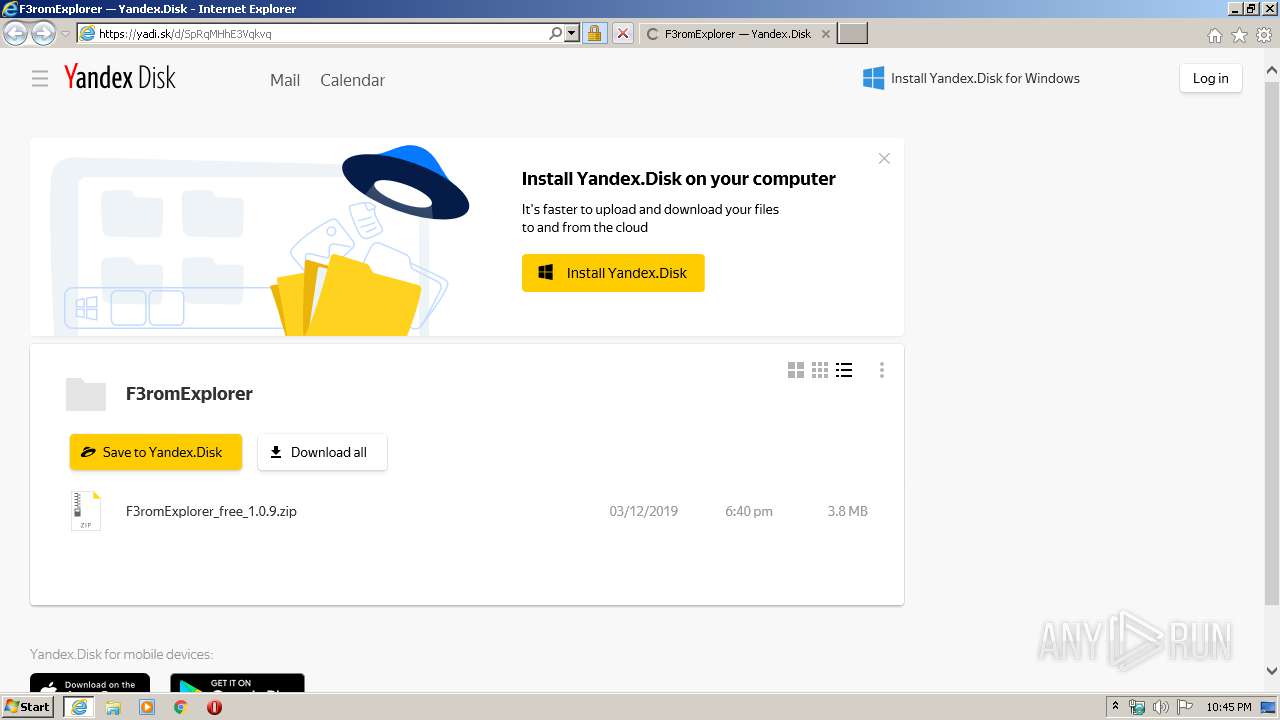
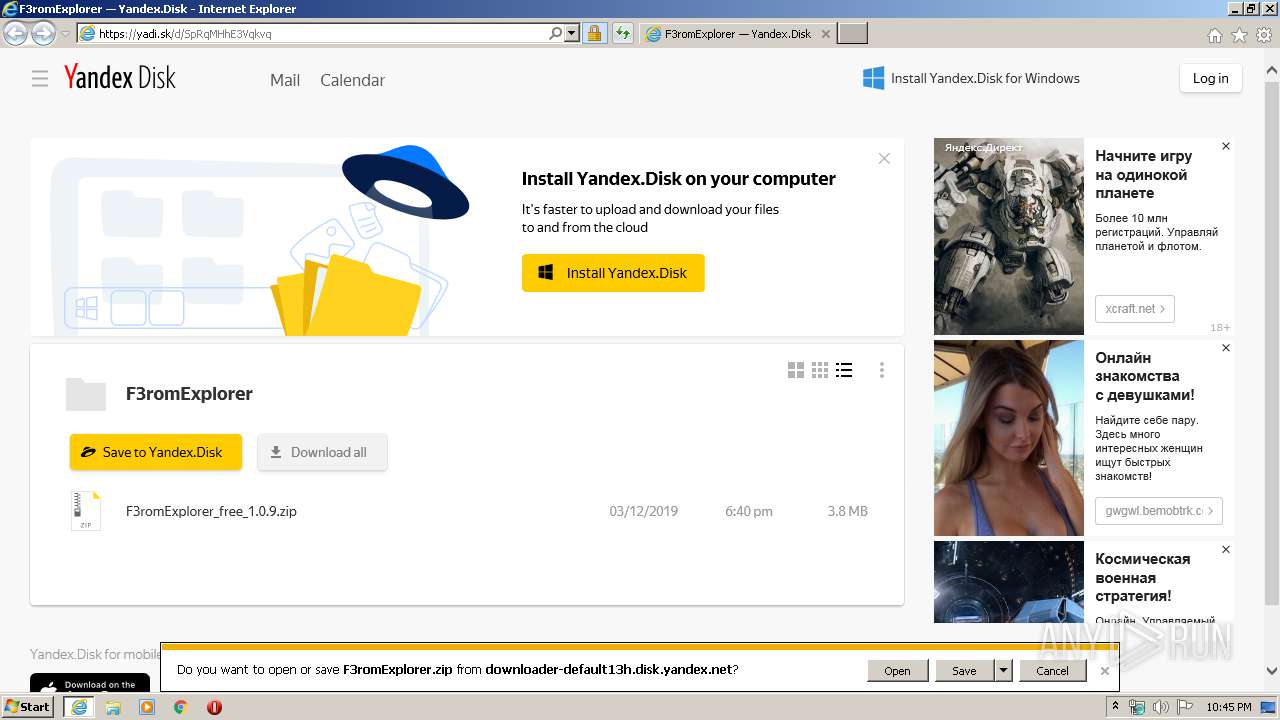
| URL: | https://yadi.sk/d/SpRqMHhE3Vqkvq |
| Full analysis: | https://app.any.run/tasks/a7b9c07c-0db4-424c-bcdd-2e2ed372d06b |
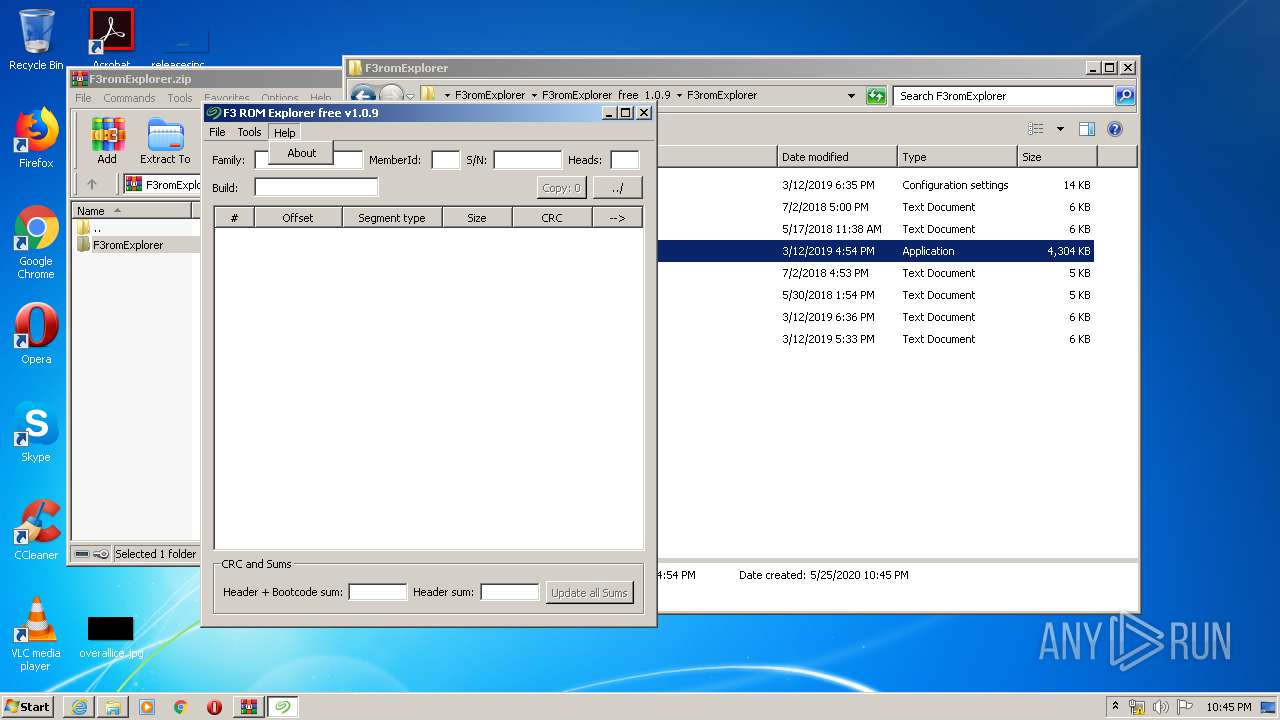
| Verdict: | Malicious activity |
| Analysis date: | May 25, 2020, 21:44:37 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 4E1A38580C0A9D6D076EF1BFAC7CBD2C |
| SHA1: | 0BA0B03443AC970C80F914AE250270A80A9FAAF8 |
| SHA256: | 60A3B8712A698281B3759559D2DE301CB5FB272355556A9C8649074A9C661529 |
| SSDEEP: | 3:N8j5VJgt8U:2hw |
MALICIOUS
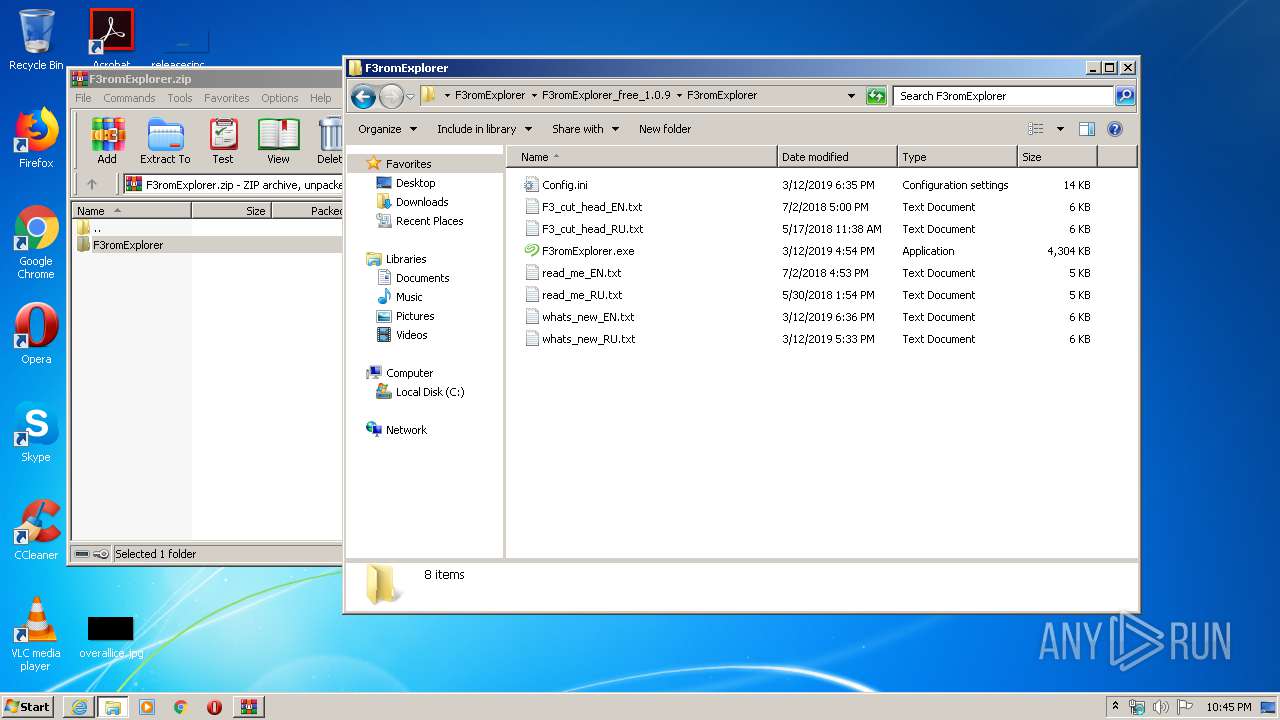
Application was dropped or rewritten from another process
- F3romExplorer.exe (PID: 3420)
SUSPICIOUS
Executable content was dropped or overwritten
- WinRAR.exe (PID: 3544)
INFO
Changes internet zones settings
- iexplore.exe (PID: 2700)
Manual execution by user
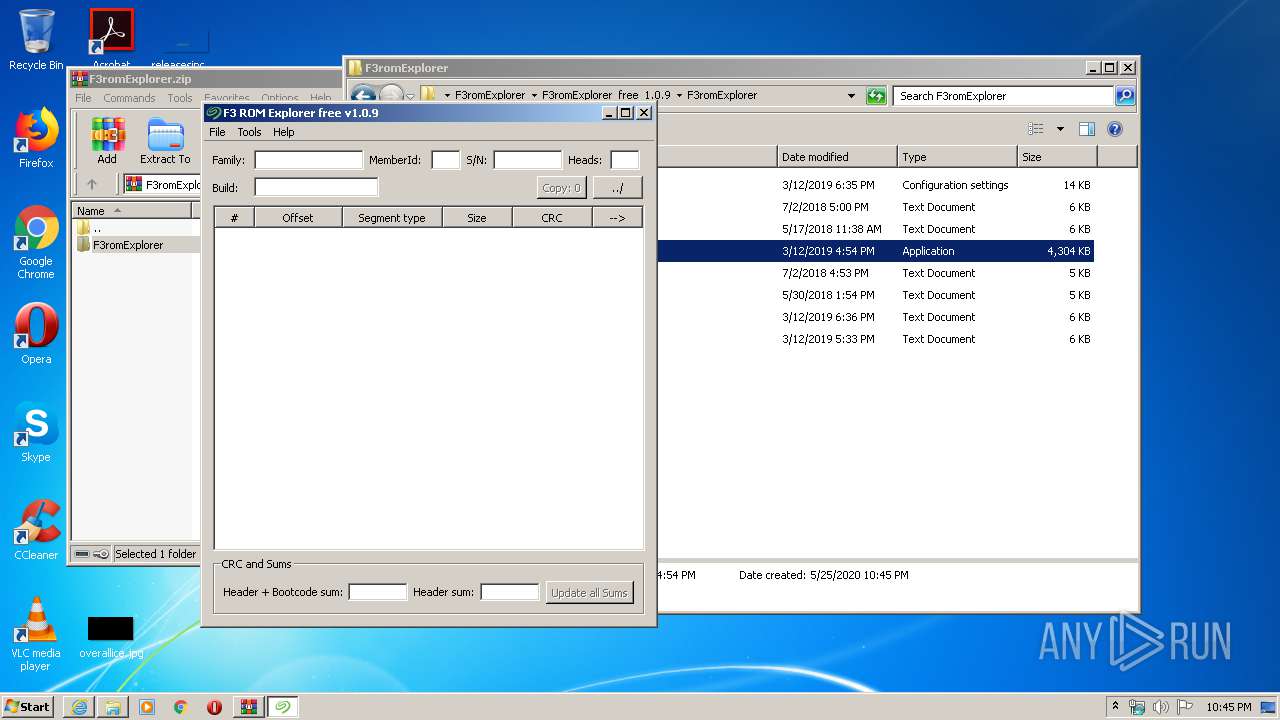
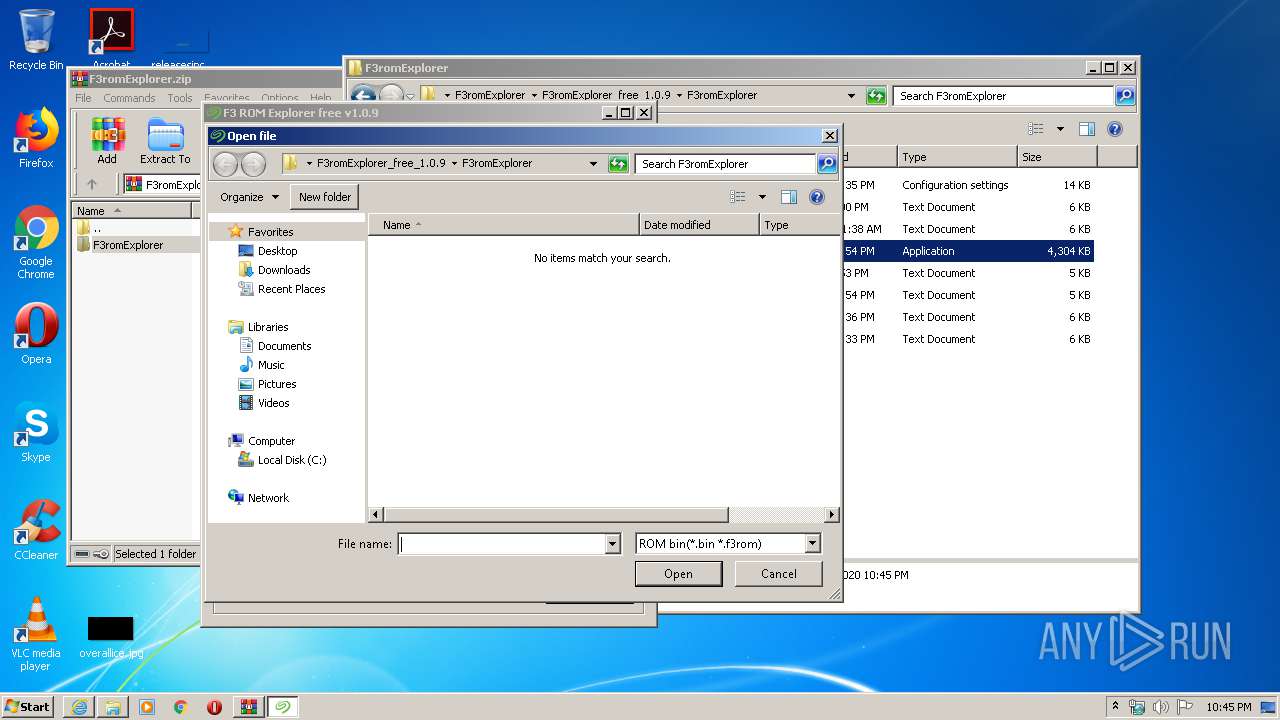
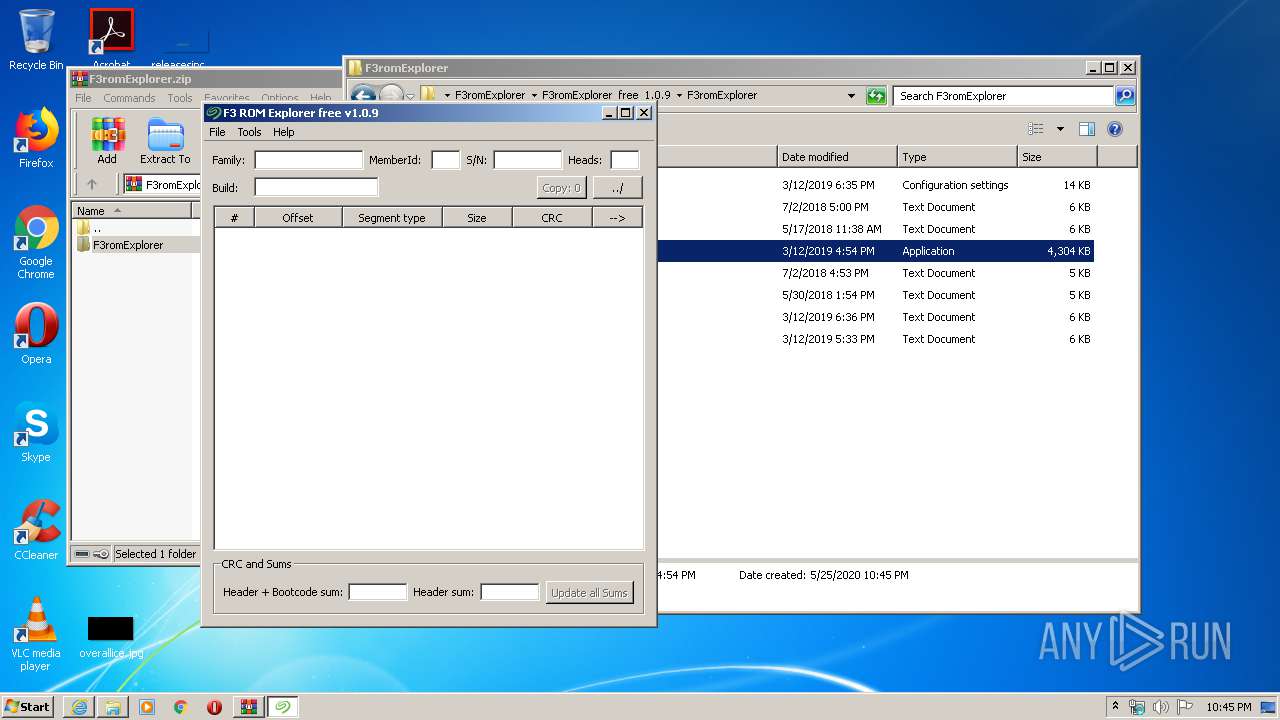
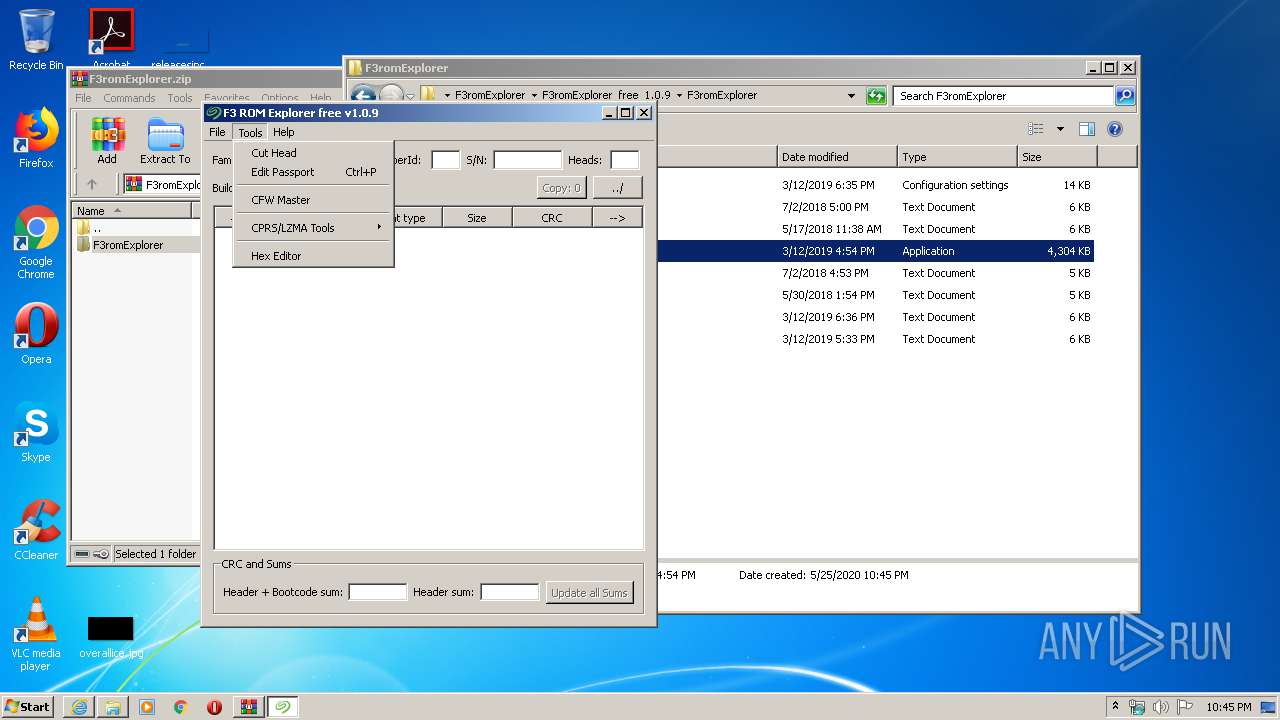
- F3romExplorer.exe (PID: 3420)
- WinRAR.exe (PID: 3544)
Reads Internet Cache Settings
- iexplore.exe (PID: 2700)
- iexplore.exe (PID: 2392)
Application launched itself
- iexplore.exe (PID: 2700)
Modifies the phishing filter of IE
- iexplore.exe (PID: 2700)
Reads internet explorer settings
- iexplore.exe (PID: 2392)
Creates files in the user directory
- iexplore.exe (PID: 2392)
Reads settings of System Certificates
- iexplore.exe (PID: 2392)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
45
Monitored processes
5
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2392 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2700 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2700 | "C:\Program Files\Internet Explorer\iexplore.exe" https://yadi.sk/d/SpRqMHhE3Vqkvq | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
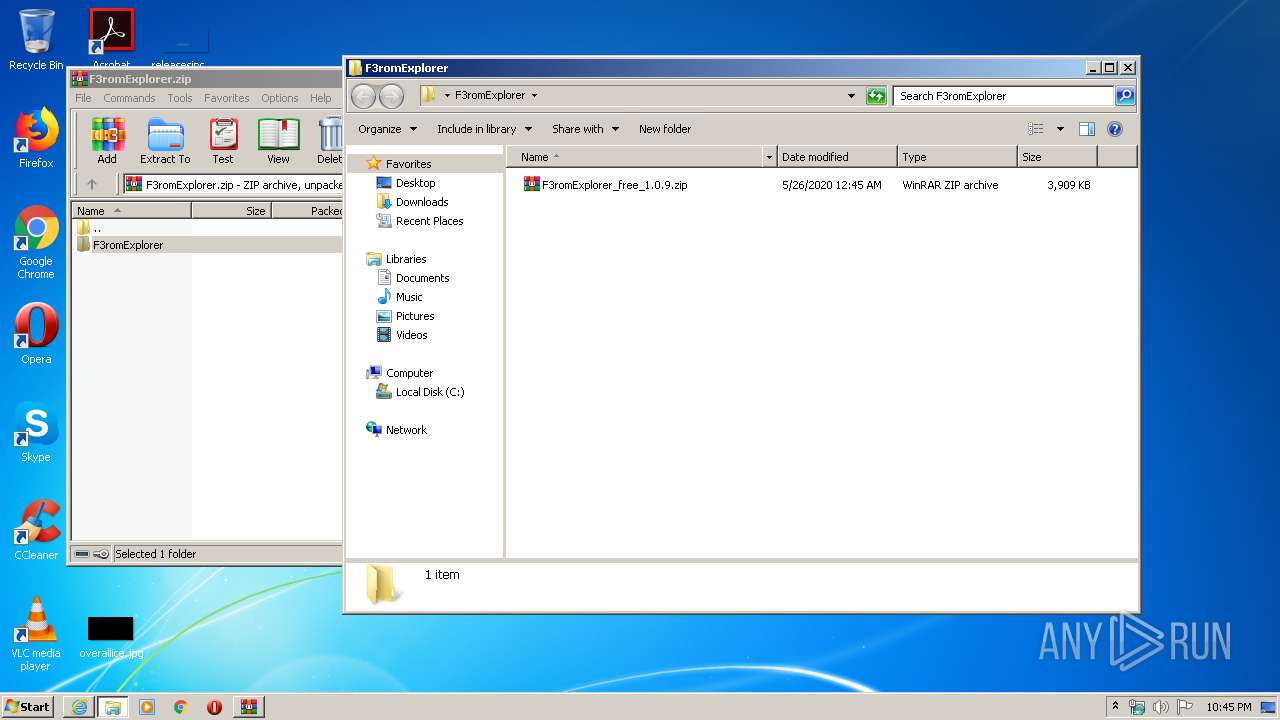
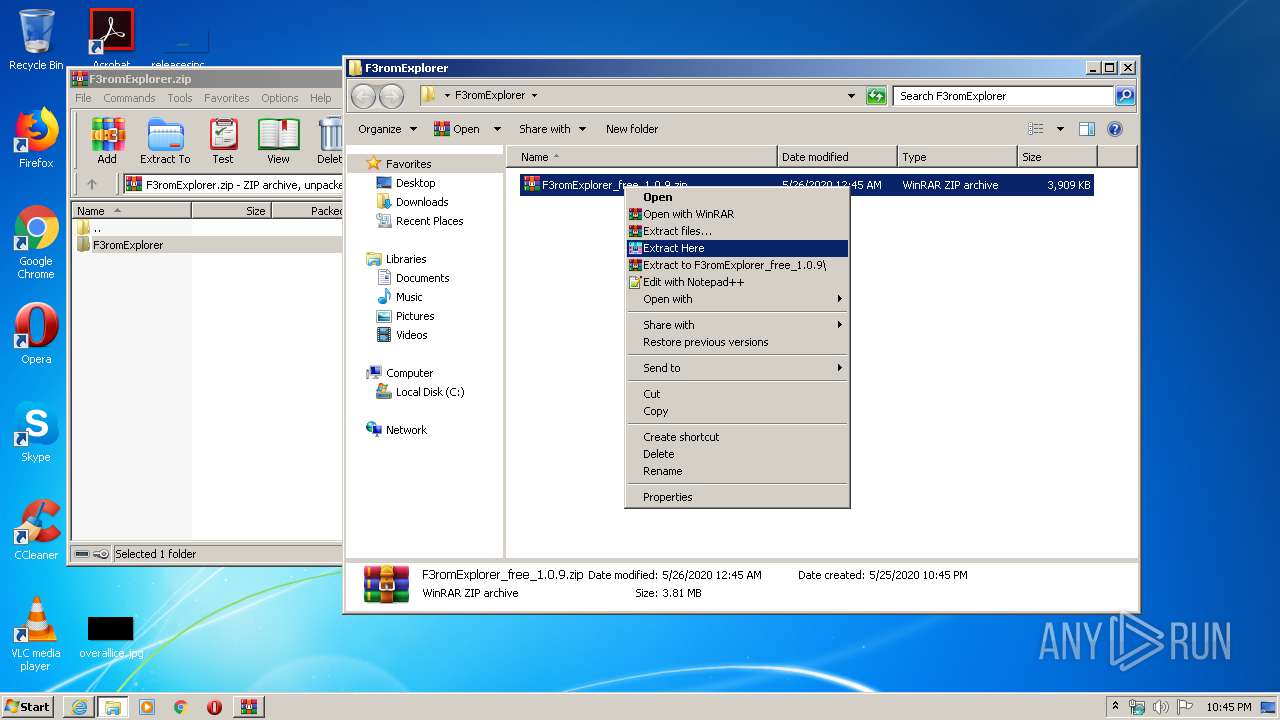
| 3420 | "C:\Users\admin\Desktop\F3romExplorer\F3romExplorer_free_1.0.9\F3romExplorer\F3romExplorer.exe" | C:\Users\admin\Desktop\F3romExplorer\F3romExplorer_free_1.0.9\F3romExplorer\F3romExplorer.exe | — | explorer.exe | |||||||||||
User: admin Company: EvRus Software Integrity Level: MEDIUM Description: F3 ROM Explorer free Exit code: 0 Modules
| |||||||||||||||
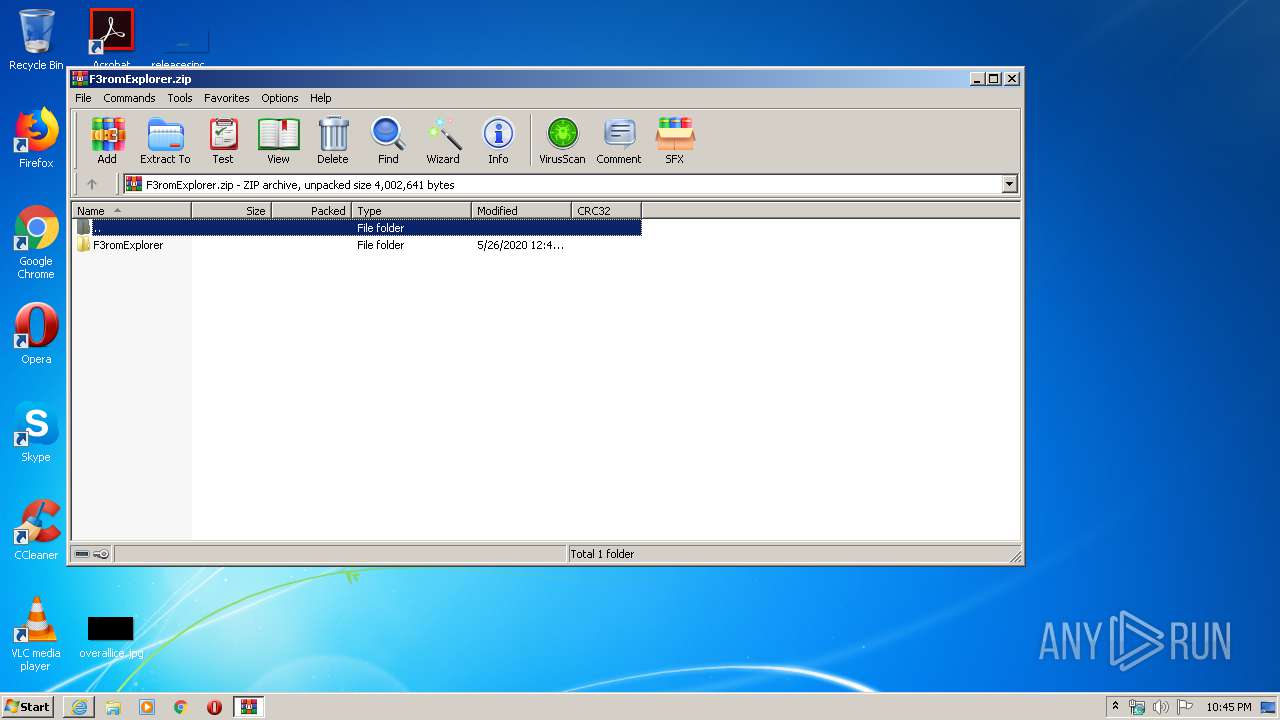
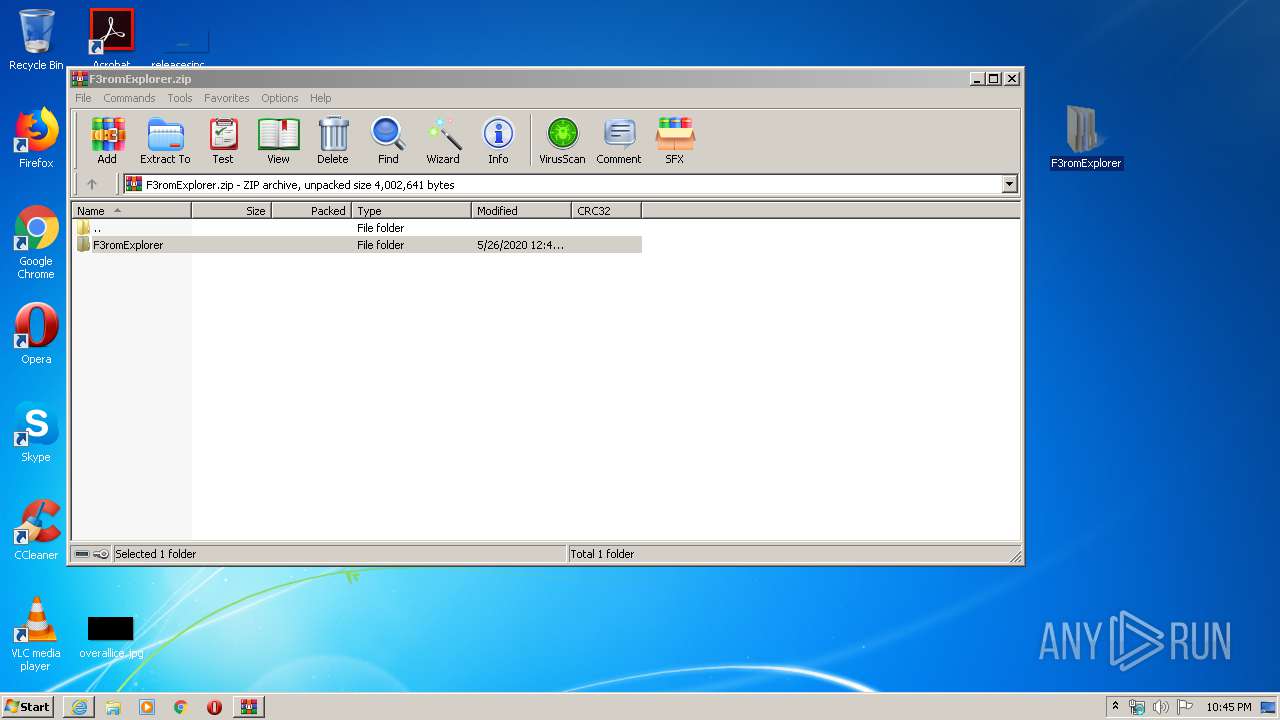
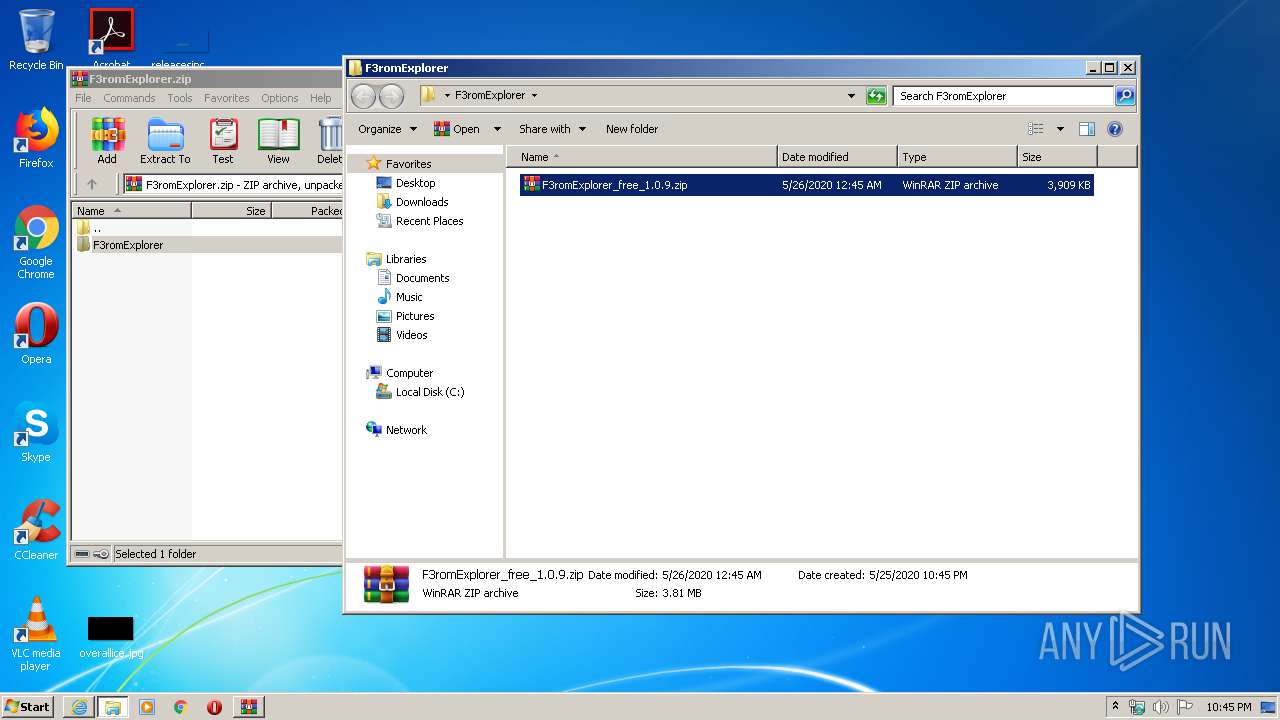
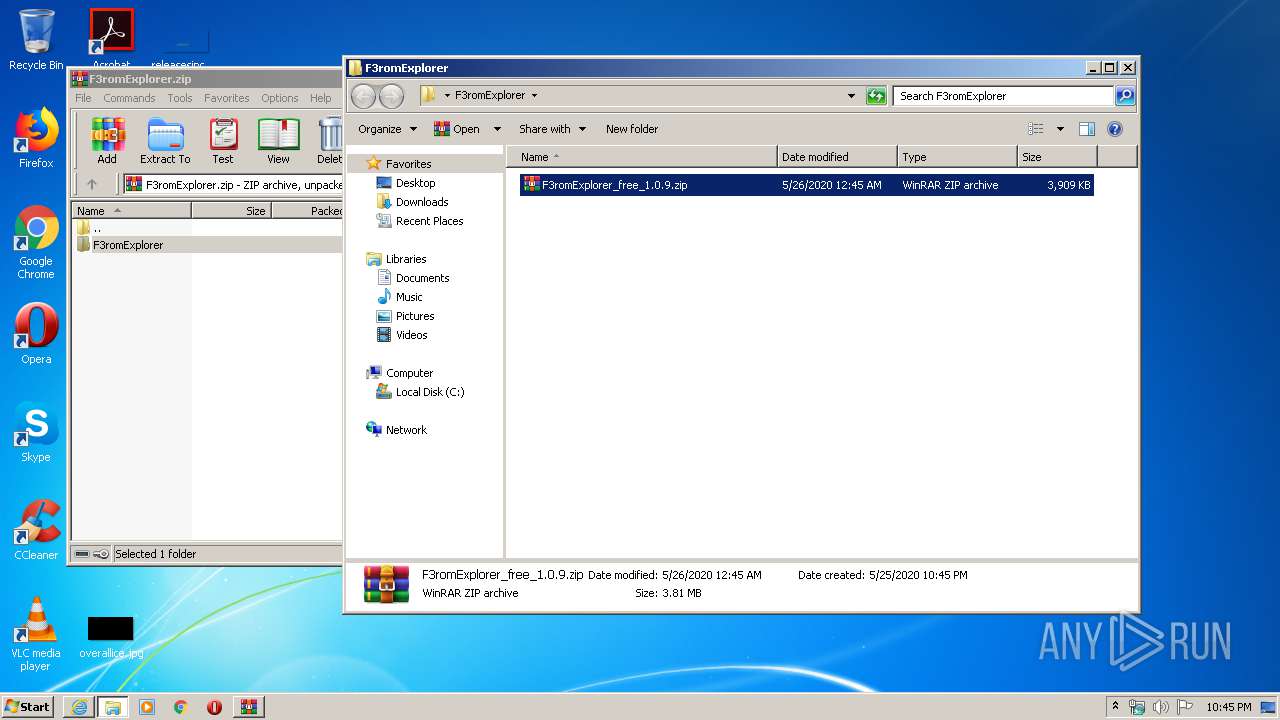
| 3444 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\6Z2BCOUL\F3romExplorer.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | iexplore.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
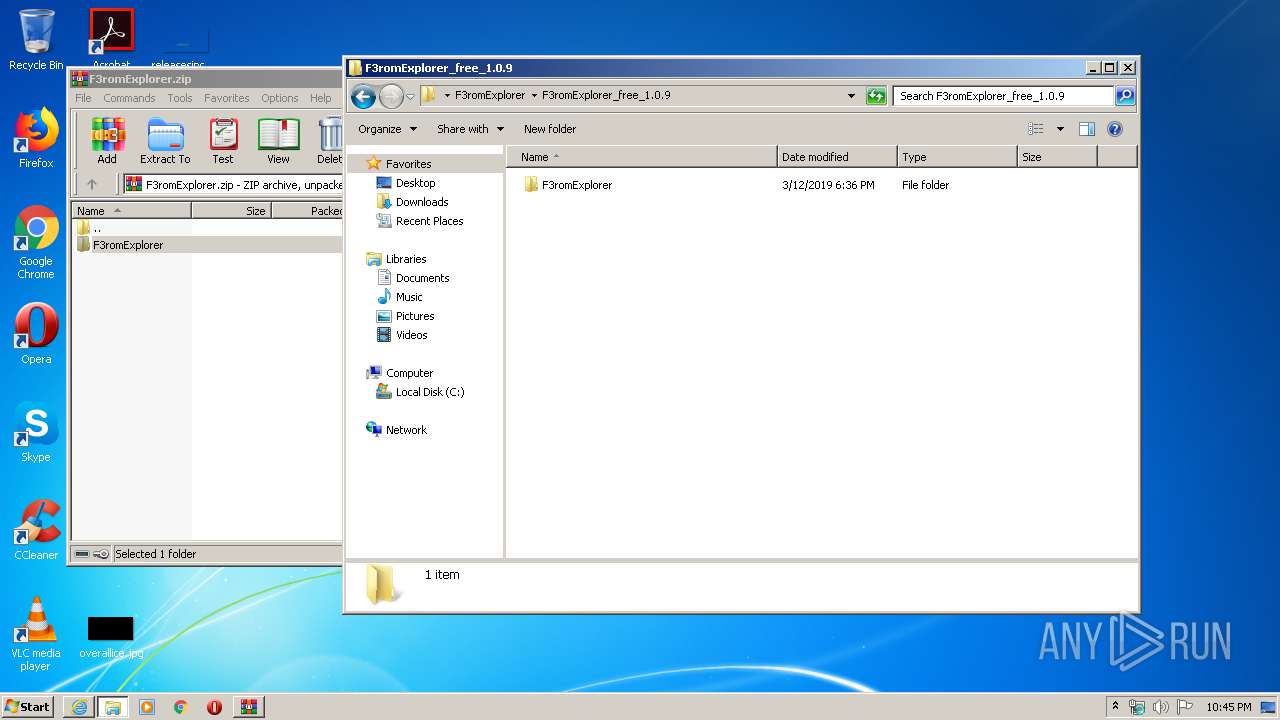
| 3544 | "C:\Program Files\WinRAR\WinRAR.exe" x -iext -ow -ver -- "C:\Users\admin\Desktop\F3romExplorer\F3romExplorer_free_1.0.9.zip" C:\Users\admin\Desktop\F3romExplorer\F3romExplorer_free_1.0.9\ | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
Total events
2 099
Read events
2 001
Write events
97
Delete events
1
Modification events
| (PID) Process: | (2700) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 3456910464 | |||
| (PID) Process: | (2700) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30814941 | |||
| (PID) Process: | (2700) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2700) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2700) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2700) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2700) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2700) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A1000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2700) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2700) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
1
Suspicious files
160
Text files
51
Unknown types
79
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2392 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Cab8C02.tmp | — | |
MD5:— | SHA256:— | |||
| 2392 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Tar8C03.tmp | — | |
MD5:— | SHA256:— | |||
| 2392 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\1B1F4BA66CDBFEC85A20E11BF729AF23_AA85F8F9DAFF33153B5AEC2E983B94B6 | binary | |
MD5:— | SHA256:— | |||
| 2392 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\E887E036775F4159E2816B7B9E527E5F_71B3F3ED127510C66B960EFE3353B255 | der | |
MD5:— | SHA256:— | |||
| 2392 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\1B1F4BA66CDBFEC85A20E11BF729AF23_AA85F8F9DAFF33153B5AEC2E983B94B6 | der | |
MD5:— | SHA256:— | |||
| 2392 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\68FAF71AF355126BCA00CE2E73CC7374_77B682CF3AAC7B00161DFFF7DEA4CC8C | der | |
MD5:— | SHA256:— | |||
| 2392 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\E887E036775F4159E2816B7B9E527E5F_71B3F3ED127510C66B960EFE3353B255 | binary | |
MD5:— | SHA256:— | |||
| 2392 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\68FAF71AF355126BCA00CE2E73CC7374_77B682CF3AAC7B00161DFFF7DEA4CC8C | binary | |
MD5:— | SHA256:— | |||
| 2392 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\SpRqMHhE3Vqkvq[1].htm | html | |
MD5:— | SHA256:— | |||
| 2392 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\DU2CRKVP.txt | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
87
TCP/UDP connections
152
DNS requests
69
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2392 | iexplore.exe | GET | 200 | 151.139.236.246:80 | http://subca.ocsp-certum.com/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBR5iK7tYk9tqQEoeQhZNkKcAol9bgQUjEPEy22YwaechGnr30oNYJY6w%2FsCEQCTkoVAAWVxX5R%2FKI%2FvyZso | US | der | 1.61 Kb | whitelisted |
2392 | iexplore.exe | GET | 200 | 151.139.236.246:80 | http://subca.ocsp-certum.com/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBR5iK7tYk9tqQEoeQhZNkKcAol9bgQUjEPEy22YwaechGnr30oNYJY6w%2FsCEQCTkoVAAWVxX5R%2FKI%2FvyZso | US | der | 1.61 Kb | whitelisted |
2392 | iexplore.exe | GET | 200 | 5.45.205.242:80 | http://yandex.ocsp-responder.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBStniMGfahyWUWDEeSLUFbNR9JLAgQUN1zjGeCyjqGoTtLPq9Dc4wtcNU0CEDUFMsy%2BHenUJ4vKnCIxEbA%3D | RU | der | 1.51 Kb | whitelisted |
2392 | iexplore.exe | GET | 200 | 5.45.205.242:80 | http://yandex.ocsp-responder.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBStniMGfahyWUWDEeSLUFbNR9JLAgQUN1zjGeCyjqGoTtLPq9Dc4wtcNU0CEGlaGsE0PYlVme%2B6wlA0LEA%3D | RU | der | 1.51 Kb | whitelisted |
2392 | iexplore.exe | GET | 200 | 5.45.205.242:80 | http://yandex.ocsp-responder.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBStniMGfahyWUWDEeSLUFbNR9JLAgQUN1zjGeCyjqGoTtLPq9Dc4wtcNU0CEFC0HyqRL1rOCzRaL288%2Fbw%3D | RU | der | 1.51 Kb | whitelisted |
2392 | iexplore.exe | GET | 200 | 5.45.205.242:80 | http://yandex.ocsp-responder.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBStniMGfahyWUWDEeSLUFbNR9JLAgQUN1zjGeCyjqGoTtLPq9Dc4wtcNU0CEFC0HyqRL1rOCzRaL288%2Fbw%3D | RU | der | 1.51 Kb | whitelisted |
2392 | iexplore.exe | GET | 200 | 104.18.21.226:80 | http://ocsp2.globalsign.com/rootr3/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBT1nGh%2FJBjWKnkPdZIzB1bqhelHBwQUj%2FBLf6guRSSuTVD6Y5qL3uLdG7wCDQHuXyId%2FGI71DM6hVc%3D | US | der | 1.48 Kb | whitelisted |
2392 | iexplore.exe | GET | 200 | 5.45.205.242:80 | http://yandex.ocsp-responder.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBStniMGfahyWUWDEeSLUFbNR9JLAgQUN1zjGeCyjqGoTtLPq9Dc4wtcNU0CEGlaGsE0PYlVme%2B6wlA0LEA%3D | RU | der | 1.51 Kb | whitelisted |
2392 | iexplore.exe | GET | 200 | 5.45.205.242:80 | http://yandex.ocsp-responder.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBStniMGfahyWUWDEeSLUFbNR9JLAgQUN1zjGeCyjqGoTtLPq9Dc4wtcNU0CEGlaGsE0PYlVme%2B6wlA0LEA%3D | RU | der | 1.51 Kb | whitelisted |
2392 | iexplore.exe | GET | 200 | 2.16.186.11:80 | http://isrg.trustid.ocsp.identrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRv9GhNQxLSSGKBnMArPUcsHYovpgQUxKexpHsscfrb4UuQdf%2FEFWCFiRACEAoBQUIAAAFThXNqC4Xspwg%3D | unknown | der | 1.37 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2392 | iexplore.exe | 151.139.236.246:80 | subca.ocsp-certum.com | netDNA | US | unknown |
2392 | iexplore.exe | 87.250.250.50:443 | disk.yandex.com | YANDEX LLC | RU | whitelisted |
2392 | iexplore.exe | 5.45.205.242:80 | yandex.ocsp-responder.com | YANDEX LLC | RU | whitelisted |
2392 | iexplore.exe | 178.154.131.215:443 | yadi.sk | YANDEX LLC | RU | whitelisted |
2392 | iexplore.exe | 93.158.134.119:443 | mc.yandex.ru | YANDEX LLC | RU | whitelisted |
2392 | iexplore.exe | 213.180.193.90:443 | an.yandex.ru | YANDEX LLC | RU | whitelisted |
2392 | iexplore.exe | 5.255.255.80:443 | yandex.ru | YANDEX LLC | RU | whitelisted |
2700 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
2392 | iexplore.exe | 87.250.247.183:443 | avatars.mds.yandex.net | YANDEX LLC | RU | whitelisted |
2392 | iexplore.exe | 87.250.250.114:443 | ysa-static.passport.yandex.ru | YANDEX LLC | RU | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
yadi.sk |
| shared |
subca.ocsp-certum.com |
| whitelisted |
yandex.ocsp-responder.com |
| whitelisted |
yastatic.net |
| whitelisted |
mc.yandex.ru |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
disk.yandex.com |
| shared |
disk.yandex.ru |
| shared |
an.yandex.ru |
| whitelisted |