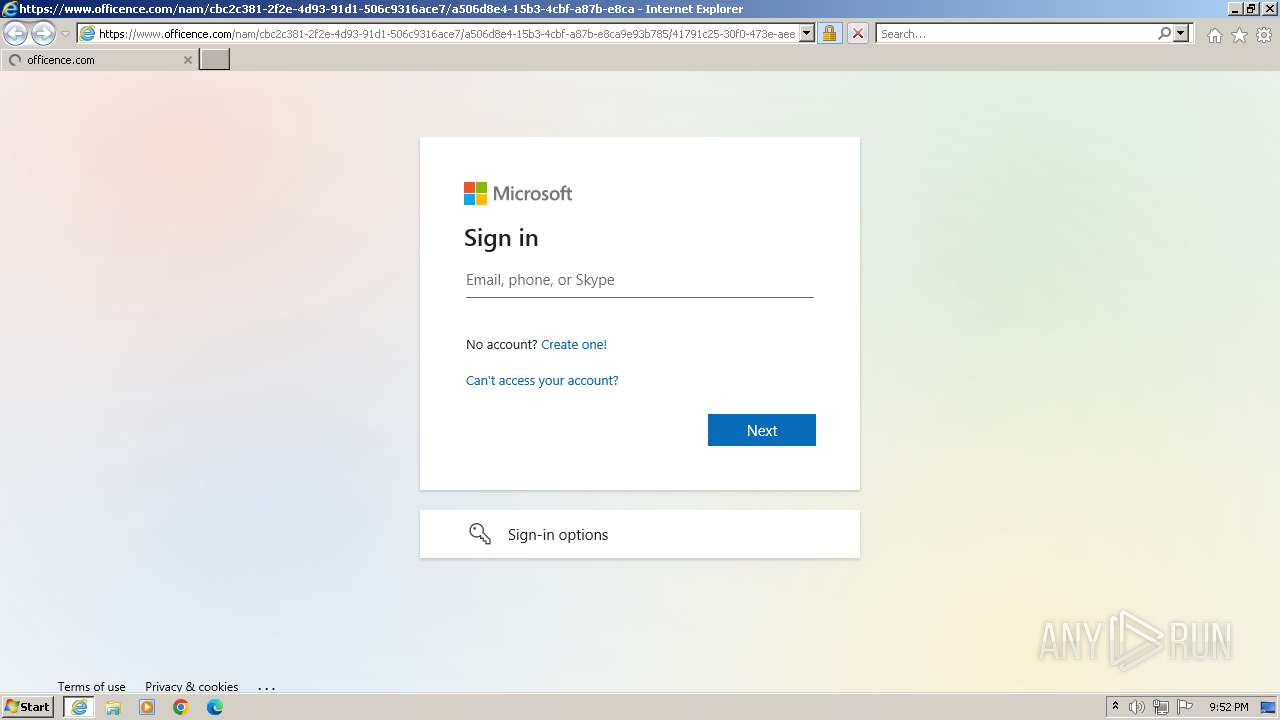
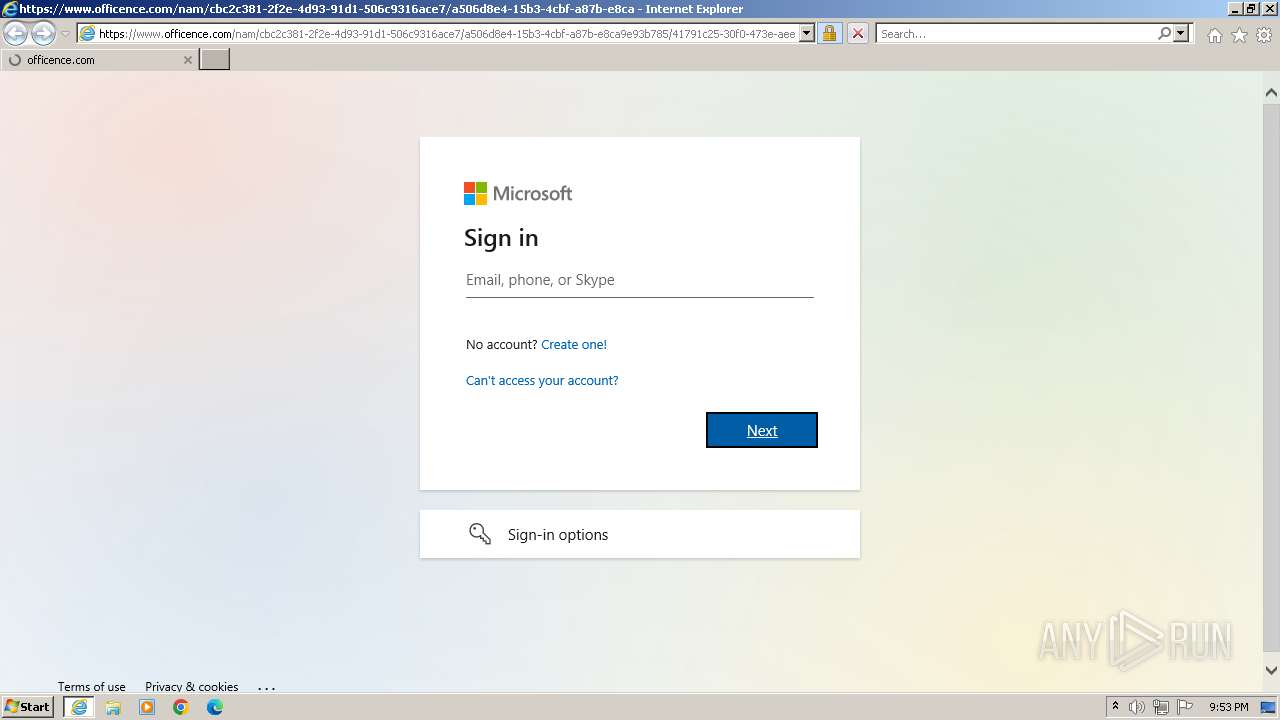
| URL: | https://www.officence.com/nam/cbc2c381-2f2e-4d93-91d1-506c9316ace7/a506d8e4-15b3-4cbf-a87b-e8ca9e93b785/41791c25-30f0-473e-aee8-86d4501542f1/login?id=VTduQmFsdW9PQmZxeFA1MlV6SWxQL1luVENZN1dxRCtXTnp2R3FGNHJ5YjJTc0hVai9YUi9WVWtXRTZDd2ZkbWNmWlBYa3F0by9Id2JlQVl5Y09OWSs3dnV2L3N4R214bk80OGtoZkFPalJZSjllcjNNYituNE1udmJnaFVRelhyQ20xTk9GemJZaHFQTk1aTFJham5PSTY3L09kQXlQeS9hUE82UGR5dTV6cTk0VklVVDExbmpTMWhwYStYOWppSGViV0NhMS85NnZpY3JjTE56UFZ2UEszUkM3cDFoRjJqOEwzQ0ZNQnNYZDQyYnVjZUowTWEzb2FLRTVJaHRRK2xkQzVyekFvZ1NSQUNGT2YvV2N0RVVuVWRtY2g1OUJEbWlWRmsvajJjbElkMFZoR1lBWXVQZXFKL1FoejlLRHFpVnM1QUxNWUNHTngrbC91TEZhL1VWSkorNU5KMTQ0SUNJSnMzR1AvY1Jxdy9ZTGc0Z2lyK3ZIRnJ6OFErbFUv |
| Full analysis: | https://app.any.run/tasks/a9b6d706-d8d3-4154-ba92-3ffffd07d956 |
| Verdict: | Malicious activity |
| Analysis date: | November 24, 2023, 21:52:50 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| SHA1: | 9CA9CE3B7196DDC26C569E89C85CD1D119B45242 |
| SHA256: | 60D375DFA15CF31676AA8CF3B3022BFF53C7EBF22C42B0FD31A6627567E566C4 |
| SSDEEP: | 12:2nhTtdoMVFWwL7nq1NV1WNmvbg+zOMPFU6WNuH0jgSvJM9qBXNI:2FAMVFWwL7KXgAU6bhhMzI |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads the Internet Settings
- sdiagnhost.exe (PID: 2996)
Reads settings of System Certificates
- msdt.exe (PID: 1860)
Process drops legitimate windows executable
- msdt.exe (PID: 1860)
INFO
Checks supported languages
- wmpnscfg.exe (PID: 120)
Reads the computer name
- wmpnscfg.exe (PID: 120)
Application launched itself
- iexplore.exe (PID: 888)
Reads the machine GUID from the registry
- wmpnscfg.exe (PID: 120)
Manual execution by a user
- wmpnscfg.exe (PID: 120)
Reads security settings of Internet Explorer
- sdiagnhost.exe (PID: 2996)
- msdt.exe (PID: 1860)
Create files in a temporary directory
- msdt.exe (PID: 1860)
Creates files or folders in the user directory
- msdt.exe (PID: 1860)
Drops the executable file immediately after the start
- msdt.exe (PID: 1860)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
42
Monitored processes
5
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 120 | "C:\Program Files\Windows Media Player\wmpnscfg.exe" | C:\Program Files\Windows Media Player\wmpnscfg.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Media Player Network Sharing Service Configuration Application Exit code: 0 Version: 12.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 888 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://www.officence.com/nam/cbc2c381-2f2e-4d93-91d1-506c9316ace7/a506d8e4-15b3-4cbf-a87b-e8ca9e93b785/41791c25-30f0-473e-aee8-86d4501542f1/login?id=VTduQmFsdW9PQmZxeFA1MlV6SWxQL1luVENZN1dxRCtXTnp2R3FGNHJ5YjJTc0hVai9YUi9WVWtXRTZDd2ZkbWNmWlBYa3F0by9Id2JlQVl5Y09OWSs3dnV2L3N4R214bk80OGtoZkFPalJZSjllcjNNYituNE1udmJnaFVRelhyQ20xTk9GemJZaHFQTk1aTFJham5PSTY3L09kQXlQeS9hUE82UGR5dTV6cTk0VklVVDExbmpTMWhwYStYOWppSGViV0NhMS85NnZpY3JjTE56UFZ2UEszUkM3cDFoRjJqOEwzQ0ZNQnNYZDQyYnVjZUowTWEzb2FLRTVJaHRRK2xkQzVyekFvZ1NSQUNGT2YvV2N0RVVuVWRtY2g1OUJEbWlWRmsvajJjbElkMFZoR1lBWXVQZXFKL1FoejlLRHFpVnM1QUxNWUNHTngrbC91TEZhL1VWSkorNU5KMTQ0SUNJSnMzR1AvY1Jxdy9ZTGc0Z2lyK3ZIRnJ6OFErbFUv" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
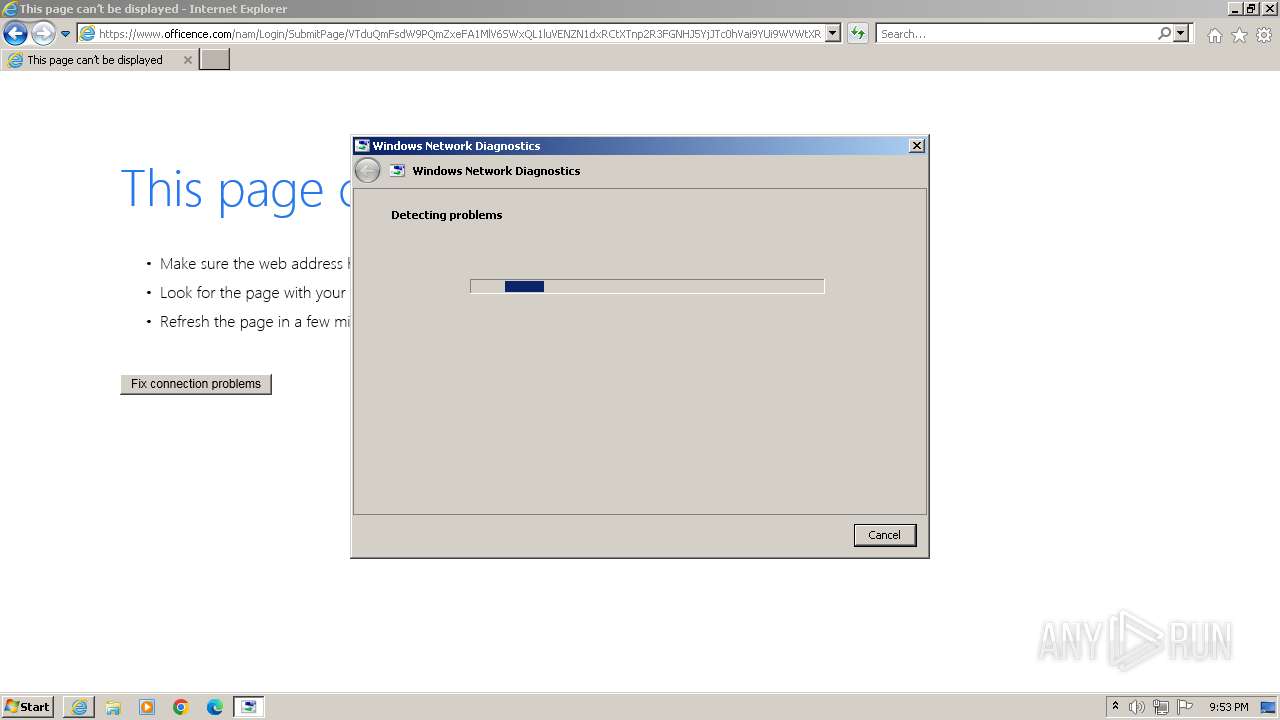
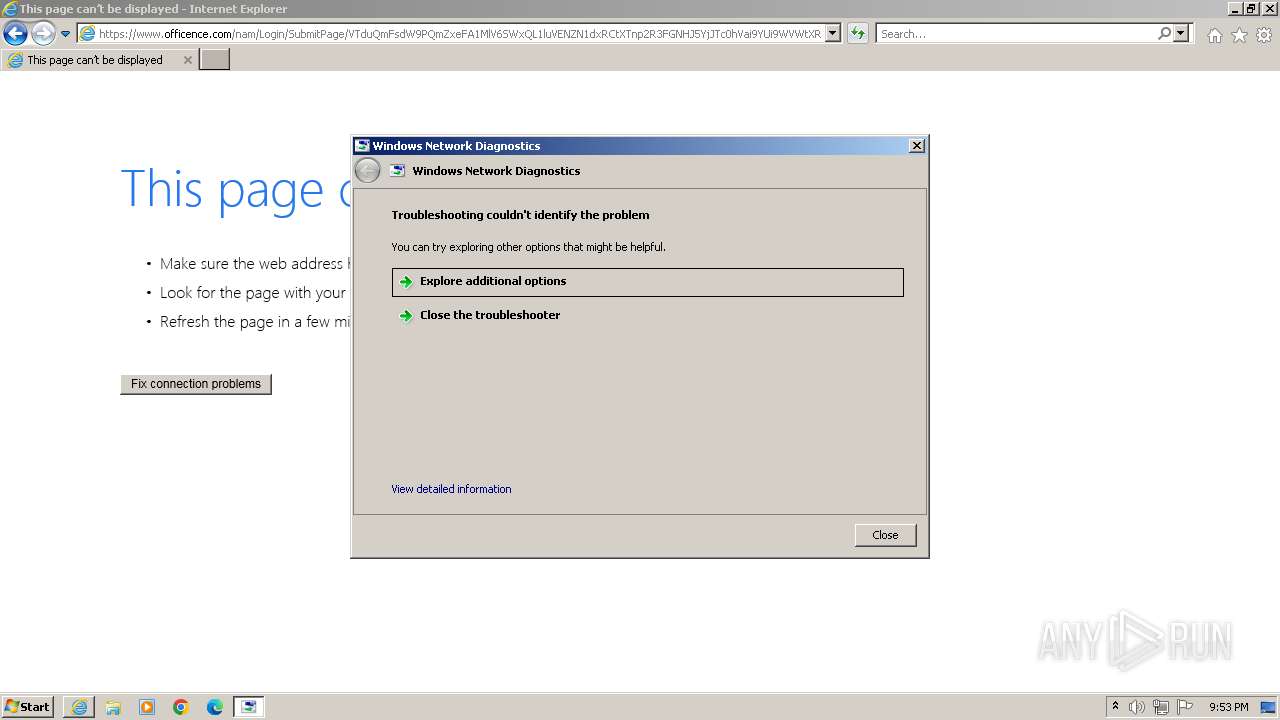
| 1860 | -modal 655678 -skip TRUE -path C:\Windows\diagnostics\system\networking -af C:\Users\admin\AppData\Local\Temp\NDF7FC6.tmp -ep NetworkDiagnosticsWeb | C:\Windows\System32\msdt.exe | — | iexplore.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Diagnostics Troubleshooting Wizard Exit code: 2 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2996 | C:\Windows\System32\sdiagnhost.exe -Embedding | C:\Windows\System32\sdiagnhost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Scripted Diagnostics Native Host Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3376 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:888 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
19 690
Read events
19 607
Write events
78
Delete events
5
Modification events
| (PID) Process: | (888) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 0 | |||
| (PID) Process: | (888) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30847387 | |||
| (PID) Process: | (888) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30847437 | |||
| (PID) Process: | (888) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (888) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (888) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (888) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (888) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (888) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (888) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
Executable files
2
Suspicious files
26
Text files
32
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3376 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | compressed | |
MD5:1BFE591A4FE3D91B03CDF26EAACD8F89 | SHA256:9CF94355051BF0F4A45724CA20D1CC02F76371B963AB7D1E38BD8997737B13D8 | |||
| 3376 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:40958E9D1DC78DA3F6048B98EC91F46E | SHA256:47F25D77AE10357AD7785A5B222F51023F75F4966C334C2CDD8D449ADA792D04 | |||
| 3376 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\7423F88C7F265F0DEFC08EA88C3BDE45_AA1E8580D4EBC816148CE81268683776 | binary | |
MD5:5B4D745BD294BEC7A2AF2FE32696C3A5 | SHA256:CA61517067B336AA65EE6E0D568B296F96B758043E5907096FC923158DCB59B5 | |||
| 3376 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\login[1].htm | html | |
MD5:FED064F2CAAF3935E3556144F4208CFC | SHA256:8C59934A57178B9C3C57B1B0BCFEDF077D8069AEF6E2ECC210DAA364D64803AC | |||
| 3376 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\2CB6B8BACCDF3D4DD9099BF71ACA4698_1237606A05AC04F9F4FBDB1AD57B72A8 | binary | |
MD5:F928FA2D4476C0BE9014D13CFD2D7865 | SHA256:ED84C74CFF64BE069D1C147273CDF21F940BFB239BEF2BC73D760E078A389981 | |||
| 3376 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\5IWPIAR9\2_bc3d32a696895f78c19df6c717586a5d[1].svg | image | |
MD5:BC3D32A696895F78C19DF6C717586A5D | SHA256:0E88B6FCBB8591EDFD28184FA70A04B6DD3AF8A14367C628EDD7CABA32E58C68 | |||
| 3376 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\7423F88C7F265F0DEFC08EA88C3BDE45_AA1E8580D4EBC816148CE81268683776 | binary | |
MD5:82D5B7E494ADC3C7FFA151D934CA1C27 | SHA256:AFA14ED349AD202C20A708254D7DB8E7C1BE389A7548747204494B6E4FFDCAE4 | |||
| 3376 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\signin-options_4e48046ce74f4b89d45037c90576bfac[1].svg | image | |
MD5:4E48046CE74F4B89D45037C90576BFAC | SHA256:8E6DB1634F1812D42516778FC890010AA57F3E39914FB4803DF2C38ABBF56D93 | |||
| 3376 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\jquery-3.5.1.min[1].js | text | |
MD5:B61AA6E2D68D21B3546B5B418BF0E9C3 | SHA256:F36844906AD2309877AAE3121B87FB15B9E09803CB4C333ADC7E1E35AC92E14B | |||
| 3376 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\E2C6CBAF0AF08CF203BA74BF0D0AB6D5_CBDCCBFE4F7A916411C1E69BDD97BB04 | binary | |
MD5:600AF3E7E8A39A6D5163060C4941D95D | SHA256:E2829DF9467059FA25D31A7719A0B291951B3A69FF105E3B60E40685917CB88A | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
23
DNS requests
25
Threats
8
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3376 | iexplore.exe | GET | 200 | 184.24.77.197:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?e925f9b3981bfc0f | unknown | compressed | 4.66 Kb | unknown |
3376 | iexplore.exe | GET | 200 | 184.24.77.197:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?f2969c510caf3352 | unknown | compressed | 4.66 Kb | unknown |
3376 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEApDqVCbATUviZV57HIIulA%3D | unknown | binary | 471 b | unknown |
3376 | iexplore.exe | GET | 200 | 204.79.197.203:80 | http://oneocsp.microsoft.com/ocsp/MFQwUjBQME4wTDAJBgUrDgMCGgUABBR2JNtr0JxEvYySpbyBWaqBmealCgQUzhUWO%2BoCo6Zr2tkr%2FeWMUr56UKgCEzMAD45SWTeIqR%2Fbw4cAAAAPjlI%3D | unknown | binary | 1.74 Kb | unknown |
1080 | svchost.exe | GET | 304 | 184.24.77.197:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?5312bc669adcb130 | unknown | — | — | unknown |
3376 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | binary | 471 b | unknown |
1080 | svchost.exe | GET | — | 184.24.77.197:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?d3beddd762d67162 | unknown | — | — | unknown |
888 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAzlnDD9eoNTLi0BRrMy%2BWU%3D | unknown | binary | 313 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
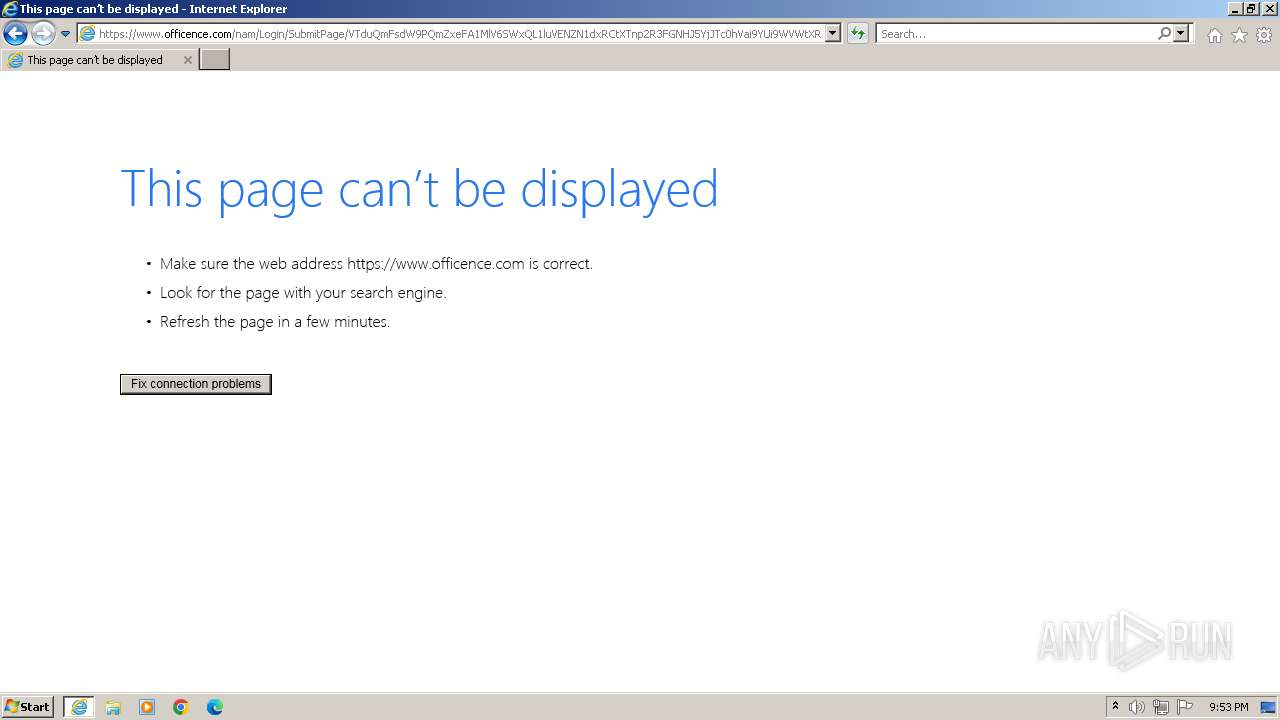
3376 | iexplore.exe | 13.107.246.44:443 | www.officence.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
2588 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
3376 | iexplore.exe | 184.24.77.197:80 | ctldl.windowsupdate.com | Akamai International B.V. | DE | unknown |
3376 | iexplore.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
3376 | iexplore.exe | 204.79.197.203:80 | oneocsp.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
1080 | svchost.exe | 184.24.77.197:80 | ctldl.windowsupdate.com | Akamai International B.V. | DE | unknown |
888 | iexplore.exe | 13.107.246.44:443 | www.officence.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.officence.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
oneocsp.microsoft.com |
| whitelisted |
aadcdn.msauth.net |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
r20swj13mr.microsoft.com |
| whitelisted |
iecvlist.microsoft.com |
| unknown |
dns.msftncsi.com |
| shared |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1080 | svchost.exe | Misc activity | ET INFO Microsoft Attack Simulation Training Domain in DNS Lookup (officence .com) |
3376 | iexplore.exe | Misc activity | ET INFO Observed Microsoft Attack Simulation Training SSL Cert (attemplate .com) |
3376 | iexplore.exe | Misc activity | ET INFO Observed Microsoft Attack Simulation Training SSL Cert (attemplate .com) |
3376 | iexplore.exe | Misc activity | ET INFO Observed Microsoft Attack Simulation Training SSL Cert (attemplate .com) |
3376 | iexplore.exe | Misc activity | ET INFO Observed Microsoft Attack Simulation Training SSL Cert (attemplate .com) |
888 | iexplore.exe | Misc activity | ET INFO Observed Microsoft Attack Simulation Training SSL Cert (attemplate .com) |
888 | iexplore.exe | Misc activity | ET INFO Observed Microsoft Attack Simulation Training SSL Cert (attemplate .com) |
3376 | iexplore.exe | Misc activity | ET INFO Observed Microsoft Attack Simulation Training SSL Cert (attemplate .com) |