| File name: | 613b31ed6f4c1c534cfe3004fe7741ca3ac080f99d22e1b0af9d80eb1add9e1c |
| Full analysis: | https://app.any.run/tasks/23e08d43-7695-4735-bc22-2ffbaebfba32 |
| Verdict: | Malicious activity |
| Analysis date: | April 29, 2025, 09:29:41 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, RAR self-extracting archive, 4 sections |
| MD5: | 80E95B38B833BB147FEE23F7A94EA963 |
| SHA1: | 68722006A2A1AC942BD12083401440BD51AE82C6 |
| SHA256: | 613B31ED6F4C1C534CFE3004FE7741CA3AC080F99D22E1B0AF9D80EB1ADD9E1C |
| SSDEEP: | 98304:apnq5lzPU4Po4QPezk5re6P/zeyzWUm5kYpbWc39dkvRihcOJNJJdy78owTGOLx9:mqm7wDyTLOrkZy9y+uXOdDWJM |
MALICIOUS
SFX dropper has been detected
- 613b31ed6f4c1c534cfe3004fe7741ca3ac080f99d22e1b0af9d80eb1add9e1c.exe (PID: 7392)
SUSPICIOUS
Reads security settings of Internet Explorer
- 613b31ed6f4c1c534cfe3004fe7741ca3ac080f99d22e1b0af9d80eb1add9e1c.exe (PID: 7392)
Application launched itself
- 613b31ed6f4c1c534cfe3004fe7741ca3ac080f99d22e1b0af9d80eb1add9e1c.exe (PID: 7392)
Executable content was dropped or overwritten
- 613b31ed6f4c1c534cfe3004fe7741ca3ac080f99d22e1b0af9d80eb1add9e1c.exe (PID: 7664)
Drops a system driver (possible attempt to evade defenses)
- 613b31ed6f4c1c534cfe3004fe7741ca3ac080f99d22e1b0af9d80eb1add9e1c.exe (PID: 7664)
INFO
Reads the computer name
- 613b31ed6f4c1c534cfe3004fe7741ca3ac080f99d22e1b0af9d80eb1add9e1c.exe (PID: 7392)
- 613b31ed6f4c1c534cfe3004fe7741ca3ac080f99d22e1b0af9d80eb1add9e1c.exe (PID: 7664)
Process checks computer location settings
- 613b31ed6f4c1c534cfe3004fe7741ca3ac080f99d22e1b0af9d80eb1add9e1c.exe (PID: 7392)
Checks supported languages
- 613b31ed6f4c1c534cfe3004fe7741ca3ac080f99d22e1b0af9d80eb1add9e1c.exe (PID: 7392)
- 613b31ed6f4c1c534cfe3004fe7741ca3ac080f99d22e1b0af9d80eb1add9e1c.exe (PID: 7664)
Creates files in the program directory
- 613b31ed6f4c1c534cfe3004fe7741ca3ac080f99d22e1b0af9d80eb1add9e1c.exe (PID: 7664)
The sample compiled with chinese language support
- 613b31ed6f4c1c534cfe3004fe7741ca3ac080f99d22e1b0af9d80eb1add9e1c.exe (PID: 7664)
The sample compiled with english language support
- 613b31ed6f4c1c534cfe3004fe7741ca3ac080f99d22e1b0af9d80eb1add9e1c.exe (PID: 7664)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2013:11:12 18:45:34+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 9 |
| CodeSize: | 153088 |
| InitializedDataSize: | 172032 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1d6d8 |
| OSVersion: | 5 |
| ImageVersion: | - |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
Total processes
135
Monitored processes
4
Malicious processes
1
Suspicious processes
1
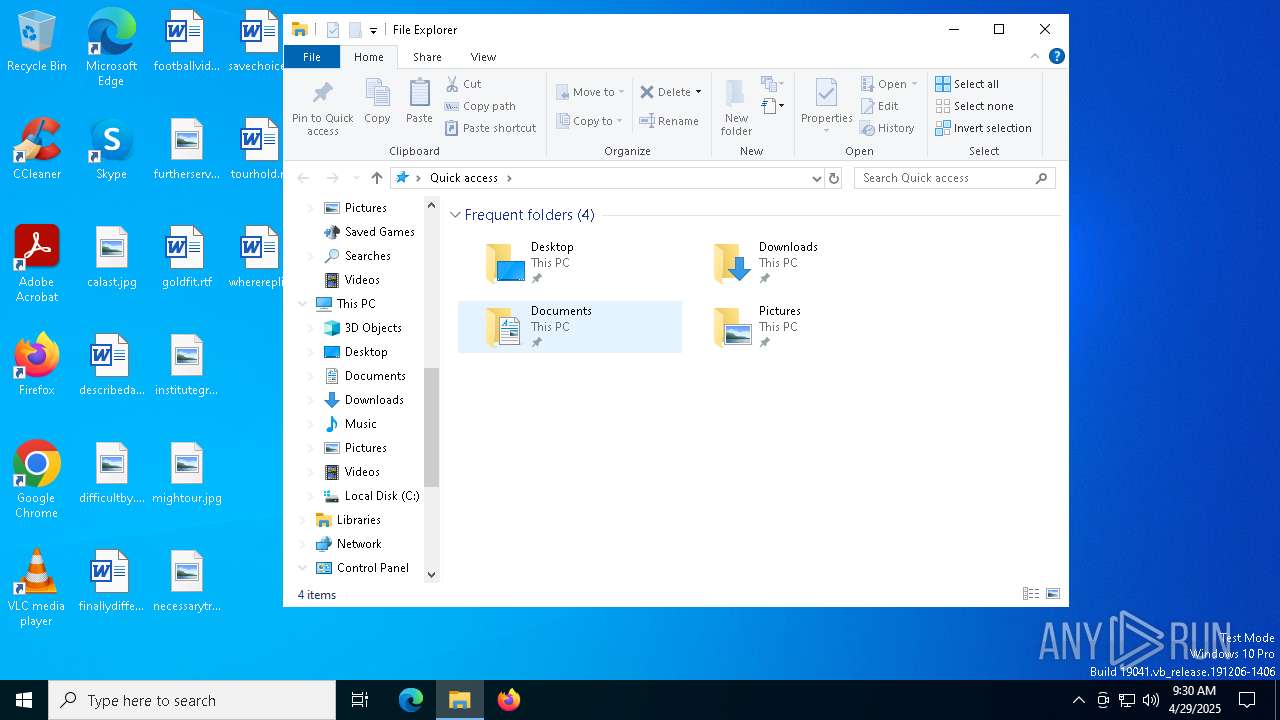
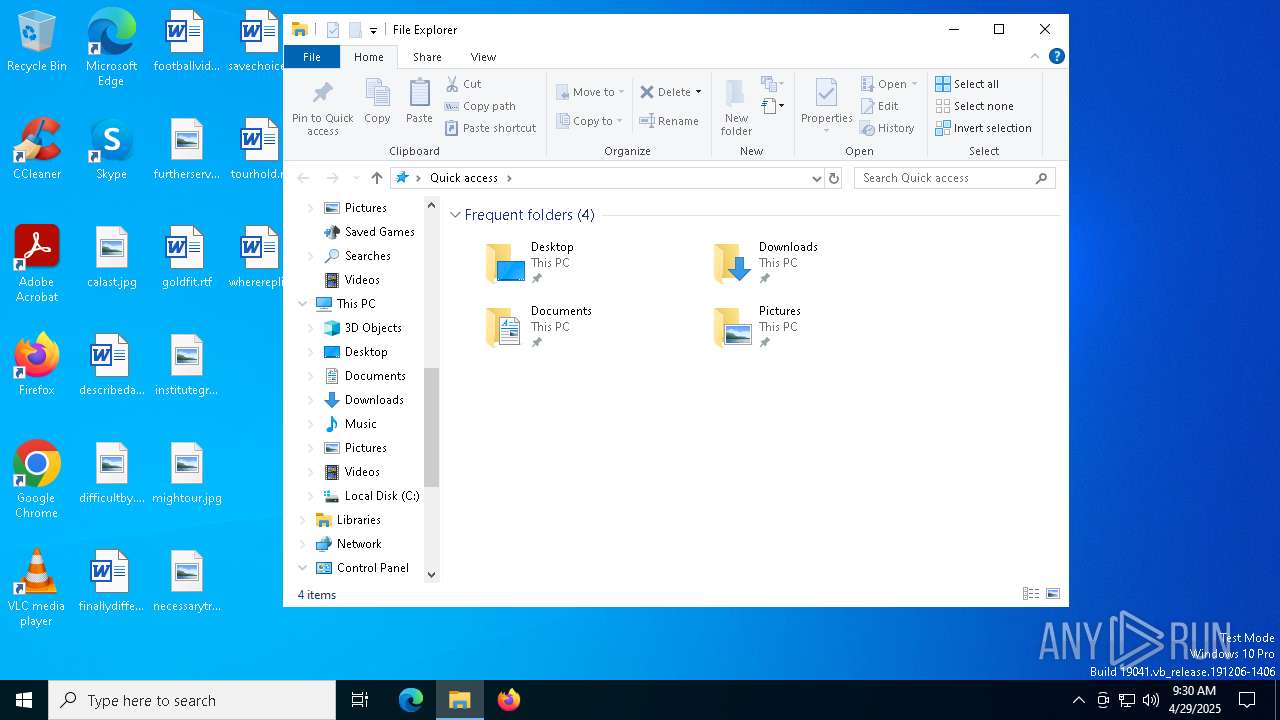
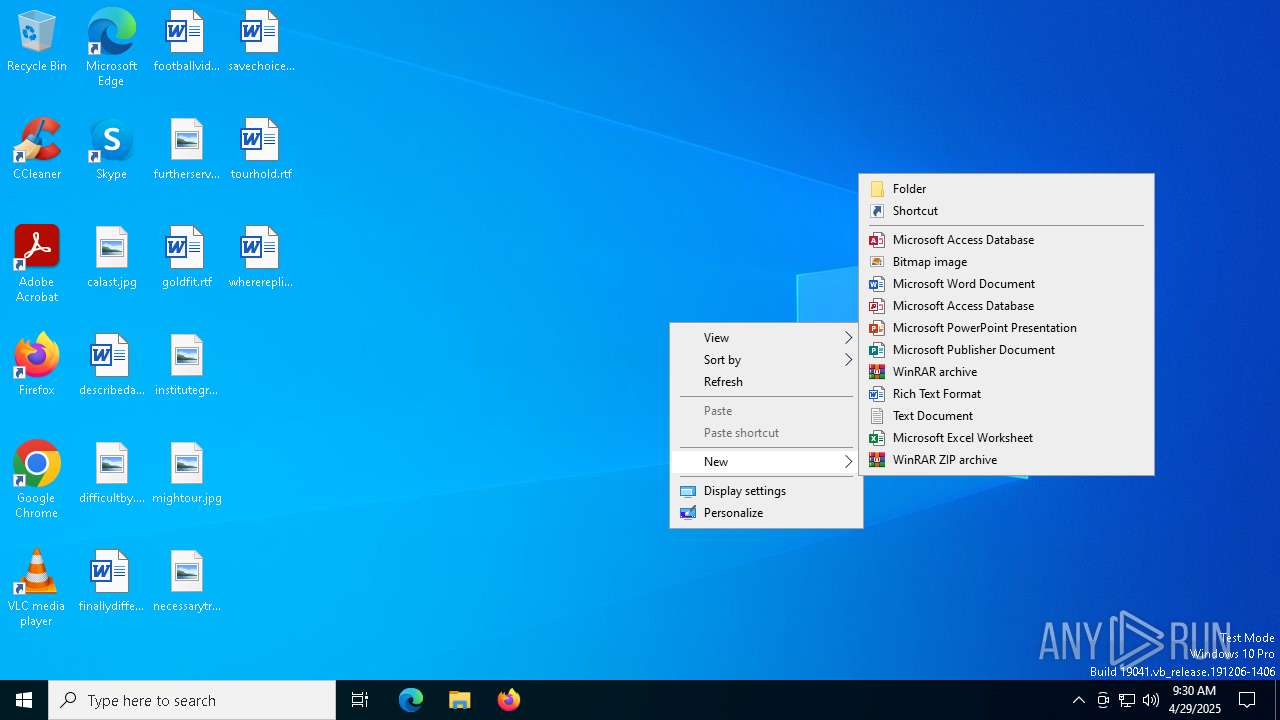
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 7392 | "C:\Users\admin\AppData\Local\Temp\613b31ed6f4c1c534cfe3004fe7741ca3ac080f99d22e1b0af9d80eb1add9e1c.exe" | C:\Users\admin\AppData\Local\Temp\613b31ed6f4c1c534cfe3004fe7741ca3ac080f99d22e1b0af9d80eb1add9e1c.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 7664 | "C:\Users\admin\AppData\Local\Temp\613b31ed6f4c1c534cfe3004fe7741ca3ac080f99d22e1b0af9d80eb1add9e1c.exe" -el -s2 "-dC:\" "-p" "-sp" | C:\Users\admin\AppData\Local\Temp\613b31ed6f4c1c534cfe3004fe7741ca3ac080f99d22e1b0af9d80eb1add9e1c.exe | 613b31ed6f4c1c534cfe3004fe7741ca3ac080f99d22e1b0af9d80eb1add9e1c.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 8044 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 8084 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | — | SppExtComObj.Exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
489
Read events
489
Write events
0
Delete events
0
Modification events
Executable files
29
Suspicious files
23
Text files
17
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7664 | 613b31ed6f4c1c534cfe3004fe7741ca3ac080f99d22e1b0af9d80eb1add9e1c.exe | C:\Program Files\装机人员工具\Everest\lang_cn.txt | text | |
MD5:4D317C88ACE3E02FE4D958E2D331FC95 | SHA256:5BF8541E3EDF3CA628FA2E5489571C86628F14B608442A907B1FACC9FD7F873E | |||
| 7664 | 613b31ed6f4c1c534cfe3004fe7741ca3ac080f99d22e1b0af9d80eb1add9e1c.exe | C:\Program Files\装机人员工具\CPUZ\cpuz.ini | text | |
MD5:48C023CFC3BF62AD6EA471EBA9289C10 | SHA256:147609A66CF4B80B3A74C8D389D373BFDAC91F2439A2EC48388307F3D7D2B169 | |||
| 7664 | 613b31ed6f4c1c534cfe3004fe7741ca3ac080f99d22e1b0af9d80eb1add9e1c.exe | C:\Program Files\绿色软件\Foxit Reader\lang_zh_cn.xml | xml | |
MD5:1AF697825E3C65E96E4920D3EED43F2F | SHA256:83373FCFA1876A3C119B571D801BBE7EBE826956971EFC9367BEF3627010EFFF | |||
| 7664 | 613b31ed6f4c1c534cfe3004fe7741ca3ac080f99d22e1b0af9d80eb1add9e1c.exe | C:\Program Files\绿色软件\Foxit Reader\FoxitReader_Preferences.ini | text | |
MD5:6FD18F8581A1BFE035AAEEC18F8853AE | SHA256:B634F1714C7E46840B0F9F59D024899A7C4229BFC0A4E11CB6C837D872E32AD3 | |||
| 7664 | 613b31ed6f4c1c534cfe3004fe7741ca3ac080f99d22e1b0af9d80eb1add9e1c.exe | C:\Program Files\绿色软件\ipmsg.exe | executable | |
MD5:E9C2B5D1ECC1C316B0BE8ED0CF5786E4 | SHA256:68C56D45D236FF7C08F6610DBB3C6643A79A16102F4174A6FDA3ACDC9F86CF07 | |||
| 7664 | 613b31ed6f4c1c534cfe3004fe7741ca3ac080f99d22e1b0af9d80eb1add9e1c.exe | C:\Program Files\装机人员工具\键盘测试\KEYBOARDTEST.HLP | binary | |
MD5:B97D7F5BC46EA55850D2074EECDB6C2A | SHA256:5FD69AEB8FBA7FB002E28FCDA01AFA0C35E7DD75D81519E638246868B2C116C9 | |||
| 7664 | 613b31ed6f4c1c534cfe3004fe7741ca3ac080f99d22e1b0af9d80eb1add9e1c.exe | C:\Program Files\装机人员工具\DisplayX.exe | executable | |
MD5:52978CB9C209F1A8802D6228210B0F6D | SHA256:1F6D012842350E00445FE28BBCE4D1B74DF56A7D14D879825CDA4B610FCF7B86 | |||
| 7664 | 613b31ed6f4c1c534cfe3004fe7741ca3ac080f99d22e1b0af9d80eb1add9e1c.exe | C:\Program Files\装机人员工具\CPUZ\cpuz.exe | executable | |
MD5:81D379591CCBC6B9BD4B65B54ADB92D4 | SHA256:3B03EC50A05CA47158FDB6792ABF908A9F49BE8263DA18B7B8A50F49D3F1A4A4 | |||
| 7664 | 613b31ed6f4c1c534cfe3004fe7741ca3ac080f99d22e1b0af9d80eb1add9e1c.exe | C:\Program Files\装机人员工具\Everest\everest.exe | executable | |
MD5:38A73E6B19F84FFD5BC853F828CBDA77 | SHA256:7D09FC3430421397751A7C040D178FD40A8AAE86D88669B67A24145F7C4E1393 | |||
| 7664 | 613b31ed6f4c1c534cfe3004fe7741ca3ac080f99d22e1b0af9d80eb1add9e1c.exe | C:\Program Files\装机人员工具\OEMDIY.EXE | executable | |
MD5:FFD97BB41E9E53EDEFB0DACB274C0F27 | SHA256:0C45684CDBDE41051FBE915A56BD85C7446A1BFF436A9B9530561380D11C5E2B | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
19
DNS requests
13
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.216.77.25:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
7348 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
7348 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 23.216.77.25:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6544 | svchost.exe | 20.190.160.64:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 184.30.131.245:80 | ocsp.digicert.com | AKAMAI-AS | US | whitelisted |
— | — | 172.211.123.249:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4244 | RUXIMICS.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2104 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |