| File name: | HorrorTrojan Special Edition Installer.exe |
| Full analysis: | https://app.any.run/tasks/325fa741-c3dc-452c-89af-5d27b459d2d5 |
| Verdict: | Malicious activity |
| Analysis date: | January 15, 2022, 14:44:17 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (console) Intel 80386, for MS Windows, UPX compressed |
| MD5: | 57A5524854D784CE379D1DF702B22645 |
| SHA1: | 171949C131EE42B4F02C9250AAA4B1E52E633AF5 |
| SHA256: | 60F48BBA56211EEED2FF0E1BFA36F91E16B452D37EA3868D9A76DCA45553A752 |
| SSDEEP: | 49152:etckccerCLrziGuZffJLF7VHa6MrZBBX45FPKCTCLyZZIBIkr:Ysr5hJLF7A6q7Bo5t5CWZZIuQ |
MALICIOUS
Drops executable file immediately after starts
- HorrorTrojan Special Edition Installer.exe (PID: 340)
SUSPICIOUS
Drops a file with too old compile date
- HorrorTrojan Special Edition Installer.exe (PID: 340)
Checks supported languages
- HorrorTrojan Special Edition Installer.exe (PID: 340)
- cmd.exe (PID: 2296)
Drops a file that was compiled in debug mode
- HorrorTrojan Special Edition Installer.exe (PID: 340)
Executable content was dropped or overwritten
- HorrorTrojan Special Edition Installer.exe (PID: 340)
Starts CMD.EXE for commands execution
- HorrorTrojan Special Edition Installer.exe (PID: 340)
Starts CHOICE.EXE (used to create a delay)
- cmd.exe (PID: 2296)
INFO
Checks supported languages
- choice.exe (PID: 2380)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | UPX compressed Win32 Executable (39.3) |
|---|---|---|
| .exe | | | Win32 EXE Yoda's Crypter (38.6) |
| .dll | | | Win32 Dynamic Link Library (generic) (9.5) |
| .exe | | | Win32 Executable (generic) (6.5) |
| .exe | | | Generic Win/DOS Executable (2.9) |
EXIF
EXE
| LegalCopyright: | 2021 |
|---|---|
| ProductVersion: | 1,0,0,0 |
| InternalName: | Trojan |
| ProductName: | HorrorTrojan Special Edition |
| FileVersion: | 1,0,0,0 |
| FileDescription: | Run only on VM |
| CompanyName: | HorrorTrojans |
| CharacterSet: | Windows, Latin1 |
| LanguageCode: | English (U.S.) |
| FileSubtype: | - |
| ObjectFileType: | Executable application |
| FileOS: | Windows 16-bit |
| FileFlags: | Debug, Pre-release, Private build |
| FileFlagsMask: | 0x003f |
| ProductVersionNumber: | 1.0.0.0 |
| FileVersionNumber: | 1.0.0.0 |
| Subsystem: | Windows command line |
| SubsystemVersion: | 4 |
| ImageVersion: | - |
| OSVersion: | 4 |
| EntryPoint: | 0x2ee6c0 |
| UninitializedDataSize: | 733184 |
| InitializedDataSize: | 155648 |
| CodeSize: | 2342912 |
| LinkerVersion: | 2.5 |
| PEType: | PE32 |
| TimeStamp: | 2010:11:08 14:12:00+01:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_CUI |
| Compilation Date: | 08-Nov-2010 13:12:00 |
| Detected languages: |
|
| CompanyName: | HorrorTrojans |
| FileDescription: | Run only on VM |
| FileVersion: | 1,0,0,0 |
| ProductName: | HorrorTrojan Special Edition |
| InternalName: | Trojan |
| ProductVersion: | 1,0,0,0 |
| LegalCopyright: | 2021 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 08-Nov-2010 13:12:00 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
UPX0 | 0x00001000 | 0x000B3000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
UPX1 | 0x000B4000 | 0x0023C000 | 0x0023B400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.9999 |
.rsrc | 0x002F0000 | 0x00026000 | 0x00025C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.48742 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.09999 | 668 | Latin 1 / Western European | UNKNOWN | RT_MANIFEST |
B | 7.99808 | 91614 | Latin 1 / Western European | UNKNOWN | RT_RCDATA |
F | 0 | 2750142 | Latin 1 / Western European | UNKNOWN | RT_RCDATA |
I | 5.90944 | 72 | Latin 1 / Western European | UNKNOWN | RT_RCDATA |
N | 4.58496 | 24 | Latin 1 / Western European | UNKNOWN | RT_RCDATA |
O | 2.58496 | 6 | Latin 1 / Western European | UNKNOWN | RT_RCDATA |
Imports
COMCTL32.dll |
GDI32.dll |
KERNEL32.DLL |
MSVCRT.dll |
OLE32.dll |
SHELL32.dll |
SHLWAPI.dll |
USER32.dll |
Total processes
42
Monitored processes
4
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 340 | "C:\Users\admin\Desktop\HorrorTrojan Special Edition Installer.exe" | C:\Users\admin\Desktop\HorrorTrojan Special Edition Installer.exe | Explorer.EXE | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2160 | "C:\Users\admin\Desktop\HorrorTrojan Special Edition Installer.exe" | C:\Users\admin\Desktop\HorrorTrojan Special Edition Installer.exe | — | Explorer.EXE | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 2296 | C:\Windows\system32\cmd.exe /c ""C:\Users\admin\AppData\Local\Temp\373A.tmp\HorrorSpecialInstall.bat"" | C:\Windows\system32\cmd.exe | — | HorrorTrojan Special Edition Installer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
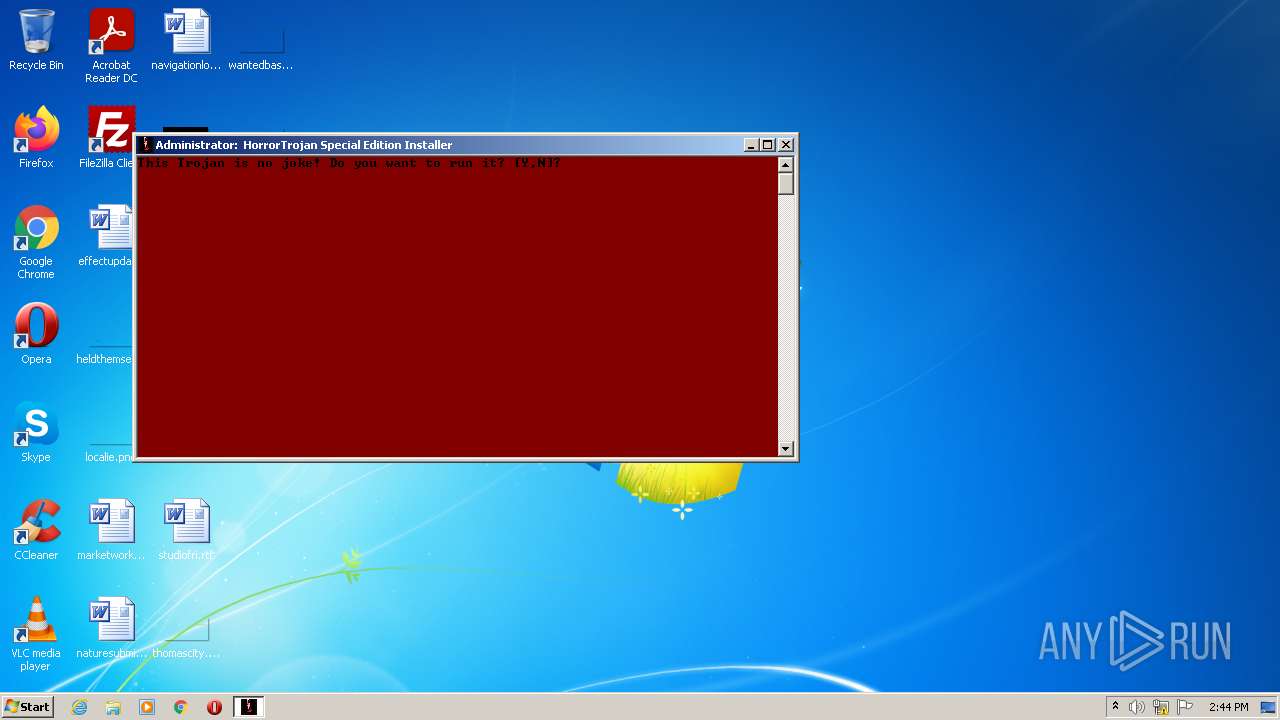
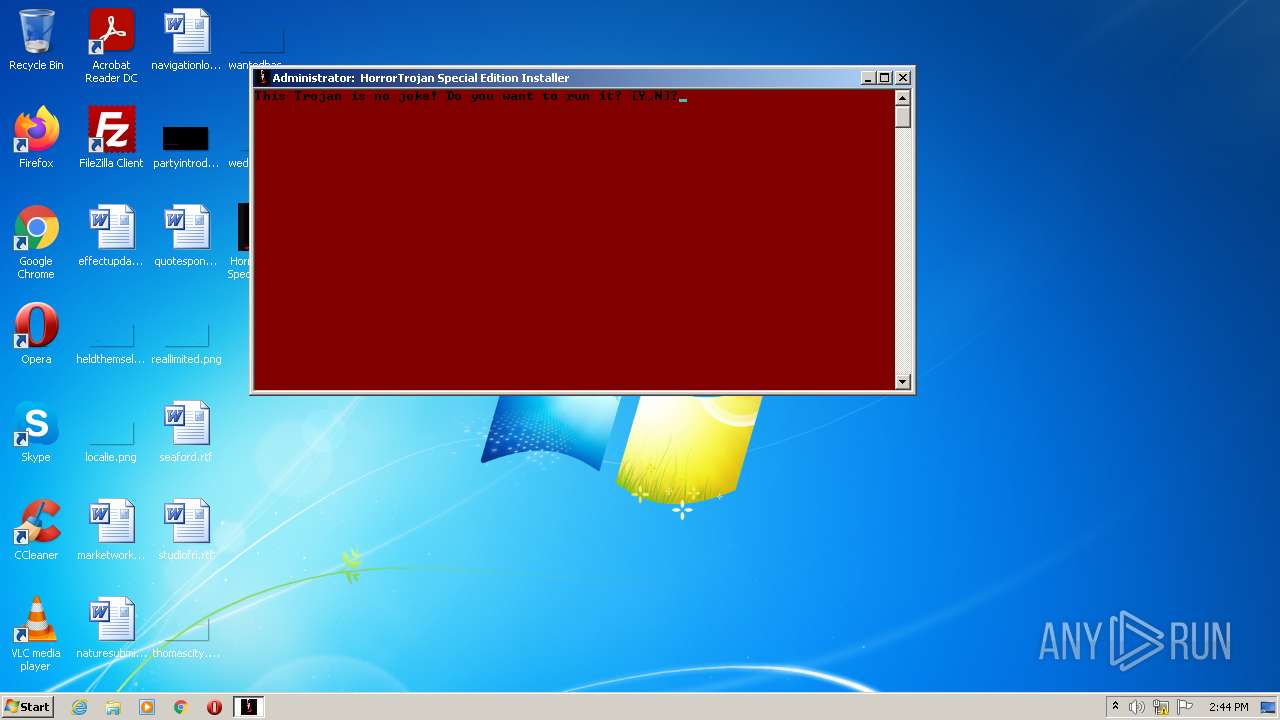
| 2380 | choice /c yn /m "This Trojan is no joke! Do you want to run it?" | C:\Windows\system32\choice.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Offers the user a choice Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
31
Read events
31
Write events
0
Delete events
0
Modification events
Executable files
3
Suspicious files
0
Text files
2
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 340 | HorrorTrojan Special Edition Installer.exe | C:\Users\admin\AppData\Local\Temp\373A.tmp\bg.bmp | image | |
MD5:F39D3B06F62B88D02D4DC93B4BED0E3C | SHA256:C85F12ED323E9AA3A943777CD23F4549697D5FF517D1EF2E2A887E7D165170F5 | |||
| 340 | HorrorTrojan Special Edition Installer.exe | C:\Users\admin\AppData\Local\Temp\373A.tmp\glitch.exe | executable | |
MD5:47801F0CF73D320054676A56D0264EDB | SHA256:F25853B17EE25C1DF537CD39BA15A338B92B0812833E3A523AA2F90EFBF766E8 | |||
| 340 | HorrorTrojan Special Edition Installer.exe | C:\Users\admin\AppData\Local\Temp\373A.tmp\WinKern64.exe | executable | |
MD5:B2A729276140C4E6CE06FCE8E7EAC724 | SHA256:5FF1ED648DBDAFAF0CCB6579B88B6947BFFA82334A2D293B99F09C4F18E72915 | |||
| 340 | HorrorTrojan Special Edition Installer.exe | C:\Users\admin\AppData\Local\Temp\373A.tmp\scream.exe | executable | |
MD5:CBF06517A75EEE73FF7A614981384457 | SHA256:AE5252BE8CAD37A12F70F94751F5A9DB15866A6C395DC5EBA505ECB05D414A9A | |||
| 340 | HorrorTrojan Special Edition Installer.exe | C:\Users\admin\AppData\Local\Temp\373A.tmp\HorrorSpecialInstall.bat | text | |
MD5:BFF1E7828F69FE2360AD5CC204835B57 | SHA256:89360AAC46BCF8AE9CB3D58FA92DAC1BCD72D53A1960A0FE91BC9A9991786F5E | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report