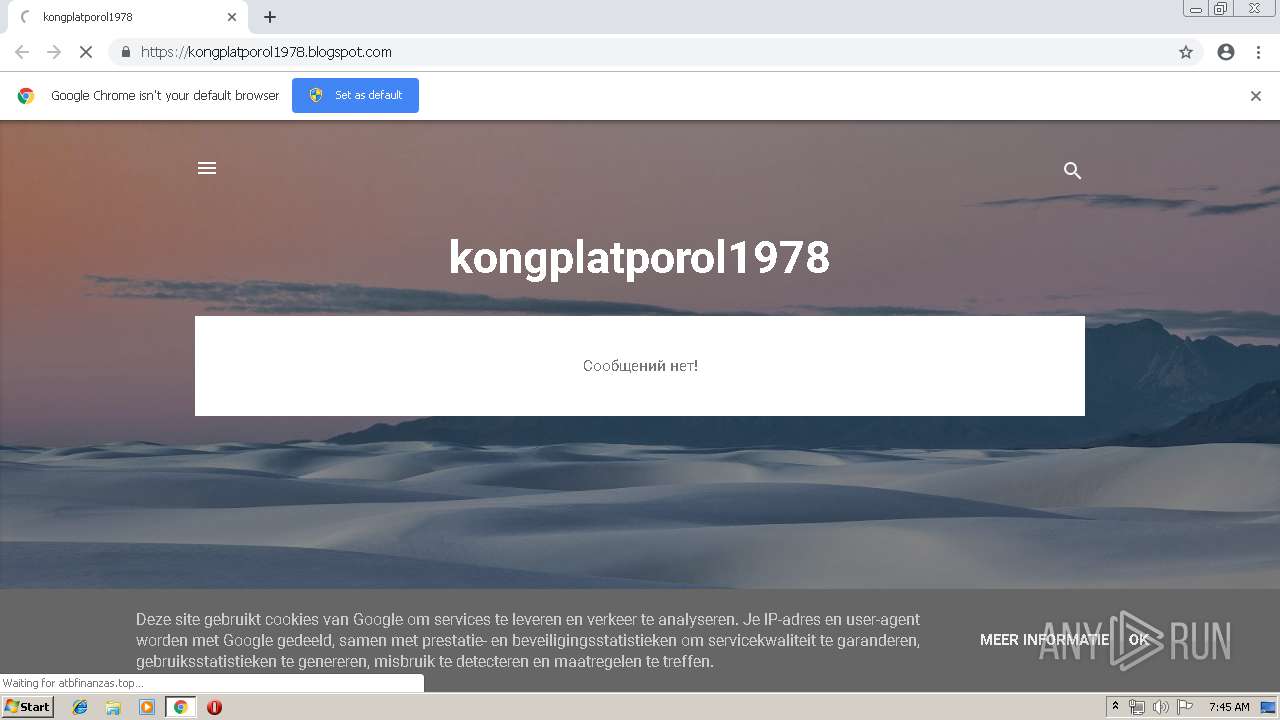
| URL: | https://kongplatporol1978.blogspot.ie/ |
| Full analysis: | https://app.any.run/tasks/aba1e5a2-fa75-4004-a52b-382a968b2daf |
| Verdict: | Malicious activity |
| Analysis date: | June 19, 2019, 06:45:02 |
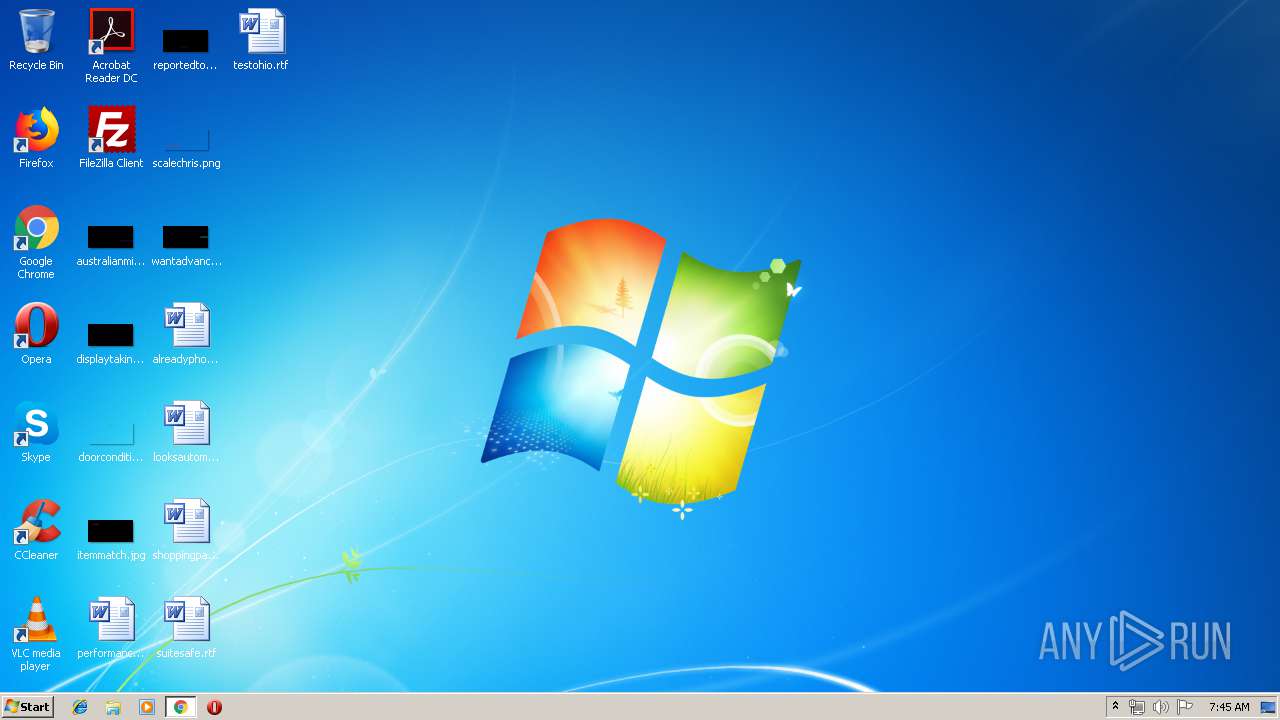
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | C0FDA7596BFB86D31CDEBAC6A7F10BA4 |
| SHA1: | 2A3182A9AF2E3FD9B6213813DD97AA2798900B8B |
| SHA256: | 60D93097D770057E2B787037FD286BFC82EBAC521247CD1CCD8BE0FD46BF9D80 |
| SSDEEP: | 3:N8PLCVOMjJrzBKn:2uVOMZ8n |
MALICIOUS
No malicious indicators.SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 2556)
INFO
Application launched itself
- chrome.exe (PID: 2556)
Reads settings of System Certificates
- chrome.exe (PID: 2556)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
53
Monitored processes
22
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1028 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=944,15379422907693368005,9165559896744267503,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAACAAwAAAQAAAAAAAAAAAGAAAAAAAAEAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=66203899630775436 --mojo-platform-channel-handle=960 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1088 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=944,15379422907693368005,9165559896744267503,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=6398452391151590874 --mojo-platform-channel-handle=4556 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1128 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=944,15379422907693368005,9165559896744267503,131072 --enable-features=PasswordImport --service-pipe-token=6540198023234917099 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=6540198023234917099 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2036 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1300 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=944,15379422907693368005,9165559896744267503,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=4005464540870109764 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=4005464540870109764 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3600 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1680 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=944,15379422907693368005,9165559896744267503,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=18107290020820195910 --mojo-platform-channel-handle=4404 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1816 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=2688 --on-initialized-event-handle=308 --parent-handle=312 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1936 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=944,15379422907693368005,9165559896744267503,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=16923714096907386804 --mojo-platform-channel-handle=4552 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2140 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=944,15379422907693368005,9165559896744267503,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=16080288862711701397 --mojo-platform-channel-handle=4244 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2304 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=944,15379422907693368005,9165559896744267503,131072 --enable-features=PasswordImport --service-pipe-token=17667289432405912191 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=17667289432405912191 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1852 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2472 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=944,15379422907693368005,9165559896744267503,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=9893749878648723832 --mojo-platform-channel-handle=4200 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
Total events
552
Read events
463
Write events
84
Delete events
5
Modification events
| (PID) Process: | (2556) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2556) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2556) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2556) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2556) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (1816) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2556-13205400316759375 |
Value: 259 | |||
| (PID) Process: | (2556) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2556) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2556) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3488-13197474229333984 |
Value: 0 | |||
| (PID) Process: | (2556) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
0
Suspicious files
23
Text files
150
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2556 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 2556 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 2556 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 2556 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_2 | — | |
MD5:— | SHA256:— | |||
| 2556 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_3 | — | |
MD5:— | SHA256:— | |||
| 2556 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\f83d95c4-d131-4416-aa73-a5e425c33f4d.tmp | — | |
MD5:— | SHA256:— | |||
| 2556 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000018.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2556 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\CURRENT | — | |
MD5:— | SHA256:— | |||
| 2556 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 2556 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
43
TCP/UDP connections
29
DNS requests
20
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2556 | chrome.exe | GET | — | 47.88.103.239:80 | http://atbfinanzas.top/favicon.ico | US | — | — | suspicious |
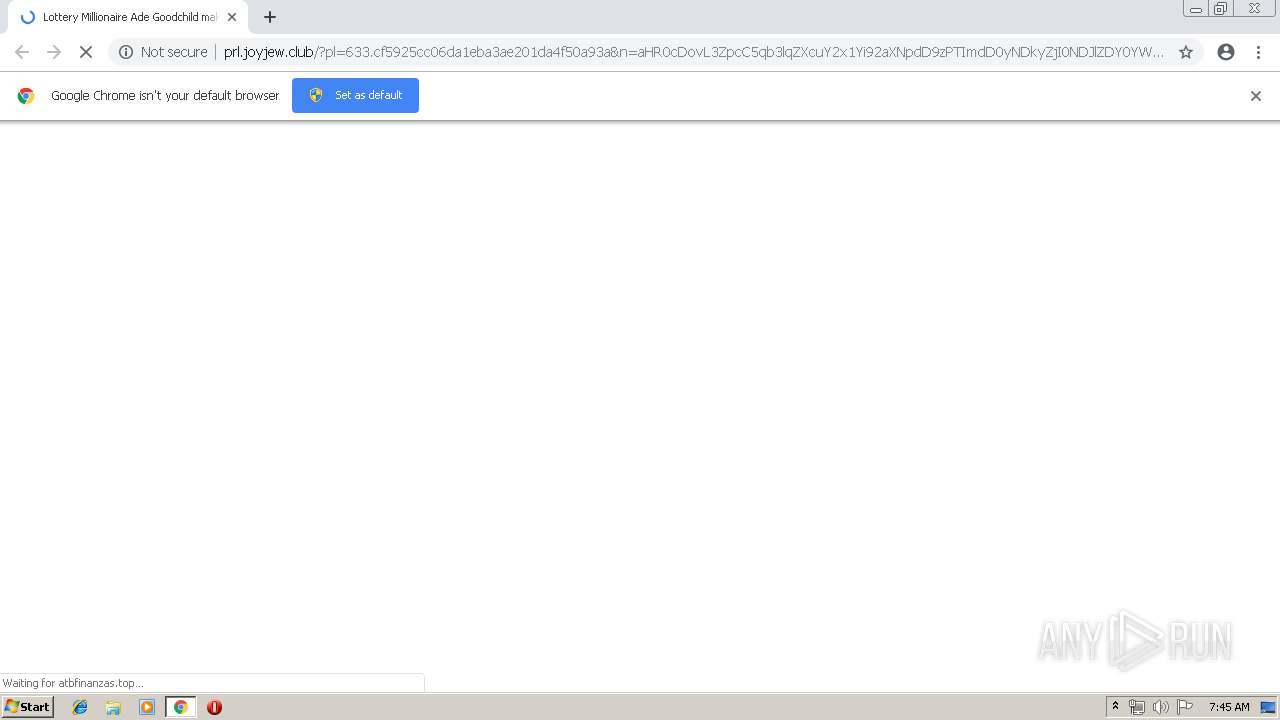
2556 | chrome.exe | GET | 302 | 104.31.86.46:80 | http://vip.joyjew.club/tracker?offer_id=2164&aff_id=225&u=1197:100&pl=633:100 | US | — | — | malicious |
2556 | chrome.exe | GET | 200 | 104.31.87.46:80 | http://prl.joyjew.club/prelands/633/css/tidyx-v2.css | US | text | 8.27 Kb | malicious |
2556 | chrome.exe | GET | 200 | 104.31.87.46:80 | http://prl.joyjew.club/prelands/633/images/Sergi.jpg | US | image | 53.0 Kb | malicious |
2556 | chrome.exe | GET | 200 | 47.88.103.239:80 | http://atbfinanzas.top/eng.html | US | html | 154 b | suspicious |
2556 | chrome.exe | GET | 200 | 104.31.87.46:80 | http://prl.joyjew.club/prelands/633/images/espic1.jpg | US | image | 37.1 Kb | malicious |
2556 | chrome.exe | GET | 200 | 104.31.87.46:80 | http://prl.joyjew.club/prelands/633/images/sharetab.png | US | image | 2.04 Kb | malicious |
2556 | chrome.exe | GET | 200 | 104.31.87.46:80 | http://prl.joyjew.club/prelands/633/images/sharedesk.png | US | image | 2.66 Kb | malicious |
2556 | chrome.exe | GET | 200 | 104.31.87.46:80 | http://prl.joyjew.club/prelands/633/images/bittrader-step21.jpg | US | image | 38.8 Kb | malicious |
2556 | chrome.exe | GET | 200 | 104.31.87.46:80 | http://prl.joyjew.club/prelands/633/css/css.css | US | text | 761 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2556 | chrome.exe | 104.31.87.46:80 | vip.joyjew.club | Cloudflare Inc | US | shared |
2556 | chrome.exe | 104.31.86.46:80 | vip.joyjew.club | Cloudflare Inc | US | shared |
2556 | chrome.exe | 172.217.22.99:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2556 | chrome.exe | 172.217.22.97:443 | kongplatporol1978.blogspot.ie | Google Inc. | US | whitelisted |
2556 | chrome.exe | 172.217.22.45:443 | accounts.google.com | Google Inc. | US | whitelisted |
2556 | chrome.exe | 172.217.23.161:443 | kongplatporol1978.blogspot.com | Google Inc. | US | whitelisted |
— | — | 172.217.23.169:443 | resources.blogblog.com | Google Inc. | US | whitelisted |
— | — | 172.217.16.201:443 | www.blogger.com | Google Inc. | US | whitelisted |
— | — | 172.217.16.195:443 | www.gstatic.com | Google Inc. | US | whitelisted |
2556 | chrome.exe | 172.217.16.193:443 | themes.googleusercontent.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
kongplatporol1978.blogspot.ie |
| whitelisted |
accounts.google.com |
| shared |
kongplatporol1978.blogspot.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
resources.blogblog.com |
| whitelisted |
www.blogger.com |
| shared |
themes.googleusercontent.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
lh3.googleusercontent.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1068 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a *.top domain - Likely Hostile |
2556 | chrome.exe | Potentially Bad Traffic | ET INFO HTTP Request to a *.top domain |