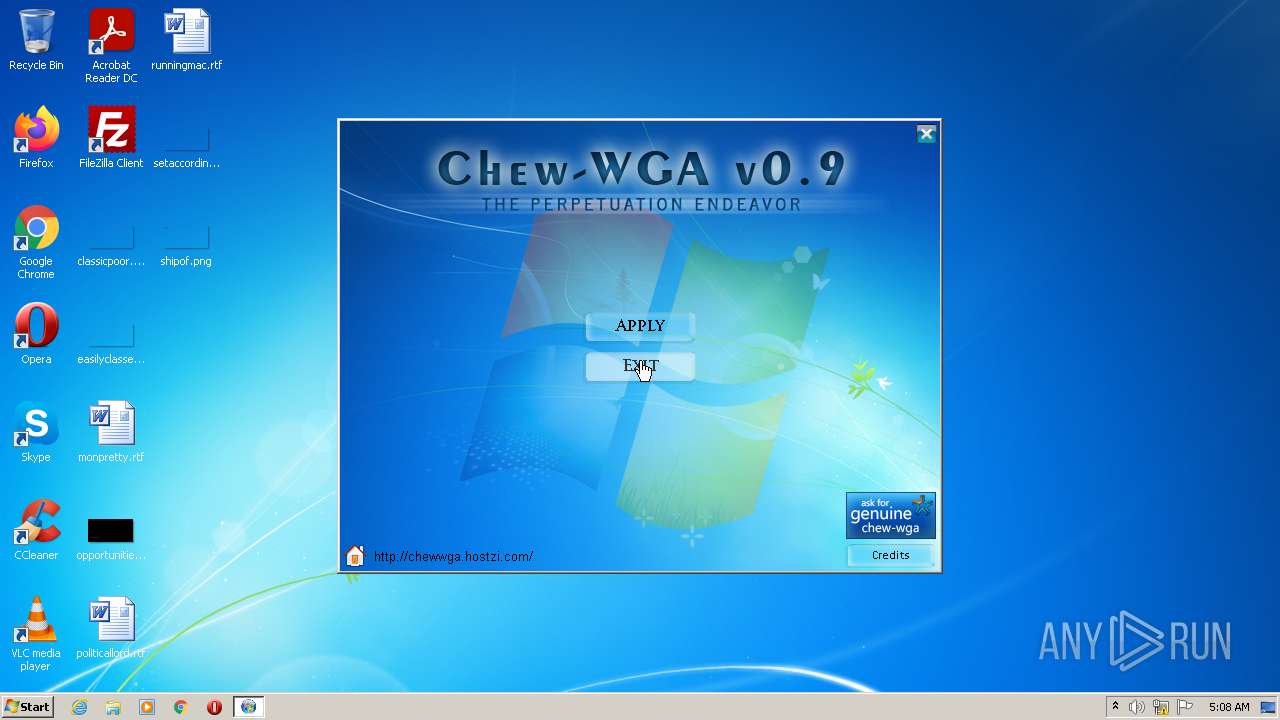
| File name: | Chew-WGA v0.9.eXe |
| Full analysis: | https://app.any.run/tasks/addd4cab-7faa-4b8b-bd3f-fe520c9485c5 |
| Verdict: | Malicious activity |
| Analysis date: | July 01, 2022, 04:08:25 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 6738D790FC0F3928A8A5F19D829CAE4D |
| SHA1: | DB0A727520178061506C7EC07A99BAC581610329 |
| SHA256: | 60CA507EF4BA7DBBB7EF6EA4B975B9B09A24D7D0C91D38D0876331203F962D98 |
| SSDEEP: | 196608:9O1vl2I4a7SdzRDymXLa4mnb0DtUog3jCUE2nKNfMILF9UBDHLSwxT1aQhS:Wt2O7Sd1ymX+4mnOU9+UCZM6kzWu12 |
MALICIOUS
Application was dropped or rewritten from another process
- autorun.exe (PID: 3964)
Drops executable file immediately after starts
- Chew-WGA v0.9.eXe (PID: 536)
SUSPICIOUS
Reads the computer name
- autorun.exe (PID: 3964)
Checks supported languages
- Chew-WGA v0.9.eXe (PID: 536)
- autorun.exe (PID: 3964)
Executable content was dropped or overwritten
- Chew-WGA v0.9.eXe (PID: 536)
Drops a file with a compile date too recent
- Chew-WGA v0.9.eXe (PID: 536)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (35.8) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (31.7) |
| .scr | | | Windows screen saver (15) |
| .dll | | | Win32 Dynamic Link Library (generic) (7.5) |
| .exe | | | Win32 Executable (generic) (5.1) |
EXIF
EXE
| ProductVersion: | 0.9.0.0 |
|---|---|
| ProductName: | Chew-WGA v0.9 |
| OriginalFileName: | cw.exe |
| LegalTrademarks: | Chew-WGA |
| LegalCopyright: | Copyright (c) 2009 - Anemeros Software |
| InternalName: | ams60_launch |
| FileVersion: | 0.9.0.0 |
| FileDescription: | The Perpetuation Endeavor |
| CompanyName: | Anemeros Software |
| Comments: | Created with AutoPlay Media Studio (www.indigorose.com) |
| CharacterSet: | ASCII |
| LanguageCode: | English (U.S.) |
| FileSubtype: | - |
| ObjectFileType: | Executable application |
| FileOS: | Win32 |
| FileFlags: | (none) |
| FileFlagsMask: | 0x0000 |
| ProductVersionNumber: | 0.9.0.0 |
| FileVersionNumber: | 0.9.0.0 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 4 |
| ImageVersion: | - |
| OSVersion: | 4 |
| EntryPoint: | 0x173a6 |
| UninitializedDataSize: | - |
| InitializedDataSize: | 458752 |
| CodeSize: | 192512 |
| LinkerVersion: | 6 |
| PEType: | PE32 |
| TimeStamp: | 2009:06:23 19:57:07+02:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 23-Jun-2009 17:57:07 |
| Detected languages: |
|
| Comments: | Created with AutoPlay Media Studio (www.indigorose.com) |
| CompanyName: | Anemeros Software |
| FileDescription: | The Perpetuation Endeavor |
| FileVersion: | 0.9.0.0 |
| InternalName: | ams60_launch |
| LegalCopyright: | Copyright (c) 2009 - Anemeros Software |
| LegalTrademarks: | Chew-WGA |
| OriginalFilename: | cw.exe |
| ProductName: | Chew-WGA v0.9 |
| ProductVersion: | 0.9.0.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000F0 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 4 |
| Time date stamp: | 23-Jun-2009 17:57:07 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0002E906 | 0x0002F000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.60114 |
.rdata | 0x00030000 | 0x0000842E | 0x00009000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.57824 |
.data | 0x00039000 | 0x00009D08 | 0x00006000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.67512 |
.rsrc | 0x00043000 | 0x000609FC | 0x00061000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.60247 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.02016 | 901 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 5.77242 | 4264 | Latin 1 / Western European | English - United States | RT_ICON |
3 | 5.67191 | 9640 | Latin 1 / Western European | English - United States | RT_ICON |
4 | 5.61132 | 16936 | Latin 1 / Western European | English - United States | RT_ICON |
5 | 5.54801 | 67624 | Latin 1 / Western European | English - United States | RT_ICON |
6 | 5.5135 | 270376 | Latin 1 / Western European | English - United States | RT_ICON |
7 | 5.44696 | 3752 | Latin 1 / Western European | English - United States | RT_ICON |
8 | 4.26041 | 9640 | Latin 1 / Western European | English - United States | RT_ICON |
9 | 3.02695 | 308 | Latin 1 / Western European | English - United States | RT_CURSOR |
10 | 2.74274 | 180 | Latin 1 / Western European | English - United States | RT_CURSOR |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
WINSPOOL.DRV |
comdlg32.dll |
Total processes
39
Monitored processes
3
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 536 | "C:\Users\admin\AppData\Local\Temp\Chew-WGA v0.9.eXe" | C:\Users\admin\AppData\Local\Temp\Chew-WGA v0.9.eXe | Explorer.EXE | ||||||||||||
User: admin Company: Anemeros Software Integrity Level: HIGH Description: The Perpetuation Endeavor Exit code: 0 Version: 0.9.0.0 Modules
| |||||||||||||||
| 3100 | "C:\Users\admin\AppData\Local\Temp\Chew-WGA v0.9.eXe" | C:\Users\admin\AppData\Local\Temp\Chew-WGA v0.9.eXe | — | Explorer.EXE | |||||||||||
User: admin Company: Anemeros Software Integrity Level: MEDIUM Description: The Perpetuation Endeavor Exit code: 3221226540 Version: 0.9.0.0 Modules
| |||||||||||||||
| 3964 | "C:\Users\admin\AppData\Local\Temp\ir_ext_temp_0\autorun.exe" "SFXSOURCE:C:\Users\admin\AppData\Local\Temp\Chew-WGA v0.9.eXe" | C:\Users\admin\AppData\Local\Temp\ir_ext_temp_0\autorun.exe | — | Chew-WGA v0.9.eXe | |||||||||||
User: admin Company: Anemeros Software Integrity Level: HIGH Description: The Perpetuation Endeavor Exit code: 0 Version: 0.9.0.0 Modules
| |||||||||||||||
Total events
373
Read events
371
Write events
2
Delete events
0
Modification events
| (PID) Process: | (3964) autorun.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Control\MediaResources\DirectSound\Speaker Configuration |
| Operation: | write | Name: | Speaker Configuration |
Value: 4 | |||
Executable files
2
Suspicious files
8
Text files
15
Unknown types
6
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 536 | Chew-WGA v0.9.eXe | C:\Users\admin\AppData\Local\Temp\ir_ext_temp_0\AutoPlay\Audio\Click1.ogg | ogg | |
MD5:93270C4FA492E4E4EDEE872A2B961DDE | SHA256:25D49CBBD65D48AD462455F1143F73EE997DF8F747E7D2213DAAB18E321C028B | |||
| 536 | Chew-WGA v0.9.eXe | C:\Users\admin\AppData\Local\Temp\ir_ext_temp_0\AutoPlay\Buttons\Sol-4.Btn | compressed | |
MD5:AAD23F06616570B7DCD713B320217179 | SHA256:4C7218EE657EA5301FB87A0F9AB282E9002B0C2B2EAED4AF3DD9E7CCA2E72613 | |||
| 536 | Chew-WGA v0.9.eXe | C:\Users\admin\AppData\Local\Temp\ir_ext_temp_0\AutoPlay\Images\done-uninstall.jpg | image | |
MD5:106FE981FD196C92AE2FF5CB4ABEF95B | SHA256:F85F3427B268DA26269D4F17BABA8989F6479F6FAF6622F36D8F89F5206C4768 | |||
| 536 | Chew-WGA v0.9.eXe | C:\Users\admin\AppData\Local\Temp\ir_ext_temp_0\AutoPlay\Audio\Shekere.ogg | ogg | |
MD5:2B1395C376D645D076CE7E2171EF9C7F | SHA256:F8D1022DEE83BF00C33AD160F4085464CA5818CA186C909030FDA3F6D9C71A79 | |||
| 536 | Chew-WGA v0.9.eXe | C:\Users\admin\AppData\Local\Temp\ir_ext_temp_0\AutoPlay\Images\done-install.jpg | image | |
MD5:B6479C2EC0E8353D8BA175D6D783612B | SHA256:457B13621CC0B8C07B048CAD8761DF175C3FEBC8B8E457789FDD88FEEDE20A83 | |||
| 536 | Chew-WGA v0.9.eXe | C:\Users\admin\AppData\Local\Temp\ir_ext_temp_0\AutoPlay\Audio\High1.ogg | ogg | |
MD5:FC2A595F574B1EAD82A6DCF06492C985 | SHA256:EE9A4903A8DF90EFF4C5B65A8073E564A3581CF73772A72EB82396E69932E769 | |||
| 536 | Chew-WGA v0.9.eXe | C:\Users\admin\AppData\Local\Temp\ir_ext_temp_0\AutoPlay\Buttons\Baslat.Btn | compressed | |
MD5:DB33064E86D7E634CB842DD2918A3E05 | SHA256:05FFCFCA2AAD8509C6A16FFBCC727F290449956E9884495D86045A129331B0A4 | |||
| 536 | Chew-WGA v0.9.eXe | C:\Users\admin\AppData\Local\Temp\ir_ext_temp_0\AutoPlay\Icons\mainicon.ico | image | |
MD5:31ACA1A1047EFBC8D2A6E22101B2227B | SHA256:A9EAAFA2C8E36BB80F58D5930694676D76DAB647B8F709F3142649BB8018FBFA | |||
| 536 | Chew-WGA v0.9.eXe | C:\Users\admin\AppData\Local\Temp\ir_ext_temp_0\AutoPlay\Images\main-screen.jpg | image | |
MD5:16ACE5798F3499D9685197740CD00735 | SHA256:0C88A592CB5448D2131A15F208580365CF383A2445ED60CA55987F42ECC4CE11 | |||
| 536 | Chew-WGA v0.9.eXe | C:\Users\admin\AppData\Local\Temp\ir_ext_temp_0\AutoPlay\Images\genuine-chew.jpg | image | |
MD5:2E2AC2C68EF9ED0E14108208DC6880BB | SHA256:510ACF5A6CE7E9570A591A48951161341DE4F1DA13E0117AB4AA6832E5BDDB97 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report