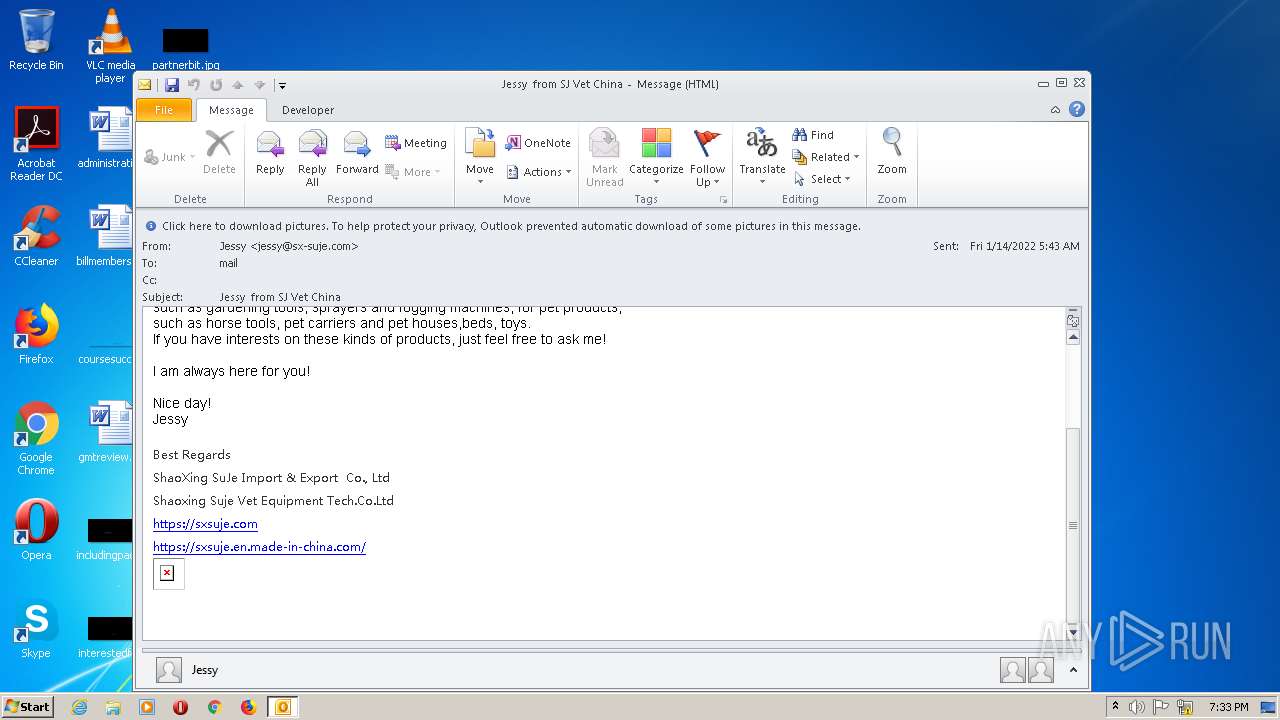
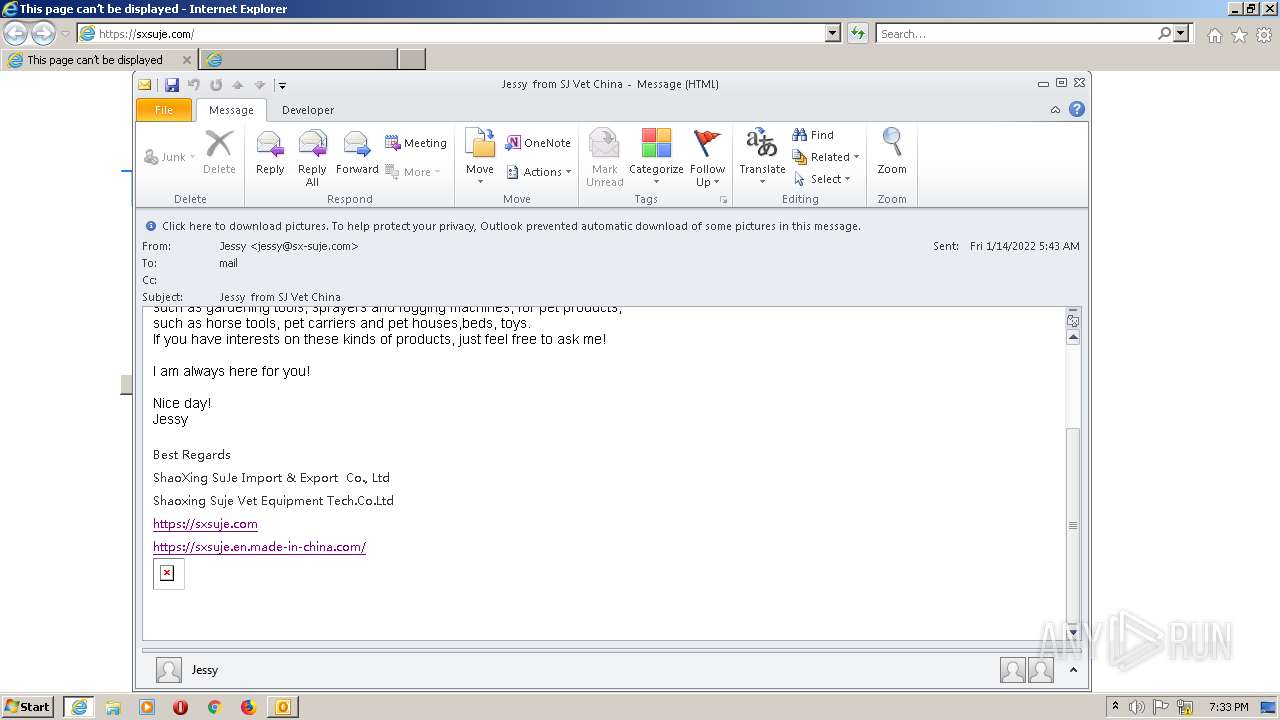
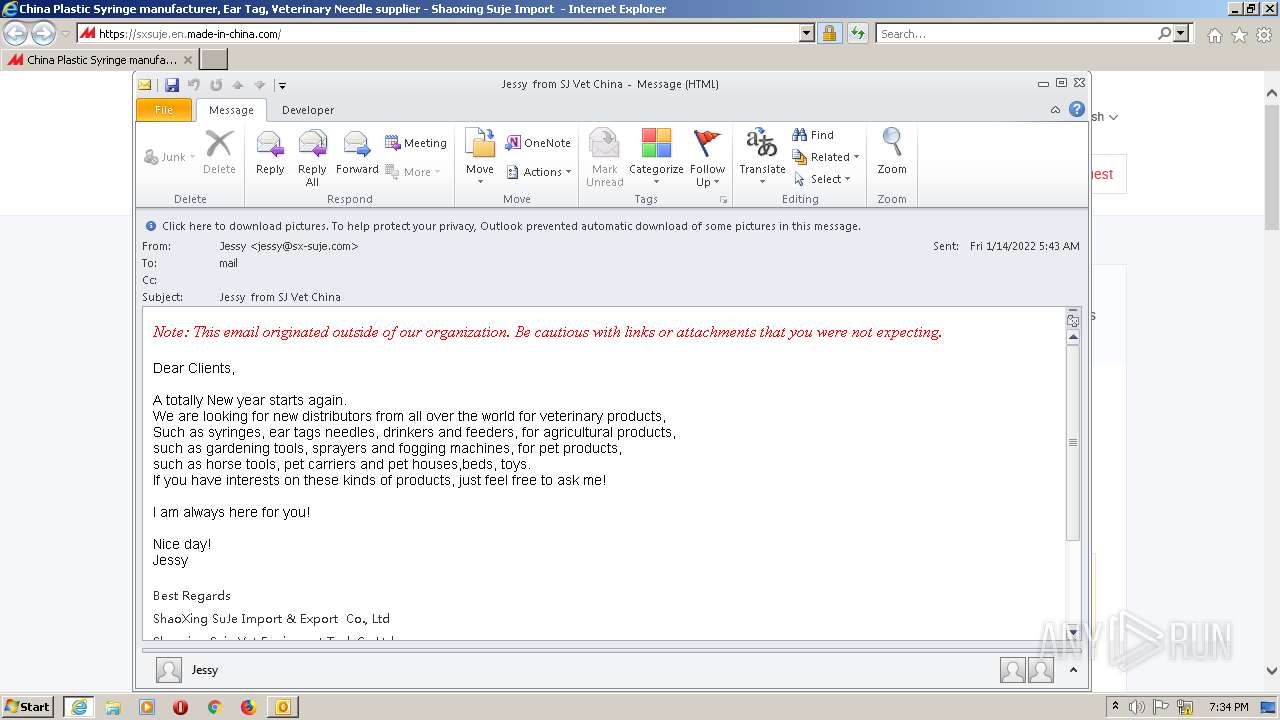
| File name: | Jessy from SJ Vet China (13.4 KB).msg |
| Full analysis: | https://app.any.run/tasks/cb34418d-aae7-4201-a871-72614c204a8d |
| Verdict: | Malicious activity |
| Analysis date: | January 14, 2022, 19:33:15 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 64 bit) |
| Indicators: | |
| MIME: | application/vnd.ms-outlook |
| File info: | CDFV2 Microsoft Outlook Message |
| MD5: | AE5EA07D1DD3A4F4F09E29847F472400 |
| SHA1: | CA61D9682313E2BBC1987E1E0EB12F1B6840B8FE |
| SHA256: | 607D5C050C77B8F588627F72BE626D67AF5A9E2F9CBB10AB07A31E68D5305185 |
| SSDEEP: | 384:8OTbAcevtYLQoTd2tzGFFzYmAVlgFwfBNDNhYEUs9PbtEDToPkxlNwl7anKKuSWa:8OivmLPQBNDNhTUsFyZgl7ac3MYn70N |
MALICIOUS
Unusual execution from Microsoft Office
- OUTLOOK.EXE (PID: 3048)
SUSPICIOUS
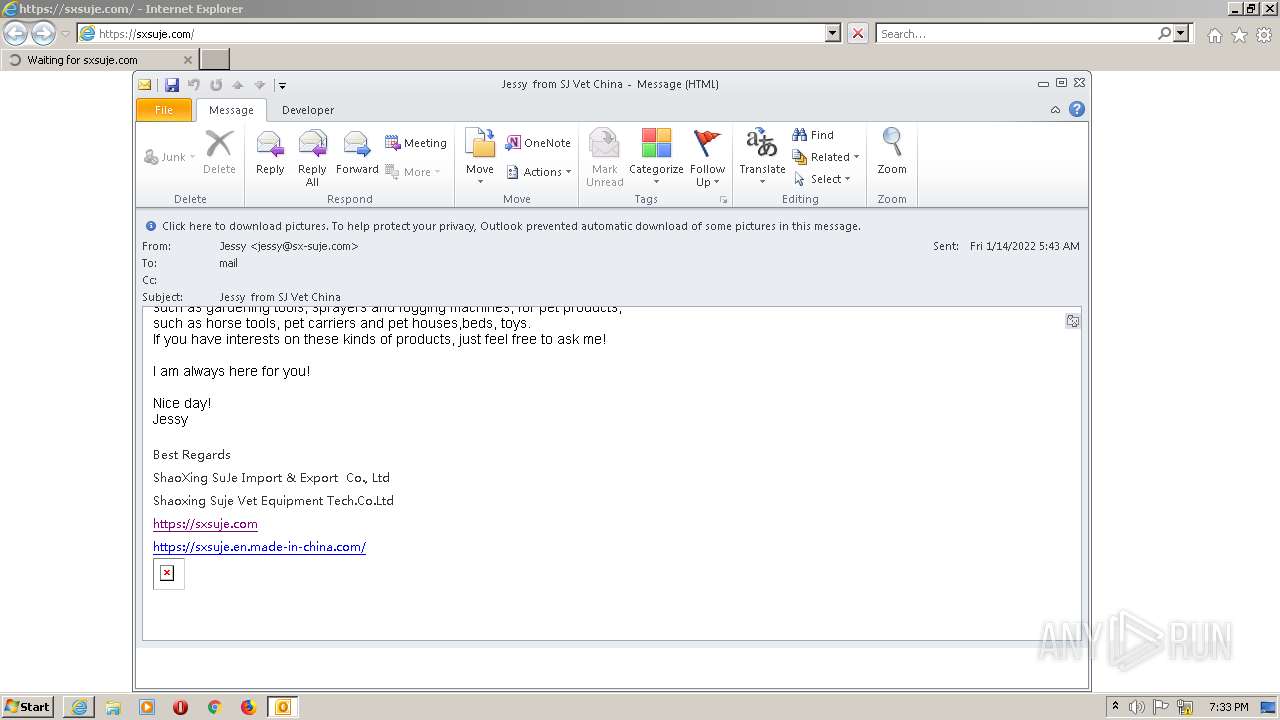
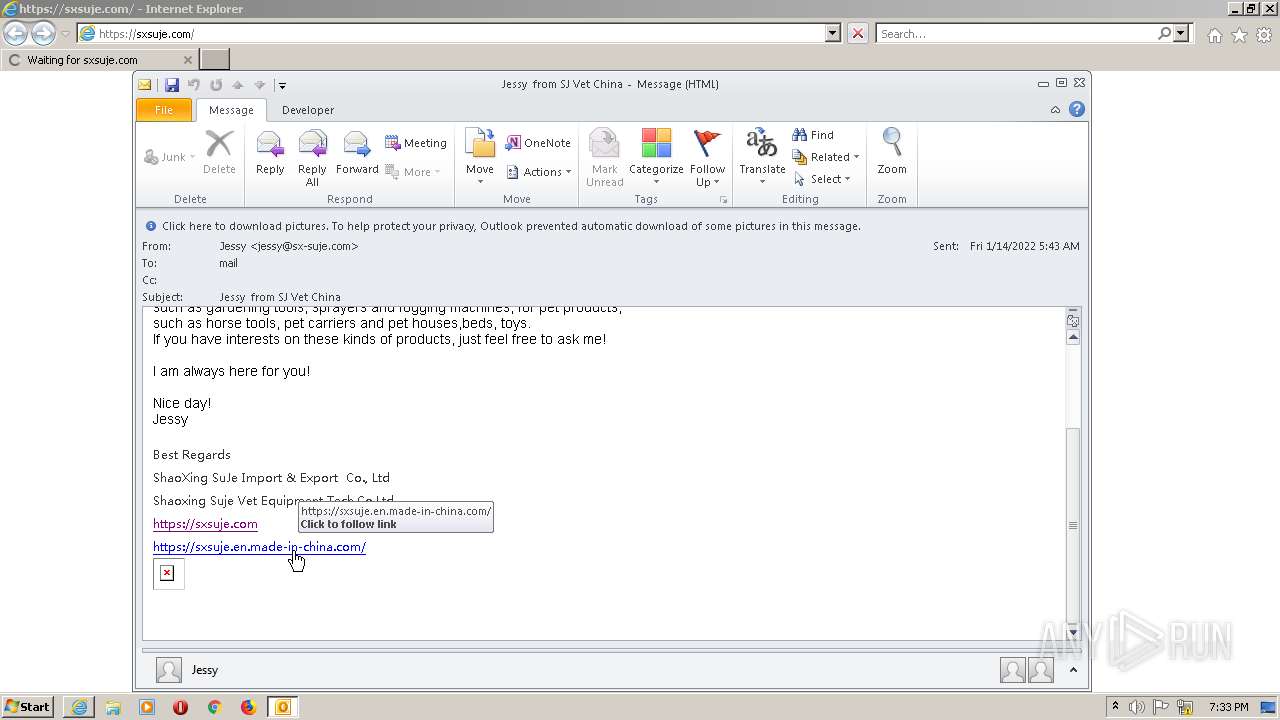
Starts Internet Explorer
- OUTLOOK.EXE (PID: 3048)
Reads Microsoft Outlook installation path
- IEXPLORE.EXE (PID: 1448)
- IEXPLORE.EXE (PID: 1396)
Reads the computer name
- FlashUtil64_27_0_0_187_ActiveX.exe (PID: 1660)
Creates files in the user directory
- FlashUtil64_27_0_0_187_ActiveX.exe (PID: 1660)
Executed via COM
- FlashUtil64_27_0_0_187_ActiveX.exe (PID: 1660)
Checks supported languages
- FlashUtil64_27_0_0_187_ActiveX.exe (PID: 1660)
INFO
Checks supported languages
- OUTLOOK.EXE (PID: 3048)
- IEXPLORE.EXE (PID: 1448)
- iexplore.exe (PID: 2264)
- IEXPLORE.EXE (PID: 1396)
Reads the computer name
- OUTLOOK.EXE (PID: 3048)
- iexplore.exe (PID: 2264)
- IEXPLORE.EXE (PID: 1448)
- IEXPLORE.EXE (PID: 1396)
Searches for installed software
- OUTLOOK.EXE (PID: 3048)
Changes internet zones settings
- iexplore.exe (PID: 2264)
Checks Windows Trust Settings
- iexplore.exe (PID: 2264)
- IEXPLORE.EXE (PID: 1396)
Reads settings of System Certificates
- iexplore.exe (PID: 2264)
- IEXPLORE.EXE (PID: 1396)
Reads internet explorer settings
- IEXPLORE.EXE (PID: 1448)
- IEXPLORE.EXE (PID: 1396)
Creates files in the user directory
- IEXPLORE.EXE (PID: 1396)
- iexplore.exe (PID: 2264)
- OUTLOOK.EXE (PID: 3048)
Reads CPU info
- IEXPLORE.EXE (PID: 1396)
Reads Microsoft Office registry keys
- OUTLOOK.EXE (PID: 3048)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msg | | | Outlook Message (58.9) |
|---|---|---|
| .oft | | | Outlook Form Template (34.4) |
Total processes
43
Monitored processes
5
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1396 | "C:\Program Files (x86)\Internet Explorer\IEXPLORE.EXE" SCODEF:2264 CREDAT:267533 /prefetch:2 | C:\Program Files (x86)\Internet Explorer\IEXPLORE.EXE | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 1448 | "C:\Program Files (x86)\Internet Explorer\IEXPLORE.EXE" SCODEF:2264 CREDAT:267521 /prefetch:2 | C:\Program Files (x86)\Internet Explorer\IEXPLORE.EXE | — | iexplore.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 1660 | C:\Windows\system32\Macromed\Flash\FlashUtil64_27_0_0_187_ActiveX.exe -Embedding | C:\Windows\system32\Macromed\Flash\FlashUtil64_27_0_0_187_ActiveX.exe | — | svchost.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: MEDIUM Description: Adobe� Flash� Player Installer/Uninstaller 27.0 r0 Exit code: 0 Version: 27,0,0,187 Modules
| |||||||||||||||
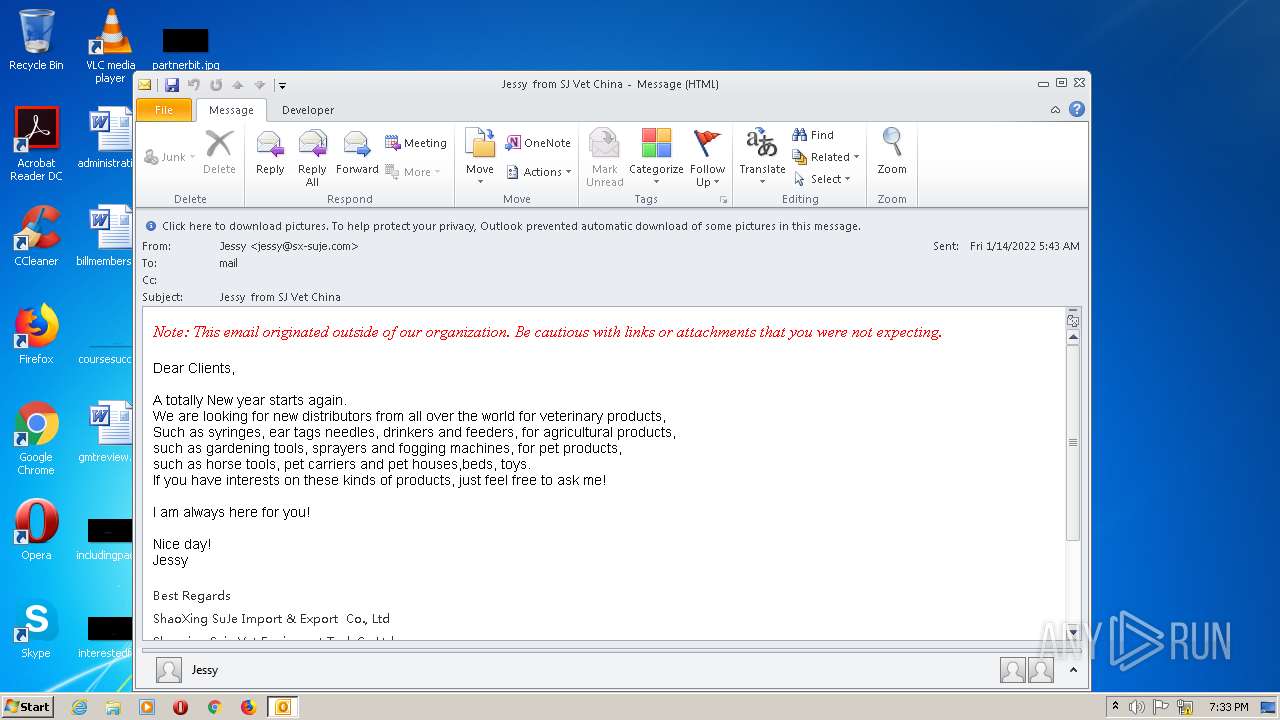
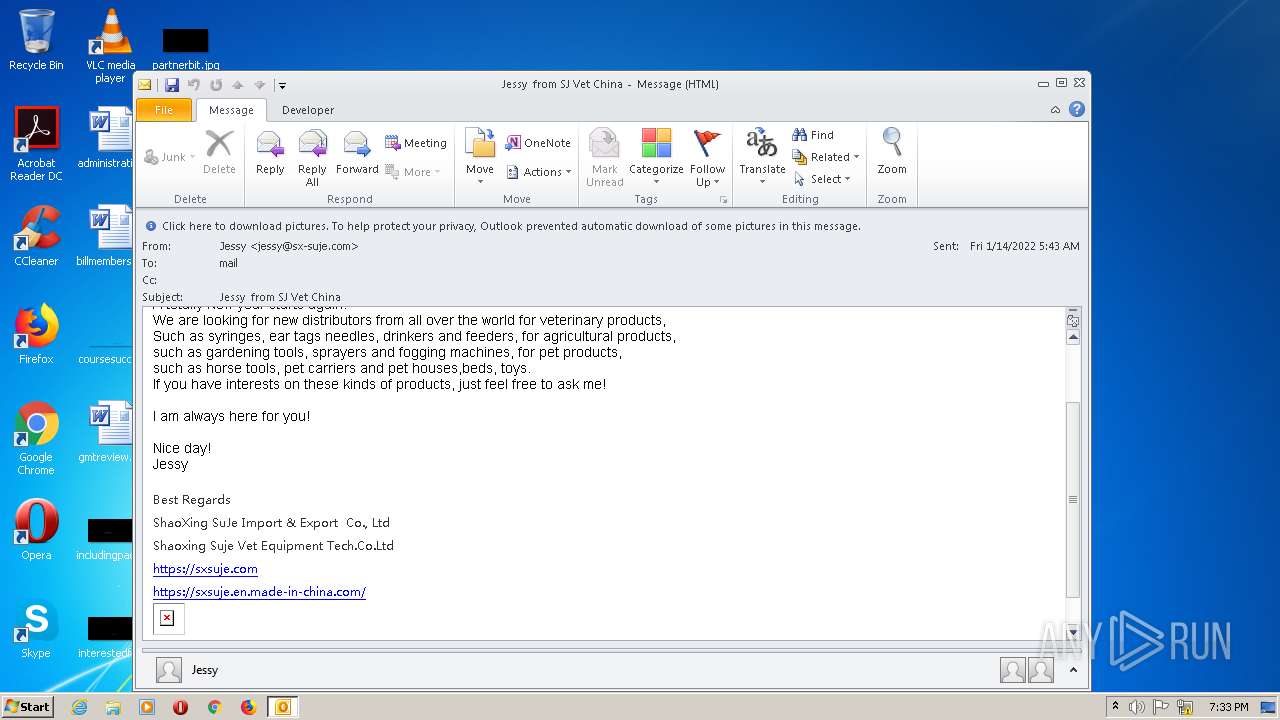
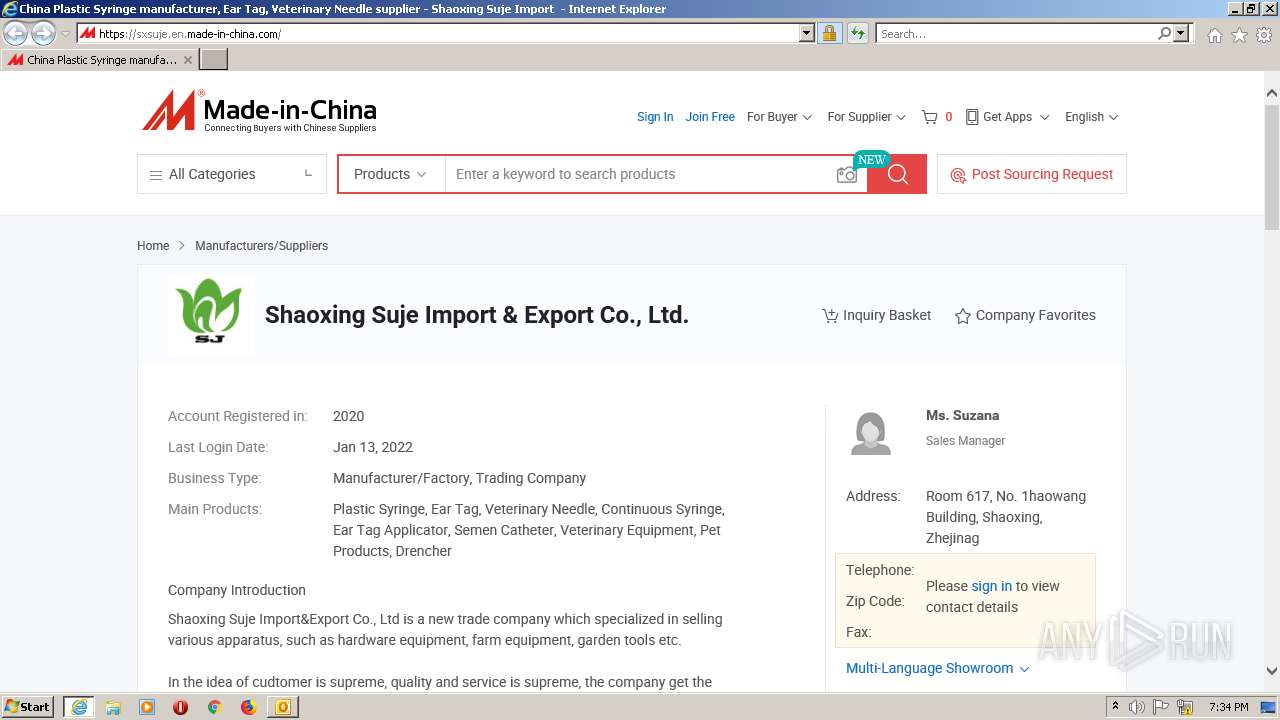
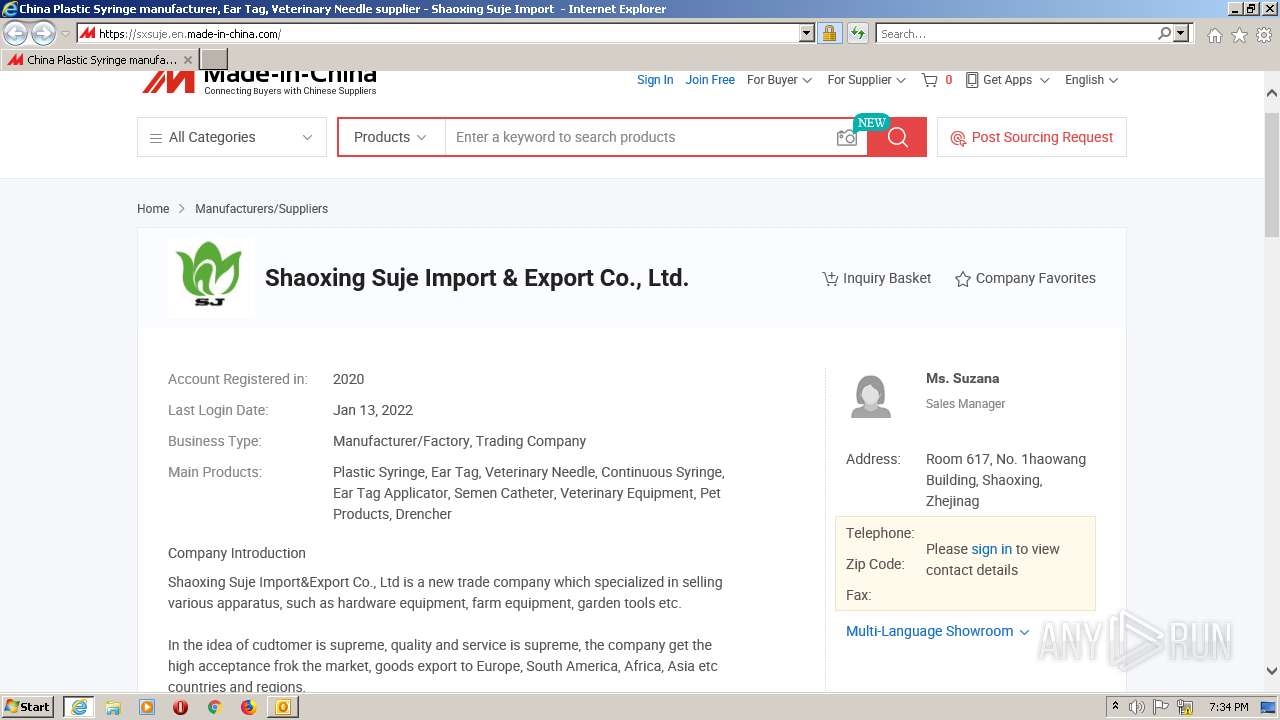
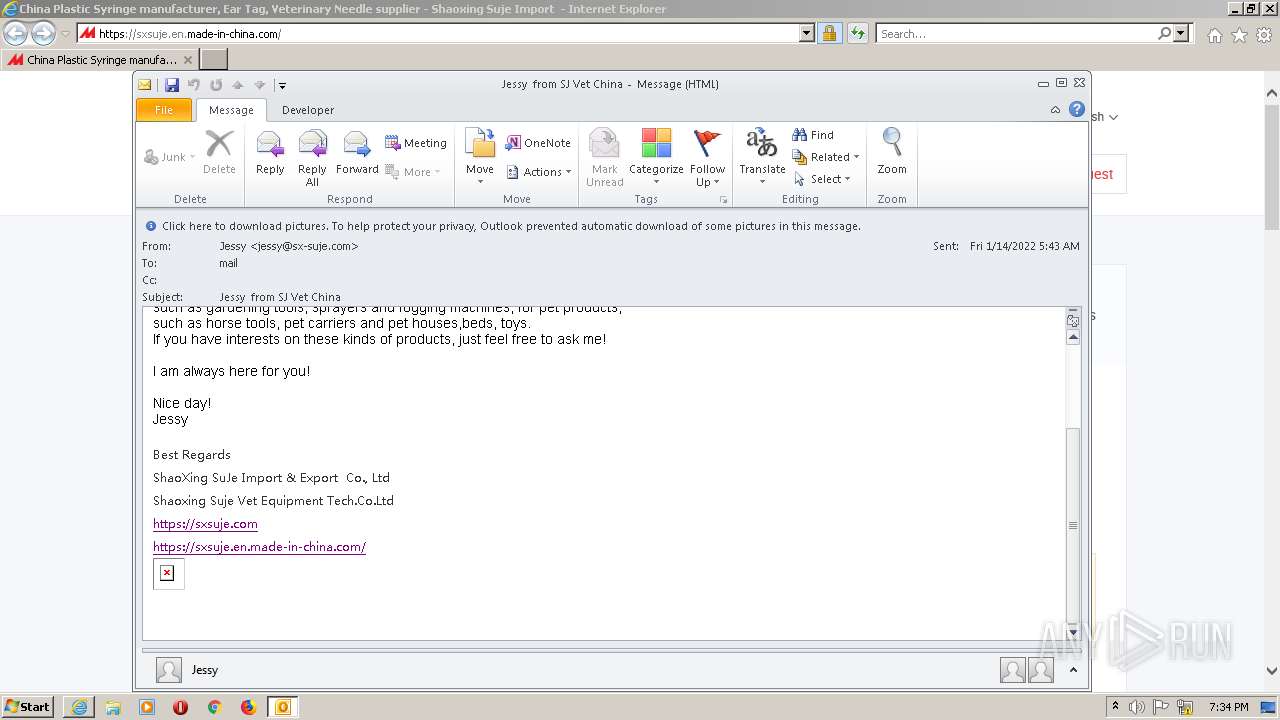
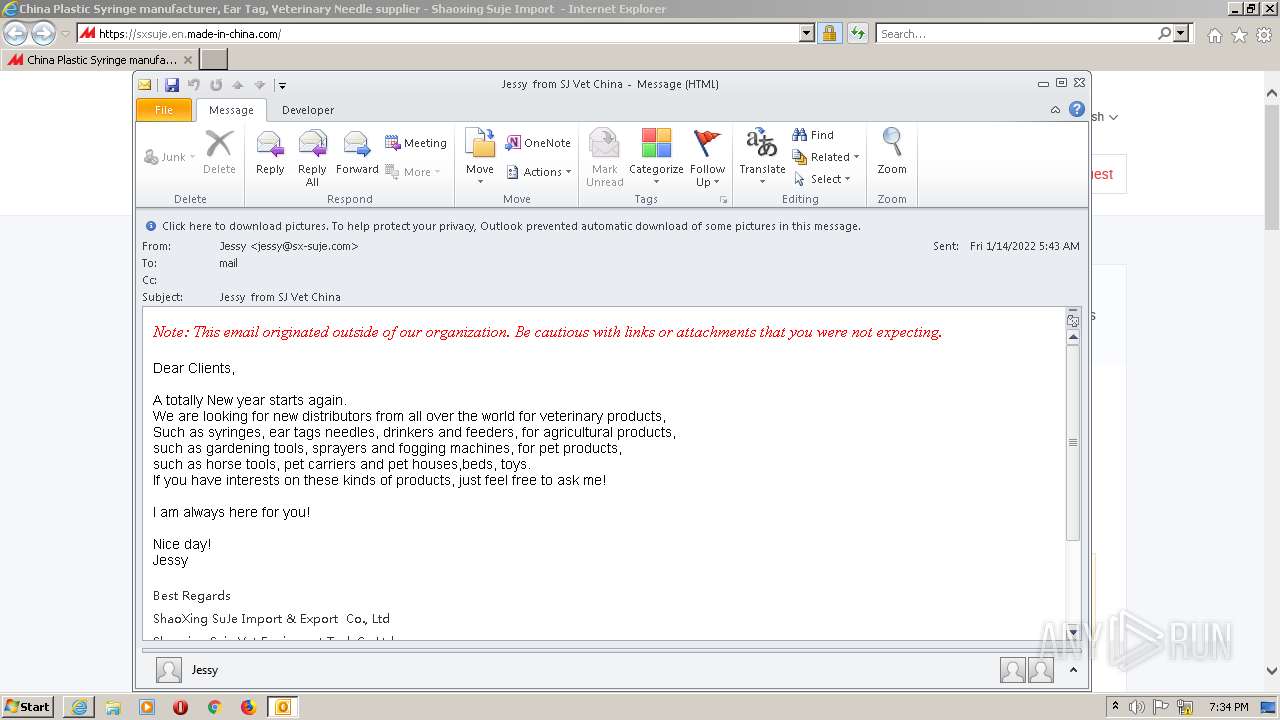
| 2264 | "C:\Program Files\Internet Explorer\iexplore.exe" https://sxsuje.com/ | C:\Program Files\Internet Explorer\iexplore.exe | OUTLOOK.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3048 | "C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE" /f "C:\Users\admin\Desktop\Jessy from SJ Vet China (13.4 KB).msg" | C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE | Explorer.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Outlook Exit code: 0 Version: 14.0.4760.1000 Modules
| |||||||||||||||
Total events
11 502
Read events
10 383
Write events
1 100
Delete events
19
Modification events
| (PID) Process: | (3048) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (3048) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (3048) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: Off | |||
| (PID) Process: | (3048) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (3048) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (3048) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (3048) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (3048) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (3048) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (3048) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1055 |
Value: Off | |||
Executable files
0
Suspicious files
11
Text files
139
Unknown types
18
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3048 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CVR63EA.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3048 | OUTLOOK.EXE | C:\Users\admin\Documents\Outlook Files\Outlook Data File - NoMail.pst | — | |
MD5:— | SHA256:— | |||
| 3048 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\outlook logging\firstrun.log | text | |
MD5:— | SHA256:— | |||
| 3048 | OUTLOOK.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$rmalEmail.dotm | pgc | |
MD5:— | SHA256:— | |||
| 2264 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\K78MRVB5\favicon[1].ico | image | |
MD5:DA597791BE3B6E732F0BC8B20E38EE62 | SHA256:5B2C34B3C4E8DD898B664DBA6C3786E2FF9869EFF55D673AA48361F11325ED07 | |||
| 1396 | IEXPLORE.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\HMWGQD5Z.txt | text | |
MD5:— | SHA256:— | |||
| 1396 | IEXPLORE.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\IF5NHPDD.txt | text | |
MD5:— | SHA256:— | |||
| 3048 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\FORMS\FRMDATA64.DAT | binary | |
MD5:C4643157E488AC6D771054CAD7D50D84 | SHA256:D4FF48EB72AA94E3BA215C87B198733048E75105D024CCA42960EF96A8E04EA6 | |||
| 3048 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Outlook\RoamCache\Stream_ConversationPrefs_2_AB5BD17E25E8BF469D5EC4C0300AC067.dat | xml | |
MD5:57F30B1BCA811C2FCB81F4C13F6A927B | SHA256:612BAD93621991CB09C347FF01EC600B46617247D5C041311FF459E247D8C2D3 | |||
| 3048 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\{2C53D9EE-771A-4F48-A809-998B8EEEE7CD}\{1C306CB1-771E-4B4B-A902-86E897877F5B}.png | image | |
MD5:4C61C12EDBC453D7AE184976E95258E1 | SHA256:296526F9A716C1AA91BA5D6F69F0EB92FDF79C2CB2CFCF0CEB22B7CCBC27035F | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
81
DNS requests
41
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3048 | OUTLOOK.EXE | GET | — | 64.4.26.155:80 | http://config.messenger.msn.com/config/msgrconfig.asmx?op=GetOlcConfig | US | — | — | whitelisted |
1396 | IEXPLORE.EXE | GET | 200 | 2.16.106.186:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?428ce02c5e9a1523 | unknown | compressed | 59.9 Kb | whitelisted |
1396 | IEXPLORE.EXE | GET | 200 | 104.18.11.39:80 | http://cacerts.digicert.com/DigiCertGlobalRootG2.crt | US | der | 914 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3048 | OUTLOOK.EXE | 64.4.26.155:80 | config.messenger.msn.com | Microsoft Corporation | US | whitelisted |
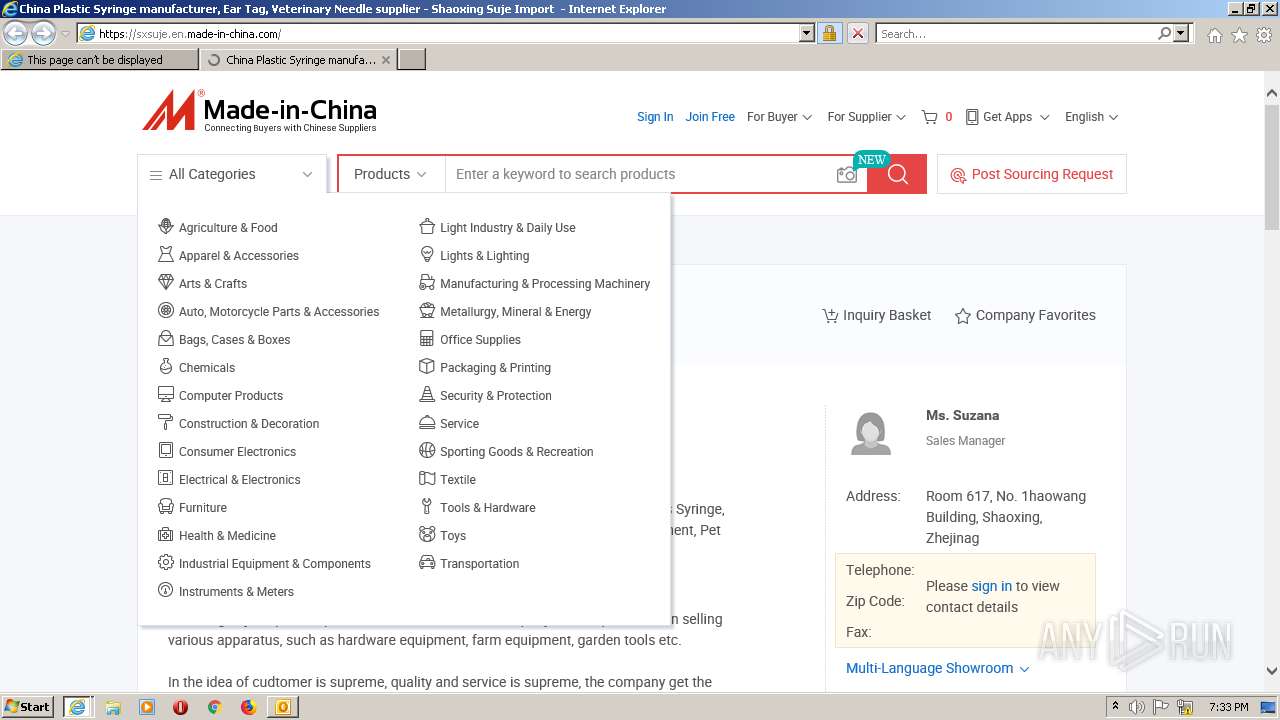
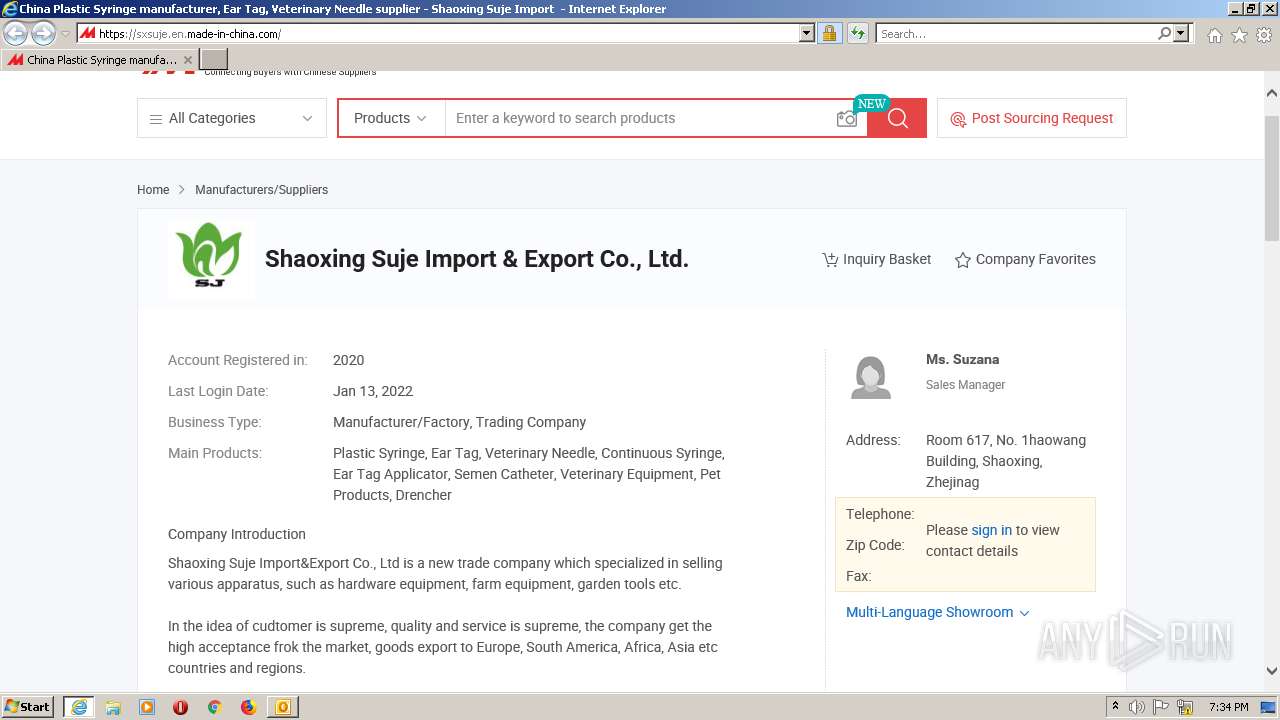
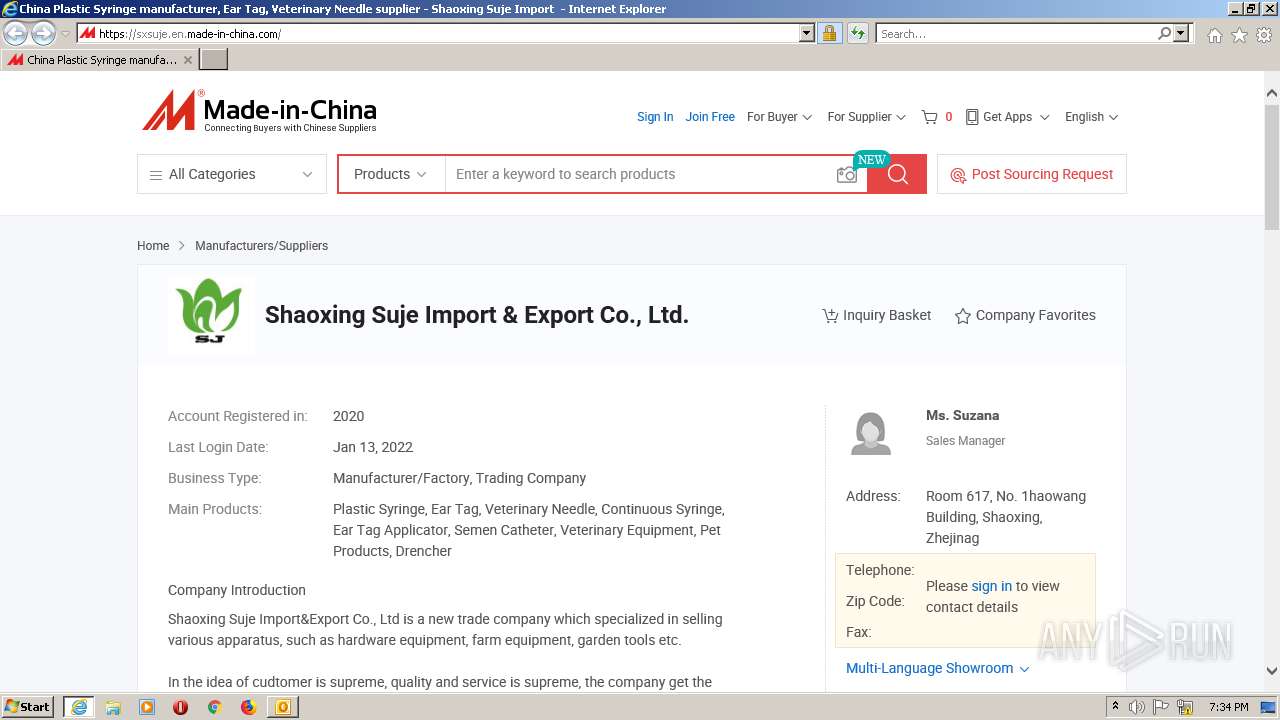
1396 | IEXPLORE.EXE | 2.16.186.131:443 | sxsuje.en.made-in-china.com | Akamai International B.V. | — | whitelisted |
2264 | iexplore.exe | 204.79.197.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
1396 | IEXPLORE.EXE | 2.16.187.56:443 | stat.made-in-china.com | Akamai International B.V. | — | whitelisted |
2264 | iexplore.exe | 2.16.186.131:443 | sxsuje.en.made-in-china.com | Akamai International B.V. | — | whitelisted |
1396 | IEXPLORE.EXE | 142.250.186.130:443 | www.googleadservices.com | Google Inc. | US | whitelisted |
1396 | IEXPLORE.EXE | 185.60.216.19:443 | connect.facebook.net | Facebook, Inc. | IE | whitelisted |
1396 | IEXPLORE.EXE | 2.16.186.154:443 | www.micstatic.com | Akamai International B.V. | — | whitelisted |
1396 | IEXPLORE.EXE | 2.16.186.195:443 | www.made-in-china.com | Akamai International B.V. | — | whitelisted |
1396 | IEXPLORE.EXE | 172.217.16.136:443 | www.googletagmanager.com | Google Inc. | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
config.messenger.msn.com |
| whitelisted |
sxsuje.com |
| unknown |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
sxsuje.en.made-in-china.com |
| suspicious |
www.micstatic.com |
| whitelisted |
stat.made-in-china.com |
| suspicious |
www.made-in-china.com |
| whitelisted |
pylon.micstatic.com |
| suspicious |
image.made-in-china.com |
| whitelisted |