| File name: | rbx.exe |
| Full analysis: | https://app.any.run/tasks/0ca7b4e7-d63e-46cd-a4f6-fa8ad051840c |
| Verdict: | Malicious activity |
| Analysis date: | September 20, 2020, 14:14:40 |
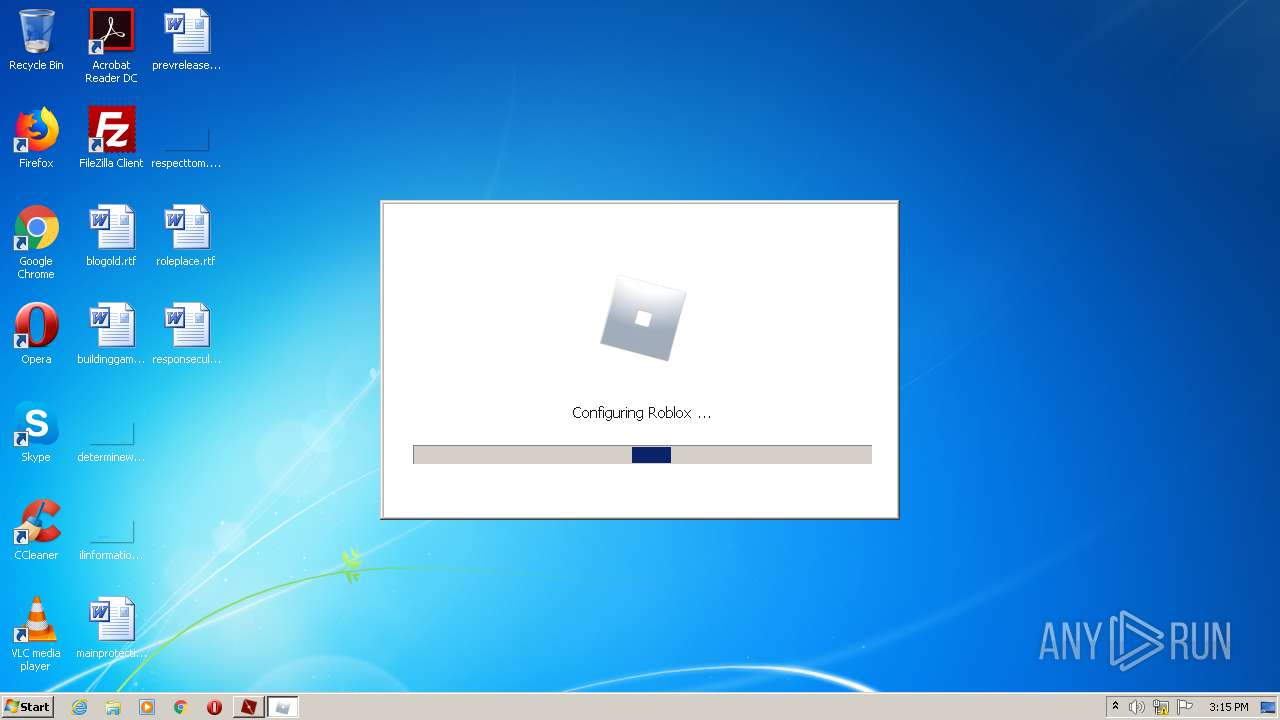
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | FEB03FAFFE612B6ACDE9F87979369094 |
| SHA1: | 3AC22DDEF5D4F6072F5D152BAD2016CF7AE7B98E |
| SHA256: | 60486A0398D61B91BACD124A13DFC3E8CAFA6FFE71AC0468C2896B4EA8C13509 |
| SSDEEP: | 24576:q9qFtP8QRhql6NBhxMYiK6mhi9lQ2sjUpSu2Q2lTQJP3mH01EVWoGwH:NR1BjPIqUSPTcPwTWaH |
MALICIOUS
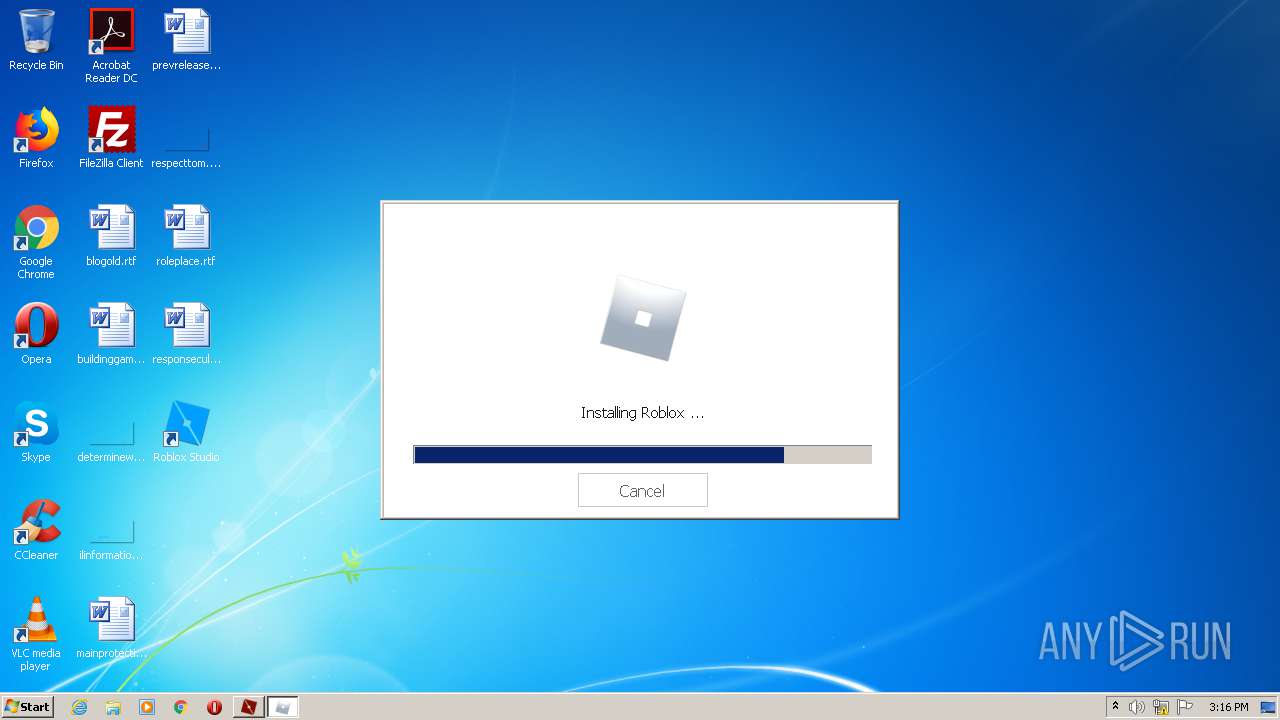
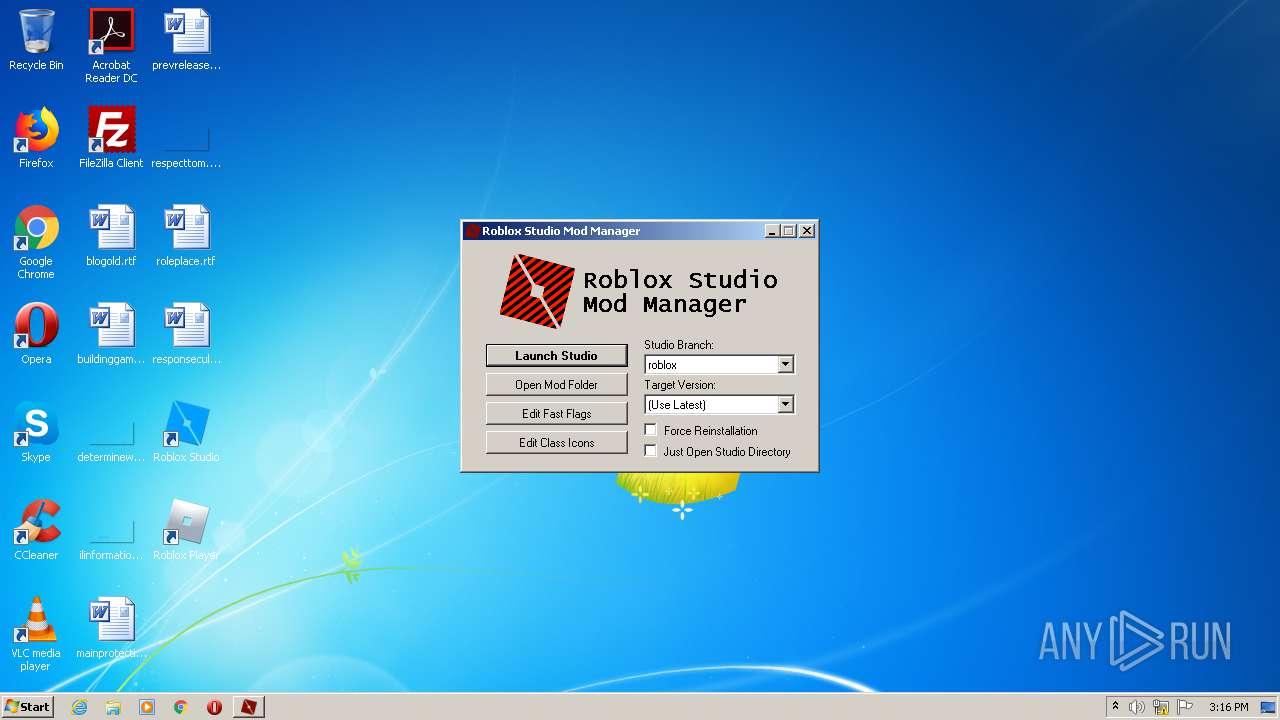
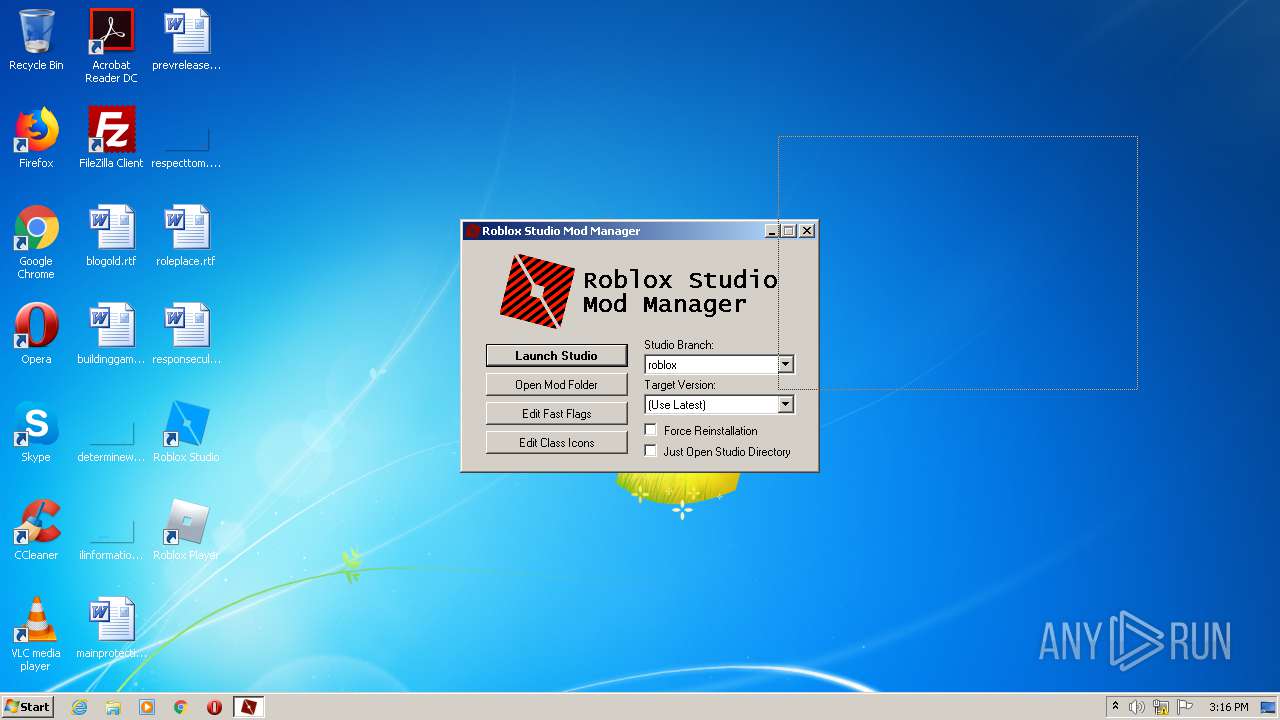
Application was dropped or rewritten from another process
- RobloxStudioModManager.exe (PID: 2772)
- RobloxPlayerLauncher.exe (PID: 3780)
- RobloxPlayerLauncher.exe (PID: 3172)
SUSPICIOUS
Reads internet explorer settings
- rbx.exe (PID: 2512)
Reads Internet Cache Settings
- RobloxPlayerLauncher.exe (PID: 3780)
- rbx.exe (PID: 2512)
- RobloxPlayerLauncher.exe (PID: 3172)
Executable content was dropped or overwritten
- rbx.exe (PID: 2512)
- RobloxPlayerLauncher.exe (PID: 3780)
Application launched itself
- RobloxPlayerLauncher.exe (PID: 3780)
Creates files in the user directory
- RobloxPlayerLauncher.exe (PID: 3780)
Modifies the open verb of a shell class
- RobloxPlayerLauncher.exe (PID: 3780)
Creates a software uninstall entry
- RobloxPlayerLauncher.exe (PID: 3780)
INFO
Reads settings of System Certificates
- RobloxPlayerLauncher.exe (PID: 3780)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (52.9) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (23.5) |
| .exe | | | DOS Executable Generic (23.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2019:04:27 22:03:33+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 14 |
| CodeSize: | 144896 |
| InitializedDataSize: | 312320 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1250b |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 27-Apr-2019 20:03:33 |
| Detected languages: |
|
| Debug artifacts: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000118 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 6 |
| Time date stamp: | 27-Apr-2019 20:03:33 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00023483 | 0x00023600 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.66783 |
.rdata | 0x00025000 | 0x00009070 | 0x00009200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.109 |
.data | 0x0002F000 | 0x000329F8 | 0x00000C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.71307 |
.gfids | 0x00062000 | 0x000000F4 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 2.15759 |
.rsrc | 0x00063000 | 0x0000DFD0 | 0x0000E000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.6366 |
.reloc | 0x00071000 | 0x00002514 | 0x00002600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.68804 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.25329 | 1875 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 5.10026 | 2216 | UNKNOWN | English - United States | RT_ICON |
3 | 5.25868 | 3752 | UNKNOWN | English - United States | RT_ICON |
4 | 5.02609 | 1128 | UNKNOWN | English - United States | RT_ICON |
5 | 5.18109 | 4264 | UNKNOWN | English - United States | RT_ICON |
6 | 5.04307 | 9640 | UNKNOWN | English - United States | RT_ICON |
7 | 3.1586 | 482 | UNKNOWN | English - United States | RT_STRING |
8 | 3.11685 | 460 | UNKNOWN | English - United States | RT_STRING |
9 | 3.15447 | 494 | UNKNOWN | English - United States | RT_STRING |
10 | 2.99727 | 326 | UNKNOWN | English - United States | RT_STRING |
Imports
KERNEL32.dll |
USER32.dll (delay-loaded) |
gdiplus.dll |
Total processes
44
Monitored processes
4
Malicious processes
2
Suspicious processes
0
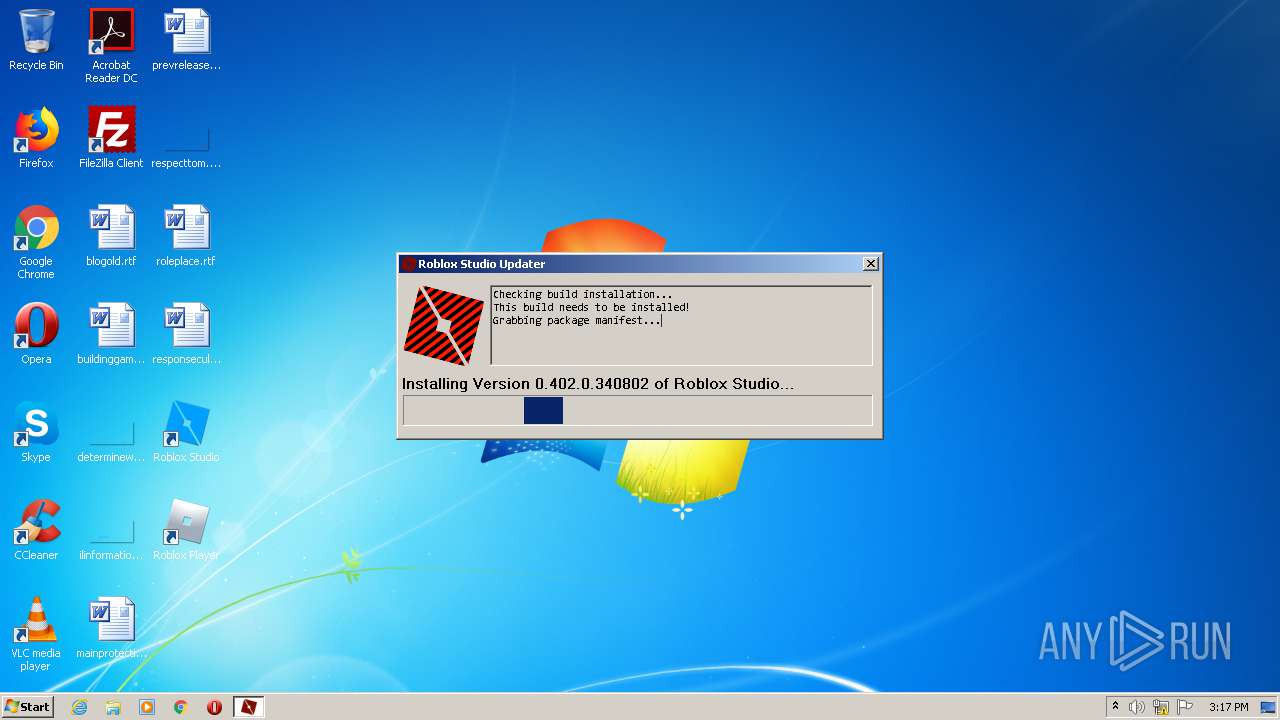
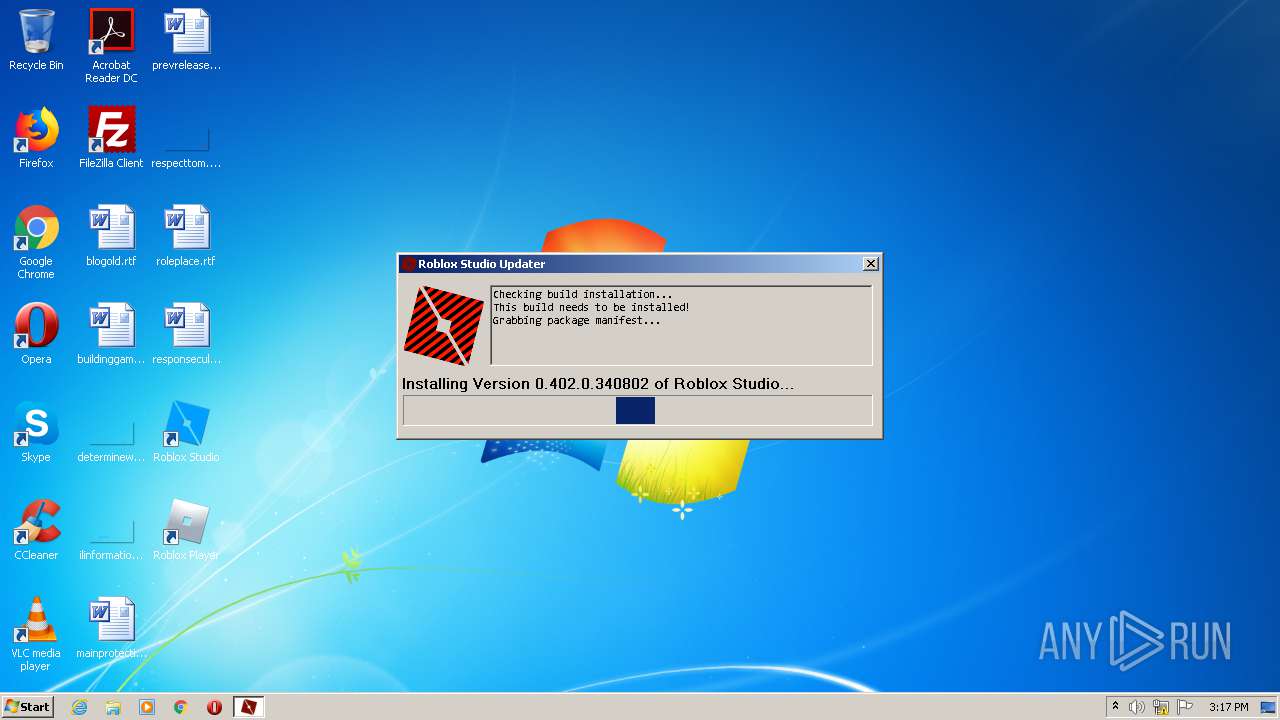
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
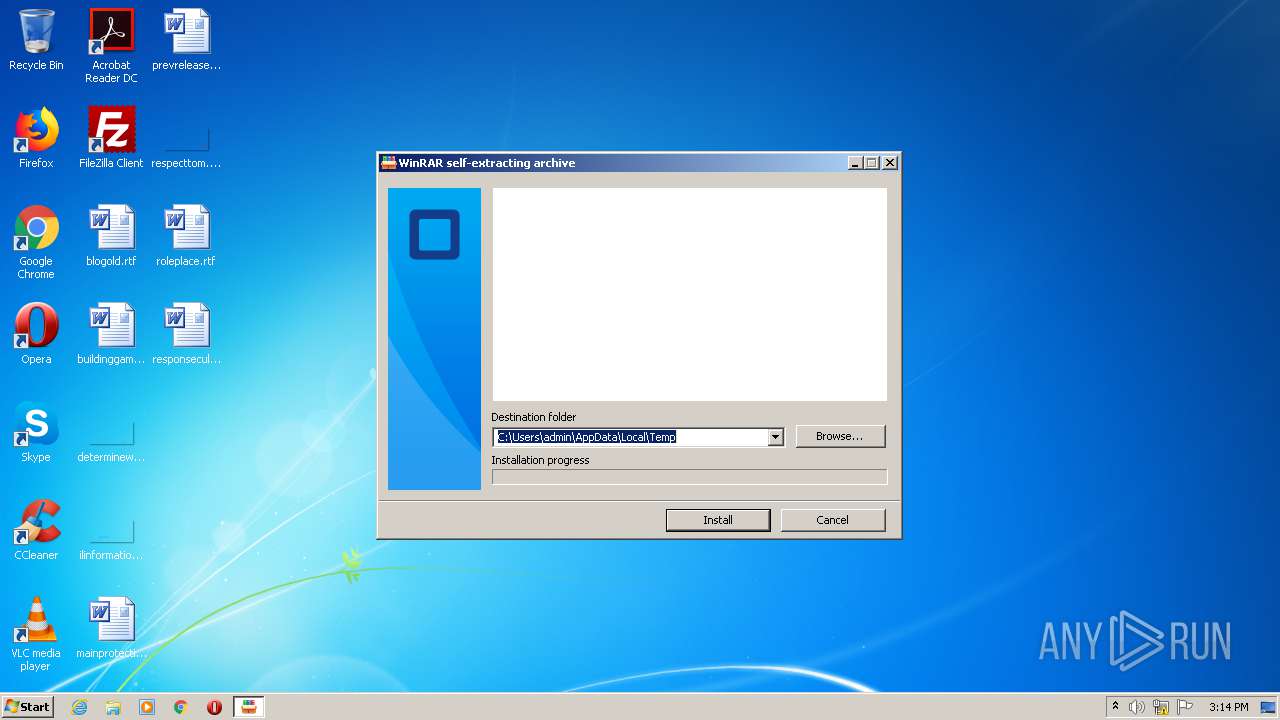
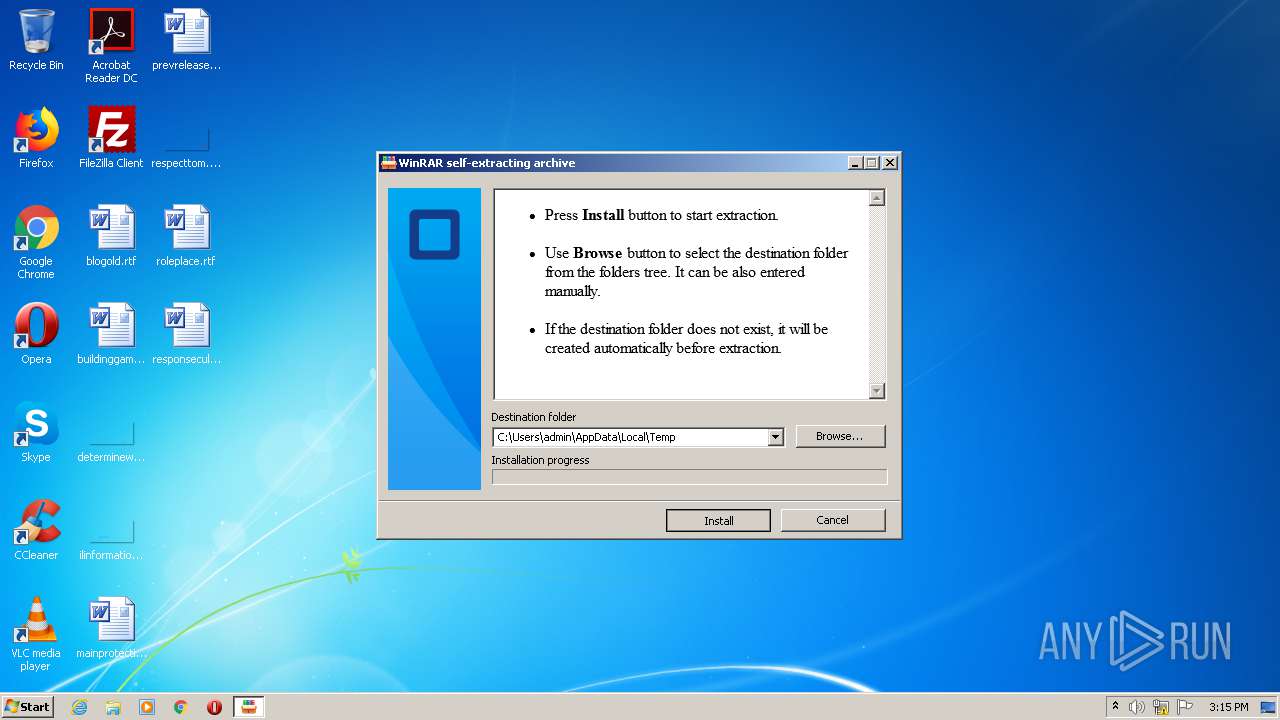
| 2512 | "C:\Users\admin\AppData\Local\Temp\rbx.exe" | C:\Users\admin\AppData\Local\Temp\rbx.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
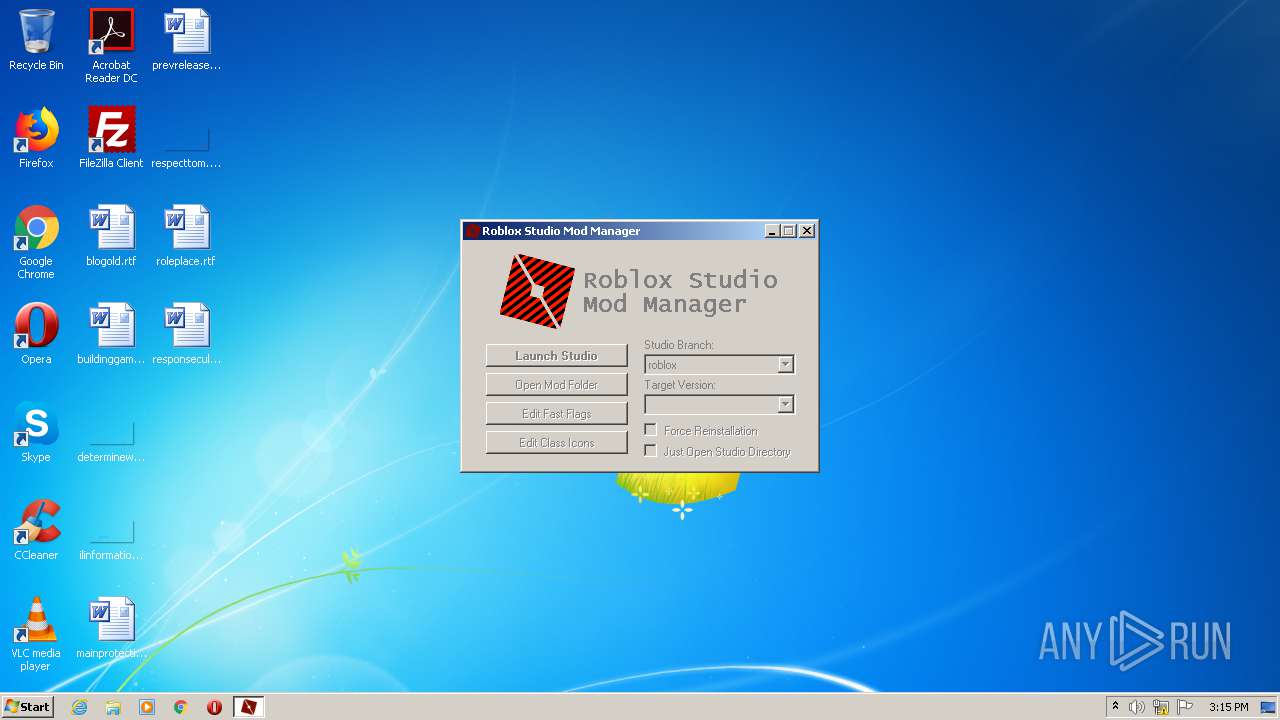
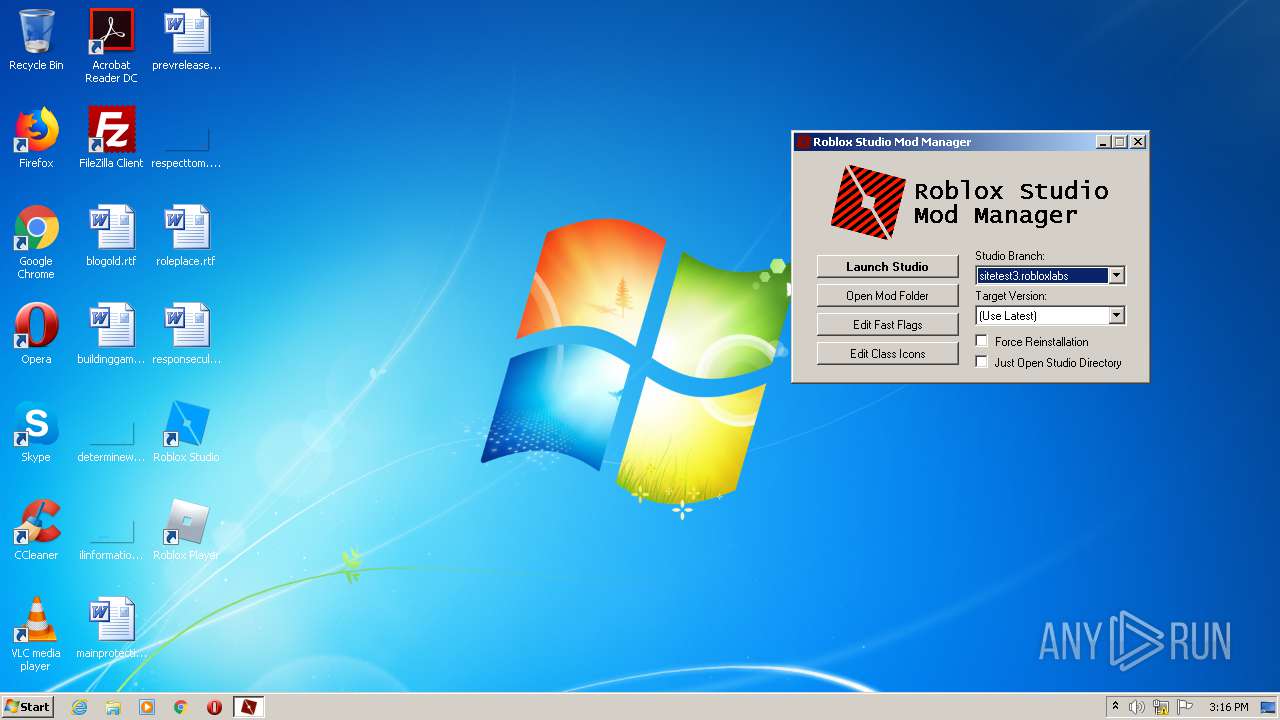
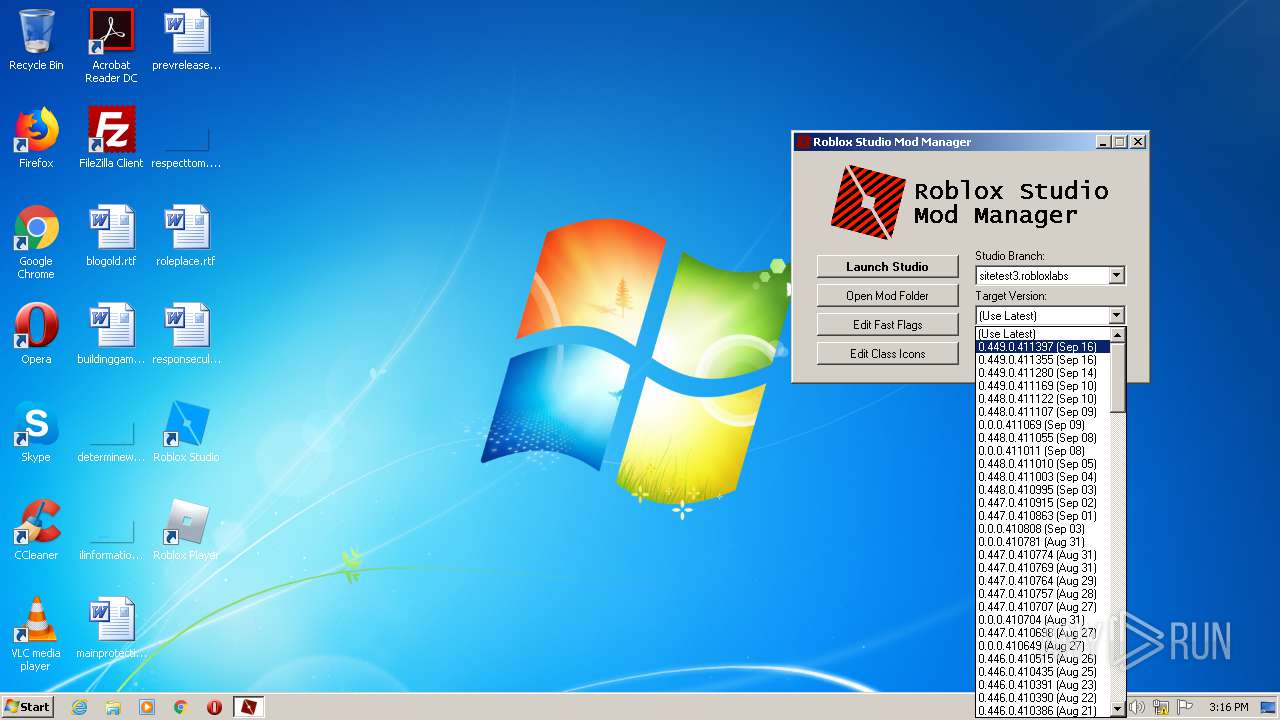
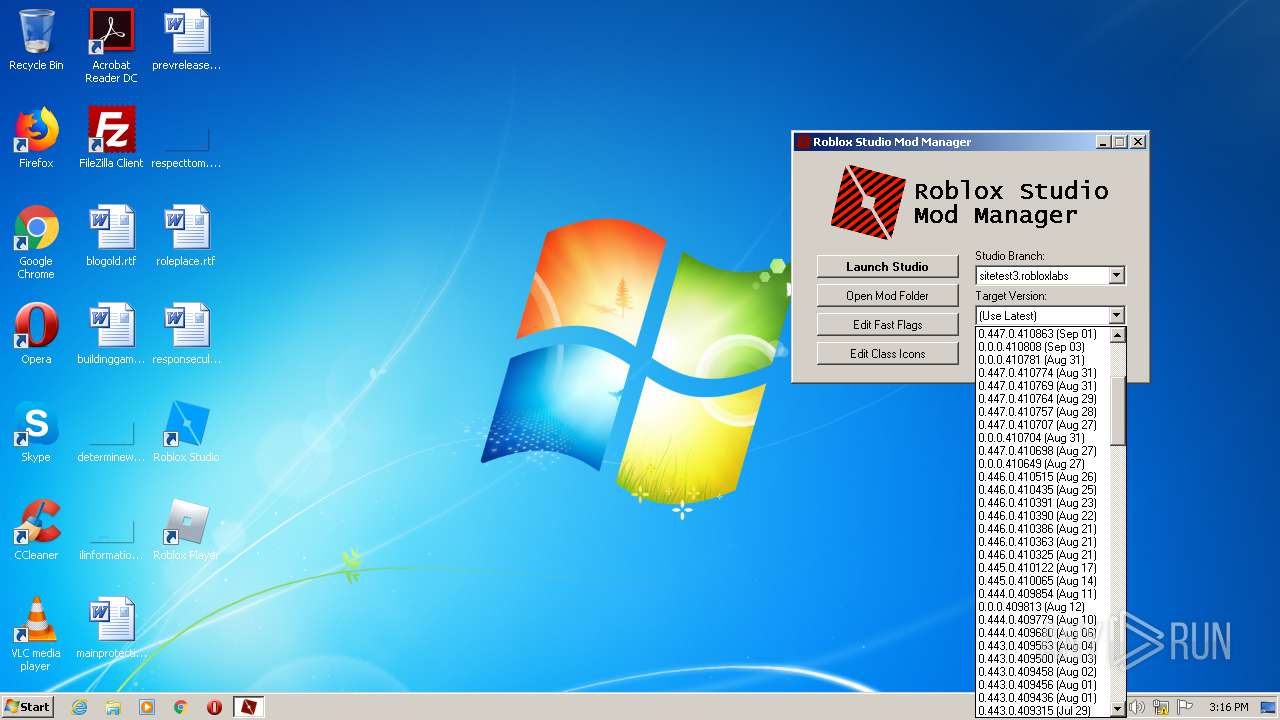
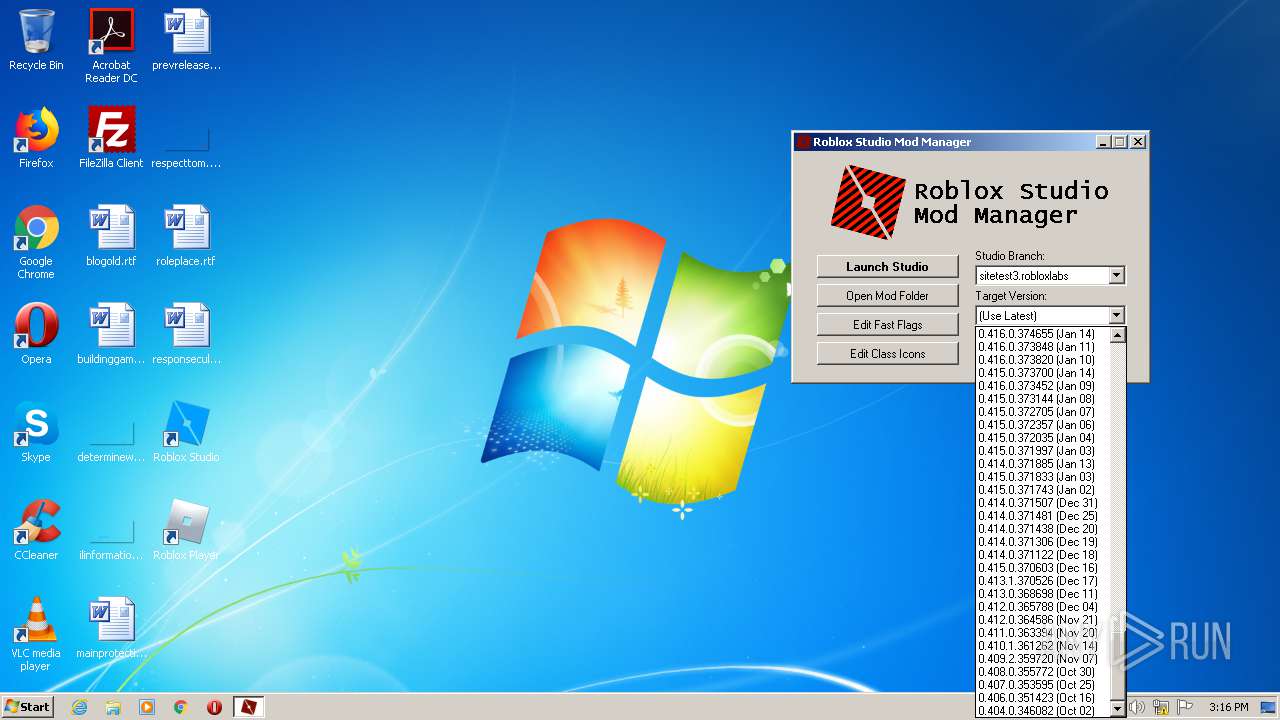
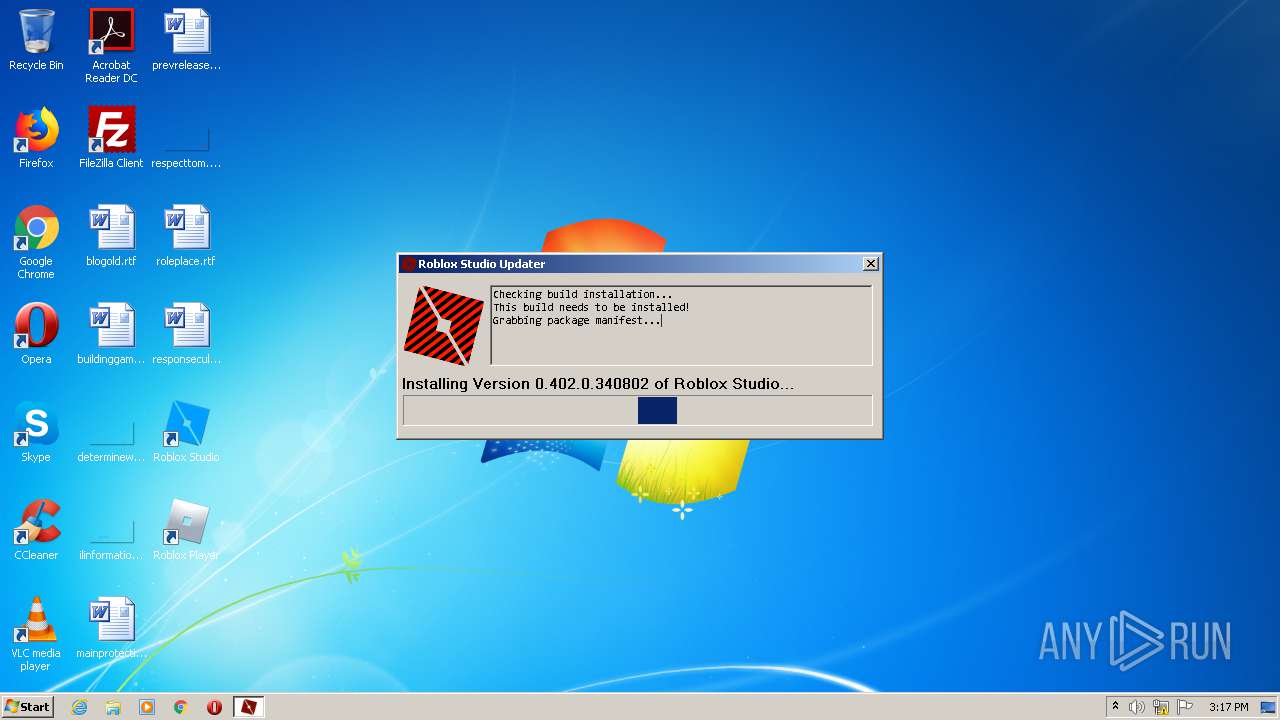
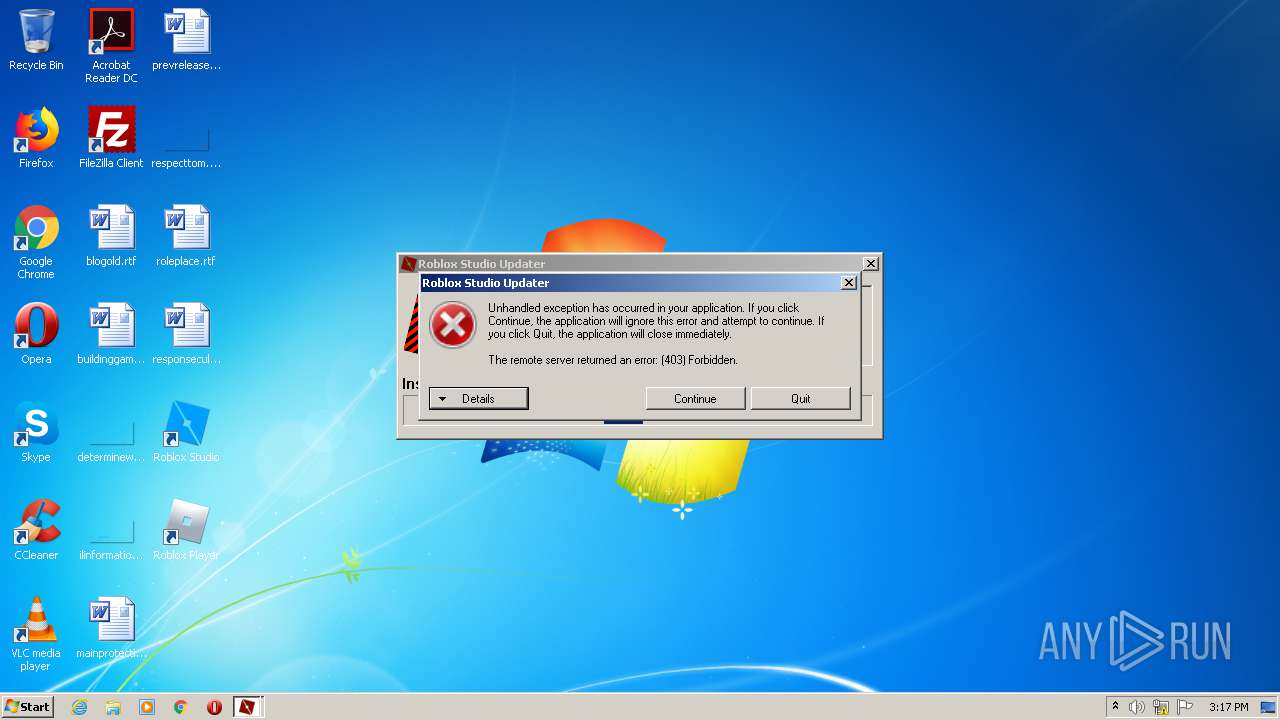
| 2772 | "C:\Users\admin\AppData\Local\Temp\RobloxStudioModManager.exe" | C:\Users\admin\AppData\Local\Temp\RobloxStudioModManager.exe | rbx.exe | ||||||||||||
User: admin Company: @CloneTeee1019 Integrity Level: MEDIUM Description: Roblox Studio Mod Manager Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 3172 | C:\Users\admin\AppData\Local\Temp\RobloxPlayerLauncher.exe --crashpad --no-rate-limit --database=C:\Users\admin\AppData\Local\Temp\crashpad_roblox --metrics-dir=C:\Users\admin\AppData\Local\Temp\crashpad_roblox --url=https://upload.crashes.rbxinfra.com/post --annotation=UploadAttachmentKiloByteLimit=100 --annotation=UploadPercentage=100 --annotation=format=minidump --annotation=token=a2440b0bfdada85f34d79b43839f2b49ea6bba474bd7d126e844bc119271a1c3 --initial-client-data=0x530,0x534,0x538,0x50c,0x540,0x24d83c,0x24d84c,0x24d85c | C:\Users\admin\AppData\Local\Temp\RobloxPlayerLauncher.exe | RobloxPlayerLauncher.exe | ||||||||||||
User: admin Company: Roblox Corporation Integrity Level: MEDIUM Description: Roblox Exit code: 0 Version: 1, 6, 0, 411244 Modules
| |||||||||||||||
| 3780 | "C:\Users\admin\AppData\Local\Temp\RobloxPlayerLauncher.exe" | C:\Users\admin\AppData\Local\Temp\RobloxPlayerLauncher.exe | rbx.exe | ||||||||||||
User: admin Company: Roblox Corporation Integrity Level: MEDIUM Description: Roblox Exit code: 0 Version: 1, 6, 0, 411244 Modules
| |||||||||||||||
Total events
970
Read events
857
Write events
113
Delete events
0
Modification events
| (PID) Process: | (2512) rbx.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2512) rbx.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2512) rbx.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2512) rbx.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2512) rbx.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3780) RobloxPlayerLauncher.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3780) RobloxPlayerLauncher.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3780) RobloxPlayerLauncher.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3780) RobloxPlayerLauncher.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (3780) RobloxPlayerLauncher.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A3000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
Executable files
6
Suspicious files
44
Text files
12
Unknown types
9
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3780 | RobloxPlayerLauncher.exe | C:\Users\admin\AppData\Local\Temp\Cab2FBF.tmp | — | |
MD5:— | SHA256:— | |||
| 3780 | RobloxPlayerLauncher.exe | C:\Users\admin\AppData\Local\Temp\Tar2FD0.tmp | — | |
MD5:— | SHA256:— | |||
| 3172 | RobloxPlayerLauncher.exe | C:\Users\admin\AppData\Local\Temp\Cab31F2.tmp | — | |
MD5:— | SHA256:— | |||
| 3172 | RobloxPlayerLauncher.exe | C:\Users\admin\AppData\Local\Temp\Tar31F3.tmp | — | |
MD5:— | SHA256:— | |||
| 3780 | RobloxPlayerLauncher.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\DZO23JVJ.txt | — | |
MD5:— | SHA256:— | |||
| 3780 | RobloxPlayerLauncher.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\PO2HN1X2\GetInstallerCdns[1].json | — | |
MD5:— | SHA256:— | |||
| 2512 | rbx.exe | C:\Users\admin\AppData\Local\Temp\RobloxPlayerLauncher.exe | executable | |
MD5:— | SHA256:— | |||
| 3780 | RobloxPlayerLauncher.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\PO2HN1X2\application[1].json | text | |
MD5:— | SHA256:— | |||
| 3780 | RobloxPlayerLauncher.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\7423F88C7F265F0DEFC08EA88C3BDE45_D975BBA8033175C8D112023D8A7A8AD6 | der | |
MD5:— | SHA256:— | |||
| 2512 | rbx.exe | C:\Users\admin\AppData\Local\Temp\RobloxStudioModManager.exe | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
20
DNS requests
18
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3780 | RobloxPlayerLauncher.exe | GET | 200 | 192.124.249.36:80 | http://ocsp.godaddy.com//MEQwQjBAMD4wPDAJBgUrDgMCGgUABBTkIInKBAzXkF0Qh0pel3lfHJ9GPAQU0sSw0pHUTBFxs2HLPaH%2B3ahq1OMCAxvnFQ%3D%3D | US | der | 1.66 Kb | whitelisted |
3780 | RobloxPlayerLauncher.exe | GET | 200 | 192.124.249.36:80 | http://ocsp.godaddy.com//MEIwQDA%2BMDwwOjAJBgUrDgMCGgUABBQdI2%2BOBkuXH93foRUj4a7lAr4rGwQUOpqFBxBnKLbv9r0FQW4gwZTaD94CAQc%3D | US | der | 1.69 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3780 | RobloxPlayerLauncher.exe | 104.111.227.55:443 | clientsettingscdn.roblox.com | Akamai International B.V. | NL | unknown |
3780 | RobloxPlayerLauncher.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2772 | RobloxStudioModManager.exe | 104.111.227.55:443 | clientsettingscdn.roblox.com | Akamai International B.V. | NL | unknown |
