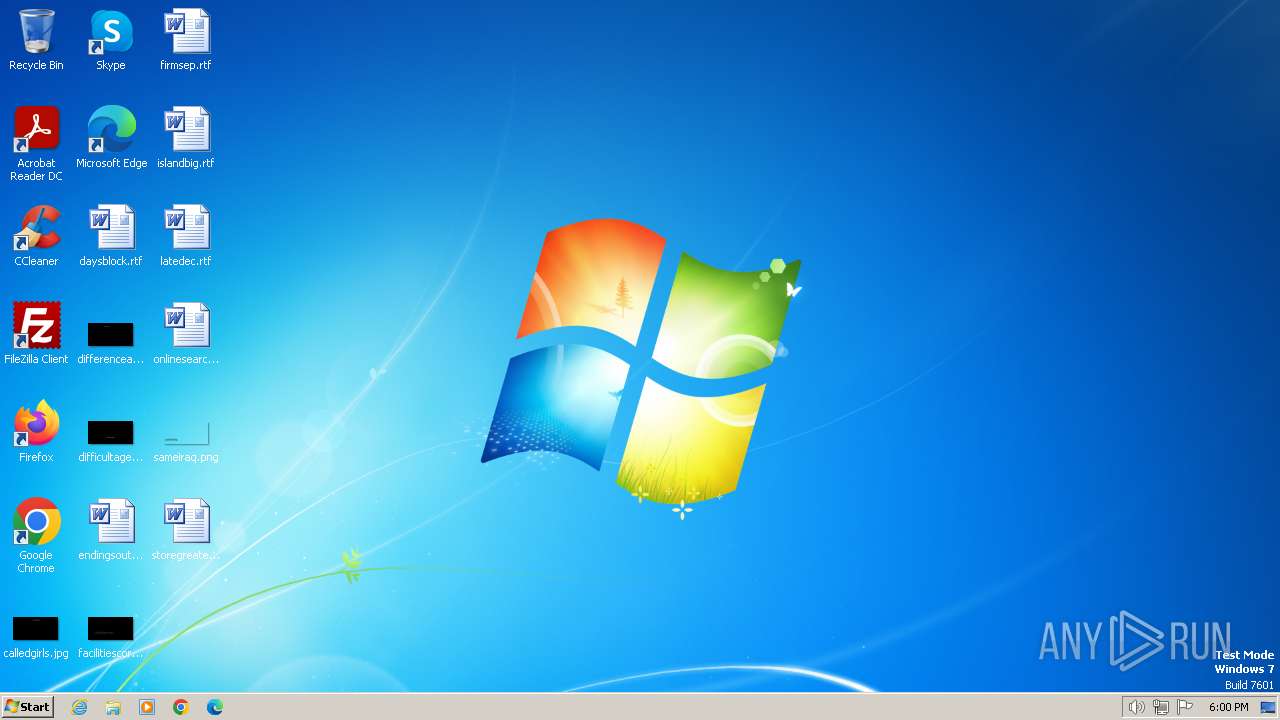
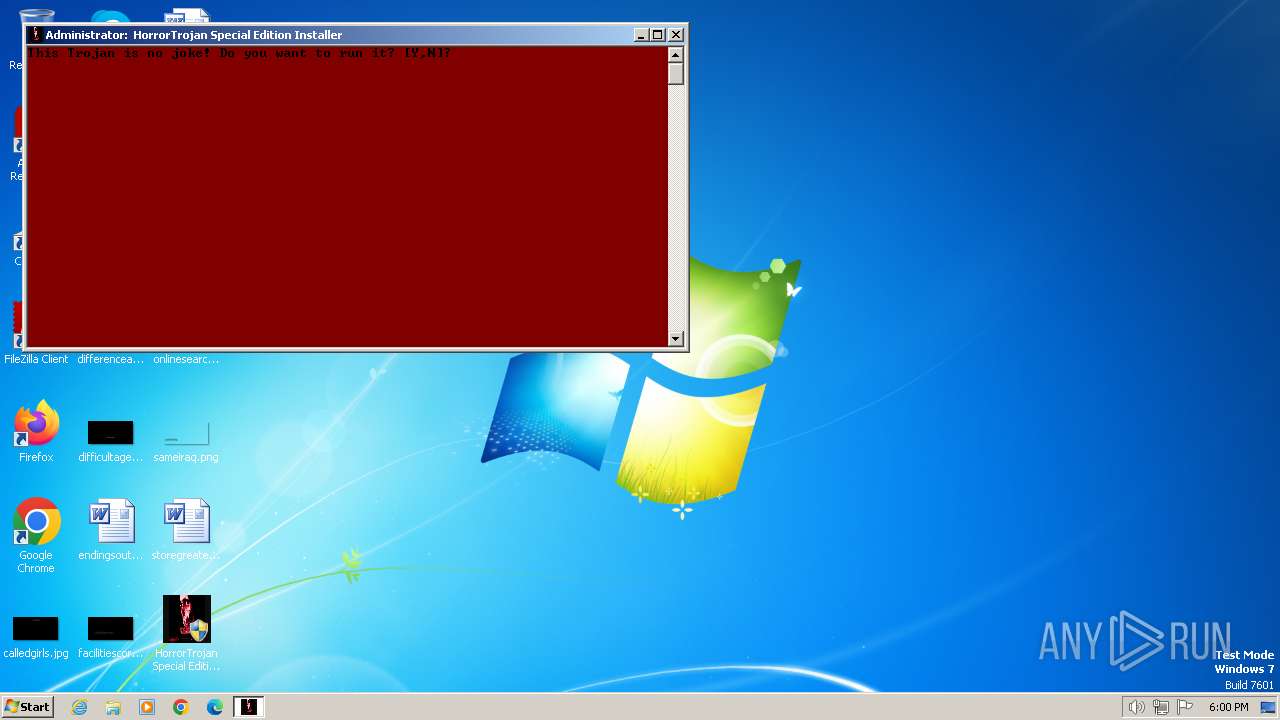
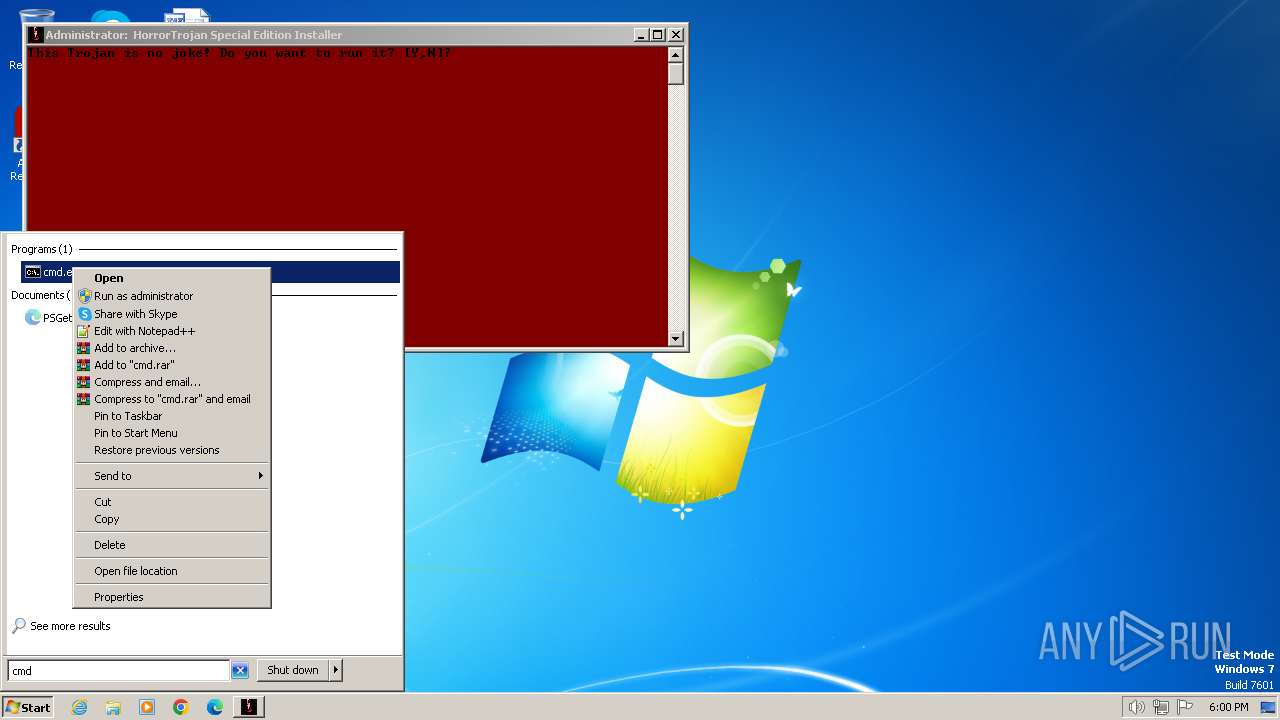
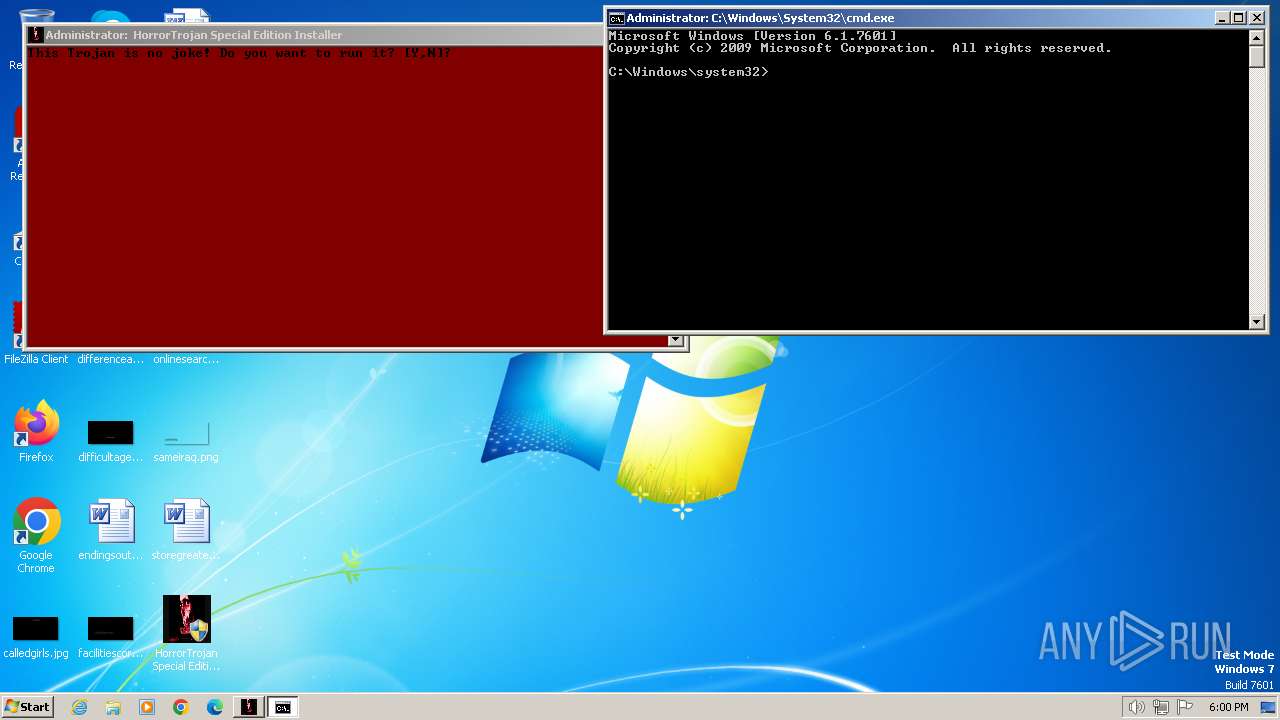
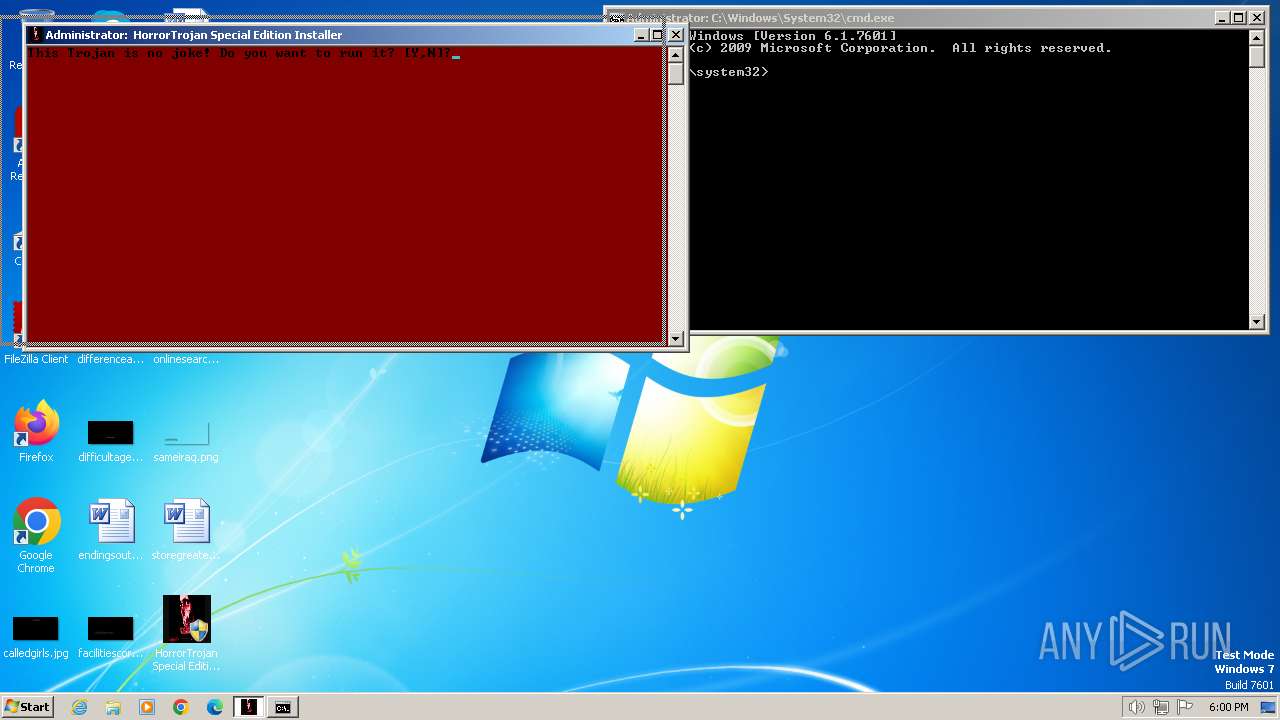
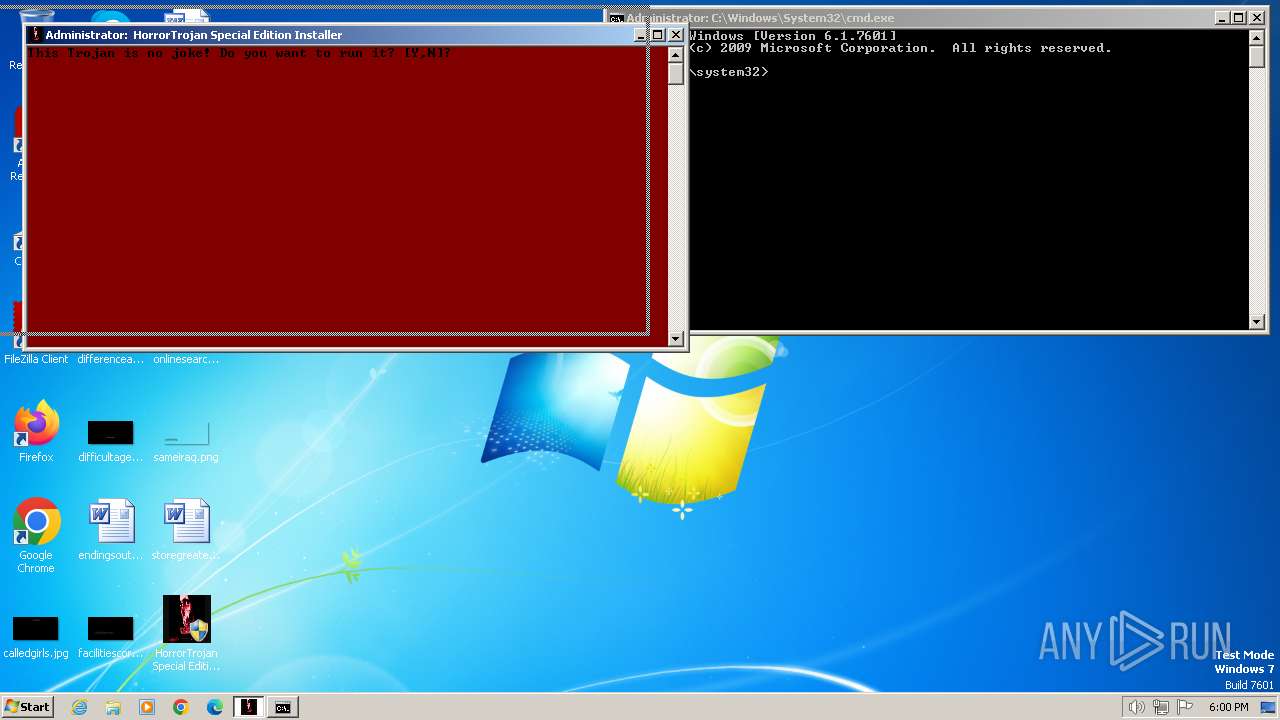
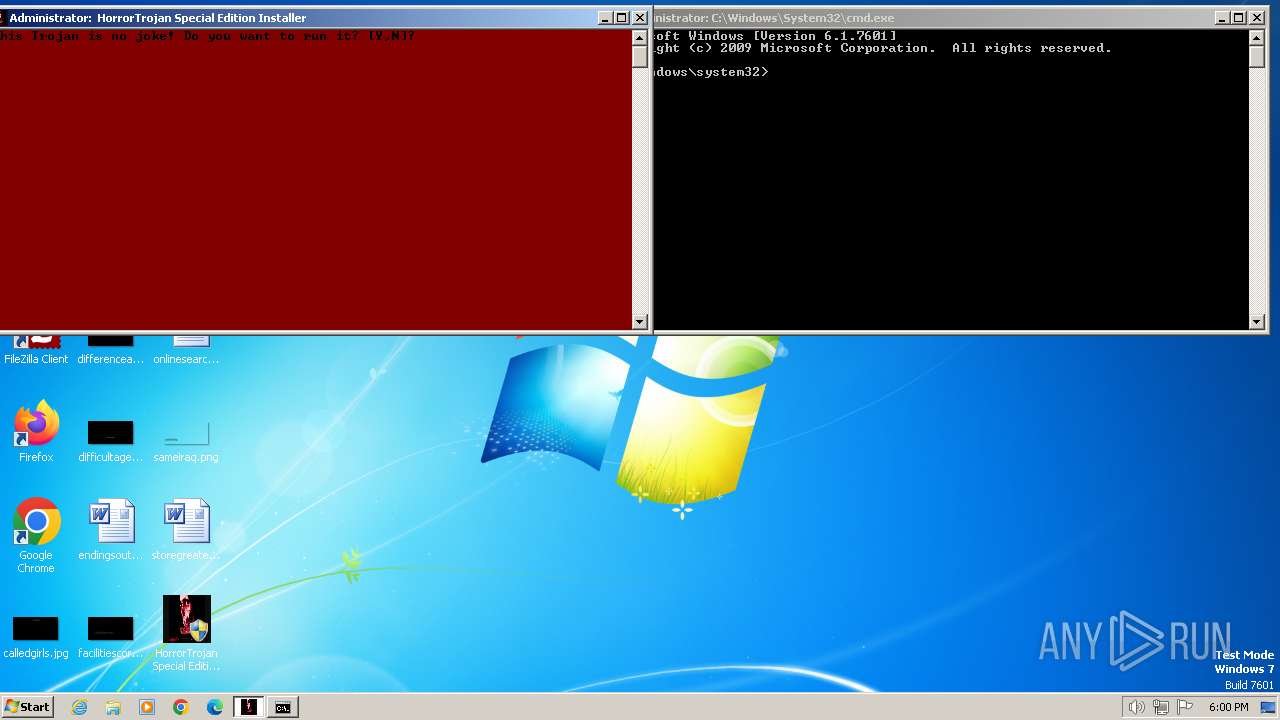
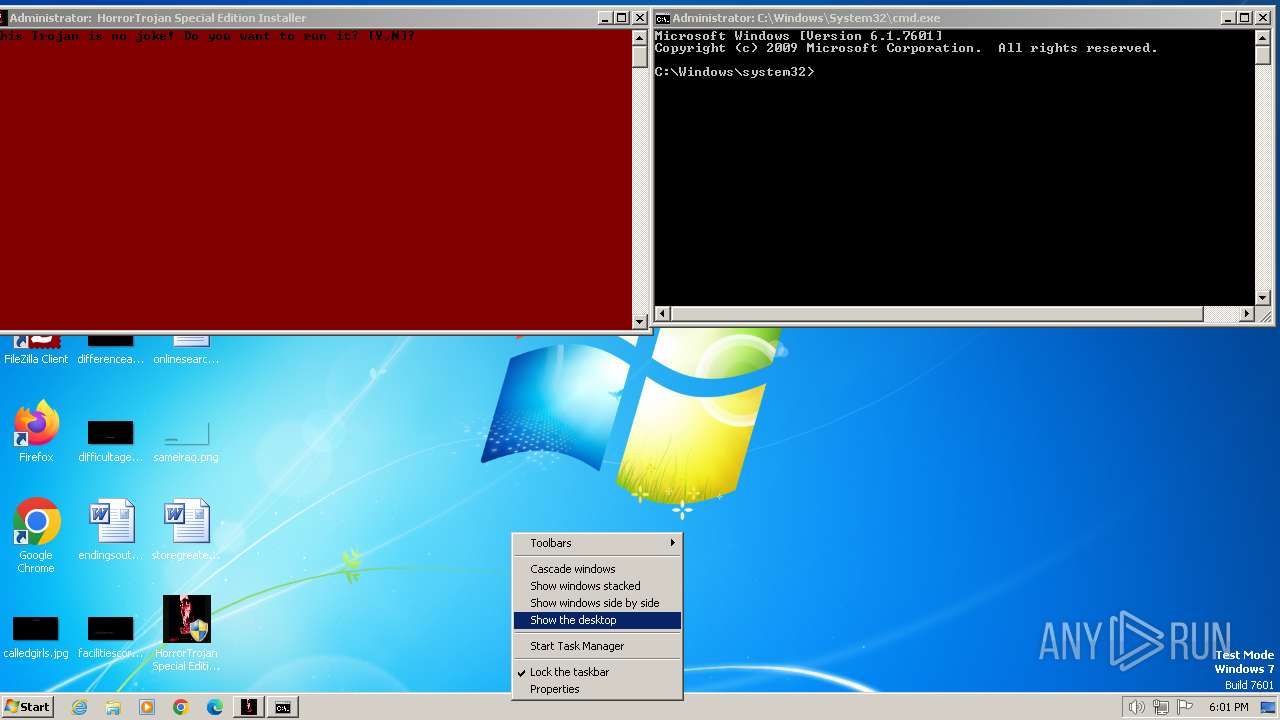
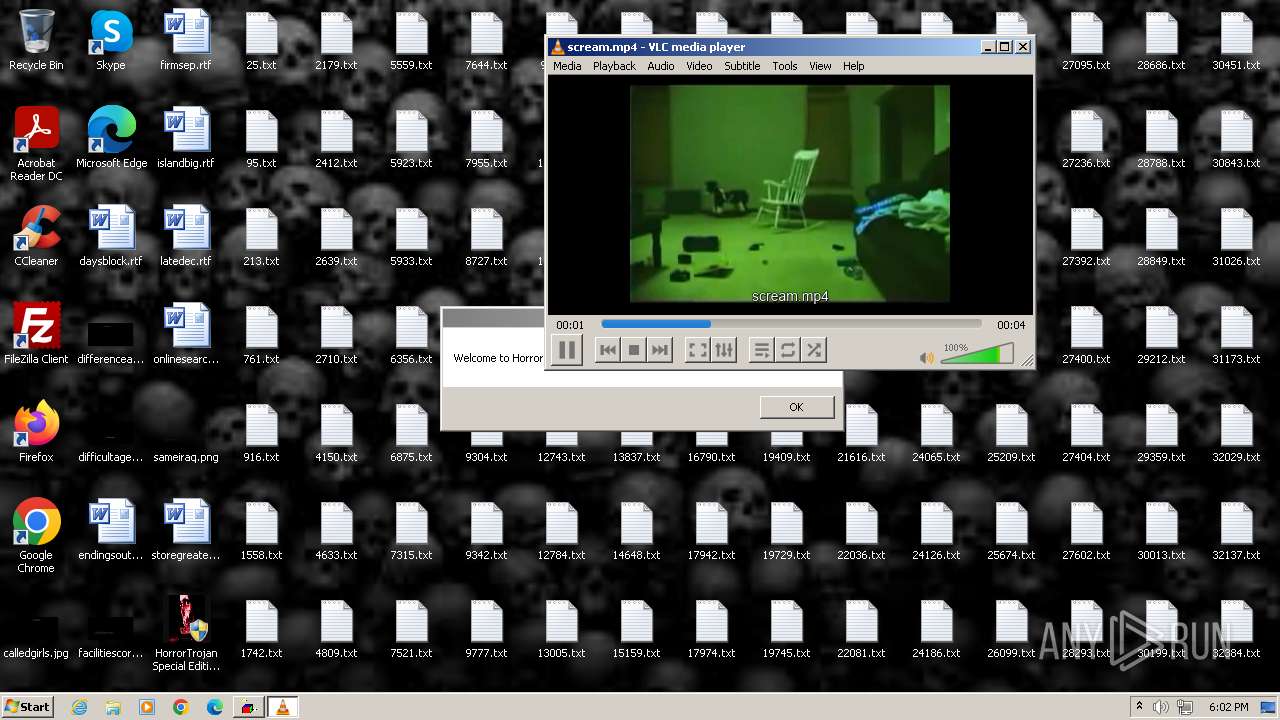
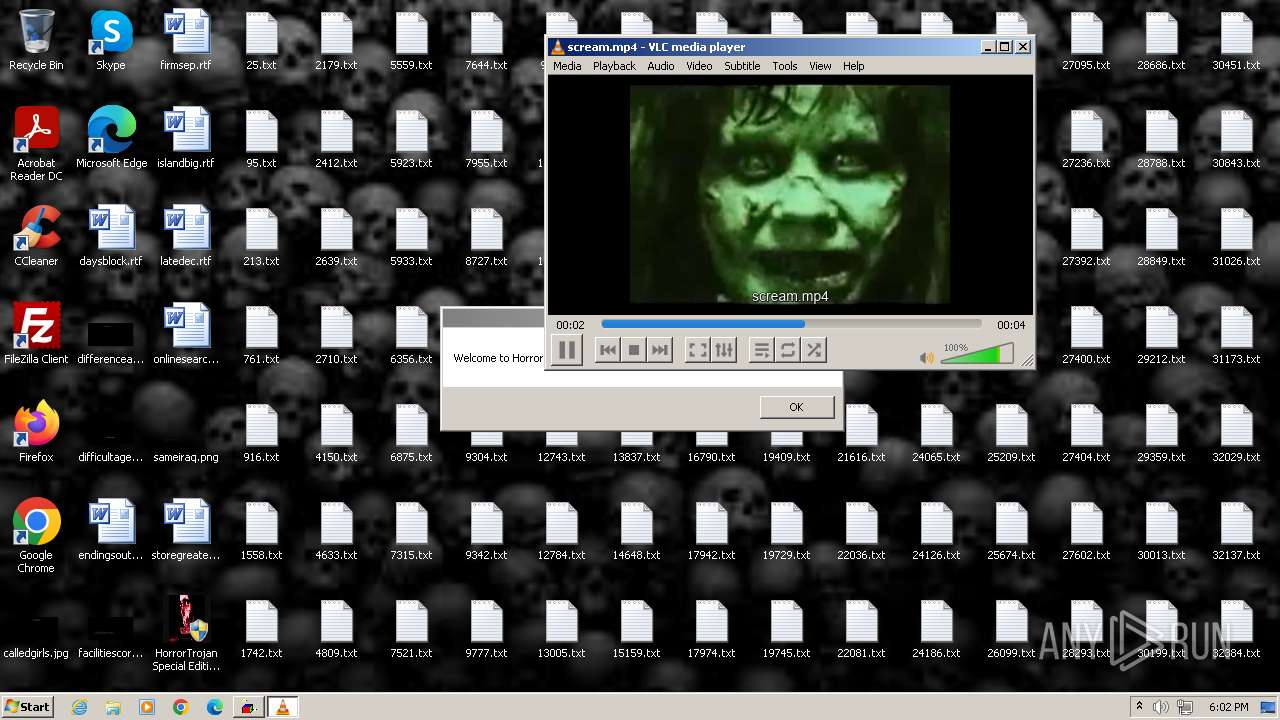
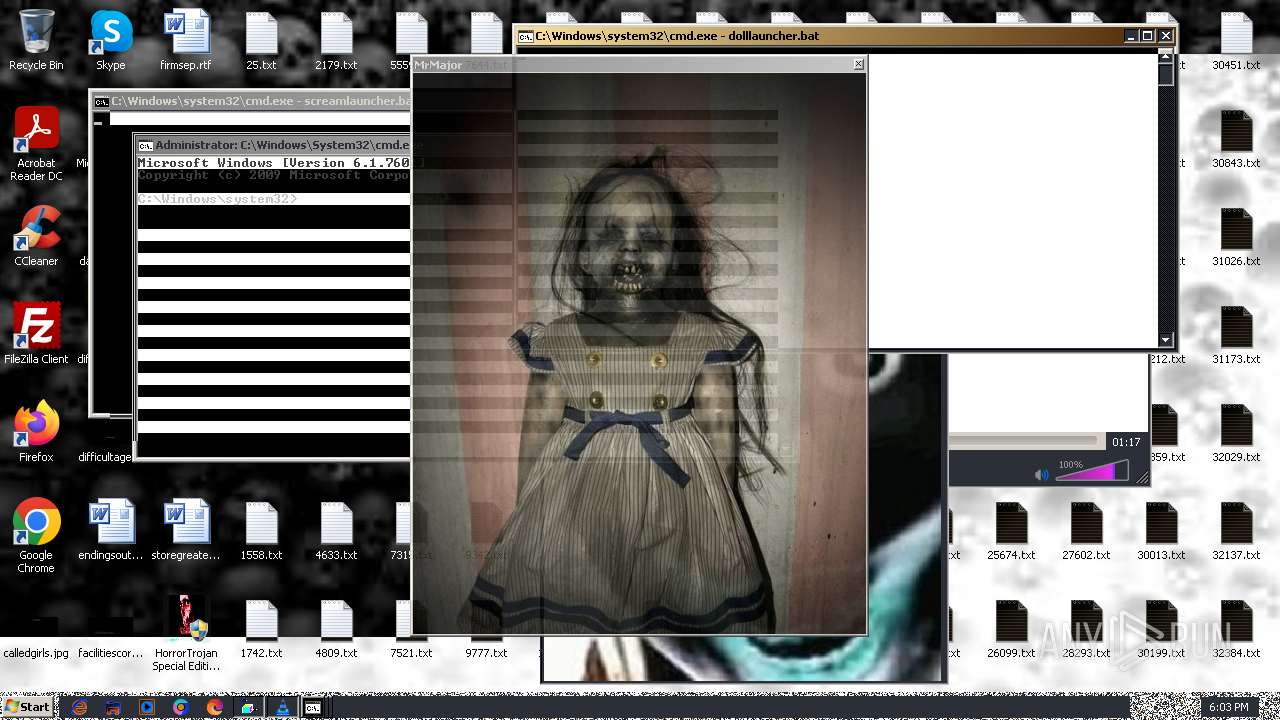
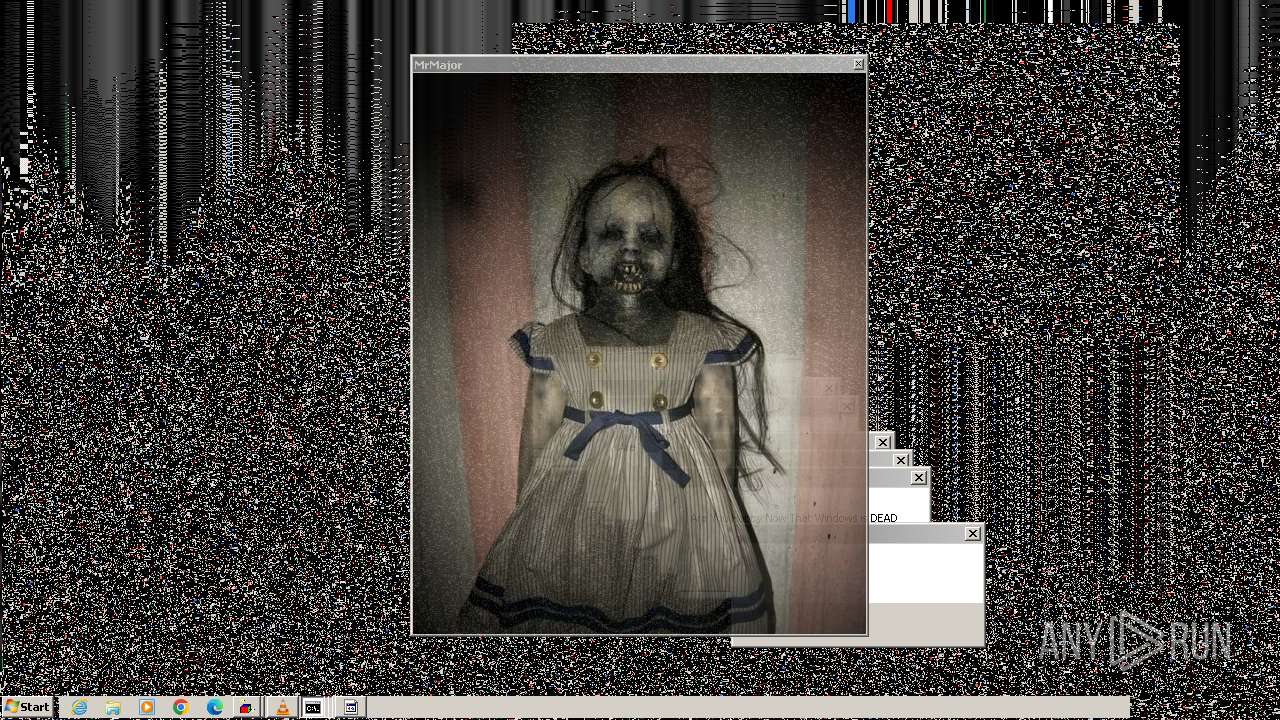
| File name: | HorrorTrojan Special Edition Installer.exe |
| Full analysis: | https://app.any.run/tasks/f9bf0800-7583-4427-8464-f699b0b8eb0f |
| Verdict: | Malicious activity |
| Analysis date: | April 16, 2024, 17:00:11 |
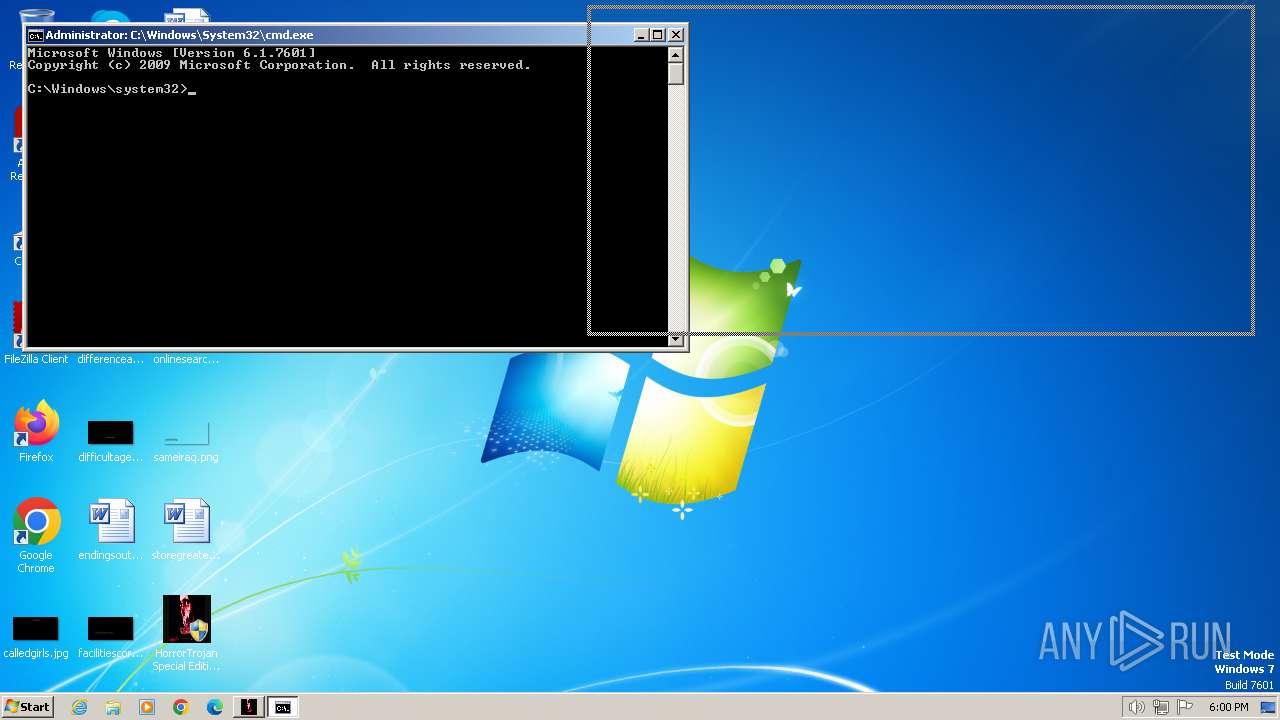
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (console) Intel 80386, for MS Windows, UPX compressed |
| MD5: | 57A5524854D784CE379D1DF702B22645 |
| SHA1: | 171949C131EE42B4F02C9250AAA4B1E52E633AF5 |
| SHA256: | 60F48BBA56211EEED2FF0E1BFA36F91E16B452D37EA3868D9A76DCA45553A752 |
| SSDEEP: | 98304:nxy0ABIKqOmA3SJe9uJJa50lESJWLTDsNTg4QcDd1P7wv2Xju44gllo+znzRGnl2:UeG |
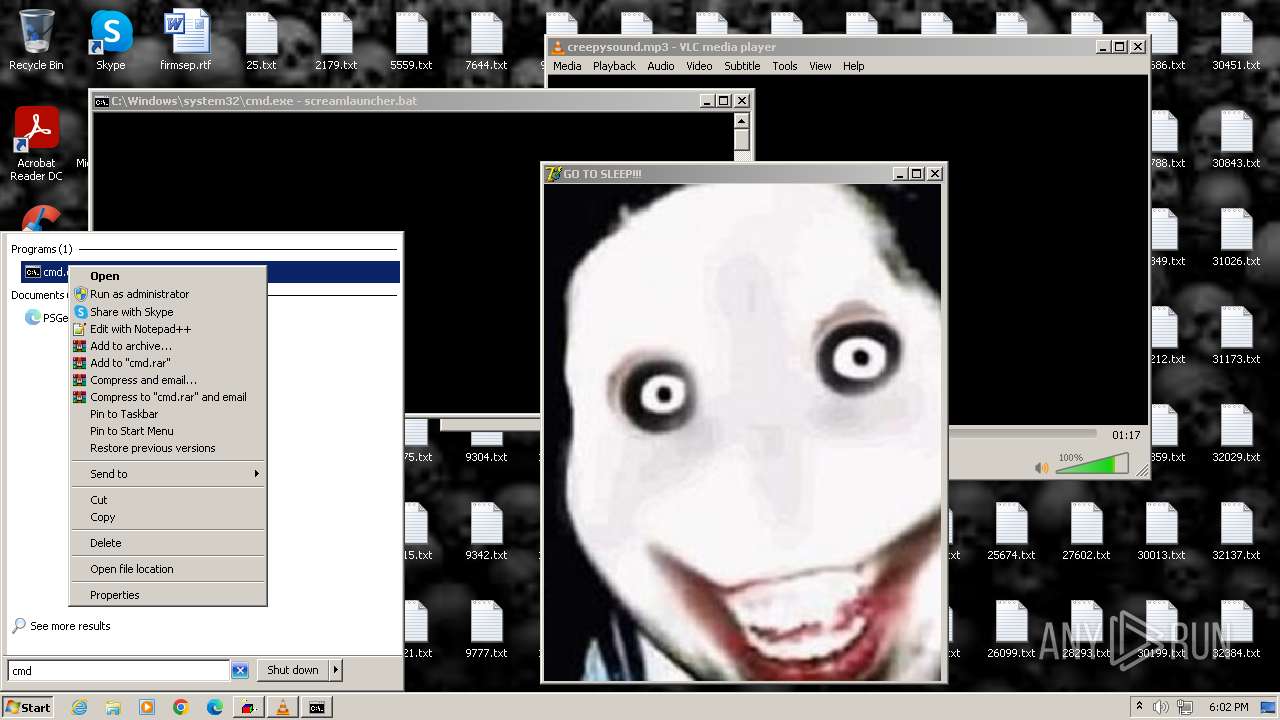
MALICIOUS
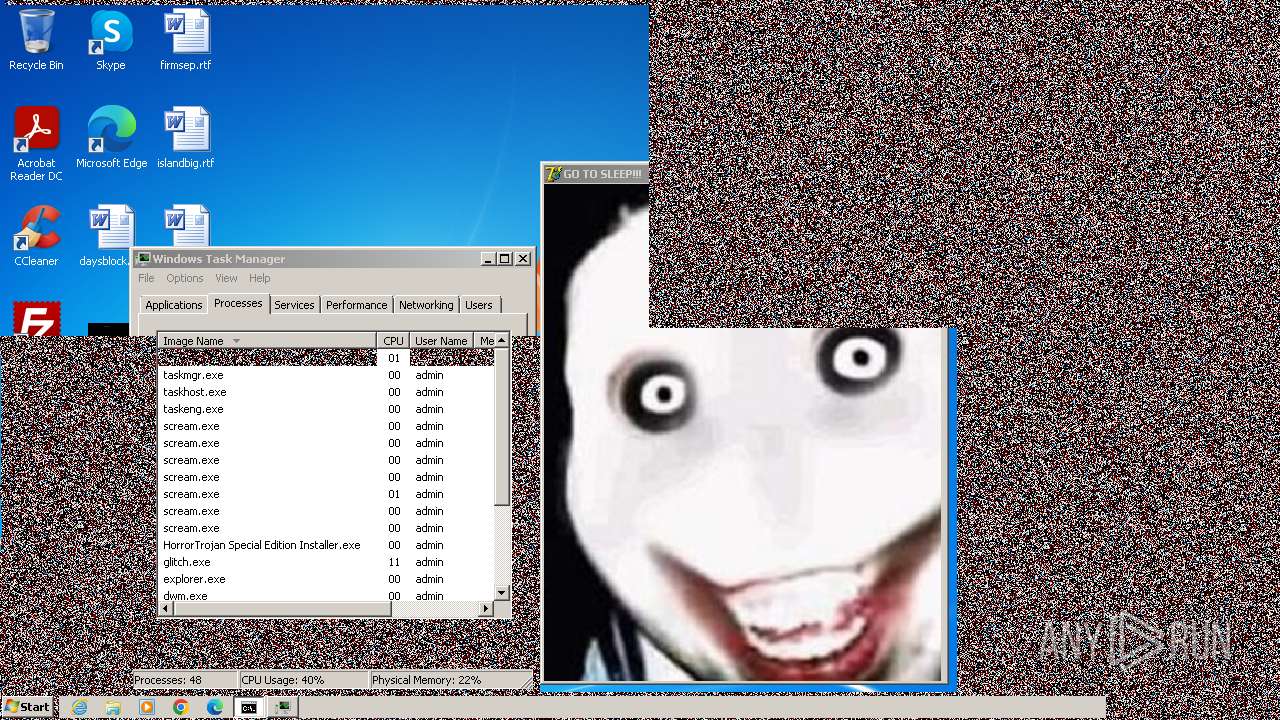
Drops the executable file immediately after the start
- HorrorTrojan Special Edition Installer.exe (PID: 3352)
- cmd.exe (PID: 3112)
- WinKern64.exe (PID: 2008)
- cmd.exe (PID: 2120)
Starts NET.EXE to view/add/change user profiles
- cmd.exe (PID: 3112)
- net.exe (PID: 1812)
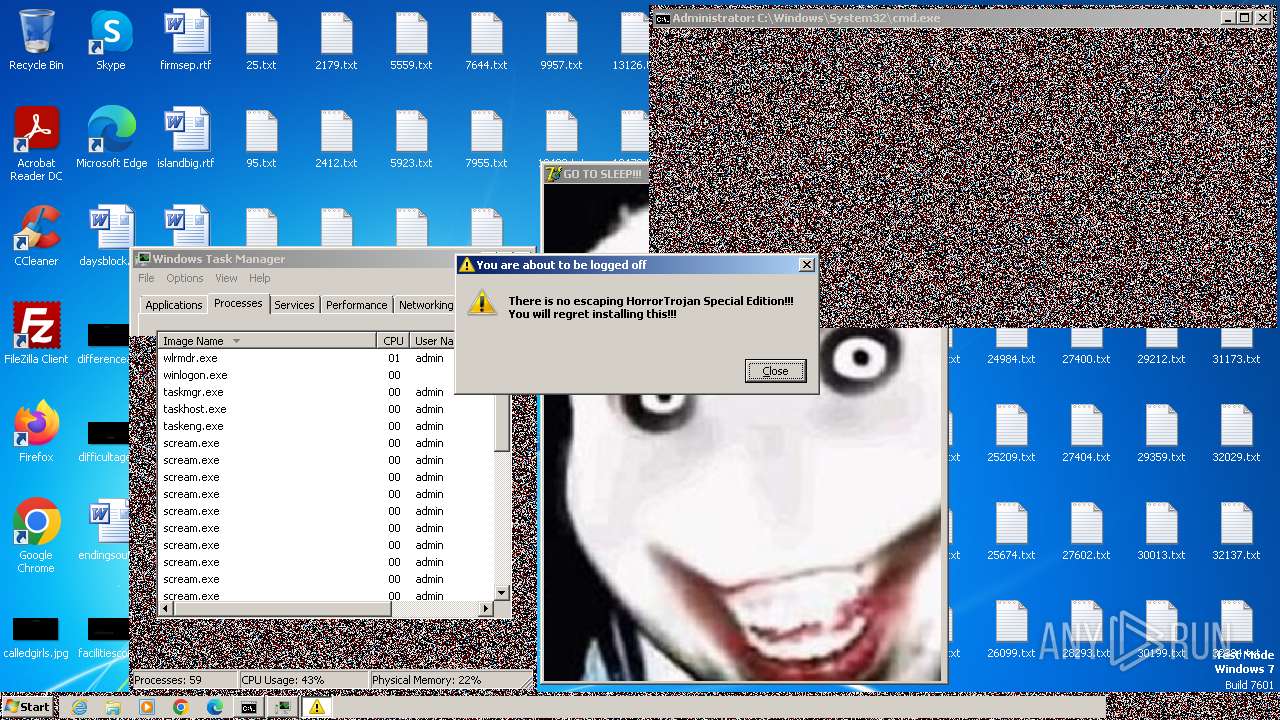
Changes the autorun value in the registry
- reg.exe (PID: 3384)
- MbrKiller.exe (PID: 2300)
UAC/LUA settings modification
- reg.exe (PID: 4036)
SUSPICIOUS
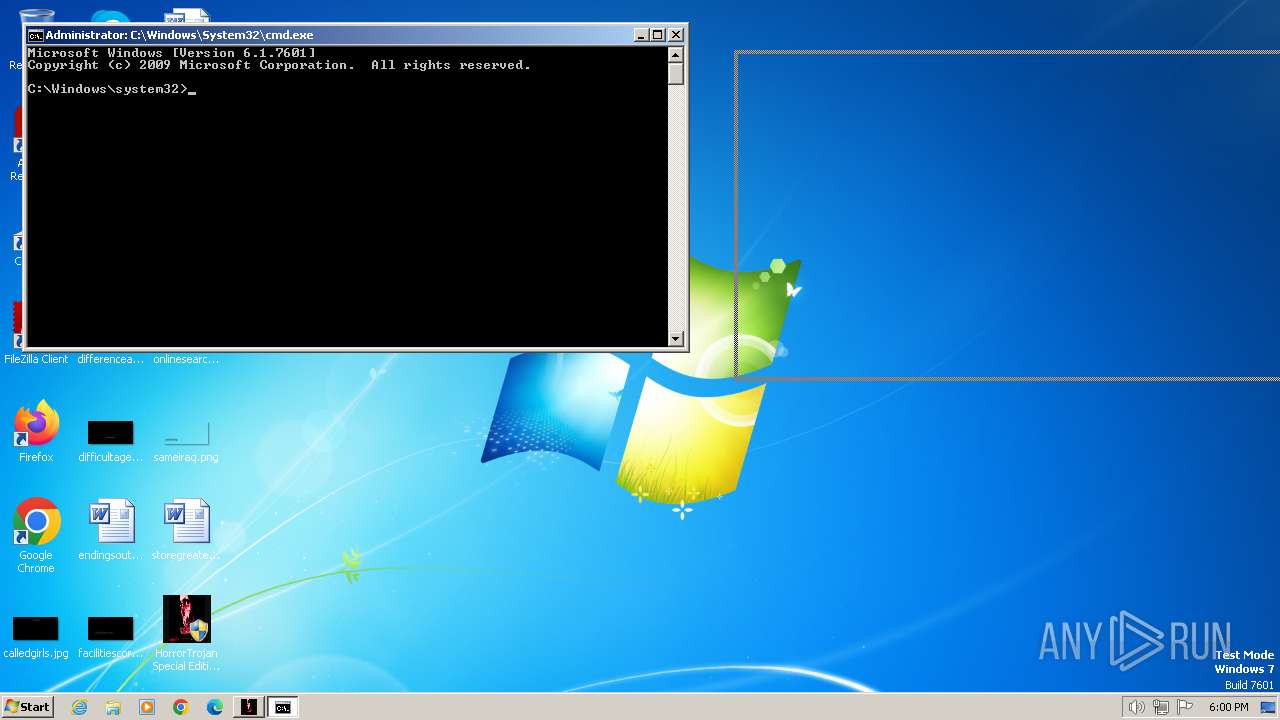
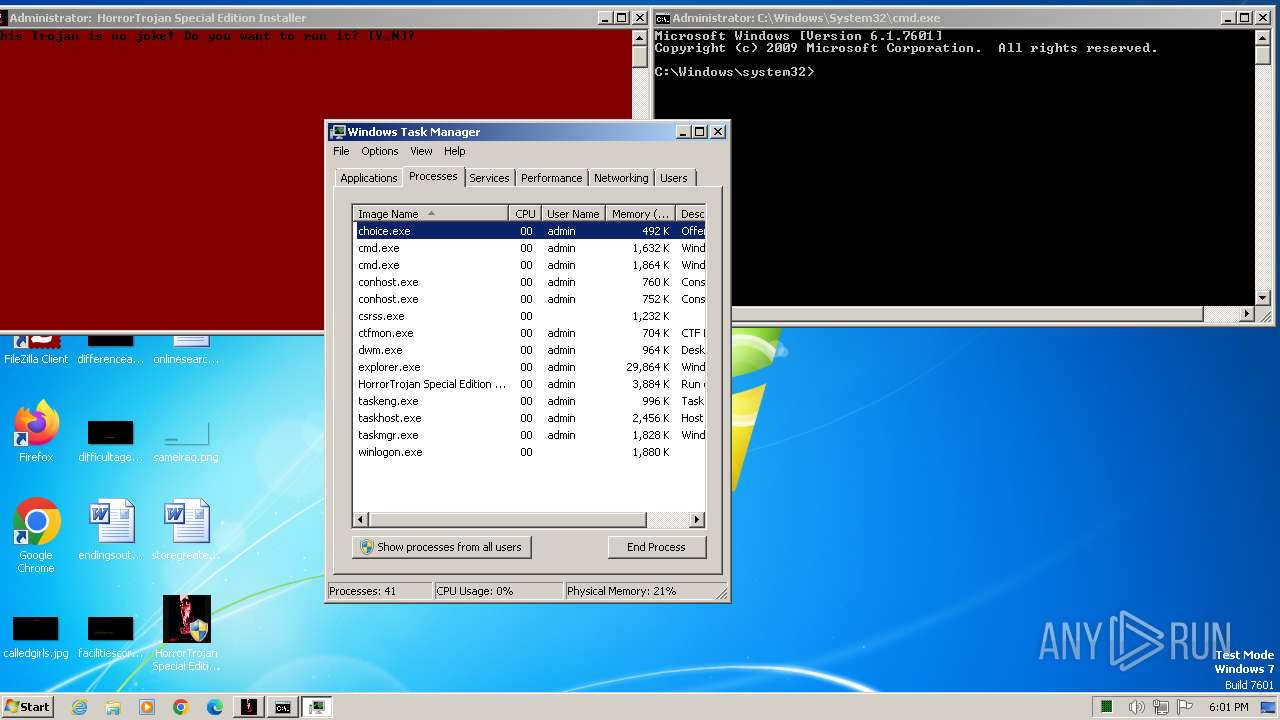
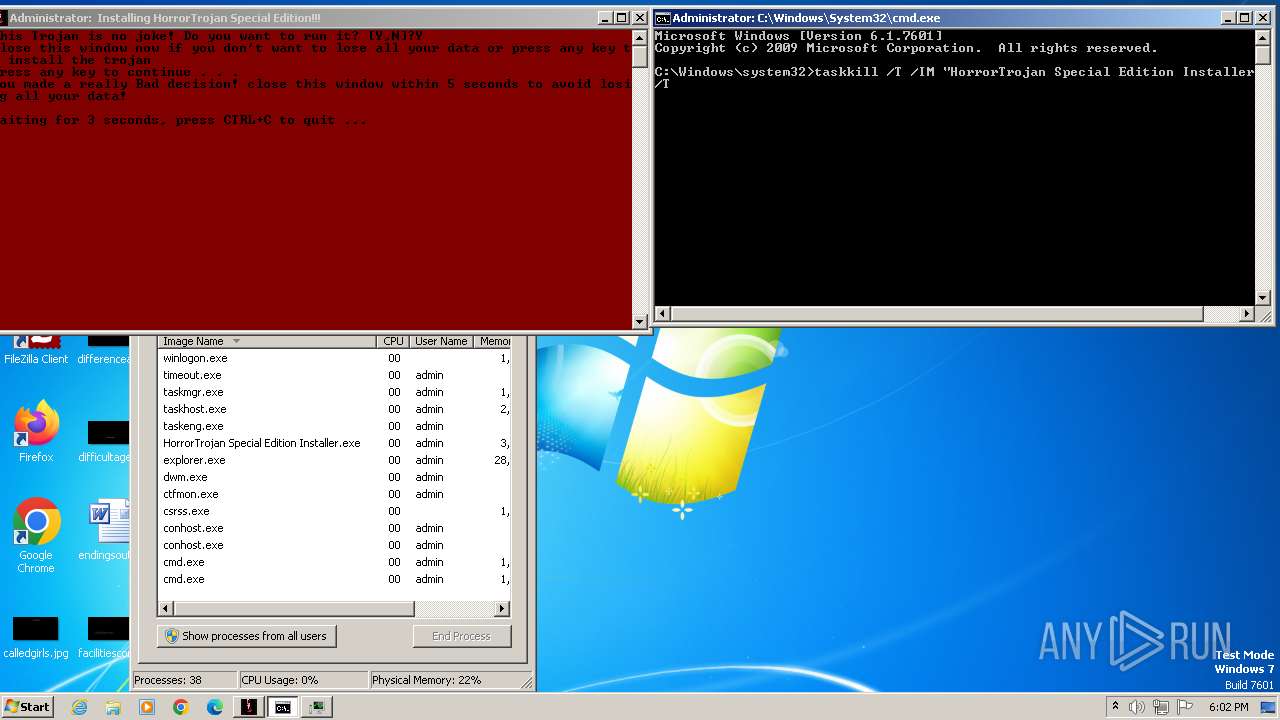
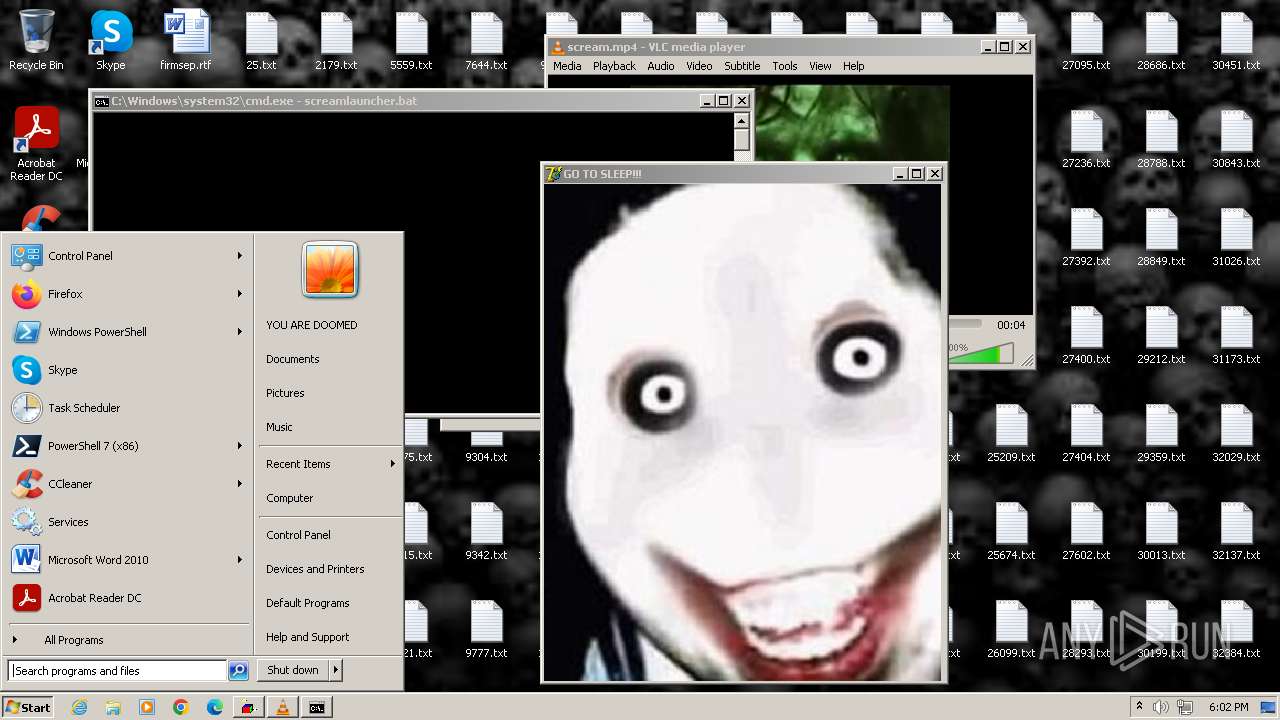
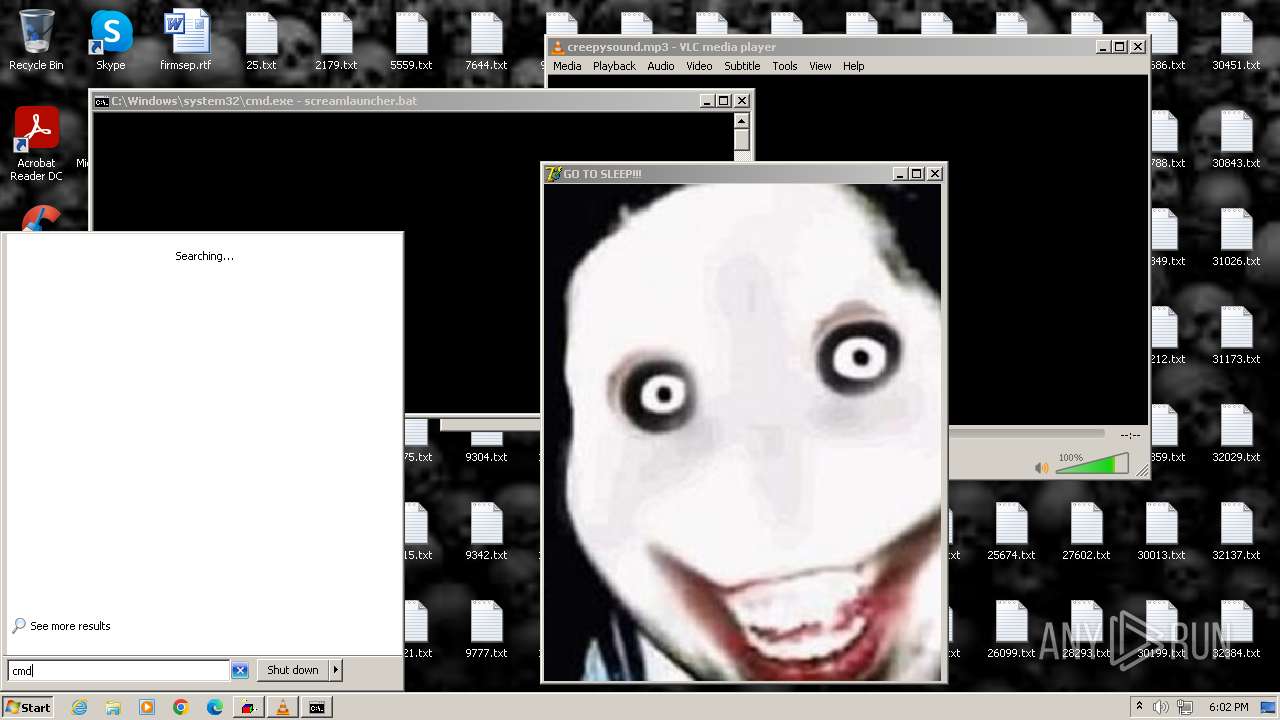
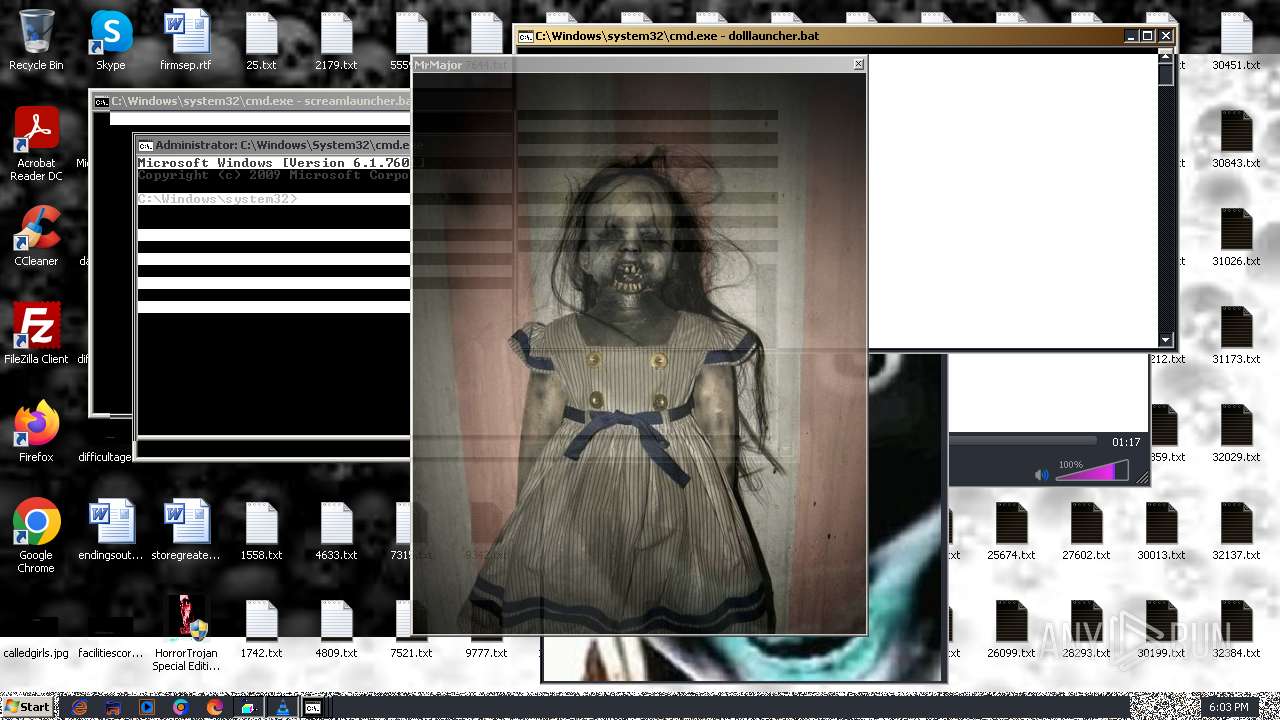
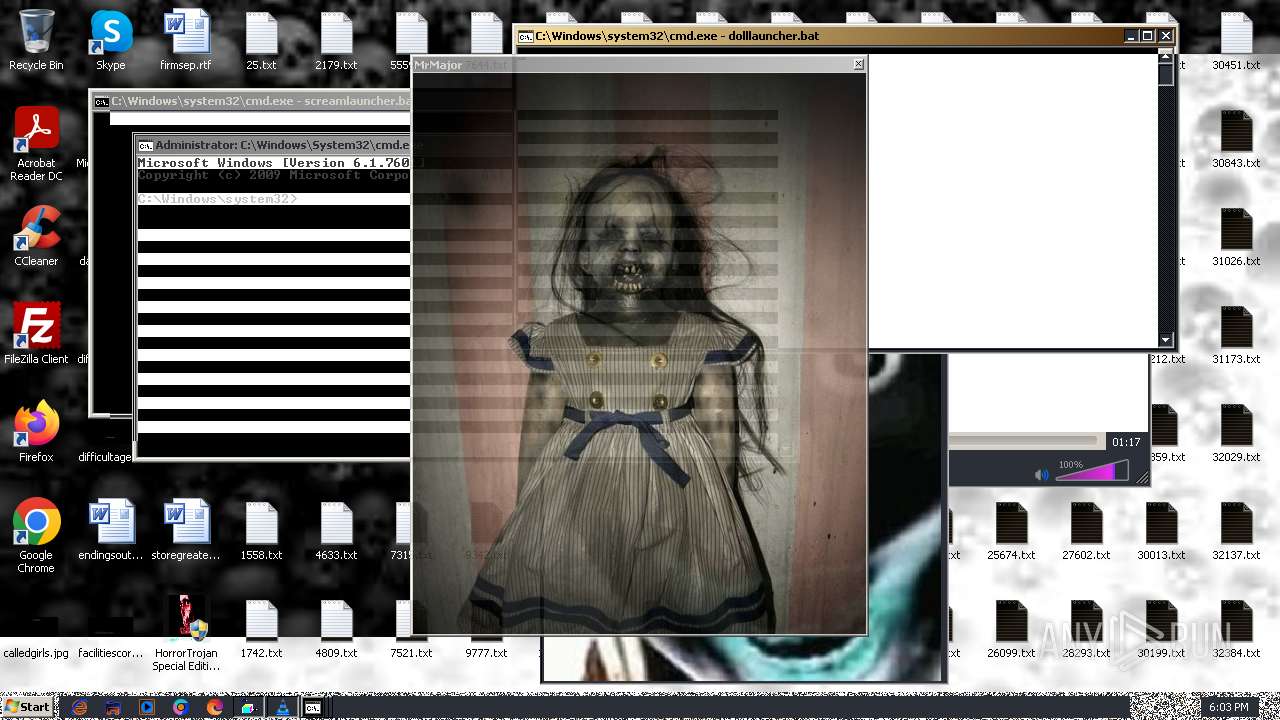
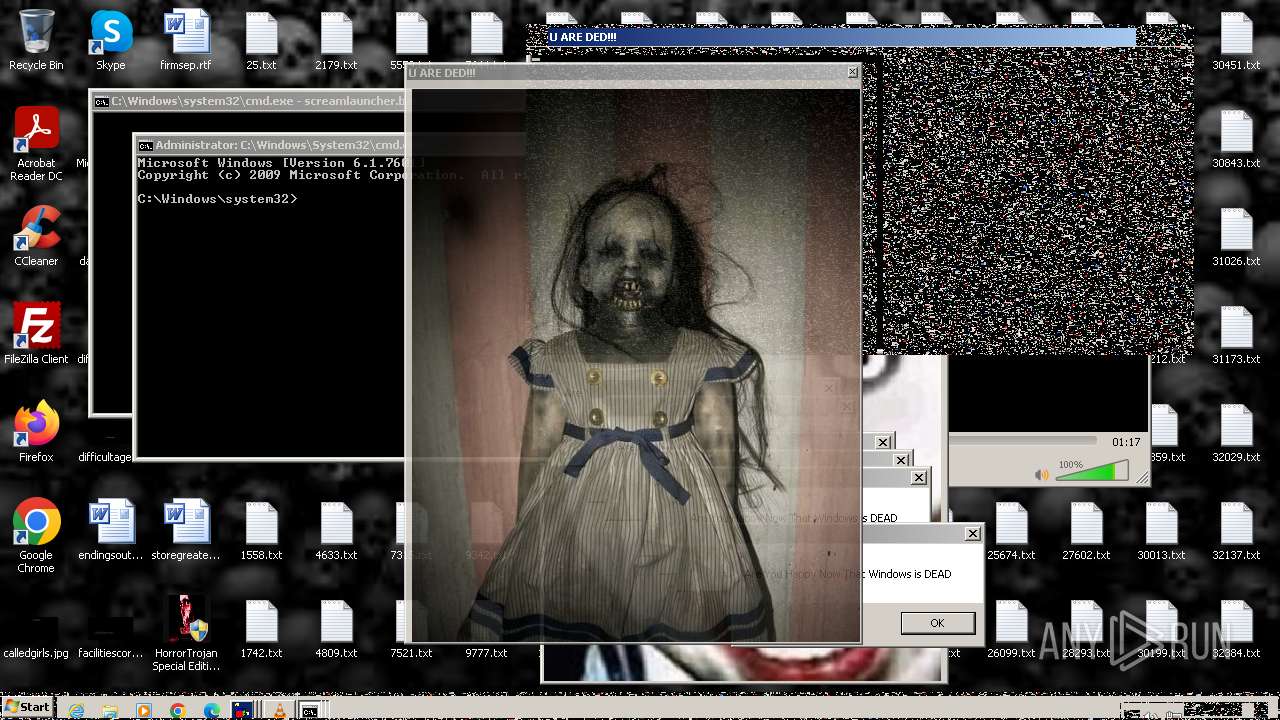
Starts CMD.EXE for commands execution
- HorrorTrojan Special Edition Installer.exe (PID: 3352)
- WinKern64.exe (PID: 2008)
- cmd.exe (PID: 2120)
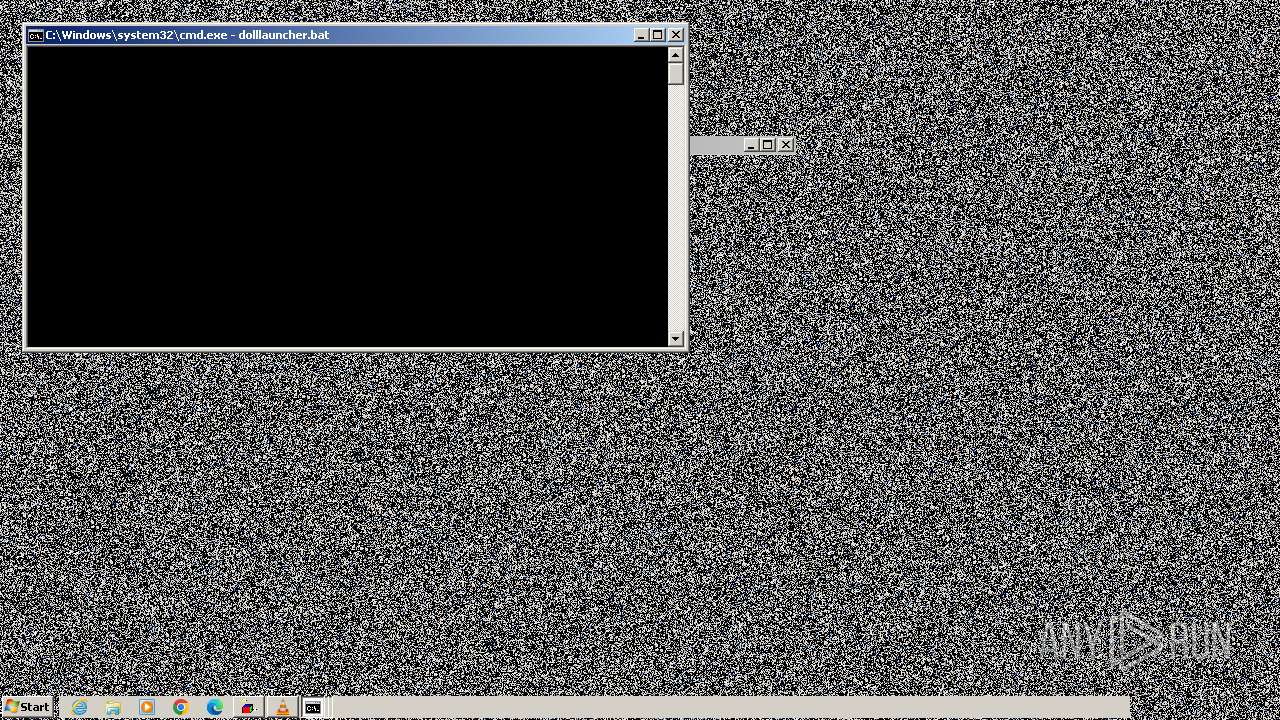
Executing commands from a ".bat" file
- HorrorTrojan Special Edition Installer.exe (PID: 3352)
- WinKern64.exe (PID: 2008)
- cmd.exe (PID: 2120)
Executable content was dropped or overwritten
- HorrorTrojan Special Edition Installer.exe (PID: 3352)
- cmd.exe (PID: 3112)
- WinKern64.exe (PID: 2008)
- cmd.exe (PID: 2120)
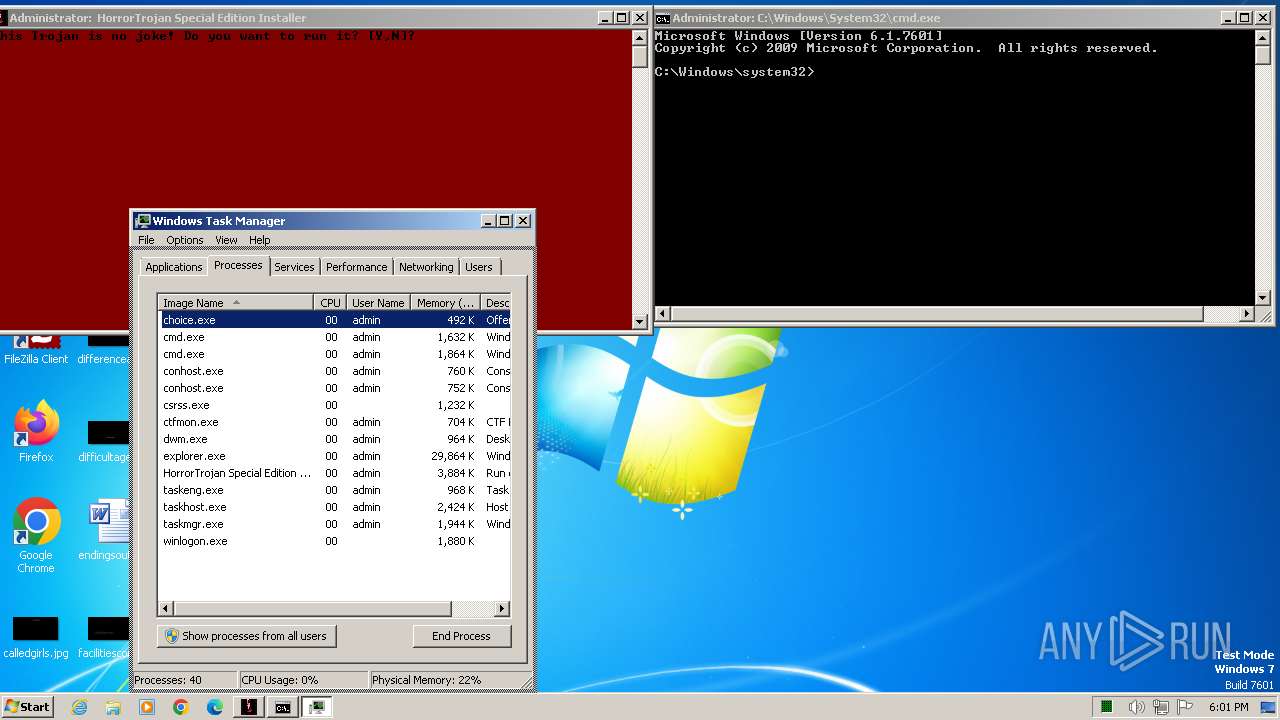
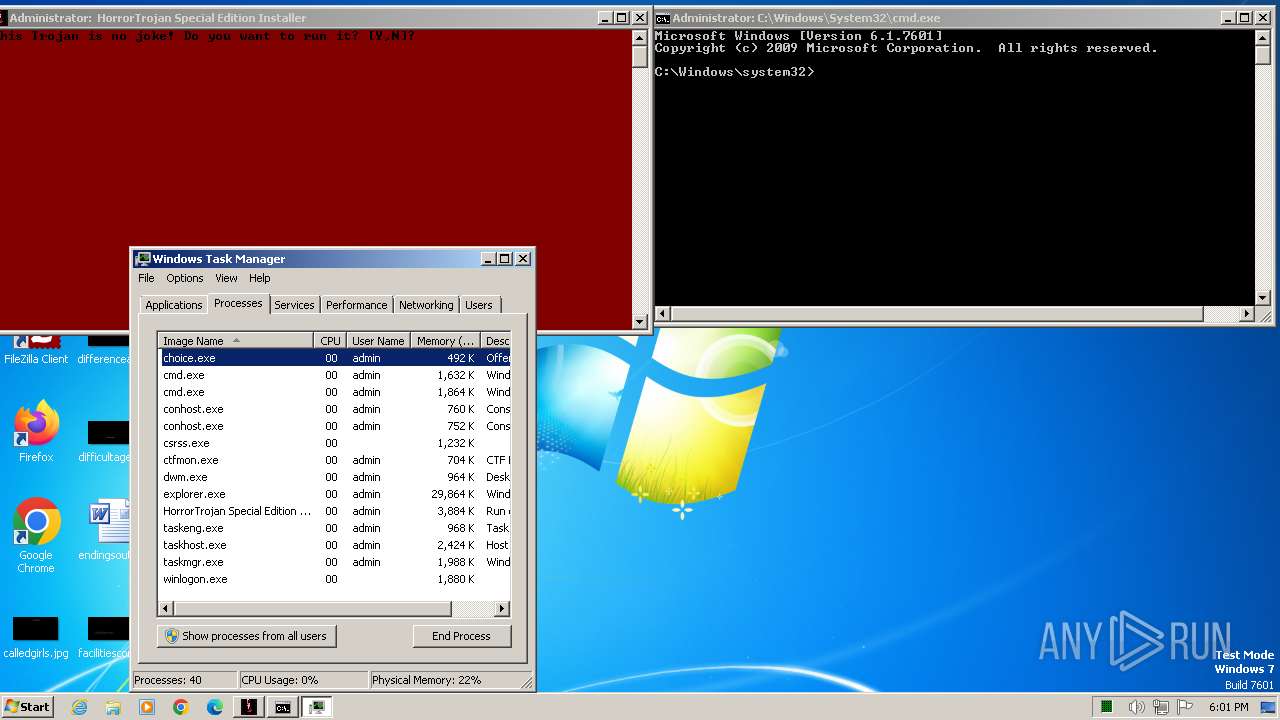
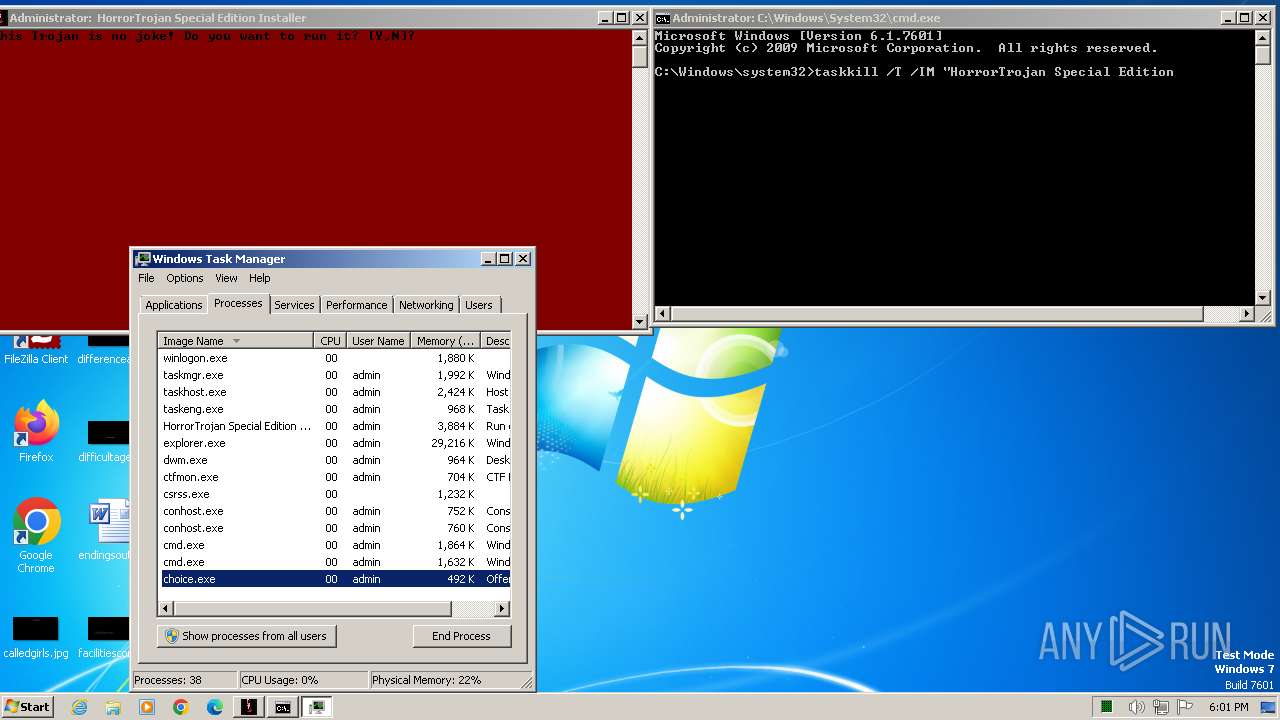
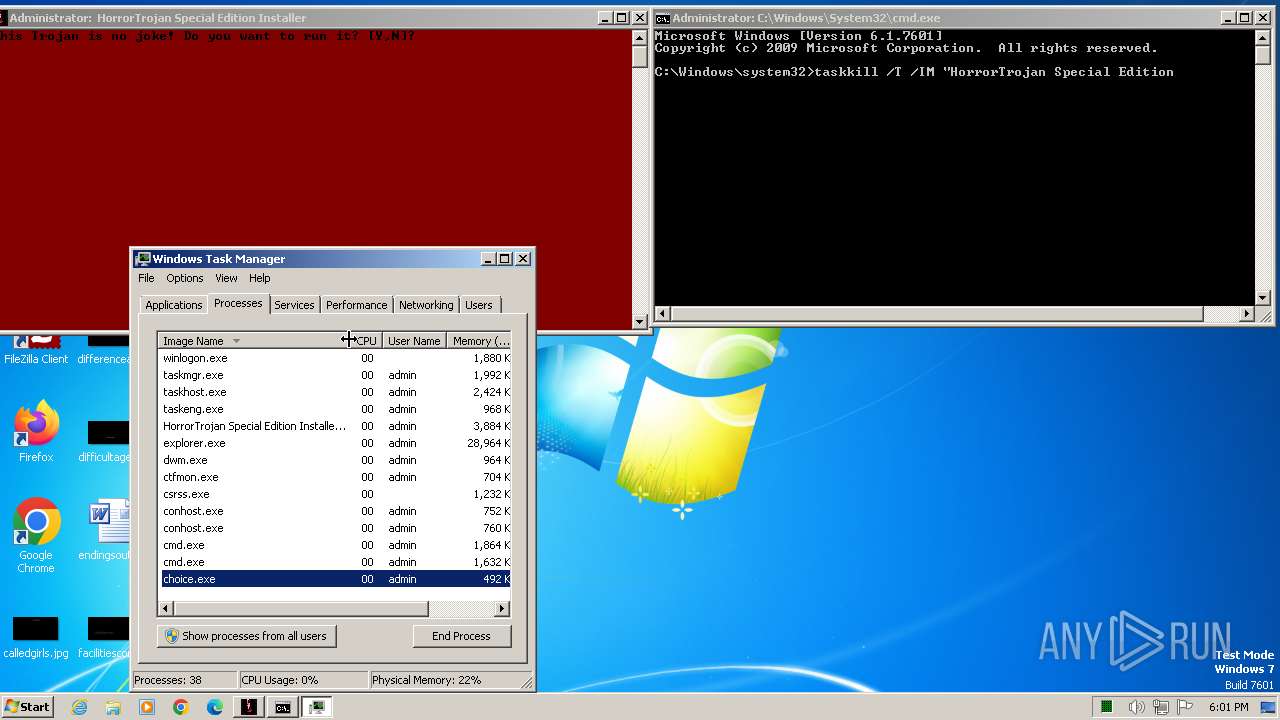
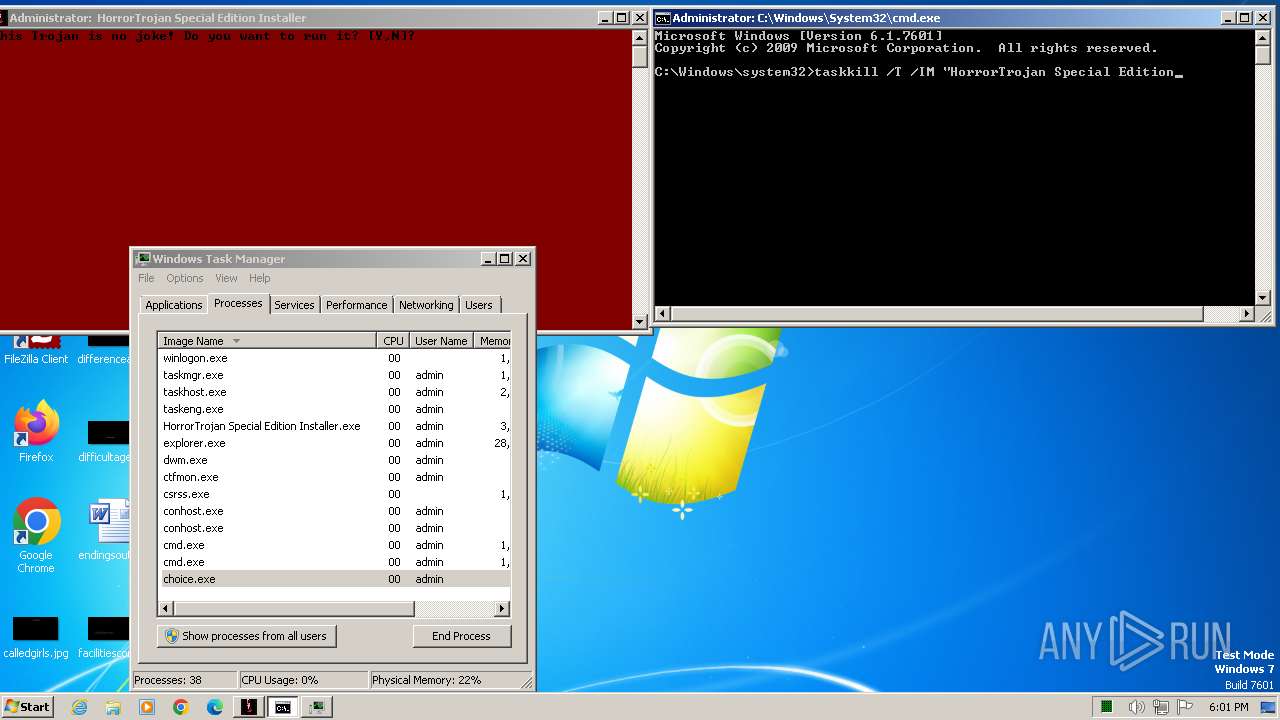
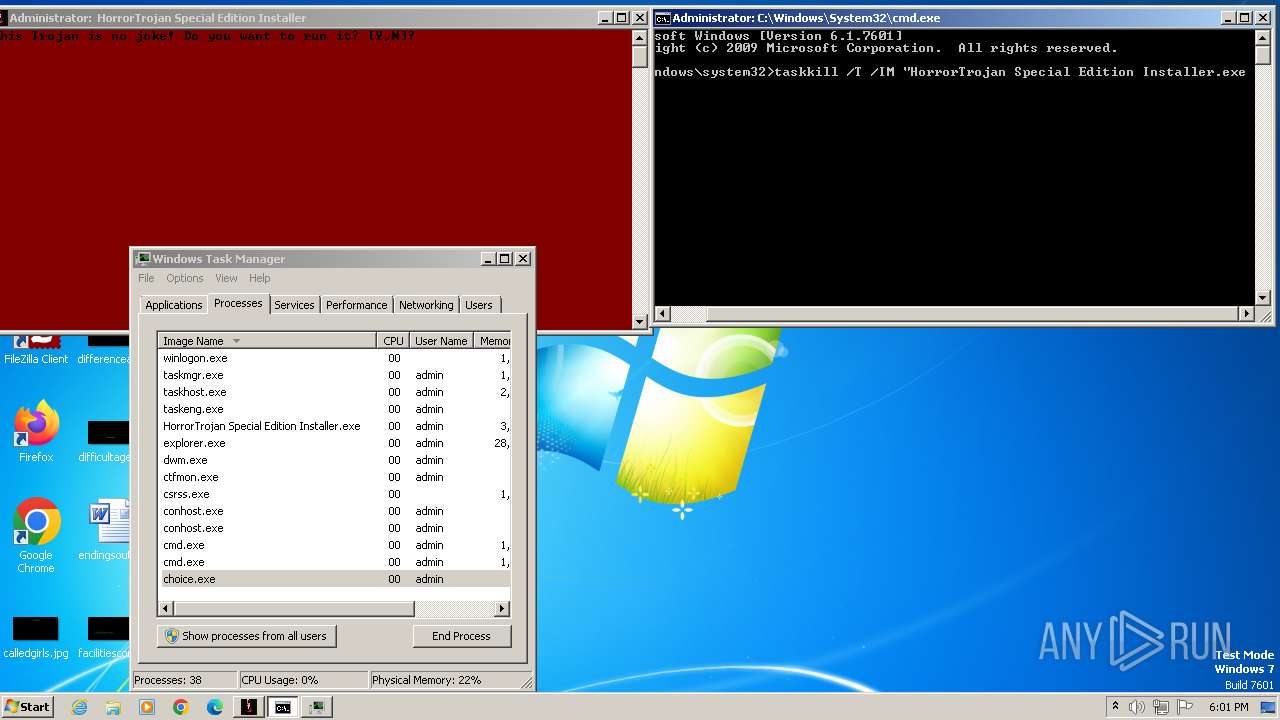
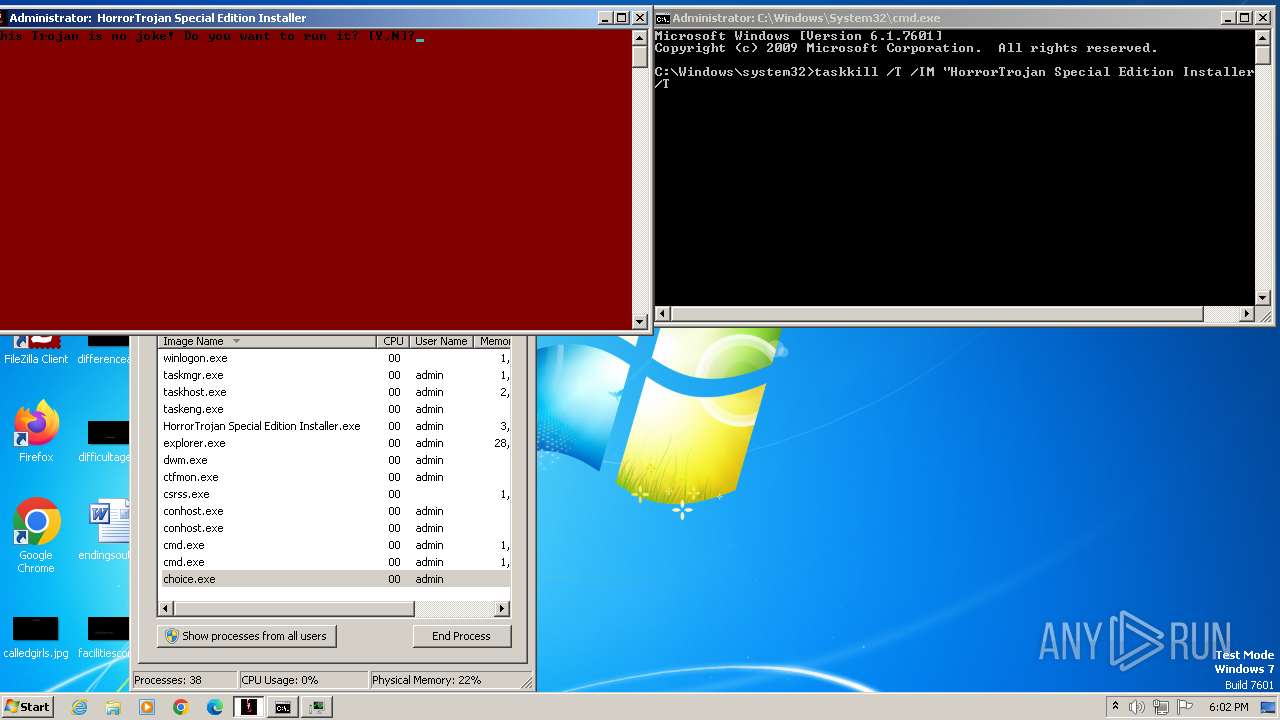
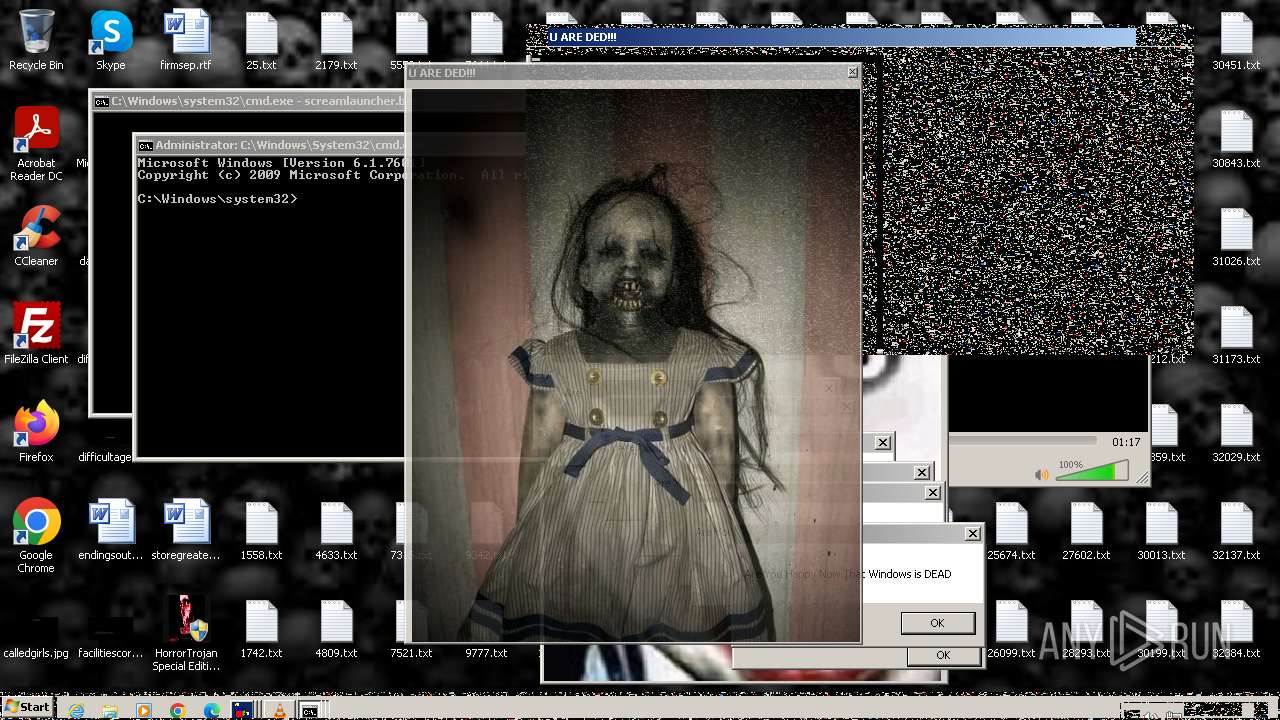
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 1028)
- cmd.exe (PID: 2120)
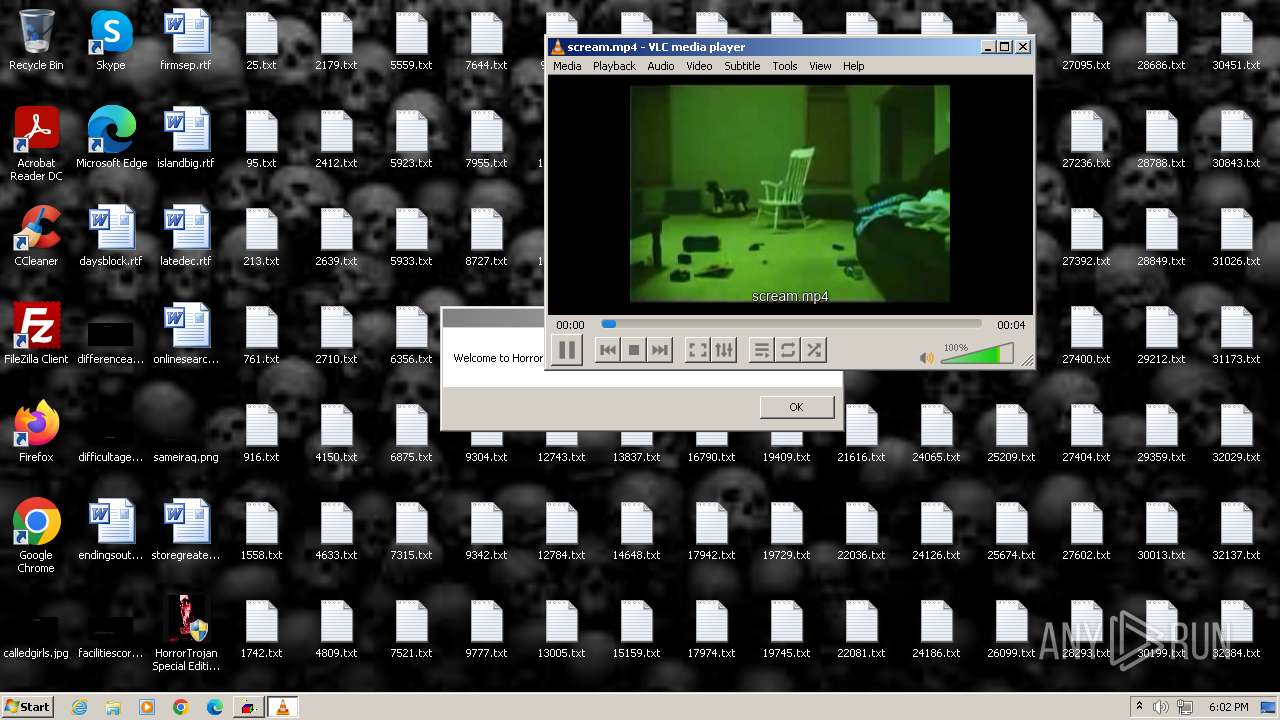
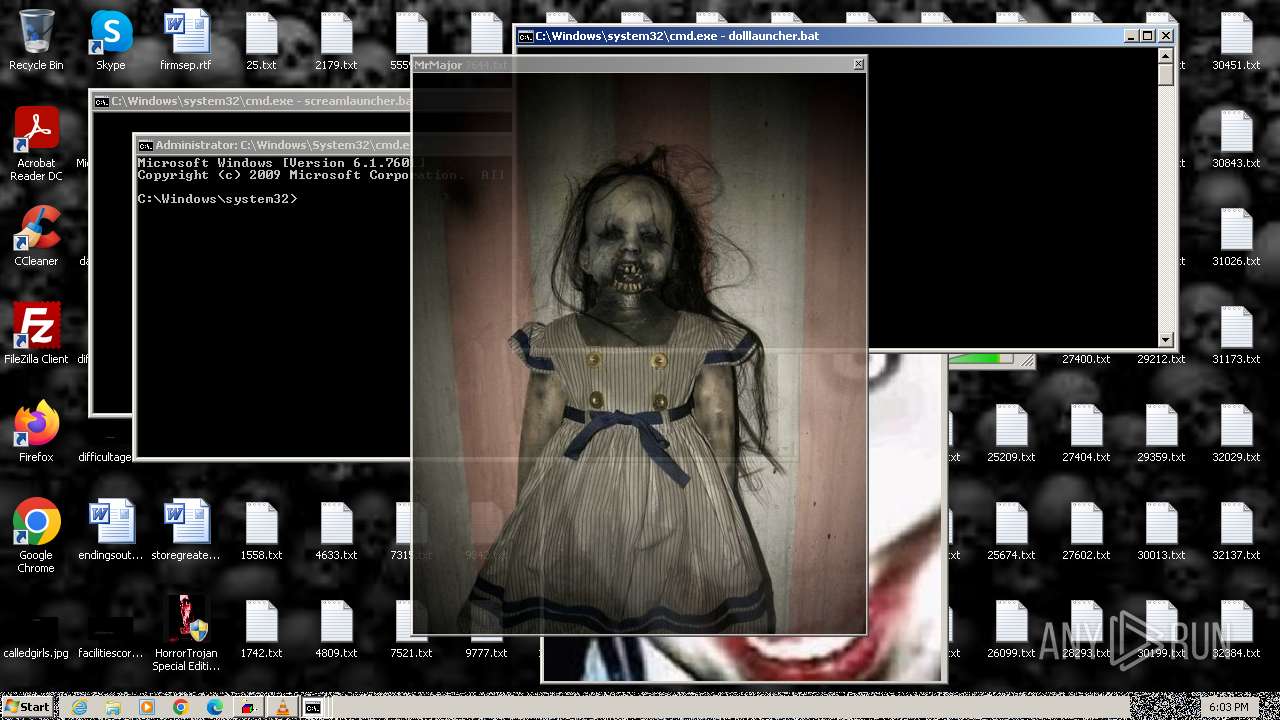
The executable file from the user directory is run by the CMD process
- glitch.exe (PID: 3920)
- scream.exe (PID: 3204)
- scream.exe (PID: 3296)
- scream.exe (PID: 3904)
- scream.exe (PID: 3032)
- scream.exe (PID: 3820)
- scream.exe (PID: 3276)
- scream.exe (PID: 2648)
- scream.exe (PID: 2960)
- scream.exe (PID: 848)
- scream.exe (PID: 3516)
- scream.exe (PID: 3664)
- scream.exe (PID: 3344)
- scream.exe (PID: 2792)
- scream.exe (PID: 3500)
- scream.exe (PID: 1824)
- scream.exe (PID: 2688)
- scream.exe (PID: 3164)
- scream.exe (PID: 1496)
- scream.exe (PID: 2848)
- scream.exe (PID: 2208)
- MbrKiller.exe (PID: 2300)
- glitch.exe (PID: 3112)
- INV.exe (PID: 3792)
- lines.exe (PID: 3884)
- melter.exe (PID: 3728)
- glitch.exe (PID: 3892)
- melter.exe (PID: 3932)
- urded.exe (PID: 2316)
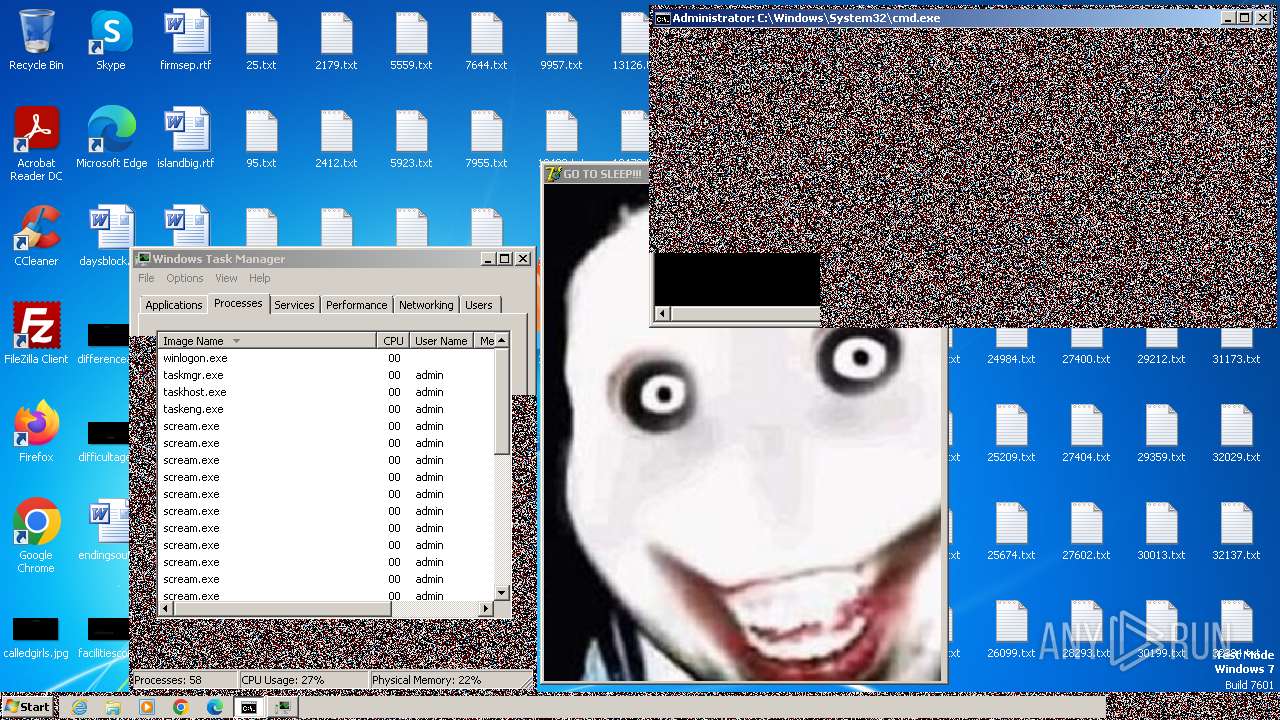
Uses TIMEOUT.EXE to delay execution
- cmd.exe (PID: 3112)
- cmd.exe (PID: 2120)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 3112)
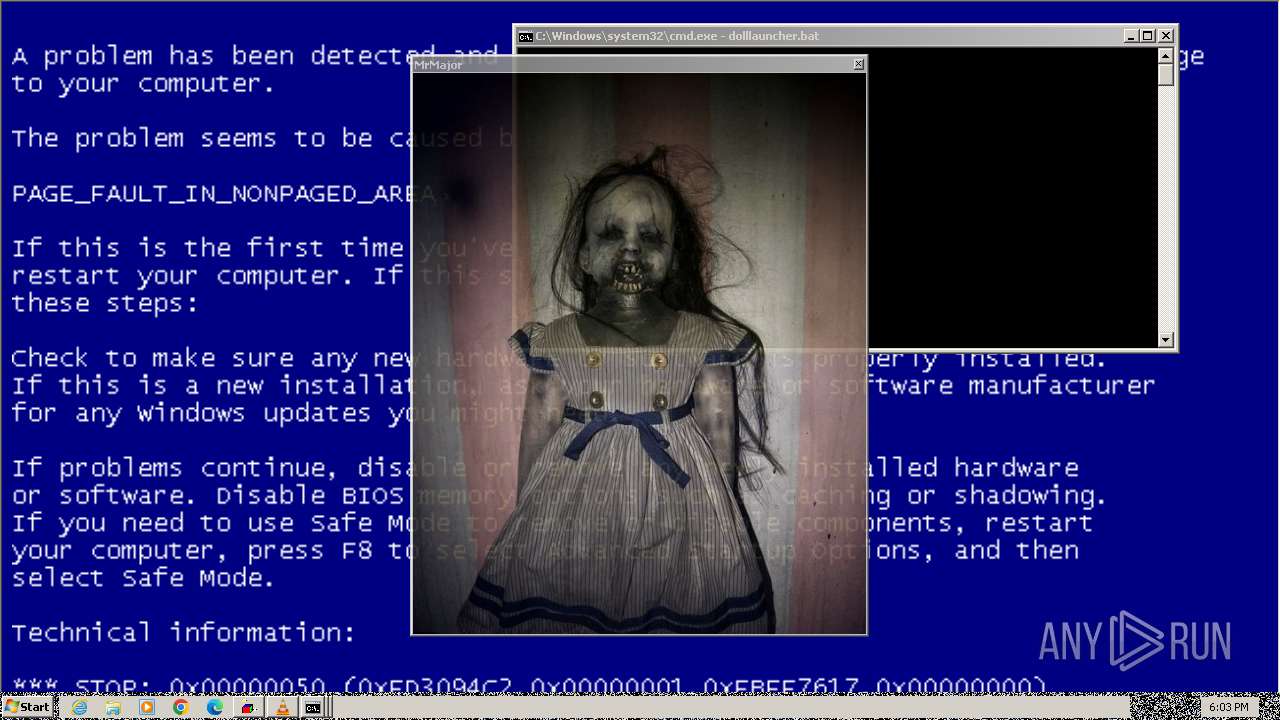
The system shut down or reboot
- cmd.exe (PID: 3112)
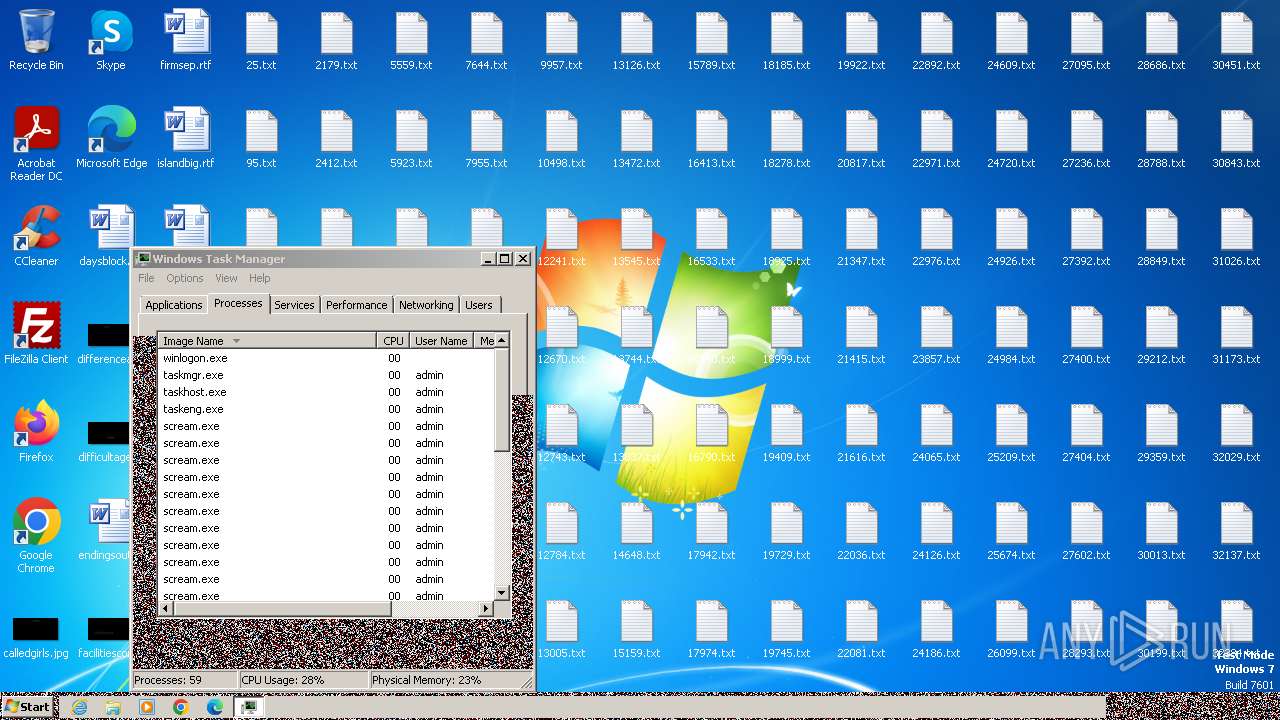
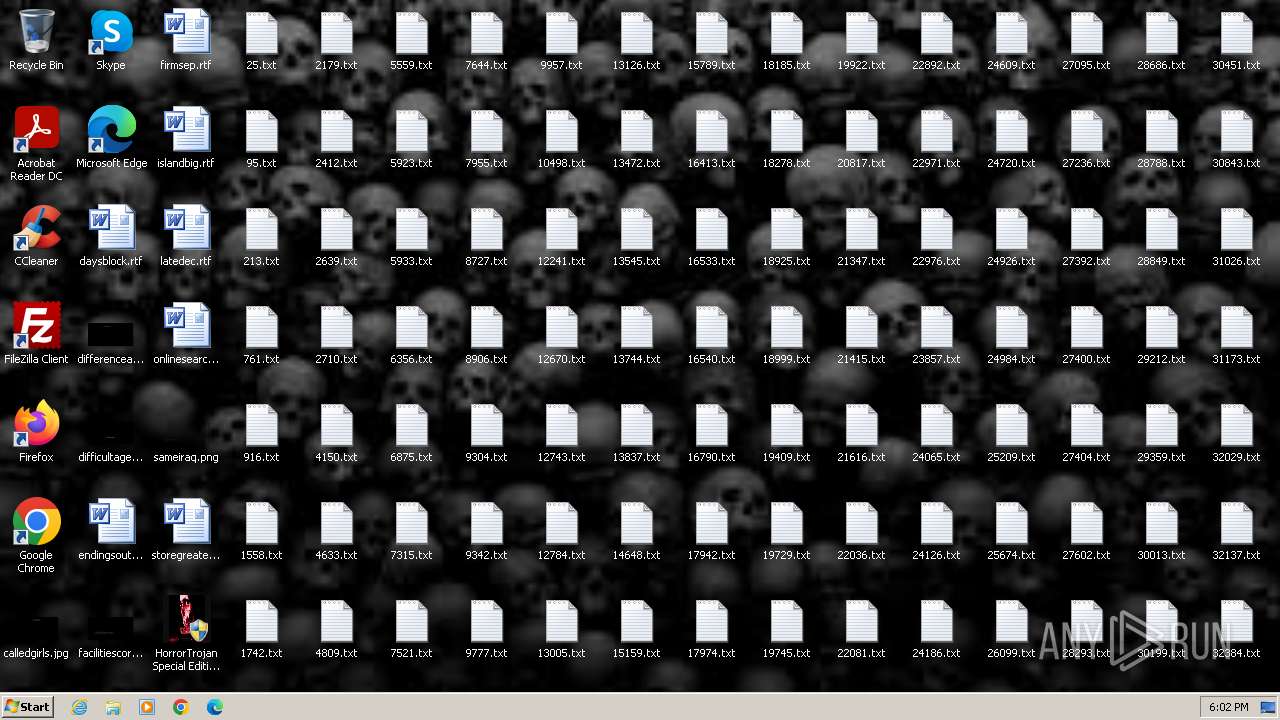
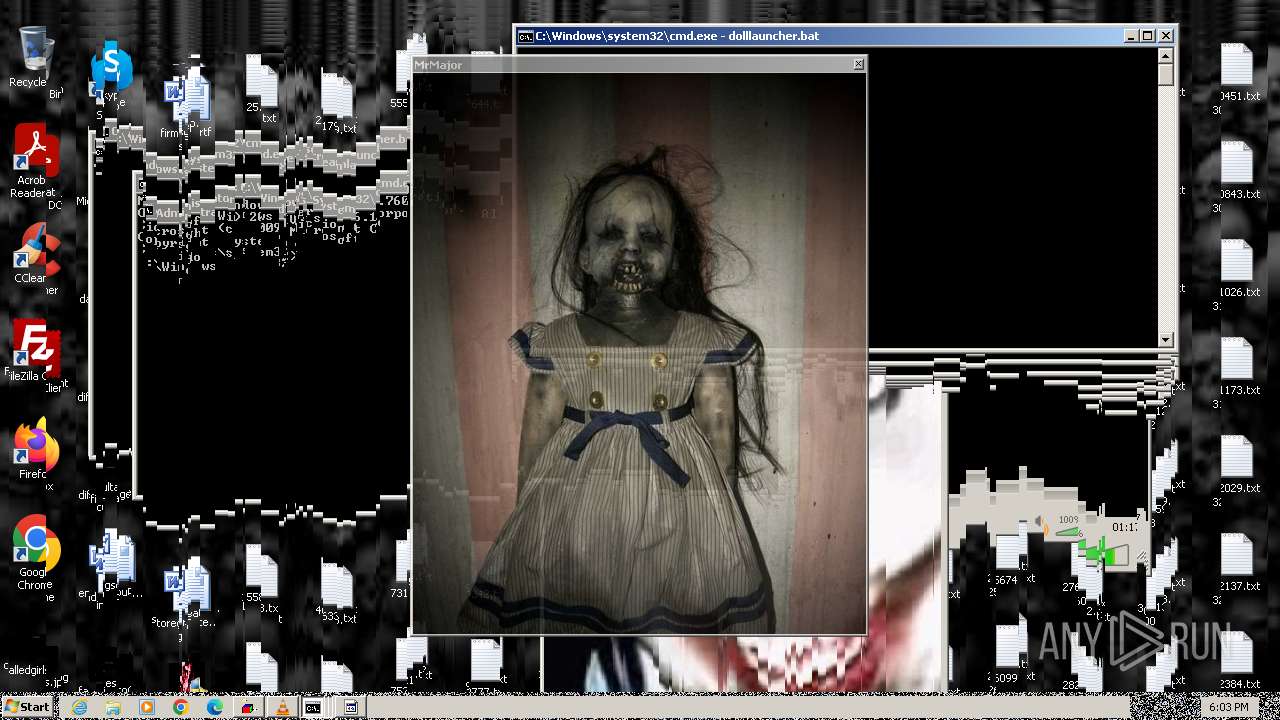
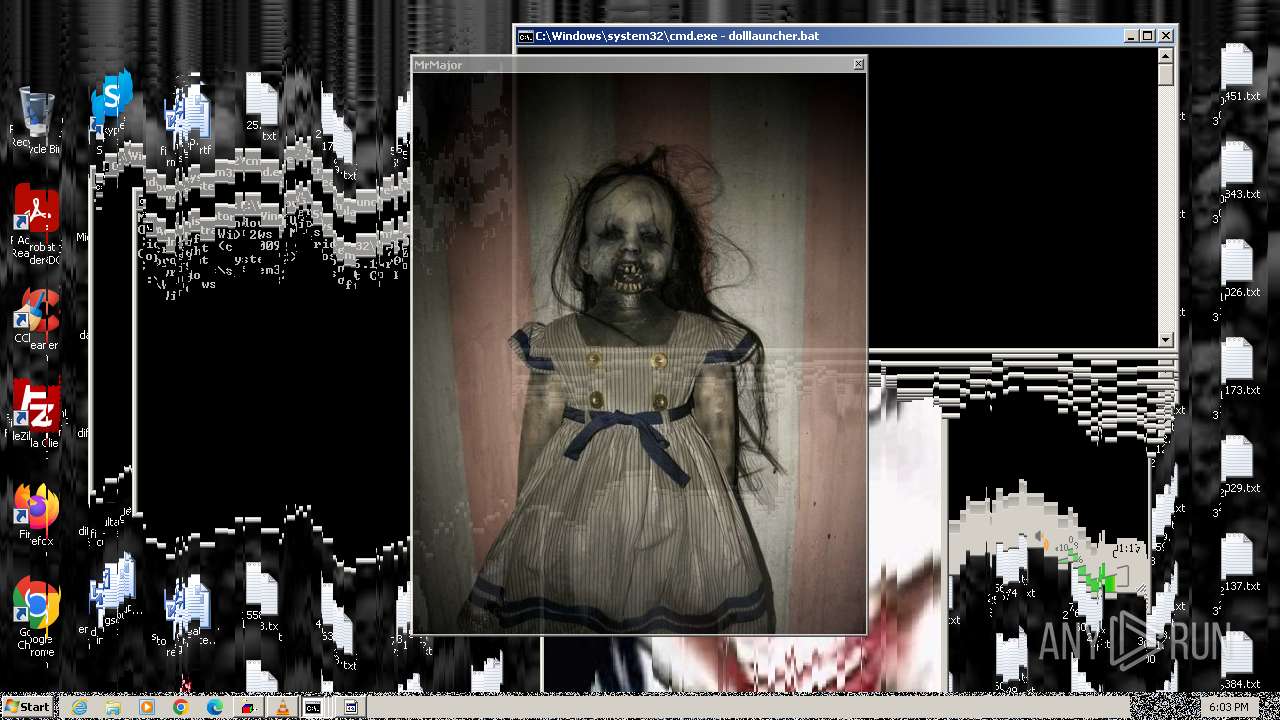
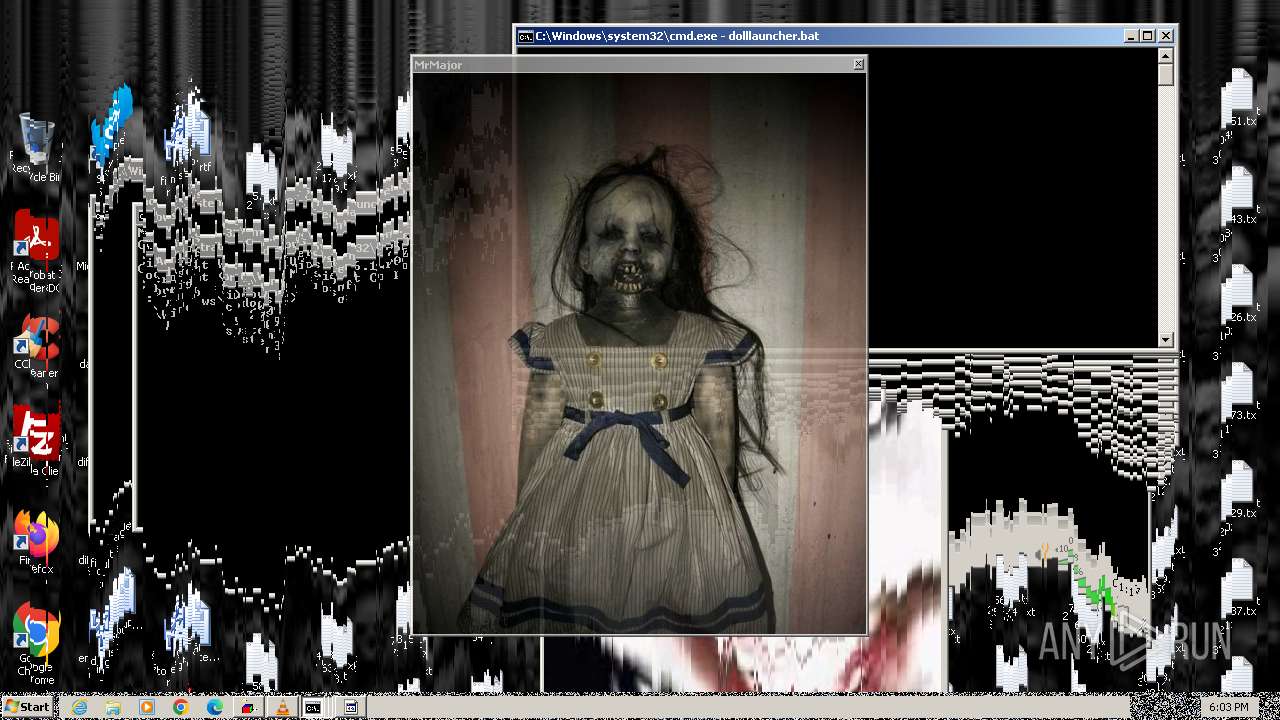
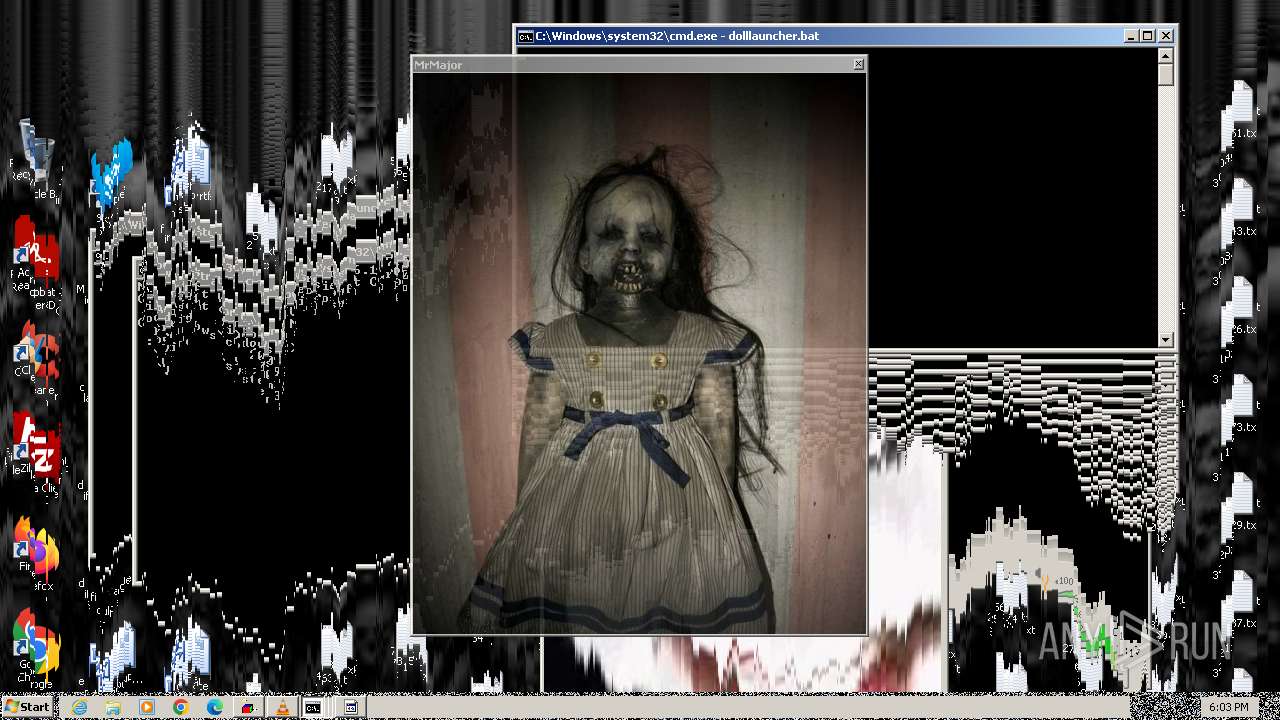
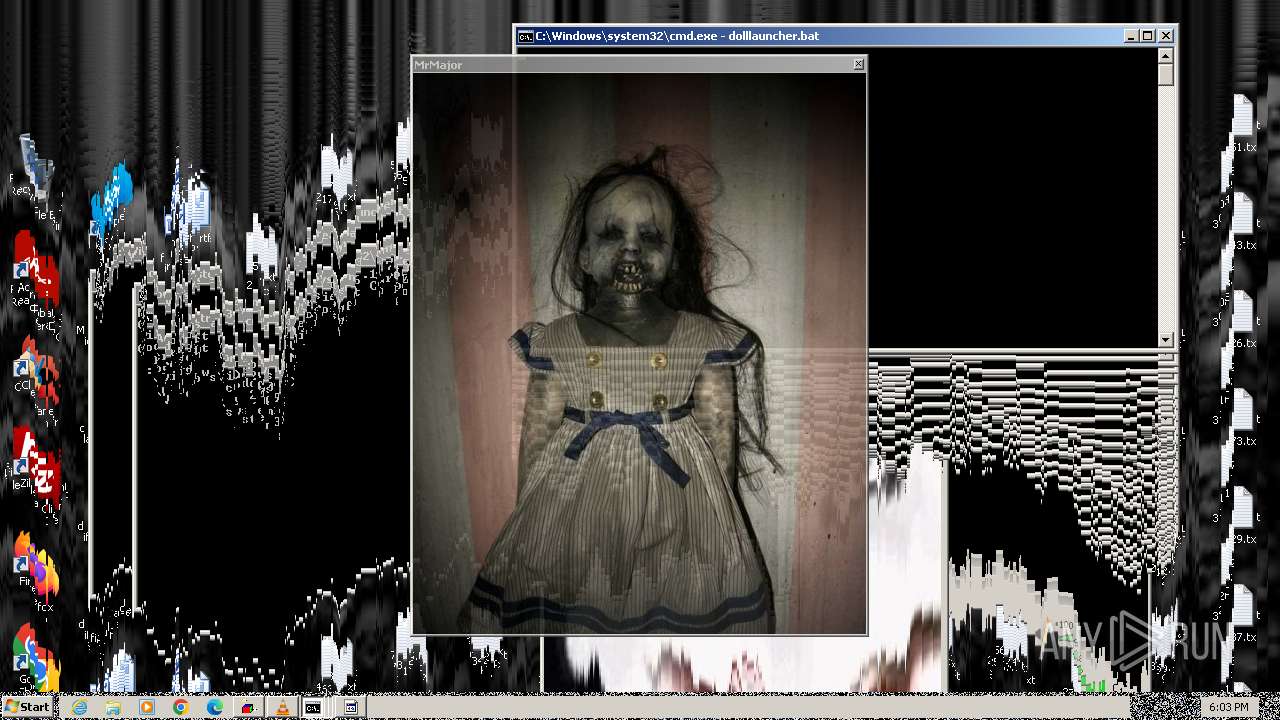
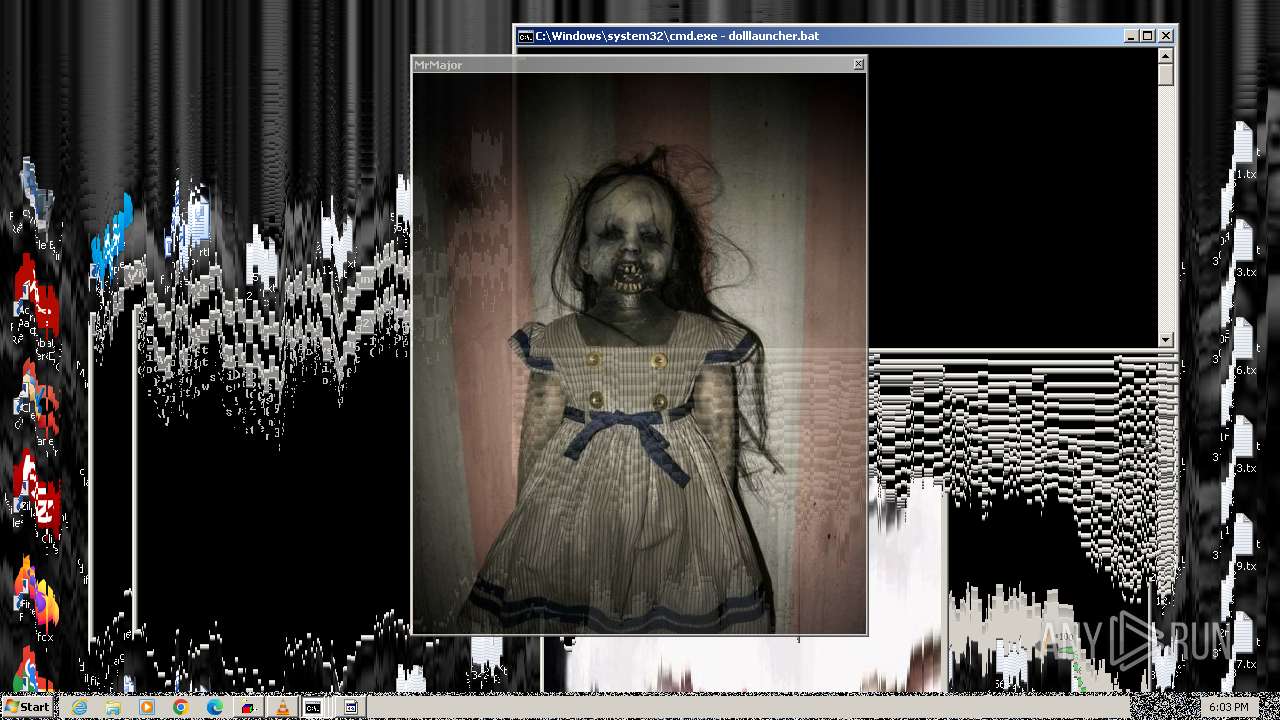
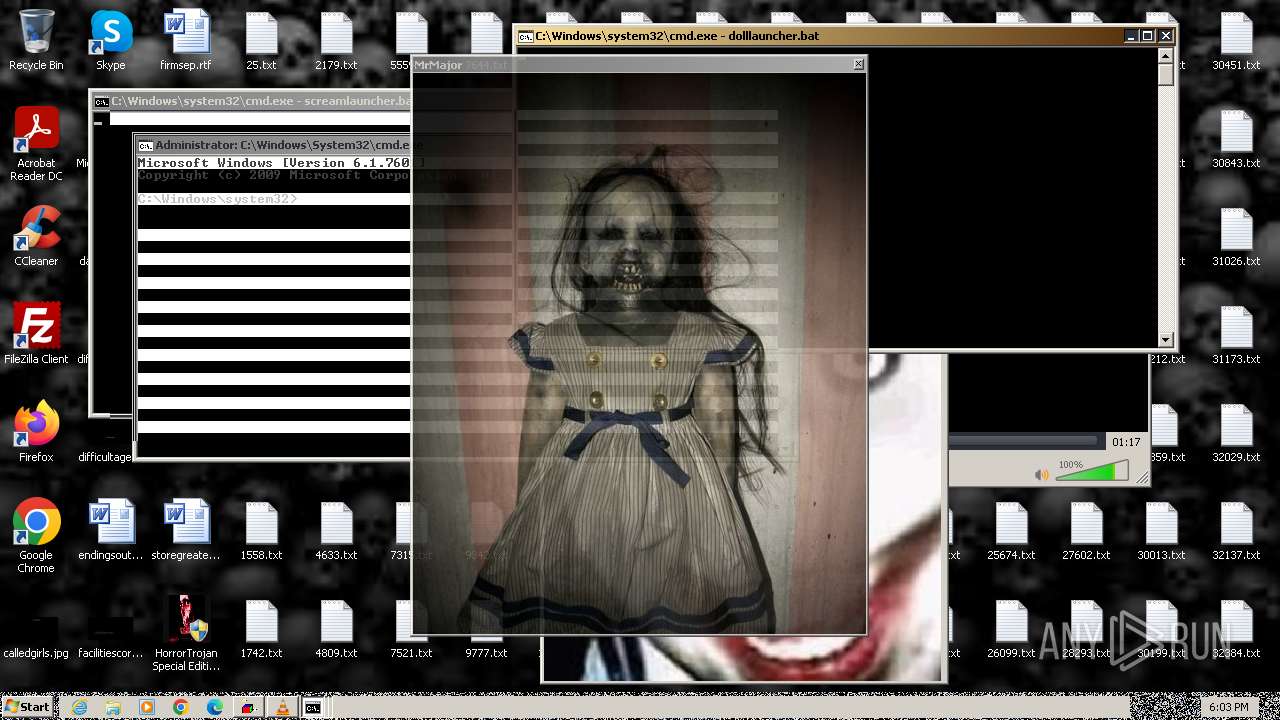
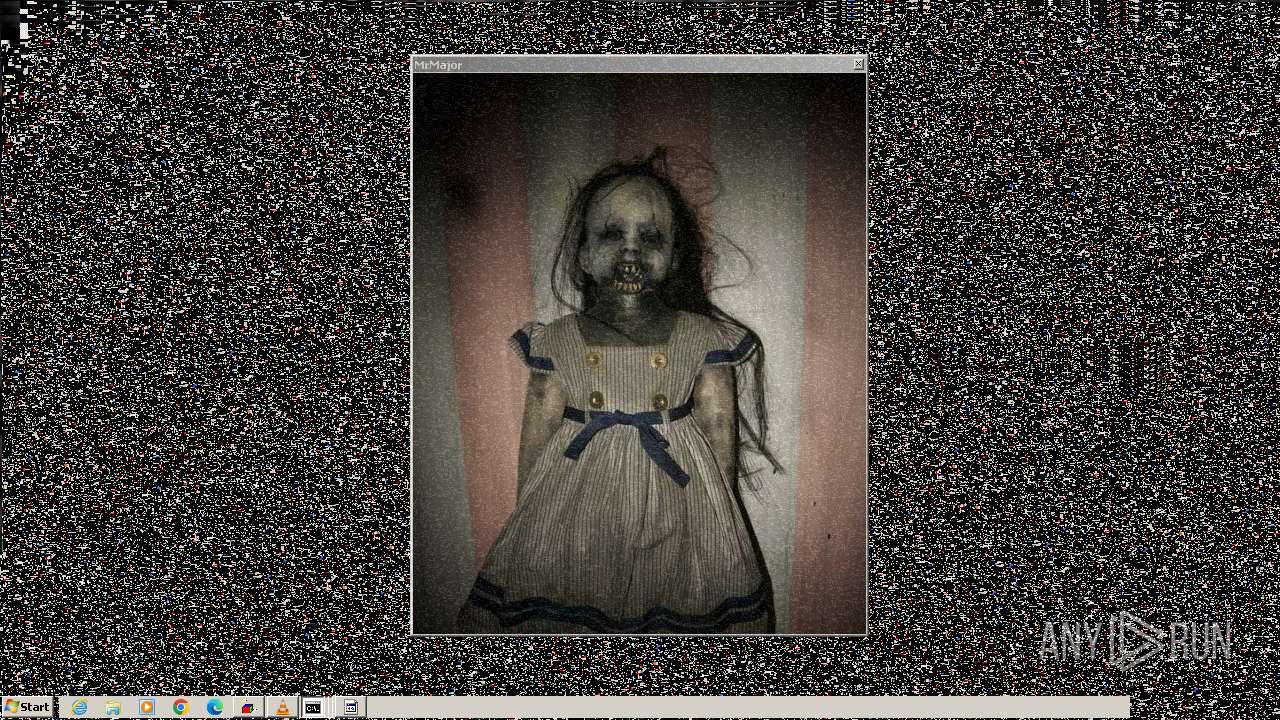
Changes the desktop background image
- reg.exe (PID: 2296)
Reads the Internet Settings
- sipnotify.exe (PID: 1444)
- WinKern64.exe (PID: 2008)
- cmd.exe (PID: 2120)
- mshta.exe (PID: 3300)
The process executes via Task Scheduler
- ctfmon.exe (PID: 1680)
- sipnotify.exe (PID: 1444)
Reads settings of System Certificates
- sipnotify.exe (PID: 1444)
Probably fake Windows Update
- schtasks.exe (PID: 2316)
Reads security settings of Internet Explorer
- WinKern64.exe (PID: 2008)
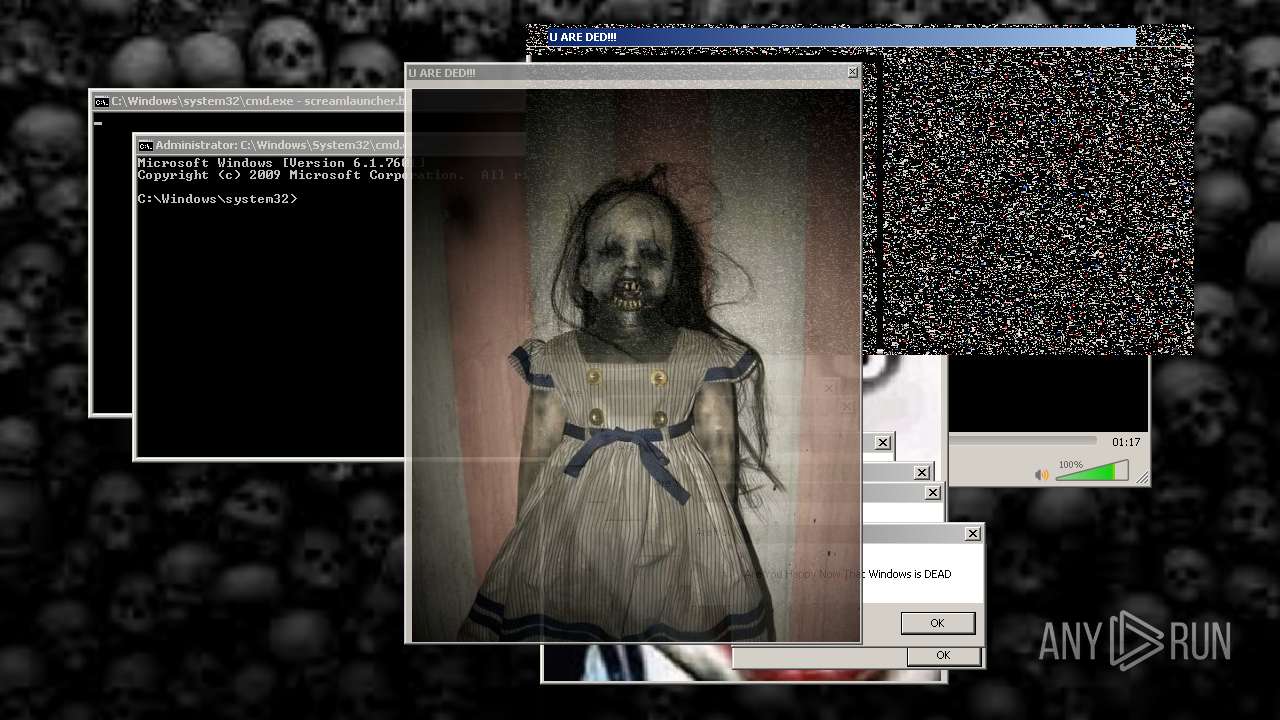
The process executes VB scripts
- cmd.exe (PID: 2120)
Application launched itself
- cmd.exe (PID: 2120)
INFO
Checks supported languages
- HorrorTrojan Special Edition Installer.exe (PID: 3352)
- scream.exe (PID: 3904)
- scream.exe (PID: 3204)
- scream.exe (PID: 3820)
- glitch.exe (PID: 3920)
- scream.exe (PID: 3664)
- scream.exe (PID: 3276)
- scream.exe (PID: 2960)
- scream.exe (PID: 848)
- scream.exe (PID: 2648)
- scream.exe (PID: 3516)
- scream.exe (PID: 3296)
- scream.exe (PID: 3032)
- scream.exe (PID: 3344)
- scream.exe (PID: 2208)
- scream.exe (PID: 2688)
- scream.exe (PID: 1824)
- scream.exe (PID: 3164)
- scream.exe (PID: 3500)
- scream.exe (PID: 2848)
- scream.exe (PID: 1496)
- scream.exe (PID: 2792)
- IMEKLMG.EXE (PID: 1692)
- IMEKLMG.EXE (PID: 1640)
- MbrKiller.exe (PID: 2300)
- WinKern64.exe (PID: 2008)
- vlc.exe (PID: 2412)
- wmpnscfg.exe (PID: 2524)
- vlc.exe (PID: 2848)
- scream.exe (PID: 2892)
- wmpnscfg.exe (PID: 2568)
- glitch.exe (PID: 3112)
- doll.exe (PID: 3264)
- INV.exe (PID: 3792)
- vlc.exe (PID: 3460)
- vlc.exe (PID: 3620)
- melter.exe (PID: 3728)
- lines.exe (PID: 3884)
- glitch.exe (PID: 3892)
- melter.exe (PID: 3932)
- urded.exe (PID: 2316)
Create files in a temporary directory
- HorrorTrojan Special Edition Installer.exe (PID: 3352)
- WinKern64.exe (PID: 2008)
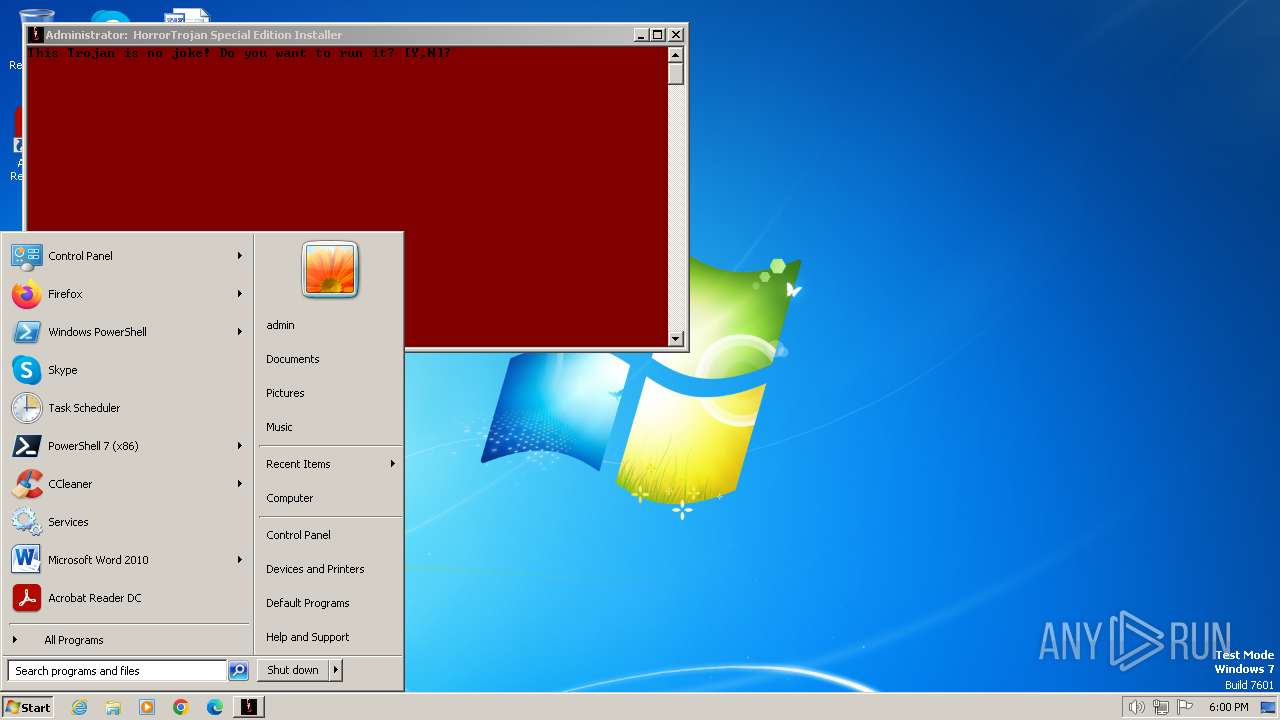
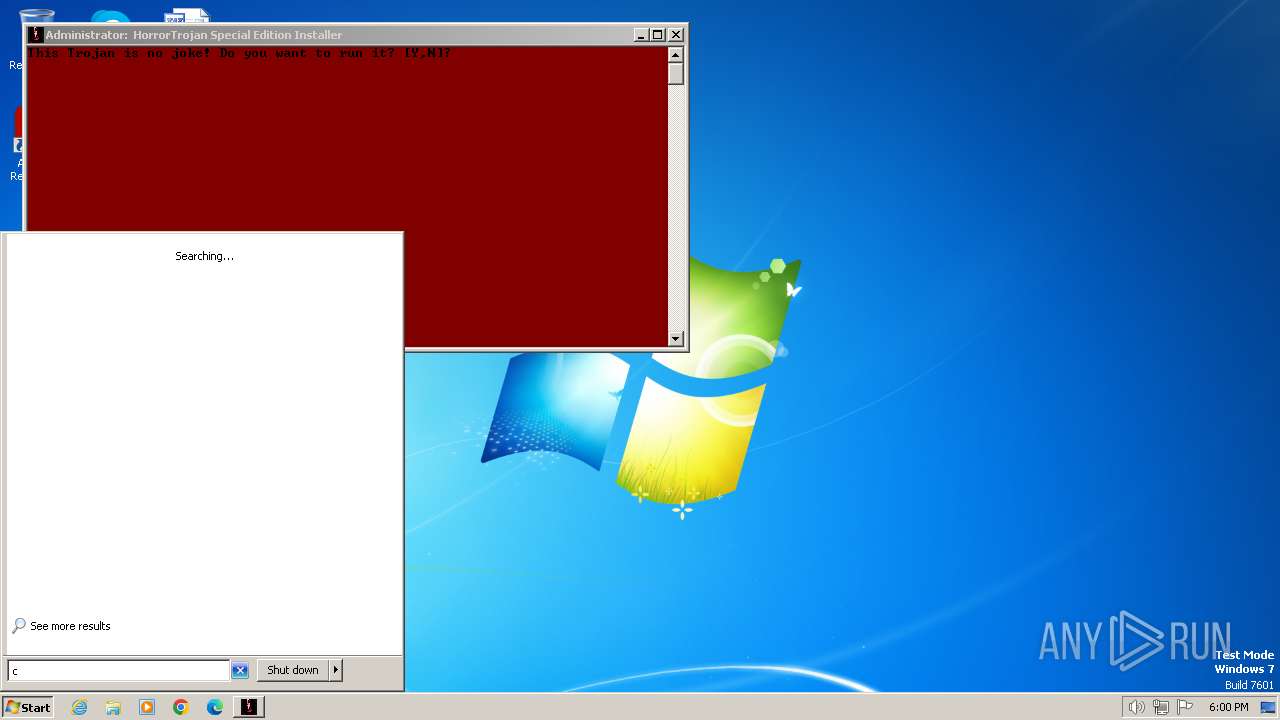
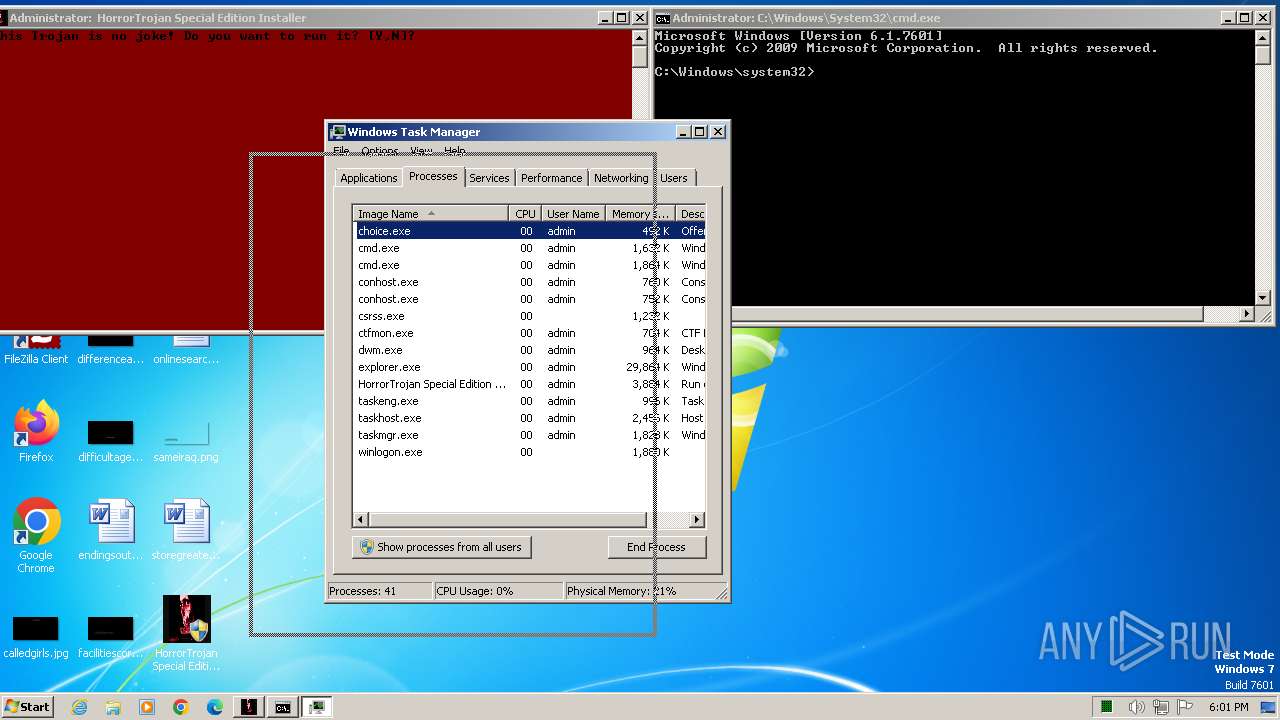
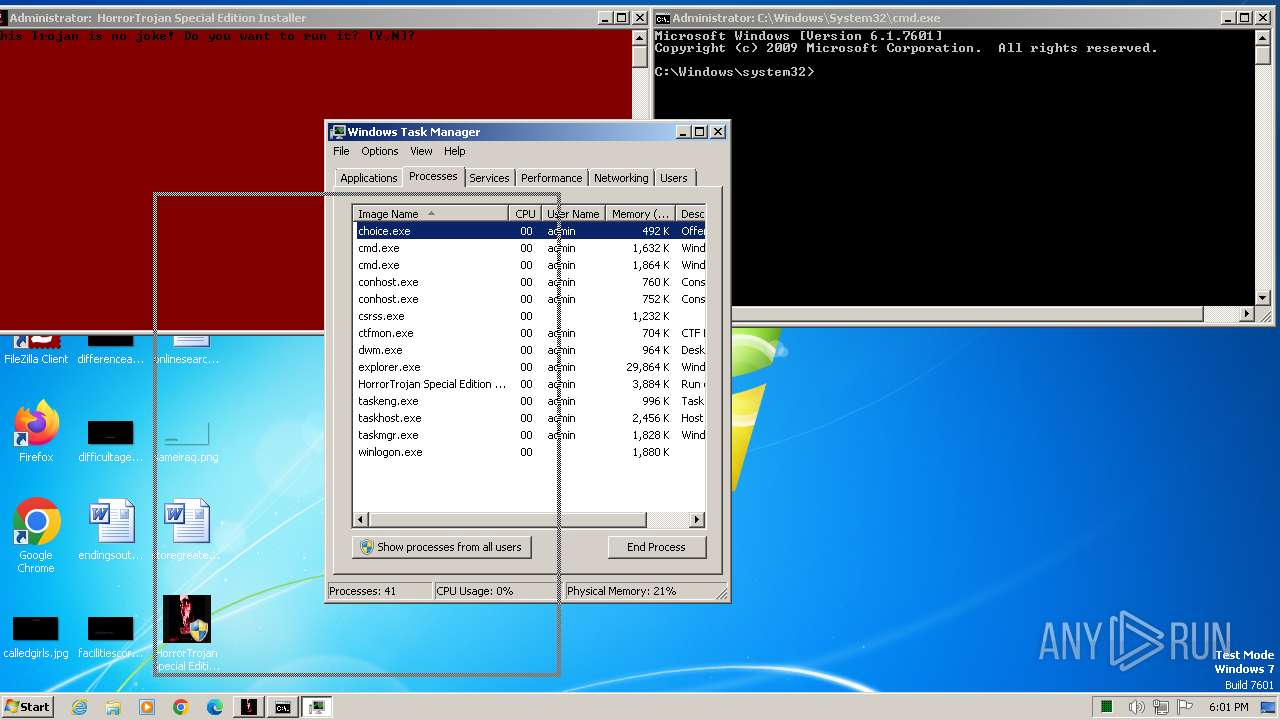
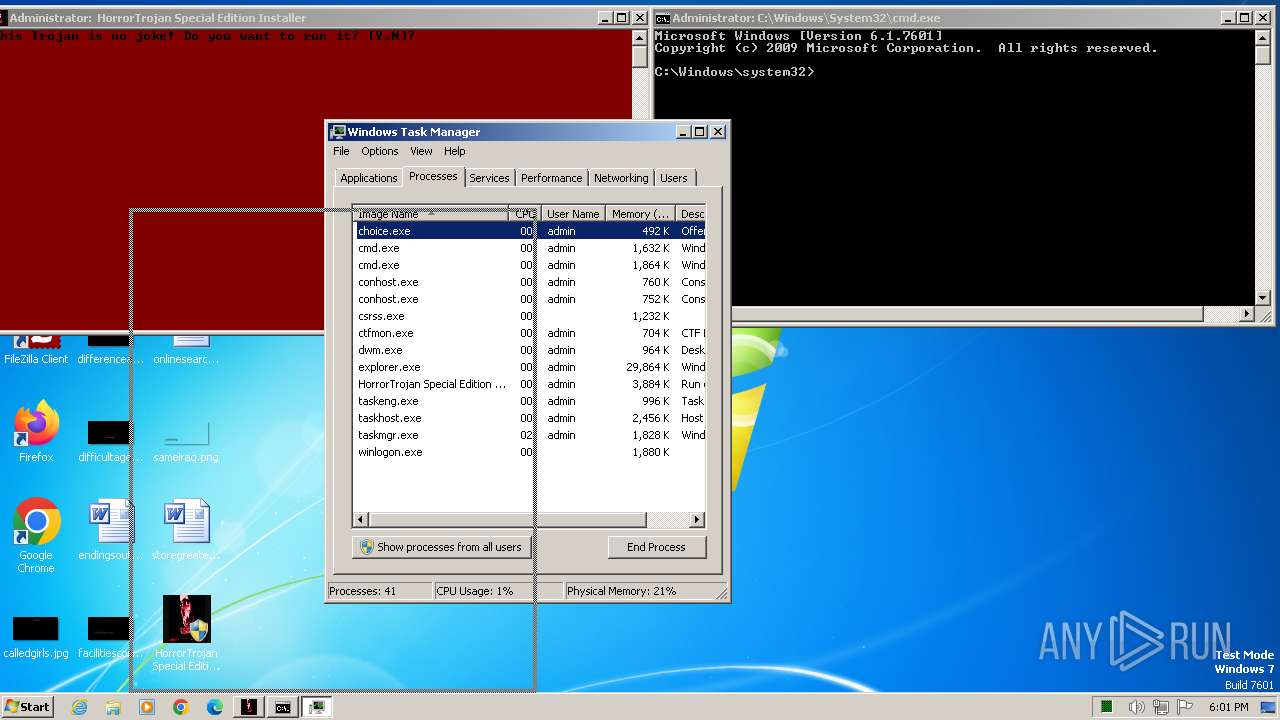
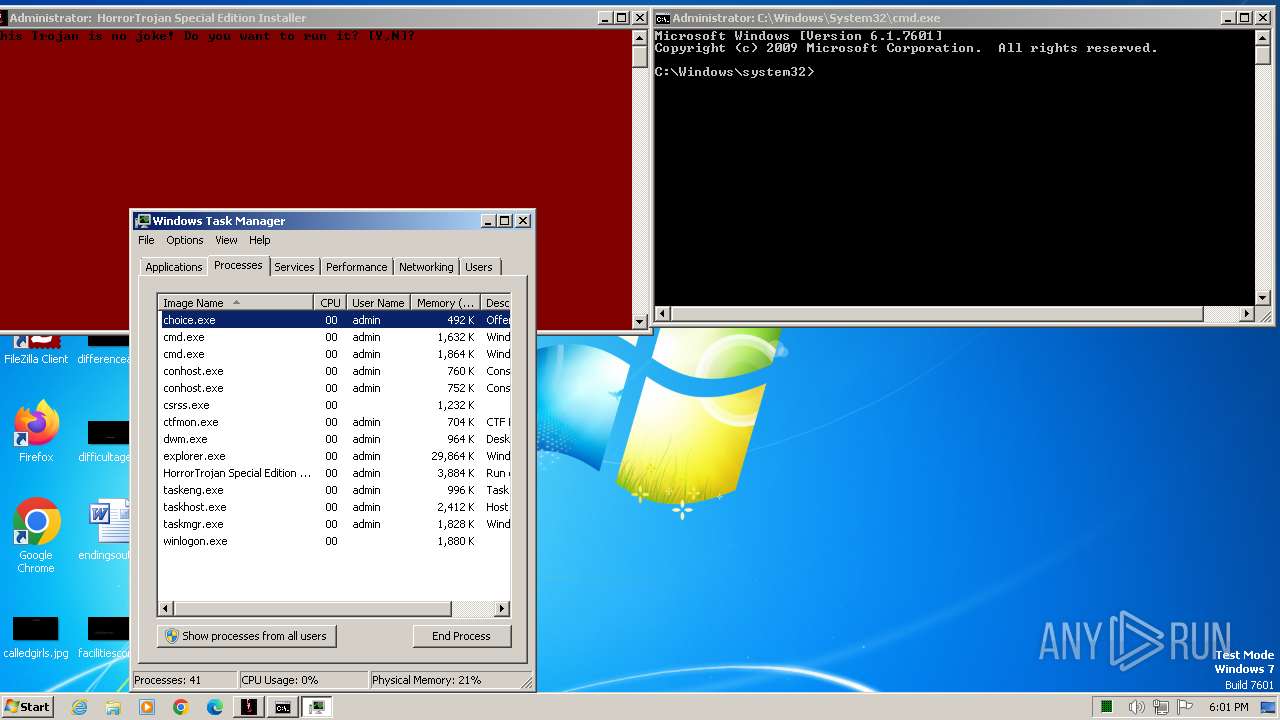
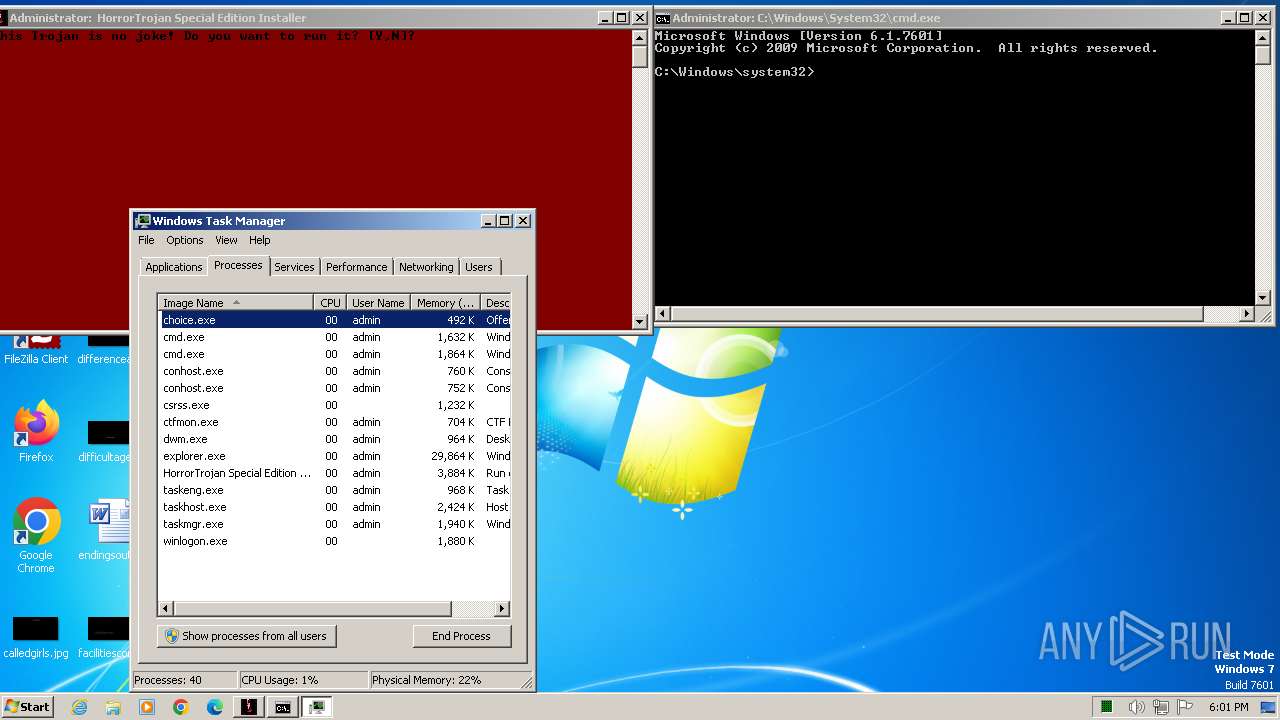
Manual execution by a user
- cmd.exe (PID: 1028)
- taskmgr.exe (PID: 3156)
- IMEKLMG.EXE (PID: 1692)
- WinKern64.exe (PID: 2008)
- IMEKLMG.EXE (PID: 1640)
- wmpnscfg.exe (PID: 2524)
- wmpnscfg.exe (PID: 2568)
- cmd.exe (PID: 3084)
Reads the time zone
- net1.exe (PID: 3868)
Reads the computer name
- IMEKLMG.EXE (PID: 1692)
- IMEKLMG.EXE (PID: 1640)
- WinKern64.exe (PID: 2008)
- wmpnscfg.exe (PID: 2524)
- wmpnscfg.exe (PID: 2568)
- vlc.exe (PID: 2412)
- doll.exe (PID: 3264)
Process checks whether UAC notifications are on
- IMEKLMG.EXE (PID: 1640)
- IMEKLMG.EXE (PID: 1692)
Reads security settings of Internet Explorer
- sipnotify.exe (PID: 1444)
Reads the software policy settings
- sipnotify.exe (PID: 1444)
Reads the machine GUID from the registry
- doll.exe (PID: 3264)
Reads Internet Explorer settings
- mshta.exe (PID: 3300)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | UPX compressed Win32 Executable (39.3) |
|---|---|---|
| .exe | | | Win32 EXE Yoda's Crypter (38.6) |
| .dll | | | Win32 Dynamic Link Library (generic) (9.5) |
| .exe | | | Win32 Executable (generic) (6.5) |
| .exe | | | Generic Win/DOS Executable (2.9) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2010:11:08 13:12:00+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 2.5 |
| CodeSize: | 2342912 |
| InitializedDataSize: | 155648 |
| UninitializedDataSize: | 733184 |
| EntryPoint: | 0x2ee6c0 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows command line |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | Debug, Pre-release, Private build |
| FileOS: | Windows 16-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
| CompanyName: | HorrorTrojans |
| FileDescription: | Run only on VM |
| FileVersion: | 1,0,0,0 |
| ProductName: | HorrorTrojan Special Edition |
| InternalName: | Trojan |
| ProductVersion: | 1,0,0,0 |
| LegalCopyright: | 2021 |
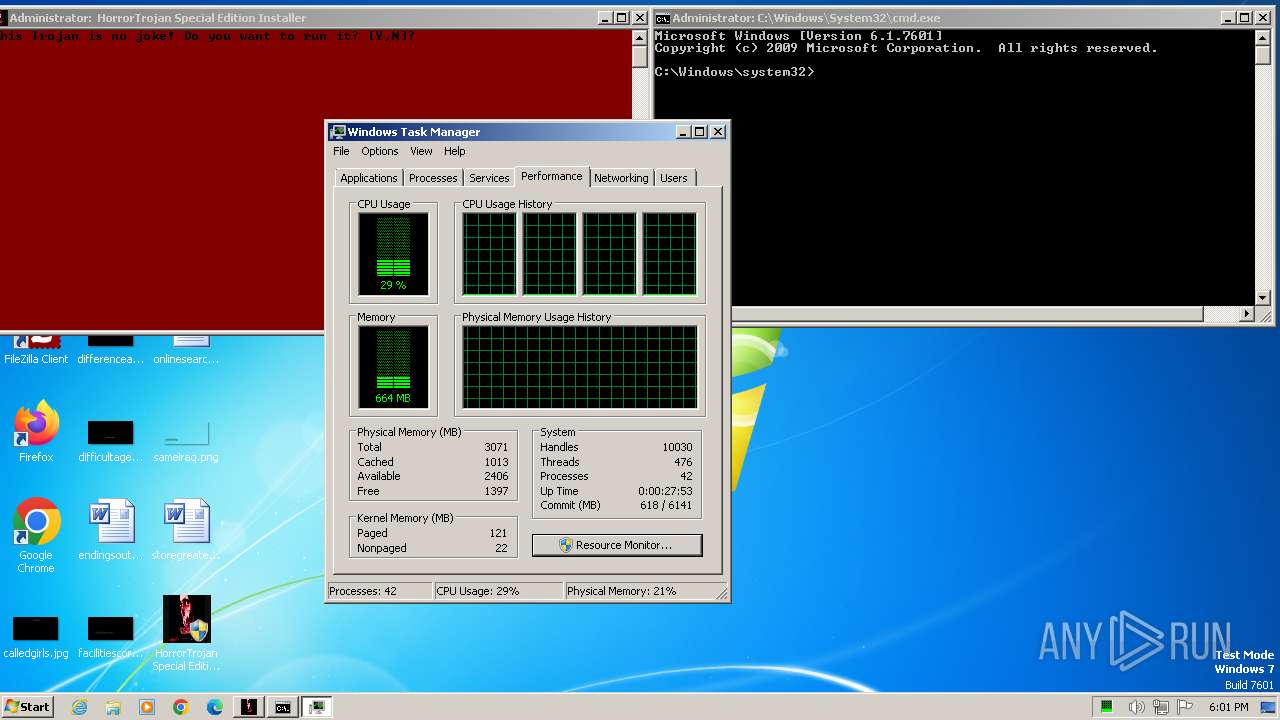
Total processes
208
Monitored processes
105
Malicious processes
5
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 284 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\AppData\Local\Temp\24BE.tmp\dead.vbs" | C:\Windows\System32\wscript.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft ® Windows Based Script Host Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 360 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\AppData\Local\Temp\24BE.tmp\dead.vbs" | C:\Windows\System32\wscript.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft ® Windows Based Script Host Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 764 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\AppData\Local\Temp\24BE.tmp\dead.vbs" | C:\Windows\System32\wscript.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft ® Windows Based Script Host Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 784 | "C:\Users\admin\Desktop\HorrorTrojan Special Edition Installer.exe" | C:\Users\admin\Desktop\HorrorTrojan Special Edition Installer.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 848 | scream.exe | C:\Users\admin\AppData\Local\Temp\E4CD.tmp\scream.exe | — | cmd.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 1073807364 Modules
| |||||||||||||||
| 988 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\AppData\Local\Temp\24BE.tmp\dead.vbs" | C:\Windows\System32\wscript.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft ® Windows Based Script Host Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 1028 | "C:\Windows\System32\cmd.exe" | C:\Windows\System32\cmd.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1073807364 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1444 | C:\Windows\system32\sipnotify.exe -LogonOrUnlock | C:\Windows\System32\sipnotify.exe | taskeng.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: sipnotify Exit code: 0 Version: 6.1.7602.20480 (win7sp1_ldr_escrow.191010-1716) Modules
| |||||||||||||||
| 1452 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\AppData\Local\Temp\24BE.tmp\dead.vbs" | C:\Windows\System32\wscript.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft ® Windows Based Script Host Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 1496 | scream.exe | C:\Users\admin\AppData\Local\Temp\E4CD.tmp\scream.exe | — | cmd.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 1073807364 Modules
| |||||||||||||||
Total events
39 124
Read events
38 900
Write events
186
Delete events
38
Modification events
| (PID) Process: | (4076) reg.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Policies\System |
| Operation: | write | Name: | DisableTaskMgr |
Value: 1 | |||
| (PID) Process: | (4036) reg.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System |
| Operation: | write | Name: | EnableLUA |
Value: 0 | |||
| (PID) Process: | (2296) reg.exe | Key: | HKEY_CURRENT_USER\Control Panel\Desktop |
| Operation: | write | Name: | Wallpaper |
Value: c:\WinNT64\bg.bmp | |||
| (PID) Process: | (3384) reg.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | System File |
Value: C:\WinNT64\WinKern64.exe | |||
| (PID) Process: | (3156) taskmgr.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\TaskManager |
| Operation: | write | Name: | Preferences |
Value: 30030000E8030000010000000100000081000000F600000019020000B50200000100000001000000000000000000000001000000000000000100000000000000000000000200000004000000090000001D000000FFFFFFFF00000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000009C00000040000000210000004600000052000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF0000000002000000010000000300000004000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF05000000000000000100000000000000020000000300000004000000FFFFFFFF00000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000630060003C005A00FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF000000000000010000000200000003000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF0400000000000000FFFFFFFF02000000FFFFFFFF4F00000028000000970000003400000050000000000000000100000002000000030000000400000000000000FFFFFFFF43000000000000000000000001000000 | |||
| (PID) Process: | (1680) ctfmon.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run |
| Operation: | delete value | Name: | internat.exe |
Value: | |||
| (PID) Process: | (1692) IMEKLMG.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\IMEKR\14.0 |
| Operation: | write | Name: | SetPreload |
Value: 1 | |||
| (PID) Process: | (1640) IMEKLMG.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\IMEJP\14.0 |
| Operation: | write | Name: | SetPreload |
Value: 1 | |||
| (PID) Process: | (2008) WinKern64.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2008) WinKern64.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
Executable files
15
Suspicious files
3
Text files
117
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3352 | HorrorTrojan Special Edition Installer.exe | C:\Users\admin\AppData\Local\Temp\E4CD.tmp\HorrorSpecialInstall.bat | text | |
MD5:— | SHA256:— | |||
| 3352 | HorrorTrojan Special Edition Installer.exe | C:\Users\admin\AppData\Local\Temp\E4CD.tmp\glitch.exe | executable | |
MD5:— | SHA256:— | |||
| 3352 | HorrorTrojan Special Edition Installer.exe | C:\Users\admin\AppData\Local\Temp\E4CD.tmp\scream.exe | executable | |
MD5:— | SHA256:— | |||
| 3352 | HorrorTrojan Special Edition Installer.exe | C:\Users\admin\AppData\Local\Temp\E4CD.tmp\bg.bmp | image | |
MD5:— | SHA256:— | |||
| 3352 | HorrorTrojan Special Edition Installer.exe | C:\Users\admin\AppData\Local\Temp\E4CD.tmp\WinKern64.exe | executable | |
MD5:— | SHA256:— | |||
| 3112 | cmd.exe | C:\Users\admin\desktop\16790.txt | text | |
MD5:— | SHA256:— | |||
| 3112 | cmd.exe | C:\Users\admin\desktop\95.txt | text | |
MD5:— | SHA256:— | |||
| 3112 | cmd.exe | C:\Users\admin\desktop\13126.txt | text | |
MD5:— | SHA256:— | |||
| 3112 | cmd.exe | C:\Users\admin\desktop\2412.txt | text | |
MD5:— | SHA256:— | |||
| 3112 | cmd.exe | C:\Users\admin\desktop\5559.txt | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
8
DNS requests
2
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1444 | sipnotify.exe | HEAD | 200 | 88.221.61.151:80 | http://query.prod.cms.rt.microsoft.com/cms/api/am/binary/RE2JgkA?v=133577641545310000 | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 224.0.0.252:5355 | — | — | — | unknown |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
1108 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
1444 | sipnotify.exe | 88.221.61.151:80 | query.prod.cms.rt.microsoft.com | AKAMAI-AS | DE | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
dns.msftncsi.com |
| shared |
query.prod.cms.rt.microsoft.com |
| whitelisted |