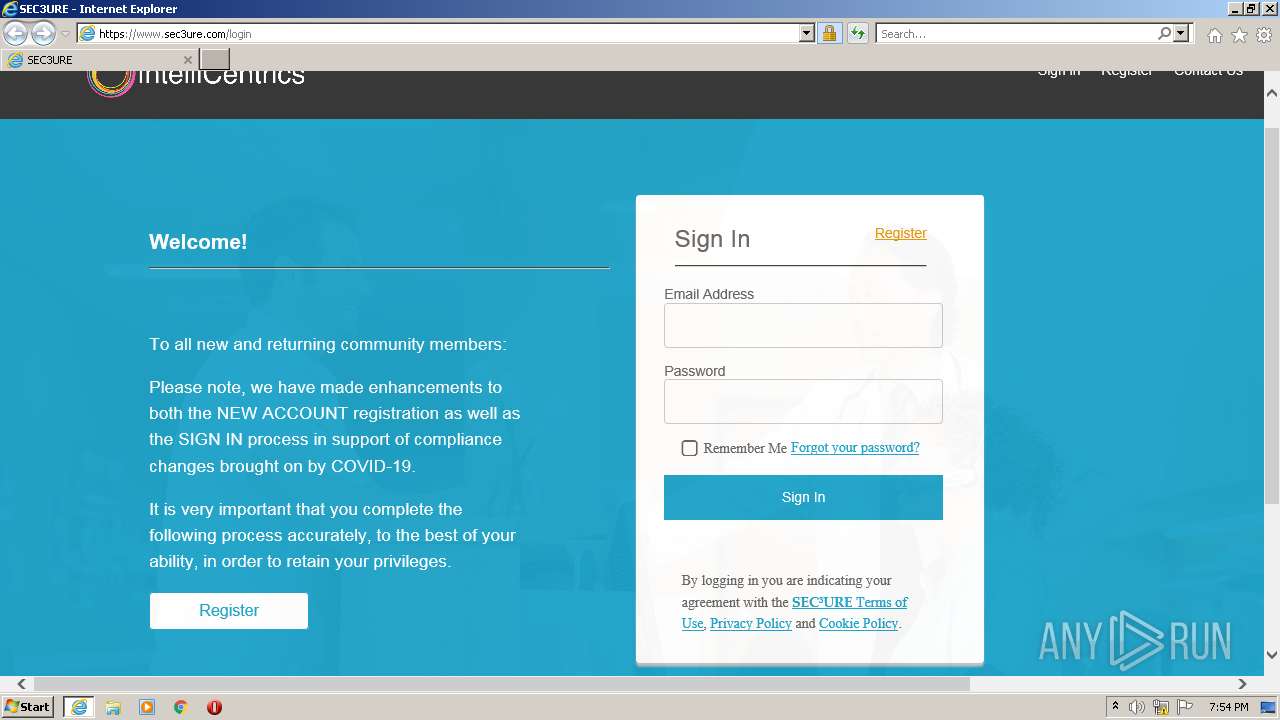
| URL: | https://u6409736.ct.sendgrid.net/ls/click?upn=hFRyAOWJqNVu8NXJyJSca8h1Yyh4oD533C0BFa97JZmlcK8NFnknKM6Aoi0FxDBLrBpA_xFjeGo6PQplDh-2FGEMLxWrpJ7UoCZLZr3Xz-2Fcn4eGgN6NOFkK-2Bk7TIQQJ-2BIZJ9XVedPXtUCqt72YuDwuuZ-2Fml4lqDnCFoMcuW8mx41vm-2FUgdj60WbLNBzCkkfkDFMfBSWs1SrIG2BN0jlROBZLnKFM9TJ6fQsmM9TOlNdVsj6Dxi6U01M3k8d0TD2CgiFAYrTqtHlUF5KHooehkJ2YzanyQ-3D-3D |
| Full analysis: | https://app.any.run/tasks/1833270a-2e1e-4802-b73d-0d8116a791a8 |
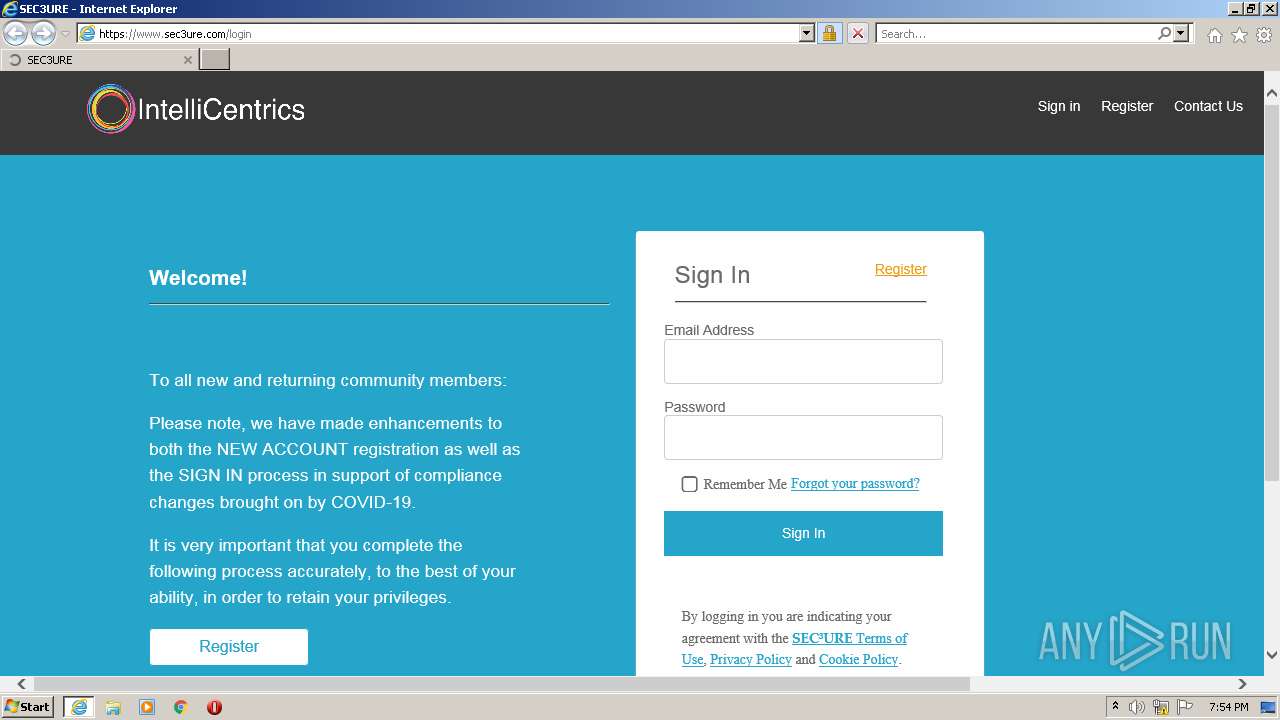
| Verdict: | Malicious activity |
| Analysis date: | January 24, 2022, 19:53:36 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 475B48367574600EA86DEAAB190DDD81 |
| SHA1: | AC3055CF6A74B1BFBC2DF8E79CD781169698441E |
| SHA256: | 60F55D0063EAB62A4E26D3EC08136A02A0A9E1305F50187133E65DB2BCED25C6 |
| SSDEEP: | 6:22TY6xC3c6Q0NU818oLjvIoIFRz/uqncvMw9SyjoJcUK1XjeOheq+Shgsppy5:22sSC3c67G82CvmzcvMw9ZkCUK1iOh3I |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 4044)
INFO
Checks supported languages
- iexplore.exe (PID: 1816)
- iexplore.exe (PID: 4044)
Reads the computer name
- iexplore.exe (PID: 1816)
- iexplore.exe (PID: 4044)
Changes internet zones settings
- iexplore.exe (PID: 1816)
Application launched itself
- iexplore.exe (PID: 1816)
Reads settings of System Certificates
- iexplore.exe (PID: 4044)
- iexplore.exe (PID: 1816)
Reads internet explorer settings
- iexplore.exe (PID: 4044)
Checks Windows Trust Settings
- iexplore.exe (PID: 4044)
- iexplore.exe (PID: 1816)
Creates files in the user directory
- iexplore.exe (PID: 4044)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
37
Monitored processes
2
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1816 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://u6409736.ct.sendgrid.net/ls/click?upn=hFRyAOWJqNVu8NXJyJSca8h1Yyh4oD533C0BFa97JZmlcK8NFnknKM6Aoi0FxDBLrBpA_xFjeGo6PQplDh-2FGEMLxWrpJ7UoCZLZr3Xz-2Fcn4eGgN6NOFkK-2Bk7TIQQJ-2BIZJ9XVedPXtUCqt72YuDwuuZ-2Fml4lqDnCFoMcuW8mx41vm-2FUgdj60WbLNBzCkkfkDFMfBSWs1SrIG2BN0jlROBZLnKFM9TJ6fQsmM9TOlNdVsj6Dxi6U01M3k8d0TD2CgiFAYrTqtHlUF5KHooehkJ2YzanyQ-3D-3D" | C:\Program Files\Internet Explorer\iexplore.exe | Explorer.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 4044 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:1816 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
10 723
Read events
10 601
Write events
122
Delete events
0
Modification events
| (PID) Process: | (1816) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (1816) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: 358416944 | |||
| (PID) Process: | (1816) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30937436 | |||
| (PID) Process: | (1816) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 658425772 | |||
| (PID) Process: | (1816) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30937436 | |||
| (PID) Process: | (1816) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (1816) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (1816) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (1816) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (1816) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
0
Suspicious files
18
Text files
26
Unknown types
15
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1816 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\6BADA8974A10C4BD62CC921D13E43B18_711ED44619924BA6DC33E69F97E7FF63 | binary | |
MD5:— | SHA256:— | |||
| 4044 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\C5FD5BF0CE6372B1CAFE381FD0BC969C | binary | |
MD5:— | SHA256:— | |||
| 1816 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\6BADA8974A10C4BD62CC921D13E43B18_711ED44619924BA6DC33E69F97E7FF63 | der | |
MD5:— | SHA256:— | |||
| 4044 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | compressed | |
MD5:F7DCB24540769805E5BB30D193944DCE | SHA256:6B88C6AC55BBD6FEA0EBE5A760D1AD2CFCE251C59D0151A1400701CB927E36EA | |||
| 4044 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:— | SHA256:— | |||
| 4044 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\C5FD5BF0CE6372B1CAFE381FD0BC969C | der | |
MD5:— | SHA256:— | |||
| 4044 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\223DE96EE265046957A660ED7C9DD9E7_EFF9B9BA98DEAA773F261FA85A0B1771 | der | |
MD5:— | SHA256:— | |||
| 4044 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\B39C403EE7698F732743C79CB583A818_F94572BF13D20C8A2D58EA30B5AB031E | der | |
MD5:— | SHA256:— | |||
| 4044 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\223DE96EE265046957A660ED7C9DD9E7_EFF9B9BA98DEAA773F261FA85A0B1771 | binary | |
MD5:— | SHA256:— | |||
| 4044 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\B39C403EE7698F732743C79CB583A818_F94572BF13D20C8A2D58EA30B5AB031E | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
15
TCP/UDP connections
50
DNS requests
22
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4044 | iexplore.exe | GET | 200 | 192.124.249.41:80 | http://crl.godaddy.com/gdroot.crl | US | der | 429 b | whitelisted |
4044 | iexplore.exe | GET | 200 | 192.124.249.24:80 | http://ocsp.godaddy.com//MEQwQjBAMD4wPDAJBgUrDgMCGgUABBTkIInKBAzXkF0Qh0pel3lfHJ9GPAQU0sSw0pHUTBFxs2HLPaH%2B3ahq1OMCAxvnFQ%3D%3D | US | der | 1.66 Kb | whitelisted |
4044 | iexplore.exe | GET | 200 | 142.250.186.131:80 | http://ocsp.pki.goog/gtsr1/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBQwkcLWD4LqGJ7bE7B1XZsEbmfwUAQU5K8rJnEaK0gnhS9SZizv8IkTcT4CDQIDvFNZazTHGPUBUGY%3D | US | der | 724 b | whitelisted |
1816 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | der | 471 b | whitelisted |
4044 | iexplore.exe | GET | 200 | 192.124.249.41:80 | http://ocsp.godaddy.com//MEkwRzBFMEMwQTAJBgUrDgMCGgUABBS2CA1fbGt26xPkOKX4ZguoUjM0TgQUQMK9J47MNIMwojPX%2B2yz8LQsgM4CCAFQWPc8P68%2F | US | der | 1.74 Kb | whitelisted |
4044 | iexplore.exe | GET | 200 | 18.66.92.207:80 | http://o.ss2.us//MEowSDBGMEQwQjAJBgUrDgMCGgUABBSLwZ6EW5gdYc9UaSEaaLjjETNtkAQUv1%2B30c7dH4b0W1Ws3NcQwg6piOcCCQCnDkpMNIK3fw%3D%3D | US | der | 1.70 Kb | whitelisted |
4044 | iexplore.exe | GET | 200 | 18.66.92.168:80 | http://s.ss2.us/r.crl | US | der | 434 b | whitelisted |
4044 | iexplore.exe | GET | 200 | 52.222.206.35:80 | http://ocsp.rootg2.amazontrust.com/MFQwUjBQME4wTDAJBgUrDgMCGgUABBSIfaREXmfqfJR3TkMYnD7O5MhzEgQUnF8A36oB1zArOIiiuG1KnPIRkYMCEwZ%2FlEoqJ83z%2BsKuKwH5CO65xMY%3D | US | der | 1.51 Kb | whitelisted |
4044 | iexplore.exe | GET | 200 | 18.66.107.199:80 | http://ocsp.sca1b.amazontrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQz9arGHWbnBV0DFzpNHz4YcTiFDQQUWaRmBlKge5WSPKOUByeWdFv5PdACEAP5dxYnC06ArHT8EAJuJCM%3D | US | der | 471 b | whitelisted |
4044 | iexplore.exe | GET | 200 | 192.124.249.41:80 | http://ocsp.godaddy.com//MEIwQDA%2BMDwwOjAJBgUrDgMCGgUABBQdI2%2BOBkuXH93foRUj4a7lAr4rGwQUOpqFBxBnKLbv9r0FQW4gwZTaD94CAQc%3D | US | der | 1.69 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4044 | iexplore.exe | 192.124.249.24:80 | ocsp.godaddy.com | Sucuri | US | suspicious |
4044 | iexplore.exe | 18.66.107.199:80 | ocsp.sca1b.amazontrust.com | Massachusetts Institute of Technology | US | whitelisted |
4044 | iexplore.exe | 209.197.3.8:80 | ctldl.windowsupdate.com | Highwinds Network Group, Inc. | US | whitelisted |
4044 | iexplore.exe | 192.124.249.41:80 | ocsp.godaddy.com | Sucuri | US | suspicious |
1816 | iexplore.exe | 131.253.33.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
— | — | 131.253.33.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
1816 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
4044 | iexplore.exe | 18.66.92.168:80 | s.ss2.us | Massachusetts Institute of Technology | US | unknown |
4044 | iexplore.exe | 52.222.206.35:80 | ocsp.rootg2.amazontrust.com | Amazon.com, Inc. | US | whitelisted |
— | — | 142.250.186.131:80 | ocsp.pki.goog | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
u6409736.ct.sendgrid.net |
| suspicious |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.godaddy.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
crl.godaddy.com |
| whitelisted |
www.sec3ure.com |
| unknown |
o.ss2.us |
| whitelisted |
s.ss2.us |
| whitelisted |