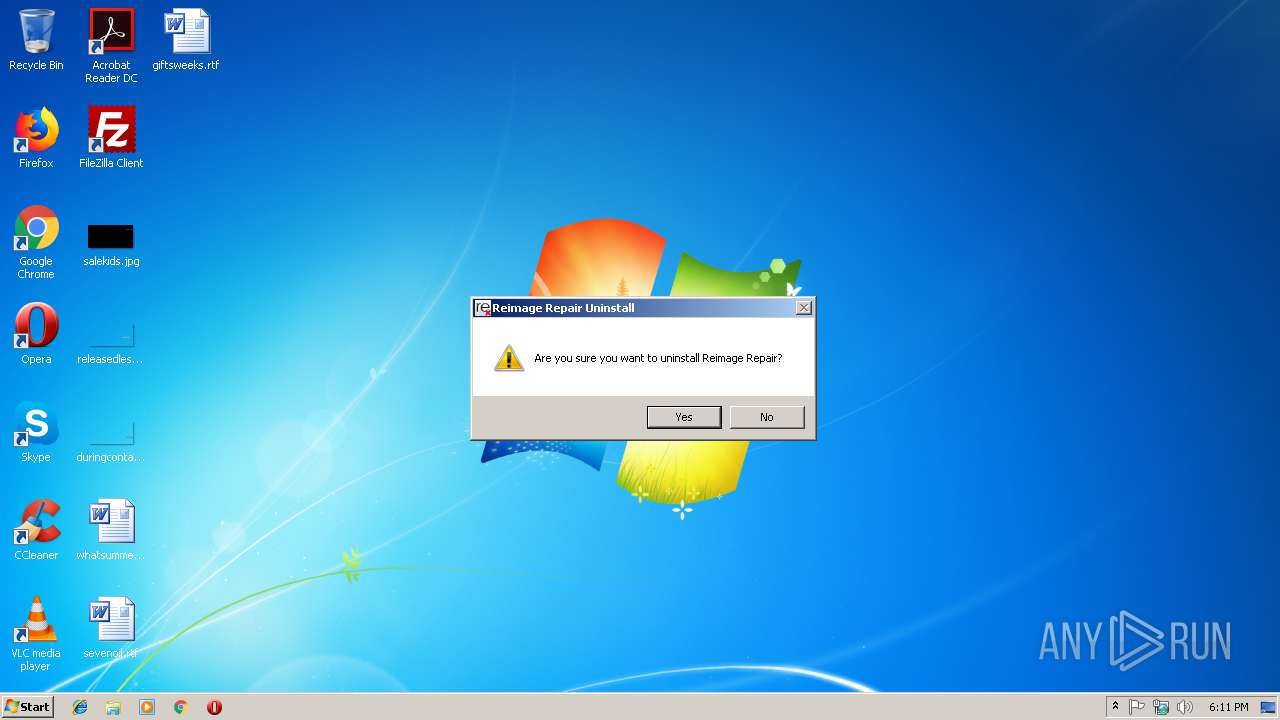
MALICIOUS
Loads dropped or rewritten executable
- Au_.exe (PID: 2920)
Application was dropped or rewritten from another process
- nsC7FD.tmp (PID: 2228)
- nsC165.tmp (PID: 3140)
- Bu_.exe (PID: 2264)
- uninst.exe (PID: 1708)
- nsF5B5.tmp (PID: 2452)
Registers / Runs the DLL via REGSVR32.EXE
- Au_.exe (PID: 2920)
SUSPICIOUS
Executable content was dropped or overwritten
- ReimagePackage.exe (PID: 3964)
- Au_.exe (PID: 2920)
- uninst.exe (PID: 1708)
Starts itself from another location
- ReimagePackage.exe (PID: 3964)
- uninst.exe (PID: 1708)
Starts application with an unusual extension
- Au_.exe (PID: 2920)
Creates files in the Windows directory
- Au_.exe (PID: 2920)
Starts CMD.EXE for commands execution
- nsC165.tmp (PID: 3140)
Uses TASKLIST.EXE to query information about running processes
- cmd.exe (PID: 3676)
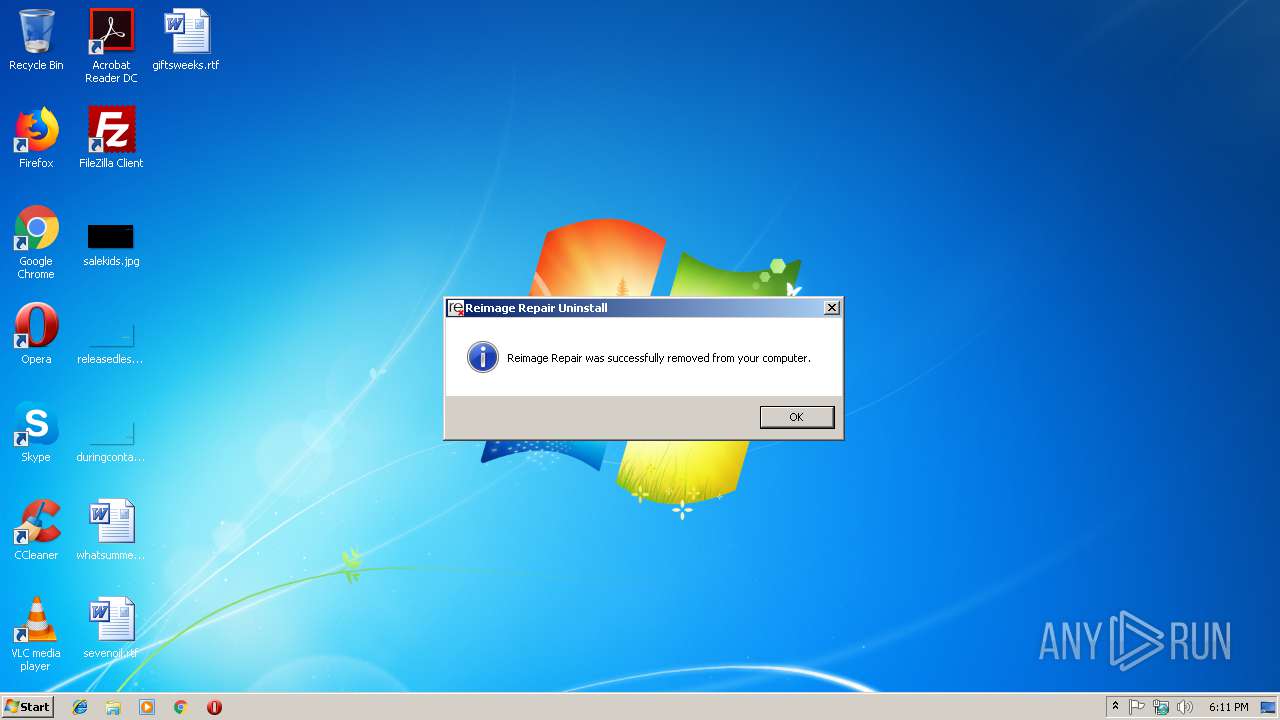
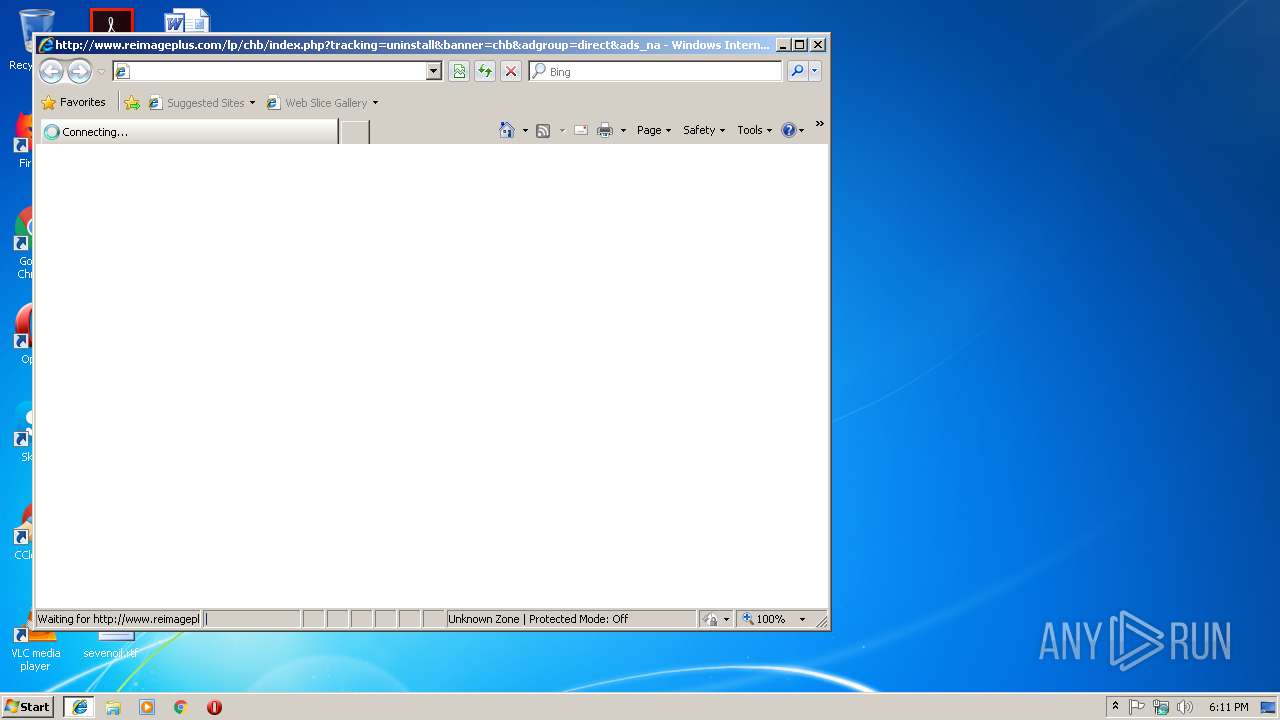
Starts Internet Explorer
- Au_.exe (PID: 2920)
INFO
Changes internet zones settings
- iexplore.exe (PID: 3308)
Application launched itself
- iexplore.exe (PID: 3308)
Creates files in the user directory
- iexplore.exe (PID: 3652)
Reads Internet Cache Settings
- iexplore.exe (PID: 3652)
- iexplore.exe (PID: 3308)
Reads internet explorer settings
- iexplore.exe (PID: 3652)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2012:02:24 20:19:59+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 10 |
| CodeSize: | 28672 |
| InitializedDataSize: | 446464 |
| UninitializedDataSize: | 16896 |
| EntryPoint: | 0x39e3 |
| OSVersion: | 5 |
| ImageVersion: | 6 |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.8.8.9 |
| ProductVersionNumber: | 1.8.8.9 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| CompanyName: | Reimage |
