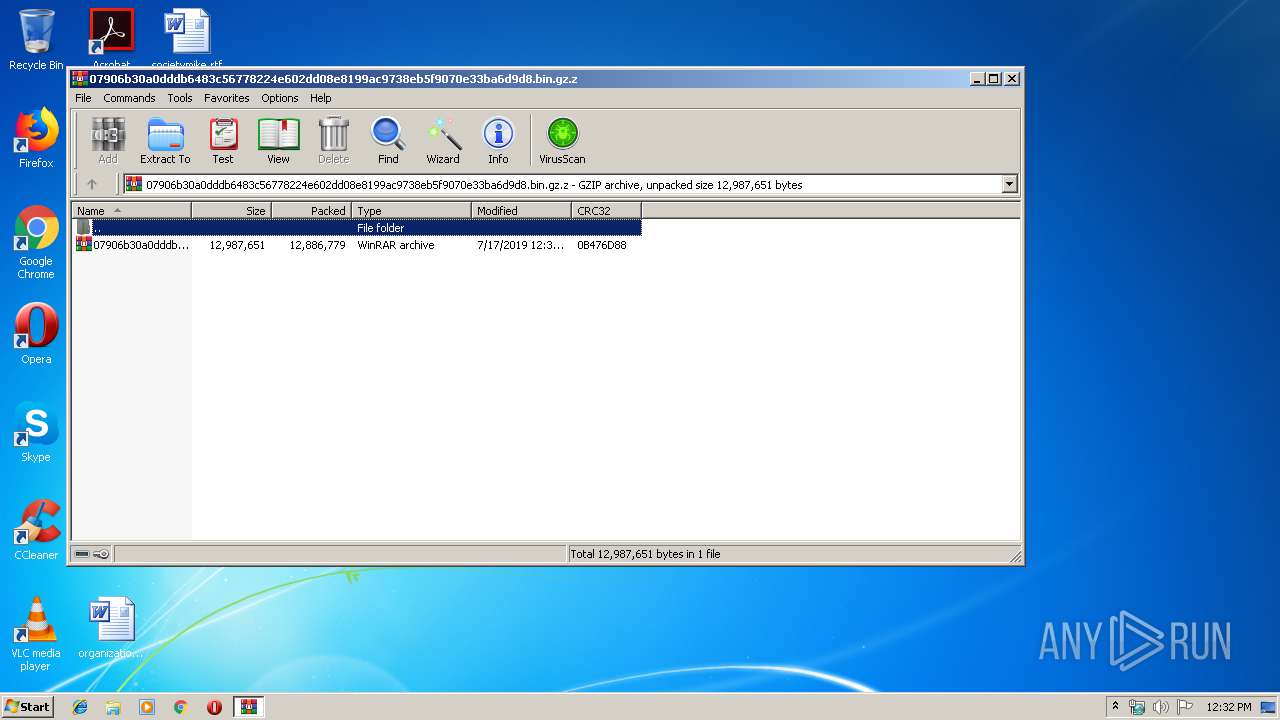
| File name: | 07906b30a0dddb6483c56778224e602dd08e8199ac9738eb5f9070e33ba6d9d8.bin.gz |
| Full analysis: | https://app.any.run/tasks/c4574029-cd1d-46f5-b6d9-37fb3d72498f |
| Verdict: | Malicious activity |
| Analysis date: | July 17, 2019, 11:31:41 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/gzip |
| File info: | gzip compressed data, max compression, from Unix |
| MD5: | 775DCC158F8E83360746C1928E05A5A0 |
| SHA1: | 4BAC37086F9594F33D4CD4D3DF96BCA70105B5EF |
| SHA256: | 61359BE1C81909C7CDFDEB97F6B537FB60A897931044A084E9275B035A4E5923 |
| SSDEEP: | 393216:0jjVyHaT+BqZ8ElAXBcBZynvOTIfJXfq3zj:0vV7+k8sci8vOEflfO |
MALICIOUS
Application was dropped or rewritten from another process
- 07906b30a0dddb6483c56778224e602dd08e8199ac9738eb5f9070e33ba6d9d8.bin.exe (PID: 2268)
- 07906b30a0dddb6483c56778224e602dd08e8199ac9738eb5f9070e33ba6d9d8.bin.exe (PID: 2412)
- Setup.exe (PID: 2804)
- IKernel.exe (PID: 3620)
- IKernel.exe (PID: 3588)
- iKernel.exe (PID: 2836)
- iKernel.exe (PID: 3676)
Loads dropped or rewritten executable
- Setup.exe (PID: 2804)
- IKernel.exe (PID: 3620)
SUSPICIOUS
Creates files in the program directory
- Setup.exe (PID: 2804)
- IKernel.exe (PID: 3620)
Executable content was dropped or overwritten
- Setup.exe (PID: 2804)
- 07906b30a0dddb6483c56778224e602dd08e8199ac9738eb5f9070e33ba6d9d8.bin.exe (PID: 2412)
- IKernel.exe (PID: 3620)
Executed via COM
- IKernel.exe (PID: 3620)
- DllHost.exe (PID: 3636)
- DrvInst.exe (PID: 3660)
Creates COM task schedule object
- IKernel.exe (PID: 3620)
Starts itself from another location
- IKernel.exe (PID: 3620)
Searches for installed software
- IKernel.exe (PID: 3620)
- DllHost.exe (PID: 3636)
Executed as Windows Service
- vssvc.exe (PID: 2584)
INFO
Manual execution by user
- 07906b30a0dddb6483c56778224e602dd08e8199ac9738eb5f9070e33ba6d9d8.bin.exe (PID: 2268)
- 07906b30a0dddb6483c56778224e602dd08e8199ac9738eb5f9070e33ba6d9d8.bin.exe (PID: 2412)
Low-level read access rights to disk partition
- vssvc.exe (PID: 2584)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .z/gz/gzip | | | GZipped data (100) |
|---|
EXIF
ZIP
| Compression: | Deflated |
|---|---|
| Flags: | (none) |
| ModifyDate: | 0000:00:00 00:00:00 |
| ExtraFlags: | Maximum Compression |
| OperatingSystem: | Unix |
Total processes
50
Monitored processes
11
Malicious processes
1
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2268 | "C:\Users\admin\Desktop\07906b30a0dddb6483c56778224e602dd08e8199ac9738eb5f9070e33ba6d9d8.bin.exe" | C:\Users\admin\Desktop\07906b30a0dddb6483c56778224e602dd08e8199ac9738eb5f9070e33ba6d9d8.bin.exe | — | explorer.exe | |||||||||||
User: admin Company: 经营者集中反垄断审查申报书 Integrity Level: MEDIUM Exit code: 3221226540 Version: 1.00.000 Modules
| |||||||||||||||
| 2412 | "C:\Users\admin\Desktop\07906b30a0dddb6483c56778224e602dd08e8199ac9738eb5f9070e33ba6d9d8.bin.exe" | C:\Users\admin\Desktop\07906b30a0dddb6483c56778224e602dd08e8199ac9738eb5f9070e33ba6d9d8.bin.exe | explorer.exe | ||||||||||||
User: admin Company: 经营者集中反垄断审查申报书 Integrity Level: HIGH Exit code: 0 Version: 1.00.000 Modules
| |||||||||||||||
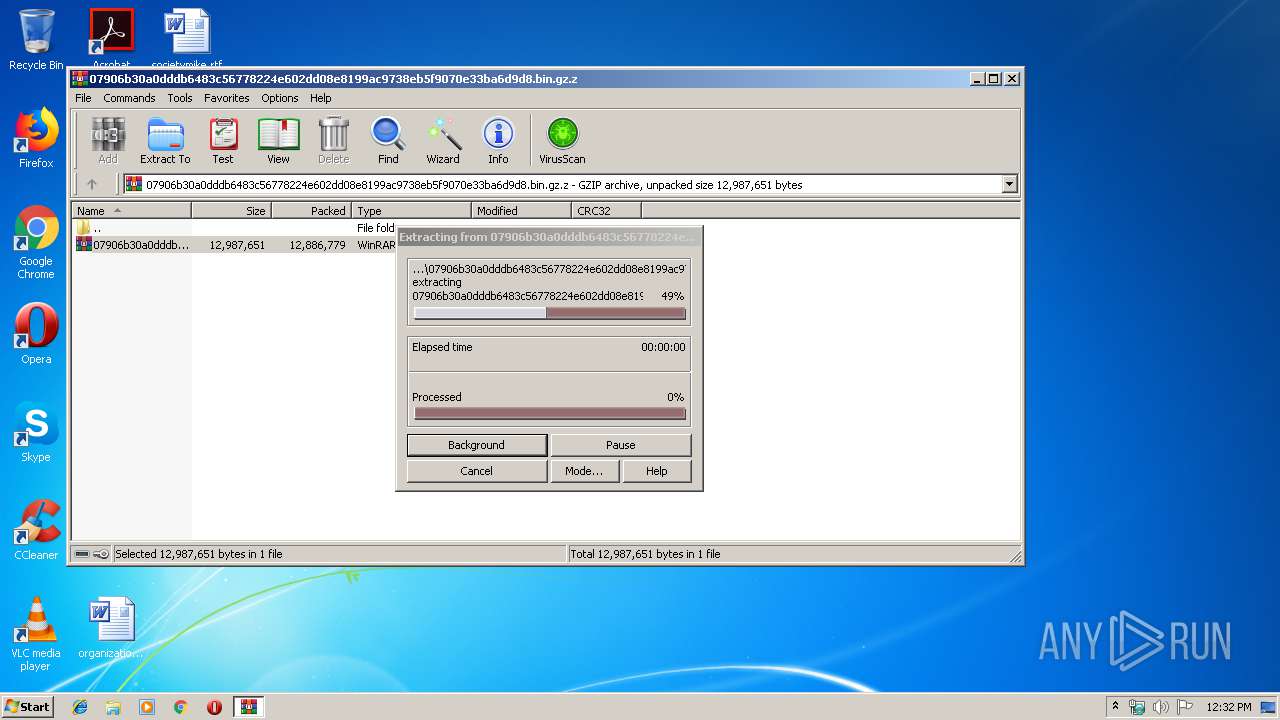
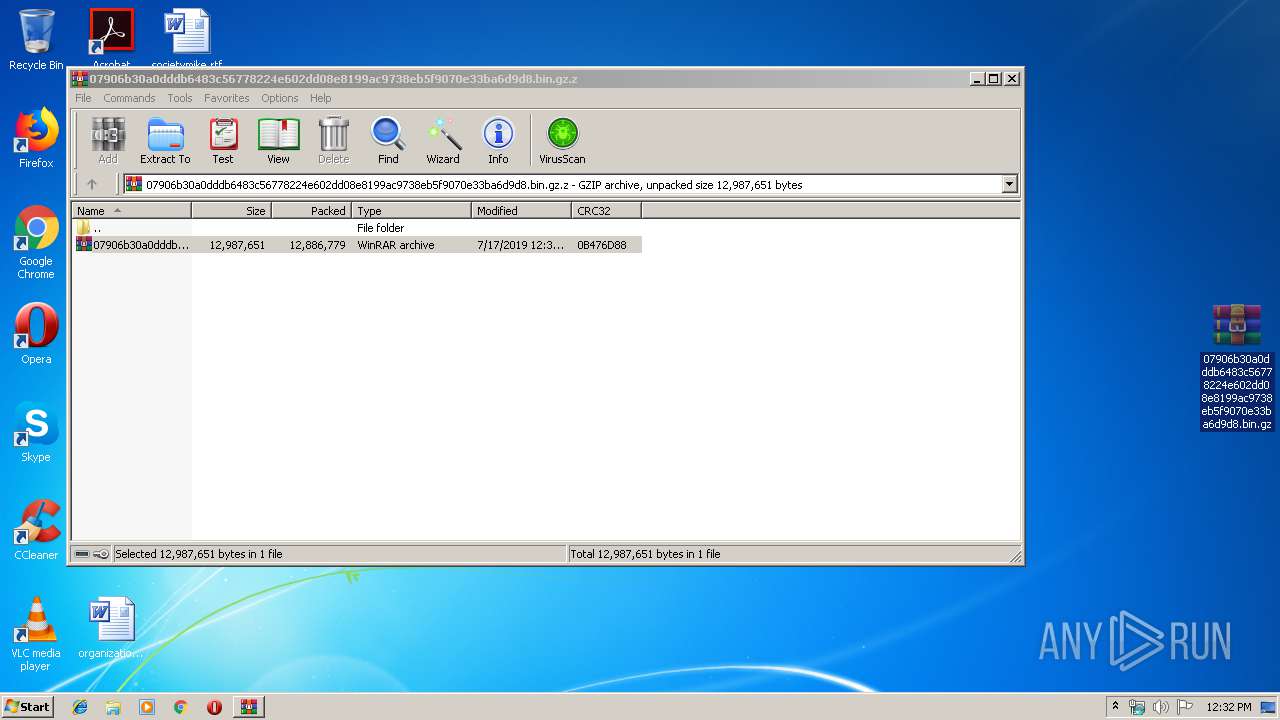
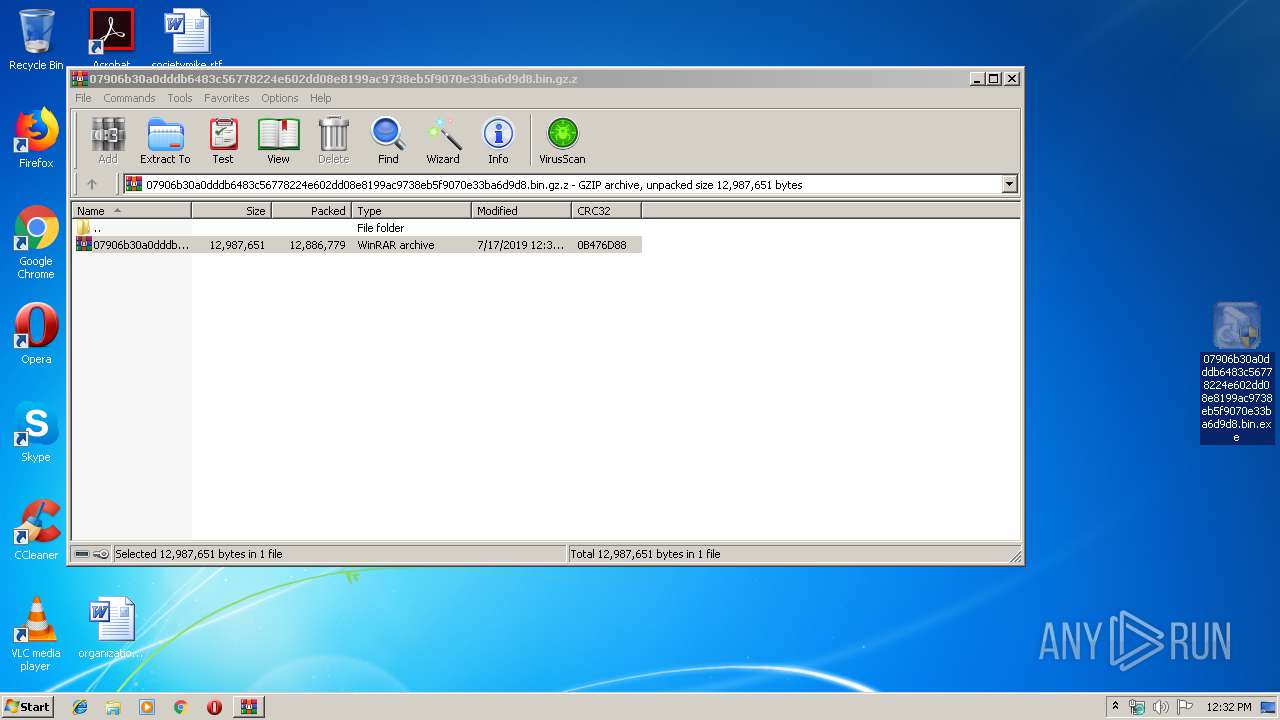
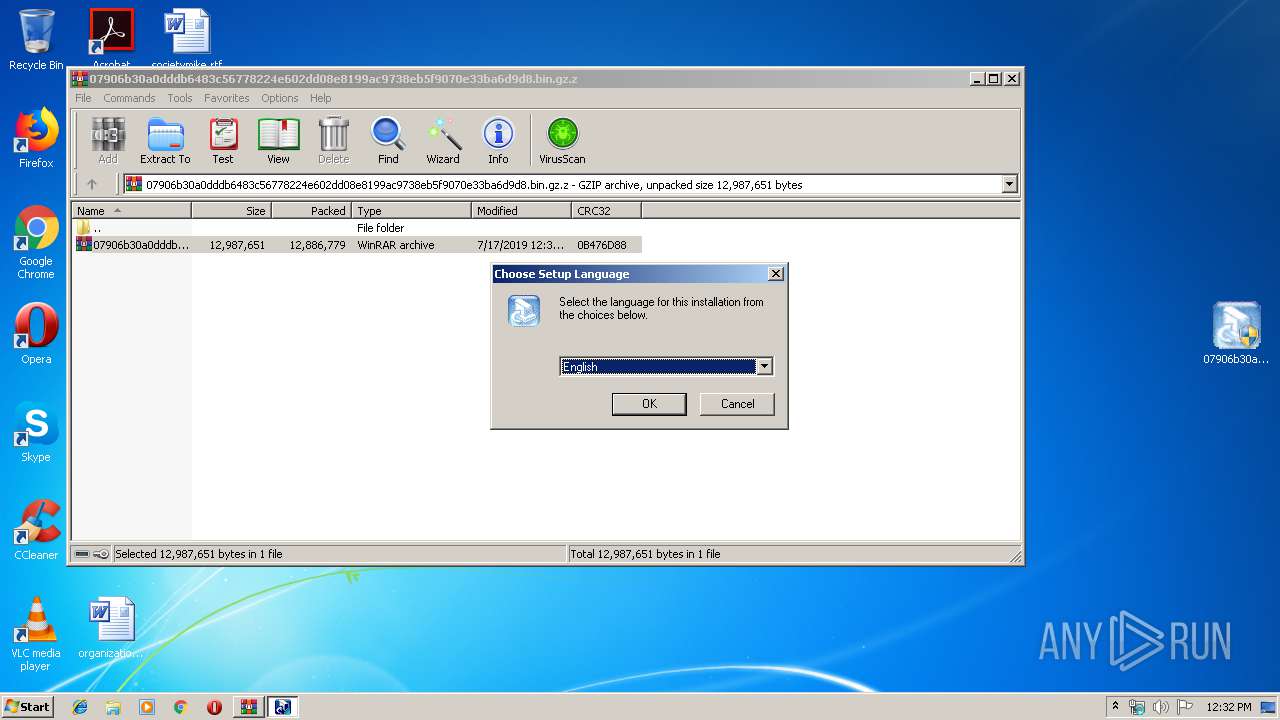
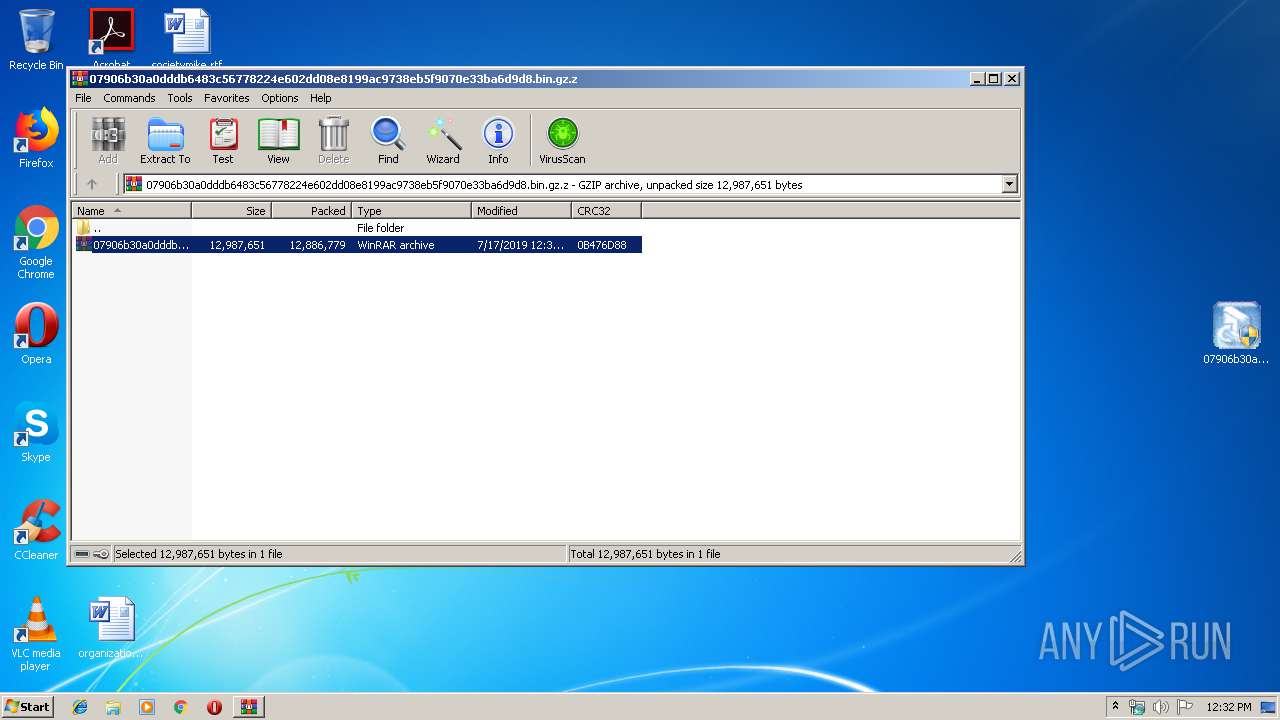
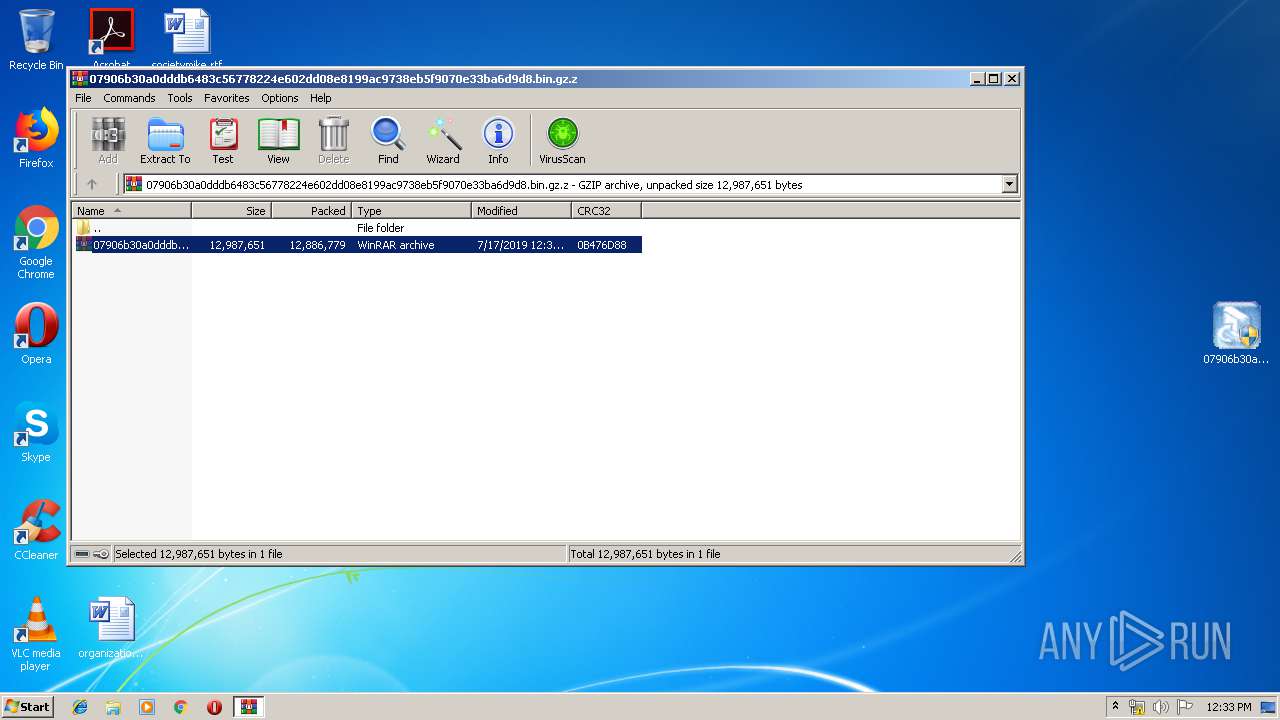
| 2480 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Desktop\07906b30a0dddb6483c56778224e602dd08e8199ac9738eb5f9070e33ba6d9d8.bin.gz.z" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 2584 | C:\Windows\system32\vssvc.exe | C:\Windows\system32\vssvc.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
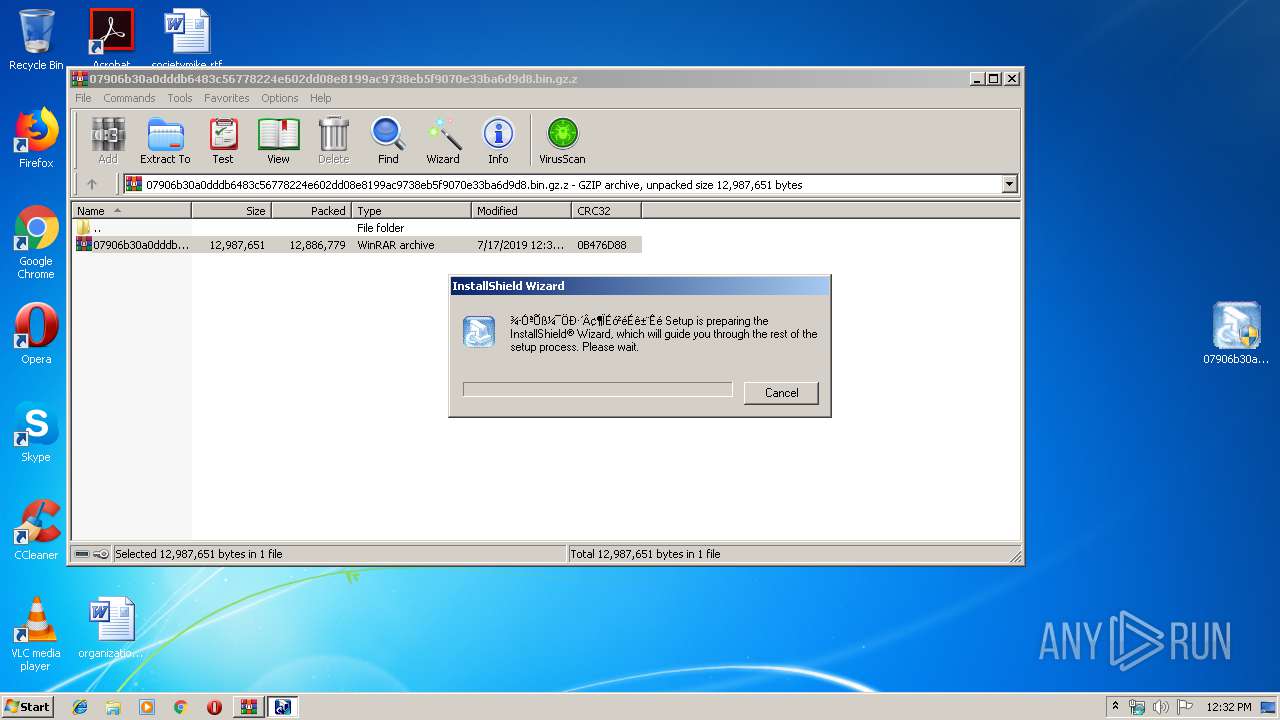
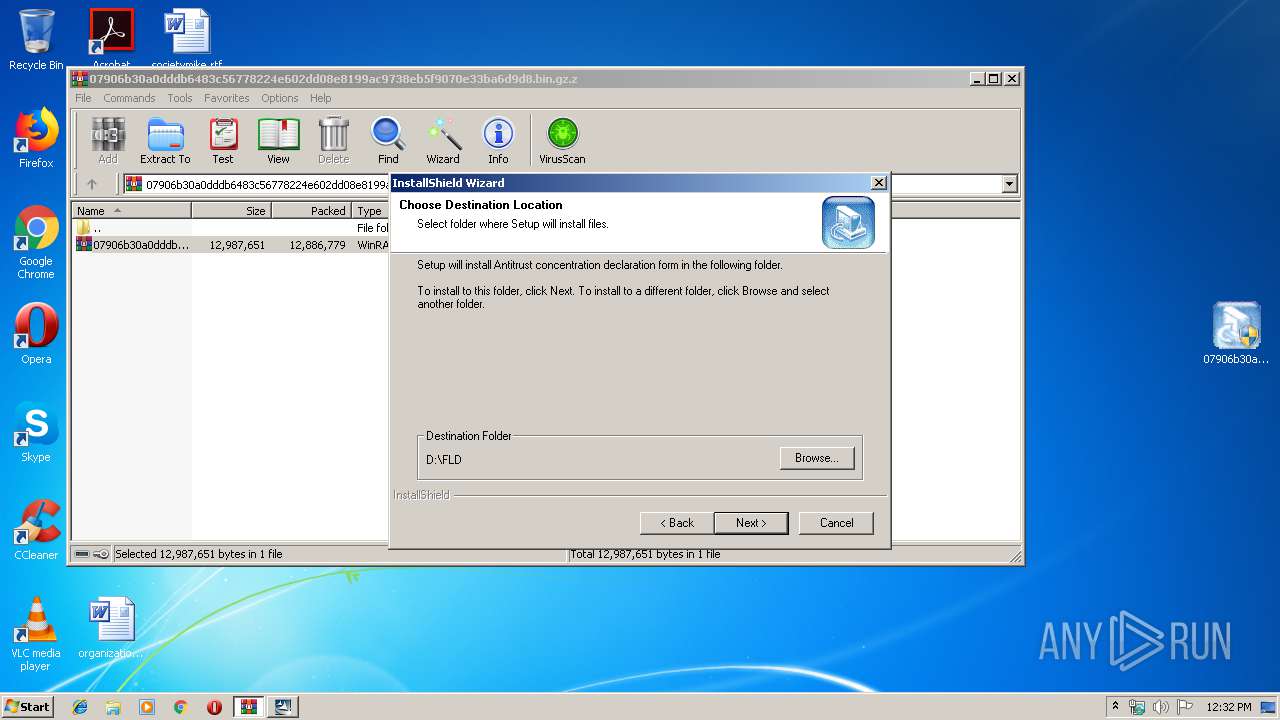
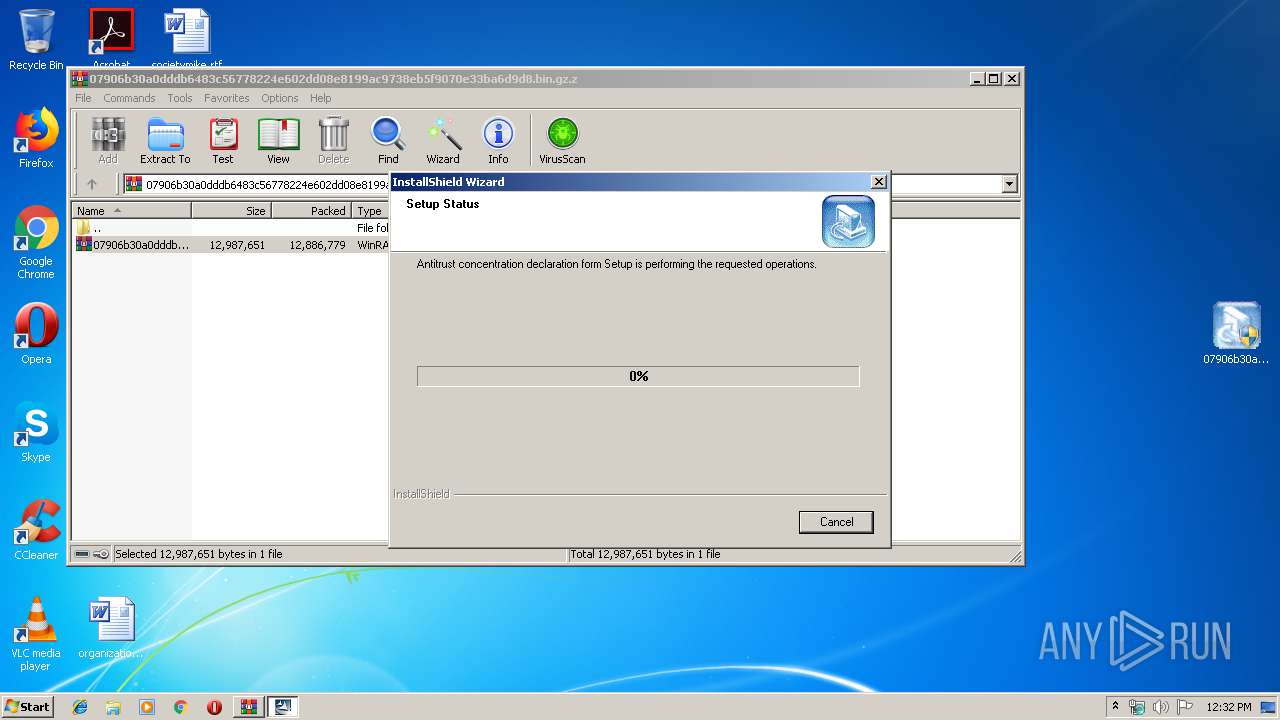
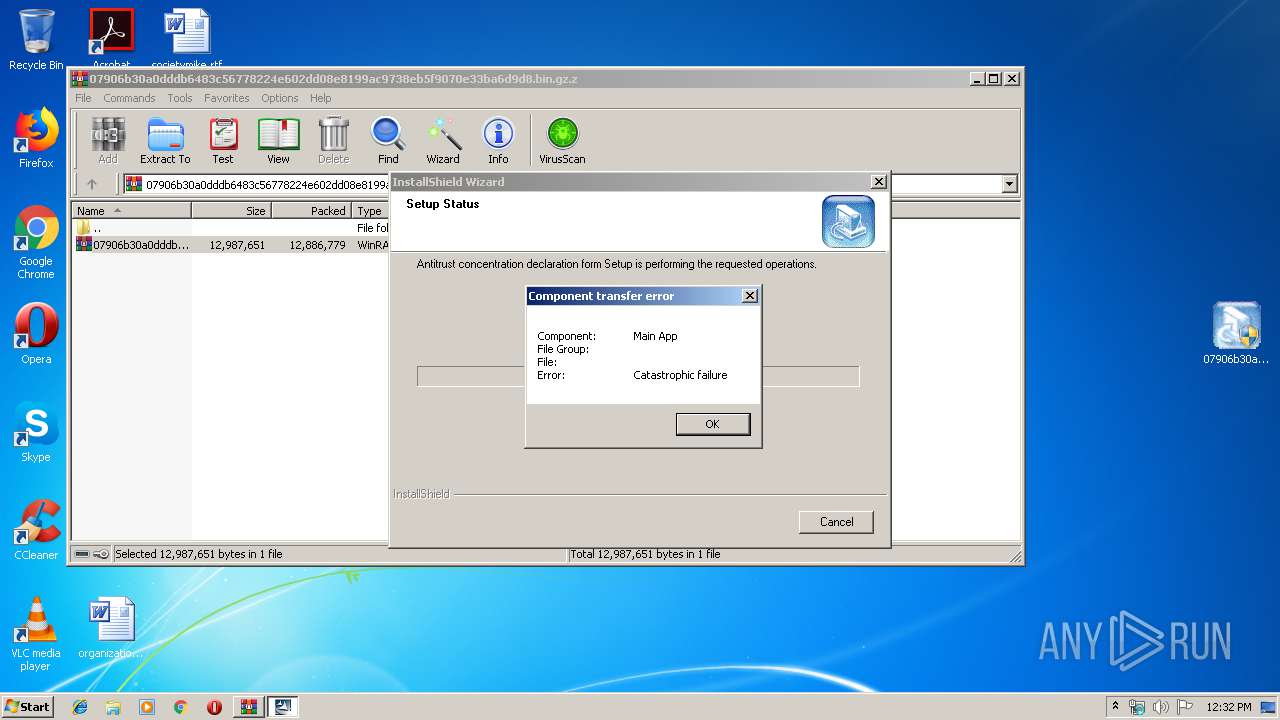
| 2804 | "C:\Users\admin\AppData\Local\Temp\pft5B5E~tmp\Disk1\Setup.exe" | C:\Users\admin\AppData\Local\Temp\pft5B5E~tmp\Disk1\Setup.exe | 07906b30a0dddb6483c56778224e602dd08e8199ac9738eb5f9070e33ba6d9d8.bin.exe | ||||||||||||
User: admin Company: InstallShield Software Corporation Integrity Level: HIGH Description: InstallShield (R) Setup Launcher Exit code: 0 Version: 6, 30, 100, 1255 Modules
| |||||||||||||||
| 2836 | "C:\Program Files\Common Files\InstallShield\engine\6\Intel 32\iKernel.exe" /REGSERVER | C:\Program Files\Common Files\InstallShield\engine\6\Intel 32\iKernel.exe | — | IKernel.exe | |||||||||||
User: admin Company: InstallShield Software Corporation Integrity Level: HIGH Description: InstallShield (R) Setup Engine Exit code: 0 Version: 6, 31, 100, 1221 Modules
| |||||||||||||||
| 3588 | "C:\Program Files\Common Files\InstallShield\Engine\6\Intel 32\IKernel.exe" -RegServer | C:\Program Files\Common Files\InstallShield\Engine\6\Intel 32\IKernel.exe | — | Setup.exe | |||||||||||
User: admin Company: InstallShield Software Corporation Integrity Level: HIGH Description: InstallShield (R) Setup Engine Exit code: 0 Version: 6, 31, 100, 1221 Modules
| |||||||||||||||
| 3620 | C:\PROGRA~1\COMMON~1\INSTAL~1\Engine\6\INTEL3~1\IKernel.exe -Embedding | C:\PROGRA~1\COMMON~1\INSTAL~1\Engine\6\INTEL3~1\IKernel.exe | svchost.exe | ||||||||||||
User: admin Company: InstallShield Software Corporation Integrity Level: HIGH Description: InstallShield (R) Setup Engine Exit code: 0 Version: 6, 31, 100, 1221 Modules
| |||||||||||||||
| 3636 | C:\Windows\system32\DllHost.exe /Processid:{F32D97DF-E3E5-4CB9-9E3E-0EB5B4E49801} | C:\Windows\system32\DllHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3660 | DrvInst.exe "1" "200" "STORAGE\VolumeSnapshot\HarddiskVolumeSnapshot21" "" "" "6f9bf5bcb" "00000000" "00000538" "000005C0" | C:\Windows\system32\DrvInst.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Driver Installation Module Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 780
Read events
710
Write events
694
Delete events
376
Modification events
| (PID) Process: | (2480) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2480) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2480) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\70\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2480) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\07906b30a0dddb6483c56778224e602dd08e8199ac9738eb5f9070e33ba6d9d8.bin.gz.z | |||
| (PID) Process: | (2480) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2480) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2480) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2480) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (3588) IKernel.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\Setup.Kernel.1 |
| Operation: | write | Name: | |
Value: InstallShield setup kernel | |||
| (PID) Process: | (3588) IKernel.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\Setup.Kernel.1\CLSID |
| Operation: | write | Name: | |
Value: {91814EC0-B5F0-11D2-80B9-00104B1F6CEA} | |||
Executable files
8
Suspicious files
7
Text files
127
Unknown types
5
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2480 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2480.14020\07906b30a0dddb6483c56778224e602dd08e8199ac9738eb5f9070e33ba6d9d8.bin.gz | — | |
MD5:— | SHA256:— | |||
| 2412 | 07906b30a0dddb6483c56778224e602dd08e8199ac9738eb5f9070e33ba6d9d8.bin.exe | C:\Users\admin\AppData\Local\Temp\ext5B3D.tmp | — | |
MD5:— | SHA256:— | |||
| 2412 | 07906b30a0dddb6483c56778224e602dd08e8199ac9738eb5f9070e33ba6d9d8.bin.exe | C:\Users\admin\AppData\Local\Temp\pft5B5E~tmp\pftw1.pkg | — | |
MD5:— | SHA256:— | |||
| 2412 | 07906b30a0dddb6483c56778224e602dd08e8199ac9738eb5f9070e33ba6d9d8.bin.exe | C:\Users\admin\AppData\Local\Temp\pft5B5E~tmp\Disk1\data2.cab | — | |
MD5:— | SHA256:— | |||
| 2804 | Setup.exe | C:\Program Files\Common Files\InstallShield\Engine\6\Intel 32\temp.000 | — | |
MD5:— | SHA256:— | |||
| 3620 | IKernel.exe | C:\Program Files\Common Files\InstallShield\engine\6\Intel 32\core6a9e.rra | — | |
MD5:— | SHA256:— | |||
| 3620 | IKernel.exe | C:\Program Files\Common Files\InstallShield\engine\6\Intel 32\ctor6aad.rra | — | |
MD5:— | SHA256:— | |||
| 3620 | IKernel.exe | C:\Program Files\Common Files\InstallShield\engine\6\Intel 32\obje6b1b.rra | — | |
MD5:— | SHA256:— | |||
| 3620 | IKernel.exe | C:\Program Files\Common Files\InstallShield\engine\6\Intel 32\iuse6b3a.rra | — | |
MD5:— | SHA256:— | |||
| 3620 | IKernel.exe | C:\Program Files\Common Files\InstallShield\IScript\iscr6be6.rra | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report