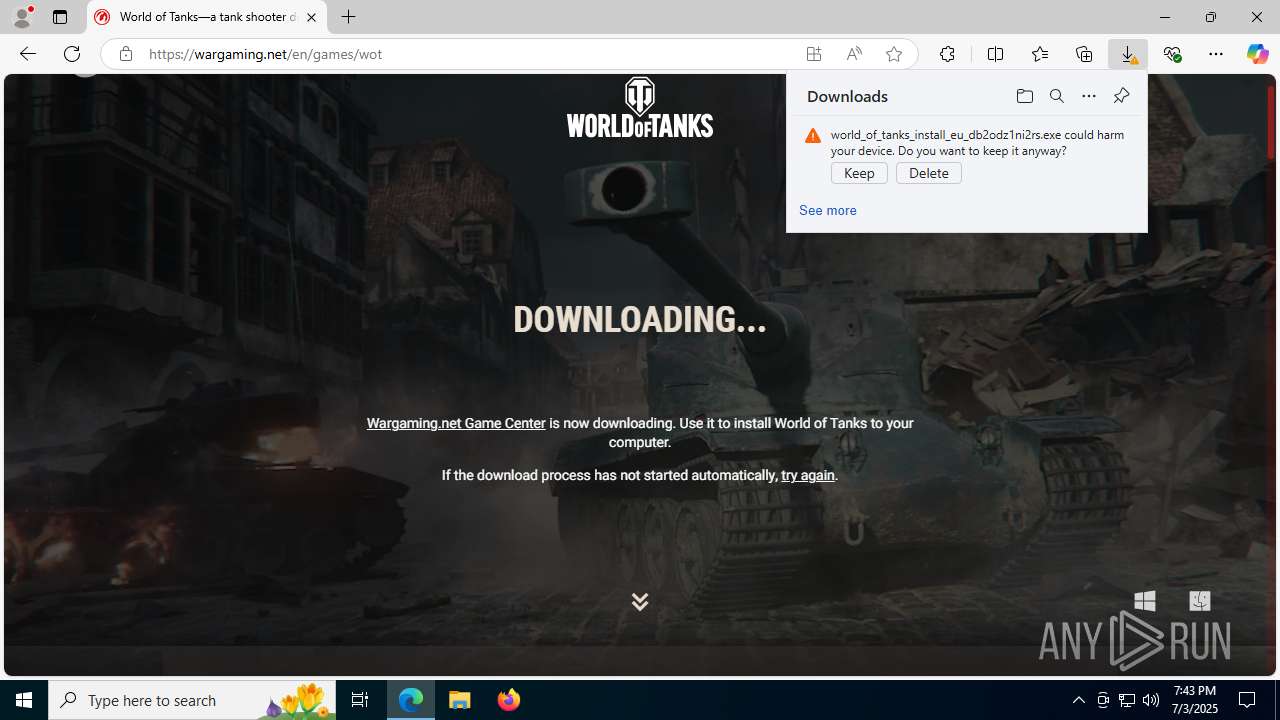
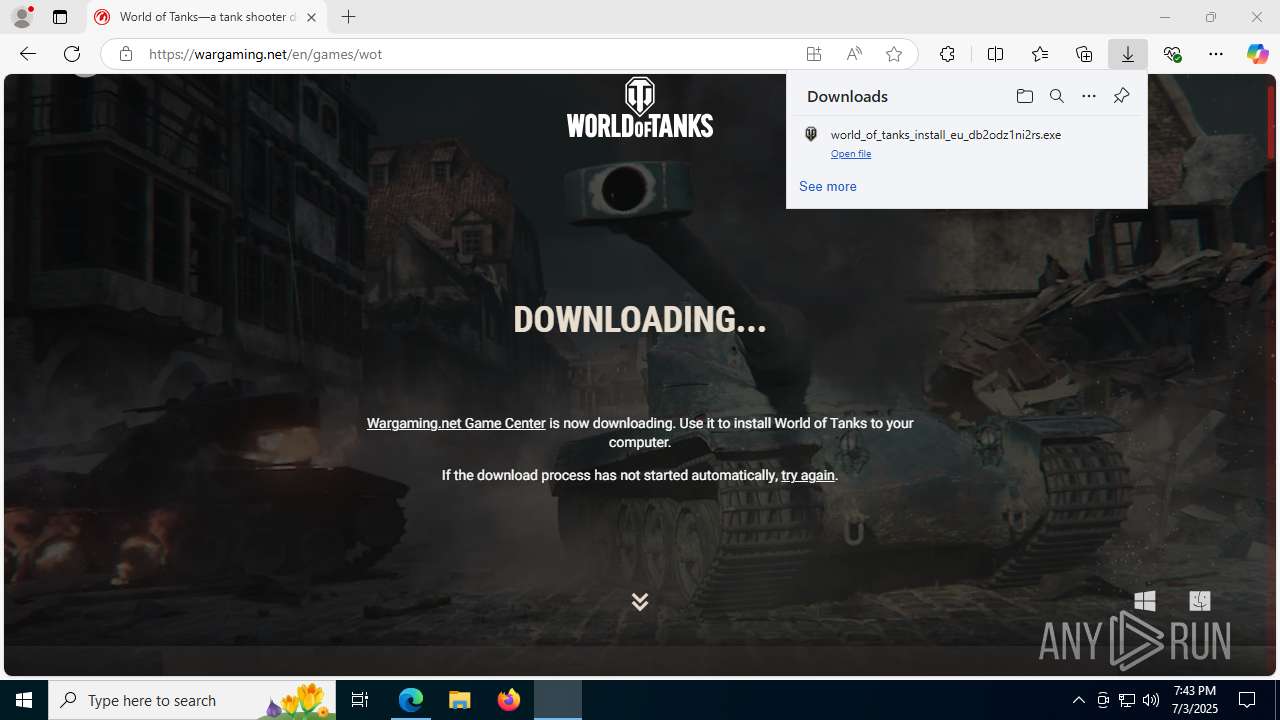
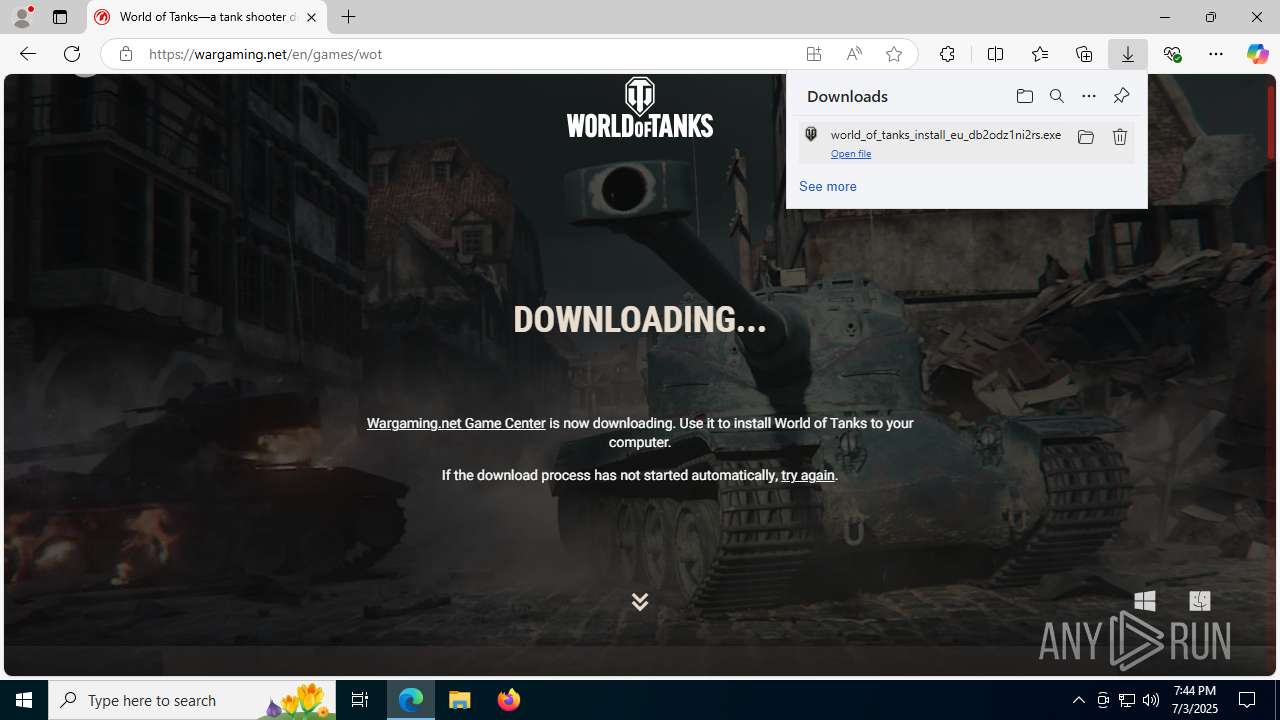
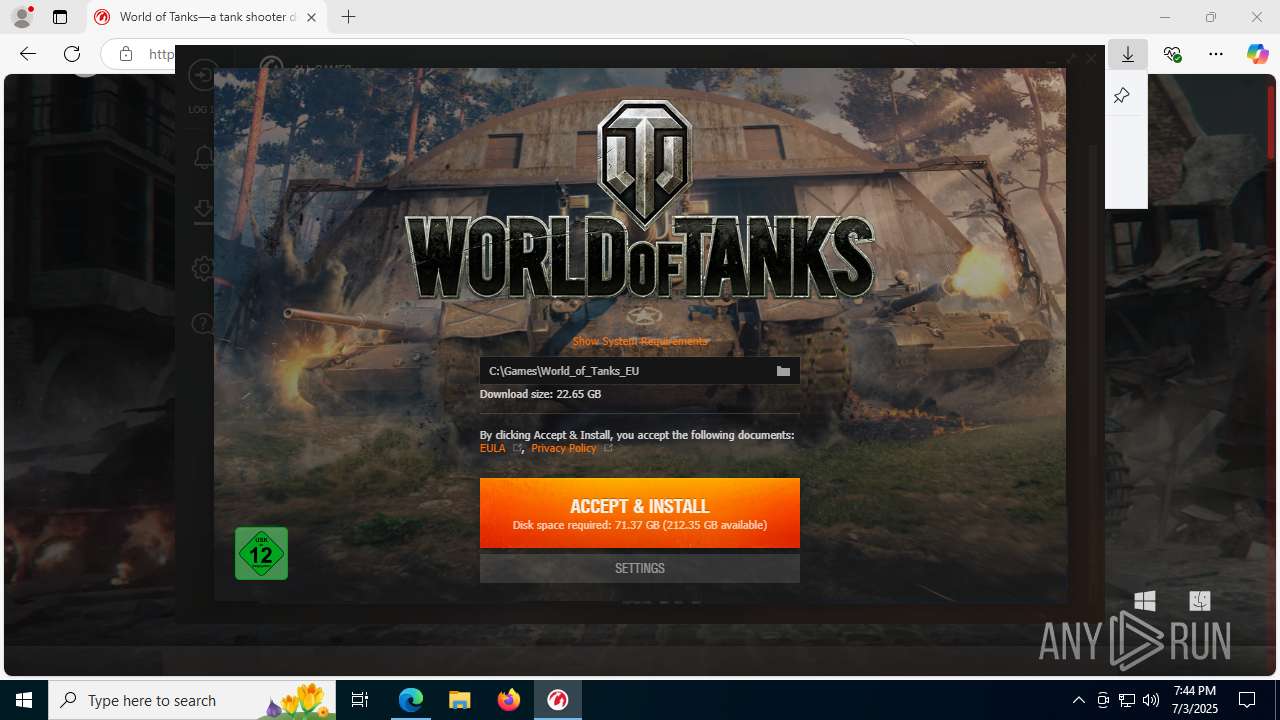
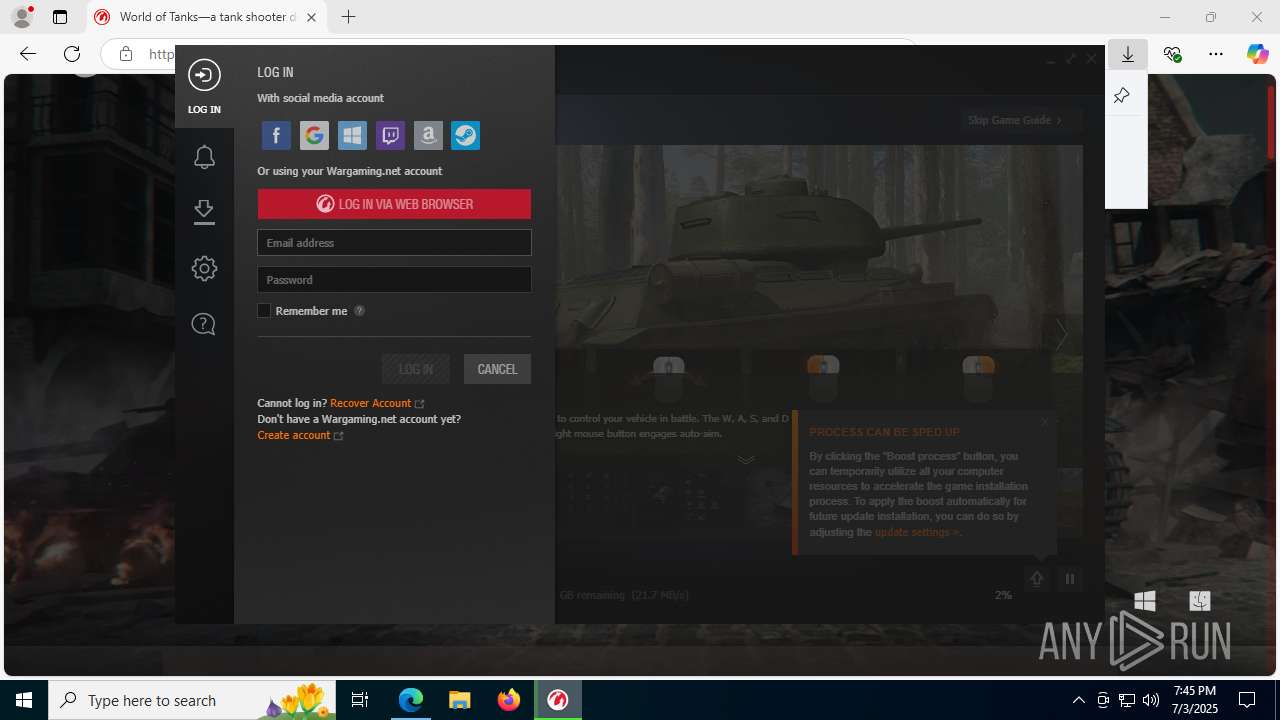
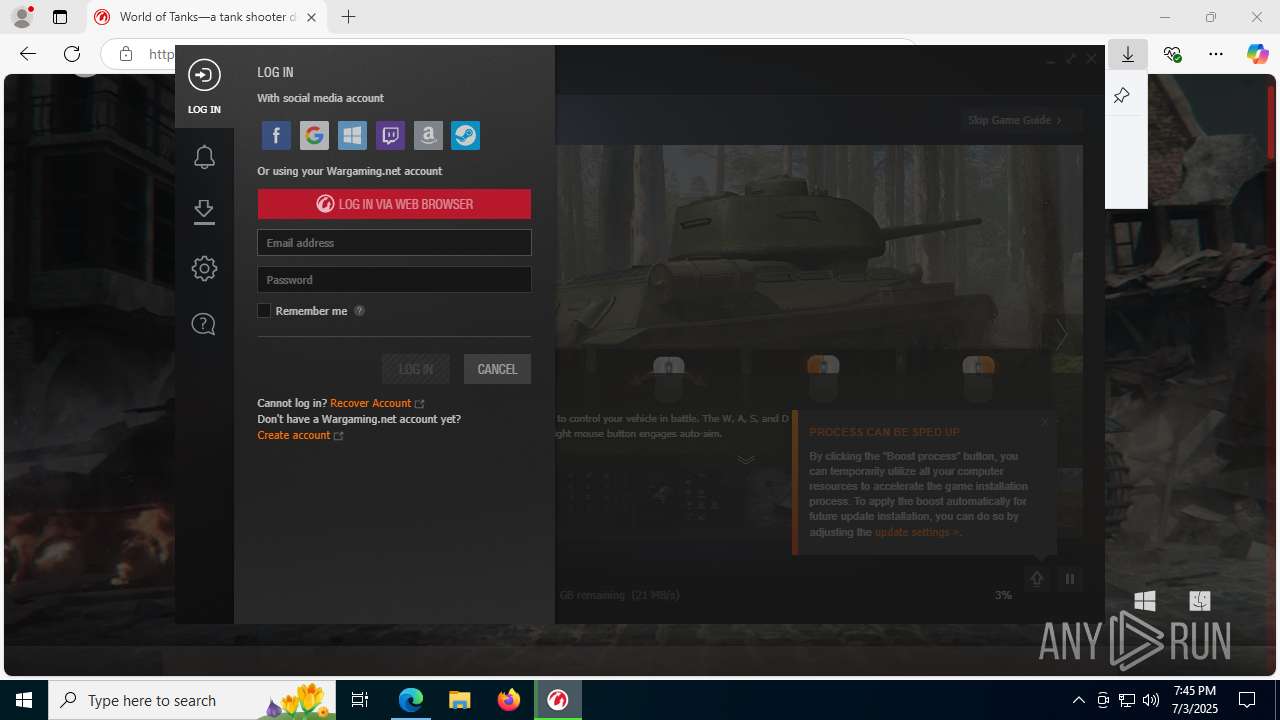
| URL: | na.wargaming.net |
| Full analysis: | https://app.any.run/tasks/da95e7f0-3316-41db-bf7e-c45057dbad74 |
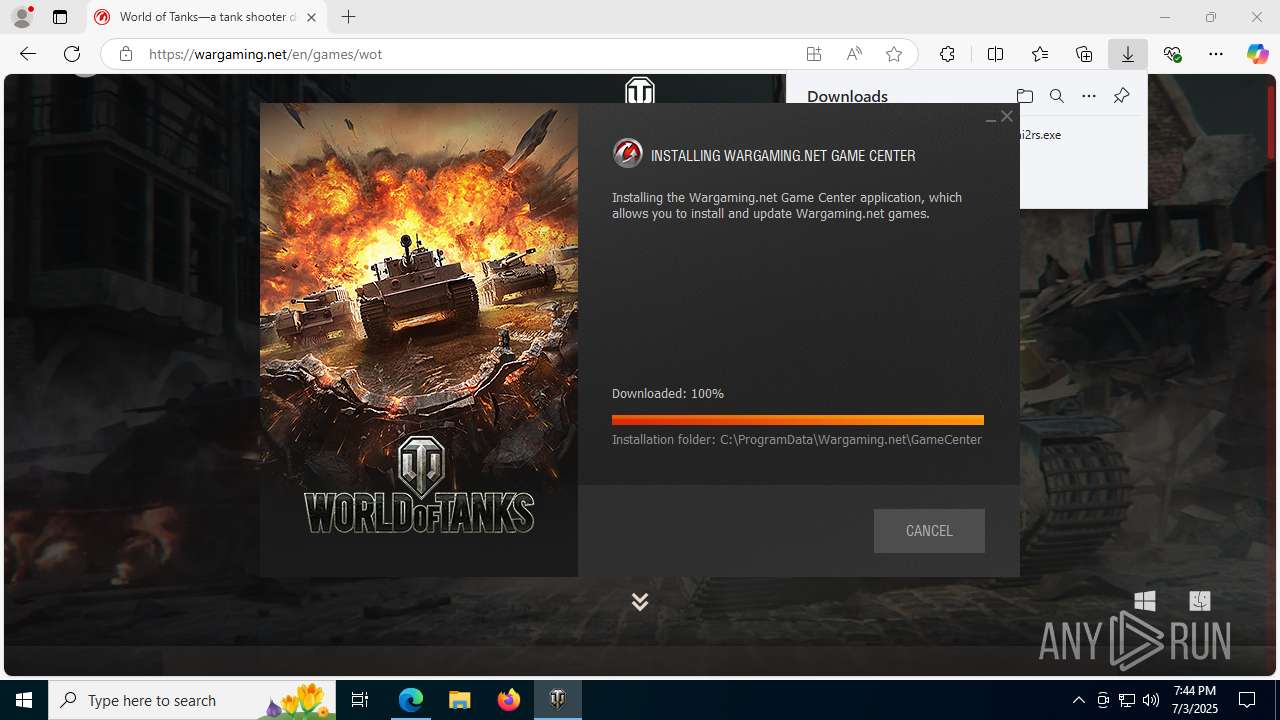
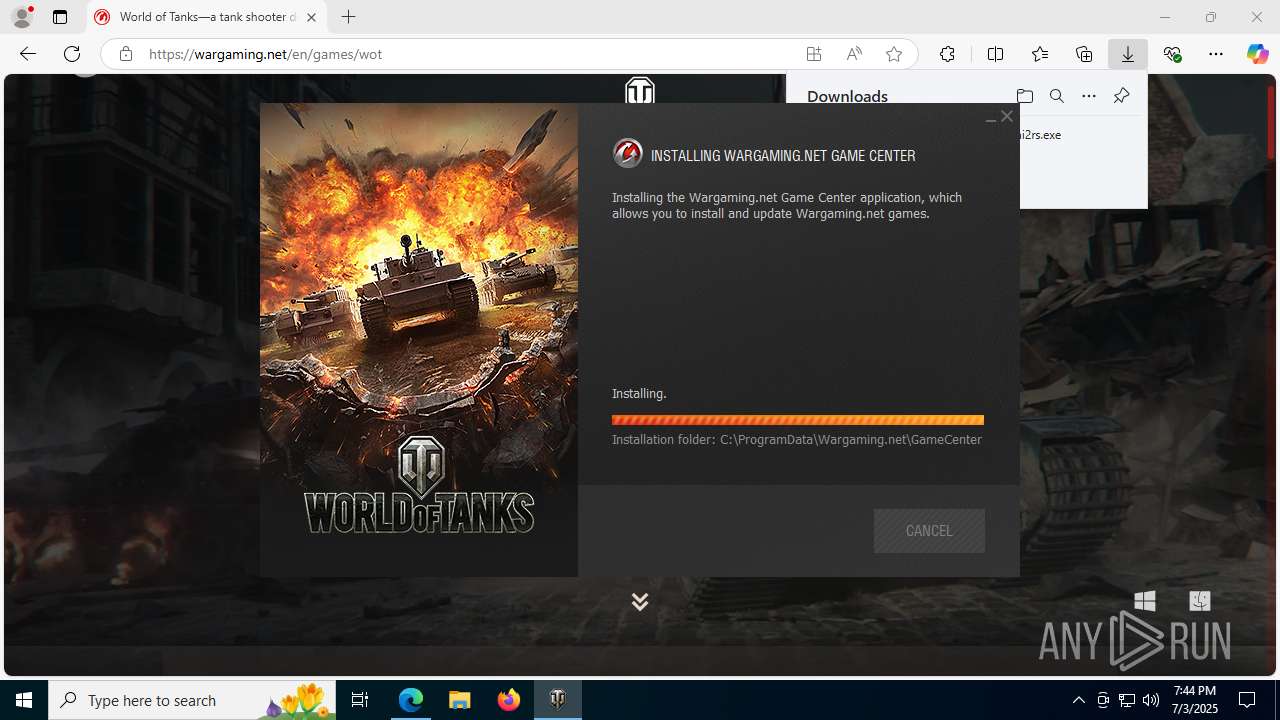
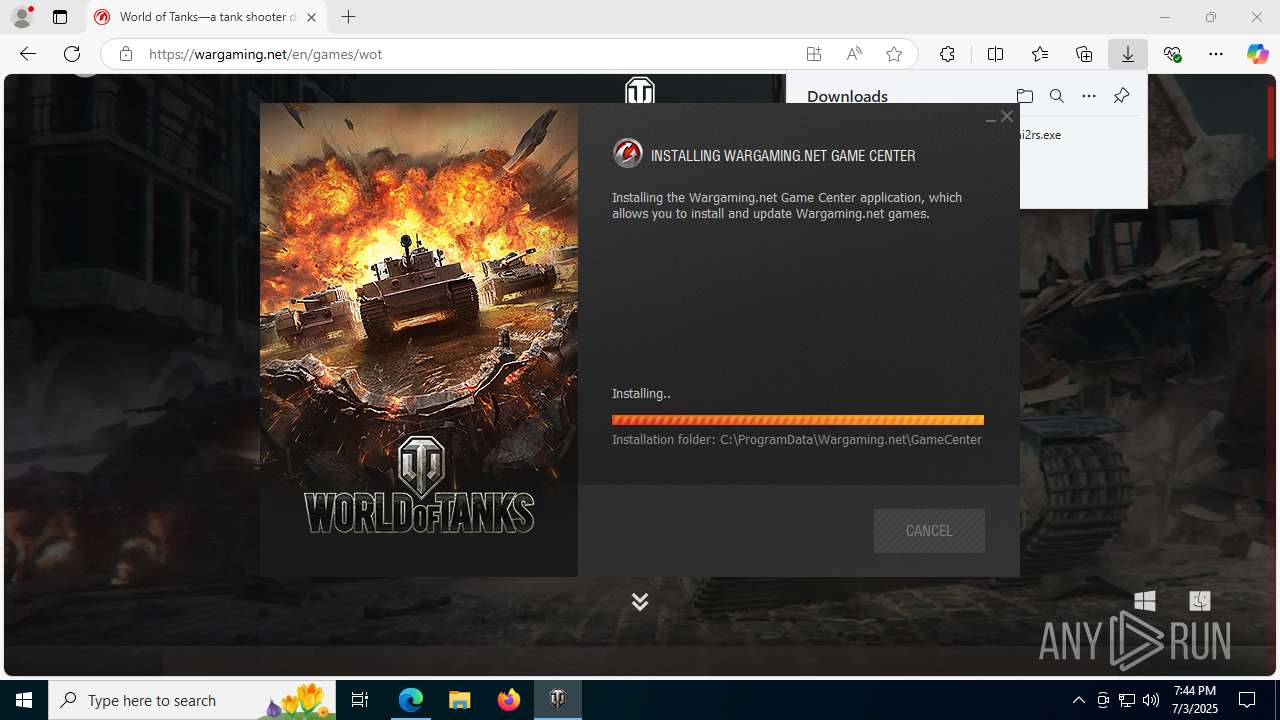
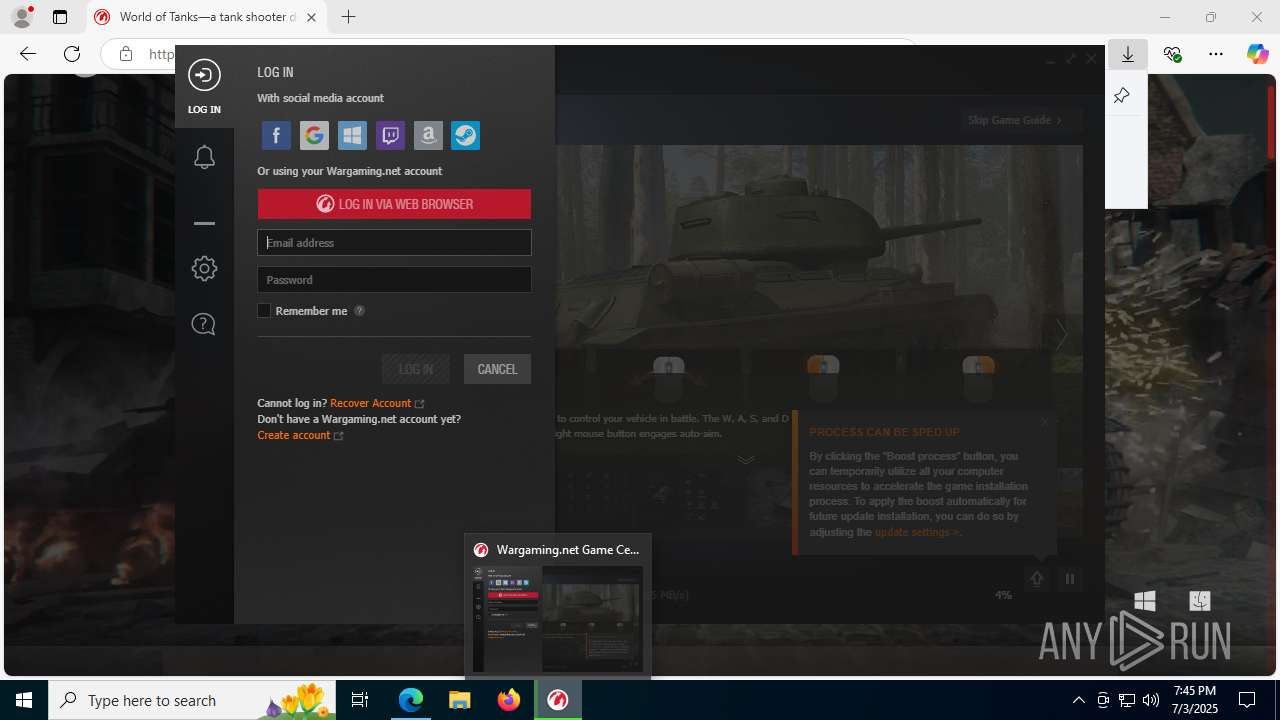
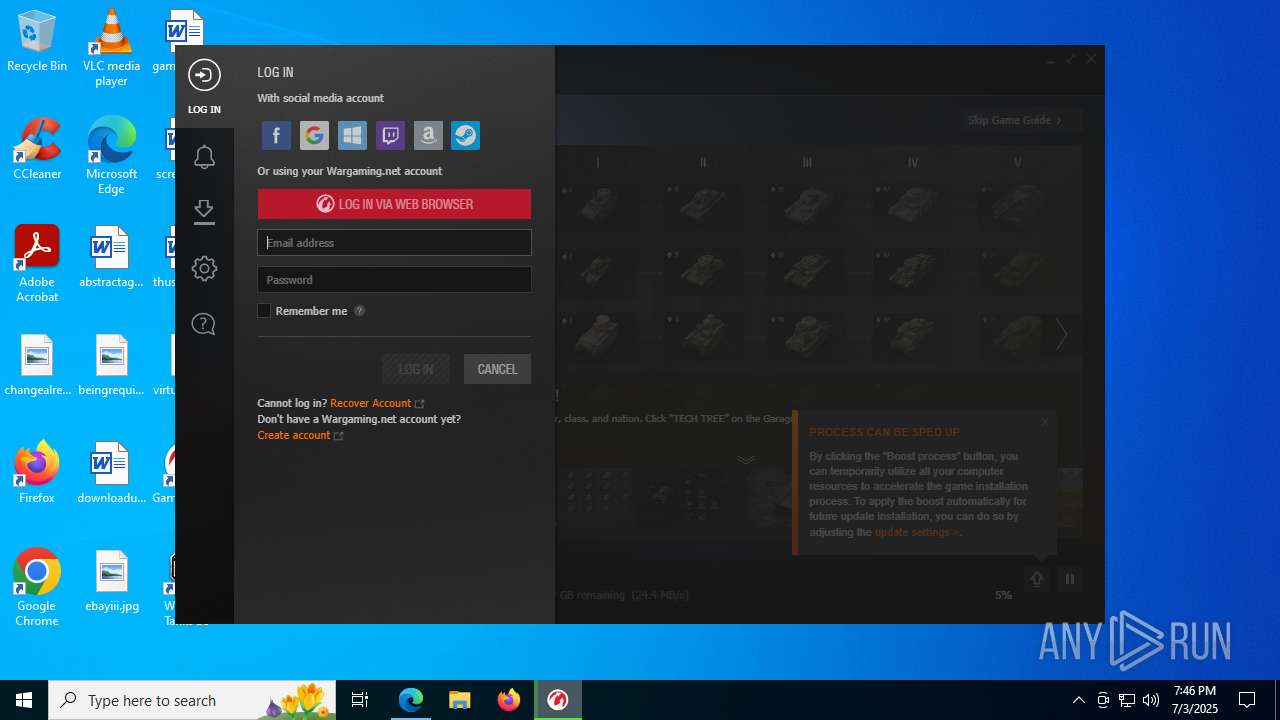
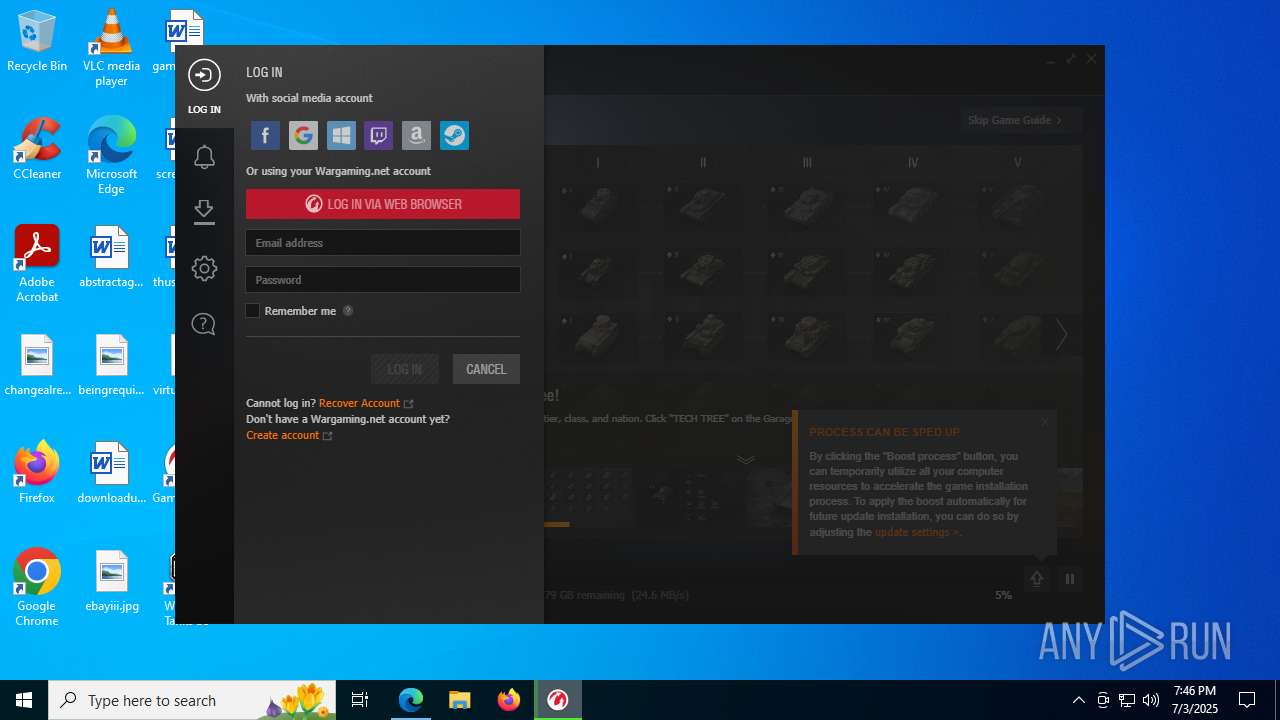
| Verdict: | Malicious activity |
| Threats: | Stealers are a group of malicious software that are intended for gaining unauthorized access to users’ information and transferring it to the attacker. The stealer malware category includes various types of programs that focus on their particular kind of data, including files, passwords, and cryptocurrency. Stealers are capable of spying on their targets by recording their keystrokes and taking screenshots. This type of malware is primarily distributed as part of phishing campaigns. |
| Analysis date: | July 03, 2025, 19:42:40 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 45221564CC1966D166D086B390CA7A14 |
| SHA1: | 6770399AE64DF34B58FED15416DF22B6E6B3EF61 |
| SHA256: | 606F91AE0AA6485D6B796B28F51FBEB2F123A9418844DE3EB8D49A77C8A32F92 |
| SSDEEP: | 3:woKCLo:woZLo |
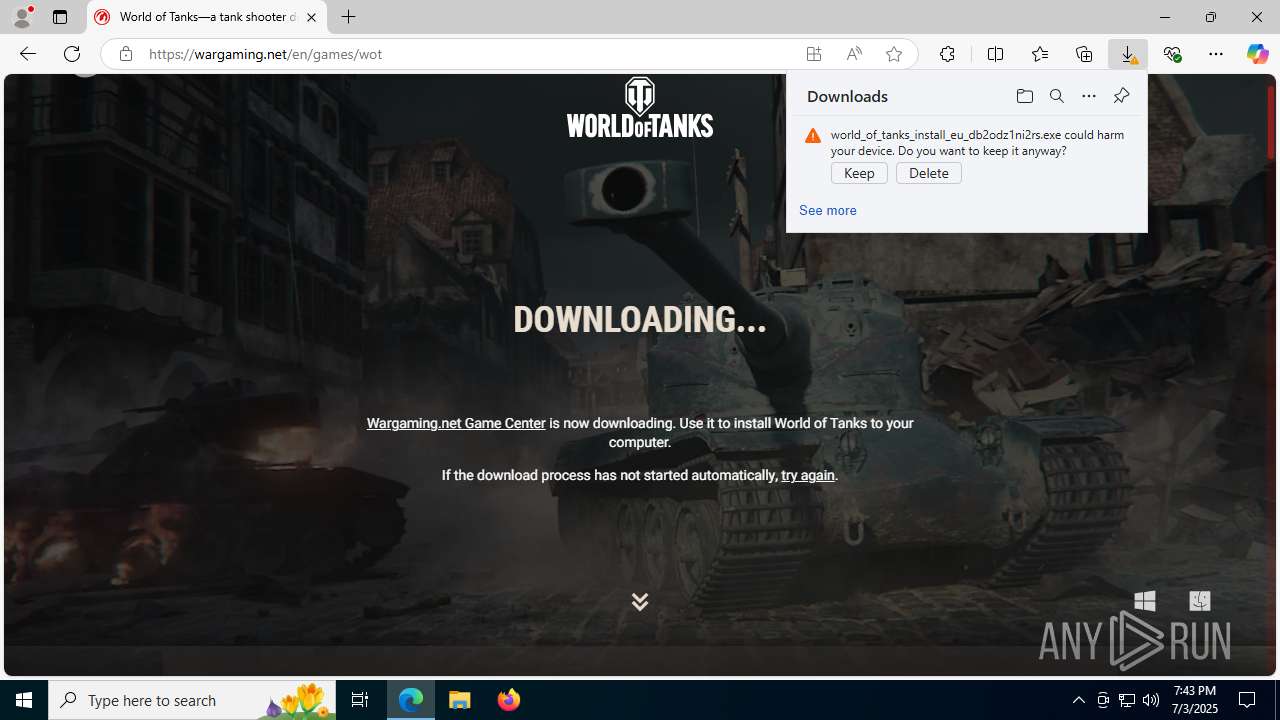
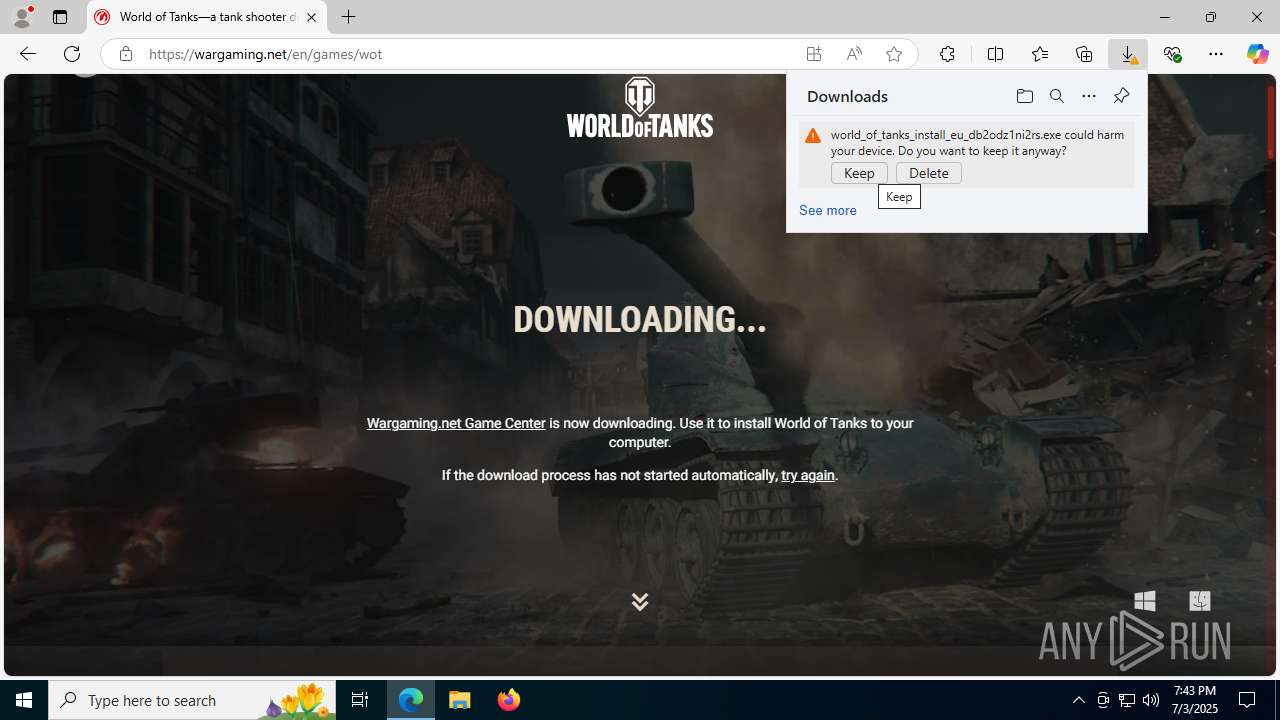
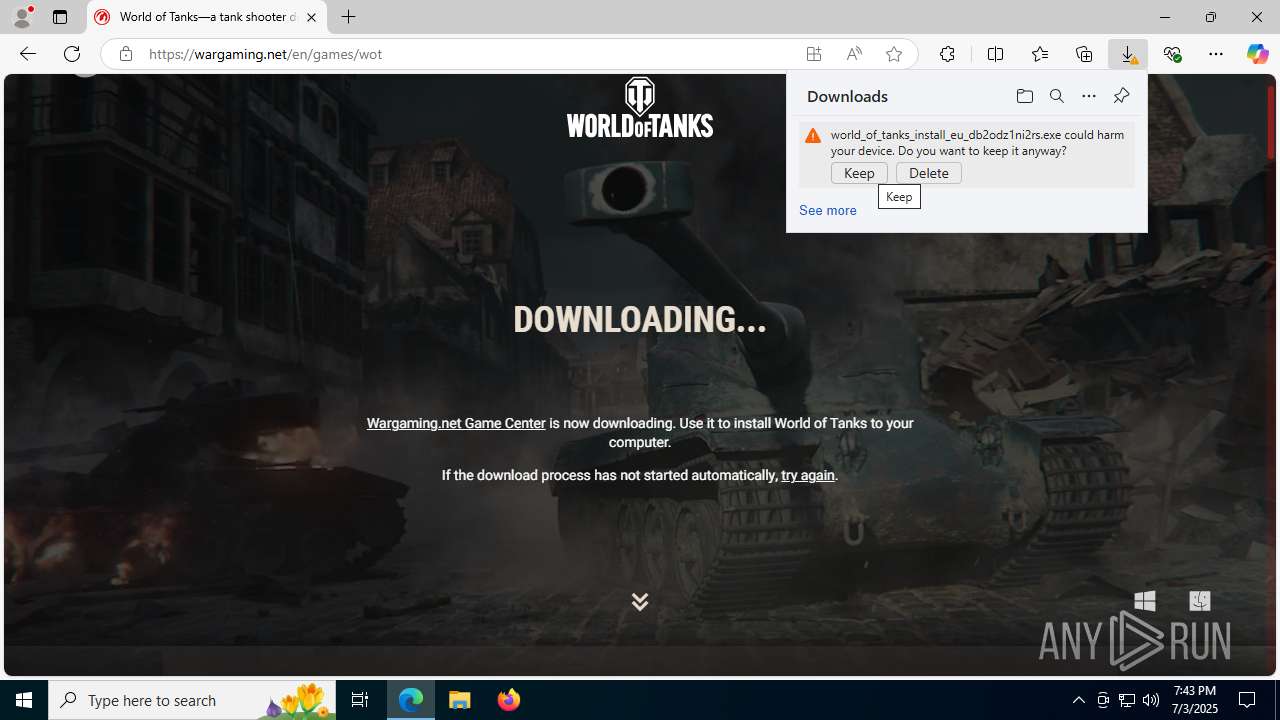
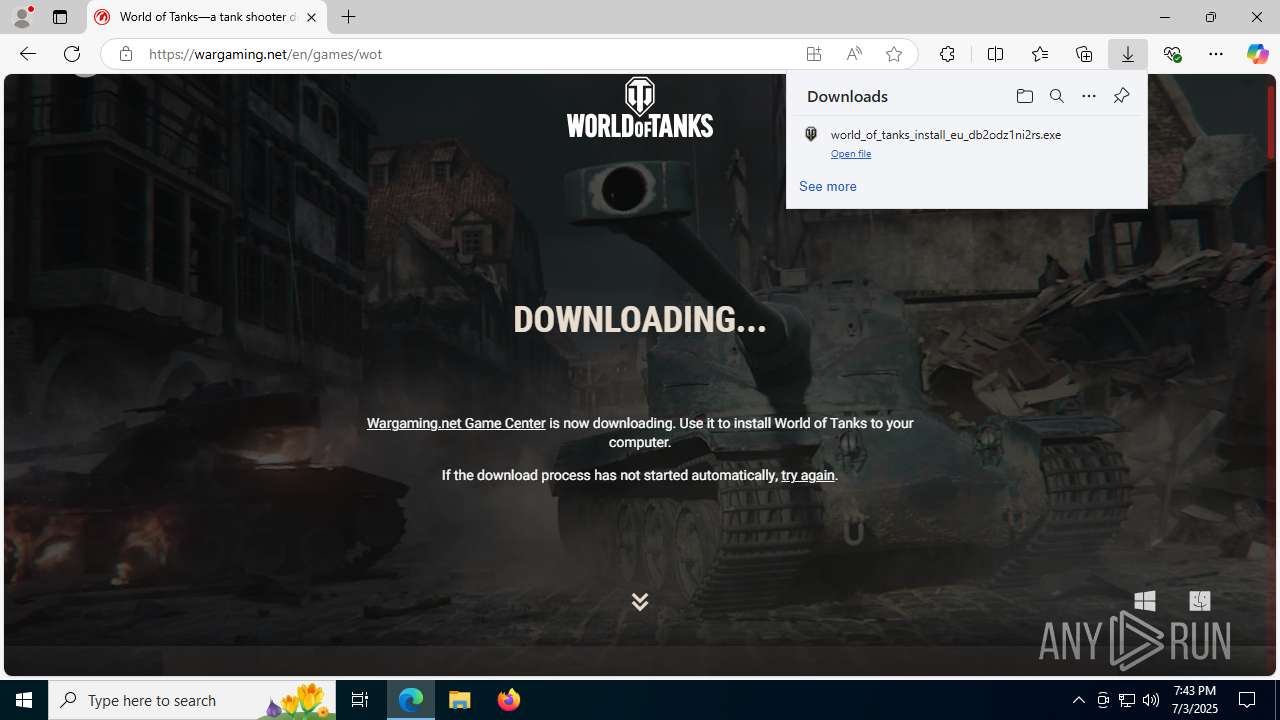
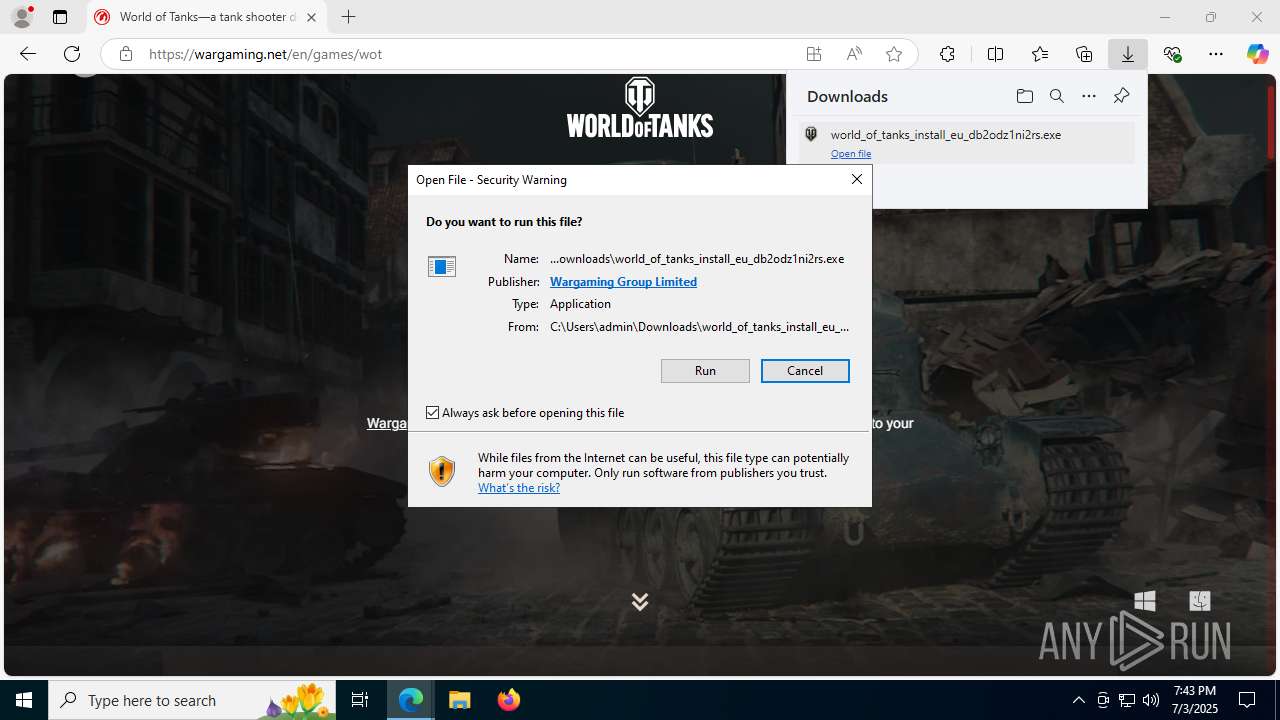
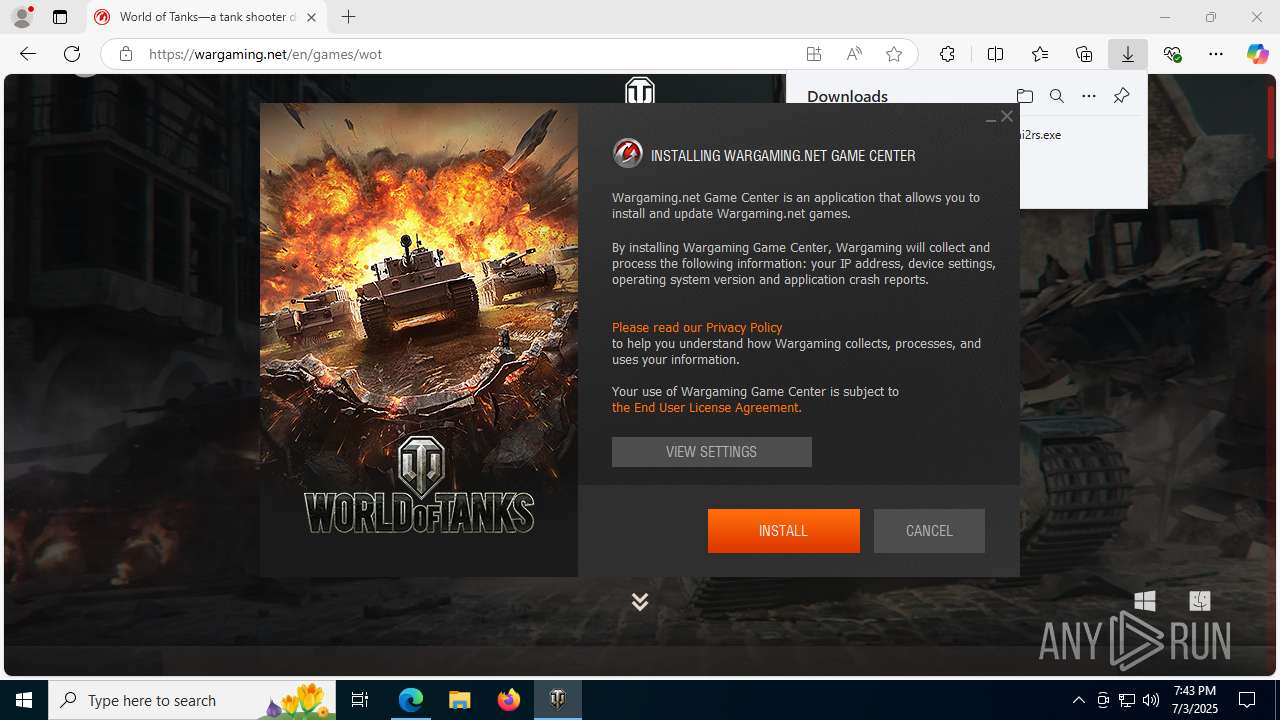
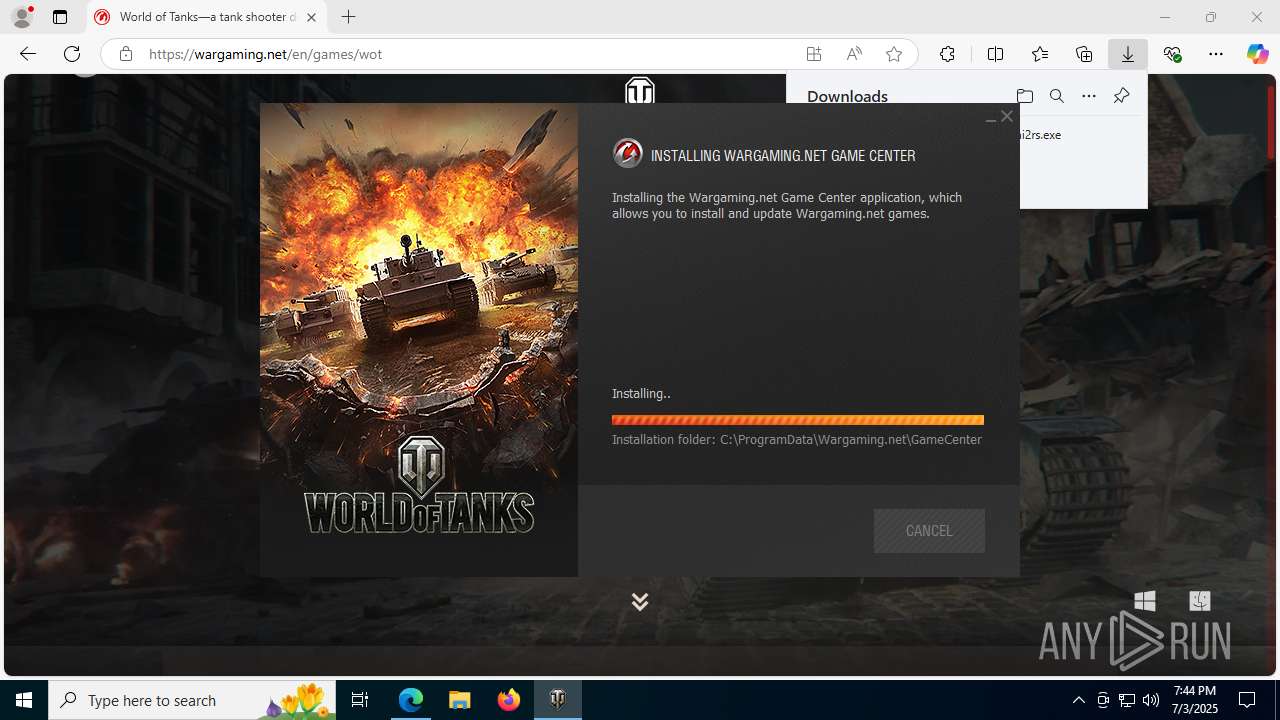
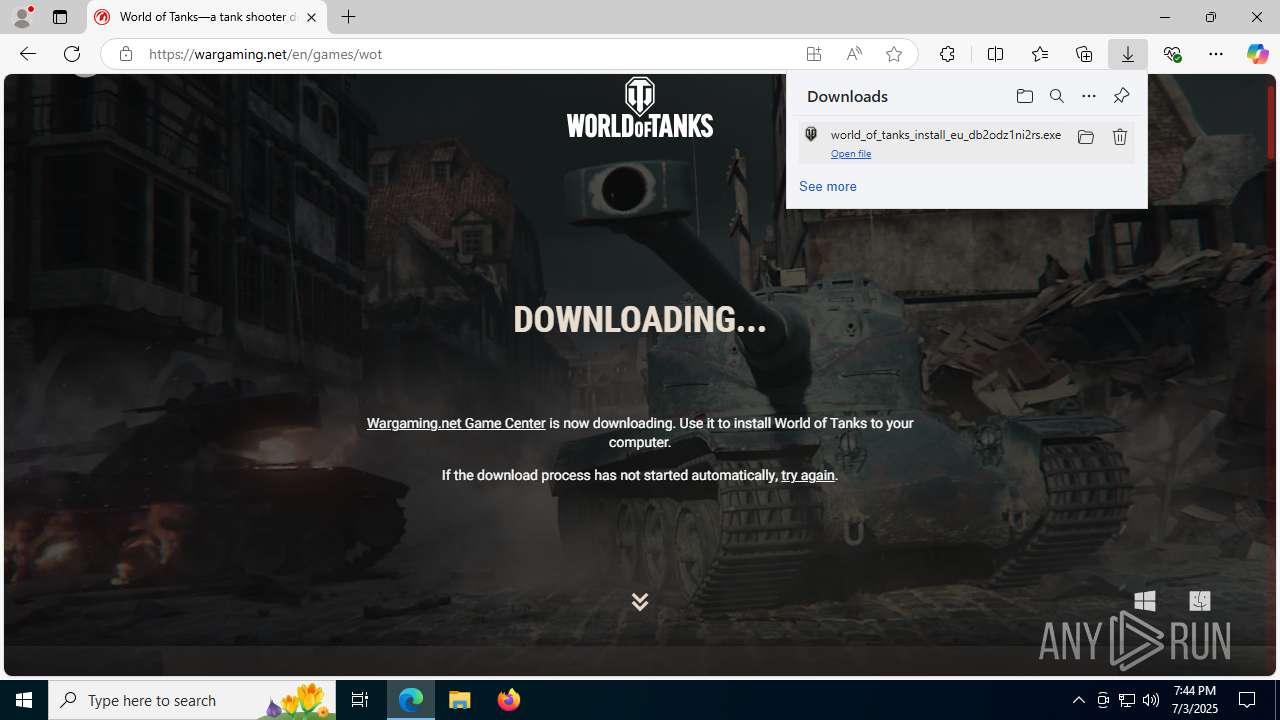
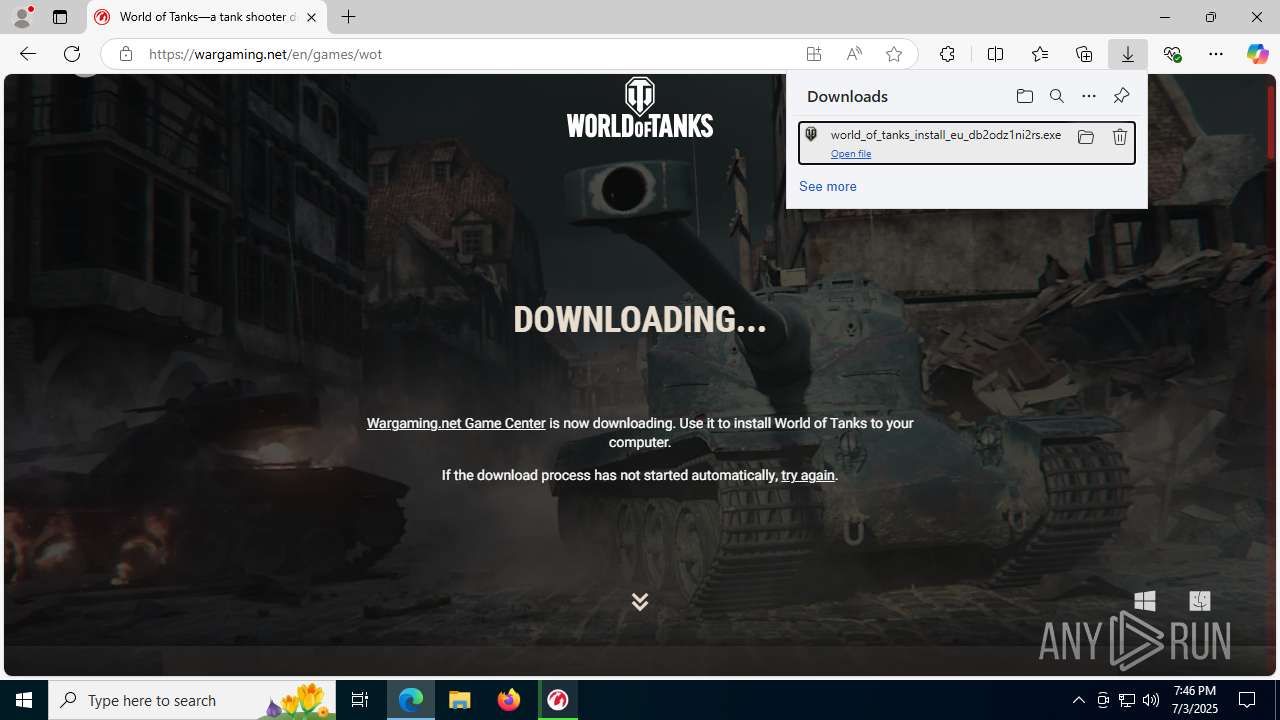
MALICIOUS
Executing a file with an untrusted certificate
- world_of_tanks_install_eu_db2odz1ni2rs.exe (PID: 5368)
- wgc.exe (PID: 5084)
- wgc.exe (PID: 7212)
- helper_process.exe (PID: 7440)
- helper_process.exe (PID: 2876)
- helper_process.exe (PID: 8520)
- helper_process.exe (PID: 8628)
- helper_process.exe (PID: 8812)
- wgc.exe (PID: 8936)
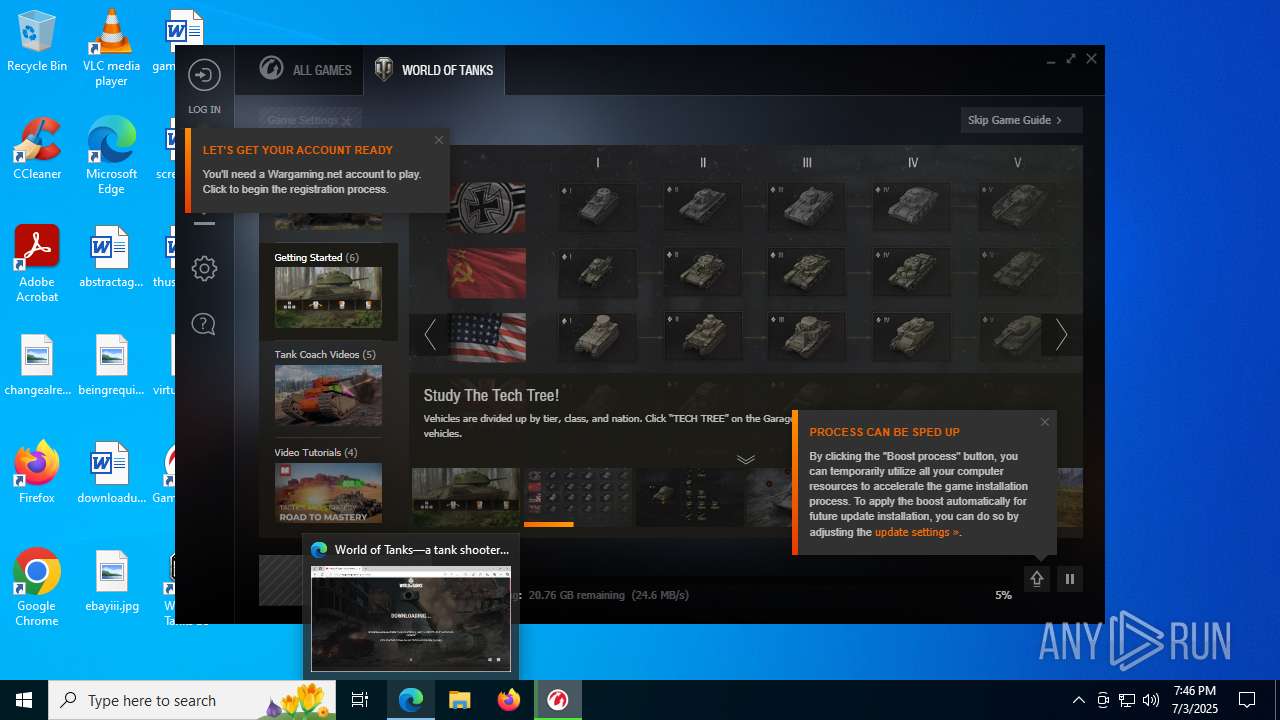
Changes the autorun value in the registry
- wgc.exe (PID: 7212)
BITTORRENT has been detected (SURICATA)
- wgc.exe (PID: 7212)
DISCORDGRABBER has been detected (YARA)
- wgc.exe (PID: 7212)
- wgc_renderer_host.exe (PID: 2512)
- wgc_renderer_host.exe (PID: 4116)
- wgc_renderer_host.exe (PID: 7420)
SUSPICIOUS
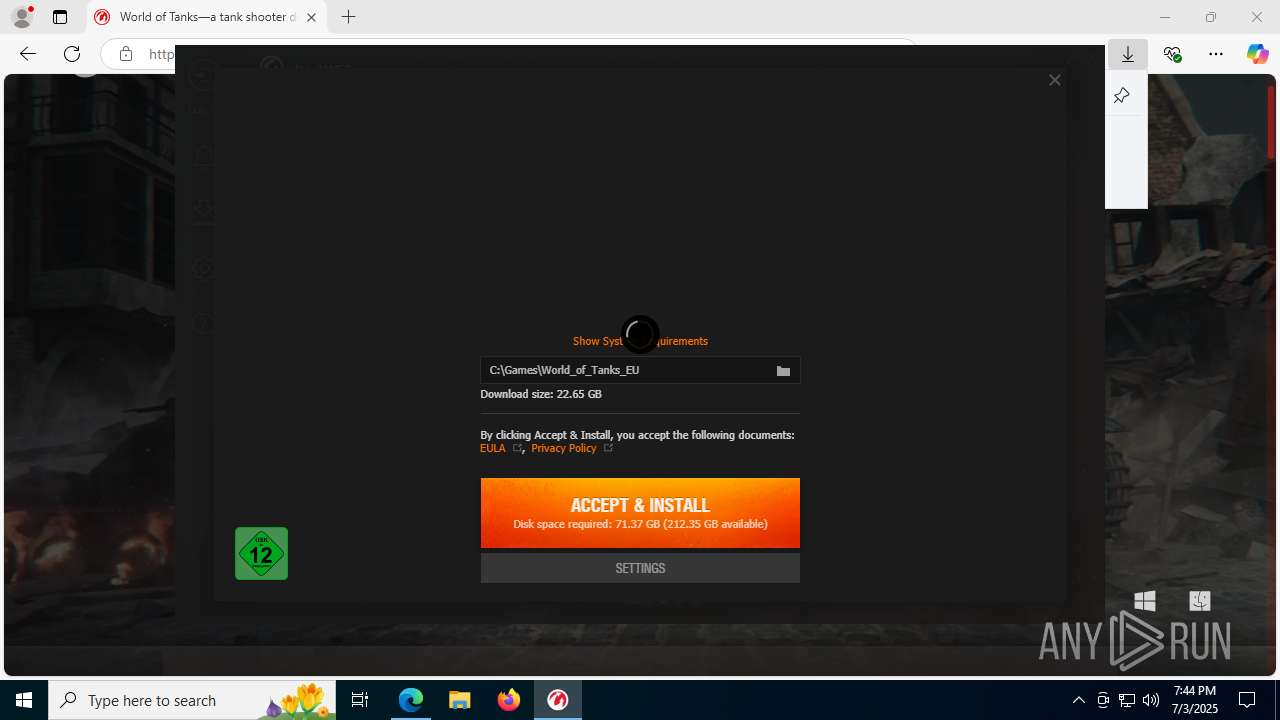
Executable content was dropped or overwritten
- world_of_tanks_install_eu_db2odz1ni2rs.exe (PID: 5368)
- world_of_tanks_install_eu_db2odz1ni2rs.tmp (PID: 3860)
- 7za.exe (PID: 3724)
- wgc.exe (PID: 7212)
Reads the Windows owner or organization settings
- world_of_tanks_install_eu_db2odz1ni2rs.tmp (PID: 3860)
Reads security settings of Internet Explorer
- world_of_tanks_install_eu_db2odz1ni2rs.tmp (PID: 3860)
Process drops legitimate windows executable
- world_of_tanks_install_eu_db2odz1ni2rs.tmp (PID: 3860)
- 7za.exe (PID: 3724)
Drops 7-zip archiver for unpacking
- world_of_tanks_install_eu_db2odz1ni2rs.tmp (PID: 3860)
- 7za.exe (PID: 3724)
Application launched itself
- wgc.exe (PID: 5084)
The process drops C-runtime libraries
- 7za.exe (PID: 3724)
Uses NETSH.EXE to add a firewall rule or allowed programs
- world_of_tanks_install_eu_db2odz1ni2rs.tmp (PID: 3860)
The process creates files with name similar to system file names
- 7za.exe (PID: 3724)
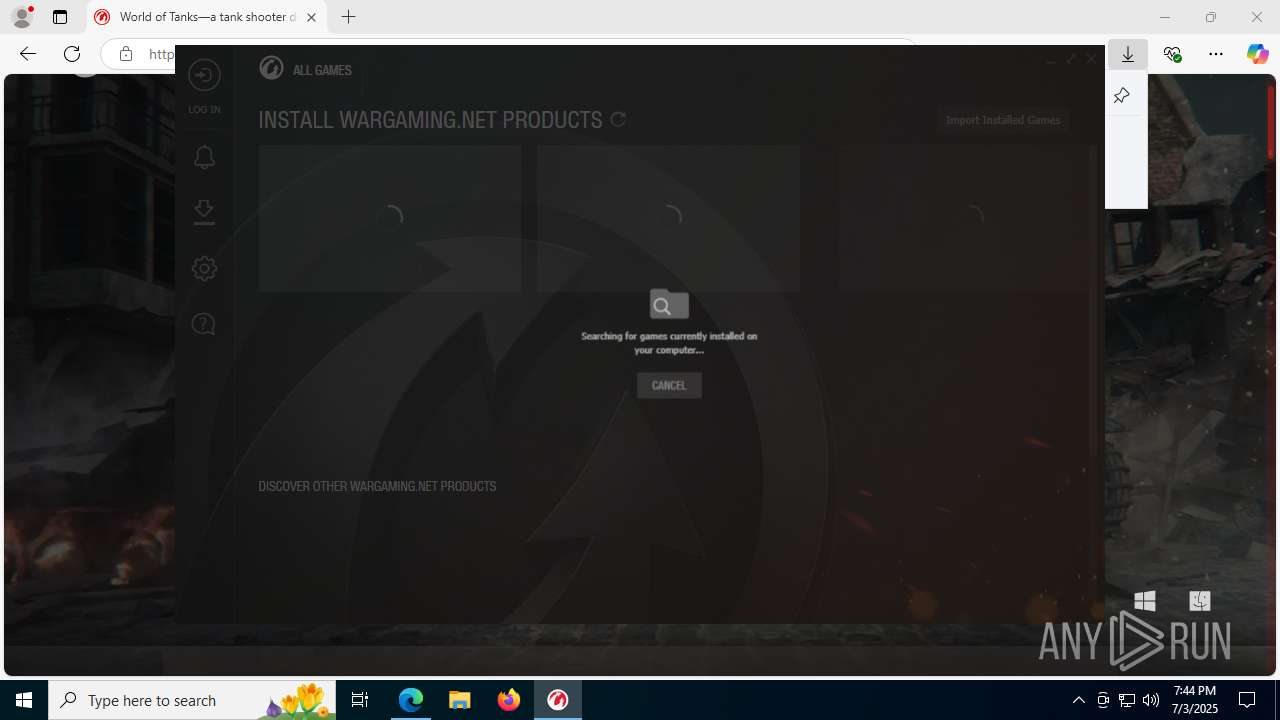
Searches for installed software
- world_of_tanks_install_eu_db2odz1ni2rs.tmp (PID: 3860)
- wgc.exe (PID: 7212)
There is functionality for taking screenshot (YARA)
- world_of_tanks_install_eu_db2odz1ni2rs.tmp (PID: 3860)
- wgc.exe (PID: 7212)
- WargamingErrorMonitor.exe (PID: 8076)
- wgc_renderer_host.exe (PID: 2512)
- wgc_renderer_host.exe (PID: 4116)
- wgc_renderer_host.exe (PID: 7420)
Creates a software uninstall entry
- wgc.exe (PID: 7212)
- wgc.exe (PID: 8936)
Found regular expressions for crypto-addresses (YARA)
- wgc.exe (PID: 7212)
- wgc_renderer_host.exe (PID: 2512)
- wgc_renderer_host.exe (PID: 4116)
- wgc_renderer_host.exe (PID: 7420)
Connects to unusual port
- wgc.exe (PID: 7212)
Potential Corporate Privacy Violation
- wgc.exe (PID: 7212)
INFO
Application launched itself
- msedge.exe (PID: 7120)
Checks supported languages
- identity_helper.exe (PID: 7944)
- world_of_tanks_install_eu_db2odz1ni2rs.exe (PID: 5368)
- world_of_tanks_install_eu_db2odz1ni2rs.tmp (PID: 3860)
- 7za.exe (PID: 6820)
- 7za.exe (PID: 3724)
- wgc.exe (PID: 5084)
- wgc.exe (PID: 7212)
- WargamingErrorMonitor.exe (PID: 8076)
- wgc_renderer_host.exe (PID: 4080)
- wgc_renderer_host.exe (PID: 2512)
- wgc_renderer_host.exe (PID: 7420)
- wgc_renderer_host.exe (PID: 7408)
- wgc_renderer_host.exe (PID: 4116)
- helper_process.exe (PID: 7440)
- helper_process.exe (PID: 2876)
- wgc_renderer_host.exe (PID: 2880)
- helper_process.exe (PID: 8628)
- helper_process.exe (PID: 8520)
- wgc_renderer_host.exe (PID: 432)
- helper_process.exe (PID: 8812)
- wgc.exe (PID: 8936)
- identity_helper.exe (PID: 5116)
- wgc_renderer_host.exe (PID: 6364)
- WargamingErrorMonitor.exe (PID: 8964)
Reads Environment values
- identity_helper.exe (PID: 7944)
- identity_helper.exe (PID: 5116)
Reads the computer name
- identity_helper.exe (PID: 7944)
- world_of_tanks_install_eu_db2odz1ni2rs.tmp (PID: 3860)
- 7za.exe (PID: 6820)
- 7za.exe (PID: 3724)
- WargamingErrorMonitor.exe (PID: 8076)
- wgc.exe (PID: 7212)
- wgc_renderer_host.exe (PID: 4080)
- wgc_renderer_host.exe (PID: 2512)
- helper_process.exe (PID: 2876)
- helper_process.exe (PID: 7440)
- wgc_renderer_host.exe (PID: 432)
- helper_process.exe (PID: 8520)
- helper_process.exe (PID: 8812)
- helper_process.exe (PID: 8628)
- wgc.exe (PID: 8936)
- identity_helper.exe (PID: 5116)
- wgc_renderer_host.exe (PID: 6364)
- WargamingErrorMonitor.exe (PID: 8964)
Create files in a temporary directory
- world_of_tanks_install_eu_db2odz1ni2rs.exe (PID: 5368)
- world_of_tanks_install_eu_db2odz1ni2rs.tmp (PID: 3860)
- wgc.exe (PID: 7212)
- dxdiag.exe (PID: 7692)
Executable content was dropped or overwritten
- msedge.exe (PID: 7120)
- msedge.exe (PID: 4920)
The sample compiled with chinese language support
- world_of_tanks_install_eu_db2odz1ni2rs.tmp (PID: 3860)
The sample compiled with english language support
- world_of_tanks_install_eu_db2odz1ni2rs.tmp (PID: 3860)
- 7za.exe (PID: 3724)
Compiled with Borland Delphi (YARA)
- world_of_tanks_install_eu_db2odz1ni2rs.tmp (PID: 3860)
Process checks whether UAC notifications are on
- world_of_tanks_install_eu_db2odz1ni2rs.tmp (PID: 3860)
- helper_process.exe (PID: 7440)
Creates files in the program directory
- world_of_tanks_install_eu_db2odz1ni2rs.tmp (PID: 3860)
- wgc.exe (PID: 5084)
- wgc.exe (PID: 7212)
- 7za.exe (PID: 3724)
- WargamingErrorMonitor.exe (PID: 8076)
- wgc_renderer_host.exe (PID: 2512)
- wgc_renderer_host.exe (PID: 7408)
- wgc_renderer_host.exe (PID: 2880)
- wgc_renderer_host.exe (PID: 4116)
- WargamingErrorMonitor.exe (PID: 8964)
- wgc.exe (PID: 8936)
The sample compiled with russian language support
- world_of_tanks_install_eu_db2odz1ni2rs.tmp (PID: 3860)
Creates a software uninstall entry
- world_of_tanks_install_eu_db2odz1ni2rs.tmp (PID: 3860)
Creates files or folders in the user directory
- world_of_tanks_install_eu_db2odz1ni2rs.tmp (PID: 3860)
- wgc.exe (PID: 7212)
- dxdiag.exe (PID: 7692)
Process checks computer location settings
- world_of_tanks_install_eu_db2odz1ni2rs.tmp (PID: 3860)
- wgc_renderer_host.exe (PID: 7408)
- wgc_renderer_host.exe (PID: 2880)
- wgc_renderer_host.exe (PID: 4116)
- wgc.exe (PID: 7212)
Reads the machine GUID from the registry
- wgc.exe (PID: 7212)
Checks proxy server information
- wgc.exe (PID: 7212)
- slui.exe (PID: 4724)
Launching a file from a Registry key
- wgc.exe (PID: 7212)
Reads the software policy settings
- wgc.exe (PID: 7212)
- dxdiag.exe (PID: 7692)
- slui.exe (PID: 4724)
Reads security settings of Internet Explorer
- dxdiag.exe (PID: 7692)
Manual execution by a user
- wgc.exe (PID: 8936)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
216
Monitored processes
69
Malicious processes
11
Suspicious processes
5
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 432 | "C:\ProgramData\Wargaming.net\GameCenter\dlls\wgc_renderer_host.exe" --type=utility --utility-sub-type=audio.mojom.AudioService --field-trial-handle=1948,1386455204447567216,479661323041003927,131072 --disable-features=CalculateNativeWinOcclusion,CookiesWithoutSameSiteMustBeSecure,SameSiteByDefaultCookies,WebRtcHideLocalIpsWithMdns --lang=en-US --service-sandbox-type=audio --no-sandbox --log-file="C:\ProgramData\Wargaming.net\GameCenter\logs\cef_20250703_194412_319.log" --log-severity=info --user-agent-product="Chrome/92.0.4515.159 WGC/25.02.00.9224" --lang=en-US --log-file="C:\ProgramData\Wargaming.net\GameCenter\logs\cef_20250703_194412_319.log" --mojo-platform-channel-handle=4820 /prefetch:8 | C:\ProgramData\Wargaming.net\GameCenter\dlls\wgc_renderer_host.exe | — | wgc.exe | |||||||||||
User: admin Company: Wargaming.net Integrity Level: MEDIUM Description: Wargaming.net Game Center Version: 25.02.00.9224 Modules
| |||||||||||||||
| 1028 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --always-read-main-dll --field-trial-handle=3648,i,14475061669492455106,9812818250248438505,262144 --variations-seed-version --mojo-platform-channel-handle=3676 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1704 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=5616,i,14475061669492455106,9812818250248438505,262144 --variations-seed-version --mojo-platform-channel-handle=5788 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2200 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2512 | "C:\ProgramData\Wargaming.net\GameCenter\dlls\wgc_renderer_host.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --field-trial-handle=1948,1386455204447567216,479661323041003927,131072 --disable-features=CalculateNativeWinOcclusion,CookiesWithoutSameSiteMustBeSecure,SameSiteByDefaultCookies,WebRtcHideLocalIpsWithMdns --lang=en-US --service-sandbox-type=none --no-sandbox --log-file="C:\ProgramData\Wargaming.net\GameCenter\logs\cef_20250703_194412_319.log" --log-severity=info --user-agent-product="Chrome/92.0.4515.159 WGC/25.02.00.9224" --lang=en-US --log-file="C:\ProgramData\Wargaming.net\GameCenter\logs\cef_20250703_194412_319.log" --mojo-platform-channel-handle=2076 /prefetch:8 | C:\ProgramData\Wargaming.net\GameCenter\dlls\wgc_renderer_host.exe | wgc.exe | ||||||||||||
User: admin Company: Wargaming.net Integrity Level: MEDIUM Description: Wargaming.net Game Center Version: 25.02.00.9224 Modules
| |||||||||||||||
| 2664 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --disable-quic --message-loop-type-ui --string-annotations --always-read-main-dll --field-trial-handle=6556,i,14475061669492455106,9812818250248438505,262144 --variations-seed-version --mojo-platform-channel-handle=7152 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2716 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data" /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Crashpad" --annotation=IsOfficialBuild=1 --annotation=channel= --annotation=chromium-version=133.0.6943.142 "--annotation=exe=C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --annotation=plat=Win64 --annotation=prod=Edge --annotation=ver=133.0.3065.92 --initial-client-data=0x294,0x298,0x29c,0x28c,0x2a4,0x7ffc4322f208,0x7ffc4322f214,0x7ffc4322f220 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2876 | "C:\ProgramData\Wargaming.net\GameCenter\dlls\helper_process.exe" helper_E2518AE9362B53E8C8214575818BC1B2 1 | C:\ProgramData\Wargaming.net\GameCenter\dlls\helper_process.exe | — | wgc.exe | |||||||||||
User: admin Company: Wargaming.net Integrity Level: MEDIUM Description: Wargaming.net Game Center Exit code: 0 Version: 25.02.00.9224 Modules
| |||||||||||||||
| 2880 | "C:\ProgramData\Wargaming.net\GameCenter\dlls\wgc_renderer_host.exe" --type=renderer --no-sandbox --autoplay-policy=no-user-gesture-required --force-device-scale-factor=1 --log-file="C:\ProgramData\Wargaming.net\GameCenter\logs\cef_20250703_194412_319.log" --field-trial-handle=1948,1386455204447567216,479661323041003927,131072 --disable-features=CalculateNativeWinOcclusion,CookiesWithoutSameSiteMustBeSecure,SameSiteByDefaultCookies,WebRtcHideLocalIpsWithMdns --disable-gpu-compositing --lang=en-US --log-file="C:\ProgramData\Wargaming.net\GameCenter\logs\cef_20250703_194412_319.log" --log-severity=info --user-agent-product="Chrome/92.0.4515.159 WGC/25.02.00.9224" --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=7 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4716 /prefetch:1 | C:\ProgramData\Wargaming.net\GameCenter\dlls\wgc_renderer_host.exe | — | wgc.exe | |||||||||||
User: admin Company: Wargaming.net Integrity Level: MEDIUM Description: Wargaming.net Game Center Version: 25.02.00.9224 Modules
| |||||||||||||||
| 3400 | "C:\Program Files\Internet Explorer\iexplore.exe" "na.wargaming.net" | C:\Program Files\Internet Explorer\iexplore.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 11.00.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
28 004
Read events
27 788
Write events
199
Delete events
17
Modification events
| (PID) Process: | (7120) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (7120) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (7120) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3400) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3400) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3400) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3400) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3400) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (3400) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | DisableFirstRunCustomize |
Value: 1 | |||
| (PID) Process: | (7120) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
Executable files
119
Suspicious files
402
Text files
305
Unknown types
867
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7120 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old~RF1759f7.TMP | — | |
MD5:— | SHA256:— | |||
| 7120 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7120 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF1759f7.TMP | — | |
MD5:— | SHA256:— | |||
| 7120 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7120 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old~RF175a07.TMP | — | |
MD5:— | SHA256:— | |||
| 7120 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7120 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF175a16.TMP | — | |
MD5:— | SHA256:— | |||
| 7120 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7120 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF175a26.TMP | — | |
MD5:— | SHA256:— | |||
| 7120 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
68
TCP/UDP connections
1 668
DNS requests
181
Threats
29
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4920 | msedge.exe | GET | 200 | 150.171.28.11:80 | http://edge.microsoft.com/browsernetworktime/time/1/current?cup2key=2:zRncwUTRfzCgVL5mGjzrGyjSV3h3BxW0rkZreilGkHg&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 2.16.241.12:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
7408 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
7408 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
5444 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
7120 | msedge.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSRXerF0eFeSWRripTgTkcJWMm7iQQUaDfg67Y7%2BF8Rhvv%2BYXsIiGX0TkICEAJE1P87D6StXHRuQAroccw%3D | unknown | — | — | whitelisted |
7120 | msedge.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBT3xL4LQLXDRDM9P665TW442vrsUQQUReuir%2FSSy4IxLVGLp6chnfNtyA8CEA6bGI750C3n79tQ4ghAGFo%3D | unknown | — | — | whitelisted |
7120 | msedge.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfIs%2BLjDtGwQ09XEB1Yeq%2BtX%2BBgQQU7NfjgtJxXWRM3y5nP%2Be6mK4cD08CEAitQLJg0pxMn17Nqb2Trtk%3D | unknown | — | — | whitelisted |
764 | lsass.exe | GET | 200 | 142.250.185.195:80 | http://ocsp.pki.goog/gsr1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCEHe9DWzbNvka6iEPxPBY0w0%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
5944 | MoUsoCoreWorker.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1268 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6492 | RUXIMICS.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4920 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4920 | msedge.exe | 150.171.28.11:80 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4920 | msedge.exe | 150.171.28.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4920 | msedge.exe | 92.223.56.8:443 | na.wargaming.net | G-Core Labs S.A. | US | whitelisted |
4920 | msedge.exe | 92.223.56.8:80 | na.wargaming.net | G-Core Labs S.A. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
na.wargaming.net |
| whitelisted |
copilot.microsoft.com |
| whitelisted |
wargaming.net |
| whitelisted |
www.bing.com |
| whitelisted |
cdn.cookielaw.org |
| whitelisted |
cdn-cm.wgcdn.co |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
4920 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
4920 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
4920 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
4920 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
4920 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
4920 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
7212 | wgc.exe | Potential Corporate Privacy Violation | ET P2P Libtorrent User-Agent |
7212 | wgc.exe | Misc activity | INFO [ANY.RUN] P2P BitTorrent Protocol |
7212 | wgc.exe | Potential Corporate Privacy Violation | ET P2P Libtorrent User-Agent |
7212 | wgc.exe | Potential Corporate Privacy Violation | GPL P2P BitTorrent announce request |
Process | Message |
|---|---|
wgc.exe | [0703/194412.363:INFO:gpu_data_manager_impl_private.cc(1550)] Falling back GPU mode. fallback_modes_.size()=3; system_shutdown=false
|
wgc_renderer_host.exe | [0703/194412.575:ERROR:gpu_init.cc(441)] Passthrough is not supported, GL is swiftshader
|
wgc.exe | [0703/194413.681:INFO:CONSOLE(2)] "Deprecation warning: use moment.updateLocale(localeName, config) to change an existing locale. moment.defineLocale(localeName, config) should only be used for creating a new locale See http://momentjs.com/guides/#/warnings/define-locale/ for more info.", source: qrc://ui/vendors-wgc-overlay-arsenal-arsenalOverlay.9b846a49609378bef1f9.js (2)
|
wgc.exe | [0703/194413.726:INFO:CONSOLE(1)] "[PostMessageService] init: start listening messages", source: qrc://ui/wgc.609292b080eb27d98c74.js (1)
|
wgc.exe | [0703/194413.759:INFO:CONSOLE(1)] "[Subscriber][Binding: overlay] No qObject for this config; ignore';
See binding #1 from config = [{"binding":"overlay","subscribers":["type"]}]", source: qrc://ui/wgc.609292b080eb27d98c74.js (1)
|
wgc.exe | [0703/194413.762:INFO:CONSOLE(1)] "%c[React][AppInstallationMonitor] render: appInstallation is empty; ignore color: #9c9c9c;", source: qrc://ui/wgc.609292b080eb27d98c74.js (1)
|
wgc.exe | [0703/194413.763:INFO:CONSOLE(1)] "[Subscriber][Binding: overlay] No qObject for this config; ignore';
See binding #1 from config = [{"binding":"overlay","subscribers":["type"]}]", source: qrc://ui/wgc.609292b080eb27d98c74.js (1)
|
wgc.exe | [0703/194413.764:INFO:CONSOLE(1)] "%c[React][GroupsMonitor] render: selectedGroup or activeGroupId is empty; ignore color: #9c9c9c;", source: qrc://ui/wgc.609292b080eb27d98c74.js (1)
|
wgc.exe | [0703/194413.764:INFO:CONSOLE(1)] "[Subscriber][Binding: overlay] No qObject for this config; ignore';
See binding #1 from config = [{"binding":"overlay","subscribers":["type"]}]", source: qrc://ui/wgc.609292b080eb27d98c74.js (1)
|
wgc.exe | [0703/194413.765:INFO:CONSOLE(1)] "%c[React][SteamOnBoardingMonitor] render: steamOnBoarding is empty; ignore color: #9c9c9c;", source: qrc://ui/wgc.609292b080eb27d98c74.js (1)
|