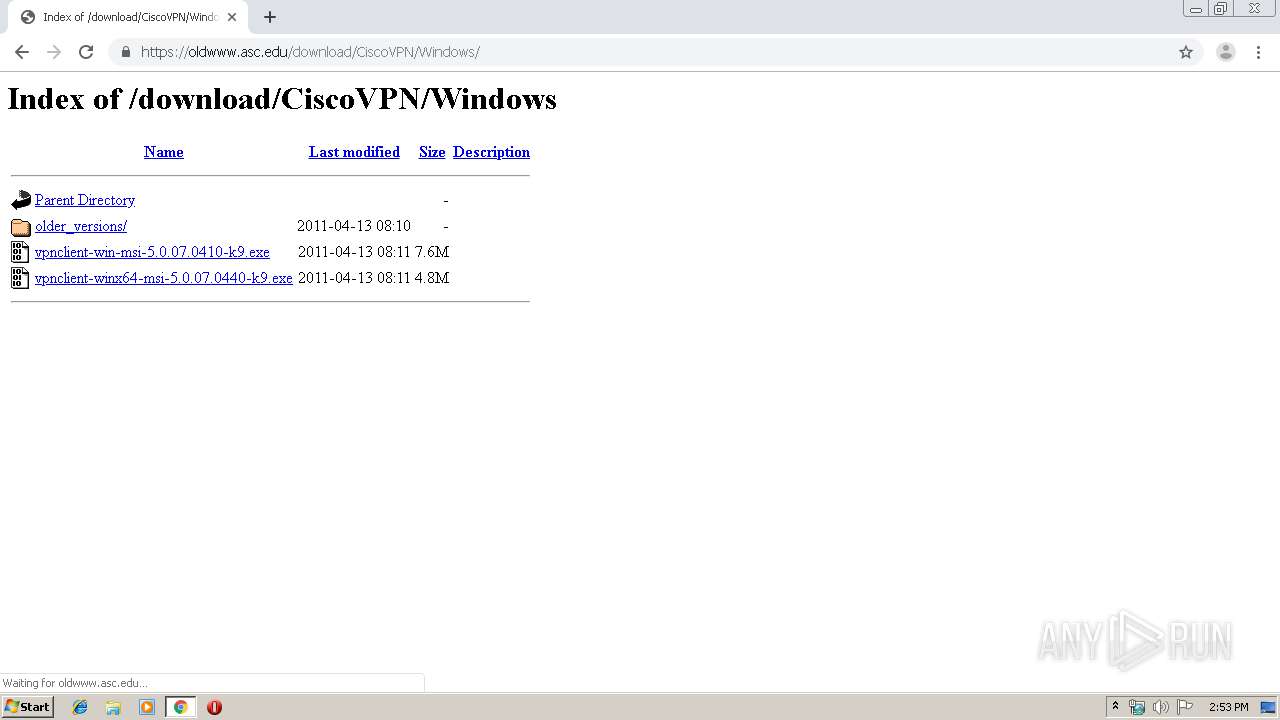
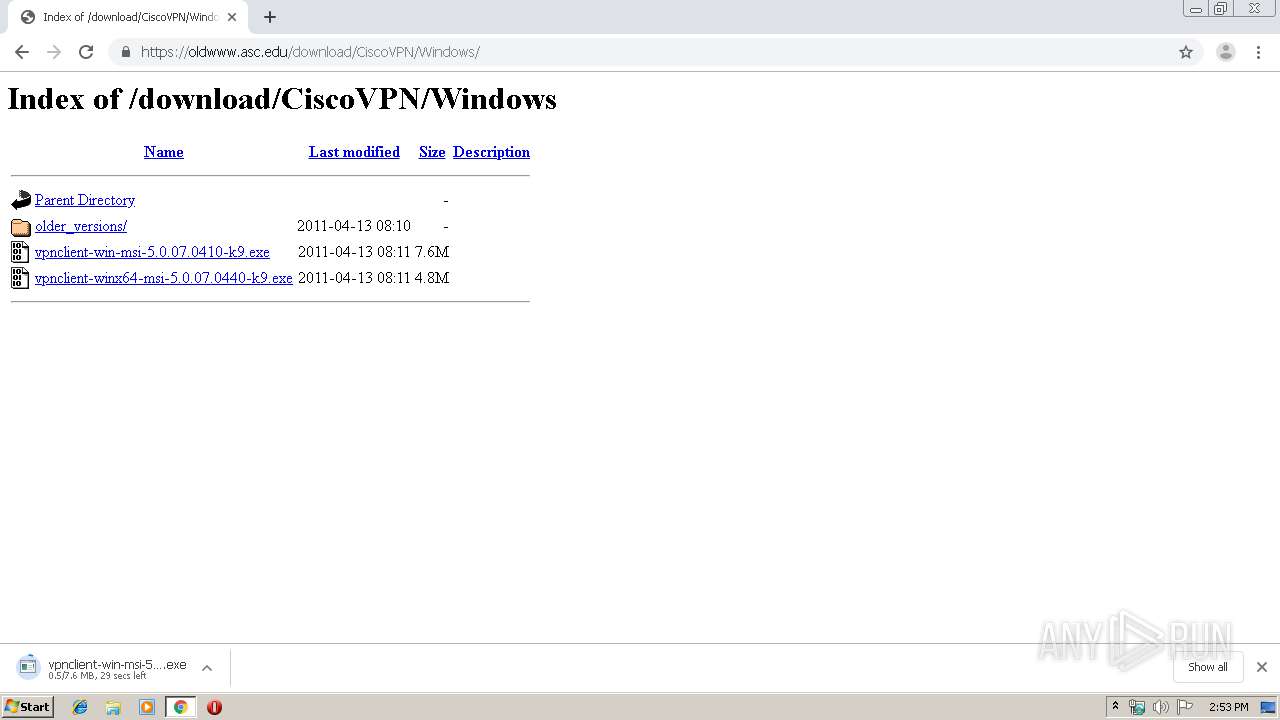
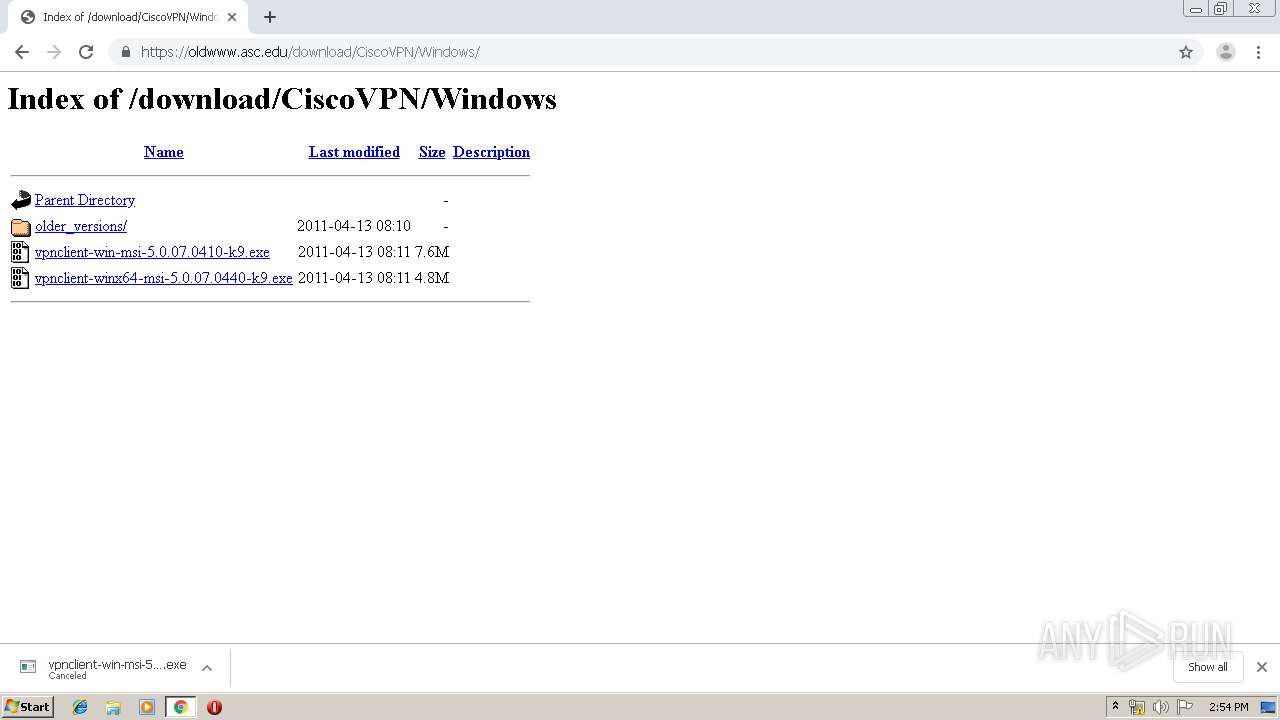
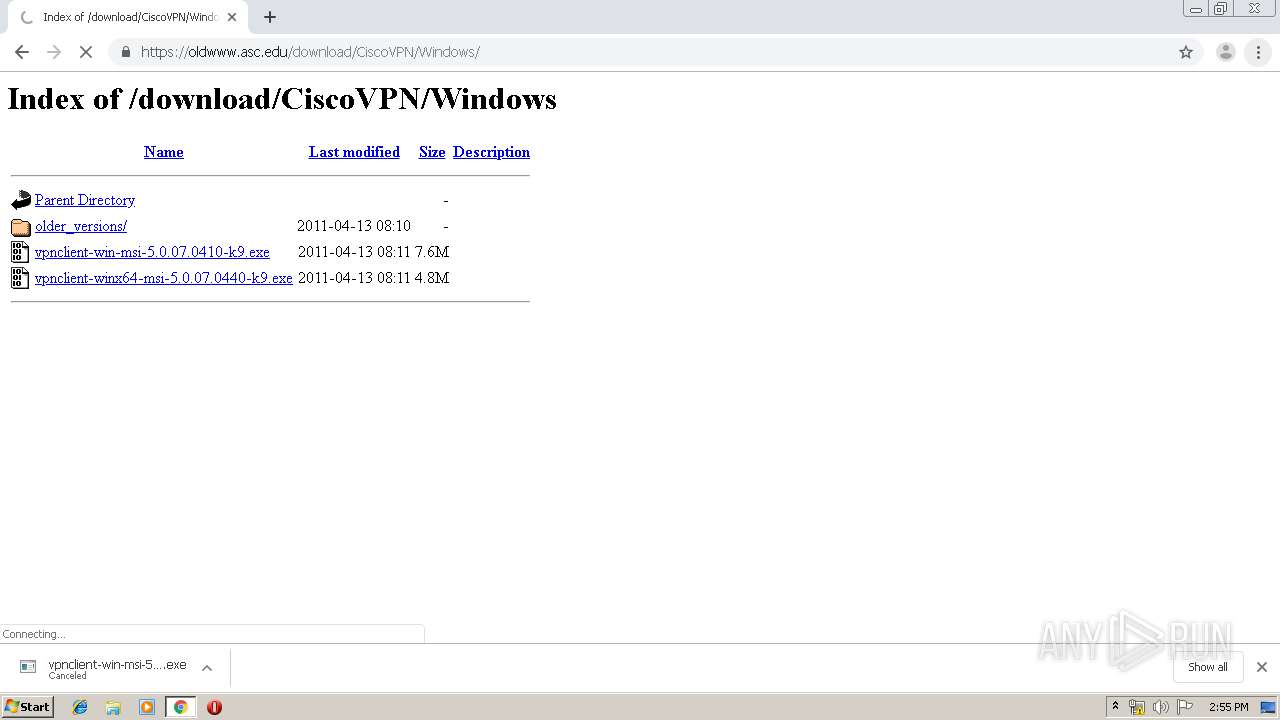
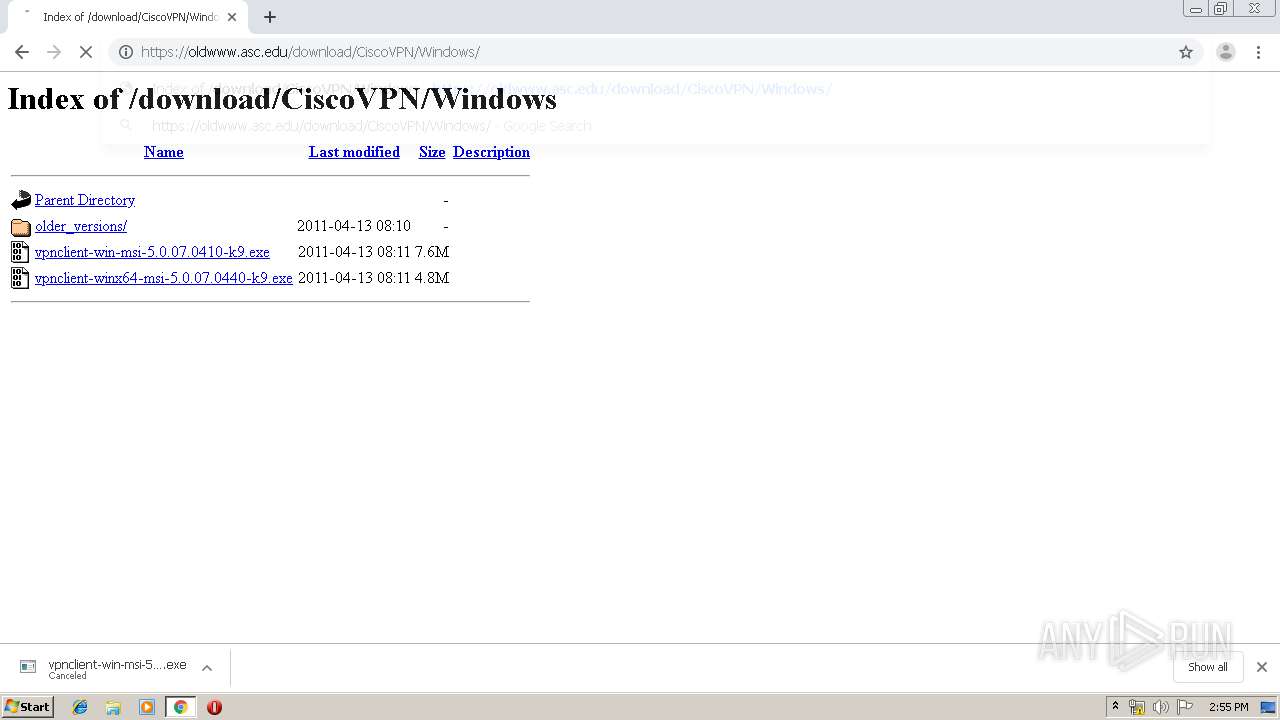
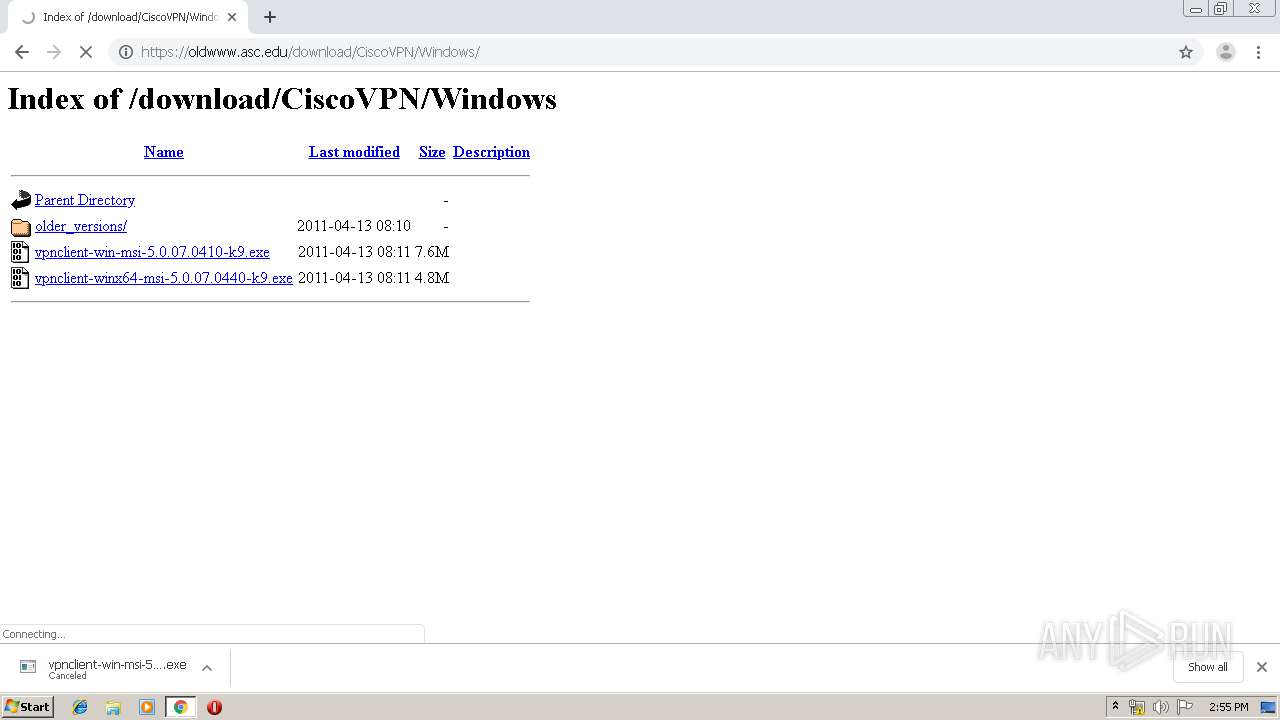
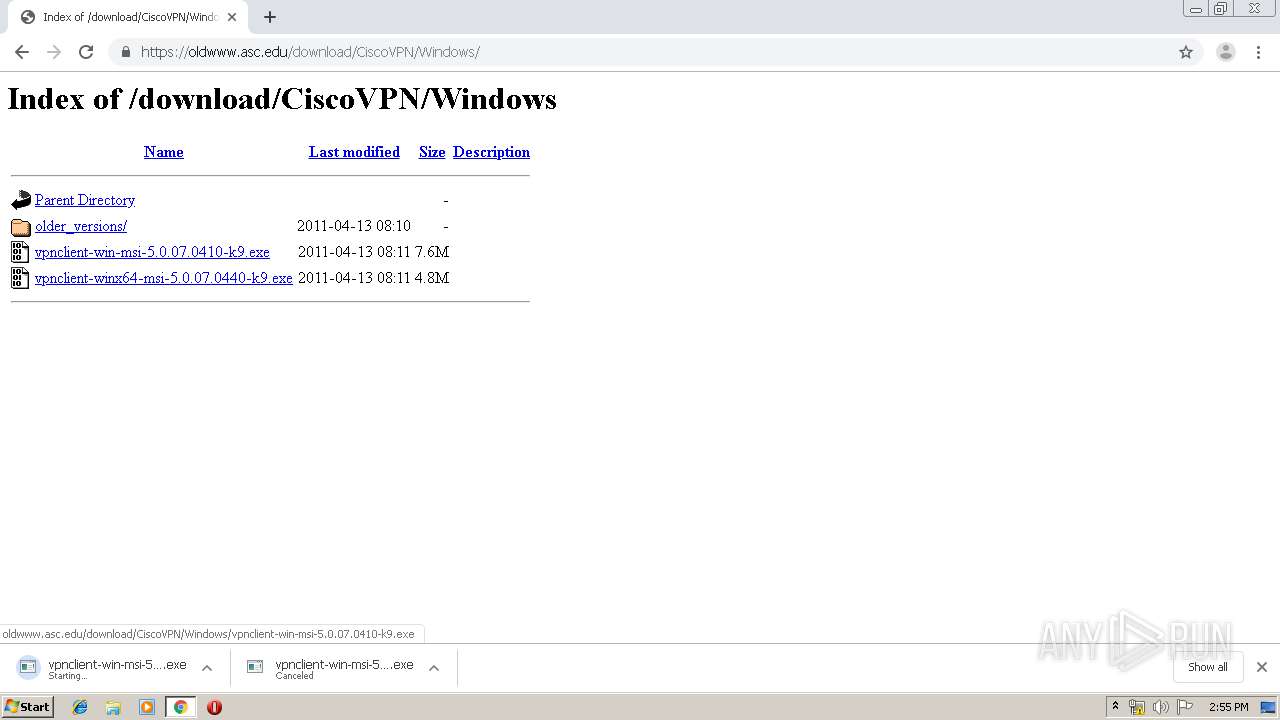
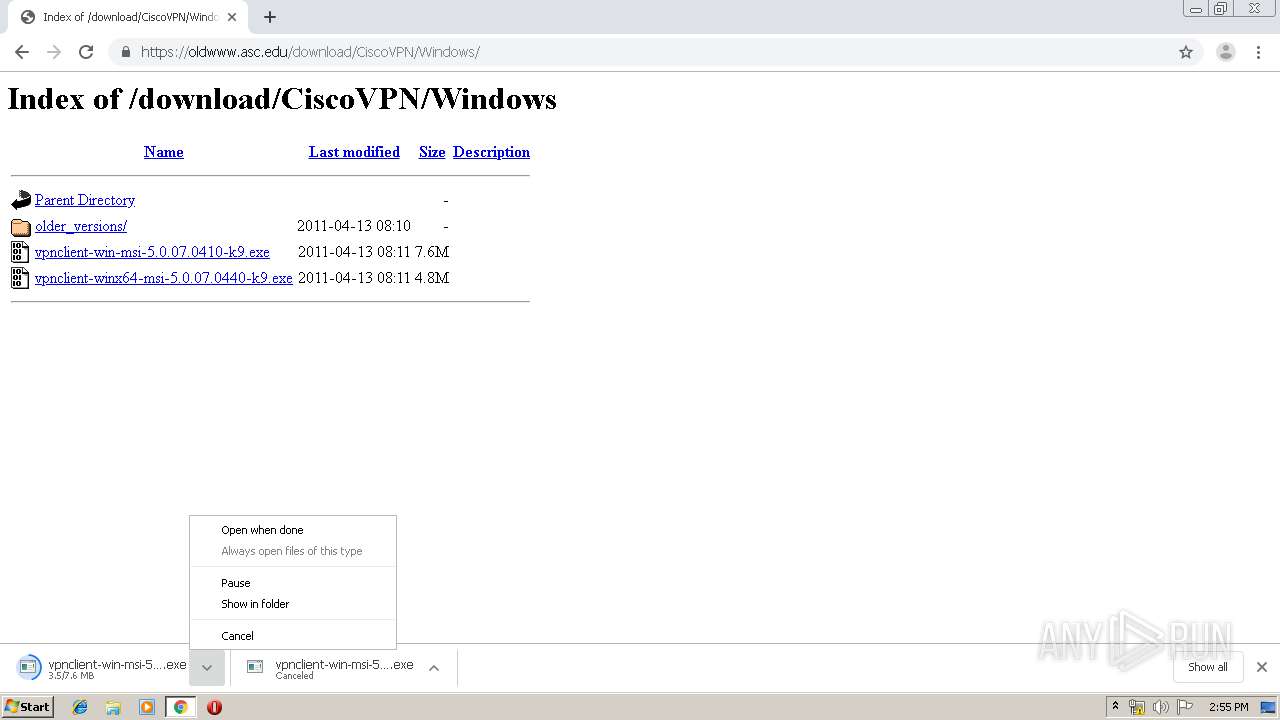
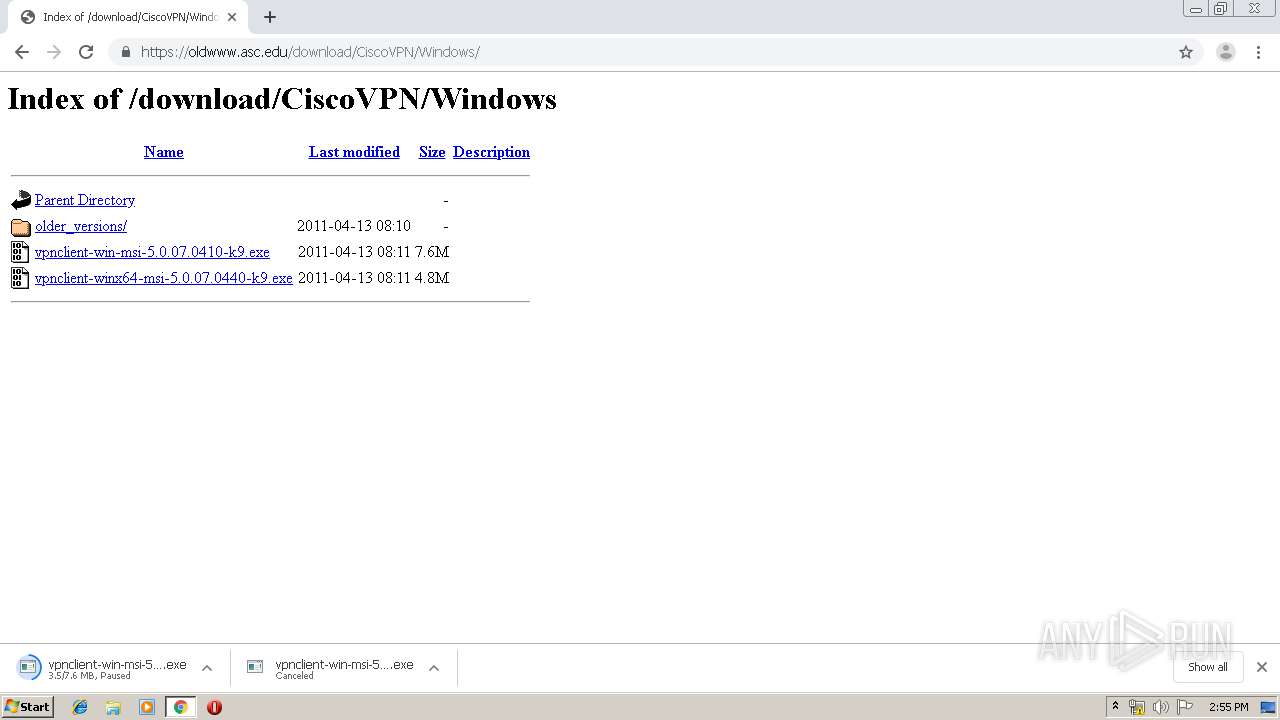
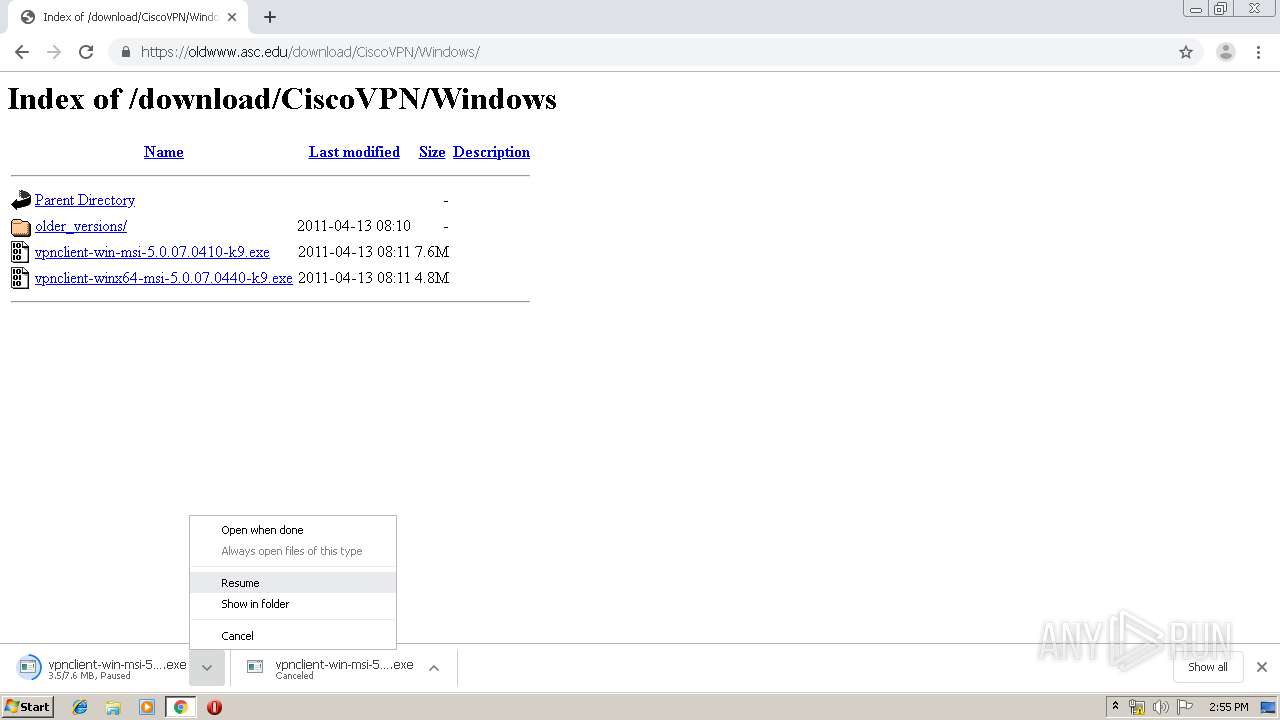
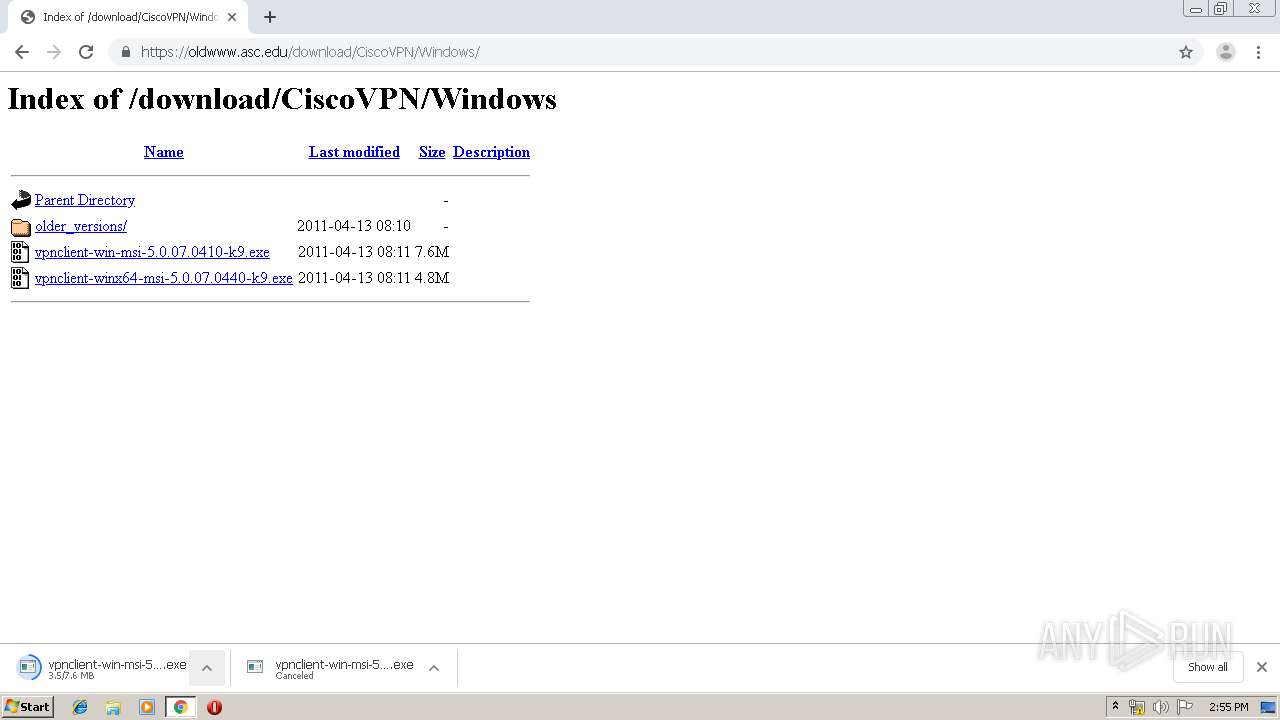
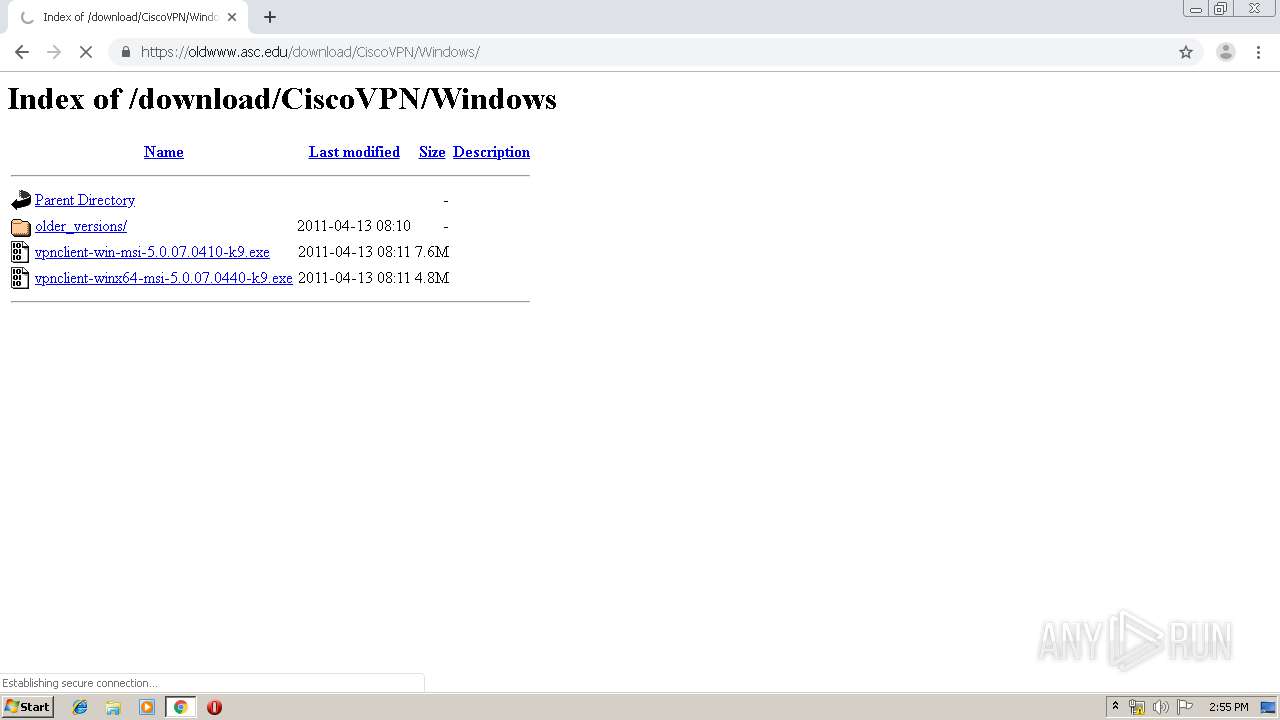
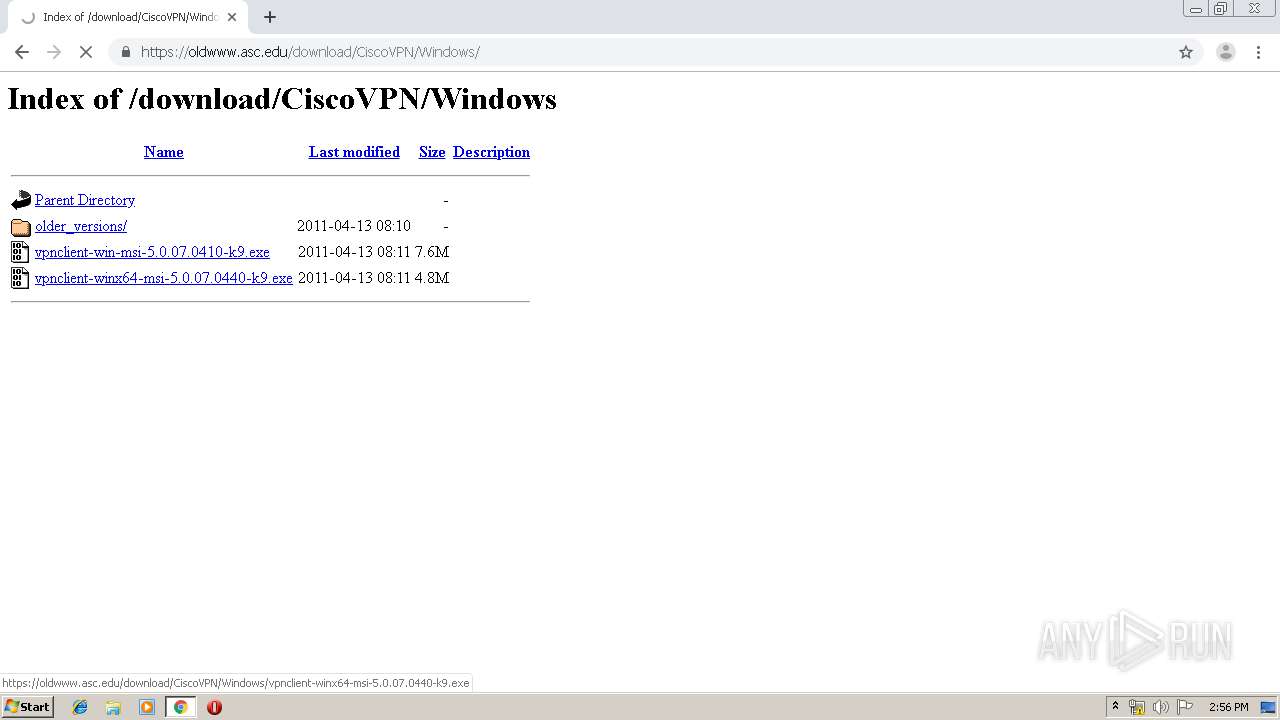
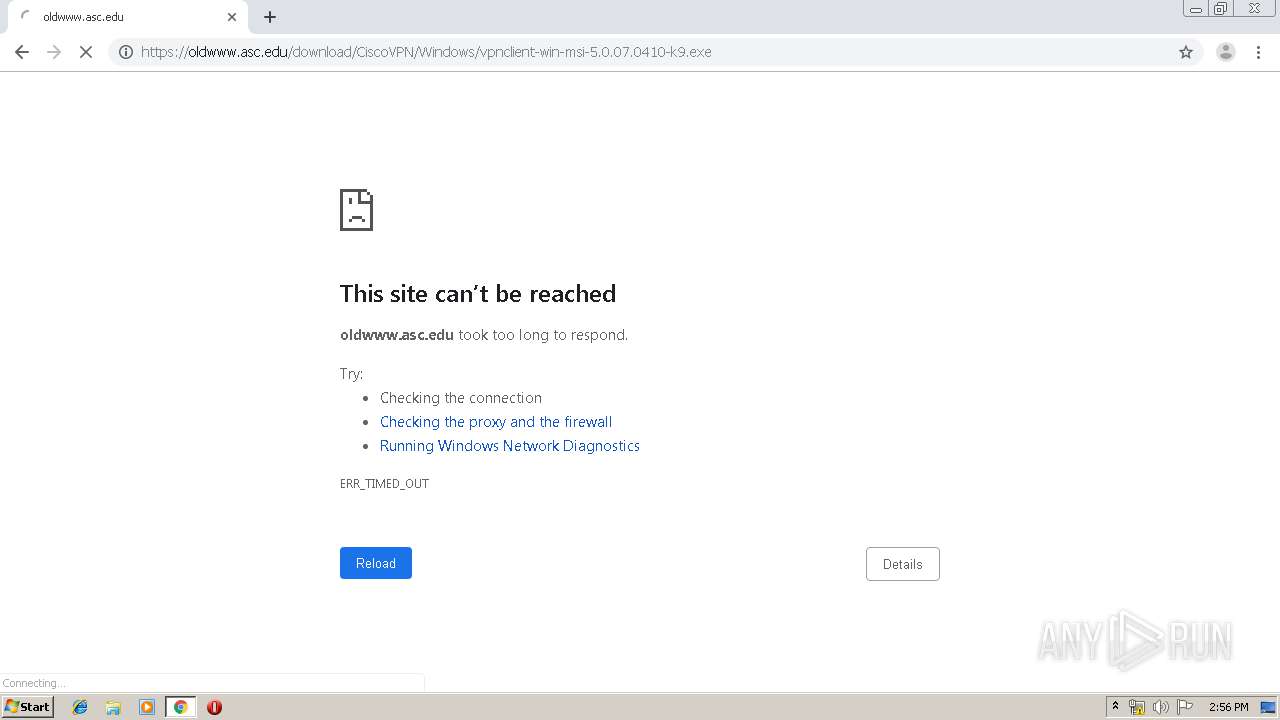
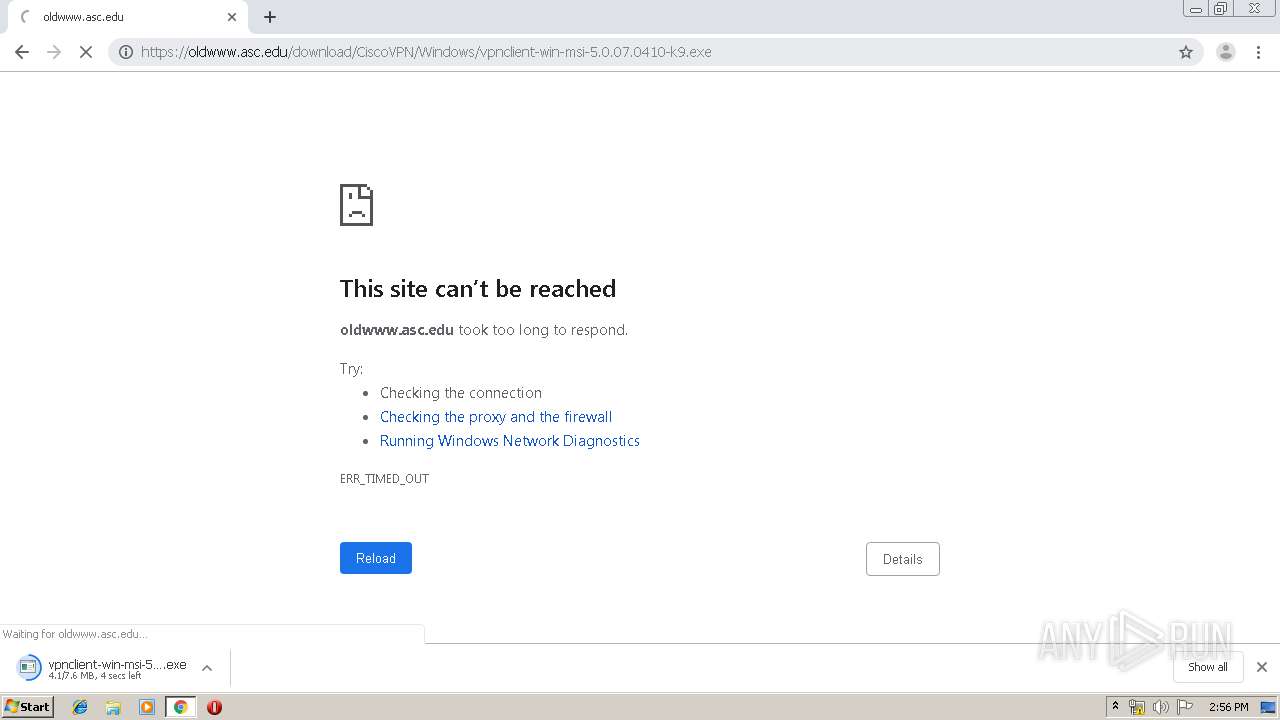
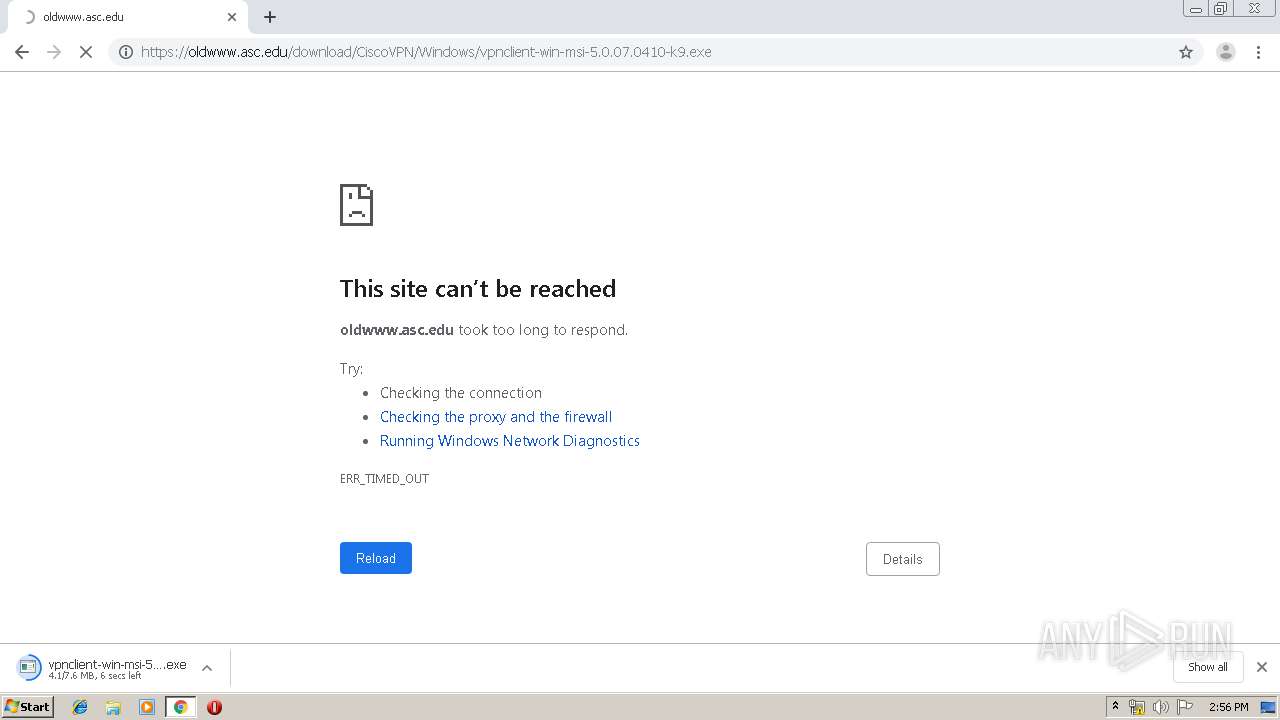
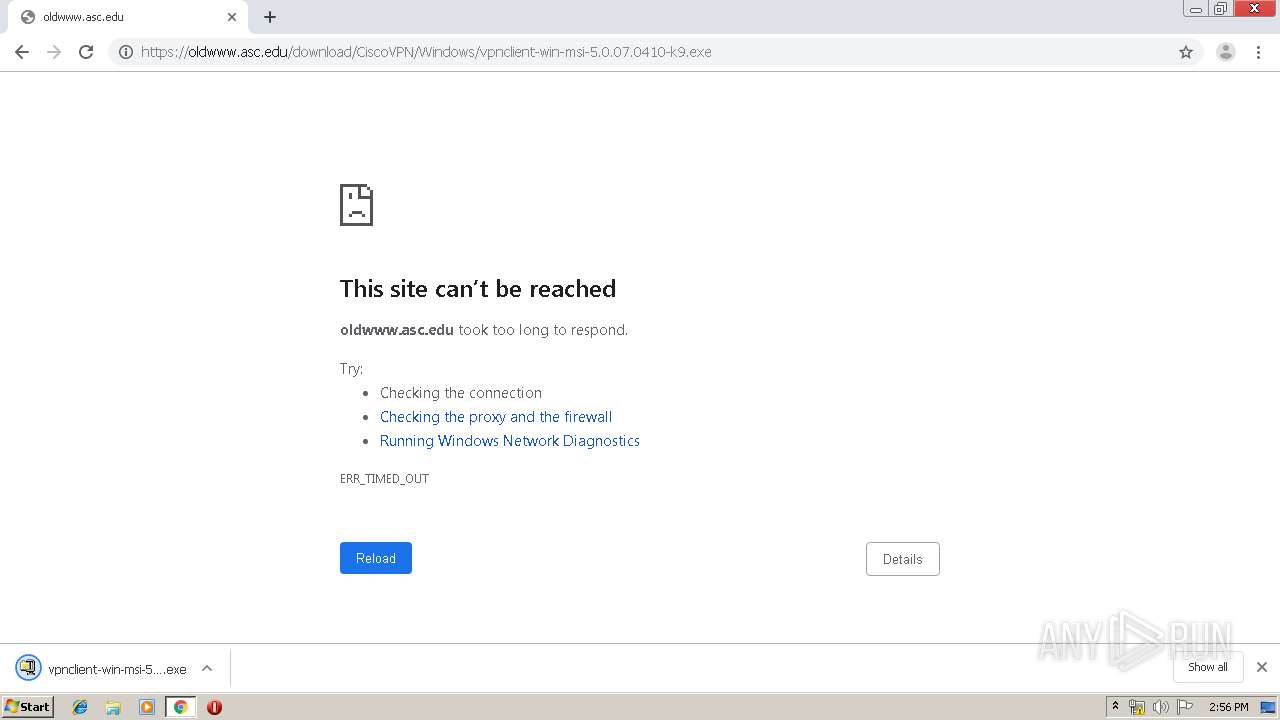
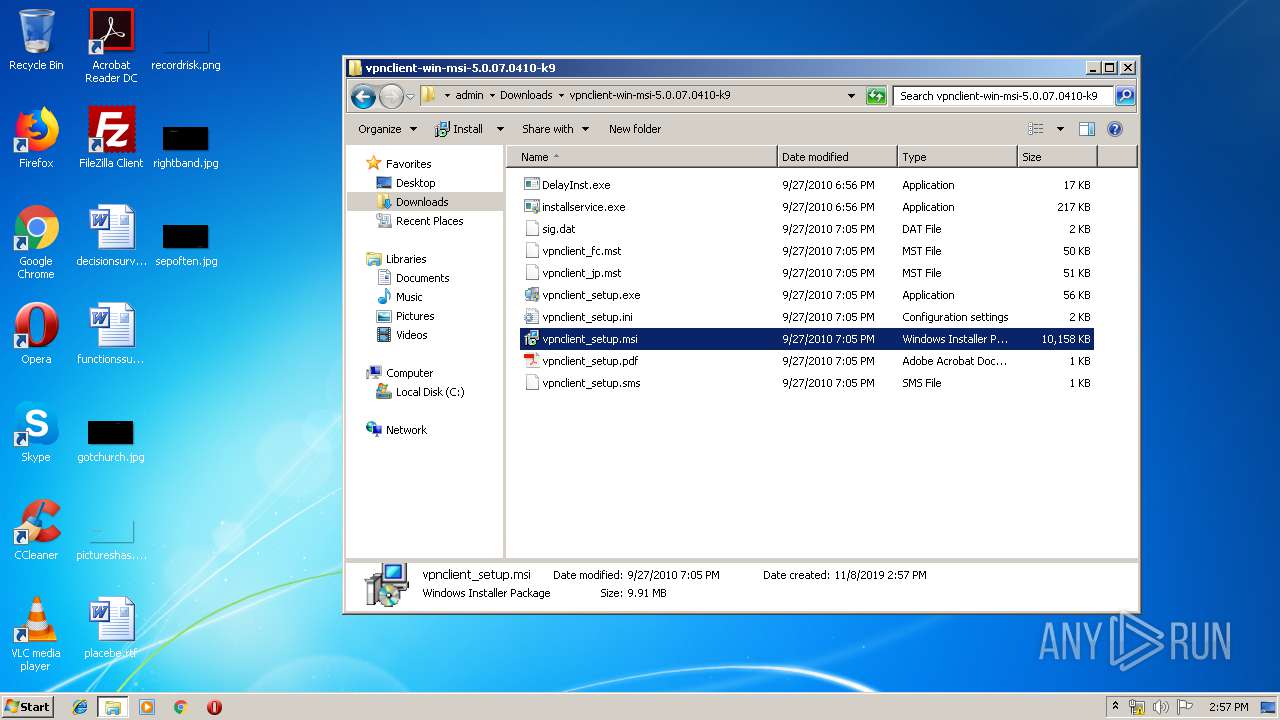
| URL: | https://oldwww.asc.edu/download/CiscoVPN/Windows/ |
| Full analysis: | https://app.any.run/tasks/6d99dac9-633a-4c53-8330-35b812883993 |
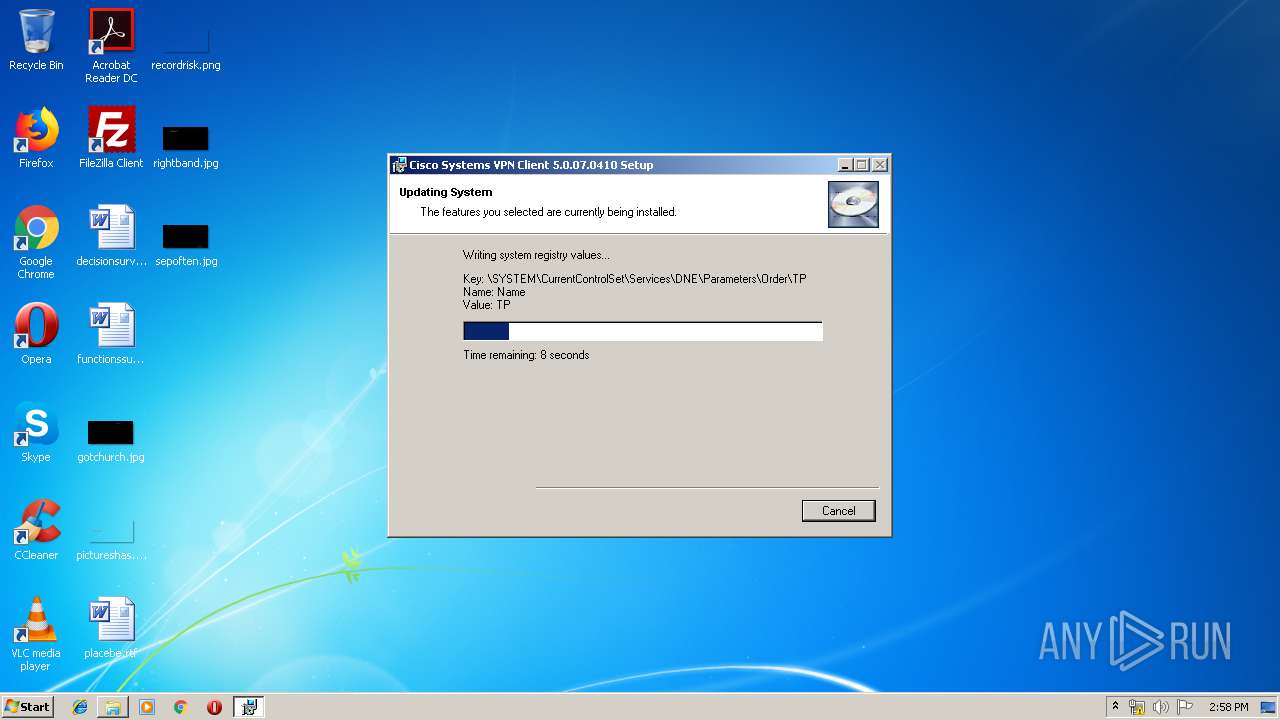
| Verdict: | Malicious activity |
| Analysis date: | November 08, 2019, 14:52:58 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 2EEBD561B6D46D374B898661ECCB8A06 |
| SHA1: | 1F34F6CD64DA0E0E07673BD0EFD662C2DF1E7C49 |
| SHA256: | 6098645587D90E5A918AE17497B8742B201CFE7AC3D773912DC9A4D035C83C1B |
| SSDEEP: | 3:N8AkdOLAjzk7BoeDN:2AkwL4YBo4N |
MALICIOUS
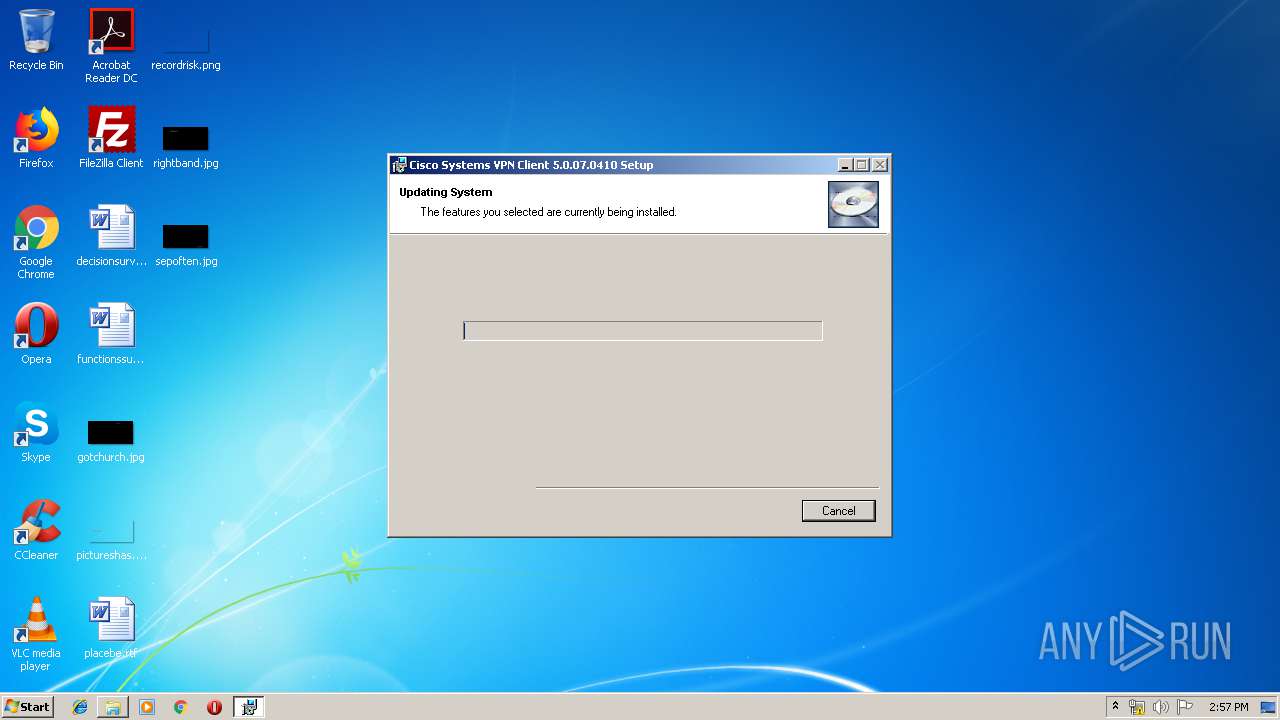
Loads dropped or rewritten executable
- svchost.exe (PID: 864)
- SearchProtocolHost.exe (PID: 3352)
- dne2000.exe (PID: 392)
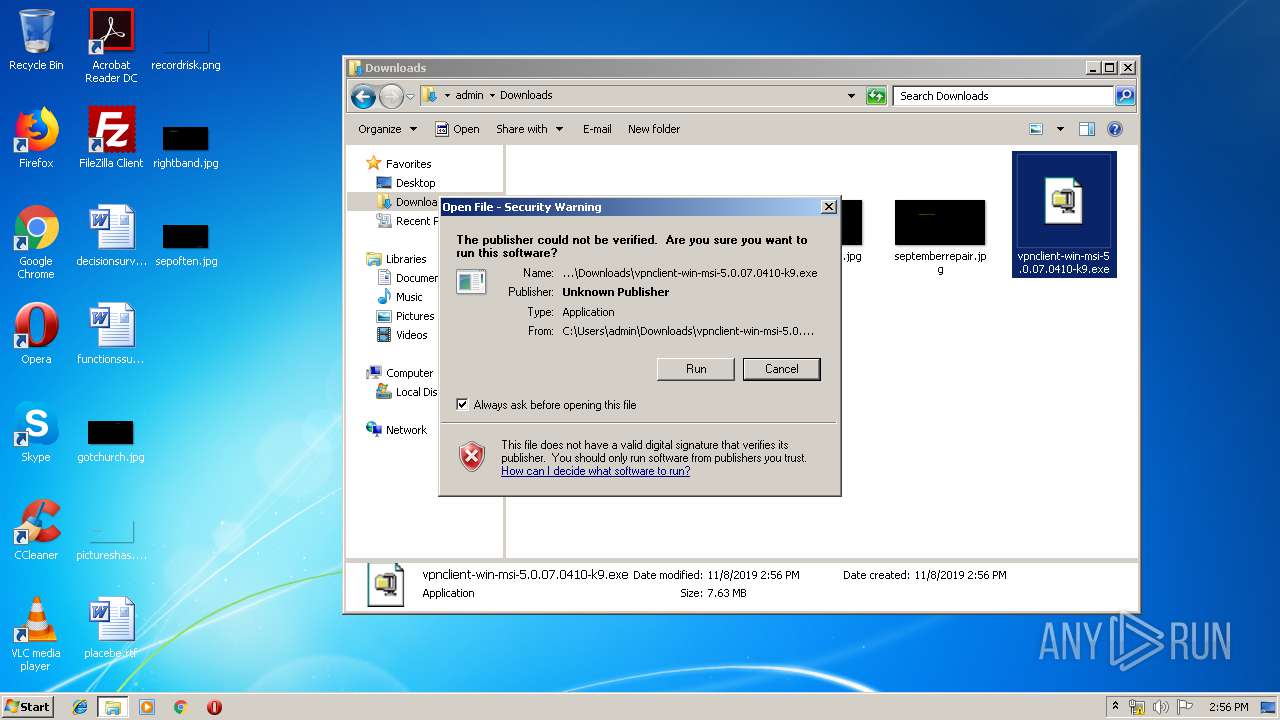
Application was dropped or rewritten from another process
- vpnclient-win-msi-5.0.07.0410-k9.exe (PID: 1956)
- WiseCustomCalla41.exe (PID: 3544)
- WiseCustomCalla50.exe (PID: 1560)
- dne2000.exe (PID: 392)
- dneinst.exe (PID: 1468)
Writes to a start menu file
- msiexec.exe (PID: 3200)
SUSPICIOUS
Executable content was dropped or overwritten
- chrome.exe (PID: 2456)
- MsiExec.exe (PID: 2860)
- chrome.exe (PID: 1216)
- WinRAR.exe (PID: 1048)
- msiexec.exe (PID: 408)
- MsiExec.exe (PID: 1212)
- msiexec.exe (PID: 3200)
- DrvInst.exe (PID: 3792)
- dne2000.exe (PID: 392)
Starts application with an unusual extension
- msiexec.exe (PID: 408)
Executed as Windows Service
- vssvc.exe (PID: 3052)
Executed via COM
- DrvInst.exe (PID: 3792)
- DrvInst.exe (PID: 3332)
Creates files in the driver directory
- msiexec.exe (PID: 3200)
- DrvInst.exe (PID: 3792)
- DrvInst.exe (PID: 3332)
- dne2000.exe (PID: 392)
Creates files in the Windows directory
- MsiExec.exe (PID: 1212)
- DrvInst.exe (PID: 3792)
- msiexec.exe (PID: 3200)
- dneinst.exe (PID: 1468)
- DrvInst.exe (PID: 3332)
- dne2000.exe (PID: 392)
Removes files from Windows directory
- DrvInst.exe (PID: 3332)
- dne2000.exe (PID: 392)
- DrvInst.exe (PID: 3792)
Creates COM task schedule object
- dne2000.exe (PID: 392)
INFO
Reads Internet Cache Settings
- chrome.exe (PID: 2456)
Application launched itself
- chrome.exe (PID: 2456)
- msiexec.exe (PID: 3200)
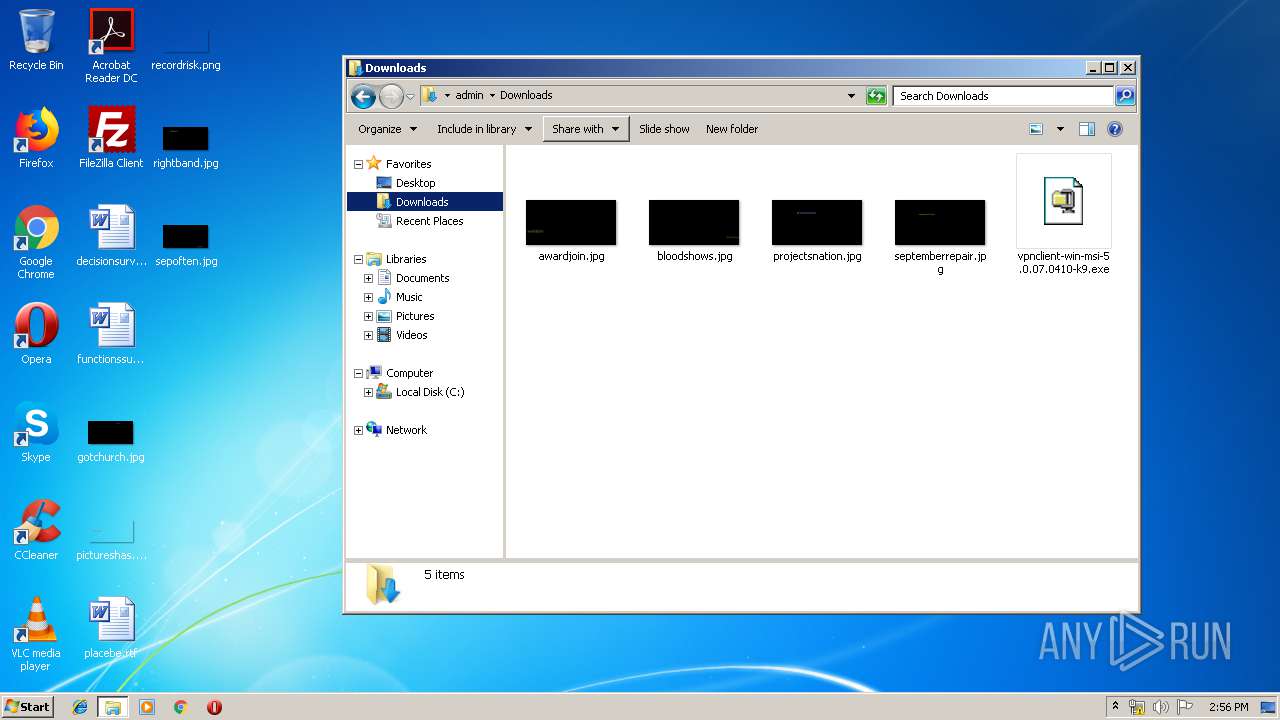
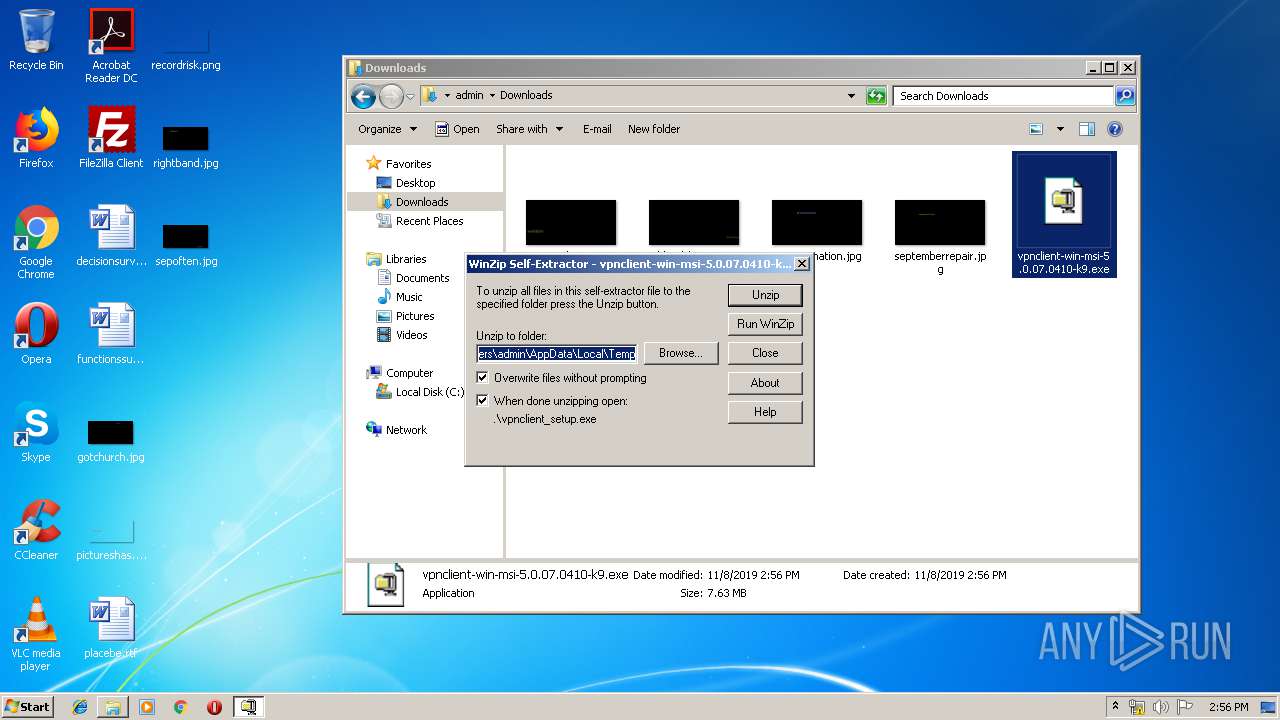
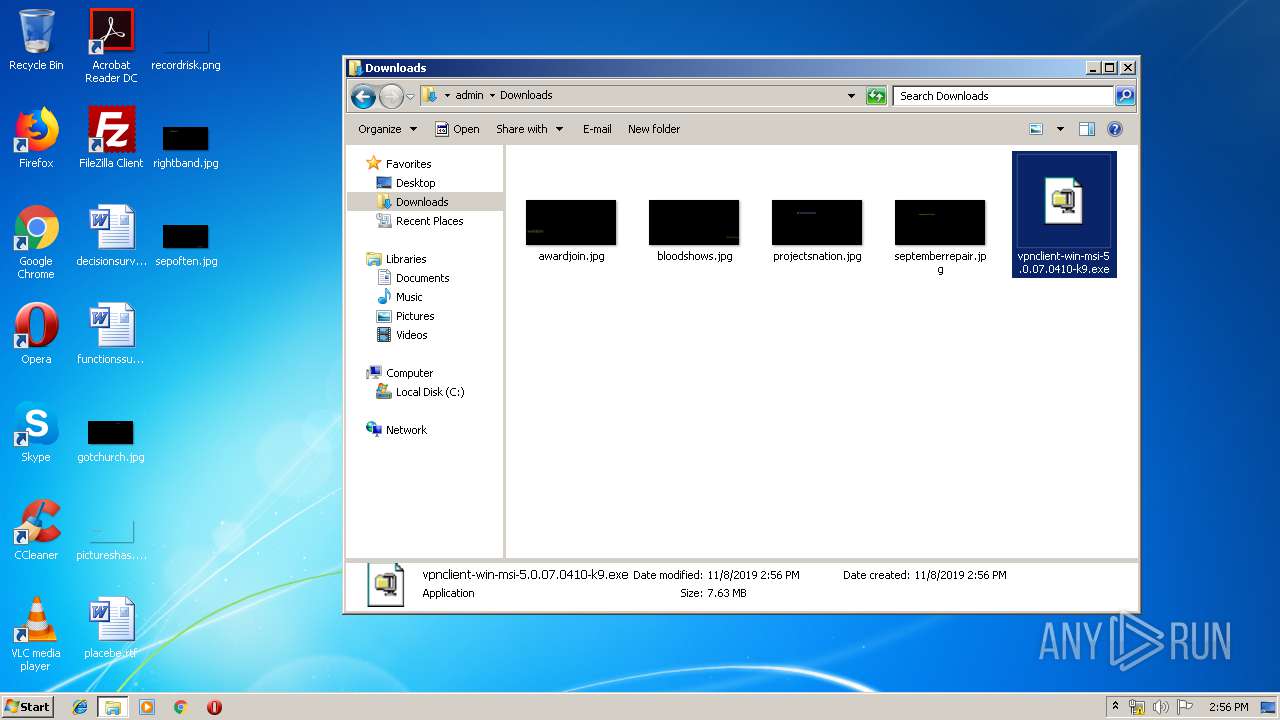
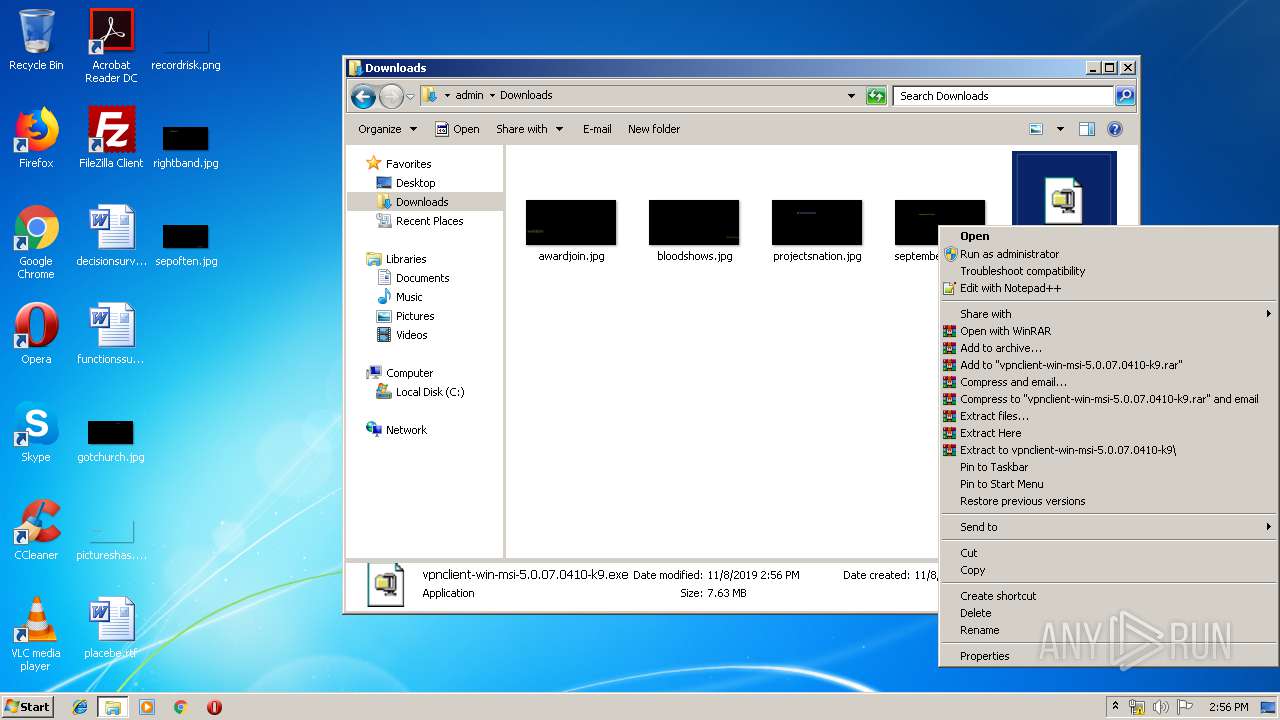
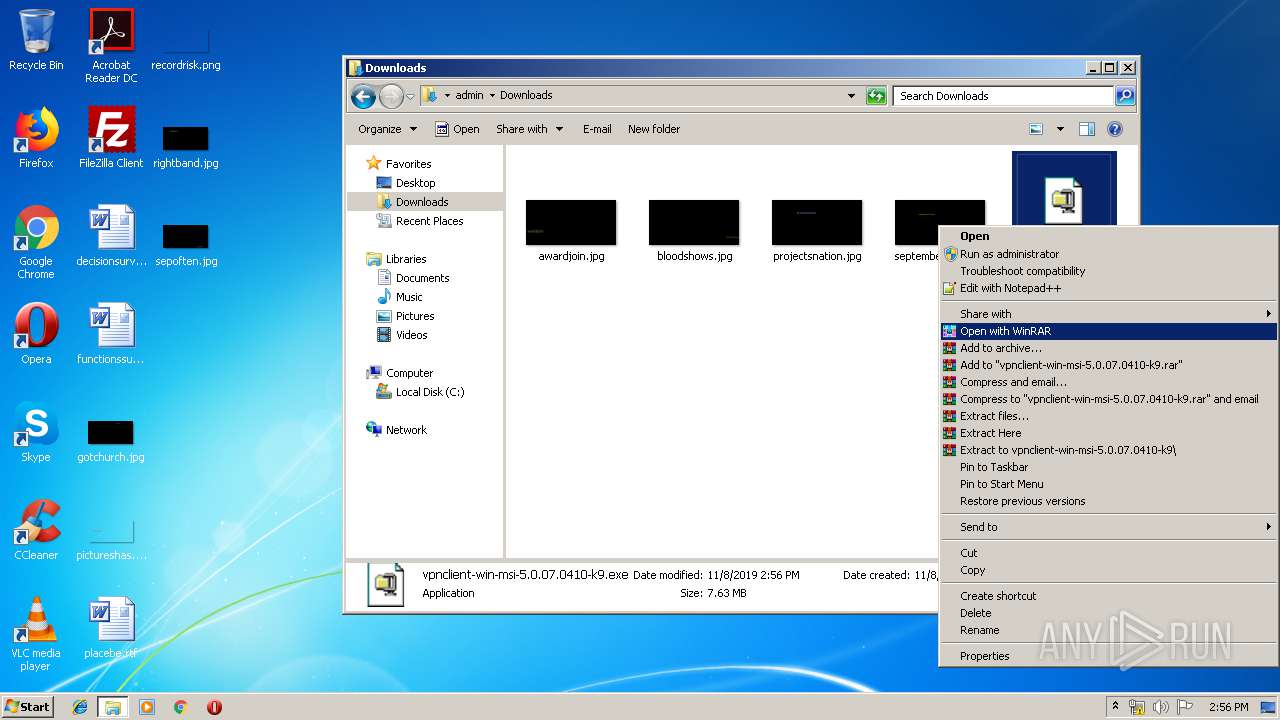
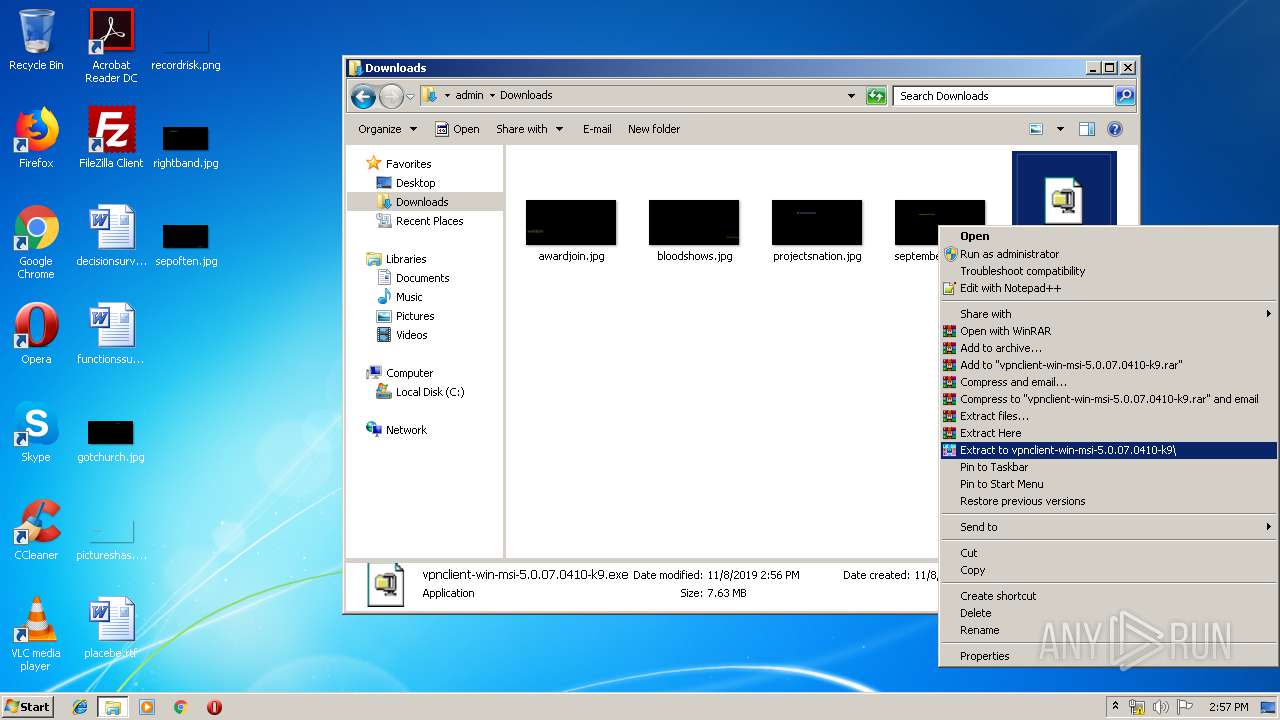
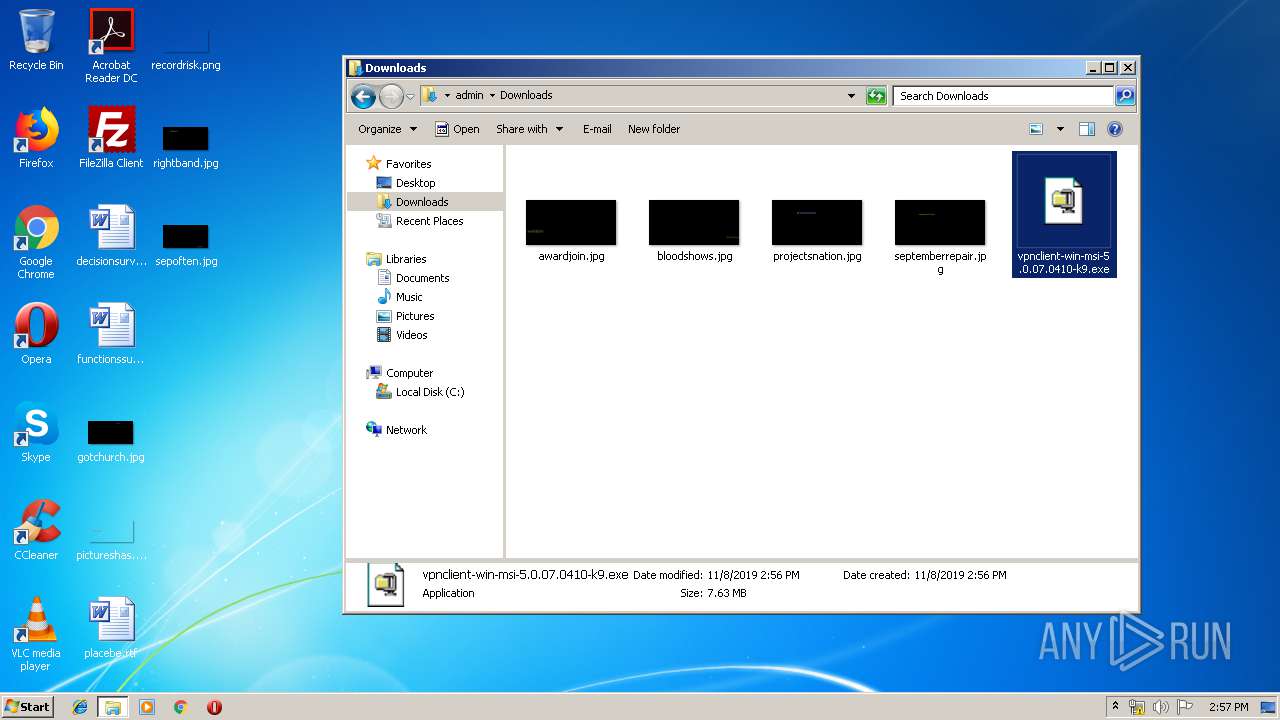
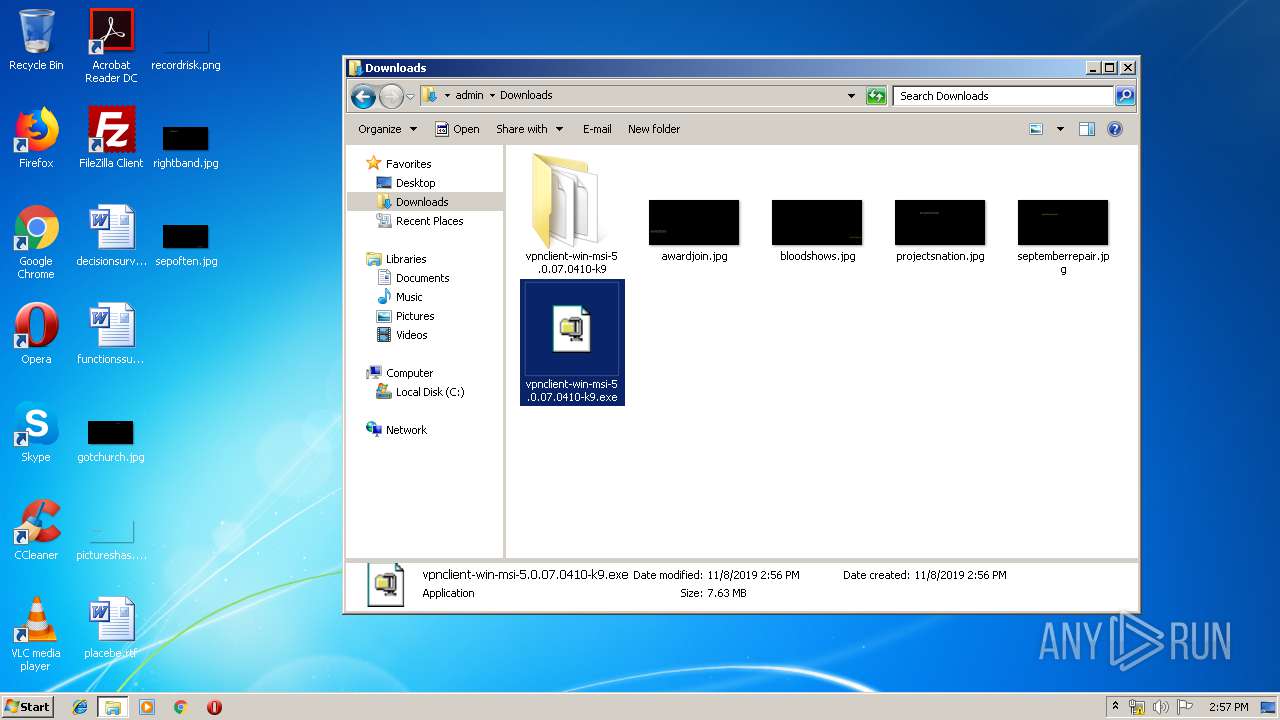
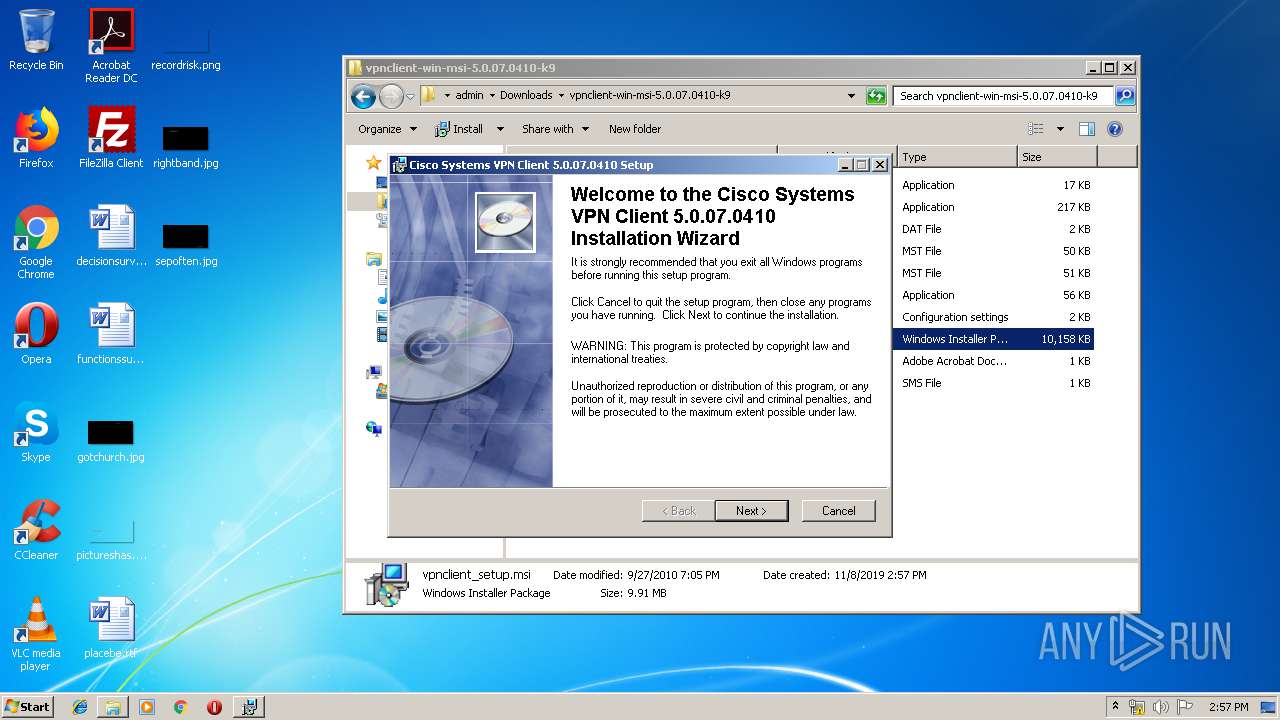
Manual execution by user
- WinRAR.exe (PID: 1048)
- msiexec.exe (PID: 408)
- explorer.exe (PID: 1556)
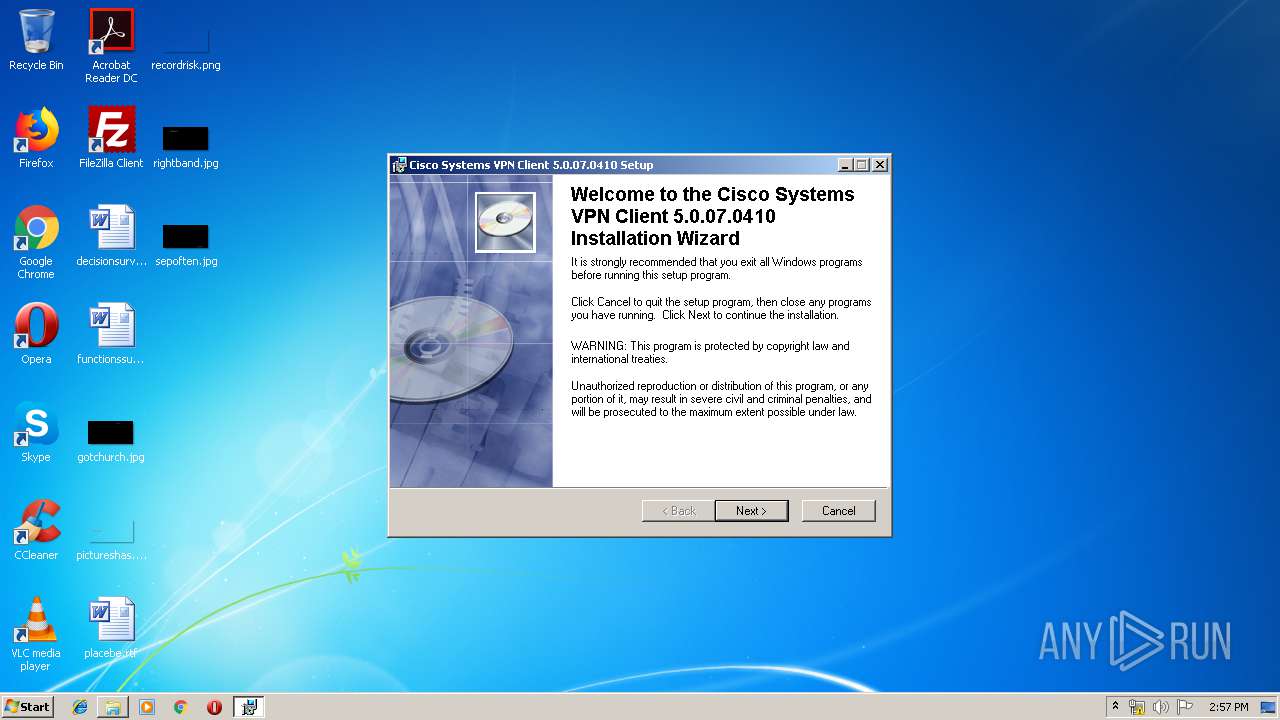
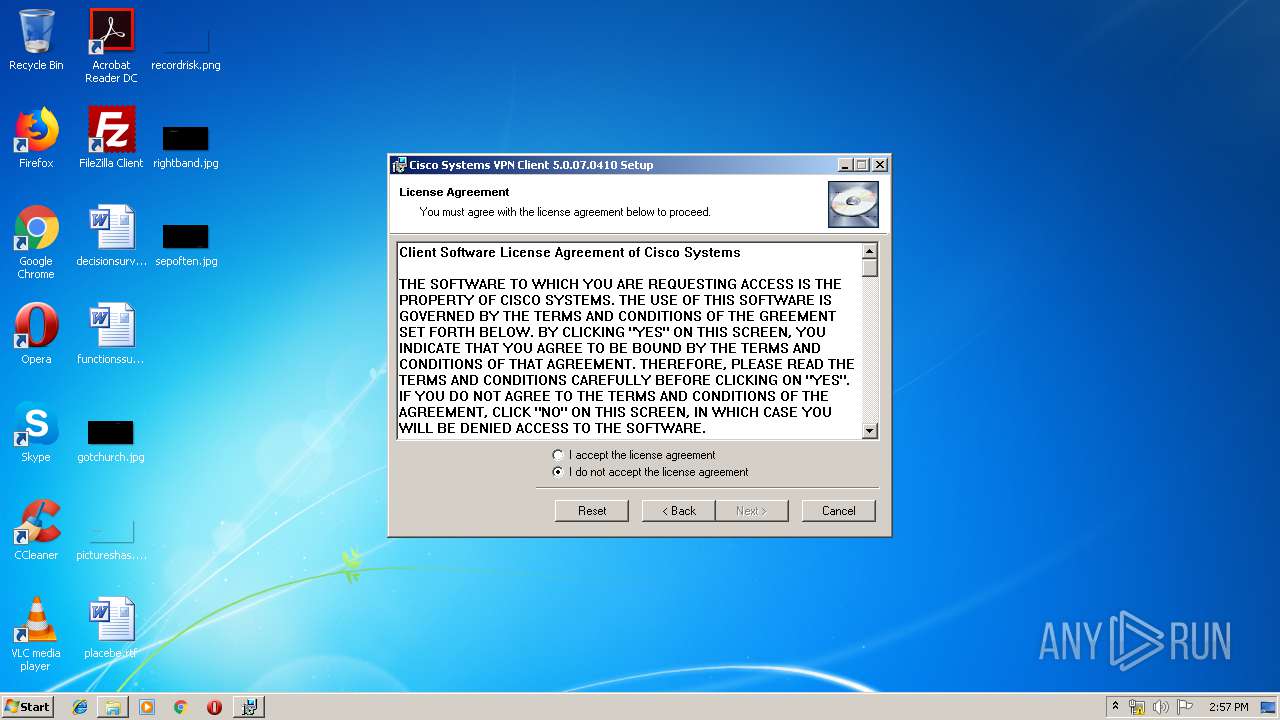
- vpnclient-win-msi-5.0.07.0410-k9.exe (PID: 1956)
Reads the hosts file
- chrome.exe (PID: 1216)
- chrome.exe (PID: 2456)
Loads dropped or rewritten executable
- MsiExec.exe (PID: 2860)
- MsiExec.exe (PID: 1212)
Searches for installed software
- msiexec.exe (PID: 3200)
Low-level read access rights to disk partition
- vssvc.exe (PID: 3052)
Creates a software uninstall entry
- msiexec.exe (PID: 3200)
Creates or modifies windows services
- msiexec.exe (PID: 3200)
Creates files in the program directory
- MsiExec.exe (PID: 2876)
- msiexec.exe (PID: 3200)
Starts application with an unusual extension
- msiexec.exe (PID: 3200)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
