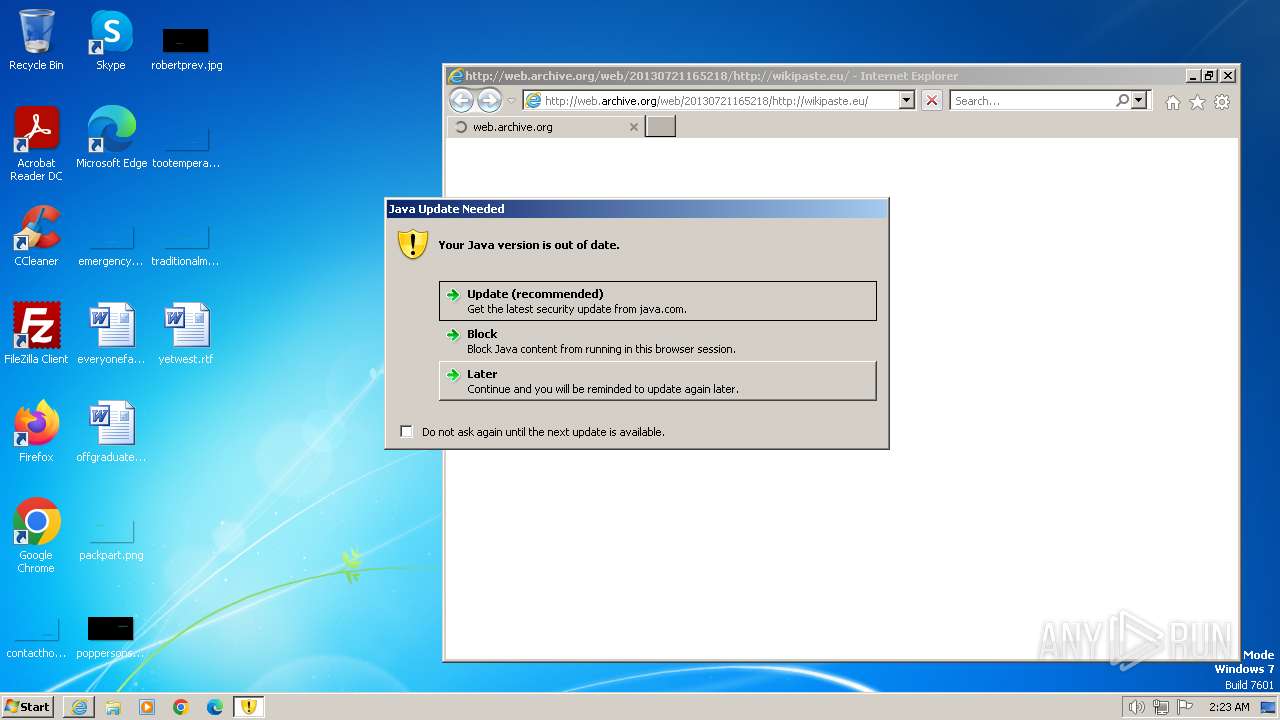
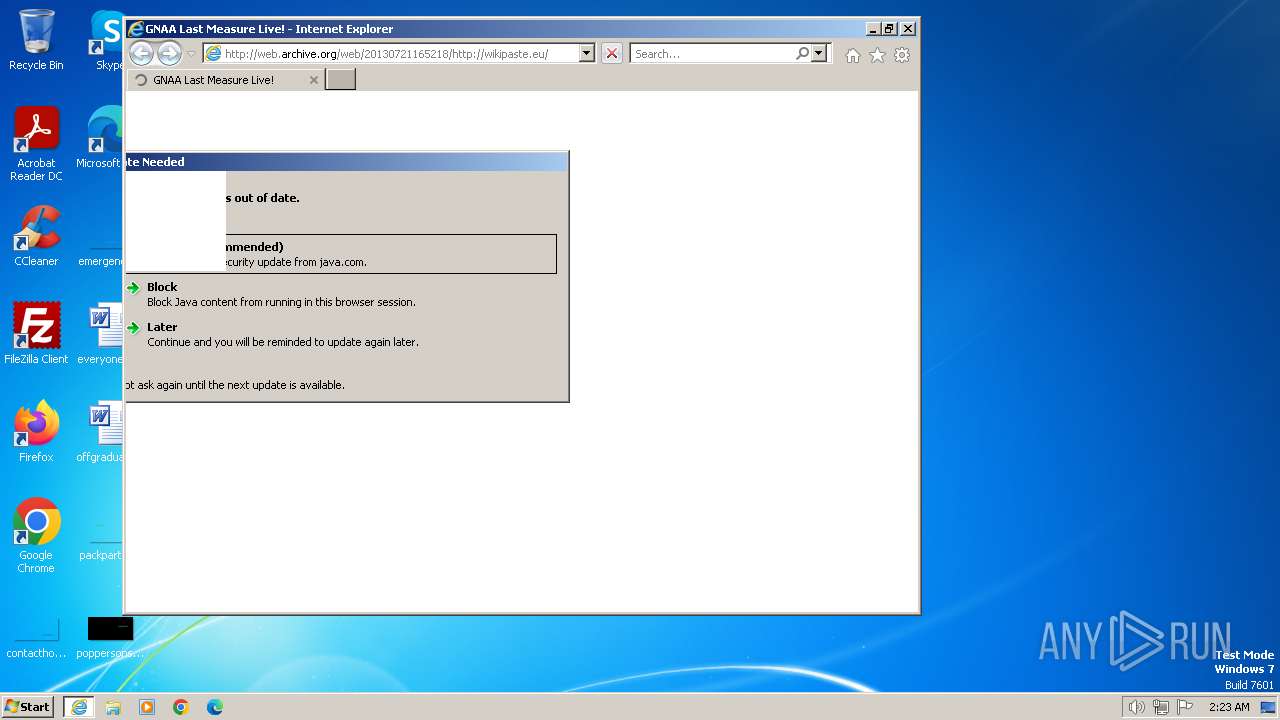
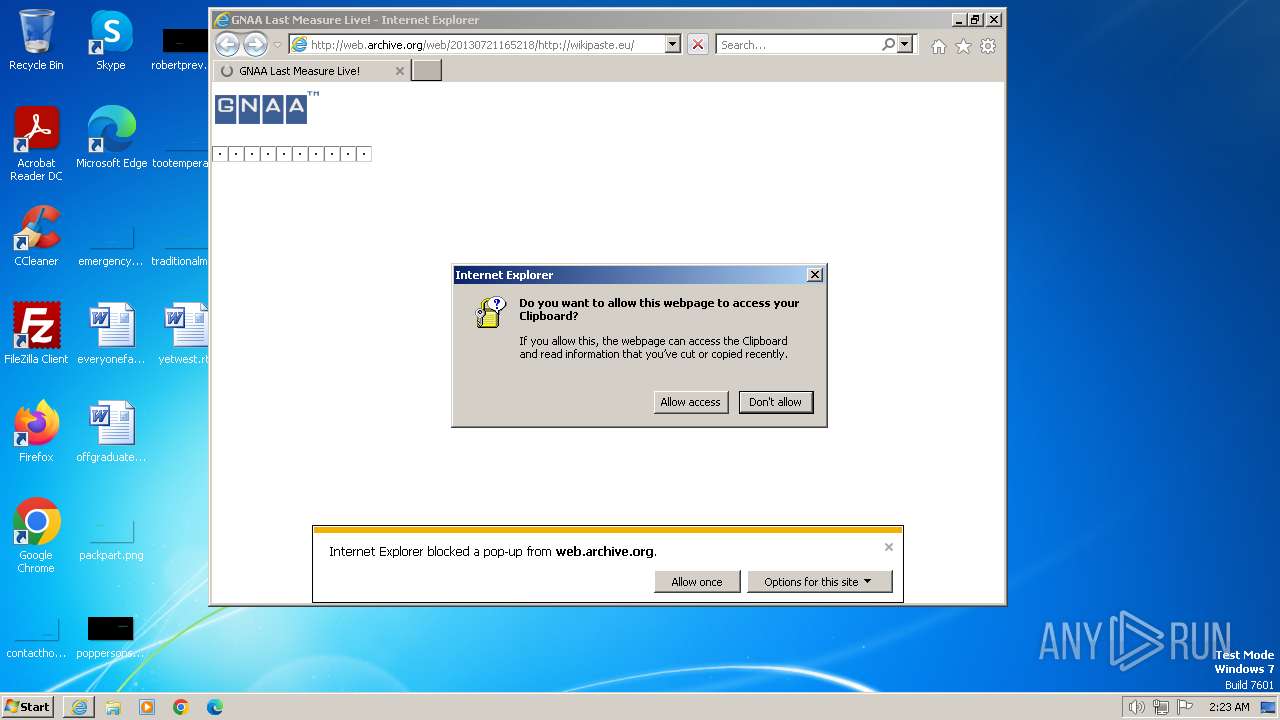
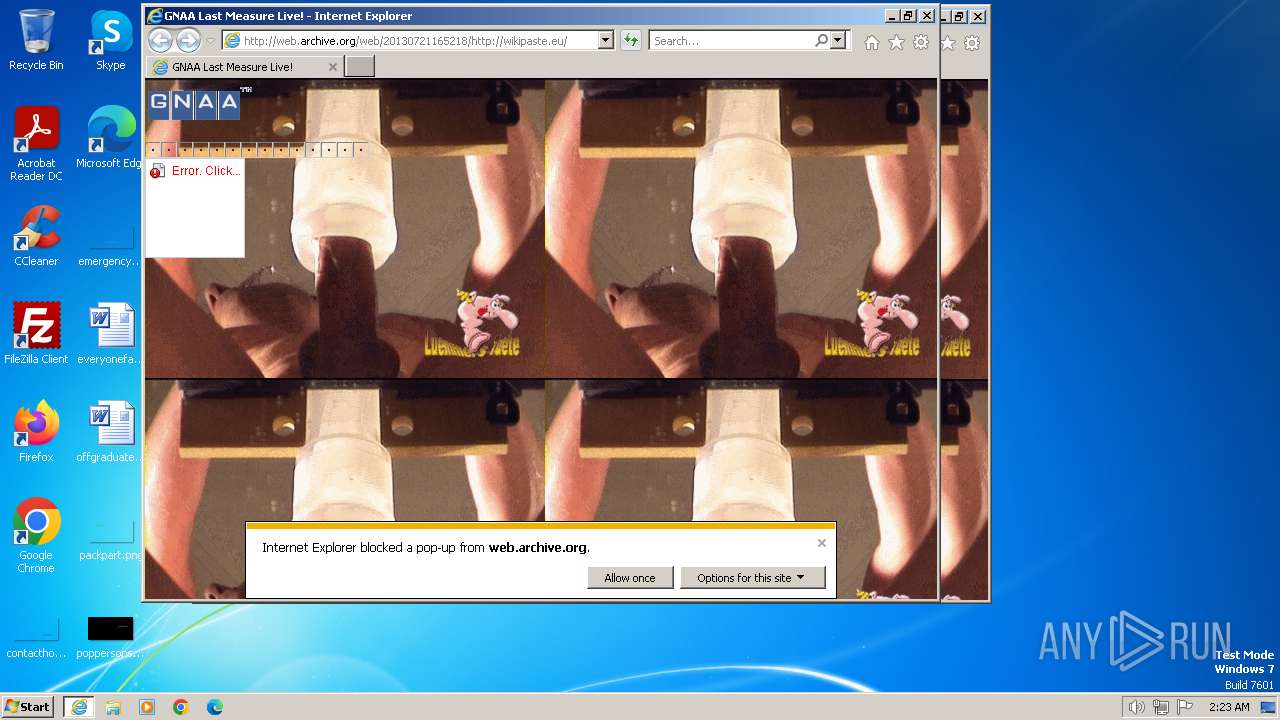
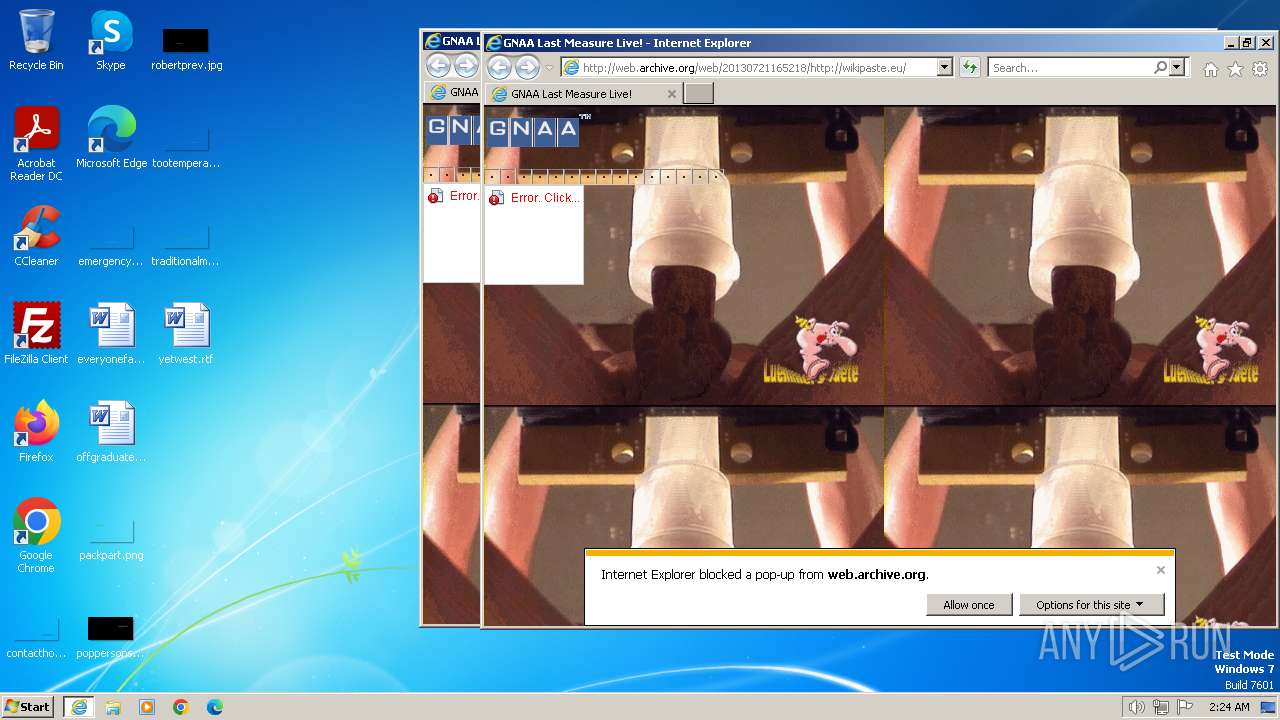
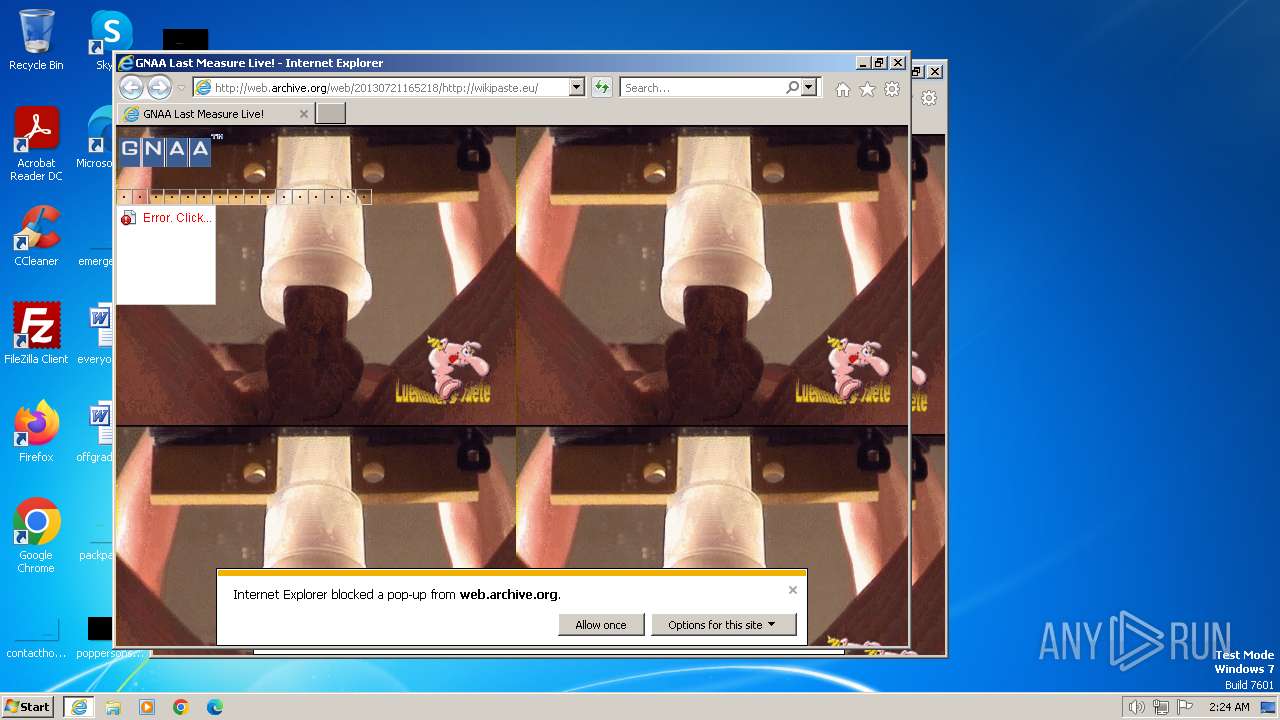
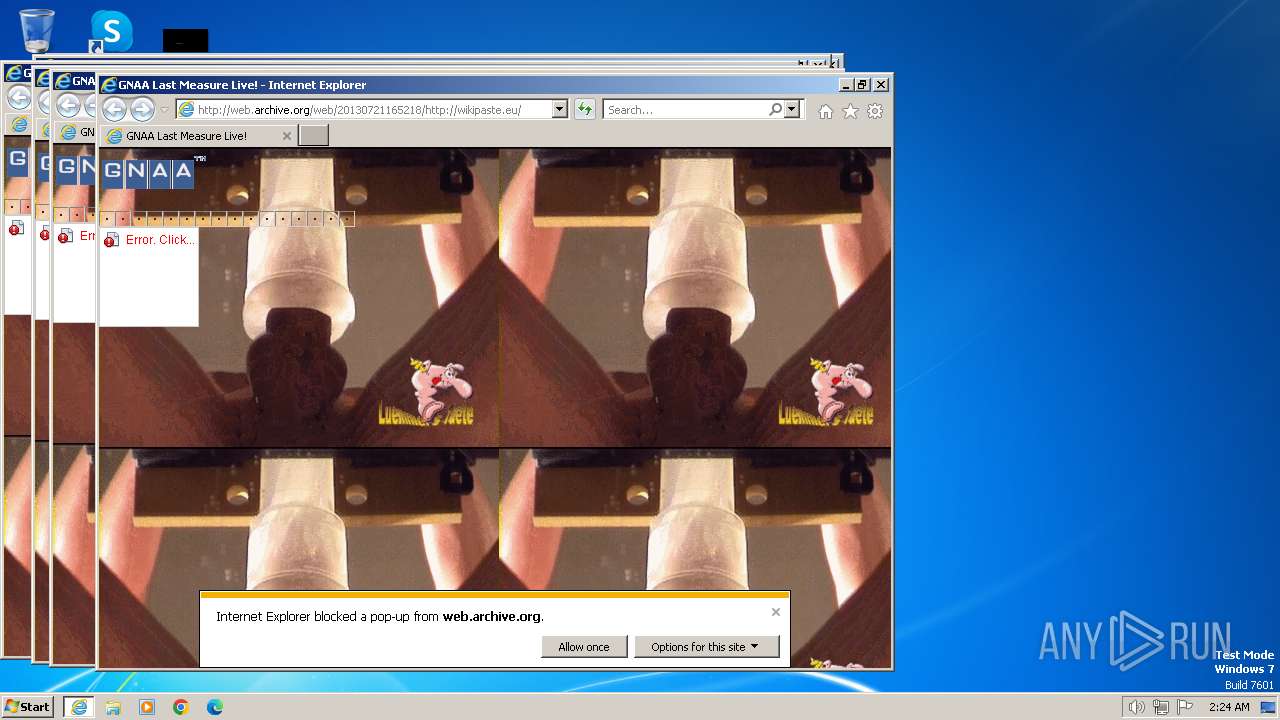
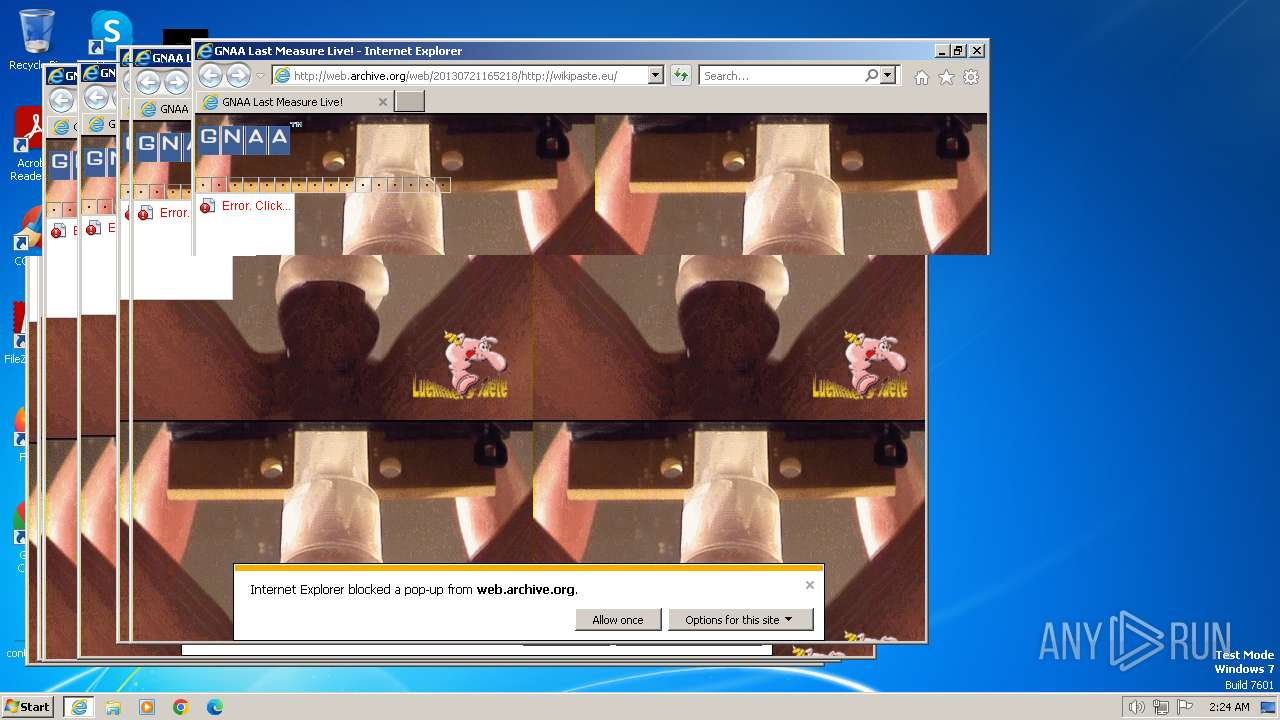
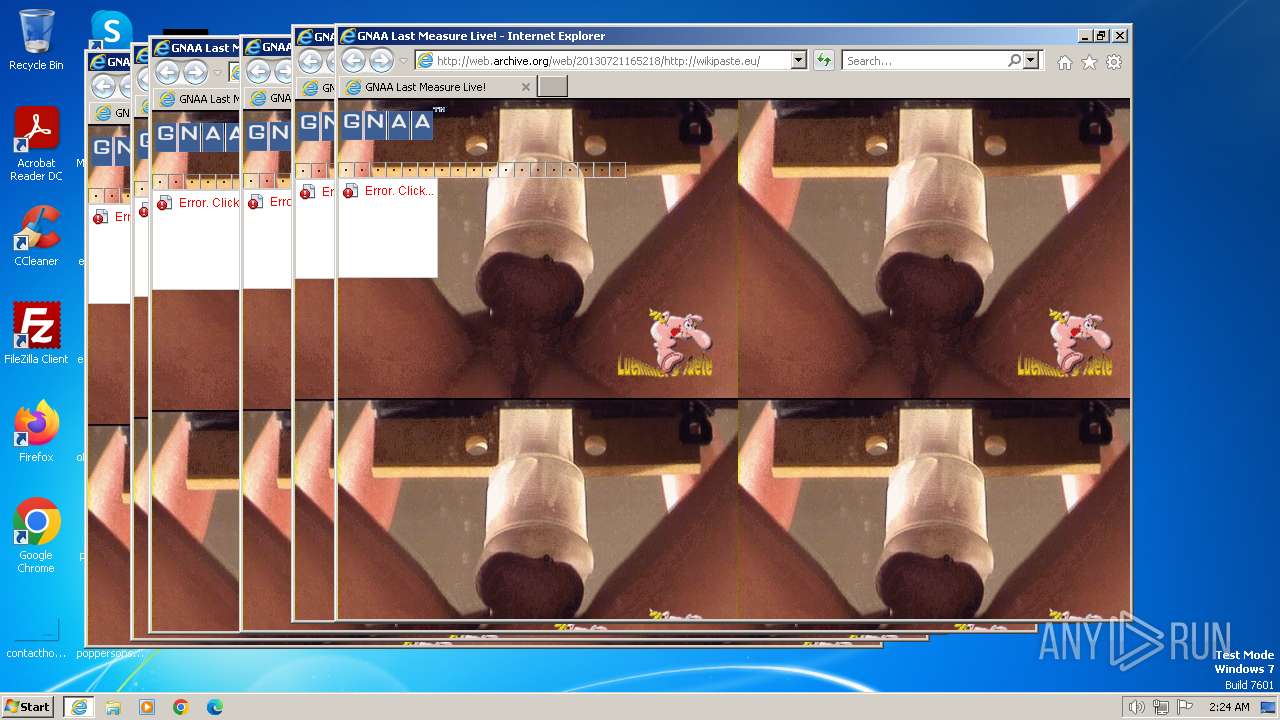
| URL: | web.archive.org/web/20130721165218/wikipaste.eu |
| Full analysis: | https://app.any.run/tasks/b01c24f5-d580-4e0b-9acd-6c48826f6860 |
| Verdict: | Malicious activity |
| Analysis date: | February 05, 2024, 02:23:04 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 48C1FEDE9EC11EF5B2398371069FA935 |
| SHA1: | FA6BE99616CF025E954C37819E1C2147DDDE1DF9 |
| SHA256: | 60FDF180D18DE6B08CA8A118AA5EC38FDB2286C5FC6AB1439D31A8E813760EA3 |
| SSDEEP: | 3:fEhXJeuSwMOuQ:f+X8uD |
MALICIOUS
No malicious indicators.SUSPICIOUS
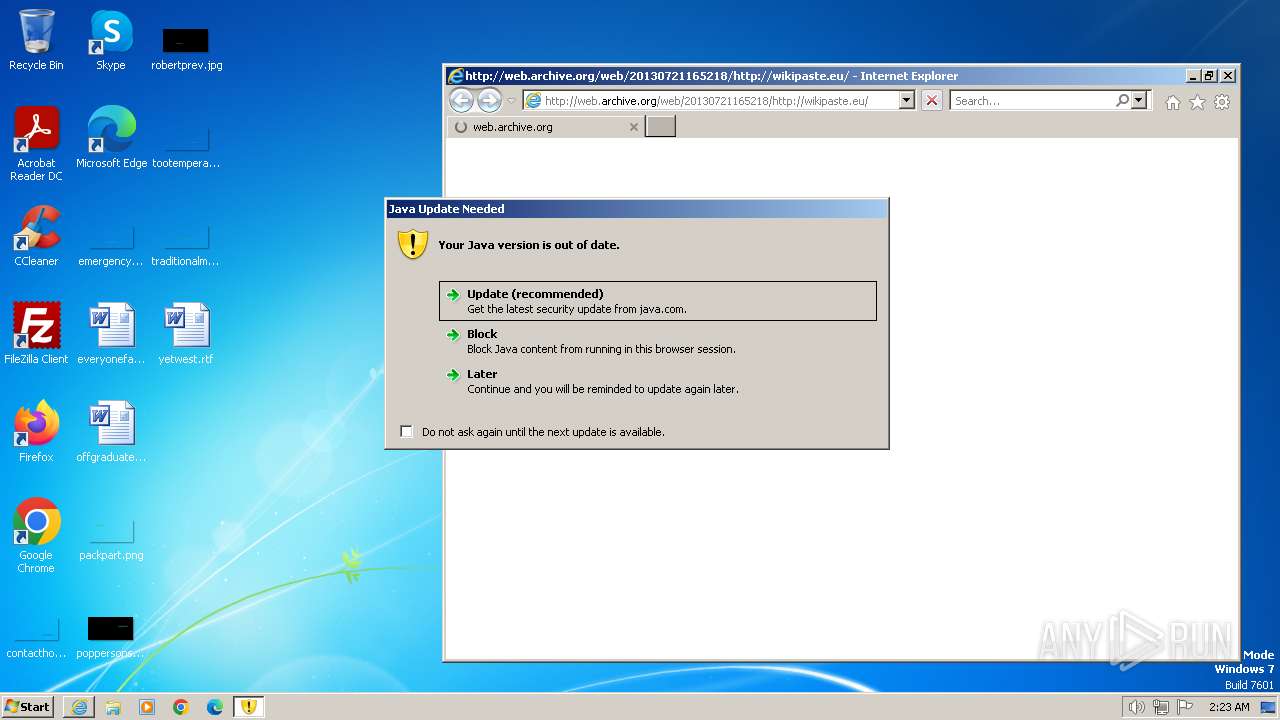
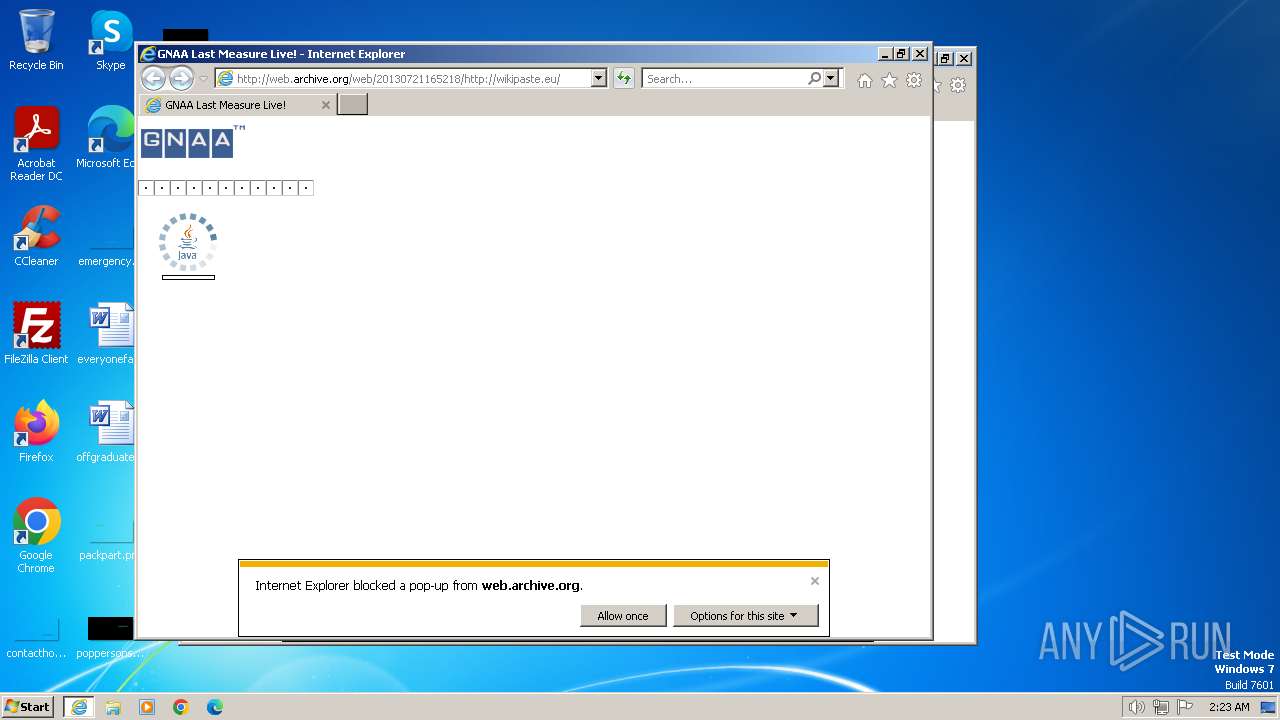
Checks for Java to be installed
- javaw.exe (PID: 3576)
- jp2launcher.exe (PID: 3600)
- javaw.exe (PID: 3820)
- javaw.exe (PID: 4032)
- jp2launcher.exe (PID: 3368)
Reads the Internet Settings
- jp2launcher.exe (PID: 3368)
INFO
Checks supported languages
- javaw.exe (PID: 3576)
- jp2launcher.exe (PID: 3600)
- javaw.exe (PID: 3820)
- javaw.exe (PID: 4032)
- wmpnscfg.exe (PID: 2964)
- jp2launcher.exe (PID: 3368)
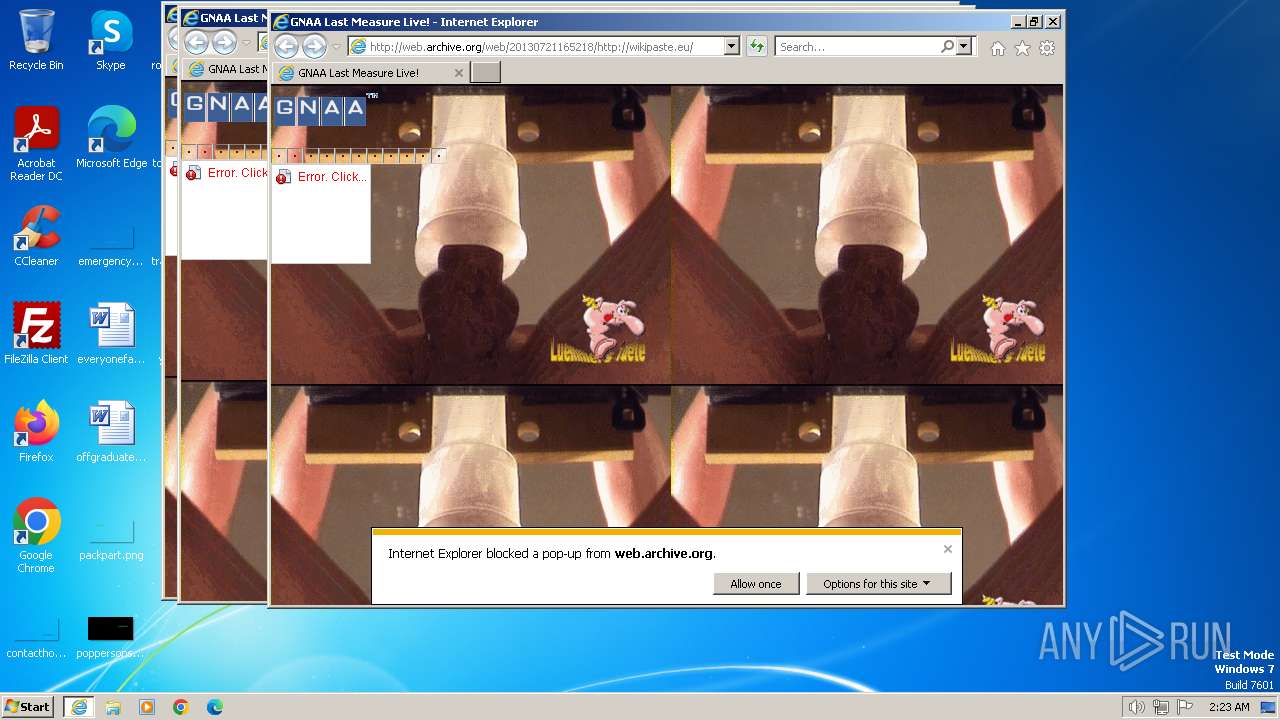
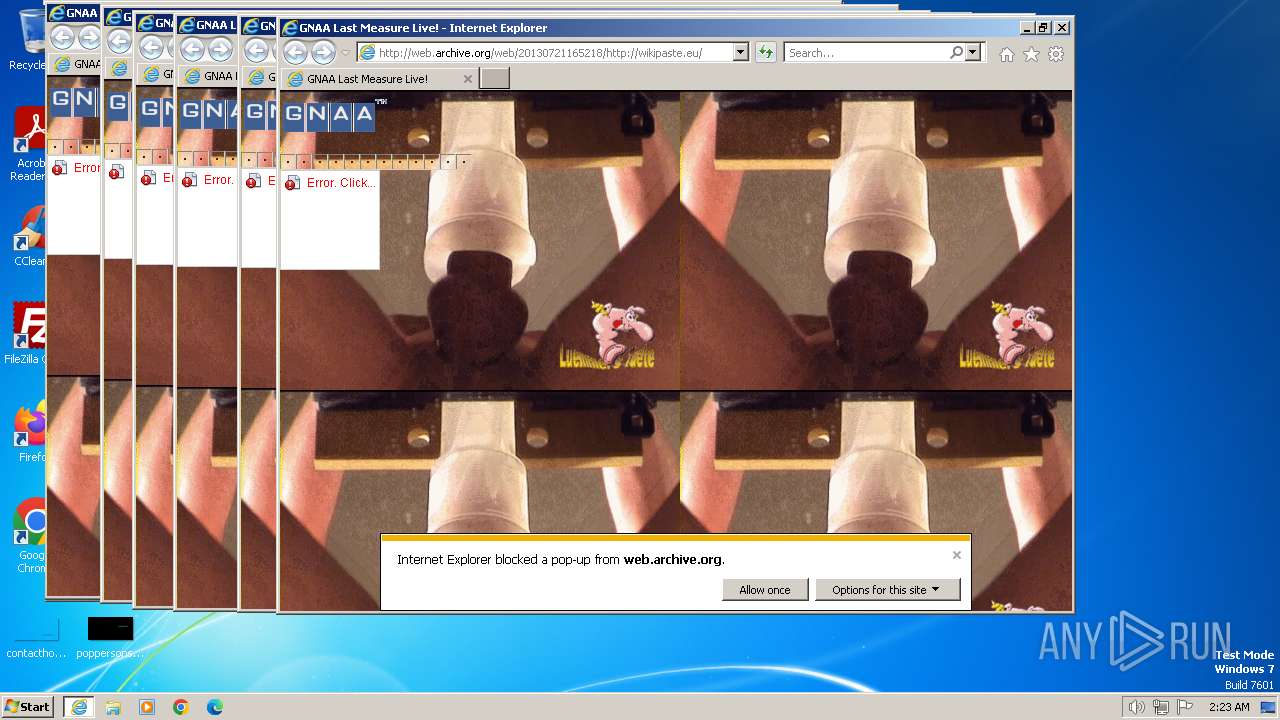
Application launched itself
- iexplore.exe (PID: 752)
Reads the computer name
- javaw.exe (PID: 3576)
- javaw.exe (PID: 3820)
- javaw.exe (PID: 4032)
- wmpnscfg.exe (PID: 2964)
- jp2launcher.exe (PID: 3368)
Create files in a temporary directory
- javaw.exe (PID: 3820)
- javaw.exe (PID: 4032)
- javaw.exe (PID: 3576)
- jp2launcher.exe (PID: 3368)
Creates files in the program directory
- javaw.exe (PID: 3576)
Checks proxy server information
- jp2launcher.exe (PID: 3368)
Manual execution by a user
- wmpnscfg.exe (PID: 2964)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
48
Monitored processes
11
Malicious processes
3
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 548 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:752 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 752 | "C:\Program Files\Internet Explorer\iexplore.exe" "web.archive.org/web/20130721165218/wikipaste.eu" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2964 | "C:\Program Files\Windows Media Player\wmpnscfg.exe" | C:\Program Files\Windows Media Player\wmpnscfg.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Media Player Network Sharing Service Configuration Application Exit code: 0 Version: 12.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3268 | "C:\Program Files\Java\jre1.8.0_271\bin\jp2launcher.exe" -secure -plugin -jre "C:\Program Files\Java\jre1.8.0_271" -vma LURfX2p2bV9sYXVuY2hlZD0xNDg3NDI0ODY3AC1EX19hcHBsZXRfbGF1bmNoZWQ9MTQ4NzM5MDI5NQAtRHN1bi5hd3Qud2FybXVwPXRydWUALURqYXZhLnNlY3VyaXR5Lm1hbmFnZXIA -ma cmVhZF9waXBlX25hbWU9anBpMl9waWQ1NDhfcGlwZTIsd3JpdGVfcGlwZV9uYW1lPWpwaTJfcGlkNTQ4X3BpcGUzAA== | C:\Program Files\Java\jre1.8.0_271\bin\jp2launcher.exe | — | iexplore.exe | |||||||||||
User: admin Company: Oracle Corporation Integrity Level: LOW Description: Java(TM) Web Launcher Exit code: 0 Version: 11.271.2.09 Modules
| |||||||||||||||
| 3368 | "C:\Program Files\Java\jre1.8.0_271\bin\jp2launcher.exe" -secure -plugin -jre "C:\Program Files\Java\jre1.8.0_271" -vma LURfX2p2bV9sYXVuY2hlZD0xNDg3NDI0ODY3AC1EX19hcHBsZXRfbGF1bmNoZWQ9MTQ4NzM5MDI5NQAtRHN1bi5hd3Qud2FybXVwPXRydWUALURqYXZhLnNlY3VyaXR5Lm1hbmFnZXIA -ma cmVhZF9waXBlX25hbWU9anBpMl9waWQ1NDhfcGlwZTIsd3JpdGVfcGlwZV9uYW1lPWpwaTJfcGlkNTQ4X3BpcGUzAA== | C:\Program Files\Java\jre1.8.0_271\bin\jp2launcher.exe | iexplore.exe | ||||||||||||
User: admin Company: Oracle Corporation Integrity Level: MEDIUM Description: Java(TM) Web Launcher Exit code: 0 Version: 11.271.2.09 Modules
| |||||||||||||||
| 3420 | C:\Windows\system32\icacls.exe C:\ProgramData\Oracle\Java\.oracle_jre_usage /grant "everyone":(OI)(CI)M | C:\Windows\System32\icacls.exe | — | javaw.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3576 | "C:\Program Files\Java\jre1.8.0_271\bin\javaw.exe" -cp "C:\PROGRA~1\Java\JRE18~1.0_2\lib\deploy.jar" com.sun.deploy.panel.ControlPanel -userConfig "deployment.expiration.decision.11.271.2" "later" | C:\Program Files\Java\jre1.8.0_271\bin\javaw.exe | — | jp2launcher.exe | |||||||||||
User: admin Company: Oracle Corporation Integrity Level: MEDIUM Description: Java(TM) Platform SE binary Exit code: 0 Version: 8.0.2710.9 Modules
| |||||||||||||||
| 3584 | "C:\PROGRA~1\Java\JRE18~1.0_2\bin\jp2launcher.exe" -sjed | C:\Program Files\Java\jre1.8.0_271\bin\jp2launcher.exe | — | iexplore.exe | |||||||||||
User: admin Company: Oracle Corporation Integrity Level: LOW Description: Java(TM) Web Launcher Exit code: 0 Version: 11.271.2.09 Modules
| |||||||||||||||
| 3600 | "C:\PROGRA~1\Java\JRE18~1.0_2\bin\jp2launcher.exe" -sjed | C:\Program Files\Java\jre1.8.0_271\bin\jp2launcher.exe | — | iexplore.exe | |||||||||||
User: admin Company: Oracle Corporation Integrity Level: MEDIUM Description: Java(TM) Web Launcher Exit code: 3 Version: 11.271.2.09 Modules
| |||||||||||||||
| 3820 | "C:\Program Files\Java\jre1.8.0_271\bin\javaw.exe" -cp "C:\PROGRA~1\Java\JRE18~1.0_2\lib\deploy.jar" com.sun.deploy.panel.ControlPanel -userConfig "deployment.expiration.decision.timestamp.11.271.2" "1707099823" | C:\Program Files\Java\jre1.8.0_271\bin\javaw.exe | — | jp2launcher.exe | |||||||||||
User: admin Company: Oracle Corporation Integrity Level: MEDIUM Description: Java(TM) Platform SE binary Exit code: 0 Version: 8.0.2710.9 Modules
| |||||||||||||||
Total events
25 773
Read events
25 686
Write events
74
Delete events
13
Modification events
| (PID) Process: | (752) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 0 | |||
| (PID) Process: | (752) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30847387 | |||
| (PID) Process: | (752) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30847437 | |||
| (PID) Process: | (752) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (752) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (752) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (752) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (752) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (752) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (752) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
Executable files
0
Suspicious files
10
Text files
21
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 548 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\223DE96EE265046957A660ED7C9DD9E7_EFF9B9BA98DEAA773F261FA85A0B1771 | binary | |
MD5:C56EF1F39C8B5552463C87BE68FF403D | SHA256:299FF200C25FDEFA883331E48ECC3B295034B5DBDE8C76744561C51D7F5E1F9F | |||
| 752 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\B6QGX7LP\favicon[1].ico | image | |
MD5:DA597791BE3B6E732F0BC8B20E38EE62 | SHA256:5B2C34B3C4E8DD898B664DBA6C3786E2FF9869EFF55D673AA48361F11325ED07 | |||
| 548 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\wikipaste[1].htm | html | |
MD5:34C98D8BA67663CF793C0ED078C8C6FF | SHA256:7683EF823EDE9CF38677CBB0EC53C4A60AF87E80A818A52F9FE5387EED2288FE | |||
| 548 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:EF71010782634F1CF0961A84843F9A70 | SHA256:93A81A30B26D3EE10A2ED5EFC1C4E530BB8172AA8E71712CA25F0BBCC0C0C731 | |||
| 548 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\223DE96EE265046957A660ED7C9DD9E7_EFF9B9BA98DEAA773F261FA85A0B1771 | binary | |
MD5:0D59F8B8A5C4CF7D519F12EE522594EE | SHA256:DE82CA920730221D8882E8A3832BDCDE6F181095506CB229B2C4731715B9A6D5 | |||
| 548 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\UPMRS43S.txt | text | |
MD5:16DC83E2D21A2763CB2DF5794010CC5A | SHA256:6D5F3A105169C23106429E4957AA45C8A09E7161EE7F71808B0AA6CFD52C9B03 | |||
| 548 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\analytics[1].js | text | |
MD5:CBC1B007EB7DE0B65EDA9EF00E069EBE | SHA256:A1F3D3BE0AF279C2DA371163D037A3D46569453A855CF91ACECA0F3695C57017 | |||
| 548 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\EB2C4AB8B68FFA4B7733A9139239A396_D76DB901EE986B889F30D8CC06229E2D | der | |
MD5:C4A7CFE0698A9DE21E1D21326B790E7A | SHA256:2373E9B772D466E988D11B77933E11562A39803BA9F4AA33E3D3352A5BE0F4FB | |||
| 752 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\6Z2BCOUL\favicon[1].ico | image | |
MD5:DA597791BE3B6E732F0BC8B20E38EE62 | SHA256:5B2C34B3C4E8DD898B664DBA6C3786E2FF9869EFF55D673AA48361F11325ED07 | |||
| 752 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\VersionManager\versionlist.xml | xml | |
MD5:CBD0581678FA40F0EDCBC7C59E0CAD10 | SHA256:159BD4343F344A08F6AF3B716B6FA679859C1BD1D7030D26FF5EF0255B86E1D9 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
99
TCP/UDP connections
523
DNS requests
12
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
548 | iexplore.exe | GET | 200 | 207.241.224.2:80 | http://archive.org/includes/analytics.js?v=cf34f82 | unknown | text | 5.01 Kb | unknown |
548 | iexplore.exe | GET | 302 | 207.241.237.3:80 | http://web.archive.org/web/20130721165218/wikipaste.eu | unknown | — | — | unknown |
548 | iexplore.exe | GET | 200 | 207.241.237.3:80 | http://web.archive.org/web/20130721165218/http://wikipaste.eu/ | unknown | html | 11.9 Kb | unknown |
548 | iexplore.exe | GET | 302 | 207.241.237.3:80 | http://web.archive.org/web/20130721165218im_/http://static.nimp.org/gnaa.png | unknown | — | — | unknown |
548 | iexplore.exe | GET | 304 | 87.248.205.0:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?58de4c165cfd91a6 | unknown | — | — | unknown |
548 | iexplore.exe | GET | 304 | 87.248.205.0:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?8ca76f517091a19b | unknown | — | — | unknown |
548 | iexplore.exe | GET | 304 | 87.248.205.0:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?f1cf821b4dd35ca6 | unknown | — | — | unknown |
548 | iexplore.exe | GET | 304 | 87.248.205.0:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?be32f5ebe361fd40 | unknown | — | — | unknown |
548 | iexplore.exe | GET | 304 | 87.248.205.0:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?4c08c575f663720e | unknown | — | — | unknown |
548 | iexplore.exe | GET | 304 | 87.248.205.0:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?e8750614d92bade0 | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
548 | iexplore.exe | 207.241.237.3:80 | web.archive.org | INTERNET-ARCHIVE | US | unknown |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
548 | iexplore.exe | 207.241.224.2:80 | archive.org | INTERNET-ARCHIVE | US | malicious |
548 | iexplore.exe | 207.241.237.2:443 | web-static.archive.org | INTERNET-ARCHIVE | US | unknown |
548 | iexplore.exe | 87.248.205.0:80 | ctldl.windowsupdate.com | LLNW | US | unknown |
548 | iexplore.exe | 192.124.249.41:80 | ocsp.godaddy.com | SUCURI-SEC | US | unknown |
752 | iexplore.exe | 2.23.209.130:443 | www.bing.com | Akamai International B.V. | GB | unknown |
548 | iexplore.exe | 207.241.224.2:443 | archive.org | INTERNET-ARCHIVE | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
web.archive.org |
| whitelisted |
archive.org |
| whitelisted |
web-static.archive.org |
| unknown |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.godaddy.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
iecvlist.microsoft.com |
| whitelisted |
r20swj13mr.microsoft.com |
| whitelisted |