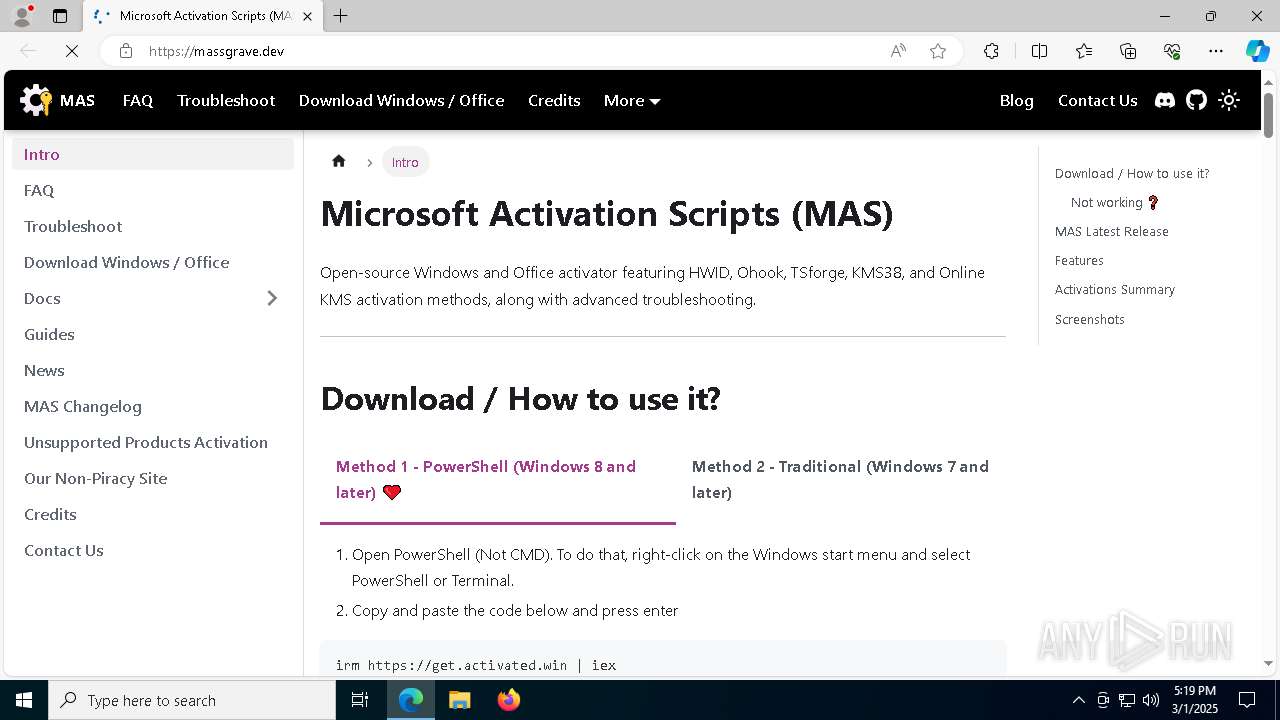
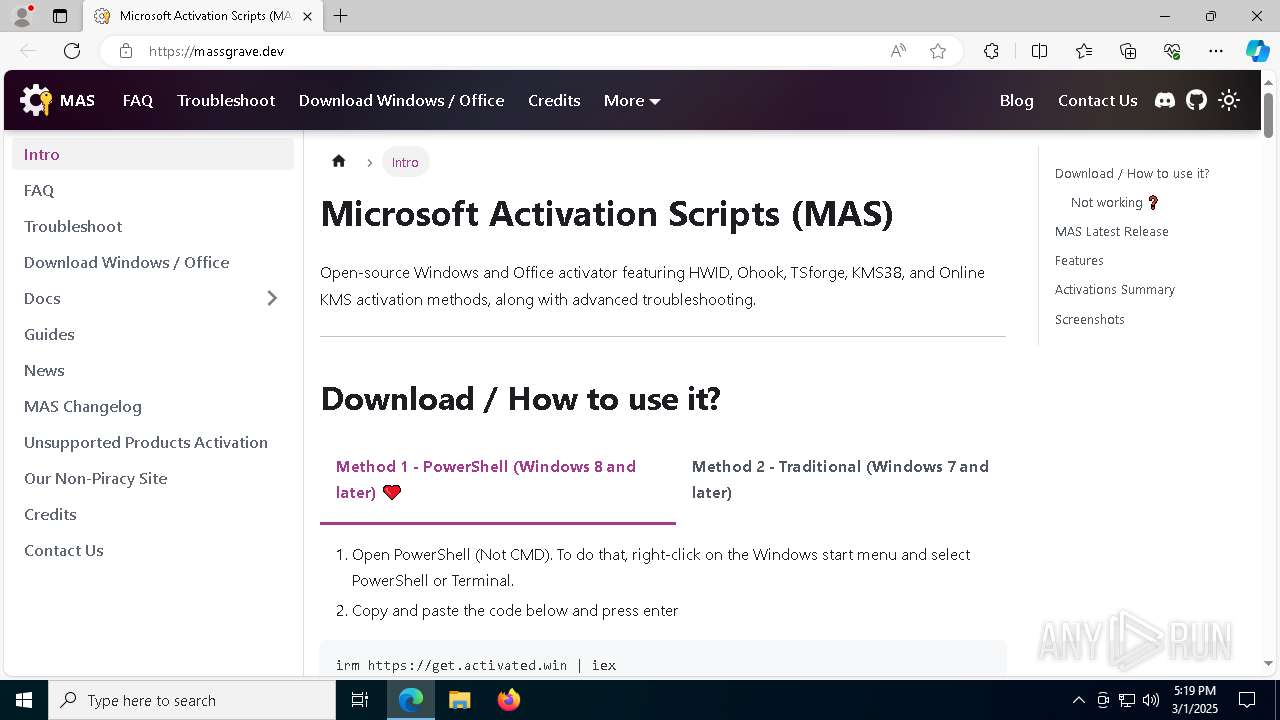
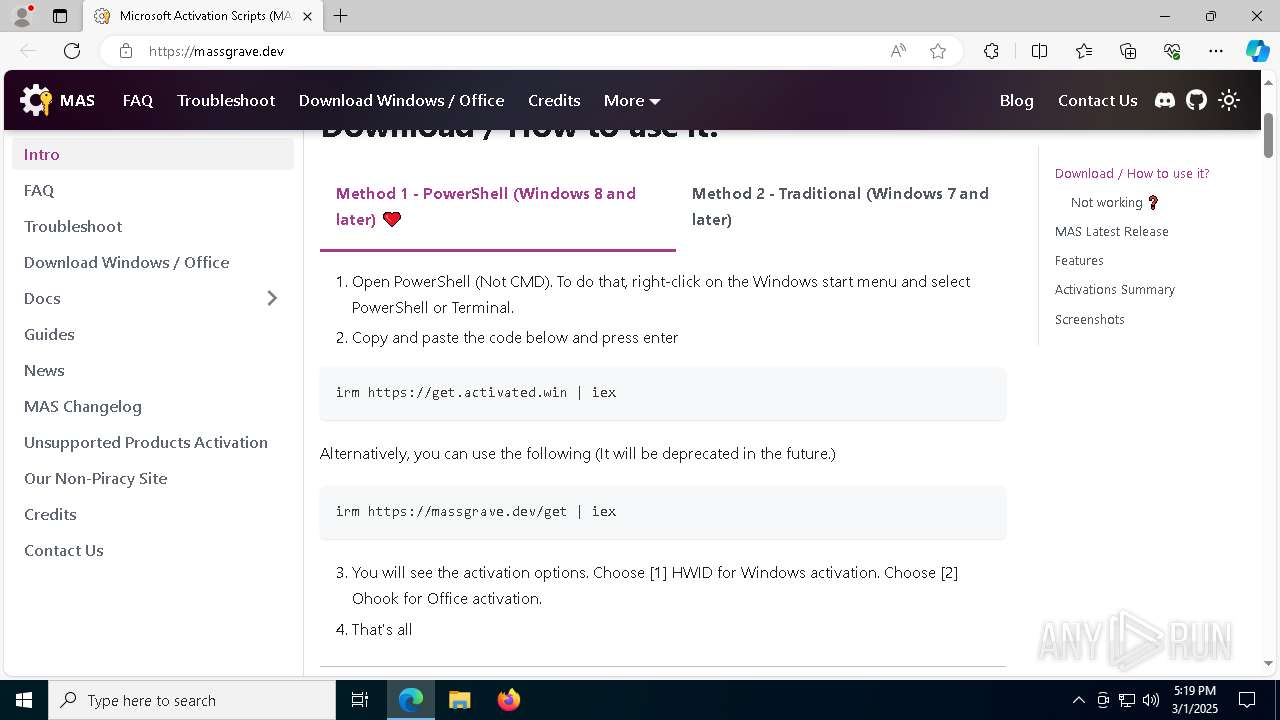
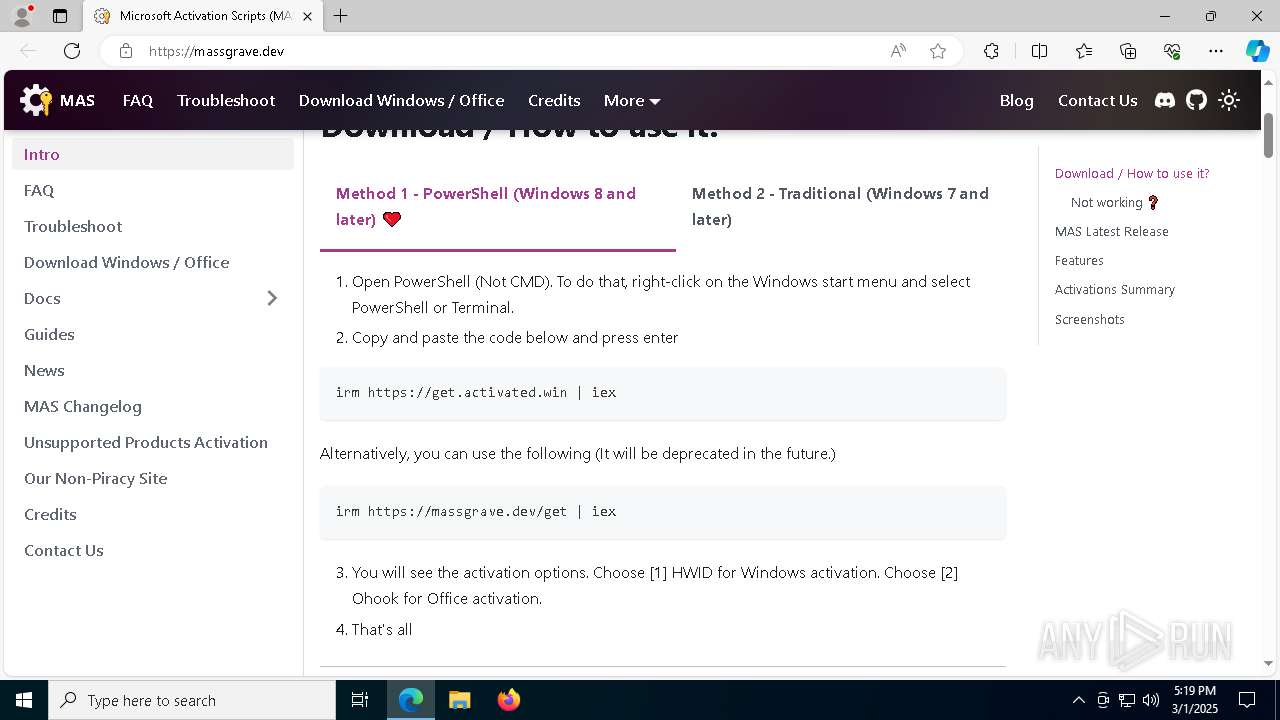
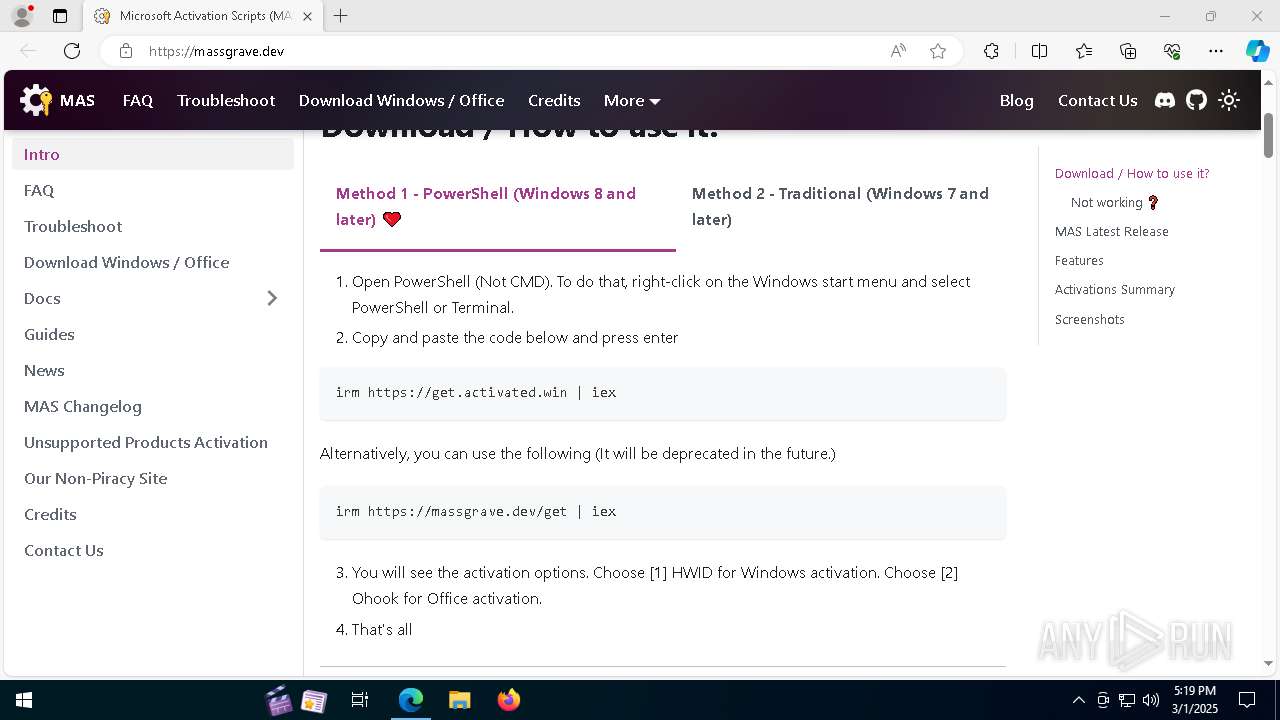
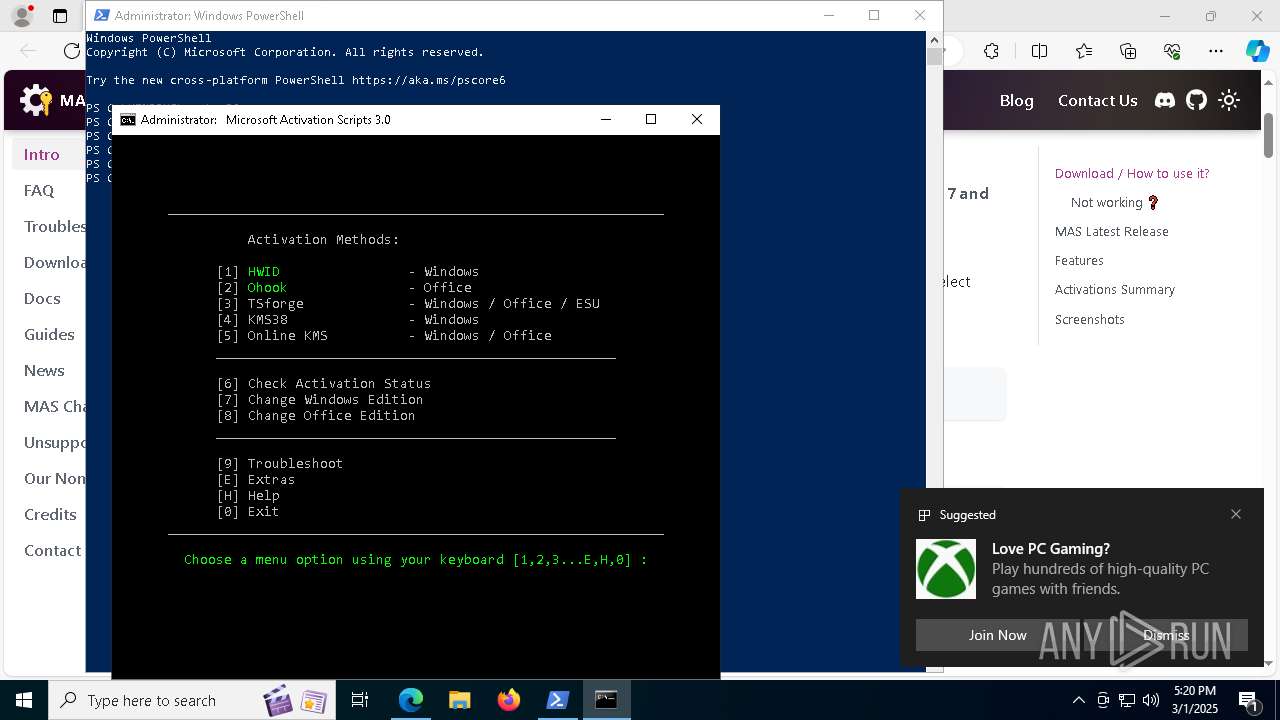
| URL: | https://massgrave.dev/ |
| Full analysis: | https://app.any.run/tasks/55fe5264-4a9d-4600-b9ea-3e627bfc6378 |
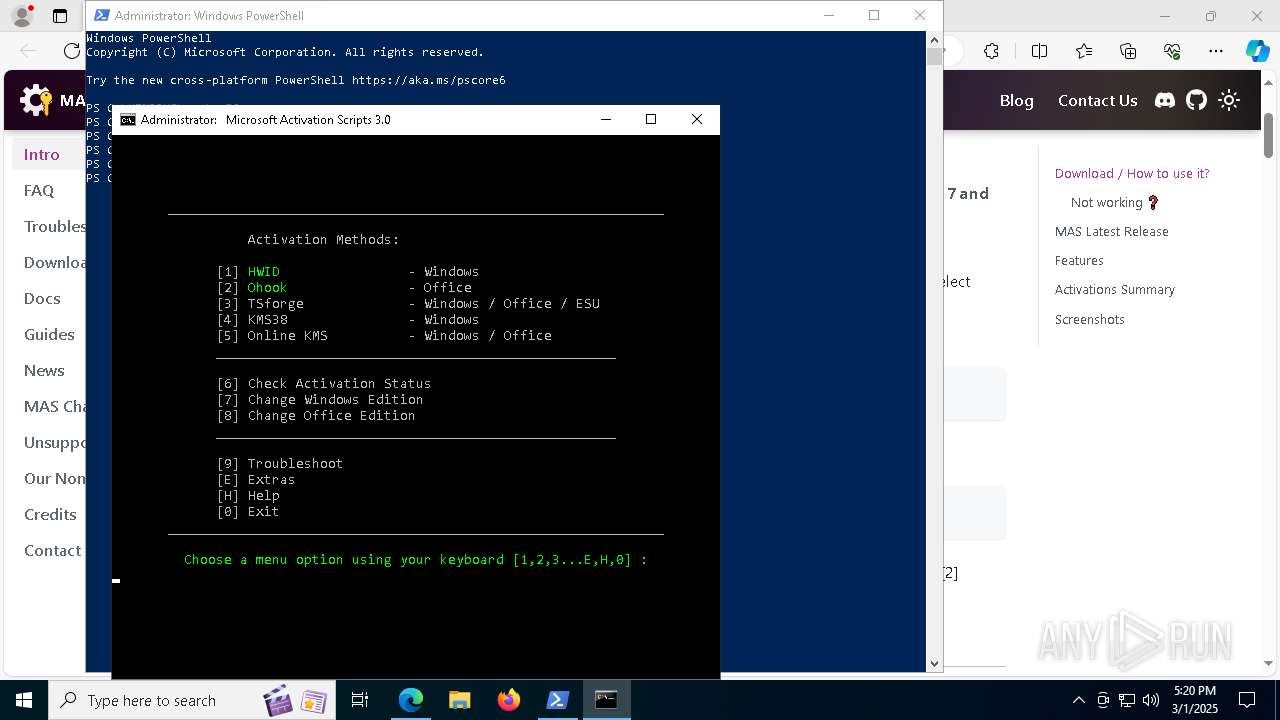
| Verdict: | Malicious activity |
| Analysis date: | March 01, 2025, 17:19:21 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MD5: | 5C95876F594CFFB1178B8861F8C741E0 |
| SHA1: | 4F3DD1555BACB0851AD877F9B40BD8DCC884A71D |
| SHA256: | 6019AF861964CFB41AE5A5FE576ACA4521AFBA41255E5C636B1F53DFA0B6BE7F |
| SSDEEP: | 3:N8a0Kn:2a0K |
MALICIOUS
No malicious indicators.SUSPICIOUS
Gets or sets the security protocol (POWERSHELL)
- powershell.exe (PID: 6044)
Uses base64 encoding (POWERSHELL)
- powershell.exe (PID: 6044)
- powershell.exe (PID: 1272)
- powershell.exe (PID: 8164)
Gets content of a file (POWERSHELL)
- powershell.exe (PID: 6044)
- powershell.exe (PID: 1272)
- powershell.exe (PID: 8164)
Creates new GUID (POWERSHELL)
- powershell.exe (PID: 6044)
Starts SC.EXE for service management
- cmd.exe (PID: 8512)
- cmd.exe (PID: 3020)
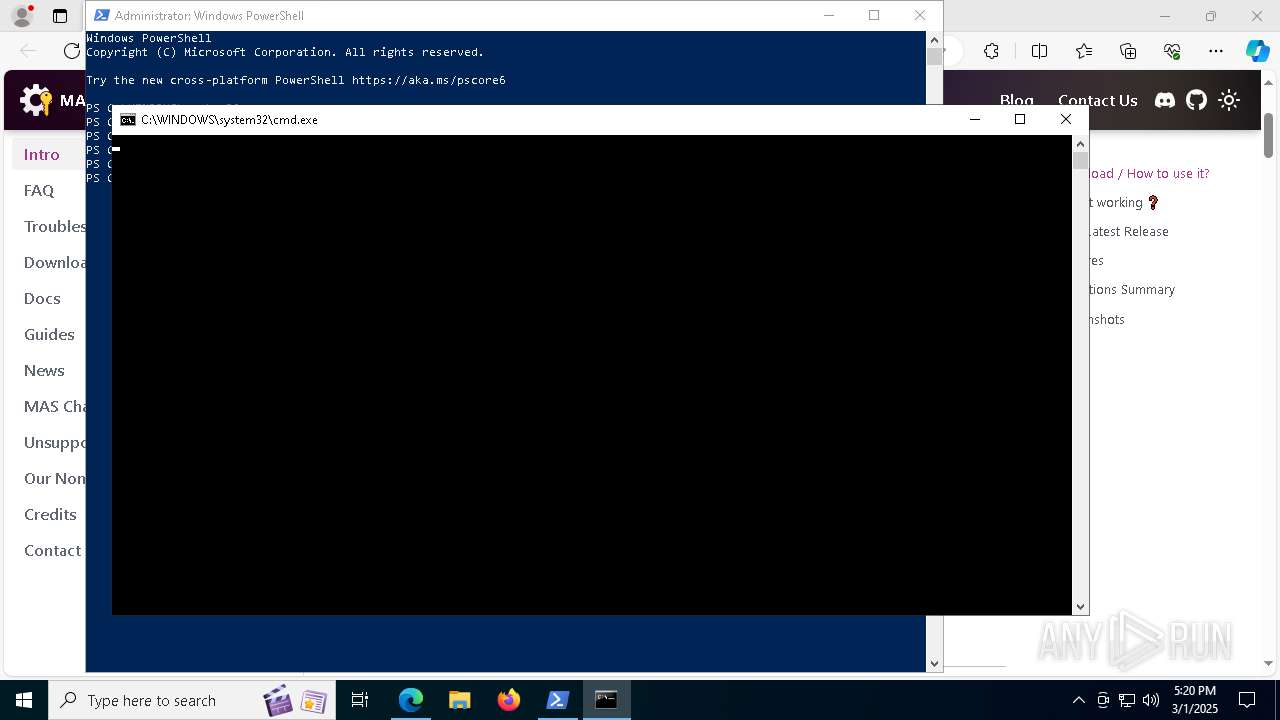
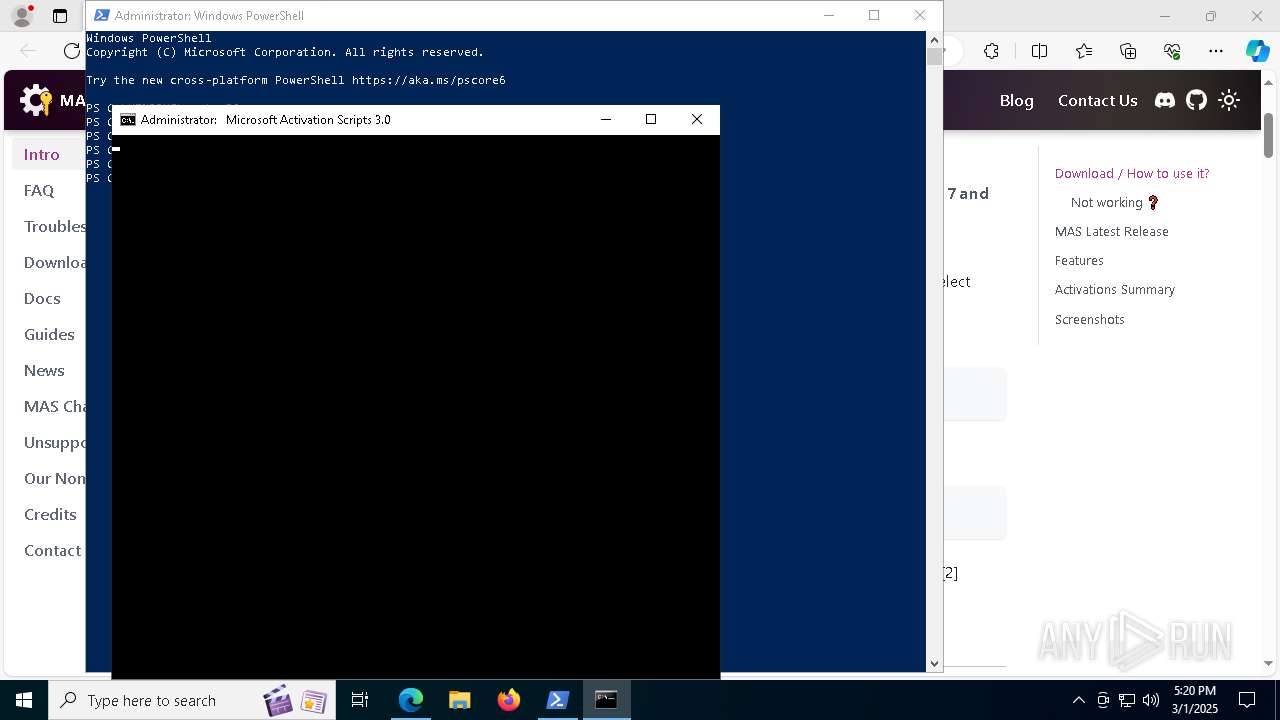
Starts CMD.EXE for commands execution
- powershell.exe (PID: 6044)
- cmd.exe (PID: 8512)
- cmd.exe (PID: 8524)
- powershell.exe (PID: 9192)
- cmd.exe (PID: 3020)
- cmd.exe (PID: 9092)
Executing commands from ".cmd" file
- powershell.exe (PID: 6044)
- powershell.exe (PID: 9192)
- cmd.exe (PID: 8512)
- cmd.exe (PID: 3020)
Windows service management via SC.EXE
- sc.exe (PID: 8712)
- sc.exe (PID: 1184)
Application launched itself
- cmd.exe (PID: 8524)
- cmd.exe (PID: 8512)
- cmd.exe (PID: 3020)
- cmd.exe (PID: 9092)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 8512)
- cmd.exe (PID: 3020)
Probably obfuscated PowerShell command line is found
- cmd.exe (PID: 8964)
- cmd.exe (PID: 8140)
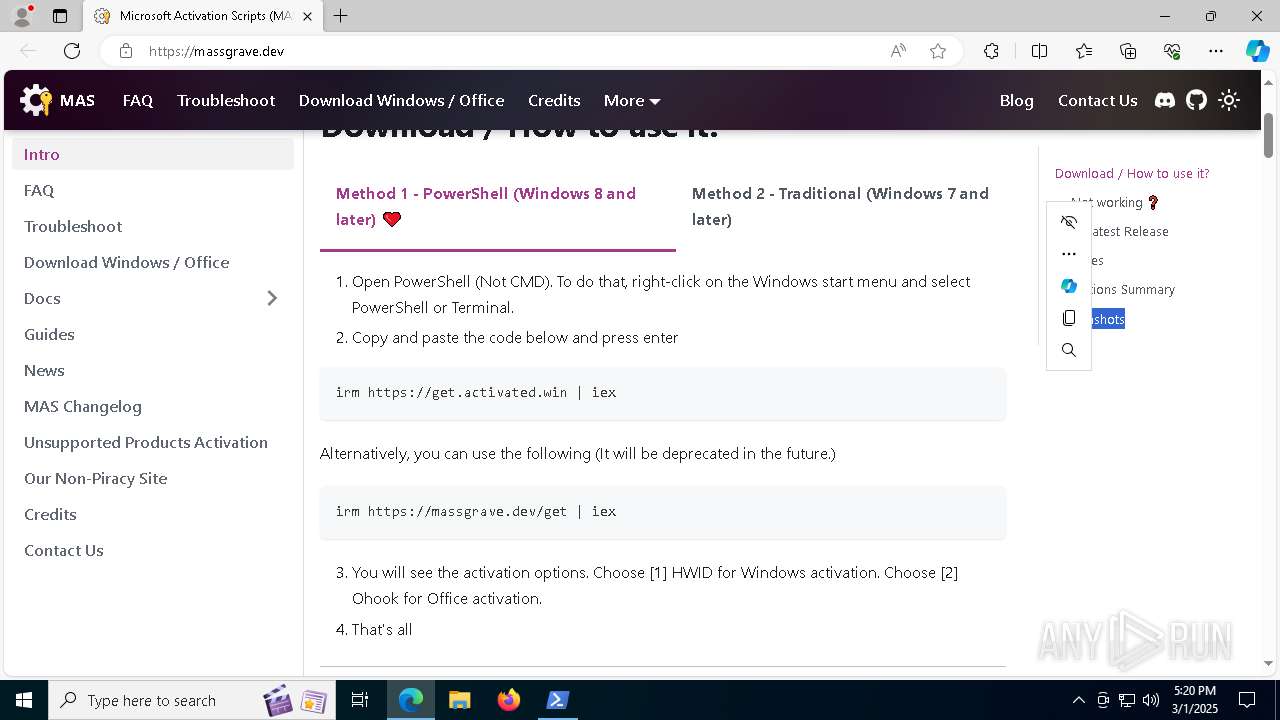
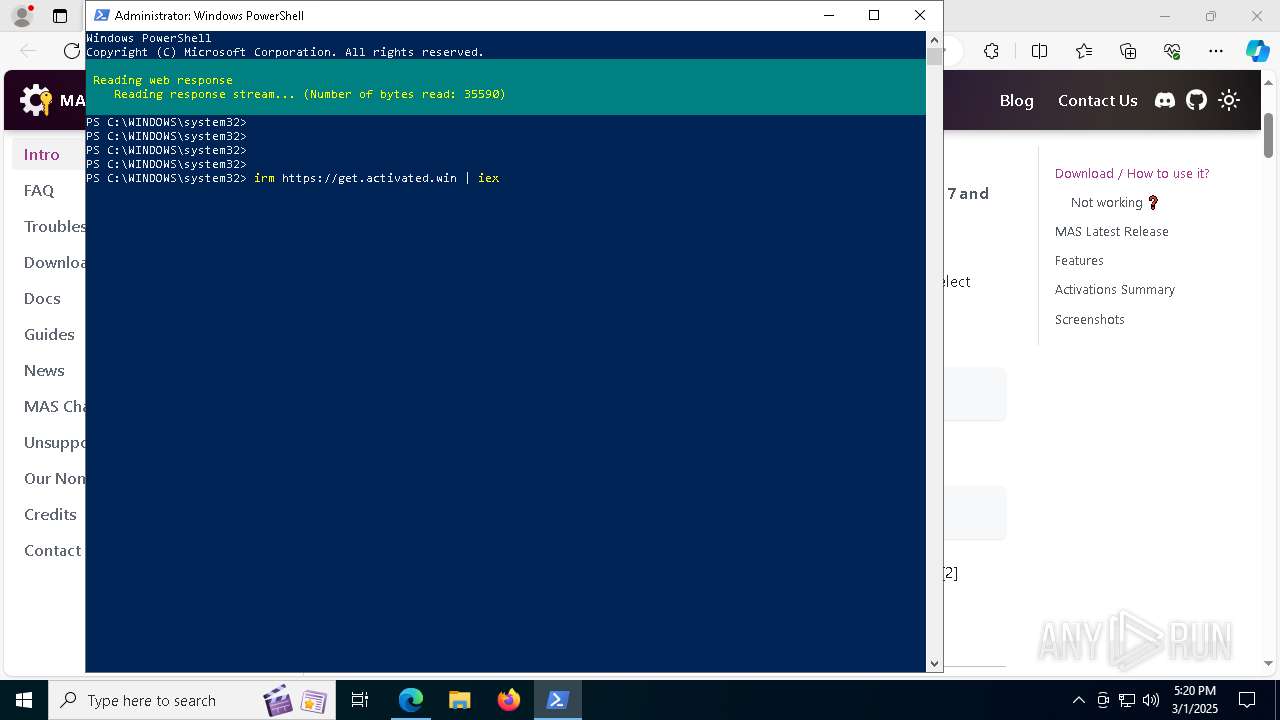
Possibly malicious use of IEX has been detected
- cmd.exe (PID: 8964)
- cmd.exe (PID: 8140)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 8964)
- cmd.exe (PID: 8512)
- cmd.exe (PID: 8140)
- cmd.exe (PID: 3020)
Uses sleep to delay execution (POWERSHELL)
- powershell.exe (PID: 1272)
- powershell.exe (PID: 8164)
- powershell.exe (PID: 6044)
Reads security settings of Internet Explorer
- ShellExperienceHost.exe (PID: 720)
INFO
Reads the software policy settings
- BackgroundTransferHost.exe (PID: 4408)
- slui.exe (PID: 8296)
Reads security settings of Internet Explorer
- BackgroundTransferHost.exe (PID: 9212)
- BackgroundTransferHost.exe (PID: 5344)
- BackgroundTransferHost.exe (PID: 9076)
- BackgroundTransferHost.exe (PID: 4408)
- BackgroundTransferHost.exe (PID: 8764)
Reads the computer name
- identity_helper.exe (PID: 8416)
- ShellExperienceHost.exe (PID: 720)
Checks proxy server information
- BackgroundTransferHost.exe (PID: 4408)
- powershell.exe (PID: 6044)
Application launched itself
- msedge.exe (PID: 3192)
Checks supported languages
- identity_helper.exe (PID: 8416)
- mode.com (PID: 8784)
- ShellExperienceHost.exe (PID: 720)
Creates a byte array (POWERSHELL)
- powershell.exe (PID: 6044)
- powershell.exe (PID: 1272)
- powershell.exe (PID: 8164)
Creates files or folders in the user directory
- BackgroundTransferHost.exe (PID: 4408)
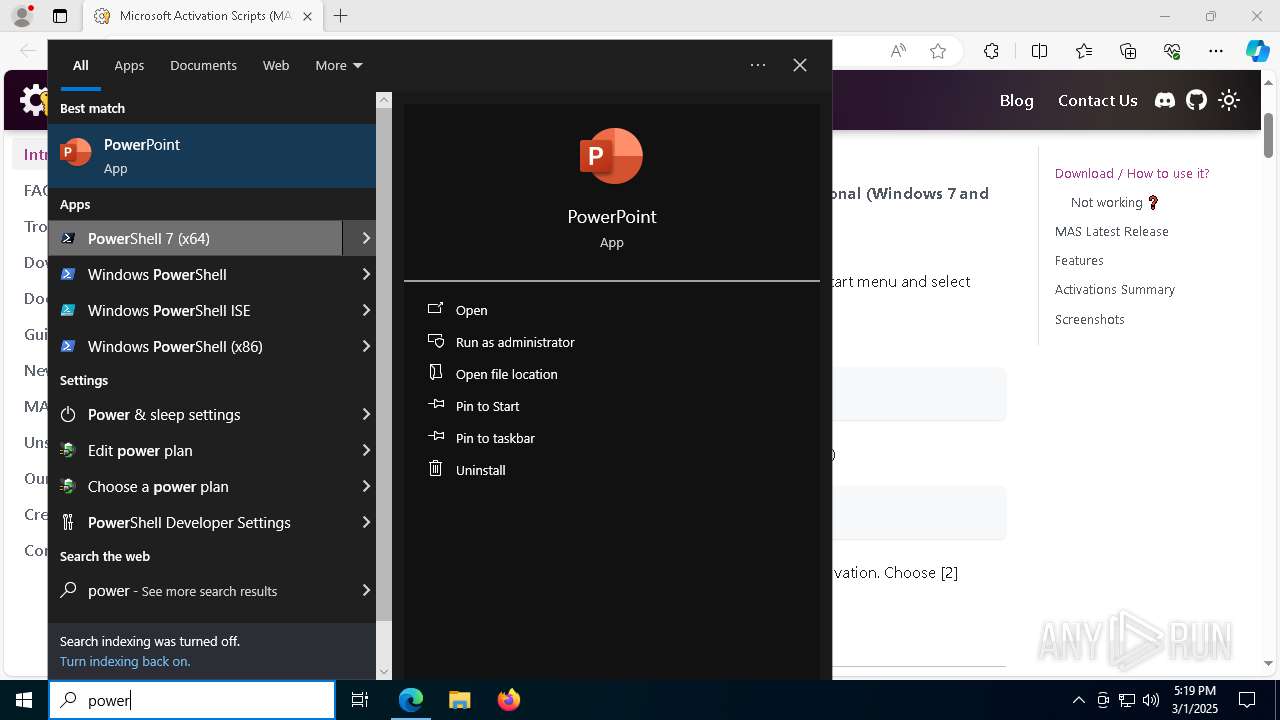
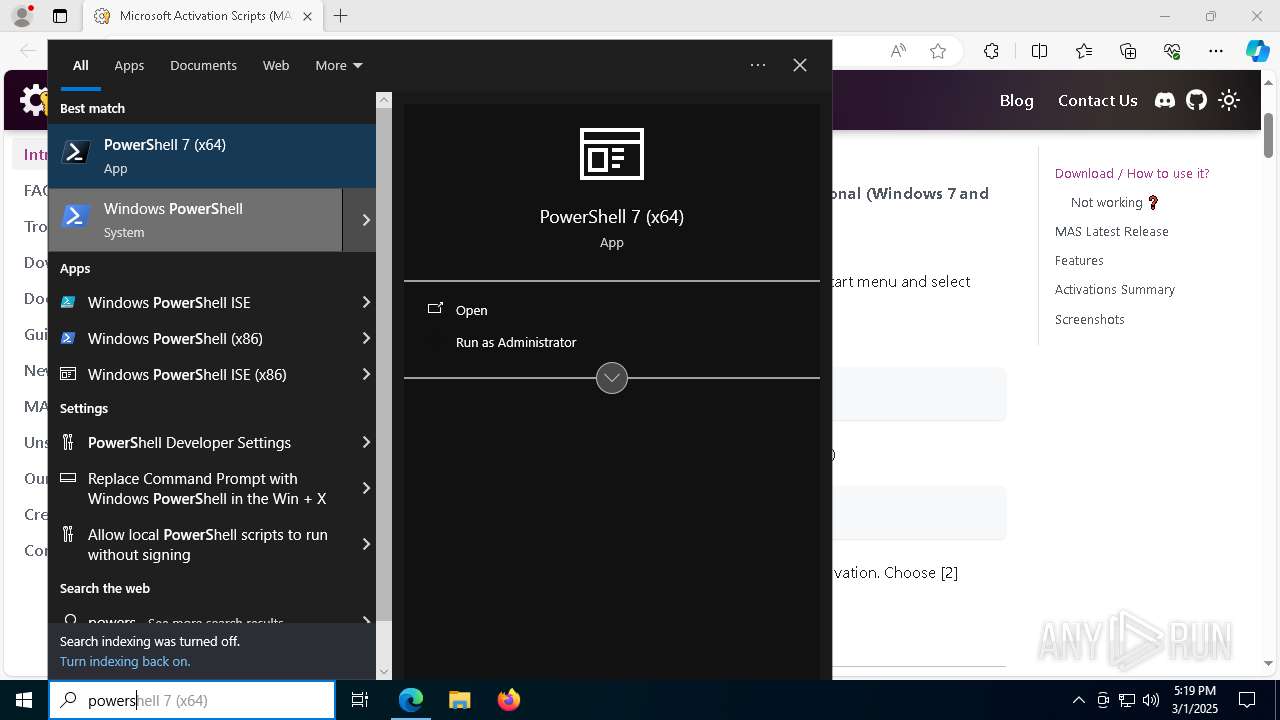
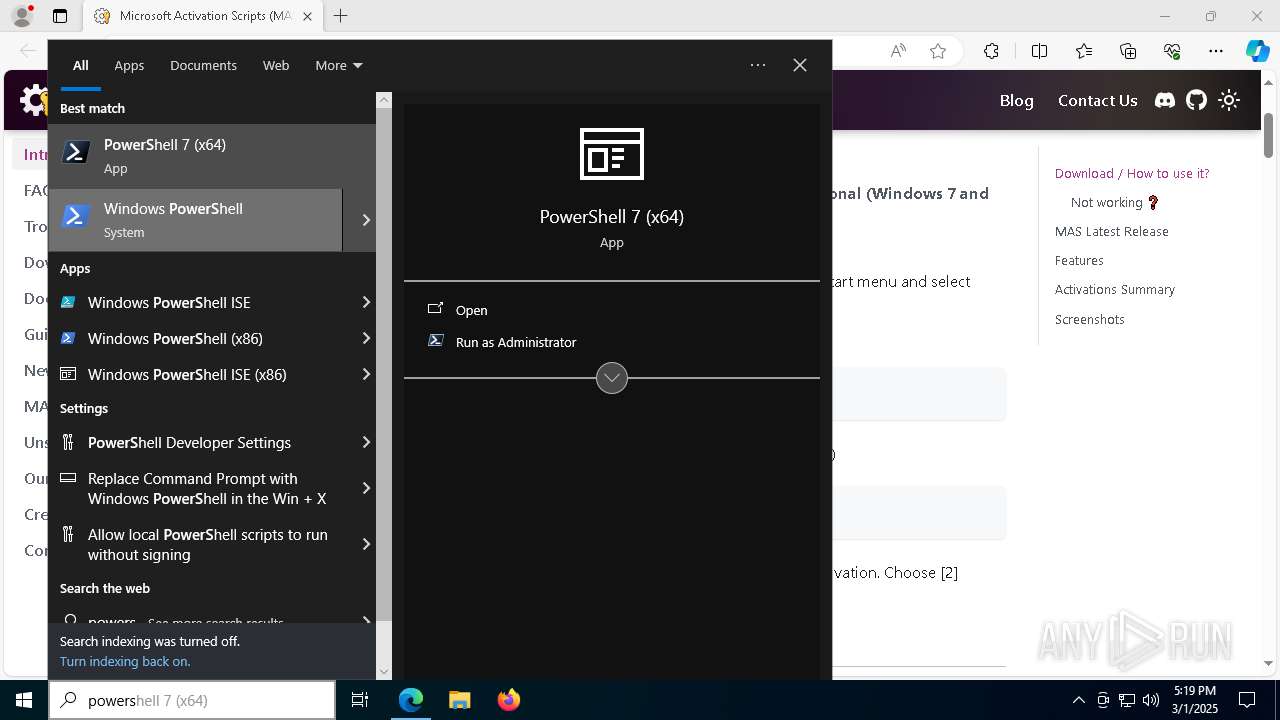
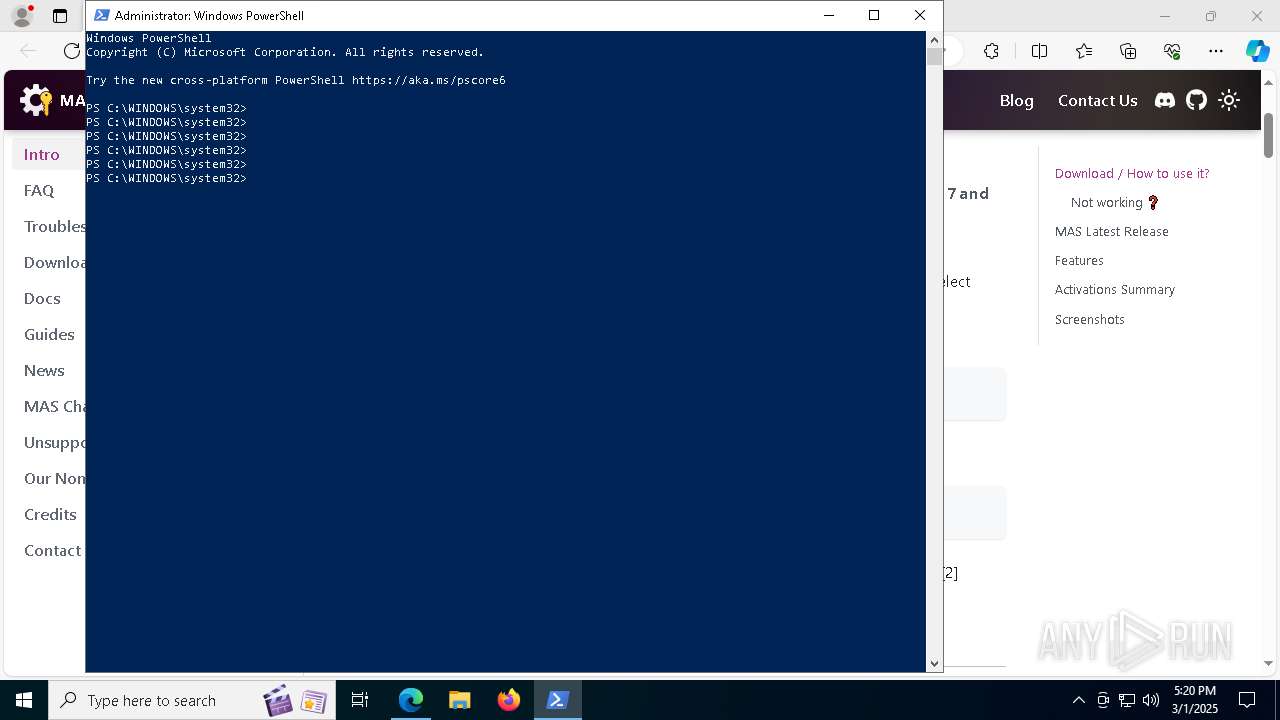
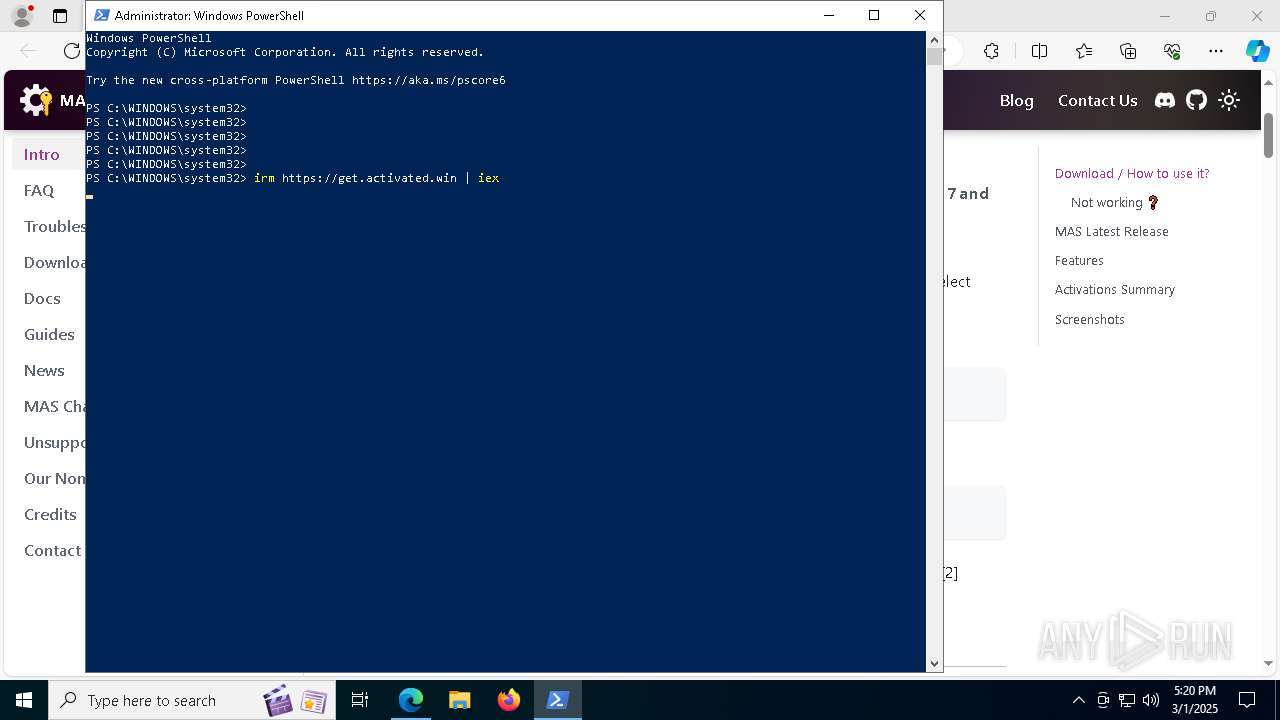
Manual execution by a user
- powershell.exe (PID: 6044)
Disables trace logs
- powershell.exe (PID: 6044)
Checks current location (POWERSHELL)
- powershell.exe (PID: 6044)
Gets a random number, or selects objects randomly from a collection (POWERSHELL)
- powershell.exe (PID: 6044)
- powershell.exe (PID: 1272)
- powershell.exe (PID: 8164)
Converts byte array into ASCII string (POWERSHELL)
- powershell.exe (PID: 6044)
- powershell.exe (PID: 1272)
- powershell.exe (PID: 8164)
Checks whether the specified file exists (POWERSHELL)
- powershell.exe (PID: 6044)
- powershell.exe (PID: 1272)
- powershell.exe (PID: 8164)
Checks operating system version
- cmd.exe (PID: 8512)
- cmd.exe (PID: 3020)
Starts MODE.COM to configure console settings
- mode.com (PID: 8784)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
243
Monitored processes
104
Malicious processes
4
Suspicious processes
6
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 496 | reg query "HKCU\Software\Microsoft\Windows\CurrentVersion\Explorer\User Shell Folders" /v Desktop | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 720 | "C:\WINDOWS\SystemApps\ShellExperienceHost_cw5n1h2txyewy\ShellExperienceHost.exe" -ServerName:App.AppXtk181tbxbce2qsex02s8tw7hfxa9xb3t.mca | C:\Windows\SystemApps\ShellExperienceHost_cw5n1h2txyewy\ShellExperienceHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Shell Experience Host Version: 10.0.19041.3758 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1052 | findstr /v "f7f81a39-5f63-5b42-9efd-1f13b5431005quot; "MAS_f176df47-11b8-480d-96f8-d3d7462f3ccf.cmd" | C:\Windows\System32\findstr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (QGREP) Utility Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1168 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=edge_search_indexer.mojom.SearchIndexerInterfaceBroker --lang=en-US --service-sandbox-type=search_indexer --message-loop-type-ui --no-appcompat-clear --mojo-platform-channel-handle=4500 --field-trial-handle=2632,i,3888868721864727491,17307888411528522727,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1184 | sc query Null | C:\Windows\System32\sc.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Service Control Manager Configuration Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1272 | powershell.exe "$f=[io.file]::ReadAllText('C:\Windows\Temp\MAS_f176df47-11b8-480d-96f8-d3d7462f3ccf.cmd') -split ':PStest:\s*';iex ($f[1])" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2140 | find /i "/S" | C:\Windows\System32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (grep) Utility Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2196 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2908 | find /i "/" | C:\Windows\System32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (grep) Utility Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3020 | "C:\WINDOWS\System32\cmd.exe" /c ""C:\Windows\Temp\MAS_f176df47-11b8-480d-96f8-d3d7462f3ccf.cmd" -el -qedit" | C:\Windows\System32\cmd.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
37 510
Read events
37 479
Write events
31
Delete events
0
Modification events
| (PID) Process: | (3192) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3192) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3192) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3192) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (3192) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: B76E8D68E18D2F00 | |||
| (PID) Process: | (3192) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 49A39768E18D2F00 | |||
| (PID) Process: | (3192) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\197226 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {3102F7F6-68B7-4F2E-ABCE-69D35CC36FC9} | |||
| (PID) Process: | (3192) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\197226 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {A81E0691-9350-4C15-90B8-DBA5A302B8F7} | |||
| (PID) Process: | (3192) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 92A1F668E18D2F00 | |||
| (PID) Process: | (3192) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | MicrosoftEdgeAutoLaunch_29EBC4579851B72EE312C449CF839B1A |
Value: "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --no-startup-window --win-session-start | |||
Executable files
8
Suspicious files
253
Text files
58
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3192 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF10becd.TMP | — | |
MD5:— | SHA256:— | |||
| 3192 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3192 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF10becd.TMP | — | |
MD5:— | SHA256:— | |||
| 3192 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3192 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF10bedd.TMP | — | |
MD5:— | SHA256:— | |||
| 3192 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3192 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF10beed.TMP | — | |
MD5:— | SHA256:— | |||
| 3192 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3192 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF10bf1c.TMP | — | |
MD5:— | SHA256:— | |||
| 3192 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
11
TCP/UDP connections
76
DNS requests
70
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
8608 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
4408 | BackgroundTransferHost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
2924 | SearchApp.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
4736 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/0529a13c-ea24-474d-87d7-66f668b071b4?P1=1741208980&P2=404&P3=2&P4=aIZeOgUVcXW0COWZo2of%2fSzZa7YtYHXIK5ch3xWyWykuhr1hUYmE3V7kkhgcVFN2tjGk9cWRGNqCBv%2bD660iJg%3d%3d | unknown | — | — | whitelisted |
4736 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/0529a13c-ea24-474d-87d7-66f668b071b4?P1=1741208980&P2=404&P3=2&P4=aIZeOgUVcXW0COWZo2of%2fSzZa7YtYHXIK5ch3xWyWykuhr1hUYmE3V7kkhgcVFN2tjGk9cWRGNqCBv%2bD660iJg%3d%3d | unknown | — | — | whitelisted |
4736 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/0529a13c-ea24-474d-87d7-66f668b071b4?P1=1741208980&P2=404&P3=2&P4=aIZeOgUVcXW0COWZo2of%2fSzZa7YtYHXIK5ch3xWyWykuhr1hUYmE3V7kkhgcVFN2tjGk9cWRGNqCBv%2bD660iJg%3d%3d | unknown | — | — | whitelisted |
8608 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
4736 | svchost.exe | HEAD | 200 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/8699fac5-cf38-4f97-a2f8-fb1e47f5e54e?P1=1741208980&P2=404&P3=2&P4=BtoexOZvYYAjVOet1Q%2bekYtHLqBNDj4USOiy1HOdbpbTFjsr7s%2bWc%2fkxsDlvLWPl%2b0sSg0CXtA80HIMZ7xJCUA%3d%3d | unknown | — | — | whitelisted |
4736 | svchost.exe | HEAD | 200 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/0529a13c-ea24-474d-87d7-66f668b071b4?P1=1741208980&P2=404&P3=2&P4=aIZeOgUVcXW0COWZo2of%2fSzZa7YtYHXIK5ch3xWyWykuhr1hUYmE3V7kkhgcVFN2tjGk9cWRGNqCBv%2bD660iJg%3d%3d | unknown | — | — | whitelisted |
4736 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/8699fac5-cf38-4f97-a2f8-fb1e47f5e54e?P1=1741208980&P2=404&P3=2&P4=BtoexOZvYYAjVOet1Q%2bekYtHLqBNDj4USOiy1HOdbpbTFjsr7s%2bWc%2fkxsDlvLWPl%2b0sSg0CXtA80HIMZ7xJCUA%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2104 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5496 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
7360 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
3192 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
7360 | msedge.exe | 104.21.22.3:443 | massgrave.dev | CLOUDFLARENET | — | unknown |
7360 | msedge.exe | 13.107.253.42:443 | edge-mobile-static.azureedge.net | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7360 | msedge.exe | 13.107.21.239:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7360 | msedge.exe | 13.107.6.158:443 | business.bing.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
massgrave.dev |
| unknown |
edge.microsoft.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
business.bing.com |
| whitelisted |
bzib.nelreports.net |
| whitelisted |
www.bing.com |
| whitelisted |
static.cloudflareinsights.com |
| whitelisted |