| FileDescription: | Reimage Package |
| FileVersion: | 1.889 |
| InternalName: | Reimage Repair |
| LegalCopyright: | © Reimage 2019 |
| LegalTrademarks: | Reimage |
| OriginalFileName: | ReimagePackage.exe |
| ProductName: | Reimage Repair |
| ProductVersion: | 1.889 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 24-Feb-2012 19:19:59 |
| Detected languages: |
|
| CompanyName: | Reimage |
| FileDescription: | Reimage Package |
| FileVersion: | 1.889 |
| InternalName: | Reimage Repair |
| LegalCopyright: | © Reimage 2019 |
| LegalTrademarks: | Reimage |
| OriginalFilename: | ReimagePackage.exe |
| ProductName: | Reimage Repair |
| ProductVersion: | 1.889 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000D0 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 6 |
| Time date stamp: | 24-Feb-2012 19:19:59 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00006F10 | 0x00007000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.49788 |
.rdata | 0x00008000 | 0x00002A92 | 0x00002C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.39389 |
.data | 0x0000B000 | 0x00067EBC | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 1.47278 |
.ndata | 0x00073000 | 0x004A1000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x00514000 | 0x0000A5BD | 0x0000A600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.46059 |
.reloc | 0x0051F000 | 0x00000F8A | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 4.36445 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.4032 | 1461 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 3.93748 | 9640 | UNKNOWN | English - United States | RT_ICON |
3 | 4.15761 | 4264 | UNKNOWN | English - United States | RT_ICON |
4 | 4.37374 | 2440 | UNKNOWN | English - United States | RT_ICON |
5 | 4.61697 | 1128 | UNKNOWN | English - United States | RT_ICON |
103 | 2.79808 | 76 | UNKNOWN | English - United States | RT_GROUP_ICON |
105 | 2.64725 | 704 | UNKNOWN | English - United States | RT_DIALOG |
106 | 2.91148 | 248 | UNKNOWN | English - United States | RT_DIALOG |
111 | 2.92787 | 238 | UNKNOWN | English - United States | RT_DIALOG |
205 | 2.68306 | 696 | UNKNOWN | English - United States | RT_DIALOG |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
VERSION.dll |
ole32.dll |
Total processes
51
Monitored processes
14
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1244 | regsvr32 /s /u "C:\Users\admin\AppData\Local\Temp\REI_Engine.dll" | C:\Windows\system32\regsvr32.exe | — | Au_.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft(C) Register Server Exit code: 3 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
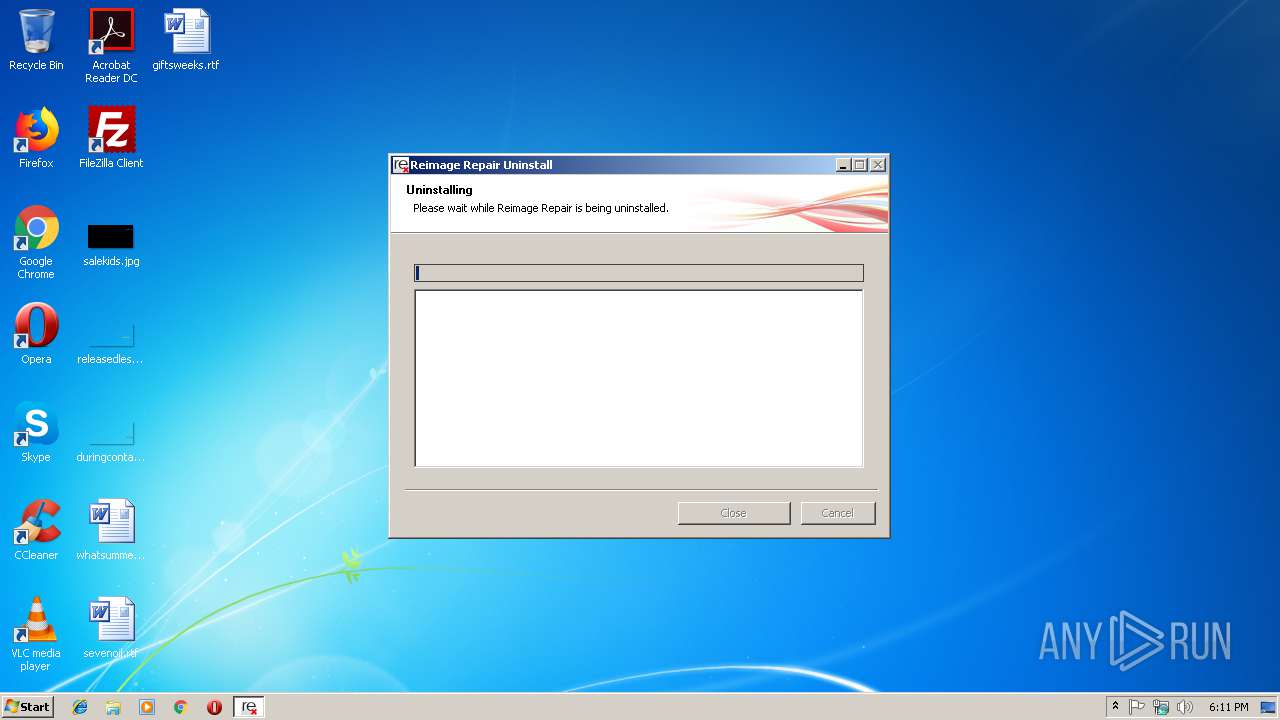
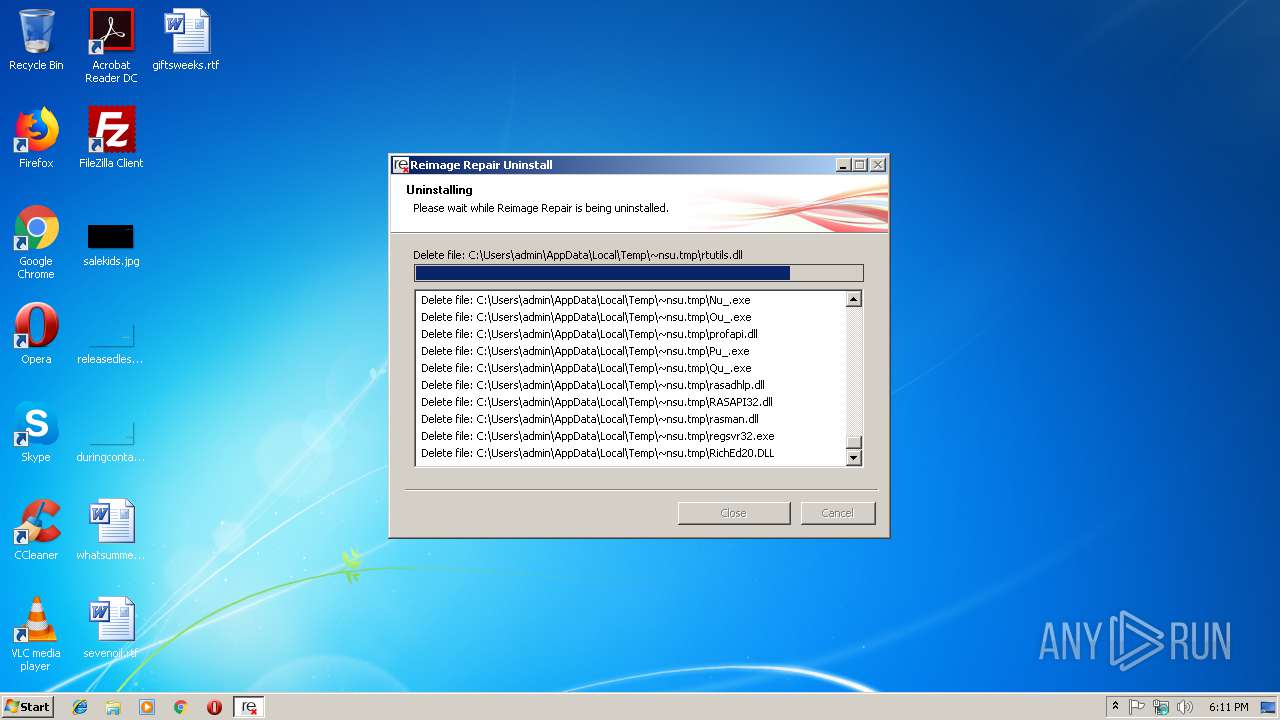
| 1708 | "C:\Users\admin\AppData\Local\Temp\uninst.exe" /Silent=True | C:\Users\admin\AppData\Local\Temp\uninst.exe | Au_.exe | ||||||||||||
User: admin Company: Reimage Integrity Level: HIGH Description: Reimage Protector Uninstaller Exit code: 0 Version: 2.023 Modules
| |||||||||||||||
| 2228 | "C:\Users\admin\AppData\Local\Temp\nso9FE2.tmp\nsC7FD.tmp" cmd /C tasklist /FI "IMAGENAME eq avupdate.exe" > C:\Users\admin\AppData\Local\Temp\IsProcessActive.txt | C:\Users\admin\AppData\Local\Temp\nso9FE2.tmp\nsC7FD.tmp | — | Au_.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 3221225501 Modules
| |||||||||||||||
| 2264 | "C:\Users\admin\AppData\Local\Temp\~nsu.tmp\Bu_.exe" /Silent=True _?=C:\Users\admin\AppData\Local\Temp\ | C:\Users\admin\AppData\Local\Temp\~nsu.tmp\Bu_.exe | — | uninst.exe | |||||||||||
User: admin Company: Reimage Integrity Level: HIGH Description: Reimage Protector Uninstaller Exit code: 3221225504 Version: 2.023 Modules
| |||||||||||||||
| 2452 | "C:\Users\admin\AppData\Local\Temp\nso9FE2.tmp\nsF5B5.tmp" "C:\Users\admin\AppData\Local\Temp\ReimageReminder.exe" -r | C:\Users\admin\AppData\Local\Temp\nso9FE2.tmp\nsF5B5.tmp | — | Au_.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 3221225501 Modules
| |||||||||||||||
| 2920 | "C:\Users\admin\AppData\Local\Temp\~nsu.tmp\Au_.exe" _?=C:\Users\admin\AppData\Local\Temp\ | C:\Users\admin\AppData\Local\Temp\~nsu.tmp\Au_.exe | ReimagePackage.exe | ||||||||||||
User: admin Company: Reimage Integrity Level: HIGH Description: Reimage Package Exit code: 0 Version: 1.889 Modules
| |||||||||||||||
| 3060 | "C:\Users\admin\AppData\Local\Temp\ReimagePackage.exe" | C:\Users\admin\AppData\Local\Temp\ReimagePackage.exe | — | explorer.exe | |||||||||||
User: admin Company: Reimage Integrity Level: MEDIUM Description: Reimage Package Exit code: 3221226540 Version: 1.889 Modules
| |||||||||||||||
| 3140 | "C:\Users\admin\AppData\Local\Temp\nso9FE2.tmp\nsC165.tmp" cmd /C tasklist /FI "IMAGENAME eq Reimage.exe" > C:\Users\admin\AppData\Local\Temp\IsProcessActive.txt | C:\Users\admin\AppData\Local\Temp\nso9FE2.tmp\nsC165.tmp | — | Au_.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 3308 | "C:\Program Files\Internet Explorer\iexplore.exe" -nohome | C:\Program Files\Internet Explorer\iexplore.exe | Au_.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 1 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3652 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3308 CREDAT:79873 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 432
Read events
1 341
Write events
88
Delete events
3
Modification events
| (PID) Process: | (3964) ReimagePackage.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Control\Session Manager |
| Operation: | write | Name: | PendingFileRenameOperations |
Value: \??\C:\Users\admin\AppData\Local\Temp\~nsu.tmp\Au_.exe | |||
| (PID) Process: | (2920) Au_.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Au__RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (2920) Au_.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Au__RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (2920) Au_.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Au__RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (2920) Au_.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Au__RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (2920) Au_.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Au__RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (2920) Au_.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Au__RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (2920) Au_.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Au__RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (2920) Au_.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Au__RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (2920) Au_.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Au__RASMANCS |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
Executable files
12
Suspicious files
2
Text files
48
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3964 | ReimagePackage.exe | C:\Users\admin\AppData\Local\Temp\nss9DDD.tmp | — | |
MD5:— | SHA256:— | |||
| 2920 | Au_.exe | C:\Users\admin\AppData\Local\Temp\nso9FE2.tmp\nsC7FD.tmp | — | |
MD5:— | SHA256:— | |||
| 3964 | ReimagePackage.exe | C:\Users\admin\AppData\Local\Temp\~nsu.tmp\Au_.exe | executable | |
MD5:— | SHA256:— | |||
| 2920 | Au_.exe | C:\Windows\Reimage.ini | text | |
MD5:— | SHA256:— | |||
| 2920 | Au_.exe | C:\Windows\reimage.ini | text | |
MD5:— | SHA256:— | |||
| 2920 | Au_.exe | C:\Users\admin\AppData\Local\Temp\nsi9FC1.tmp | — | |
MD5:— | SHA256:— | |||
| 3308 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\R9ZEWH8D\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 2920 | Au_.exe | C:\Users\admin\AppData\Local\Temp\nso9FE2.tmp\uninstall-form.bmp | image | |
MD5:— | SHA256:— | |||
| 3308 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 2920 | Au_.exe | C:\Users\admin\AppData\Local\Temp\nso9FE2.tmp\warning.bmp | image | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
31
TCP/UDP connections
20
DNS requests
11
Threats
8
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2920 | Au_.exe | GET | 200 | 161.47.7.14:80 | http://www.reimageplus.com/events4mem.php?version=1889&SessionID=a939ec8e-60cb-4575-8d57-6f9719d11498&MinorSessionID=0fe0080b067b4648846e8463eb&id=UNINT¶m=&trackutil= | US | — | — | suspicious |
2920 | Au_.exe | GET | 200 | 161.47.7.14:80 | http://www.reimageplus.com/events4mem.php?version=1889&SessionID=a939ec8e-60cb-4575-8d57-6f9719d11498&MinorSessionID=0fe0080b067b4648846e8463eb&id=UNIYN¶m=protdis&trackutil= | US | — | — | suspicious |
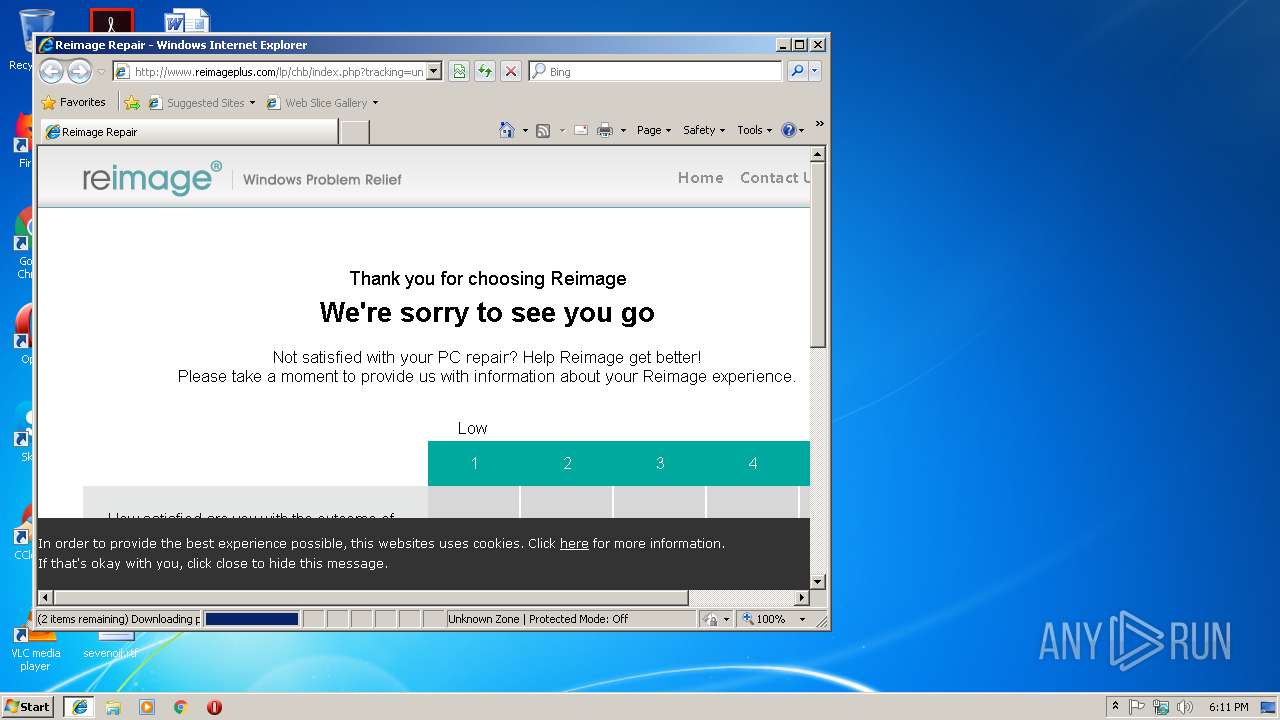
3652 | iexplore.exe | GET | 200 | 161.47.7.14:80 | http://www.reimageplus.com/lp/chb/index.php?tracking=uninstall&banner=chb&adgroup=direct&ads_name=direct&keyword=direct&nms=1&whf=true&lpx=chb | US | html | 2.36 Kb | suspicious |
3652 | iexplore.exe | GET | 200 | 161.47.7.14:80 | http://www.reimageplus.com/lp/chb/index_src.php?tracking=uninstall&banner=chb&adgroup=direct&ads_name=direct&keyword=direct&nms=1&whf=true&lpx=chb | US | html | 7.61 Kb | suspicious |
3652 | iexplore.exe | GET | 200 | 161.47.7.14:80 | http://www.reimageplus.com/lp/chb/css/style.css | US | text | 2.01 Kb | suspicious |
3652 | iexplore.exe | GET | 200 | 161.47.7.14:80 | http://www.reimageplus.com/lp/chb/scripts/main.js | US | text | 6.38 Kb | suspicious |
3652 | iexplore.exe | GET | 200 | 205.185.208.80:80 | http://cdnrep.reimageplus.com/website/newwebsite/lp/chb/row_tooltip.png | US | image | 440 b | suspicious |
3652 | iexplore.exe | GET | 200 | 161.47.7.14:80 | http://www.reimageplus.com/assets/styles/jquery.fancybox/jquery.fancybox-2.css | US | text | 1.57 Kb | suspicious |
3652 | iexplore.exe | GET | 301 | 161.47.7.14:80 | http://www.reimageplus.com/includes/router_land.php?tracking=uninstall&banner=chb&lpx=chb&whf=true | US | text | 22 b | suspicious |
3652 | iexplore.exe | GET | 200 | 216.58.205.234:80 | http://ajax.googleapis.com/ajax/libs/jquery/1.5.1/jquery.min.js | US | text | 29.1 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2920 | Au_.exe | 161.47.7.14:80 | www.reimageplus.com | Rackspace Ltd. | US | malicious |
2920 | Au_.exe | 50.56.53.60:80 | webservice.reimageplus.com | Rackspace Ltd. | US | malicious |
3308 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3652 | iexplore.exe | 161.47.7.14:80 | www.reimageplus.com | Rackspace Ltd. | US | malicious |
3652 | iexplore.exe | 205.185.208.80:80 | cdnrep.reimage.com | Highwinds Network Group, Inc. | US | suspicious |
3652 | iexplore.exe | 216.58.205.234:80 | ajax.googleapis.com | Google Inc. | US | whitelisted |
3652 | iexplore.exe | 23.45.106.123:443 | seal.websecurity.norton.com | Akamai International B.V. | NL | whitelisted |
3652 | iexplore.exe | 74.125.133.155:80 | stats.g.doubleclick.net | Google Inc. | US | whitelisted |
3652 | iexplore.exe | 54.192.130.138:80 | images.scanalert.com | Amazon.com, Inc. | US | unknown |
3652 | iexplore.exe | 216.58.208.34:80 | www.googleadservices.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.reimageplus.com |
| suspicious |
webservice.reimageplus.com |
| whitelisted |
www.bing.com |
| whitelisted |
ajax.googleapis.com |
| whitelisted |
cdnrep.reimage.com |
| whitelisted |
cdnrep.reimageplus.com |
| suspicious |
seal.websecurity.norton.com |
| whitelisted |
www.googleadservices.com |
| whitelisted |
images.scanalert.com |
| shared |
stats.g.doubleclick.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2920 | Au_.exe | A Network Trojan was detected | ET POLICY User-Agent (NSIS_Inetc (Mozilla)) - Sometimes used by hostile installers |
2920 | Au_.exe | Misc activity | SUSPICIOUS [PTsecurity] Suspicious HTTP header - Sometimes used by hostile installer |
2920 | Au_.exe | A Network Trojan was detected | ET POLICY User-Agent (NSIS_Inetc (Mozilla)) - Sometimes used by hostile installers |
2920 | Au_.exe | Misc activity | SUSPICIOUS [PTsecurity] Suspicious HTTP header - Sometimes used by hostile installer |
2920 | Au_.exe | A Network Trojan was detected | ET POLICY User-Agent (NSIS_Inetc (Mozilla)) - Sometimes used by hostile installers |
2920 | Au_.exe | Misc activity | SUSPICIOUS [PTsecurity] Suspicious HTTP header - Sometimes used by hostile installer |
2920 | Au_.exe | A Network Trojan was detected | ET POLICY User-Agent (NSIS_Inetc (Mozilla)) - Sometimes used by hostile installers |
2920 | Au_.exe | Misc activity | SUSPICIOUS [PTsecurity] Suspicious HTTP header - Sometimes used by hostile installer |