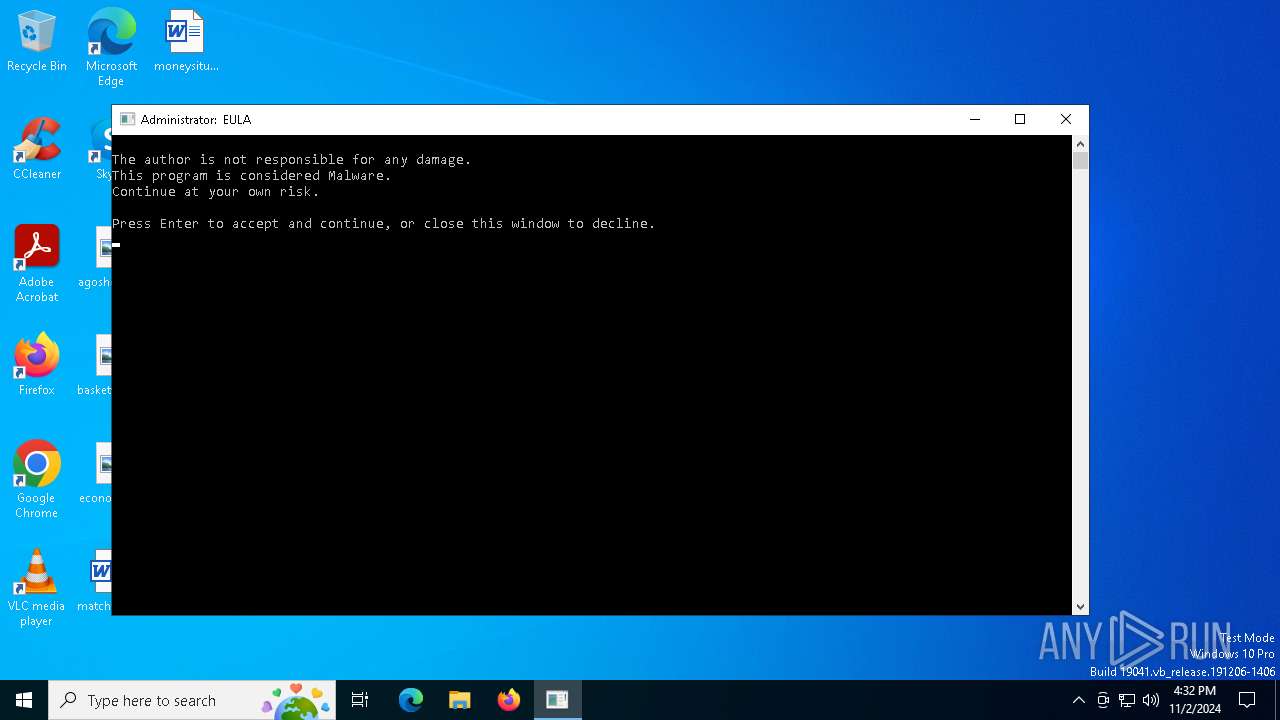
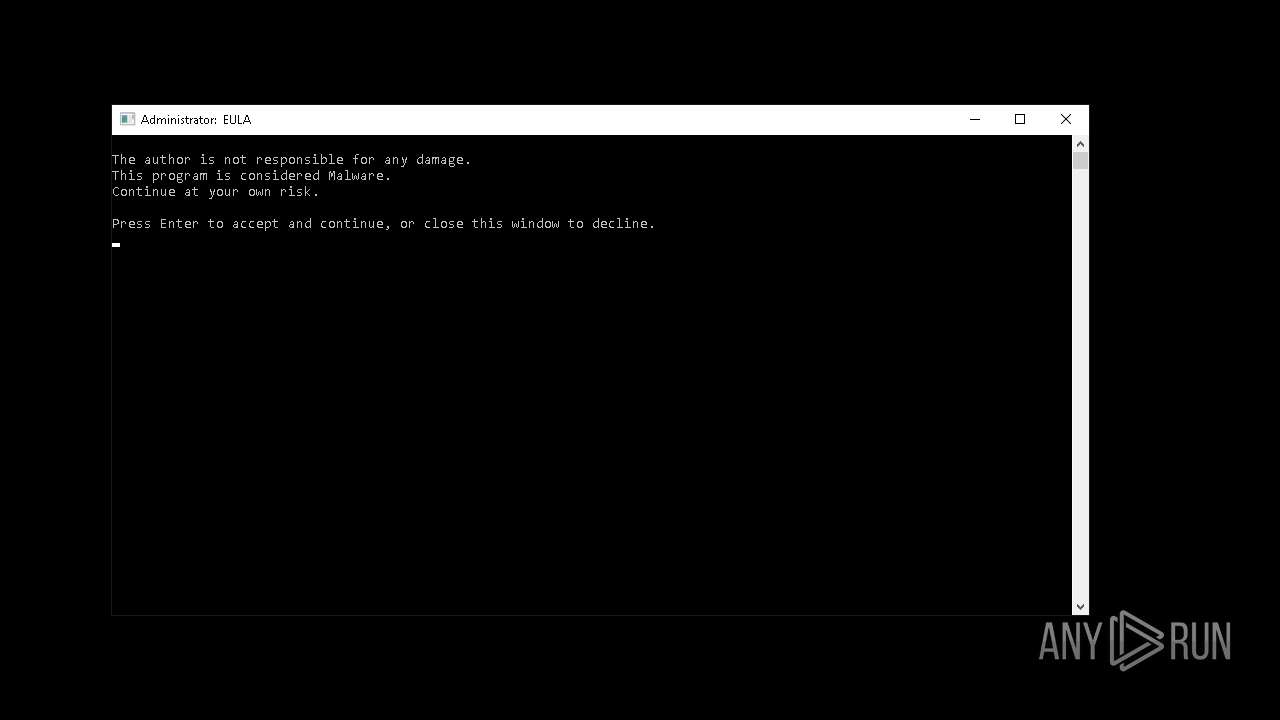
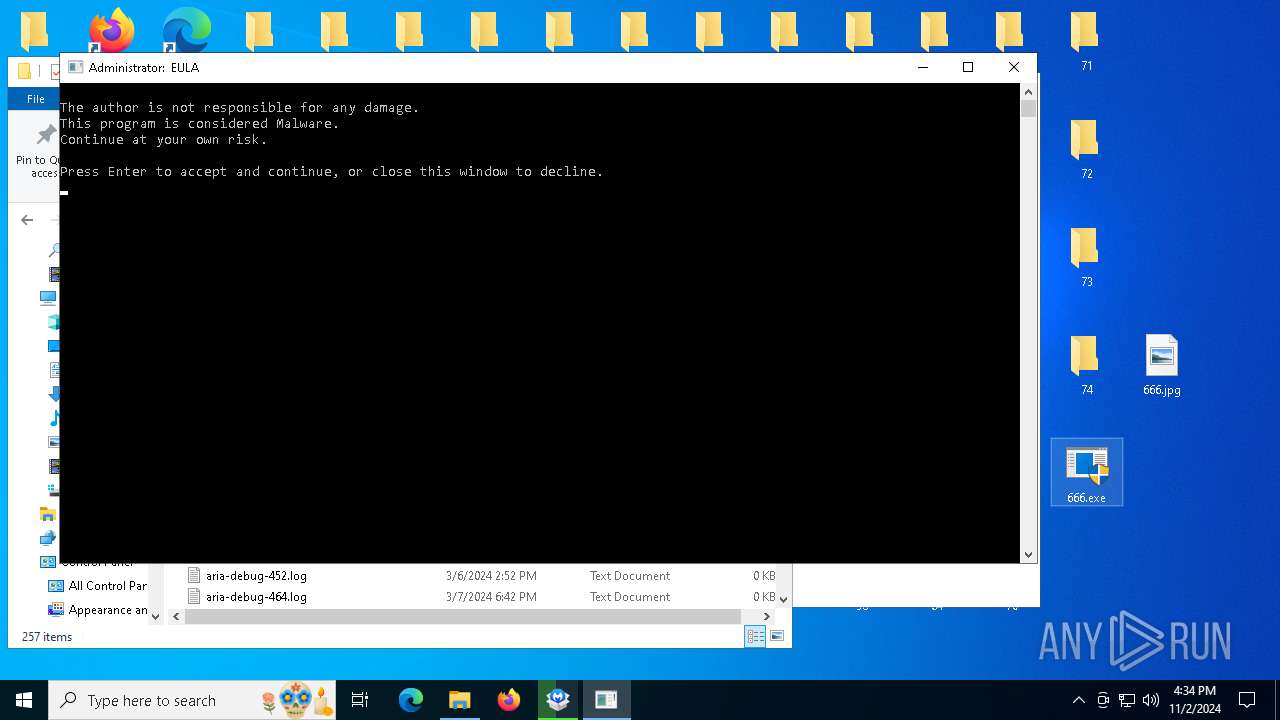
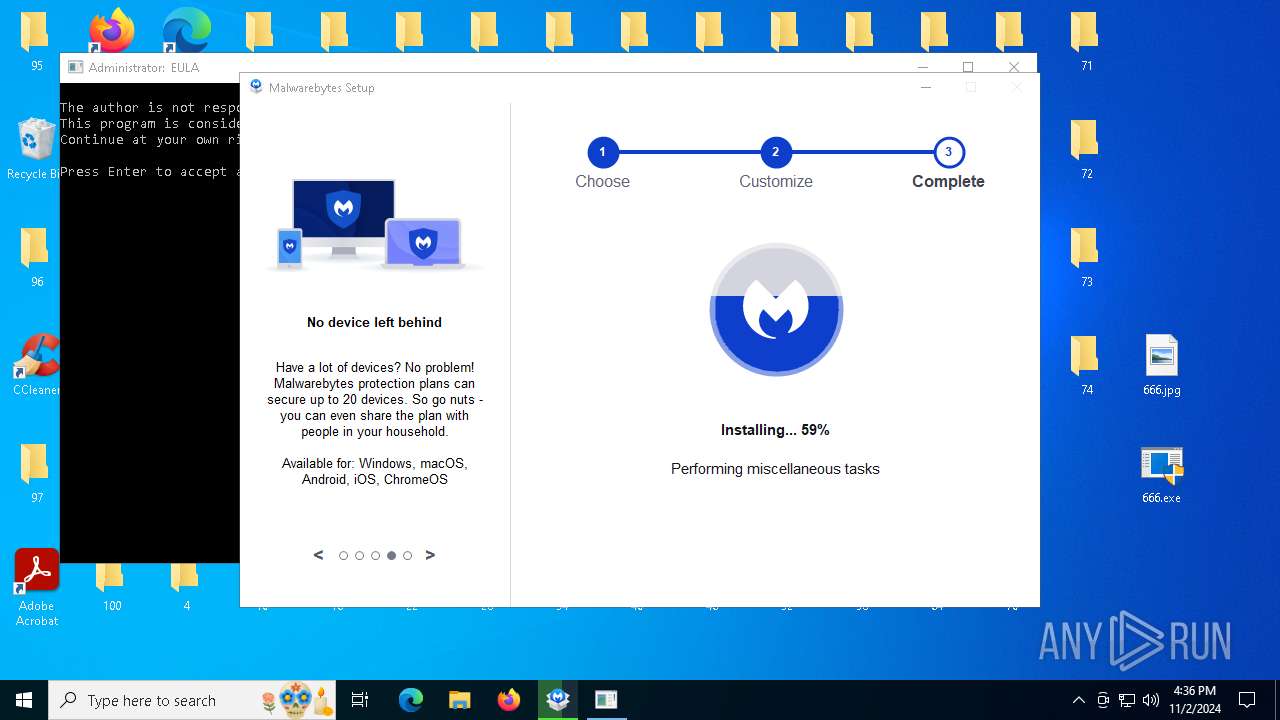
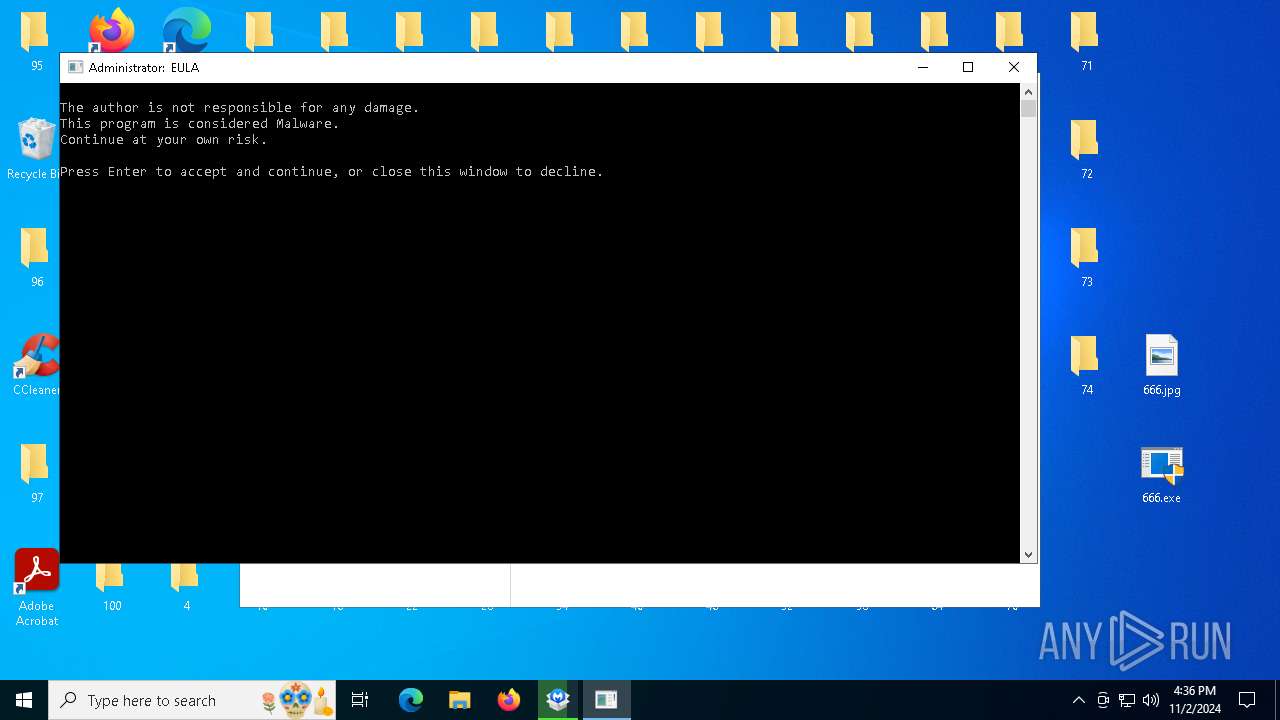
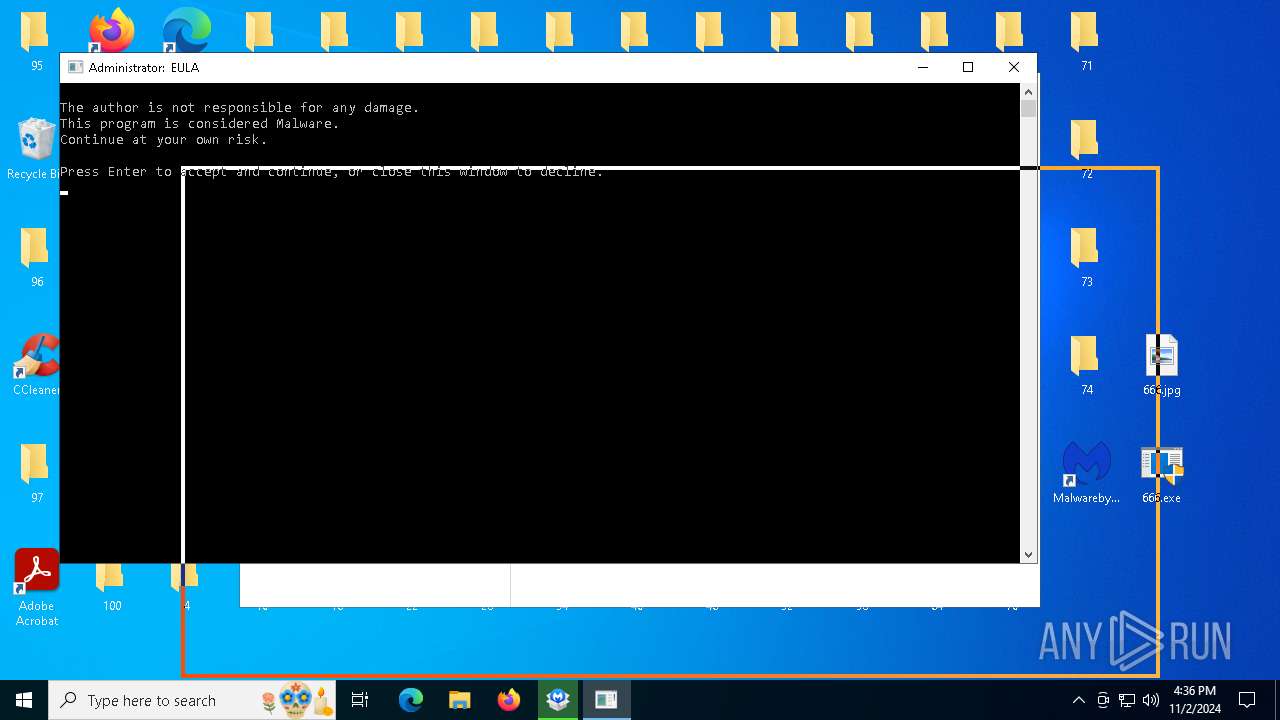
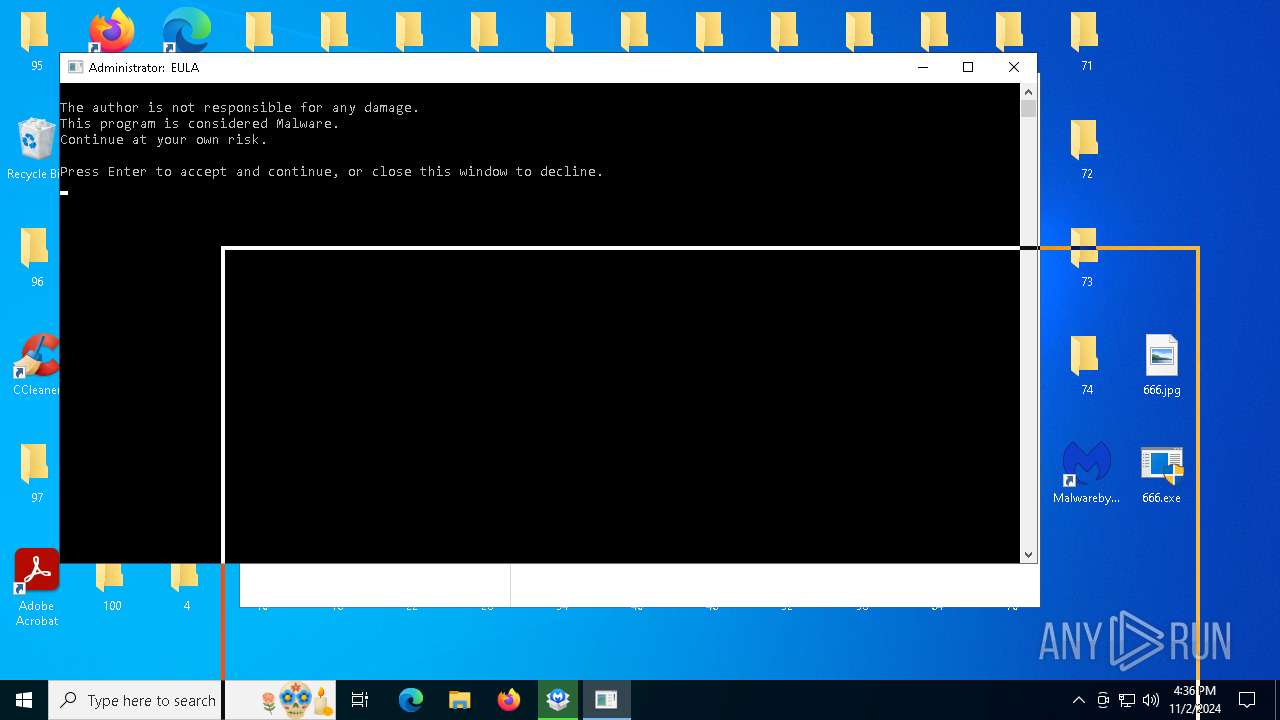
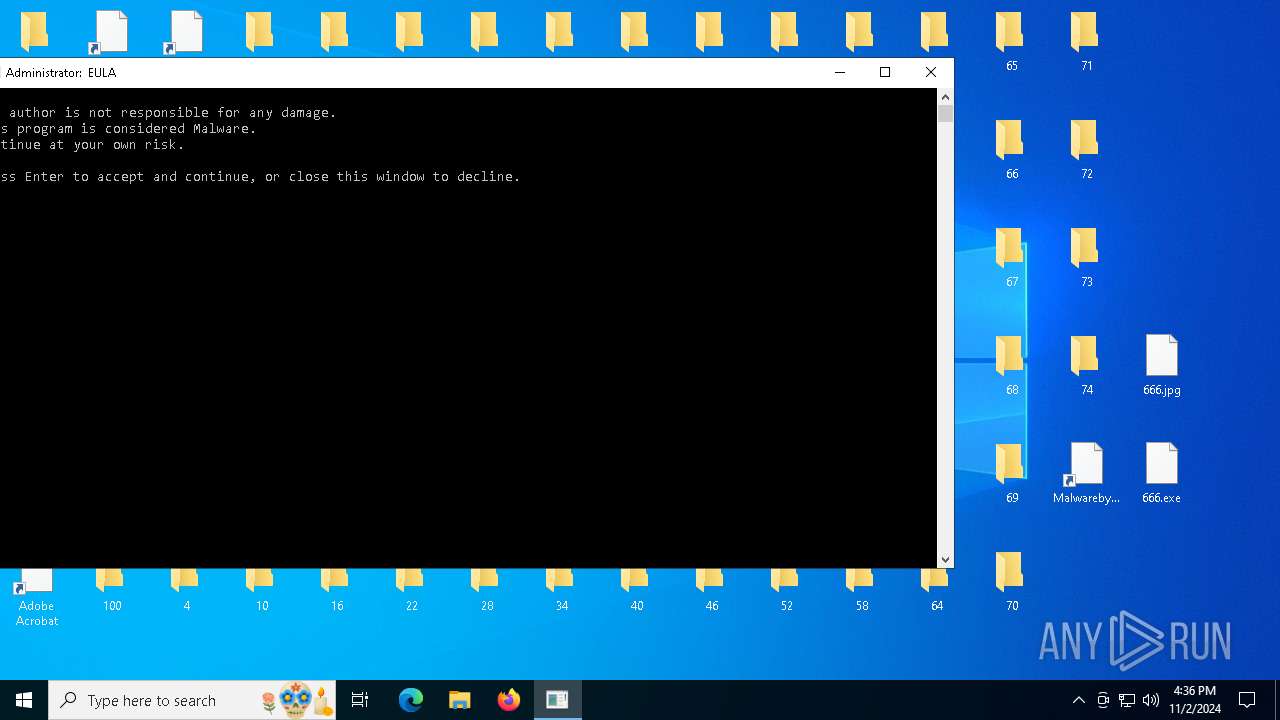
| File name: | 666.exe |
| Full analysis: | https://app.any.run/tasks/34f7b154-1c23-4ebd-bcbd-530f2a92498a |
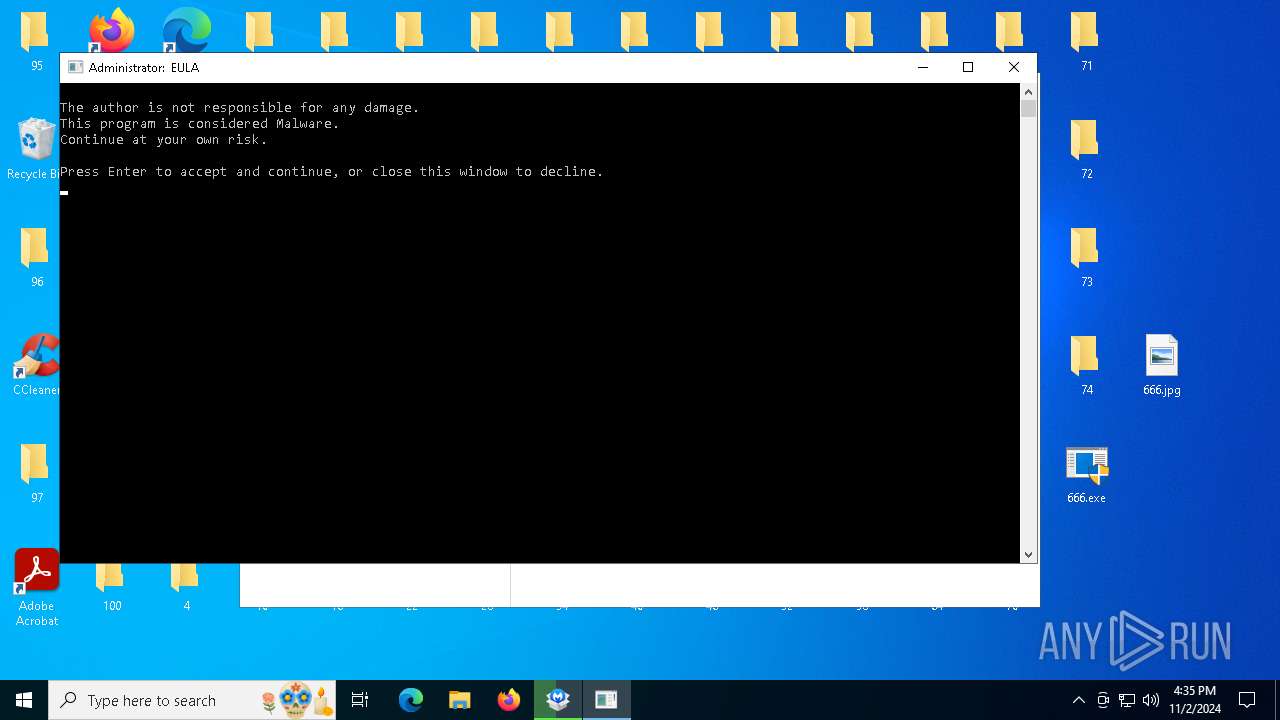
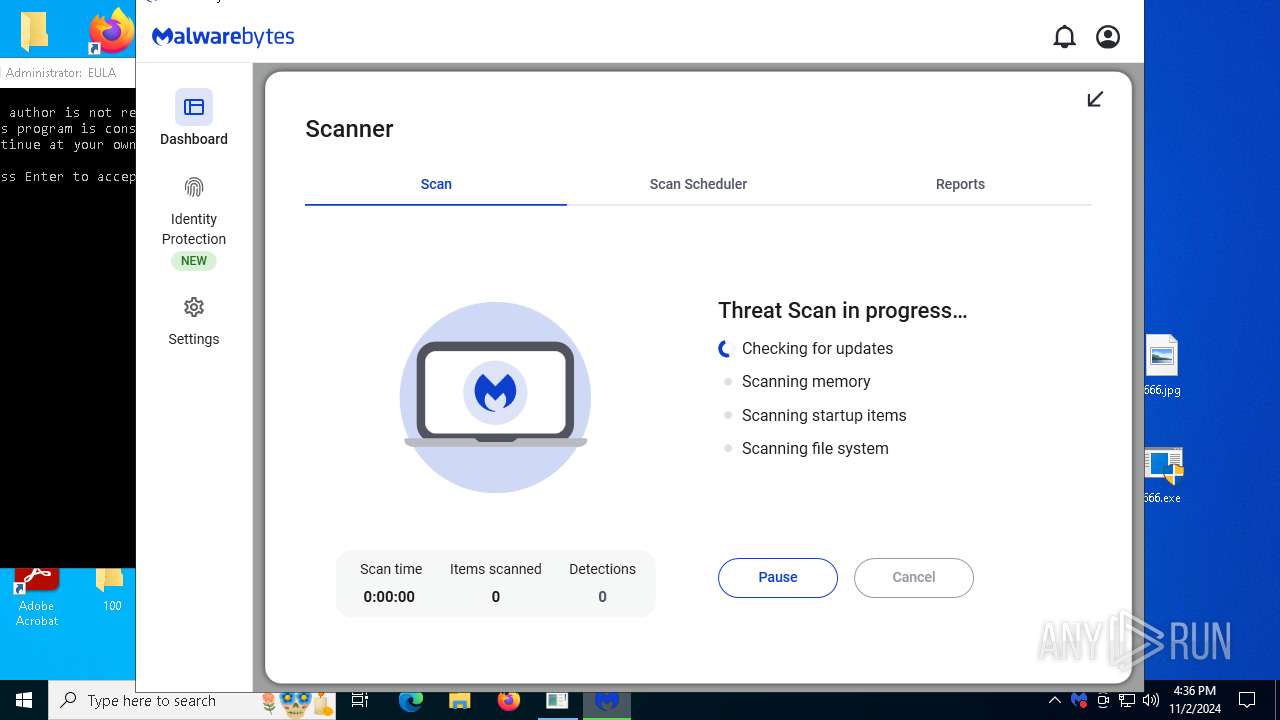
| Verdict: | Malicious activity |
| Analysis date: | November 02, 2024, 16:32:40 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
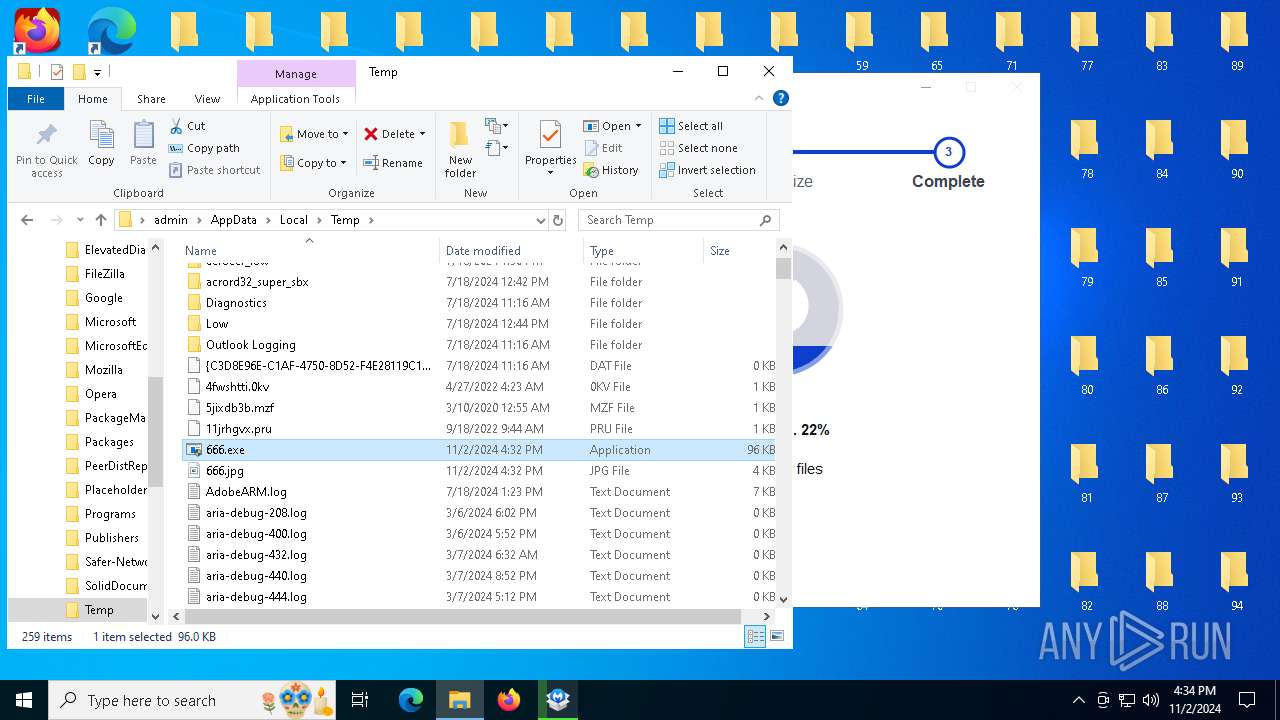
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (console) Intel 80386, for MS Windows, 5 sections |
| MD5: | E8335C96A6D84AE303D2908E79EBA24B |
| SHA1: | D2D1FFCDC96CC7AD4F6C13B36A10B11A512EC77A |
| SHA256: | 60352F191D73298DA994108F5940C4811B1AFE7F7F9244367BE4F1EDE0E6C2D7 |
| SSDEEP: | 3072:rCYa+0Nu6vQAkQ5S7JmyxCbBKhiTbMoIL:YQLi8NiTbXk |
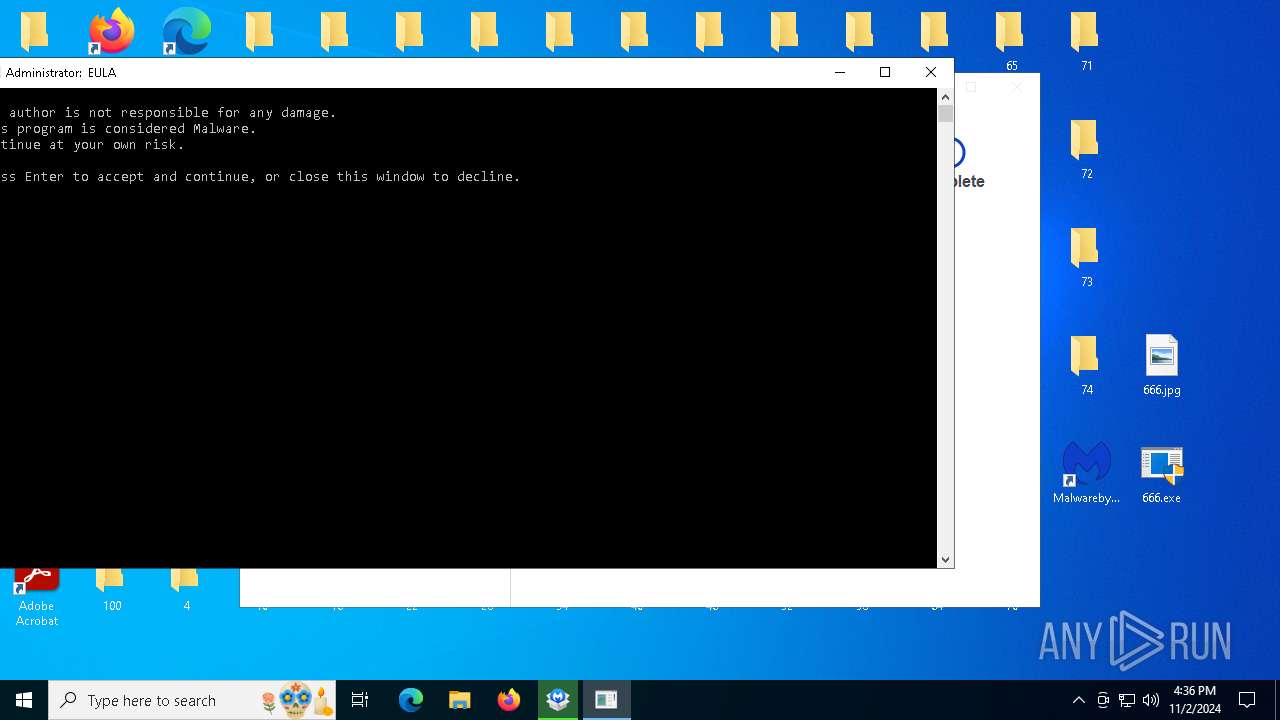
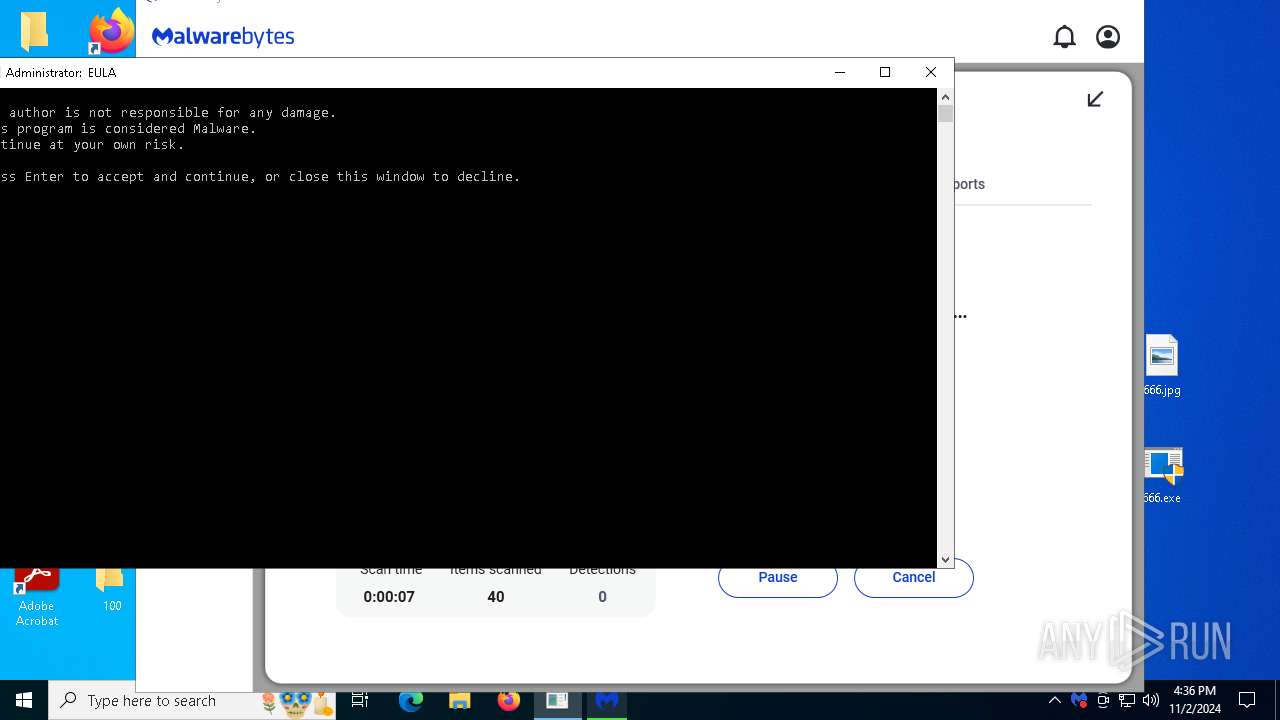
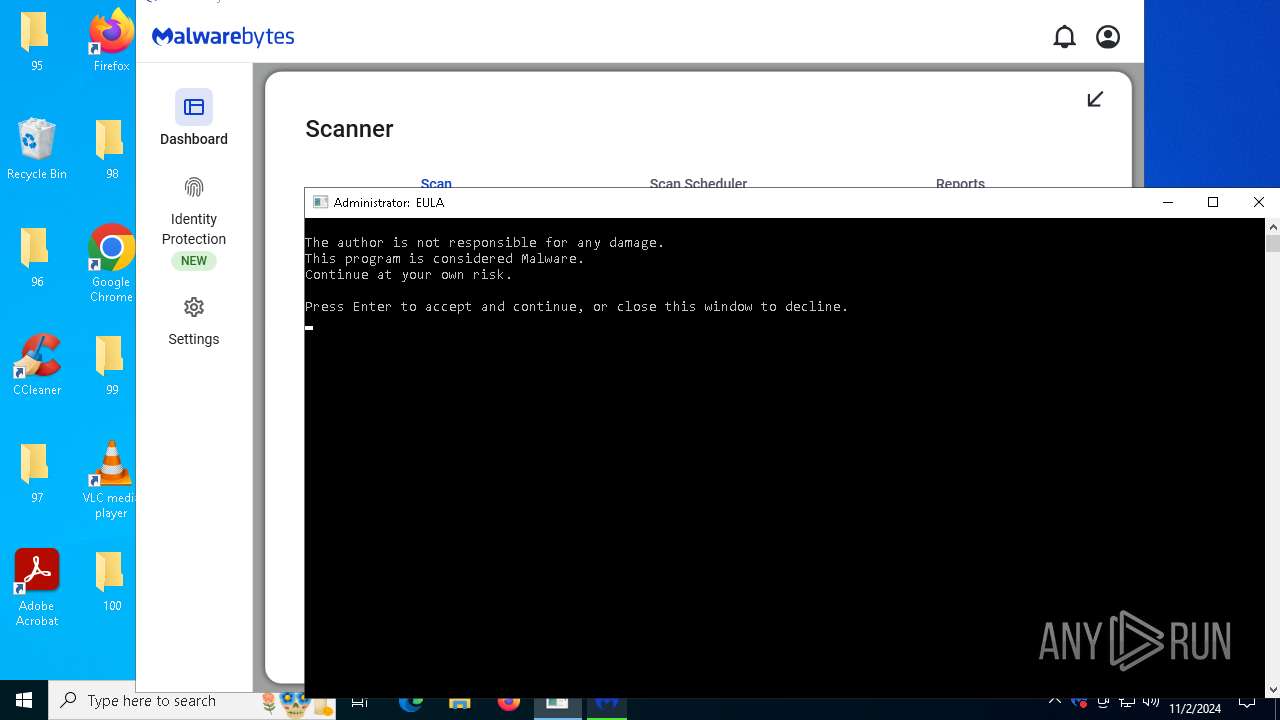
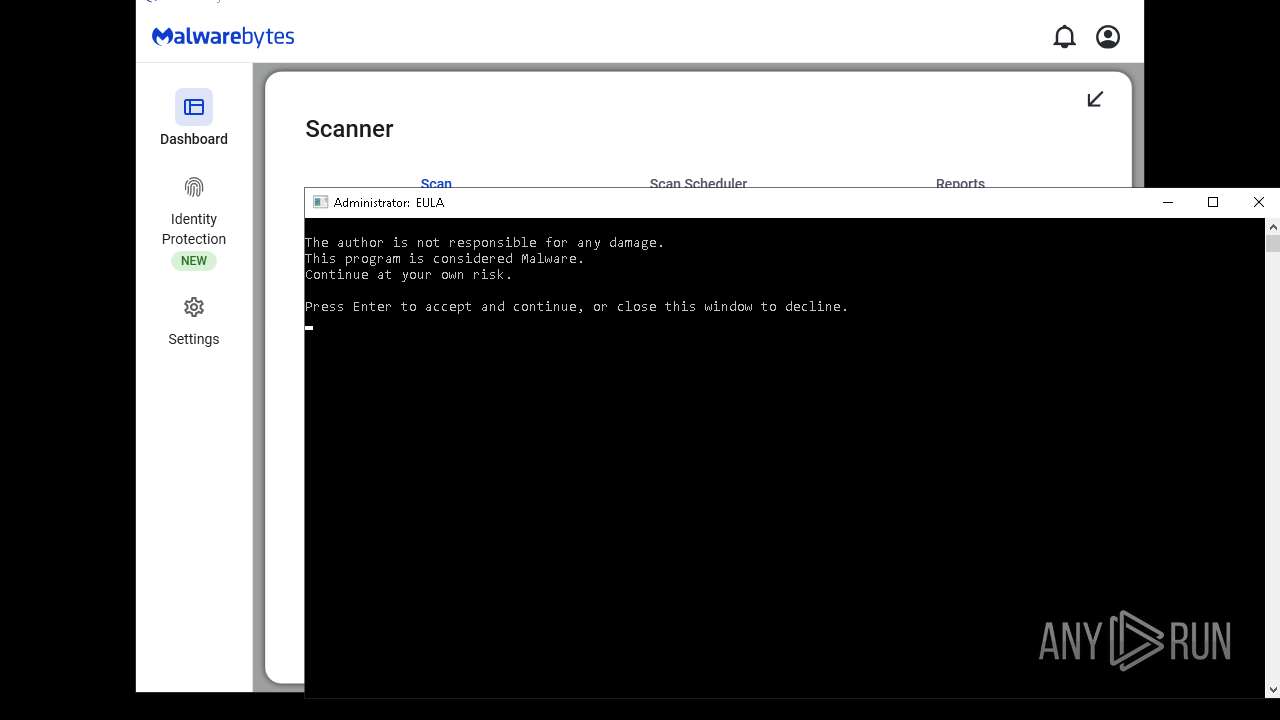
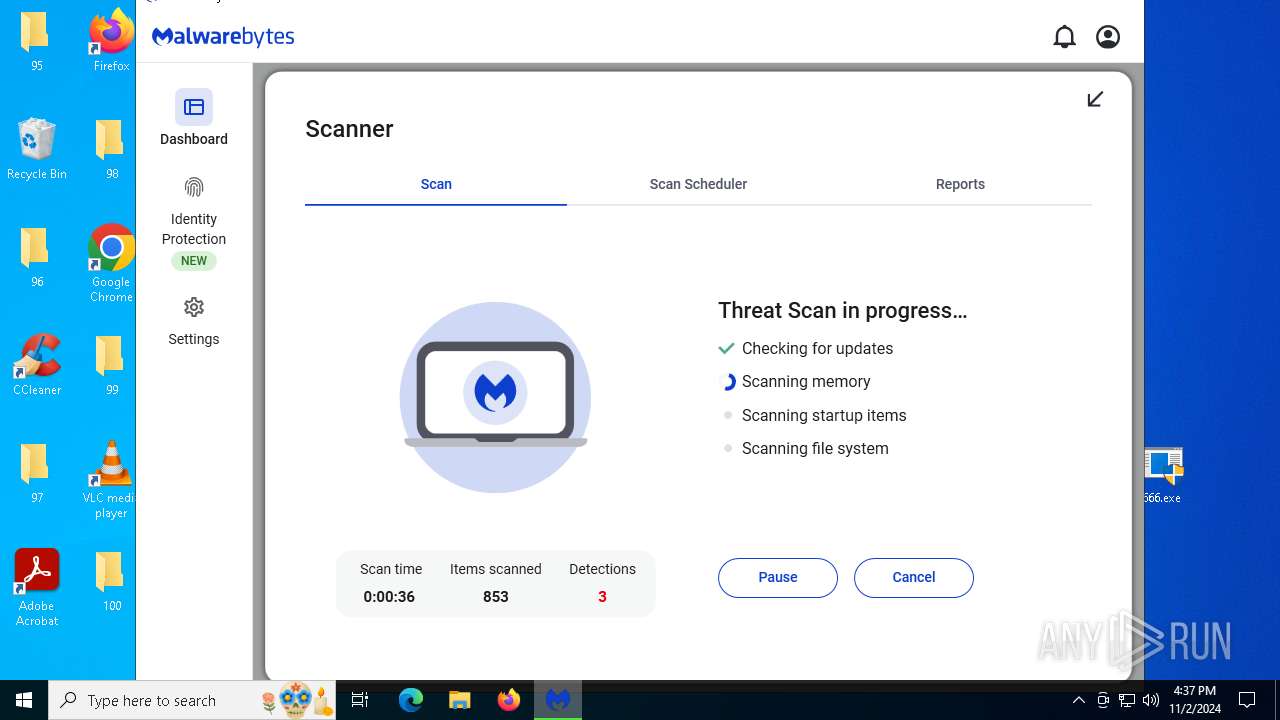
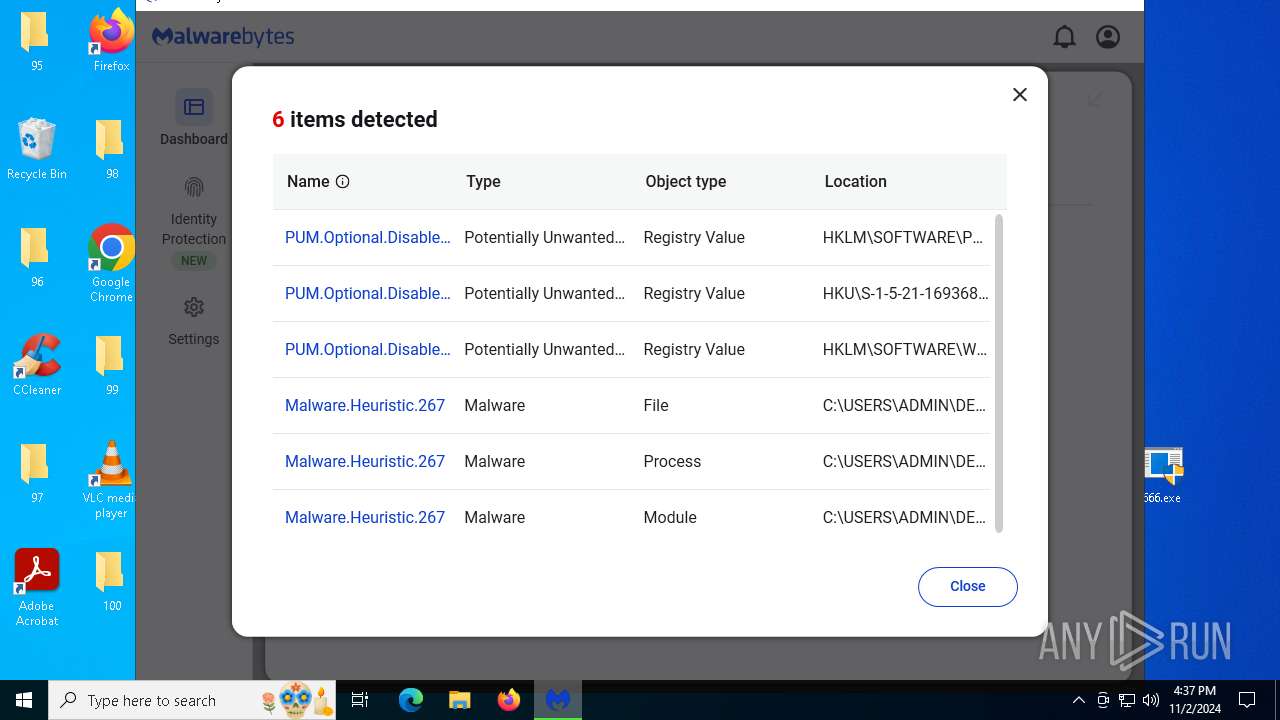
MALICIOUS
Starts NET.EXE to view/add/change user profiles
- cmd.exe (PID: 4348)
- net.exe (PID: 5356)
- net.exe (PID: 6184)
- net.exe (PID: 2312)
- net.exe (PID: 1204)
- cmd.exe (PID: 7456)
- net.exe (PID: 3936)
- net.exe (PID: 6316)
Starts NET.EXE to view/change users localgroup
- net.exe (PID: 6164)
- net.exe (PID: 5332)
- cmd.exe (PID: 4348)
SUSPICIOUS
Starts CMD.EXE for commands execution
- 666.exe (PID: 4868)
- 666.exe (PID: 7056)
Executing commands from a ".bat" file
- 666.exe (PID: 4868)
- 666.exe (PID: 7056)
Uses TASKKILL.EXE to kill Browsers
- cmd.exe (PID: 4348)
- cmd.exe (PID: 7456)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 4348)
- cmd.exe (PID: 7456)
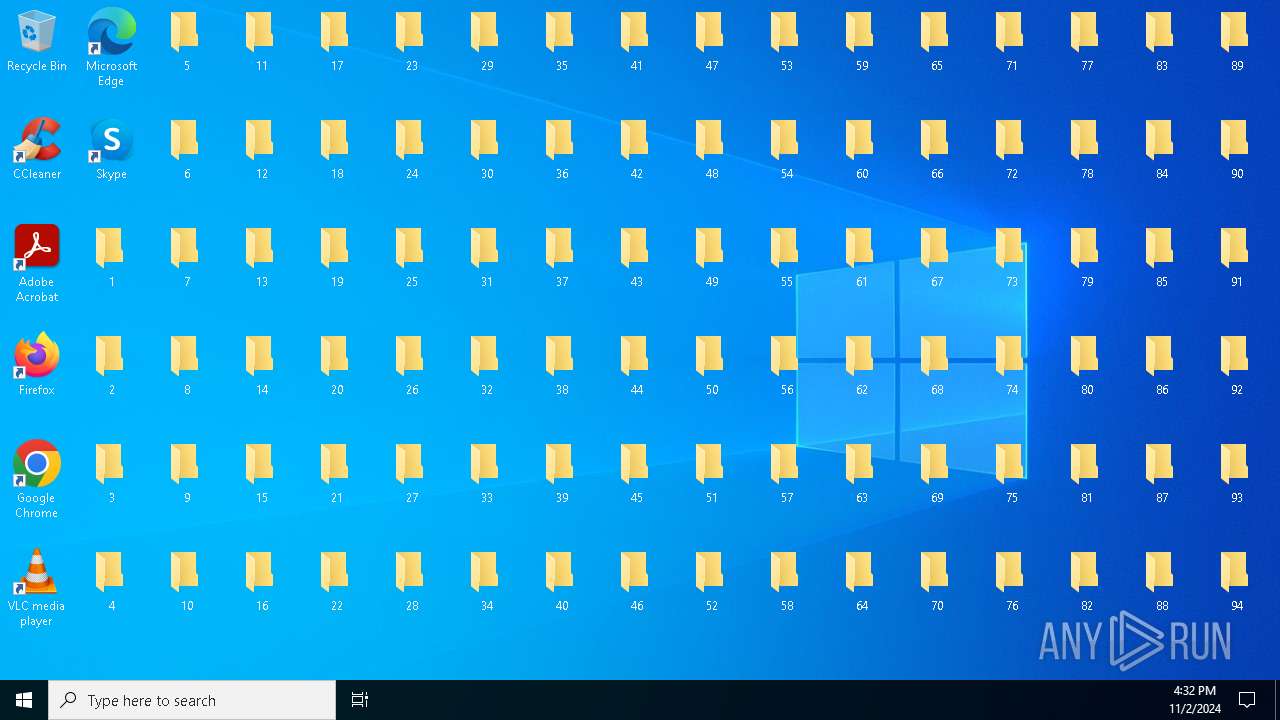
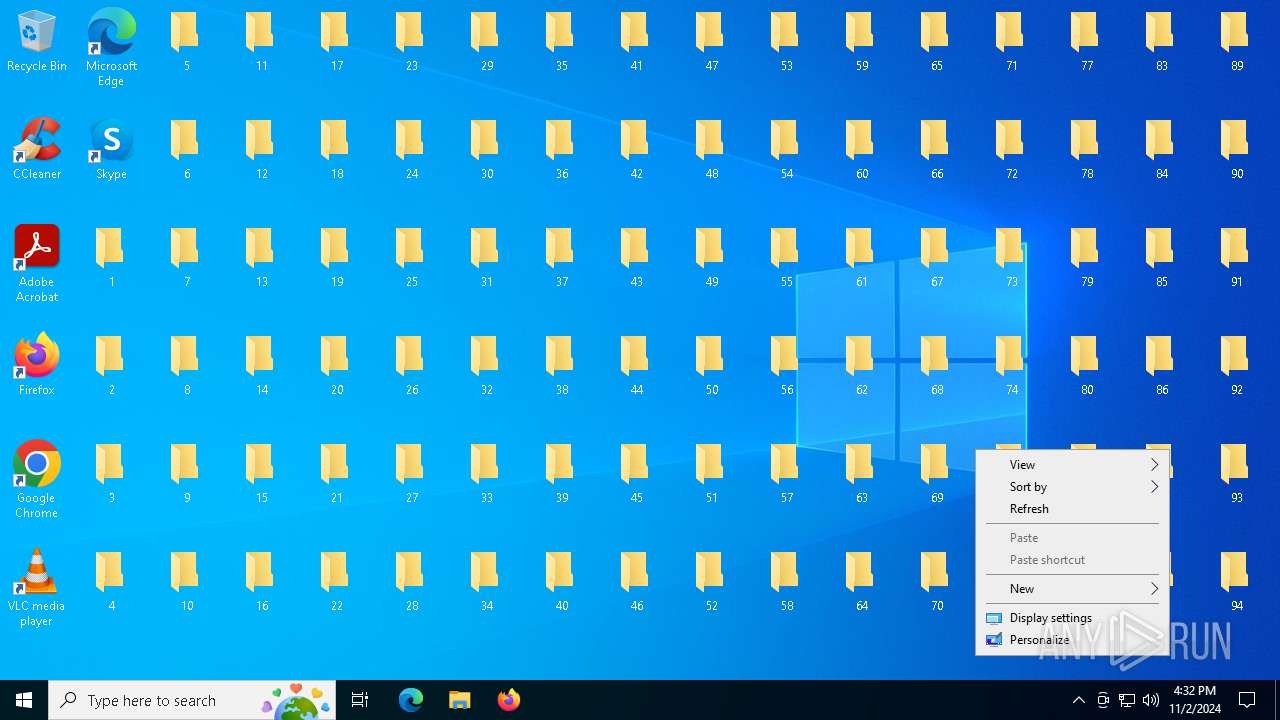
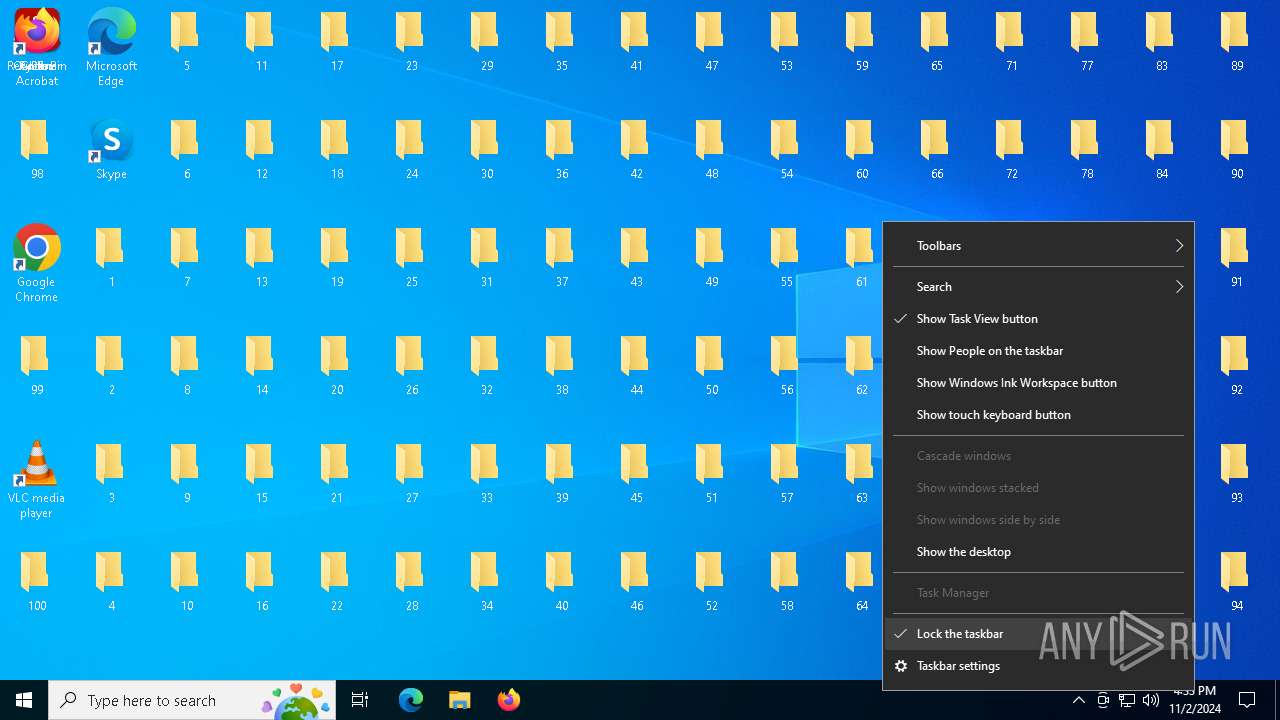
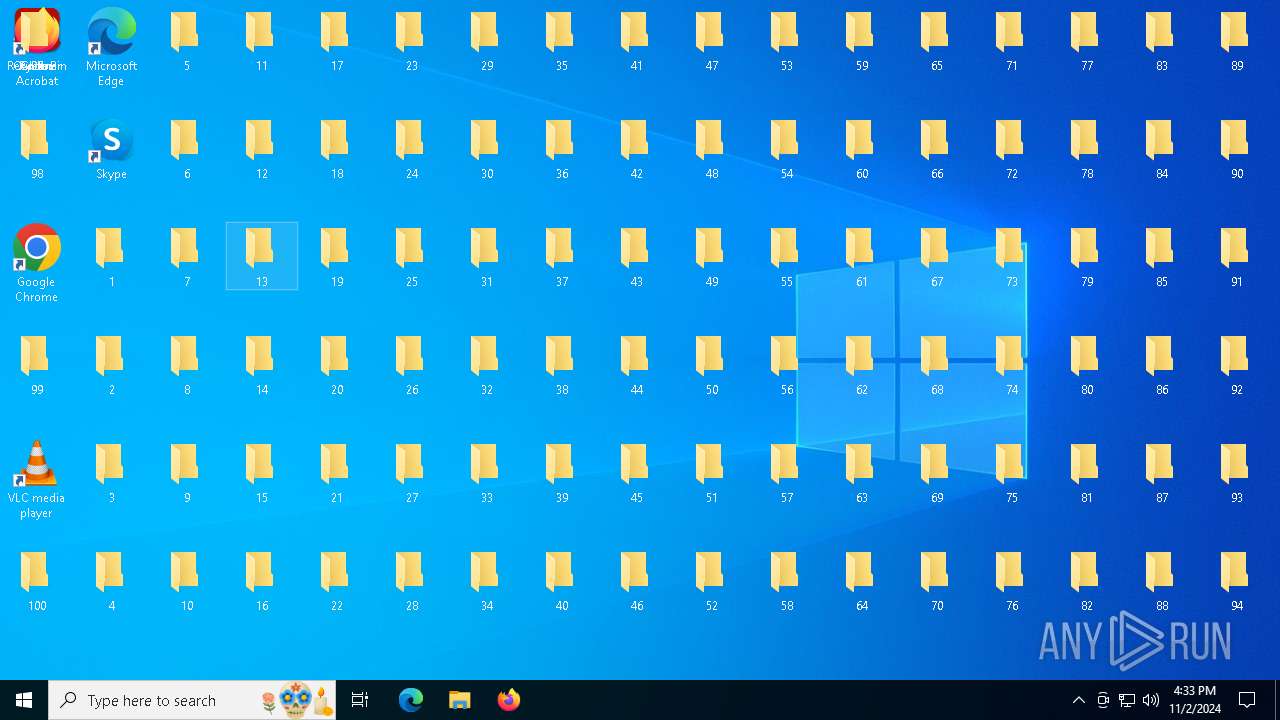
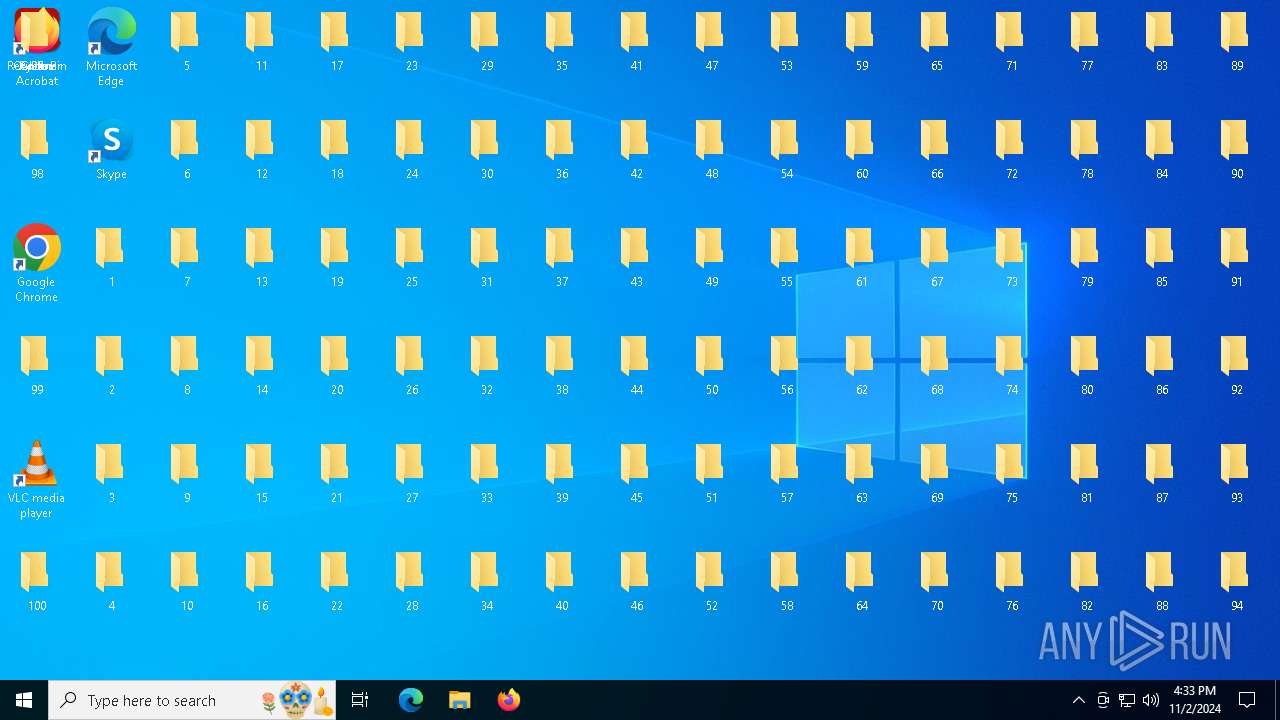
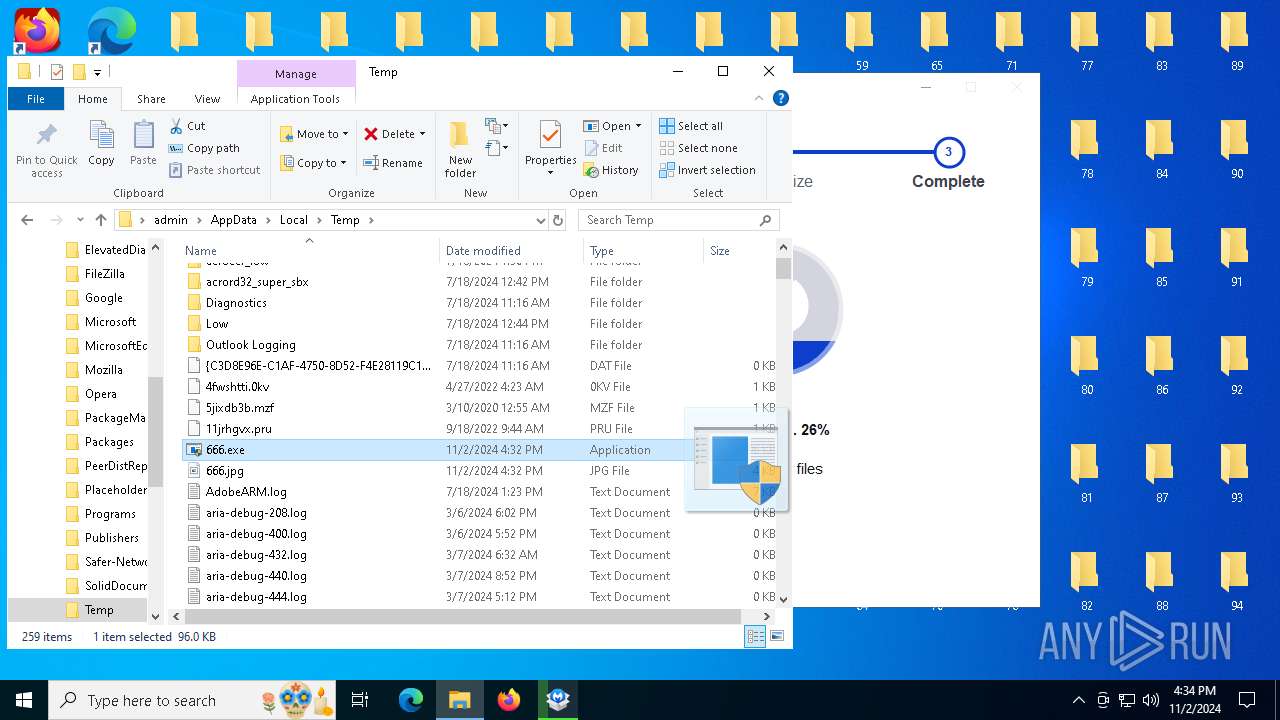
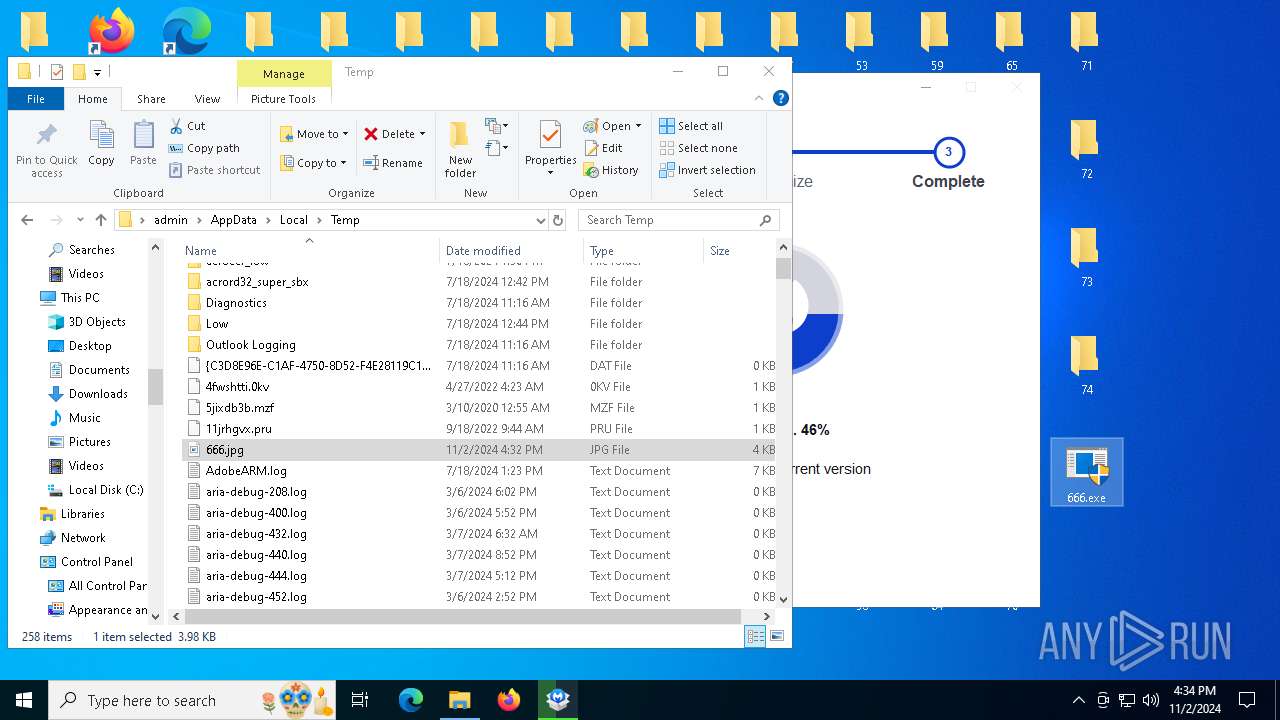
Changes the desktop background image
- reg.exe (PID: 5984)
Uses RUNDLL32.EXE to load library
- cmd.exe (PID: 4348)
- cmd.exe (PID: 7456)
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 4348)
- cmd.exe (PID: 7456)
Starts application with an unusual extension
- cmd.exe (PID: 4348)
- cmd.exe (PID: 7456)
Reads security settings of Internet Explorer
- StartMenuExperienceHost.exe (PID: 4704)
Reads the date of Windows installation
- StartMenuExperienceHost.exe (PID: 4704)
- SearchApp.exe (PID: 5532)
The process executes VB scripts
- cmd.exe (PID: 4348)
The process executes via Task Scheduler
- explorer.exe (PID: 6596)
- explorer.exe (PID: 6408)
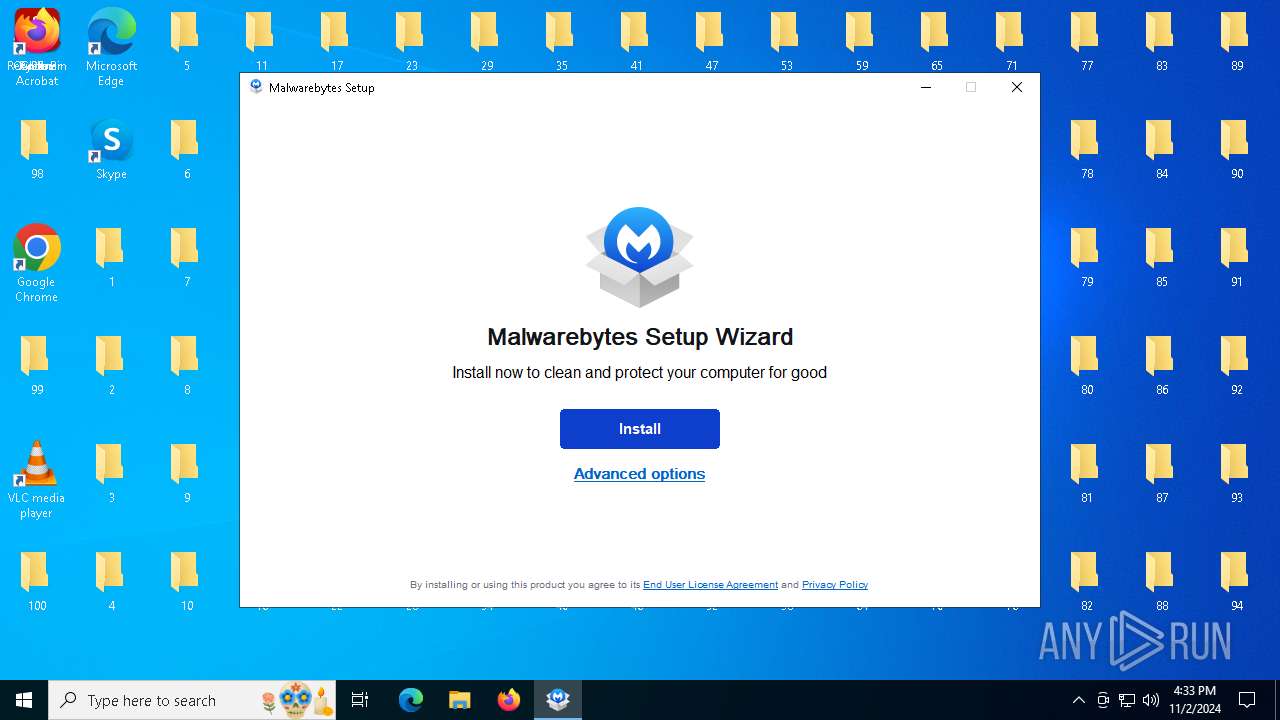
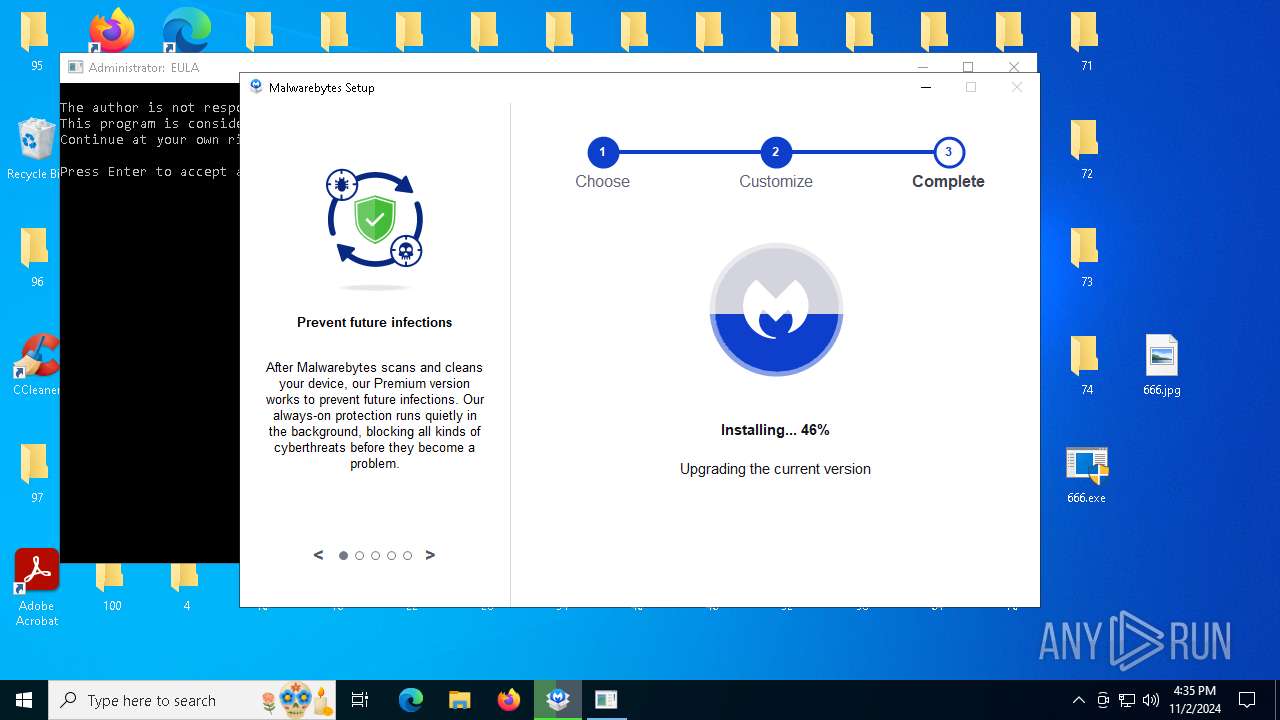
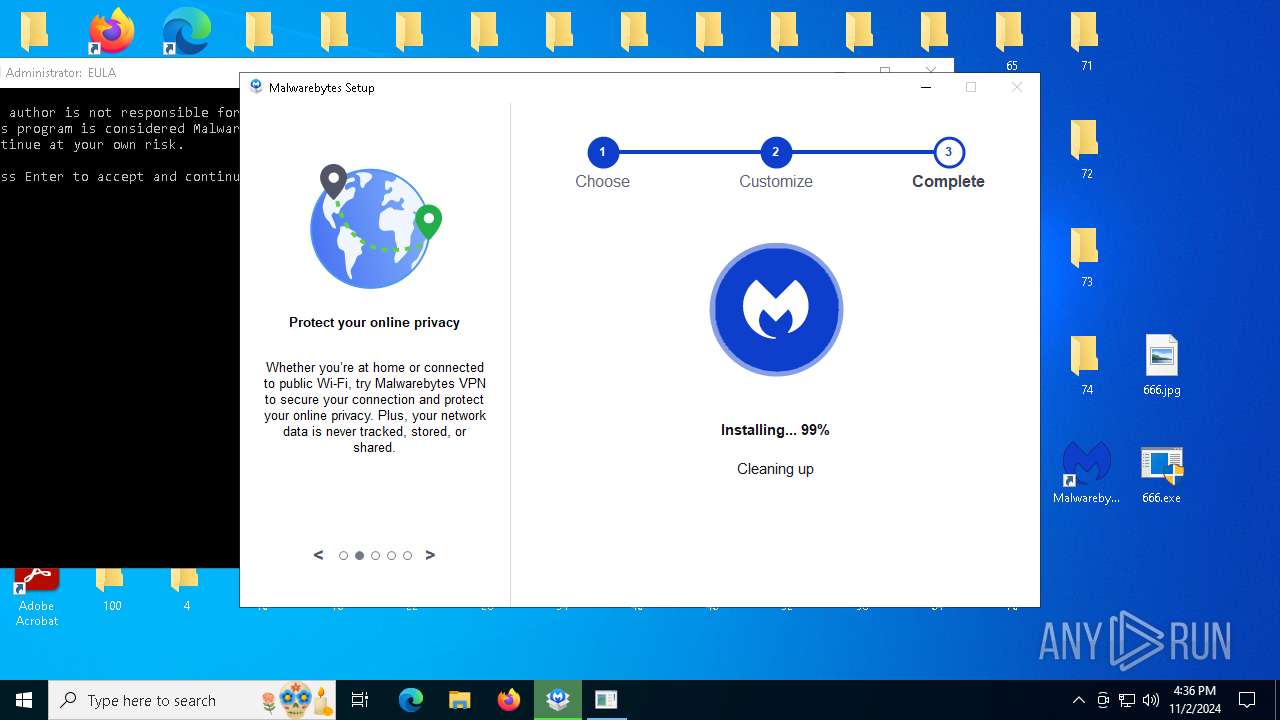
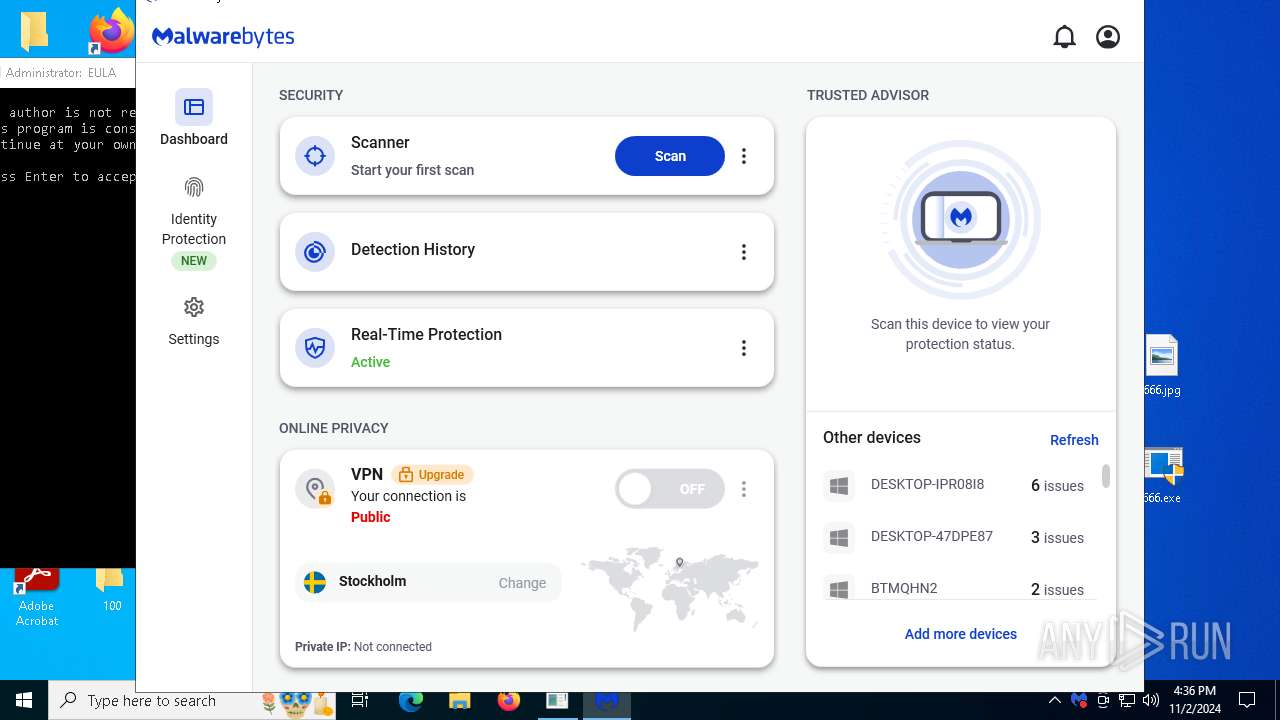
Drops 7-zip archiver for unpacking
- MBAMInstallerService.exe (PID: 6480)
Drops a system driver (possible attempt to evade defenses)
- MBAMInstallerService.exe (PID: 6480)
- MBVpnTunnelService.exe (PID: 8040)
- drvinst.exe (PID: 7196)
- MBAMService.exe (PID: 7620)
- MBAMService.exe (PID: 7148)
Executable content was dropped or overwritten
- MBSetup.exe (PID: 5388)
- MBAMInstallerService.exe (PID: 6480)
- explorer.exe (PID: 6596)
- drvinst.exe (PID: 7196)
- MBAMService.exe (PID: 7620)
- MBAMService.exe (PID: 7148)
- MBVpnTunnelService.exe (PID: 8040)
Process drops legitimate windows executable
- MBAMInstallerService.exe (PID: 6480)
- MBAMService.exe (PID: 7148)
Executes as Windows Service
- MBAMInstallerService.exe (PID: 6480)
- MBAMService.exe (PID: 7148)
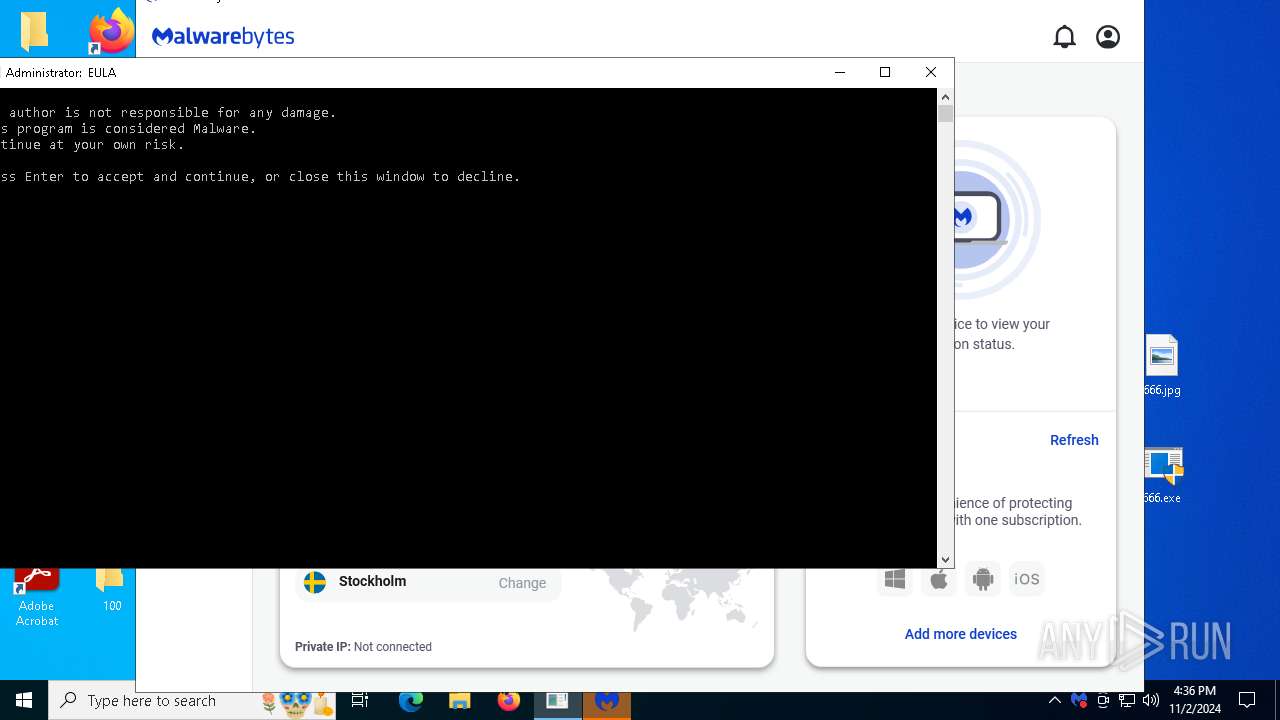
Application launched itself
- Malwarebytes.exe (PID: 1748)
The process drops C-runtime libraries
- MBAMInstallerService.exe (PID: 6480)
- MBAMService.exe (PID: 7148)
INFO
Checks supported languages
- 666.exe (PID: 4868)
- chcp.com (PID: 6216)
- TextInputHost.exe (PID: 4720)
- StartMenuExperienceHost.exe (PID: 4704)
- SearchApp.exe (PID: 5532)
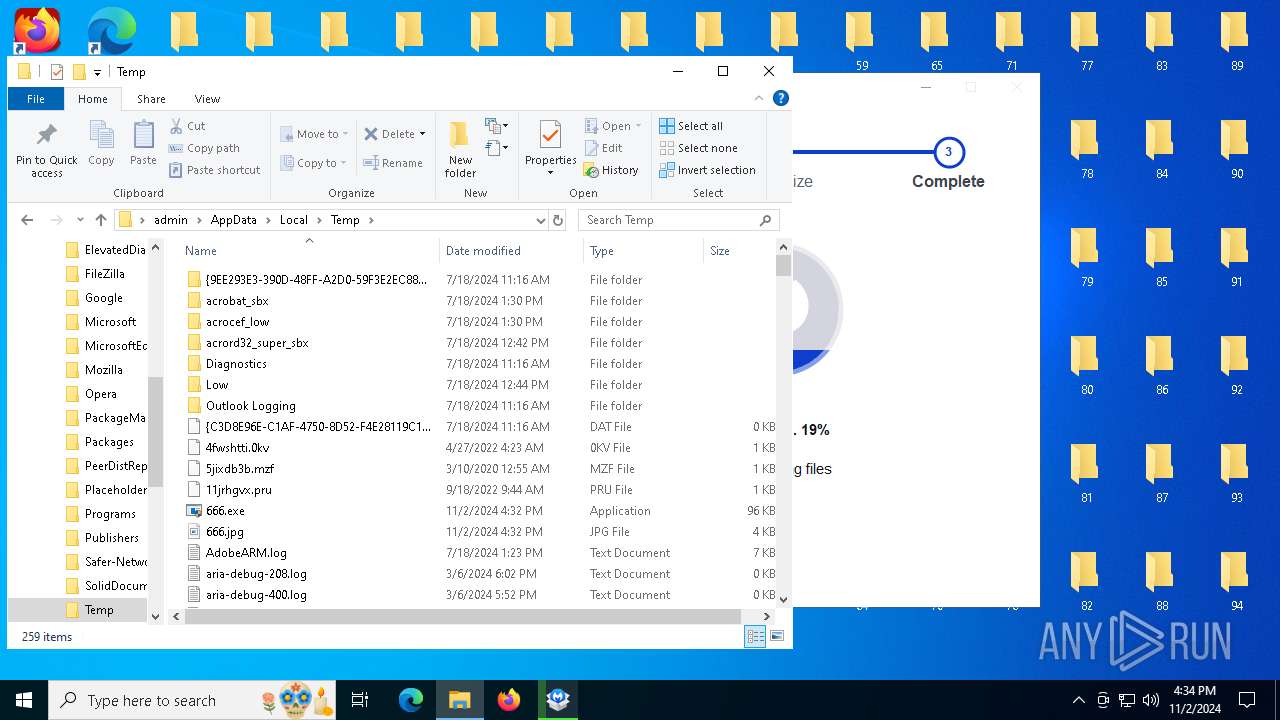
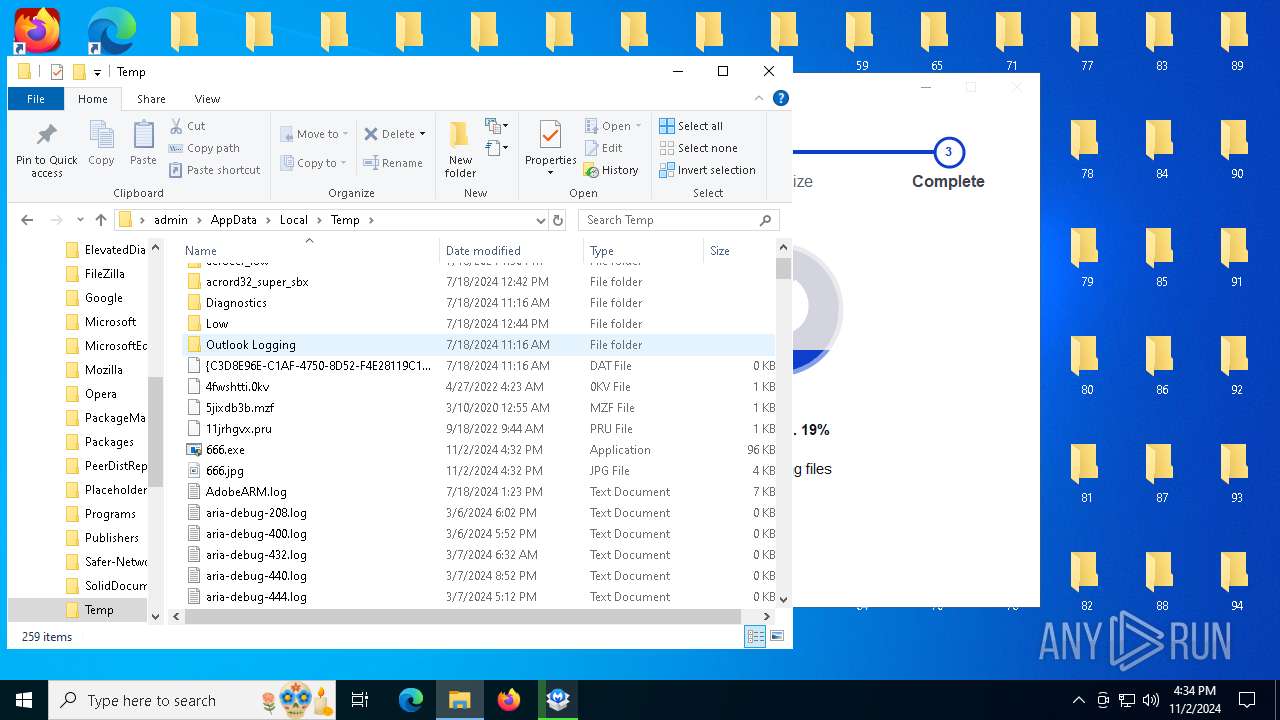
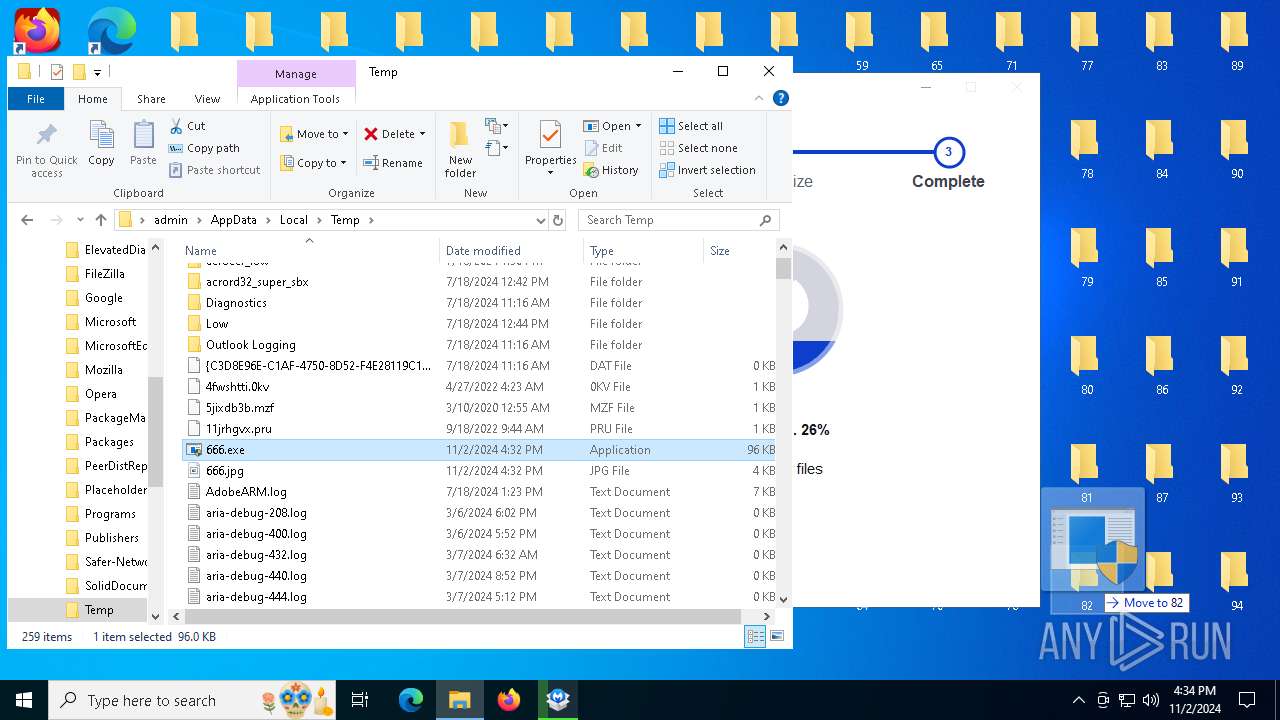
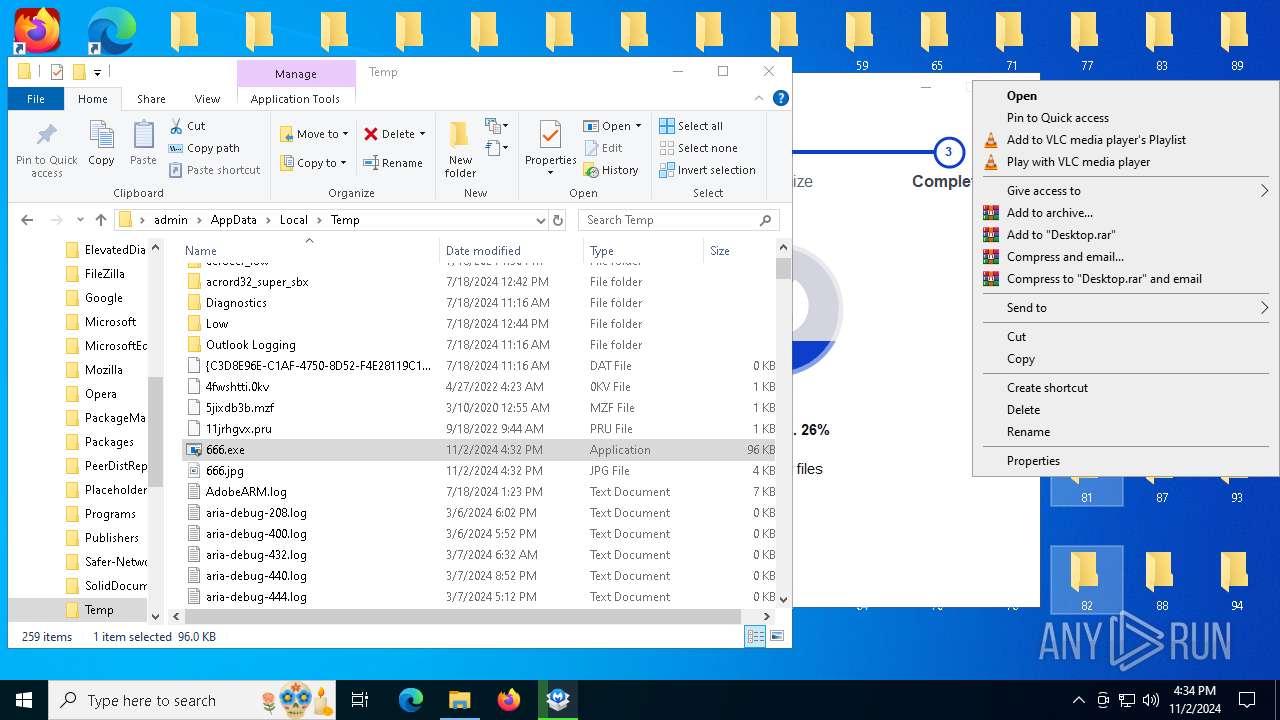
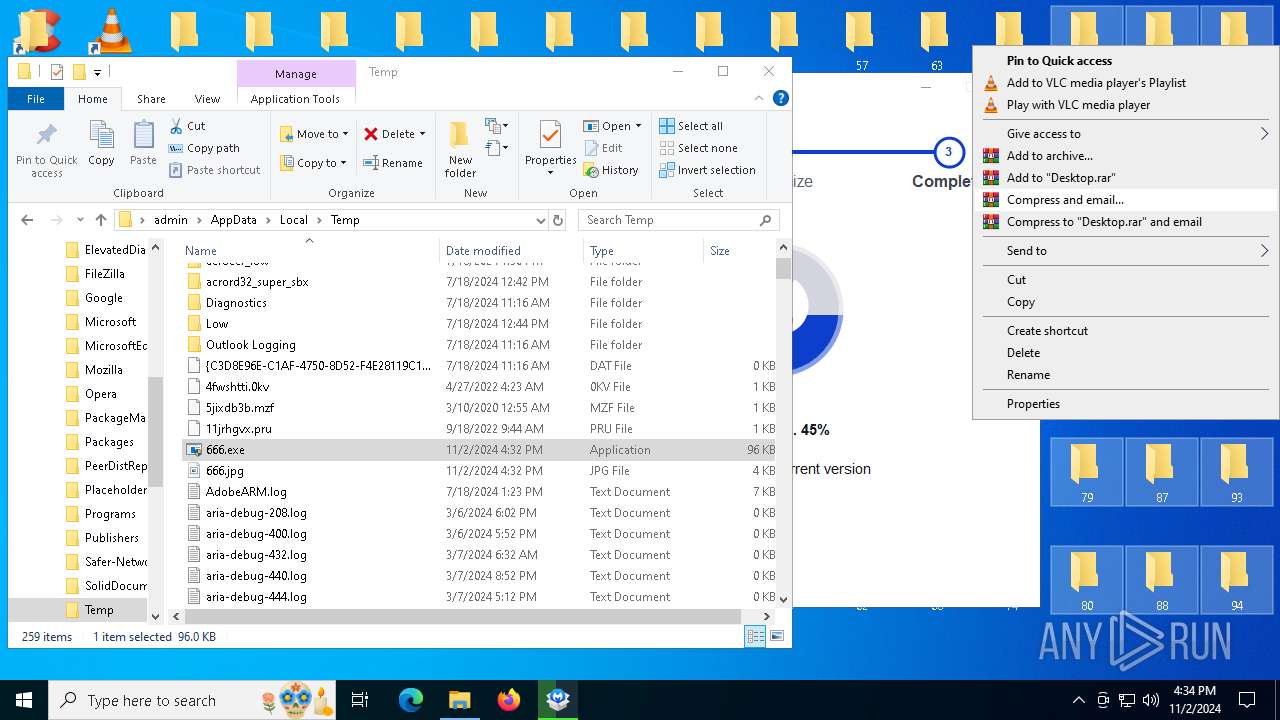
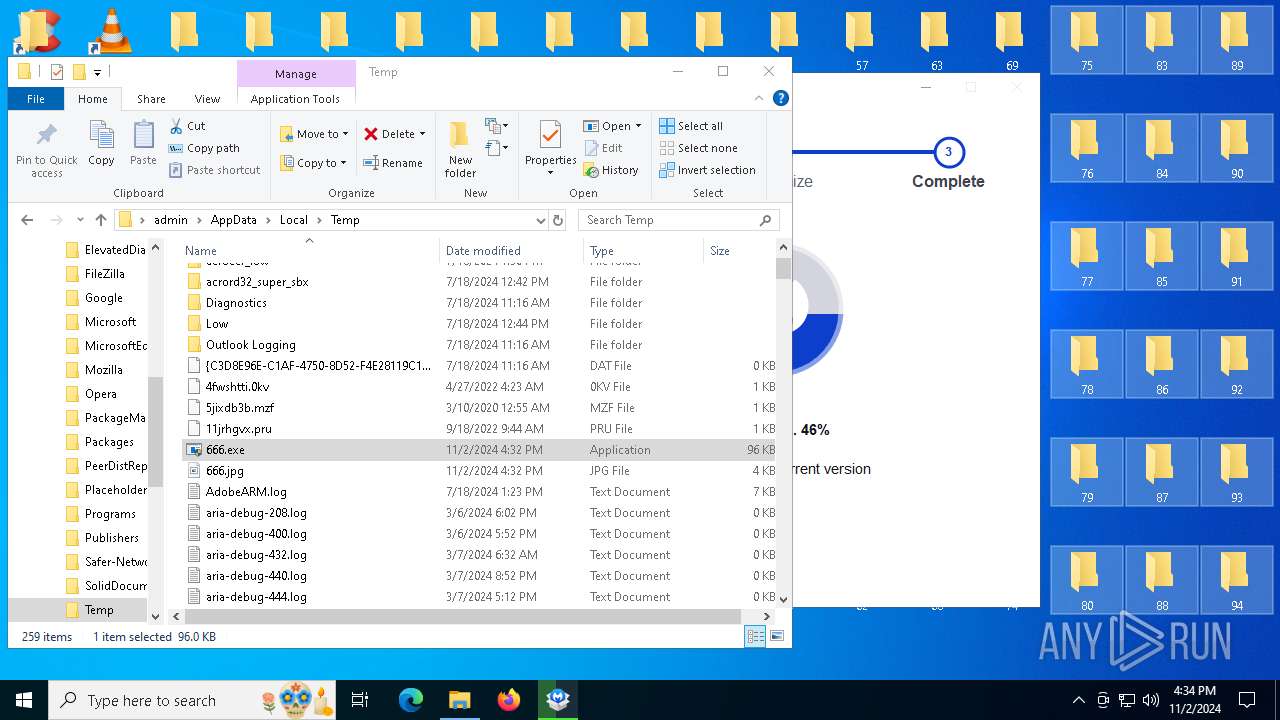
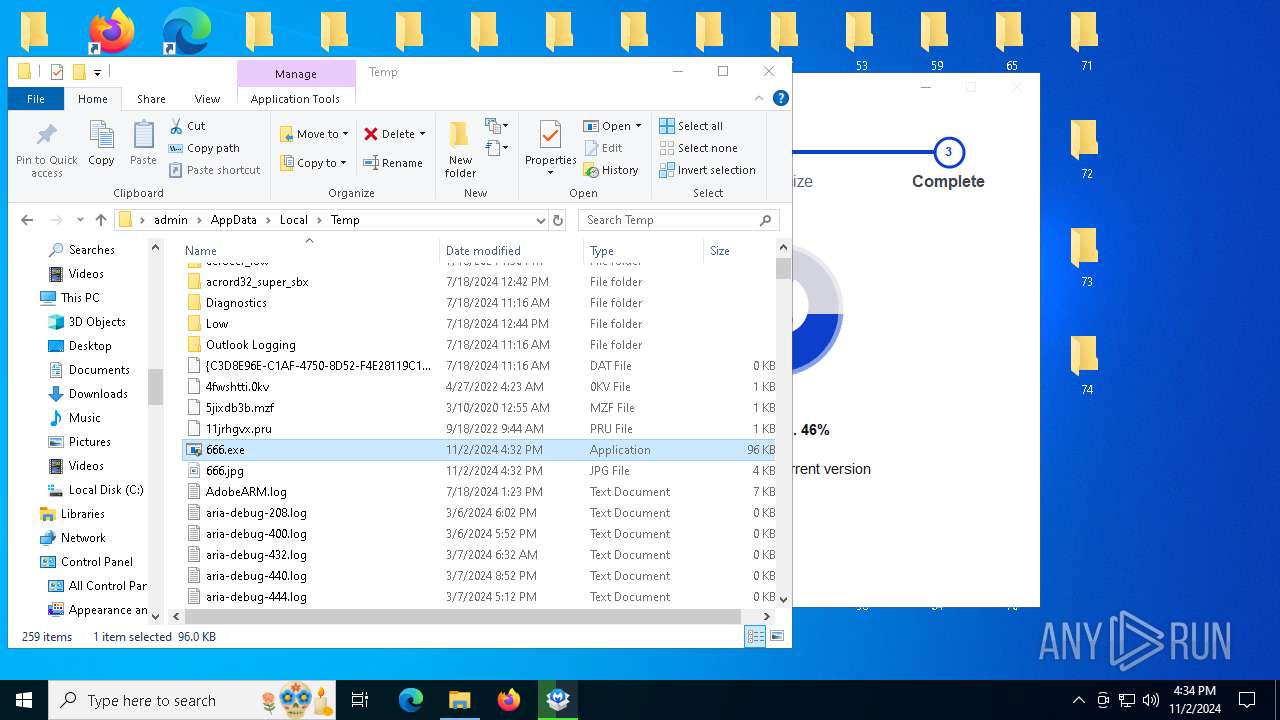
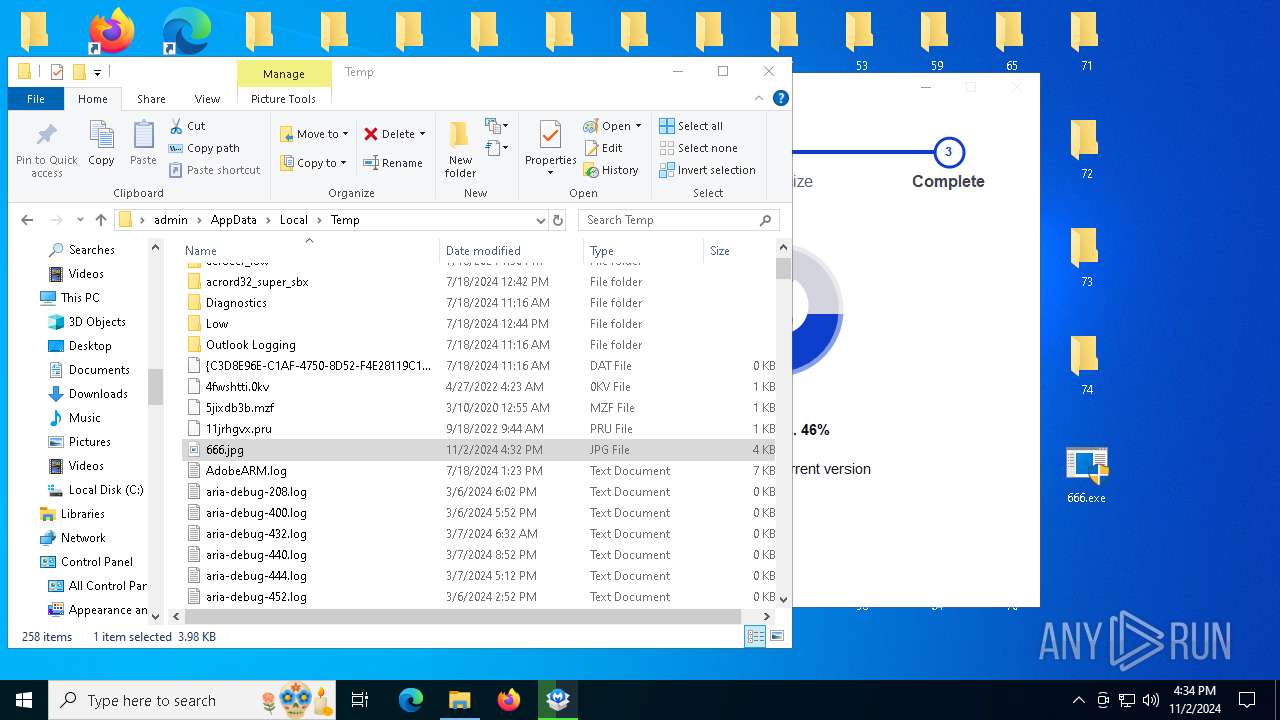
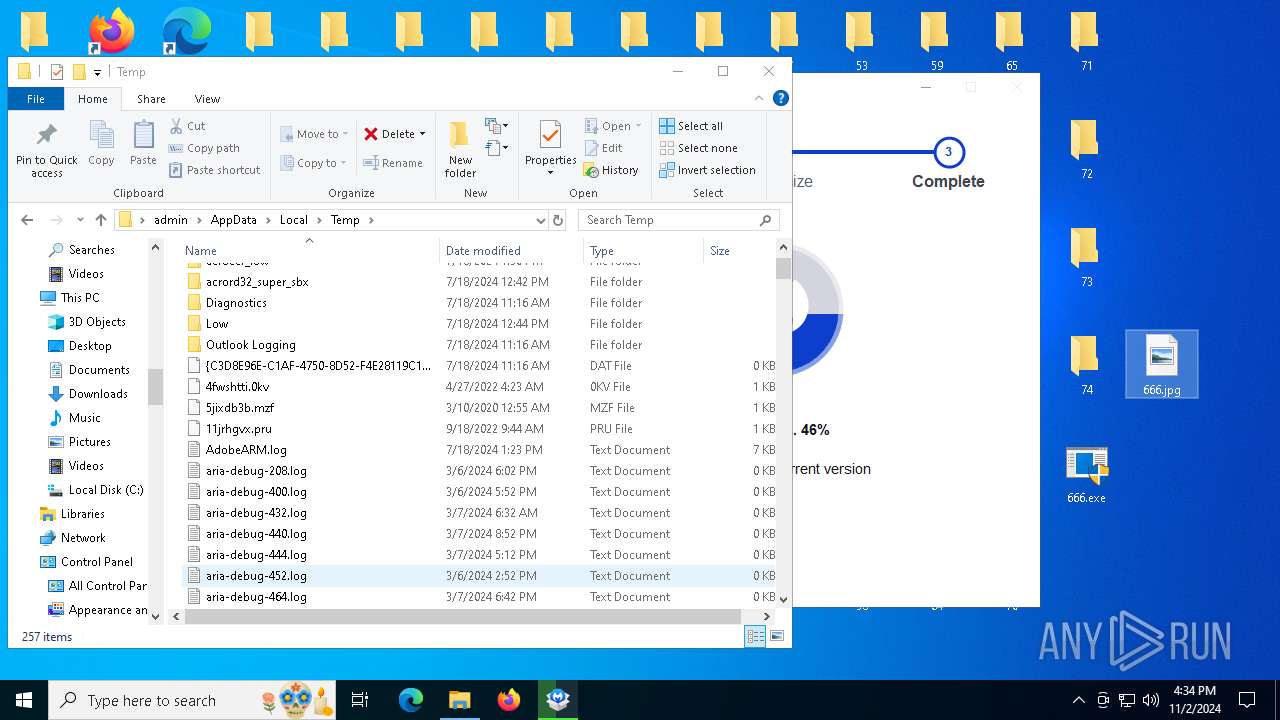
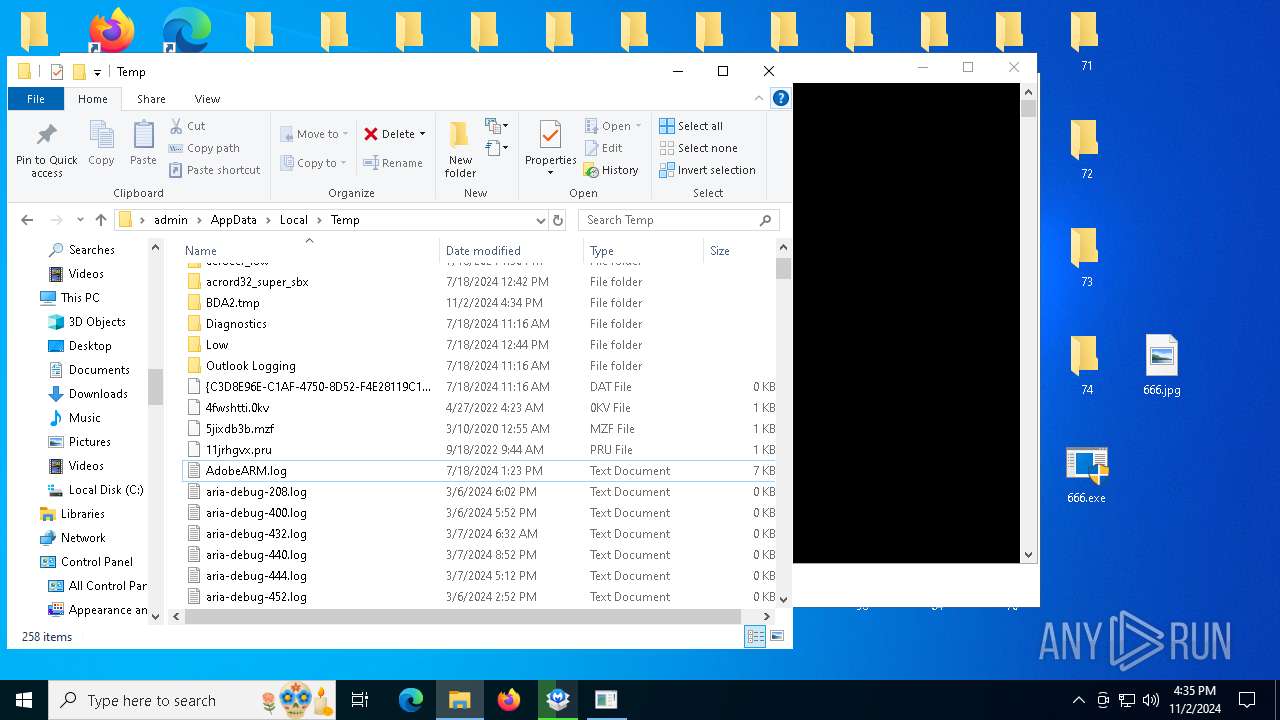
Create files in a temporary directory
- 666.exe (PID: 4868)
- cmd.exe (PID: 4348)
Changes the display of characters in the console
- cmd.exe (PID: 4348)
- cmd.exe (PID: 7456)
Reads security settings of Internet Explorer
- cscript.exe (PID: 300)
- explorer.exe (PID: 6596)
Creates files or folders in the user directory
- explorer.exe (PID: 6596)
Reads the computer name
- TextInputHost.exe (PID: 4720)
- StartMenuExperienceHost.exe (PID: 4704)
- SearchApp.exe (PID: 5532)
Sends debugging messages
- StartMenuExperienceHost.exe (PID: 4704)
Process checks computer location settings
- StartMenuExperienceHost.exe (PID: 4704)
- SearchApp.exe (PID: 5532)
Checks proxy server information
- SearchApp.exe (PID: 5532)
- explorer.exe (PID: 6596)
Reads the machine GUID from the registry
- SearchApp.exe (PID: 5532)
Reads the software policy settings
- SearchApp.exe (PID: 5532)
Executable content was dropped or overwritten
- chrome.exe (PID: 1376)
- chrome.exe (PID: 6632)
Application launched itself
- chrome.exe (PID: 6632)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (41) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (36.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.6) |
| .exe | | | Win32 Executable (generic) (5.9) |
| .exe | | | Win16/32 Executable Delphi generic (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2019:07:30 08:52:45+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 2.5 |
| CodeSize: | 70656 |
| InitializedDataSize: | 26624 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1000 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows command line |
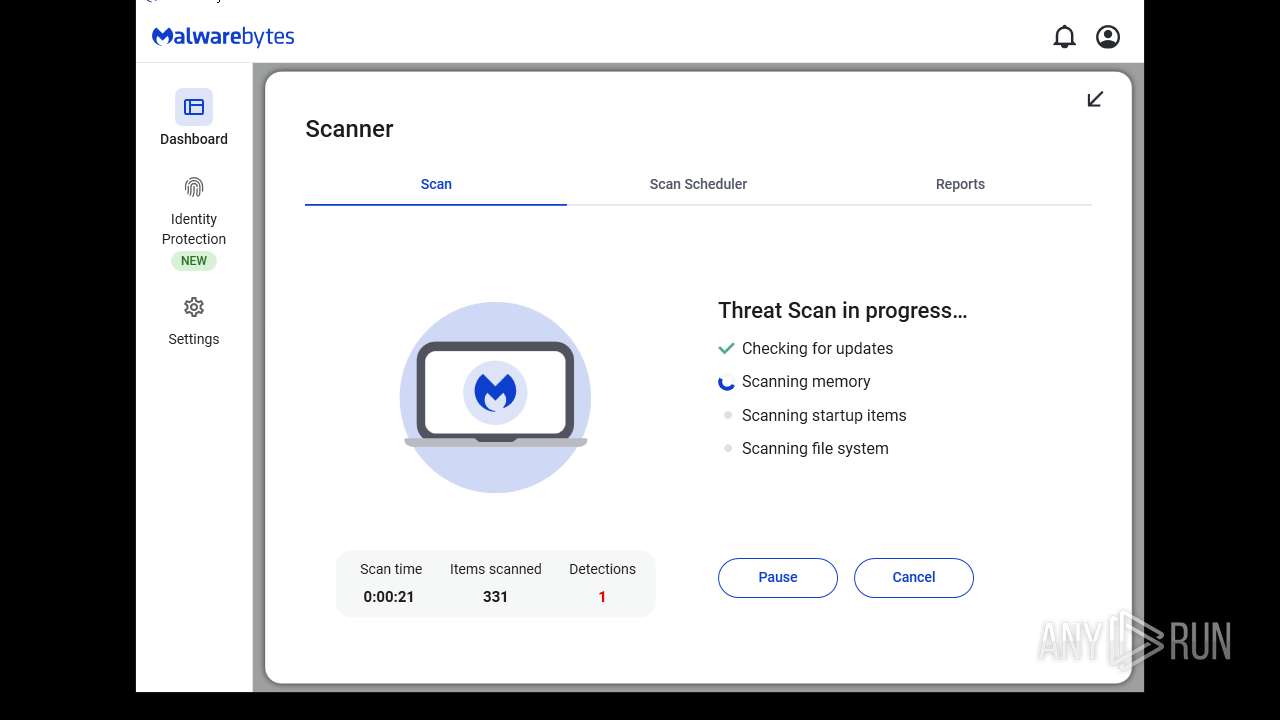
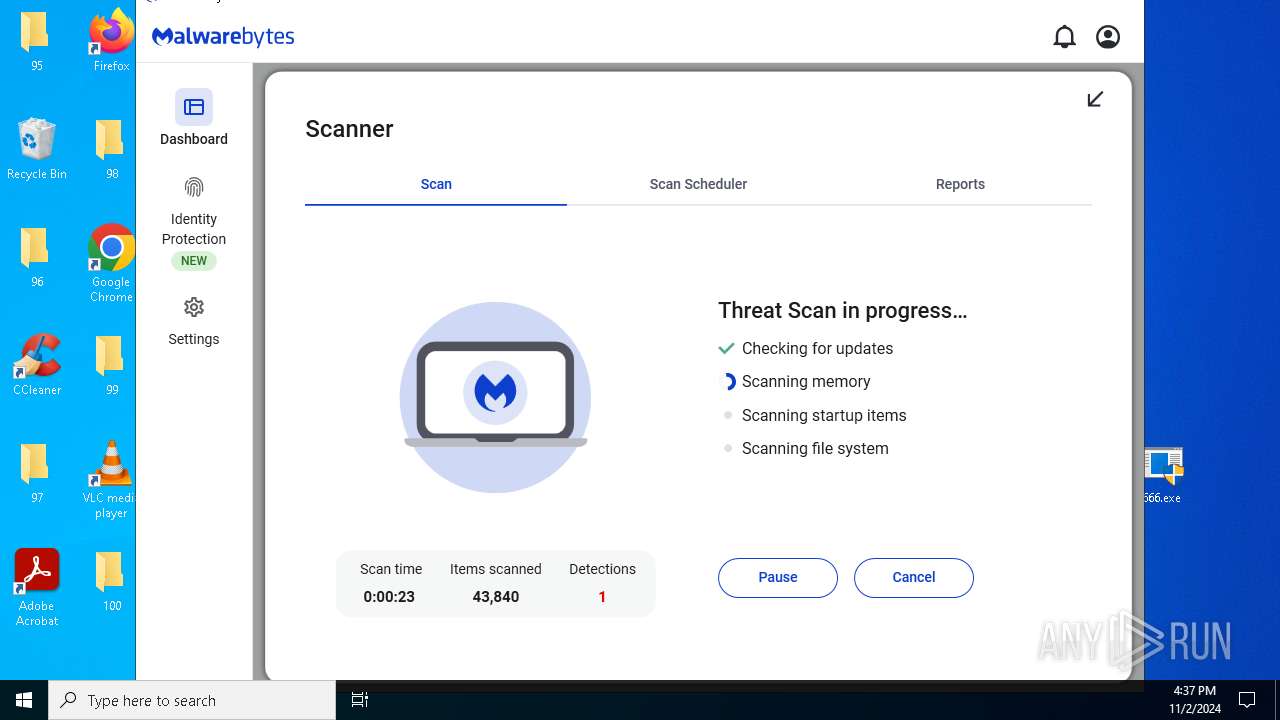
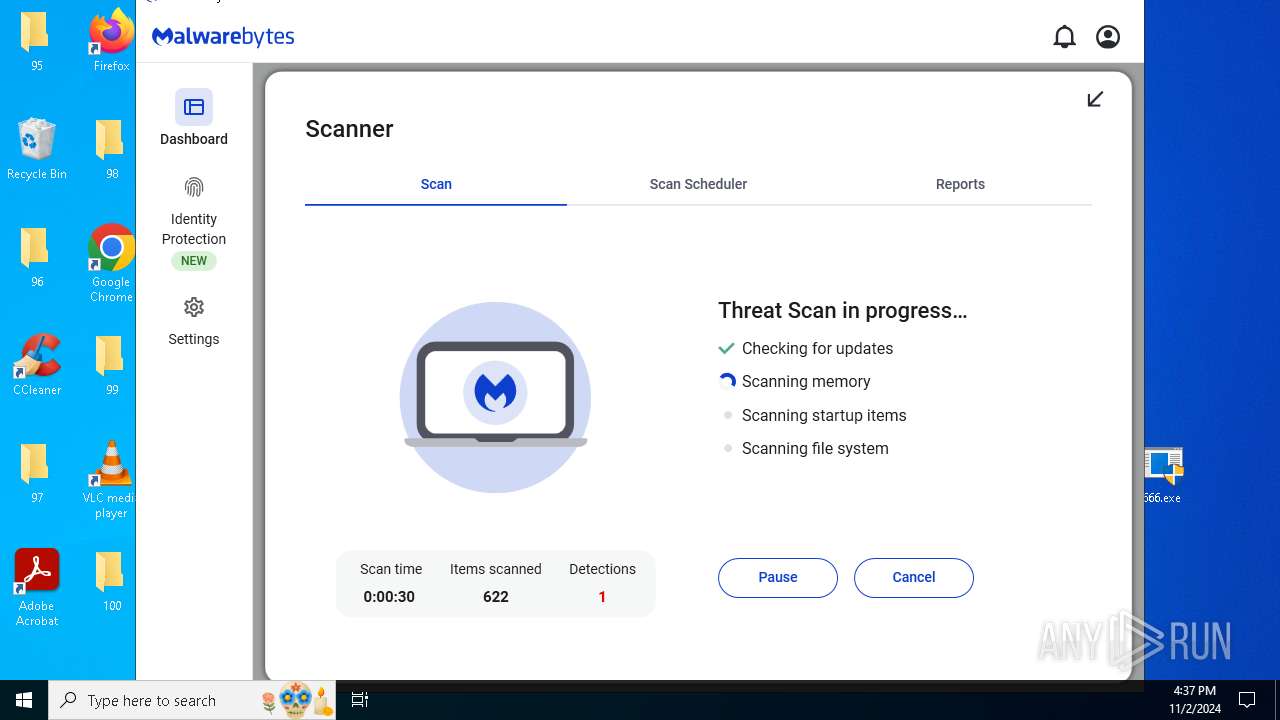
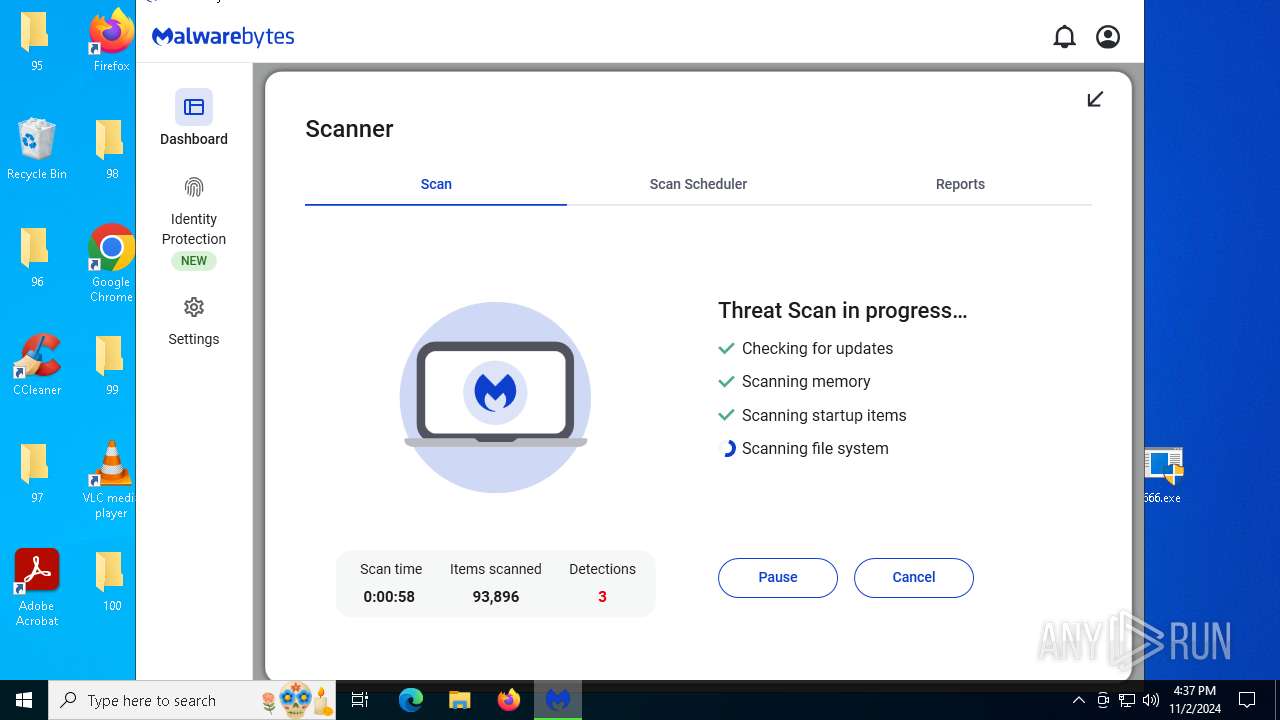
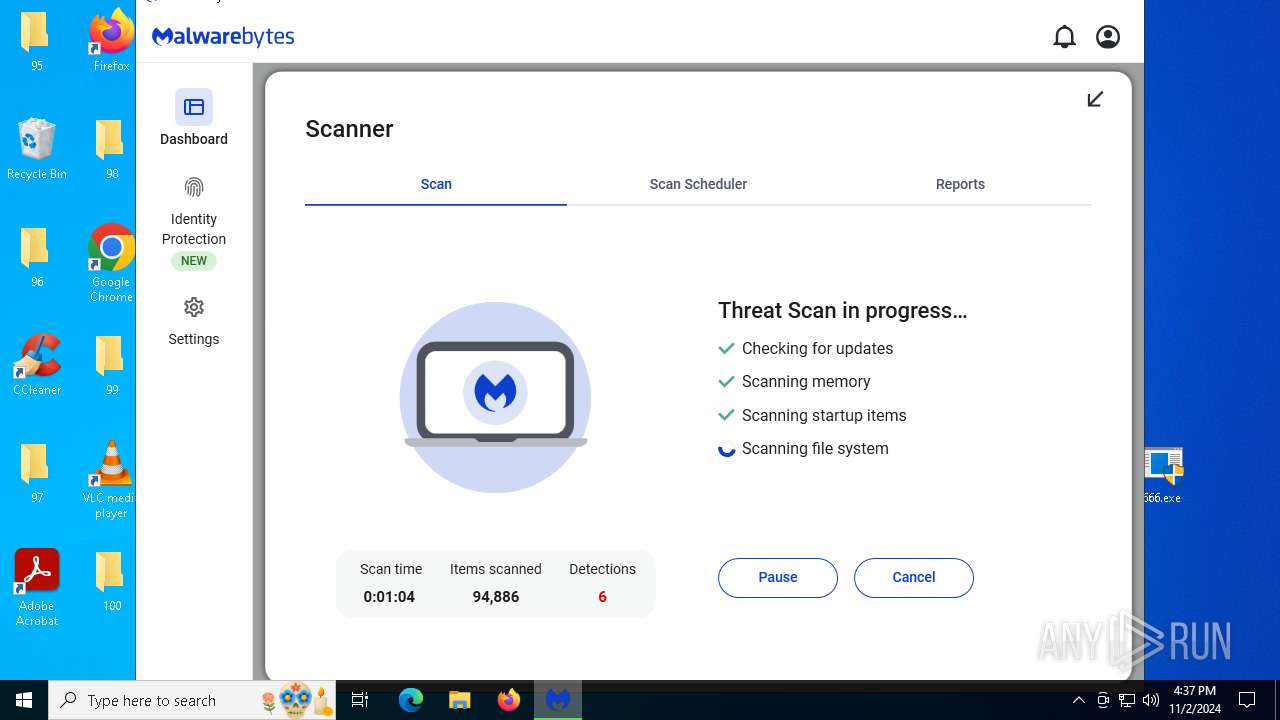
Total processes
259
Monitored processes
109
Malicious processes
7
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 300 | cscript //nologo C:\Users\admin\AppData\Local\Temp\msg.vbs | C:\Windows\System32\cscript.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft ® Console Based Script Host Exit code: 1 Version: 5.812.10240.16384 Modules
| |||||||||||||||
| 300 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1204 | net user "無路可走" "death" /add /y | C:\Windows\System32\net.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1376 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=2080 --field-trial-handle=1908,i,11897072220825111232,4026521430511633490,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:3 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 1396 | C:\WINDOWS\system32\net1 user "你是下一個" | C:\Windows\System32\net1.exe | — | net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) | |||||||||||||||
| 1748 | "C:\Program Files\Malwarebytes\Anti-Malware\Malwarebytes.exe" | C:\Program Files\Malwarebytes\Anti-Malware\Malwarebytes.exe | — | explorer.exe | |||||||||||
User: admin Company: Malwarebytes Integrity Level: MEDIUM Description: Malwarebytes Exit code: 0 Version: 5.0.0.997 | |||||||||||||||
| 1784 | taskkill /f /im iexplore.exe | C:\Windows\System32\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 128 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2312 | net user "無路可走" | C:\Windows\System32\net.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 2 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2376 | reg add "HKEY_CURRENT_USER\Control Panel\Desktop" /v WallpaperStyle /t REG_SZ /d "2" /f | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2464 | "C:\Program Files\Malwarebytes\Anti-Malware\MBAMWsc.exe" /wac 0 /status on true /updatesubstatus none /scansubstatus none /settingssubstatus none | C:\Program Files\Malwarebytes\Anti-Malware\MBAMWsc.exe | — | MBAMService.exe | |||||||||||
User: SYSTEM Company: Malwarebytes Integrity Level: SYSTEM Exit code: 0 Version: 3.1.0.245 | |||||||||||||||
Total events
71 771
Read events
71 187
Write events
519
Delete events
65
Modification events
| (PID) Process: | (5264) reg.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System |
| Operation: | write | Name: | DisableTaskMgr |
Value: 1 | |||
| (PID) Process: | (5984) reg.exe | Key: | HKEY_CURRENT_USER\Control Panel\Desktop |
| Operation: | write | Name: | Wallpaper |
Value: C:\Users\admin\Desktop\666.jpg | |||
| (PID) Process: | (2376) reg.exe | Key: | HKEY_CURRENT_USER\Control Panel\Desktop |
| Operation: | write | Name: | WallpaperStyle |
Value: 2 | |||
| (PID) Process: | (7104) reg.exe | Key: | HKEY_CURRENT_USER\Control Panel\Desktop |
| Operation: | write | Name: | TileWallpaper |
Value: 0 | |||
| (PID) Process: | (5512) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\MountPoints2\CPC\Volume\{eaf65672-68c3-4f99-8d5c-104b5f4d8fff} |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (5512) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\MountPoints2\CPC\Volume\{2f5c5e73-85a9-11eb-90a8-9a9b76358421} |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (5512) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\MountPoints2\CPC\Volume\{2f5c5e72-85a9-11eb-90a8-9a9b76358421} |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (5512) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\MountPoints2\CPC\Volume\{2f5c5e71-85a9-11eb-90a8-9a9b76358421} |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (5512) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\MountPoints2\CPC\Volume |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (6596) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\MountPoints2\CPC\Volume\{2f5c5e72-85a9-11eb-90a8-9a9b76358421} |
| Operation: | write | Name: | Data |
Value: D60D00000DF0ADBA41000000080000000000008000000000000000300000000000000000FF06E703FF00000016000000FA99B7261F00000004400000030000000000000000000000000000000000000000005C005C003F005C00530054004F005200410047004500230056006F006C0075006D00650023007B00390030006300660033006400640036002D0030006100660037002D0031003100650063002D0062003400380030002D003800300036006500360066003600650036003900360033007D002300300030003000300030003000300030003100460035003000300030003000300023007B00350033006600350036003300300064002D0062003600620066002D0031003100640030002D0039003400660032002D003000300061003000630039003100650066006200380062007D000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000005C005C003F005C0056006F006C0075006D0065007B00320066003500630035006500370032002D0038003500610039002D0031003100650062002D0039003000610038002D003900610039006200370036003300350038003400320031007D005C0000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000004E005400460053000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF0000 | |||
Executable files
1 459
Suspicious files
642
Text files
439
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5532 | SearchApp.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.Search_cw5n1h2txyewy\LocalState\DeviceSearchCache\AppCache133750387743883404.txt~RF8d7cb.TMP | — | |
MD5:— | SHA256:— | |||
| 4868 | 666.exe | C:\Users\admin\AppData\Local\Temp\B36A.tmp\B36B.tmp\B36C.bat | text | |
MD5:F2650F2B7CD26B6042303D74D8CB9560 | SHA256:E6A31BAF0726C64A08E2D5E7AC4C28D56B43C3343BE0FB758230229D92584530 | |||
| 5532 | SearchApp.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.Search_cw5n1h2txyewy\LocalState\DeviceSearchCache\AppCache133750387743883404.txt | ini | |
MD5:EBA9D627AEFA0148EA256382E454768F | SHA256:85F02886D53B7427792E54BCEE97D366AD46F78CF90AA25DCC3FAE29ED7FA7F8 | |||
| 6596 | explorer.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Themes\CachedFiles\CachedImage_1280_720_POS2.jpg | image | |
MD5:616B934933CA03FD399AC5E68982517C | SHA256:7B40AD3547C32DE01852CA3D39B2EE95700B8E01E21FDA7C09B4E7C85392EA34 | |||
| 5532 | SearchApp.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.Search_cw5n1h2txyewy\AC\INetCache\Q84V0JUH\-UAIppANYxiGpRWJy2NDph4qOEw.gz[1].js | binary | |
MD5:9E527B91C2D8B31B0017B76049B5E4E3 | SHA256:38EDF0F961C1CCB287880B88F12F370775FC65B2E28227EEE215E849CDBE9BBC | |||
| 5532 | SearchApp.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.Search_cw5n1h2txyewy\AC\Microsoft\CryptnetUrlCache\MetaData\26C212D9399727259664BDFCA073966E_F9F7D6A7ECE73106D2A8C63168CDA10D | binary | |
MD5:7424BE0448152311C7AF080046598BC0 | SHA256:7B668578EFDFEA0F563EAE55B9E4492391989B3FE9919189CD704B534131DB2B | |||
| 4868 | 666.exe | C:\Users\admin\AppData\Local\Temp\666.jpg | image | |
MD5:B0058B62EEF8F75CC5817C2727581049 | SHA256:7A437FEDC2CF3AC7CE6C6004A77C8D76745E92E5820FB2C3334AE21576EB1FFB | |||
| 5532 | SearchApp.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.Search_cw5n1h2txyewy\AC\Microsoft\CryptnetUrlCache\Content\26C212D9399727259664BDFCA073966E_F9F7D6A7ECE73106D2A8C63168CDA10D | der | |
MD5:309C222F85BCA69AF3BF3301770614A4 | SHA256:8A6AC095CD1CCF7E3AEC06632AAFE71FBC7FC2E12BE0D2E98A58E17CCB43067D | |||
| 5532 | SearchApp.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.Search_cw5n1h2txyewy\LocalState\DeviceSearchCache\AppCache133750387743883404.txt.~tmp | text | |
MD5:EBA9D627AEFA0148EA256382E454768F | SHA256:85F02886D53B7427792E54BCEE97D366AD46F78CF90AA25DCC3FAE29ED7FA7F8 | |||
| 5532 | SearchApp.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.Search_cw5n1h2txyewy\AC\AppCache\5Y734AMR\63\4-xJy3tX6bM2BGl5zKioiEcQ1TU[1].css | text | |
MD5:94D8383805B336E533D1D234AAA98A21 | SHA256:699D6C87C646D3875C45FAB214BFE2E385B54F325F25818C72C2C45C1A5F6897 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
64
TCP/UDP connections
160
DNS requests
148
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6944 | svchost.exe | GET | 200 | 23.32.185.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | BR | binary | 973 b | whitelisted |
— | — | GET | 200 | 23.53.40.178:80 | http://crl.microsoft.com/pki/crl/products/MicCodSigPCA_08-31-2010.crl | DE | binary | 564 b | whitelisted |
6944 | svchost.exe | GET | 200 | 2.16.241.19:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | DE | binary | 1.01 Kb | whitelisted |
5532 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | US | binary | 314 b | whitelisted |
3600 | SIHClient.exe | GET | 200 | 23.52.120.96:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | DE | binary | 418 b | whitelisted |
2776 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | binary | 471 b | whitelisted |
3600 | SIHClient.exe | GET | 200 | 23.52.120.96:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | DE | binary | 408 b | whitelisted |
3844 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | US | binary | 471 b | whitelisted |
— | — | GET | 200 | 172.64.149.23:80 | http://ocsp.sectigo.com/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBQRz3ETyLz2DaZTxGOH%2BA%2BjK7MkGAQUJGWTmAgB6E7U1kzqZFXhwPr7z7MCEQCmV%2Fd4sxrlI9ZnExcY0W6y | US | binary | 638 b | whitelisted |
— | — | GET | 200 | 172.64.149.23:80 | http://crl.comodoca.com/AAACertificateServices.crl | US | binary | 607 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
6944 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5488 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3396 | RUXIMICS.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6944 | svchost.exe | 2.16.241.19:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
6944 | svchost.exe | 23.32.185.131:80 | www.microsoft.com | AKAMAI-AS | BR | whitelisted |
5532 | SearchApp.exe | 2.23.209.182:443 | r.bing.com | Akamai International B.V. | GB | whitelisted |
5532 | SearchApp.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
5532 | SearchApp.exe | 2.23.209.179:443 | r.bing.com | Akamai International B.V. | GB | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
r.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
www.bing.com |
| whitelisted |
th.bing.com |
| whitelisted |
login.live.com |
| whitelisted |
go.microsoft.com |
| whitelisted |