84
Monitored processes
42
Malicious processes
8
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 392 | C:\PROGRA~1\COMMON~1\DETERM~1\DNE\dne2000.exe -c s -l "C:\PROGRA~1\COMMON~1\DETERM~1\DNE\dne2000.inf" -i dni_dne | C:\PROGRA~1\COMMON~1\DETERM~1\DNE\dne2000.exe | dneinst.exe | ||||||||||||
User: SYSTEM Company: Deterministic Networks, Inc. Integrity Level: SYSTEM Description: DNE Network Config Exit code: 0 Version: 3.22.5.18001 Modules
| |||||||||||||||
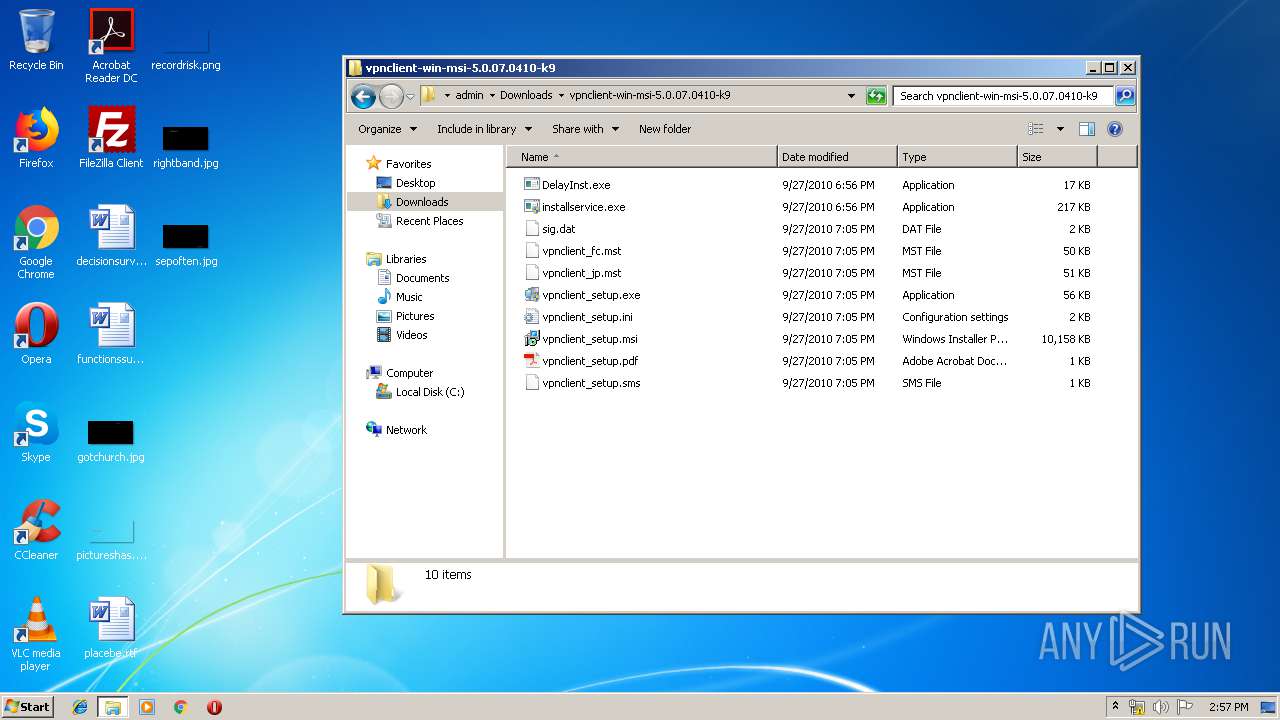
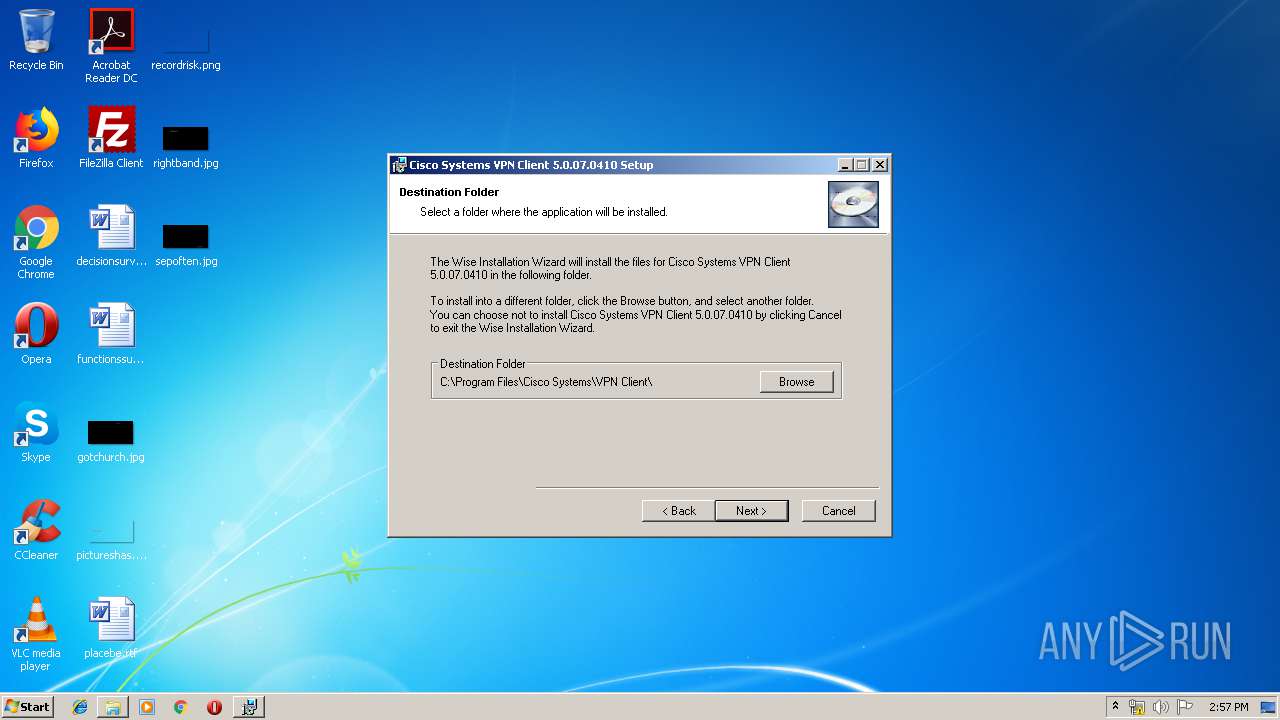
| 408 | "C:\Windows\System32\msiexec.exe" /i "C:\Users\admin\Downloads\vpnclient-win-msi-5.0.07.0410-k9\vpnclient_setup.msi" | C:\Windows\System32\msiexec.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 532 | "C:\Users\admin\AppData\Local\Temp\MSI606F.tmp" -cmd NormalizeDneRefCounts -osver 601 | C:\Users\admin\AppData\Local\Temp\MSI606F.tmp | — | msiexec.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 600 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=960,8258059197814396005,7608730329170942867,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=13607563541276352630 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2256 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 864 | C:\Windows\system32\svchost.exe -k netsvcs | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 996 | "C:\Windows\Installer\MSI9B0.tmp" -cmd CopyAndBackupFiles -src "C:\Users\admin\Downloads\vpnclient-win-msi-5.0.07.0410-k9\" -dst "C:\Program Files\Cisco Systems\VPN Client\Profiles" -file *.pcf -rb 0 | C:\Windows\Installer\MSI9B0.tmp | — | msiexec.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1048 | "C:\Program Files\WinRAR\WinRAR.exe" x -iext -ow -ver -- "C:\Users\admin\Downloads\vpnclient-win-msi-5.0.07.0410-k9.exe" C:\Users\admin\Downloads\vpnclient-win-msi-5.0.07.0410-k9\ | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 1152 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=960,8258059197814396005,7608730329170942867,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=928865748756772807 --mojo-platform-channel-handle=2540 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1212 | C:\Windows\system32\MsiExec.exe -Embedding 155162C23C1BDDDB73F5B2038559E991 | C:\Windows\system32\MsiExec.exe | msiexec.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1216 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=960,8258059197814396005,7608730329170942867,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=14065412409508111613 --mojo-platform-channel-handle=1544 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
2 715
Read events
1 974
Write events
735
Delete events
6
Modification events
| (PID) Process: | (2456) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2456) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2456) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2456) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2456) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2448) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2456-13217698394963375 |
Value: 259 | |||
| (PID) Process: | (2456) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2456) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2456) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 1512-13197841398593750 |
Value: 0 | |||
| (PID) Process: | (2456) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
84
Suspicious files
69
Text files
373
Unknown types
43
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2456 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\feb7fd29-50cd-4301-865f-6ceba9bc97c2.tmp | — | |
MD5:— | SHA256:— | |||
| 2456 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000020.dbtmp | — | |
MD5:— | SHA256:— | |||
| 864 | svchost.exe | C:\Windows\appcompat\programs\RecentFileCache.bcf | txt | |
MD5:— | SHA256:— | |||
| 2456 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2456 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF39a6ca.TMP | text | |
MD5:— | SHA256:— | |||
| 2456 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2456 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2456 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old~RF39a737.TMP | text | |
MD5:— | SHA256:— | |||
| 2456 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 2456 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
39
DNS requests
19
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1216 | chrome.exe | GET | 204 | 172.217.23.163:80 | http://www.gstatic.com/generate_204 | US | — | — | whitelisted |
1216 | chrome.exe | GET | — | 172.217.23.163:80 | http://www.gstatic.com/generate_204 | US | — | — | whitelisted |
1216 | chrome.exe | GET | 200 | 74.125.4.216:80 | http://r2---sn-aigzrney.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx?cms_redirect=yes&mip=185.92.25.20&mm=28&mn=sn-aigzrney&ms=nvh&mt=1573224742&mv=m&mvi=1&pl=24&shardbypass=yes | US | crx | 293 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1216 | chrome.exe | 216.58.205.227:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
1216 | chrome.exe | 216.58.207.77:443 | accounts.google.com | Google Inc. | US | whitelisted |
1216 | chrome.exe | 216.58.208.36:443 | www.google.com | Google Inc. | US | whitelisted |
1216 | chrome.exe | 129.66.13.111:443 | oldwww.asc.edu | Alabama Supercomputer Network | US | unknown |
1216 | chrome.exe | 172.217.23.110:443 | clients2.google.com | Google Inc. | US | whitelisted |
1216 | chrome.exe | 172.217.23.163:80 | www.gstatic.com | Google Inc. | US | whitelisted |
1216 | chrome.exe | 172.217.21.193:443 | clients2.googleusercontent.com | Google Inc. | US | whitelisted |
1216 | chrome.exe | 172.217.23.163:443 | www.gstatic.com | Google Inc. | US | whitelisted |
1216 | chrome.exe | 172.217.23.106:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
1216 | chrome.exe | 172.217.21.238:443 | sb-ssl.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
oldwww.asc.edu |
| unknown |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com |
| malicious |
ssl.gstatic.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
clients2.google.com |
| whitelisted |
redirector.gvt1.com |
| whitelisted |
r2---sn-aigzrney.gvt1.com |
| whitelisted |
clients2.googleusercontent.com |
| whitelisted |
Threats
Process | Message |
|---|---|
MsiExec.exe | UpgradeCheck: Begin...
|
MsiExec.exe | UpgradeCheck: ...End
|
MsiExec.exe | DnecaLogInit starting (dneca, 1.3.2.17951)
|
MsiExec.exe | DnecaLogInit starting (dneca, 1.3.2.17951)
|
MsiExec.exe | DnLogInit, logfile fqn = 'C:\Windows\temp\dneca.log'
|
MsiExec.exe | DnLogInit, logfile fqn = 'C:\Windows\temp\dneca.log'
|
MsiExec.exe | LOG: |
MsiExec.exe | MakeDirectory, looking for C:\Windows\temp |
MsiExec.exe | LOG: |
MsiExec.exe | MakeDirectory, directory exists already |