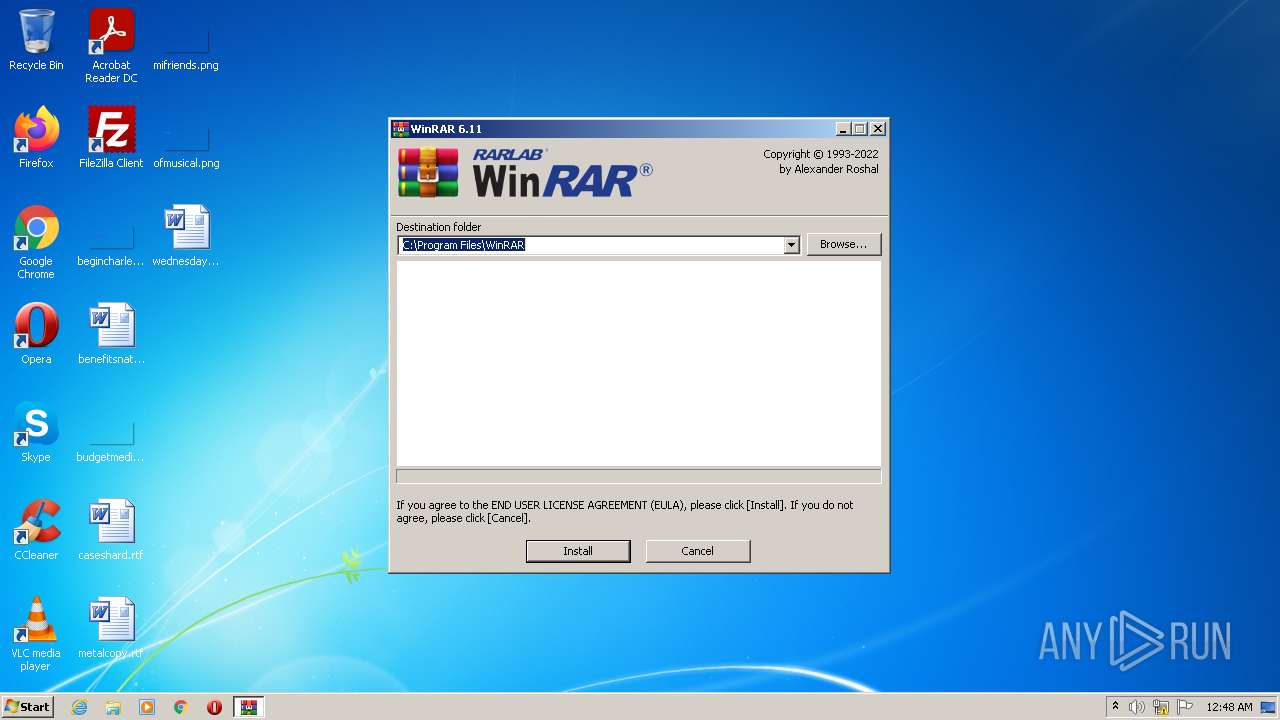
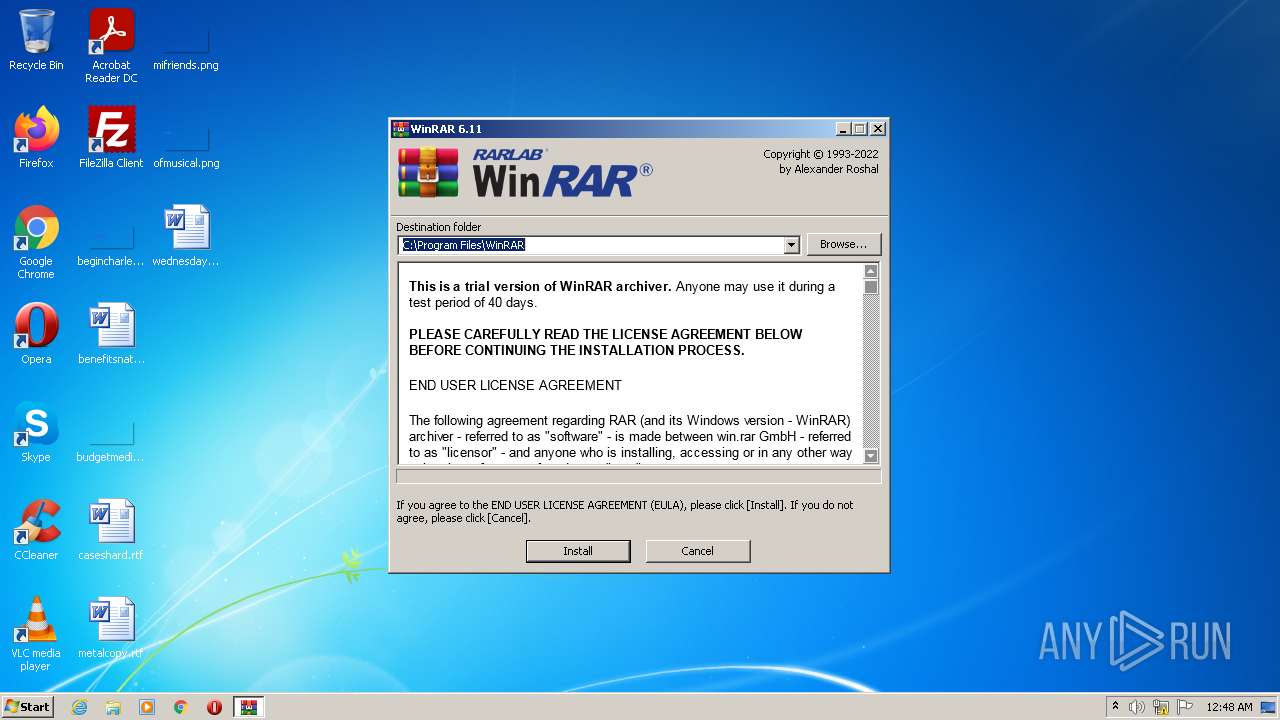
| download: | winrar-x32-611.exe |
| Full analysis: | https://app.any.run/tasks/78bcc46f-fa82-4087-bb0a-c6d6fb58940d |
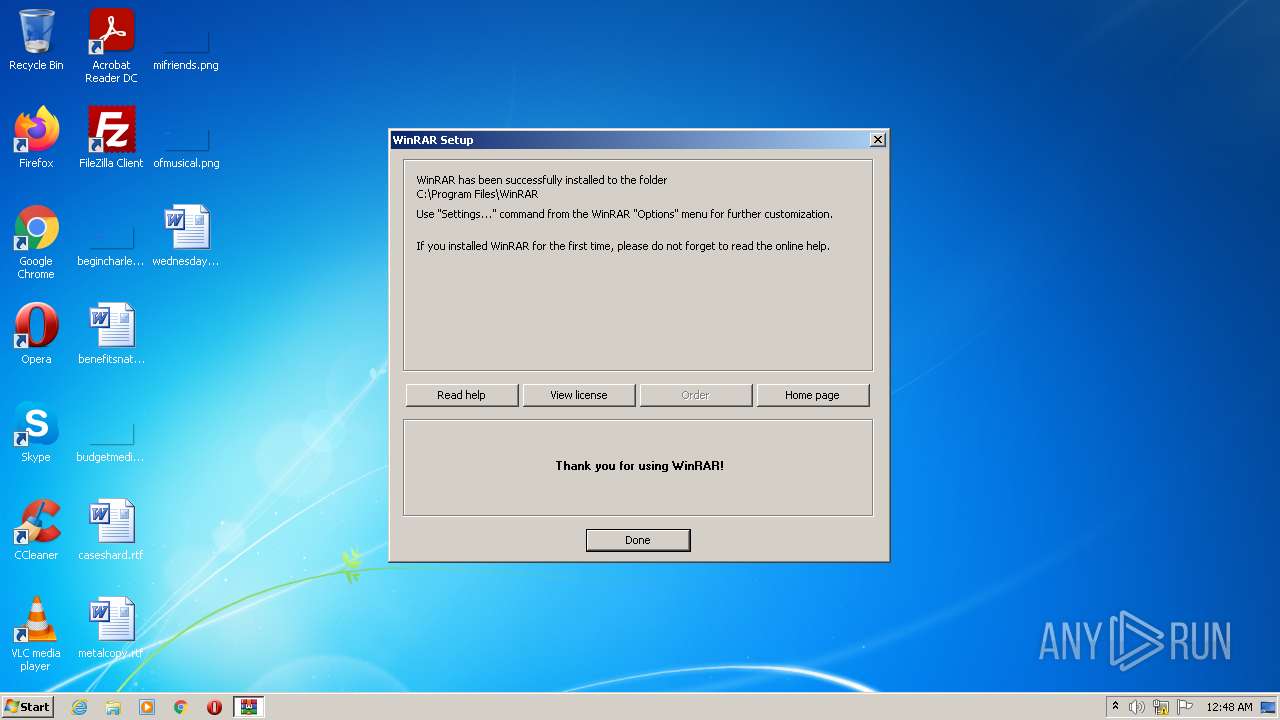
| Verdict: | Malicious activity |
| Analysis date: | May 20, 2022, 23:48:39 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 86620899349D77D663FA1EF82F2352D5 |
| SHA1: | 4FB479D8EBC2BF37702BD51101E7465B30F4968D |
| SHA256: | 6124FCE45E0413021160EAF4B4652AE6B6BDD4967082094F7D457207AA349F1F |
| SSDEEP: | 49152:6eZBvOBfJXAUDjGcSV4ogt9dqM374vywN+AsHq7V/nKAH7+ghjFxqAGx99jxcF:6eZBvOBfKujQY37CywFHV/n3BxGx9q |
MALICIOUS
Application was dropped or rewritten from another process
- uninstall.exe (PID: 2316)
- WinRAR.exe (PID: 1332)
Drops executable file immediately after starts
- winrar-x32-611.exe (PID: 1912)
SUSPICIOUS
Checks supported languages
- winrar-x32-611.exe (PID: 1912)
- uninstall.exe (PID: 2316)
- WinRAR.exe (PID: 1332)
Reads Microsoft Outlook installation path
- winrar-x32-611.exe (PID: 1912)
Reads the computer name
- winrar-x32-611.exe (PID: 1912)
- uninstall.exe (PID: 2316)
- WinRAR.exe (PID: 1332)
Reads internet explorer settings
- winrar-x32-611.exe (PID: 1912)
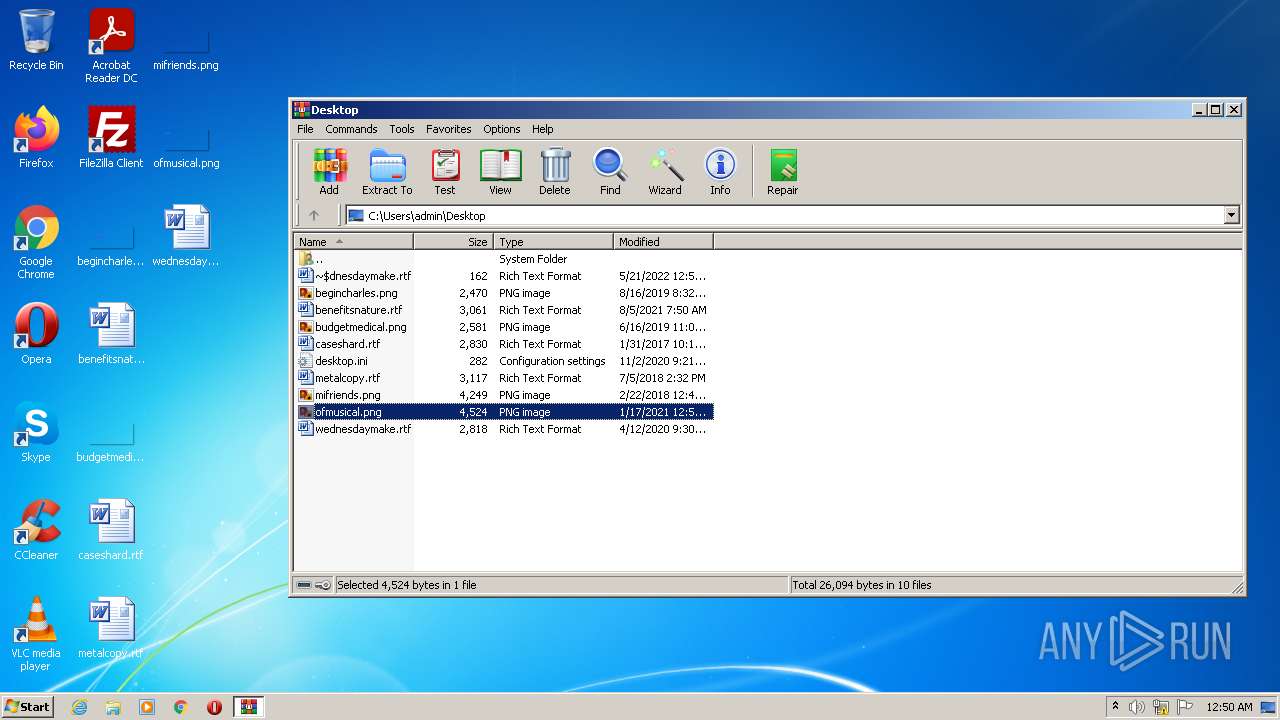
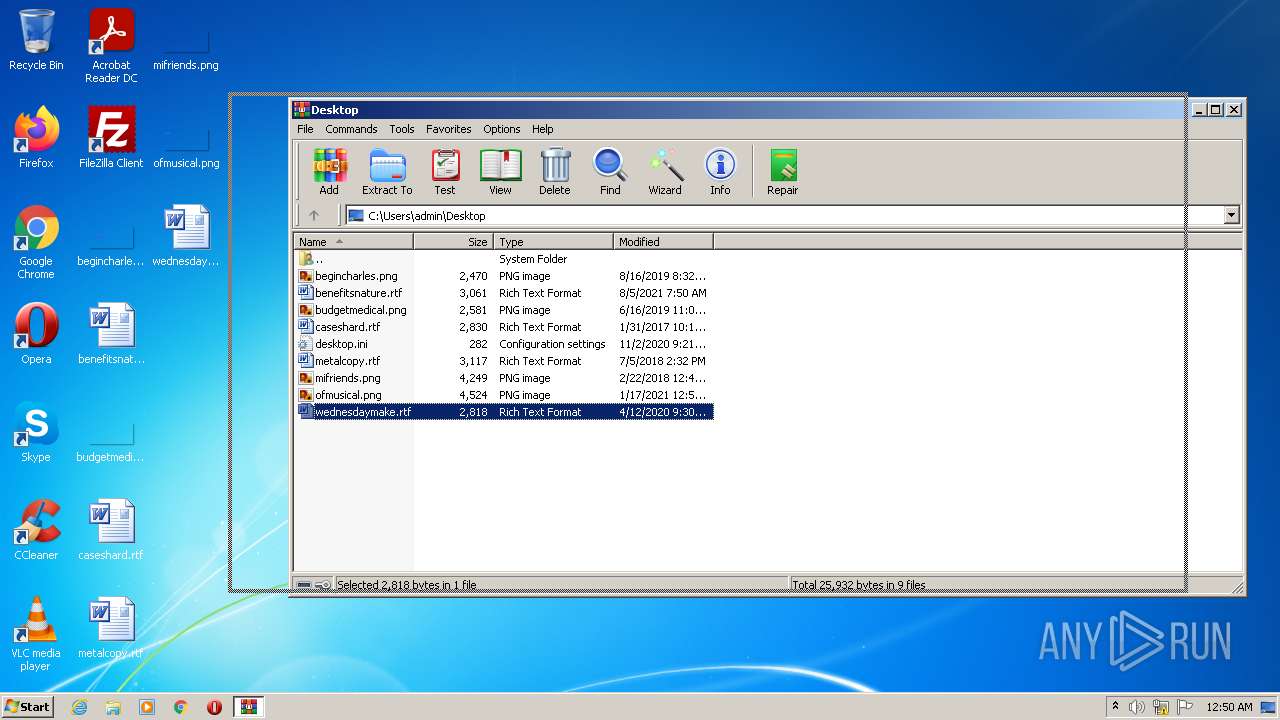
Creates files in the program directory
- winrar-x32-611.exe (PID: 1912)
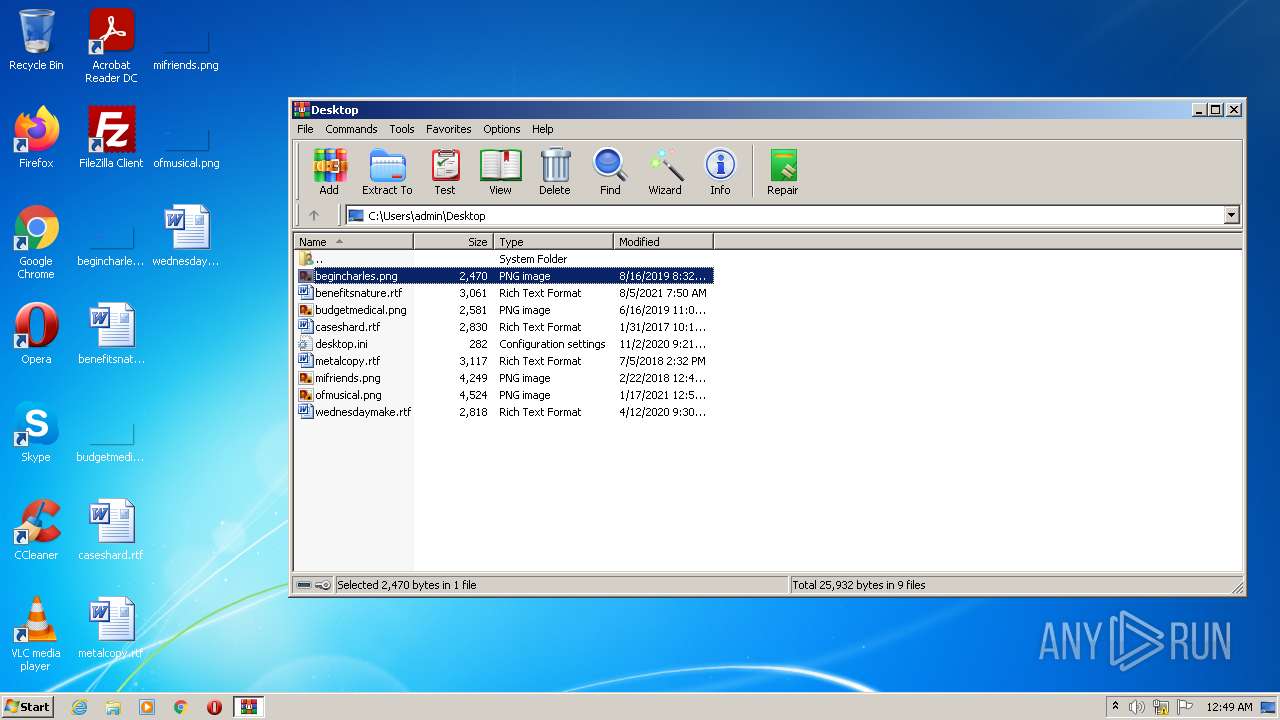
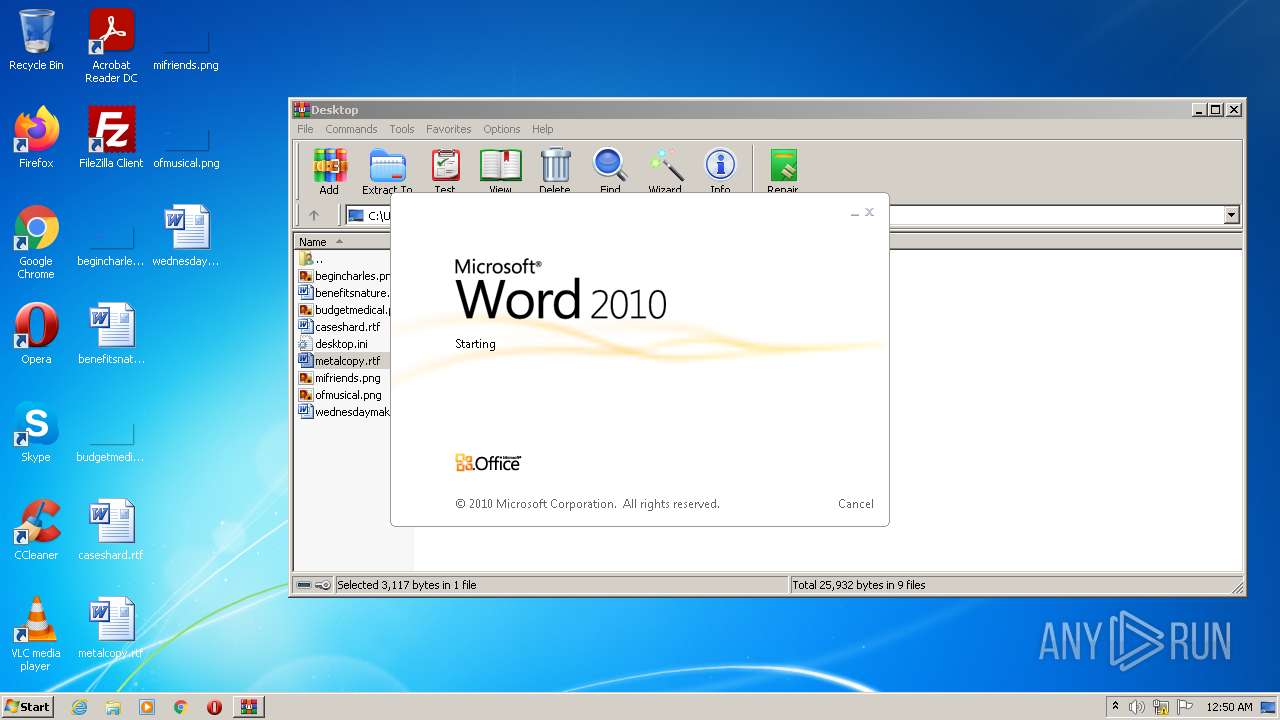
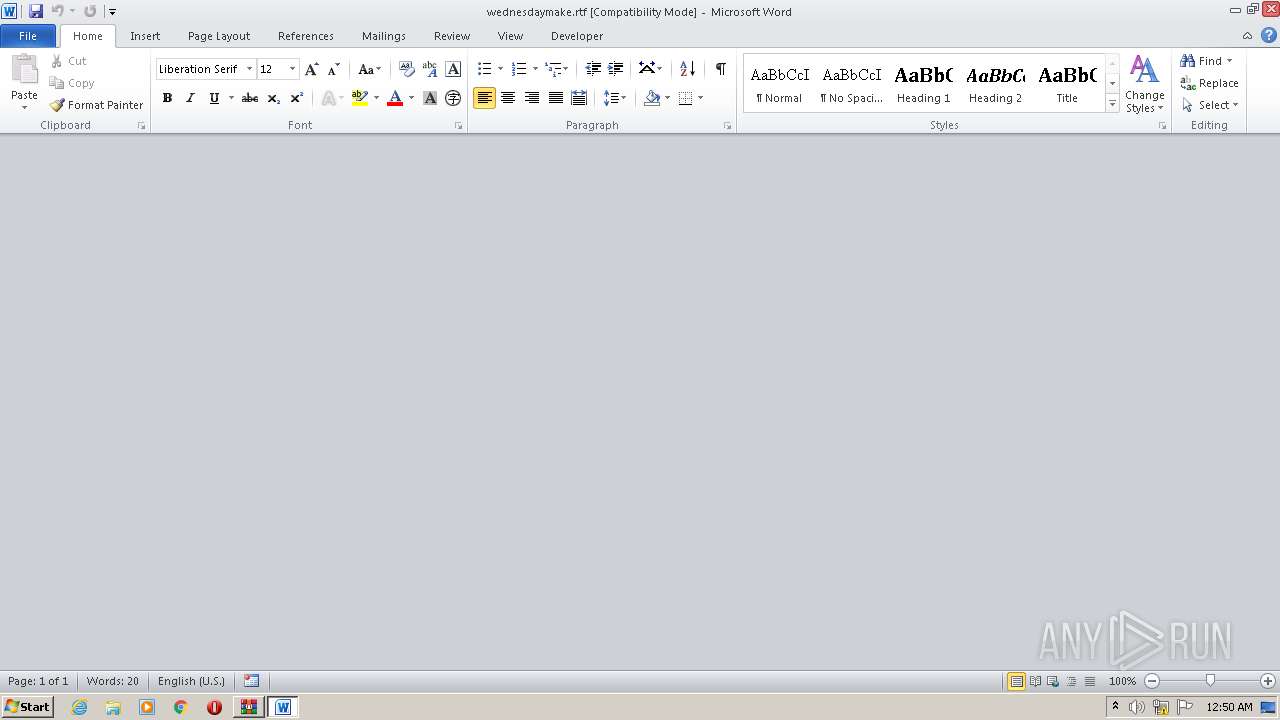
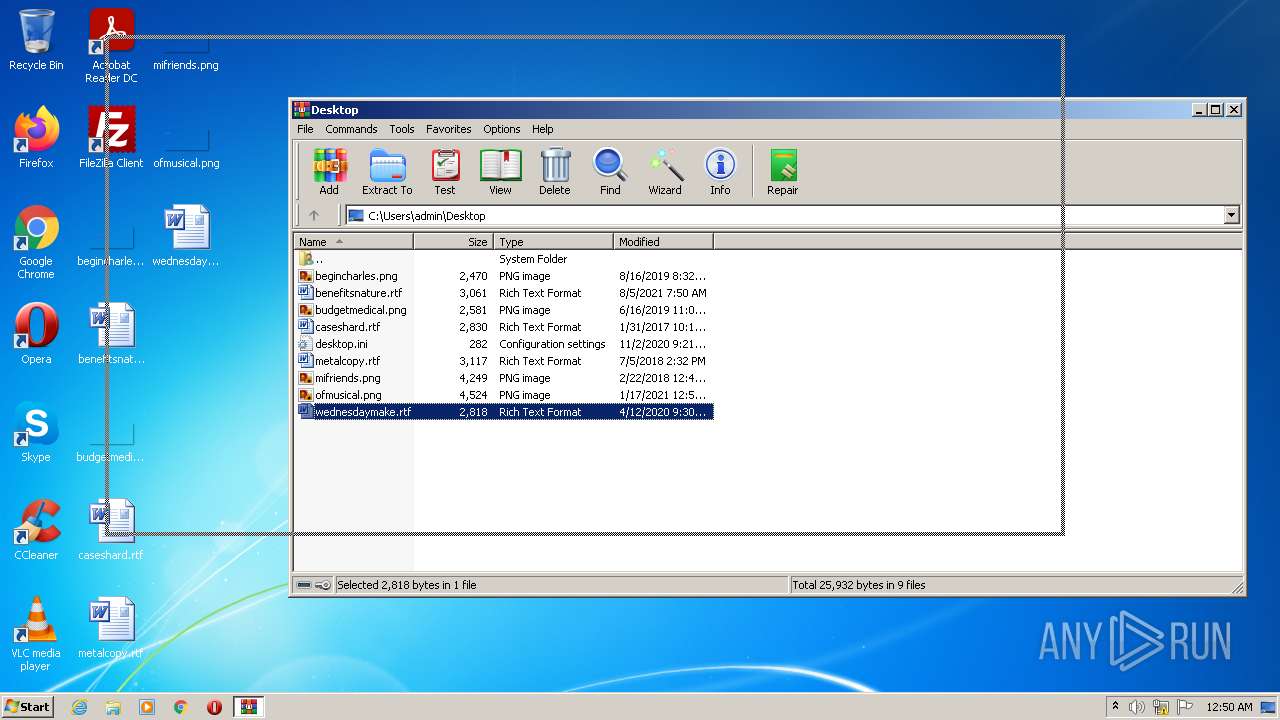
Starts Microsoft Office Application
- WinRAR.exe (PID: 1332)
Executable content was dropped or overwritten
- winrar-x32-611.exe (PID: 1912)
Drops a file with a compile date too recent
- winrar-x32-611.exe (PID: 1912)
Executed via COM
- DllHost.exe (PID: 3312)
- DllHost.exe (PID: 2936)
- DllHost.exe (PID: 1900)
Creates/Modifies COM task schedule object
- uninstall.exe (PID: 2316)
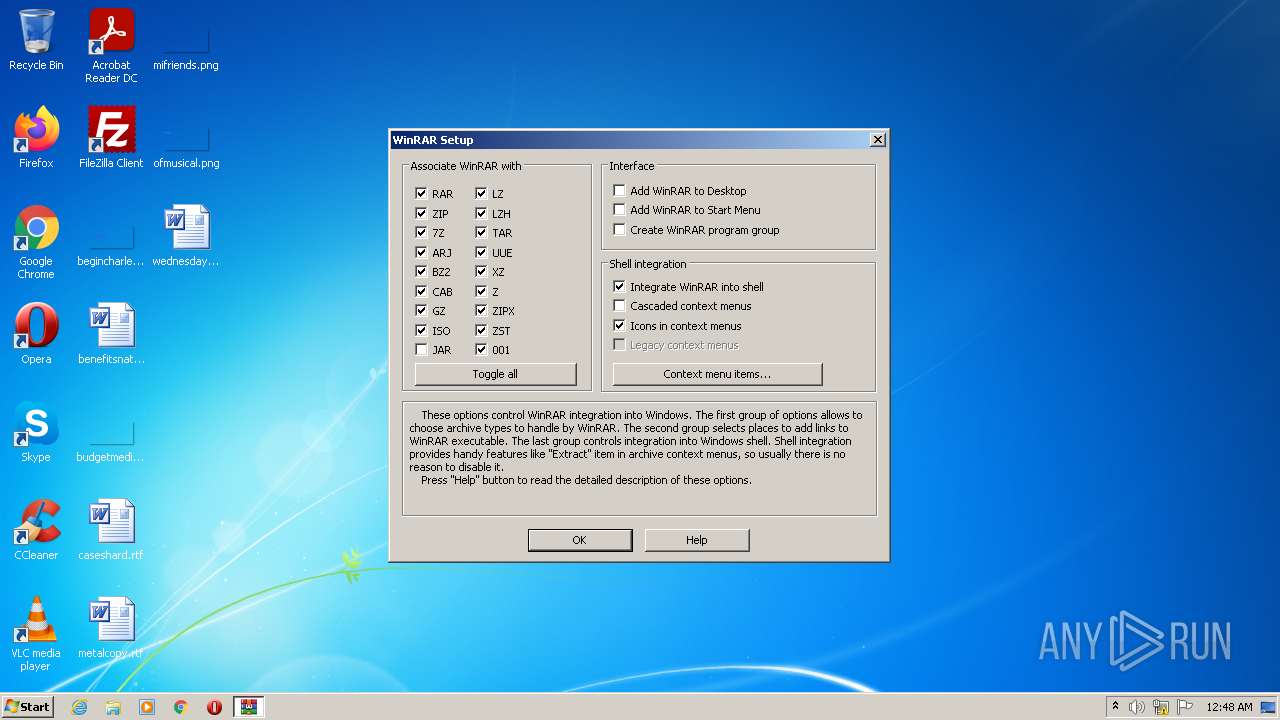
Changes default file association
- uninstall.exe (PID: 2316)
Searches for installed software
- uninstall.exe (PID: 2316)
Creates a software uninstall entry
- uninstall.exe (PID: 2316)
INFO
Checks supported languages
- DllHost.exe (PID: 3312)
- DllHost.exe (PID: 1900)
- WINWORD.EXE (PID: 652)
- WINWORD.EXE (PID: 572)
- DllHost.exe (PID: 2936)
- WINWORD.EXE (PID: 3868)
- WINWORD.EXE (PID: 1572)
Reads Microsoft Office registry keys
- WinRAR.exe (PID: 1332)
- WINWORD.EXE (PID: 572)
- WINWORD.EXE (PID: 652)
- WINWORD.EXE (PID: 1572)
- WINWORD.EXE (PID: 3868)
Reads the computer name
- DllHost.exe (PID: 3312)
- DllHost.exe (PID: 1900)
- WINWORD.EXE (PID: 652)
- WINWORD.EXE (PID: 572)
- DllHost.exe (PID: 2936)
- WINWORD.EXE (PID: 1572)
- WINWORD.EXE (PID: 3868)
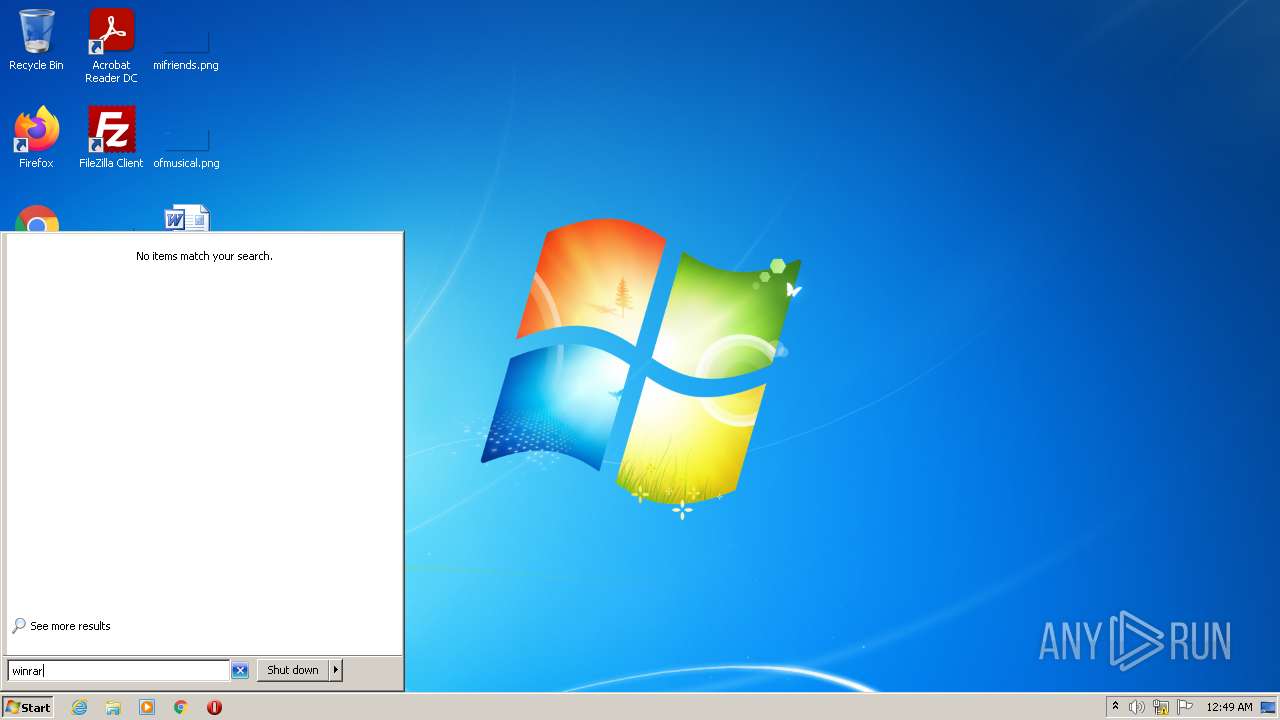
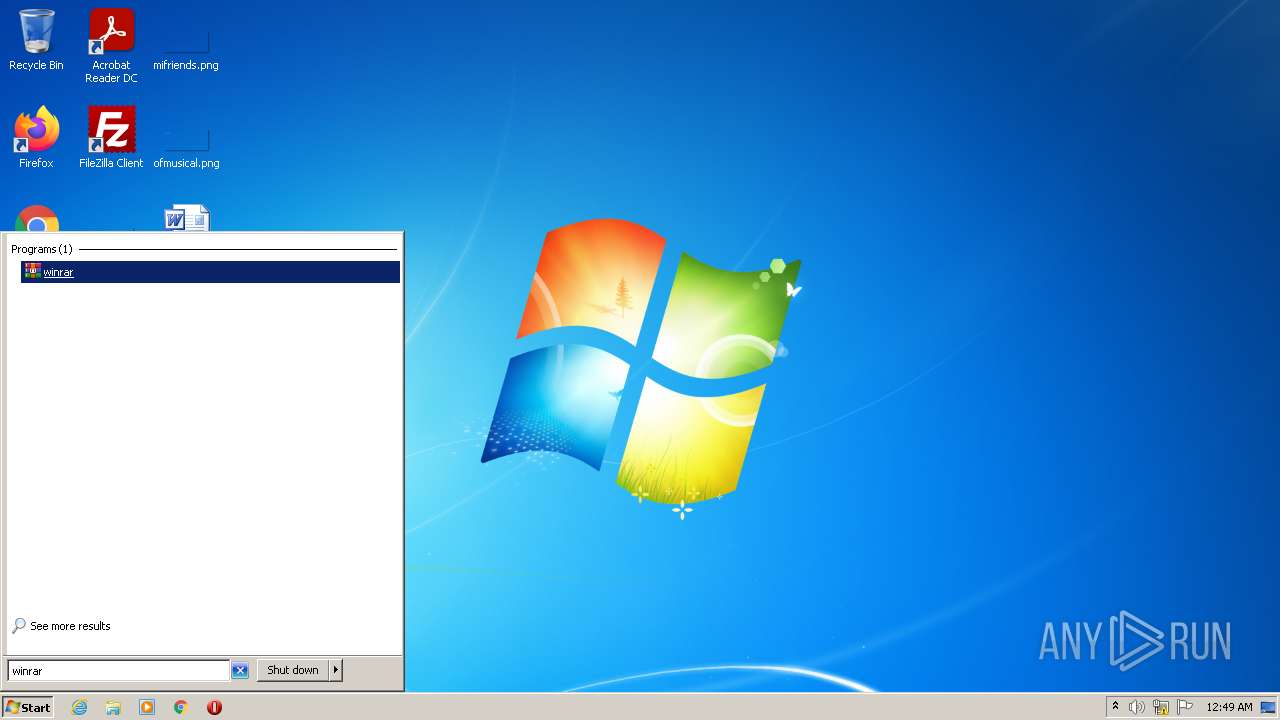
Manual execution by user
- WinRAR.exe (PID: 1332)
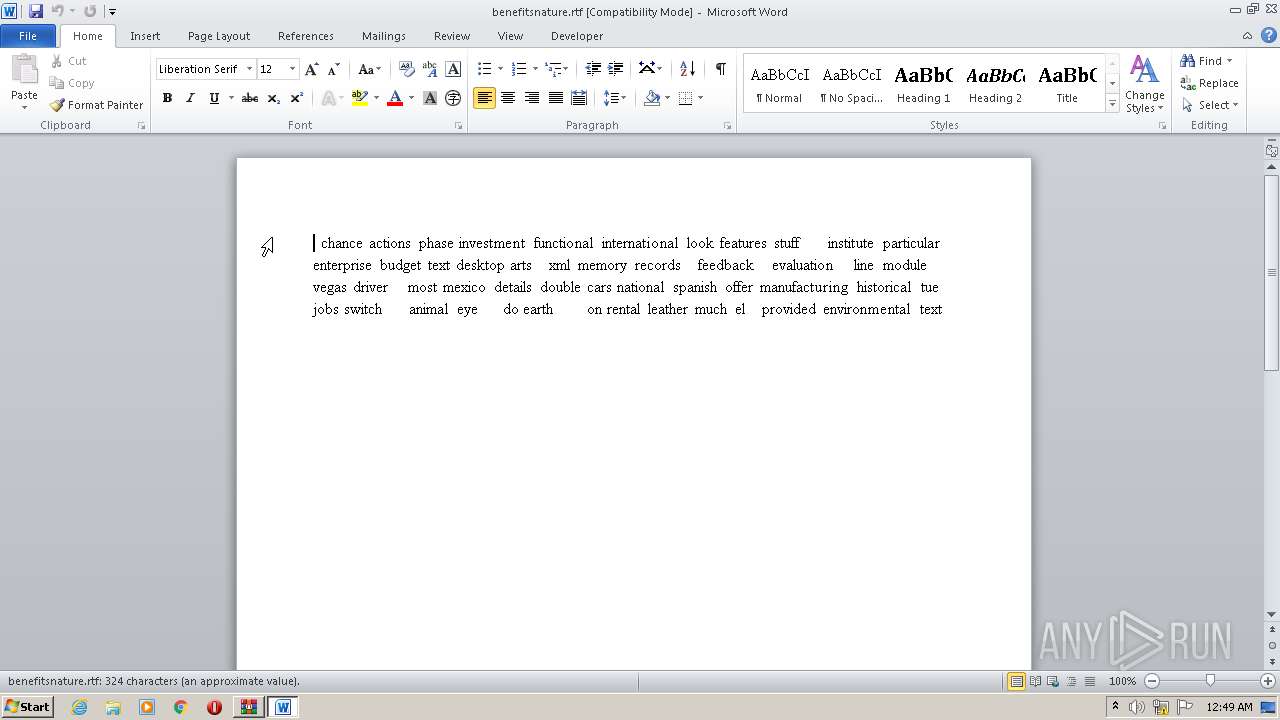
Creates files in the user directory
- WINWORD.EXE (PID: 652)
- WINWORD.EXE (PID: 572)
- WINWORD.EXE (PID: 1572)
- WINWORD.EXE (PID: 3868)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (52.9) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (23.5) |
| .exe | | | DOS Executable Generic (23.5) |
EXIF
EXE
| OriginalFileName: | WinRAR.exe |
|---|---|
| LegalCopyright: | Copyright © Alexander Roshal 1993-2022 |
| InternalName: | WinRAR |
| ProductVersion: | 6.11.0 |
| FileVersion: | 6.11.0 |
| FileDescription: | WinRAR archiver |
| CompanyName: | Alexander Roshal |
| ProductName: | WinRAR |
| CharacterSet: | Windows, Latin1 |
| LanguageCode: | English (U.S.) |
| FileSubtype: | - |
| ObjectFileType: | Executable application |
| FileOS: | Win32 |
| FileFlags: | (none) |
| FileFlagsMask: | 0x0000 |
| ProductVersionNumber: | 6.11.0.0 |
| FileVersionNumber: | 6.11.0.0 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 6 |
| ImageVersion: | - |
| OSVersion: | 6 |
| EntryPoint: | 0x1edb0 |
| UninitializedDataSize: | - |
| InitializedDataSize: | 360448 |
| CodeSize: | 211968 |
| LinkerVersion: | 14.3 |
| PEType: | PE32 |
| TimeStamp: | 2022:03:03 14:16:12+01:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 03-Mar-2022 13:16:12 |
| Detected languages: |
|
| Debug artifacts: |
|
| ProductName: | WinRAR |
| CompanyName: | Alexander Roshal |
| FileDescription: | WinRAR archiver |
| FileVersion: | 6.11.0 |
| ProductVersion: | 6.11.0 |
| InternalName: | WinRAR |
| LegalCopyright: | Copyright © Alexander Roshal 1993-2022 |
| OriginalFilename: | WinRAR.exe |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000118 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 6 |
| Time date stamp: | 03-Mar-2022 13:16:12 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00033A9C | 0x00033C00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.70431 |
.rdata | 0x00035000 | 0x0000A8BC | 0x0000AA00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.19022 |
.data | 0x00040000 | 0x000246D4 | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.02454 |
.didat | 0x00065000 | 0x0000017C | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.24496 |
.rsrc | 0x00066000 | 0x00027000 | 0x00026800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.75782 |
.reloc | 0x0008D000 | 0x00002300 | 0x00002400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.59537 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.26297 | 1872 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 6.03536 | 2216 | UNKNOWN | English - United States | RT_ICON |
3 | 6.24591 | 3752 | UNKNOWN | English - United States | RT_ICON |
4 | 5.57239 | 1128 | UNKNOWN | English - United States | RT_ICON |
5 | 6.35851 | 4264 | UNKNOWN | English - United States | RT_ICON |
6 | 5.9392 | 9640 | UNKNOWN | English - United States | RT_ICON |
7 | 3.11482 | 376 | UNKNOWN | English - United States | RT_STRING |
8 | 3.14988 | 436 | UNKNOWN | English - United States | RT_STRING |
9 | 3.11812 | 410 | UNKNOWN | English - United States | RT_STRING |
10 | 2.99727 | 326 | UNKNOWN | English - United States | RT_STRING |
Imports
COMCTL32.dll (delay-loaded) |
KERNEL32.dll |
OLEAUT32.dll |
gdiplus.dll |
Total processes
53
Monitored processes
11
Malicious processes
3
Suspicious processes
0
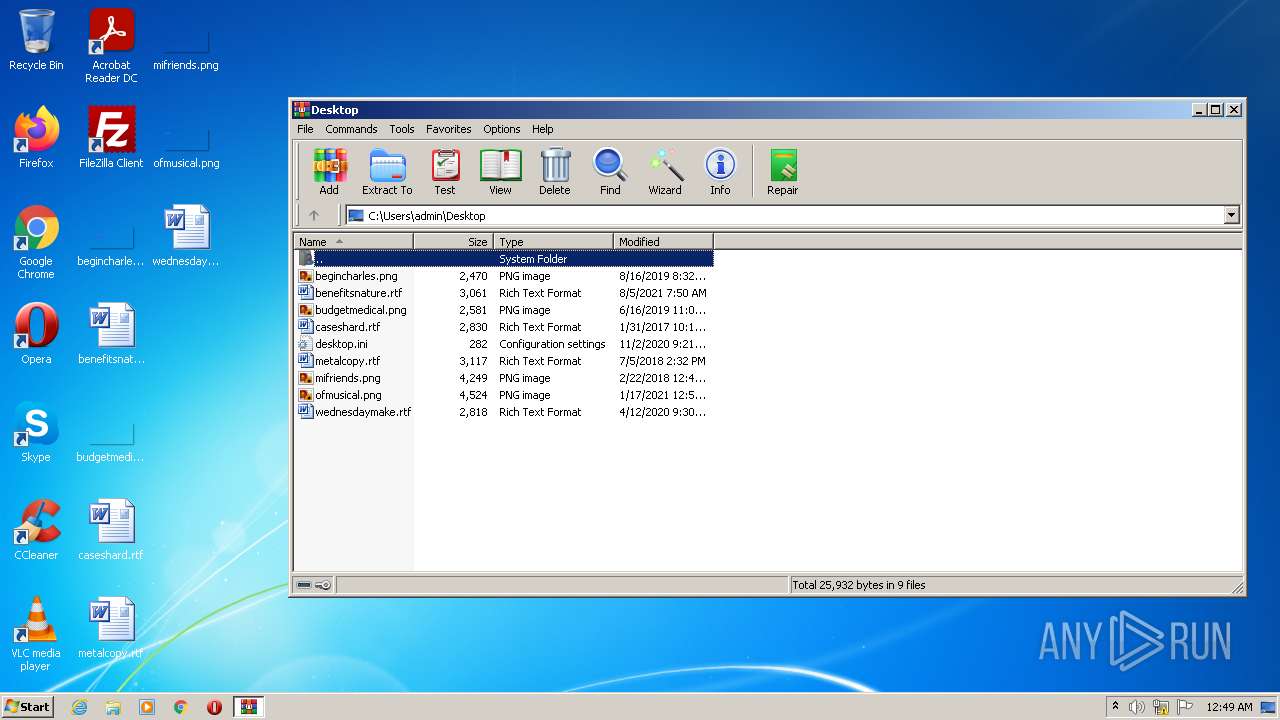
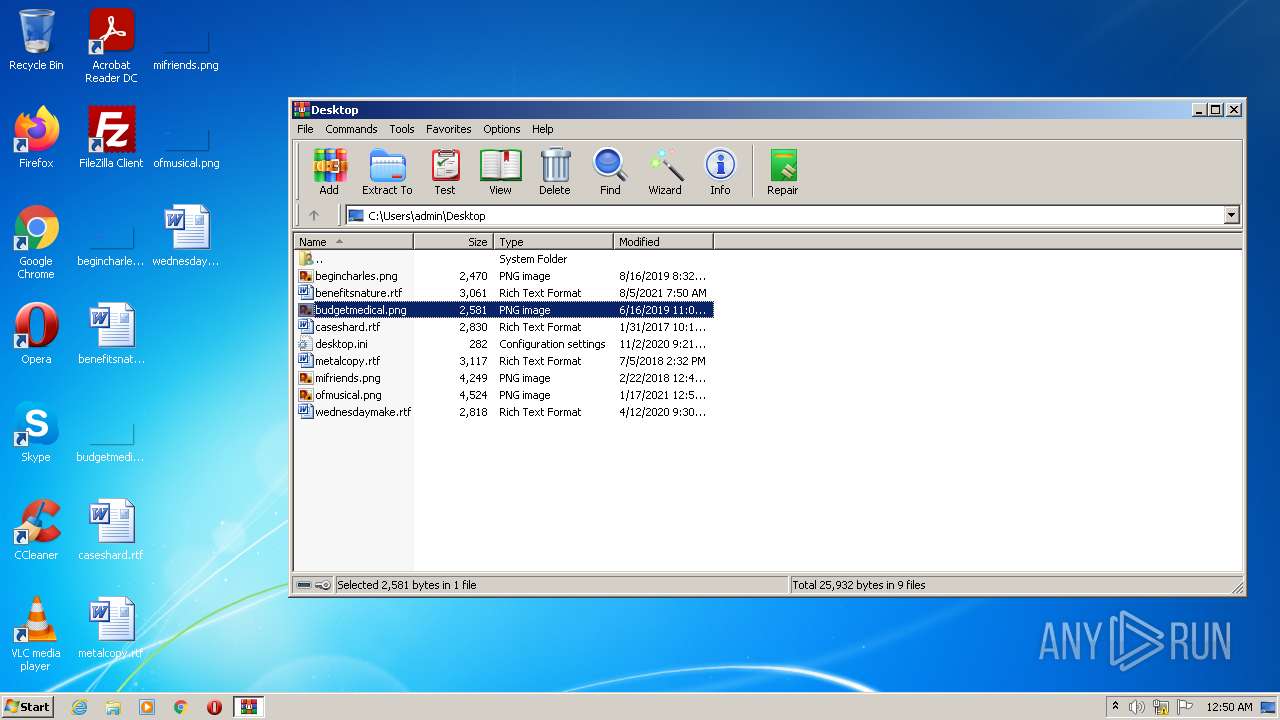
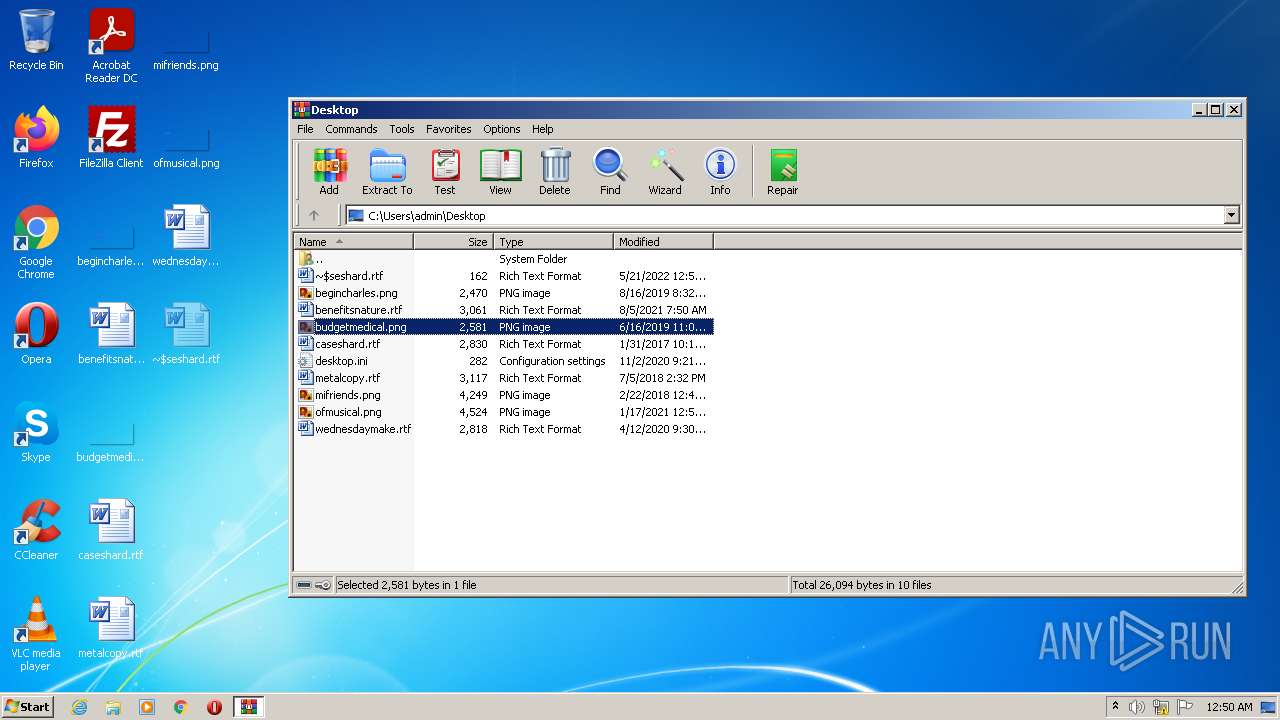
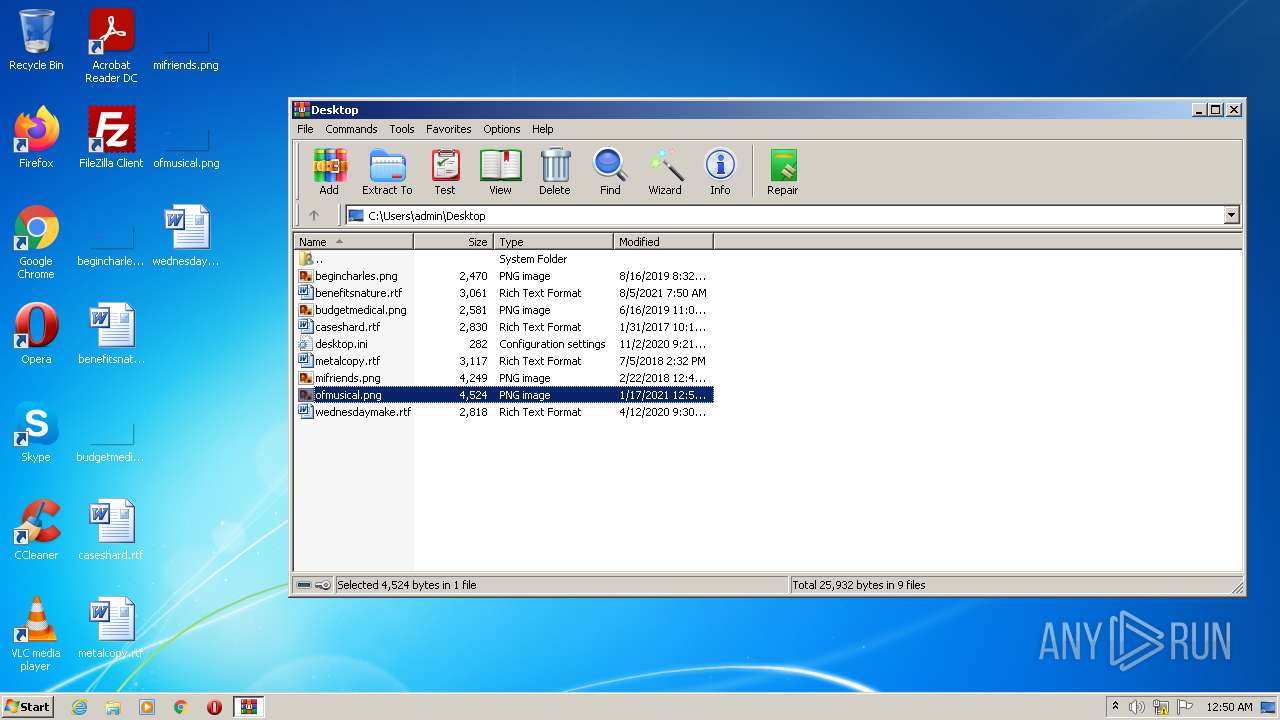
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
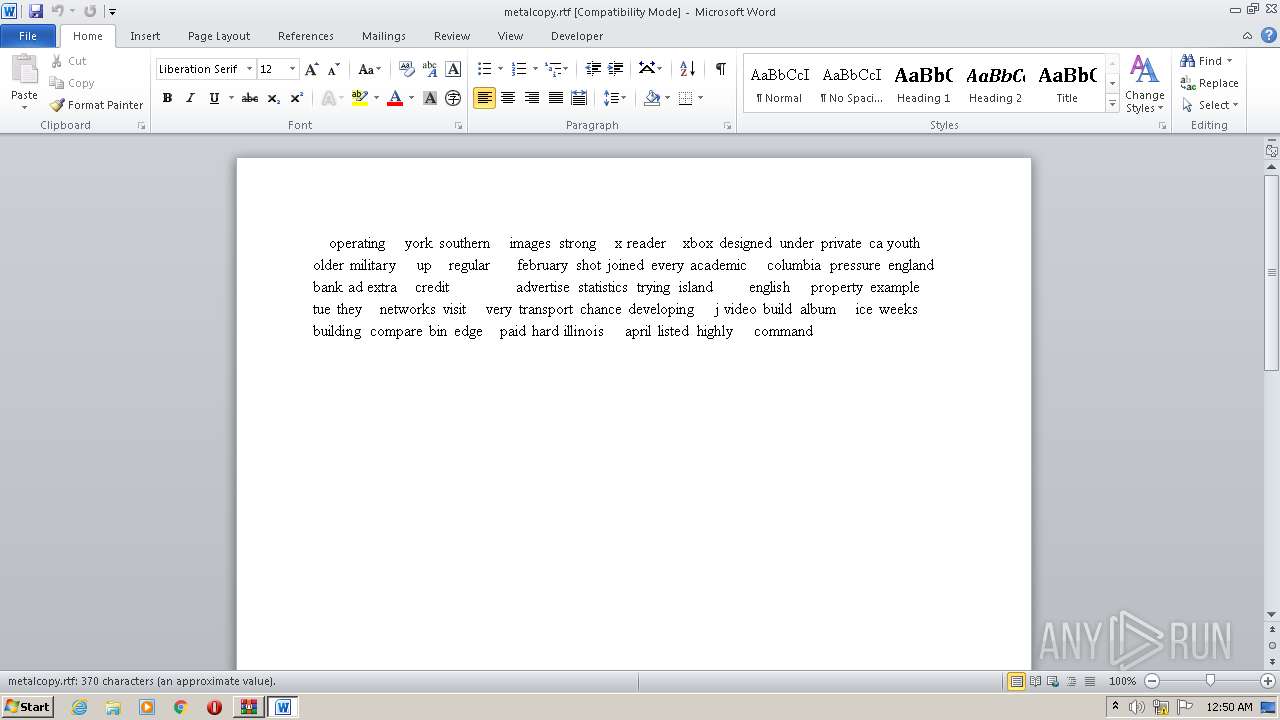
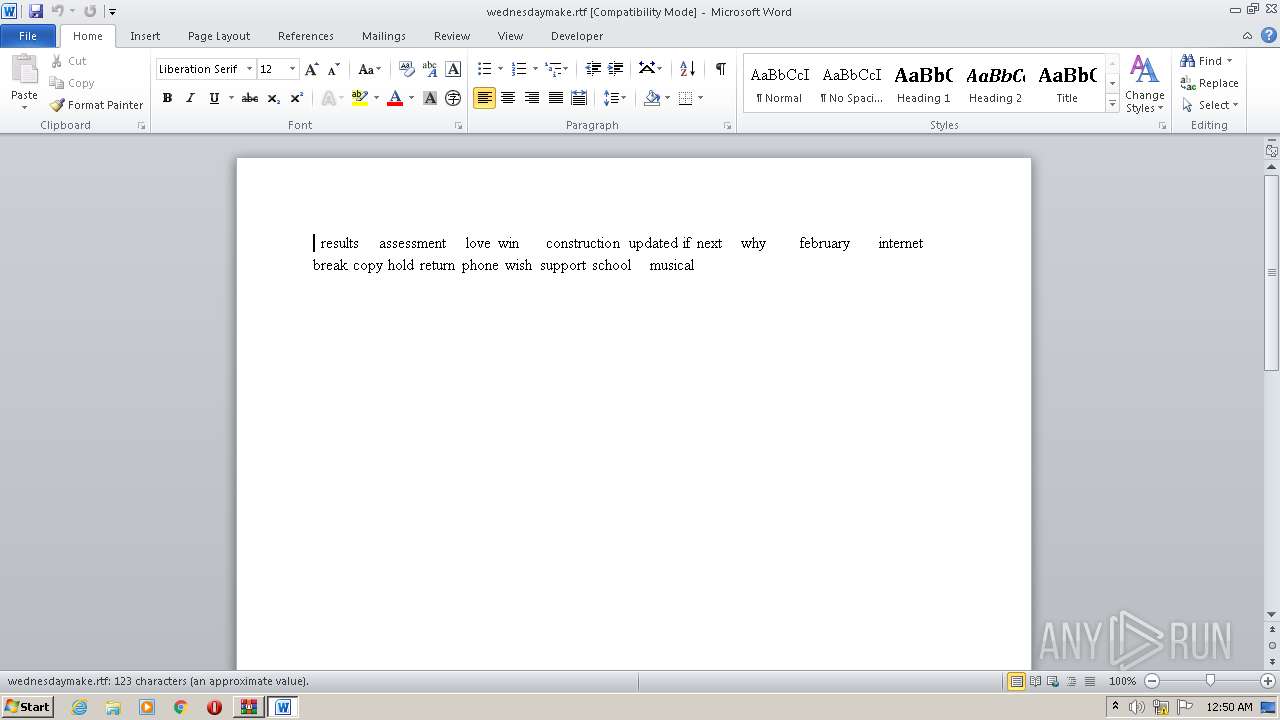
| 572 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\metalcopy.rtf" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | WinRAR.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 652 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\caseshard.rtf" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | WinRAR.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
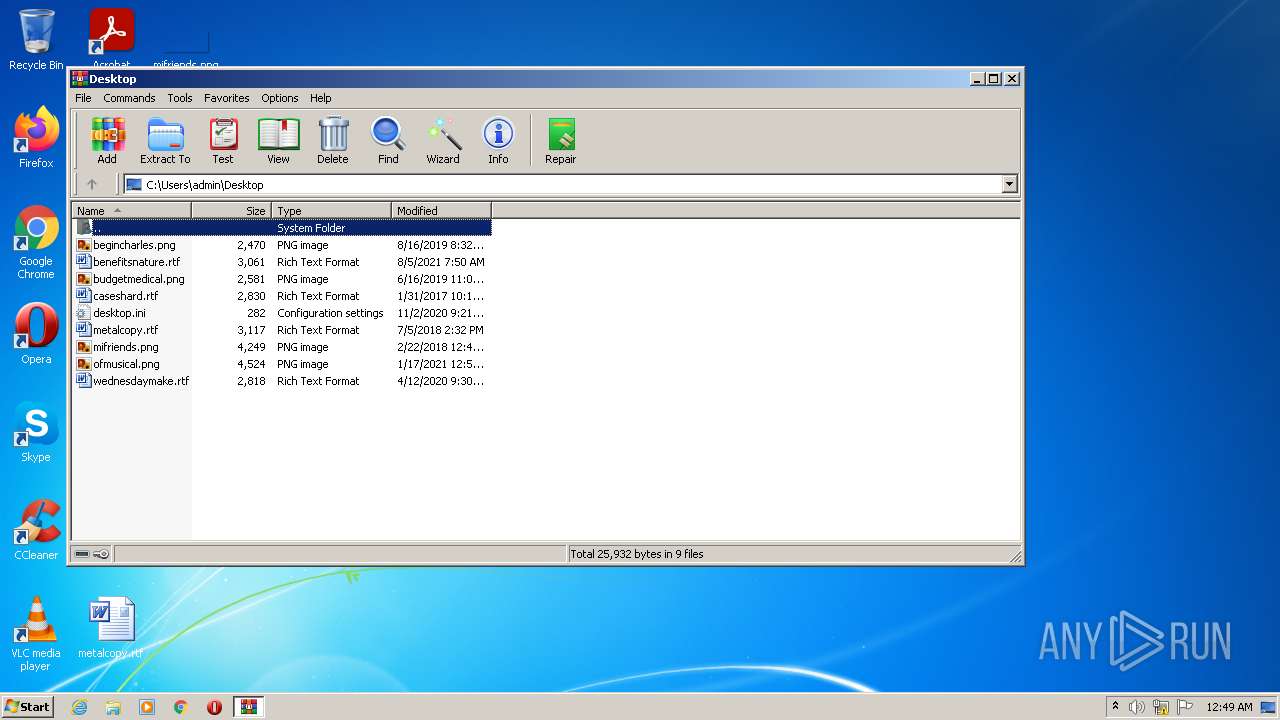
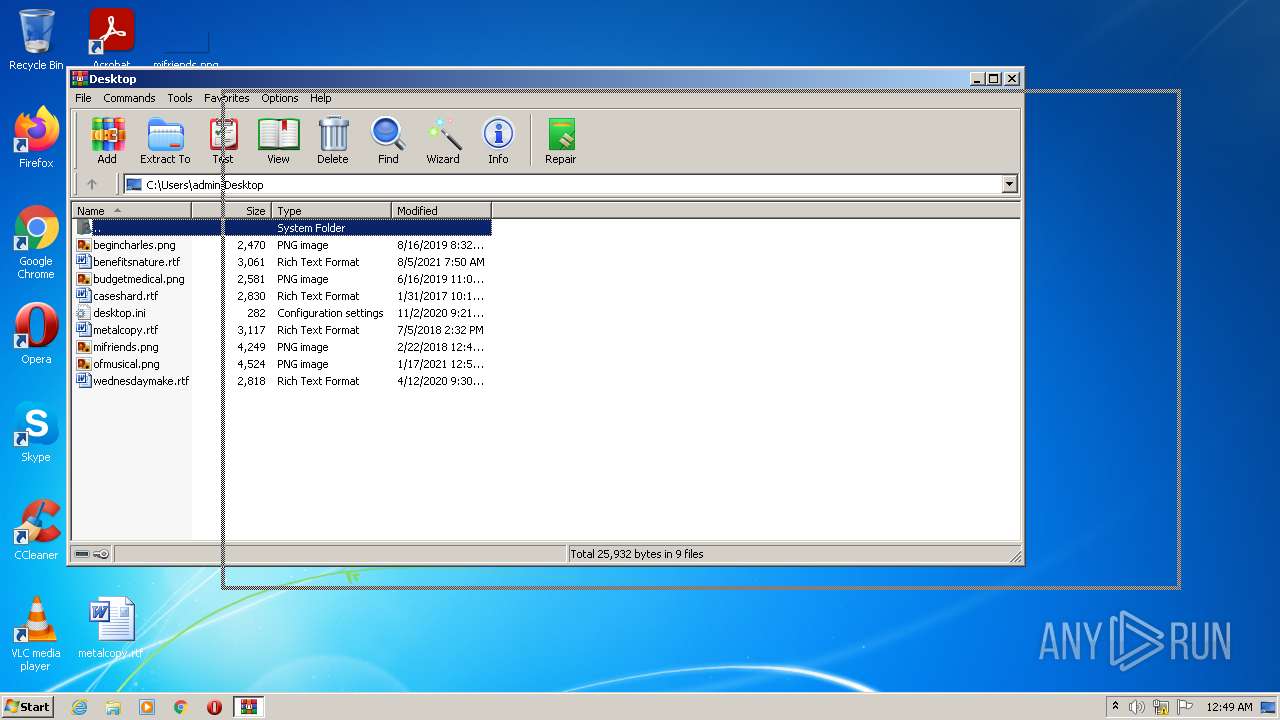
| 1332 | "C:\Program Files\WinRAR\WinRAR.exe" | C:\Program Files\WinRAR\WinRAR.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 6.11.0 Modules
| |||||||||||||||
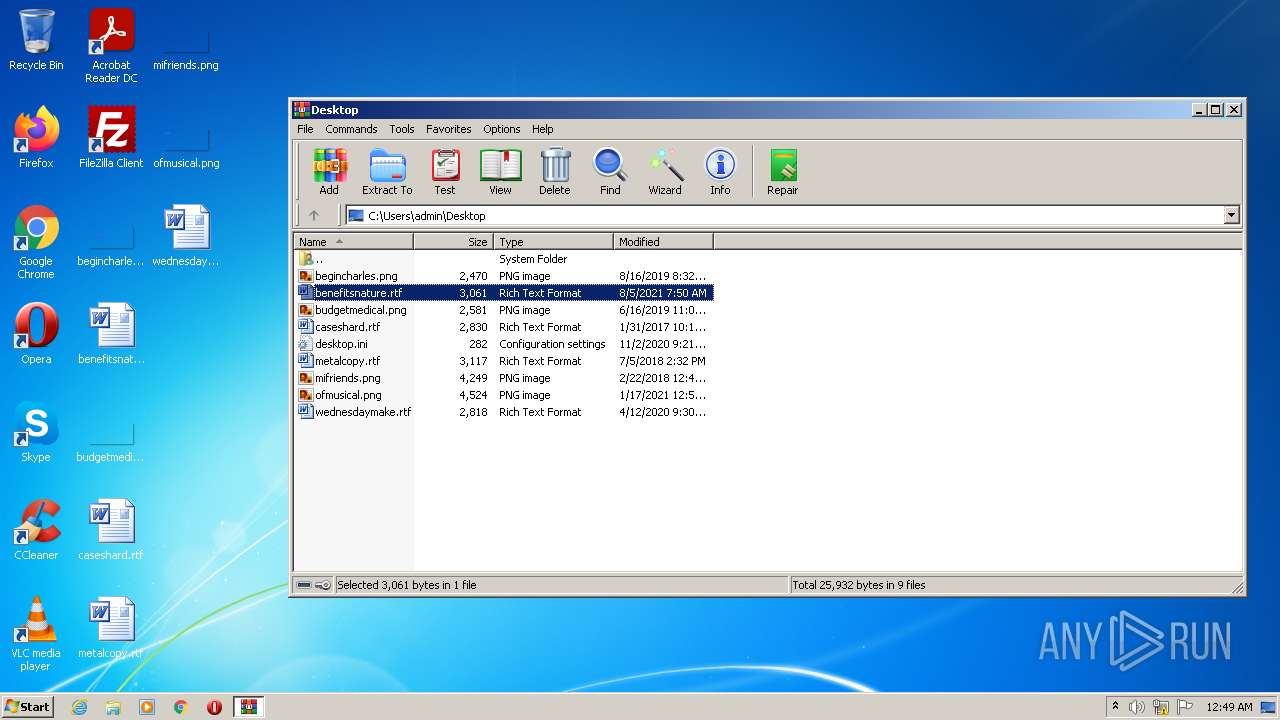
| 1572 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\benefitsnature.rtf" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | WinRAR.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 1900 | C:\Windows\system32\DllHost.exe /Processid:{76D0CB12-7604-4048-B83C-1005C7DDC503} | C:\Windows\system32\DllHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1912 | "C:\Users\admin\AppData\Local\Temp\winrar-x32-611.exe" | C:\Users\admin\AppData\Local\Temp\winrar-x32-611.exe | Explorer.EXE | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: HIGH Description: WinRAR archiver Exit code: 0 Version: 6.11.0 Modules
| |||||||||||||||
| 2316 | "C:\Program Files\WinRAR\uninstall.exe" /setup | C:\Program Files\WinRAR\uninstall.exe | — | winrar-x32-611.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: HIGH Description: Uninstall WinRAR Exit code: 0 Version: 6.11.0 Modules
| |||||||||||||||
| 2908 | "C:\Users\admin\AppData\Local\Temp\winrar-x32-611.exe" | C:\Users\admin\AppData\Local\Temp\winrar-x32-611.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 3221226540 Version: 6.11.0 Modules
| |||||||||||||||
| 2936 | C:\Windows\system32\DllHost.exe /Processid:{76D0CB12-7604-4048-B83C-1005C7DDC503} | C:\Windows\system32\DllHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3312 | C:\Windows\system32\DllHost.exe /Processid:{76D0CB12-7604-4048-B83C-1005C7DDC503} | C:\Windows\system32\DllHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
12 162
Read events
10 805
Write events
780
Delete events
577
Modification events
| (PID) Process: | (1912) winrar-x32-611.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (1912) winrar-x32-611.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (1912) winrar-x32-611.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (1912) winrar-x32-611.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (1912) winrar-x32-611.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (1912) winrar-x32-611.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (1912) winrar-x32-611.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (1912) winrar-x32-611.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR SFX |
| Operation: | write | Name: | C%%Program Files%WinRAR |
Value: C:\Program Files\WinRAR | |||
| (PID) Process: | (2316) uninstall.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Setup\.rar |
| Operation: | write | Name: | Set |
Value: 1 | |||
| (PID) Process: | (2316) uninstall.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Setup\.zip |
| Operation: | write | Name: | Set |
Value: 1 | |||
Executable files
10
Suspicious files
5
Text files
9
Unknown types
25
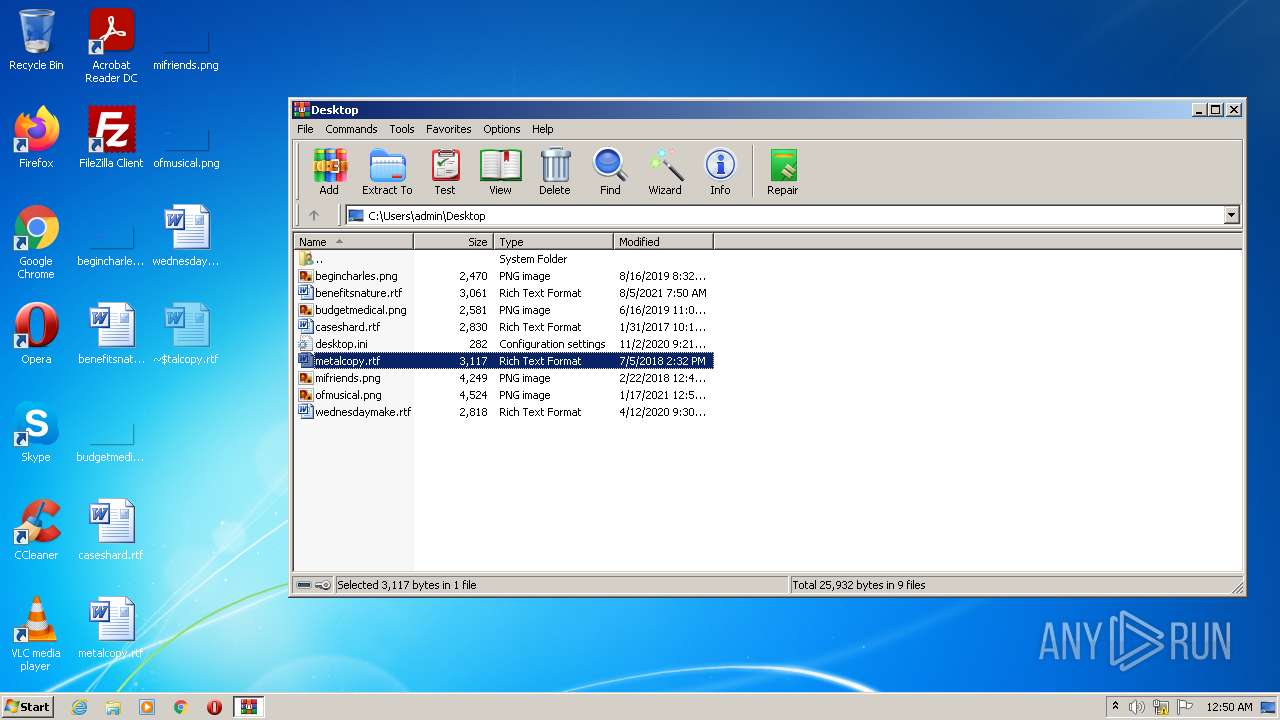
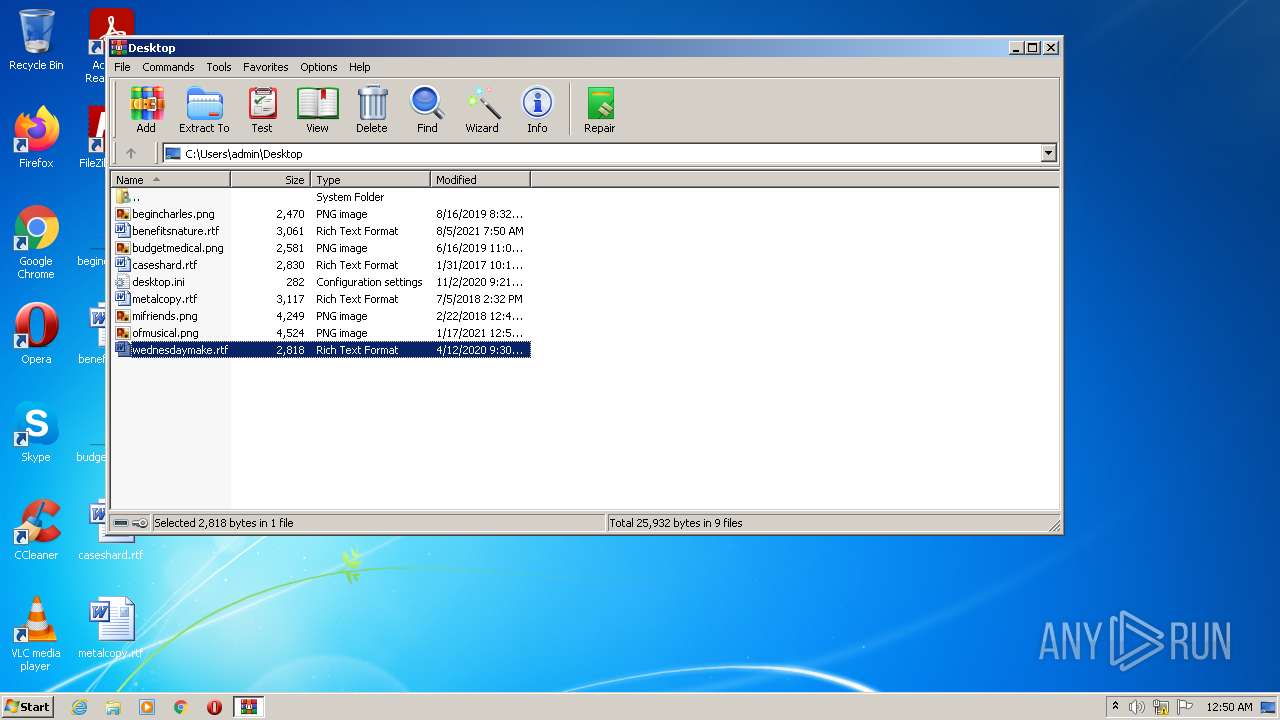
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1912 | winrar-x32-611.exe | C:\Program Files\WinRAR\Uninstall.exe | executable | |
MD5:— | SHA256:— | |||
| 1572 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR4563.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 1912 | winrar-x32-611.exe | C:\Program Files\WinRAR\ReadMe.txt | text | |
MD5:00D0A57A6D64EE3DE8F4D5529D6C6447 | SHA256:FCD13E1B97AF47B8B923BA97AE15E9731C66093609667C3171D5DD24A6F7F2E6 | |||
| 1912 | winrar-x32-611.exe | C:\Program Files\WinRAR\WhatsNew.txt | text | |
MD5:D4C768C52EE077EB09BAC094F4AF8310 | SHA256:8089DFBEBDF2142C7F60F5C12098859417B3C997F0B24B696CCAA78A50F3726C | |||
| 1912 | winrar-x32-611.exe | C:\Program Files\WinRAR\Order.htm | html | |
MD5:5C336DE3B3D794322AD9E5915E3A509F | SHA256:BCE29EF3B95306CB7B304FB8C3039BE7157356D9F9D4E7E1C6BFBF02A117F48F | |||
| 1912 | winrar-x32-611.exe | C:\Program Files\WinRAR\RarExt.dll | executable | |
MD5:1F3BB0F89E7CD67A76220EA2E3E7D8C6 | SHA256:68ECB747F523D122C1C2094B3FB6035F7F76FBD948A97E3D42EE526824546FEC | |||
| 1912 | winrar-x32-611.exe | C:\Program Files\WinRAR\Uninstall.lst | text | |
MD5:34BE8F16B04C175C40630A92D40F82E6 | SHA256:7CD94B59159B6C353E4F50F8AE26D4D8DF6AE7405CA0B68914E89FEA1C5183F5 | |||
| 1912 | winrar-x32-611.exe | C:\Program Files\WinRAR\Rar.exe | executable | |
MD5:300D43860DC6961BBECE819912C930BC | SHA256:792708CE3FEC9DA37408CE4179B118D79B4804878D233C602B490C3BD0EAF02A | |||
| 1912 | winrar-x32-611.exe | C:\Program Files\WinRAR\UnRAR.exe | executable | |
MD5:7B20A77FDD2307781F2256E448944B8A | SHA256:98D5500FA8640CC12D272D631814067252DC4CEC857E41000DA7B26071CDC05C | |||
| 652 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR8F6C.tmp.cvr | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report