analyze malware
- Huge database of samples and IOCs
- Custom VM setup
- Unlimited submissions
- Interactive approach
| File name: | procchack.exe |
| Full analysis: | https://app.any.run/tasks/4a0c3c3b-ed50-4966-9b90-5dffa99de93f |
| Verdict: | Malicious activity |
| Analysis date: | August 13, 2019, 21:53:27 |
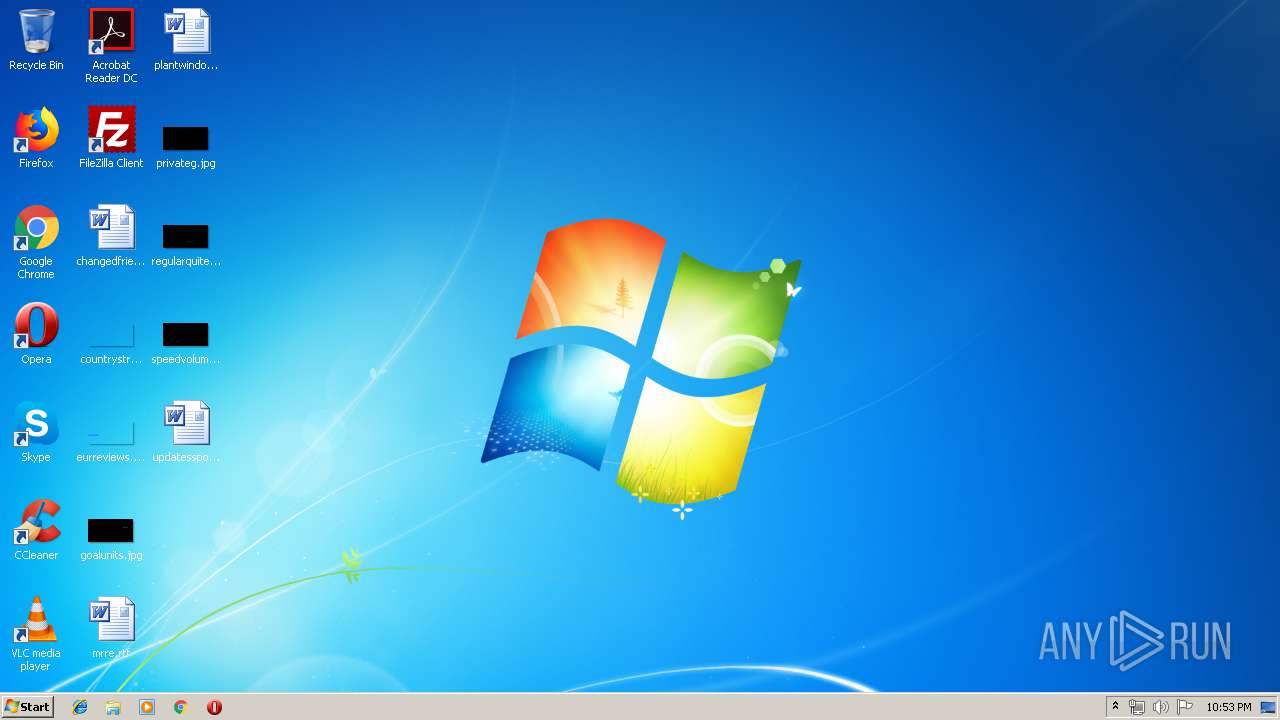
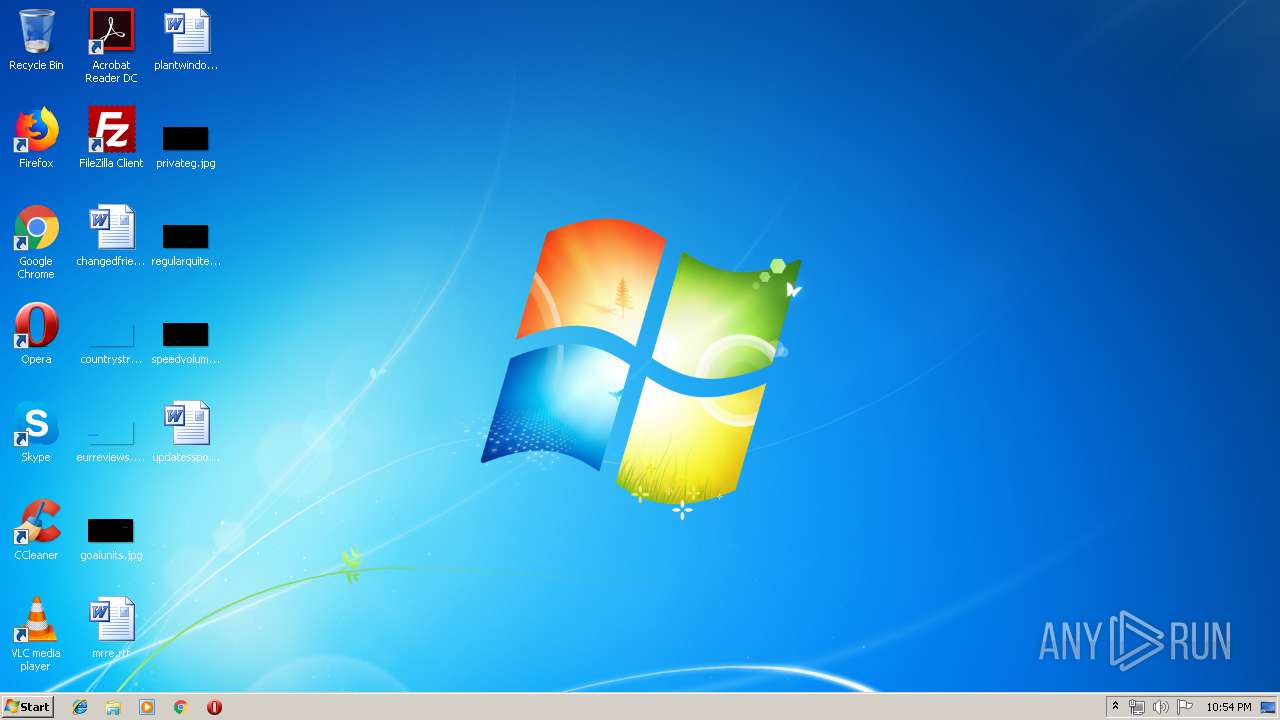
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | DA5CEBF94B1149923C90E593FD2E9158 |
| SHA1: | FF77B45E58D76F784567FE7CFA440486E1BFB995 |
| SHA256: | 605D5BF540C574AAAE1C90C804EA032B771AC704B41CC340784F97E6B5D409F5 |
| SSDEEP: | 49152:roYZFoKWEKtWzl+vaPDb0XFZdKAcJhey6Ri7odkg9mXDNqcV:EYDofpAYvoI0B7o3aNP |
MALICIOUS
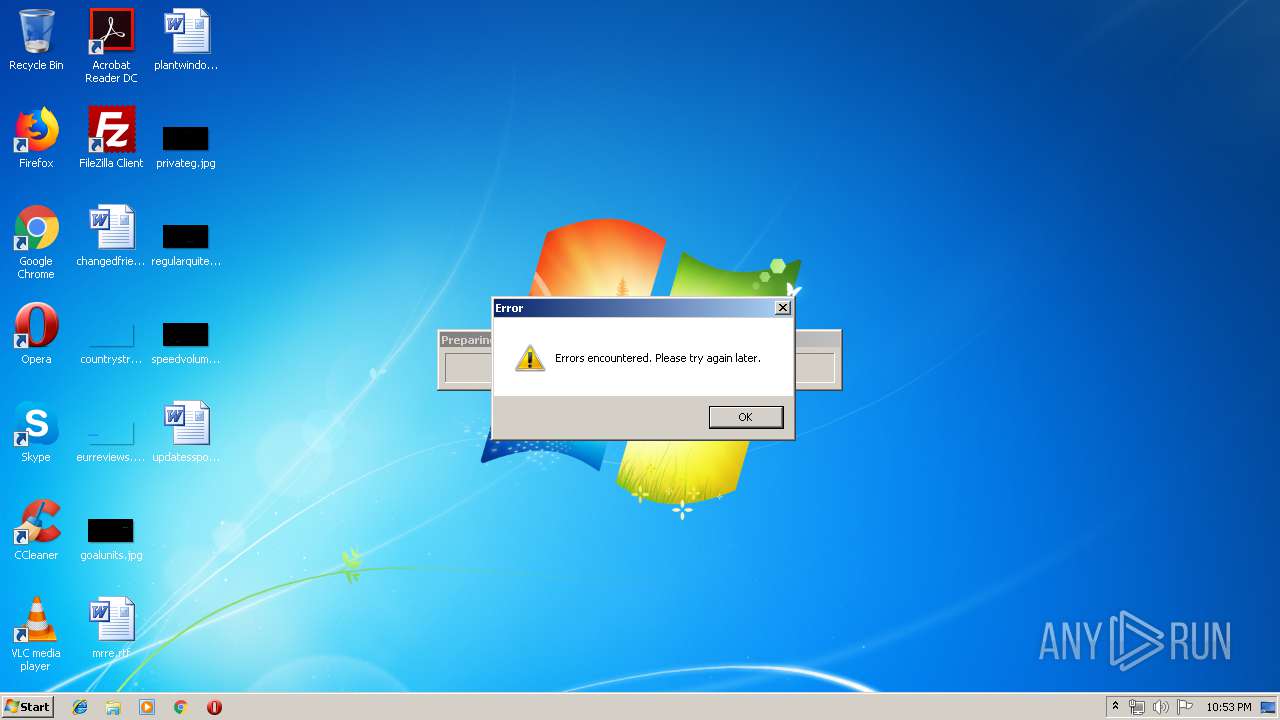
PREPSCRAM was detected
- procchack.exe (PID: 3020)
Connects to CnC server
- procchack.exe (PID: 3020)
SUSPICIOUS
Application launched itself
- procchack.exe (PID: 2132)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (52.9) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (23.5) |
| .exe | | | DOS Executable Generic (23.5) |
EXIF
EXE
| Subsystem: | Windows GUI |
|---|---|
| SubsystemVersion: | 5.1 |
| ImageVersion: | - |
| OSVersion: | 5.1 |
| EntryPoint: | 0x8ee3 |
| UninitializedDataSize: | 5120 |
| InitializedDataSize: | 687104 |
| CodeSize: | 35840 |
| LinkerVersion: | 12 |
| PEType: | PE32 |
| TimeStamp: | 2019:06:18 20:34:13+02:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 18-Jun-2019 18:34:13 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000040 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 7 |
| Time date stamp: | 18-Jun-2019 18:34:13 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
_BSS | 0x00001000 | 0x00001400 | 0x00001400 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.text | 0x00003000 | 0x00009000 | 0x00008C00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.21102 |
.rdata | 0x0000C000 | 0x0000B600 | 0x0000B600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.75014 |
_RDATA | 0x00018000 | 0x00081000 | 0x00080E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.52412 |
_IDT | 0x00099000 | 0x00001000 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 3.02971 |
.rsrc | 0x0009A000 | 0x0001B000 | 0x0001AE00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.351 |
.reloc | 0x000B5000 | 0x00001000 | 0x00000010 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 2.20282 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.33374 | 1070 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 5.50544 | 9540 | UNKNOWN | UNKNOWN | RT_ICON |
3 | 5.7837 | 17546 | UNKNOWN | UNKNOWN | RT_ICON |
4 | 5.4618 | 30948 | UNKNOWN | UNKNOWN | RT_ICON |
5 | 6.07706 | 49113 | UNKNOWN | UNKNOWN | RT_ICON |
101 | 1.54015 | 64 | UNKNOWN | UNKNOWN | RT_GROUP_ICON |
102 | 1.96928 | 50 | UNKNOWN | UNKNOWN | RT_GROUP_ICON |
Imports
kernel32.dll |
user32.dll |
Total processes
40
Monitored processes
2
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process |
|---|---|---|---|---|
| 2132 | "C:\Users\admin\AppData\Local\Temp\procchack.exe" | C:\Users\admin\AppData\Local\Temp\procchack.exe | — | explorer.exe |
User: admin Integrity Level: MEDIUM Exit code: 0 | ||||
| 3020 | "C:\Users\admin\AppData\Local\Temp\procchack.exe" "C:\Users\admin\AppData\Local\Temp\procchack.exe" | C:\Users\admin\AppData\Local\Temp\procchack.exe | procchack.exe | |
User: admin Integrity Level: HIGH Exit code: 0 | ||||
Total events
354
Read events
350
Write events
4
Delete events
0
Modification events
| (PID) Process: | (2132) procchack.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2132) procchack.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
0
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
1
DNS requests
1
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3020 | procchack.exe | GET | 200 | 13.35.254.108:80 | http://d1hq9wbcfo7dcl.cloudfront.net/offer.php?affId=7512&trackingId=421984183&instId=7584&ho_trackingid=HO421984183&cc=DE&sb=x86&wv=7sp1&db=InternetExplorer&uac=1&cid=5d979308c3b6ea5ad7e984e628c8cac1&v=3&net=4.7.03062&ie=8%2e0%2e7601%2e17514&res=1280x720&osd=677&kid=hqmrb21bekpv3g516u3 | US | — | — | shared |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3020 | procchack.exe | 13.35.254.108:80 | d1hq9wbcfo7dcl.cloudfront.net | — | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
d1hq9wbcfo7dcl.cloudfront.net |
| shared |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3020 | procchack.exe | Unknown Traffic | ET INFO Suspicious User-Agent (1 space) |
3020 | procchack.exe | Misc activity | ADWARE [PTsecurity] SoftwareBundler:Win32/Prepscram |
3 ETPRO signatures available at the full report