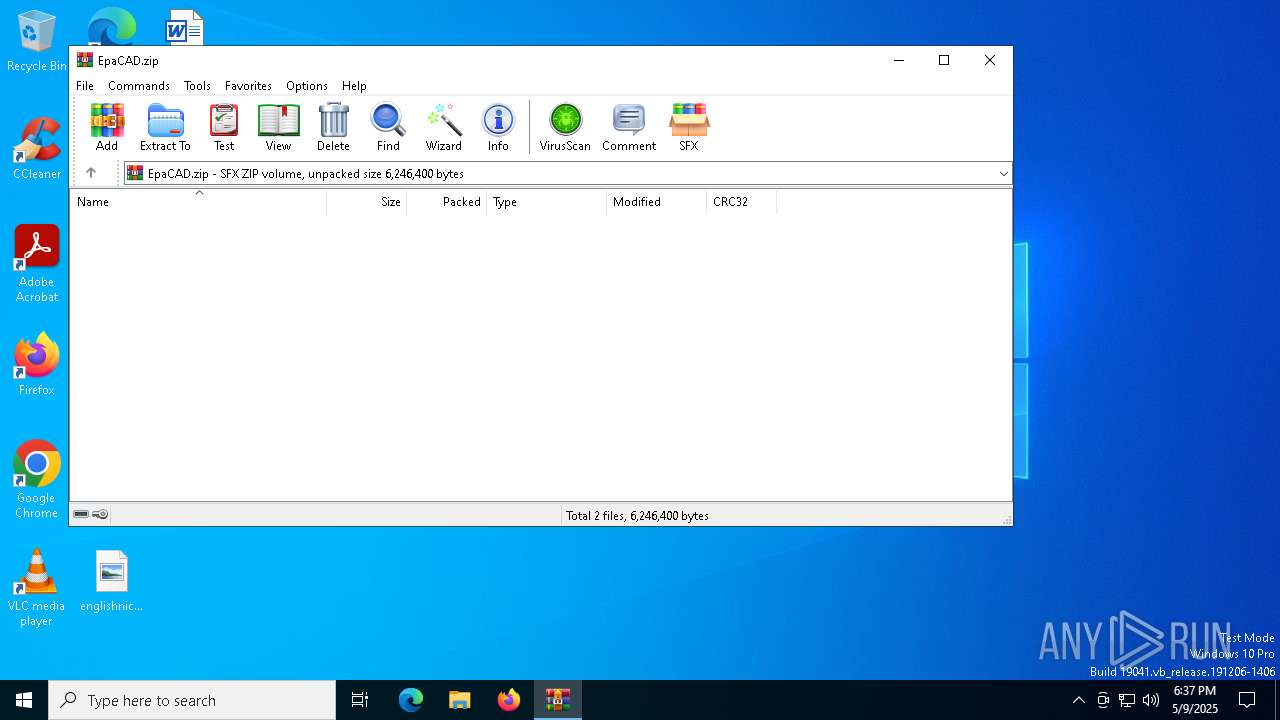
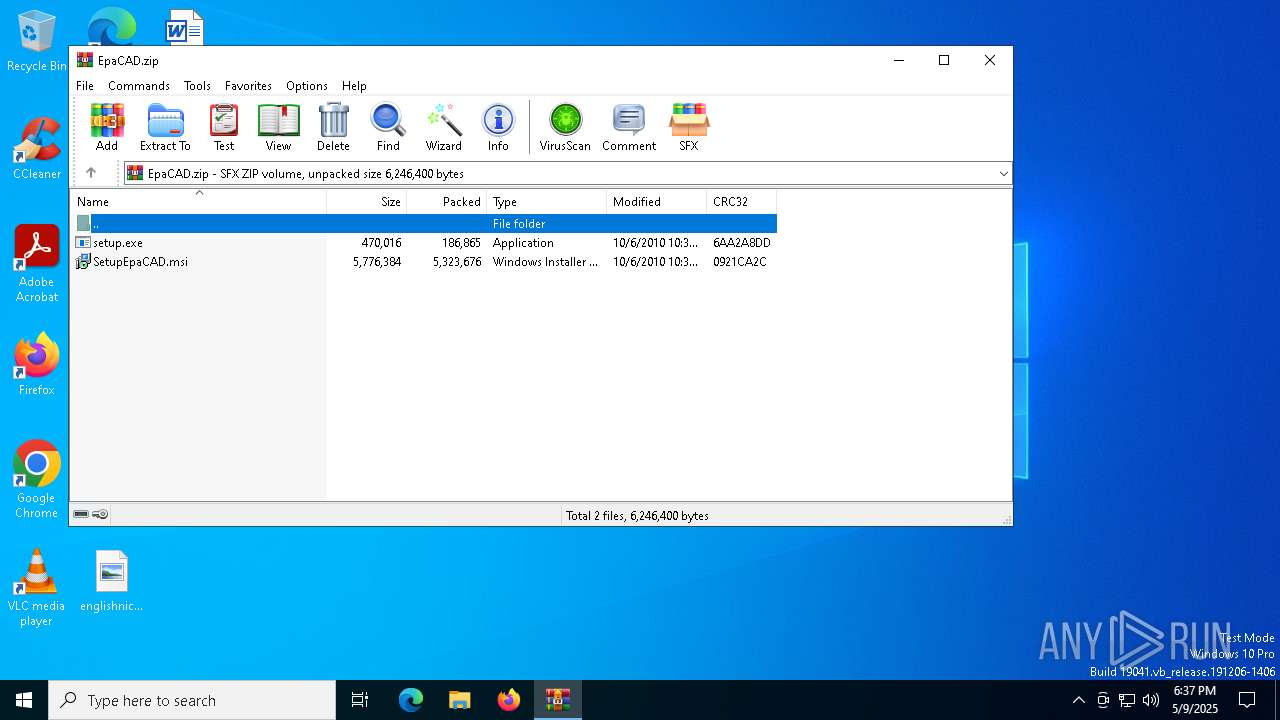
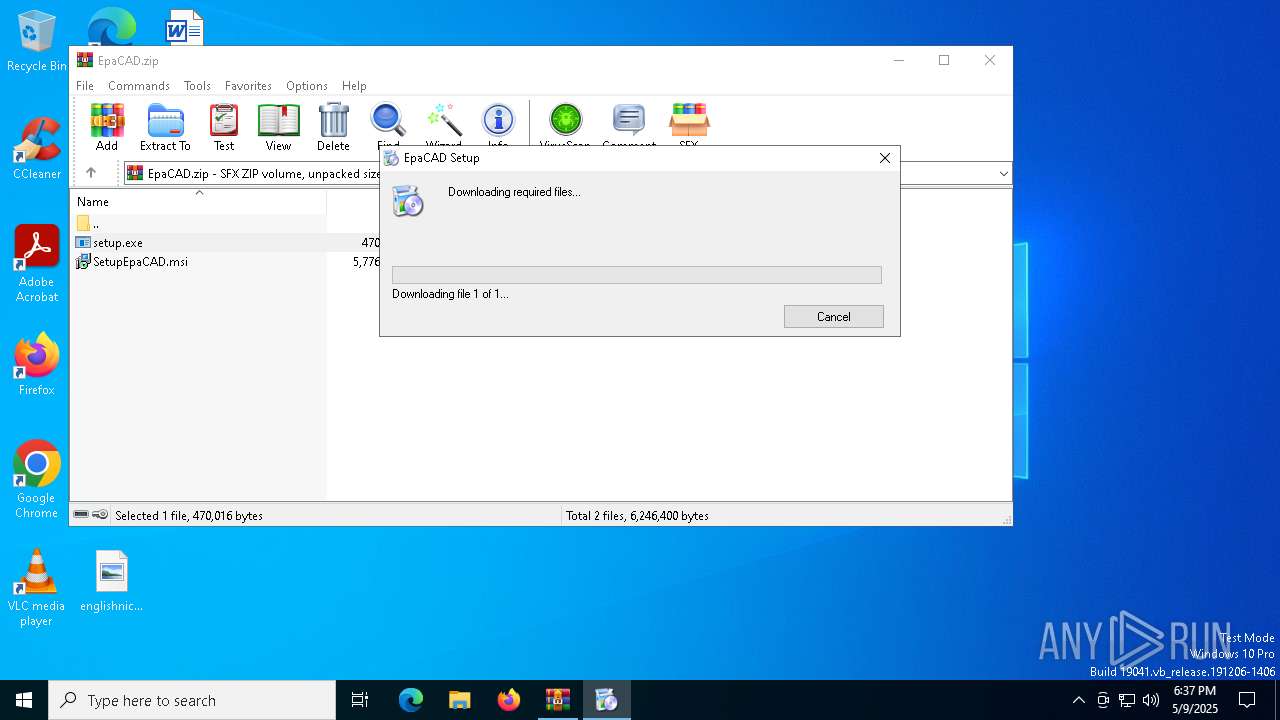
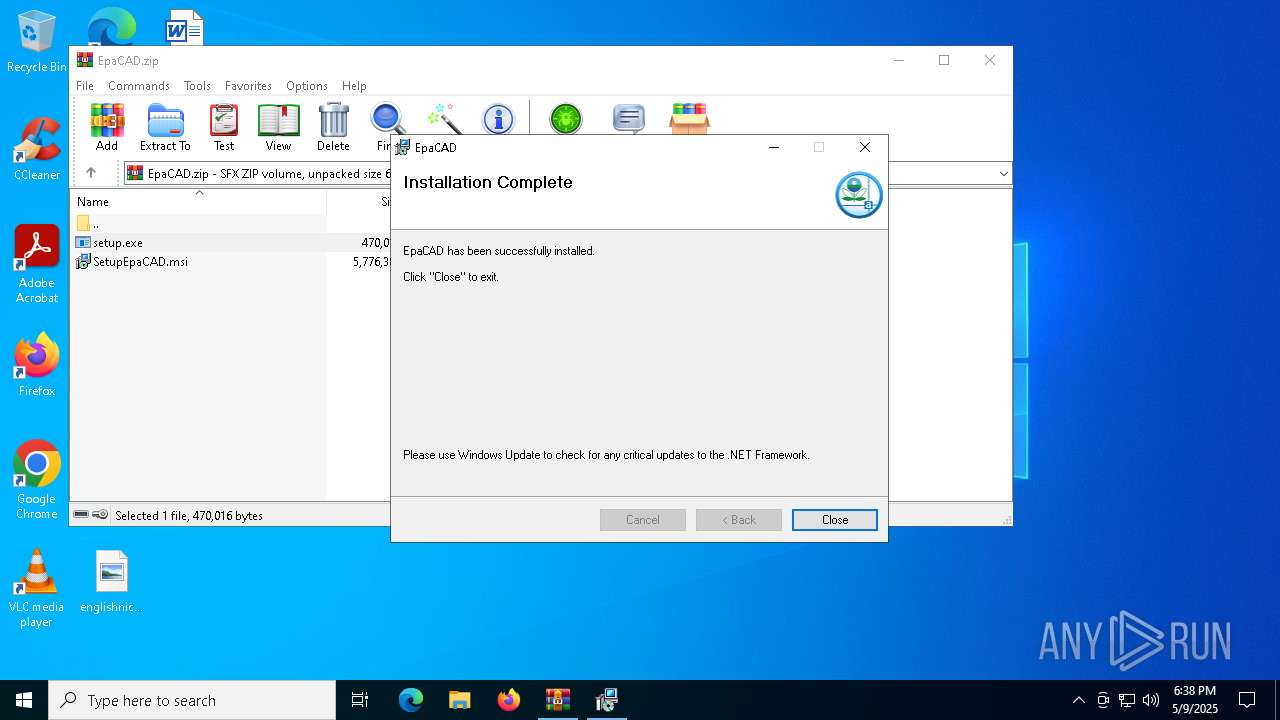
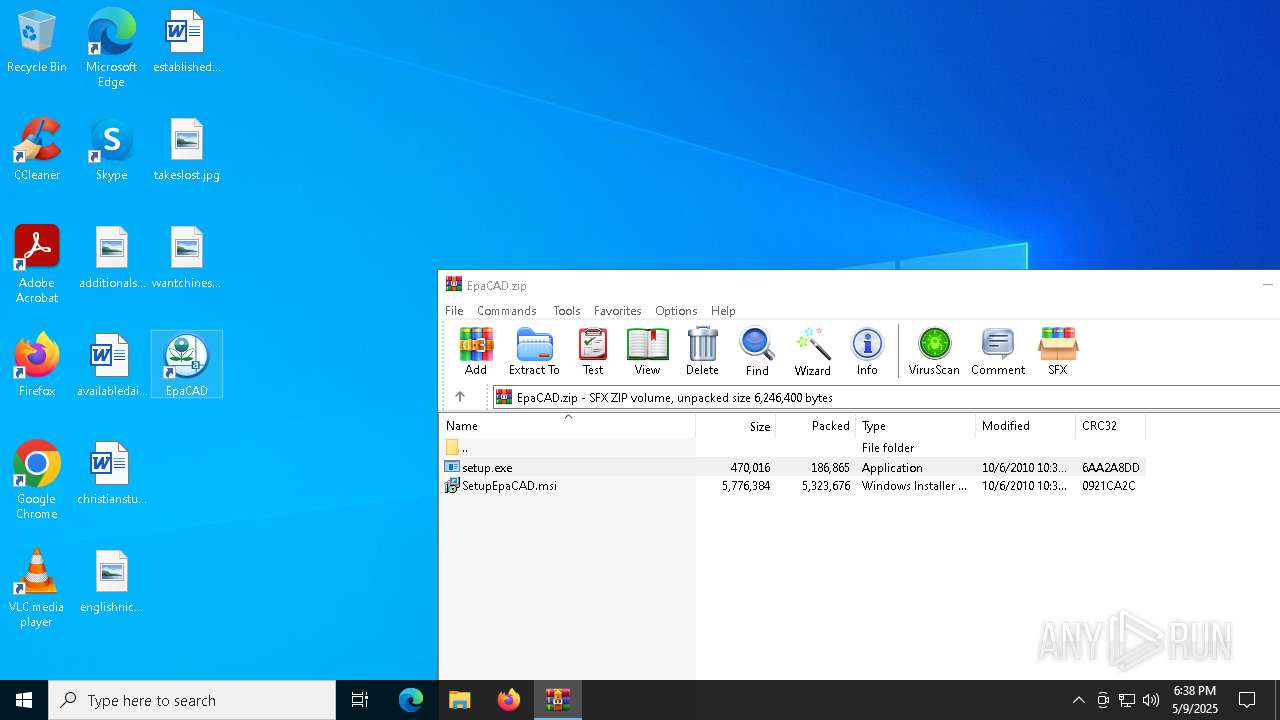
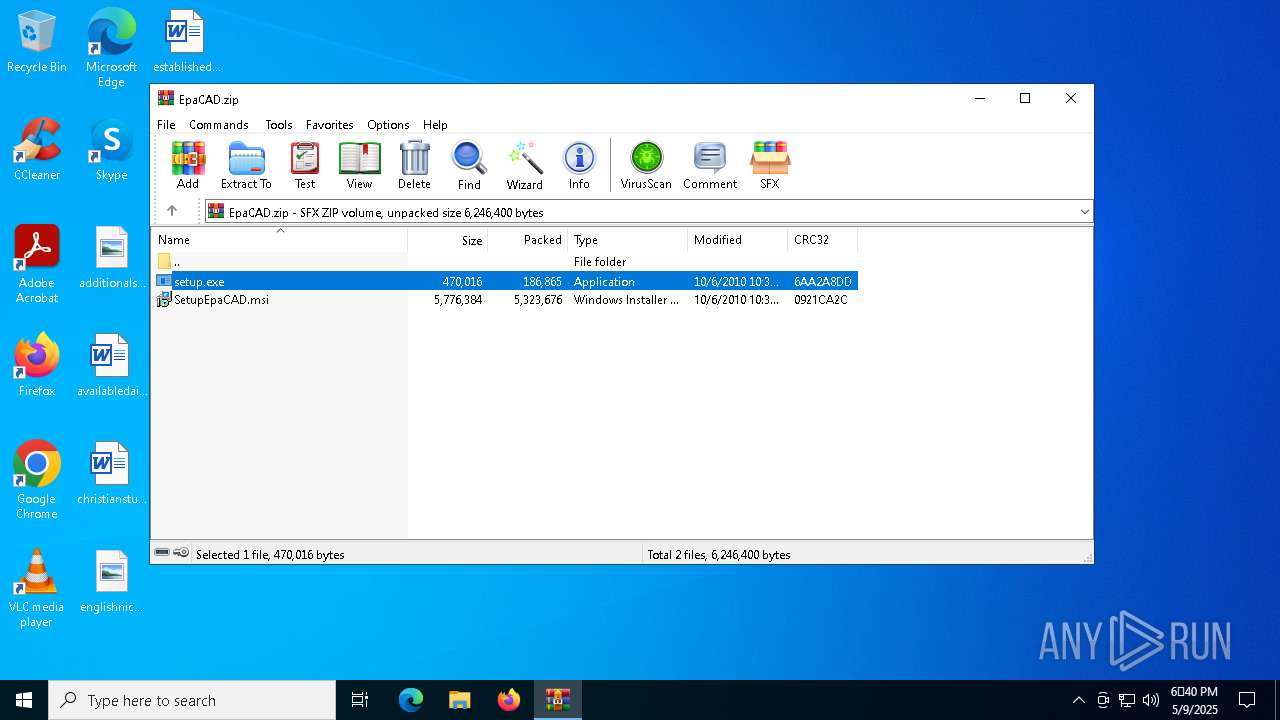
| File name: | EpaCAD.zip |
| Full analysis: | https://app.any.run/tasks/d78c2b48-6913-43f7-b98e-f569950a1ac5 |
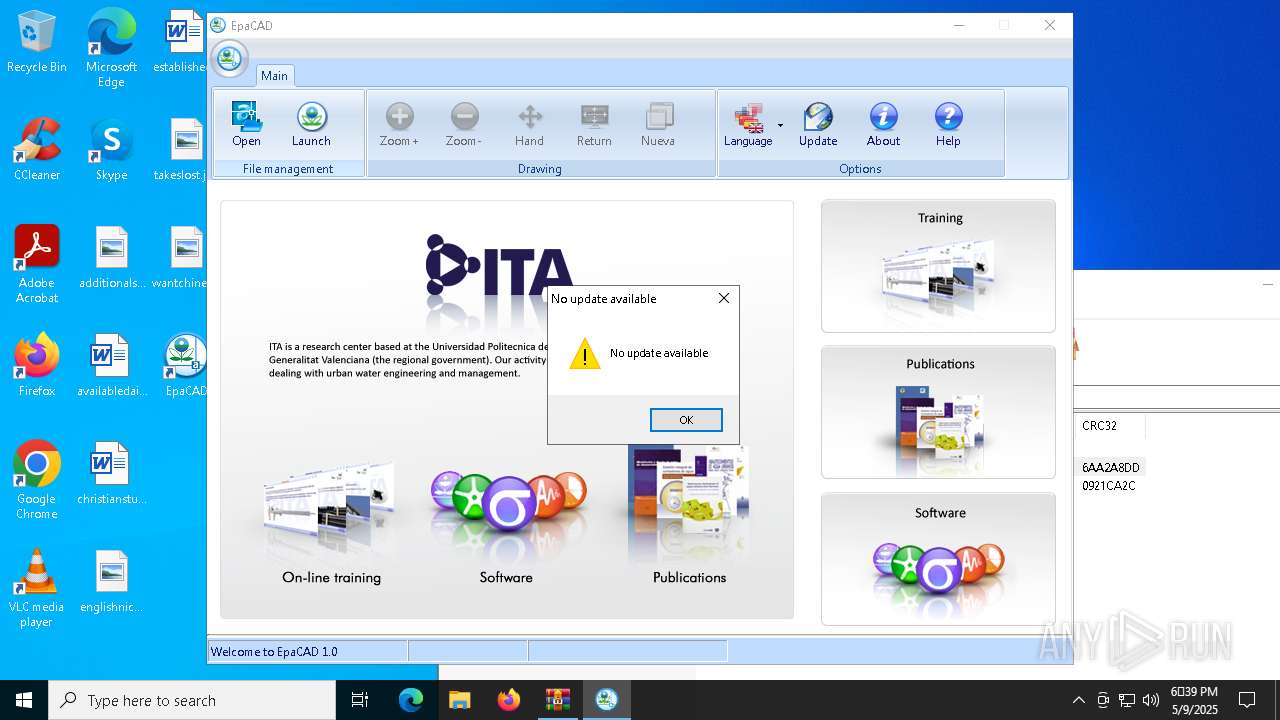
| Verdict: | Malicious activity |
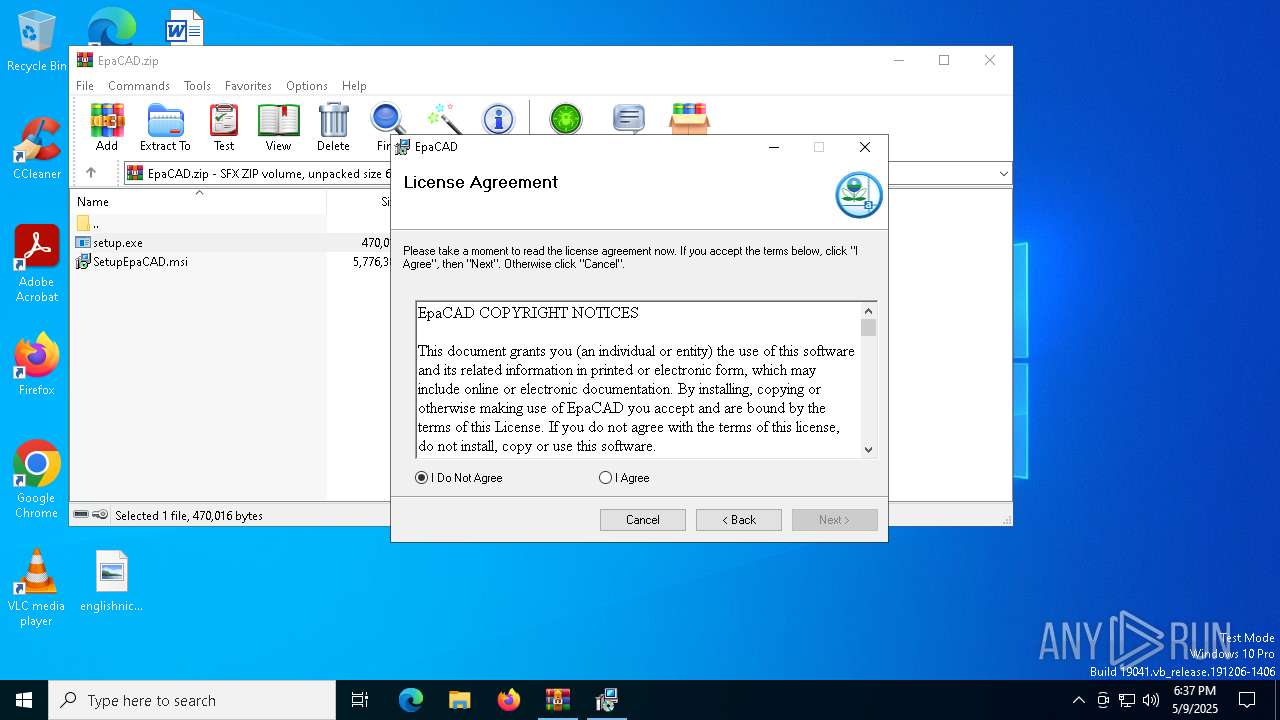
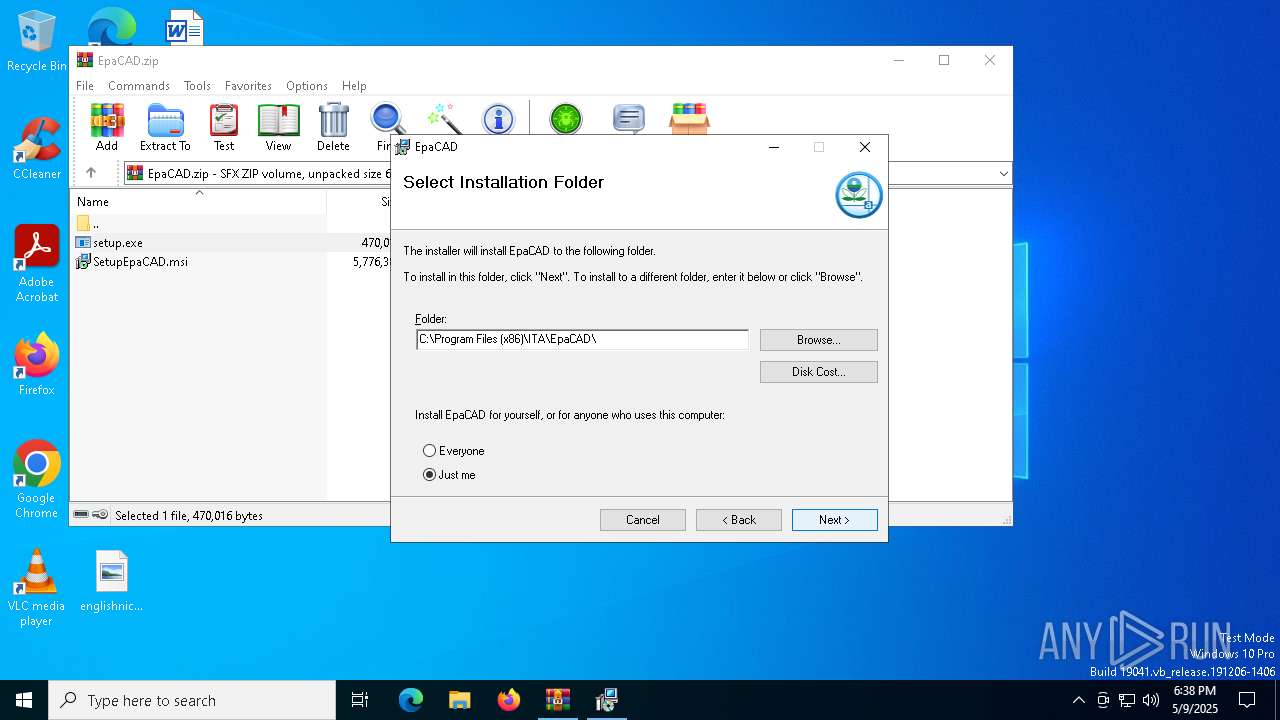
| Analysis date: | May 09, 2025, 18:37:13 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data |
| MD5: | 688B32A0951963FD3F8AED8232E91DDB |
| SHA1: | 455F81AB52EF2D981E141B2871E9CFCB6C3B7E80 |
| SHA256: | 6111ADF2B05953C4A62A9FF0ED967537BE36FE7A3BE9B115FF8EF7D59AF19974 |
| SSDEEP: | 98304:qPdfrebOMvlUB6gybzN+7n/UoZAePU1vwIB5l6PAw2Ji3kaUSjgYQXf8PPyqoULc:tzKXp0oq |
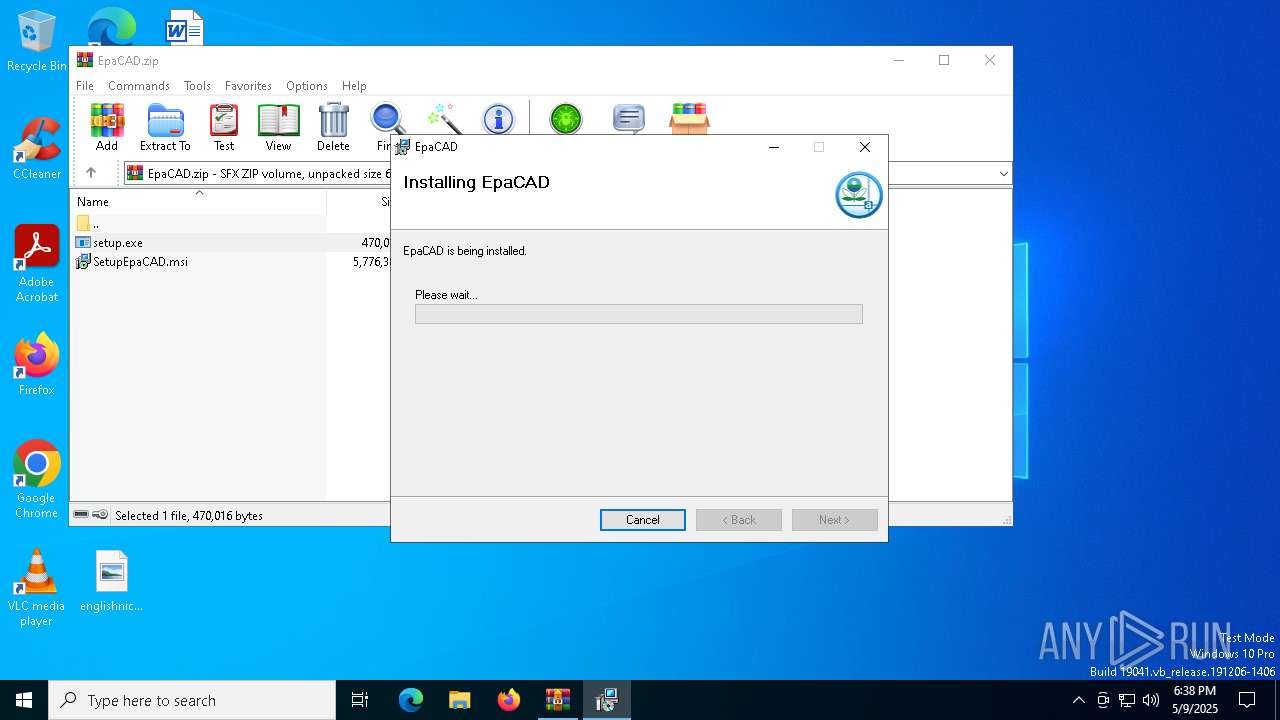
MALICIOUS
Executing a file with an untrusted certificate
- dotNetFx35setup.exe (PID: 1012)
- dotNetFx35setup.exe (PID: 5008)
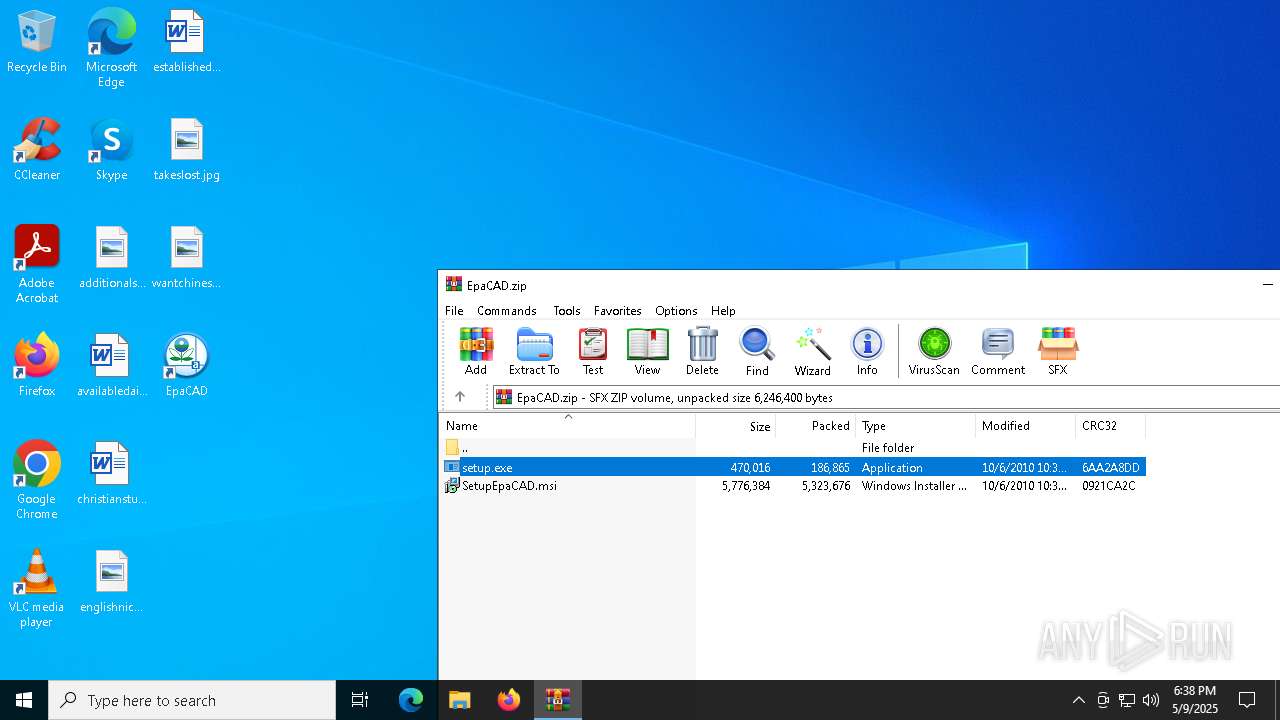
Starts Visual C# compiler
- EpaCAD.exe (PID: 4696)
SUSPICIOUS
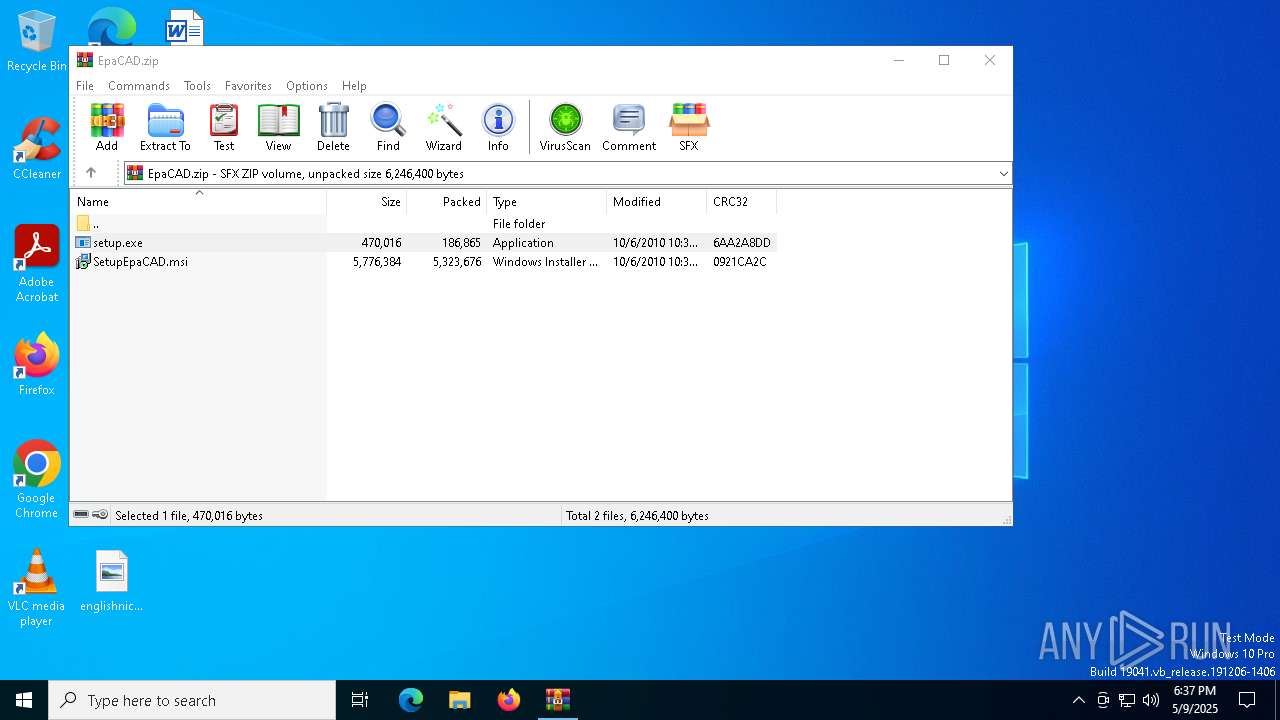
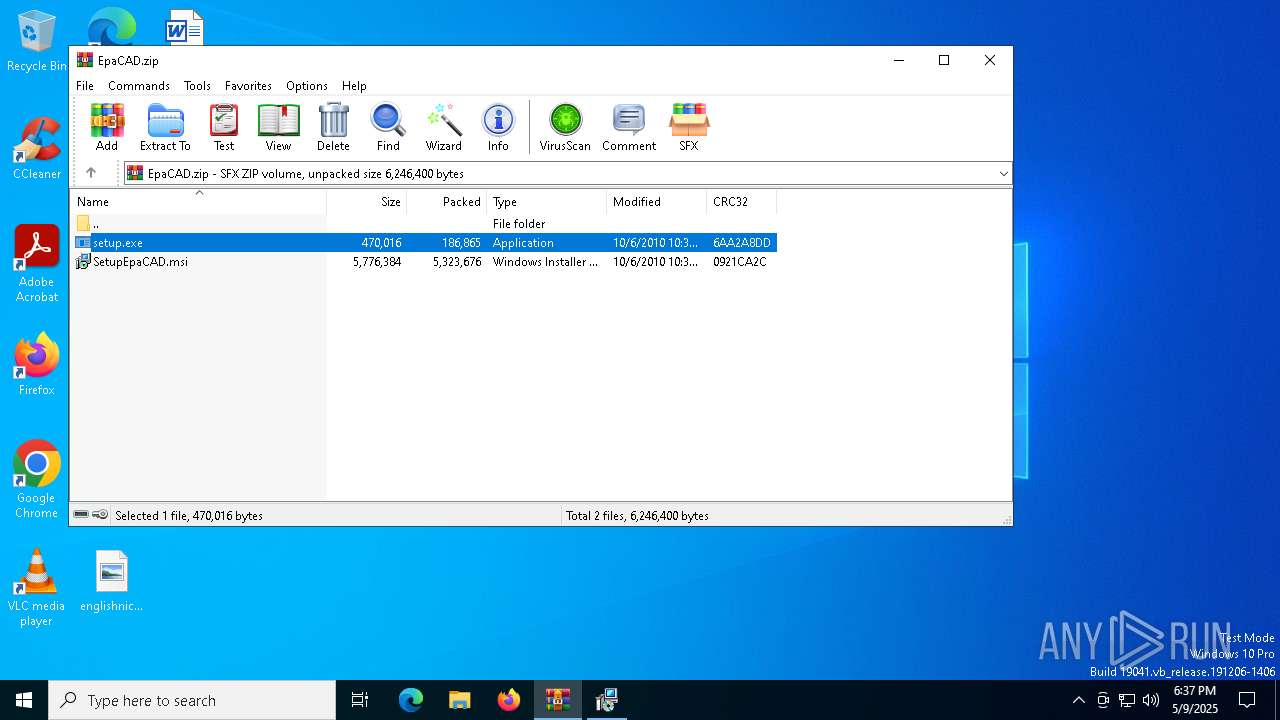
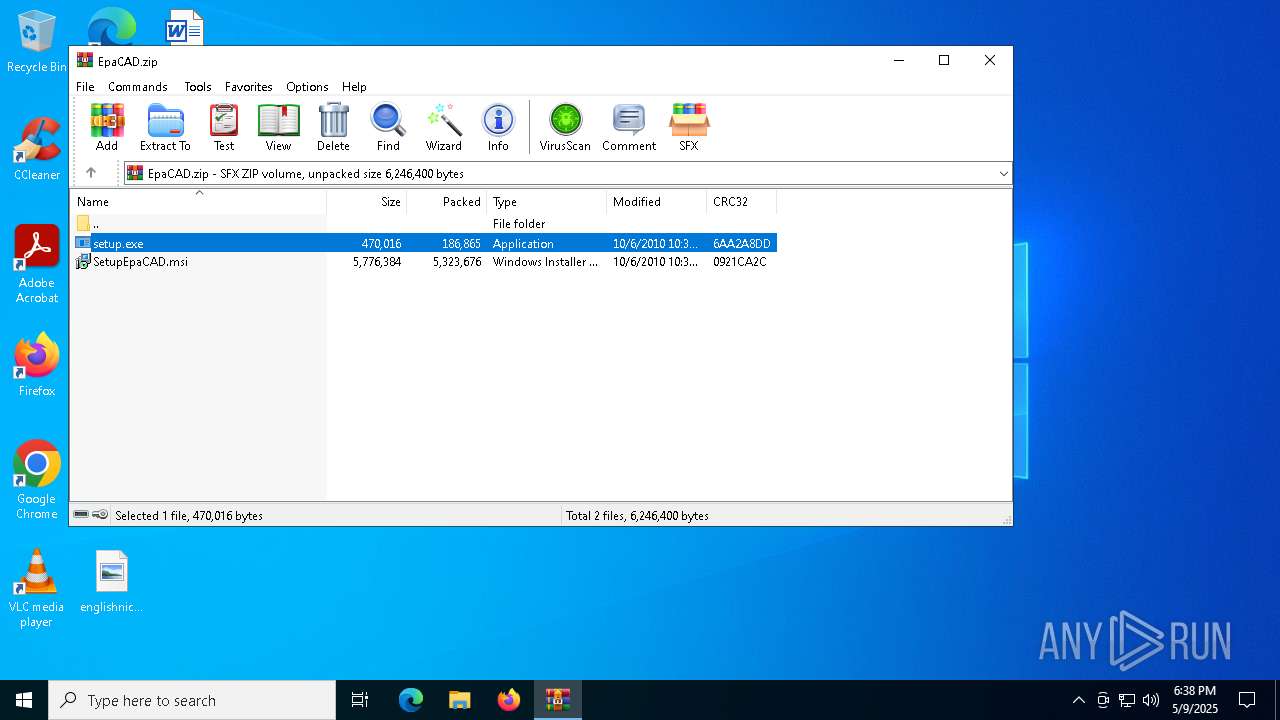
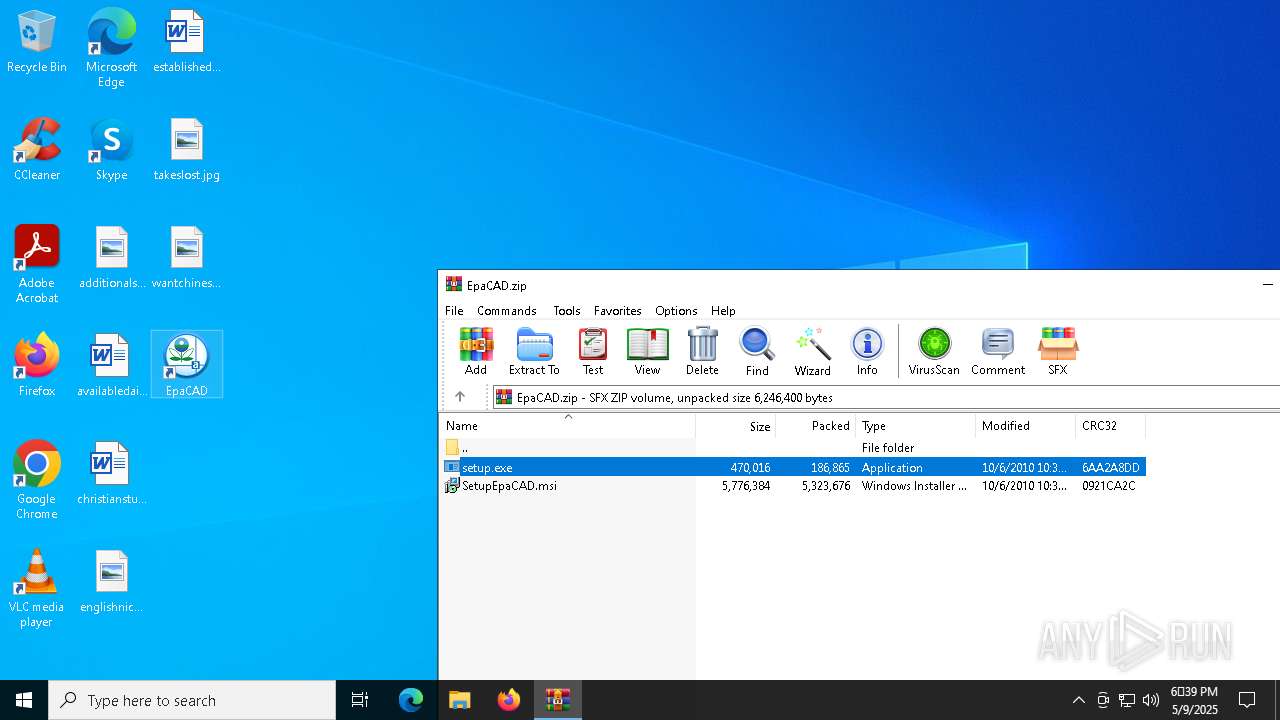
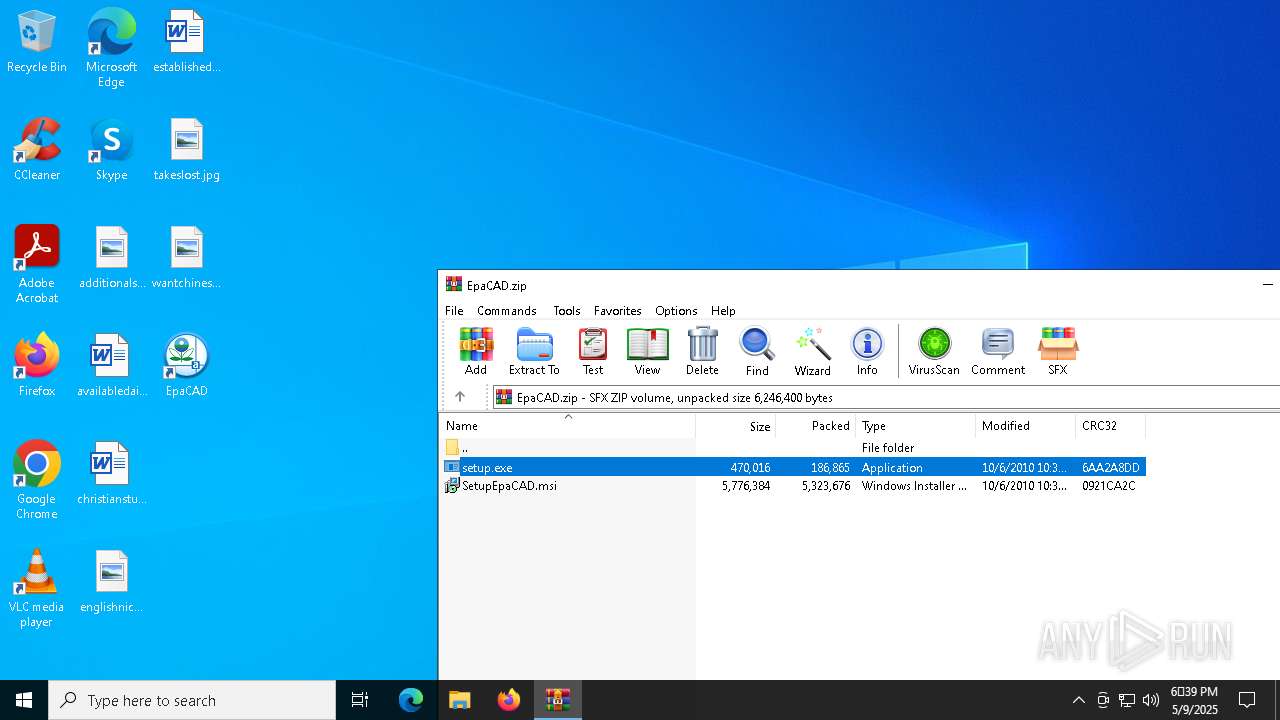
Process drops legitimate windows executable
- WinRAR.exe (PID: 5364)
- setup.exe (PID: 2340)
- msiexec.exe (PID: 1228)
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 5364)
- setup.exe (PID: 2340)
Executable content was dropped or overwritten
- setup.exe (PID: 2340)
- csc.exe (PID: 3304)
Starts a Microsoft application from unusual location
- dotNetFx35setup.exe (PID: 1012)
- dotNetFx35setup.exe (PID: 5008)
Executes as Windows Service
- VSSVC.exe (PID: 5360)
Uses .NET C# to load dll
- EpaCAD.exe (PID: 4696)
INFO
Executable content was dropped or overwritten
- WinRAR.exe (PID: 5364)
- msiexec.exe (PID: 1164)
- msiexec.exe (PID: 1228)
The sample compiled with english language support
- WinRAR.exe (PID: 5364)
- setup.exe (PID: 2340)
- msiexec.exe (PID: 1228)
Reads the computer name
- setup.exe (PID: 2340)
- msiexec.exe (PID: 1300)
- msiexec.exe (PID: 1228)
Checks supported languages
- setup.exe (PID: 2340)
- msiexec.exe (PID: 1228)
- msiexec.exe (PID: 1300)
Create files in a temporary directory
- setup.exe (PID: 2340)
- msiexec.exe (PID: 1300)
Reads the software policy settings
- setup.exe (PID: 2340)
- slui.exe (PID: 720)
Checks proxy server information
- setup.exe (PID: 2340)
Reads the machine GUID from the registry
- setup.exe (PID: 2340)
Creates files or folders in the user directory
- setup.exe (PID: 2340)
Process checks computer location settings
- setup.exe (PID: 2340)
The sample compiled with spanish language support
- msiexec.exe (PID: 1228)
Manages system restore points
- SrTasks.exe (PID: 2692)
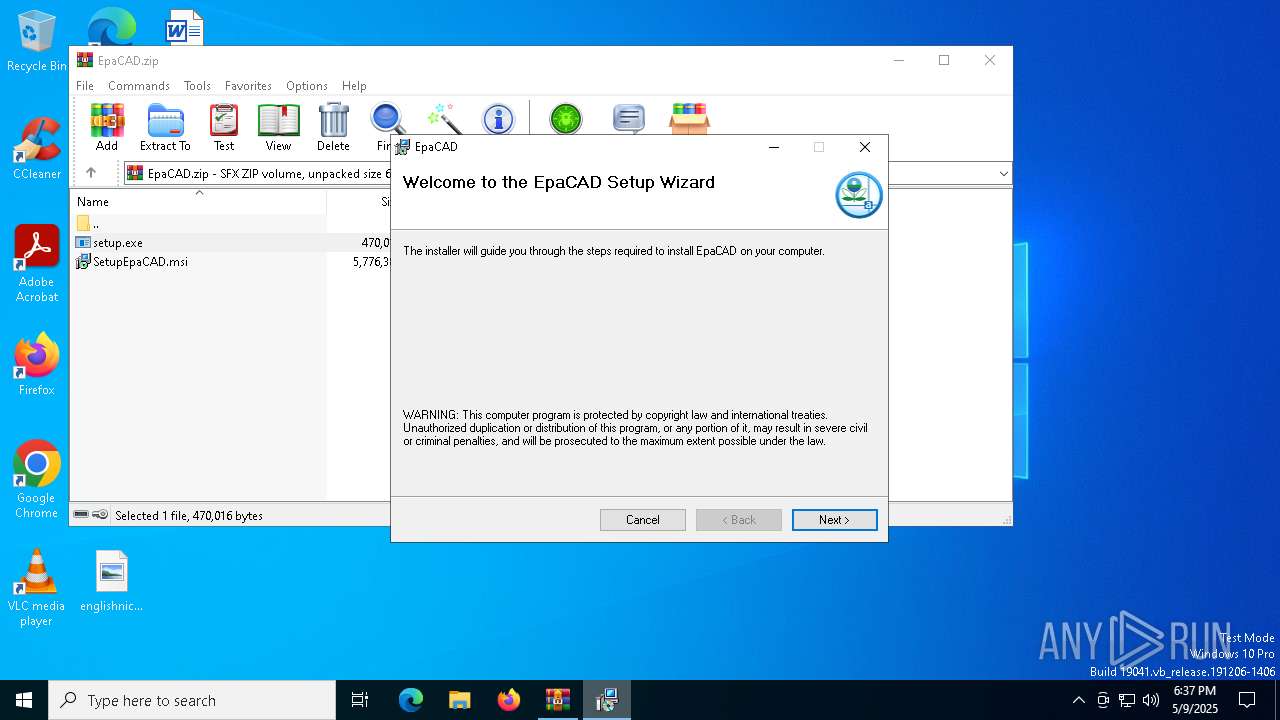
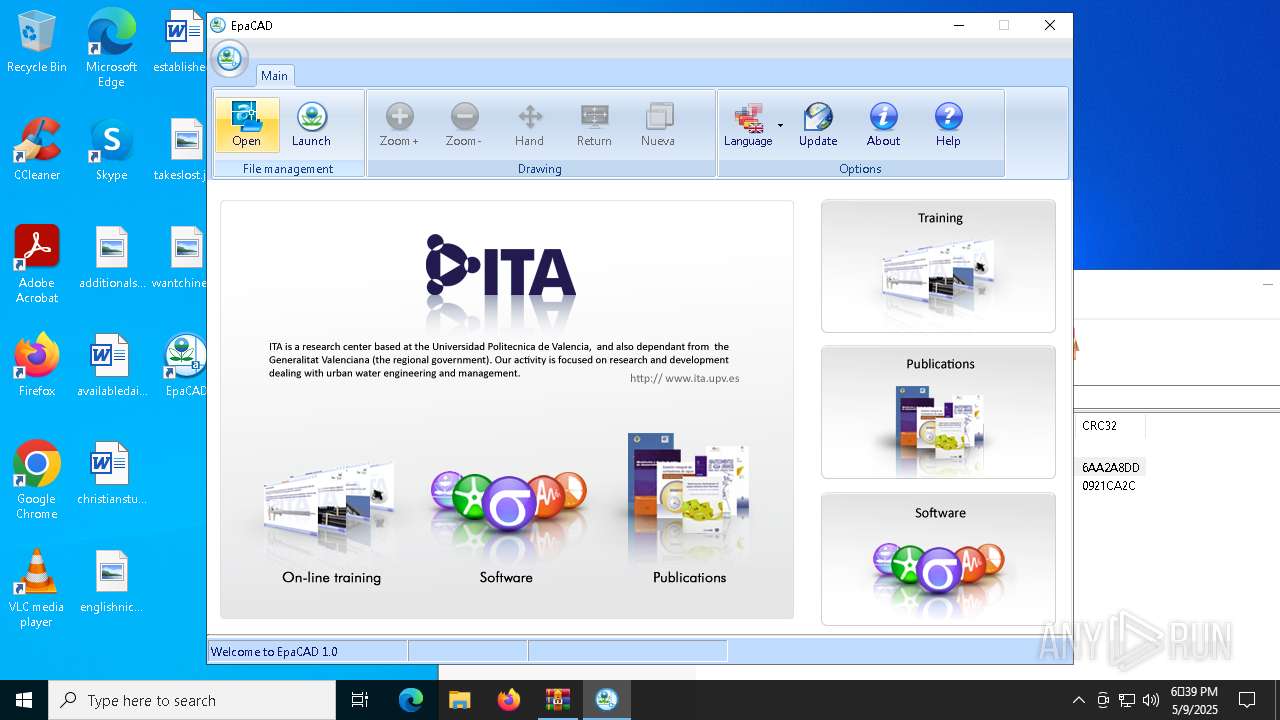
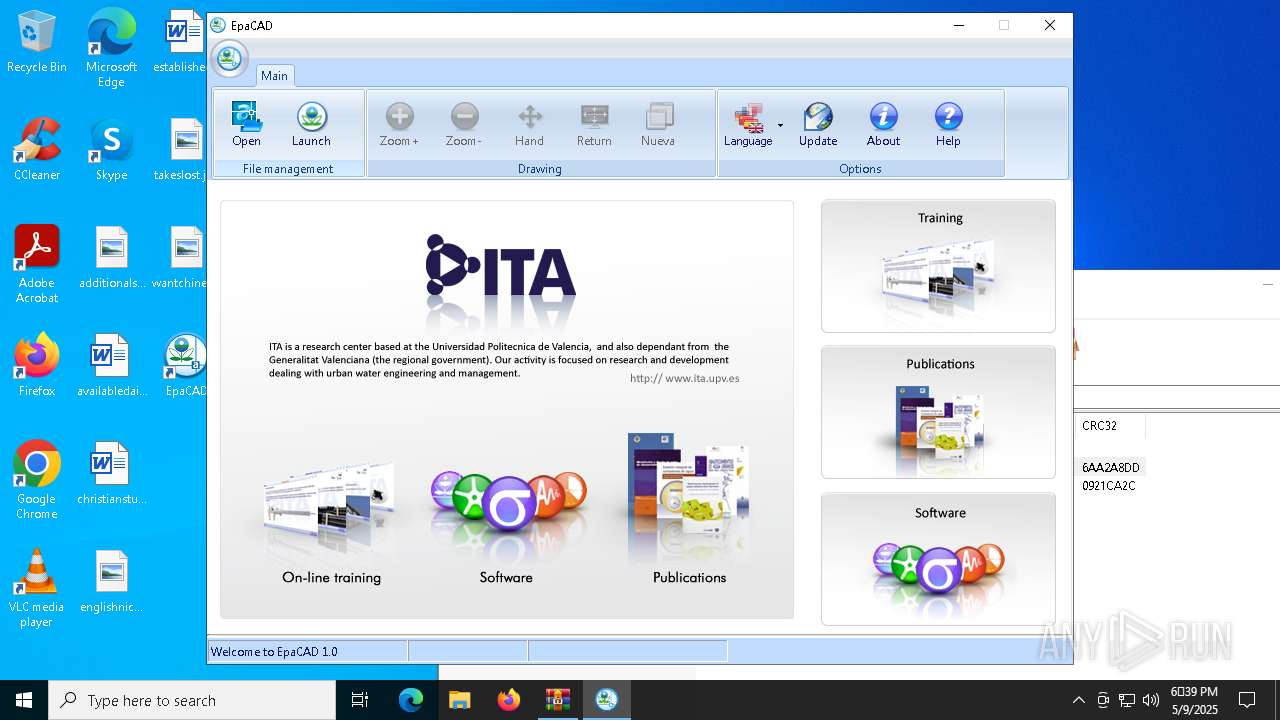
Manual execution by a user
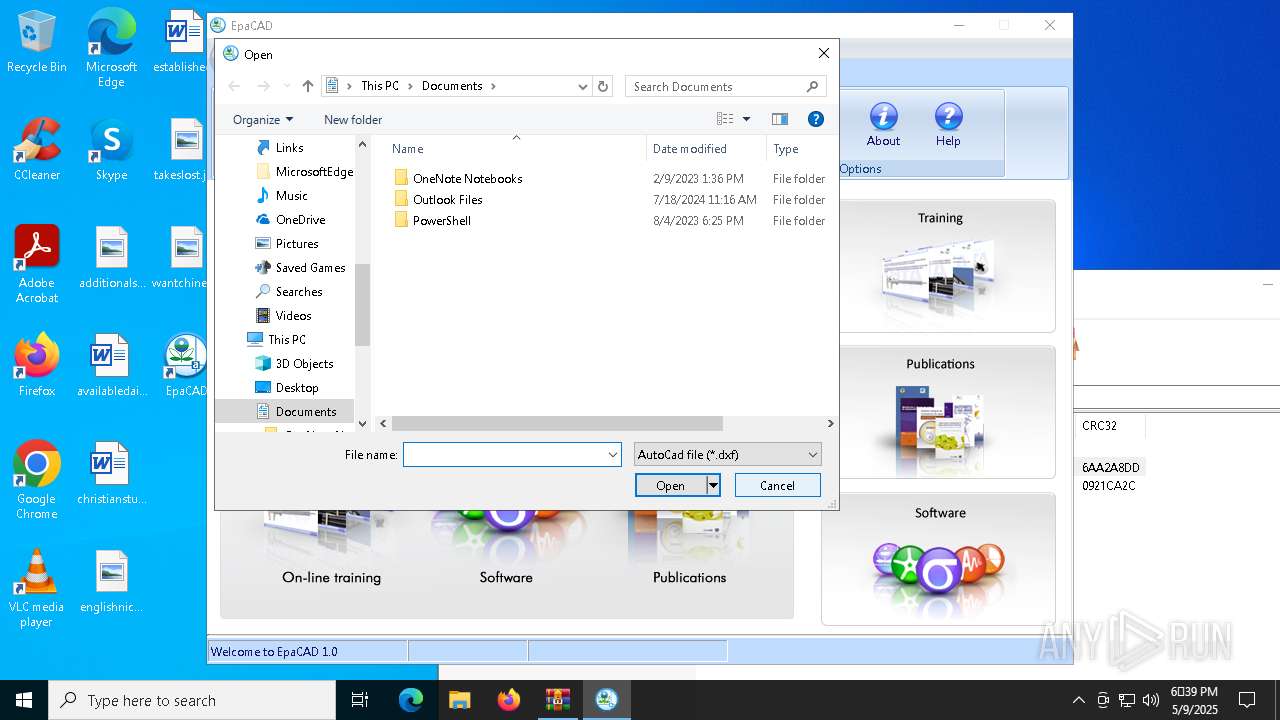
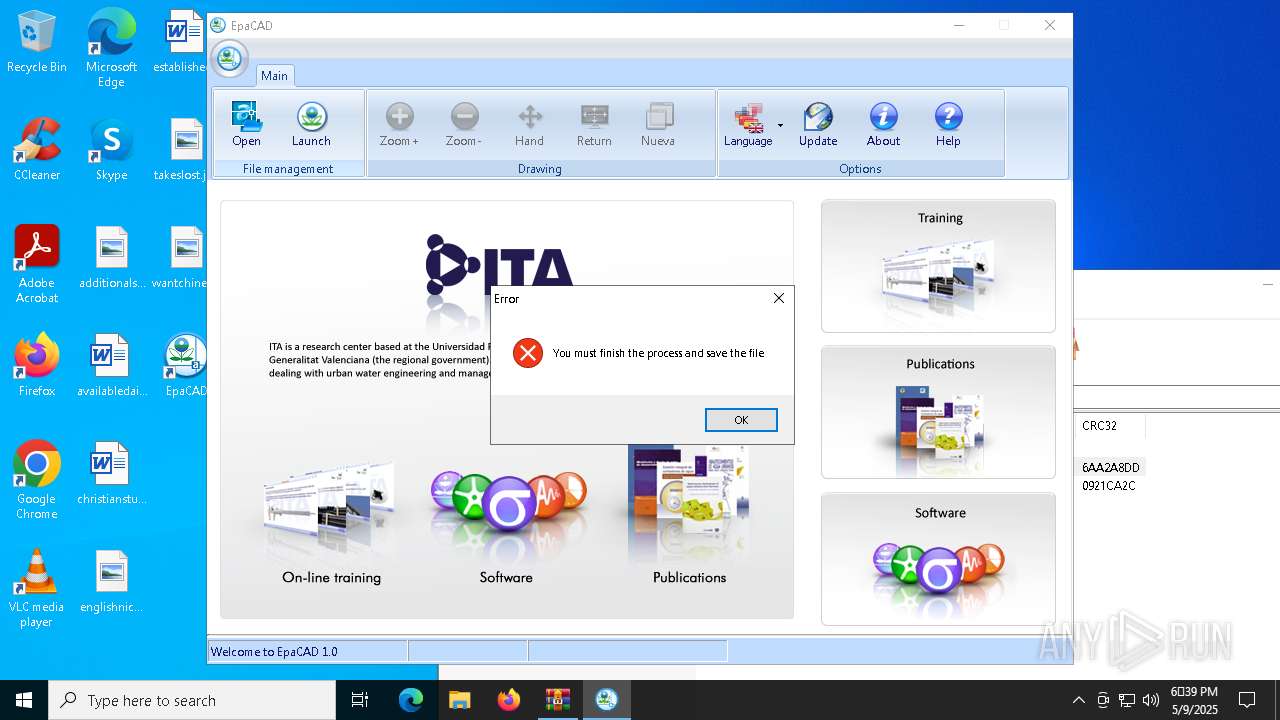
- EpaCAD.exe (PID: 4696)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
155
Monitored processes
19
Malicious processes
1
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 720 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | SppExtComObj.Exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
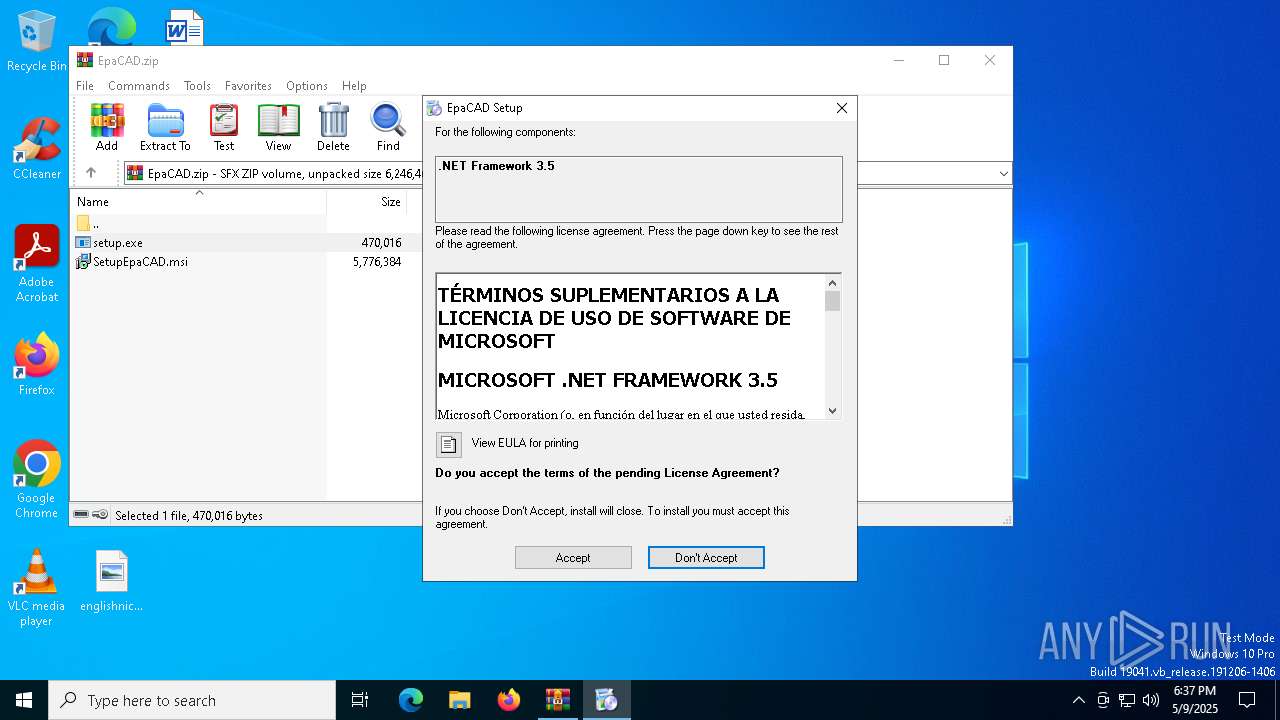
| 1012 | "C:\Users\admin\AppData\Local\Temp\VSDEA91.tmp\DotNetFX35\dotNetFx35setup.exe" /lang:esn /passive /norestart | C:\Users\admin\AppData\Local\Temp\VSDEA91.tmp\DotNetFX35\dotNetFx35setup.exe | — | setup.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft .NET Framework 3.5 Setup Exit code: 3221226540 Version: 3.5.21022.08 Modules
| |||||||||||||||
| 1164 | "C:\Windows\SysWOW64\msiexec.exe" -I "C:\Users\admin\AppData\Local\Temp\Rar$EXa5364.16111\SetupEpaCAD.msi" | C:\Windows\SysWOW64\msiexec.exe | setup.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1228 | C:\WINDOWS\system32\msiexec.exe /V | C:\Windows\System32\msiexec.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Version: 5.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1280 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | SrTasks.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1300 | C:\Windows\syswow64\MsiExec.exe -Embedding CC0394EC9E34266F68B791D428AE1AA8 C | C:\Windows\SysWOW64\msiexec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1600 | C:\Windows\syswow64\MsiExec.exe -Embedding FD8AB4CDFDA565C958A1F29B2060840C E Global\MSI0000 | C:\Windows\SysWOW64\msiexec.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2084 | C:\Windows\syswow64\MsiExec.exe -Embedding 4AF38DAE04611DD4A9C6D3596771BFA0 | C:\Windows\SysWOW64\msiexec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2240 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2288 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | csc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
15 450
Read events
15 041
Write events
387
Delete events
22
Modification events
| (PID) Process: | (5364) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (5364) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (5364) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (5364) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\EpaCAD.zip | |||
| (PID) Process: | (5364) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (5364) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (5364) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (5364) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2340) setup.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2340) setup.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
Executable files
29
Suspicious files
42
Text files
22
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
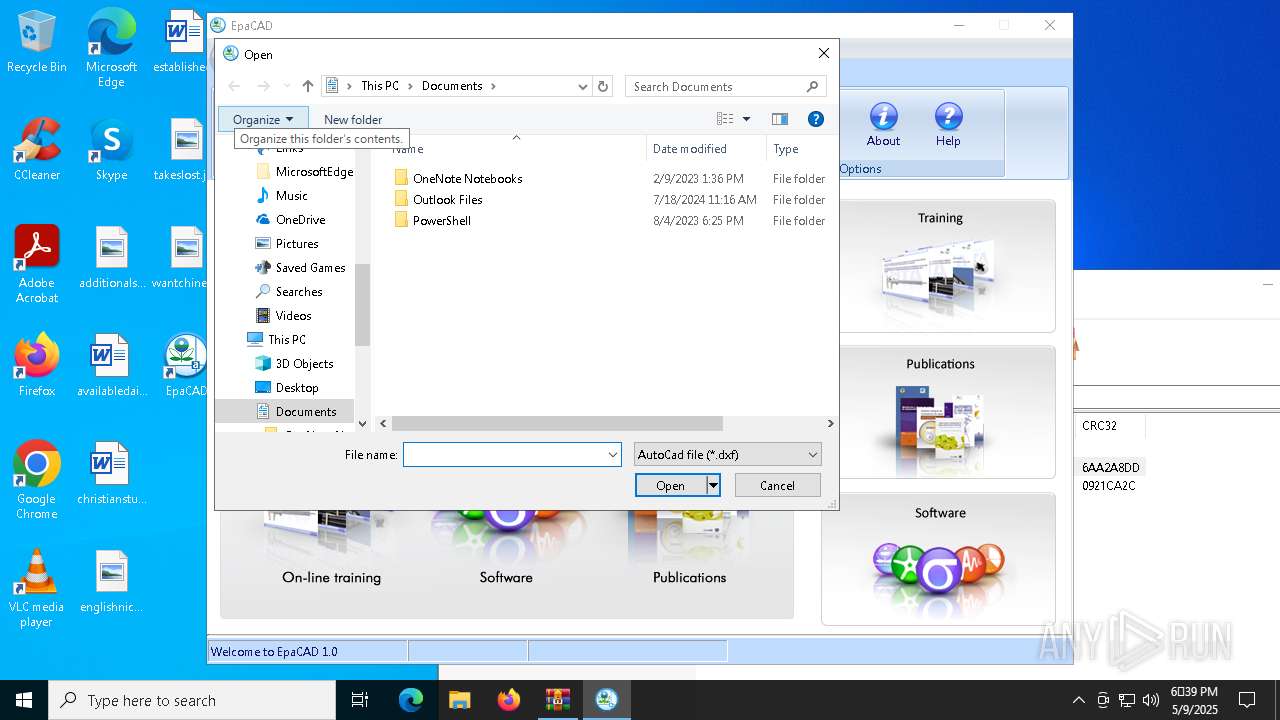
| 5364 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa5364.16111\SetupEpaCAD.msi | — | |
MD5:— | SHA256:— | |||
| 1228 | msiexec.exe | C:\System Volume Information\SPP\metadata-2 | — | |
MD5:— | SHA256:— | |||
| 1228 | msiexec.exe | C:\Windows\Installer\11fcfb.msi | — | |
MD5:— | SHA256:— | |||
| 2340 | setup.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\E2C6CBAF0AF08CF203BA74BF0D0AB6D5_CBDCCBFE4F7A916411C1E69BDD97BB04 | binary | |
MD5:BC904762BCDFB25B9915ED65B40144D9 | SHA256:4BD78B5D4B500141B336A82E83BFAAECE7ED30123C0B1AC67B0FDA9C7DCC2CE7 | |||
| 2340 | setup.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\E2C6CBAF0AF08CF203BA74BF0D0AB6D5_CBDCCBFE4F7A916411C1E69BDD97BB04 | binary | |
MD5:9AB744C8EE27A659C7AA07A68EBDB2E6 | SHA256:322429656D76BF4E611D49BC25B8F2C702E7E8E770F655815F830DD790231D5F | |||
| 2340 | setup.exe | C:\Users\admin\AppData\Local\Temp\VSDEA91.tmp\setup.exe | executable | |
MD5:7754F8078BDA5A4DE05C23A8621A64BE | SHA256:12FA94DFC572724D82B91AC18DE0A027F2930CDA3A423AEEB8F464C0496B7176 | |||
| 5364 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa5364.16111\setup.exe | executable | |
MD5:7754F8078BDA5A4DE05C23A8621A64BE | SHA256:12FA94DFC572724D82B91AC18DE0A027F2930CDA3A423AEEB8F464C0496B7176 | |||
| 1300 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\CFG1700.tmp | xml | |
MD5:17AF548F88A3199AA8A63A72201F470F | SHA256:A558DBE555749CD3BDD62060FDBBA72720C4F4A186D5870B977ED2ACF9721D9E | |||
| 1164 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\MSI1683.tmp | executable | |
MD5:D5CBD20B1B0D410590D9EBFBC86A7362 | SHA256:A128ABDC6A6DB3EF8CBB523462D43FF6FD68015F83242D5FACB4AA78F1661769 | |||
| 2340 | setup.exe | C:\Users\admin\AppData\Local\Temp\VSDEA91.tmp\install.log | text | |
MD5:ADBFDC97C891E92A877C9F29231B3123 | SHA256:59455A22526A28B875F89FDAF0CAE1FD1EDCB24E988774570245D95E677E46E1 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
38
DNS requests
19
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.53.40.178:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
2340 | setup.exe | GET | 302 | 23.35.238.131:80 | http://go.microsoft.com/fwlink/?LinkId=97964 | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 23.67.160.244:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
2340 | setup.exe | GET | 200 | 23.67.160.244:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEApDqVCbATUviZV57HIIulA%3D | unknown | — | — | whitelisted |
2340 | setup.exe | GET | 200 | 23.53.40.178:80 | http://crl.microsoft.com/pki/crl/products/CSPCA.crl | unknown | — | — | whitelisted |
5116 | SIHClient.exe | GET | 200 | 23.52.120.96:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
5116 | SIHClient.exe | GET | 200 | 23.52.120.96:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
4696 | EpaCAD.exe | GET | 301 | 35.214.192.20:80 | http://www.epacad.com/program/info-en.php | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 23.53.40.178:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
3216 | svchost.exe | 172.211.123.249:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
6544 | svchost.exe | 20.190.159.73:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6544 | svchost.exe | 23.67.160.244:80 | ocsp.digicert.com | AKAMAI-AS | JP | whitelisted |
2104 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2340 | setup.exe | 23.35.238.131:80 | go.microsoft.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
download.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |