| File name: | sample_36 |
| Full analysis: | https://app.any.run/tasks/35f365bd-6b3e-4219-a186-a4b89e6f9098 |
| Verdict: | Malicious activity |
| Analysis date: | November 30, 2020, 10:18:42 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | F417DA4BEF7683B60054D75FBA790524 |
| SHA1: | B744187D78F09785518AF5D4156A01A62EBE805E |
| SHA256: | 60EAFEC9A14B925D6A2850C1065619E81F363BC68B651C165E14AFA041B26F6E |
| SSDEEP: | 12288:N6Bnj6mhb11mxoF3UZSvG/VN5MbWekRsOye4wm:Nyjn11mmUKEVqdUE |
MALICIOUS
Drops executable file immediately after starts
- sample_36.exe (PID: 1772)
Changes the autorun value in the registry
- winlogon.exe (PID: 2532)
SUSPICIOUS
Starts itself from another location
- sample_36.exe (PID: 1772)
Creates files in the Windows directory
- sample_36.exe (PID: 1772)
Drops a file with too old compile date
- sample_36.exe (PID: 1772)
Executable content was dropped or overwritten
- sample_36.exe (PID: 1772)
INFO
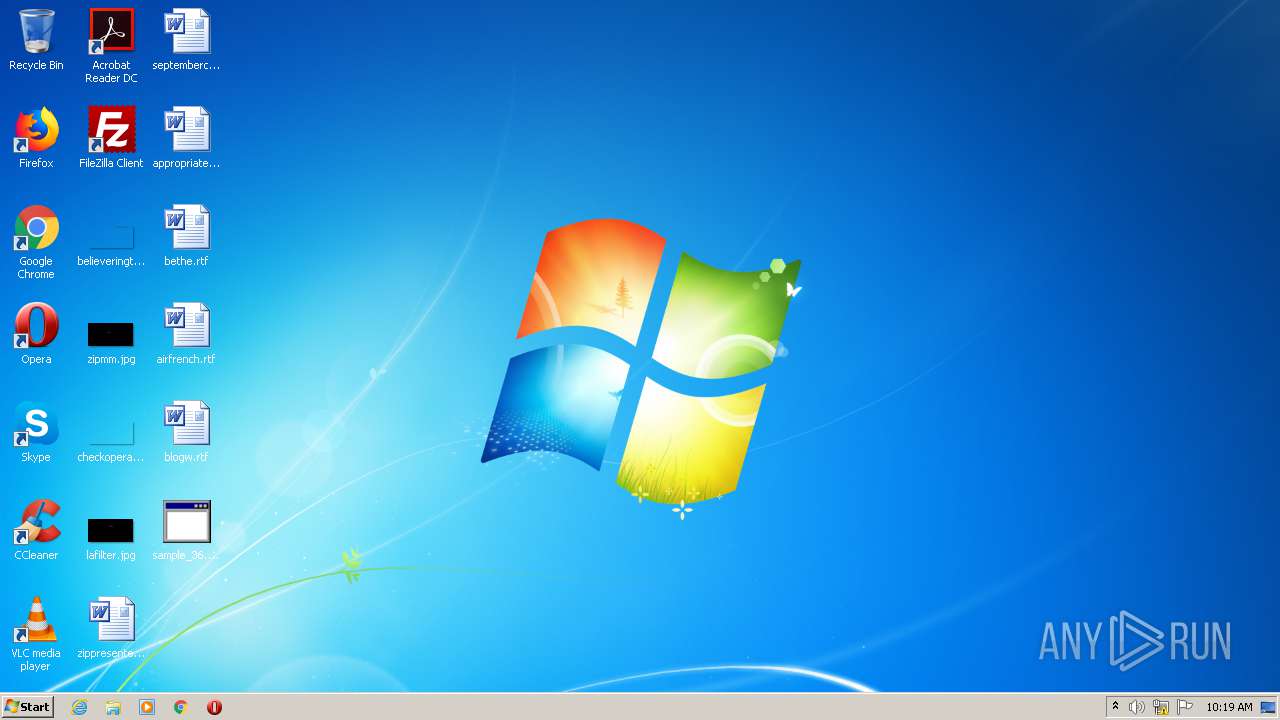
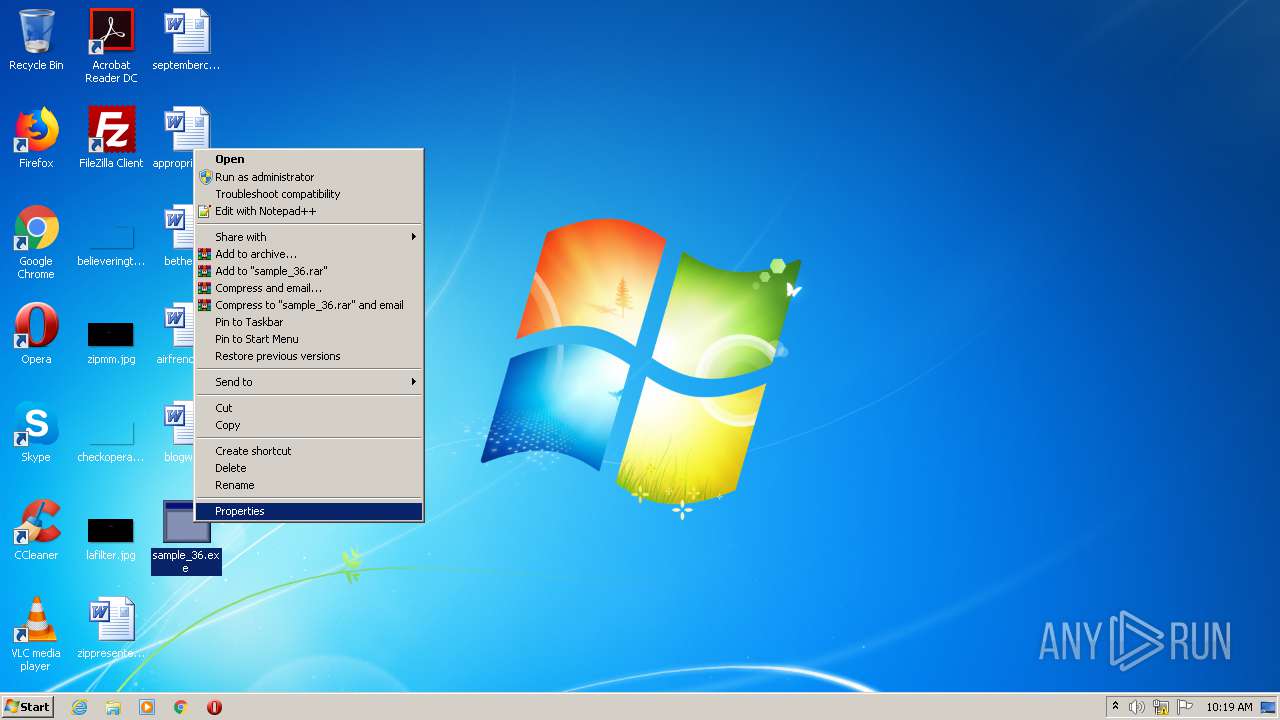
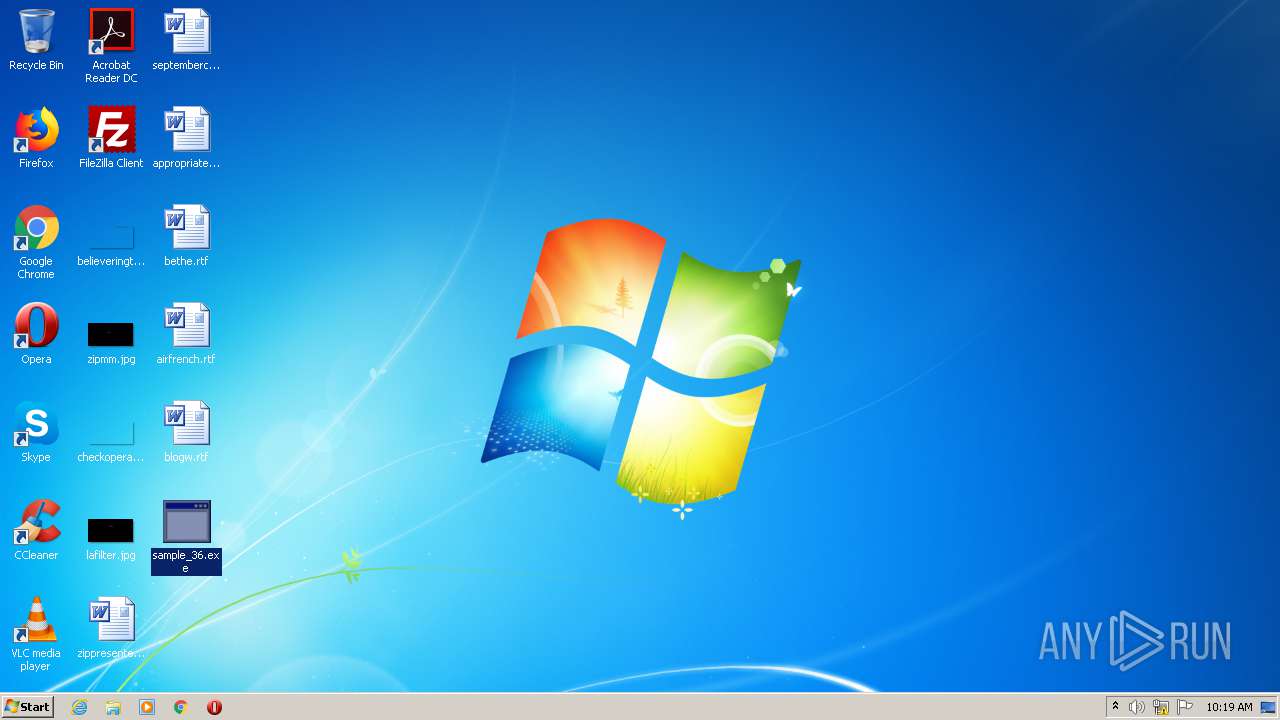
Manual execution by user
- sample_36.exe (PID: 1772)
- sample_36.exe (PID: 2632)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable Borland Delphi 7 (68.4) |
|---|---|---|
| .exe | | | Win32 Executable Borland Delphi 6 (27) |
| .exe | | | Win32 Executable Delphi generic (1.4) |
| .scr | | | Windows screen saver (1.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (0.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 1992:06:20 00:22:17+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 548864 |
| InitializedDataSize: | 97792 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x86dec |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 19-Jun-1992 22:22:17 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 8 |
| Time date stamp: | 19-Jun-1992 22:22:17 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
CODE | 0x00001000 | 0x00085E58 | 0x00086000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.55591 |
DATA | 0x00087000 | 0x000027A8 | 0x00002800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.06303 |
BSS | 0x0008A000 | 0x00001035 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x0008C000 | 0x0000243A | 0x00002600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.90564 |
.tls | 0x0008F000 | 0x00000010 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x00090000 | 0x00000018 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 0.186583 |
.reloc | 0x00091000 | 0x0000928C | 0x00009400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 6.62384 |
.rsrc | 0x0009B000 | 0x00009A00 | 0x00009A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 4.62909 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 3.58178 | 2216 | UNKNOWN | Icelandic - Iceland | RT_ICON |
2 | 2.80231 | 308 | UNKNOWN | UNKNOWN | RT_CURSOR |
3 | 3.00046 | 308 | UNKNOWN | UNKNOWN | RT_CURSOR |
4 | 2.56318 | 308 | UNKNOWN | UNKNOWN | RT_CURSOR |
5 | 2.6949 | 308 | UNKNOWN | UNKNOWN | RT_CURSOR |
6 | 2.62527 | 308 | UNKNOWN | UNKNOWN | RT_CURSOR |
7 | 2.91604 | 308 | UNKNOWN | UNKNOWN | RT_CURSOR |
4074 | 3.03356 | 340 | UNKNOWN | UNKNOWN | RT_STRING |
4075 | 3.24171 | 1052 | UNKNOWN | UNKNOWN | RT_STRING |
4076 | 3.15413 | 932 | UNKNOWN | UNKNOWN | RT_STRING |
Imports
advapi32.dll |
comctl32.dll |
gdi32.dll |
kernel32.dll |
oleaut32.dll |
shell32.dll |
user32.dll |
version.dll |
winmm.dll |
Total processes
40
Monitored processes
4
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1772 | "C:\Users\admin\Desktop\sample_36.exe" | C:\Users\admin\Desktop\sample_36.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2308 | "C:\Users\admin\Desktop\sample_36.exe" | C:\Users\admin\Desktop\sample_36.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2532 | C:\Windows\system\winlogon.exe | C:\Windows\system\winlogon.exe | sample_36.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2632 | "C:\Users\admin\Desktop\sample_36.exe" | C:\Users\admin\Desktop\sample_36.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
871
Read events
3
Write events
868
Delete events
0
Modification events
| (PID) Process: | (2532) winlogon.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | Tarani |
Value: :\Windows\system\winlogon.exe | |||
Executable files
1
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1772 | sample_36.exe | C:\Windows\system\winlogon.exe | executable | |
MD5:F417DA4BEF7683B60054D75FBA790524 | SHA256:60EAFEC9A14B925D6A2850C1065619E81F363BC68B651C165E14AFA041B26F6E | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
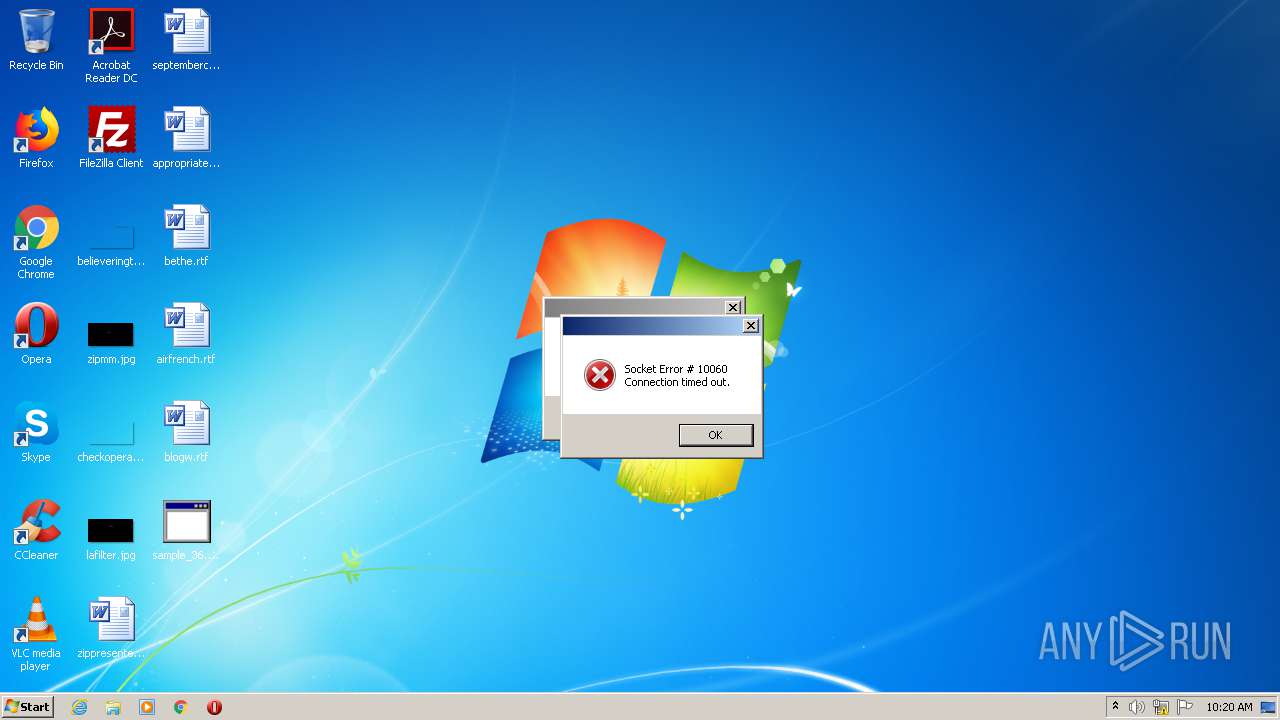
HTTP(S) requests
0
TCP/UDP connections
4
DNS requests
3
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2532 | winlogon.exe | 217.17.41.93:8074 | — | ATM S.A. | PL | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
dns.msftncsi.com |
| shared |