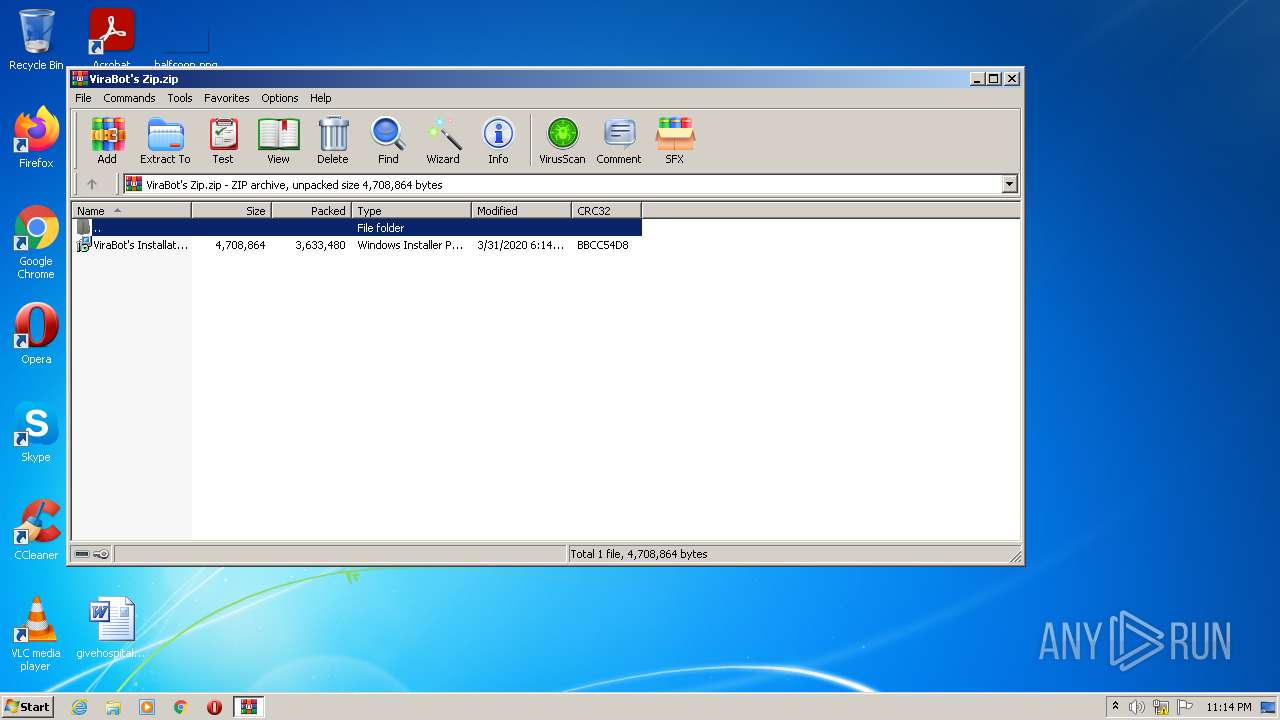
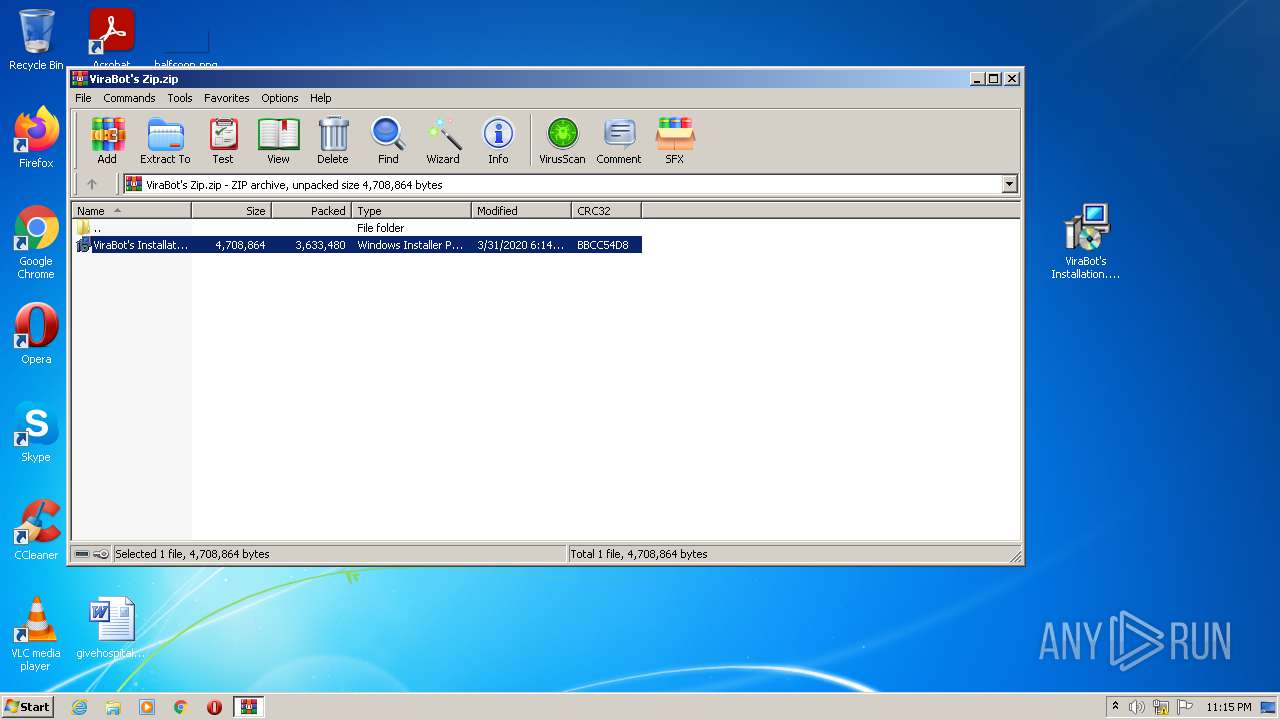
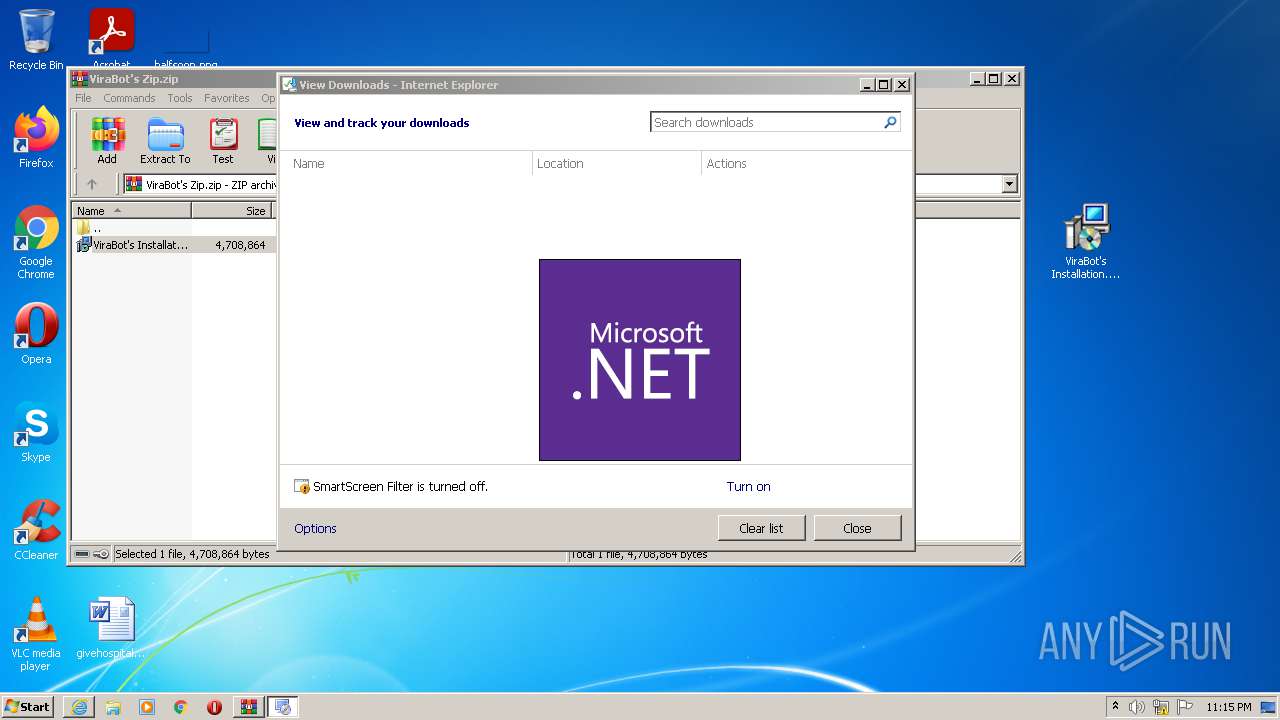
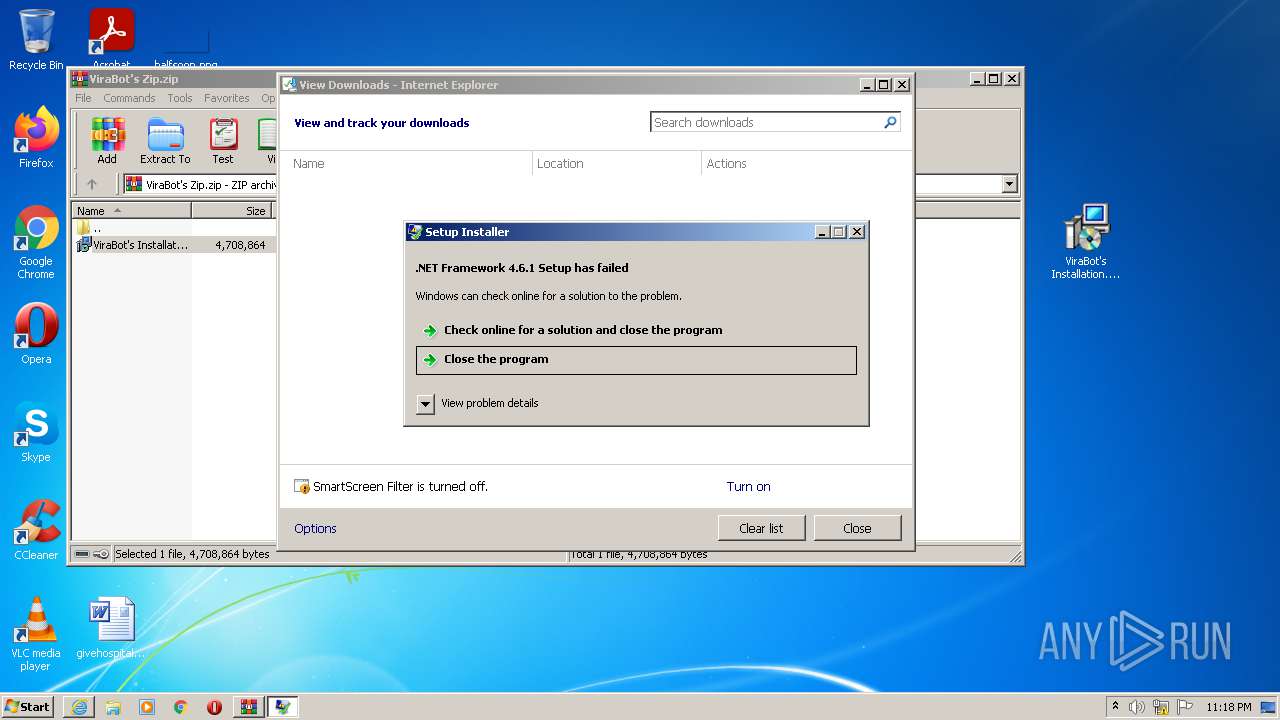
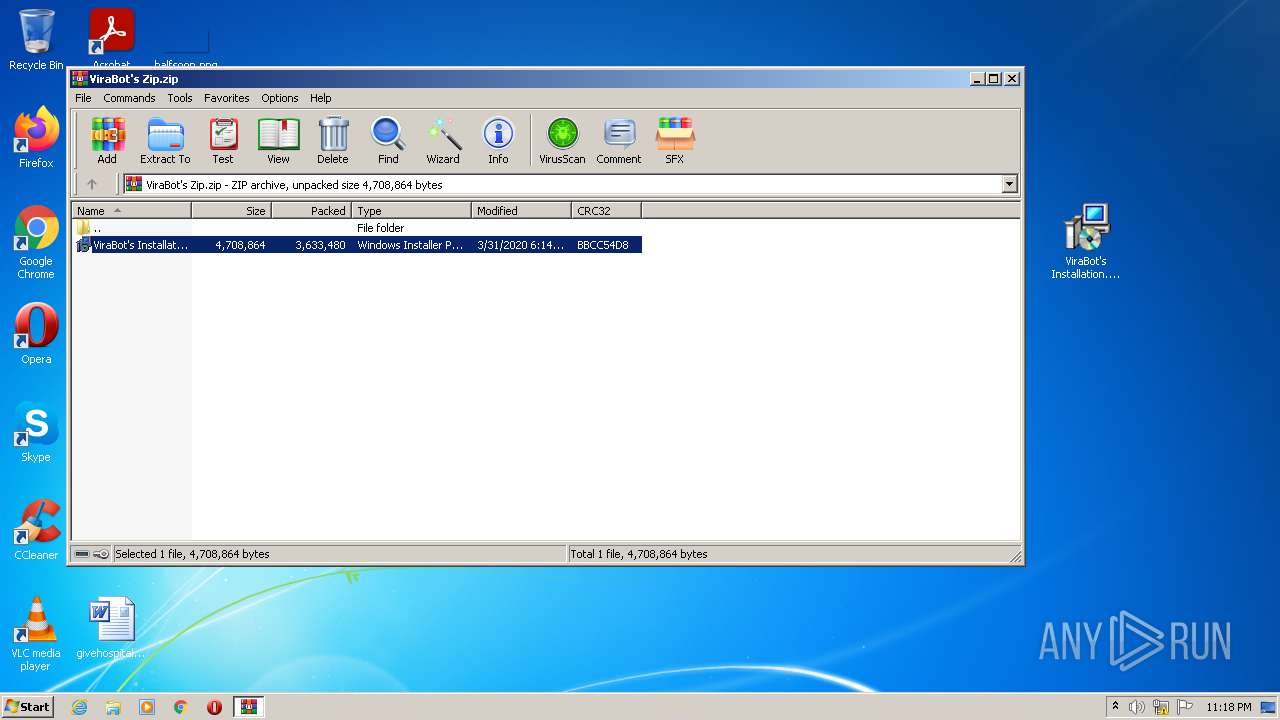
| File name: | ViraBot's Zip.zip |
| Full analysis: | https://app.any.run/tasks/dc047c52-19ed-4d5f-8a93-4643b97b4a0d |
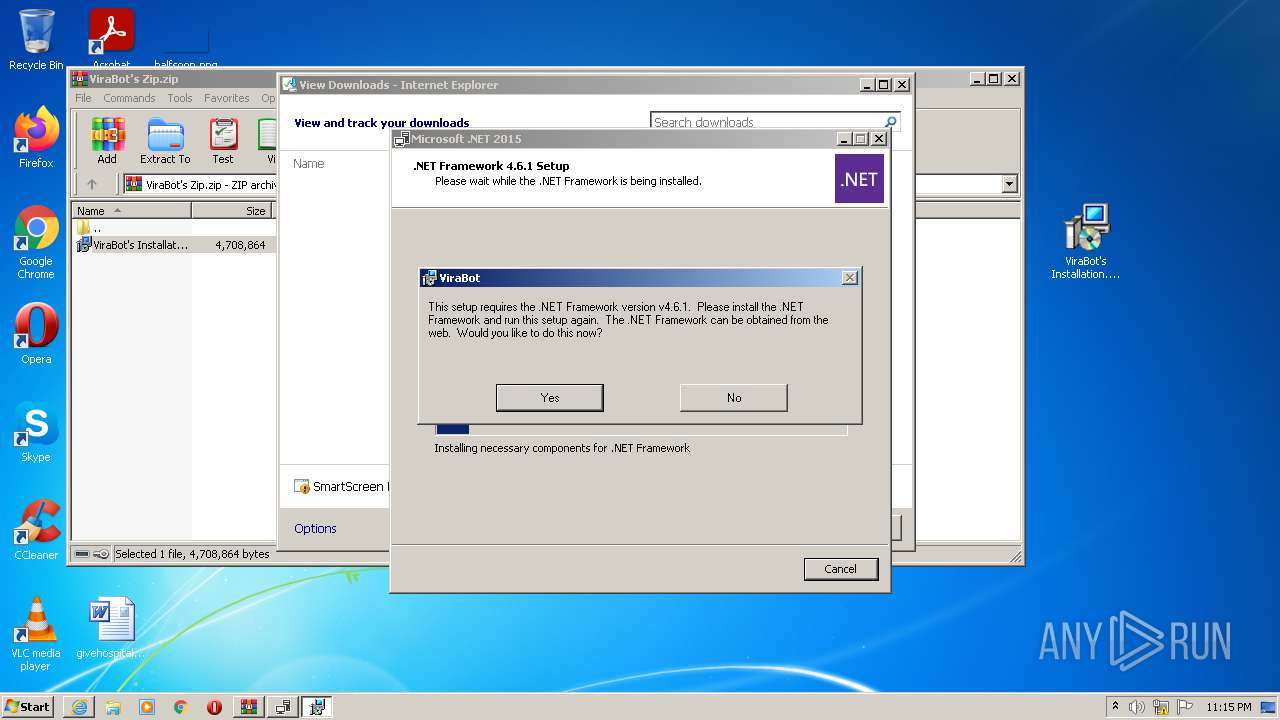
| Verdict: | Malicious activity |
| Analysis date: | August 11, 2021, 22:14:39 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | B7B2BD573CA9D60392CCC72267F23956 |
| SHA1: | 17C2E1C8A145AC86406ECFD50773DA2B76EF3549 |
| SHA256: | 612B69432A2B40CDB095C634717A93AFADEAD8E9A20C1958C5FD76C983797C87 |
| SSDEEP: | 98304:7vSc3xnGvv1/1cDOd2tUMpCgDYkqcgj8gVWw1lhy5xER:7vRhna1caQLpCMYkqlIgNwA |
MALICIOUS
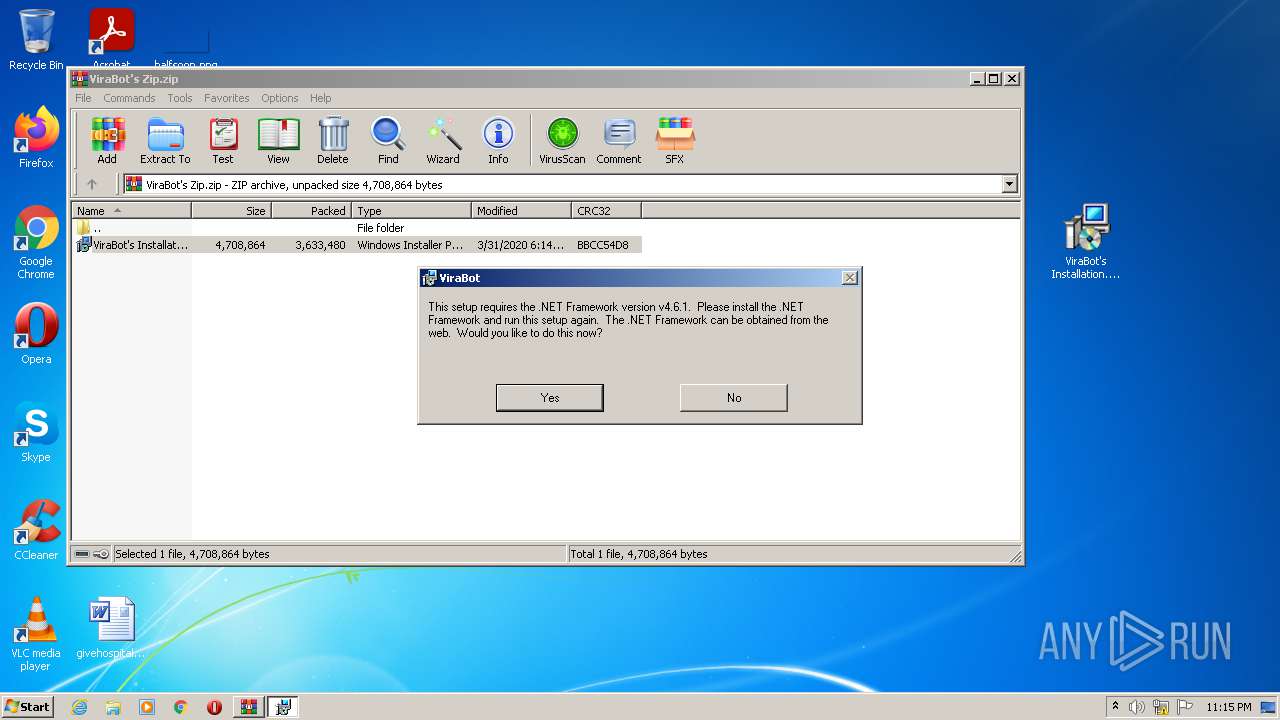
Loads dropped or rewritten executable
- MsiExec.exe (PID: 2072)
- Setup.exe (PID: 3988)
- MsiExec.exe (PID: 2680)
- MsiExec.exe (PID: 2748)
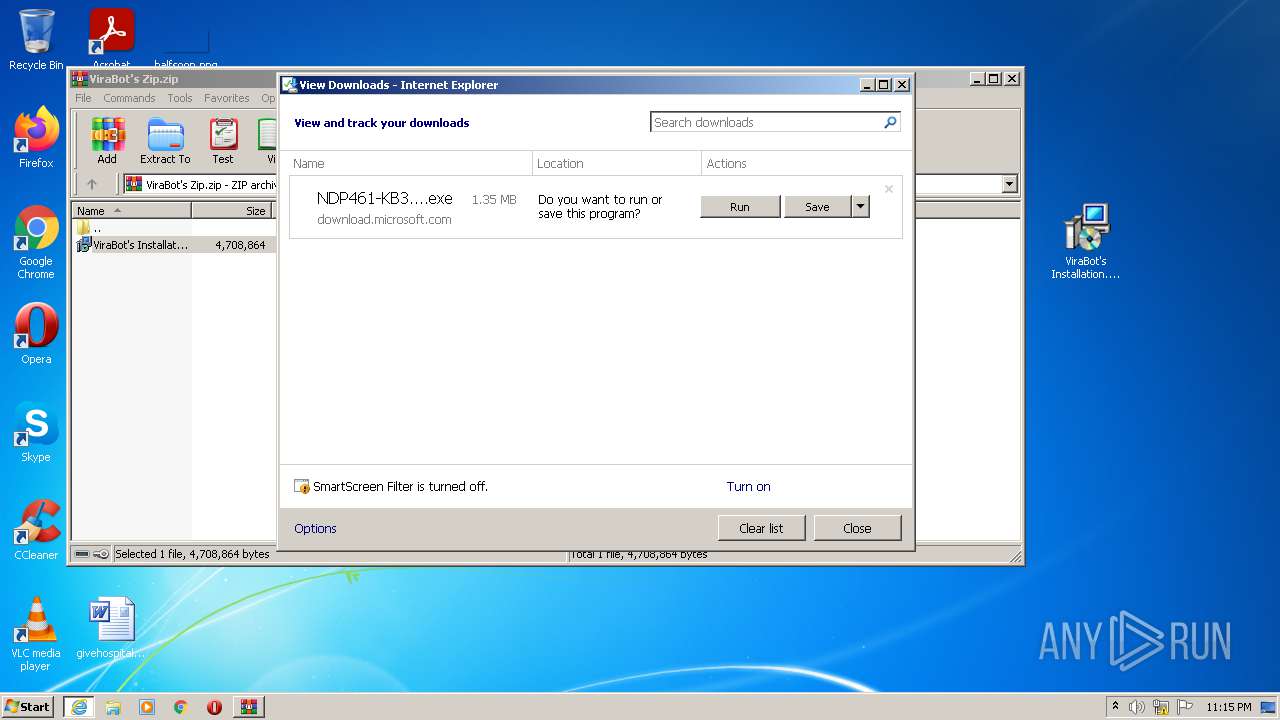
Drops executable file immediately after starts
- msiexec.exe (PID: 3544)
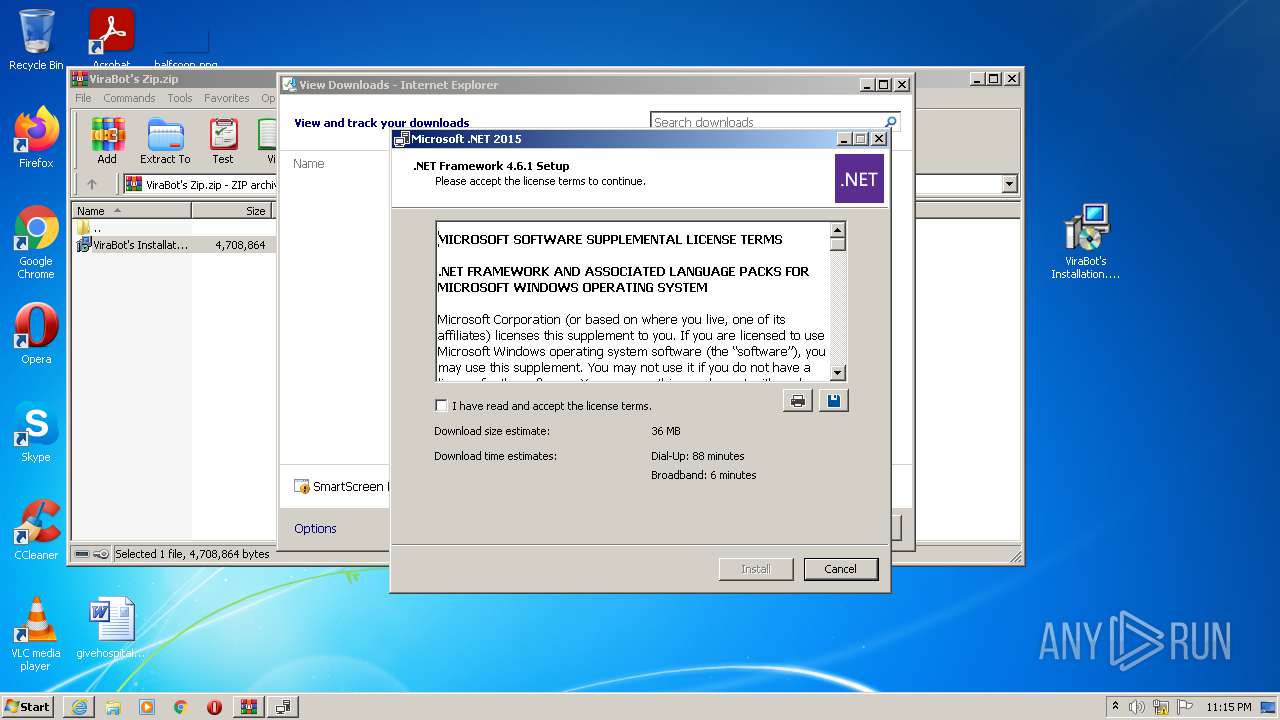
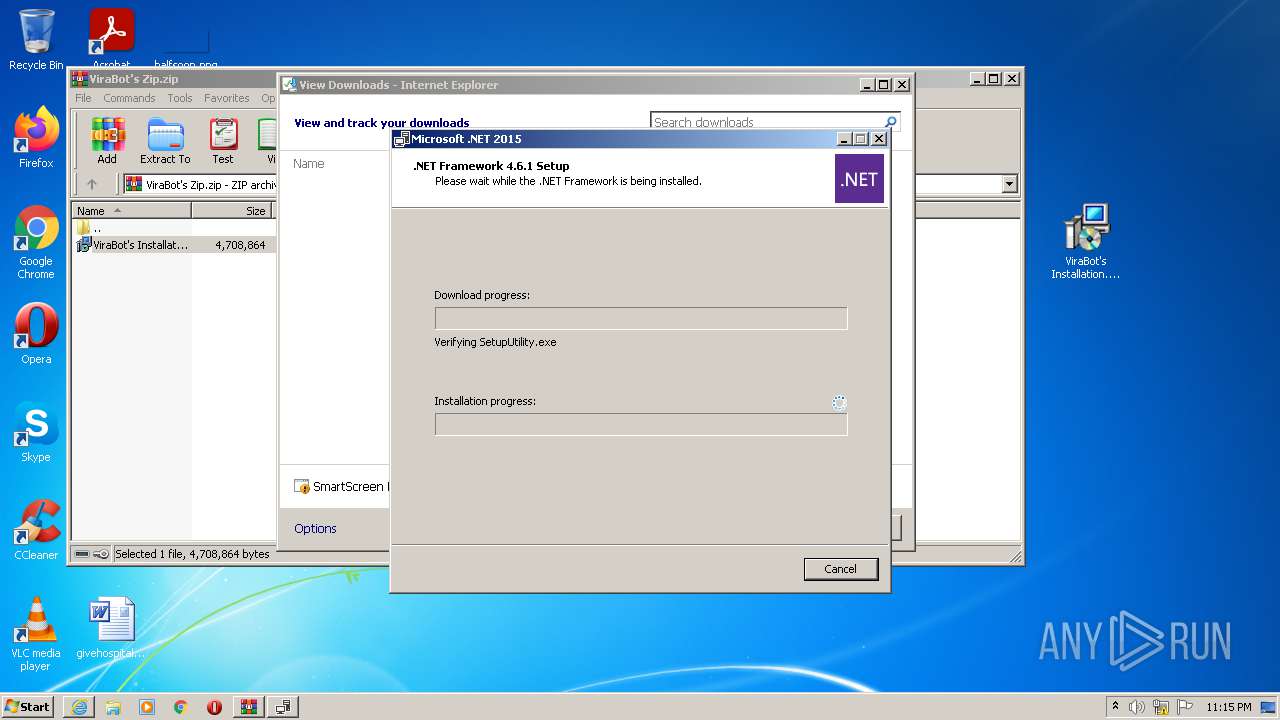
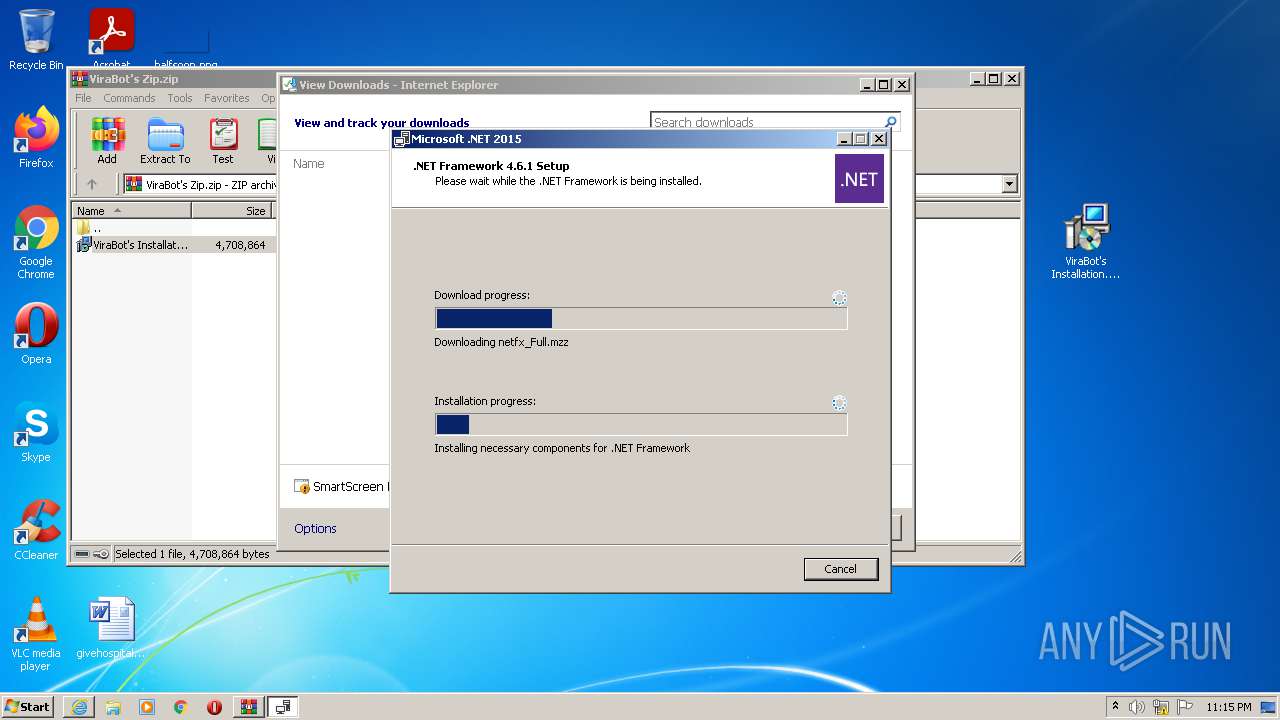
- NDP461-KB3102438-Web.exe (PID: 3552)
- msiexec.exe (PID: 3520)
- msiexec.exe (PID: 400)
Application was dropped or rewritten from another process
- NDP461-KB3102438-Web.exe (PID: 2664)
- Setup.exe (PID: 3988)
- SetupUtility.exe (PID: 748)
- SetupUtility.exe (PID: 4048)
- NDP461-KB3102438-Web.exe (PID: 3552)
Actions looks like stealing of personal data
- NDP461-KB3102438-Web.exe (PID: 3552)
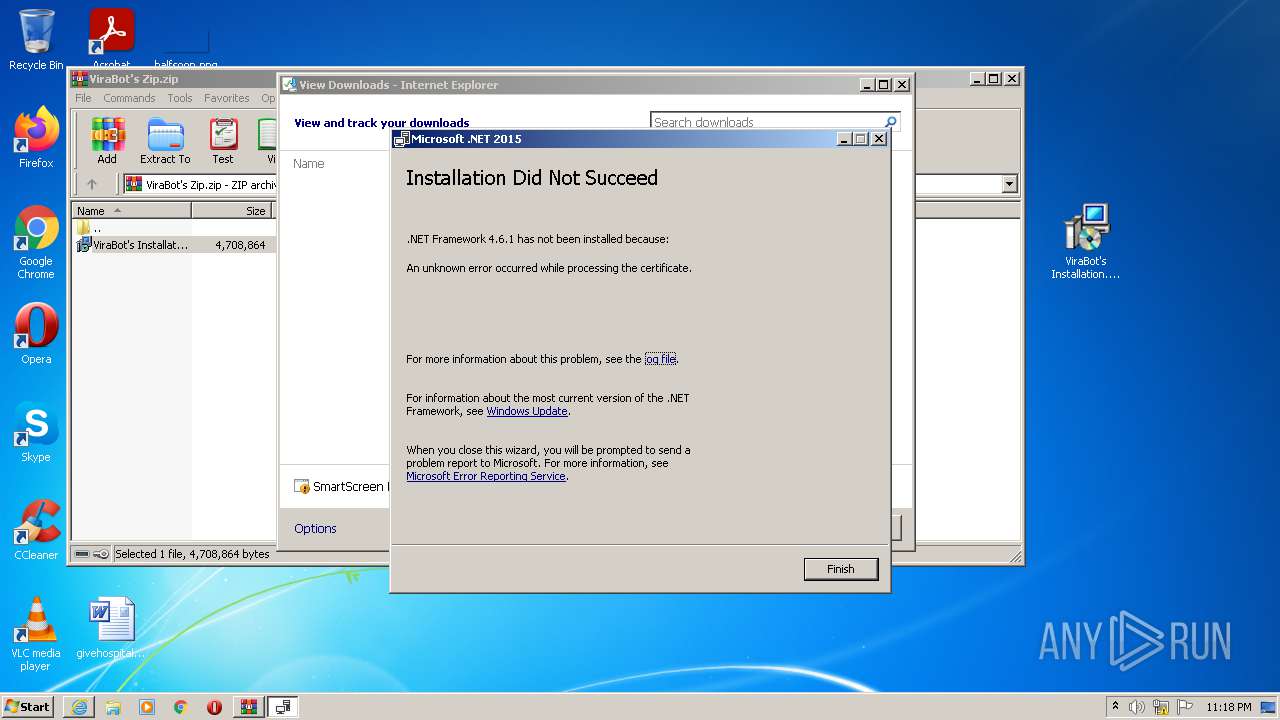
Changes settings of System certificates
- Setup.exe (PID: 3988)
SUSPICIOUS
Reads the Windows organization settings
- msiexec.exe (PID: 3544)
- msiexec.exe (PID: 3520)
- msiexec.exe (PID: 400)
Checks supported languages
- WinRAR.exe (PID: 2300)
- NDP461-KB3102438-Web.exe (PID: 3552)
- Setup.exe (PID: 3988)
- SetupUtility.exe (PID: 4048)
- SetupUtility.exe (PID: 748)
- TMP3F7D.tmp.exe (PID: 3292)
Reads the computer name
- WinRAR.exe (PID: 2300)
- NDP461-KB3102438-Web.exe (PID: 3552)
- Setup.exe (PID: 3988)
- SetupUtility.exe (PID: 748)
- SetupUtility.exe (PID: 4048)
- TMP3F7D.tmp.exe (PID: 3292)
Executed as Windows Service
- msiexec.exe (PID: 3724)
Reads Windows owner or organization settings
- msiexec.exe (PID: 3544)
- msiexec.exe (PID: 3520)
- msiexec.exe (PID: 400)
Application launched itself
- msiexec.exe (PID: 3724)
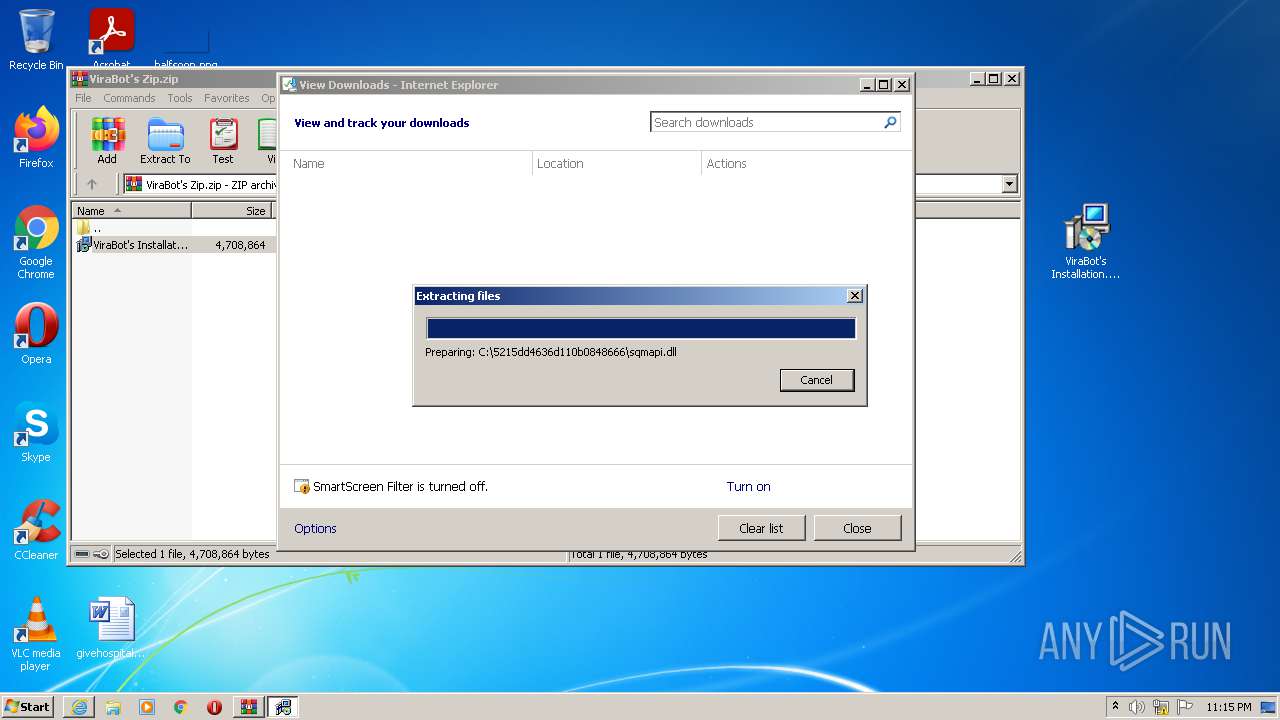
Executable content was dropped or overwritten
- msiexec.exe (PID: 3544)
- iexplore.exe (PID: 3748)
- iexplore.exe (PID: 316)
- msiexec.exe (PID: 3520)
- msiexec.exe (PID: 400)
- Setup.exe (PID: 3988)
- TMP3F7D.tmp.exe (PID: 3292)
- NDP461-KB3102438-Web.exe (PID: 3552)
Drops a file that was compiled in debug mode
- msiexec.exe (PID: 3544)
- iexplore.exe (PID: 316)
- iexplore.exe (PID: 3748)
- NDP461-KB3102438-Web.exe (PID: 3552)
- msiexec.exe (PID: 3520)
- msiexec.exe (PID: 400)
Starts Internet Explorer
- MsiExec.exe (PID: 2072)
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 316)
Reads CPU info
- Setup.exe (PID: 3988)
Reads Environment values
- Setup.exe (PID: 3988)
Creates files in the program directory
- Setup.exe (PID: 3988)
INFO
Manual execution by user
- msiexec.exe (PID: 3544)
- msiexec.exe (PID: 3520)
- msiexec.exe (PID: 400)
Reads the computer name
- msiexec.exe (PID: 3544)
- MsiExec.exe (PID: 2072)
- msiexec.exe (PID: 3724)
- iexplore.exe (PID: 3748)
- iexplore.exe (PID: 316)
- msiexec.exe (PID: 3520)
- MsiExec.exe (PID: 2680)
- msiexec.exe (PID: 400)
- MsiExec.exe (PID: 2748)
Checks supported languages
- MsiExec.exe (PID: 2072)
- msiexec.exe (PID: 3544)
- msiexec.exe (PID: 3724)
- iexplore.exe (PID: 3748)
- iexplore.exe (PID: 316)
- MsiExec.exe (PID: 2680)
- msiexec.exe (PID: 400)
- msiexec.exe (PID: 3520)
- MsiExec.exe (PID: 2748)
Changes internet zones settings
- iexplore.exe (PID: 3748)
Reads settings of System Certificates
- iexplore.exe (PID: 316)
- iexplore.exe (PID: 3748)
- Setup.exe (PID: 3988)
Application launched itself
- iexplore.exe (PID: 3748)
Modifies the phishing filter of IE
- iexplore.exe (PID: 3748)
Checks Windows Trust Settings
- iexplore.exe (PID: 316)
- iexplore.exe (PID: 3748)
- Setup.exe (PID: 3988)
Reads the date of Windows installation
- iexplore.exe (PID: 3748)
Dropped object may contain Bitcoin addresses
- SetupUtility.exe (PID: 748)
- Setup.exe (PID: 3988)
Creates files in the user directory
- iexplore.exe (PID: 3748)
Adds / modifies Windows certificates
- iexplore.exe (PID: 3748)
Changes settings of System certificates
- iexplore.exe (PID: 3748)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
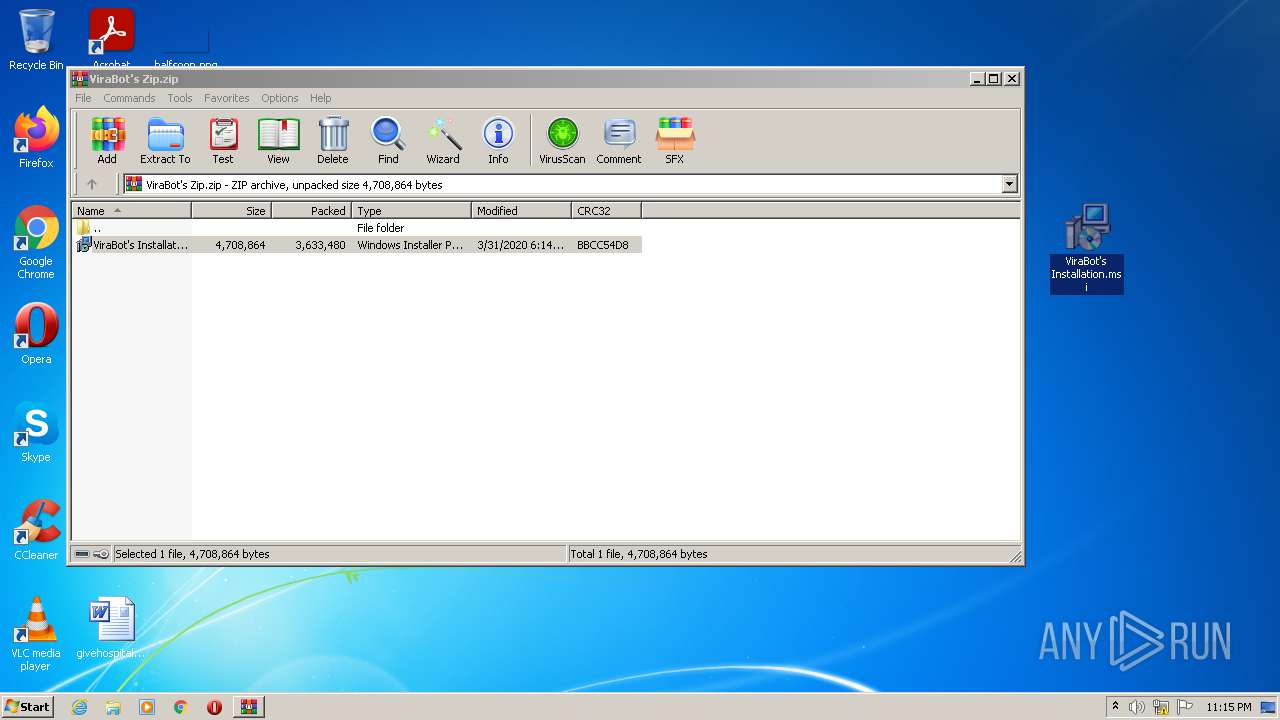
| ZipFileName: | ViraBot's Installation.msi |
|---|---|
| ZipUncompressedSize: | 4708864 |
| ZipCompressedSize: | 3633480 |
| ZipCRC: | 0xbbcc54d8 |
| ZipModifyDate: | 2020:03:31 18:14:27 |
| ZipCompression: | Deflated |
| ZipBitFlag: | - |
| ZipRequiredVersion: | 20 |
Total processes
55
Monitored processes
16
Malicious processes
7
Suspicious processes
5
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 316 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3748 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 400 | "C:\Windows\System32\msiexec.exe" /i "C:\Users\admin\Desktop\ViraBot's Installation.msi" | C:\Windows\System32\msiexec.exe | Explorer.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows� installer Exit code: 1603 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 748 | SetupUtility.exe /aupause | C:\5215dd4636d110b0848666\SetupUtility.exe | — | Setup.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft .NET Framework 4.5 Setup Exit code: 0 Version: 14.0.1055.0 built by: NETFXREL2 Modules
| |||||||||||||||
| 2072 | C:\Windows\system32\MsiExec.exe -Embedding 81DC33F1A374FC1727D4997146DE25D0 C | C:\Windows\system32\MsiExec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows� installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2300 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\ViraBot's Zip.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 2664 | "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\78RFYB7Z\NDP461-KB3102438-Web.exe" | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\78RFYB7Z\NDP461-KB3102438-Web.exe | — | iexplore.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft .NET Framework 4.6.1 Setup Exit code: 3221226540 Version: 4.6.01055.00 Modules
| |||||||||||||||
| 2680 | C:\Windows\system32\MsiExec.exe -Embedding AAB14ECE63C0201820154DE8DD3C5E15 C | C:\Windows\system32\MsiExec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows� installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2748 | C:\Windows\system32\MsiExec.exe -Embedding D3526BDFE1D9CFDCA418B2A569863191 C | C:\Windows\system32\MsiExec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows� installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3292 | TMP3F7D.tmp.exe /Q /X:C:\5215dd4636d110b0848666\TMP3F7D.tmp.exe.tmp | C:\5215dd4636d110b0848666\TMP3F7D.tmp.exe | Setup.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft .NET Framework 4.6.1 Setup Exit code: 0 Version: 4.6.01055.00 Modules
| |||||||||||||||
| 3520 | "C:\Windows\System32\msiexec.exe" /i "C:\Users\admin\Desktop\ViraBot's Installation.msi" | C:\Windows\System32\msiexec.exe | Explorer.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows� installer Exit code: 1603 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
23 031
Read events
22 848
Write events
173
Delete events
10
Modification events
| (PID) Process: | (2300) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2300) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2300) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16C\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2300) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\virtio_ivshmem_master_build.zip | |||
| (PID) Process: | (2300) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\ViraBot's Zip.zip | |||
| (PID) Process: | (2300) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2300) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2300) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2300) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2300) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16C\52C64B7E |
| Operation: | write | Name: | @C:\Windows\System32\msimsg.dll,-34 |
Value: Windows Installer Package | |||
Executable files
45
Suspicious files
16
Text files
88
Unknown types
12
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2300 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2300.26512\ViraBot's Installation.msi | — | |
MD5:— | SHA256:— | |||
| 316 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:— | SHA256:— | |||
| 316 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\6BADA8974A10C4BD62CC921D13E43B18_711ED44619924BA6DC33E69F97E7FF63 | der | |
MD5:— | SHA256:— | |||
| 316 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\6BADA8974A10C4BD62CC921D13E43B18_711ED44619924BA6DC33E69F97E7FF63 | binary | |
MD5:— | SHA256:— | |||
| 3748 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Active\{9921B06B-FAF1-11EB-B39C-12A9866C77DE}.dat | binary | |
MD5:— | SHA256:— | |||
| 3748 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF292A2DF6A32F89B1.TMP | gmc | |
MD5:— | SHA256:— | |||
| 316 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\5IWPIAR9\NDP461-KB3102438-Web[1].exe | executable | |
MD5:— | SHA256:— | |||
| 316 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\6BADA8974A10C4BD62CC921D13E43B18_1DC6D7385EA816C957BA2B715AC5C442 | binary | |
MD5:— | SHA256:— | |||
| 316 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\6BADA8974A10C4BD62CC921D13E43B18_1DC6D7385EA816C957BA2B715AC5C442 | der | |
MD5:— | SHA256:— | |||
| 3544 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\MSIF0AB.tmp | executable | |
MD5:3DAD1EAF900AC0D557048901F39C40EC | SHA256:AE90445E7C28C72EACE289A334D483DAA051E654B8F12A95DD1C7A25287C815B | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
30
TCP/UDP connections
28
DNS requests
17
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
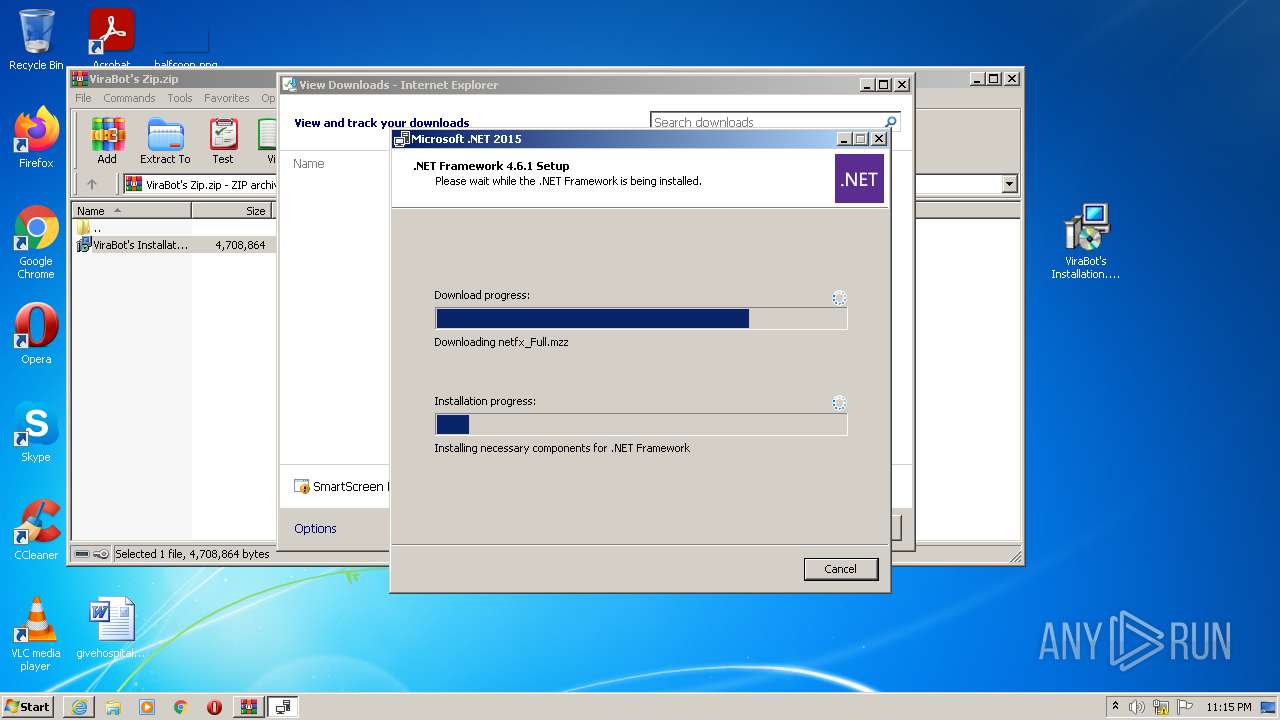
896 | svchost.exe | HEAD | 302 | 23.15.254.176:80 | http://go.microsoft.com/fwlink/?LinkId=671735&clcid=0x409 | NL | — | — | whitelisted |
896 | svchost.exe | GET | 302 | 23.15.254.176:80 | http://go.microsoft.com/fwlink/?LinkId=671733&clcid=0x409 | NL | — | — | whitelisted |
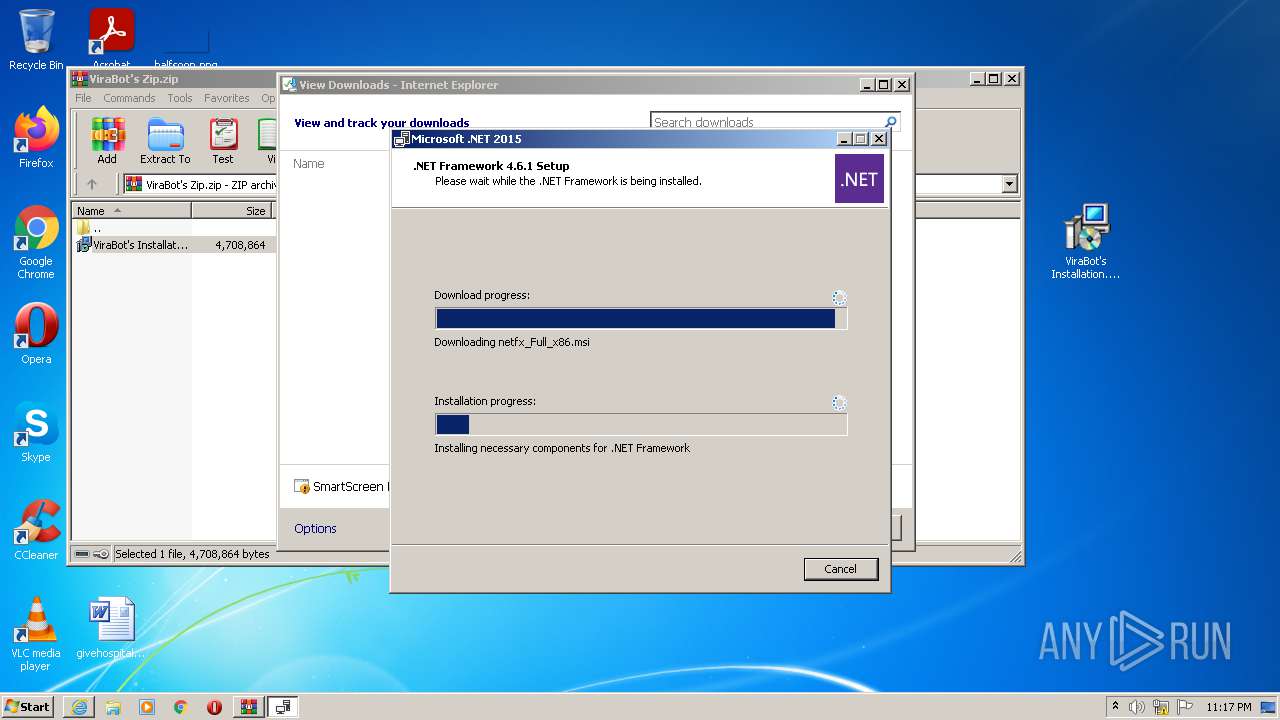
3988 | Setup.exe | GET | 302 | 23.15.254.176:80 | http://go.microsoft.com/fwlink/?LinkId=671733&clcid=0x409 | NL | — | — | whitelisted |
3988 | Setup.exe | GET | 302 | 23.15.254.176:80 | http://go.microsoft.com/fwlink/?LinkId=671733&clcid=0x409 | NL | — | — | whitelisted |
896 | svchost.exe | GET | 302 | 23.15.254.176:80 | http://go.microsoft.com/fwlink/?LinkId=671735&clcid=0x409 | NL | — | — | whitelisted |
896 | svchost.exe | HEAD | 302 | 23.15.254.176:80 | http://go.microsoft.com/fwlink/?LinkId=671733&clcid=0x409 | NL | — | — | whitelisted |
896 | svchost.exe | HEAD | 302 | 23.15.254.176:80 | http://go.microsoft.com/fwlink/?LinkId=671733&clcid=0x409 | NL | — | — | whitelisted |
316 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA%2BnRyLFPYjID1ie%2Bx%2BdSjo%3D | US | der | 1.47 Kb | whitelisted |
3748 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | der | 471 b | whitelisted |
3988 | Setup.exe | GET | 200 | 104.79.89.142:80 | http://www.microsoft.com/pkiops/crl/MicCodSigPCA2011_2011-07-08.crl | US | der | 1.05 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
316 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
316 | iexplore.exe | 23.47.208.114:443 | download.microsoft.com | NTT DOCOMO, INC. | US | suspicious |
3988 | Setup.exe | 92.123.194.154:80 | crl.microsoft.com | Akamai International B.V. | — | suspicious |
896 | svchost.exe | 23.15.254.176:80 | go.microsoft.com | Akamai Technologies, Inc. | NL | malicious |
896 | svchost.exe | 23.47.208.114:443 | download.microsoft.com | NTT DOCOMO, INC. | US | suspicious |
3748 | iexplore.exe | 152.199.19.161:443 | iecvlist.microsoft.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3748 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3748 | iexplore.exe | 204.79.197.203:443 | www.msn.com | Microsoft Corporation | US | malicious |
3988 | Setup.exe | 23.15.254.176:80 | go.microsoft.com | Akamai Technologies, Inc. | NL | malicious |
3988 | Setup.exe | 68.232.34.200:443 | download.visualstudio.microsoft.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
go.microsoft.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
download.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
iecvlist.microsoft.com |
| whitelisted |
r20swj13mr.microsoft.com |
| whitelisted |
download.visualstudio.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
ieonline.microsoft.com |
| whitelisted |
Threats
Process | Message |
|---|---|
Setup.exe | An unknown error occurred while processing the certificate.
|
Setup.exe | An unknown error occurred while processing the certificate.
|