3780 | RobloxPlayerLauncher.exe | 128.116.121.3:443 | ephemeralcounters.api.roblox.com | University Corporation for Atmospheric Research | US | suspicious |
3780 | RobloxPlayerLauncher.exe | 192.124.249.36:80 | ocsp.godaddy.com | Sucuri | US | suspicious |
3172 | RobloxPlayerLauncher.exe | 104.111.227.55:443 | clientsettingscdn.roblox.com | Akamai International B.V. | NL | unknown |
3780 | RobloxPlayerLauncher.exe | 205.185.216.10:443 | setup.rbxcdn.com | Highwinds Network Group, Inc. | US | whitelisted |
3780 | RobloxPlayerLauncher.exe | 128.116.123.3:443 | www.roblox.com | University Corporation for Atmospheric Research | US | suspicious |
3172 | RobloxPlayerLauncher.exe | 128.116.121.3:443 | ephemeralcounters.api.roblox.com | University Corporation for Atmospheric Research | US | suspicious |
3780 | RobloxPlayerLauncher.exe | 54.165.151.168:8092 | ec2-54-165-151-168.compute-1.amazonaws.com | Amazon.com, Inc. | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientsettingscdn.roblox.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
s3.amazonaws.com |
| shared |
ephemeralcounters.api.roblox.com |
| whitelisted |
ocsp.godaddy.com |
| whitelisted |
setup.rbxcdn.qq.com |
| suspicious |
clientsettingscdn.roblox.qq.com |
| unknown |
setup.rbxcdn.com |
| whitelisted |
setup-ak.rbxcdn.com |
| whitelisted |
setup-ll.rbxcdn.com |
| whitelisted |