| File name: | 1.ps1 |
| Full analysis: | https://app.any.run/tasks/f6f39931-d969-4ad9-aa9d-70897d6616c4 |
| Verdict: | Malicious activity |
| Analysis date: | September 19, 2019, 01:46:57 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | text/plain |
| File info: | ASCII text, with very long lines, with CRLF line terminators |
| MD5: | 8663492E8AAED5F17F77E51AE92F997A |
| SHA1: | C525F37D82D539D99967E567649C01A063909E6A |
| SHA256: | 6056AA8C477D1BA68635836307537649AF0439ACBE749589A852EC09CD2A26CB |
| SSDEEP: | 24576:D9b35P4keTMQ6VRHYwq6xitjMvK0Nv2U8eCte4TxVTMKY7Bu:prVjeGit6/MxTMKGBu |
MALICIOUS
Application was dropped or rewritten from another process
- yjlr.exe (PID: 2824)
- yjlr.exe (PID: 2328)
- yjlr.exe (PID: 2396)
- yjlr.exe (PID: 2456)
- yjlr.exe (PID: 2584)
- yjlr.exe (PID: 2508)
- yjlr.exe (PID: 2656)
- yjlr.exe (PID: 2728)
- yjlr.exe (PID: 2804)
- yjlr.exe (PID: 2872)
- yjlr.exe (PID: 2932)
- yjlr.exe (PID: 2988)
- yjlr.exe (PID: 3056)
- yjlr.exe (PID: 3708)
- yjlr.exe (PID: 3384)
- yjlr.exe (PID: 3444)
- yjlr.exe (PID: 3644)
- yjlr.exe (PID: 3548)
- yjlr.exe (PID: 3780)
- yjlr.exe (PID: 3888)
- yjlr.exe (PID: 3996)
- yjlr.exe (PID: 3132)
- yjlr.exe (PID: 3196)
- yjlr.exe (PID: 3188)
- yjlr.exe (PID: 3320)
- yjlr.exe (PID: 3508)
- yjlr.exe (PID: 3808)
- yjlr.exe (PID: 2412)
- yjlr.exe (PID: 2672)
- yjlr.exe (PID: 2564)
- yjlr.exe (PID: 2724)
- yjlr.exe (PID: 2840)
- yjlr.exe (PID: 2976)
- yjlr.exe (PID: 3060)
- yjlr.exe (PID: 3944)
- yjlr.exe (PID: 1648)
- yjlr.exe (PID: 4060)
- yjlr.exe (PID: 2188)
- yjlr.exe (PID: 2260)
- yjlr.exe (PID: 2320)
- yjlr.exe (PID: 2492)
- yjlr.exe (PID: 2916)
- yjlr.exe (PID: 3624)
- yjlr.exe (PID: 3896)
- yjlr.exe (PID: 2280)
- yjlr.exe (PID: 3840)
- yjlr.exe (PID: 3868)
- yjlr.exe (PID: 3976)
- yjlr.exe (PID: 4076)
- yjlr.exe (PID: 2144)
- yjlr.exe (PID: 2148)
- yjlr.exe (PID: 3232)
- yjlr.exe (PID: 3300)
- yjlr.exe (PID: 3404)
- yjlr.exe (PID: 3416)
- yjlr.exe (PID: 3140)
- yjlr.exe (PID: 3556)
- yjlr.exe (PID: 3696)
- yjlr.exe (PID: 2812)
- yjlr.exe (PID: 3296)
- yjlr.exe (PID: 3012)
- yjlr.exe (PID: 3108)
- yjlr.exe (PID: 3760)
- yjlr.exe (PID: 3588)
- yjlr.exe (PID: 3704)
- yjlr.exe (PID: 3936)
- yjlr.exe (PID: 4068)
- yjlr.exe (PID: 324)
- yjlr.exe (PID: 2240)
- yjlr.exe (PID: 2380)
- yjlr.exe (PID: 2488)
- yjlr.exe (PID: 2692)
- yjlr.exe (PID: 2580)
- yjlr.exe (PID: 2908)
- yjlr.exe (PID: 3128)
- yjlr.exe (PID: 3396)
- yjlr.exe (PID: 3480)
- yjlr.exe (PID: 3880)
- yjlr.exe (PID: 2316)
- yjlr.exe (PID: 2600)
- yjlr.exe (PID: 2760)
- yjlr.exe (PID: 2892)
- yjlr.exe (PID: 2944)
- yjlr.exe (PID: 3092)
- yjlr.exe (PID: 3360)
- yjlr.exe (PID: 3236)
- yjlr.exe (PID: 2164)
- yjlr.exe (PID: 3420)
- yjlr.exe (PID: 3592)
- yjlr.exe (PID: 3684)
- yjlr.exe (PID: 3836)
- yjlr.exe (PID: 3948)
- yjlr.exe (PID: 4020)
- yjlr.exe (PID: 2304)
- yjlr.exe (PID: 2468)
- yjlr.exe (PID: 2408)
- yjlr.exe (PID: 2556)
- yjlr.exe (PID: 2744)
- yjlr.exe (PID: 2860)
- yjlr.exe (PID: 3052)
- yjlr.exe (PID: 3156)
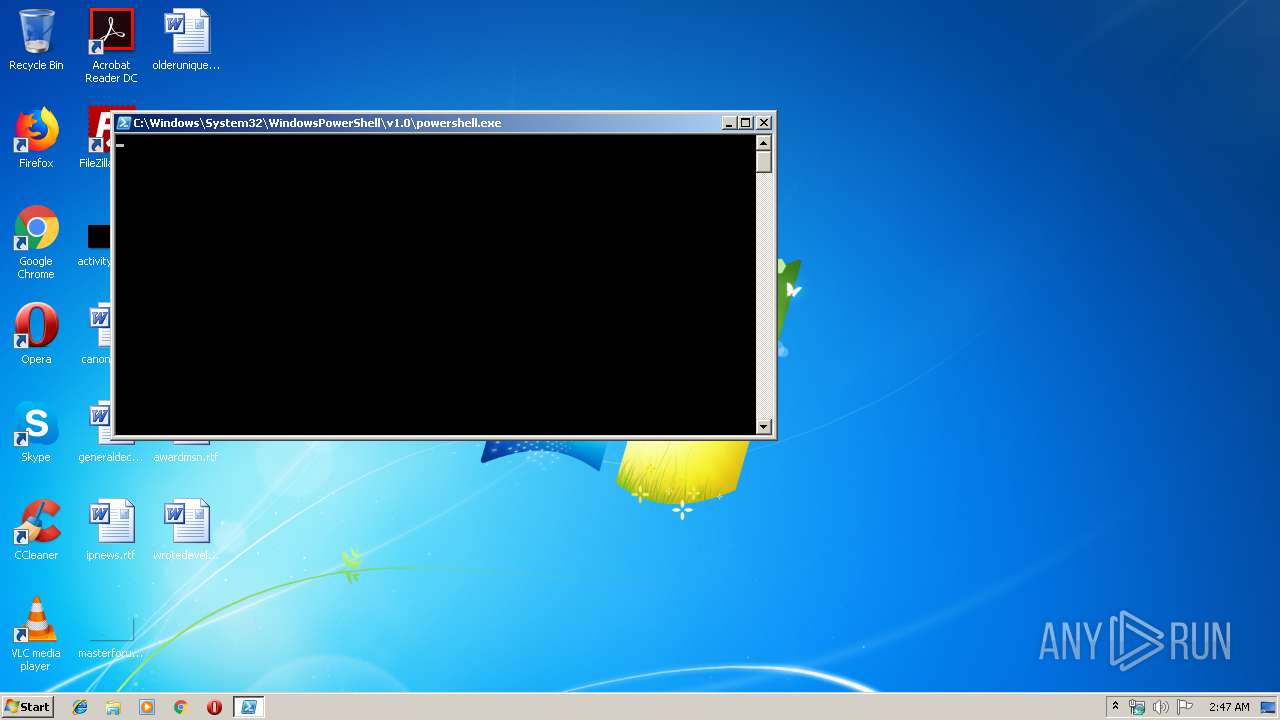
SUSPICIOUS
Executable content was dropped or overwritten
- powershell.exe (PID: 3004)
PowerShell script executed
- powershell.exe (PID: 3004)
Creates files in the user directory
- powershell.exe (PID: 3004)
Application launched itself
- yjlr.exe (PID: 2824)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
134
Monitored processes
102
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||
|---|---|---|---|---|---|---|---|
| 324 | "C:\Users\Public\yjlr.exe" | C:\Users\Public\yjlr.exe | — | yjlr.exe | |||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||
| 1648 | "C:\Users\Public\yjlr.exe" | C:\Users\Public\yjlr.exe | — | yjlr.exe | |||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||
| 2144 | "C:\Users\Public\yjlr.exe" | C:\Users\Public\yjlr.exe | — | yjlr.exe | |||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||
| 2148 | "C:\Users\Public\yjlr.exe" | C:\Users\Public\yjlr.exe | — | yjlr.exe | |||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||
| 2164 | "C:\Users\Public\yjlr.exe" | C:\Users\Public\yjlr.exe | — | yjlr.exe | |||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||
| 2188 | "C:\Users\Public\yjlr.exe" | C:\Users\Public\yjlr.exe | — | yjlr.exe | |||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||
| 2240 | "C:\Users\Public\yjlr.exe" | C:\Users\Public\yjlr.exe | — | yjlr.exe | |||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||
| 2260 | "C:\Users\Public\yjlr.exe" | C:\Users\Public\yjlr.exe | — | yjlr.exe | |||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||
| 2280 | "C:\Users\Public\yjlr.exe" | C:\Users\Public\yjlr.exe | — | yjlr.exe | |||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||
| 2304 | "C:\Users\Public\yjlr.exe" | C:\Users\Public\yjlr.exe | — | yjlr.exe | |||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||
Total events
218
Read events
159
Write events
59
Delete events
0
Modification events
| (PID) Process: | (3004) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\72\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3004) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3004) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
1
Suspicious files
2
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3004 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\XRI72YZT25CIMW5HUMSL.temp | — | |
MD5:— | SHA256:— | |||
| 3004 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF169c54.TMP | binary | |
MD5:— | SHA256:— | |||
| 3004 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 3004 | powershell.exe | C:\Users\Public\yjlr.exe | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report