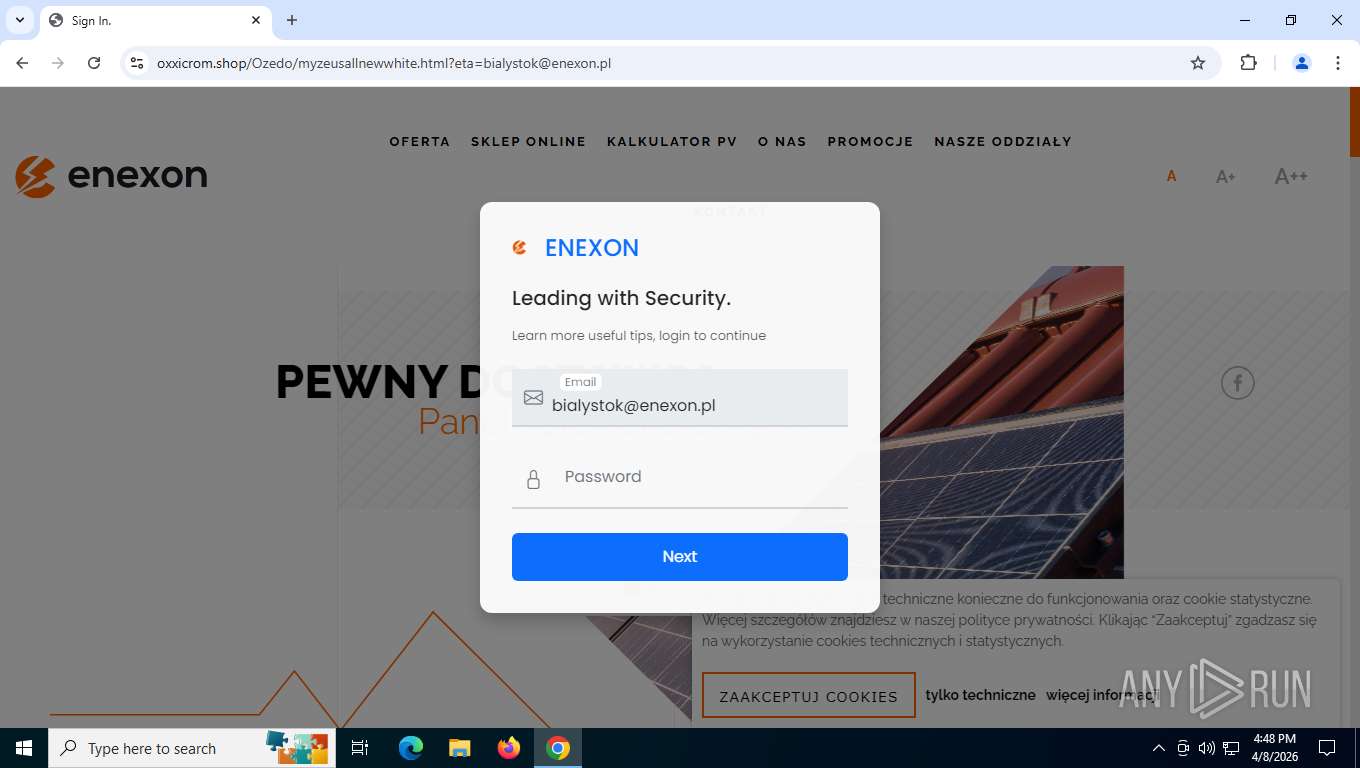
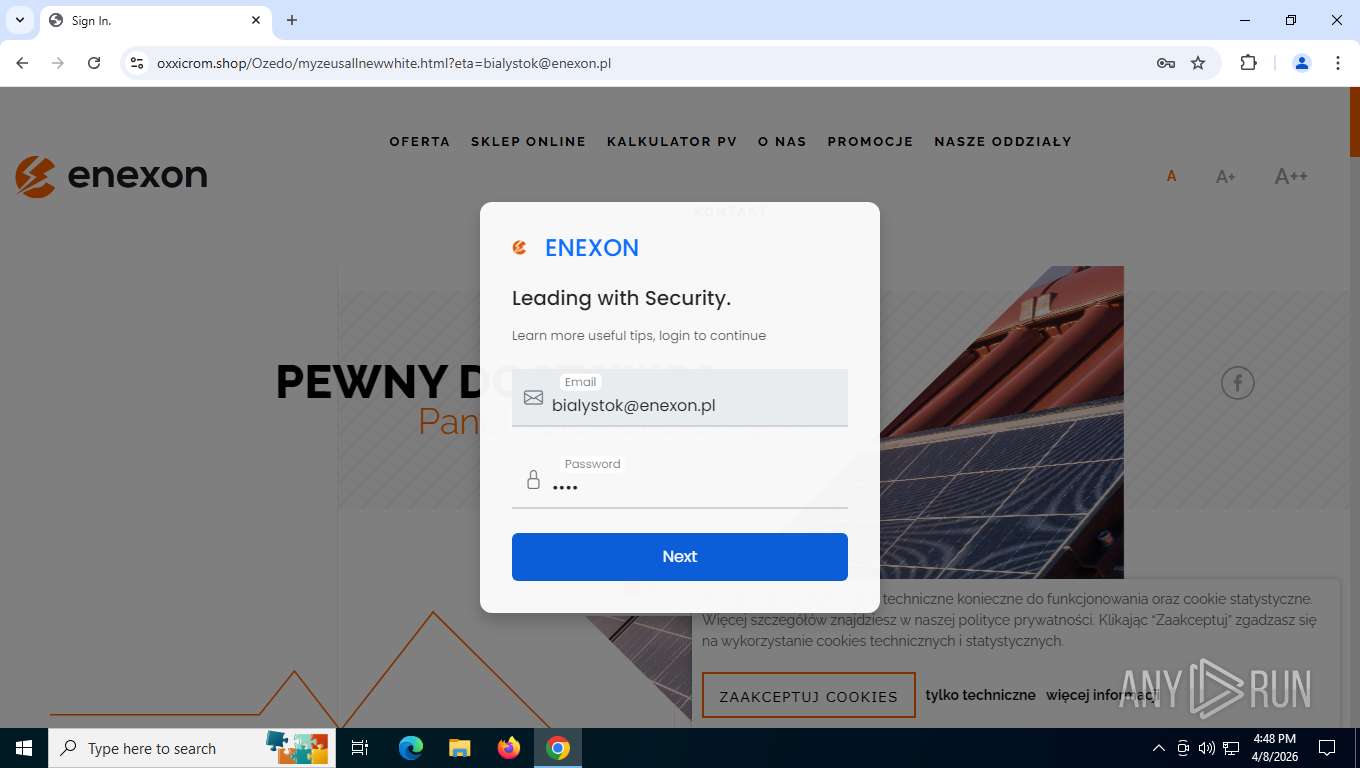
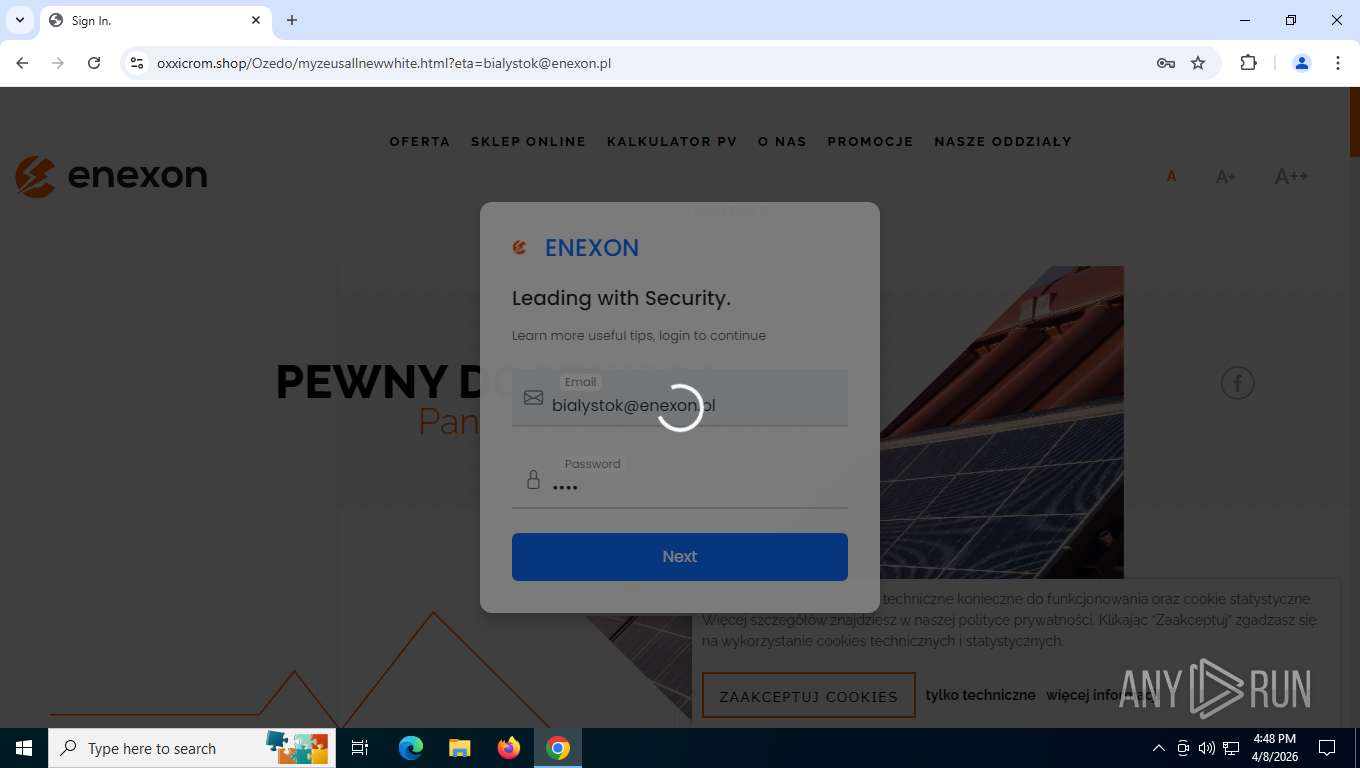
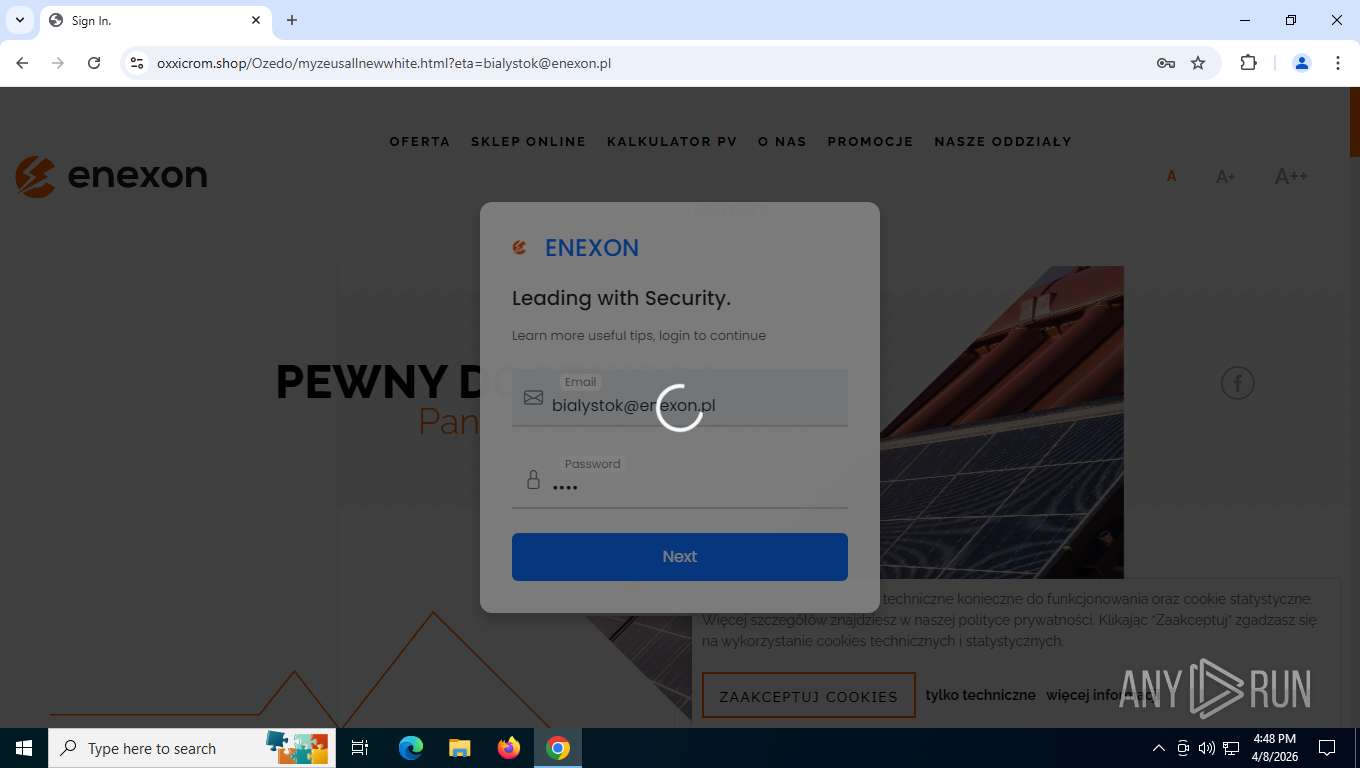
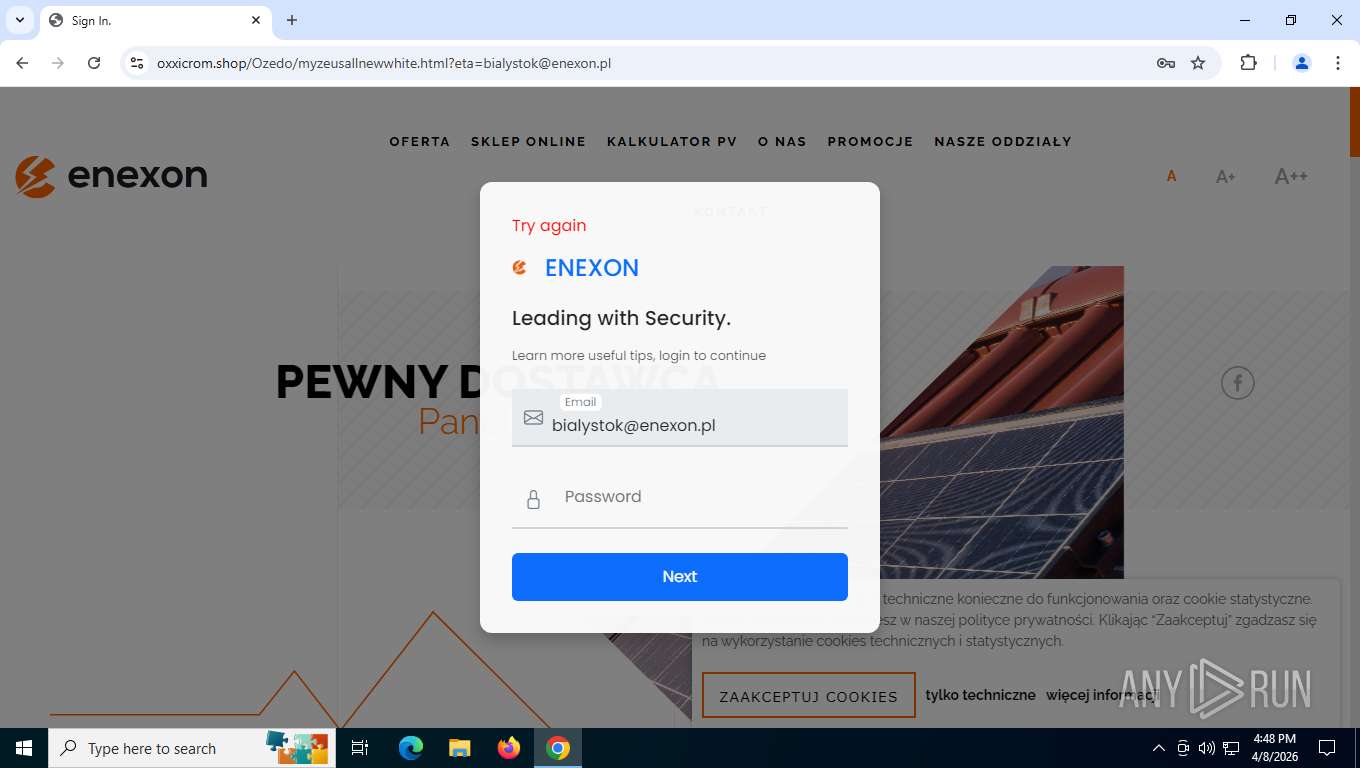
| URL: | https://oxxicrom.shop/Ozedo/myzeusallnewwhite.html?eta=bialystok@enexon.pl |
| Full analysis: | https://app.any.run/tasks/286a5b00-ac12-44d6-8305-df55e0226bac |
| Verdict: | Malicious activity |
| Analysis date: | April 08, 2026, 20:48:21 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | F25F93ACE947FE8E929C431DF2DE2D1F |
| SHA1: | 01A3B7D86DD7C27745FBABD1A70ECC61BDC631B1 |
| SHA256: | 60B814F90DF9DF17588EB33DCEC5D0AEC080761BB8A3BE620C3D2ED229443960 |
| SSDEEP: | 3:N8UOGXHzKqfAsPQwomP0aAiqzikKJn:2UOGjKkAidAi/kS |
MALICIOUS
PHISHING has been detected (SURICATA)
- chrome.exe (PID: 4300)
SUSPICIOUS
No suspicious indicators.INFO
Application launched itself
- chrome.exe (PID: 2684)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
157
Monitored processes
28
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 784 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --string-annotations --enable-dinosaur-easter-egg-alt-images --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --device-scale-factor=1 --num-raster-threads=3 --enable-main-frame-before-activation --renderer-client-id=9 --field-trial-handle=5744,i,14968465545928635059,1690386868321603067,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version=20251218-201203.402000 --mojo-platform-channel-handle=5588 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Version: 133.0.6943.127 Modules
| |||||||||||||||
| 1500 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --disable-quic --string-annotations --field-trial-handle=6112,i,14968465545928635059,1690386868321603067,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version=20251218-201203.402000 --mojo-platform-channel-handle=5656 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 1536 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --field-trial-handle=6008,i,14968465545928635059,1690386868321603067,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version=20251218-201203.402000 --mojo-platform-channel-handle=4820 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 1684 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --disable-quic --string-annotations --field-trial-handle=5400,i,14968465545928635059,1690386868321603067,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version=20251218-201203.402000 --mojo-platform-channel-handle=6132 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 1904 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --field-trial-handle=6076,i,14968465545928635059,1690386868321603067,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version=20251218-201203.402000 --mojo-platform-channel-handle=6056 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 2576 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --disable-quic --string-annotations --field-trial-handle=5860,i,14968465545928635059,1690386868321603067,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version=20251218-201203.402000 --mojo-platform-channel-handle=4904 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 2576 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --disable-quic --string-annotations --field-trial-handle=5684,i,14968465545928635059,1690386868321603067,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version=20251218-201203.402000 --mojo-platform-channel-handle=4892 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 2684 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --disable-features=HttpsUpgrades,HttpsFirstModeV2,HttpsOnlyMode,HttpsFirstBalancedMode --no-first-run --no-default-browser-check https://oxxicrom.shop/Ozedo/myzeusallnewwhite.html?eta=bialystok@enexon.pl | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Version: 133.0.6943.127 Modules
| |||||||||||||||
| 2692 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win64 --annotation=prod=Chrome --annotation=ver=133.0.6943.127 --initial-client-data=0x21c,0x220,0x224,0x1f8,0x228,0x7ffe2388fff8,0x7ffe23890004,0x7ffe23890010 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Version: 133.0.6943.127 Modules
| |||||||||||||||
| 2724 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --field-trial-handle=5708,i,14968465545928635059,1690386868321603067,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version=20251218-201203.402000 --mojo-platform-channel-handle=6104 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
Total events
0
Read events
0
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
36
Text files
36
Unknown types
109
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2684 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\ClientCertificates\LOG.old~RFe0192.TMP | — | |
MD5:— | SHA256:— | |||
| 2684 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\ClientCertificates\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2684 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old~RFe01a1.TMP | — | |
MD5:— | SHA256:— | |||
| 2684 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2684 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old~RFe01a1.TMP | — | |
MD5:— | SHA256:— | |||
| 2684 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Segmentation Platform\SegmentInfoDB\LOG.old~RFe0192.TMP | — | |
MD5:— | SHA256:— | |||
| 2684 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old~RFe01a1.TMP | — | |
MD5:— | SHA256:— | |||
| 2684 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Segmentation Platform\SegmentInfoDB\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2684 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2684 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\LOG.old~RFe01a1.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
171
TCP/UDP connections
74
DNS requests
82
Threats
21
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.55.110.193:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | NL | binary | 825 b | whitelisted |
— | — | GET | 200 | 23.52.181.212:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | US | binary | 814 b | whitelisted |
4300 | chrome.exe | GET | 200 | 142.250.154.94:443 | https://clientservices.googleapis.com/chrome-variations/seed?osname=win&channel=stable&milestone=133 | US | compressed | 88.8 Kb | whitelisted |
4300 | chrome.exe | GET | 200 | 142.251.127.102:80 | http://clients2.google.com/time/1/current?cup2key=8:FntnLqGwaY77wwfXlMhpqEg4WAVQmJ3Y3FSaj0yX-vg&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | US | binary | 105 b | whitelisted |
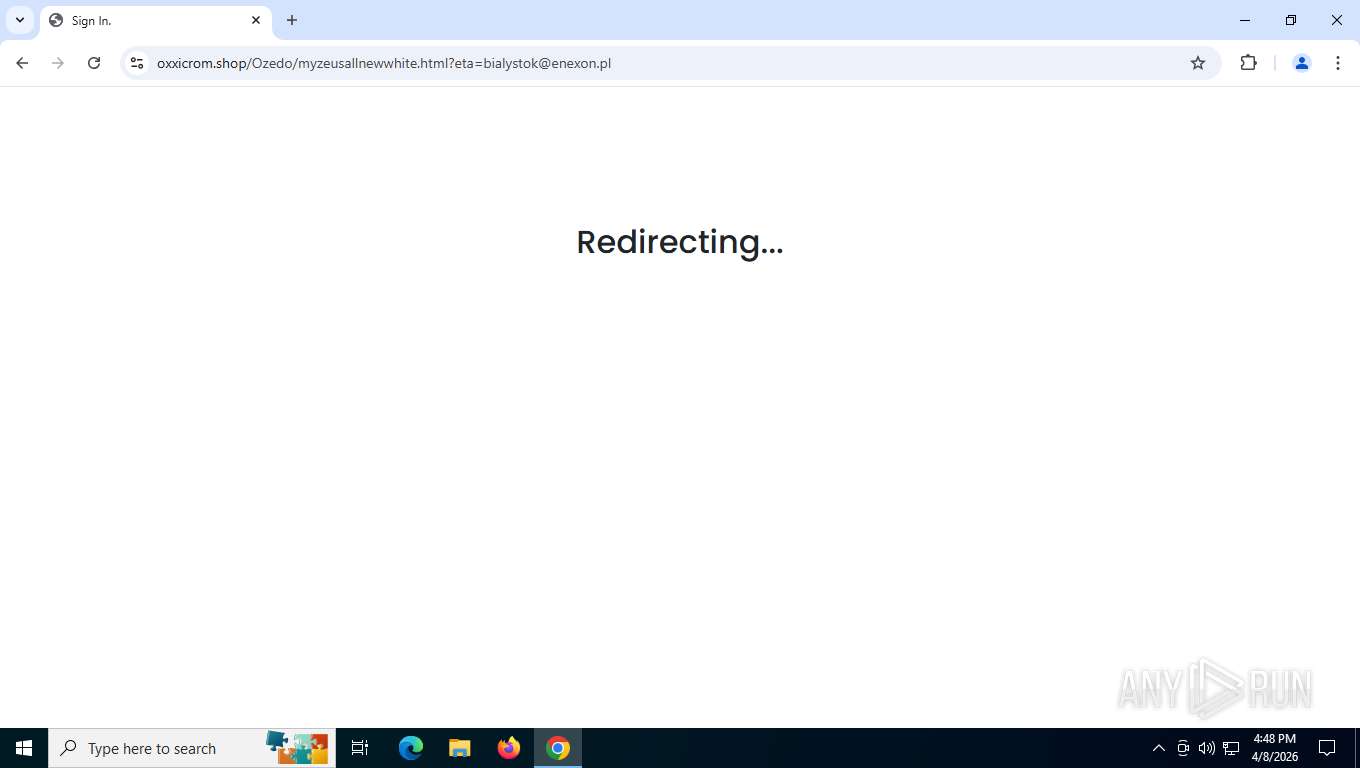
4300 | chrome.exe | GET | 302 | 188.114.97.3:443 | https://oxxicrom.shop/Ozedo/myzeusallnewwhite.html?eta=bialystok@enexon.pl | US | binary | 142 b | malicious |
4300 | chrome.exe | GET | 200 | 188.114.97.3:443 | https://oxxicrom.shop/favicon.ico | US | binary | 1.24 Kb | malicious |
4300 | chrome.exe | GET | 200 | 188.114.97.3:443 | https://oxxicrom.shop/?v=9f8d&session=12f32bf829df55143edaae13fe6222e6&cid=888d828896294d4a&iat=1775681309&loc=US&build=6.1.0 | US | binary | 6.51 Kb | malicious |
4300 | chrome.exe | GET | 200 | 188.114.97.3:443 | https://oxxicrom.shop/Ozedo/myzeusallnewwhite.html?eta=bialystok@enexon.pl | US | binary | 1.24 Kb | malicious |
4300 | chrome.exe | GET | 200 | 142.251.127.95:443 | https://safebrowsingohttpgateway.googleapis.com/v1/ohttp/hpkekeyconfig?key=AIzaSyA2KlwBX3mkFo30om9LUFYQhpqLoa_BNhE | US | binary | 41 b | whitelisted |
4300 | chrome.exe | POST | 200 | 142.251.127.84:443 | https://accounts.google.com/ListAccounts?gpsia=1&source=ChromiumBrowser&json=standard | US | text | 17 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
6076 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:137 | — | Not routed | — | whitelisted |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
— | — | 23.55.110.193:80 | crl.microsoft.com | AKAMAI-ASN1 | NL | whitelisted |
— | — | 23.52.181.212:80 | www.microsoft.com | AKAMAI-AS | US | whitelisted |
— | — | 48.192.1.65:443 | activation-v2.sls.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:138 | — | Not routed | — | whitelisted |
4300 | chrome.exe | 142.251.127.102:80 | clients2.google.com | GOOGLE | US | whitelisted |
4300 | chrome.exe | 142.251.127.95:443 | safebrowsingohttpgateway.googleapis.com | GOOGLE | US | whitelisted |
4300 | chrome.exe | 142.250.154.94:443 | clientservices.googleapis.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
clients2.google.com |
| whitelisted |
safebrowsingohttpgateway.googleapis.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
oxxicrom.shop |
| unknown |
accounts.google.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
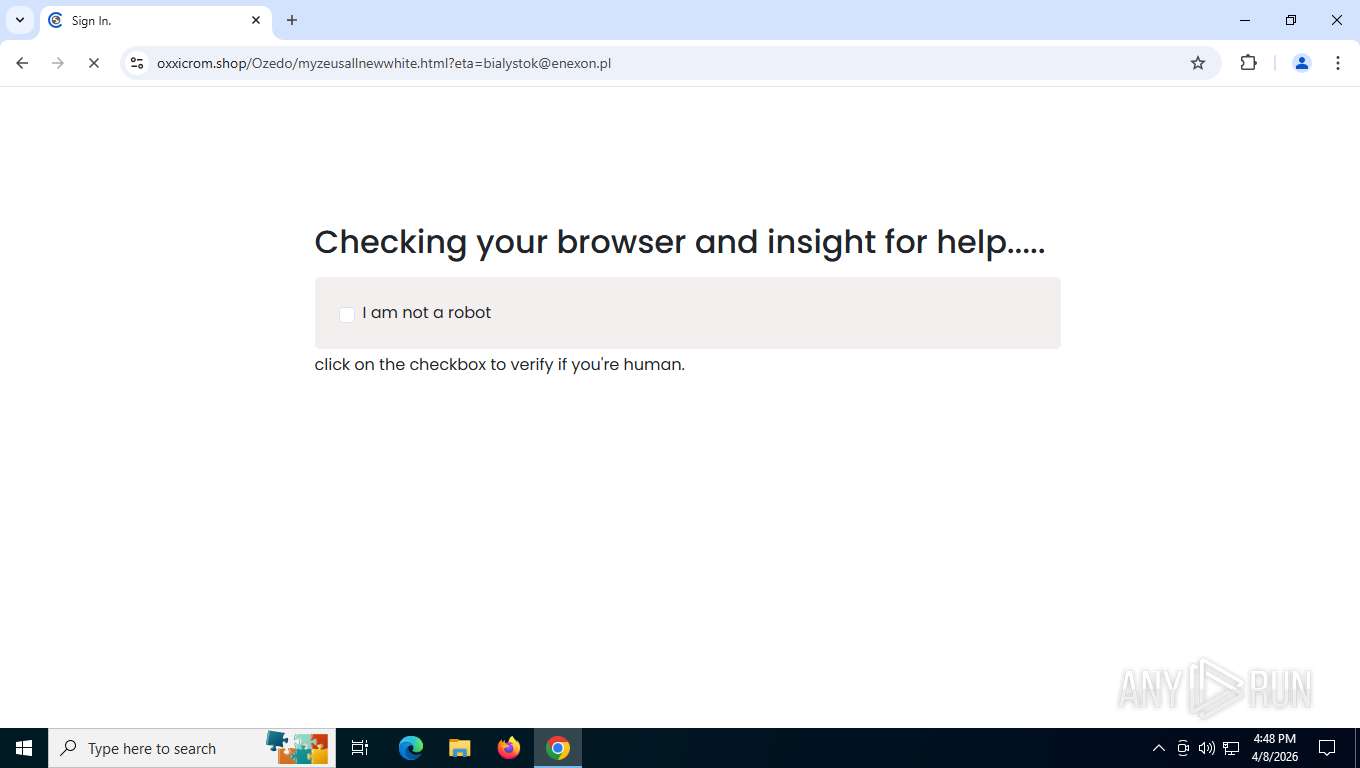
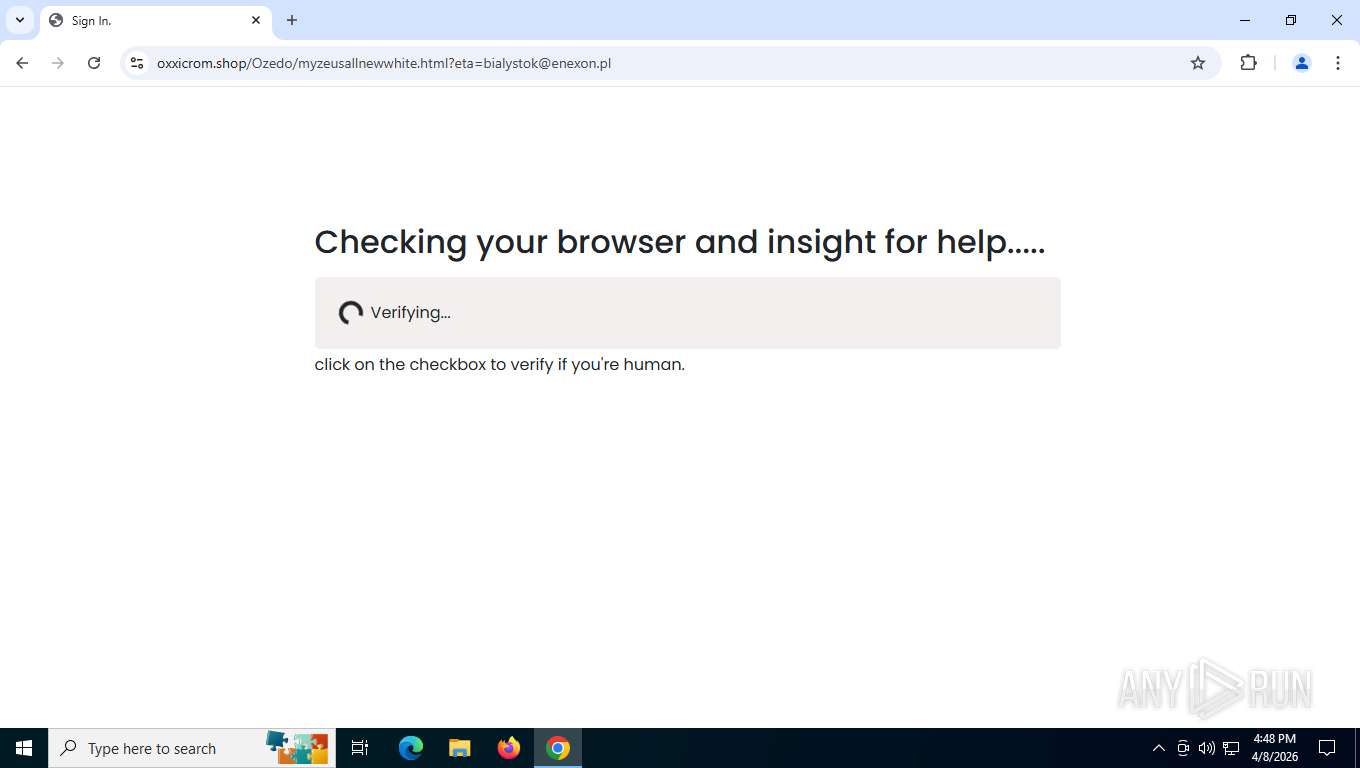
4300 | chrome.exe | Possible Social Engineering Attempted | PHISHING [ANY.RUN] Fake CAPTCHA Redirect Page URL Pattern |
4300 | chrome.exe | Possible Social Engineering Attempted | PHISHING [ANY.RUN] Fake CAPTCHA Redirect Page URL Pattern |
4300 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |
4300 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |
4300 | chrome.exe | Misc activity | ET INFO External IP Lookup Domain (ipify .org) in DNS Lookup |
4300 | chrome.exe | Misc activity | ET INFO External IP Lookup Domain (ipify .org) in DNS Lookup |
4300 | chrome.exe | Misc activity | ET INFO External IP Address Lookup Domain (ipify .org) in TLS SNI |
4300 | chrome.exe | A Network Trojan was detected | ET MALWARE RMM Payload Delivery Behvaior Observed in HTTP Cookies |
4300 | chrome.exe | A Network Trojan was detected | ET MALWARE RMM Payload Delivery Behvaior Observed in HTTP Cookies |
4300 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |