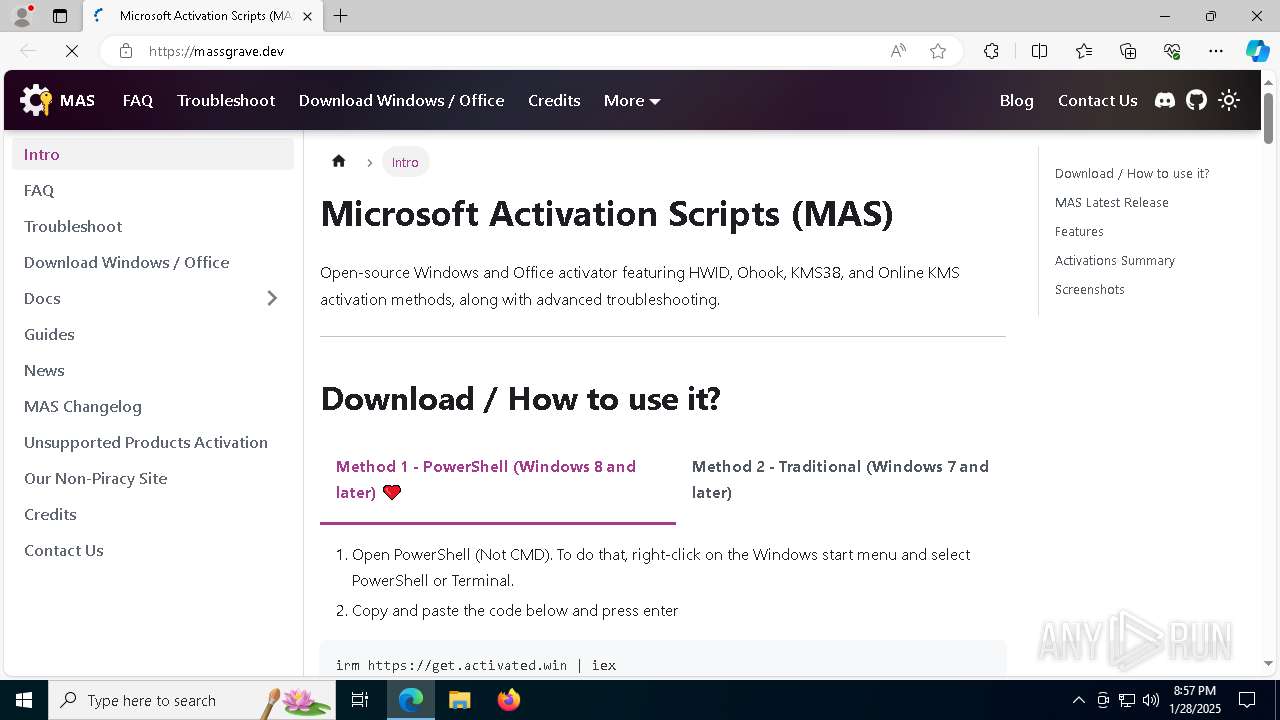
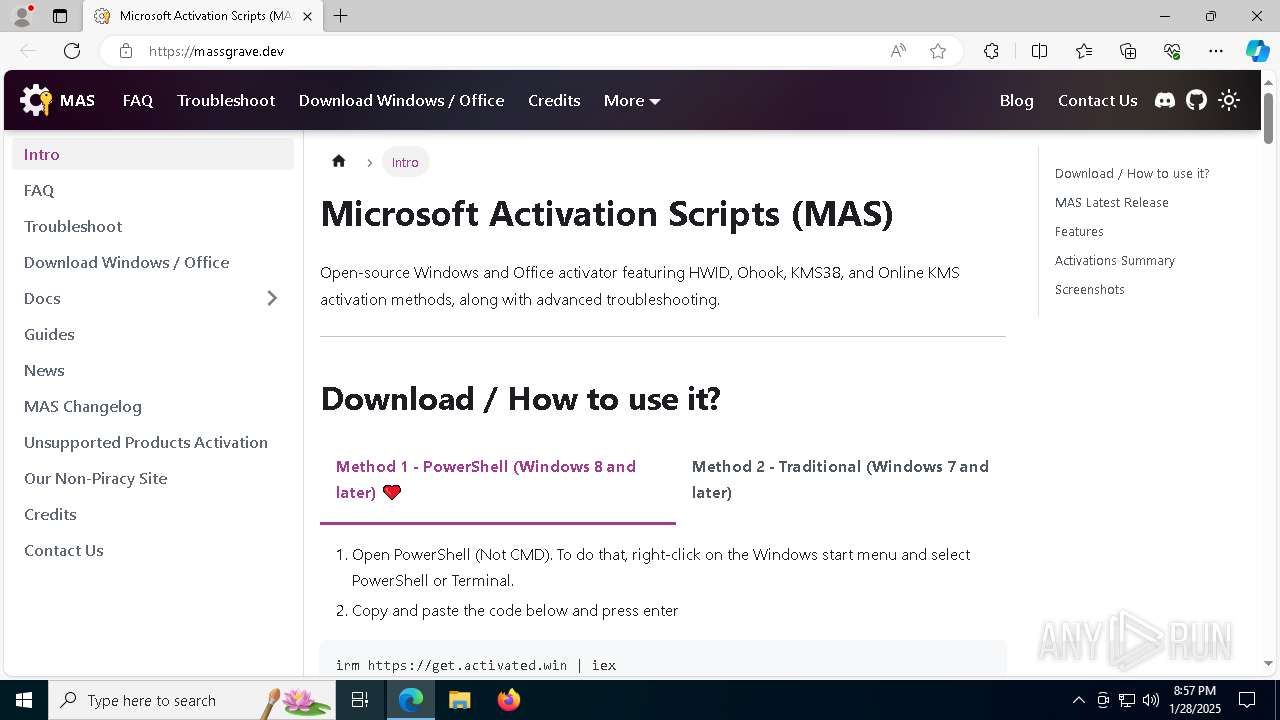
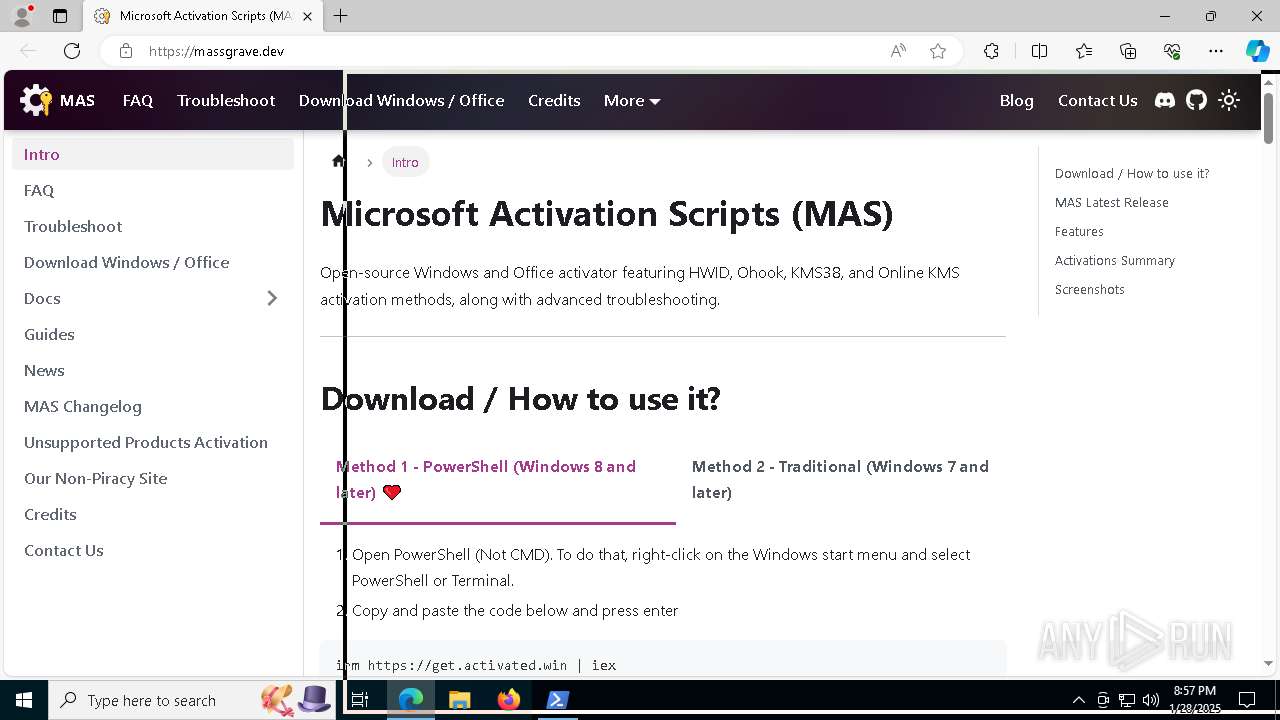
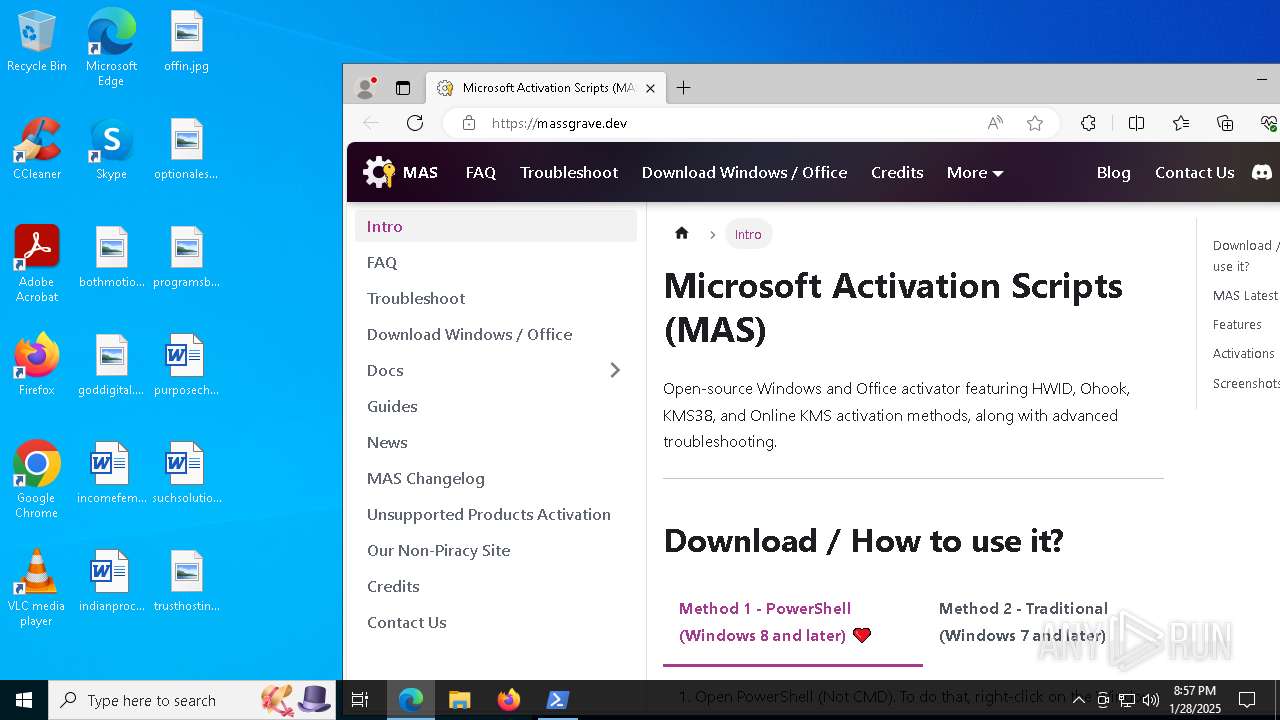
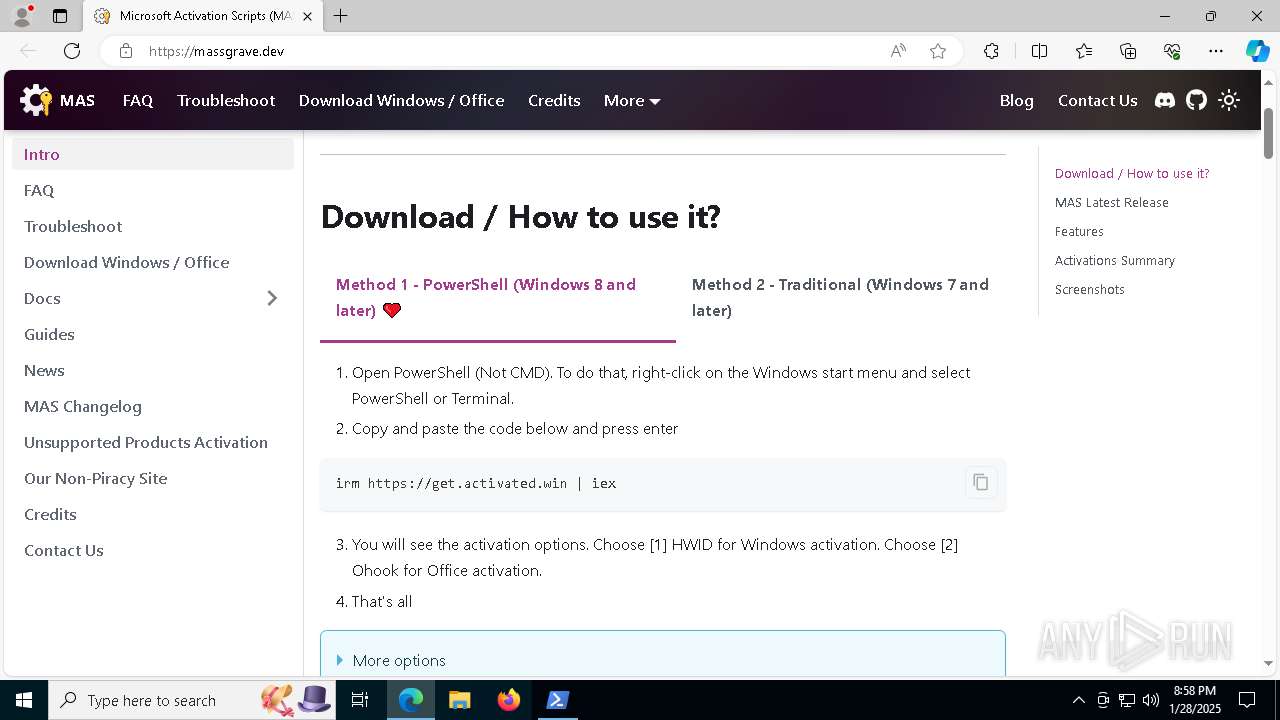
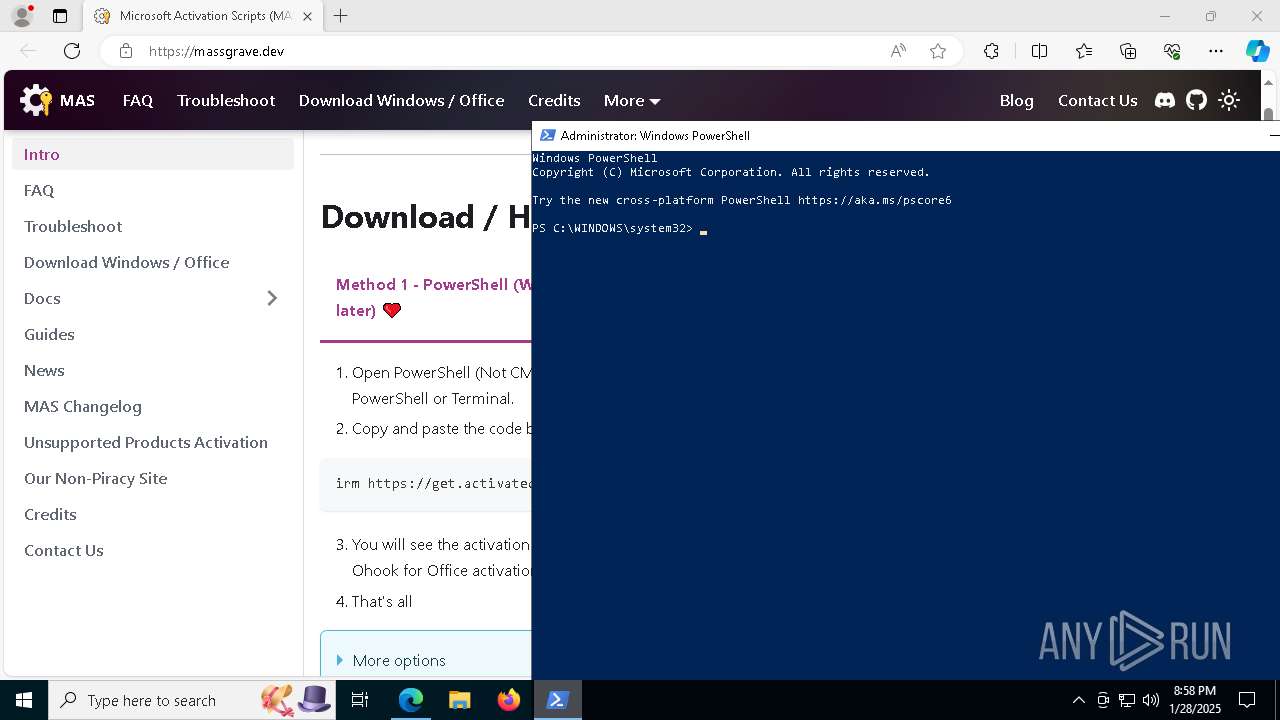
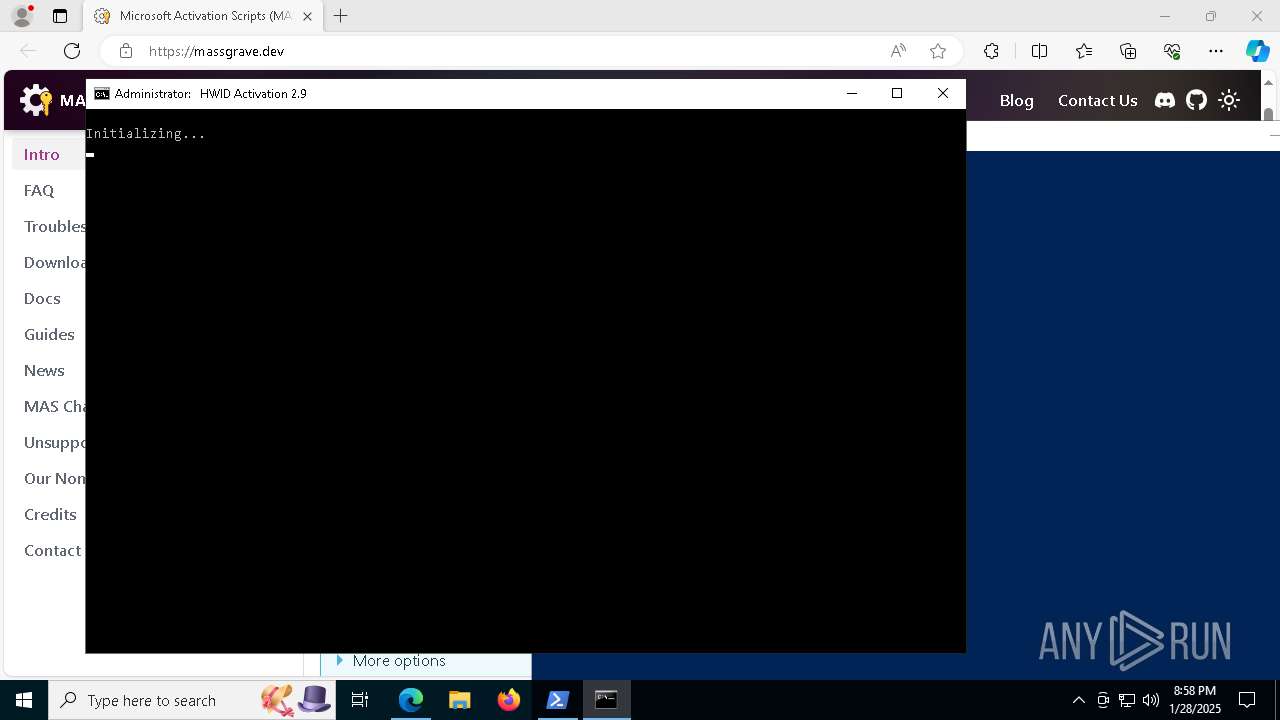
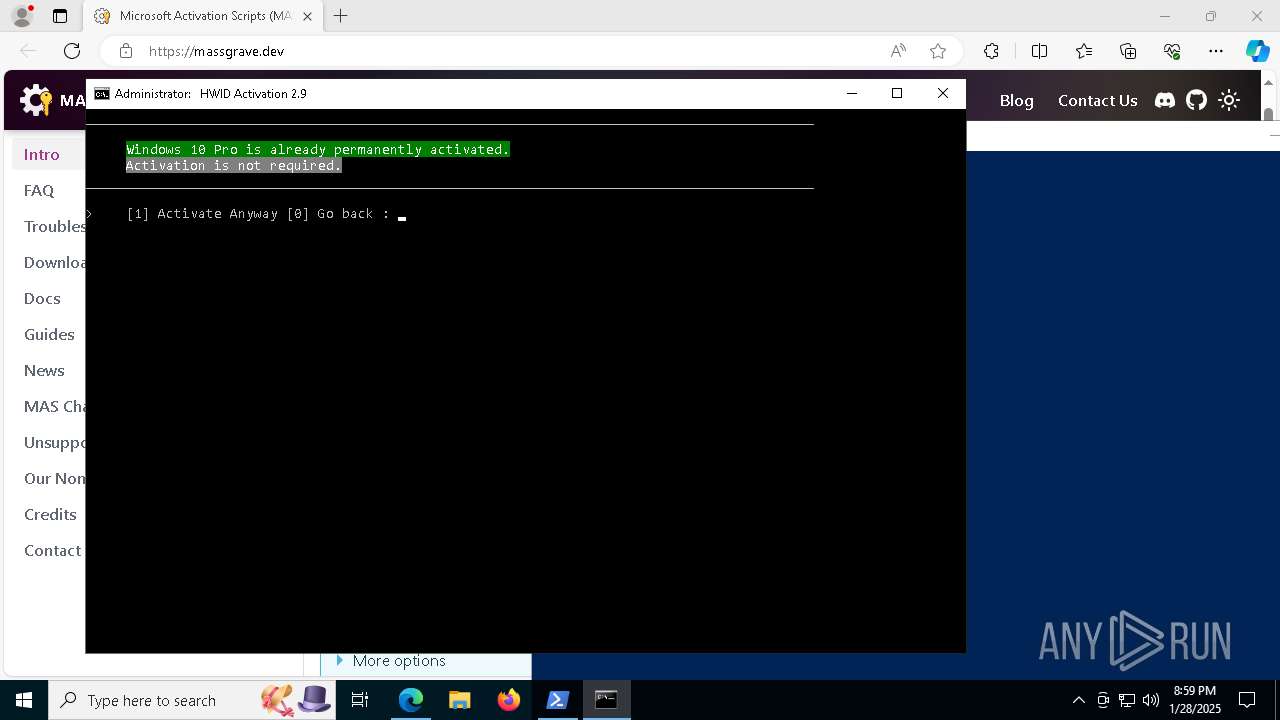
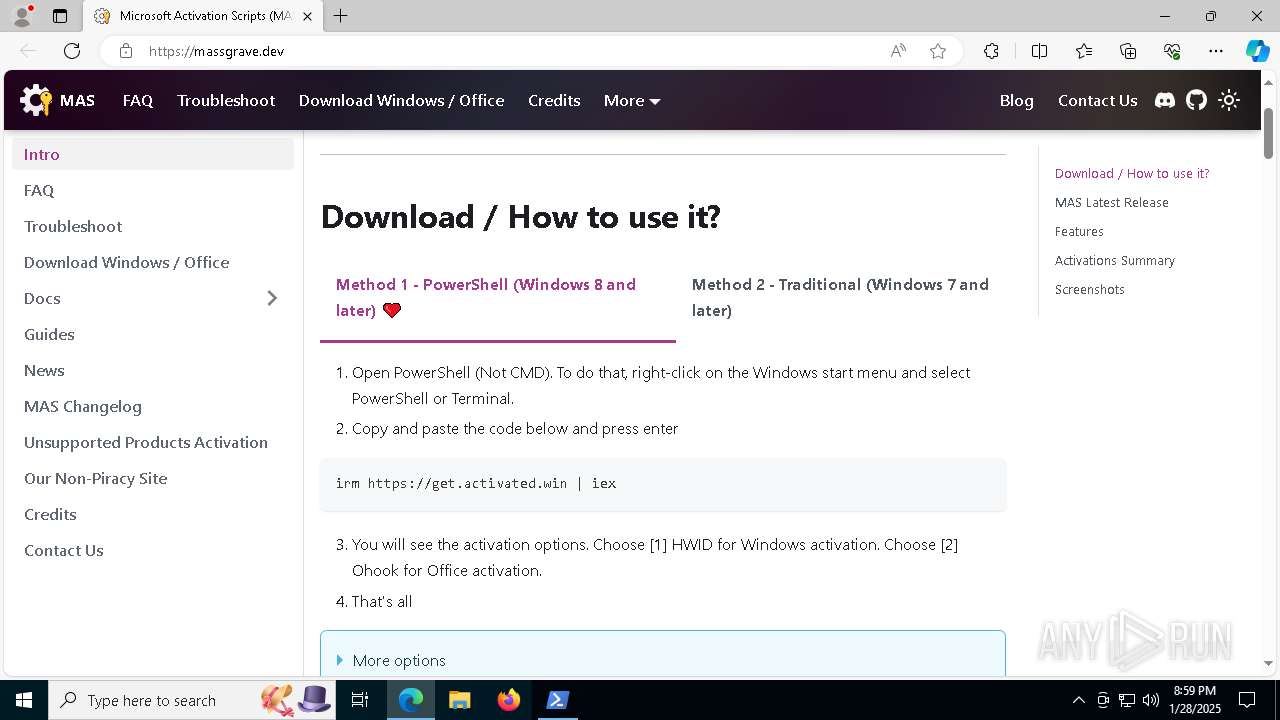
| URL: | https://massgrave.dev/ |
| Full analysis: | https://app.any.run/tasks/ed655d92-407a-40f5-8de4-26a87485c6ec |
| Verdict: | Malicious activity |
| Analysis date: | January 28, 2025, 20:57:21 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MD5: | 5C95876F594CFFB1178B8861F8C741E0 |
| SHA1: | 4F3DD1555BACB0851AD877F9B40BD8DCC884A71D |
| SHA256: | 6019AF861964CFB41AE5A5FE576ACA4521AFBA41255E5C636B1F53DFA0B6BE7F |
| SSDEEP: | 3:N8a0Kn:2a0K |
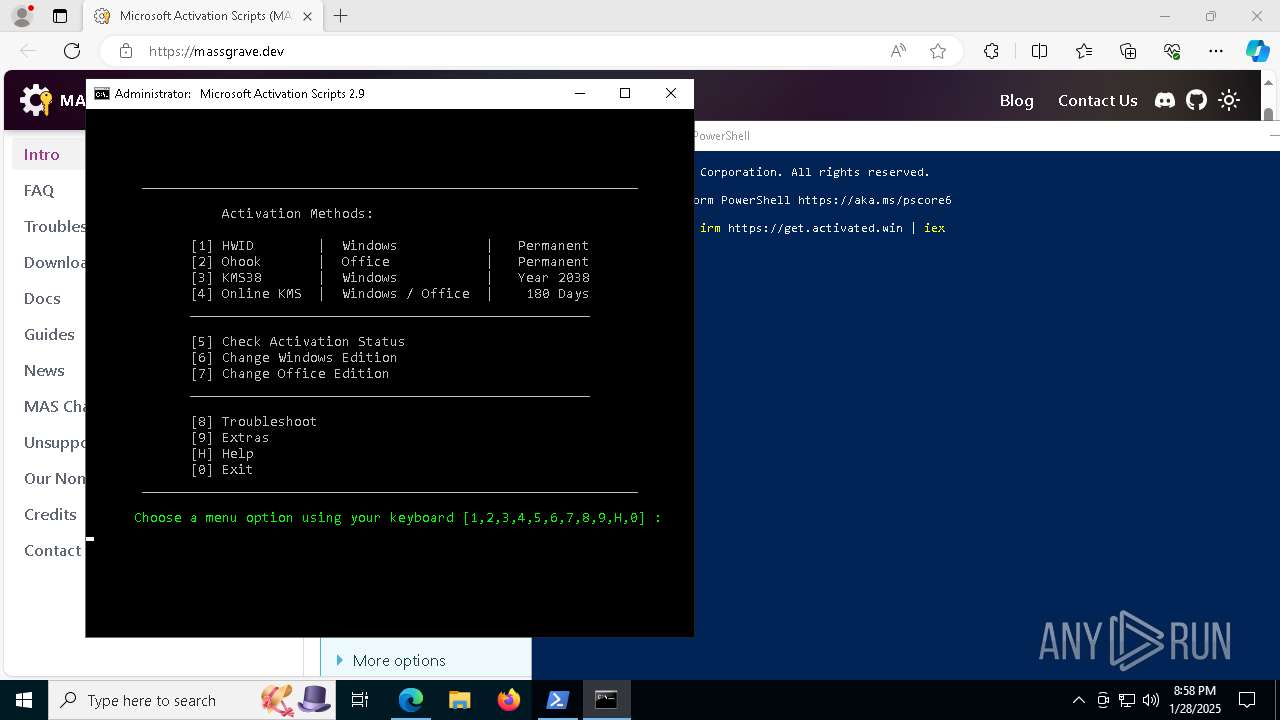
MALICIOUS
No malicious indicators.SUSPICIOUS
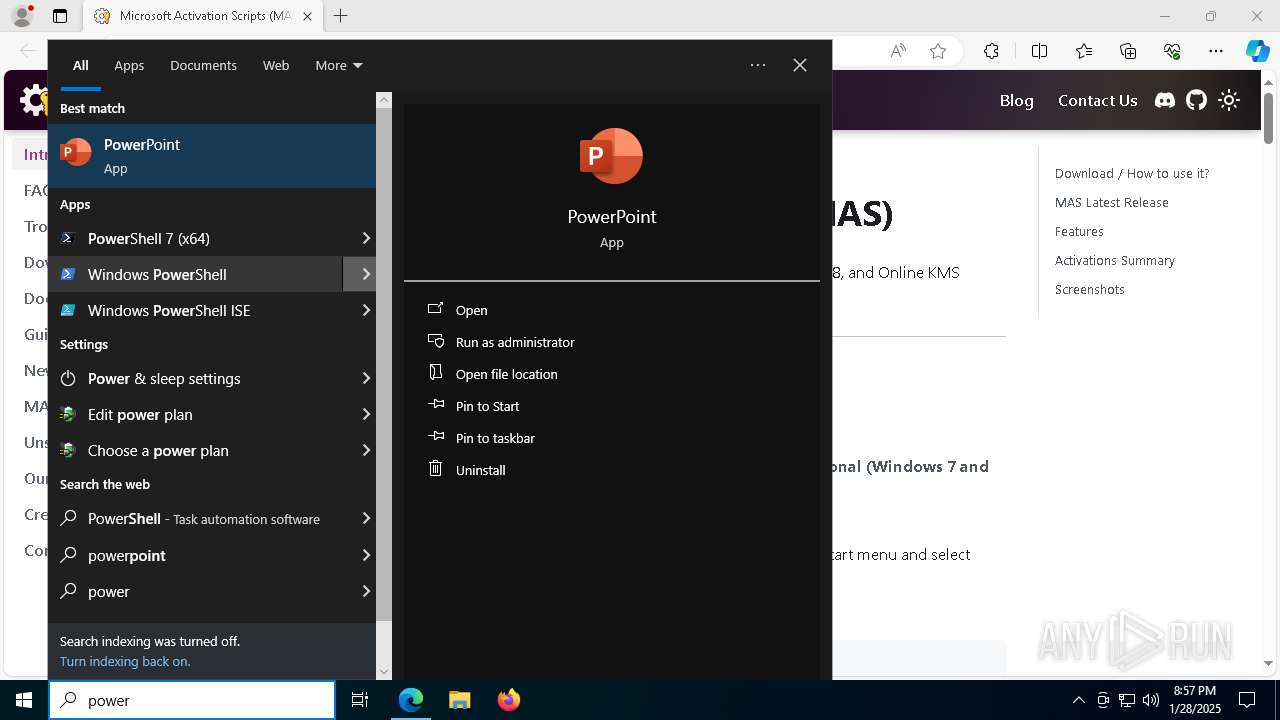
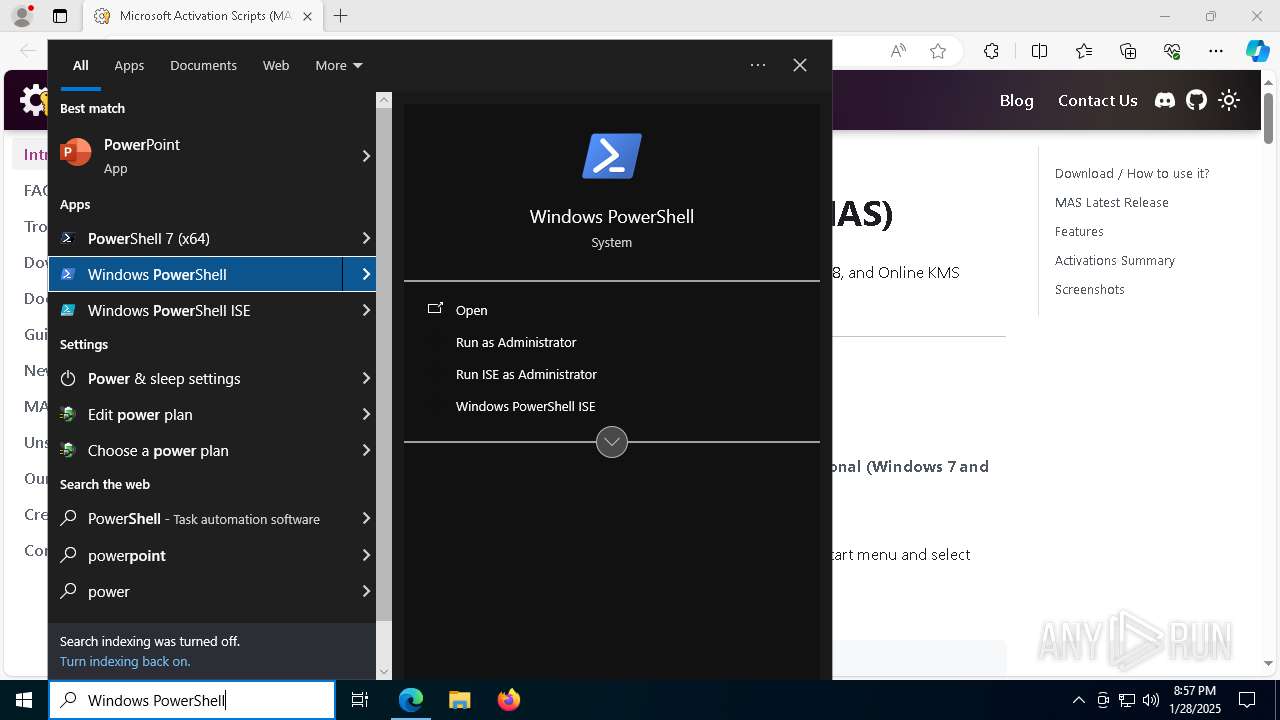
The process executes via Task Scheduler
- powershell.exe (PID: 4400)
Gets content of a file (POWERSHELL)
- powershell.exe (PID: 4400)
- powershell.exe (PID: 2996)
- powershell.exe (PID: 6592)
- powershell.exe (PID: 3680)
Gets or sets the security protocol (POWERSHELL)
- powershell.exe (PID: 4400)
Uses base64 encoding (POWERSHELL)
- powershell.exe (PID: 4400)
- powershell.exe (PID: 2996)
- powershell.exe (PID: 6592)
- powershell.exe (PID: 3680)
Creates new GUID (POWERSHELL)
- powershell.exe (PID: 4400)
Executing commands from ".cmd" file
- powershell.exe (PID: 4400)
- cmd.exe (PID: 3420)
- powershell.exe (PID: 2972)
- cmd.exe (PID: 6280)
Starts CMD.EXE for commands execution
- powershell.exe (PID: 4400)
- cmd.exe (PID: 5392)
- cmd.exe (PID: 3420)
- powershell.exe (PID: 2972)
- cmd.exe (PID: 7976)
- cmd.exe (PID: 6280)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 3420)
- cmd.exe (PID: 6280)
Windows service management via SC.EXE
- sc.exe (PID: 7456)
- sc.exe (PID: 7264)
- sc.exe (PID: 2088)
- sc.exe (PID: 4472)
Starts SC.EXE for service management
- cmd.exe (PID: 3420)
- cmd.exe (PID: 6280)
Application launched itself
- cmd.exe (PID: 5392)
- cmd.exe (PID: 3420)
- cmd.exe (PID: 6280)
- cmd.exe (PID: 7976)
- powershell.exe (PID: 4384)
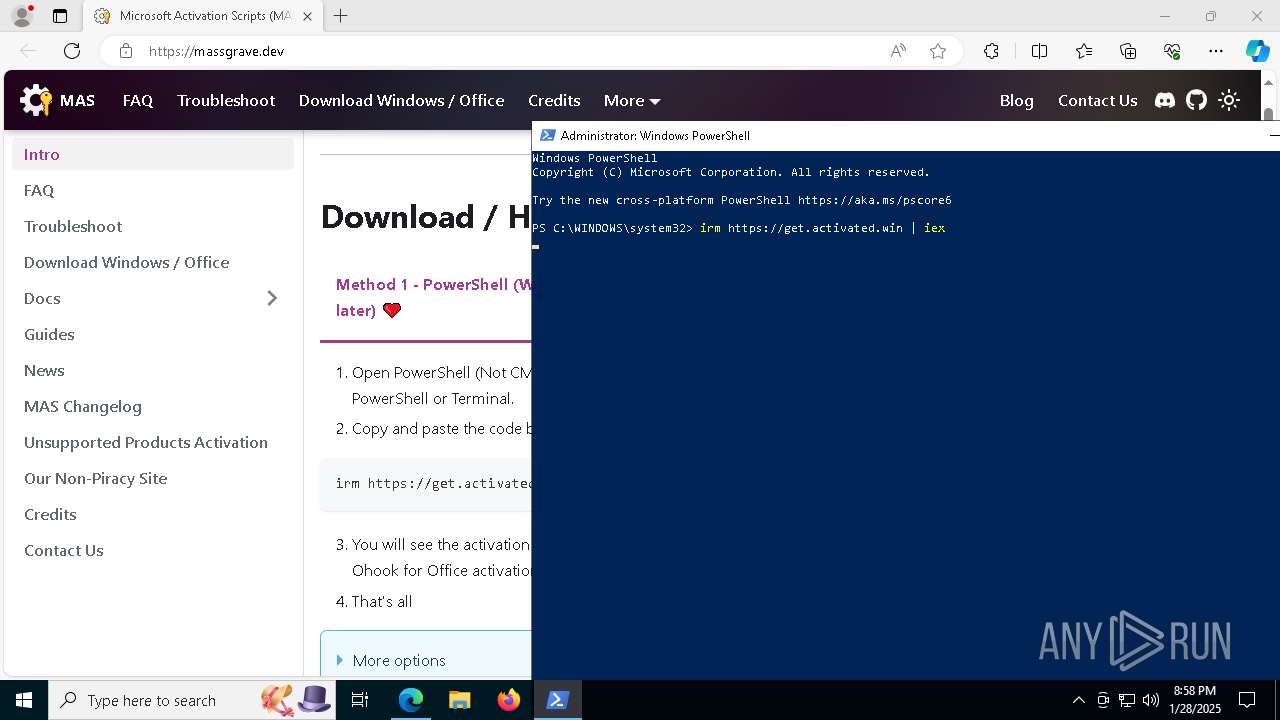
Possibly malicious use of IEX has been detected
- cmd.exe (PID: 1744)
- cmd.exe (PID: 536)
- cmd.exe (PID: 6280)
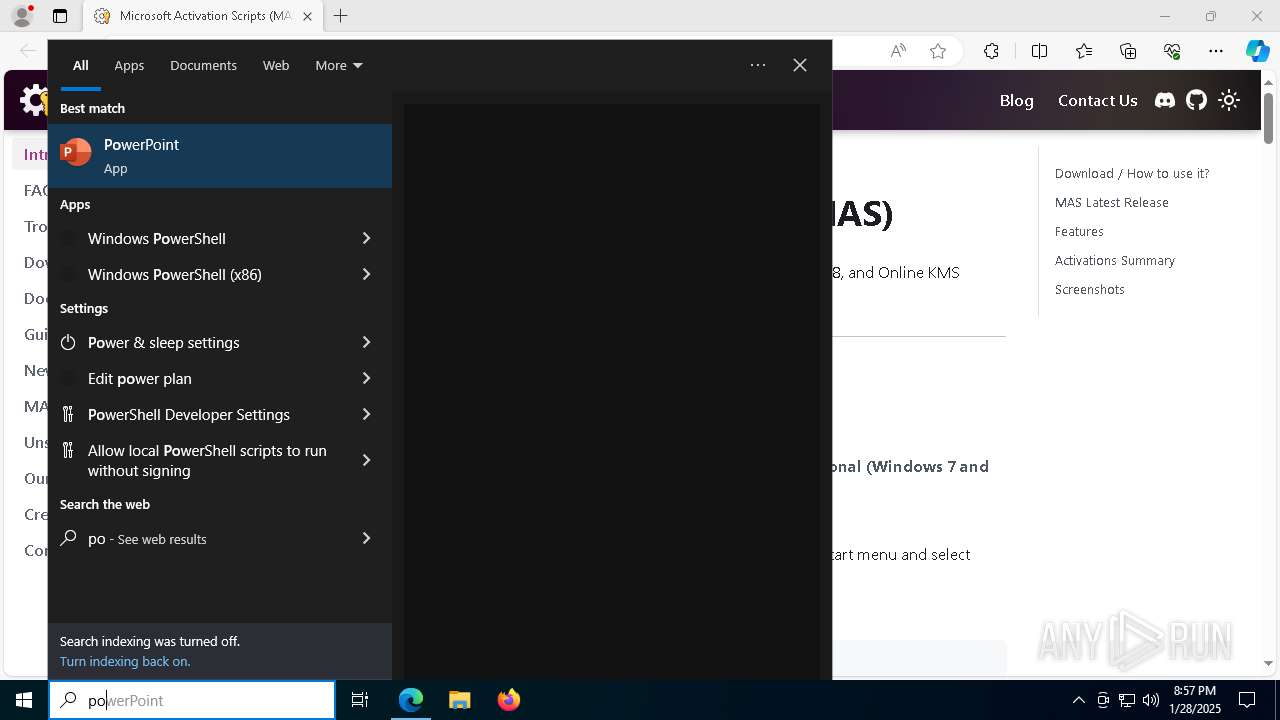
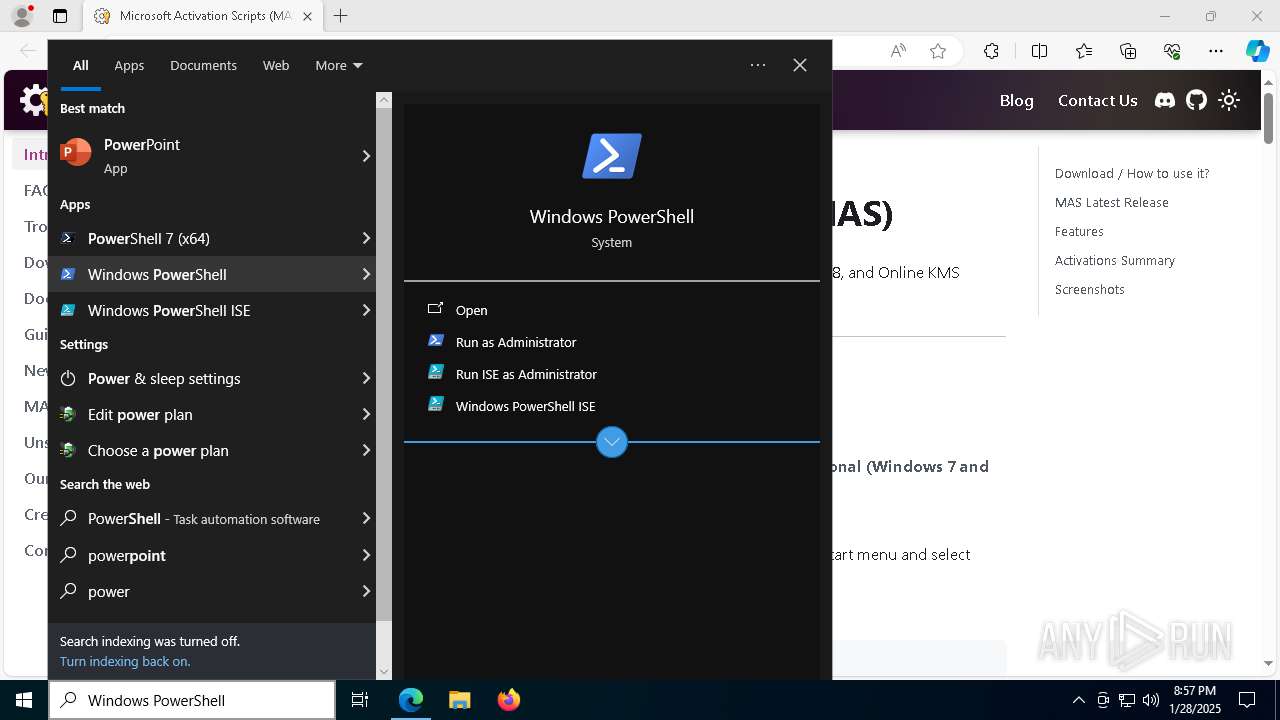
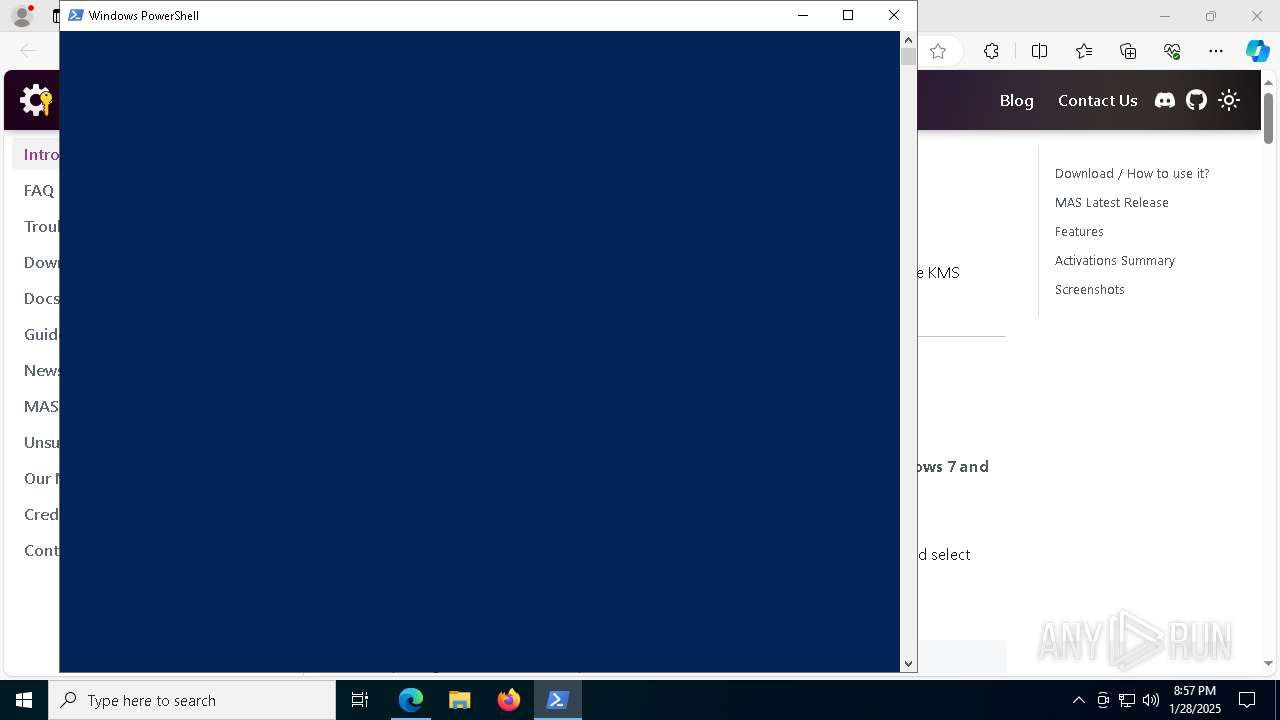
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 1744)
- cmd.exe (PID: 3420)
- cmd.exe (PID: 536)
- cmd.exe (PID: 6280)
- cmd.exe (PID: 2792)
- cmd.exe (PID: 6604)
- powershell.exe (PID: 4384)
Probably obfuscated PowerShell command line is found
- cmd.exe (PID: 1744)
- cmd.exe (PID: 536)
- cmd.exe (PID: 6280)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 6280)
Hides command output
- cmd.exe (PID: 7912)
- cmd.exe (PID: 7228)
Uses WMIC.EXE to obtain computer system information
- cmd.exe (PID: 4816)
Uses WMIC.EXE to obtain operating system information
- cmd.exe (PID: 7228)
The process bypasses the loading of PowerShell profile settings
- powershell.exe (PID: 4384)
The process hides Powershell's copyright startup banner
- powershell.exe (PID: 4384)
Uses WMIC.EXE to obtain Windows Installer data
- cmd.exe (PID: 6280)
INFO
Checks supported languages
- identity_helper.exe (PID: 7228)
- mode.com (PID: 5912)
Reads the computer name
- identity_helper.exe (PID: 7228)
Disables trace logs
- powershell.exe (PID: 4400)
Reads Environment values
- identity_helper.exe (PID: 7228)
Checks current location (POWERSHELL)
- powershell.exe (PID: 4400)
Checks proxy server information
- powershell.exe (PID: 4400)
Checks whether the specified file exists (POWERSHELL)
- powershell.exe (PID: 4400)
- powershell.exe (PID: 6592)
- powershell.exe (PID: 3680)
- powershell.exe (PID: 2996)
Gets a random number, or selects objects randomly from a collection (POWERSHELL)
- powershell.exe (PID: 4400)
- powershell.exe (PID: 2996)
- powershell.exe (PID: 6592)
- powershell.exe (PID: 3680)
Converts byte array into ASCII string (POWERSHELL)
- powershell.exe (PID: 4400)
- powershell.exe (PID: 2996)
- powershell.exe (PID: 6592)
- powershell.exe (PID: 3680)
Checks operating system version
- cmd.exe (PID: 3420)
- cmd.exe (PID: 6280)
Application launched itself
- msedge.exe (PID: 6324)
Starts MODE.COM to configure console settings
- mode.com (PID: 5392)
- mode.com (PID: 5912)
Reads security settings of Internet Explorer
- WMIC.exe (PID: 7584)
- WMIC.exe (PID: 4840)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
266
Monitored processes
133
Malicious processes
4
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 236 | C:\WINDOWS\System32\cmd.exe /S /D /c" echo "-el -qedit" " | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 444 | find /i "FullLanguage" | C:\Windows\System32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (grep) Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 524 | C:\WINDOWS\System32\cmd.exe /S /D /c" echo "AMD64 " " | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 524 | find /i "/" | C:\Windows\System32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (grep) Utility Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 536 | cmd /c "powershell.exe "$f=[io.file]::ReadAllText('C:\Windows\Temp\MAS_ee67f42d-6087-4f72-b3a2-2a6dc065cb04.cmd') -split ':PStest:\s*';iex ($f[1])"" | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1152 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6784 --field-trial-handle=2452,i,1148459261568104309,3255451980804049178,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1216 | find /i "Subscription_is_activated" | C:\Windows\System32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (grep) Utility Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1292 | C:\WINDOWS\System32\cmd.exe /S /D /c" echo "0" " | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1400 | find /i "ARM64" | C:\Windows\System32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (grep) Utility Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1488 | C:\WINDOWS\System32\cmd.exe /S /D /c" echo "-el -qedit" " | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
60 876
Read events
60 861
Write events
15
Delete events
0
Modification events
| (PID) Process: | (6324) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 288357B9608B2F00 | |||
| (PID) Process: | (6324) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\459466 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {DC21120C-A8D1-4FAB-A011-7B377A055C27} | |||
| (PID) Process: | (6324) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\459466 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {E7F4B62C-EB65-44A2-917D-50AA23483D75} | |||
| (PID) Process: | (6324) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\459466 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {E7A89419-47CB-435D-B80D-58EE9FA2BE29} | |||
| (PID) Process: | (6324) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (6324) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (6324) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (6324) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (6324) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 274E4CB9608B2F00 | |||
| (PID) Process: | (6324) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 0210A3B9608B2F00 | |||
Executable files
8
Suspicious files
186
Text files
70
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6324 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF137e4b.TMP | — | |
MD5:— | SHA256:— | |||
| 6324 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6324 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF137e3c.TMP | — | |
MD5:— | SHA256:— | |||
| 6324 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF137e5b.TMP | — | |
MD5:— | SHA256:— | |||
| 6324 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6324 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF137e6a.TMP | — | |
MD5:— | SHA256:— | |||
| 6324 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6324 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6324 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF137e6a.TMP | — | |
MD5:— | SHA256:— | |||
| 6324 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
29
TCP/UDP connections
72
DNS requests
62
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4992 | svchost.exe | GET | 200 | 2.16.253.202:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
7732 | backgroundTaskHost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
7960 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
1448 | svchost.exe | HEAD | 200 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9b9f8fb4-8a65-41e4-bda3-5416858f0aeb?P1=1738329356&P2=404&P3=2&P4=V3qI%2fUKduzxjIsUcvb31SAZMzzX51rktujSTc%2fZOSb0aTg45X4MWFf7LkBhsrKTgIBlTmXAOMzbEQQQa8jg0ZA%3d%3d | unknown | — | — | whitelisted |
1448 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9b9f8fb4-8a65-41e4-bda3-5416858f0aeb?P1=1738329356&P2=404&P3=2&P4=V3qI%2fUKduzxjIsUcvb31SAZMzzX51rktujSTc%2fZOSb0aTg45X4MWFf7LkBhsrKTgIBlTmXAOMzbEQQQa8jg0ZA%3d%3d | unknown | — | — | whitelisted |
7960 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
1448 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9b9f8fb4-8a65-41e4-bda3-5416858f0aeb?P1=1738329356&P2=404&P3=2&P4=V3qI%2fUKduzxjIsUcvb31SAZMzzX51rktujSTc%2fZOSb0aTg45X4MWFf7LkBhsrKTgIBlTmXAOMzbEQQQa8jg0ZA%3d%3d | unknown | — | — | whitelisted |
1448 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9b9f8fb4-8a65-41e4-bda3-5416858f0aeb?P1=1738329356&P2=404&P3=2&P4=V3qI%2fUKduzxjIsUcvb31SAZMzzX51rktujSTc%2fZOSb0aTg45X4MWFf7LkBhsrKTgIBlTmXAOMzbEQQQa8jg0ZA%3d%3d | unknown | — | — | whitelisted |
1448 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9b9f8fb4-8a65-41e4-bda3-5416858f0aeb?P1=1738329356&P2=404&P3=2&P4=V3qI%2fUKduzxjIsUcvb31SAZMzzX51rktujSTc%2fZOSb0aTg45X4MWFf7LkBhsrKTgIBlTmXAOMzbEQQQa8jg0ZA%3d%3d | unknown | — | — | whitelisted |
1448 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/0c269ced-c74b-4e70-9b58-6e7999b292c0?P1=1738329356&P2=404&P3=2&P4=LzDNl3D6BE9XIWDaIJWNYGMQ6G3yMHslShSRcpYBkYTtJRPS2HgDQRgp5d4OqK4MLL5xsD57MRLuknmqVPXXCg%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4992 | svchost.exe | 2.16.253.202:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | 2.16.253.202:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6324 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
6688 | msedge.exe | 172.67.201.171:443 | massgrave.dev | — | — | unknown |
6688 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6688 | msedge.exe | 204.79.197.239:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6688 | msedge.exe | 13.107.246.45:443 | edge-mobile-static.azureedge.net | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6688 | msedge.exe | 13.107.6.158:443 | business.bing.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
massgrave.dev |
| unknown |
edge.microsoft.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
business.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
static.cloudflareinsights.com |
| whitelisted |
bzib.nelreports.net |
| whitelisted |
cloudflareinsights.com |
| unknown |