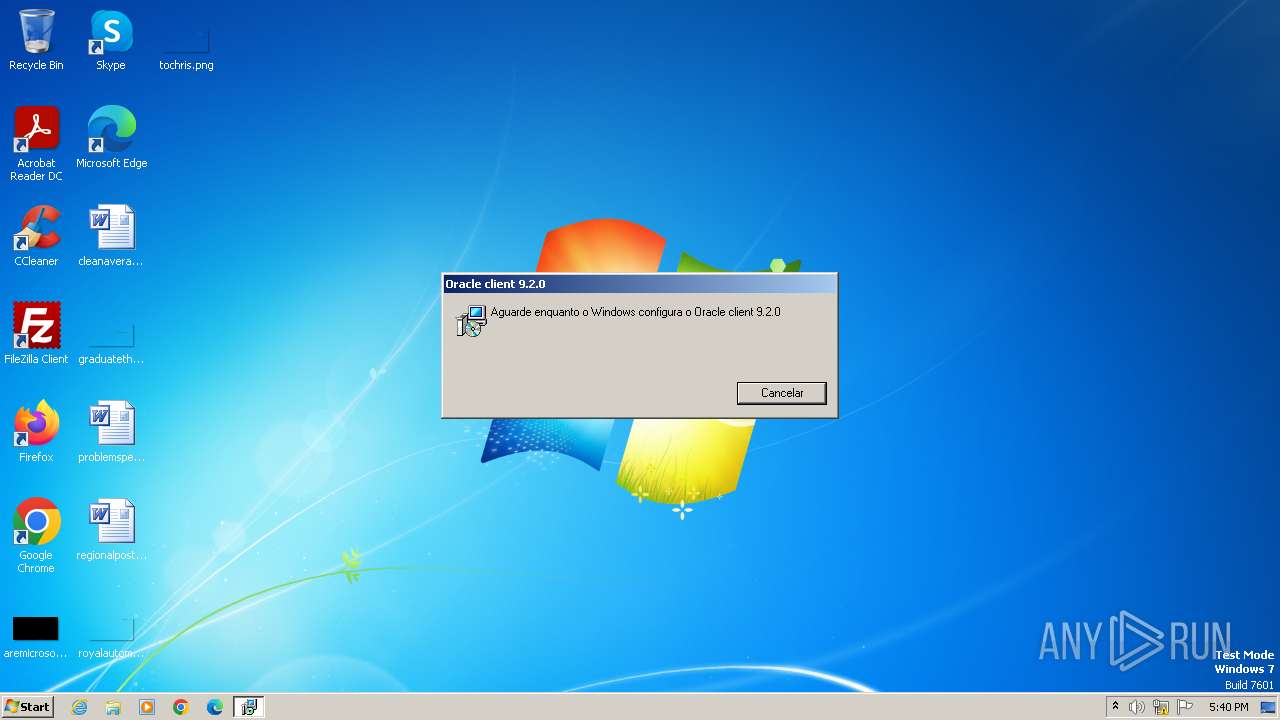
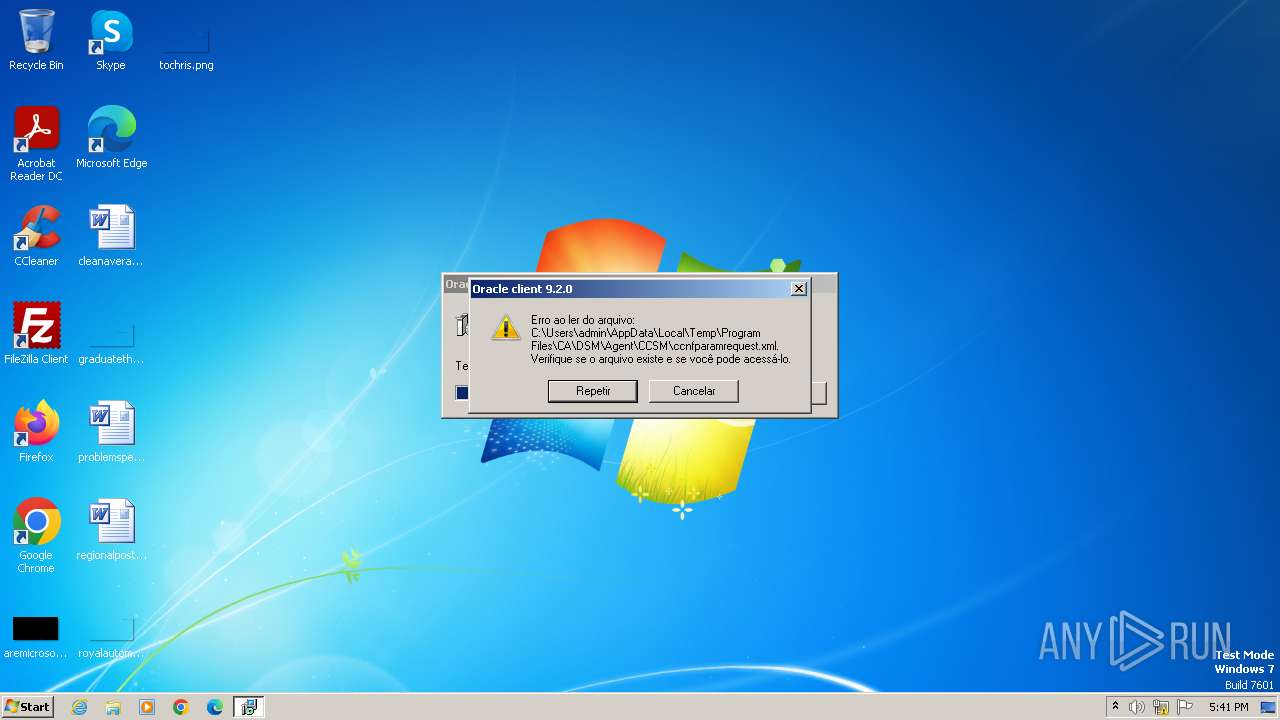
| File name: | Oracle client 9.2.0.msi |
| Full analysis: | https://app.any.run/tasks/420987b1-5cea-4447-97df-240eb3abf8ed |
| Verdict: | Malicious activity |
| Analysis date: | May 10, 2024, 16:40:31 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-msi |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.0, MSI Installer, Code page: 1252, Title: Installation Database, Subject: Oracle client 9.2.0, Author: Default Manufacturer, Keywords: Installer,MSI,Database, Comments: This installer database contains the logic and data required to install Oracle client 9.2.0., Template: Intel;1046, Last Saved By: Administrador, Revision Number: {A6C4EE1A-D010-4799-BB09-84EF3EAE931E}, Create Time/Date: Wed Oct 29 21:30:29 2008, Number of Pages: 200, Number of Words: 0, Name of Creating Application: OnDemand WinINSTALL 9.50.0000, Security: 0 |
| MD5: | DFBFCFA27CDEEC0C82921EBE5895E4F2 |
| SHA1: | 6B7AA383A89DB0CA2096F36255C0C58E4A8706E3 |
| SHA256: | 604414CA3E6E9B29147621BFFA65550735764AA560E075CC4CAB0E7B7319C452 |
| SSDEEP: | 12288:lYe3WrM9HbzCWjoL7BKf5iRoF2mbYILdZANPV:lYe3WI9HbzCWcLEQoF2mbYILdZANPV |
MALICIOUS
Drops the executable file immediately after the start
- msiexec.exe (PID: 4016)
- msiexec.exe (PID: 3976)
SUSPICIOUS
Executes as Windows Service
- VSSVC.exe (PID: 4060)
Reads the Windows owner or organization settings
- msiexec.exe (PID: 4016)
The process verifies whether the antivirus software is installed
- msiexec.exe (PID: 4016)
INFO
Reads the computer name
- msiexec.exe (PID: 4016)
Checks supported languages
- msiexec.exe (PID: 4016)
Create files in a temporary directory
- msiexec.exe (PID: 4016)
- msiexec.exe (PID: 3976)
Reads the machine GUID from the registry
- msiexec.exe (PID: 4016)
Executable content was dropped or overwritten
- msiexec.exe (PID: 4016)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msi | | | Microsoft Windows Installer (88.6) |
|---|---|---|
| .mst | | | Windows SDK Setup Transform Script (10) |
| .msi | | | Microsoft Installer (100) |
EXIF
FlashPix
| CodePage: | Windows Latin 1 (Western European) |
|---|---|
| Title: | Installation Database |
| Subject: | Oracle client 9.2.0 |
| Author: | Default Manufacturer |
| Keywords: | Installer,MSI,Database |
| Comments: | This installer database contains the logic and data required to install Oracle client 9.2.0. |
| Template: | Intel;1046 |
| LastModifiedBy: | Administrador |
| RevisionNumber: | {A6C4EE1A-D010-4799-BB09-84EF3EAE931E} |
| CreateDate: | 2008:10:29 21:30:29 |
| Pages: | 200 |
| Words: | - |
| Software: | OnDemand WinINSTALL 9.50.0000 |
| Security: | None |
Total processes
36
Monitored processes
3
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 3976 | "C:\Windows\System32\msiexec.exe" /i "C:\Users\admin\AppData\Local\Temp\Oracle client 9.2.0.msi" | C:\Windows\System32\msiexec.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 4016 | C:\Windows\system32\msiexec.exe /V | C:\Windows\System32\msiexec.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 4060 | C:\Windows\system32\vssvc.exe | C:\Windows\System32\VSSVC.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
11 349
Read events
7 281
Write events
4 068
Delete events
0
Modification events
| (PID) Process: | (4016) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SystemRestore |
| Operation: | write | Name: | SrCreateRp (Enter) |
Value: 4000000000000000641594CAF8A2DA01B00F0000D40F0000D5070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (4016) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SPP |
| Operation: | write | Name: | SppCreate (Enter) |
Value: 4000000000000000641594CAF8A2DA01B00F0000D40F0000D0070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (4016) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SPP |
| Operation: | write | Name: | LastIndex |
Value: 75 | |||
| (PID) Process: | (4016) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGatherWriterMetadata (Enter) |
Value: 4000000000000000D6B156CCF8A2DA01B00F0000D40F0000D3070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (4016) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\VssapiPublisher |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4000000000000000D6B156CCF8A2DA01B00F0000F0020000E8030000010000000000000000000000A1E75CFB657B9F4082959D339F666E150000000000000000 | |||
| (PID) Process: | (4060) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\ASR Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4000000000000000F2FF64CCF8A2DA01DC0F0000E80F0000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (4060) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\Registry Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4000000000000000F2FF64CCF8A2DA01DC0F0000FC070000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (4060) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\Shadow Copy Optimization Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4000000000000000F2FF64CCF8A2DA01DC0F0000E40F0000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (4060) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\COM+ REGDB Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4000000000000000F2FF64CCF8A2DA01DC0F0000EC070000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (4060) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\COM+ REGDB Writer |
| Operation: | write | Name: | IDENTIFY (Leave) |
Value: 400000000000000000276CCCF8A2DA01DC0F0000EC070000E8030000000000000100000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
1
Suspicious files
4
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4016 | msiexec.exe | C:\System Volume Information\SPP\OnlineMetadataCache\{fb5ce7a1-7b65-409f-8295-9d339f666e15}_OnDiskSnapshotProp | — | |
MD5:— | SHA256:— | |||
| 4016 | msiexec.exe | C:\System Volume Information\SPP\metadata-2 | — | |
MD5:— | SHA256:— | |||
| 4016 | msiexec.exe | C:\Windows\Installer\MSI63BD.tmp | binary | |
MD5:5A14CC43A5D47D6DFB8456B9B9FDB35E | SHA256:1D19AD5853FBB3C28E41AAFE36A72DE63078F437FF976373504F948C4AAA4F6D | |||
| 4016 | msiexec.exe | C:\Windows\Installer\1057e6.msi | executable | |
MD5:DFBFCFA27CDEEC0C82921EBE5895E4F2 | SHA256:604414CA3E6E9B29147621BFFA65550735764AA560E075CC4CAB0E7B7319C452 | |||
| 4016 | msiexec.exe | C:\Windows\Installer\1057e8.ipi | binary | |
MD5:FACE8AB338BBF74D69AD3E746EBD6165 | SHA256:F22E4BC6E9DEAD833F8EA88B8E6BDCC433EEC5836B16D636498E0E1CFE121B87 | |||
| 4016 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\~DF8EA686AD9B10634A.TMP | binary | |
MD5:74CCCE57AC3119ACD6A50CAD4C51B6B6 | SHA256:BFF9077C94EBA1061516C4FFA103D8660EF04399503F4C42DB96F1AFC248D6CB | |||
| 4016 | msiexec.exe | C:\System Volume Information\SPP\snapshot-2 | binary | |
MD5:B96B8DB7ED41A35128FB6A68364212FB | SHA256:A9BC2218A9ED51486F4C66A48952AB40806C827EF02241C793B61E13CDCB88D7 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
4
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 224.0.0.252:5355 | — | — | — | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1088 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |