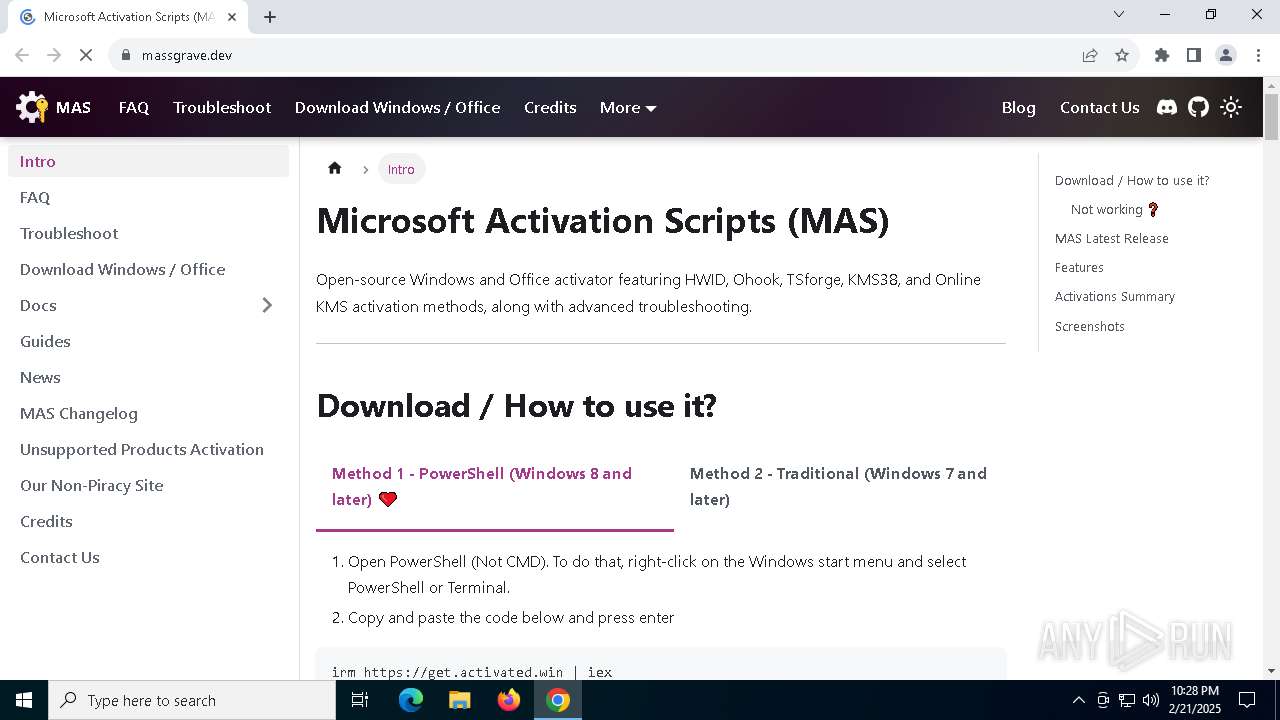
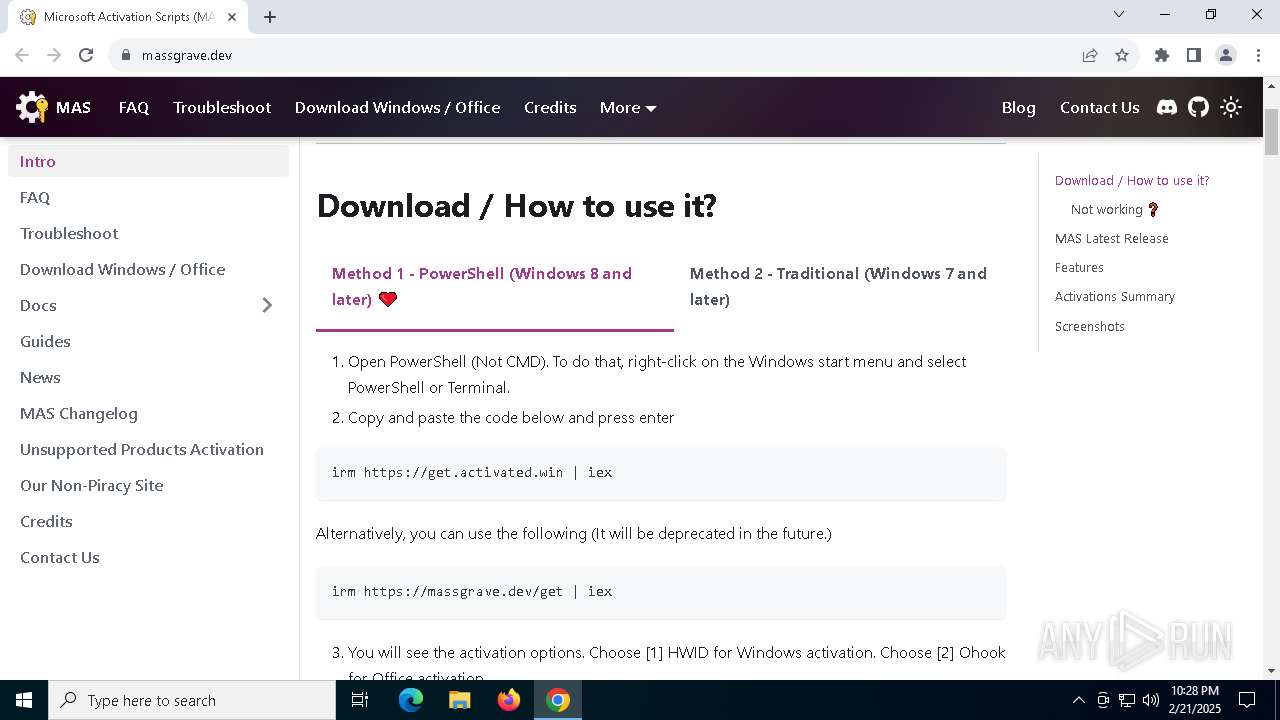
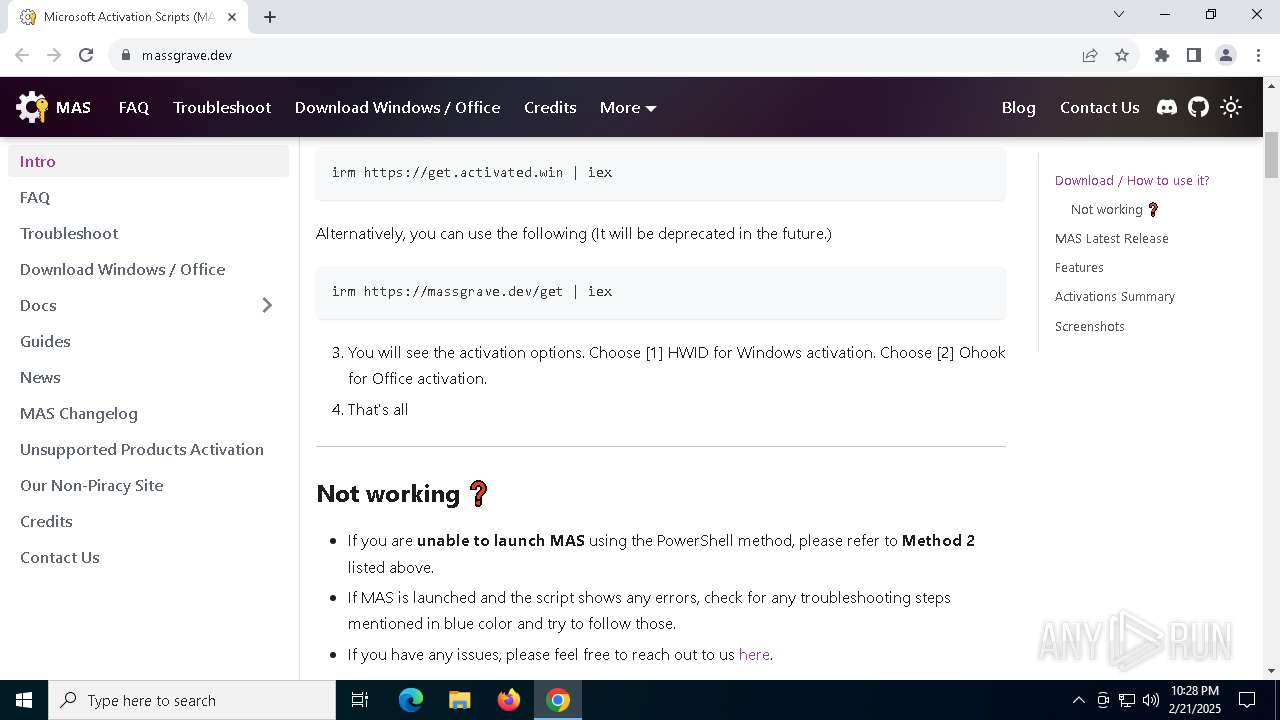
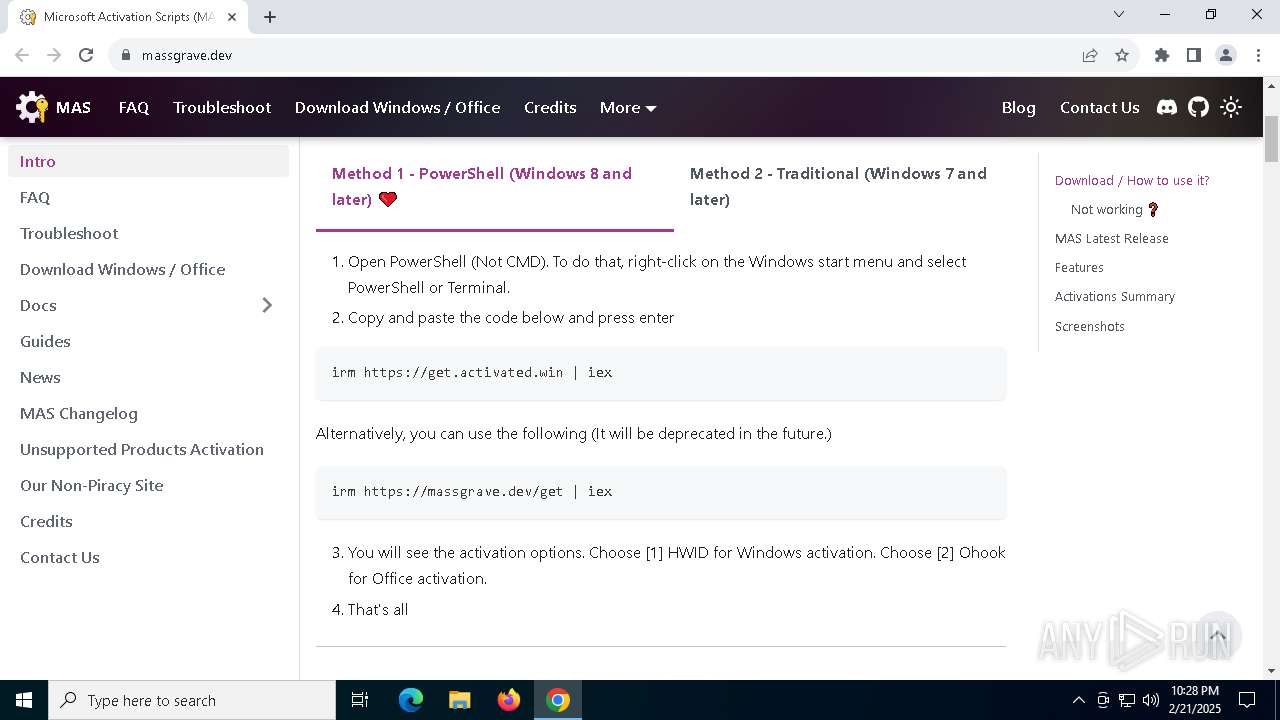
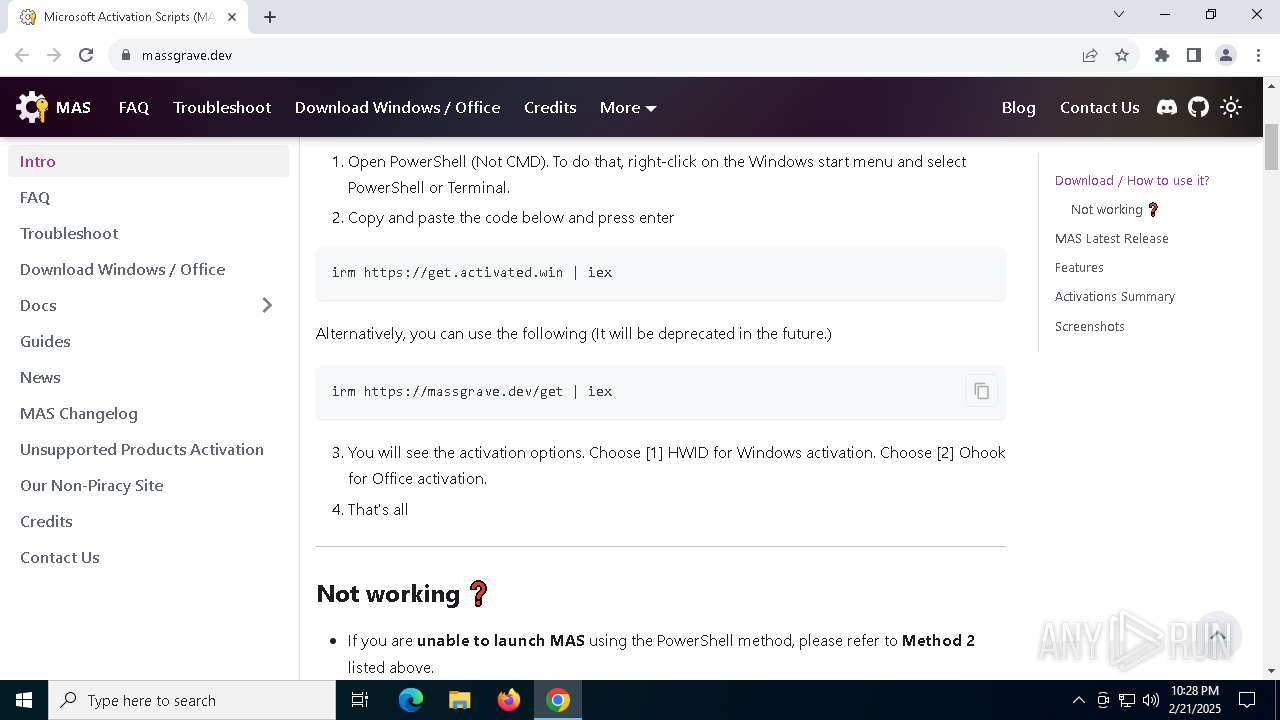
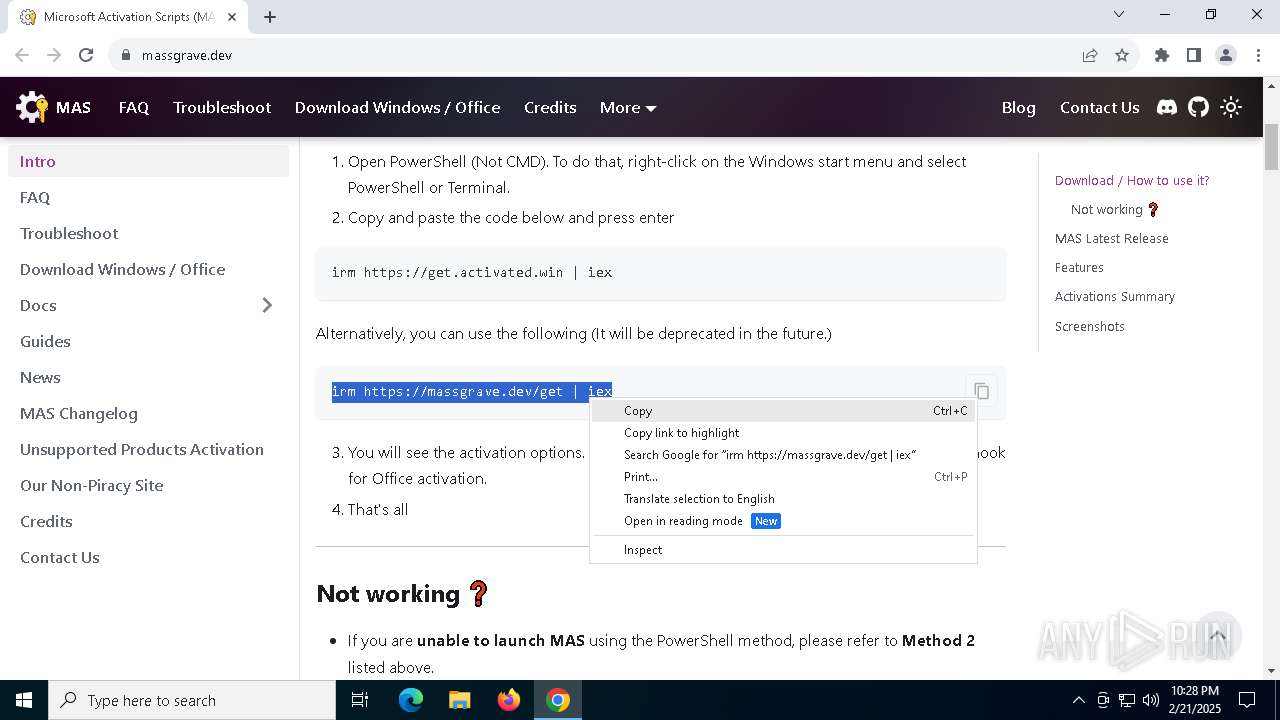
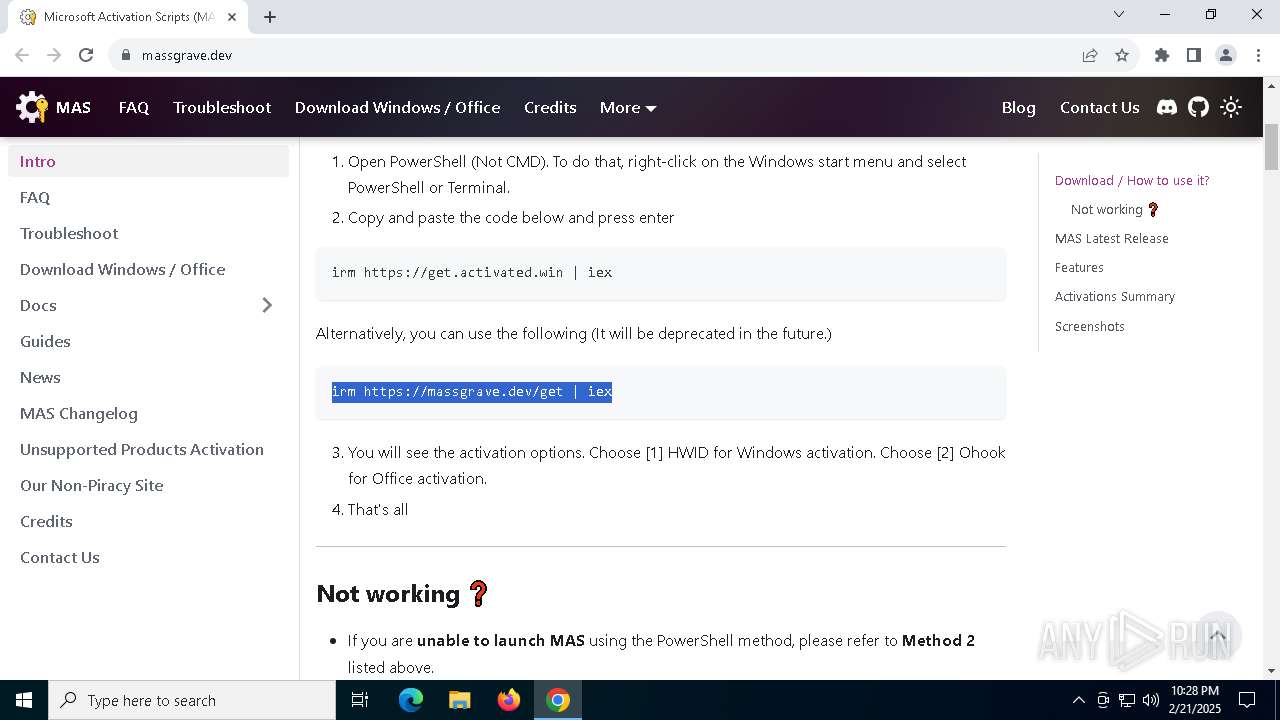
| URL: | https://massgrave.dev/ |
| Full analysis: | https://app.any.run/tasks/ca3d79ac-194f-4825-93ce-1ab9d1179175 |
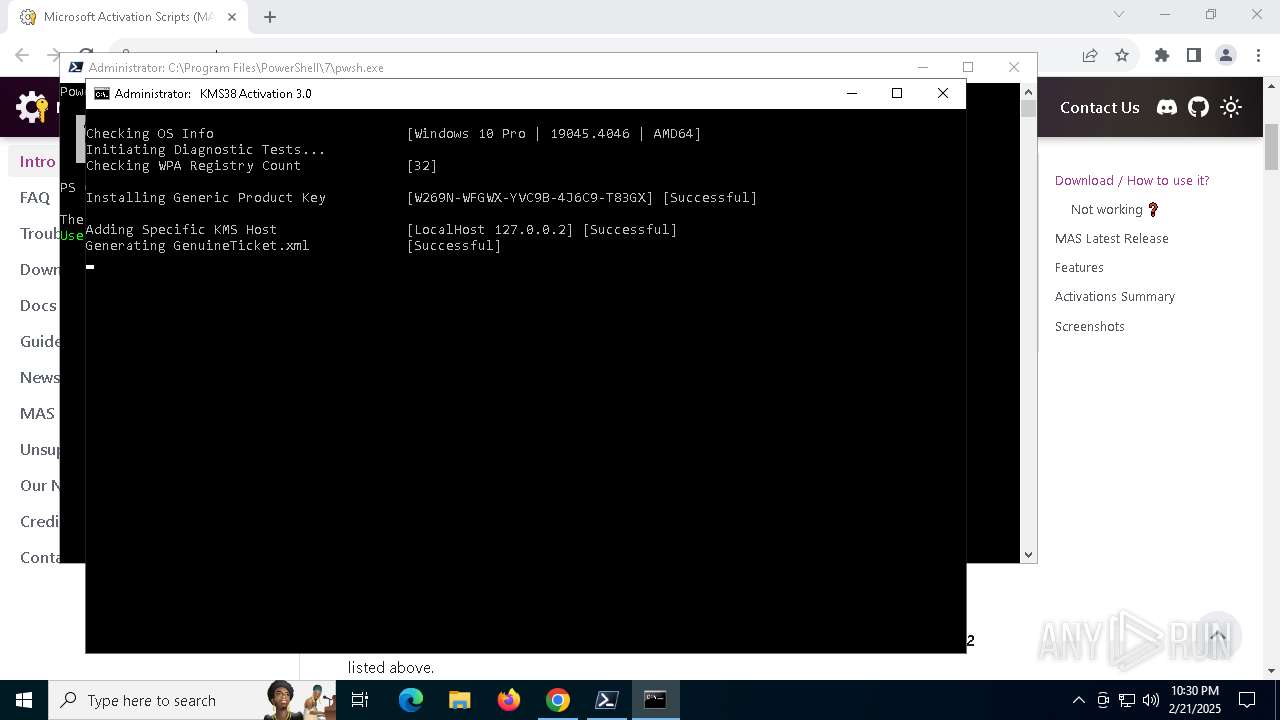
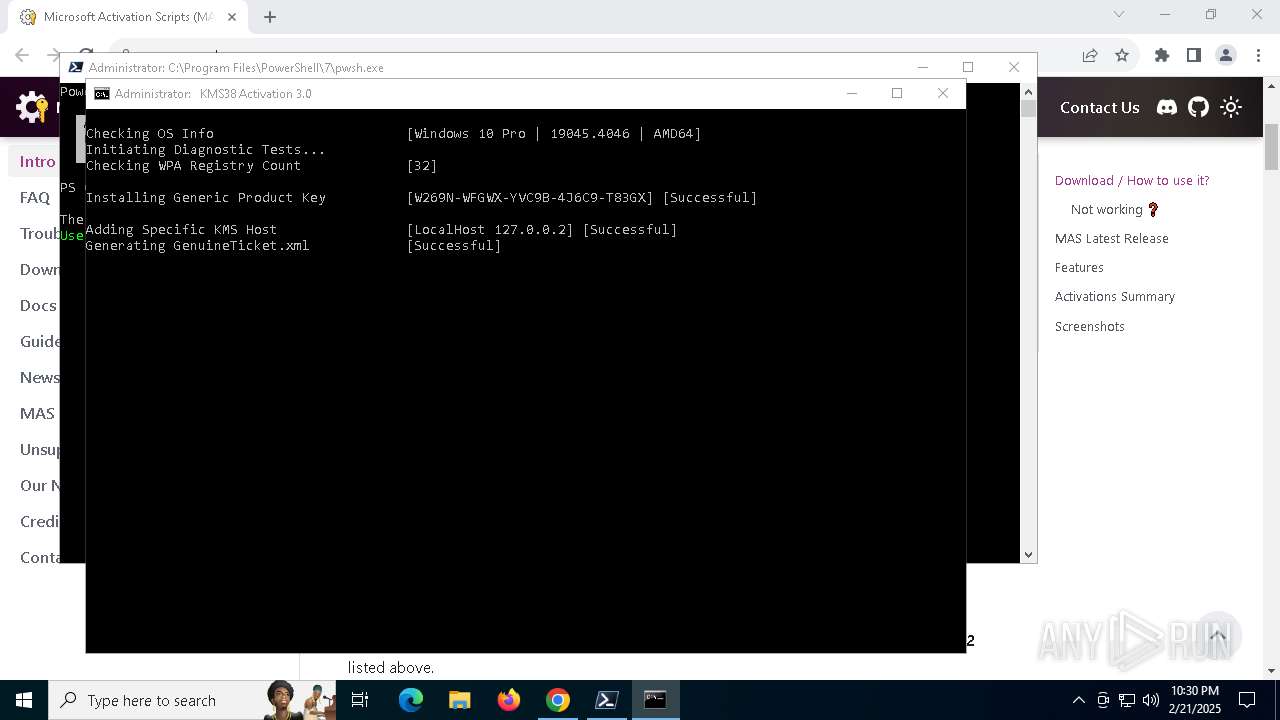
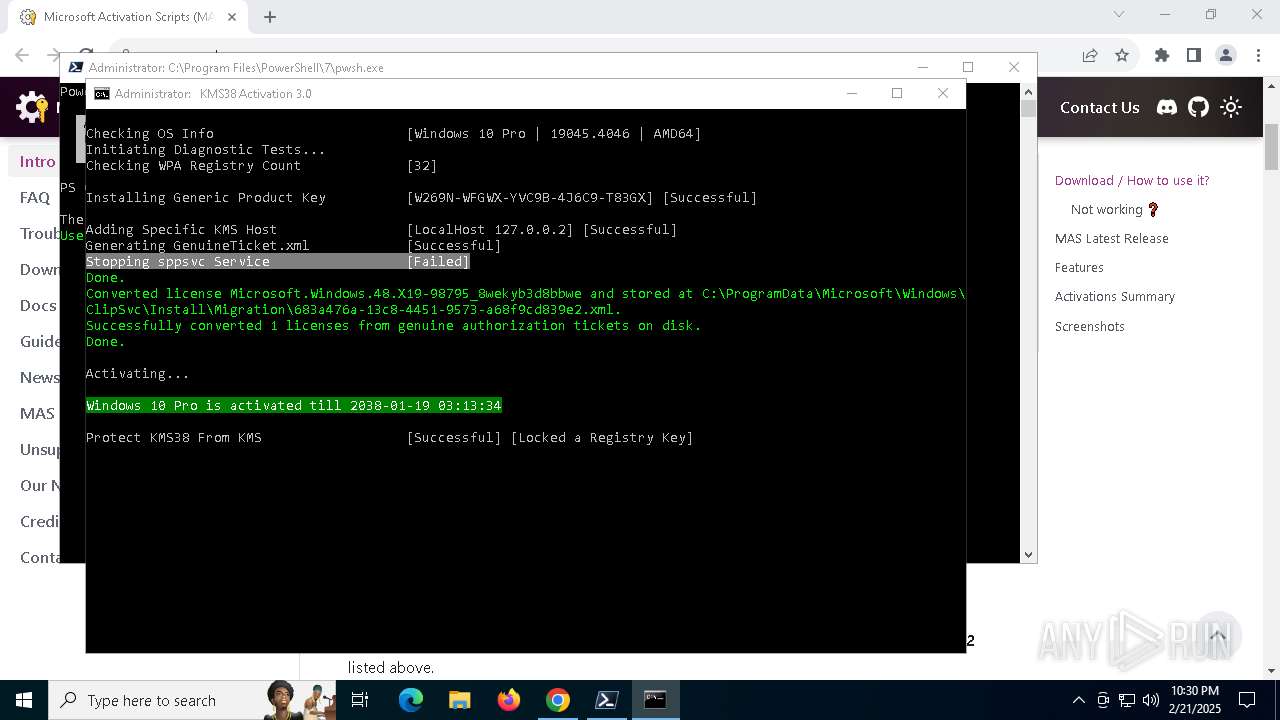
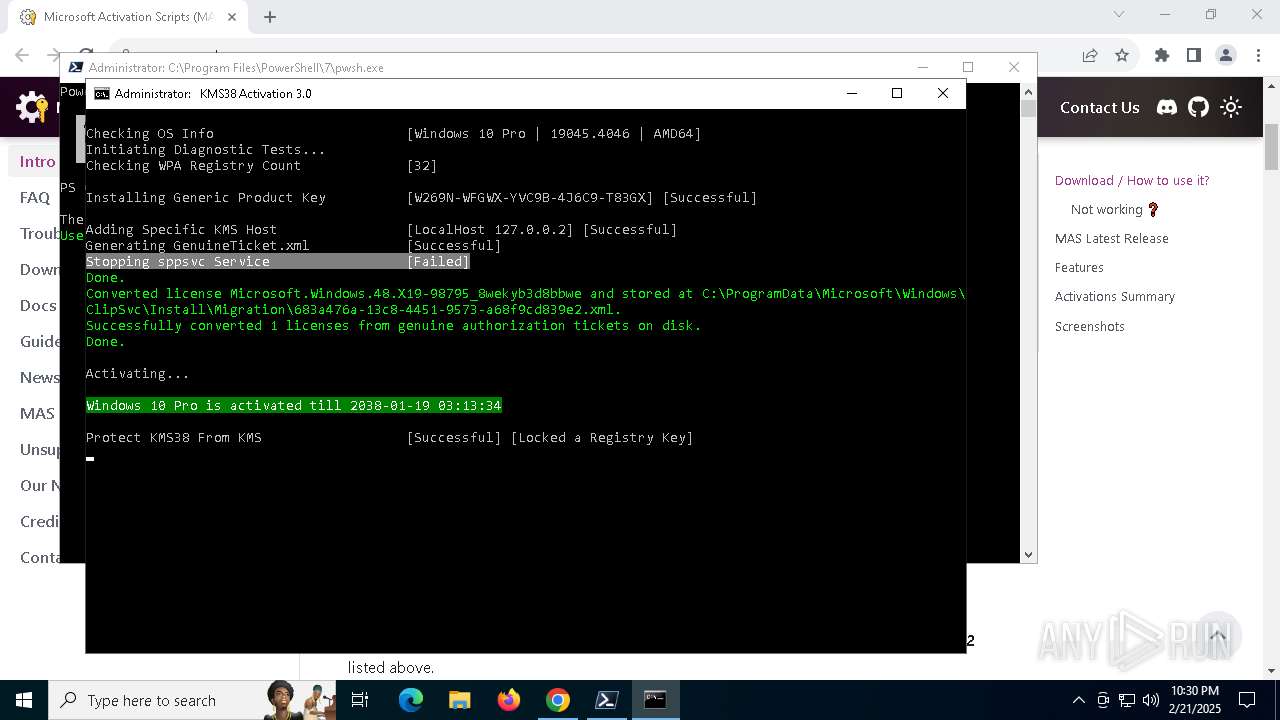
| Verdict: | Malicious activity |
| Analysis date: | February 21, 2025, 22:27:57 |
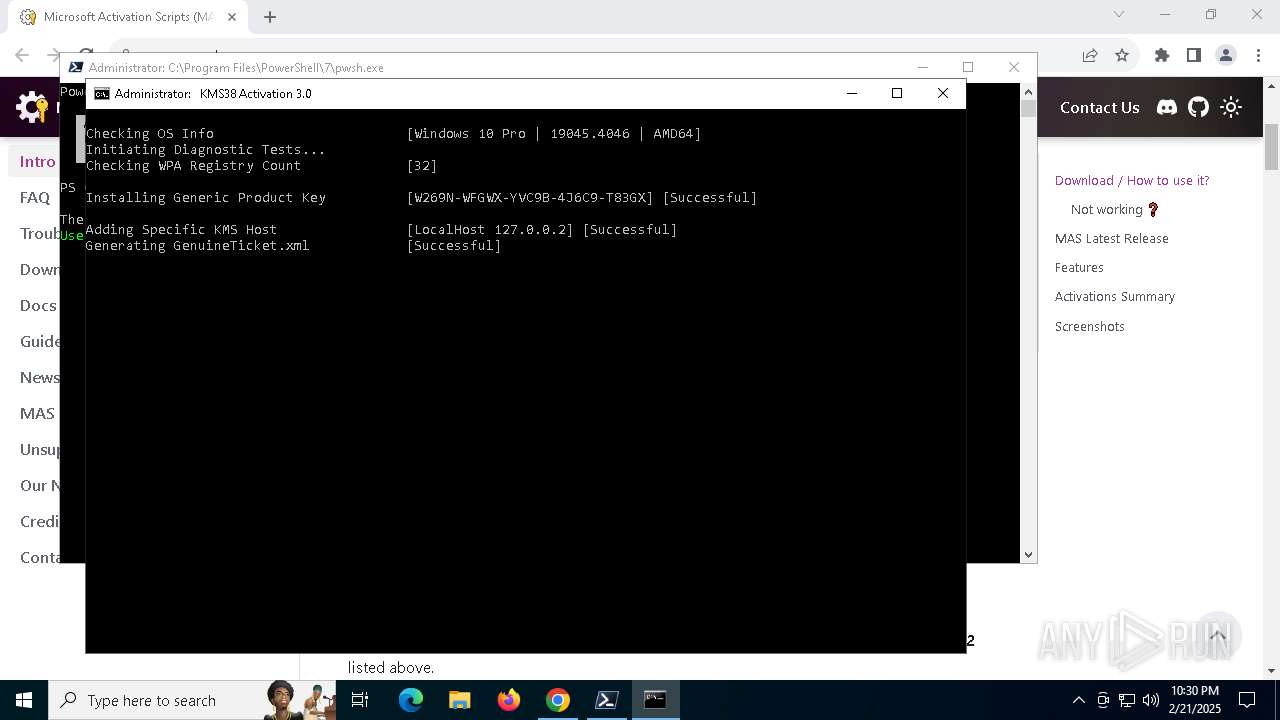
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 5C95876F594CFFB1178B8861F8C741E0 |
| SHA1: | 4F3DD1555BACB0851AD877F9B40BD8DCC884A71D |
| SHA256: | 6019AF861964CFB41AE5A5FE576ACA4521AFBA41255E5C636B1F53DFA0B6BE7F |
| SSDEEP: | 3:N8a0Kn:2a0K |
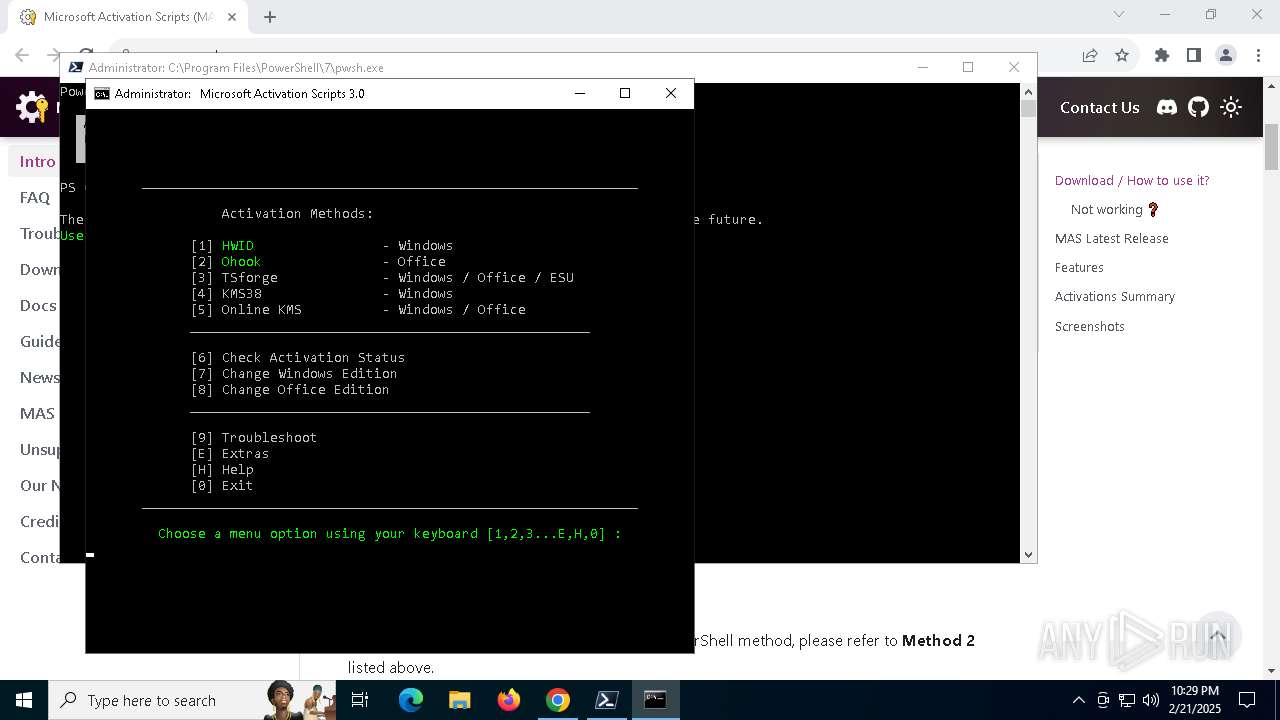
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads the date of Windows installation
- pwsh.exe (PID: 7208)
The process executes via Task Scheduler
- pwsh.exe (PID: 7208)
Executing commands from ".cmd" file
- pwsh.exe (PID: 7208)
- cmd.exe (PID: 7700)
- cmd.exe (PID: 7060)
- powershell.exe (PID: 4984)
Starts SC.EXE for service management
- cmd.exe (PID: 7700)
- cmd.exe (PID: 7060)
Windows service management via SC.EXE
- sc.exe (PID: 7760)
- sc.exe (PID: 7320)
- sc.exe (PID: 7540)
- sc.exe (PID: 7788)
- sc.exe (PID: 836)
- sc.exe (PID: 5556)
- sc.exe (PID: 3824)
- sc.exe (PID: 3416)
- sc.exe (PID: 7400)
- sc.exe (PID: 5912)
- sc.exe (PID: 7504)
- sc.exe (PID: 7036)
- sc.exe (PID: 6424)
- sc.exe (PID: 6856)
- sc.exe (PID: 1344)
- sc.exe (PID: 5036)
- sc.exe (PID: 4668)
- sc.exe (PID: 6416)
- sc.exe (PID: 2420)
- sc.exe (PID: 1744)
- sc.exe (PID: 7692)
- sc.exe (PID: 7764)
- sc.exe (PID: 5236)
- sc.exe (PID: 5748)
- sc.exe (PID: 3620)
- sc.exe (PID: 6156)
- sc.exe (PID: 4624)
Starts CMD.EXE for commands execution
- pwsh.exe (PID: 7208)
- cmd.exe (PID: 7920)
- cmd.exe (PID: 7700)
- cmd.exe (PID: 1804)
- powershell.exe (PID: 4984)
- cmd.exe (PID: 7060)
- cmd.exe (PID: 8172)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 7700)
- cmd.exe (PID: 7060)
Application launched itself
- cmd.exe (PID: 7920)
- cmd.exe (PID: 7700)
- cmd.exe (PID: 1804)
- cmd.exe (PID: 8172)
- cmd.exe (PID: 7060)
- powershell.exe (PID: 7812)
- powershell.exe (PID: 4952)
- powershell.exe (PID: 7580)
- ClipUp.exe (PID: 1304)
- powershell.exe (PID: 5320)
Uses sleep to delay execution (POWERSHELL)
- powershell.exe (PID: 8052)
- powershell.exe (PID: 2008)
- powershell.exe (PID: 7088)
- powershell.exe (PID: 7832)
- powershell.exe (PID: 6160)
Gets content of a file (POWERSHELL)
- powershell.exe (PID: 8052)
- powershell.exe (PID: 2008)
- powershell.exe (PID: 7088)
- powershell.exe (PID: 7832)
- powershell.exe (PID: 6160)
Uses base64 encoding (POWERSHELL)
- powershell.exe (PID: 8052)
- powershell.exe (PID: 2008)
- powershell.exe (PID: 7088)
- powershell.exe (PID: 7832)
- powershell.exe (PID: 6160)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 7700)
- cmd.exe (PID: 8020)
- cmd.exe (PID: 5696)
- cmd.exe (PID: 7060)
- cmd.exe (PID: 7332)
- cmd.exe (PID: 6032)
- powershell.exe (PID: 7812)
- cmd.exe (PID: 7780)
- powershell.exe (PID: 4952)
- cmd.exe (PID: 4300)
- cmd.exe (PID: 3172)
- powershell.exe (PID: 7580)
- cmd.exe (PID: 2972)
- powershell.exe (PID: 5320)
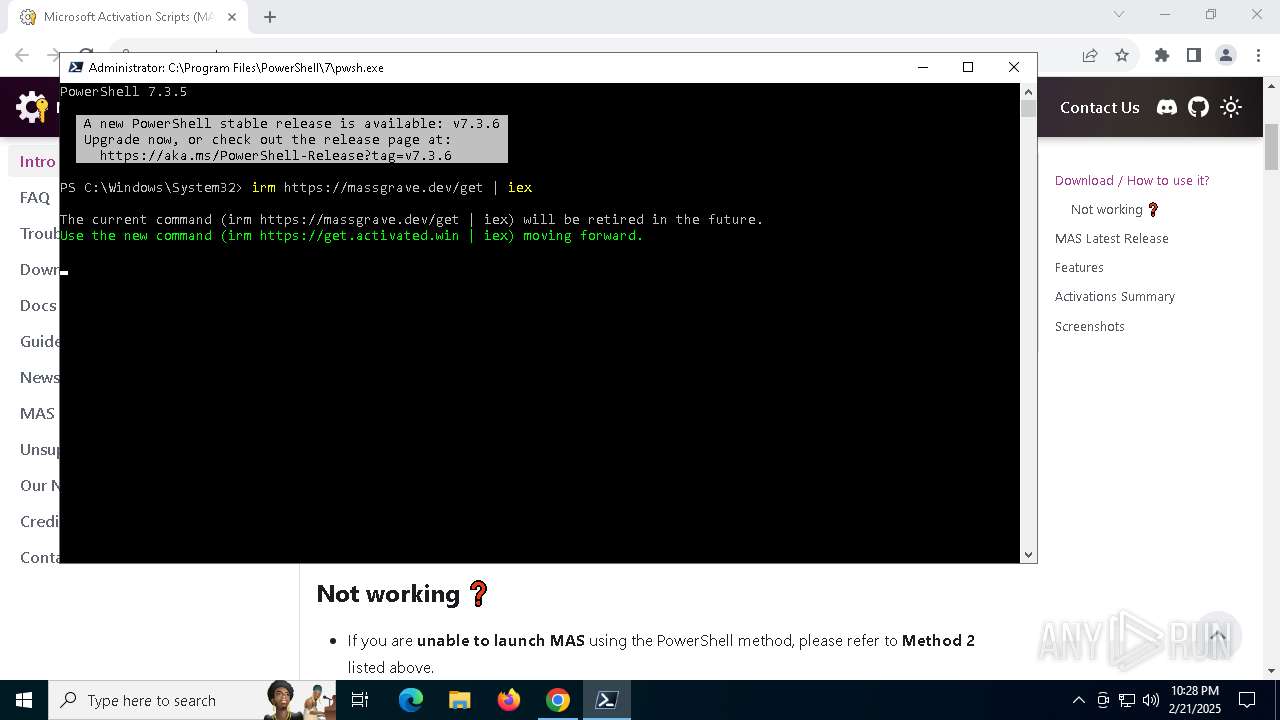
Probably obfuscated PowerShell command line is found
- cmd.exe (PID: 8020)
- cmd.exe (PID: 5696)
- cmd.exe (PID: 7060)
- cmd.exe (PID: 7780)
Possibly malicious use of IEX has been detected
- cmd.exe (PID: 8020)
- cmd.exe (PID: 5696)
- cmd.exe (PID: 7060)
- cmd.exe (PID: 7780)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 7060)
Uses WMIC.EXE to obtain computer system information
- cmd.exe (PID: 6076)
- cmd.exe (PID: 7060)
Hides command output
- cmd.exe (PID: 2572)
- cmd.exe (PID: 3928)
- cmd.exe (PID: 7780)
- cmd.exe (PID: 8056)
- cmd.exe (PID: 4824)
- cmd.exe (PID: 7408)
- cmd.exe (PID: 7320)
- cmd.exe (PID: 4300)
- cmd.exe (PID: 5748)
- cmd.exe (PID: 6156)
- cmd.exe (PID: 5592)
- cmd.exe (PID: 3172)
- cmd.exe (PID: 1348)
Uses WMIC.EXE to obtain operating system information
- cmd.exe (PID: 2572)
The process bypasses the loading of PowerShell profile settings
- powershell.exe (PID: 7812)
- powershell.exe (PID: 4952)
- powershell.exe (PID: 7580)
- powershell.exe (PID: 5320)
The process hides Powershell's copyright startup banner
- powershell.exe (PID: 7812)
- powershell.exe (PID: 4952)
- powershell.exe (PID: 7580)
- powershell.exe (PID: 5320)
Uses WMIC.EXE to obtain Windows Installer data
- cmd.exe (PID: 7060)
- cmd.exe (PID: 4824)
- cmd.exe (PID: 8056)
- cmd.exe (PID: 5592)
- cmd.exe (PID: 5748)
- cmd.exe (PID: 6156)
- cmd.exe (PID: 1348)
Uses WMIC.EXE to obtain service application data
- cmd.exe (PID: 7060)
Executes application which crashes
- powershell.exe (PID: 7752)
- powershell.exe (PID: 8160)
The process creates files with name similar to system file names
- WerFault.exe (PID: 7408)
- WerFault.exe (PID: 5256)
Uses TIMEOUT.EXE to delay execution
- cmd.exe (PID: 7060)
INFO
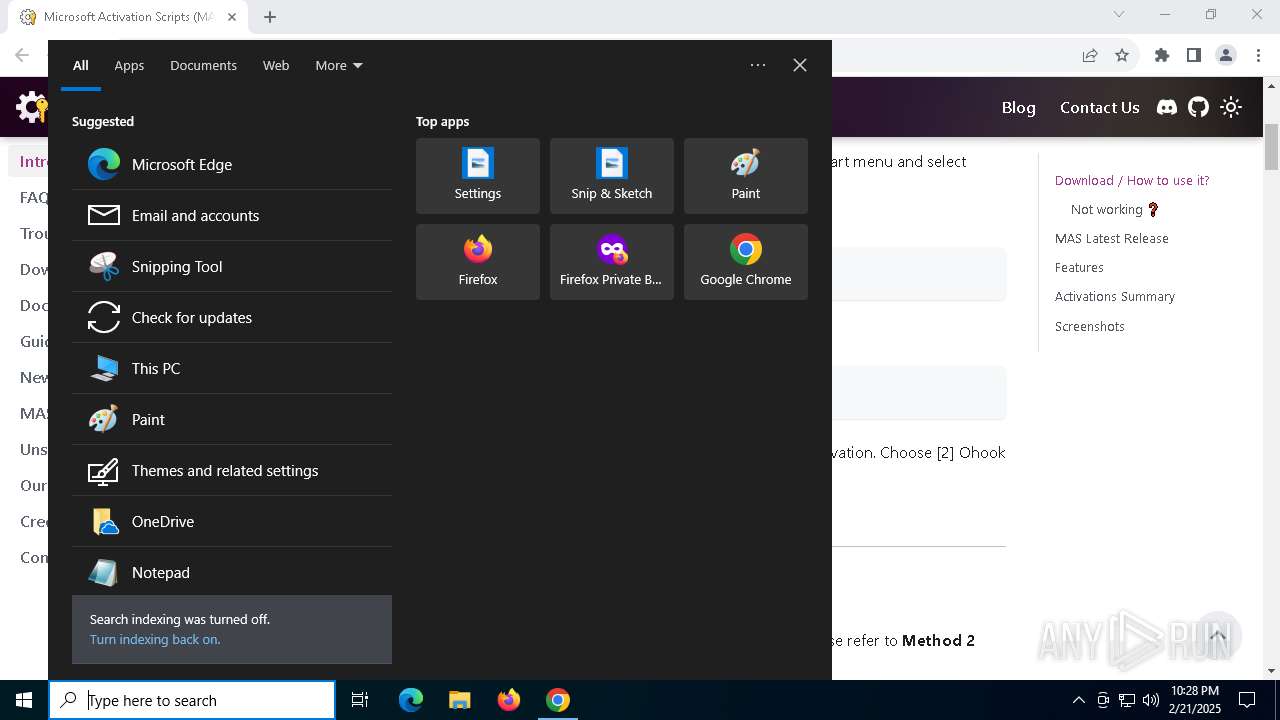
Checks supported languages
- pwsh.exe (PID: 7208)
- mode.com (PID: 7860)
- mode.com (PID: 5268)
- mode.com (PID: 6676)
Process checks computer location settings
- pwsh.exe (PID: 7208)
Reads the computer name
- pwsh.exe (PID: 7208)
Checks operating system version
- cmd.exe (PID: 7700)
- cmd.exe (PID: 7060)
Converts byte array into ASCII string (POWERSHELL)
- powershell.exe (PID: 8052)
- powershell.exe (PID: 2008)
- powershell.exe (PID: 7088)
- powershell.exe (PID: 7832)
- powershell.exe (PID: 6160)
Checks whether the specified file exists (POWERSHELL)
- powershell.exe (PID: 8052)
- powershell.exe (PID: 2008)
- powershell.exe (PID: 7088)
- powershell.exe (PID: 7832)
- powershell.exe (PID: 6160)
Gets a random number, or selects objects randomly from a collection (POWERSHELL)
- powershell.exe (PID: 8052)
- powershell.exe (PID: 2008)
- powershell.exe (PID: 7088)
- powershell.exe (PID: 7832)
- powershell.exe (PID: 6160)
Application launched itself
- chrome.exe (PID: 6280)
Creates a byte array (POWERSHELL)
- powershell.exe (PID: 2008)
- powershell.exe (PID: 7088)
- powershell.exe (PID: 8052)
- powershell.exe (PID: 7832)
- powershell.exe (PID: 6160)
Starts MODE.COM to configure console settings
- mode.com (PID: 7860)
- mode.com (PID: 5268)
- mode.com (PID: 6676)
Reads security settings of Internet Explorer
- WMIC.exe (PID: 2432)
- WMIC.exe (PID: 7176)
- WMIC.exe (PID: 7064)
- WMIC.exe (PID: 8108)
- WMIC.exe (PID: 4500)
- WMIC.exe (PID: 4392)
- WMIC.exe (PID: 2632)
- WMIC.exe (PID: 6148)
- WMIC.exe (PID: 4528)
- WMIC.exe (PID: 2092)
- WMIC.exe (PID: 6424)
- WMIC.exe (PID: 4596)
The sample compiled with english language support
- chrome.exe (PID: 6872)
Executable content was dropped or overwritten
- chrome.exe (PID: 6872)
Creates files in the program directory
- cmd.exe (PID: 7060)
- ClipUp.exe (PID: 768)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 7576)
Checks proxy server information
- WerFault.exe (PID: 7408)
- WerFault.exe (PID: 5256)
Reads the software policy settings
- WerFault.exe (PID: 7408)
- WerFault.exe (PID: 5256)
Creates files or folders in the user directory
- WerFault.exe (PID: 7408)
- WerFault.exe (PID: 5256)
Create files in a temporary directory
- ClipUp.exe (PID: 768)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
420
Monitored processes
275
Malicious processes
4
Suspicious processes
14
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 396 | reg query "HKLM\SOFTWARE\Microsoft\Windows\CurrentVersion\Setup\State" /v ImageState | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 488 | find /i "2de67392-b7a7-462a-b1ca-108dd189f588" | C:\Windows\System32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (grep) Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 556 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 736 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 768 | clipup -v -o -ppl C:\Users\admin\AppData\Local\Temp\tem9D82.tmp | C:\Windows\System32\ClipUp.exe | — | ClipUp.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Client License Platform migration tool Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 836 | sc query KeyIso | C:\Windows\System32\sc.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Service Control Manager Configuration Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1076 | reg query "HKU\S-1-5-20\Software\Microsoft\Windows NT\CurrentVersion\SoftwareProtectionPlatform\Policies" | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1216 | ping -4 -n 1 updatecheck30.activated.win | C:\Windows\System32\PING.EXE | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: TCP/IP Ping Command Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1296 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | ClipUp.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1304 | find /i "Subscription_is_activated" | C:\Windows\System32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (grep) Utility Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
148 812
Read events
148 745
Write events
52
Delete events
15
Modification events
| (PID) Process: | (6280) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (6280) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (6280) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (6280) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (6280) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (6280) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Common\Rlz\Events\C |
| Operation: | write | Name: | C1I |
Value: 1 | |||
| (PID) Process: | (6280) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Common\Rlz\Events\C |
| Operation: | write | Name: | C2I |
Value: 1 | |||
| (PID) Process: | (6280) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Common\Rlz\Events\C |
| Operation: | write | Name: | C7I |
Value: 1 | |||
| (PID) Process: | (6280) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Common\Rlz\Events\C |
| Operation: | write | Name: | C1S |
Value: 1 | |||
| (PID) Process: | (6280) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Common\Rlz\Events\C |
| Operation: | write | Name: | C7S |
Value: 1 | |||
Executable files
5
Suspicious files
116
Text files
92
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6280 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF13697b.TMP | — | |
MD5:— | SHA256:— | |||
| 6280 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old~RF13697b.TMP | — | |
MD5:— | SHA256:— | |||
| 6280 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6280 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6280 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old~RF13698b.TMP | — | |
MD5:— | SHA256:— | |||
| 6280 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old~RF13698b.TMP | — | |
MD5:— | SHA256:— | |||
| 6280 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6280 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6280 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old~RF13698b.TMP | — | |
MD5:— | SHA256:— | |||
| 6280 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old~RF13698b.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
27
TCP/UDP connections
72
DNS requests
59
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.48.23.177:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
— | — | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
1176 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
4824 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
3564 | backgroundTaskHost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
4824 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
7208 | pwsh.exe | GET | 200 | 23.48.23.140:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
7896 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/imoffpf67hel7kbknqflao2oo4_1.0.2738.0/neifaoindggfcjicffkgpmnlppeffabd_1.0.2738.0_win64_kj4dp5kifwxbdodqls7e5nzhtm.crx3 | unknown | — | — | whitelisted |
7896 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/imoffpf67hel7kbknqflao2oo4_1.0.2738.0/neifaoindggfcjicffkgpmnlppeffabd_1.0.2738.0_win64_kj4dp5kifwxbdodqls7e5nzhtm.crx3 | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3220 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 23.48.23.177:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5064 | SearchApp.exe | 104.126.37.144:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
— | — | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
— | — | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
1176 | svchost.exe | 40.126.32.138:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
google.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
login.live.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
massgrave.dev |
| unknown |
accounts.google.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7208 | pwsh.exe | Not Suspicious Traffic | INFO [ANY.RUN] Azure Front Door domain observed in TLS SNI ( .azurefd .net) |
2192 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |