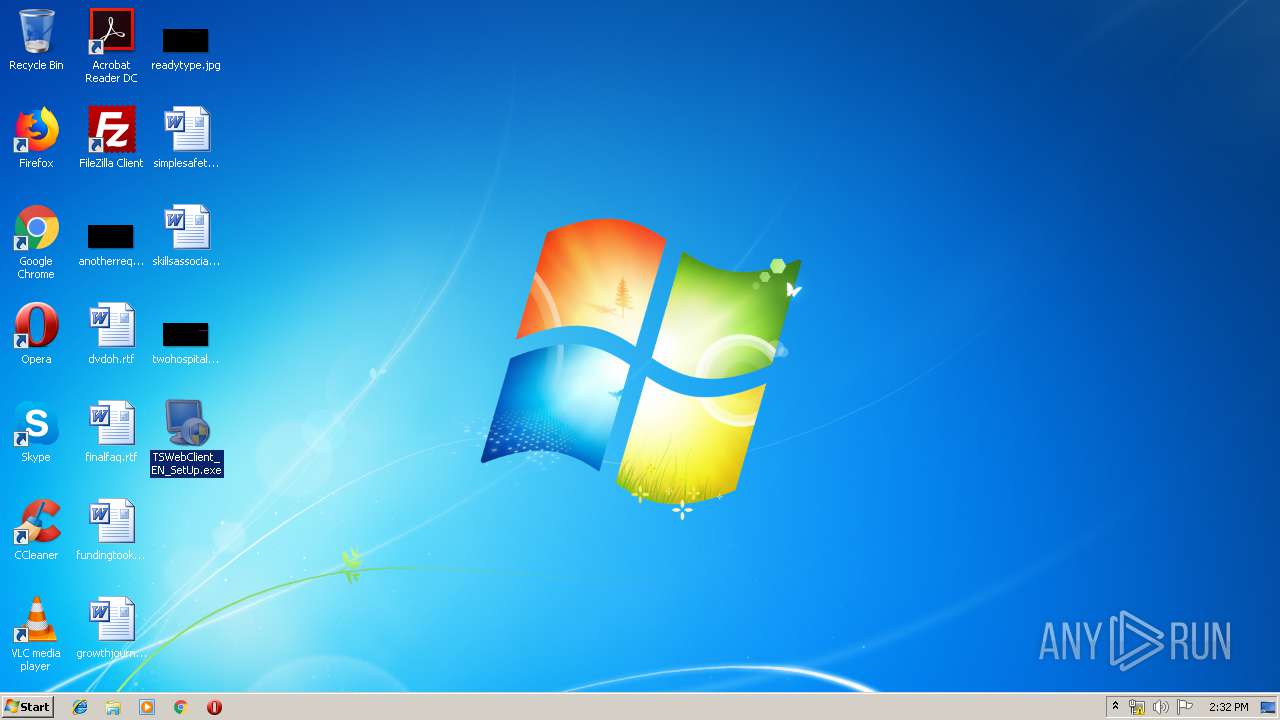
| File name: | TSWebClient_EN_SetUp.exe |
| Full analysis: | https://app.any.run/tasks/44f59e73-d92d-4214-9fbf-6069a7764a53 |
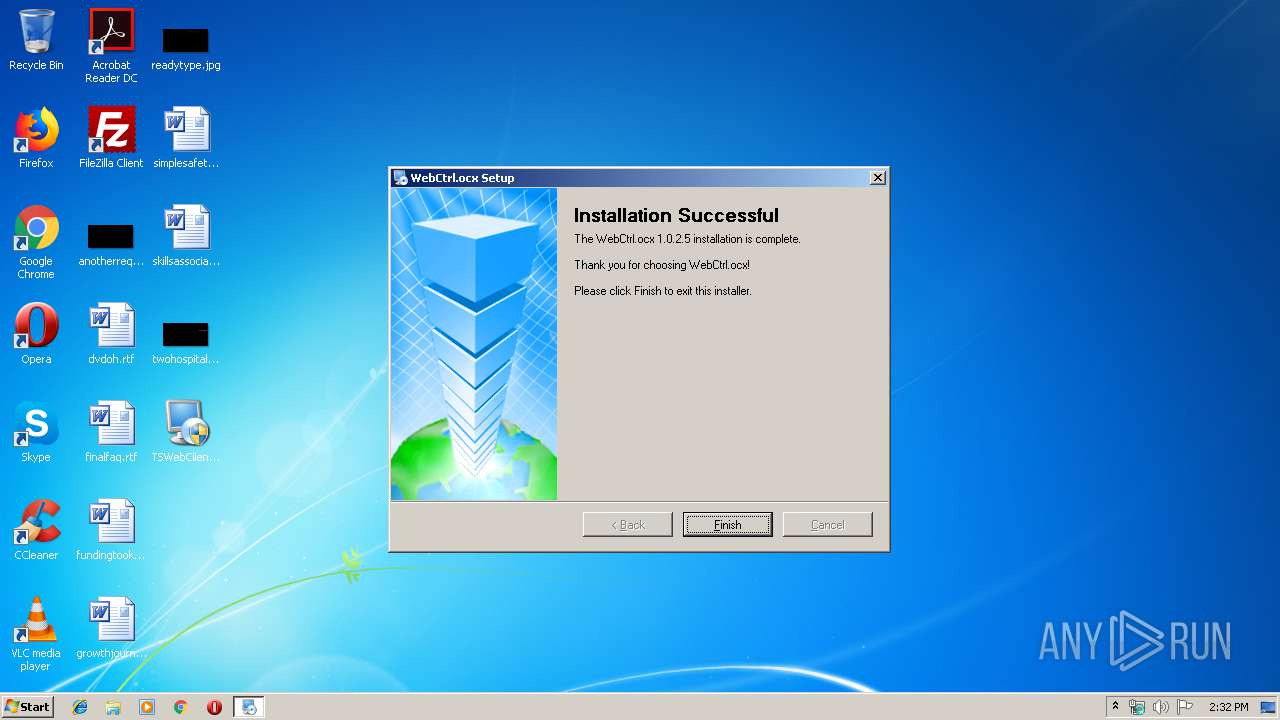
| Verdict: | Malicious activity |
| Analysis date: | December 17, 2019, 14:31:40 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | E8F0184E99DAB82FD95E06B0BF8D949A |
| SHA1: | DDF6B4E625D33BF332F3A17F691FF57BC4BC5F42 |
| SHA256: | 61217BF7ADB1AF5BC4783063844BF668EF3EE354D33E9F66314AA69CF1378B16 |
| SSDEEP: | 393216:Uc4m+fpsrCDP9yl5Mt7g+FBgcqS5nUTlCAv4mB3:UnCuDP9kCt7J7glSqTlLL1 |
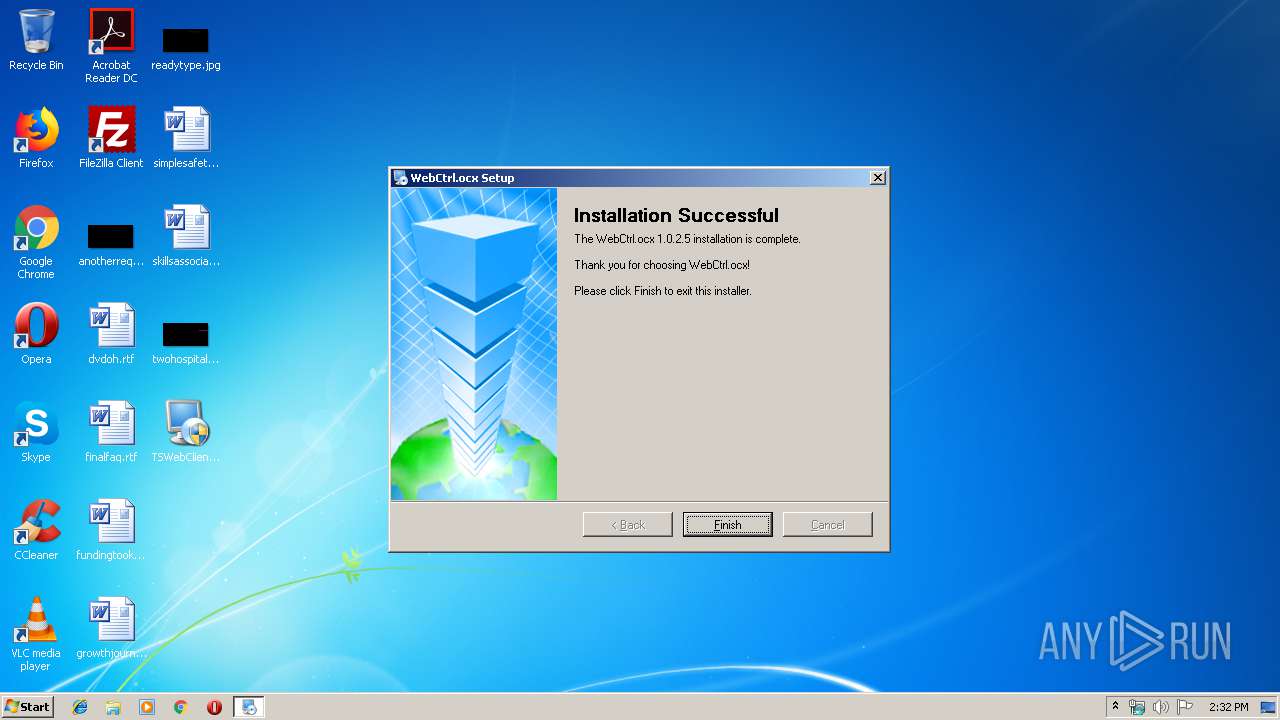
MALICIOUS
Application was dropped or rewritten from another process
- irsetup.exe (PID: 4016)
- irsetup.exe (PID: 3248)
- irsetup.exe (PID: 1044)
Loads dropped or rewritten executable
- irsetup.exe (PID: 4016)
- irsetup.exe (PID: 3248)
- irsetup.exe (PID: 1044)
SUSPICIOUS
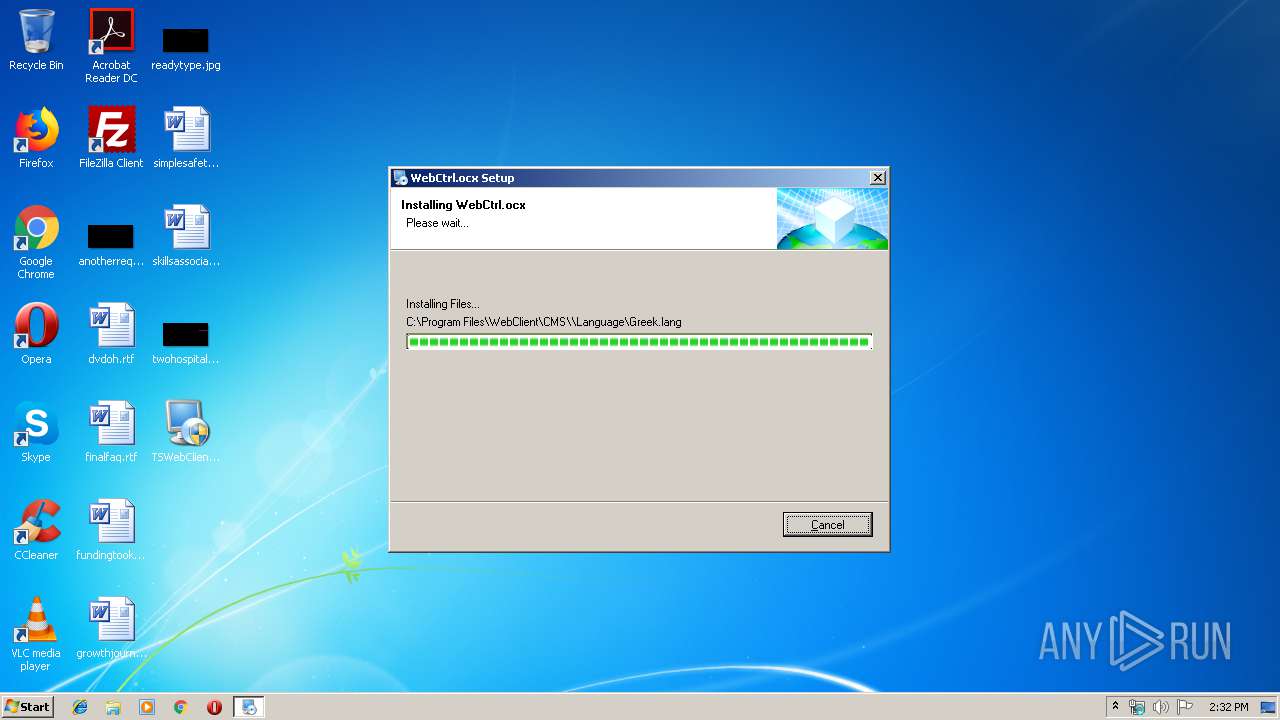
Creates files in the Windows directory
- irsetup.exe (PID: 4016)
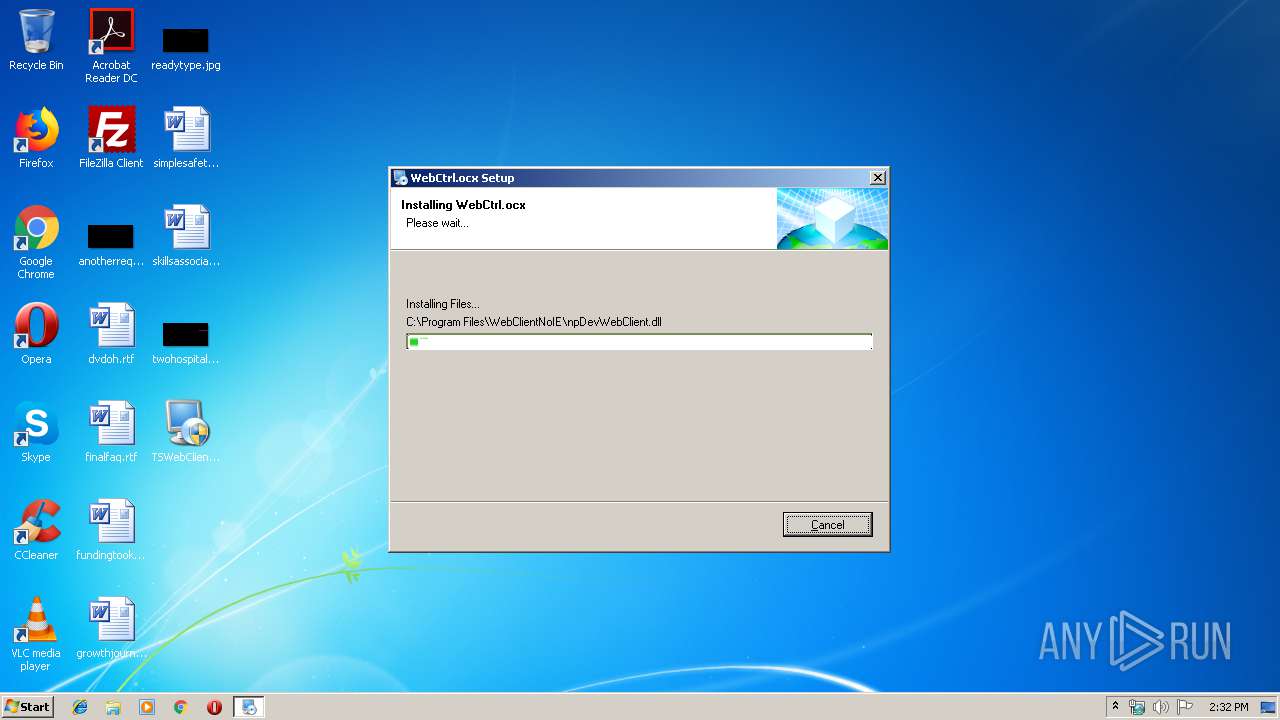
Creates files in the program directory
- irsetup.exe (PID: 3248)
- irsetup.exe (PID: 1044)
- irsetup.exe (PID: 4016)
Creates COM task schedule object
- irsetup.exe (PID: 4016)
- irsetup.exe (PID: 3248)
- irsetup.exe (PID: 1044)
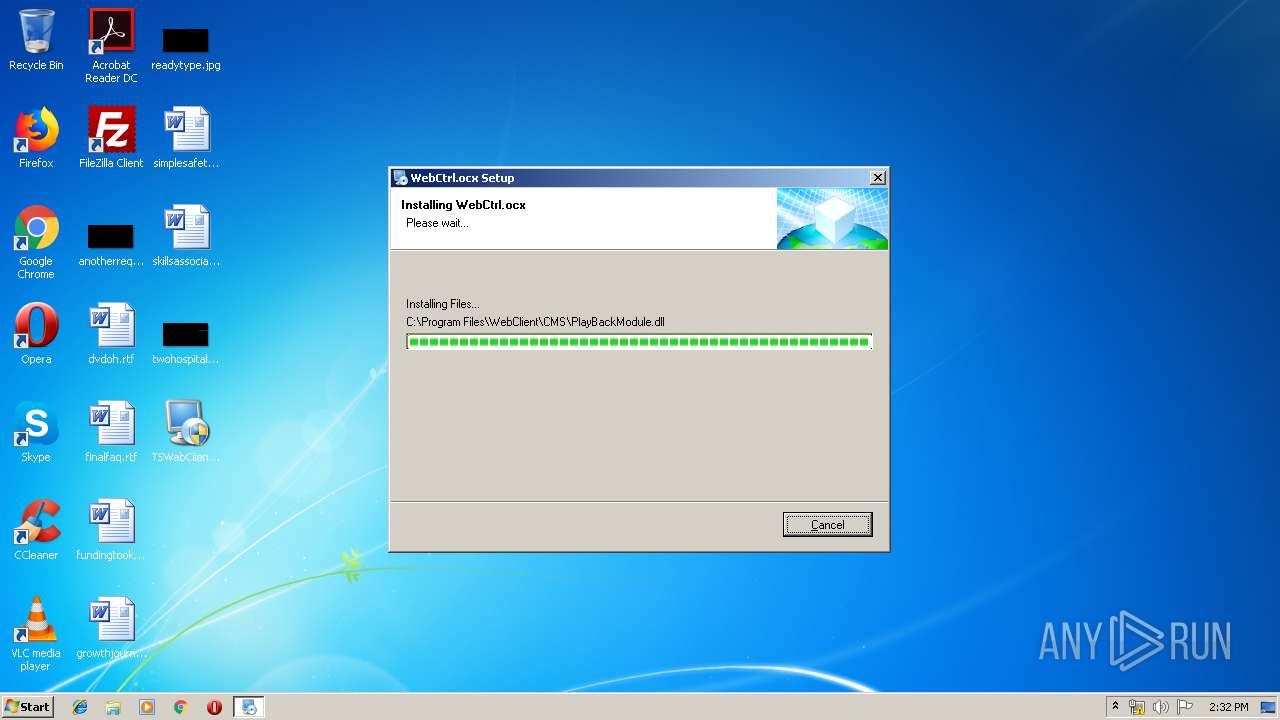
Executable content was dropped or overwritten
- irsetup.exe (PID: 3248)
- TSWebClient_EN_SetUp.exe (PID: 2416)
- irsetup.exe (PID: 4016)
- TSWebClient_EN_SetUp.exe (PID: 1796)
- TSWebClient_EN_SetUp.exe (PID: 3888)
- irsetup.exe (PID: 1044)
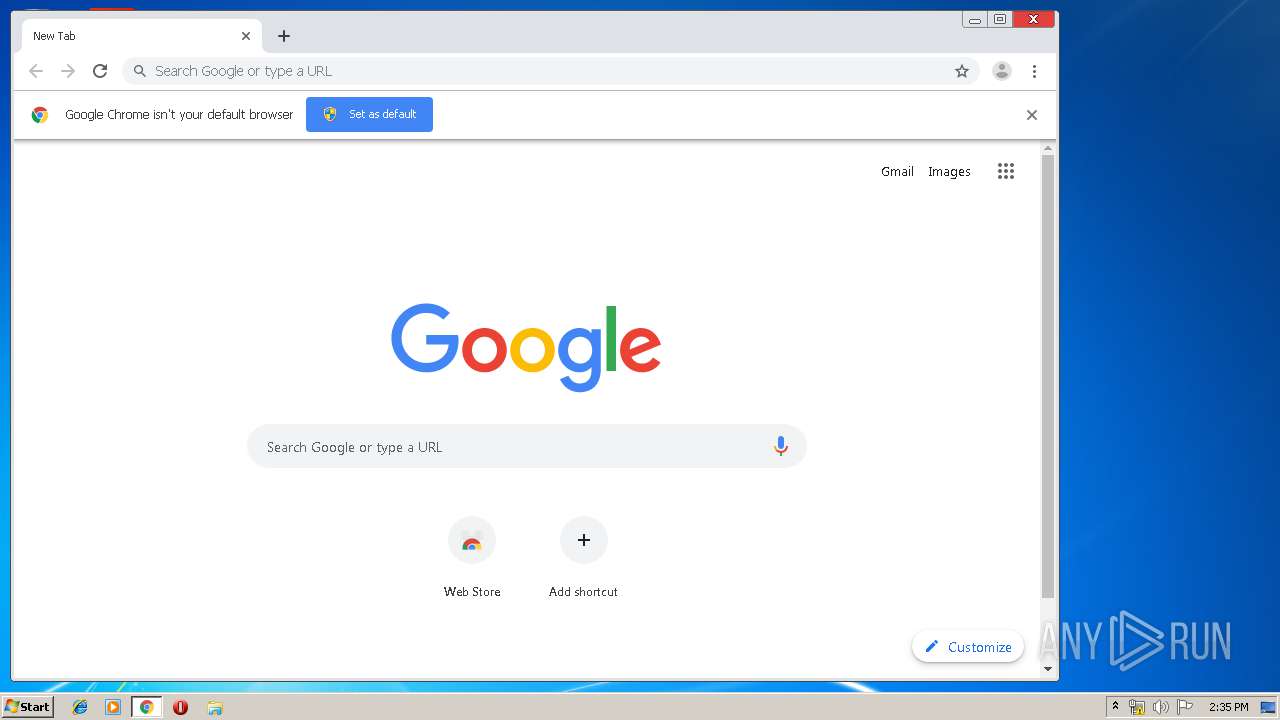
Modifies files in Chrome extension folder
- chrome.exe (PID: 3276)
INFO
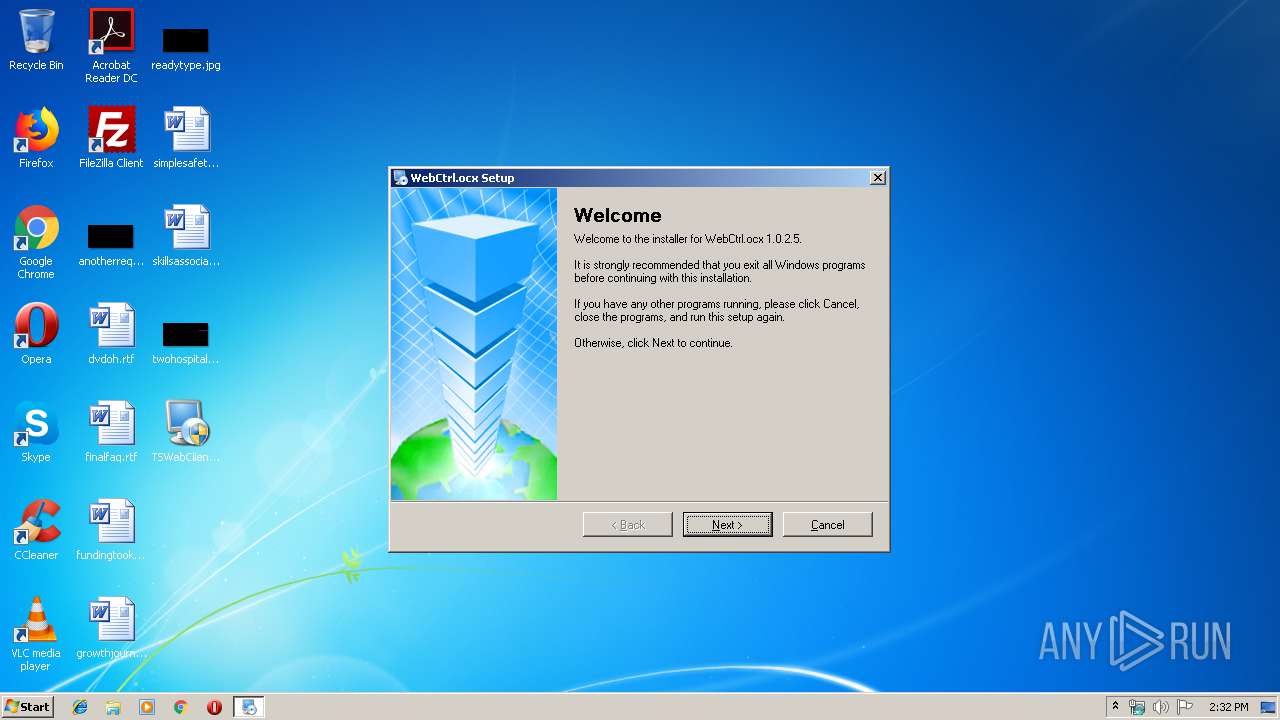
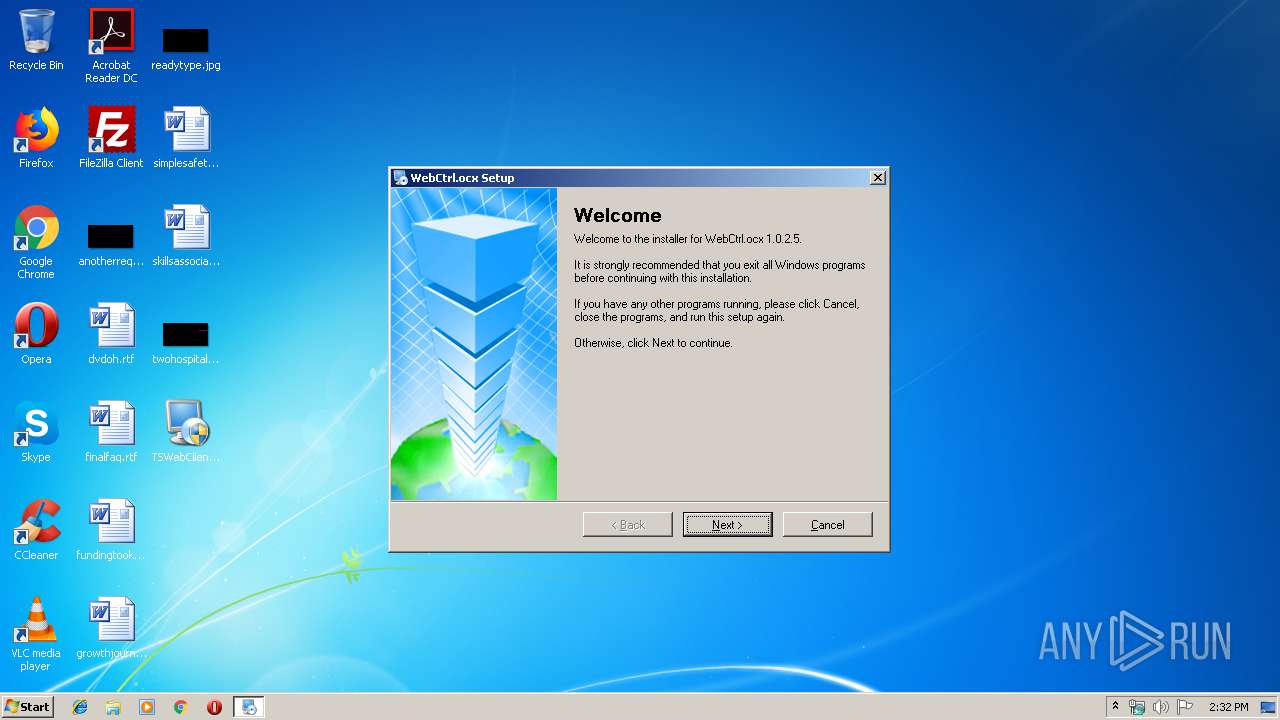
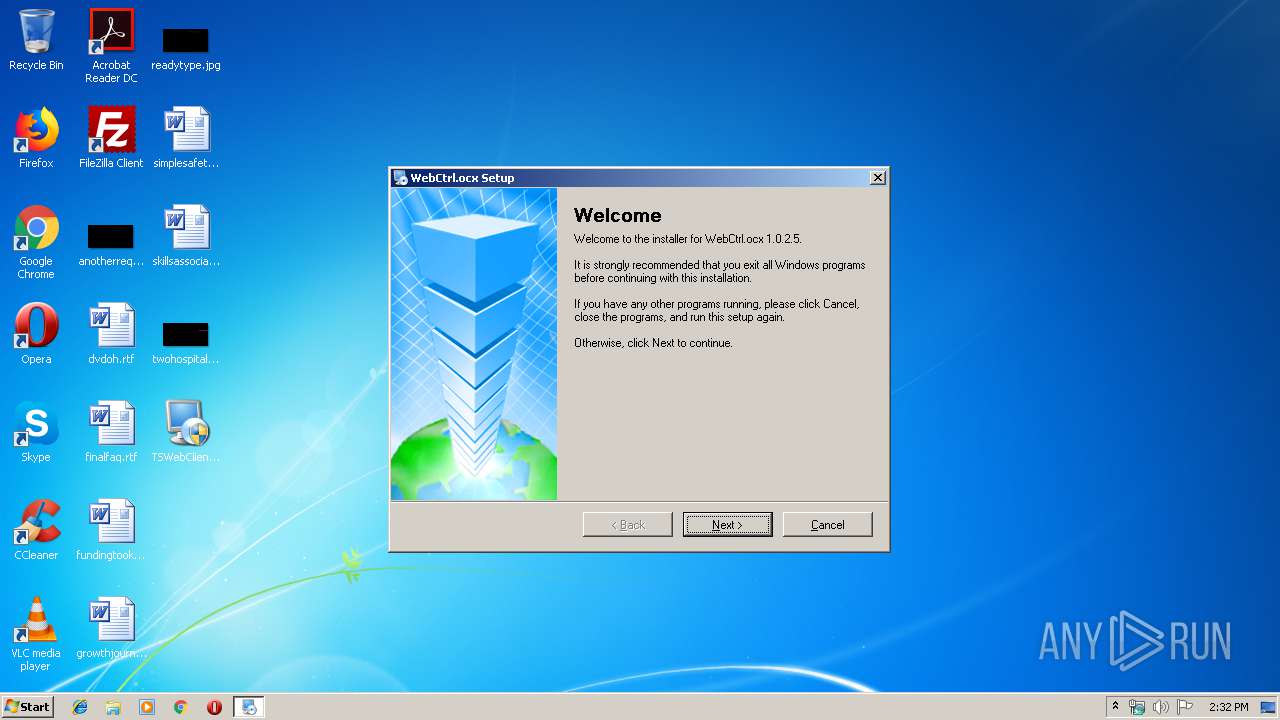
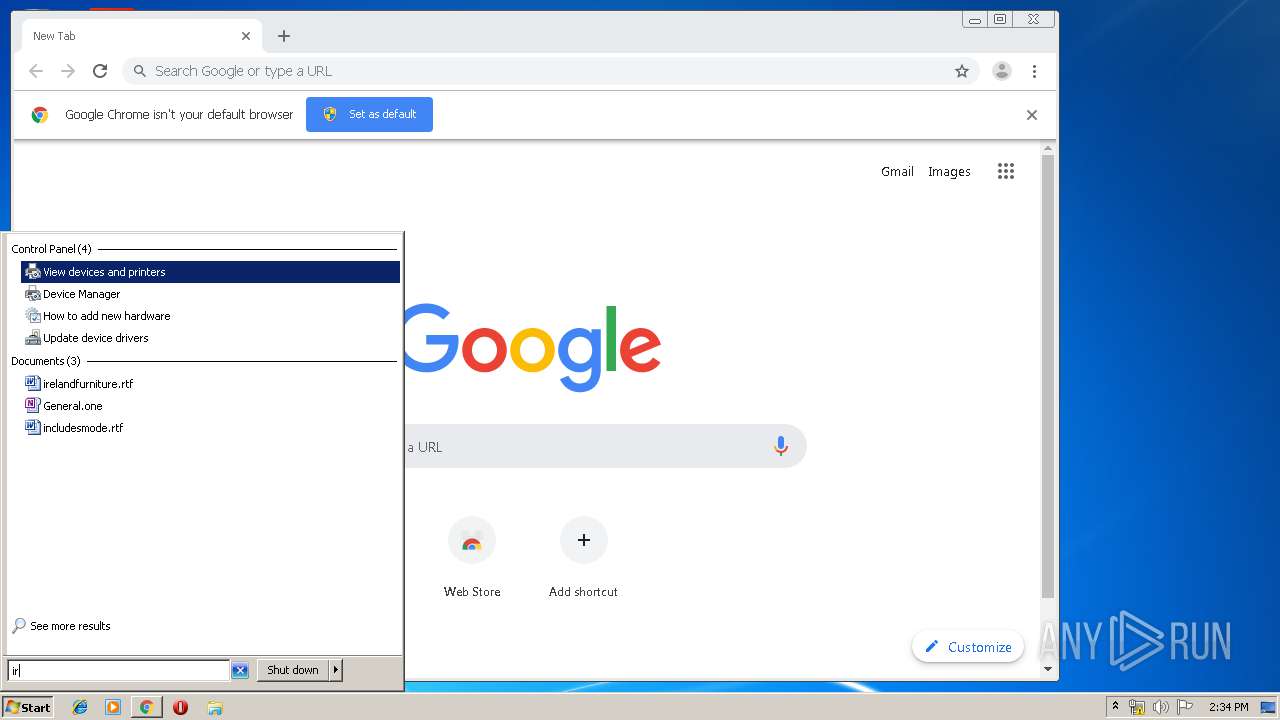
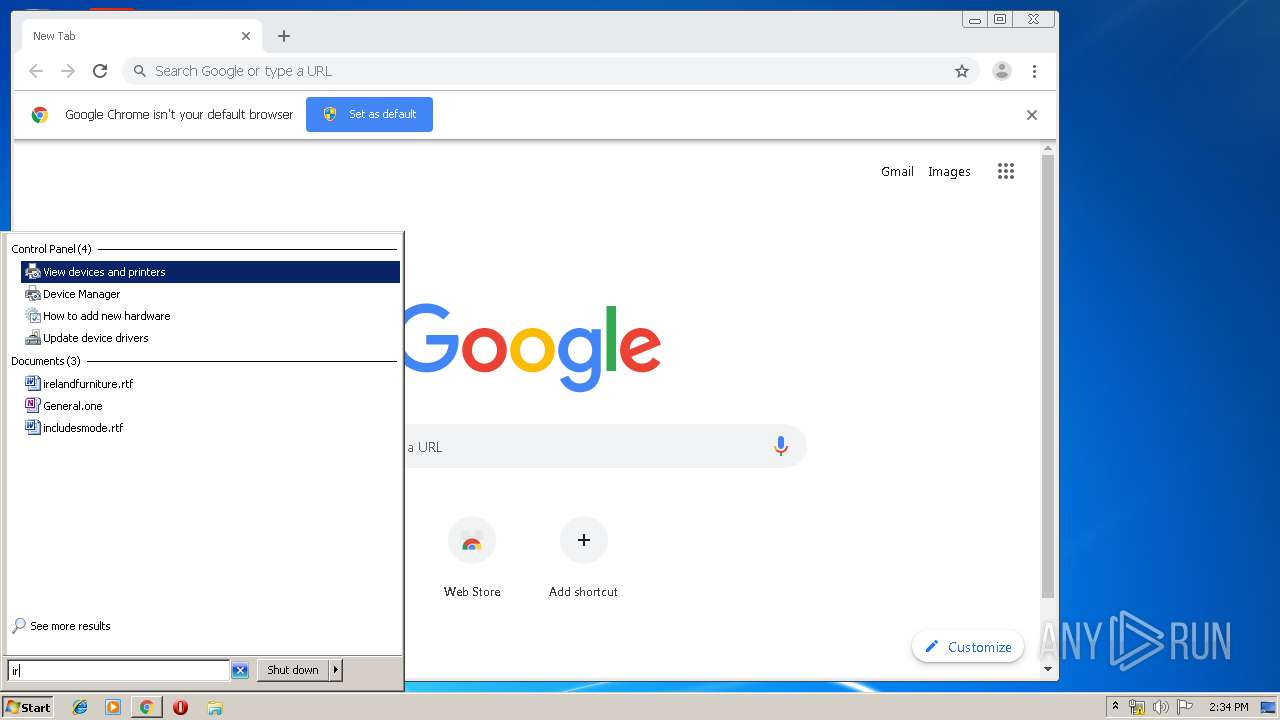
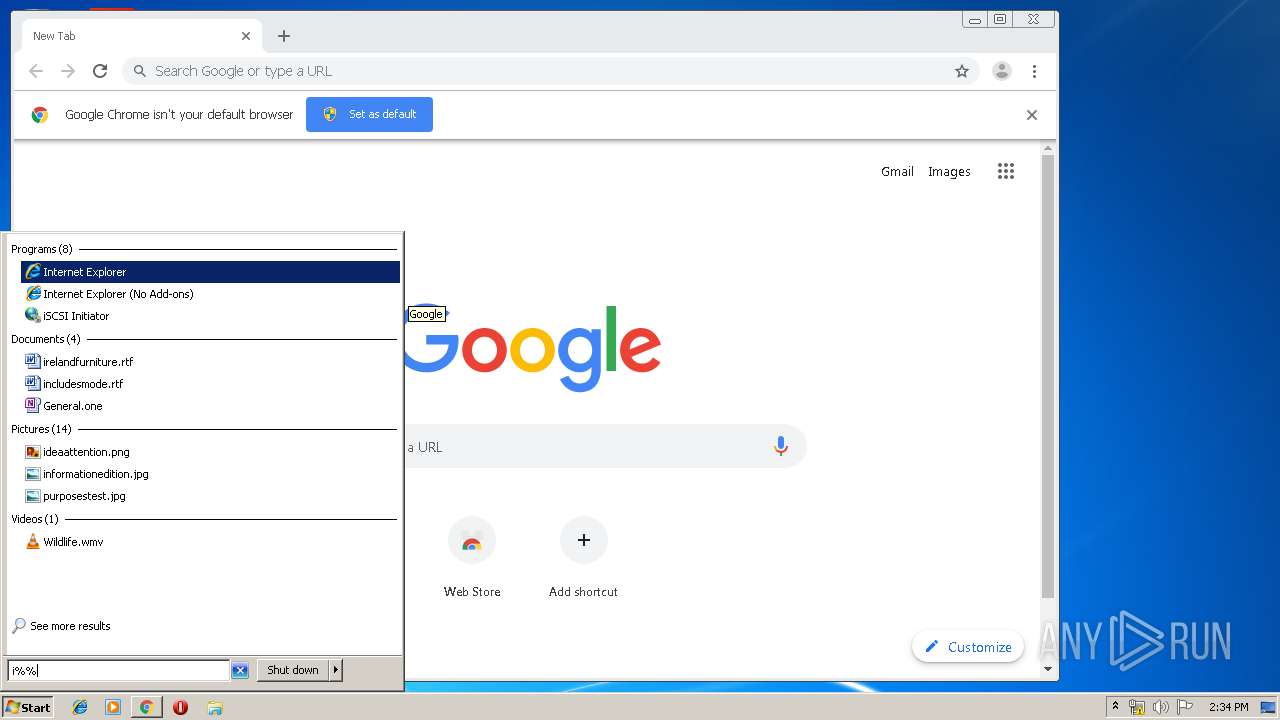
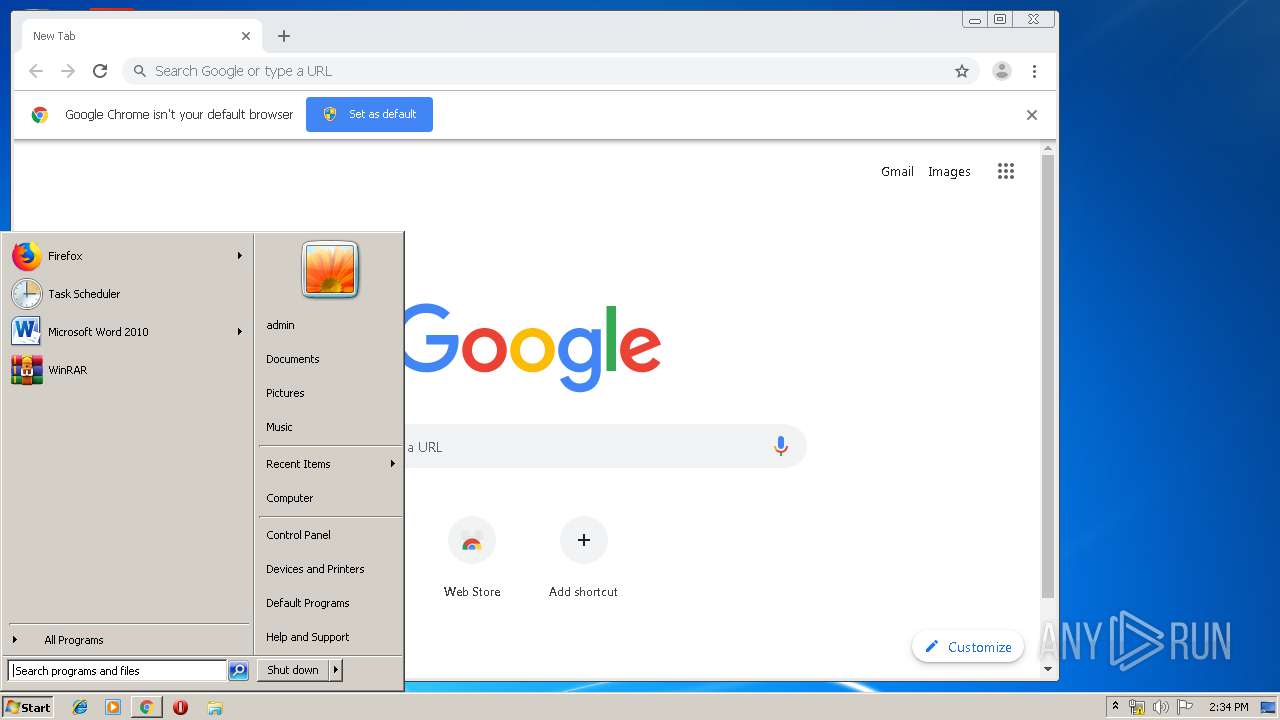
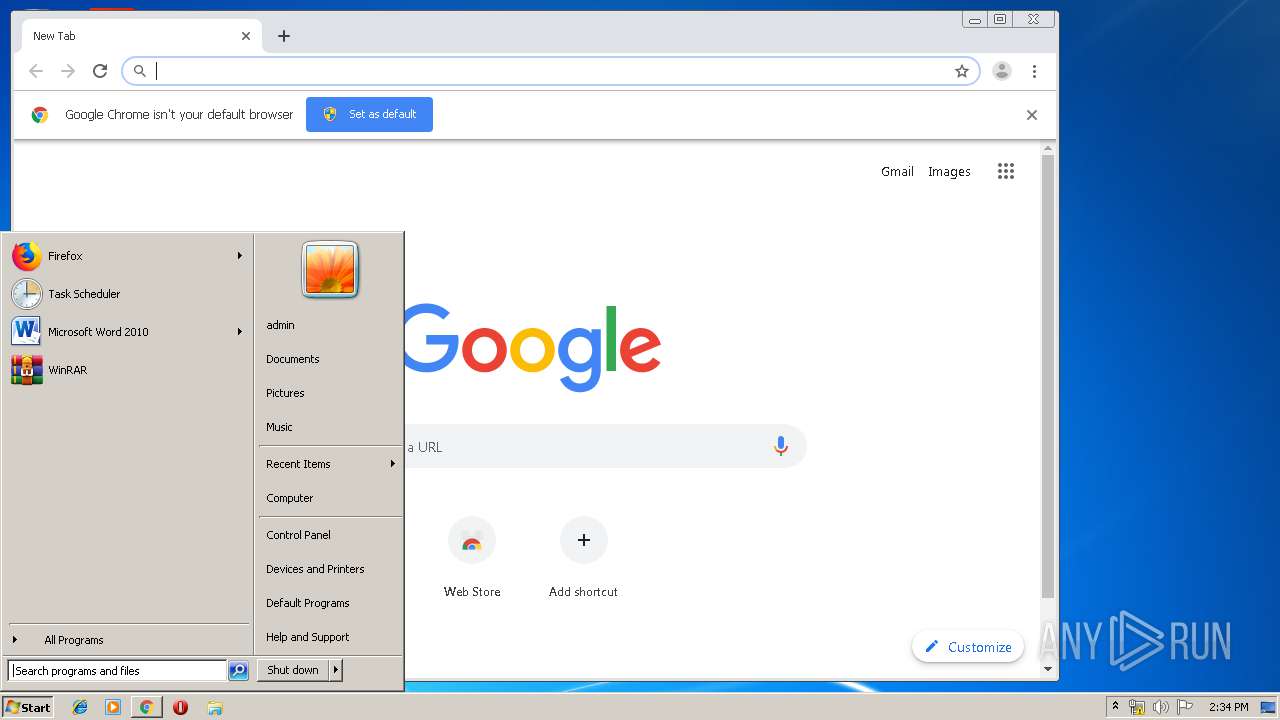
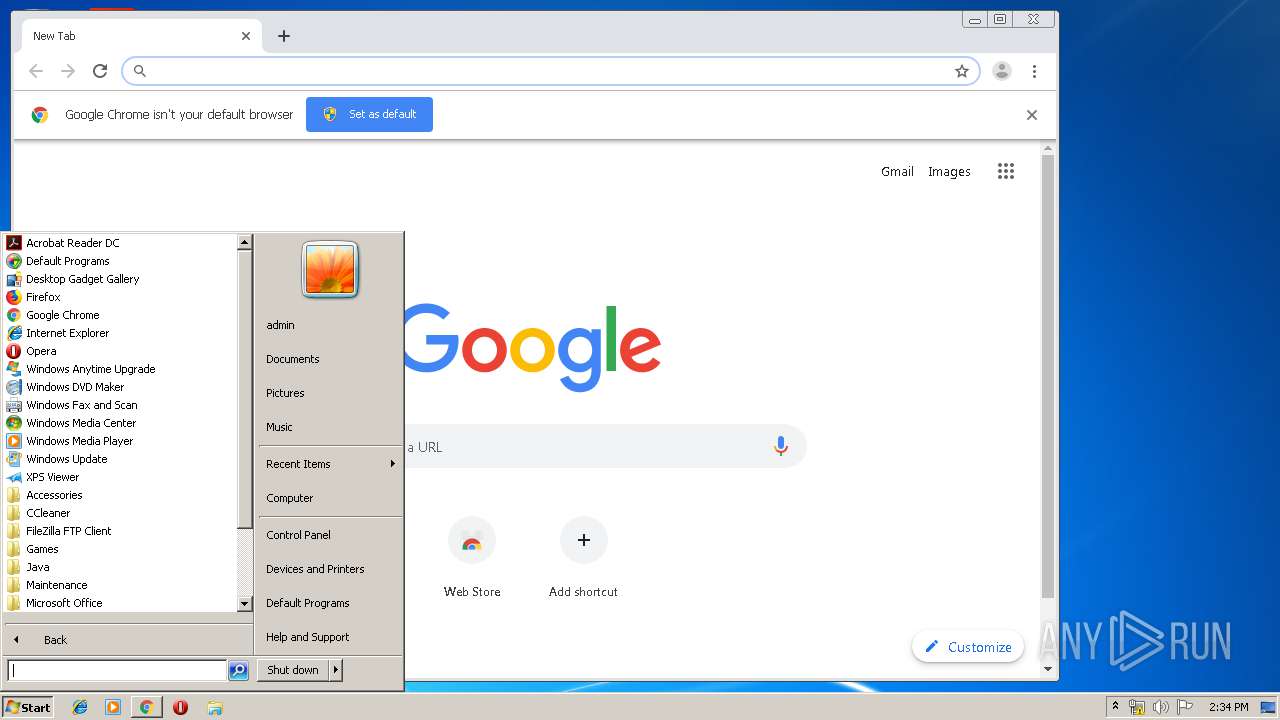
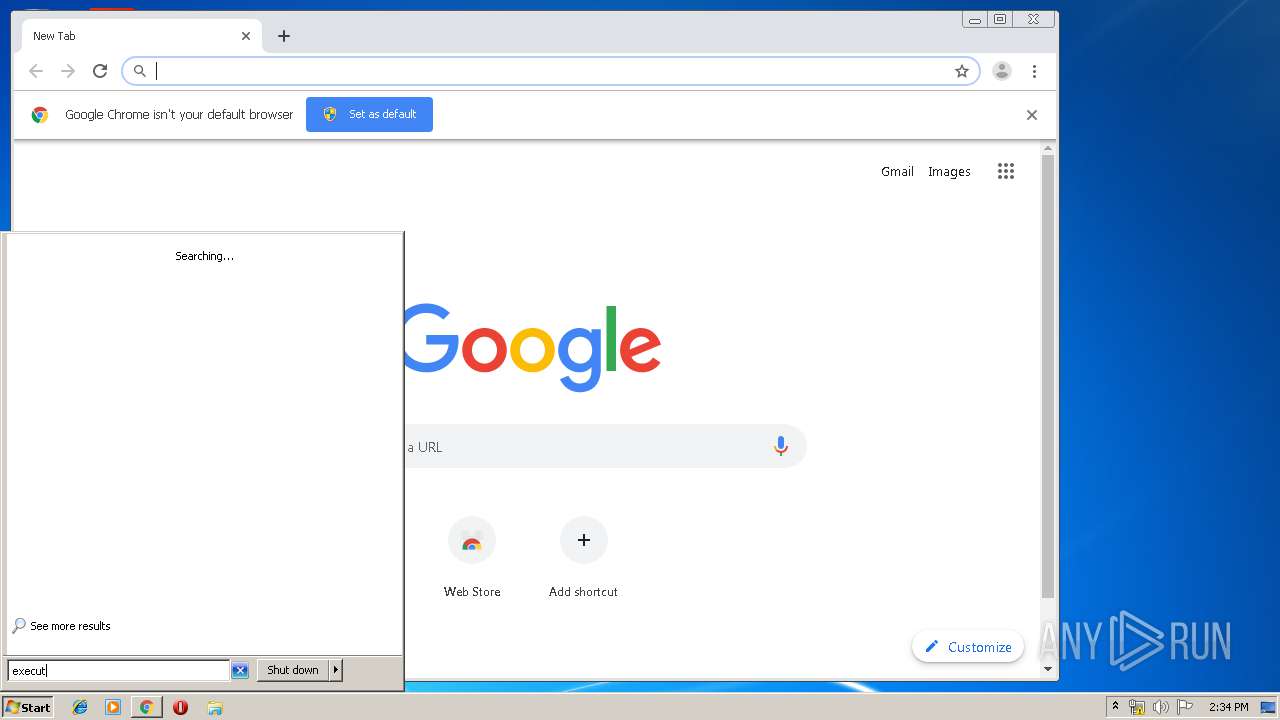
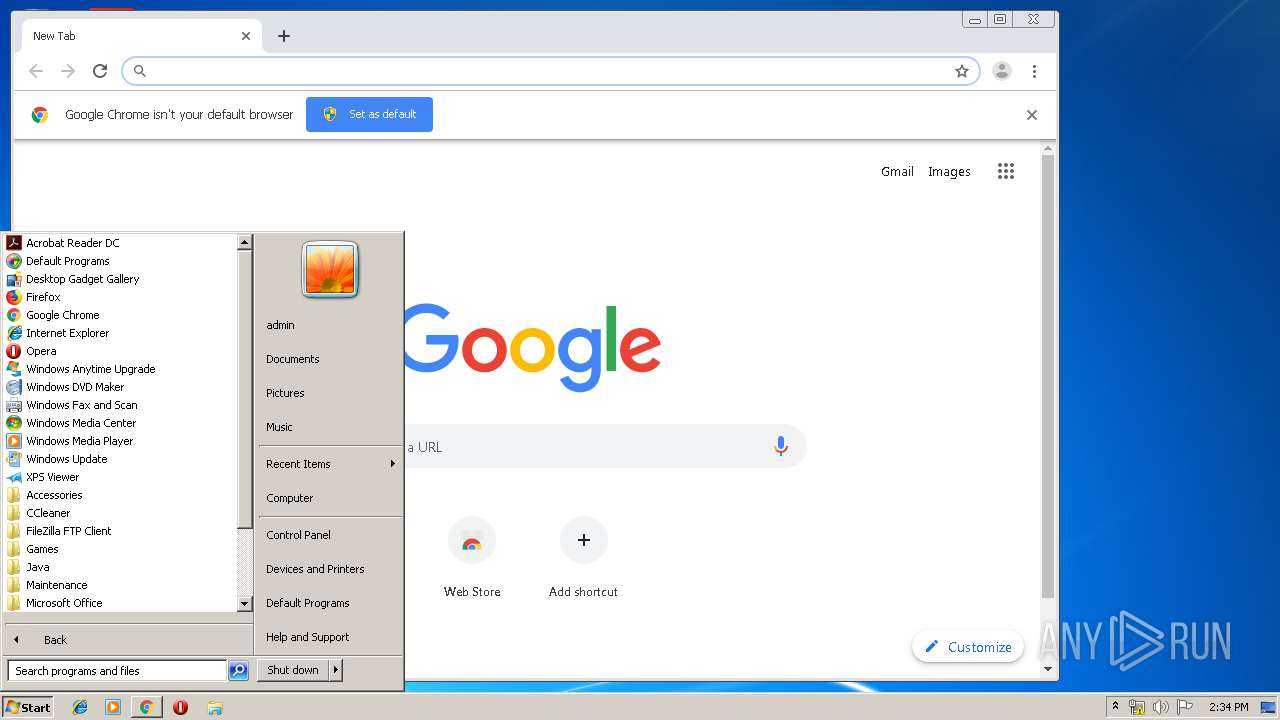
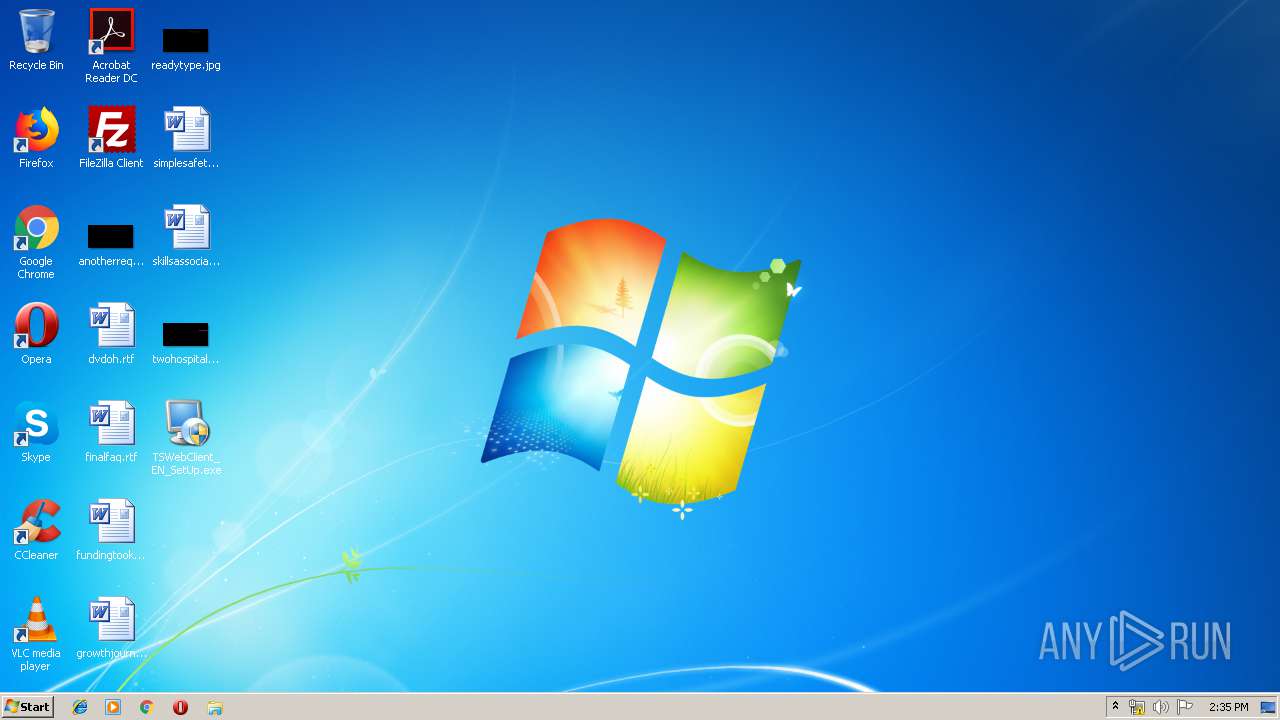
Manual execution by user
- TSWebClient_EN_SetUp.exe (PID: 504)
- TSWebClient_EN_SetUp.exe (PID: 1796)
- TSWebClient_EN_SetUp.exe (PID: 3888)
- TSWebClient_EN_SetUp.exe (PID: 3820)
- explorer.exe (PID: 2076)
- chrome.exe (PID: 3276)
Reads the hosts file
- chrome.exe (PID: 3276)
- chrome.exe (PID: 1792)
Application launched itself
- chrome.exe (PID: 3276)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (31) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (27.4) |
| .exe | | | Win32 EXE Yoda's Crypter (26.4) |
| .dll | | | Win32 Dynamic Link Library (generic) (6.5) |
| .exe | | | Win32 Executable (generic) (4.4) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2005:02:28 17:42:46+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 20480 |
| InitializedDataSize: | 49152 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1df4 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 7.0.2.0 |
| ProductVersionNumber: | 7.0.2.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | Private build |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
| Comments: | Created with Setup Factory 7.0 |
| CompanyName: | - |
| FileDescription: | Setup Application |
| FileVersion: | 7.0.2.0 |
| InternalName: | suf70_launch |
| LegalCopyright: | Setup Engine Copyright © 2004 Indigo Rose Corporation |
| LegalTrademarks: | Setup Factory is a trademark of Indigo Rose Corporation. |
| OriginalFileName: | suf70_launch.exe |
| PrivateBuild: | - |
| ProductName: | Setup Factory 7.0 Runtime |
| ProductVersion: | 7.0.2.0 |
| SpecialBuild: | - |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 28-Feb-2005 16:42:46 |
| Detected languages: |
|
| Comments: | Created with Setup Factory 7.0 |
| CompanyName: | - |
| FileDescription: | Setup Application |
| FileVersion: | 7.0.2.0 |
| InternalName: | suf70_launch |
| LegalCopyright: | Setup Engine Copyright © 2004 Indigo Rose Corporation |
| LegalTrademarks: | Setup Factory is a trademark of Indigo Rose Corporation. |
| OriginalFilename: | suf70_launch.exe |
| PrivateBuild: | - |
| ProductName: | Setup Factory 7.0 Runtime |
| ProductVersion: | 7.0.2.0 |
| SpecialBuild: | - |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000E0 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 4 |
| Time date stamp: | 28-Feb-2005 16:42:46 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x000048C6 | 0x00005000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.30338 |
.rdata | 0x00006000 | 0x00000D64 | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.71945 |
.data | 0x00007000 | 0x000032E0 | 0x00003000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 1.02247 |
.rsrc | 0x0000B000 | 0x00006930 | 0x00007000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.41164 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 3.39836 | 1100 | UNKNOWN | English - United States | RT_VERSION |
2 | 4.31421 | 1384 | UNKNOWN | English - United States | RT_ICON |
3 | 5.9477 | 1128 | UNKNOWN | English - United States | RT_ICON |
4 | 3.78233 | 744 | UNKNOWN | English - United States | RT_ICON |
5 | 6.14953 | 2216 | UNKNOWN | English - United States | RT_ICON |
6 | 5.83714 | 4264 | UNKNOWN | English - United States | RT_ICON |
7 | 3.64397 | 1640 | UNKNOWN | English - United States | RT_ICON |
8 | 5.84115 | 3752 | UNKNOWN | English - United States | RT_ICON |
9 | 5.41049 | 9640 | UNKNOWN | English - United States | RT_ICON |
101 | 2.89097 | 132 | UNKNOWN | English - United States | RT_GROUP_ICON |
Imports
KERNEL32.dll |
USER32.dll |
Total processes
84
Monitored processes
38
Malicious processes
6
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 392 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1028,361551200739623134,9253027207447147197,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=1799851506330864092 --mojo-platform-channel-handle=3500 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 444 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1028,361551200739623134,9253027207447147197,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=11012868815689386230 --mojo-platform-channel-handle=3852 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 504 | "C:\Users\admin\Desktop\TSWebClient_EN_SetUp.exe" | C:\Users\admin\Desktop\TSWebClient_EN_SetUp.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Setup Application Exit code: 3221226540 Version: 7.0.2.0 Modules
| |||||||||||||||
| 788 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1028,361551200739623134,9253027207447147197,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=17785376909613422470 --mojo-platform-channel-handle=3940 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 856 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1028,361551200739623134,9253027207447147197,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=1068010252259237594 --mojo-platform-channel-handle=4232 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1044 | __IRAOFF:520716 "__IRAFN:C:\Users\admin\Desktop\TSWebClient_EN_SetUp.exe" | C:\Users\admin\AppData\Local\Temp\_ir_sf7_temp_0\irsetup.exe | TSWebClient_EN_SetUp.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Setup Application Exit code: 0 Version: 7.0.1.0 Modules
| |||||||||||||||
| 1316 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=2604 --on-initialized-event-handle=312 --parent-handle=316 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1792 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1028,361551200739623134,9253027207447147197,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=7519587114503700119 --mojo-platform-channel-handle=1604 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1796 | "C:\Users\admin\Desktop\TSWebClient_EN_SetUp.exe" | C:\Users\admin\Desktop\TSWebClient_EN_SetUp.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Setup Application Exit code: 0 Version: 7.0.2.0 Modules
| |||||||||||||||
| 1800 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1028,361551200739623134,9253027207447147197,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=9668032455557246779 --mojo-platform-channel-handle=3468 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
1 127
Read events
772
Write events
318
Delete events
37
Modification events
| (PID) Process: | (4016) irsetup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\TypeLib\{BFB8E4C4-D4C9-4767-9B64-C963E00A75F5}\1.0 |
| Operation: | write | Name: | |
Value: VideoWindow ActiveX Control module | |||
| (PID) Process: | (4016) irsetup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\TypeLib\{BFB8E4C4-D4C9-4767-9B64-C963E00A75F5}\1.0\FLAGS |
| Operation: | write | Name: | |
Value: 2 | |||
| (PID) Process: | (4016) irsetup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\TypeLib\{BFB8E4C4-D4C9-4767-9B64-C963E00A75F5}\1.0\0\win32 |
| Operation: | write | Name: | |
Value: C:\Program Files\WebClient\CMS\VideoWnd.ocx | |||
| (PID) Process: | (4016) irsetup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\TypeLib\{BFB8E4C4-D4C9-4767-9B64-C963E00A75F5}\1.0\HELPDIR |
| Operation: | write | Name: | |
Value: | |||
| (PID) Process: | (4016) irsetup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\Interface\{57C5FB7D-8BDC-4690-BB0A-DDB9289F817F} |
| Operation: | write | Name: | |
Value: _DVideoWindow | |||
| (PID) Process: | (4016) irsetup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\Interface\{57C5FB7D-8BDC-4690-BB0A-DDB9289F817F}\ProxyStubClsid |
| Operation: | write | Name: | |
Value: {00020420-0000-0000-C000-000000000046} | |||
| (PID) Process: | (4016) irsetup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\Interface\{57C5FB7D-8BDC-4690-BB0A-DDB9289F817F}\ProxyStubClsid32 |
| Operation: | write | Name: | |
Value: {00020420-0000-0000-C000-000000000046} | |||
| (PID) Process: | (4016) irsetup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\Interface\{57C5FB7D-8BDC-4690-BB0A-DDB9289F817F}\TypeLib |
| Operation: | write | Name: | |
Value: {BFB8E4C4-D4C9-4767-9B64-C963E00A75F5} | |||
| (PID) Process: | (4016) irsetup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\Interface\{57C5FB7D-8BDC-4690-BB0A-DDB9289F817F}\TypeLib |
| Operation: | write | Name: | Version |
Value: 1.0 | |||
| (PID) Process: | (4016) irsetup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\Interface\{94A4D02D-2EF6-4B56-8202-7002309440A8} |
| Operation: | write | Name: | |
Value: _DVideoWindowEvents | |||
Executable files
57
Suspicious files
35
Text files
371
Unknown types
22
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4016 | irsetup.exe | C:\Users\admin\AppData\Local\Temp\_ir_sf7_temp_0\irsetup.dat | — | |
MD5:— | SHA256:— | |||
| 4016 | irsetup.exe | C:\Windows\WebCtrl.ocx Setup Log.txt | text | |
MD5:— | SHA256:— | |||
| 4016 | irsetup.exe | C:\Program Files\WebClient\CMS\ConfigureModule.dll | executable | |
MD5:— | SHA256:— | |||
| 4016 | irsetup.exe | C:\Program Files\WebClient\CMS\PlayBackModule.dll | executable | |
MD5:— | SHA256:— | |||
| 4016 | irsetup.exe | C:\Program Files\WebClient\CMS\NetSdkModule.dll | executable | |
MD5:— | SHA256:— | |||
| 2416 | TSWebClient_EN_SetUp.exe | C:\Users\admin\AppData\Local\Temp\_ir_sf7_temp_0\irsetup.exe | executable | |
MD5:75CA7FF96BF5A316C3AF2DE6A412BD54 | SHA256:D95B5BF9CA97C1900DE5357743282BAB655D61D616606485088E1708559B7CF1 | |||
| 4016 | irsetup.exe | C:\Program Files\WebClient\CMS\DllDeinterlace.dll | executable | |
MD5:CA1E43C58F45B08DD979189111D66643 | SHA256:E3E85612BF20ADD5240F7308C077FAA4ADE6FD3E313D32836F0FE313D1EB8C3A | |||
| 4016 | irsetup.exe | C:\Program Files\WebClient\CMS\bottom.bmp | image | |
MD5:19C73BD1E1850D762EBF58508608762F | SHA256:E7E3043913EE22EB080DC17D55FEE10FD18D6B27C594523C6D88C1408DEF0B31 | |||
| 4016 | irsetup.exe | C:\Program Files\WebClient\CMS\mp_thumb.jpg | image | |
MD5:019B6EF1743DD24A6D9A970979B65255 | SHA256:5079C33ACED132997F65C49BB70ADCA663C565B2A6653E29705720D1AD265192 | |||
| 4016 | irsetup.exe | C:\Program Files\WebClient\CMS\Dialog.bmp | image | |
MD5:5BF521E12F1F0C663513056D8F6497E0 | SHA256:B9CA267C43C16992708D94982AF777F3CD7E76F7078232655FDDF919BFCB919E | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
22
DNS requests
17
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1792 | chrome.exe | GET | 302 | 172.217.16.46:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 522 b | whitelisted |
1792 | chrome.exe | GET | 302 | 172.217.16.46:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 517 b | whitelisted |
1792 | chrome.exe | GET | 200 | 87.245.222.141:80 | http://r2---sn-gxuo03g-vqne.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx?cms_redirect=yes&mip=185.207.139.2&mm=28&mn=sn-gxuo03g-vqne&ms=nvh&mt=1576592494&mv=u&mvi=1&pl=22&shardbypass=yes | GB | crx | 293 Kb | whitelisted |
1792 | chrome.exe | GET | 200 | 87.245.222.142:80 | http://r3---sn-gxuo03g-vqne.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mip=185.207.139.2&mm=28&mn=sn-gxuo03g-vqne&ms=nvh&mt=1576592494&mv=u&mvi=2&pl=22&shardbypass=yes | GB | crx | 862 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1792 | chrome.exe | 172.217.16.3:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
1792 | chrome.exe | 172.217.16.35:443 | www.google.com.ua | Google Inc. | US | whitelisted |
1792 | chrome.exe | 172.217.16.45:443 | accounts.google.com | Google Inc. | US | whitelisted |
1792 | chrome.exe | 172.217.16.42:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
1792 | chrome.exe | 216.58.215.78:443 | ogs.google.com | Google Inc. | US | whitelisted |
1792 | chrome.exe | 172.217.16.14:443 | apis.google.com | Google Inc. | US | whitelisted |
1792 | chrome.exe | 216.58.215.68:443 | www.google.com | Google Inc. | US | whitelisted |
1792 | chrome.exe | 172.217.16.46:80 | redirector.gvt1.com | Google Inc. | US | whitelisted |
1792 | chrome.exe | 87.245.222.141:80 | r2---sn-gxuo03g-vqne.gvt1.com | RETN Limited | GB | whitelisted |
1792 | chrome.exe | 172.217.16.33:443 | clients2.googleusercontent.com | Google Inc. | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com.ua |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
ogs.google.com |
| whitelisted |
www.google.com |
| malicious |
clients2.google.com |
| whitelisted |