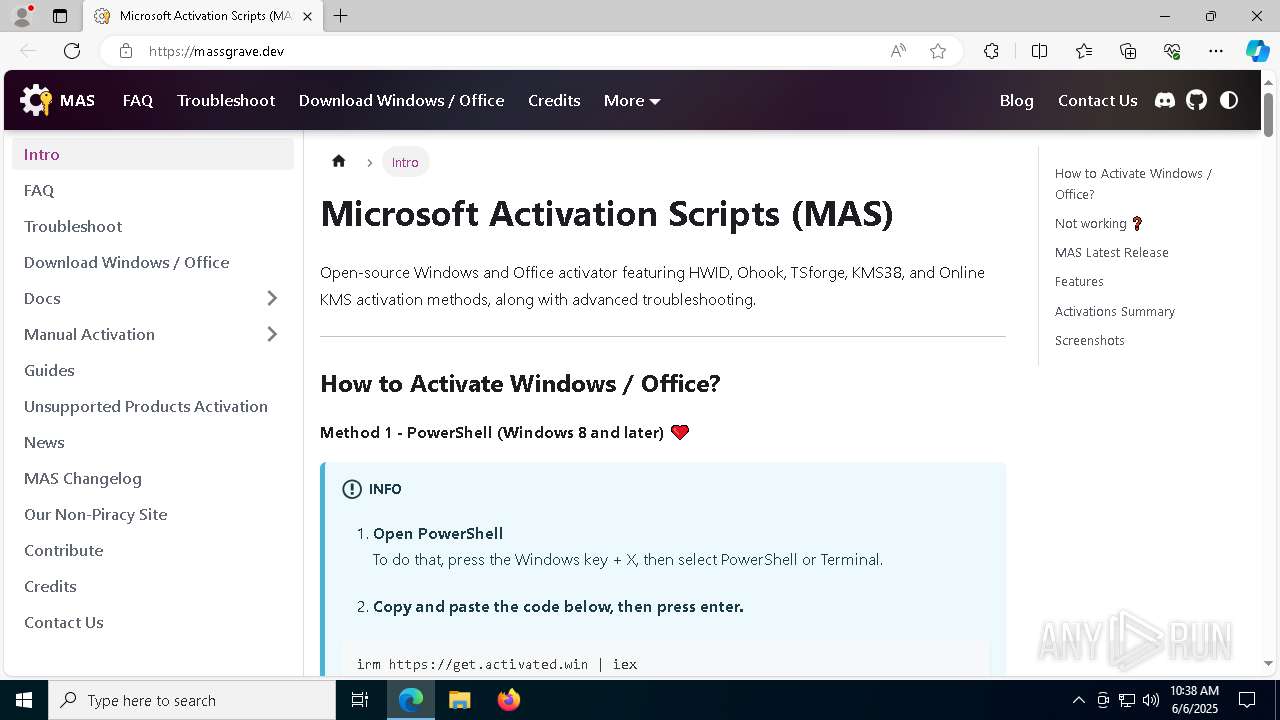
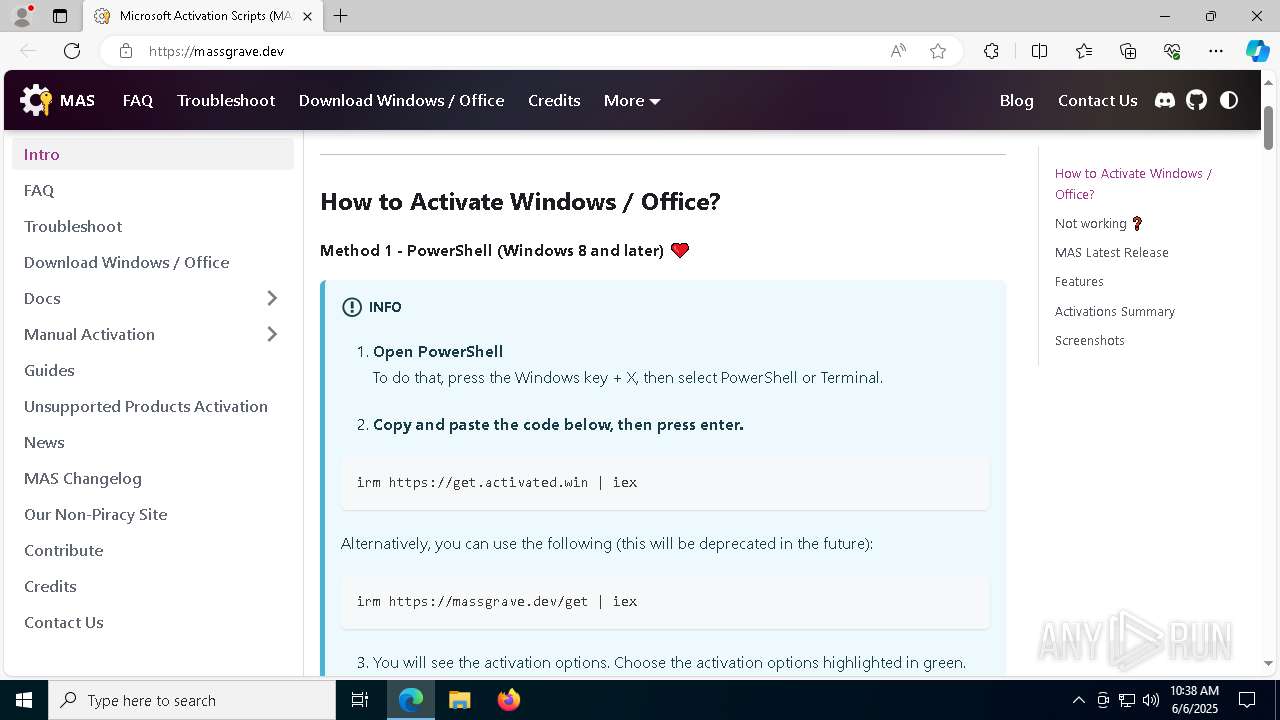
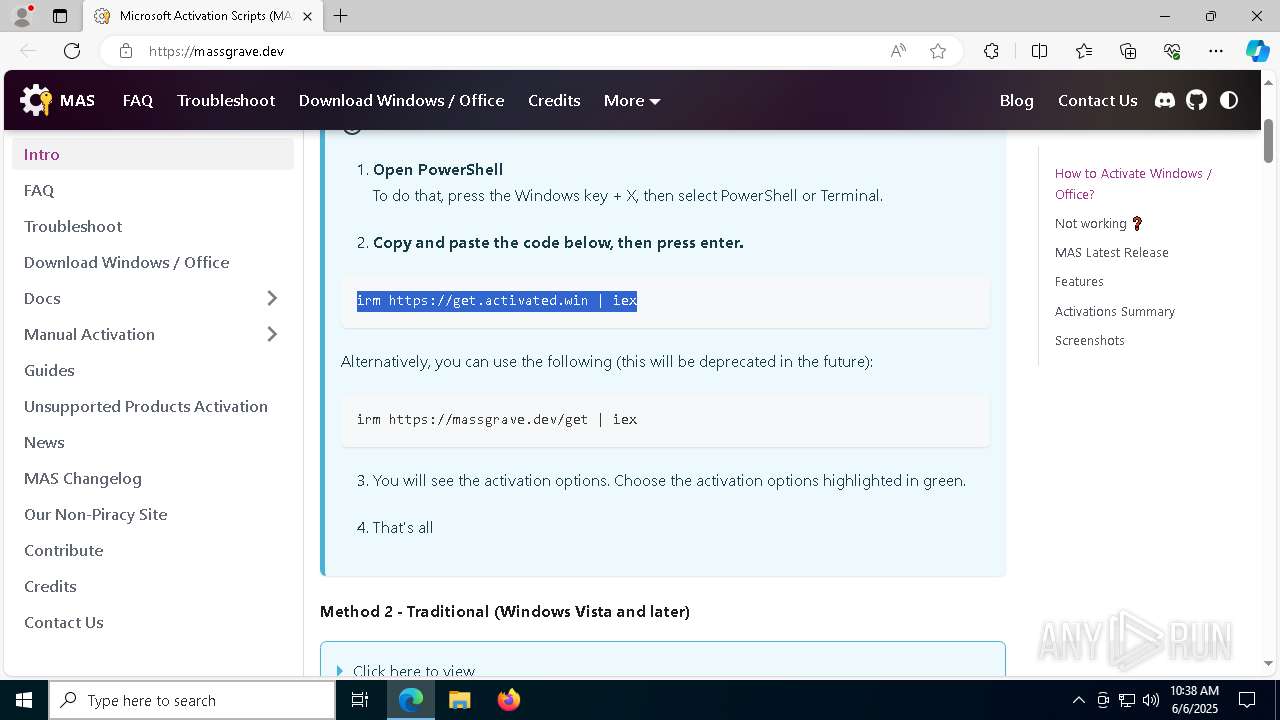
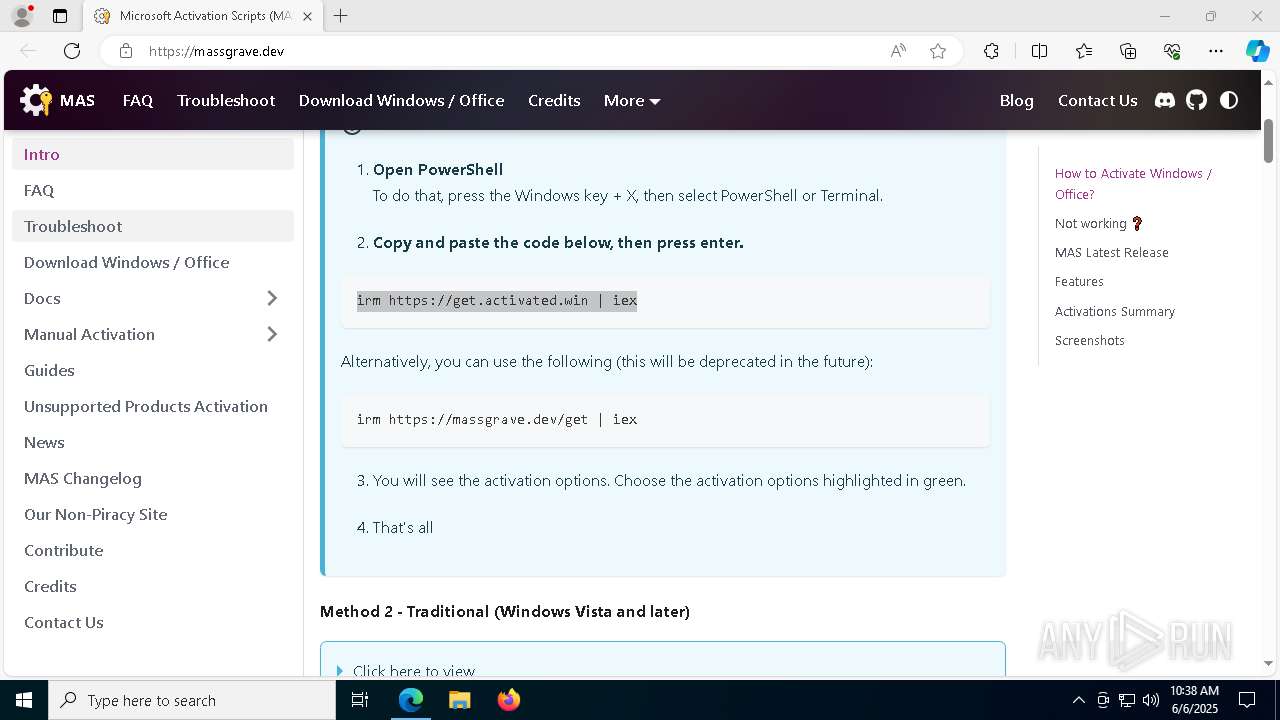
| URL: | https://massgrave.dev/ |
| Full analysis: | https://app.any.run/tasks/b2f28de2-415f-4b8d-b4bc-dfef0fe084f4 |
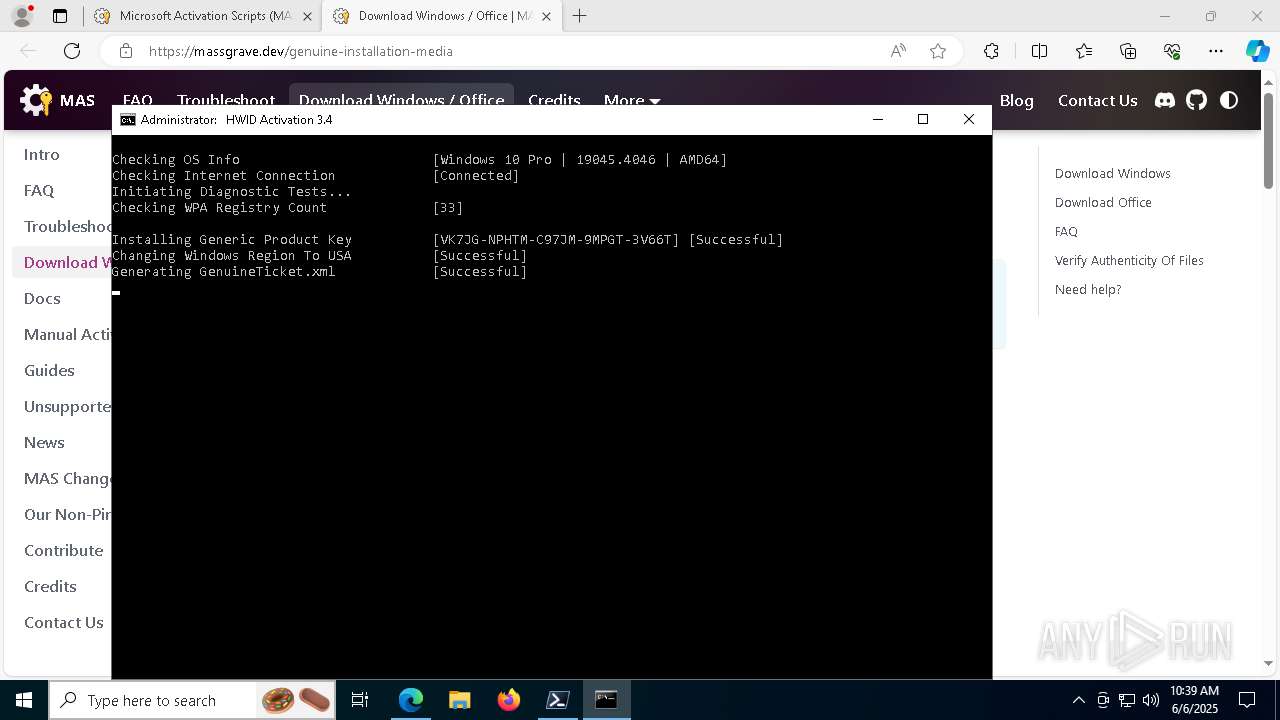
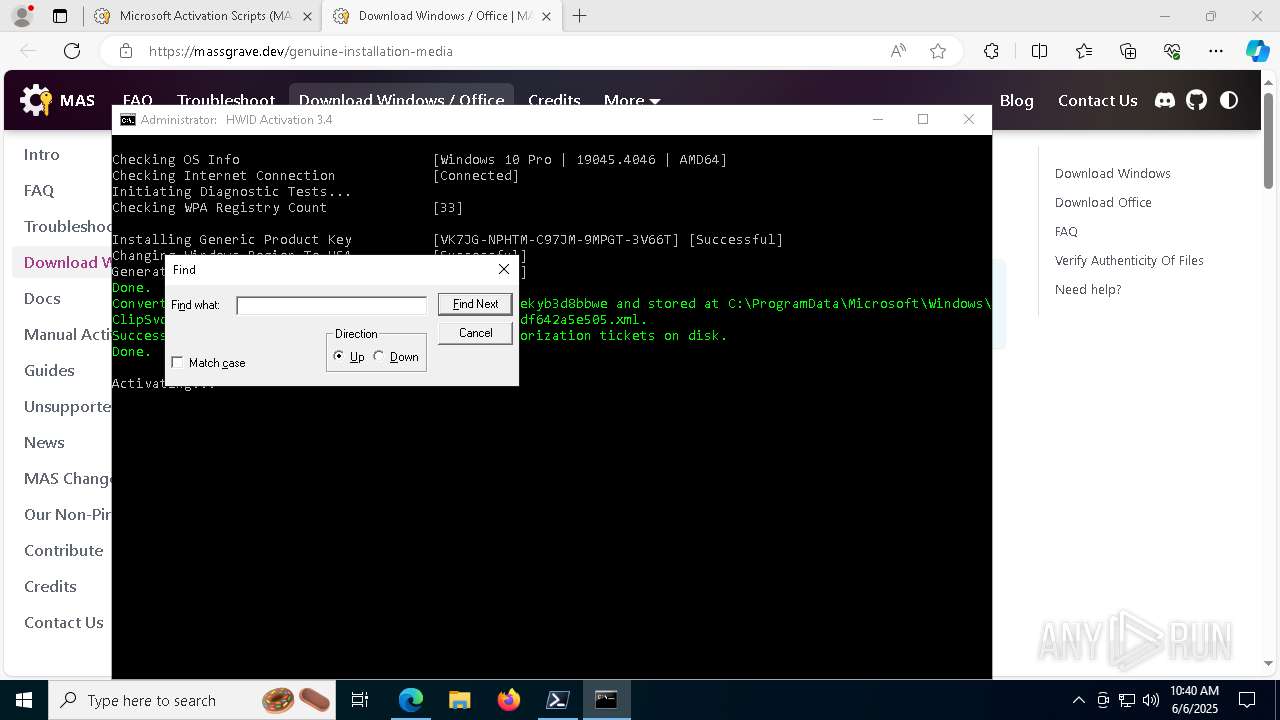
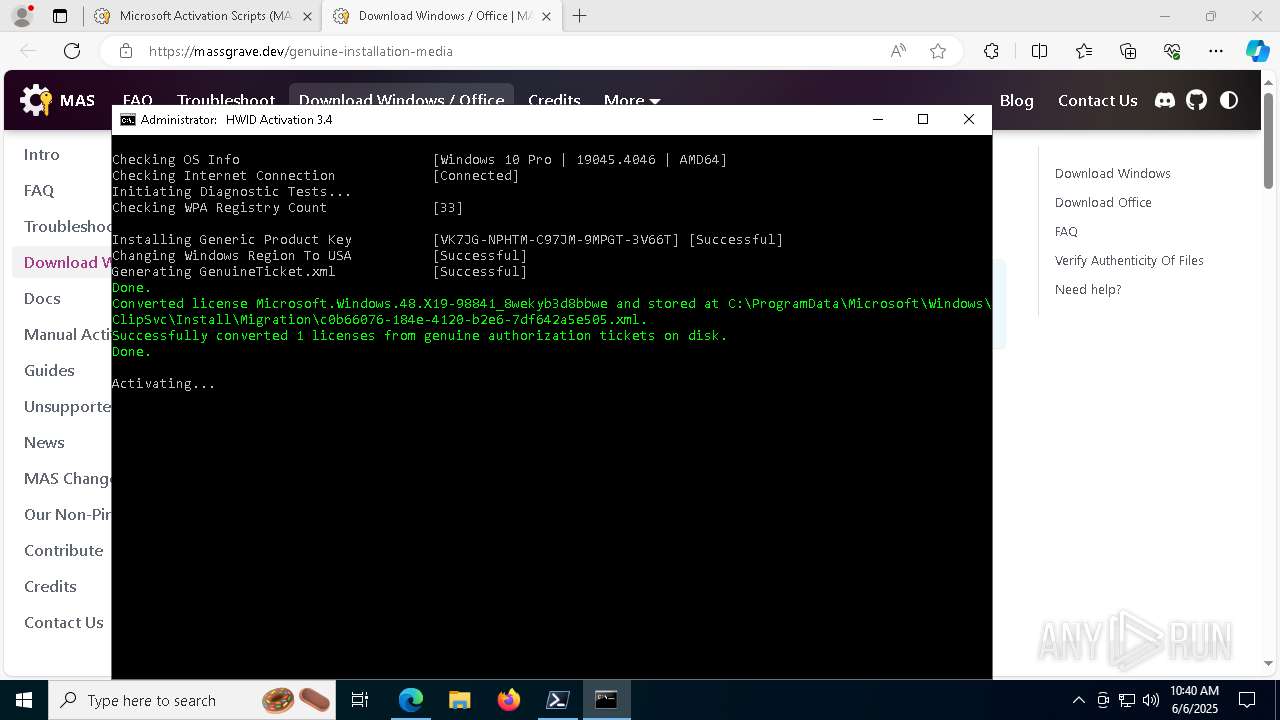
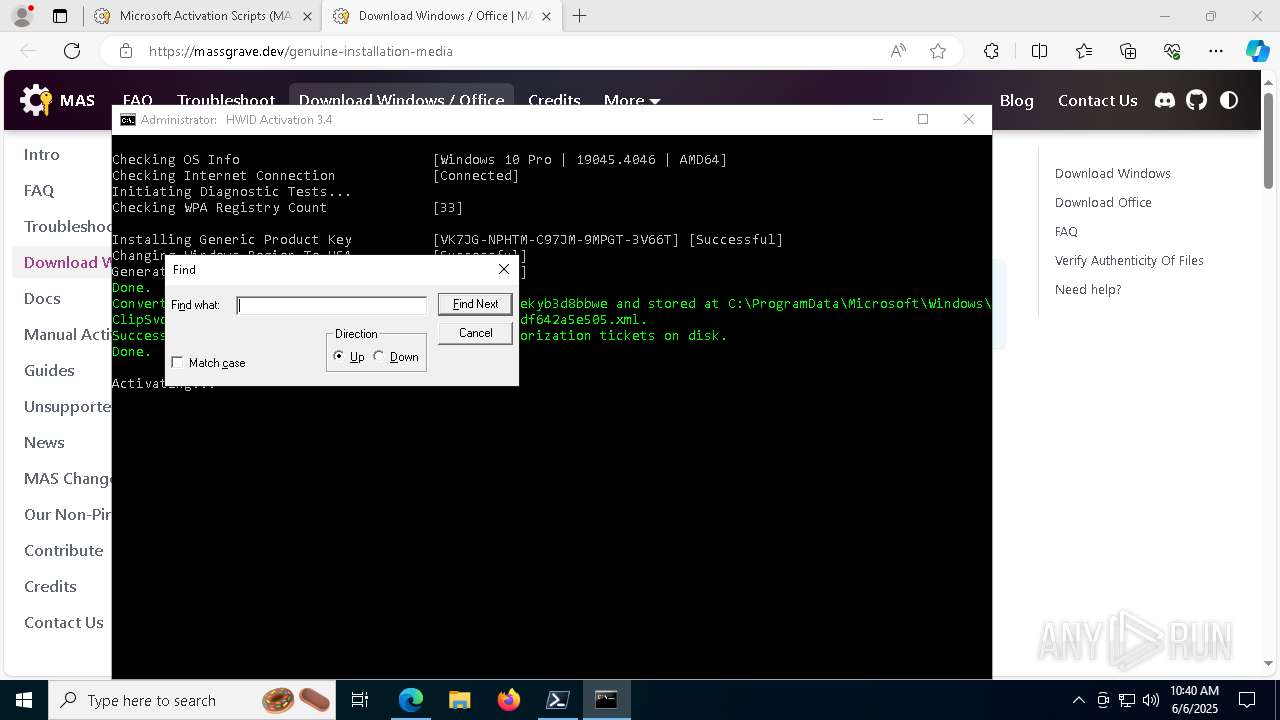
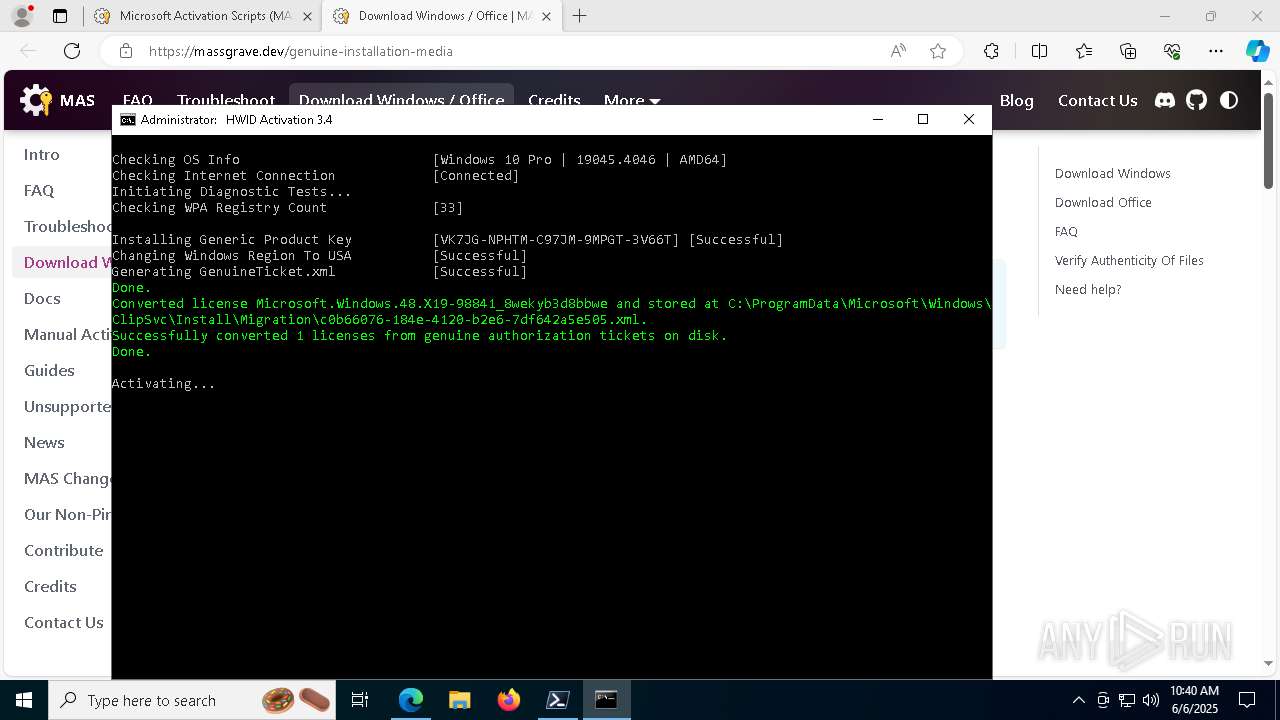
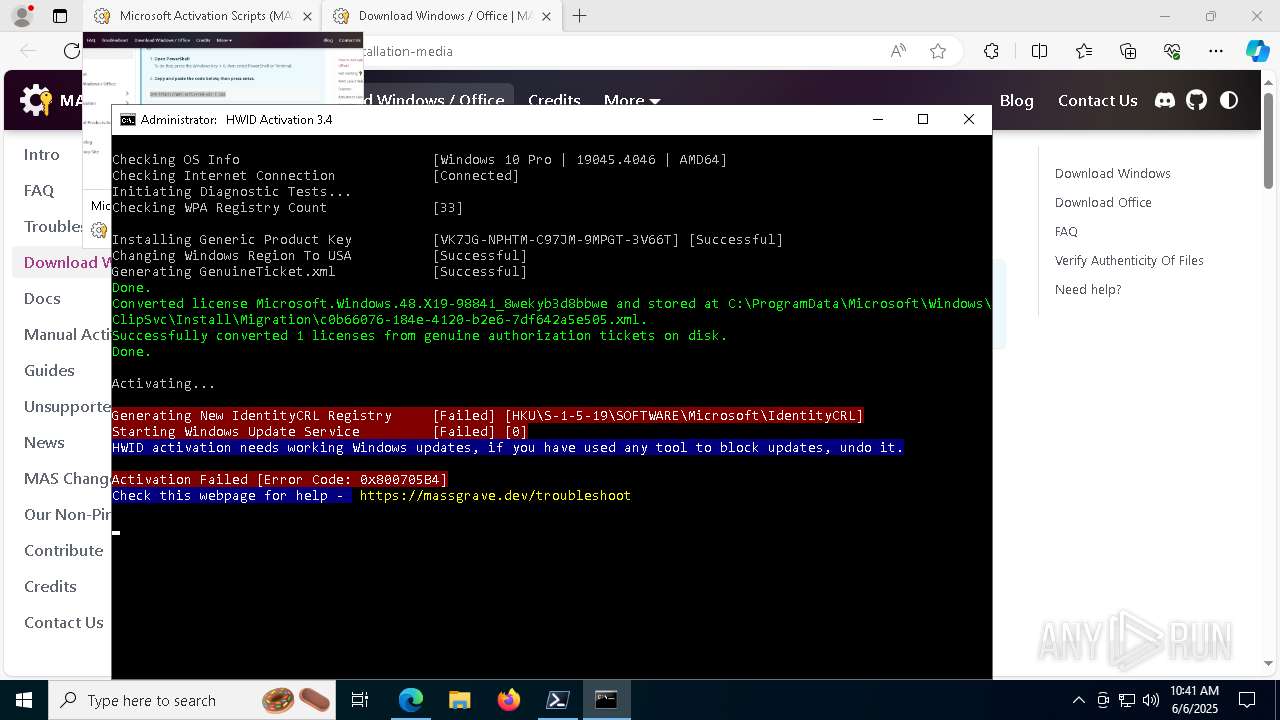
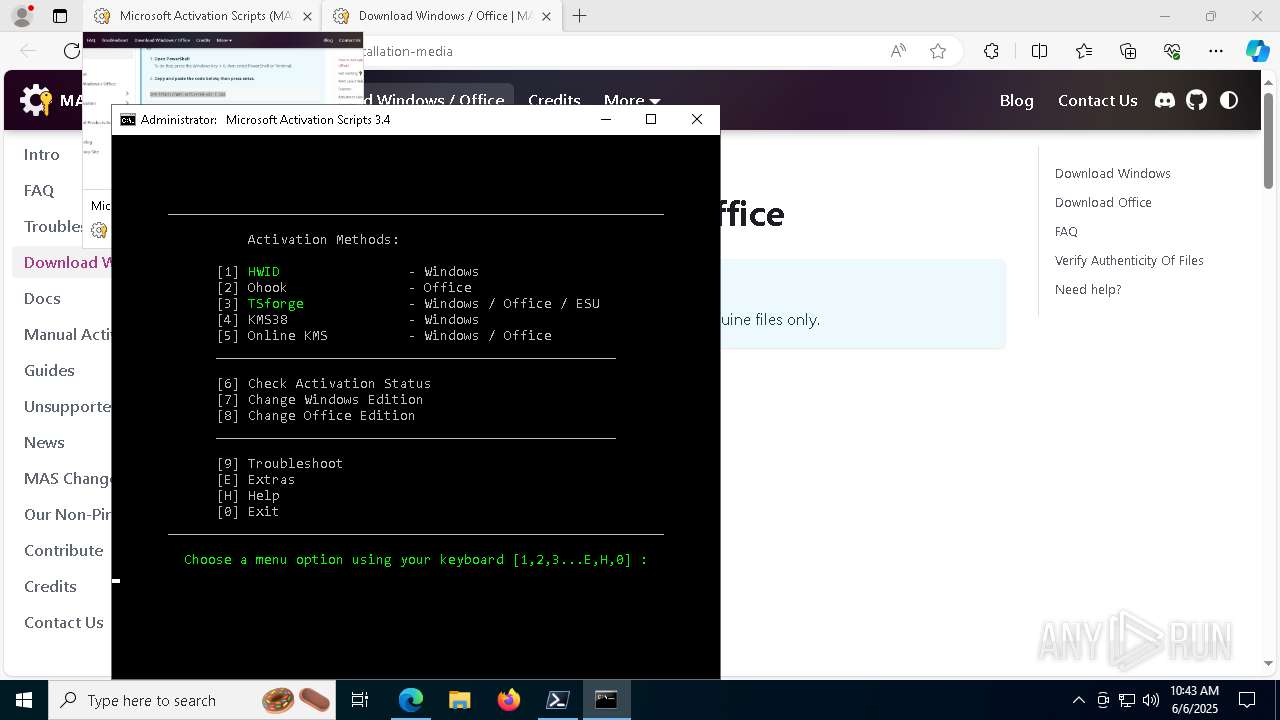
| Verdict: | Malicious activity |
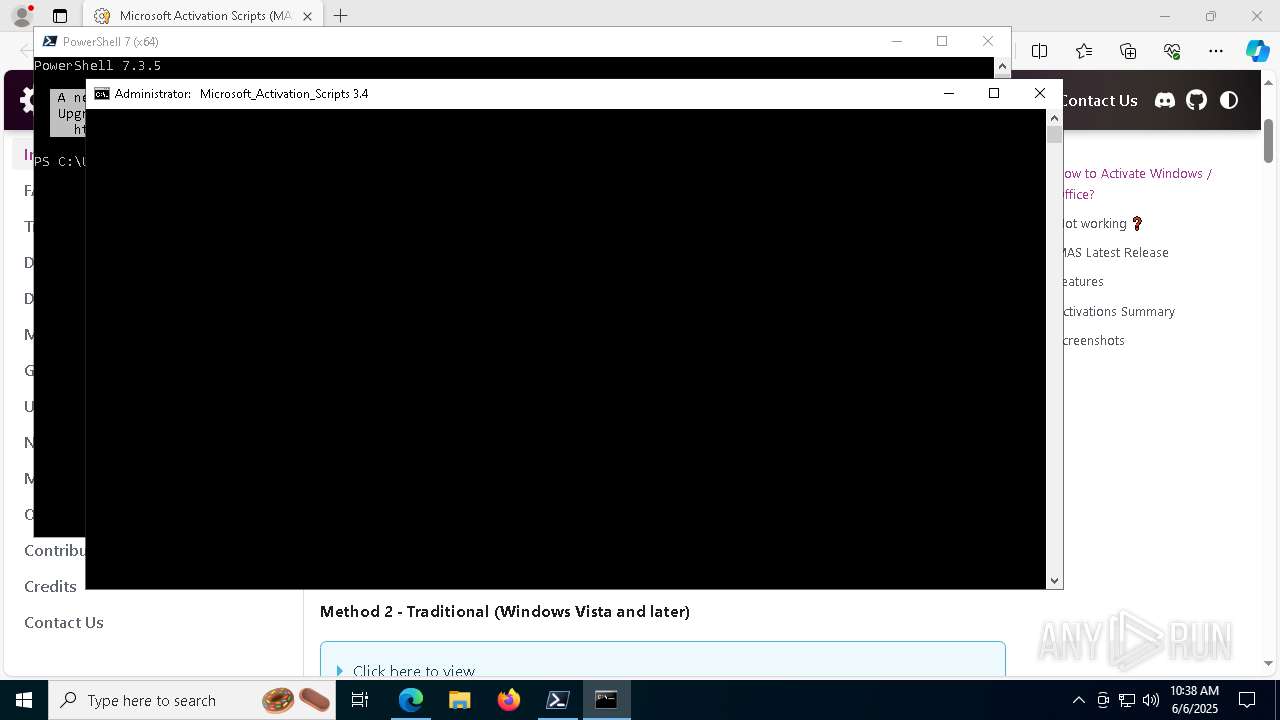
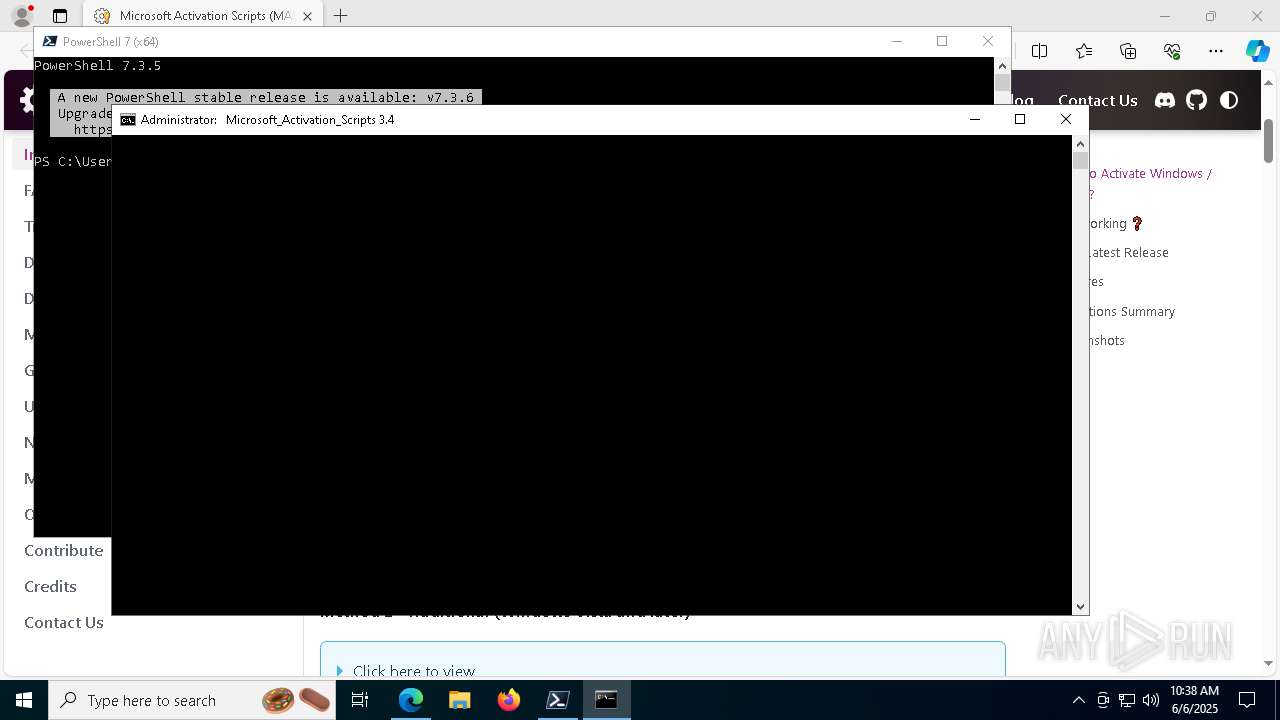
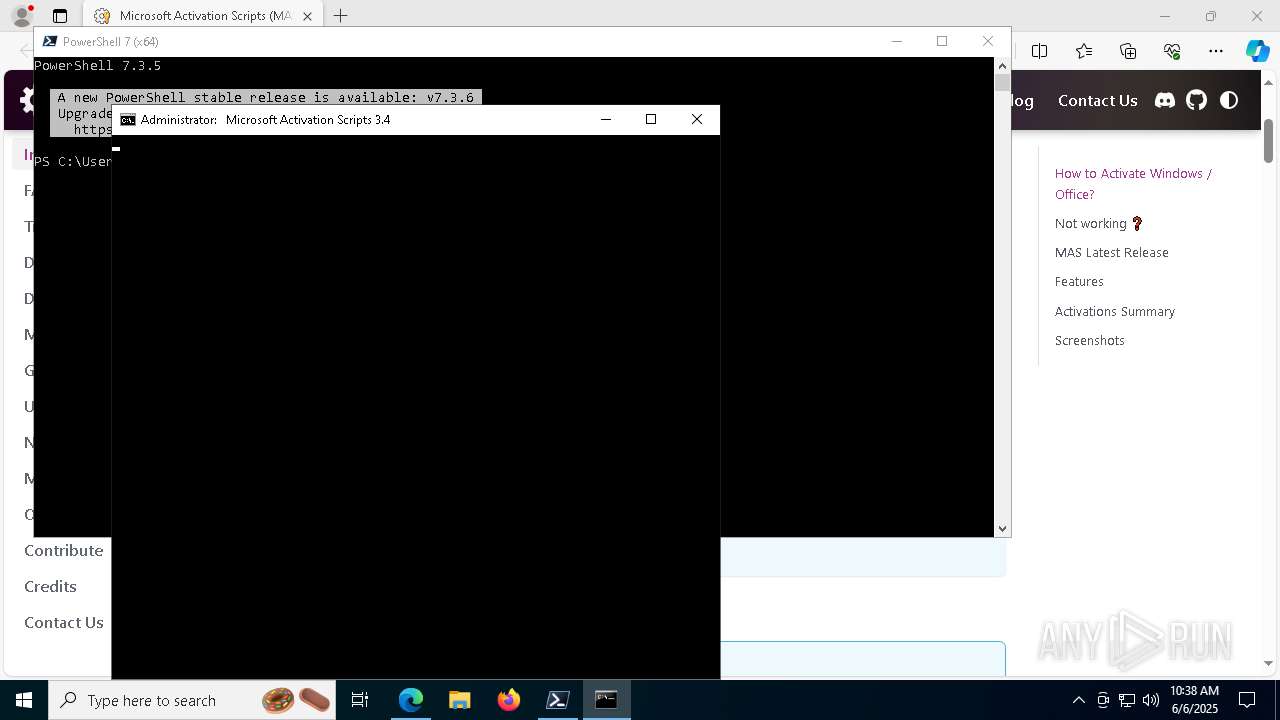
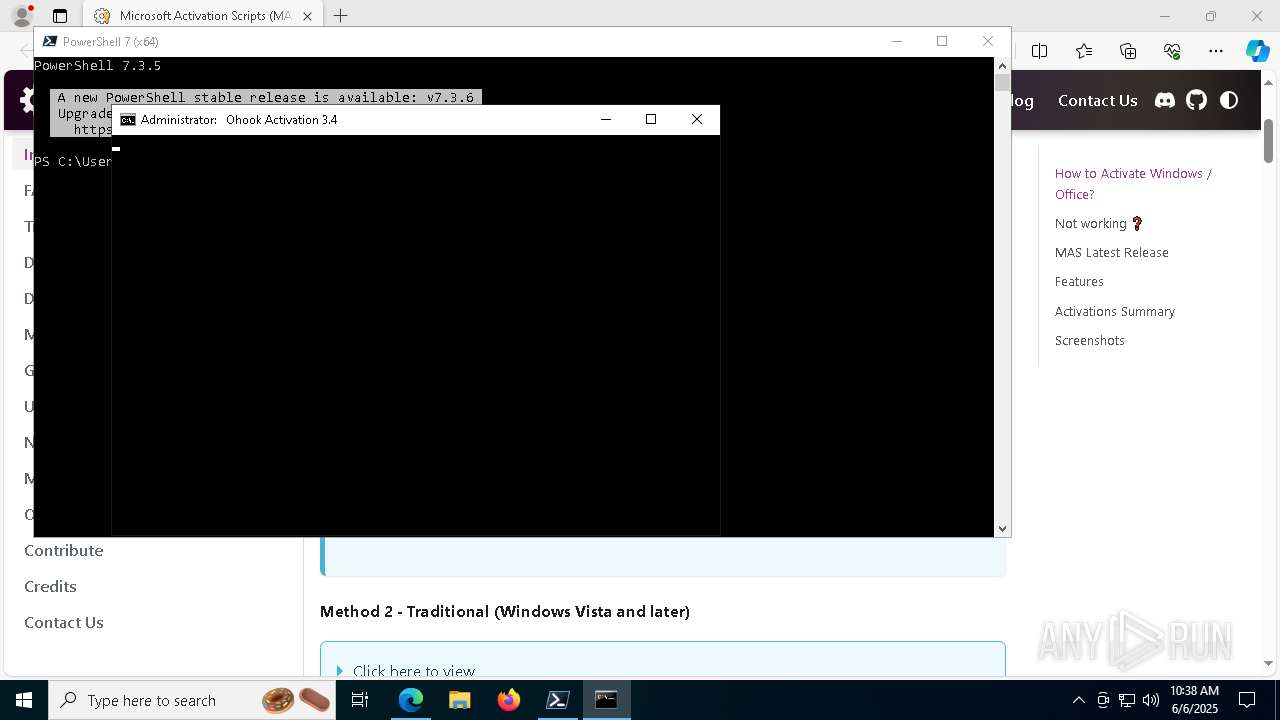
| Analysis date: | June 06, 2025, 10:38:02 |
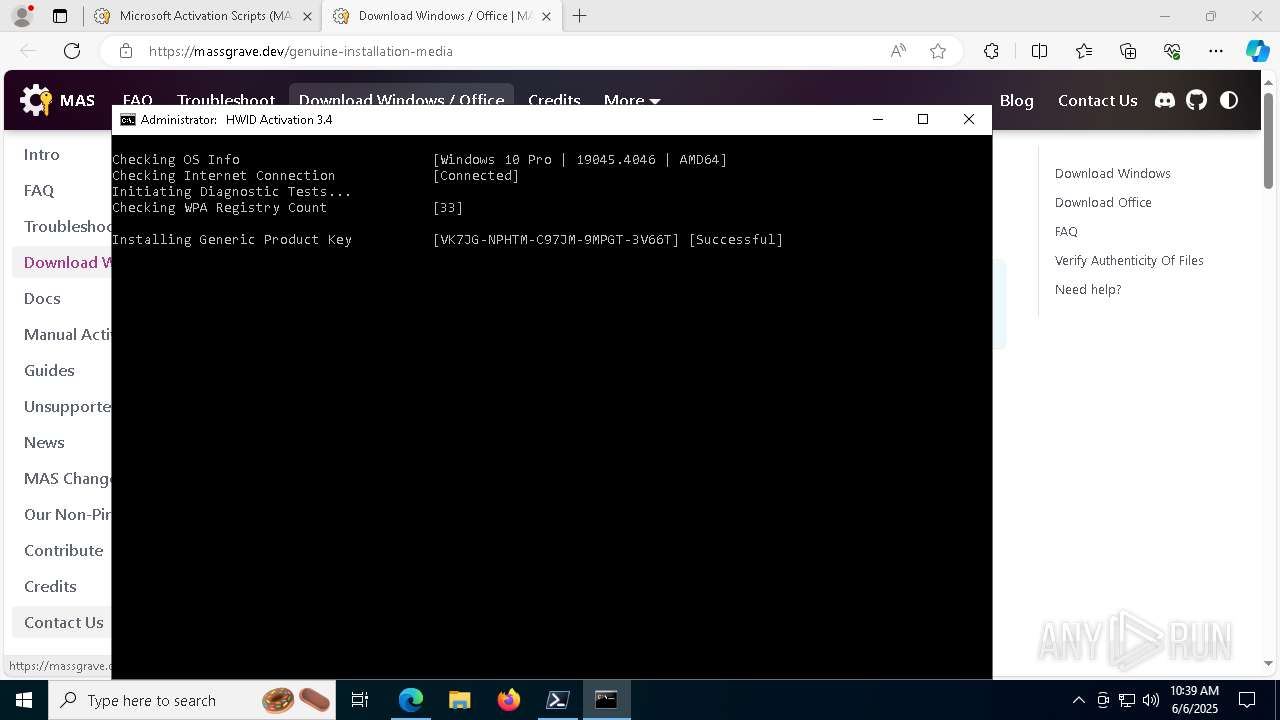
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MD5: | 5C95876F594CFFB1178B8861F8C741E0 |
| SHA1: | 4F3DD1555BACB0851AD877F9B40BD8DCC884A71D |
| SHA256: | 6019AF861964CFB41AE5A5FE576ACA4521AFBA41255E5C636B1F53DFA0B6BE7F |
| SSDEEP: | 3:N8a0Kn:2a0K |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads the date of Windows installation
- pwsh.exe (PID: 6800)
Starts CMD.EXE for commands execution
- pwsh.exe (PID: 6800)
- cmd.exe (PID: 4172)
- cmd.exe (PID: 7744)
- powershell.exe (PID: 7616)
- cmd.exe (PID: 1072)
- cmd.exe (PID: 456)
- cmd.exe (PID: 7508)
- cmd.exe (PID: 6060)
Executing commands from ".cmd" file
- pwsh.exe (PID: 6800)
- cmd.exe (PID: 4172)
- powershell.exe (PID: 7616)
- cmd.exe (PID: 1072)
- cmd.exe (PID: 6060)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 4172)
- cmd.exe (PID: 1072)
- cmd.exe (PID: 6060)
- cmd.exe (PID: 8080)
- cmd.exe (PID: 7280)
Windows service management via SC.EXE
- sc.exe (PID: 3032)
- sc.exe (PID: 2796)
- sc.exe (PID: 7300)
- sc.exe (PID: 6392)
- sc.exe (PID: 7240)
- sc.exe (PID: 7600)
- sc.exe (PID: 3016)
- sc.exe (PID: 7584)
- sc.exe (PID: 3804)
- sc.exe (PID: 2316)
- sc.exe (PID: 7504)
- sc.exe (PID: 6264)
- sc.exe (PID: 7512)
- sc.exe (PID: 1804)
- sc.exe (PID: 5984)
- sc.exe (PID: 6464)
- sc.exe (PID: 3124)
- sc.exe (PID: 6404)
- sc.exe (PID: 7656)
- sc.exe (PID: 7584)
- sc.exe (PID: 8160)
- sc.exe (PID: 8028)
- sc.exe (PID: 2240)
- sc.exe (PID: 6392)
- sc.exe (PID: 8076)
- sc.exe (PID: 5676)
- sc.exe (PID: 2316)
- sc.exe (PID: 232)
- sc.exe (PID: 7892)
- sc.exe (PID: 3016)
- sc.exe (PID: 3796)
- sc.exe (PID: 4220)
- sc.exe (PID: 6816)
- sc.exe (PID: 6268)
- sc.exe (PID: 4728)
- sc.exe (PID: 7452)
- sc.exe (PID: 7692)
- sc.exe (PID: 7368)
- sc.exe (PID: 4284)
Starts SC.EXE for service management
- cmd.exe (PID: 4172)
- cmd.exe (PID: 1072)
- cmd.exe (PID: 6060)
Application launched itself
- cmd.exe (PID: 4172)
- cmd.exe (PID: 7744)
- cmd.exe (PID: 456)
- cmd.exe (PID: 1072)
- cmd.exe (PID: 6060)
- cmd.exe (PID: 7508)
- powershell.exe (PID: 1088)
- powershell.exe (PID: 2124)
- powershell.exe (PID: 2408)
- powershell.exe (PID: 7380)
- ClipUp.exe (PID: 7276)
- powershell.exe (PID: 1056)
- powershell.exe (PID: 2028)
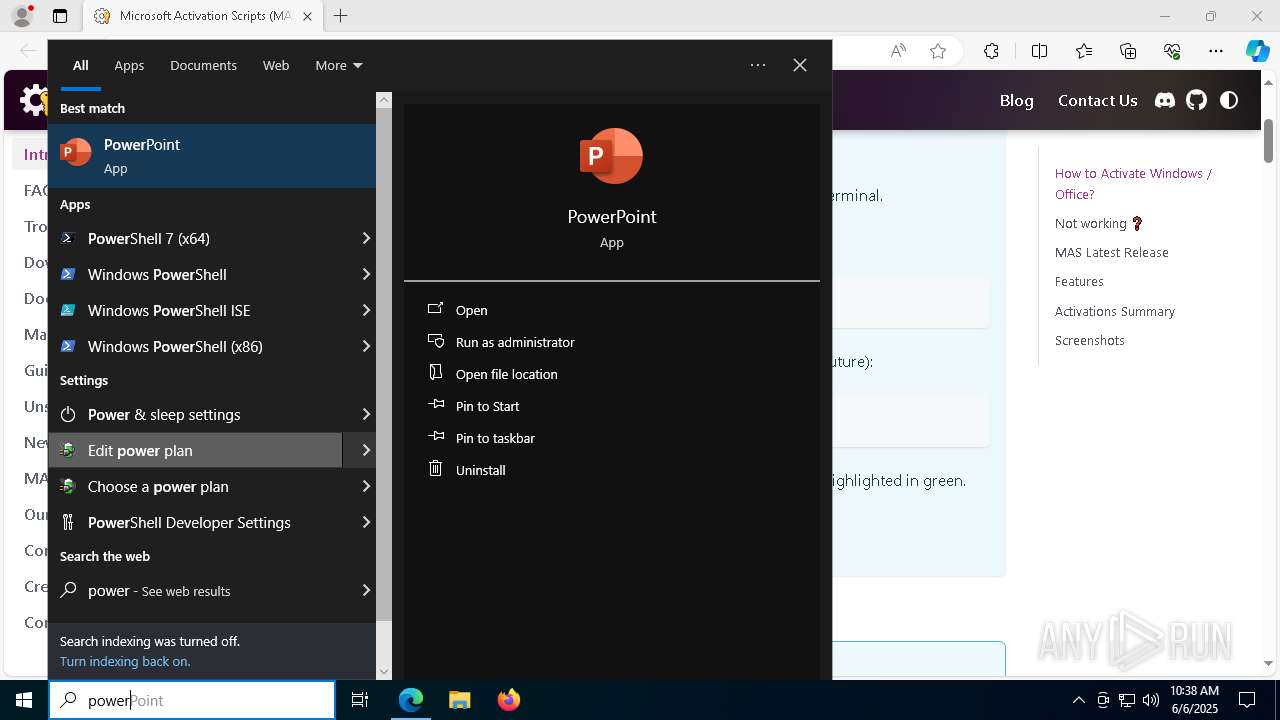
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 4172)
- cmd.exe (PID: 2240)
- cmd.exe (PID: 8028)
- cmd.exe (PID: 7692)
- cmd.exe (PID: 6060)
- cmd.exe (PID: 1300)
- powershell.exe (PID: 1088)
- cmd.exe (PID: 6072)
- cmd.exe (PID: 524)
- cmd.exe (PID: 4424)
- powershell.exe (PID: 2124)
- cmd.exe (PID: 8028)
- powershell.exe (PID: 2408)
- powershell.exe (PID: 7380)
- powershell.exe (PID: 2028)
- powershell.exe (PID: 1056)
Hides command output
- cmd.exe (PID: 2240)
- cmd.exe (PID: 8028)
- cmd.exe (PID: 7280)
- cmd.exe (PID: 8080)
- cmd.exe (PID: 6668)
- cmd.exe (PID: 7272)
- cmd.exe (PID: 524)
- cmd.exe (PID: 232)
- cmd.exe (PID: 5044)
- cmd.exe (PID: 2392)
- cmd.exe (PID: 2316)
- cmd.exe (PID: 6072)
- cmd.exe (PID: 8100)
- cmd.exe (PID: 5384)
- cmd.exe (PID: 1300)
Executes script without checking the security policy
- powershell.exe (PID: 6416)
- powershell.exe (PID: 7616)
- powershell.exe (PID: 2740)
- powershell.exe (PID: 7508)
- powershell.exe (PID: 7252)
- powershell.exe (PID: 4120)
- powershell.exe (PID: 1088)
- powershell.exe (PID: 4276)
- powershell.exe (PID: 7372)
- powershell.exe (PID: 6344)
- powershell.exe (PID: 2124)
- powershell.exe (PID: 1804)
- powershell.exe (PID: 6976)
- powershell.exe (PID: 6464)
- powershell.exe (PID: 4428)
- powershell.exe (PID: 6720)
- powershell.exe (PID: 5332)
- powershell.exe (PID: 2408)
- powershell.exe (PID: 7380)
- powershell.exe (PID: 2896)
- powershell.exe (PID: 5236)
- powershell.exe (PID: 4276)
- powershell.exe (PID: 1056)
- powershell.exe (PID: 3968)
- powershell.exe (PID: 2028)
- powershell.exe (PID: 7596)
Probably obfuscated PowerShell command line is found
- cmd.exe (PID: 2240)
- cmd.exe (PID: 8028)
- cmd.exe (PID: 6060)
- cmd.exe (PID: 1300)
- cmd.exe (PID: 524)
- cmd.exe (PID: 8028)
The process bypasses the loading of PowerShell profile settings
- cmd.exe (PID: 4172)
- cmd.exe (PID: 2240)
- cmd.exe (PID: 8028)
- cmd.exe (PID: 7692)
- cmd.exe (PID: 6060)
- cmd.exe (PID: 1300)
- powershell.exe (PID: 1088)
- cmd.exe (PID: 524)
- cmd.exe (PID: 6072)
- cmd.exe (PID: 4424)
- powershell.exe (PID: 2124)
- cmd.exe (PID: 8028)
- powershell.exe (PID: 2408)
- powershell.exe (PID: 7380)
- powershell.exe (PID: 2028)
- powershell.exe (PID: 1056)
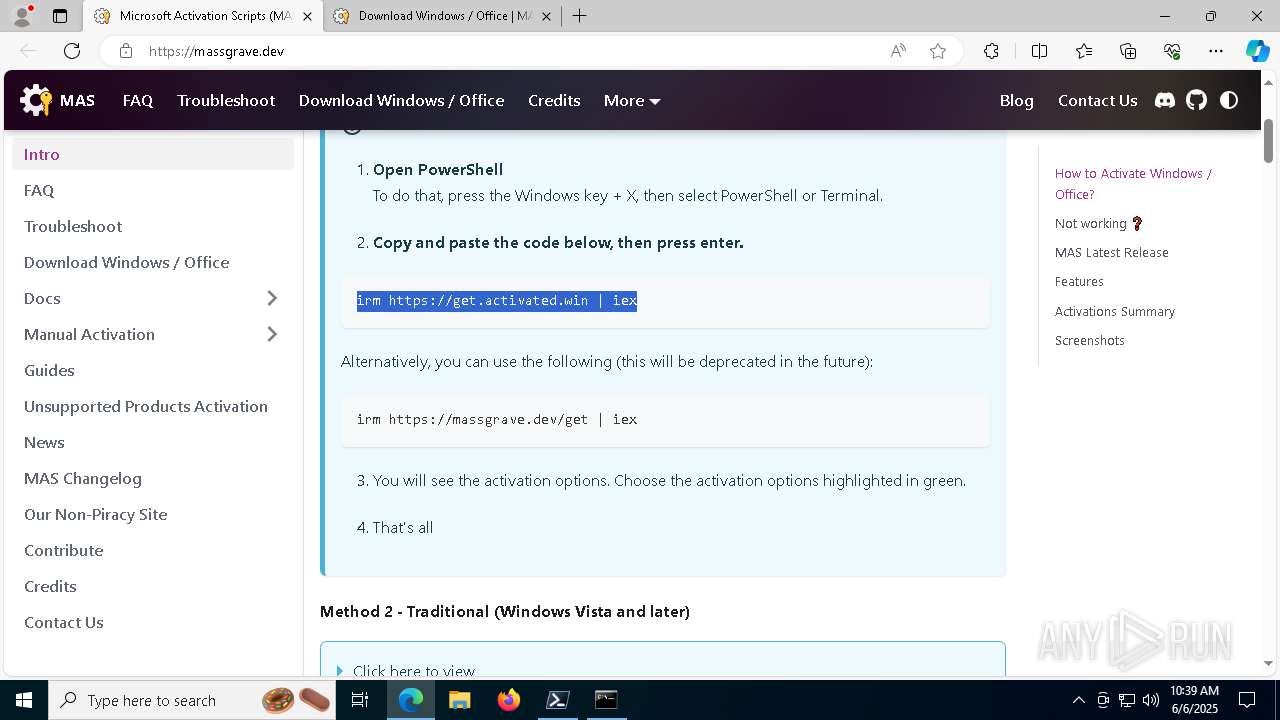
Possibly malicious use of IEX has been detected
- cmd.exe (PID: 2240)
- cmd.exe (PID: 8028)
- cmd.exe (PID: 6060)
- cmd.exe (PID: 524)
Uses sleep to delay execution (POWERSHELL)
- powershell.exe (PID: 6416)
- powershell.exe (PID: 2740)
Uses base64 encoding (POWERSHELL)
- powershell.exe (PID: 6416)
- powershell.exe (PID: 2740)
Gets content of a file (POWERSHELL)
- powershell.exe (PID: 6416)
- powershell.exe (PID: 2740)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 1072)
- cmd.exe (PID: 6060)
Get information on the list of running processes
- cmd.exe (PID: 6060)
- cmd.exe (PID: 7280)
- cmd.exe (PID: 8080)
Uses WMIC.EXE to obtain computer system information
- cmd.exe (PID: 4008)
- cmd.exe (PID: 6060)
Uses WMIC.EXE to obtain operating system information
- cmd.exe (PID: 6668)
Probably file/command deobfuscation
- cmd.exe (PID: 1300)
- cmd.exe (PID: 8028)
Uses WMIC.EXE to obtain Windows Installer data
- cmd.exe (PID: 6060)
- cmd.exe (PID: 5044)
- cmd.exe (PID: 2392)
- cmd.exe (PID: 5384)
The process hides Powershell's copyright startup banner
- powershell.exe (PID: 1088)
- powershell.exe (PID: 2124)
- powershell.exe (PID: 2408)
- powershell.exe (PID: 7380)
- powershell.exe (PID: 1056)
- powershell.exe (PID: 2028)
Uses WMIC.EXE to obtain service application data
- cmd.exe (PID: 6060)
Process uses IPCONFIG to clear DNS cache
- cmd.exe (PID: 6060)
Executes application which crashes
- powershell.exe (PID: 300)
INFO
Reads the computer name
- identity_helper.exe (PID: 6436)
- pwsh.exe (PID: 6800)
Application launched itself
- msedge.exe (PID: 7700)
Checks supported languages
- identity_helper.exe (PID: 6436)
- mode.com (PID: 7892)
- mode.com (PID: 7872)
- pwsh.exe (PID: 6800)
Process checks computer location settings
- pwsh.exe (PID: 6800)
Checks operating system version
- cmd.exe (PID: 4172)
- cmd.exe (PID: 1072)
- cmd.exe (PID: 6060)
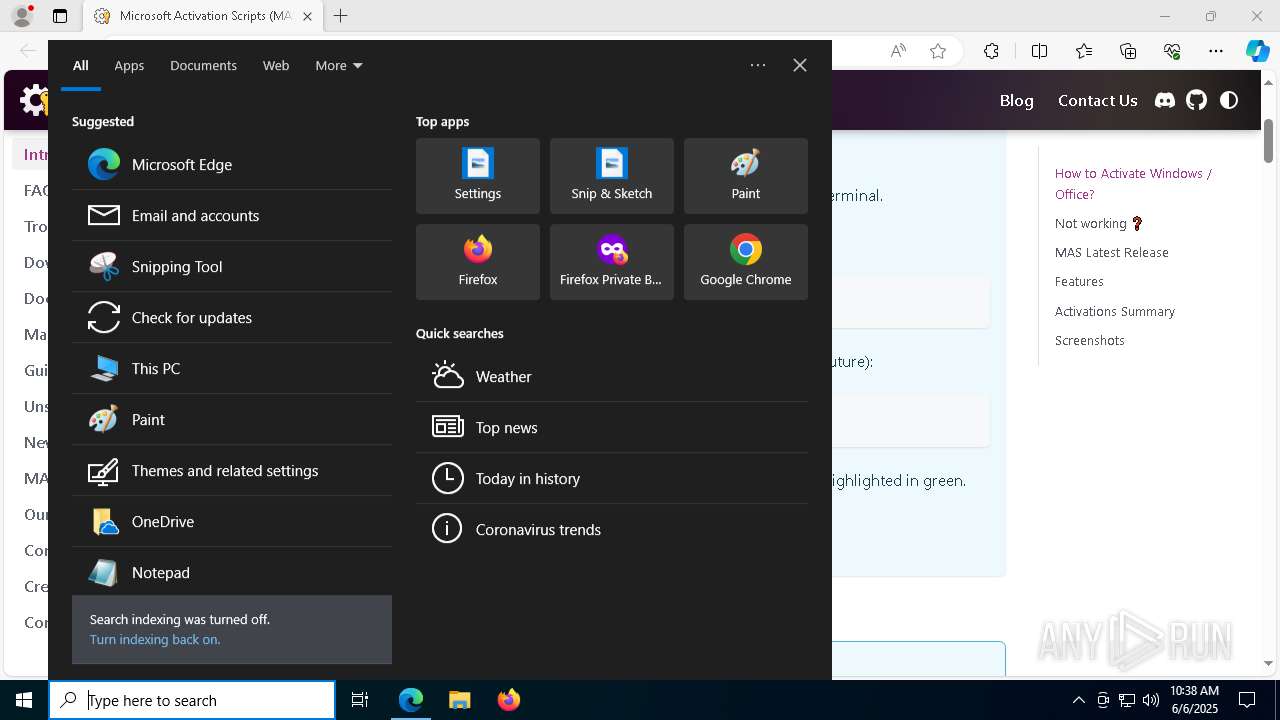
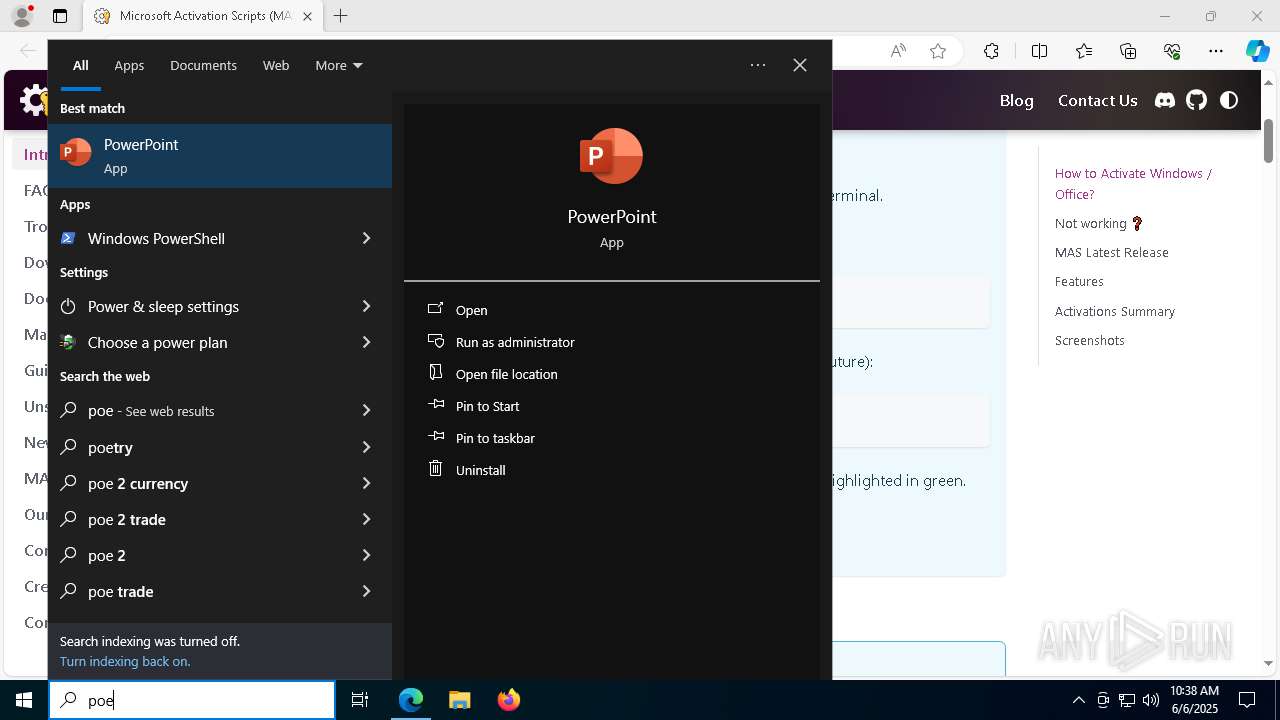
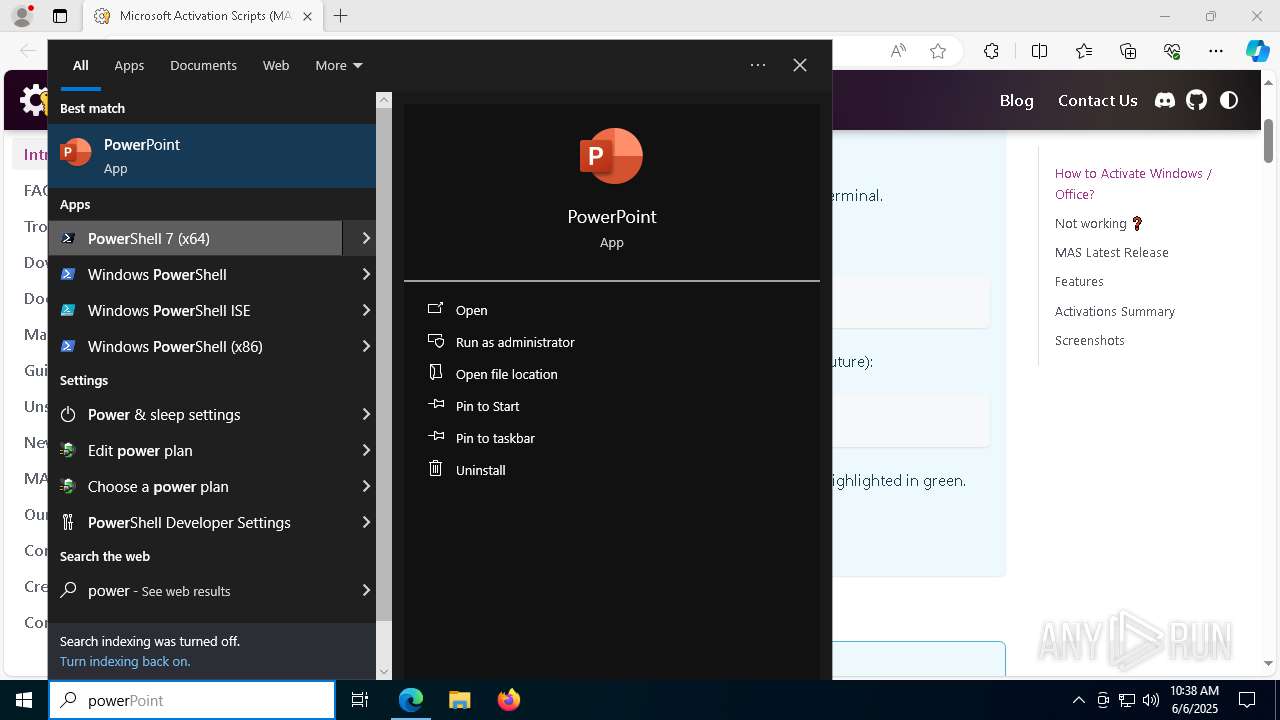
Manual execution by a user
- pwsh.exe (PID: 6800)
Converts byte array into ASCII string (POWERSHELL)
- powershell.exe (PID: 6416)
- powershell.exe (PID: 2740)
Checks whether the specified file exists (POWERSHELL)
- powershell.exe (PID: 6416)
- powershell.exe (PID: 2740)
Creates a byte array (POWERSHELL)
- powershell.exe (PID: 6416)
- powershell.exe (PID: 2740)
Starts MODE.COM to configure console settings
- mode.com (PID: 7892)
- mode.com (PID: 7872)
- mode.com (PID: 2236)
- mode.com (PID: 456)
- mode.com (PID: 7512)
- mode.com (PID: 6976)
- mode.com (PID: 8100)
- mode.com (PID: 7692)
Reads Environment values
- identity_helper.exe (PID: 6436)
The sample compiled with english language support
- msedge.exe (PID: 3800)
Executable content was dropped or overwritten
- msedge.exe (PID: 3800)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
603
Monitored processes
456
Malicious processes
8
Suspicious processes
11
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 132 | find /i "0x0" | C:\Windows\System32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Find String (grep) Utility Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 132 | C:\WINDOWS\System32\cmd.exe /S /D /c" echo "C:\Users\admin\AppData\Local\Temp\MAS_77dbbf8b-4769-4764-a942-954355dcebaa.cmd" " | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 132 | find /i "-onenote.exe-" | C:\Windows\System32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (grep) Utility Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 208 | C:\WINDOWS\System32\cmd.exe /S /D /c" echo -smss.exe- -csrss.exe- -wininit.exe- -services.exe- -lsass.exe- -svchost.exe- -fontdrvhost.exe- -svchost.exe- -svchost.exe- -svchost.exe- -svchost.exe- -svchost.exe- -svchost.exe- -svchost.exe- -svchost.exe- -svchost.exe- -svchost.exe- -svchost.exe- -svchost.exe- -svchost.exe- -svchost.exe- -svchost.exe- -svchost.exe- -svchost.exe- -svchost.exe- -svchost.exe- -svchost.exe- -svchost.exe- -svchost.exe- -svchost.exe- -svchost.exe- -svchost.exe- -svchost.exe- -svchost.exe- -svchost.exe- -svchost.exe- -svchost.exe- -svchost.exe- -spoolsv.exe- -svchost.exe- -svchost.exe- -svchost.exe- -svchost.exe- -dasHost.exe- -svchost.exe- -svchost.exe- -svchost.exe- -OfficeClickToRun.exe- -svchost.exe- -svchost.exe- -svchost.exe- -svchost.exe- -svchost.exe- -svchost.exe- -svchost.exe- -svchost.exe- -svchost.exe- -svchost.exe- -svchost.exe- -svchost.exe- -dllhost.exe- -svchost.exe- -MoUsoCoreWorker.exe- -svchost.exe- -svchost.exe- -svchost.exe- -uhssvc.exe- -svchost.exe- -svchost.exe- -csrss.exe- -winlogon.exe- -fontdrvhost.exe- -dwm.exe- -sihost.exe- -svchost.exe- -svchost.exe- -explorer.exe- -svchost.exe- -dllhost.exe- -RuntimeBroker.exe- -SearchApp.exe- -RuntimeBroker.exe- -ctfmon.exe- -RuntimeBroker.exe- -SystemSettings.exe- -ApplicationFrameHost.exe- -UserOOBEBroker.exe- -svchost.exe- -svchost.exe- -svchost.exe- -svchost.exe- -TextInputHost.exe- -dllhost.exe- -audiodg.exe- -svchost.exe- -svchost.exe- -svchost.exe- -svchost.exe- -WmiPrvSE.exe- -svchost.exe- -svchost.exe- -svchost.exe- -svchost.exe- -svchost.exe- -svchost.exe- -sppsvc.exe- -msedge.exe- -msedge.exe- -msedge.exe- -msedge.exe- -msedge.exe- -msedge.exe- -msedge.exe- -msedge.exe- -SppExtComObj.Exe- -slui.exe- -pwsh.exe- -conhost.exe- -cmd.exe- -conhost.exe- -cmd.exe- -tasklist.exe- -findstr.exe- " | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 208 | wmic path Win32_ComputerSystem get CreationClassName /value | C:\Windows\System32\wbem\WMIC.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: WMI Commandline Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 208 | reg query "HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\sppsvc.exe" | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 232 | sc start Winmgmt | C:\Windows\System32\sc.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Service Control Manager Configuration Tool Exit code: 1056 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 232 | C:\WINDOWS\System32\cmd.exe /c reg query "HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SoftwareProtectionPlatform" /v TokenStore 2>nul | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 300 | reg query HKLM\SYSTEM\CurrentControlSet\Services\Winmgmt /v ObjectName | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 300 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -Version 5.1 -s -NoLogo -NoProfile | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 3221225725 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
168 845
Read events
168 783
Write events
52
Delete events
10
Modification events
| (PID) Process: | (7700) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: F0B5E61B7B952F00 | |||
| (PID) Process: | (7700) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\131970 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {D32E6C5D-2F5B-45ED-A956-97E503DA19DA} | |||
| (PID) Process: | (7700) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\131970 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {78F995A4-D8DA-4C49-9791-A608BDE7A9CE} | |||
| (PID) Process: | (7700) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\131970 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {969E2261-6AC1-4C00-B75B-217A9F282B80} | |||
| (PID) Process: | (7700) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (7700) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (7700) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (7700) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (7700) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 8EAFDF1B7B952F00 | |||
| (PID) Process: | (7700) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: F052161C7B952F00 | |||
Executable files
9
Suspicious files
586
Text files
162
Unknown types
5
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7700 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Local State~RF11f588.TMP | — | |
MD5:— | SHA256:— | |||
| 7700 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\Sync Data\LevelDB\LOG.old~RF11f5a8.TMP | — | |
MD5:— | SHA256:— | |||
| 7700 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF11f5c7.TMP | — | |
MD5:— | SHA256:— | |||
| 7700 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7700 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF11f5e6.TMP | — | |
MD5:— | SHA256:— | |||
| 7700 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7700 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF11f5e6.TMP | — | |
MD5:— | SHA256:— | |||
| 7700 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7700 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\Service Worker\Database\LOG.old~RF11f5b7.TMP | — | |
MD5:— | SHA256:— | |||
| 7700 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\Service Worker\Database\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
30
TCP/UDP connections
88
DNS requests
90
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.219.150.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 2.16.168.114:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
2924 | SearchApp.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
2392 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
2392 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
2924 | SearchApp.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
6800 | pwsh.exe | GET | 200 | 23.216.77.25:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
7924 | svchost.exe | HEAD | 200 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/5cbc98ff-b69b-4fda-ad94-17ec2f9cf48b?P1=1749577472&P2=404&P3=2&P4=JKtk%2fkWKnsEOvKpyYCFLXBD6mfHHsMvpApiXQT%2bDOTSsinECrA%2fXH9Bc30168jUmEi4objW9Lb2qOWkGRZYYUg%3d%3d | unknown | — | — | whitelisted |
6800 | pwsh.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicCodSigPCA2011_2011-07-08.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
3176 | RUXIMICS.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5496 | MoUsoCoreWorker.exe | 2.16.168.114:80 | crl.microsoft.com | Akamai International B.V. | RU | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.219.150.101:80 | www.microsoft.com | AKAMAI-AS | CL | whitelisted |
5496 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
7700 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
7484 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7484 | msedge.exe | 104.21.22.3:443 | massgrave.dev | CLOUDFLARENET | — | unknown |
7484 | msedge.exe | 13.107.246.45:443 | edge-mobile-static.azureedge.net | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
massgrave.dev |
| unknown |
edge.microsoft.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
business.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
6800 | pwsh.exe | Not Suspicious Traffic | INFO [ANY.RUN] Azure Front Door domain observed in TLS SNI ( .azurefd .net) |
7484 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
7484 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |