| File name: | message_.eml |
| Full analysis: | https://app.any.run/tasks/26690df4-3129-4d65-8d3e-3b3d51f57efb |
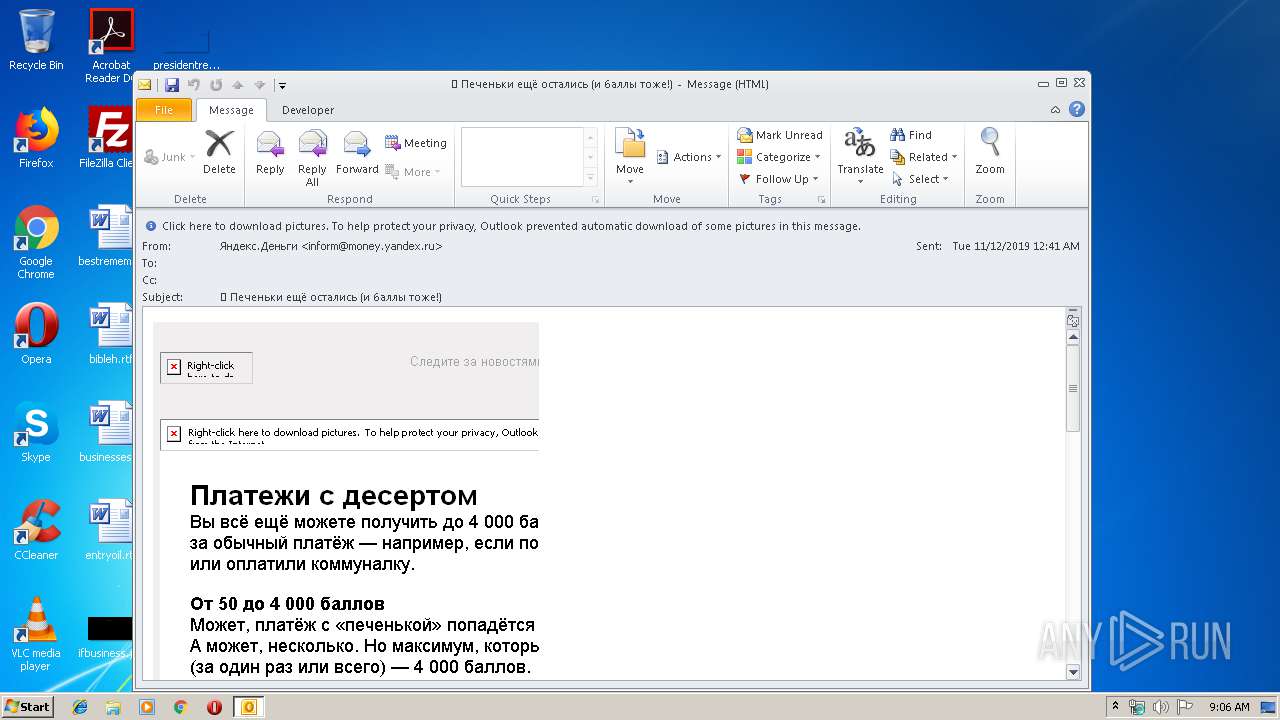
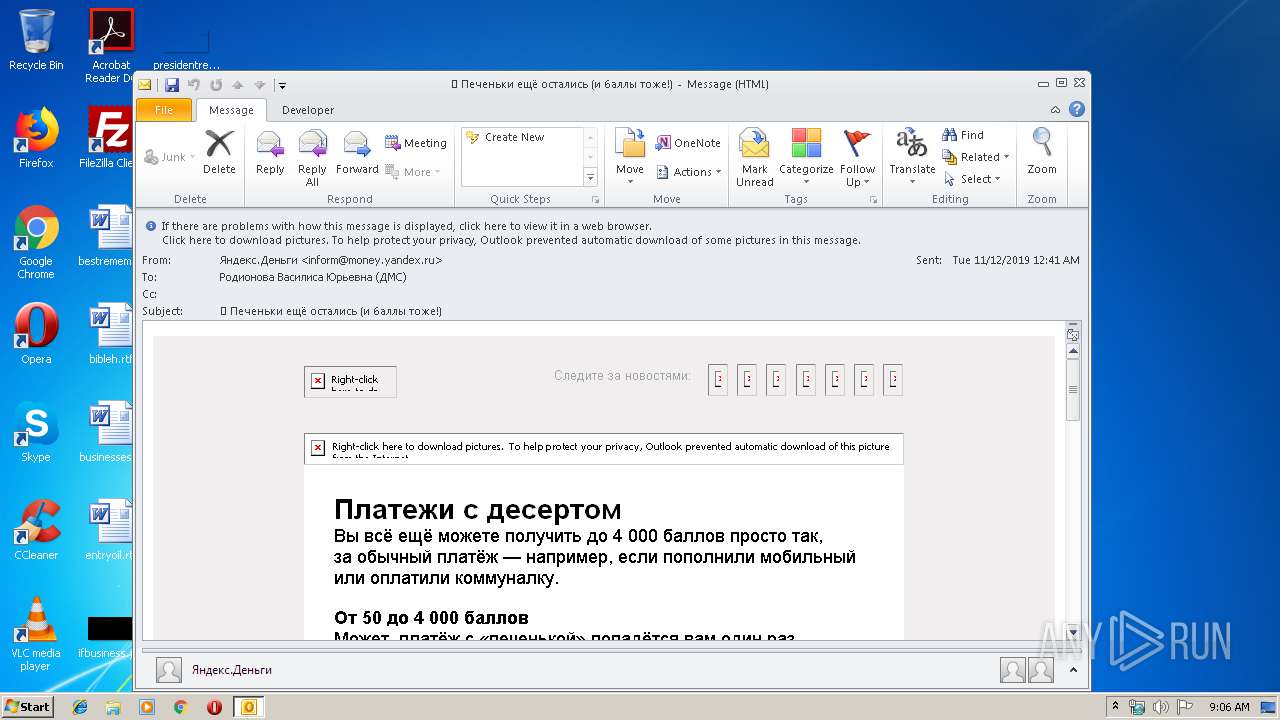
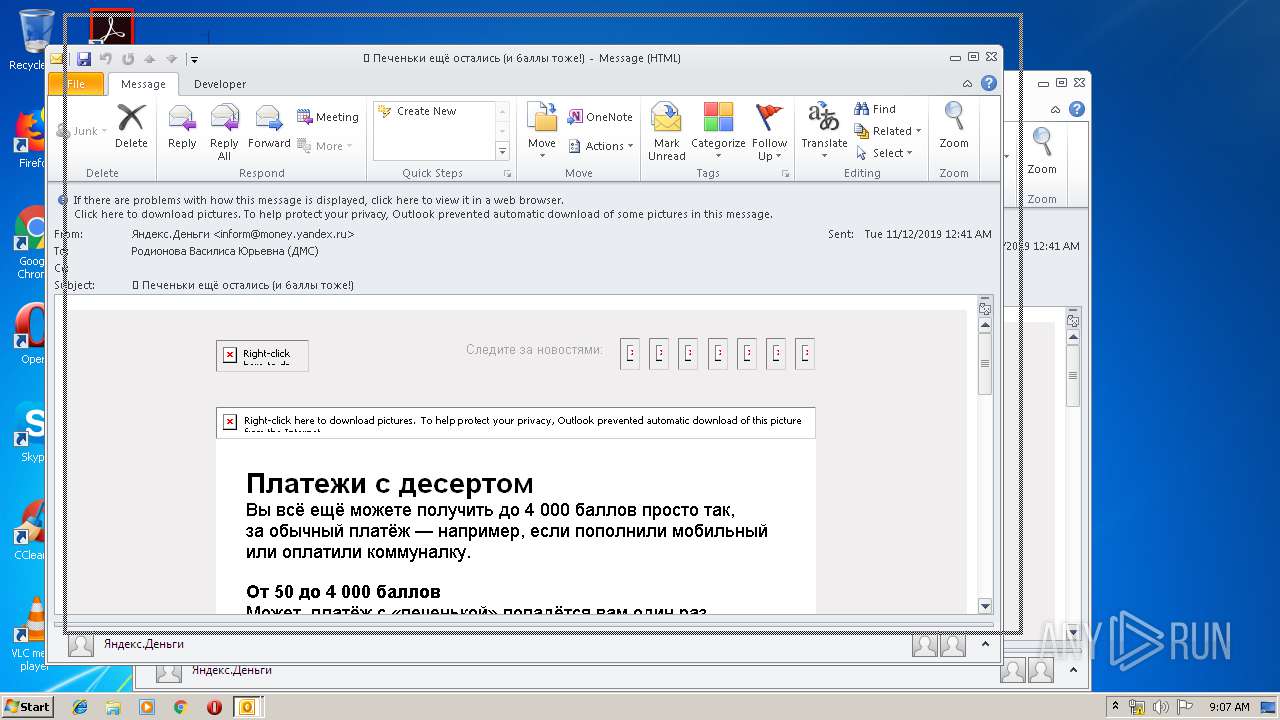
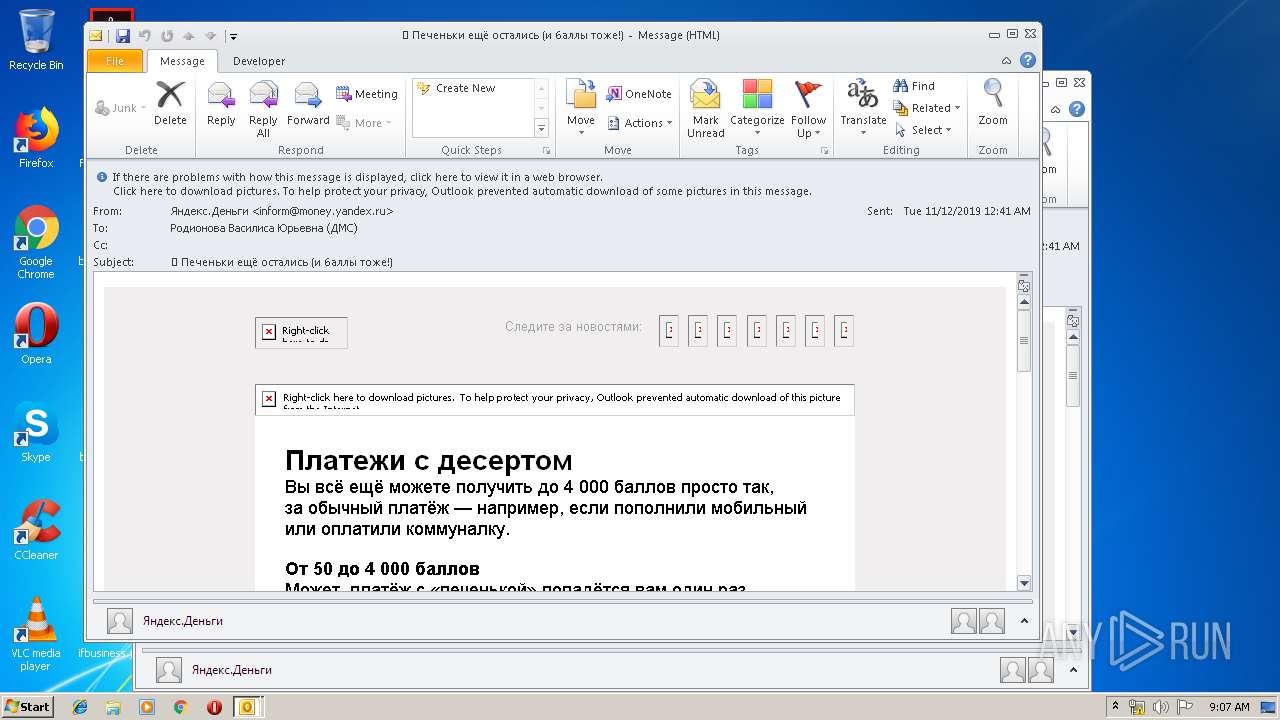
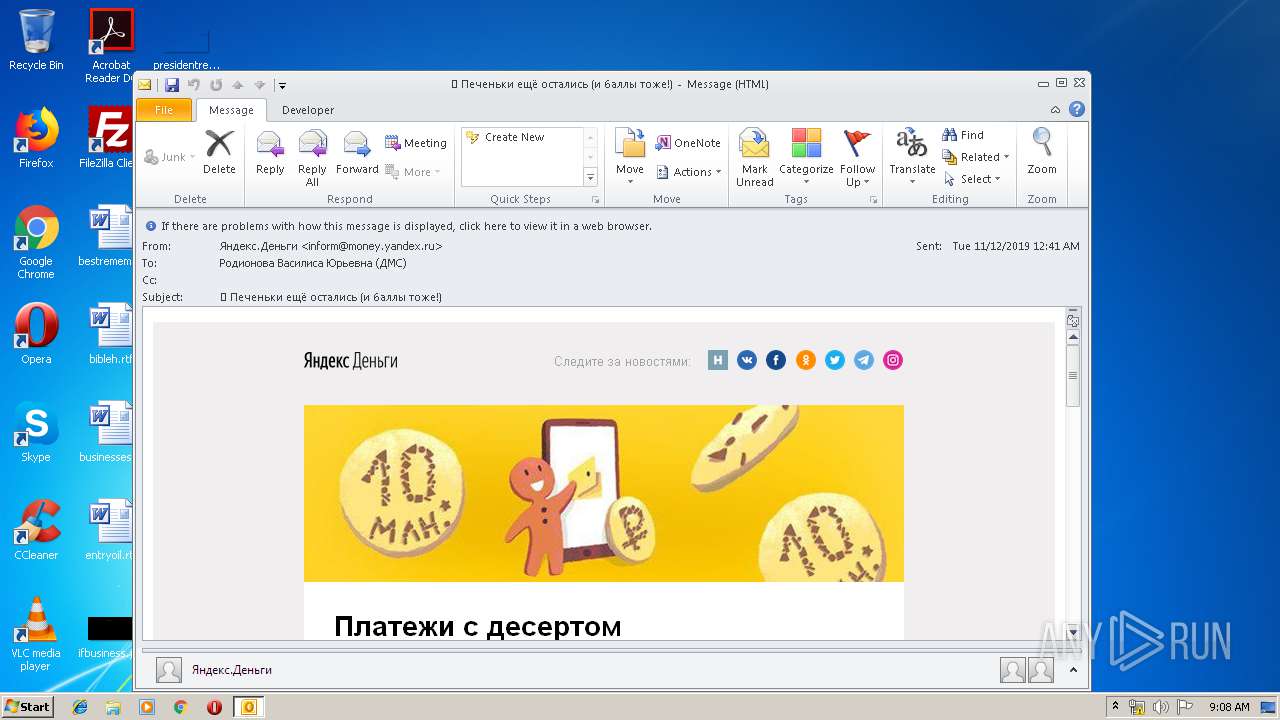
| Verdict: | Malicious activity |
| Analysis date: | November 12, 2019, 09:06:41 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | message/rfc822 |
| File info: | RFC 822 mail, ASCII text, with very long lines, with CRLF line terminators |
| MD5: | 85E27FBD891A255B7FF4F4F46773C26B |
| SHA1: | 95E6A4AD7F2BB0AAD1BB470AA9857500EE833D57 |
| SHA256: | 60E5DA4AE52F3156D68B82327166A9DE61620013D274272D0C779BCE067FA632 |
| SSDEEP: | 768:GNoLdKXkU+9wd38Vz/rU09GhzW99x+XKawiZUtL5lscbGXK3a0g8gO/aUR:Gog38VTrU1VW6dqtLzPMKBTgO/ak |
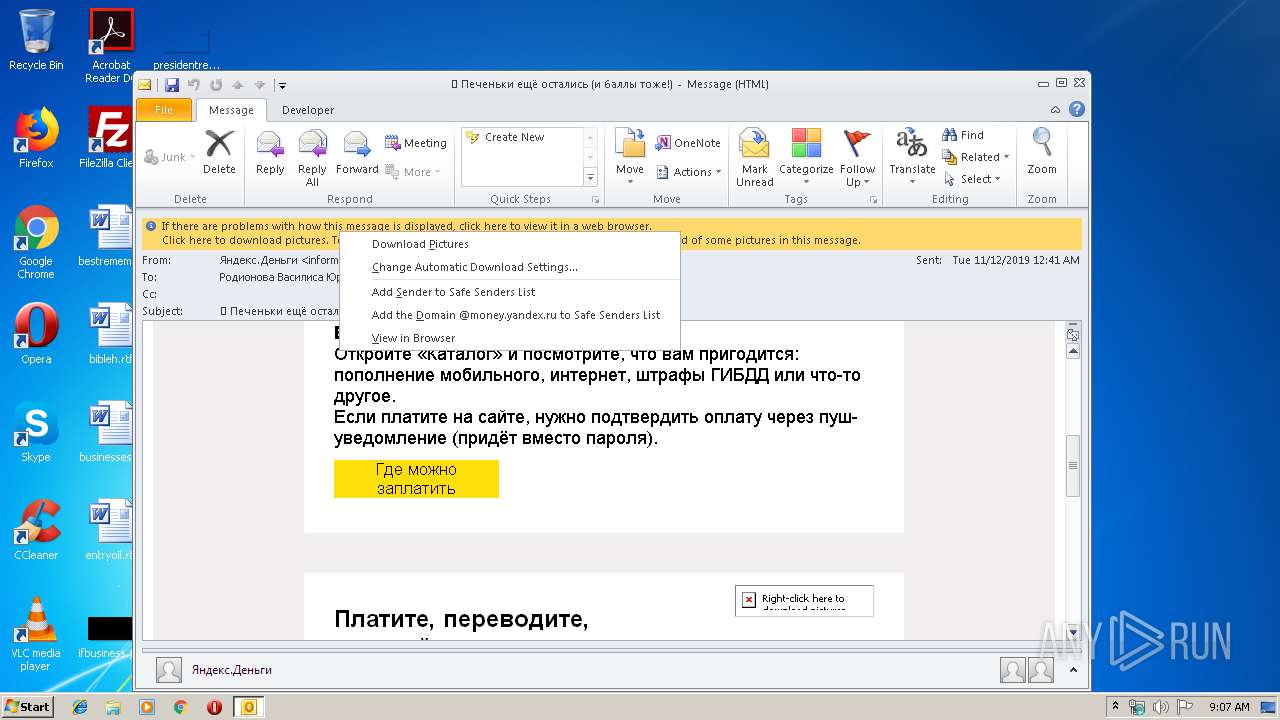
MALICIOUS
Changes settings of System certificates
- OUTLOOK.EXE (PID: 2148)
SUSPICIOUS
Reads Internet Cache Settings
- OUTLOOK.EXE (PID: 2148)
Creates files in the user directory
- OUTLOOK.EXE (PID: 2148)
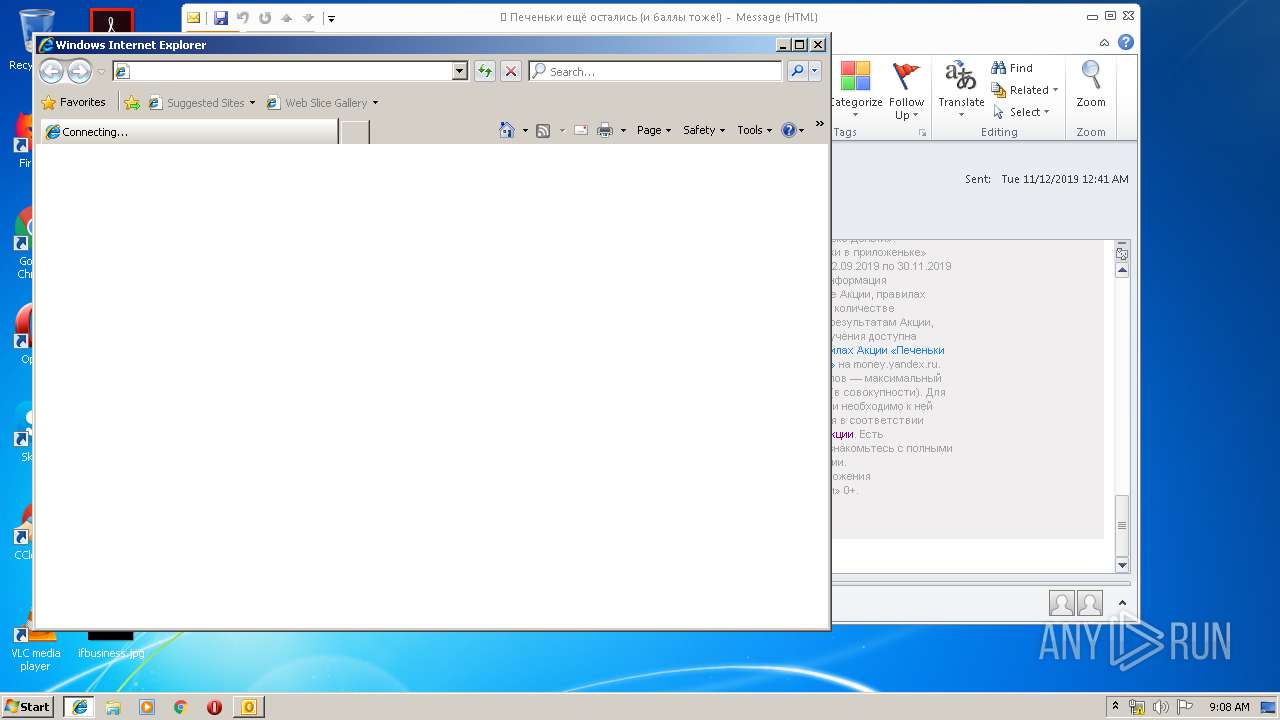
Starts Internet Explorer
- OUTLOOK.EXE (PID: 2148)
Executed via COM
- OUTLOOK.EXE (PID: 3988)
INFO
Reads Microsoft Office registry keys
- OUTLOOK.EXE (PID: 3988)
- OUTLOOK.EXE (PID: 2148)
Changes internet zones settings
- iexplore.exe (PID: 2336)
Application launched itself
- iexplore.exe (PID: 2336)
Reads internet explorer settings
- iexplore.exe (PID: 3468)
Reads Internet Cache Settings
- iexplore.exe (PID: 3468)
Creates files in the user directory
- iexplore.exe (PID: 3468)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2336)
Reads settings of System Certificates
- OUTLOOK.EXE (PID: 2148)
- iexplore.exe (PID: 2336)
Changes settings of System certificates
- iexplore.exe (PID: 2336)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .eml | | | E-Mail message (Var. 5) (100) |
|---|
Total processes
40
Monitored processes
4
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
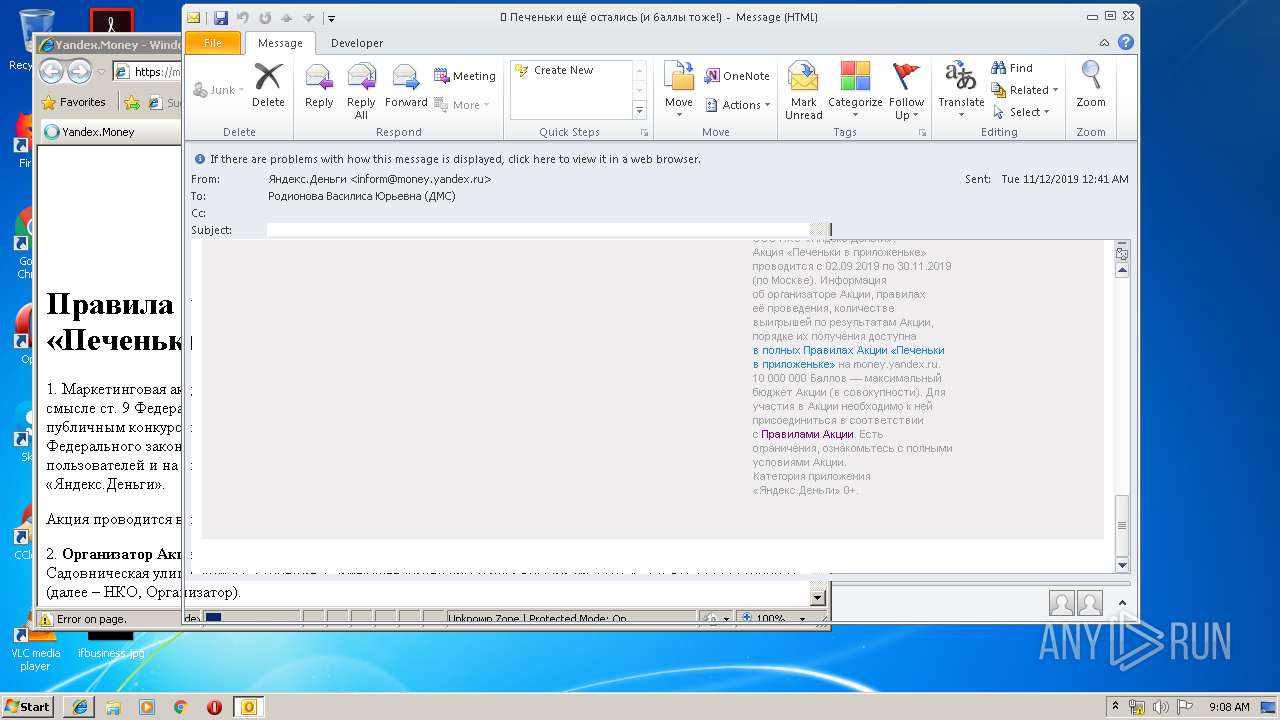
| 2148 | "C:\PROGRA~1\MICROS~1\Office14\OUTLOOK.EXE" /eml "C:\Users\admin\AppData\Local\Temp\message_.eml" | C:\PROGRA~1\MICROS~1\Office14\OUTLOOK.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Outlook Exit code: 0 Version: 14.0.6025.1000 Modules
| |||||||||||||||
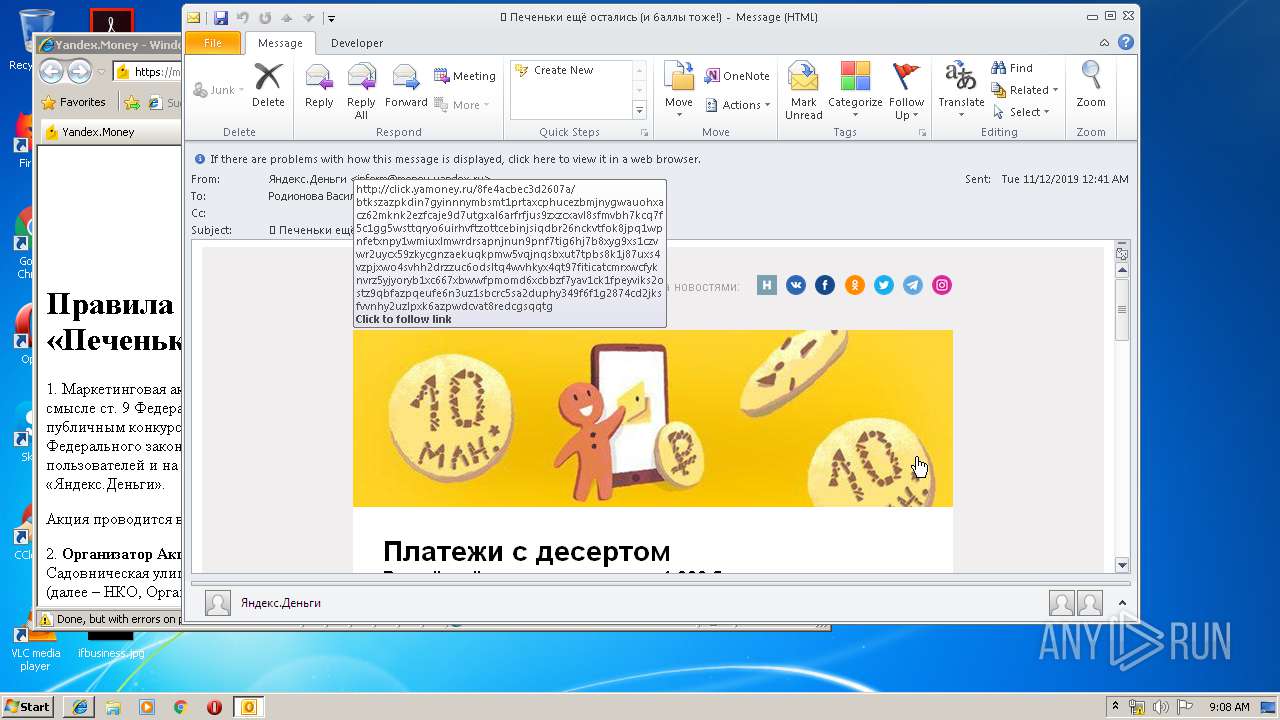
| 2336 | "C:\Program Files\Internet Explorer\iexplore.exe" http://click.yamoney.ru/5183c1c632b5eebb/scaJAVVvyVprrgSgsZAkJDGSQv9VZVknbSBYVNGPyj5n7xL3CB97pGyxdQziMgiSFcMk2AT8dhLuXq1hdYXPsGaUyCfX7j1adeSMGSjfAVkD8M9hiZi2T32V2wxdpQdhjTQaWATz693Ez3ozr7cb9Mb48DzMcsBhEhciW8AWRZ1dTWexBqpTzeR8QQCvSAY7FNfMTS5dUA1UEYJu6wCh4TuuSfAZf9n3yekxUakEdnbdVjKdwrcVkFhf2bAu2rfmYkaq2BYe14kYvhC3mm9tnLJxSbTiHwn6L7MtJTFK9gvnTvKGcn2jwr9ycRgpGZVZuWpwnsH5kbBGXwza3t9Rv8hVcvLoKetB7BPNswVxTPJiUMAQFFryLyz112cybMiwxXxCWQK7HJm9SgkWgYtKpM5z4NQTbKEaKDmtmXMhjLpjEgtym249bt9i89E4eB6j8ZTmYEQPtgxfqpmZqosJA6 | C:\Program Files\Internet Explorer\iexplore.exe | OUTLOOK.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3468 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2336 CREDAT:71937 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3988 | "C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE" -Embedding | C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Outlook Exit code: 0 Version: 14.0.6025.1000 Modules
| |||||||||||||||
Total events
2 173
Read events
1 504
Write events
647
Delete events
22
Modification events
| (PID) Process: | (2148) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2148) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (2148) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (2148) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (2148) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (2148) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (2148) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (2148) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (2148) OUTLOOK.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1332478132 | |||
| (PID) Process: | (2148) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources |
| Operation: | write | Name: | UISnapshot |
Value: 1033;1046;1036;1031;1040;1041;1049;3082;1042;1055 | |||
Executable files
0
Suspicious files
3
Text files
75
Unknown types
8
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2148 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CVRA6CA.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2148 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\outlook logging\firstrun.log | text | |
MD5:— | SHA256:— | |||
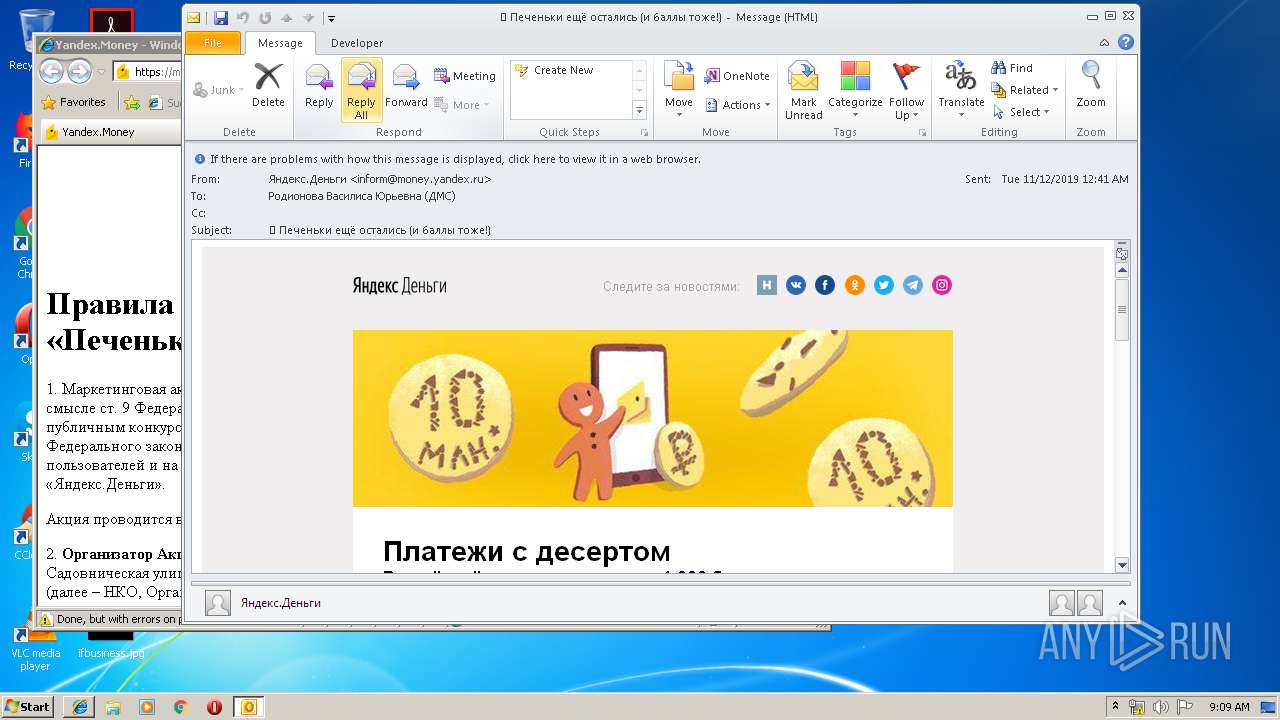
| 2148 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\LH043OAM\mzl.wgyjzvif[1].png | image | |
MD5:— | SHA256:— | |||
| 2148 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\JGRR2OYX\yamoney_logo_new2018[1].png | image | |
MD5:— | SHA256:— | |||
| 2148 | OUTLOOK.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\admin@radikal[1].txt | — | |
MD5:— | SHA256:— | |||
| 2148 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\LH043OAM\soc-4[1].png | image | |
MD5:— | SHA256:— | |||
| 2148 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Outlook\RoamCache\Stream_AvailabilityOptions_2_B7DBCFFFD09438419D5C3E42CE44B7F2.dat | xml | |
MD5:EEAA832C12F20DE6AAAA9C7B77626E72 | SHA256:C4C9A90F2C961D9EE79CF08FBEE647ED7DE0202288E876C7BAAD00F4CA29CA16 | |||
| 2148 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Outlook\mapisvc.inf | text | |
MD5:48DD6CAE43CE26B992C35799FCD76898 | SHA256:7BFE1F3691E2B4FB4D61FBF5E9F7782FBE49DA1342DBD32201C2CC8E540DBD1A | |||
| 2148 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\JGRR2OYX\gp[1].png | image | |
MD5:— | SHA256:— | |||
| 2148 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Outlook\RoamCache\Stream_Calendar_2_867842E20A13E84A8CC2159364CB3661.dat | xml | |
MD5:B21ED3BD946332FF6EBC41A87776C6BB | SHA256:B1AAC4E817CD10670B785EF8E5523C4A883F44138E50486987DC73054A46F6F4 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
23
TCP/UDP connections
30
DNS requests
13
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2148 | OUTLOOK.EXE | GET | — | 64.4.26.155:80 | http://config.messenger.msn.com/config/msgrconfig.asmx?op=GetOlcConfig | US | — | — | whitelisted |
2148 | OUTLOOK.EXE | GET | 301 | 109.235.165.47:80 | http://click.yamoney.ru/c5dc9ff8c/22e164cccdf7f64a/gq4b7aPjsnMV3kBkd3G6N4iRYSywkaRroDGne7AVnNNxU9HTdsETuUJ4raUm9e1E5U | RU | html | 76 b | unknown |
2148 | OUTLOOK.EXE | GET | 301 | 109.235.165.47:80 | http://click.yamoney.ru/c5dc9ff8c/1f76bf681bf7bcdc/gq4b7aPjsnMUSCrPQXB9yTYtPFXRmhek68rHmyREFFTiRG7Y4DhmDC4Kuw6keYf4jM | RU | html | 80 b | unknown |
2148 | OUTLOOK.EXE | GET | 301 | 109.235.165.47:80 | http://click.yamoney.ru/450053f00fbbe097/JP91ofAkAVoN6jRYhwSLHZ2b1J7hsRFYUphaMvHg7WM6yuxWPc5rVjq3LMR28FfEpZykKe5iMQHs4ybhCvoj6jZhAyL2HyAJeK16BPE46jn8j4V7KYfARgvyJXGF5dbqXCffyCNM7tnfaiEGbDH5tdZpxoYc9euUPFpCtCfRTA4WcJVhabw1136749YAxt6vaDMvQ9JTdeXfT3eCKTXoegKdCZHbcaApSmoSFMDfjn2pEYA32rMDd2jPsQ769ruvHgATs1Ly62yNeykzhyvLkxvy9DV5BdW291QKWWARjCs57E62aT | RU | html | 230 b | unknown |
2148 | OUTLOOK.EXE | GET | 301 | 109.235.165.47:80 | http://click.yamoney.ru/c5dc9ff8c/3a4006c00aac4317/yPZFoqcXNXSKF4ME7VRYnKw7e7j7USBdm3fiMYCSamgecTnYubChNw5T4Sm5s8ygyDE3csoi6GC7Tv44YUgkBmb5jNaf3RA3PEEMgDE6PYvTVqHeqTA8WJNTWzLFuwaTA7esVVMkWjUhiP3sYrLiHPSfM89XrWBGmV7wb3jJrw6ZnVmpEqAUm7FzvSJBVQdE8yEnQq9QGYfjMvCwYFv3GM4QoSivyAvLsrpS52VpnHbQwzrweUDFjBYhdVFjmhMickbevFg4gpg6FBJ6AxutsfNQpKpygsyRwFq8evnVvsxptLjXv8APMov44Gt4tUbZHASCUNGJczkKio63dFTSz3EmR8jgDs3BArDNQK2PEqRGgBansPRhyB1poWvXyucrJauBxa6yvTYecxmR1f6Atbtw6jrMmSc4kEegWAycuV2CPTcPknrV4jzQQRiAd3eonk5fJyAhiE3Wkg3udaBEmWn7TXjLZCEP4 | RU | html | 382 b | unknown |
2148 | OUTLOOK.EXE | GET | 301 | 109.235.165.47:80 | http://click.yamoney.ru/c5dc9ff8c/aeaeabc2f4c77b52/co3Ppxd4DEqWrvNvxb2Pha51C9B9USoB1gfmLmF7htpn5QehJqzEynmumJv9BCPkJMY4zUrmVMYtN | RU | html | 84 b | unknown |
2148 | OUTLOOK.EXE | GET | 301 | 109.235.165.47:80 | http://click.yamoney.ru/c5dc9ff8c/6fecac51145965a8/co3Ppxd4DEqWLwe6fuNxCzCUP5wgWcnjetWTwRxJ5G7Q1FJMUaxMCaVmfrFw1xYKKD4wAMew74Emd | RU | html | 84 b | unknown |
2148 | OUTLOOK.EXE | GET | 301 | 109.235.165.47:80 | http://click.yamoney.ru/c5dc9ff8c/7f23dbbdd03392f4/gq4b7aPjsnMUSCrPQXB9yTYtPFXRmhek68rHmyREFFTiBzUVhdCkeB9iCKWB6WptC5 | RU | html | 83 b | unknown |
2148 | OUTLOOK.EXE | GET | 301 | 109.235.165.47:80 | http://click.yamoney.ru/c5dc9ff8c/fd41eda11b3d1741/4uKEwvTPRSzY23iHmCmi2WxRUH9uNsiaYzitj5o1RNE7451VvjLqtB8rzWdJdhv8mvY9yXgTZ8D1AMdhf9jwrmY8mbuUnQP5xt8oMcguquyc5pnTpu6LsgW5UubEXBsmuMNiod2R6dQGvAEyGZT41SRGDYUVFR1Vb7HkR3Sjwpi7iYcfmreWpP691KRBDTTUd1wXDXfv4ouknUkVTpwqaNsNrGkyrPmoFPYmQcgLkbazYL1hABj1JGW7gW6hGV6rJzHjgEDVCN7bzLXnogsE1Dbq18h4SCnmiEGFh115KroS86Bh5ovaXVAiXoePHCWaa11rJ31JbEVGJfDpWN6KzpfEV9pr6xAtryKafqxTjAVrw2WP7RfXJEUyFQwtTc9fbsbLPC3wy3VyWNYRriMSsBwVgJ5X3eCG | RU | html | 339 b | unknown |
2148 | OUTLOOK.EXE | GET | 301 | 109.235.165.47:80 | http://click.yamoney.ru/c5dc9ff8c/0f8401e65154767c/gq4b7aPjsnMUSCrPQXB9yTYtPFXRmhek68rHmyREFFTiAkS1Q1YQK3mEvyrfVV3xoZ | RU | html | 81 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
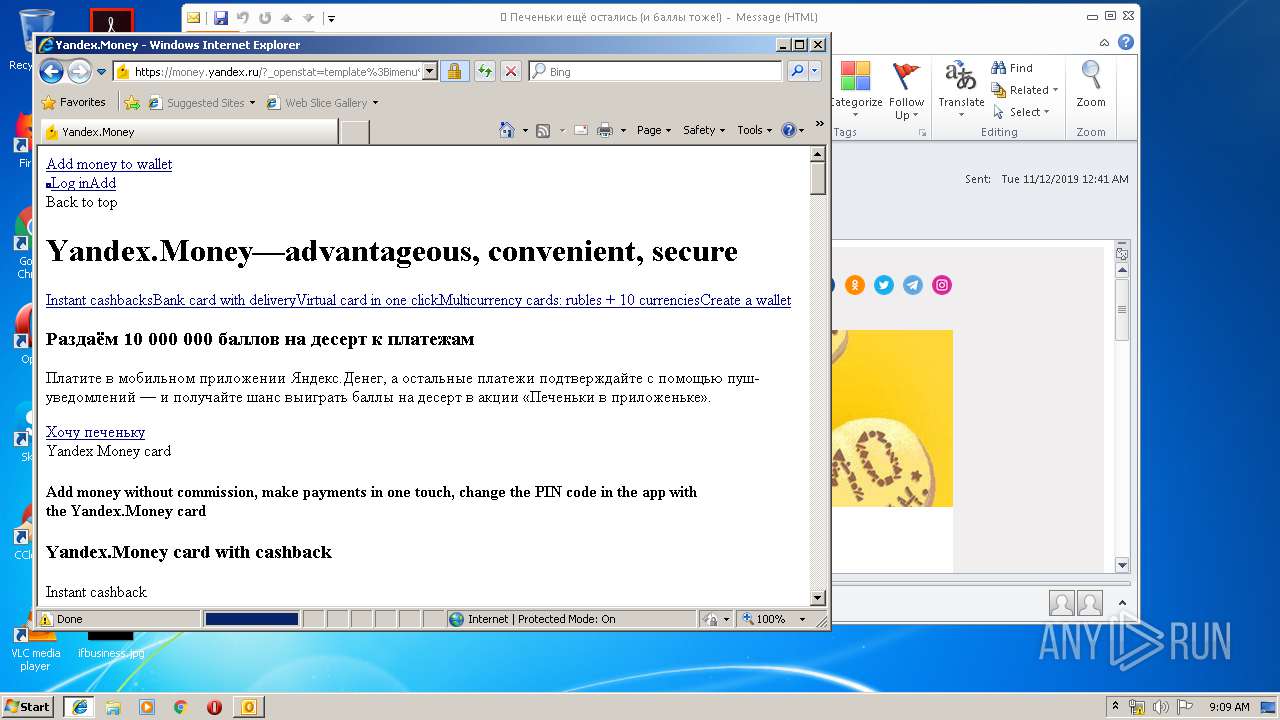
2148 | OUTLOOK.EXE | 109.235.165.47:80 | click.yamoney.ru | Yandex.Money NBCO LLC | RU | unknown |
2148 | OUTLOOK.EXE | 109.235.165.182:443 | money.yandex.ru | Yandex.Money NBCO LLC | RU | unknown |
2148 | OUTLOOK.EXE | 95.213.184.41:443 | imgems.ru | OOO Network of data-centers Selectel | RU | unknown |
2148 | OUTLOOK.EXE | 81.176.238.212:443 | b.radikal.ru | JSC RTComm.RU | RU | unknown |
2148 | OUTLOOK.EXE | 81.176.238.214:443 | d.radikal.ru | JSC RTComm.RU | RU | unknown |
2148 | OUTLOOK.EXE | 91.199.212.52:80 | crt.sectigo.com | Comodo CA Ltd | GB | suspicious |
3468 | iexplore.exe | 109.235.165.47:80 | click.yamoney.ru | Yandex.Money NBCO LLC | RU | unknown |
3468 | iexplore.exe | 109.235.165.42:443 | pxl.yamoney.ru | Yandex.Money NBCO LLC | RU | unknown |
3468 | iexplore.exe | 178.154.131.216:443 | yastatic.net | YANDEX LLC | RU | whitelisted |
3468 | iexplore.exe | 87.250.251.153:443 | ext.captcha.yandex.net | YANDEX LLC | RU | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
config.messenger.msn.com |
| whitelisted |
click.yamoney.ru |
| unknown |
a129.phobos.apple.com |
| suspicious |
money.yandex.ru |
| whitelisted |
imgems.ru |
| unknown |
d.radikal.ru |
| unknown |
b.radikal.ru |
| unknown |
pxl.yamoney.ru |
| unknown |
crt.sectigo.com |
| whitelisted |
crt.usertrust.com |
| whitelisted |